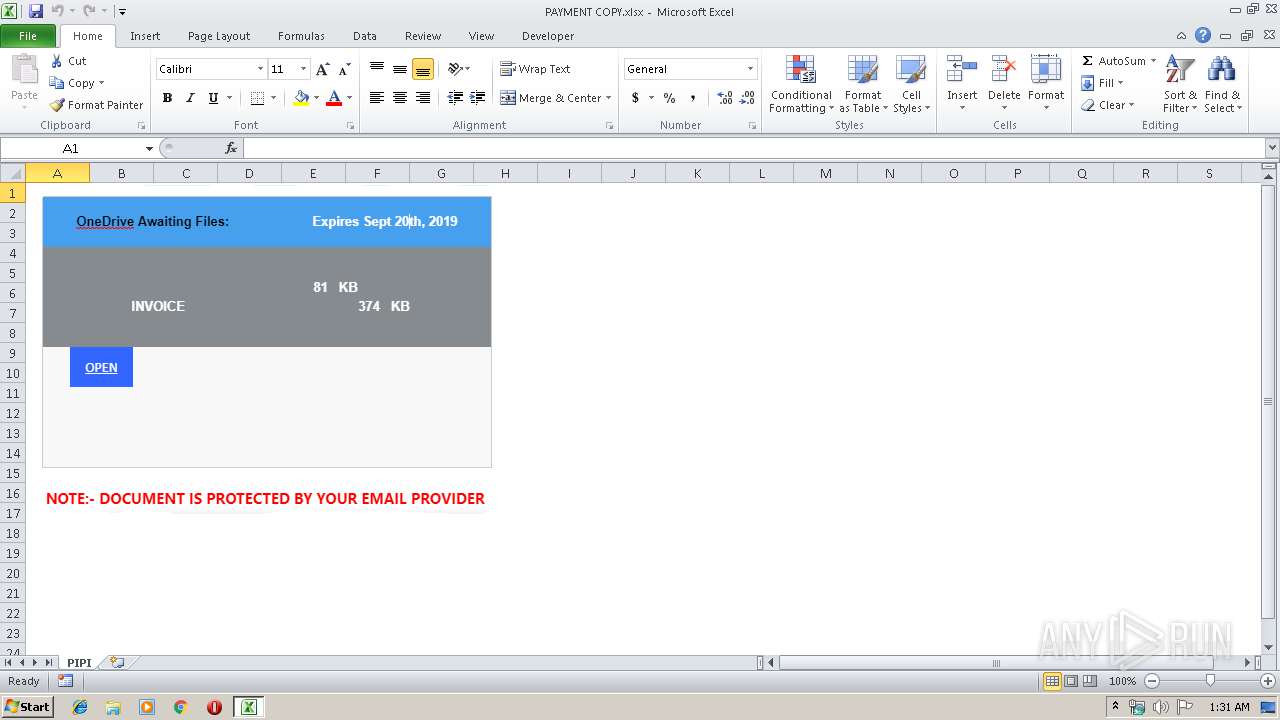
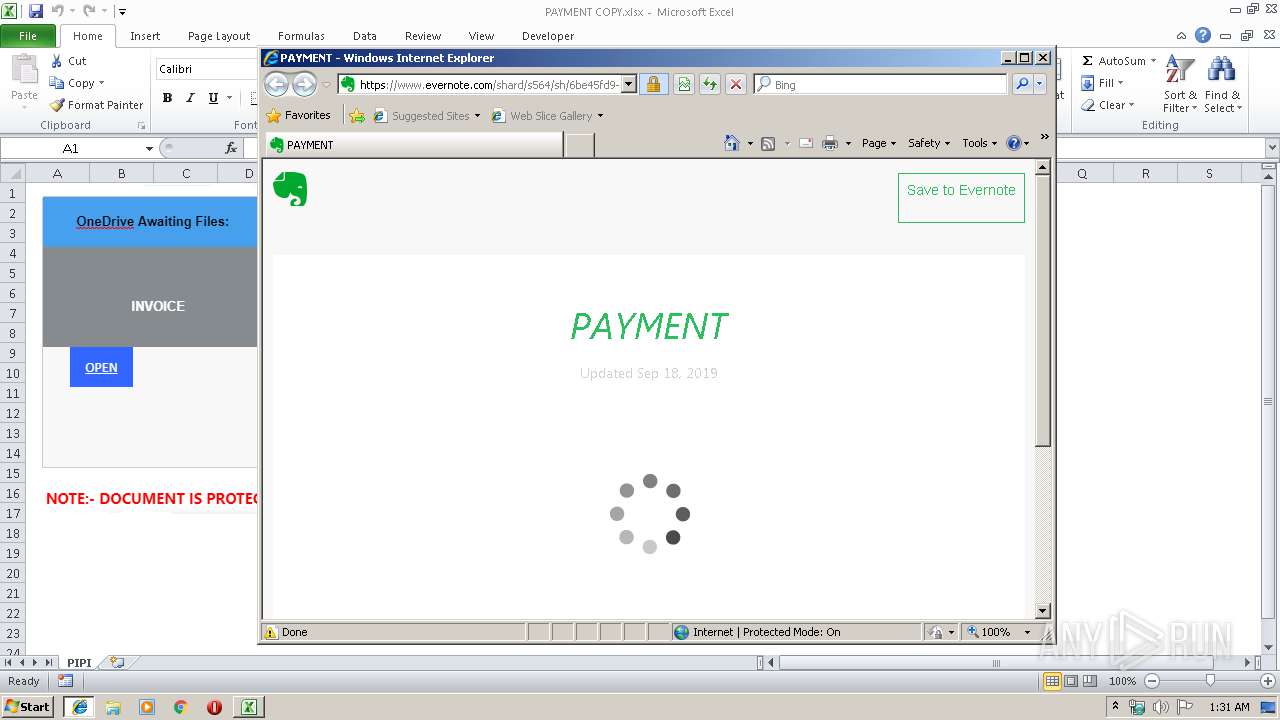
| File name: | PAYMENT COPY.xlsx |
| Full analysis: | https://app.any.run/tasks/c7ae65d6-2485-4d9b-9bc7-9711ffbfe3af |
| Verdict: | Malicious activity |
| Analysis date: | September 19, 2019, 00:30:45 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.openxmlformats-officedocument.spreadsheetml.sheet |
| File info: | Microsoft Excel 2007+ |
| MD5: | 80580CCB11C88147A73E1C7001BF835E |
| SHA1: | A0F349AAAB4D1FAA38399778BD868937028EE3D4 |
| SHA256: | DA3F984330691FC6A1DF9B73D040719964C55C234916CC67319E016D4ABE79FB |
| SSDEEP: | 384:bnO3vGMOcXRoUlM9z6RO6md5IbnW/anumTmz9MTGaacboyUVu:bnEvhXRoxqE5Sn4anumTmYGaUlQ |
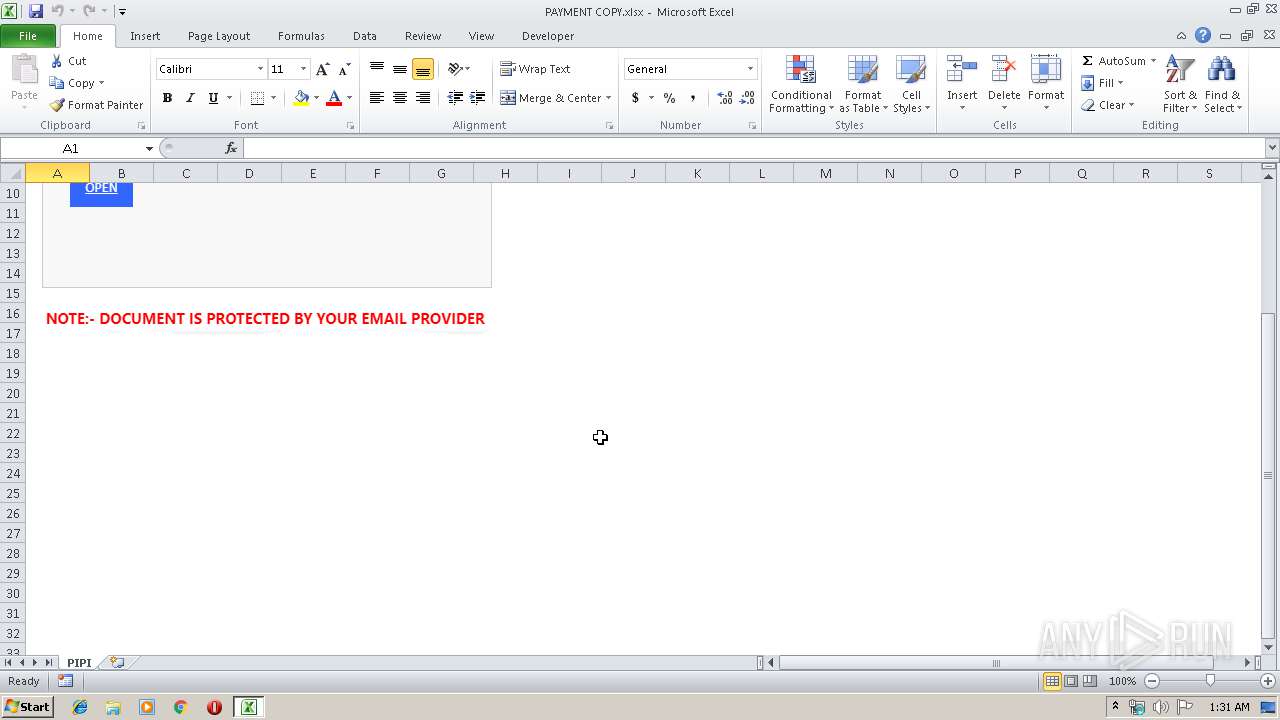
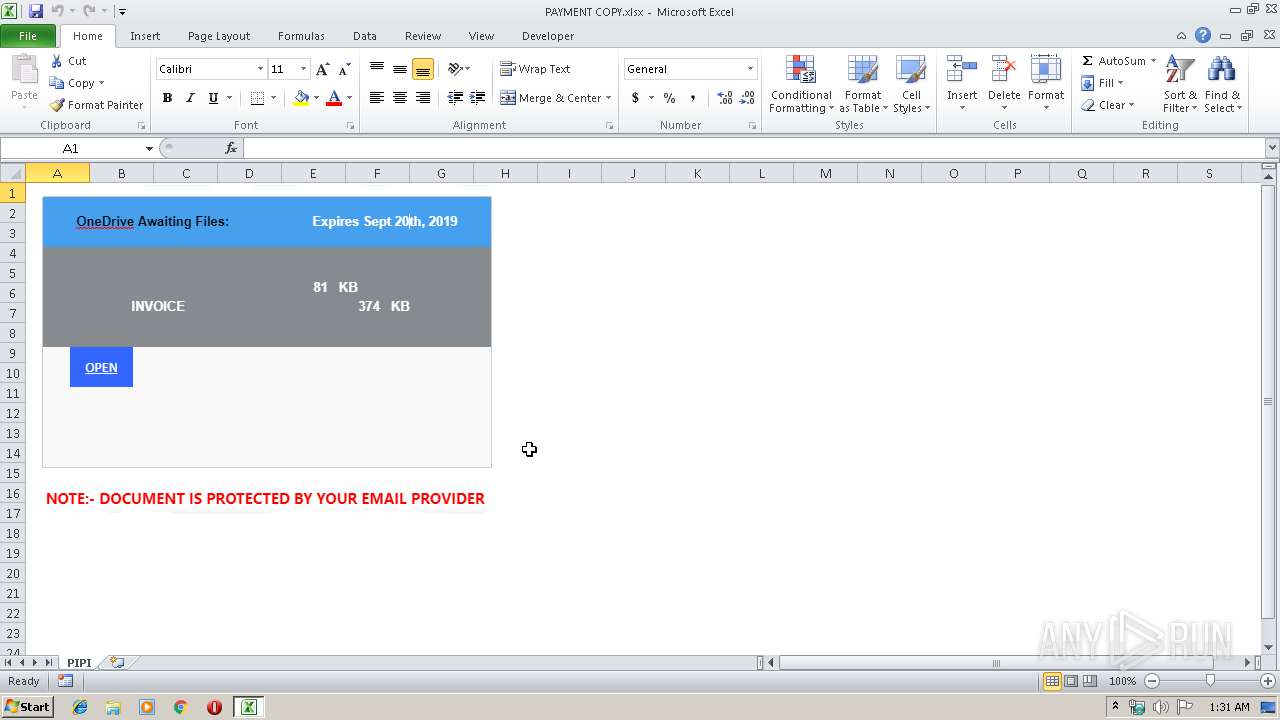
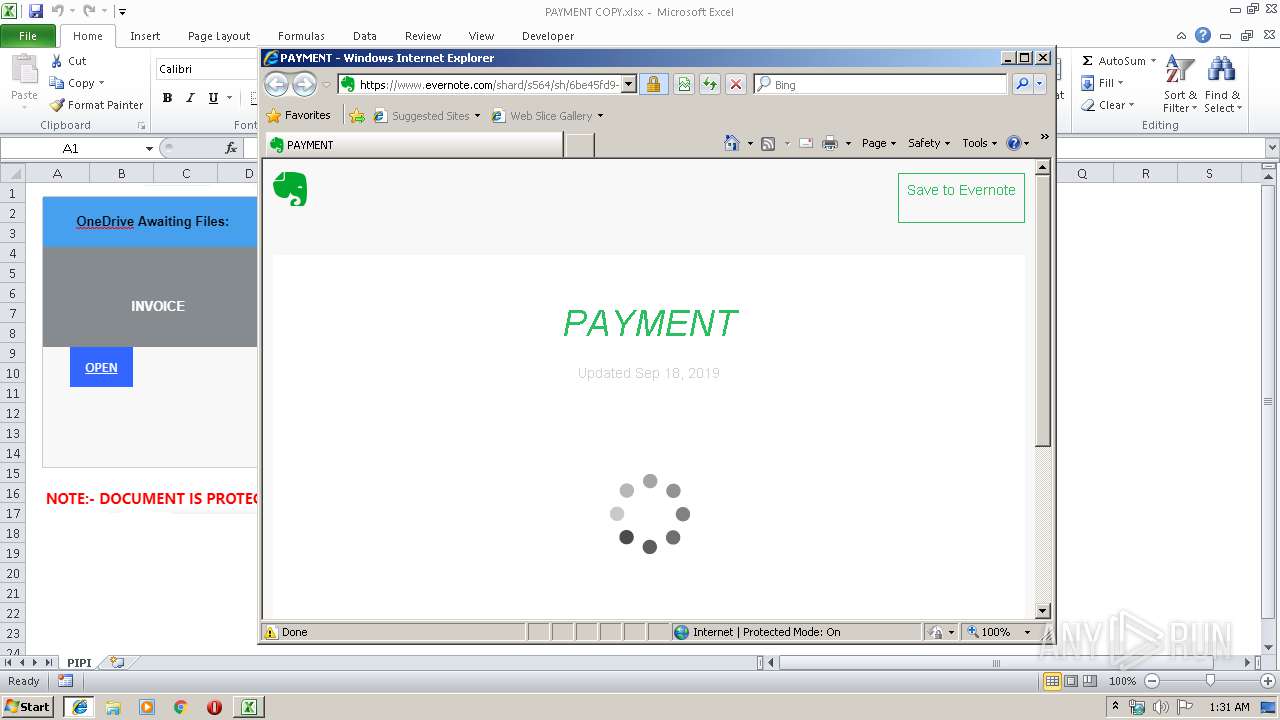
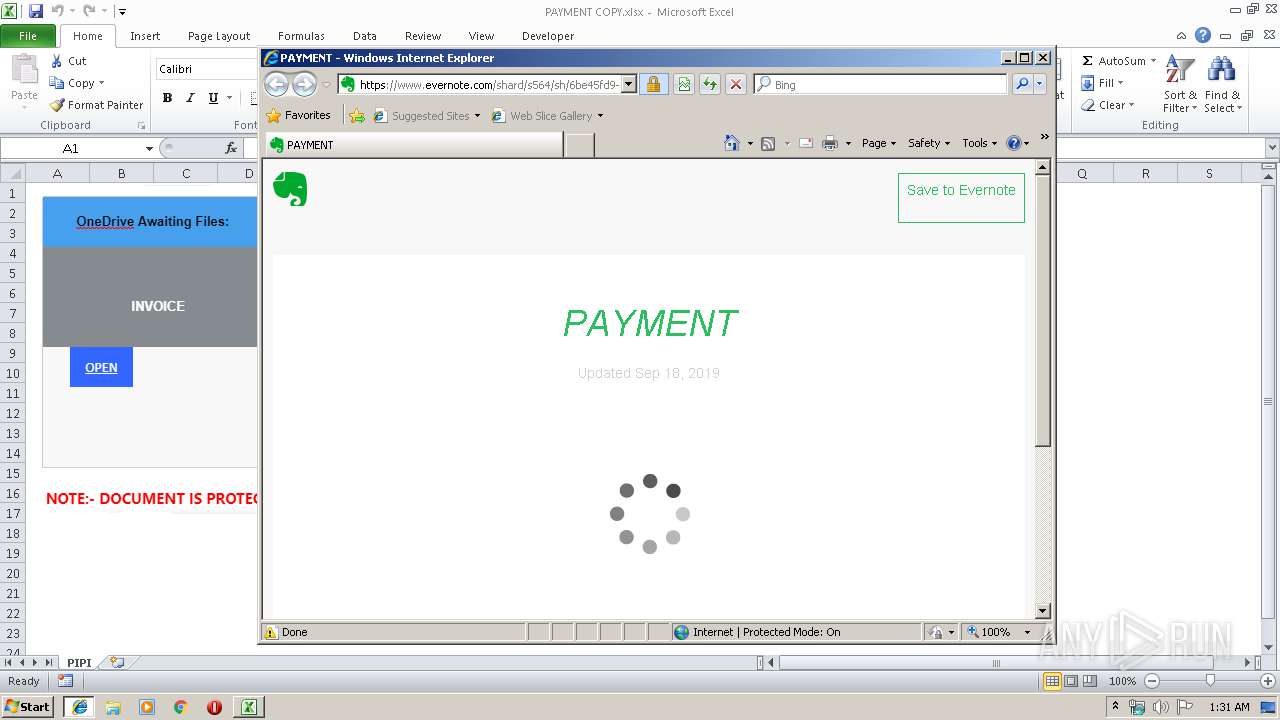
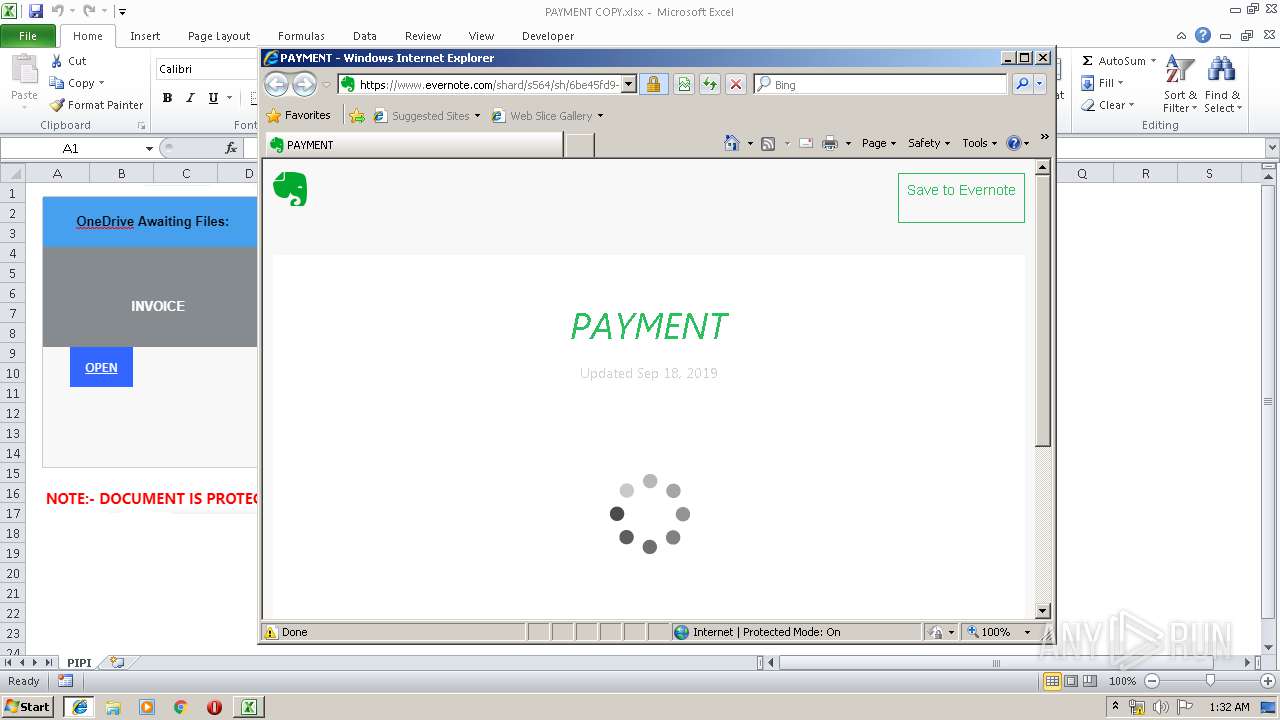
MALICIOUS
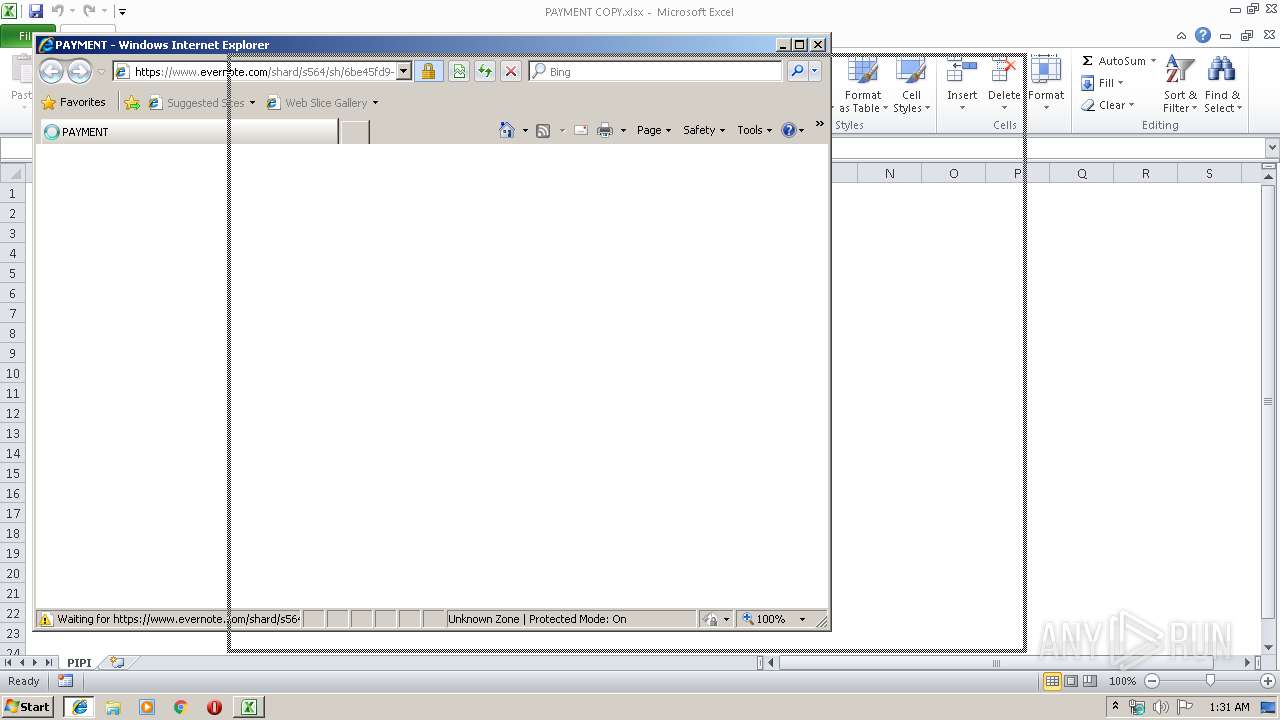
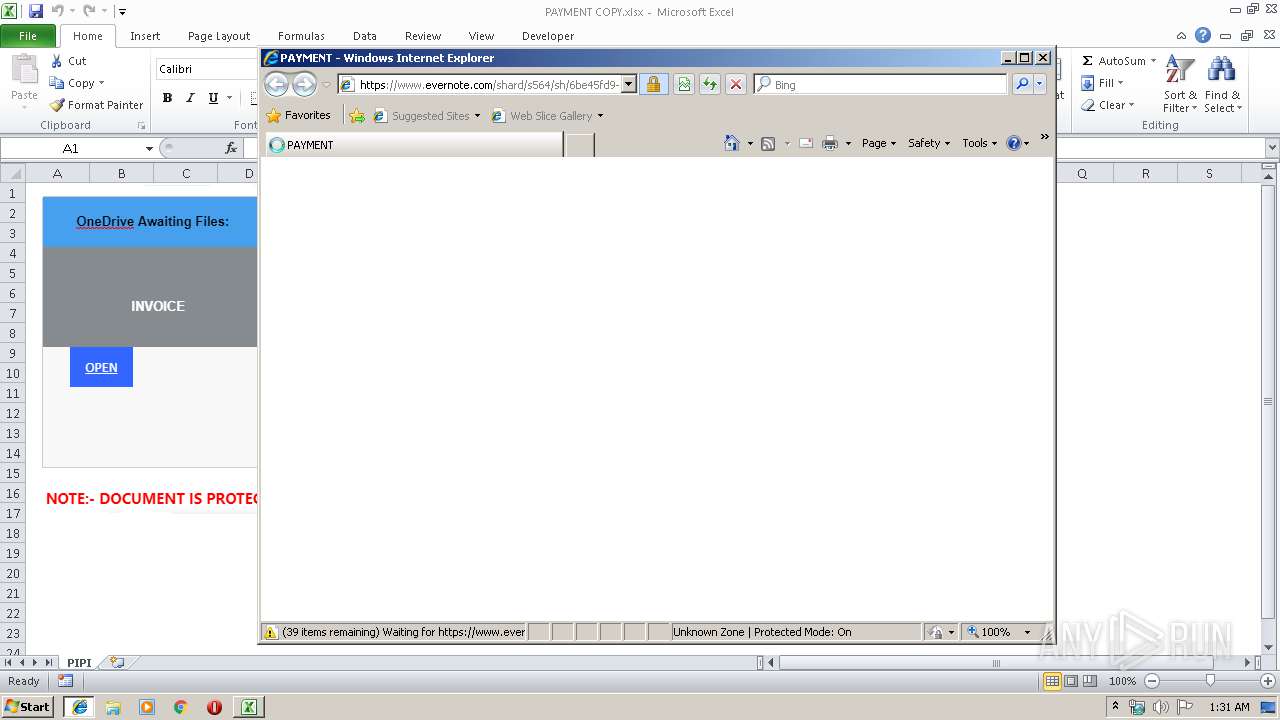
