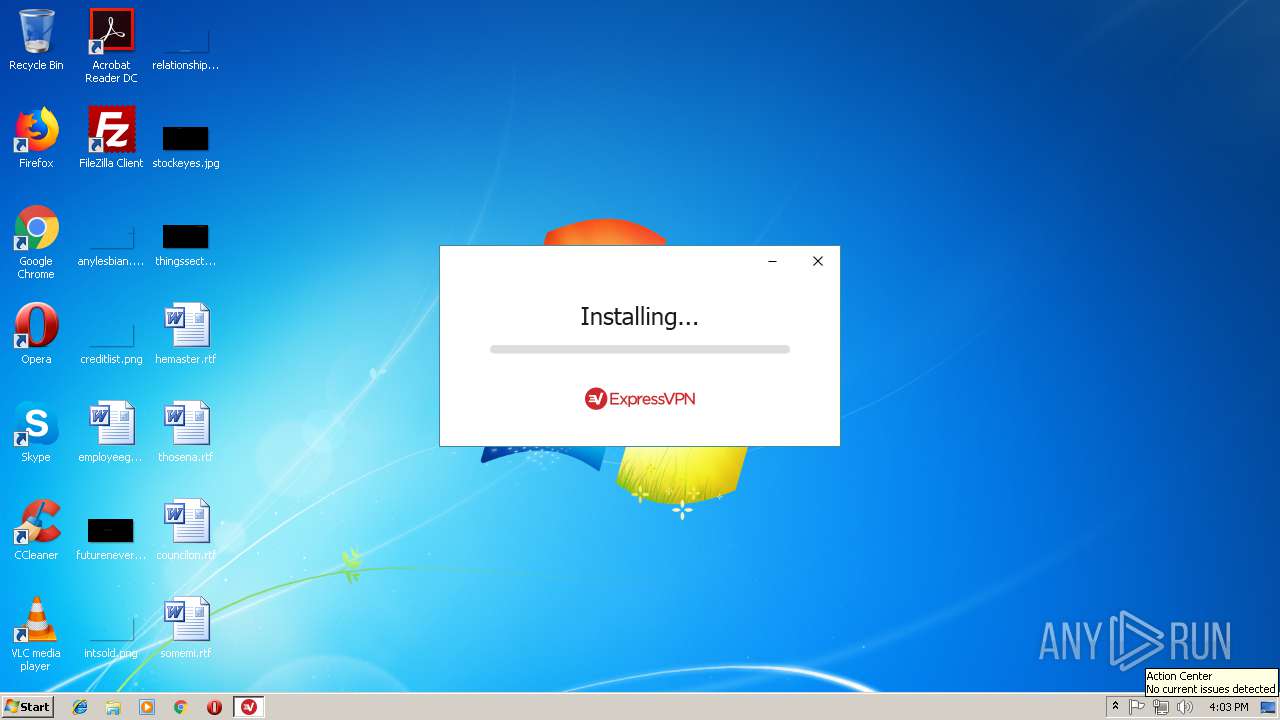
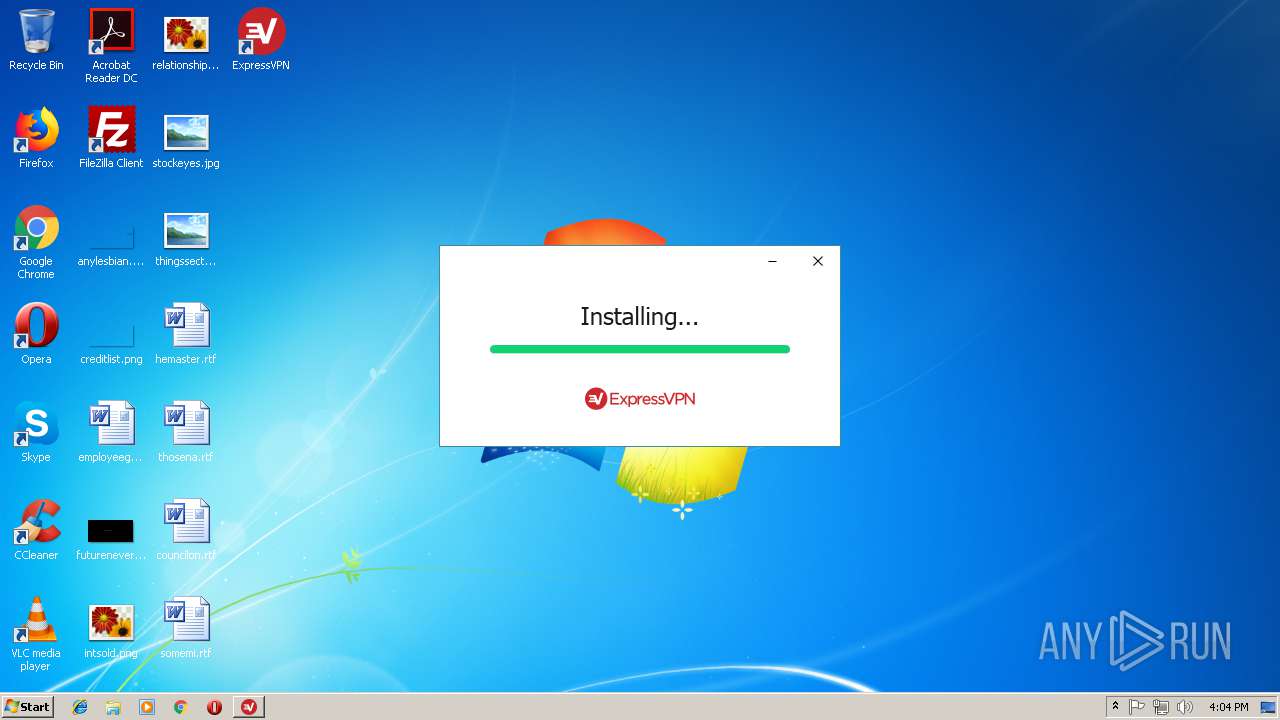
| download: | expressvpn_6.8.0.5735.exe |
| Full analysis: | https://app.any.run/tasks/c114955f-d684-402b-9d71-1ad957ec121c |
| Verdict: | Malicious activity |
| Analysis date: | November 08, 2018, 16:02:46 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 894AF58163167F60B95EB23FD96419C7 |
| SHA1: | 146C6B128CD00953F98C049BA07972627ECD6DC8 |
| SHA256: | DA3728F8CB1CEFE9AD0C47FDCD0E4E4E3DDD33B70AB4ECEB34E9B07ED6E8F60B |
| SSDEEP: | 393216:pk9twp6DcYnKjKseuFenbny9ze7Bah2perEDEH0JxgFPQNfF7swza1RroqAeRih4:pkrwp6DcYn0KXuobn8oMe6SEH0JEPQxY |
MALICIOUS
Loads dropped or rewritten executable
- expressvpn_6.8.0.5735.exe (PID: 1968)
- rundll32.exe (PID: 2564)
- rundll32.exe (PID: 2604)
- rundll32.exe (PID: 3904)
- rundll32.exe (PID: 2220)
- rundll32.exe (PID: 3116)
- ExpressVPN.exe (PID: 2132)
- XvUtil.exe (PID: 3168)
- ExpressVPN-Installer.exe (PID: 3896)
- xvpnd.exe (PID: 584)
- XvUtil.exe (PID: 2468)
- XvUtil.exe (PID: 2016)
Application was dropped or rewritten from another process
- expressvpn_6.8.0.5735.exe (PID: 1968)
- ExpressVPN_6.8.0.5735.exe (PID: 3080)
- ExpressVPN.exe (PID: 2132)
- ExpressVPN-Installer.exe (PID: 3896)
- tapinstall.exe (PID: 3484)
- XvUtil.exe (PID: 3168)
- nssm.exe (PID: 1692)
- nssm.exe (PID: 3376)
- nssm.exe (PID: 2660)
- nssm.exe (PID: 2916)
- nssm.exe (PID: 2160)
- xvpnd.exe (PID: 584)
- XvUtil.exe (PID: 2468)
- XvUtil.exe (PID: 2016)
- nssm.exe (PID: 3544)
- nssm.exe (PID: 2648)
Changes settings of System certificates
- msiexec.exe (PID: 3424)
Changes the autorun value in the registry
- ExpressVPN_6.8.0.5735.exe (PID: 3080)
Starts NET.EXE for service management
- xvpnd.exe (PID: 584)
SUSPICIOUS
Executable content was dropped or overwritten
- expressvpn_6.8.0.5735.exe (PID: 1968)
- expressvpn_6.8.0.5735.exe (PID: 3120)
- ExpressVPN_6.8.0.5735.exe (PID: 3080)
- rundll32.exe (PID: 2564)
- rundll32.exe (PID: 3904)
- msiexec.exe (PID: 3424)
- rundll32.exe (PID: 2220)
- rundll32.exe (PID: 3116)
- tapinstall.exe (PID: 3484)
- DrvInst.exe (PID: 2652)
- DrvInst.exe (PID: 2796)
Starts itself from another location
- expressvpn_6.8.0.5735.exe (PID: 1968)
Creates or modifies windows services
- ExpressVPN_6.8.0.5735.exe (PID: 3080)
- DrvInst.exe (PID: 2652)
- nssm.exe (PID: 1692)
- nssm.exe (PID: 2660)
- nssm.exe (PID: 2916)
- nssm.exe (PID: 2160)
- DrvInst.exe (PID: 2796)
Searches for installed software
- ExpressVPN_6.8.0.5735.exe (PID: 3080)
- DrvInst.exe (PID: 2652)
Adds / modifies Windows certificates
