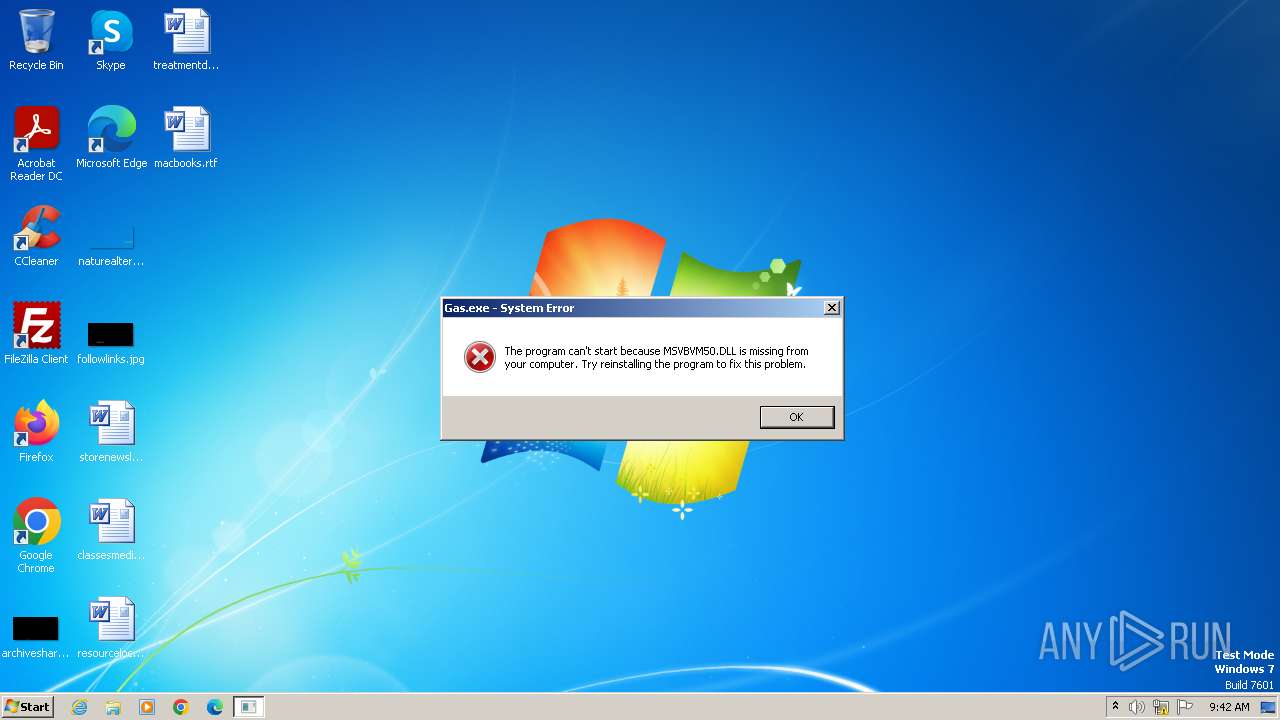
| File name: | Gas.exe |
| Full analysis: | https://app.any.run/tasks/b51b97e0-c6b2-453c-8336-caa0dc9738dc |
| Verdict: | Malicious activity |
| Analysis date: | May 06, 2024, 08:42:04 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | E7AF185503236E623705368A443A17D9 |
| SHA1: | 863084D6E7F3ED1BA6CC43F0746445B9AD218474 |
| SHA256: | DA3F40B66CC657EA33DBF547EB05D8D4FB5FB5CF753689D0222039A3292C937A |
| SSDEEP: | 192:KtRj6/XFyk9YPdXTH08W8c3LXLtYmEBI9qHVDEV4:WV6fFy2Ylz0TiBIw1Dc4 |
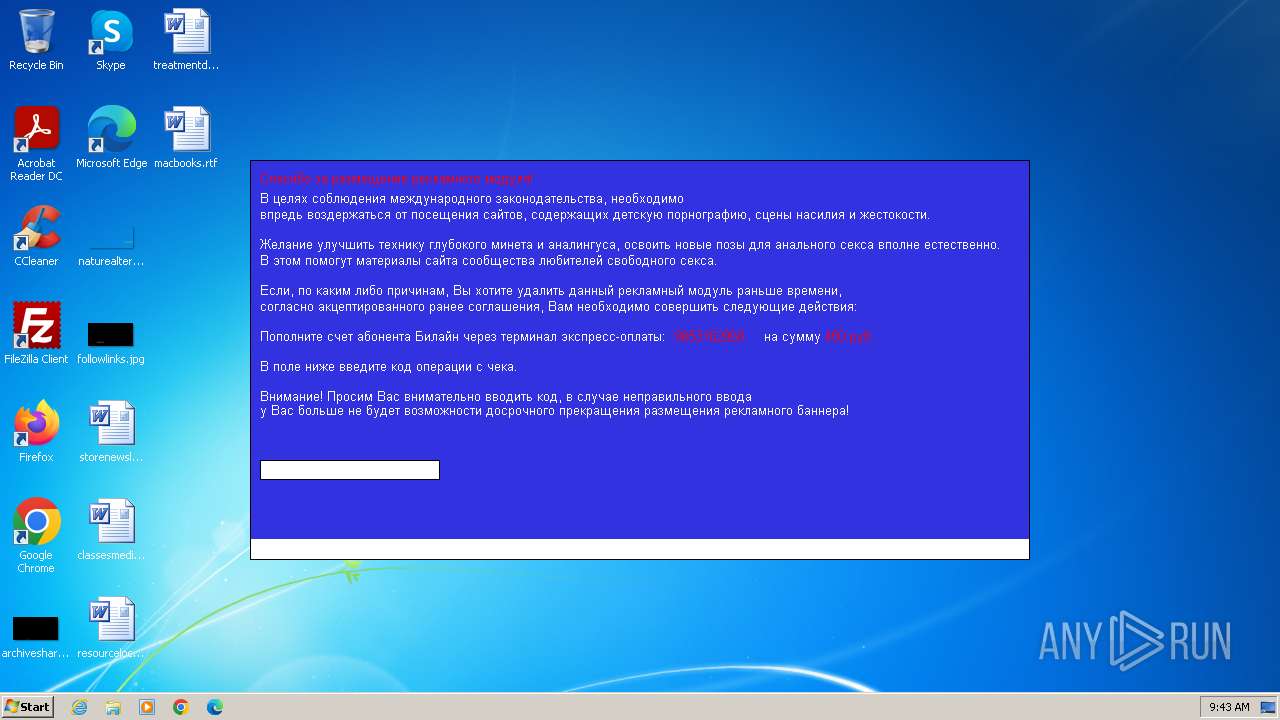
MALICIOUS
Drops the executable file immediately after the start
- Gas.exe (PID: 3988)
Changes the autorun value in the registry
- reg.exe (PID: 2040)
- reg.exe (PID: 1872)
SUSPICIOUS
The system shut down or reboot
- HMBlocker.exe (PID: 4048)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 1024)
- cmd.exe (PID: 1136)
Reads security settings of Internet Explorer
- HMBlocker.exe (PID: 4048)
Starts CMD.EXE for commands execution
- HMBlocker.exe (PID: 4048)
Reads the Internet Settings
- HMBlocker.exe (PID: 4048)
- sipnotify.exe (PID: 1556)
The process executes via Task Scheduler
- ctfmon.exe (PID: 1576)
- sipnotify.exe (PID: 1556)
Reads settings of System Certificates
- sipnotify.exe (PID: 1556)
INFO
Manual execution by a user
- HMBlocker.exe (PID: 4048)
- IMEKLMG.EXE (PID: 1820)
- IMEKLMG.EXE (PID: 312)
- 2503326475.exe (PID: 2060)
- cmd.exe (PID: 2088)
Reads the computer name
- HMBlocker.exe (PID: 4048)
- IMEKLMG.EXE (PID: 1820)
- IMEKLMG.EXE (PID: 312)
- 2503326475.exe (PID: 2060)
Checks supported languages
- HMBlocker.exe (PID: 4048)
- IMEKLMG.EXE (PID: 312)
- IMEKLMG.EXE (PID: 1820)
- 2503326475.exe (PID: 2060)
Process checks whether UAC notifications are on
- IMEKLMG.EXE (PID: 1820)
- IMEKLMG.EXE (PID: 312)
Reads security settings of Internet Explorer
- sipnotify.exe (PID: 1556)
Reads the software policy settings
- sipnotify.exe (PID: 1556)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable Microsoft Visual Basic 5 (92.7) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (2.7) |
| .exe | | | Win32 Executable (generic) (1.8) |
| .exe | | | Win16/32 Executable Delphi generic (0.8) |
| .exe | | | Generic Win/DOS Executable (0.8) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 1998:03:12 06:32:23+00:00 |
