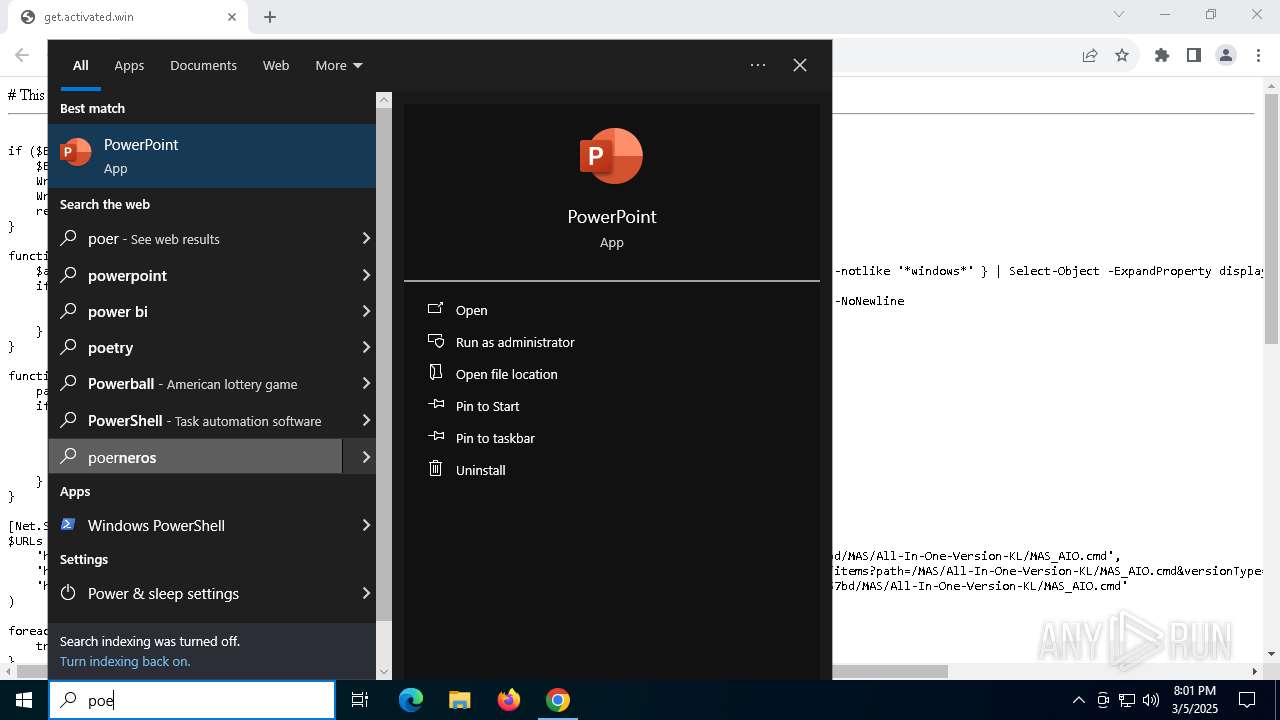
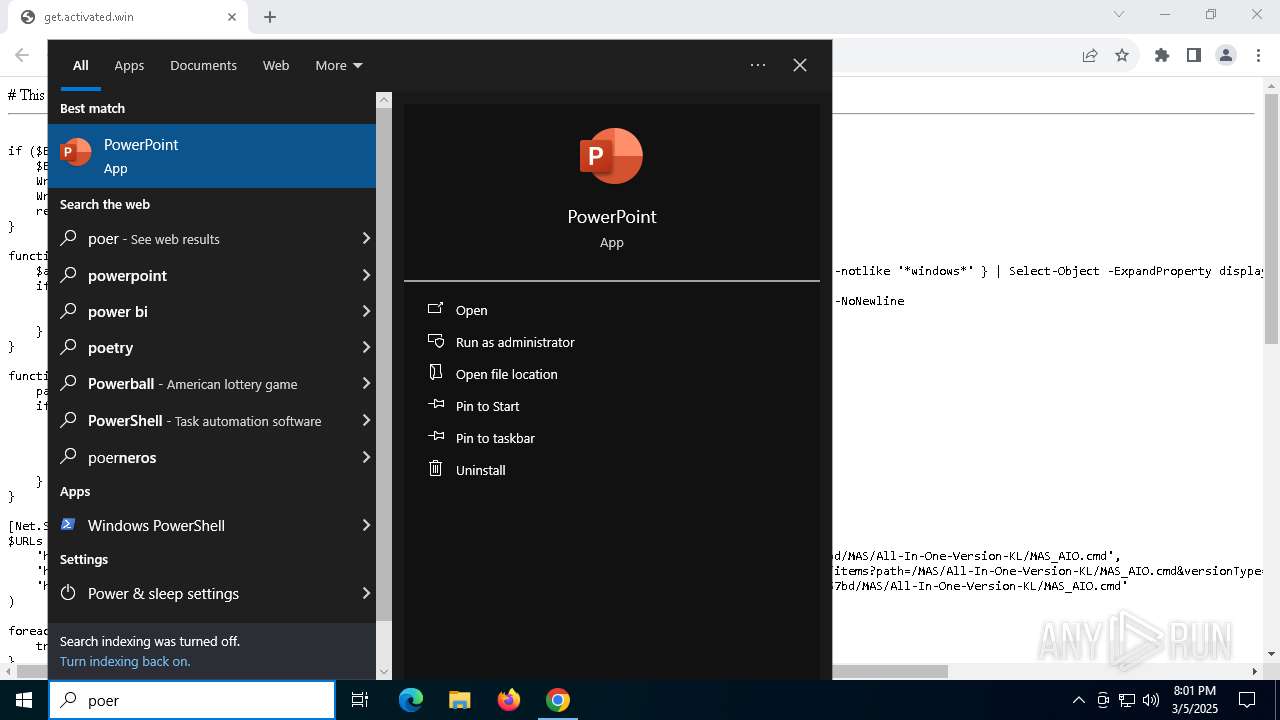
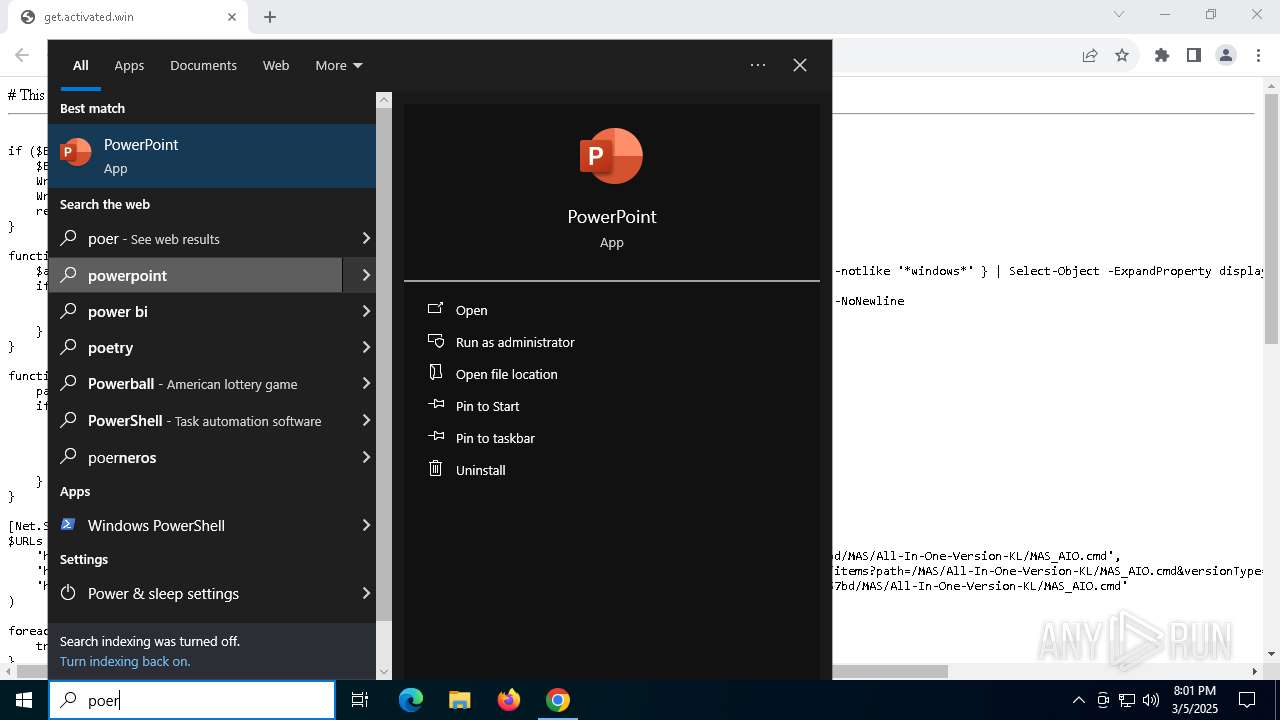
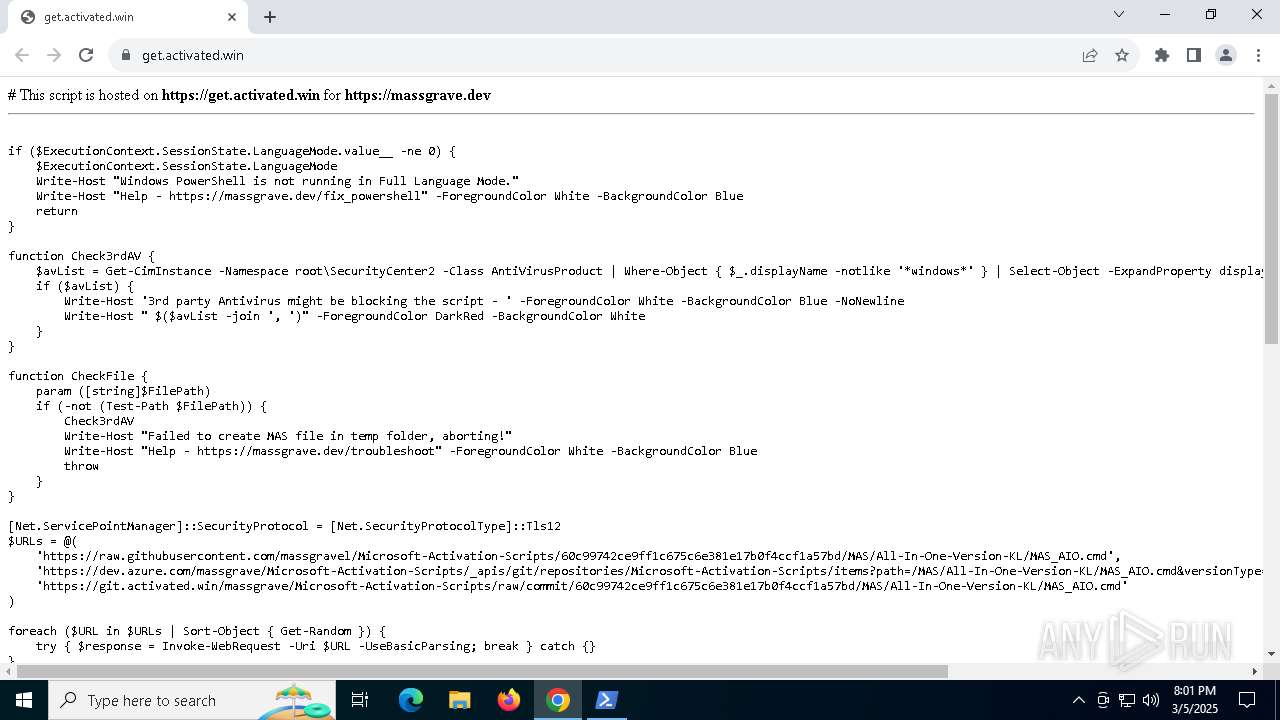
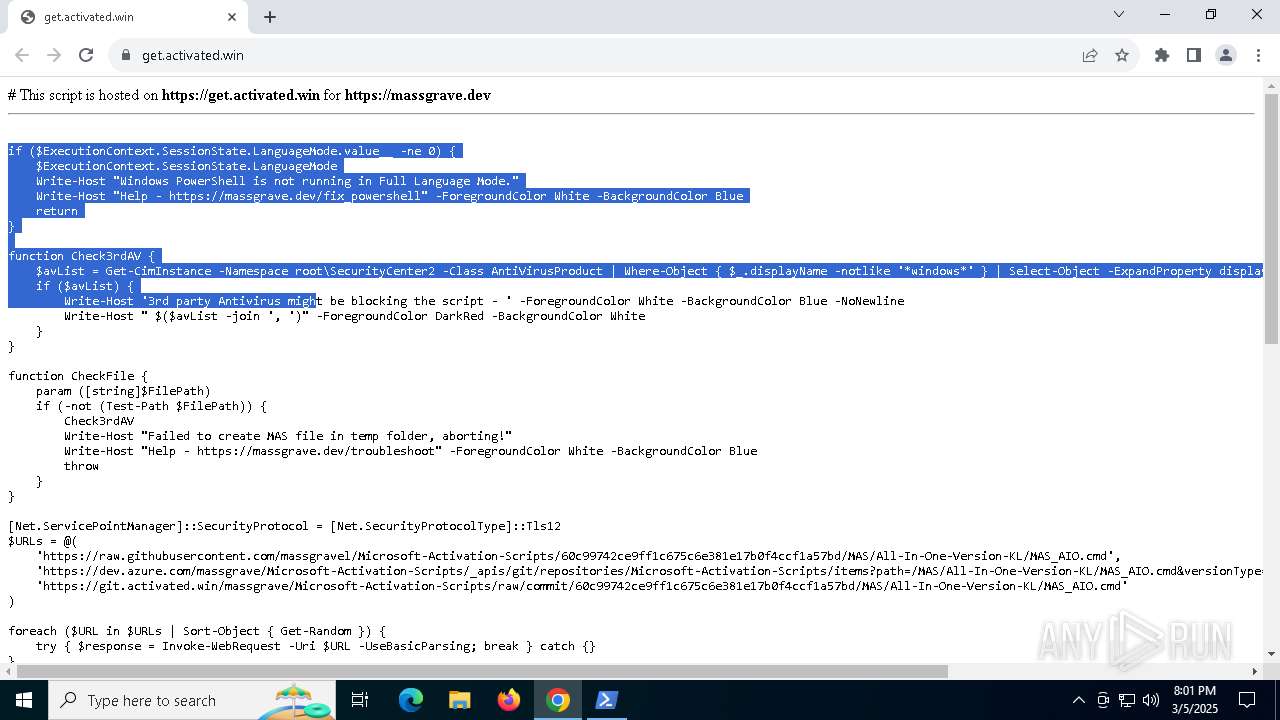
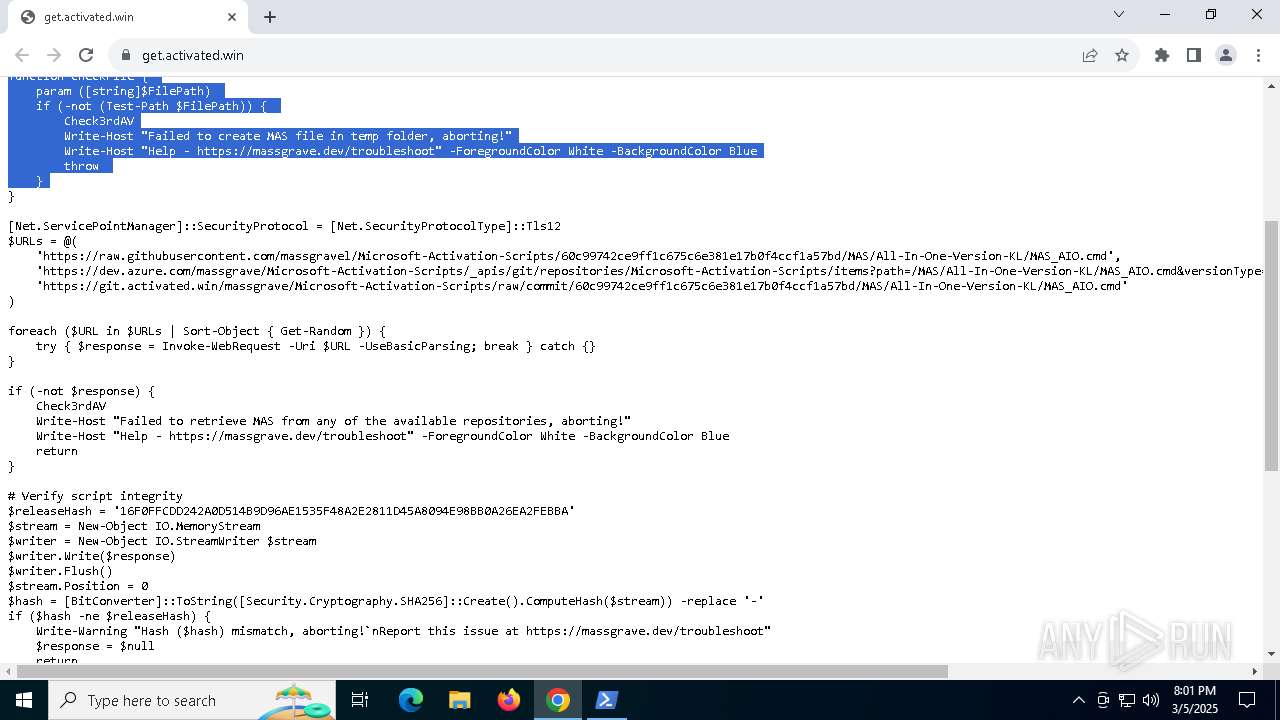
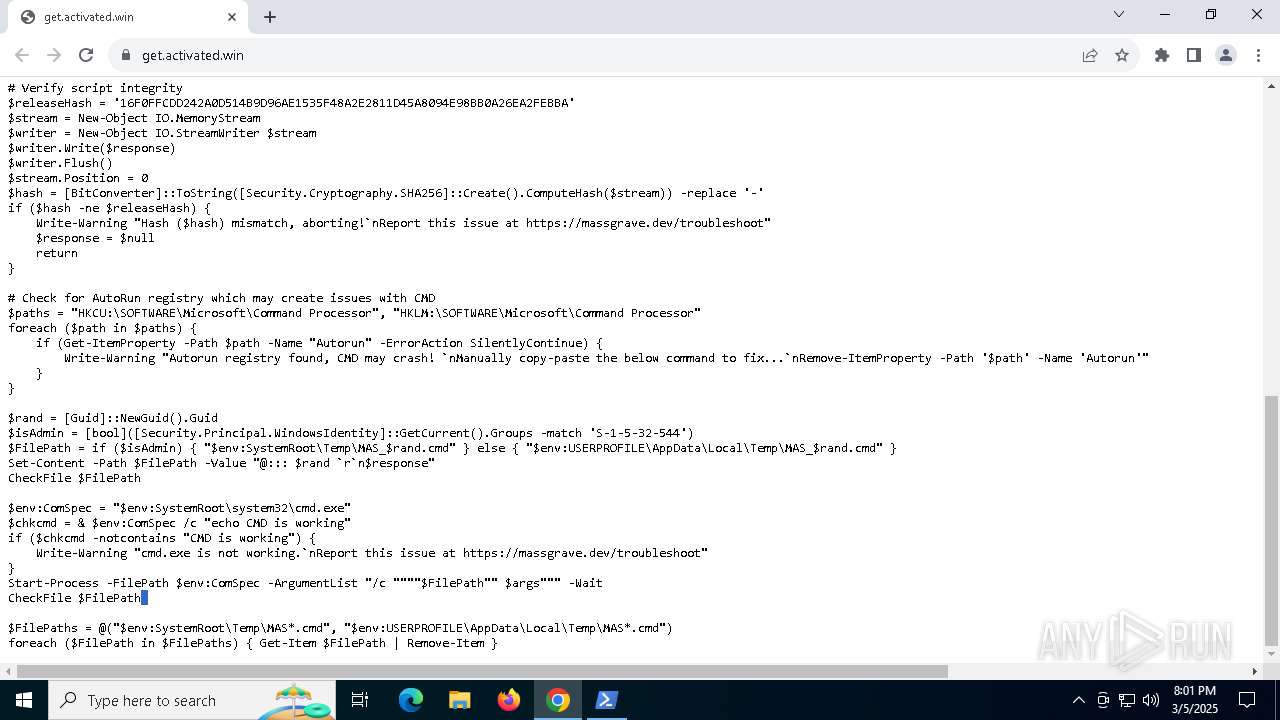
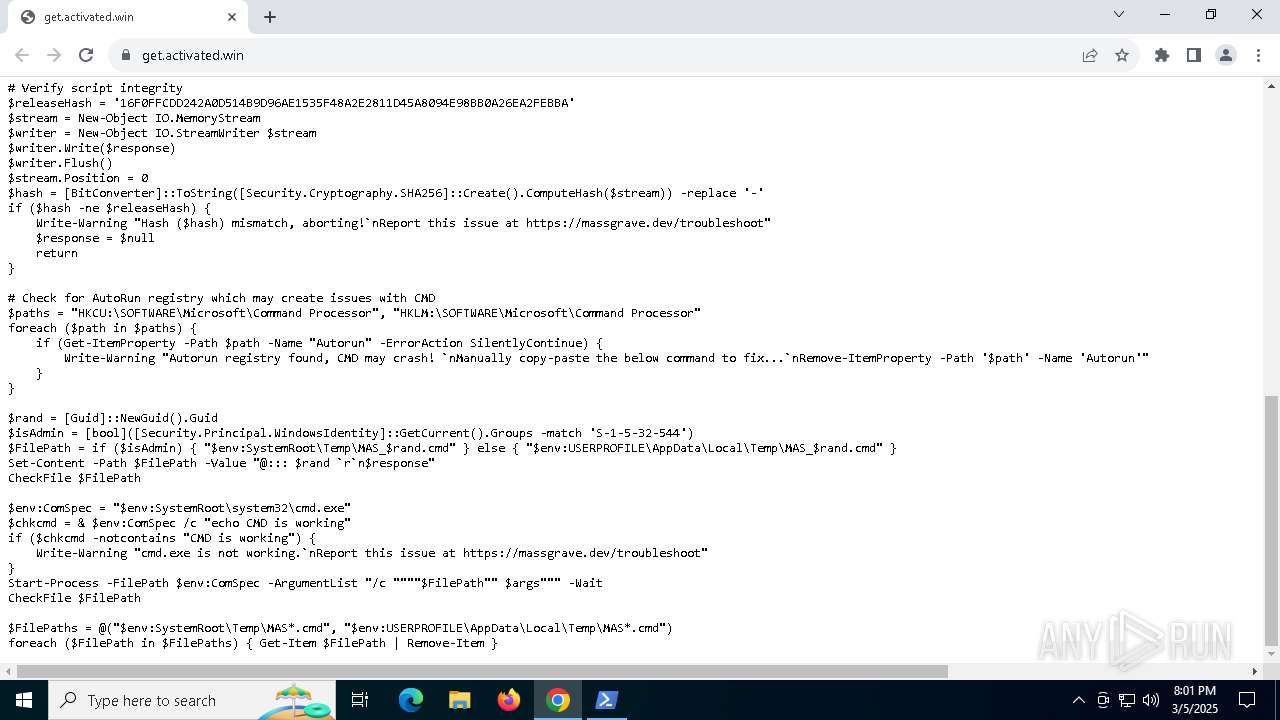
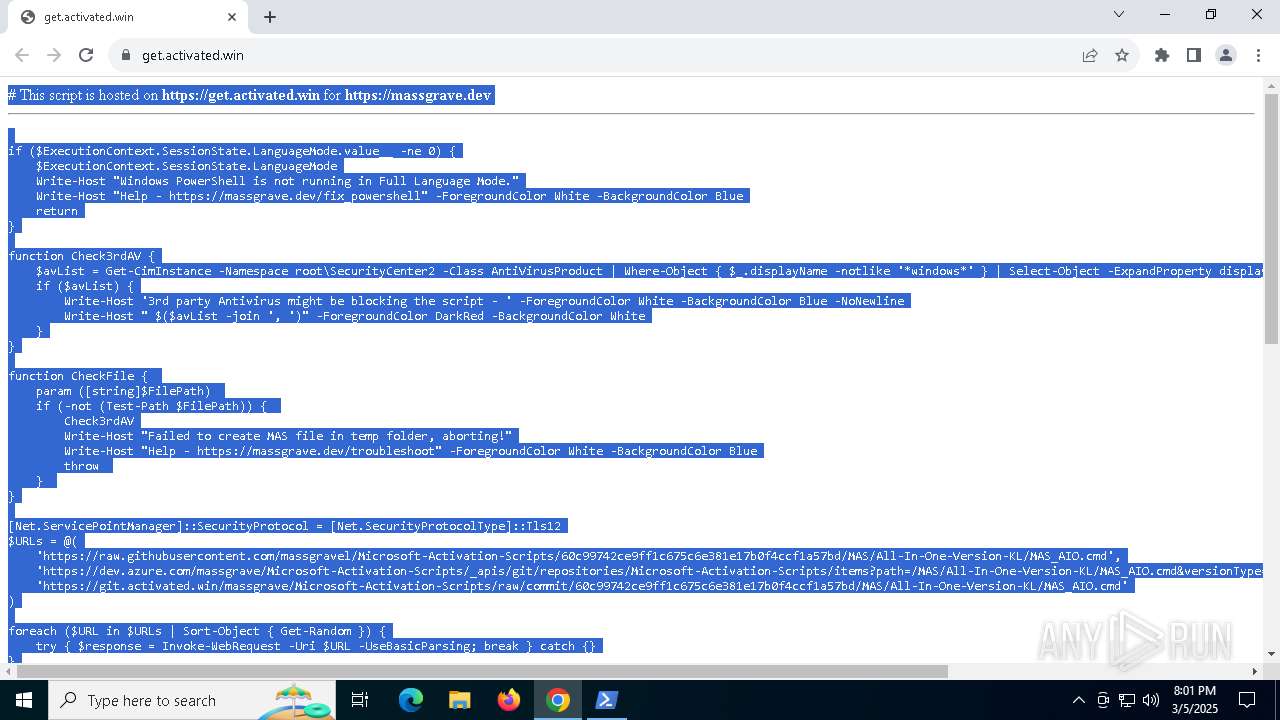
| URL: | https://get.activated.win |
| Full analysis: | https://app.any.run/tasks/77922efc-f7ce-4bd9-978b-5c25430bebb6 |
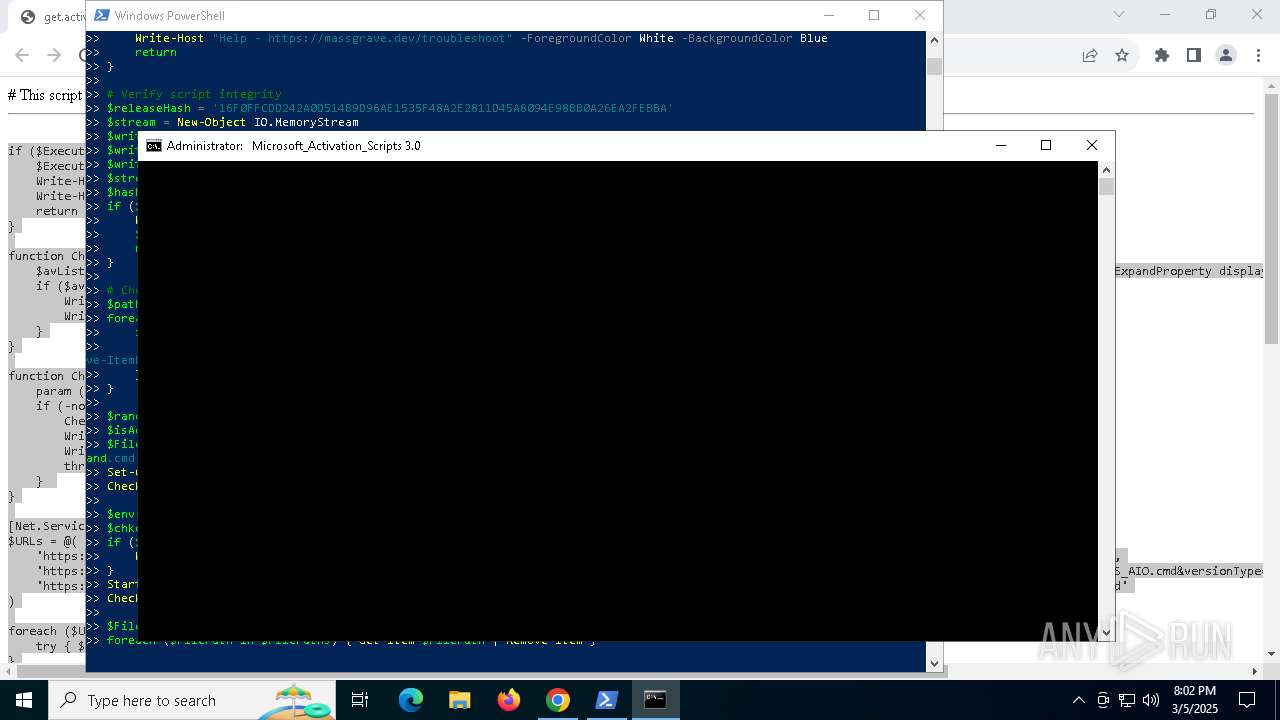
| Verdict: | Malicious activity |
| Analysis date: | March 05, 2025, 20:01:05 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 4B01CC7DAC134B0FED2FD49A298DD72D |
| SHA1: | C350A907D3B85F7AC2A94FAECA014F2FC0E8AEFF |
| SHA256: | DA21A74A1684EE4CD6067EBBFF51AB8F57B5D73C22A41AFB524FBAEBD867E1CD |
| SSDEEP: | 3:N8hsTE2mML:2omK |
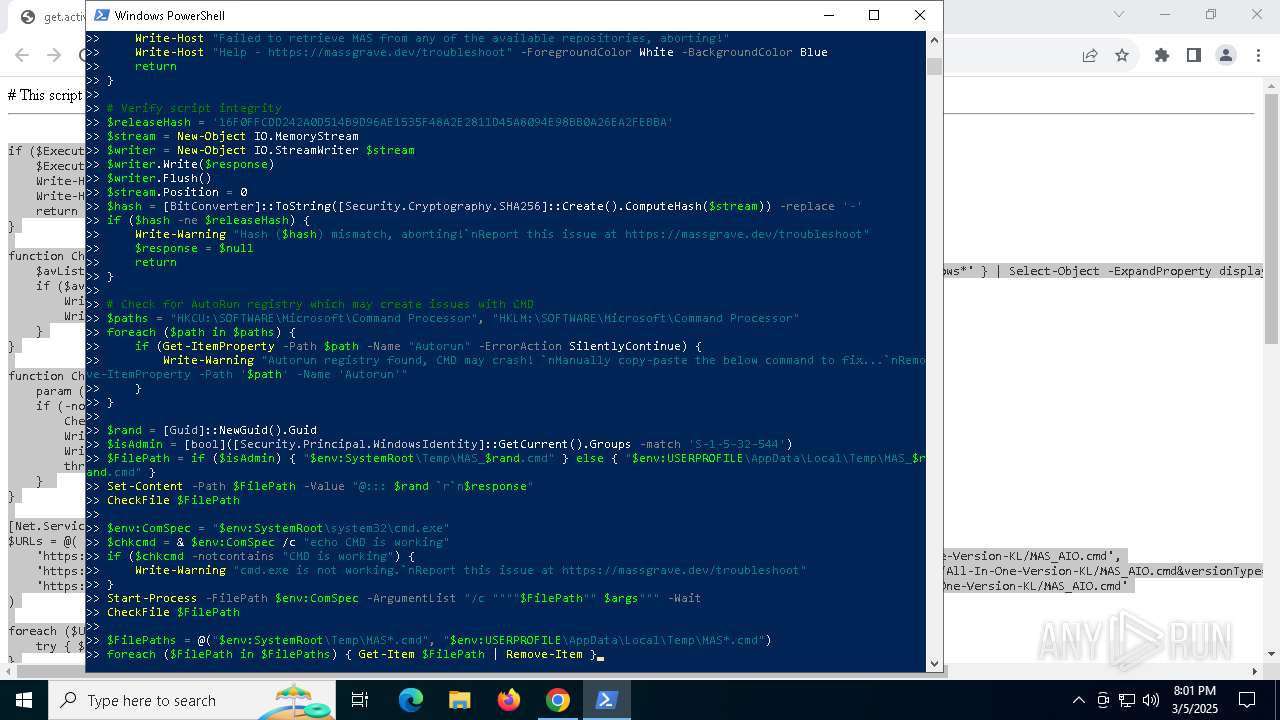
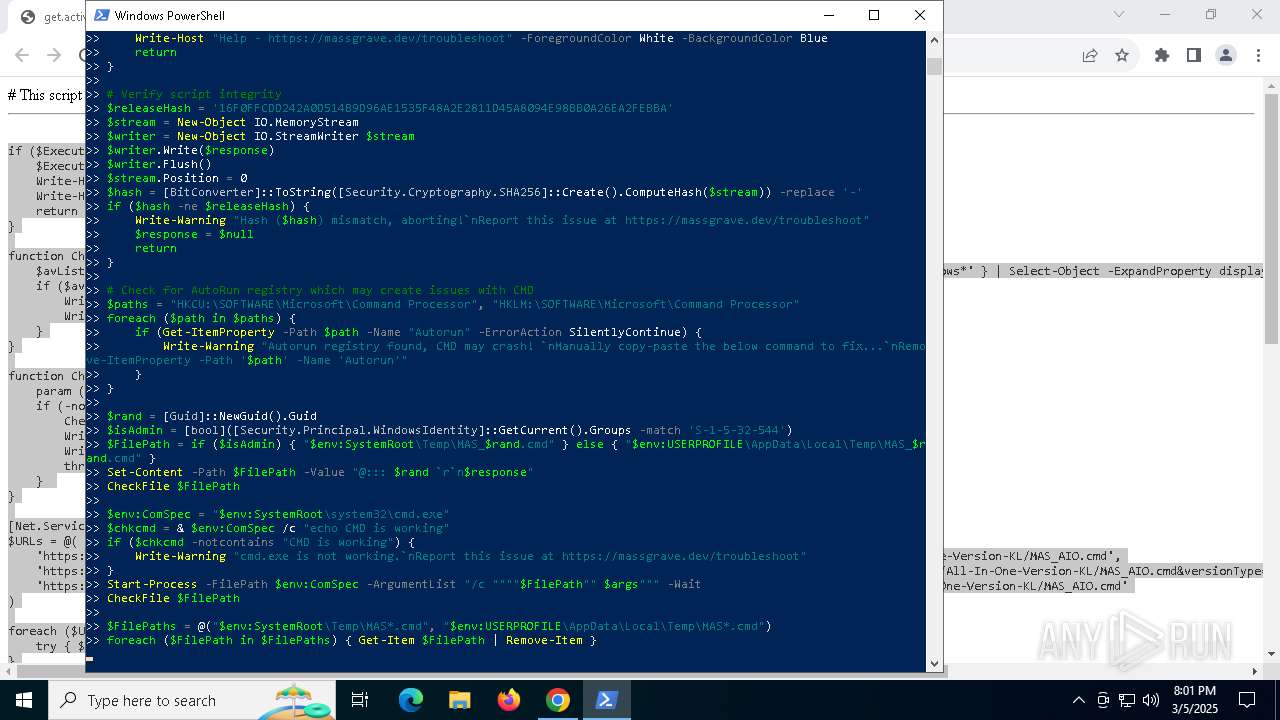
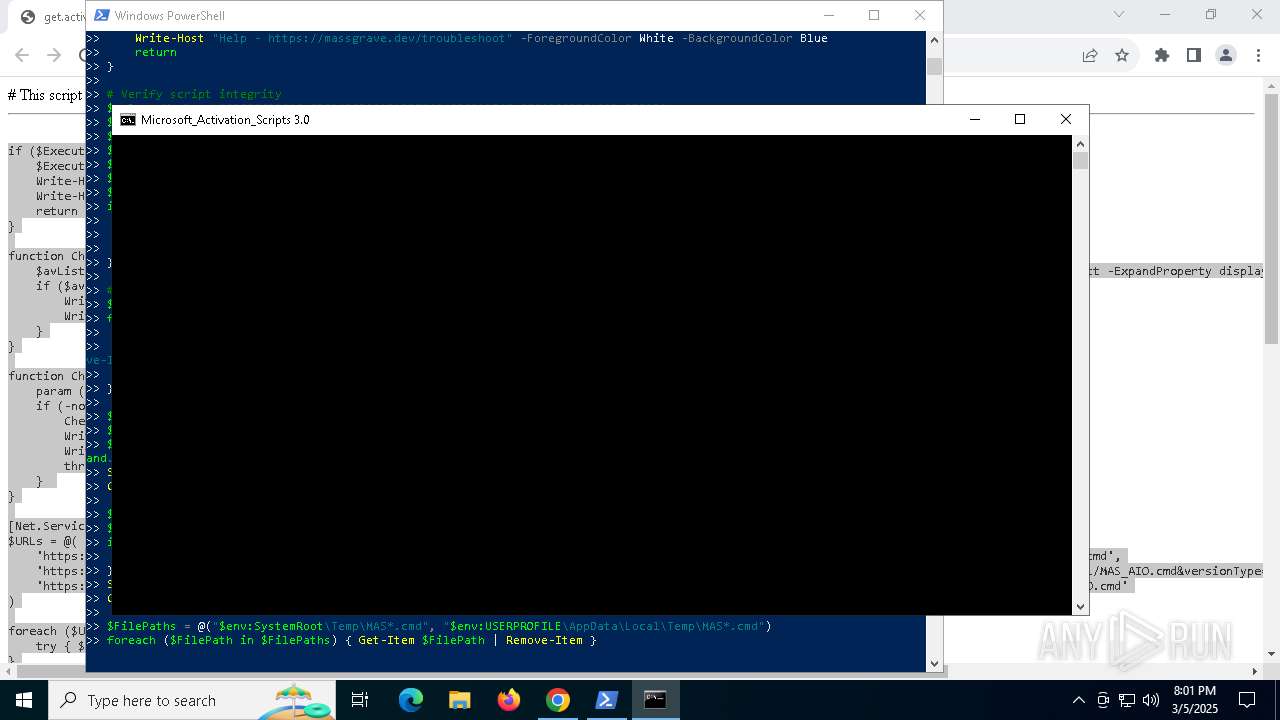
MALICIOUS
Modifies registry (POWERSHELL)
- powershell.exe (PID: 5756)
SUSPICIOUS
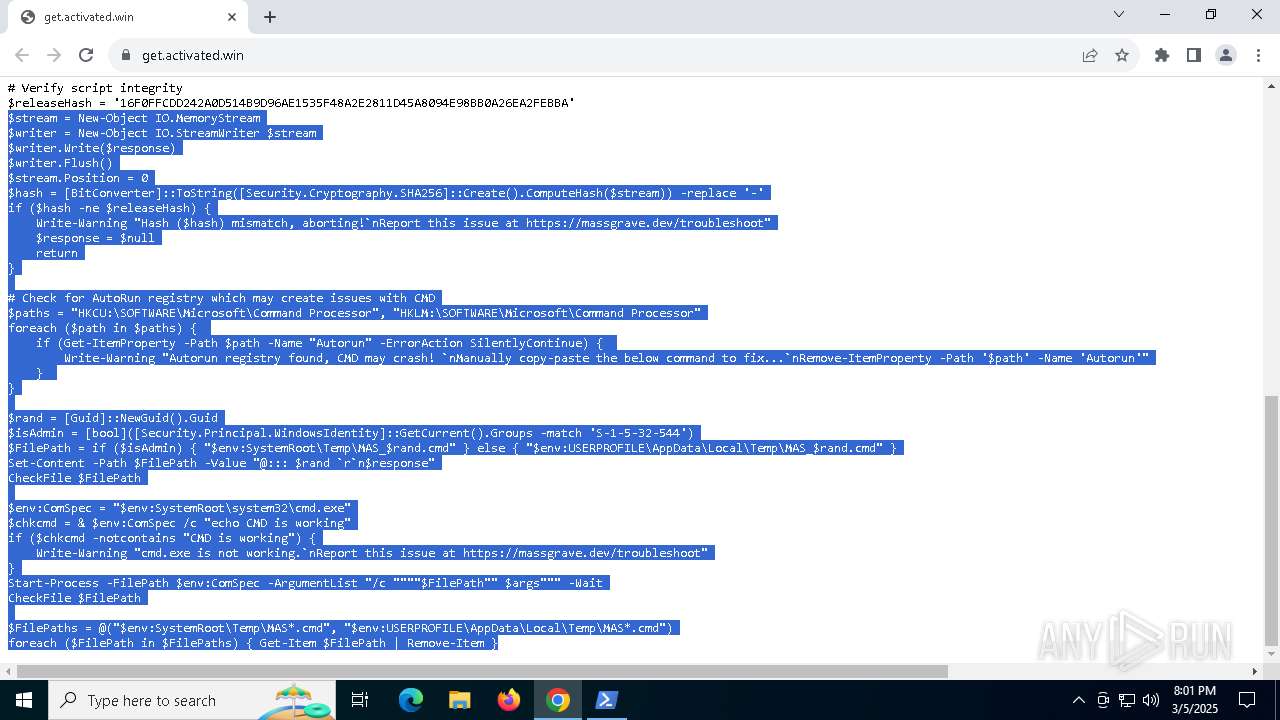
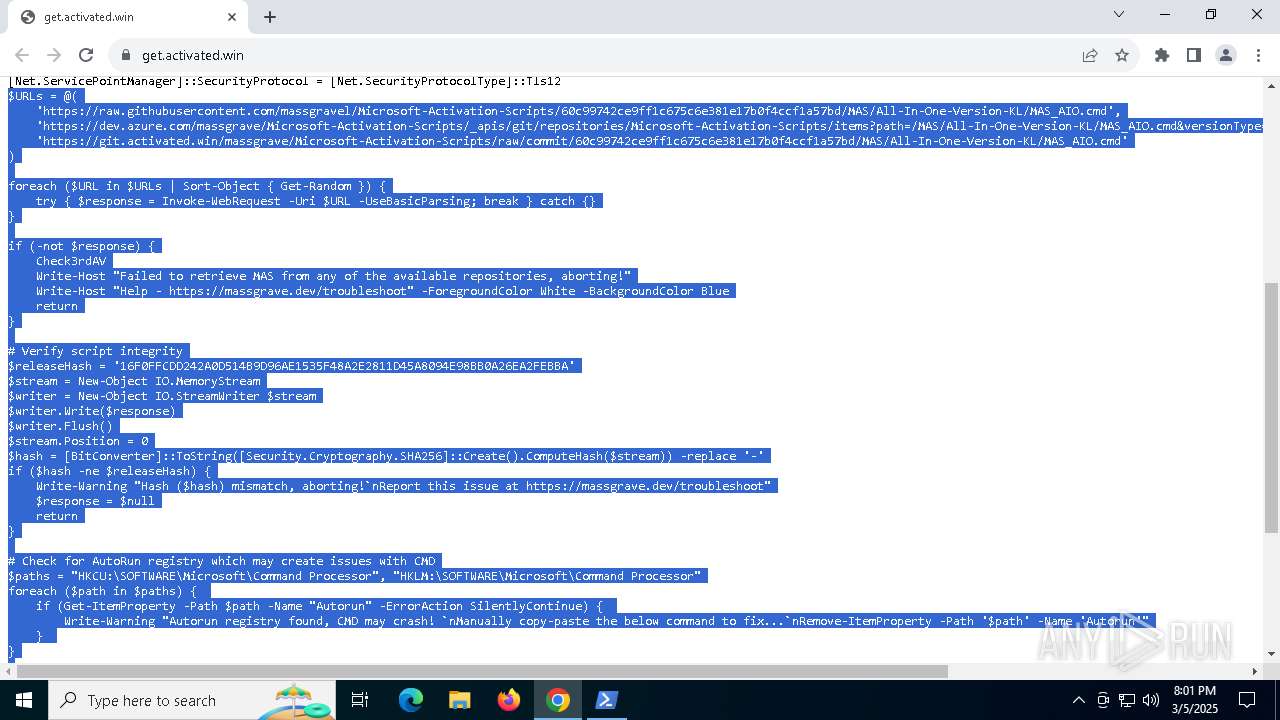
Gets or sets the security protocol (POWERSHELL)