Unusual execution from Microsoft Office
- EXCEL.EXE (PID: 2732)
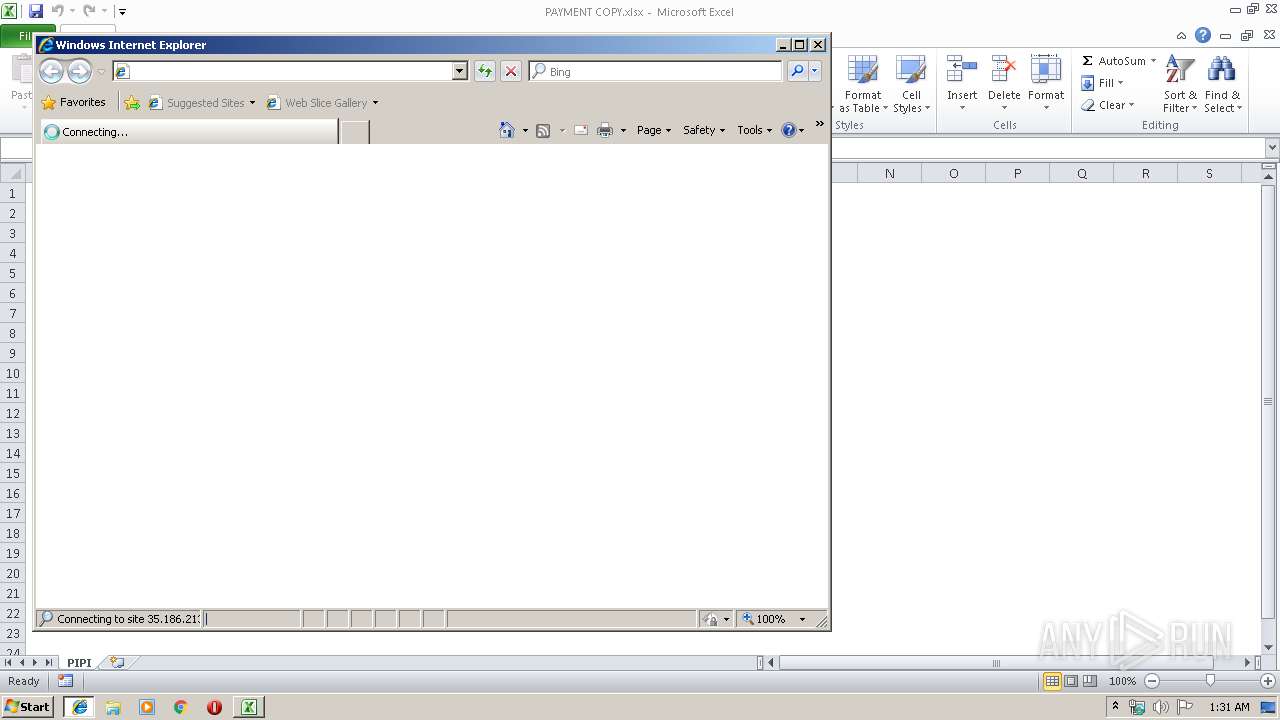
SUSPICIOUS
Starts Internet Explorer
- EXCEL.EXE (PID: 2732)
Executed via COM
- FlashUtil32_26_0_0_131_ActiveX.exe (PID: 2936)
INFO
Creates files in the user directory
- EXCEL.EXE (PID: 2732)
- iexplore.exe (PID: 2436)
- FlashUtil32_26_0_0_131_ActiveX.exe (PID: 2936)
Reads Microsoft Office registry keys
- EXCEL.EXE (PID: 2732)
Changes internet zones settings
- iexplore.exe (PID: 1248)
Reads Internet Cache Settings
- iexplore.exe (PID: 2436)
Reads internet explorer settings
- iexplore.exe (PID: 2436)
Dropped object may contain Bitcoin addresses
- iexplore.exe (PID: 2436)
Reads settings of System Certificates
- iexplore.exe (PID: 1248)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .xlsx | | | Excel Microsoft Office Open XML Format document (61.2) |
|---|---|---|
| .zip | | | Open Packaging Conventions container (31.5) |
| .zip | | | ZIP compressed archive (7.2) |