| ImageFileCharacteristics: | Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 4.2 |
| CodeSize: | 12800 |
| InitializedDataSize: | 11776 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1038 |
| OSVersion: | 4 |
| ImageVersion: | 1 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| Comments: | We're Cookin With Gas Now. |
| CompanyName: | PCS Inc. |
| FileDescription: | Something :) |
| LegalCopyright: | Copyright 1998 PCS Inc. |
| ProductName: | Happy Program. |
| FileVersion: | 1 |
| ProductVersion: | 1 |
| InternalName: | Virus |
| OriginalFileName: | Virus.exe |
Total processes
88
Monitored processes
13
Malicious processes
1
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 312 | "C:\Program Files\Common Files\microsoft shared\IME14\SHARED\IMEKLMG.EXE" /SetPreload /JPN /Log | C:\Program Files\Common Files\microsoft shared\IME14\SHARED\IMEKLMG.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Office IME 2010 Exit code: 1 Version: 14.0.4734.1000 Modules
| |||||||||||||||
| 1024 | "C:\Windows\System32\cmd.exe" /c REG ADD HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run /v 2503326475 /t REG_SZ /d "C:\Users\admin\2503326475\2503326475.exe" /f | C:\Windows\System32\cmd.exe | — | HMBlocker.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1136 | "C:\Windows\System32\cmd.exe" /c REG ADD HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\RunOnce /v 2503326475_del /t REG_SZ /d "cmd /c del \"C:\Users\admin\Desktop\HMBlocker.exe\"" /f | C:\Windows\System32\cmd.exe | — | HMBlocker.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1556 | C:\Windows\system32\sipnotify.exe -LogonOrUnlock | C:\Windows\System32\sipnotify.exe | taskeng.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: sipnotify Exit code: 0 Version: 6.1.7602.20480 (win7sp1_ldr_escrow.191010-1716) Modules
| |||||||||||||||
| 1576 | C:\Windows\System32\ctfmon.exe | C:\Windows\System32\ctfmon.exe | — | taskeng.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: CTF Loader Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1820 | "C:\Program Files\Common Files\microsoft shared\IME14\SHARED\IMEKLMG.EXE" /SetPreload /KOR /Log | C:\Program Files\Common Files\microsoft shared\IME14\SHARED\IMEKLMG.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Office IME 2010 Exit code: 1 Version: 14.0.4734.1000 Modules