- powershell.exe (PID: 5756)
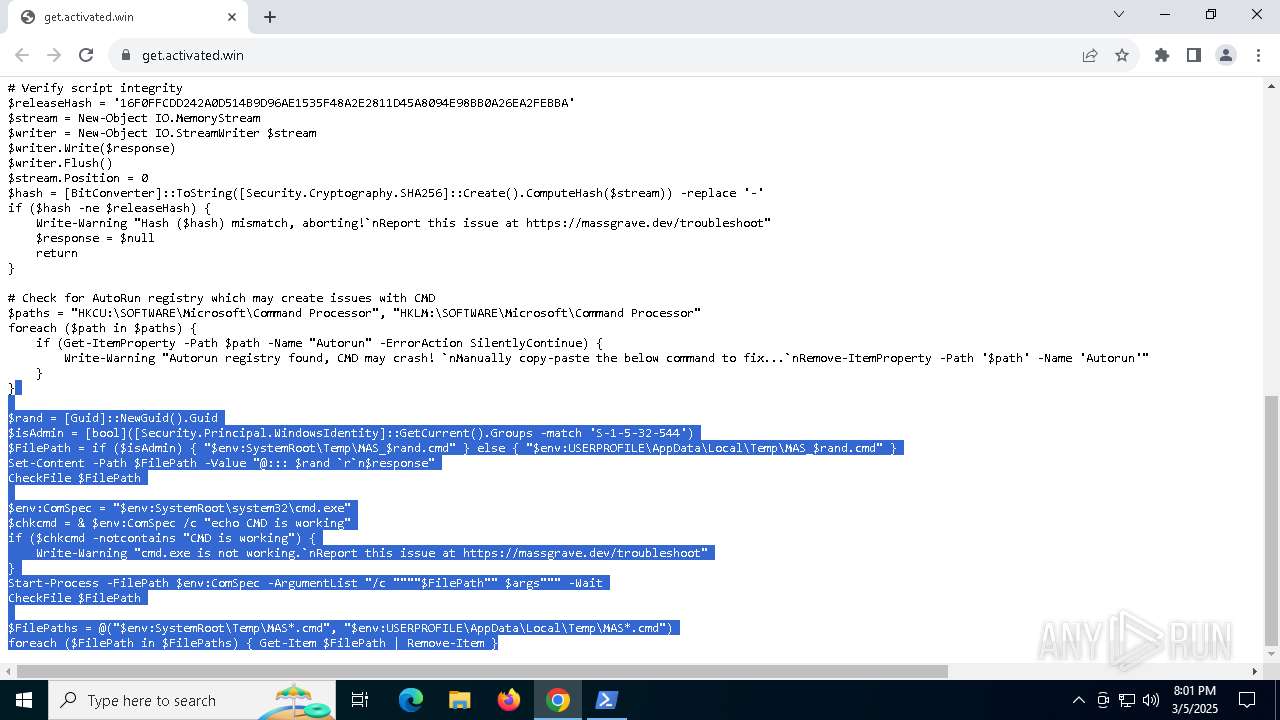
Creates new GUID (POWERSHELL)
- powershell.exe (PID: 5756)
Windows service management via SC.EXE
- sc.exe (PID: 6620)
- sc.exe (PID: 6208)
- sc.exe (PID: 8016)
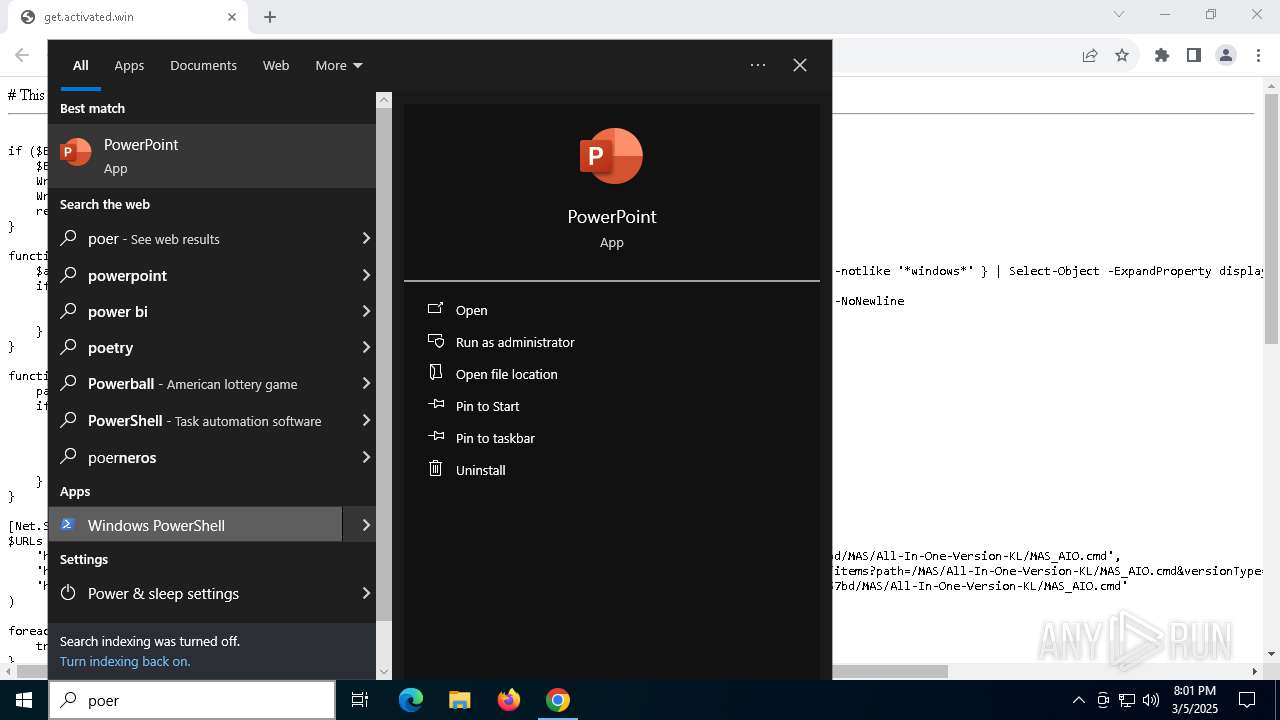
Starts CMD.EXE for commands execution
- powershell.exe (PID: 5756)
- cmd.exe (PID: 7968)
- cmd.exe (PID: 856)
- powershell.exe (PID: 668)
- cmd.exe (PID: 5084)
- cmd.exe (PID: 5308)
- powershell.exe (PID: 5936)
- cmd.exe (PID: 7636)
- cmd.exe (PID: 4756)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 7968)
- cmd.exe (PID: 5084)
- cmd.exe (PID: 4756)
Starts SC.EXE for service management
- cmd.exe (PID: 7968)
- cmd.exe (PID: 5084)
- cmd.exe (PID: 4756)
Application launched itself
- cmd.exe (PID: 7968)
- cmd.exe (PID: 856)
- cmd.exe (PID: 5084)
- cmd.exe (PID: 5308)
- cmd.exe (PID: 7636)
- cmd.exe (PID: 4756)
Executing commands from ".cmd" file
- cmd.exe (PID: 7968)
- powershell.exe (PID: 5756)
- powershell.exe (PID: 668)
- cmd.exe (PID: 5084)
- powershell.exe (PID: 5936)
- cmd.exe (PID: 4756)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 6572)
- cmd.exe (PID: 7968)
- cmd.exe (PID: 6228)
- cmd.exe (PID: 5084)