- msiexec.exe (PID: 3424)
Creates files in the program directory
- ExpressVPN_6.8.0.5735.exe (PID: 3080)
- rundll32.exe (PID: 2220)
- xvpnd.exe (PID: 584)
Uses RUNDLL32.EXE to load library
- MsiExec.exe (PID: 1540)
- MsiExec.exe (PID: 3172)
- DrvInst.exe (PID: 2652)
Creates files in the user directory
- ExpressVPN.exe (PID: 2132)
Creates files in the Windows directory
- tapinstall.exe (PID: 3484)
- DrvInst.exe (PID: 2652)
- DrvInst.exe (PID: 2796)
Creates files in the driver directory
- DrvInst.exe (PID: 2652)
- DrvInst.exe (PID: 2796)
Removes files from Windows directory
- DrvInst.exe (PID: 2652)
- DrvInst.exe (PID: 2796)
Starts SC.EXE for service management
- xvpnd.exe (PID: 584)
Uses TASKKILL.EXE to kill process
- xvpnd.exe (PID: 584)
Creates a software uninstall entry
- ExpressVPN_6.8.0.5735.exe (PID: 3080)
Reads Environment values
- ExpressVPN.exe (PID: 2132)
Uses NETSH.EXE for network configuration
- XvUtil.exe (PID: 2468)
- XvUtil.exe (PID: 2016)
INFO
Adds / modifies Windows certificates
- DrvInst.exe (PID: 4080)
Application launched itself
- msiexec.exe (PID: 3424)
Changes settings of System certificates
- DrvInst.exe (PID: 4080)
Loads dropped or rewritten executable
- MsiExec.exe (PID: 3172)
- MsiExec.exe (PID: 1540)
Creates or modifies windows services
- vssvc.exe (PID: 1552)
Creates files in the program directory
- msiexec.exe (PID: 3424)
Creates a software uninstall entry
- msiexec.exe (PID: 3424)
Low-level read access rights to disk partition
- vssvc.exe (PID: 1552)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (52.9) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (23.5) |
| .exe | | | DOS Executable Generic (23.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2017:05:01 16:33:52+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 14.1 |
| CodeSize: | 302080 |
| InitializedDataSize: | 529408 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x2e1fd |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 6.8.0.5735 |
| ProductVersionNumber: | 6.8.0.5735 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| CompanyName: | ExpressVPN |
| FileDescription: | ExpressVPN |
| FileVersion: | 6.8.0.5735 |
| InternalName: | setup |
| LegalCopyright: | Copyright (c) ExpressVPN. All rights reserved. |
| OriginalFileName: | ExpressVPN_6.8.0.5735.exe |
| ProductName: | ExpressVPN |
| ProductVersion: | 6.8.0.5735 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 01-May-2017 14:33:52 |
| Detected languages: |
|
| Debug artifacts: |
|
| CompanyName: | ExpressVPN |