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0006 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 1980:01:01 00:00:00 |
| ZipCRC: | 0xfa08cdcc |
| ZipCompressedSize: | 361 |
| ZipUncompressedSize: | 1202 |
| ZipFileName: | [Content_Types].xml |
XMP
| Title: | Capture |
|---|
XML
| LastModifiedBy: | nelz163 163 |
|---|---|
| CreateDate: | 2019:09:18 09:51:44Z |
| ModifyDate: | 2019:09:18 09:51:44Z |
| Application: | Microsoft Excel |
| DocSecurity: | None |
| ScaleCrop: | No |
| HeadingPairs: |
|
| TitlesOfParts: | PIPI |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| AppVersion: | 16.03 |
Total processes
37
Monitored processes
4
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1248 | "C:\Program Files\Internet Explorer\iexplore.exe" -nohome | C:\Program Files\Internet Explorer\iexplore.exe | EXCEL.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2436 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:1248 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2732 | "C:\Program Files\Microsoft Office\Office14\EXCEL.EXE" /dde | C:\Program Files\Microsoft Office\Office14\EXCEL.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Excel Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2936 | C:\Windows\system32\Macromed\Flash\FlashUtil32_26_0_0_131_ActiveX.exe -Embedding | C:\Windows\system32\Macromed\Flash\FlashUtil32_26_0_0_131_ActiveX.exe | — | svchost.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: MEDIUM Description: Adobe® Flash® Player Installer/Uninstaller 26.0 r0 Exit code: 0 Version: 26,0,0,131 Modules
| |||||||||||||||
Total events
1 043
Read events
931
Write events
103
Delete events
9
Modification events
| (PID) Process: | (2732) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency\StartupItems |
| Operation: | write | Name: | bq! |
Value: 62712100AC0A0000010000000000000000000000 | |||