| |||||||||||||||
| 1872 | REG ADD HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\RunOnce /v 2503326475_del /t REG_SZ /d "cmd /c del \"C:\Users\admin\Desktop\HMBlocker.exe\"" /f | C:\Windows\System32\reg.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2040 | REG ADD HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run /v 2503326475 /t REG_SZ /d "C:\Users\admin\2503326475\2503326475.exe" /f | C:\Windows\System32\reg.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2060 | "C:\Users\admin\2503326475\2503326475.exe" | C:\Users\admin\2503326475\2503326475.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Modules
| |||||||||||||||
| 2088 | "C:\Windows\System32\cmd.exe" /c del "C:\Users\admin\Desktop\HMBlocker.exe" | C:\Windows\System32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
4 877
Read events
4 816
Write events
48
Delete events
13
Modification events
| (PID) Process: | (4048) HMBlocker.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (4048) HMBlocker.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (4048) HMBlocker.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (4048) HMBlocker.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (2040) reg.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | 2503326475 |
Value: C:\Users\admin\2503326475\2503326475.exe | |||
| (PID) Process: | (1872) reg.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\RunOnce |
| Operation: | write | Name: | 2503326475_del |
Value: cmd /c del "C:\Users\admin\Desktop\HMBlocker.exe" | |||
| (PID) Process: | (1576) ctfmon.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run |
| Operation: | delete value | Name: | internat.exe |
Value: | |||
| (PID) Process: | (312) IMEKLMG.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\IMEJP\14.0 |
| Operation: | write | Name: | SetPreload |
Value: 1 | |||
| (PID) Process: | (1820) IMEKLMG.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\IMEKR\14.0 |
| Operation: | write | Name: | SetPreload |
Value: 1 | |||
| (PID) Process: | (1556) sipnotify.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\182\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
Executable files
0
Suspicious files
1
Text files
6