| FileDescription: | ExpressVPN |
| FileVersion: | 6.8.0.5735 |
| InternalName: | setup |
| LegalCopyright: | Copyright (c) ExpressVPN. All rights reserved. |
| OriginalFilename: | ExpressVPN_6.8.0.5735.exe |
| ProductName: | ExpressVPN |
| ProductVersion: | 6.8.0.5735 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000118 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 7 |
| Time date stamp: | 01-May-2017 14:33:52 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00049A67 | 0x00049C00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.56282 |
.rdata | 0x0004B000 | 0x0001EC60 | 0x0001EE00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.10841 |
.data | 0x0006A000 | 0x00001730 | 0x00000A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.15458 |
.wixburn8 | 0x0006C000 | 0x00000038 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 0.751437 |
.tls | 0x0006D000 | 0x00000009 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x0006E000 | 0x0005D814 | 0x0005DA00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 2.736 |
.reloc | 0x000CC000 | 0x00003DEC | 0x00003E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.79026 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.30829 | 1234 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 3.21143 | 4264 | Latin 1 / Western European | English - United States | RT_ICON |
3 | 3.53678 | 9640 | Latin 1 / Western European | English - United States | RT_ICON |
4 | 2.73924 | 16936 | Latin 1 / Western European | English - United States | RT_ICON |
5 | 2.47079 | 67624 | Latin 1 / Western European | English - United States | RT_ICON |
6 | 2.3062 | 270376 | Latin 1 / Western European | English - United States | RT_ICON |
Imports
ADVAPI32.dll |
Cabinet.dll (delay-loaded) |
GDI32.dll |
KERNEL32.dll |
OLEAUT32.dll |
RPCRT4.dll |
SHELL32.dll |
USER32.dll |
ole32.dll |
Total processes
86
Monitored processes
40
Malicious processes
18
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 584 | "C:\Program Files\ExpressVPN\xvpn-ui\..\xvpnd\xvpnd.exe" --workdir C:\ProgramData\ExpressVPN\v4\ --client-version 6.8.0 --client-build 6.8.0.5735 --verbose start | C:\Program Files\ExpressVPN\xvpnd\xvpnd.exe | nssm.exe | ||||||||||||
User: SYSTEM Integrity Level: SYSTEM Exit code: 0 Modules
| |||||||||||||||