| (PID) Process: | (2732) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2732) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (2732) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel |
| Operation: | write | Name: | MTTT |
Value: AC0A0000D87AA284816ED50100000000 | |||
| (PID) Process: | (2732) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency\StartupItems |
| Operation: | delete value | Name: | bq! |
Value: 62712100AC0A0000010000000000000000000000 | |||
| (PID) Process: | (2732) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency\StartupItems |
| Operation: | delete key | Name: | |
Value: | |||
| (PID) Process: | (2732) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency |
| Operation: | delete key | Name: | |
Value: | |||
| (PID) Process: | (2732) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2732) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2732) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency\DocumentRecovery\16A7FD |
| Operation: | write | Name: | 16A7FD |
Value: 04000000AC0A00003300000043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C004C006F00630061006C005C00540065006D0070005C005000410059004D0045004E005400200043004F00500059002E0078006C0073007800000000002200000043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C004C006F00630061006C005C00540065006D0070005C000100000000000000B0691686816ED501FDA71600FDA7160000000000AC020000001000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
0
Suspicious files
21
Text files
44
Unknown types
27
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2732 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\CVRA1E2.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2732 | EXCEL.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\LH043OAM\cad388c45ebf7d9a9a1b7981d0d694fb[1].txt | — | |
MD5:— | SHA256:— | |||
| 1248 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\LH043OAM\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 1248 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 2436 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\6H0VEGU4\cad388c45ebf7d9a9a1b7981d0d694fb[1].txt | — | |