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1556 | sipnotify.exe | C:\Users\admin\AppData\Local\microsoft\windows\SipNotify\eoscontent\main.jpg | image | |
MD5:B342ACE63F77961249A084C61EABC884 | SHA256:E5067BBA2095B5DA7C3171EC116E9A92337E24E471339B0860A160076EFE49B9 | |||
| 1556 | sipnotify.exe | C:\Users\admin\AppData\Local\microsoft\windows\SipNotify\eoscontent\script.js | text | |
MD5:A2682382967C351F7ED21762F9E5DE9E | SHA256:36B1D26F1EC69685648C0528C2FCE95A3C2DBECF828CDFA4A8B4239A15B644A2 | |||
| 1556 | sipnotify.exe | C:\Users\admin\AppData\Local\microsoft\windows\SipNotify\eoscontent\microsoft-logo.png | image | |
MD5:B7C73A0CFBA68CC70C35EF9C63703CE4 | SHA256:1D8B27A0266FF526CF95447F3701592A908848467D37C09A00A2516C1F29A013 | |||
| 1556 | sipnotify.exe | C:\Users\admin\AppData\Local\microsoft\windows\SipNotify\eoscontent\styles.css | text | |
MD5:3383EEF350240253D7C2C2564381B3CB | SHA256:85443493D86D6D7FB0E07BC9705DFC9C858086FBA1B0E508092AB328D5F145E8 | |||
| 2060 | 2503326475.exe | C:\Users\admin\2503326475\T | text | |
MD5:CEE631121C2EC9232F3A2F028AD5C89B | SHA256:0604CD3138FEED202EF293E062DA2F4720F77A05D25EE036A7A01C9CFCDD1F0A | |||
| 1556 | sipnotify.exe | C:\Users\admin\AppData\Local\microsoft\windows\SipNotify\eoscontent\metadata.json | binary | |
MD5:E8A970BA6CE386EED9A5E724F26212A6 | SHA256:7E06107D585D8FC7870998F3856DCC3E35800AA97E4406AAB83BC8444B6CBDE3 | |||
| 1556 | sipnotify.exe | C:\Users\admin\AppData\Local\microsoft\windows\SipNotify\eoscontent\en-us.html | html | |
MD5:9752942B57692148B9F614CF4C119A36 | SHA256:E31B834DD53FA6815F396FC09C726636ABF98F3367F0CF1590EF5EB3801C75D1 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
10
DNS requests
1
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1556 | sipnotify.exe | HEAD | 200 | 2.23.65.216:80 | http://query.prod.cms.rt.microsoft.com/cms/api/am/binary/RE2JgkA?v=133594621866250000 | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 224.0.0.252:5355 | — | — | — | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1088 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
1096 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
1556 | sipnotify.exe | 2.23.65.216:80 | query.prod.cms.rt.microsoft.com | AKAMAI-AS | DE | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
query.prod.cms.rt.microsoft.com |
| whitelisted |