| 1360 | C:\Windows\System32\taskkill.exe /f /im openvpn.exe | C:\Windows\System32\taskkill.exe | — | xvpnd.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1540 | C:\Windows\system32\MsiExec.exe -Embedding A4B7DEA1BAFCA546DB0329A755050324 | C:\Windows\system32\MsiExec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1552 | C:\Windows\system32\vssvc.exe | C:\Windows\system32\vssvc.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1600 | C:\Windows\System32\net.exe start expressvpnsplittunnel | C:\Windows\System32\net.exe | — | xvpnd.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Net Command Exit code: 2 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1692 | "C:\Program Files\ExpressVPN\xvpn-ui\..\bootstrap\x86\nssm.exe" install ExpressVPNService "C:\Program Files\ExpressVPN\xvpn-ui\..\xvpnd\xvpnd.exe" | C:\Program Files\ExpressVPN\bootstrap\x86\nssm.exe | — | ExpressVPN-Installer.exe | |||||||||||
User: admin Integrity Level: HIGH Description: The non-sucking service manager Exit code: 0 Version: 2.24 Modules
| |||||||||||||||
| 1968 | "C:\Users\admin\AppData\Local\Temp\{963A2D65-8ECA-4759-AF5B-34B5655FE9AB}\.cr\expressvpn_6.8.0.5735.exe" -burn.clean.room="C:\Users\admin\AppData\Local\Temp\expressvpn_6.8.0.5735.exe" -burn.filehandle.attached=148 -burn.filehandle.self=156 | C:\Users\admin\AppData\Local\Temp\{963A2D65-8ECA-4759-AF5B-34B5655FE9AB}\.cr\expressvpn_6.8.0.5735.exe | expressvpn_6.8.0.5735.exe | ||||||||||||
User: admin Company: ExpressVPN Integrity Level: MEDIUM Description: ExpressVPN Exit code: 0 Version: 6.8.0.5735 Modules
| |||||||||||||||
| 2016 | "C:\Program Files\ExpressVPN\xvpnd\windows\xvutil\XvUtil.exe" OptimizeNetwork | C:\Program Files\ExpressVPN\xvpnd\windows\xvutil\XvUtil.exe | — | xvpnd.exe | |||||||||||
User: SYSTEM Company: ExpressVPN Integrity Level: SYSTEM Description: XvUtil Exit code: 0 Version: 6.8.0.5735 Modules
| |||||||||||||||
| 2132 | "C:\Program Files\ExpressVPN\xvpn-ui\ExpressVPN.exe" install | C:\Program Files\ExpressVPN\xvpn-ui\ExpressVPN.exe | ExpressVPN_6.8.0.5735.exe | ||||||||||||
User: admin Company: ExpressVPN Integrity Level: HIGH Description: ExpressVPN Exit code: 0 Version: 6.8.0.5735 Modules
| |||||||||||||||
| 2160 | "C:\Program Files\ExpressVPN\bootstrap\x86\nssm.exe" | C:\Program Files\ExpressVPN\bootstrap\x86\nssm.exe | — | services.exe | |||||||||||
User: SYSTEM Integrity Level: SYSTEM Description: The non-sucking service manager Exit code: 0 Version: 2.24 Modules
| |||||||||||||||
Total events
4 536
Read events
2 361
Write events
2 111
Delete events
64
Modification events
| (PID) Process: | (1968) expressvpn_6.8.0.5735.exe | Key: | HKEY_CURRENT_USER\Software\ExpressVPN |
| Operation: | write | Name: | UserId |
Value: 80ac92d4-7ba5-430c-9056-dba1362e7fc4 | |||