MD5:— | SHA256:— | |||
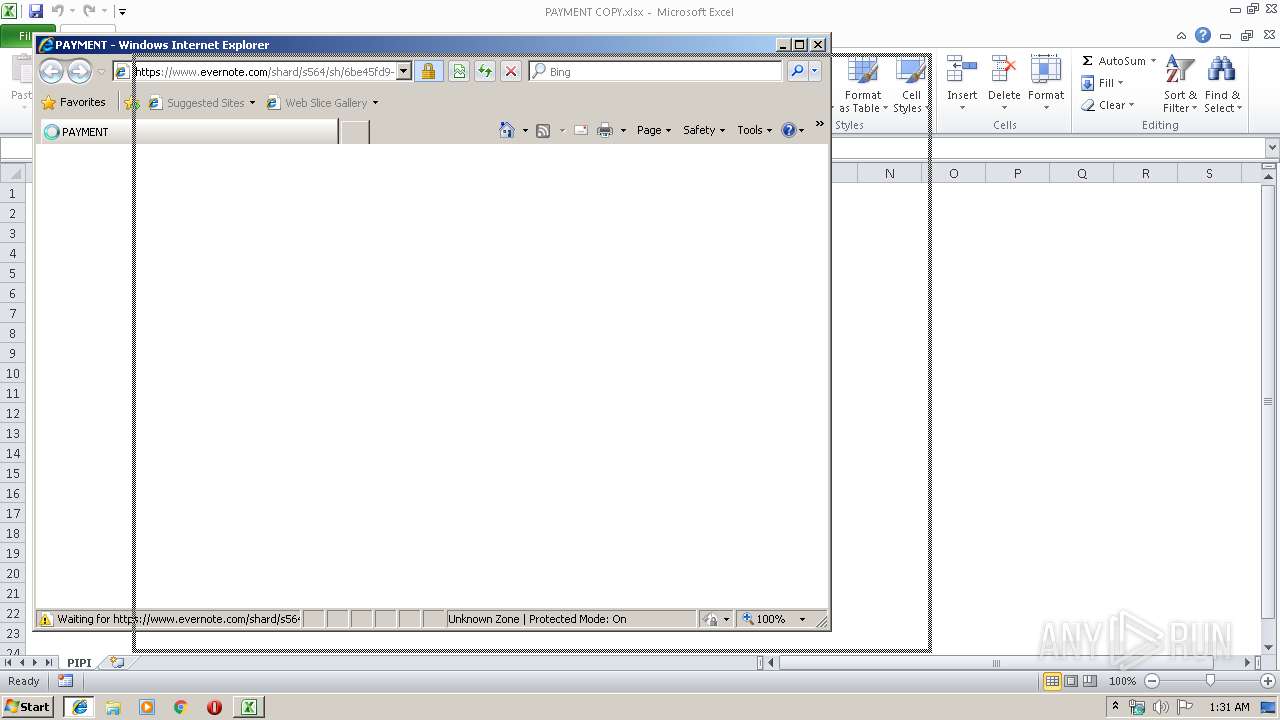
| 2436 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\admin@evernote[2].txt | — | |
MD5:— | SHA256:— | |||
| 2732 | EXCEL.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\admin@evernote[1].txt | text | |
MD5:— | SHA256:— | |||
| 2436 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\admin@www.evernote[1].txt | — | |
MD5:— | SHA256:— | |||
| 2436 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\index.dat | dat | |
MD5:— | SHA256:— | |||
| 2436 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\6H0VEGU4\cad388c45ebf7d9a9a1b7981d0d694fb[1].htm | html | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
51
DNS requests
6
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1248 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1248 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