- cmd.exe (PID: 5392)
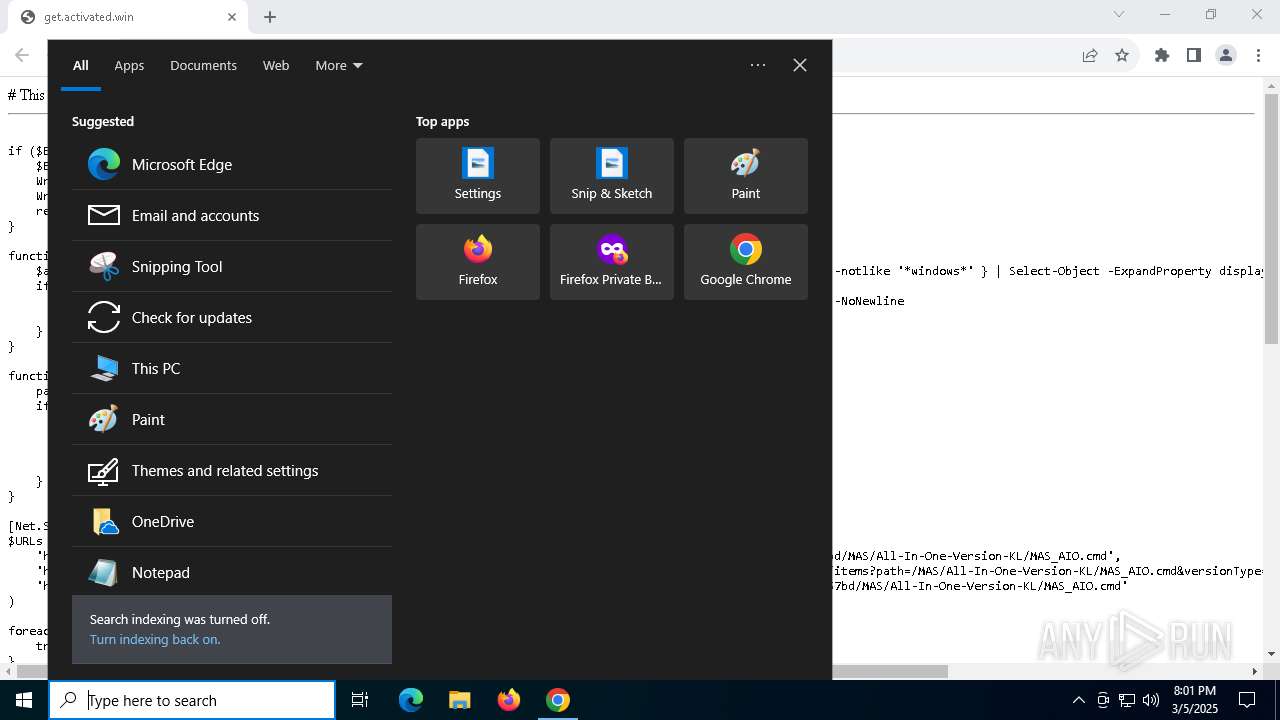
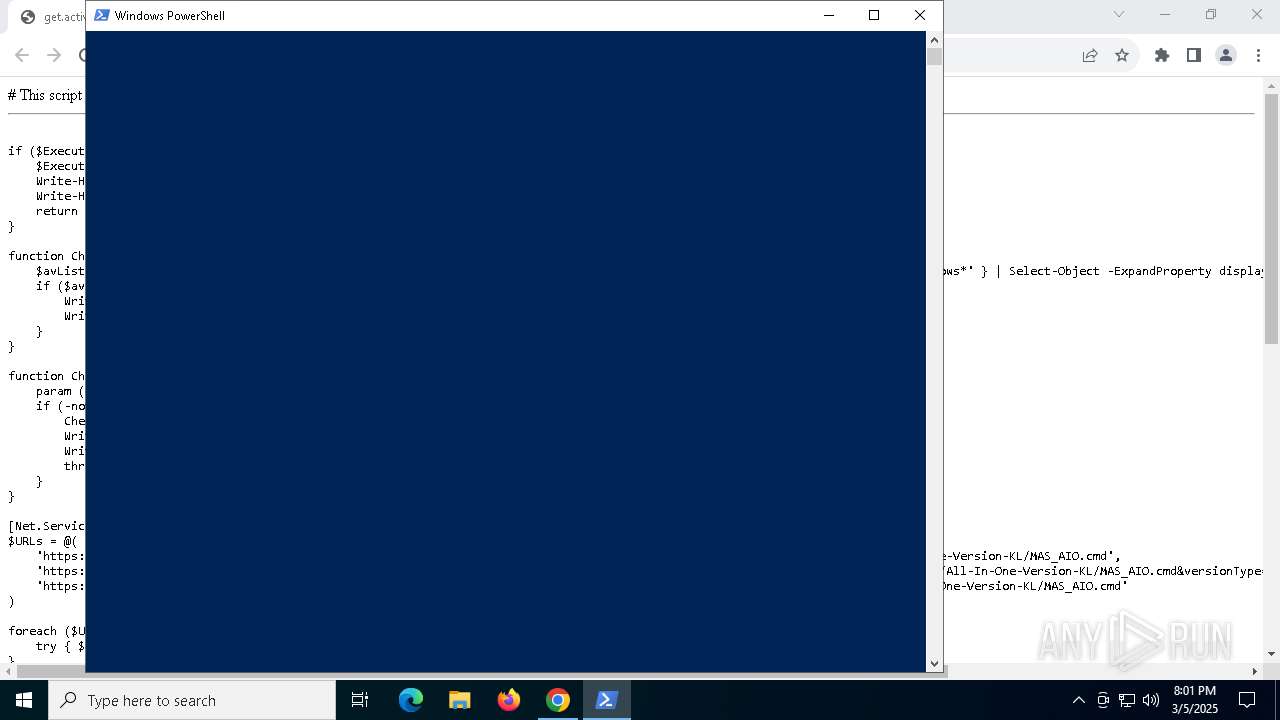
Probably obfuscated PowerShell command line is found
- cmd.exe (PID: 6572)
- cmd.exe (PID: 6228)
- cmd.exe (PID: 5392)
Possibly malicious use of IEX has been detected
- cmd.exe (PID: 6572)
- cmd.exe (PID: 6228)
- cmd.exe (PID: 5392)
Uses base64 encoding (POWERSHELL)
- powershell.exe (PID: 7748)
- powershell.exe (PID: 5756)
- powershell.exe (PID: 1324)
- powershell.exe (PID: 8144)
Gets content of a file (POWERSHELL)
- powershell.exe (PID: 7748)
- powershell.exe (PID: 5756)
- powershell.exe (PID: 1324)
- powershell.exe (PID: 8144)
Uses sleep to delay execution (POWERSHELL)
- powershell.exe (PID: 7748)
- powershell.exe (PID: 5756)
- powershell.exe (PID: 1324)
- powershell.exe (PID: 8144)
INFO
Application launched itself
- chrome.exe (PID: 2516)
Checks proxy server information
- BackgroundTransferHost.exe (PID: 6676)
Gets a random number, or selects objects randomly from a collection (POWERSHELL)
- powershell.exe (PID: 5756)
- powershell.exe (PID: 7748)
- powershell.exe (PID: 1324)
- powershell.exe (PID: 8144)
Checks whether the specified file exists (POWERSHELL)
- powershell.exe (PID: 5756)