| (PID) Process: | (1968) expressvpn_6.8.0.5735.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Direct3D\MostRecentApplication |
| Operation: | write | Name: | Name |
Value: expressvpn_6.8.0.5735.exe | |||
| (PID) Process: | (1968) expressvpn_6.8.0.5735.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (1968) expressvpn_6.8.0.5735.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3080) ExpressVPN_6.8.0.5735.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SystemRestore |
| Operation: | write | Name: | SrCreateRp (Enter) |
Value: 400000000000000043A5DD9C7C77D401080C0000600B0000D5070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3080) ExpressVPN_6.8.0.5735.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SPP |
| Operation: | write | Name: | SppCreate (Enter) |
Value: 400000000000000069CBDD9C7C77D401080C0000600B0000D0070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3080) ExpressVPN_6.8.0.5735.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SPP |
| Operation: | write | Name: | LastIndex |
Value: 20 | |||
| (PID) Process: | (3080) ExpressVPN_6.8.0.5735.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGatherWriterMetadata (Enter) |
Value: 40000000000000000FD3429D7C77D401080C0000600B0000D3070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3080) ExpressVPN_6.8.0.5735.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\VssapiPublisher |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 400000000000000015EF489D7C77D401080C0000680E0000E8030000010000000000000000000000AE4A83A4DAF8094097EDF3885425F2E80000000000000000 | |||
| (PID) Process: | (1552) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\ASR Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4000000000000000B8E15F9D7C77D40110060000A40B0000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
114
Suspicious files
62
Text files
596
Unknown types
22
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1968 | expressvpn_6.8.0.5735.exe | C:\Users\admin\AppData\Local\Temp\{4FA0D830-9A61-47B9-884A-801385181BA7}\.ba\WixSharp Setup.exe | executable | |
MD5:— | SHA256:— | |||
| 1968 | expressvpn_6.8.0.5735.exe | C:\Users\admin\AppData\Local\Temp\{4FA0D830-9A61-47B9-884A-801385181BA7}\.ba\mbapreq.png | image | |
MD5:A356956FD269567B8F4612A33802637B | SHA256:A401A225ADDAF89110B4B0F6E8CF94779E7C0640BCDD2D670FFCF05AAB0DAD03 | |||
| 1968 | expressvpn_6.8.0.5735.exe | C:\Users\admin\AppData\Local\Temp\{4FA0D830-9A61-47B9-884A-801385181BA7}\.ba\Microsoft.Deployment.WindowsInstaller.dll | executable | |