2436 | iexplore.exe | 216.58.207.78:443 | www.google-analytics.com | Google Inc. | US | whitelisted |
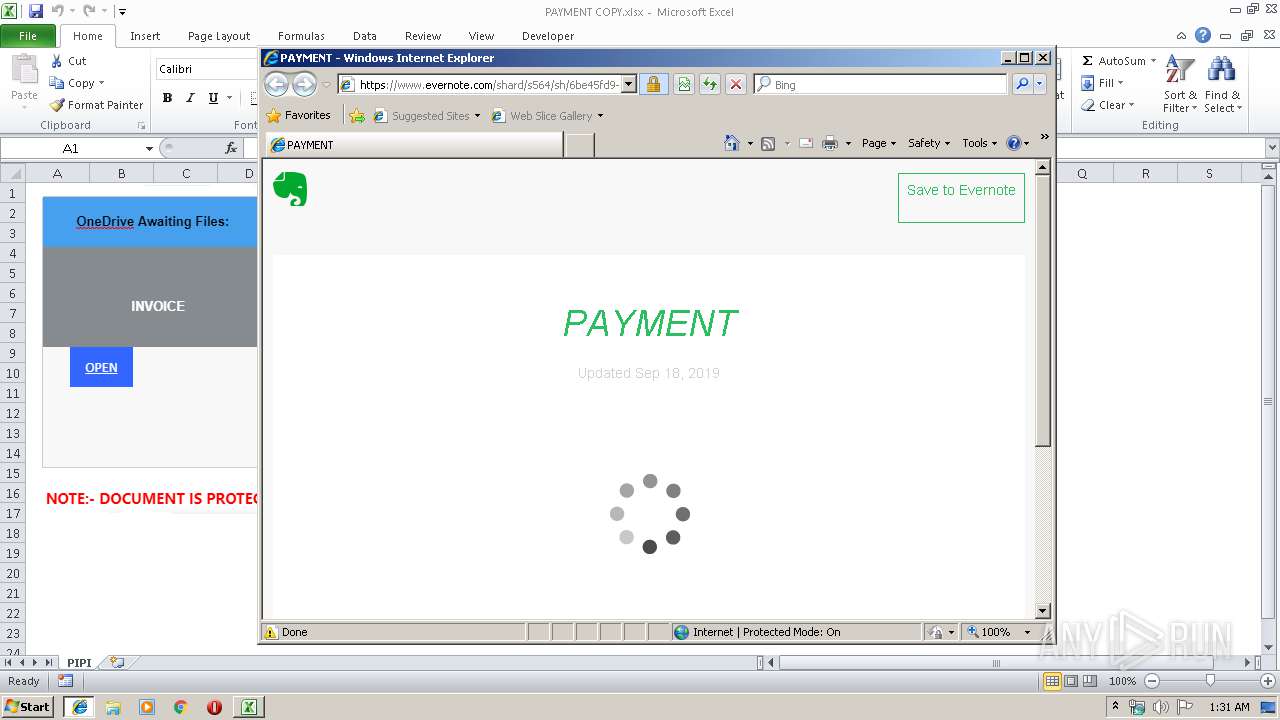
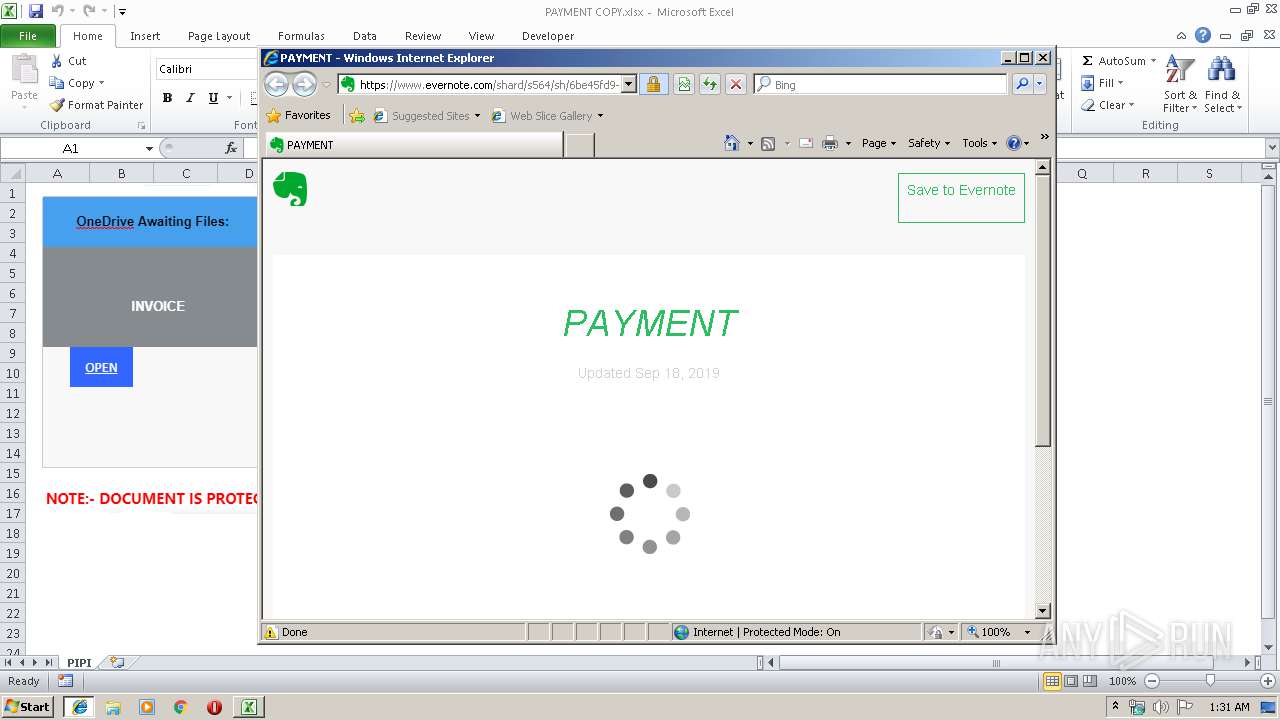
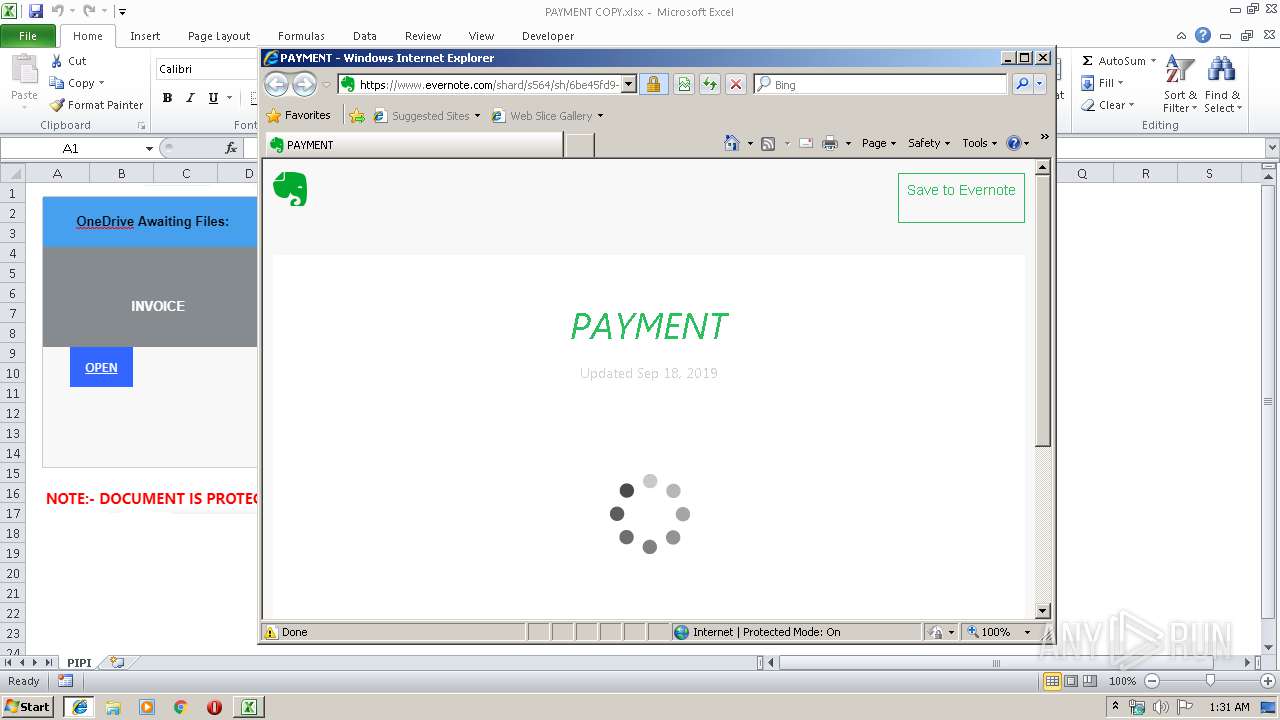
2732 | EXCEL.EXE | 35.186.213.138:443 | www.evernote.com | Google Inc. | US | unknown |
2436 | iexplore.exe | 35.186.213.138:443 | www.evernote.com | Google Inc. | US | unknown |
2436 | iexplore.exe | 173.194.76.155:443 | stats.g.doubleclick.net | Google Inc. | US | whitelisted |
— | — | 172.217.21.196:443 | www.google.com | Google Inc. | US | whitelisted |
1248 | iexplore.exe | 35.186.213.138:443 | www.evernote.com | Google Inc. | US | unknown |
2436 | iexplore.exe | 216.58.210.3:443 | www.google.lt | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.evernote.com |
| whitelisted |
www.bing.com |
| whitelisted |
www.google-analytics.com |
| whitelisted |
stats.g.doubleclick.net |
| whitelisted |
www.google.com |
| malicious |
www.google.lt |
| whitelisted |