- powershell.exe (PID: 1324)
- powershell.exe (PID: 7748)
- powershell.exe (PID: 8144)
Converts byte array into ASCII string (POWERSHELL)
- powershell.exe (PID: 5756)
- powershell.exe (PID: 1324)
- powershell.exe (PID: 7748)
- powershell.exe (PID: 8144)
Creates a byte array (POWERSHELL)
- powershell.exe (PID: 5756)
- powershell.exe (PID: 7748)
- powershell.exe (PID: 1324)
- powershell.exe (PID: 8144)
Checks operating system version
- cmd.exe (PID: 7968)
- cmd.exe (PID: 5084)
- cmd.exe (PID: 4756)
Checks current location (POWERSHELL)
- powershell.exe (PID: 5756)
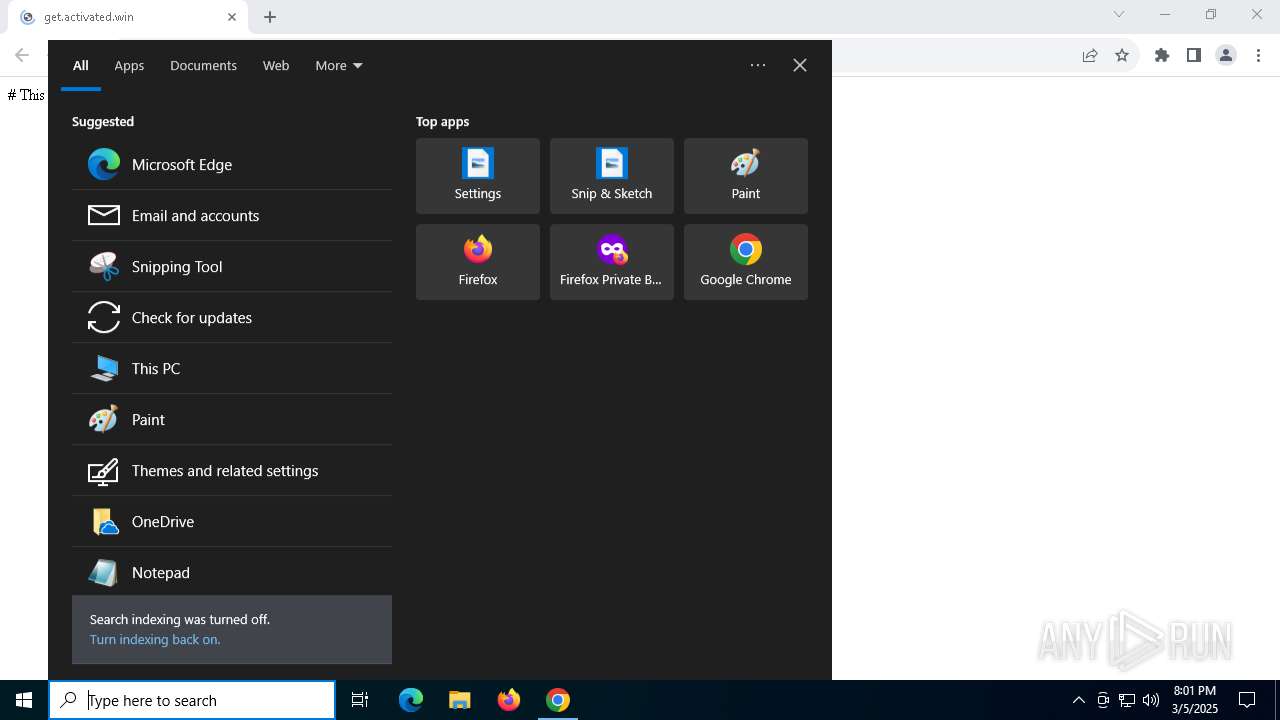
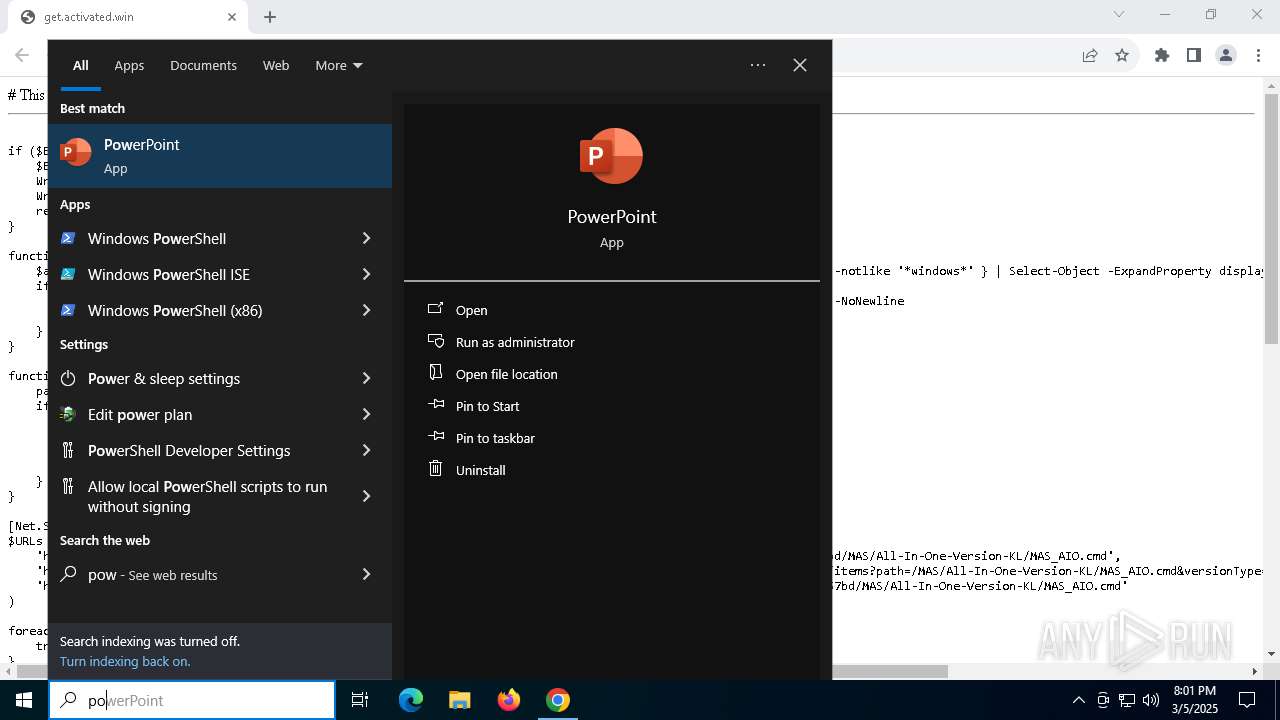
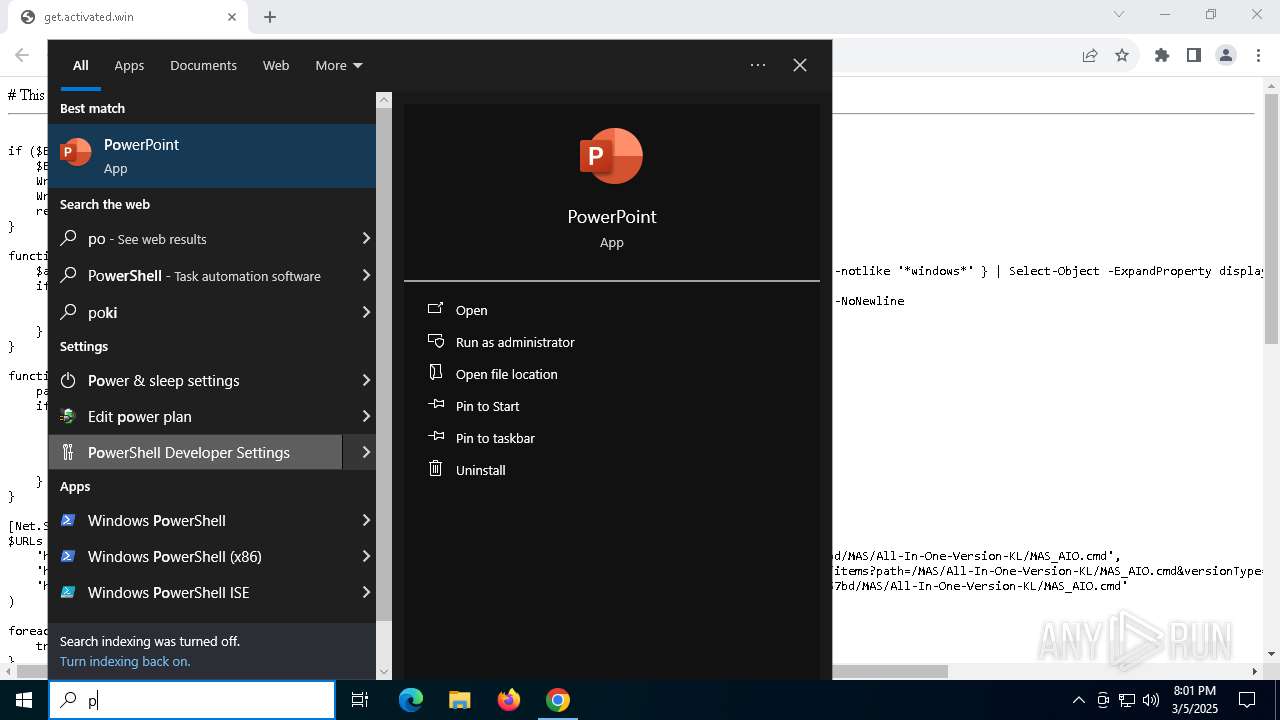
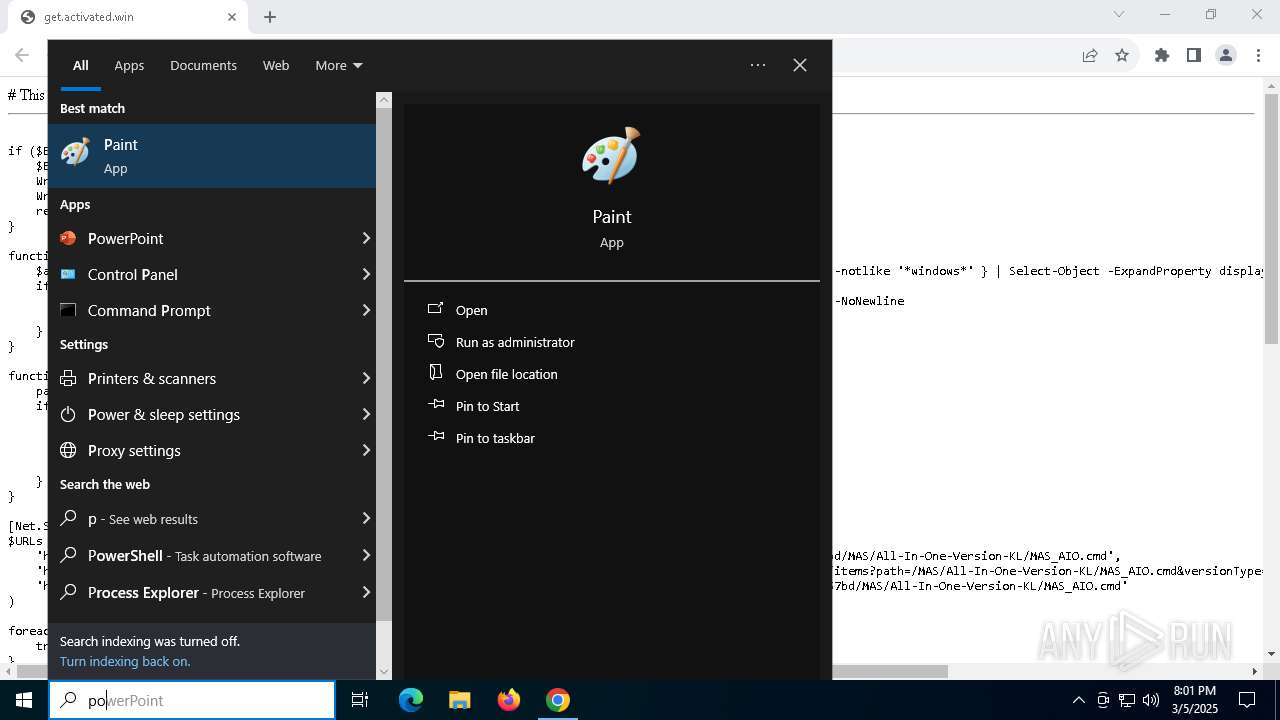
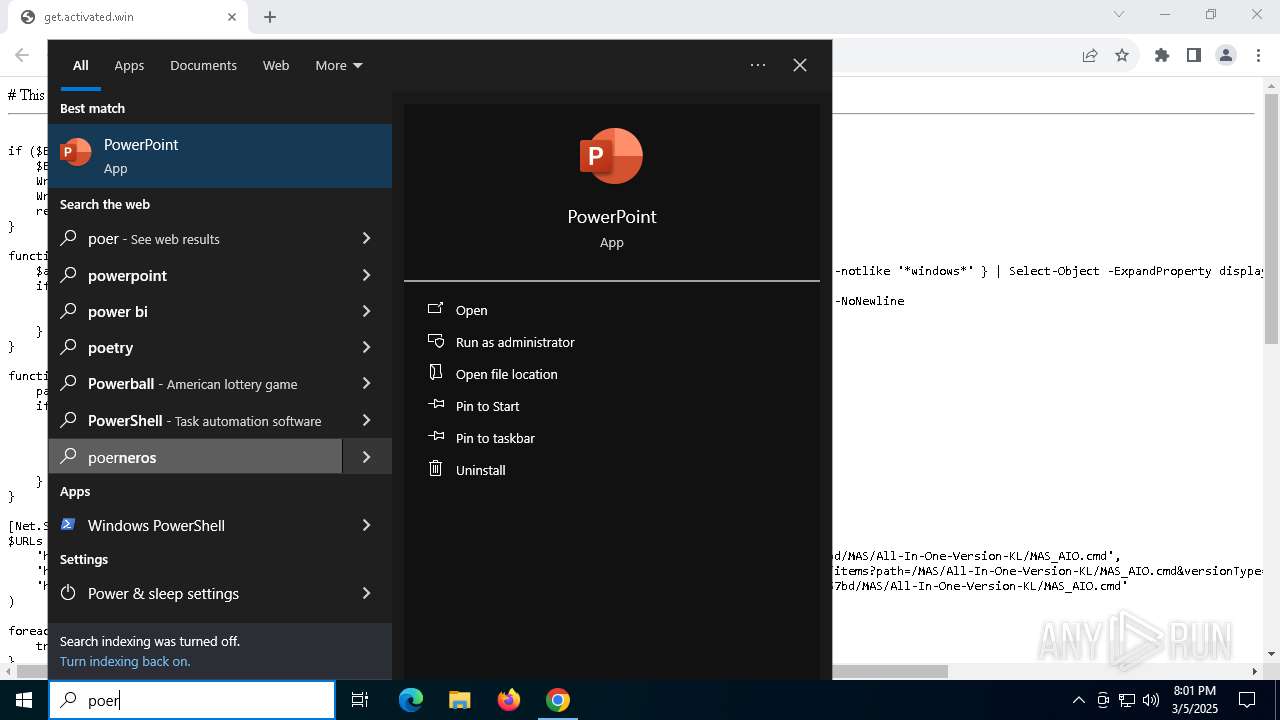
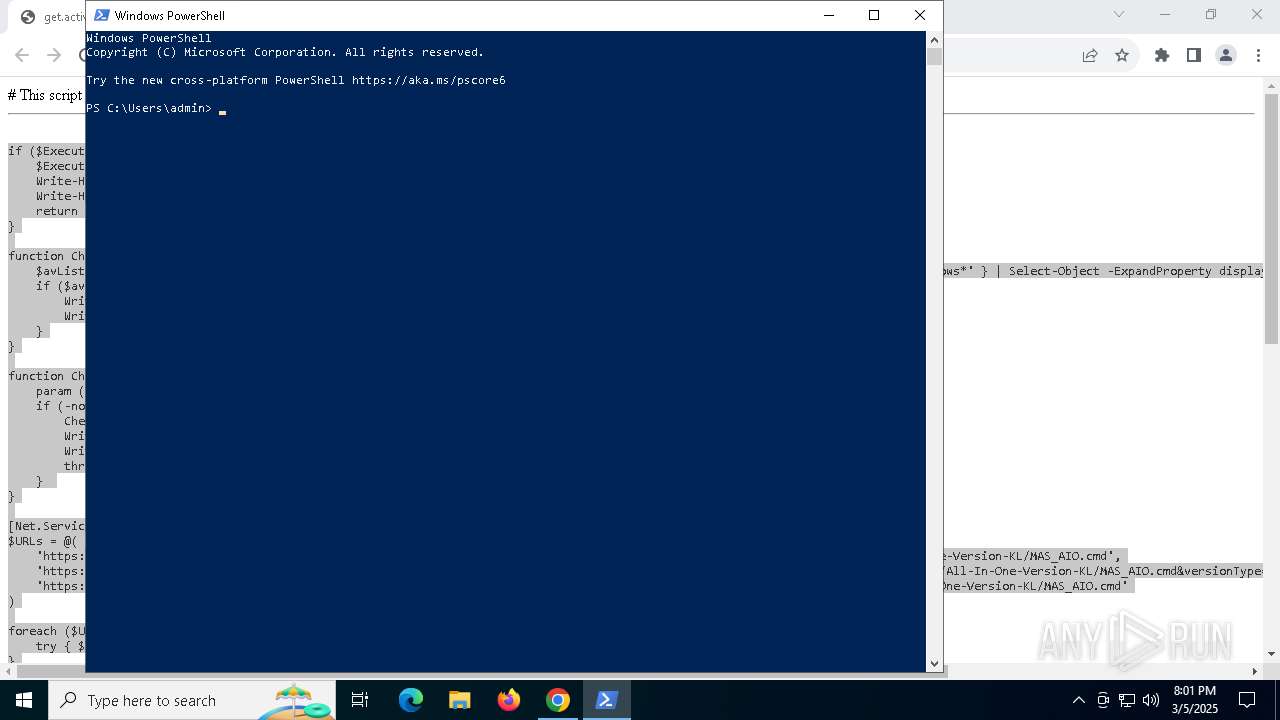
Manual execution by a user
- powershell.exe (PID: 5756)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
219
Monitored processes
82
Malicious processes
6
Suspicious processes
8
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 668 | powershell.exe "start cmd.exe -arg '/c \""""C:\Users\admin\AppData\Local\Temp\MAS_87251111-bcda-49de-9fdf-c6c4cda29ba0.cmd""" -el \"' -verb