MD5:5EF88919012E4A3D8A1E2955DC8C8D81 | SHA256:3E54286E348EBD3D70EAED8174CCA500455C3E098CDD1FCCB167BC43D93DB29D | |||
| 1968 | expressvpn_6.8.0.5735.exe | C:\Users\admin\AppData\Local\Temp\{4FA0D830-9A61-47B9-884A-801385181BA7}\.ba\1030\mbapreq.wxl | xml | |
MD5:7C6E4CE87870B3B5E71D3EF4555500F8 | SHA256:CAC263E0E90A4087446A290055257B1C39F17E11F065598CB2286DF4332C7696 | |||
| 1968 | expressvpn_6.8.0.5735.exe | C:\Users\admin\AppData\Local\Temp\{4FA0D830-9A61-47B9-884A-801385181BA7}\.ba\mbahost.dll | executable | |
MD5:50FC7F7C7CE6E83AF568B43649F69FF8 | SHA256:C4C1CE0850535D9591F6D67F094B3985B32547193605F81F302315BF0CA7005E | |||
| 1968 | expressvpn_6.8.0.5735.exe | C:\Users\admin\AppData\Local\Temp\{4FA0D830-9A61-47B9-884A-801385181BA7}\.ba\Castle.Core.dll | executable | |
MD5:D081621AEF9EDBB8F2D31F8B3AB9350B | SHA256:80F311ADAED94D41436F9A00CBB3F7B010107C7BA4E445FDE8A5E9ECC42BB8BA | |||
| 1968 | expressvpn_6.8.0.5735.exe | C:\Users\admin\AppData\Local\Temp\{4FA0D830-9A61-47B9-884A-801385181BA7}\.ba\1028\mbapreq.wxl | xml | |
MD5:1D4B831F77EFEC96FFBC70BC4B59B8B5 | SHA256:1B93556F07C35AC0564D57E0743CCBA231950962C6506C8D4A74A31CD66FD04C | |||
| 1968 | expressvpn_6.8.0.5735.exe | C:\Users\admin\AppData\Local\Temp\{4FA0D830-9A61-47B9-884A-801385181BA7}\.ba\mbapreq.thm | xml | |
MD5:A20778EC90A094A62A6C3A6AB2A6DC7D | SHA256:F8C3A03F47F0B9B3C20F0522A2481DA28C77FECDBB302F8DD8FBED87758CBAEA | |||
| 1968 | expressvpn_6.8.0.5735.exe | C:\Users\admin\AppData\Local\Temp\{4FA0D830-9A61-47B9-884A-801385181BA7}\.ba\1029\mbapreq.wxl | xml | |
MD5:CC8C6D04DC707B38E0F0C08BA16FE49B | SHA256:DC445E2457ED31ABF536871F90FF7CC96800A40B6BC033F37D45E3156A3B4FA9 | |||
| 1968 | expressvpn_6.8.0.5735.exe | C:\Users\admin\AppData\Local\Temp\{4FA0D830-9A61-47B9-884A-801385181BA7}\.ba\BootstrapperCore.dll | executable | |
MD5:1197872FA5DBF0A9D8C742558812DDE8 | SHA256:C1232F304EC8B3CE1626569AC28C6D1EEEA2EB891FC52D39E56F0D6102AC3D7E | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
6
DNS requests
2
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3424 | msiexec.exe | GET | 200 | 104.16.90.188:80 | http://crt.comodoca.com/COMODORSAAddTrustCA.crt | US | der | 1.37 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
584 | xvpnd.exe | 198.143.130.82:443 | www.lbhydju.net | SingleHop, Inc. | US | unknown |
3424 | msiexec.exe | 104.16.90.188:80 | crt.comodoca.com | Cloudflare Inc | US | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
crt.comodoca.com |
| whitelisted |
www.lbhydju.net |
| unknown |