runas" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 856 | C:\WINDOWS\System32\cmd.exe /c echo prompt $E | cmd | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 856 | fltmc | C:\Windows\System32\fltMC.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Filter Manager Control Program Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 968 | findstr /v "f7f81a39-5f63-5b42-9efd-1f13b5431005quot; "MAS_87251111-bcda-49de-9fdf-c6c4cda29ba0.cmd" | C:\Windows\System32\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Find String (QGREP) Utility Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1040 | "BackgroundTransferHost.exe" -ServerName:BackgroundTransferHost.1 | C:\Windows\System32\BackgroundTransferHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Download/Upload Host Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1052 | C:\WINDOWS\System32\cmd.exe /S /D /c" echo "C:\Users\admin\AppData\Local\Temp\MAS_87251111-bcda-49de-9fdf-c6c4cda29ba0.cmd" " | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1088 | fltmc | C:\Windows\System32\fltMC.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Filter Manager Control Program Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1096 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1324 | reg query "HKCU\Console" /v ForceV2 | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1324 | powershell.exe "$f=[io.file]::ReadAllText('C:\Users\admin\AppData\Local\Temp\MAS_87251111-bcda-49de-9fdf-c6c4cda29ba0.cmd') -split ':PStest:\s*';iex ($f[1])" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
35 931
Read events
35 911
Write events
20
Delete events
0
Modification events
| (PID) Process: | (2516) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2516) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2516) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2516) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (2516) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (6560) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (6560) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (6560) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (6676) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (6676) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
Executable files
0
Suspicious files
37
Text files
34
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2516 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old~RF10d718.TMP | — | |
MD5:— | SHA256:— | |||
| 2516 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2516 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old~RF10d737.TMP | — | |
MD5:— | SHA256:— | |||
| 2516 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2516 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old~RF10d737.TMP | — | |
MD5:— | SHA256:— | |||
| 2516 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old~RF10d737.TMP | — | |
MD5:— | SHA256:— | |||
| 2516 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2516 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2516 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF10d737.TMP | — | |
MD5:— | SHA256:— | |||
| 2516 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
48
DNS requests
24
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6544 | svchost.exe | GET | 200 | 23.40.158.218:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6036 | backgroundTaskHost.exe | GET | 200 | 23.40.158.218:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
2924 | SearchApp.exe | GET | 200 | 23.40.158.218:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
2692 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
6676 | BackgroundTransferHost.exe | GET | 200 | 23.40.158.218:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
2692 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2104 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5496 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3216 | svchost.exe | 40.113.110.67:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6544 | svchost.exe | 20.190.159.71:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6544 | svchost.exe | 23.40.158.218:80 | ocsp.digicert.com | AKAMAI-AS | MX | whitelisted |
2516 | chrome.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
7320 | chrome.exe | 172.67.219.75:443 | get.activated.win | CLOUDFLARENET | US | malicious |
7320 | chrome.exe | 142.250.153.84:443 | accounts.google.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
get.activated.win |
| malicious |
accounts.google.com |
| whitelisted |
www.bing.com |
| whitelisted |
a.nel.cloudflare.com |
| whitelisted |
www.google.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7320 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
7320 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |