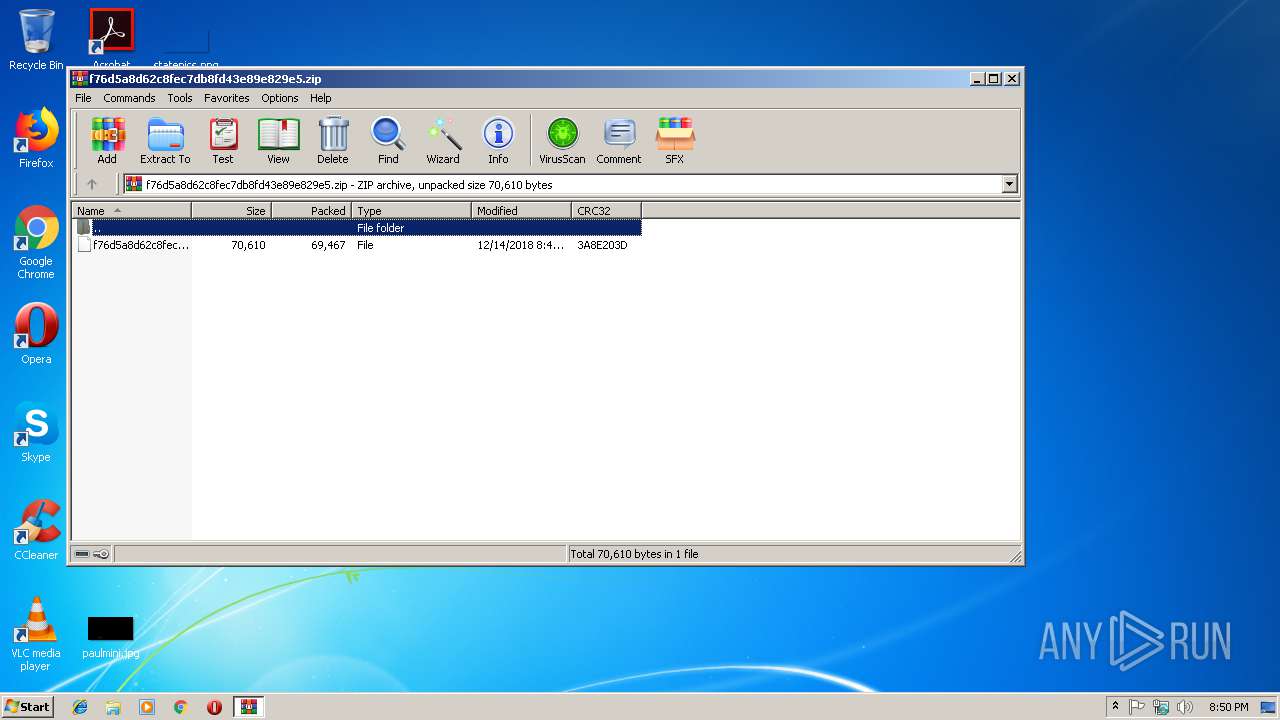
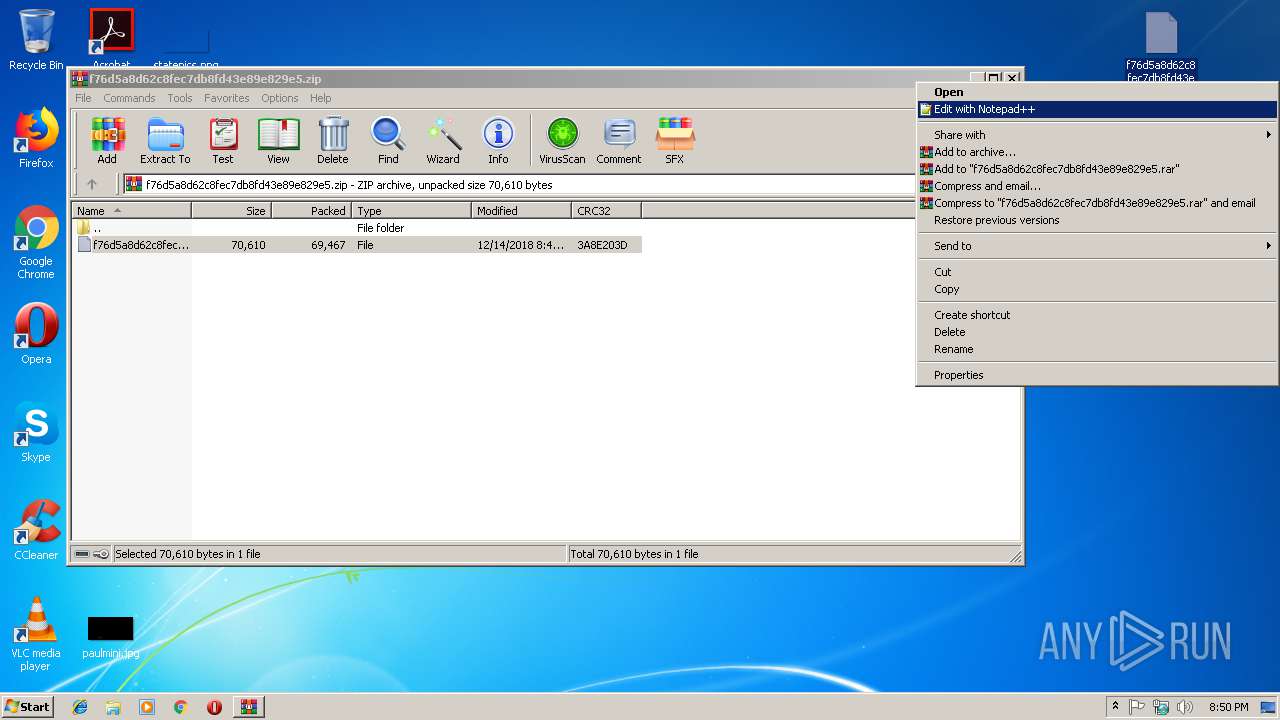
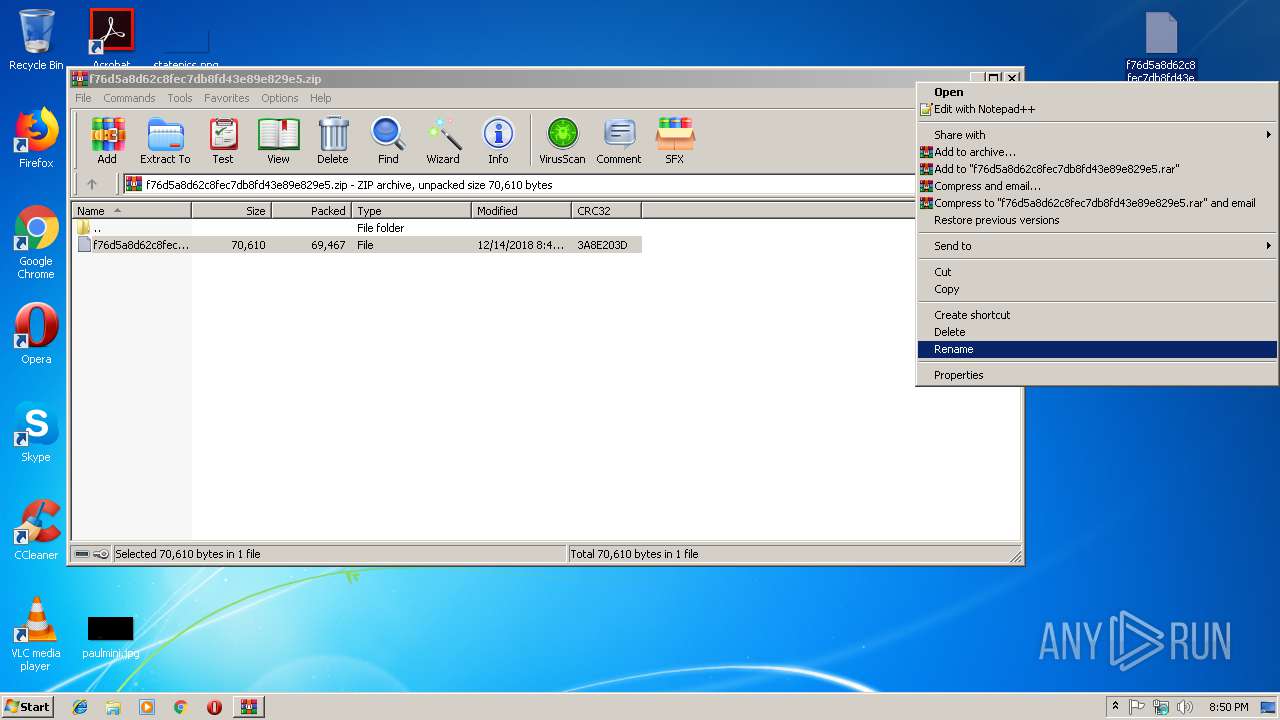
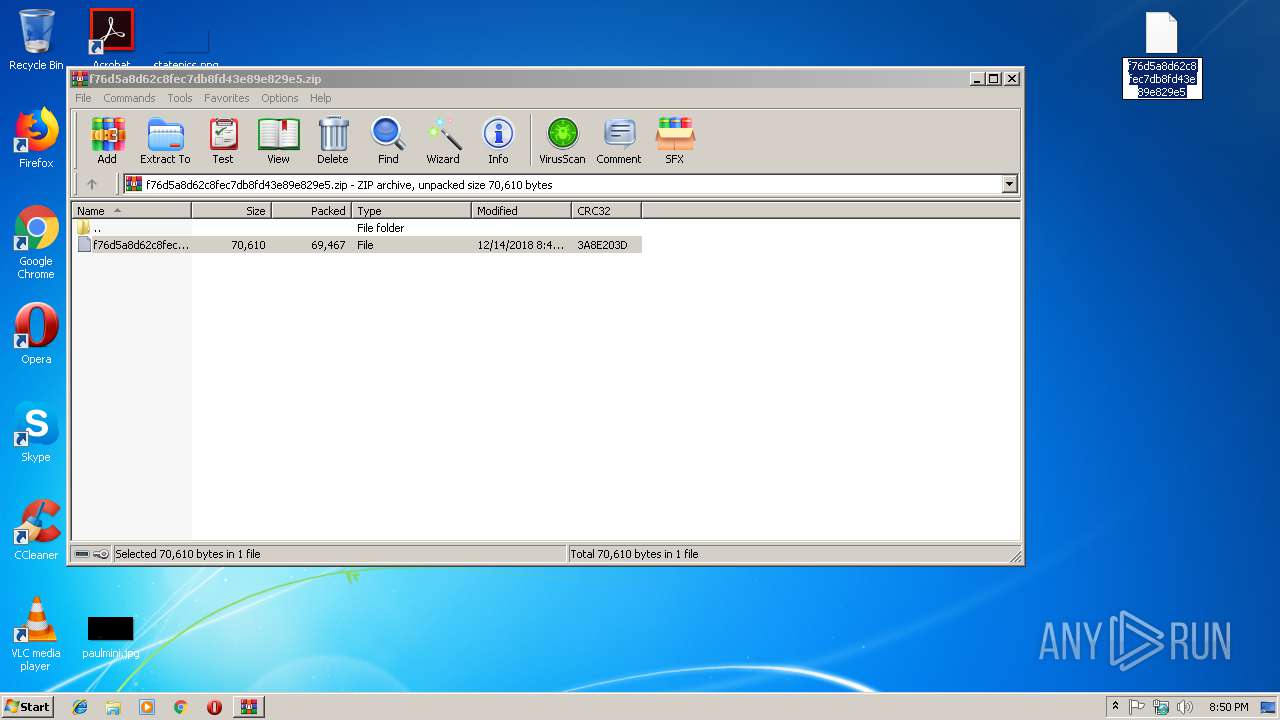
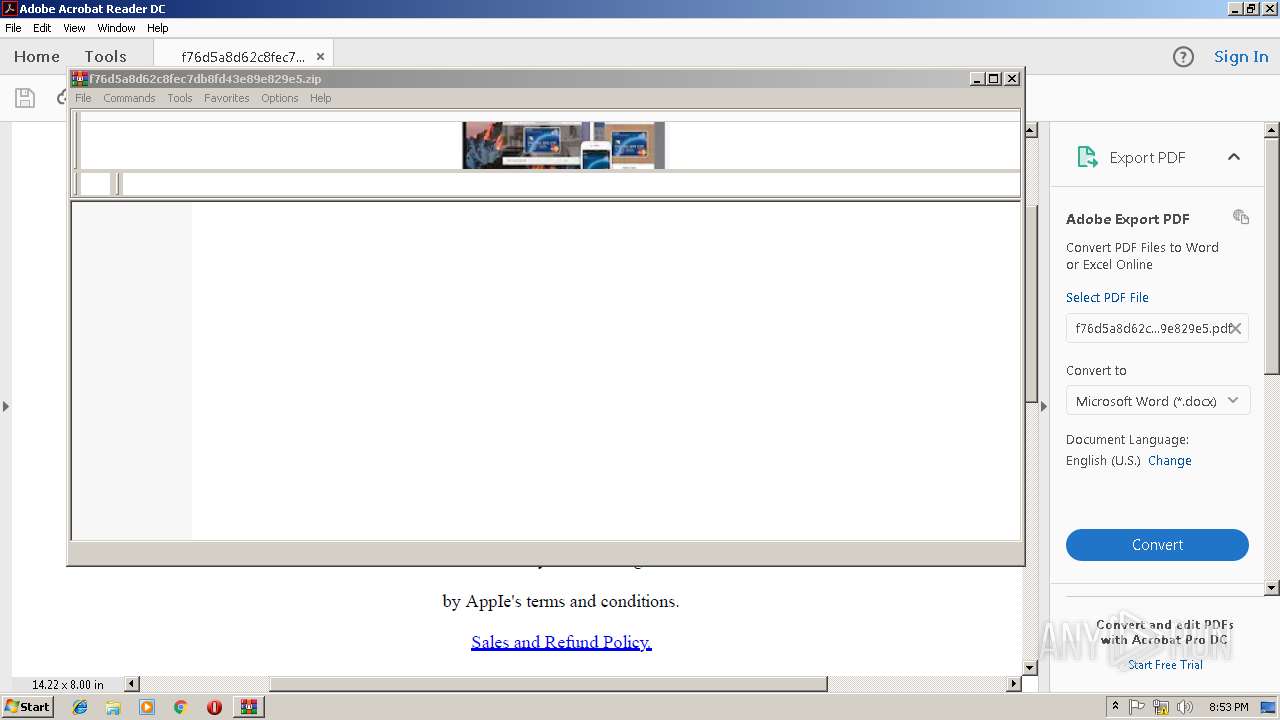
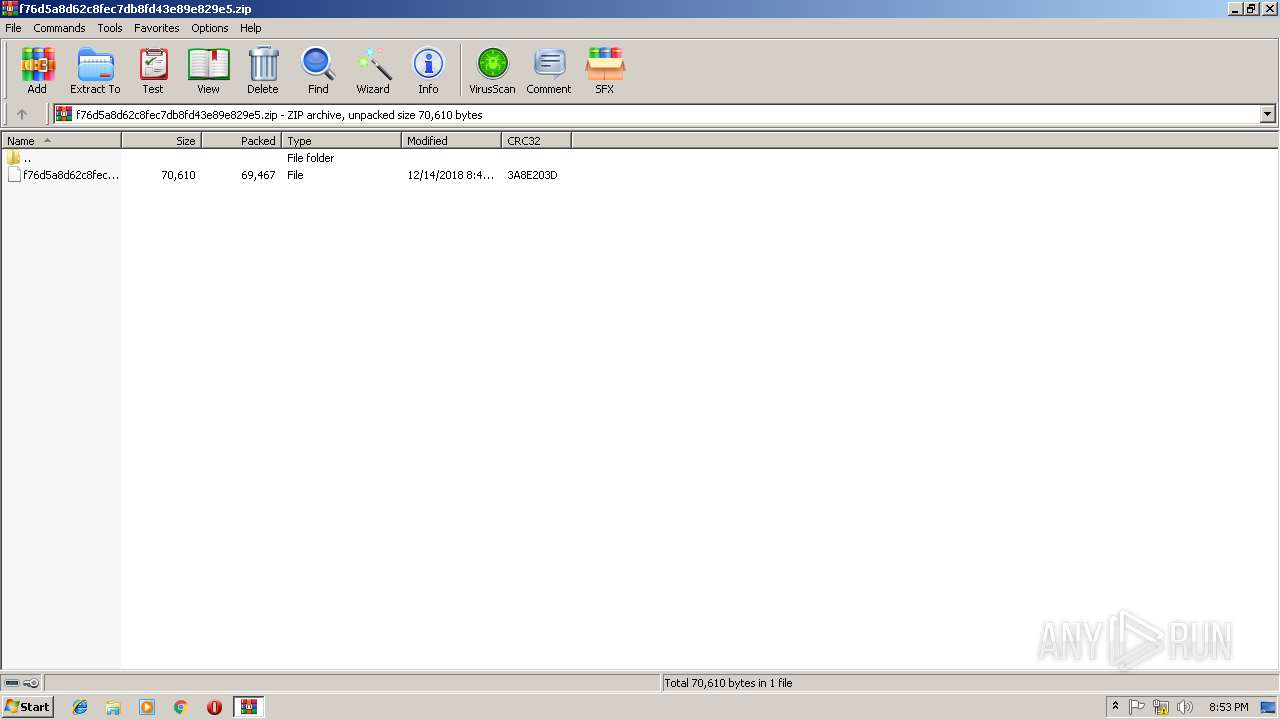
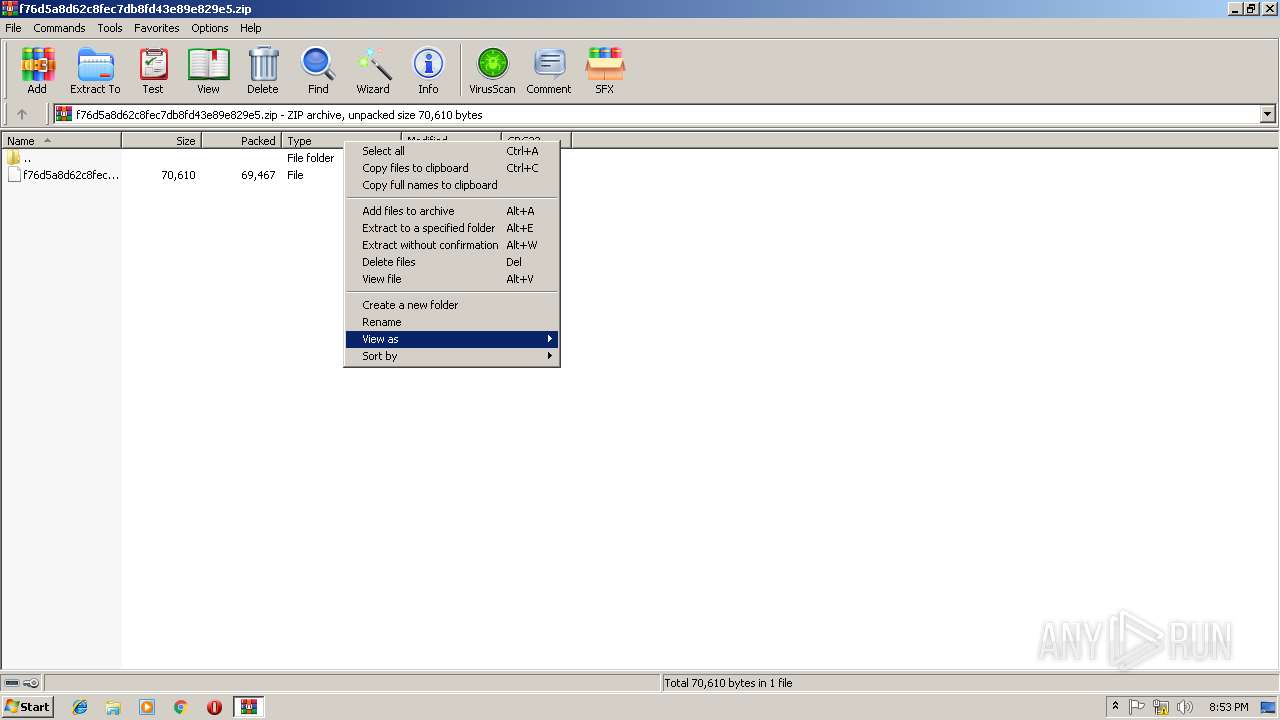
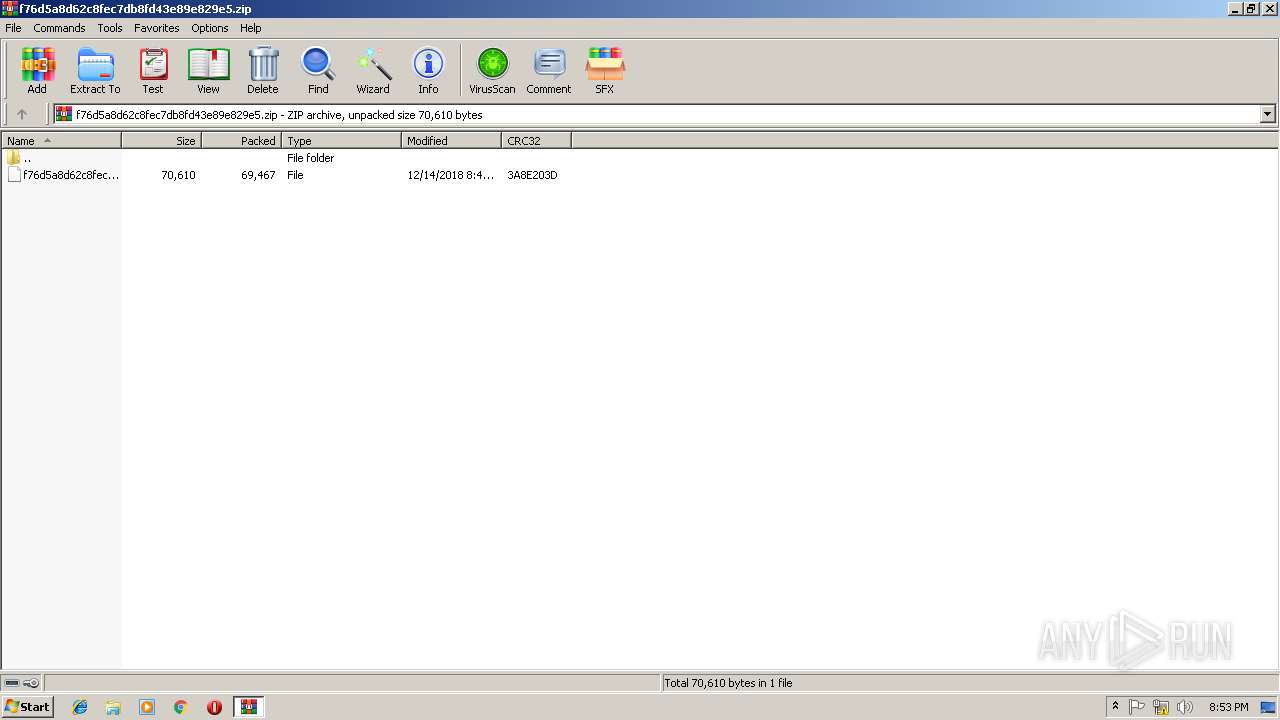
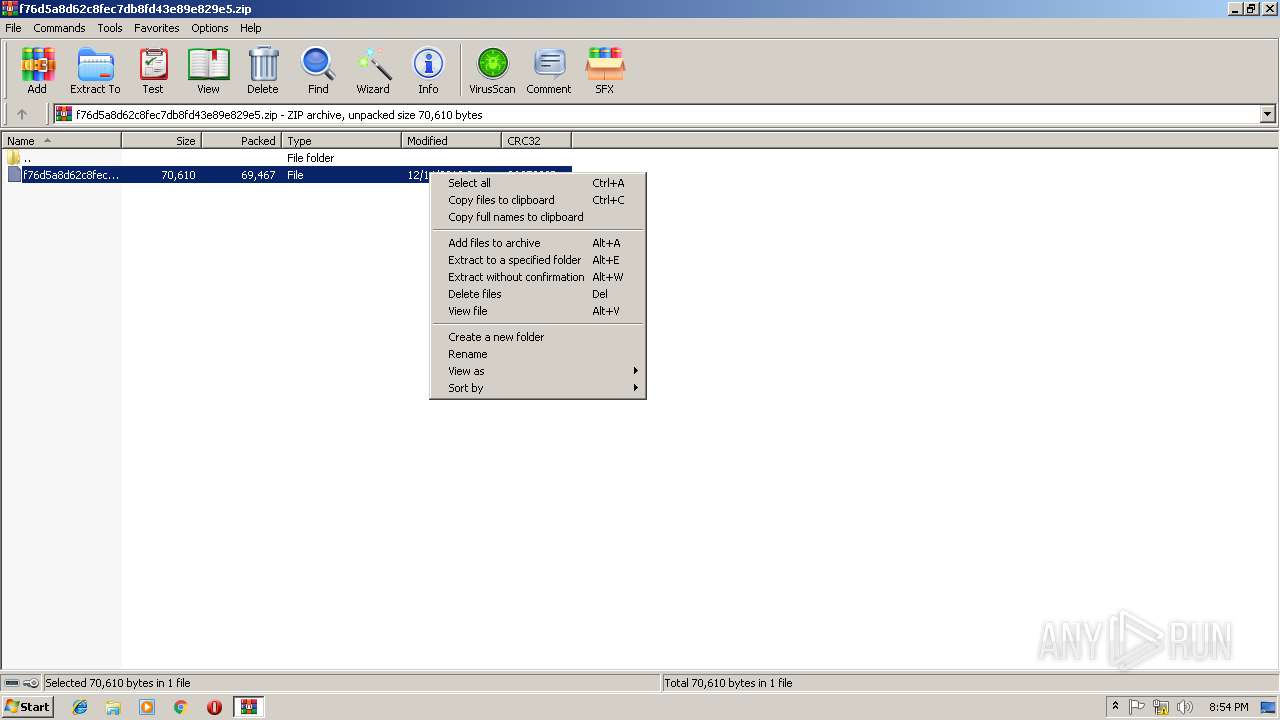
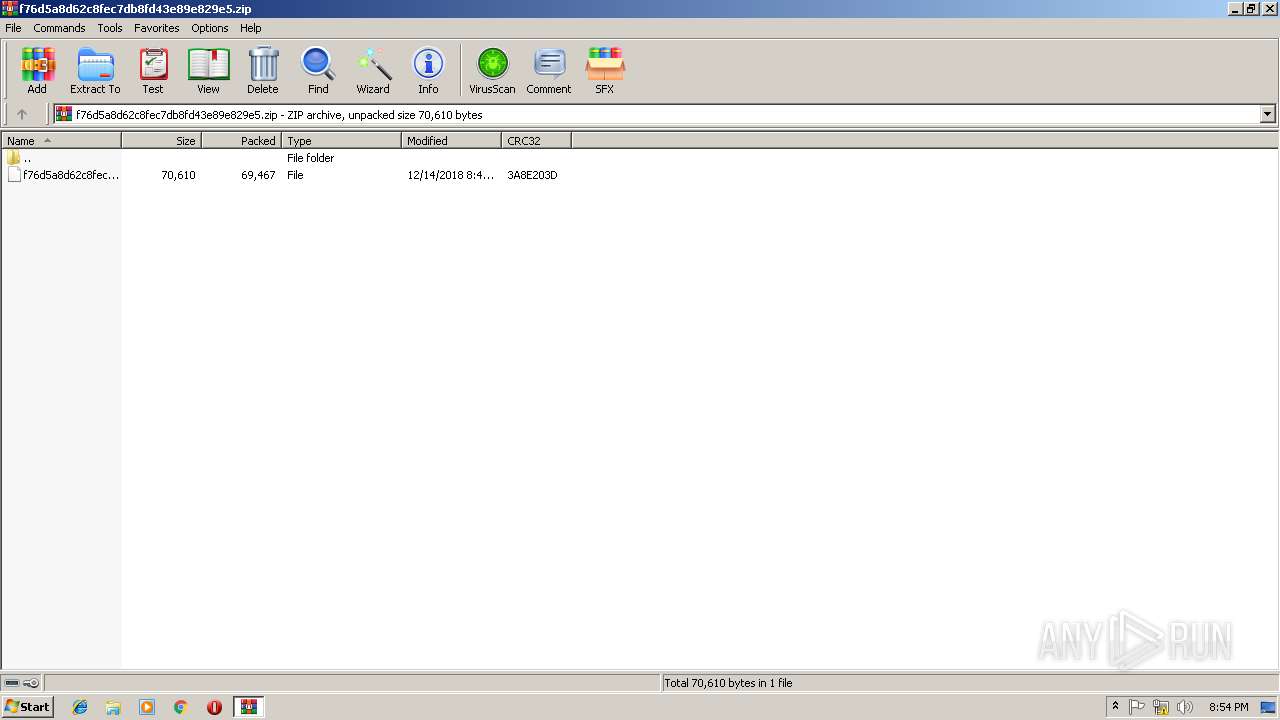
| File name: | f76d5a8d62c8fec7db8fd43e89e829e5.zip |
| Full analysis: | https://app.any.run/tasks/7c8dba1d-6eac-41b9-ac82-991077d5e077 |
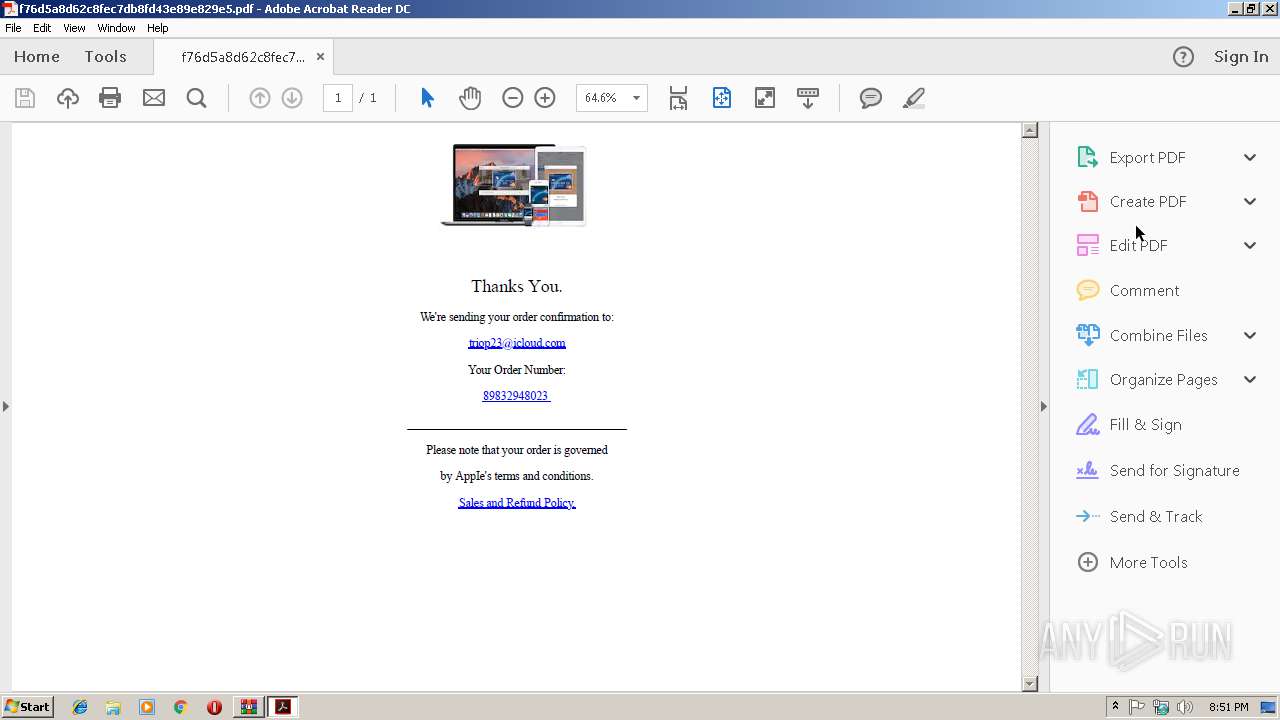
| Verdict: | Malicious activity |
| Analysis date: | December 14, 2018, 20:50:00 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 7E4C18B885CF6121C0314176C649ABCC |
| SHA1: | 1AAA6AECFDFDF5FDC1CA9282AD1404BDC17BD2FA |
| SHA256: | DA1D5EB42FC22D8E51A55802EAEF549182A816F7DE197E7EF7B4CC36B3BFB70C |
| SSDEEP: | 1536:nLw40Hr3iOO/YvXRGPCqkQA17GUp3wJ8stnK:nLubiOJvwaXL17GW3wKspK |
MALICIOUS
Loads the Task Scheduler COM API
- MsiExec.exe (PID: 3456)
- MsiExec.exe (PID: 2532)
SUSPICIOUS
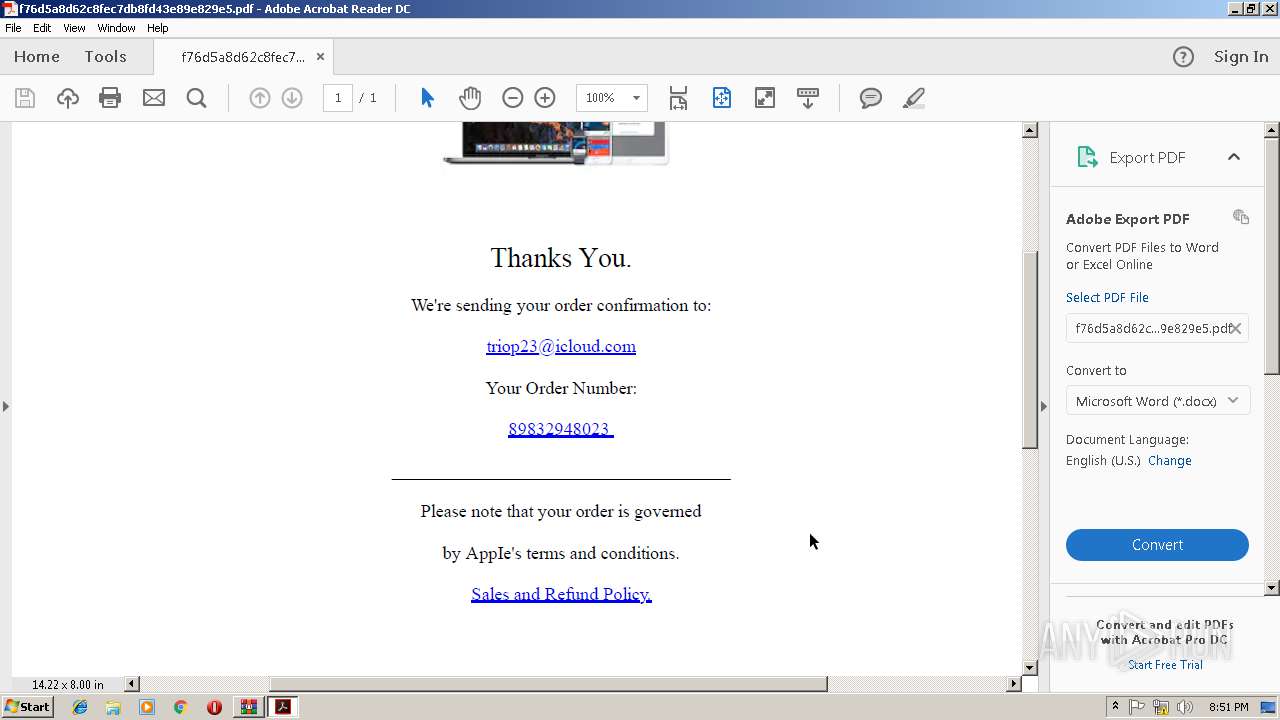
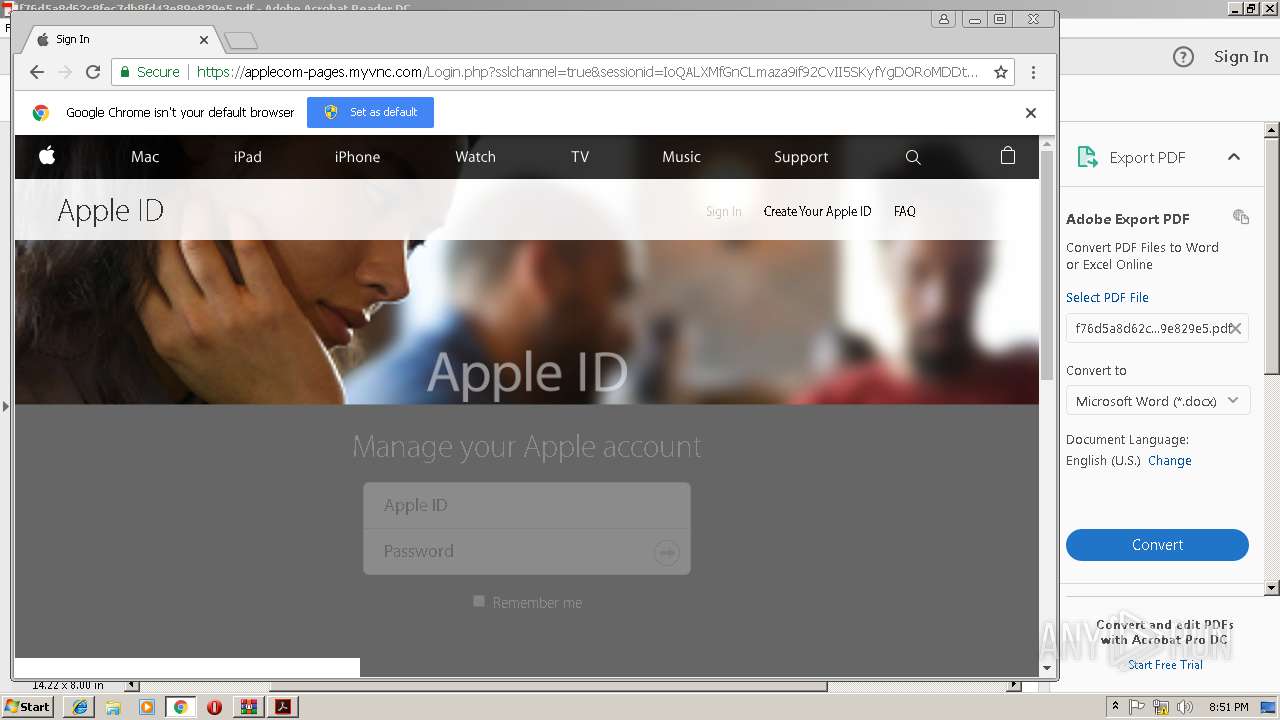
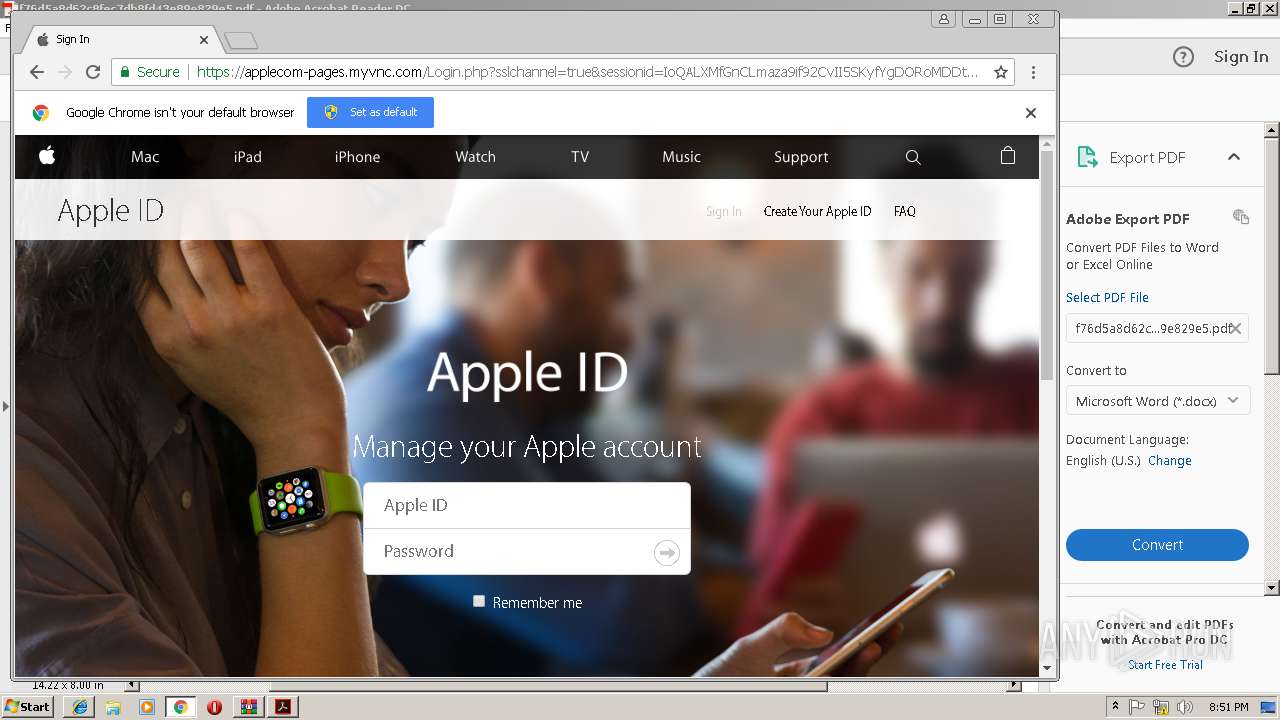
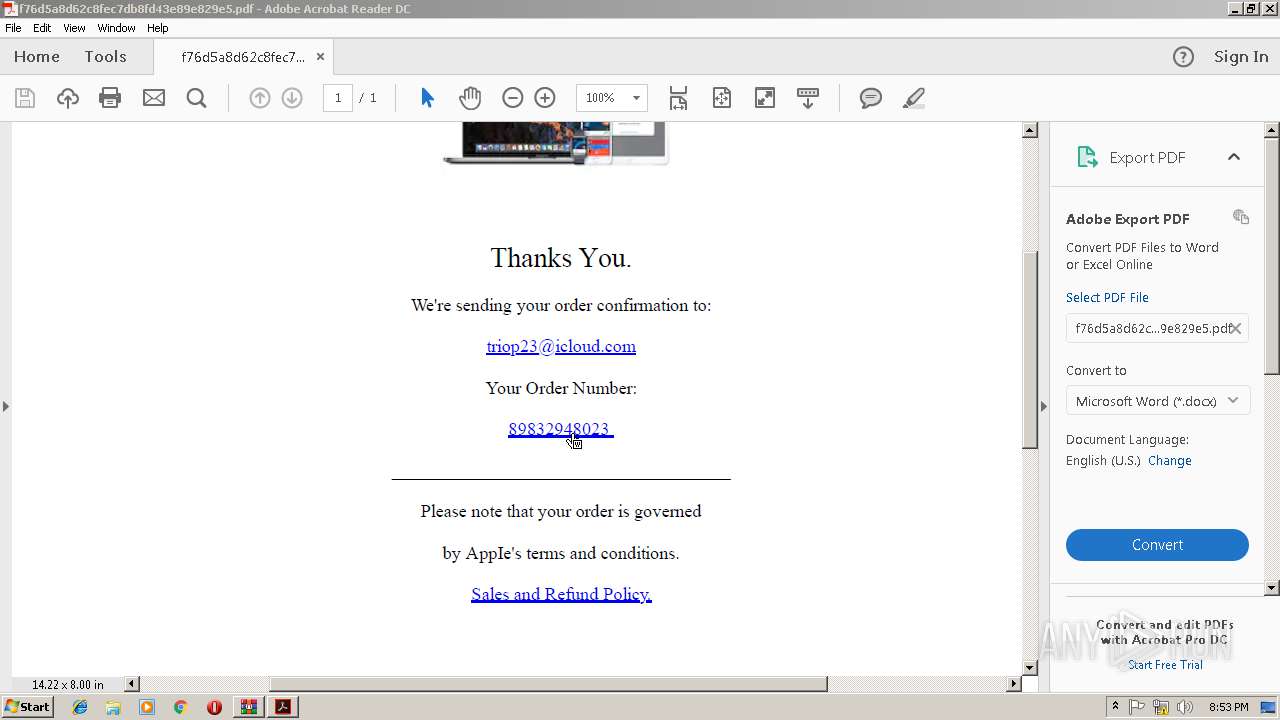
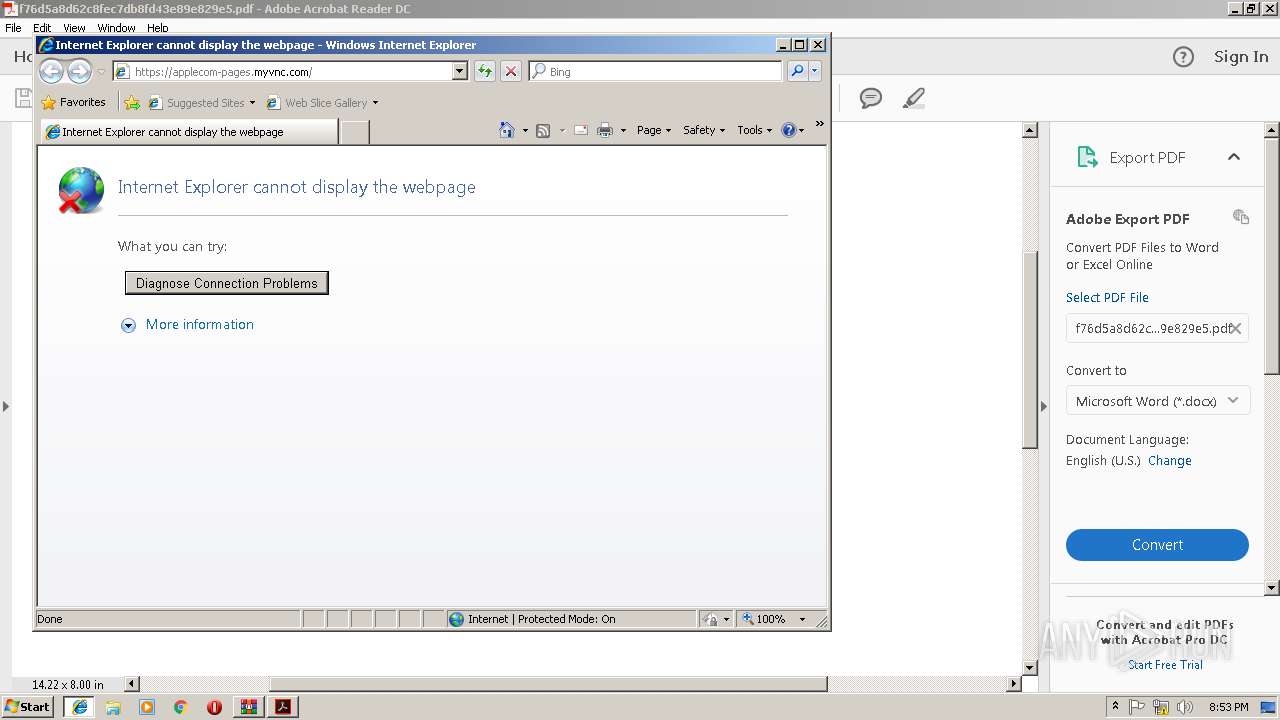
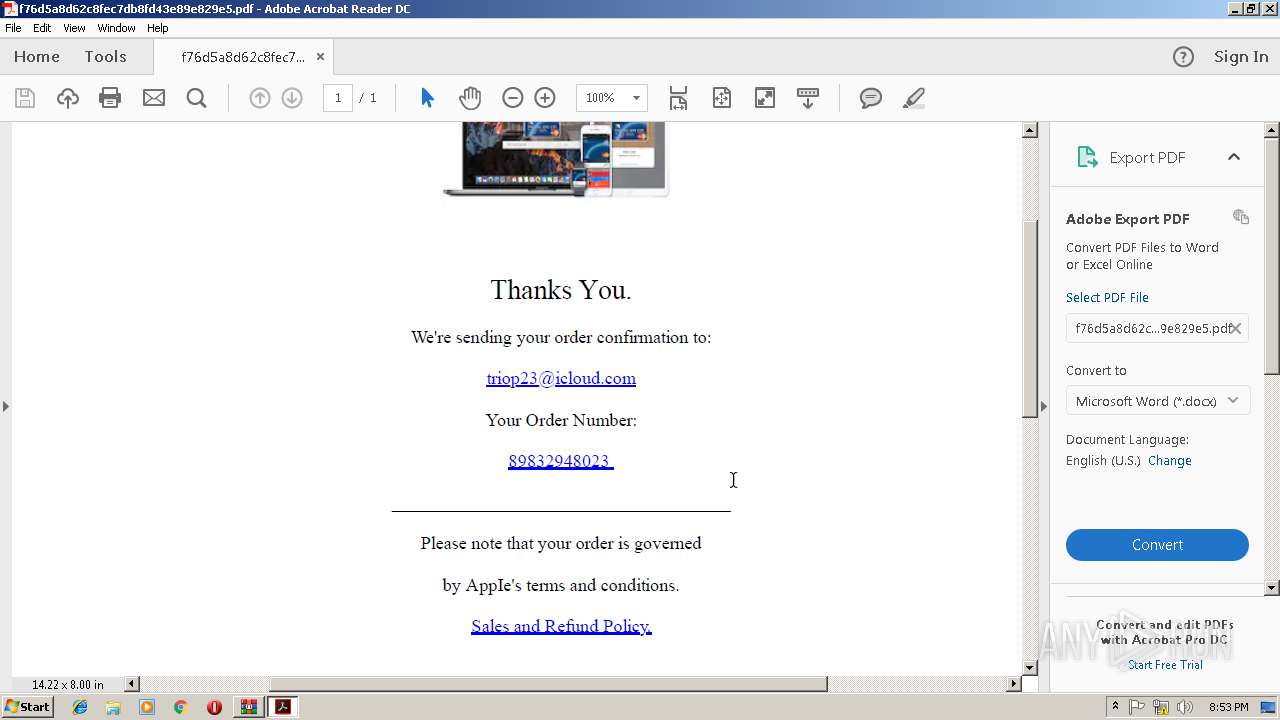
Starts Internet Explorer
- AcroRd32.exe (PID: 2416)
Executable content was dropped or overwritten
- AdobeARM.exe (PID: 2836)
Creates files in the program directory
- AdobeARM.exe (PID: 2836)
INFO
Application launched itself
- AcroRd32.exe (PID: 2416)
- RdrCEF.exe (PID: 2316)
- chrome.exe (PID: 3540)
- iexplore.exe (PID: 3628)
- msiexec.exe (PID: 3592)
Reads Internet Cache Settings
- iexplore.exe (PID: 2144)
- iexplore.exe (PID: 3892)
- iexplore.exe (PID: 3740)
Changes internet zones settings
- iexplore.exe (PID: 3672)
- iexplore.exe (PID: 3628)
- iexplore.exe (PID: 2980)
Reads internet explorer settings
- iexplore.exe (PID: 2144)
- iexplore.exe (PID: 3892)
- iexplore.exe (PID: 3740)
Creates files in the user directory
- iexplore.exe (PID: 3672)
- AcroRd32.exe (PID: 2416)
Creates files in the program directory
- msiexec.exe (PID: 3592)
Reads settings of System Certificates
- msiexec.exe (PID: 3592)
Creates a software uninstall entry
- msiexec.exe (PID: 3592)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
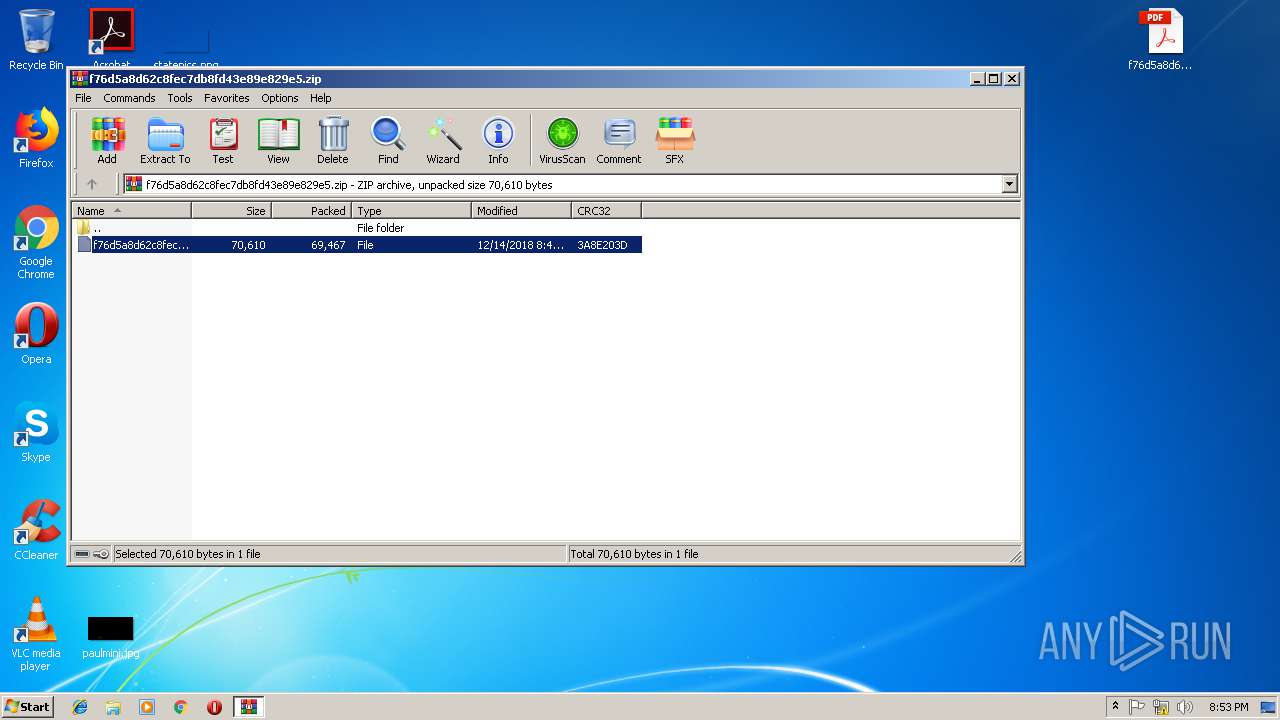
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
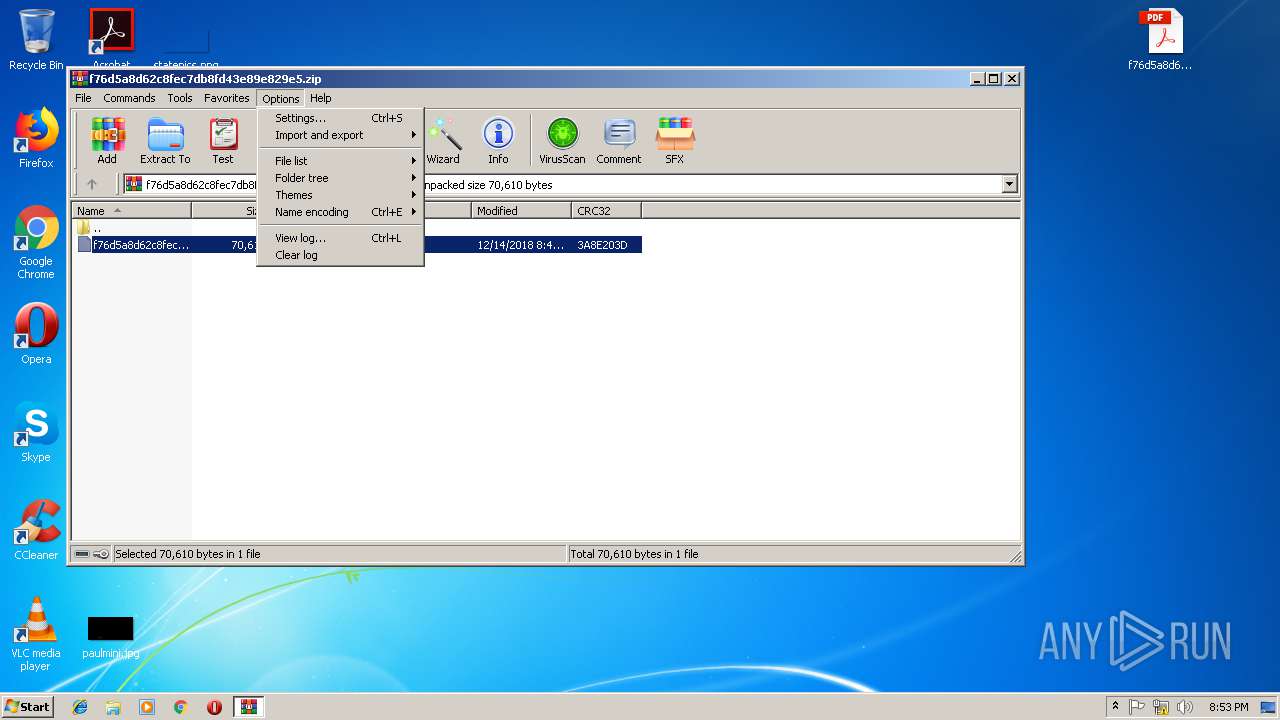
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
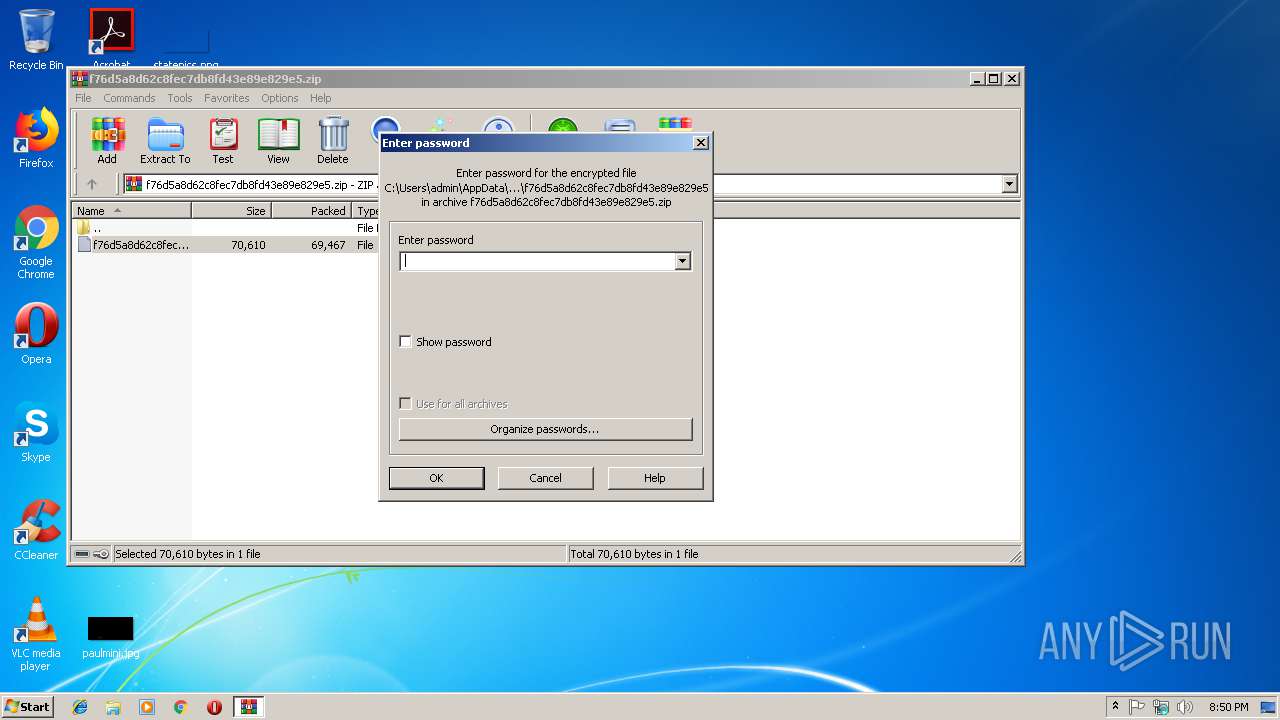
| ZipBitFlag: | 0x0009 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2018:12:14 14:43:06 |
| ZipCRC: | 0x3a8e203d |
| ZipCompressedSize: | 69467 |
| ZipUncompressedSize: | 70610 |
| ZipFileName: | f76d5a8d62c8fec7db8fd43e89e829e5 |
Total processes
59
Monitored processes
28
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 916 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=964,16967714429937657404,9953281958399892548,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=1C93AA7CD70F3FDF9417B9815B6730B2 --mojo-platform-channel-handle=3652 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 1348 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=3524 --on-initialized-event-handle=304 --parent-handle=308 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2112 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\Reader_sl.exe" | C:\Program Files\Adobe\Acrobat Reader DC\Reader\Reader_sl.exe | — | AdobeARM.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: MEDIUM Description: Adobe Acrobat SpeedLauncher Exit code: 0 Version: 15.23.20053.211670 Modules
| |||||||||||||||
| 2144 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3672 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2236 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe" --type=renderer "C:\Users\admin\Desktop\f76d5a8d62c8fec7db8fd43e89e829e5.pdf" | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe | — | AcroRd32.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: LOW Description: Adobe Acrobat Reader DC Exit code: 1 Version: 15.23.20070.215641 Modules
| |||||||||||||||
| 2304 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=964,16967714429937657404,9953281958399892548,131072 --enable-features=PasswordImport --service-pipe-token=9CB65E55A4A1A48C9D8756E64810CFE0 --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=9CB65E55A4A1A48C9D8756E64810CFE0 --renderer-client-id=3 --mojo-platform-channel-handle=2144 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2316 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe" --backgroundcolor=16448250 | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe | — | AcroRd32.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: MEDIUM Description: Adobe RdrCEF Exit code: 3221225547 Version: 15.23.20053.211670 Modules
| |||||||||||||||
| 2380 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=964,16967714429937657404,9953281958399892548,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=82E9D85207A47A08001450182DCAA19C --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=82E9D85207A47A08001450182DCAA19C --renderer-client-id=7 --mojo-platform-channel-handle=3896 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2416 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe" "C:\Users\admin\Desktop\f76d5a8d62c8fec7db8fd43e89e829e5.pdf" | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe | explorer.exe | ||||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: MEDIUM Description: Adobe Acrobat Reader DC Exit code: 1 Version: 15.23.20070.215641 Modules
| |||||||||||||||
| 2532 | C:\Windows\system32\MsiExec.exe -Embedding DD0EC78C81A7F829CFDC22A6A4AD2996 M Global\MSI0000 | C:\Windows\system32\MsiExec.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
2 580
Read events
2 212
Write events
343
Delete events
25
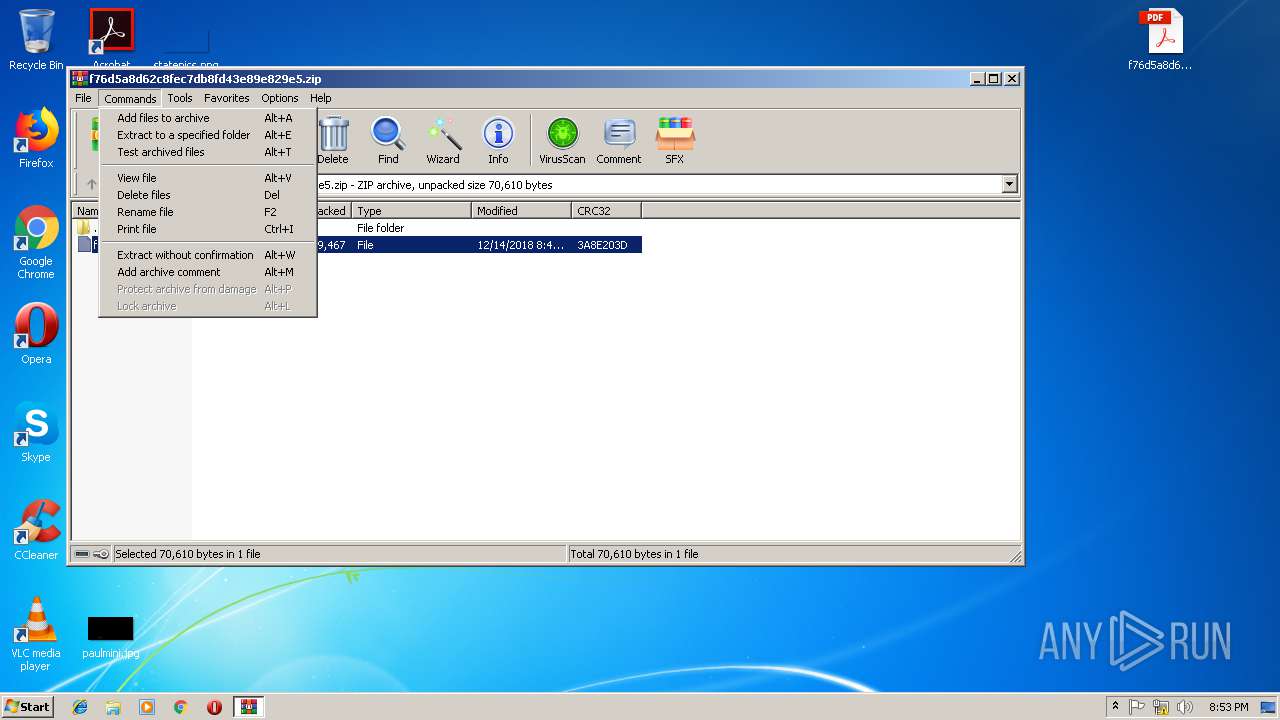
Modification events
| (PID) Process: | (3460) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3460) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3460) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3460) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\f76d5a8d62c8fec7db8fd43e89e829e5.zip | |||
| (PID) Process: | (3460) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3460) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3460) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3460) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (3460) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
| (PID) Process: | (2236) AcroRd32.exe | Key: | HKEY_CURRENT_USER\Software\Adobe\Acrobat Reader\DC\ExitSection |
| Operation: | write | Name: | bLastExitNormal |
Value: 0 | |||
Executable files
2
Suspicious files
87
Text files
155
Unknown types
23
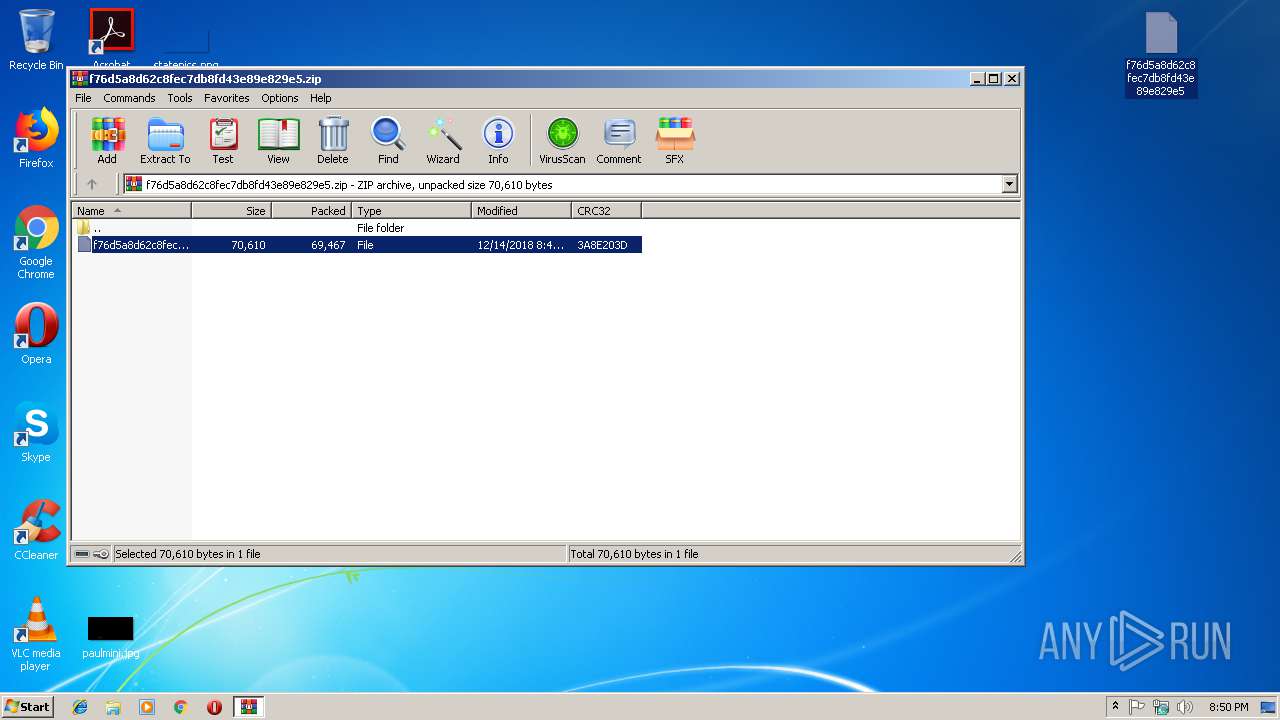
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3460 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb3460.13689\f76d5a8d62c8fec7db8fd43e89e829e5 | — | |
MD5:— | SHA256:— | |||
| 2236 | AcroRd32.exe | C:\Users\admin\AppData\LocalLow\Adobe\Acrobat\DC\ReaderMessages-journal | — | |
MD5:— | SHA256:— | |||
| 2236 | AcroRd32.exe | C:\Users\admin\AppData\Local\Temp\acrord32_sbx\A9R282085_i6cizz_1q4.tmp | — | |
MD5:— | SHA256:— | |||
| 2236 | AcroRd32.exe | C:\Users\admin\AppData\Local\Temp\acrord32_sbx\A9Rtdgdgj_i6cizy_1q4.tmp | — | |
MD5:— | SHA256:— | |||
| 2236 | AcroRd32.exe | C:\Users\admin\AppData\Local\Temp\acrord32_sbx\A9R1get5mf_i6cj01_1q4.tmp | — | |
MD5:— | SHA256:— | |||
| 2236 | AcroRd32.exe | C:\Users\admin\AppData\Local\Temp\acrord32_sbx\A9R7h2txu_i6cj00_1q4.tmp | — | |
MD5:— | SHA256:— | |||
| 2236 | AcroRd32.exe | C:\Users\admin\AppData\Local\Temp\acrord32_sbx\A9Ry4ab3p_i6cj02_1q4.tmp | — | |
MD5:— | SHA256:— | |||
| 3672 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\RB73MZ6Y\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 3672 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 3540 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Service Worker\Database\LOG.old | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
44
DNS requests
19
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2416 | AcroRd32.exe | GET | 304 | 2.16.186.33:80 | http://acroipm2.adobe.com/15/rdr/ENU/win/nooem/none/consumer/277_15_23_20070.zip | unknown | — | — | whitelisted |
2416 | AcroRd32.exe | GET | 304 | 2.16.186.33:80 | http://acroipm2.adobe.com/15/rdr/ENU/win/nooem/none/consumer/278_15_23_20070.zip | unknown | — | — | whitelisted |
2416 | AcroRd32.exe | GET | 304 | 2.16.186.33:80 | http://acroipm2.adobe.com/15/rdr/ENU/win/nooem/none/consumer/281_15_23_20070.zip | unknown | — | — | whitelisted |
2416 | AcroRd32.exe | GET | 304 | 2.16.186.33:80 | http://acroipm2.adobe.com/15/rdr/ENU/win/nooem/none/consumer/message.zip | unknown | — | — | whitelisted |
2416 | AcroRd32.exe | GET | 304 | 2.16.186.33:80 | http://acroipm2.adobe.com/15/rdr/ENU/win/nooem/none/consumer/280_15_23_20070.zip | unknown | — | — | whitelisted |
3672 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
3628 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
2980 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
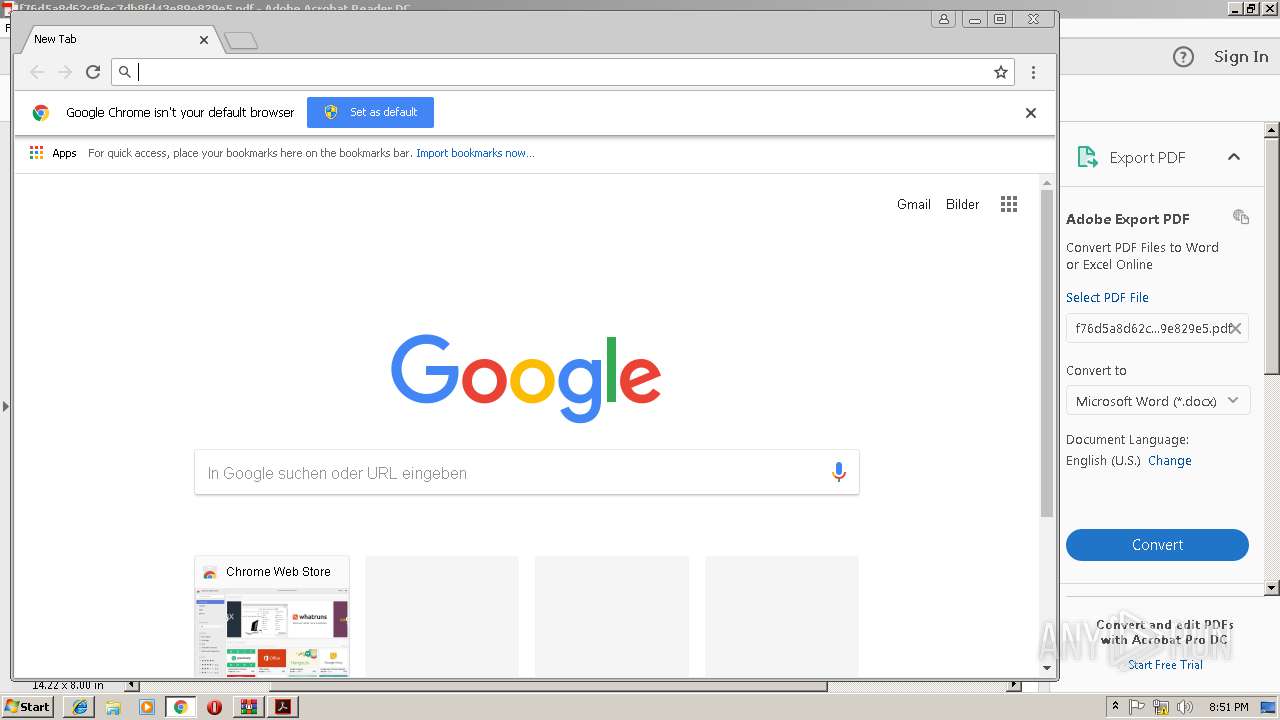
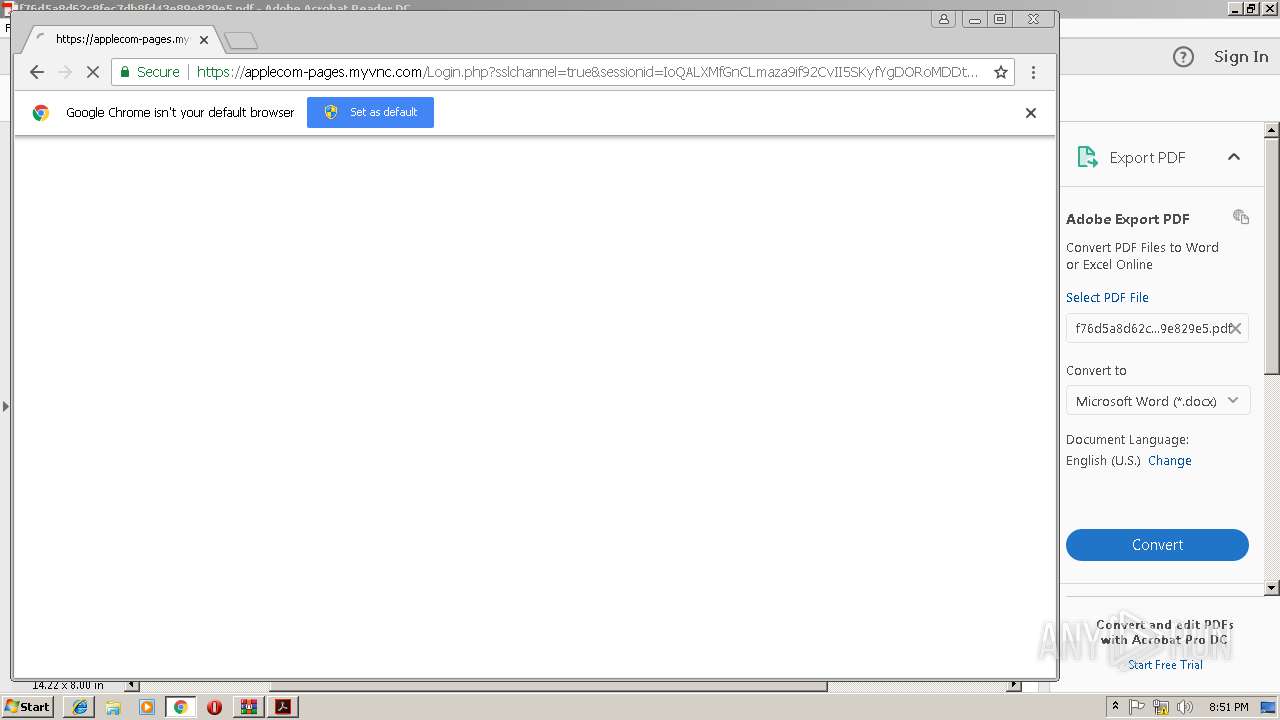
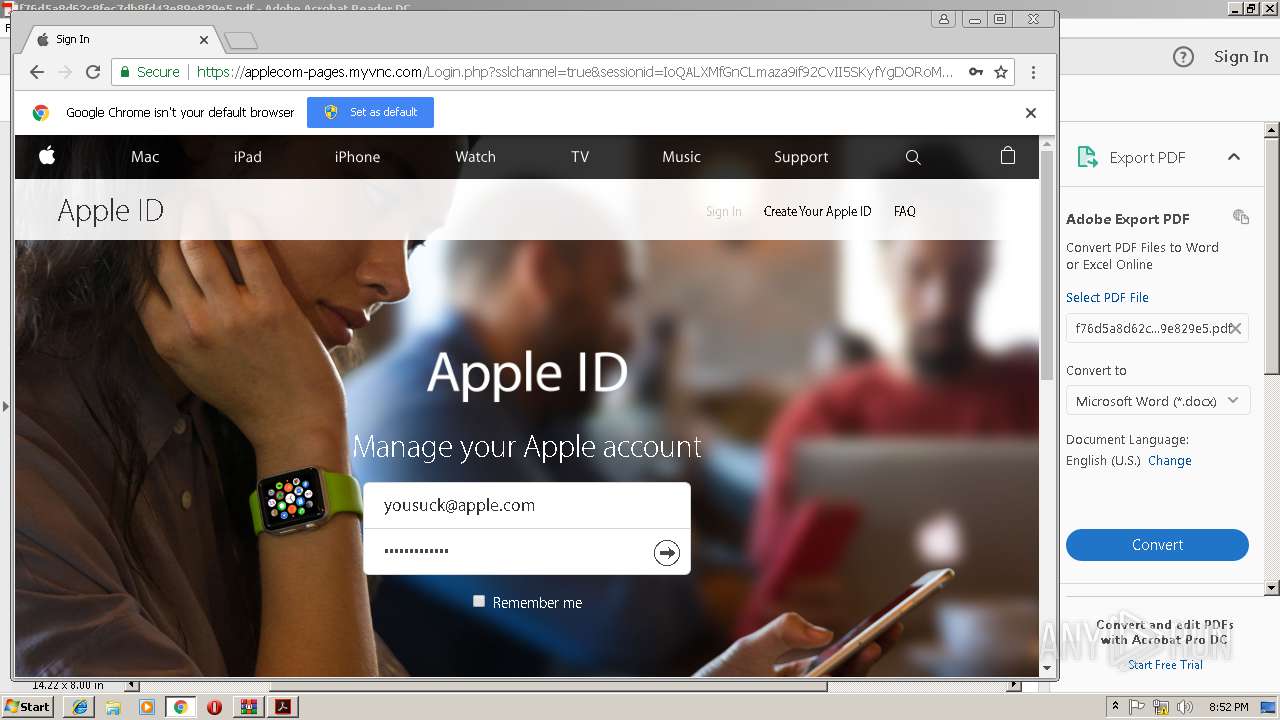
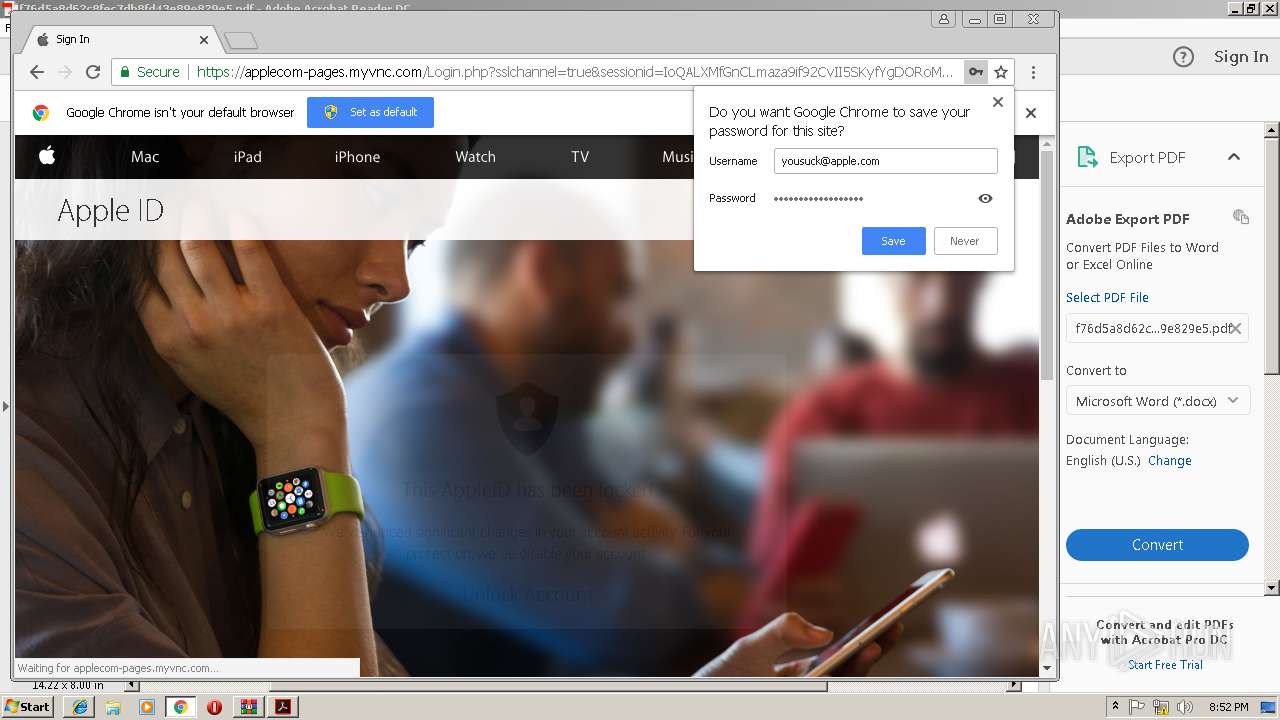
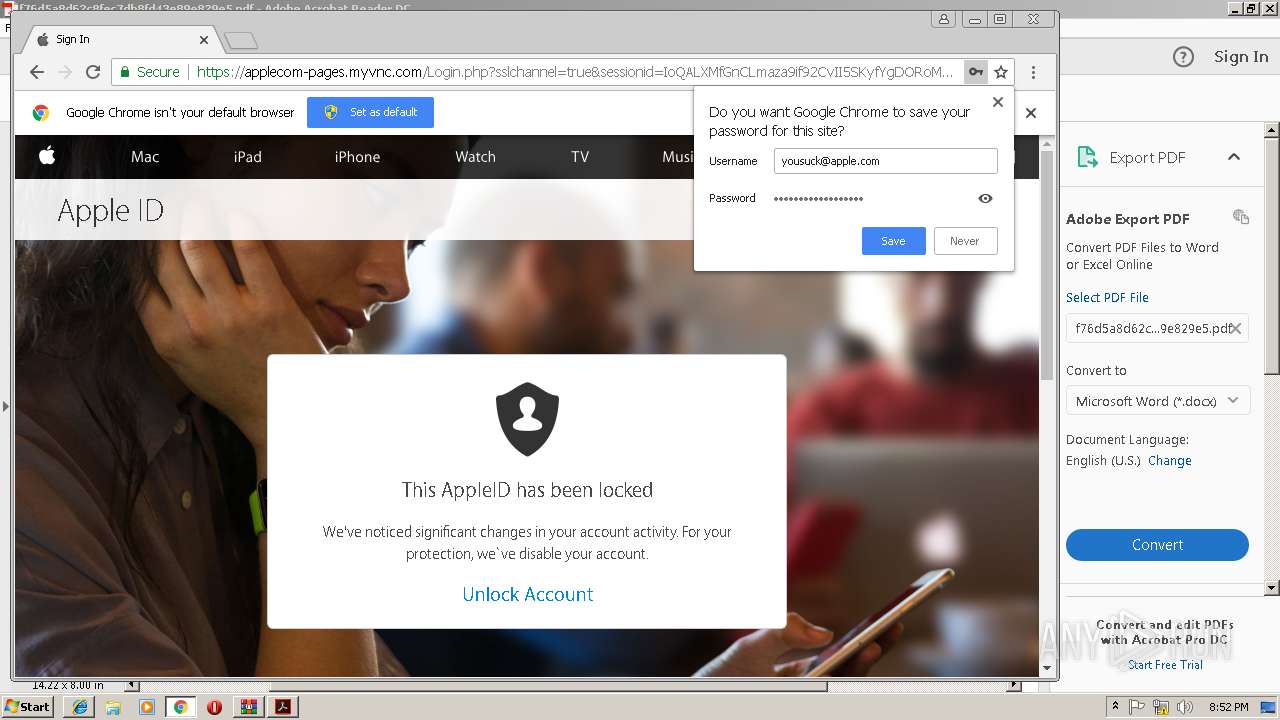
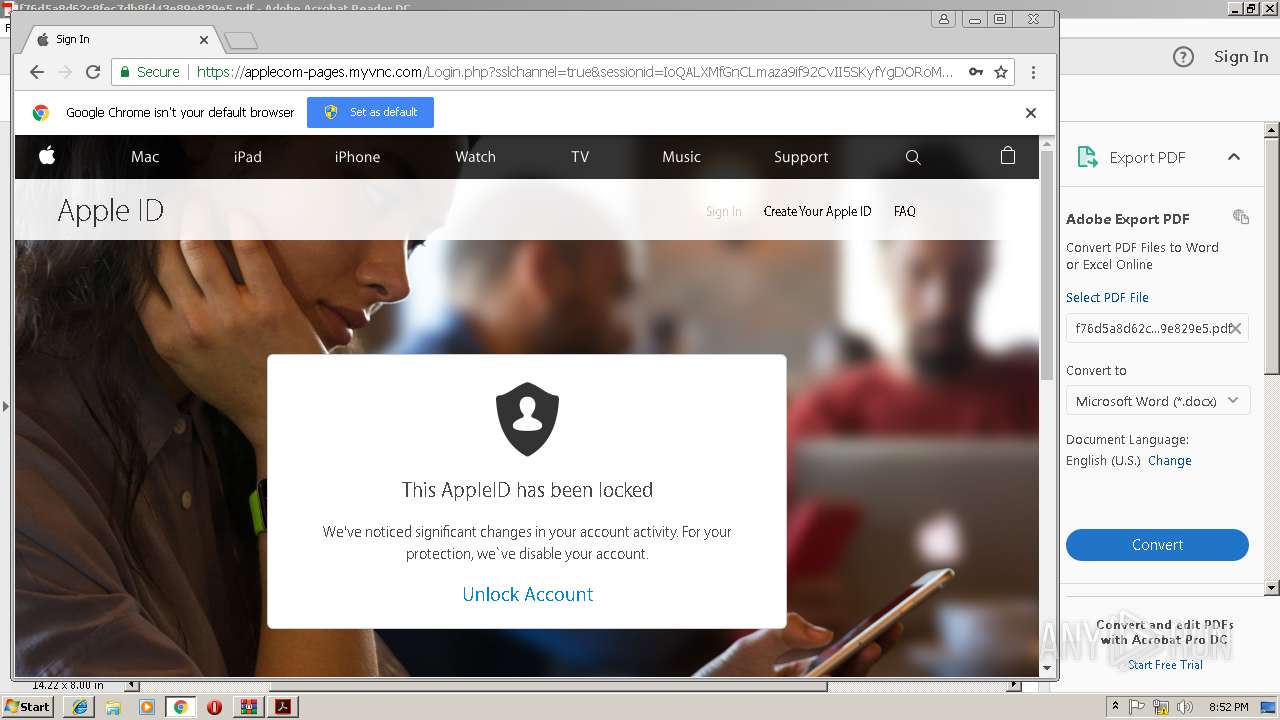
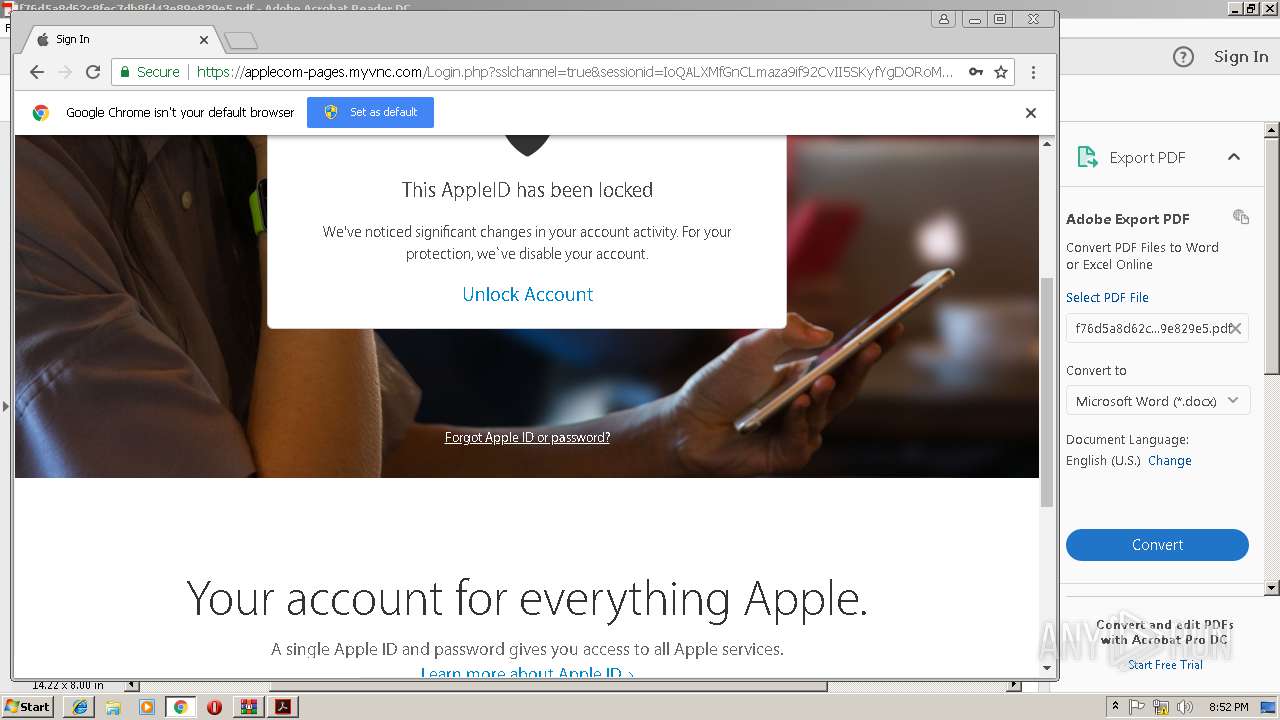
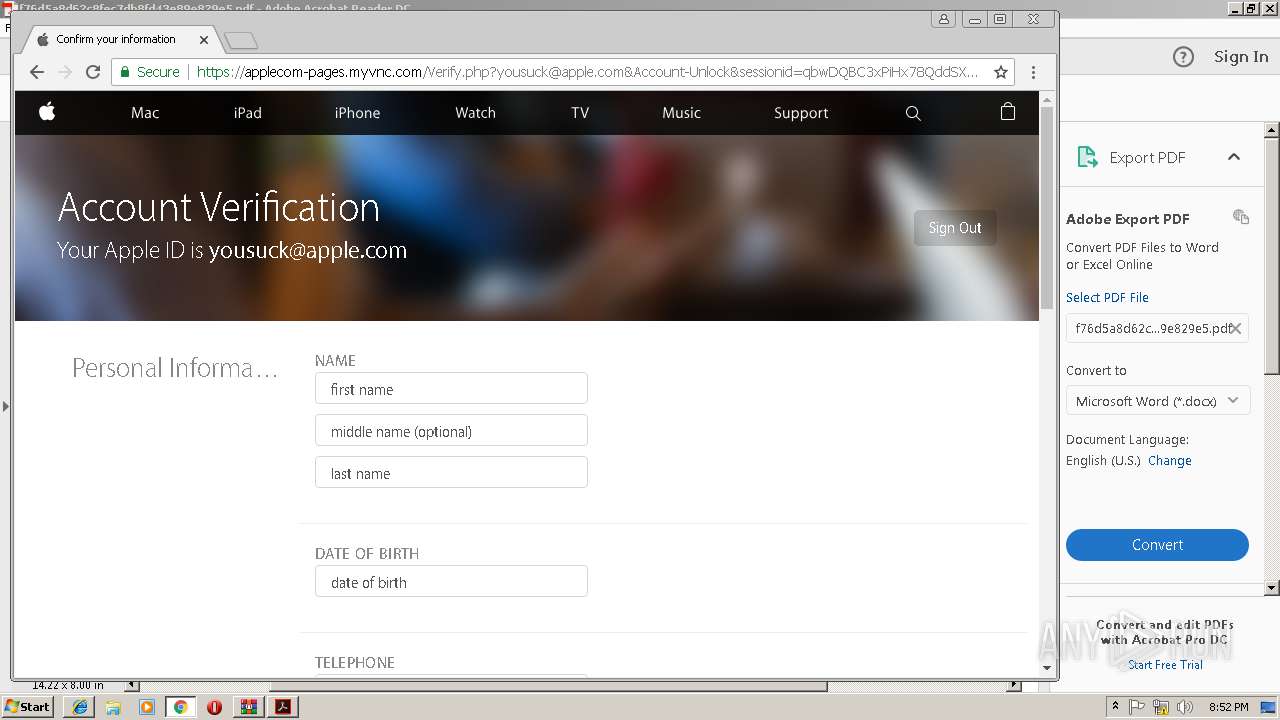
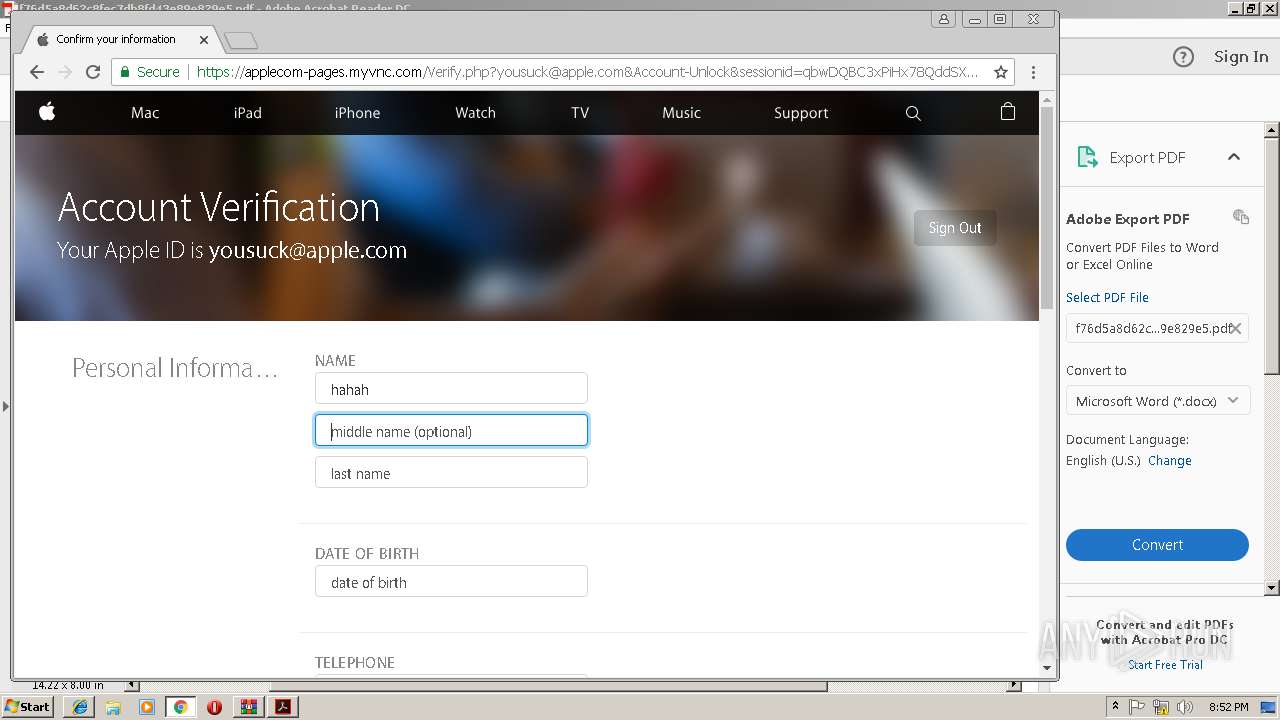
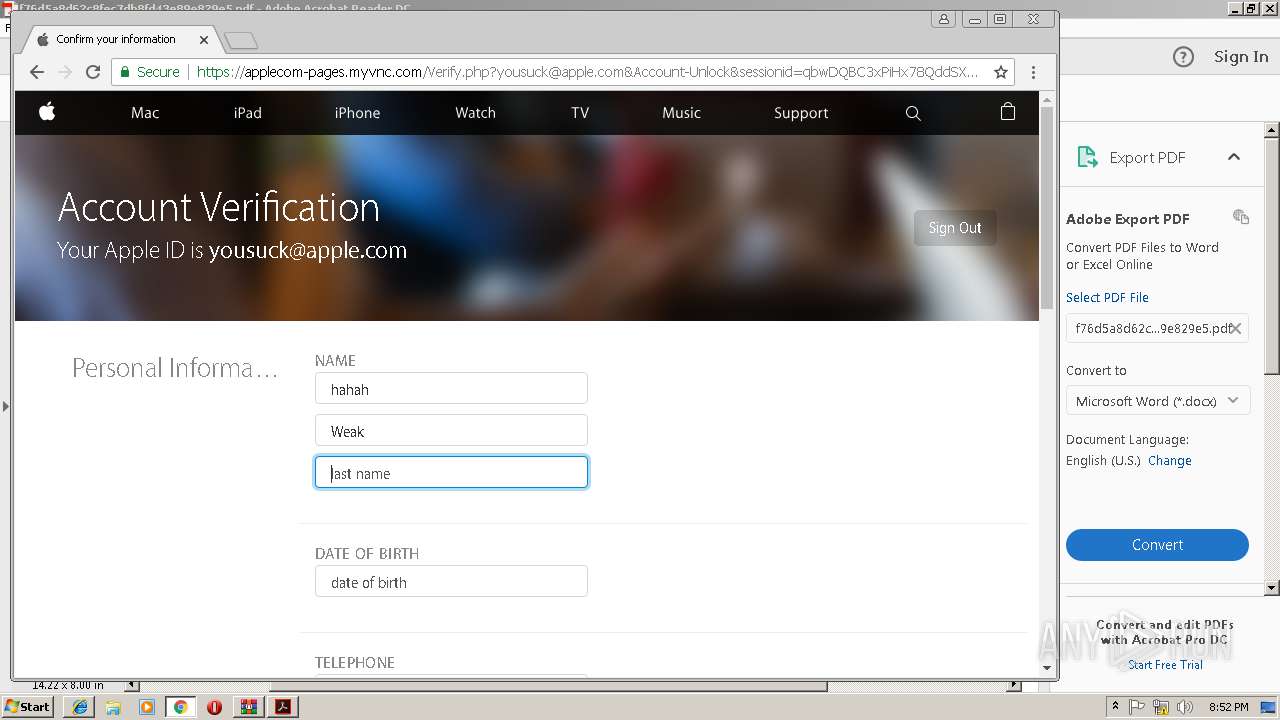
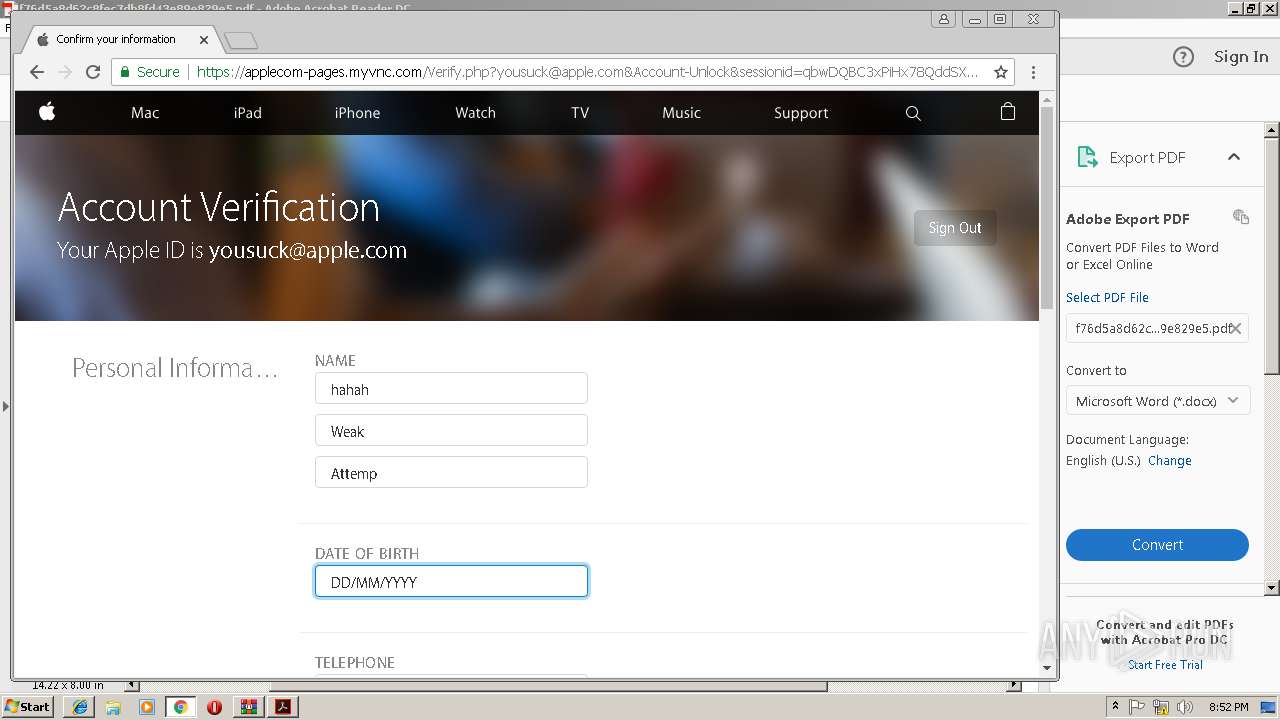
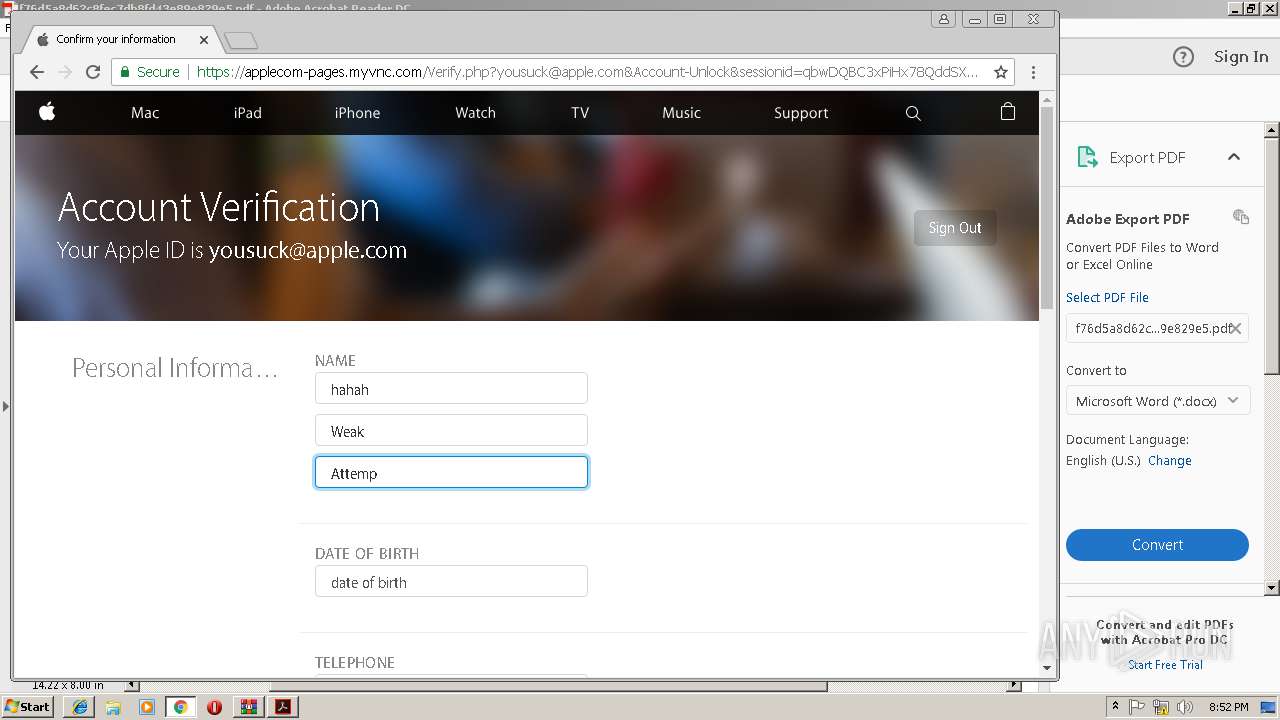
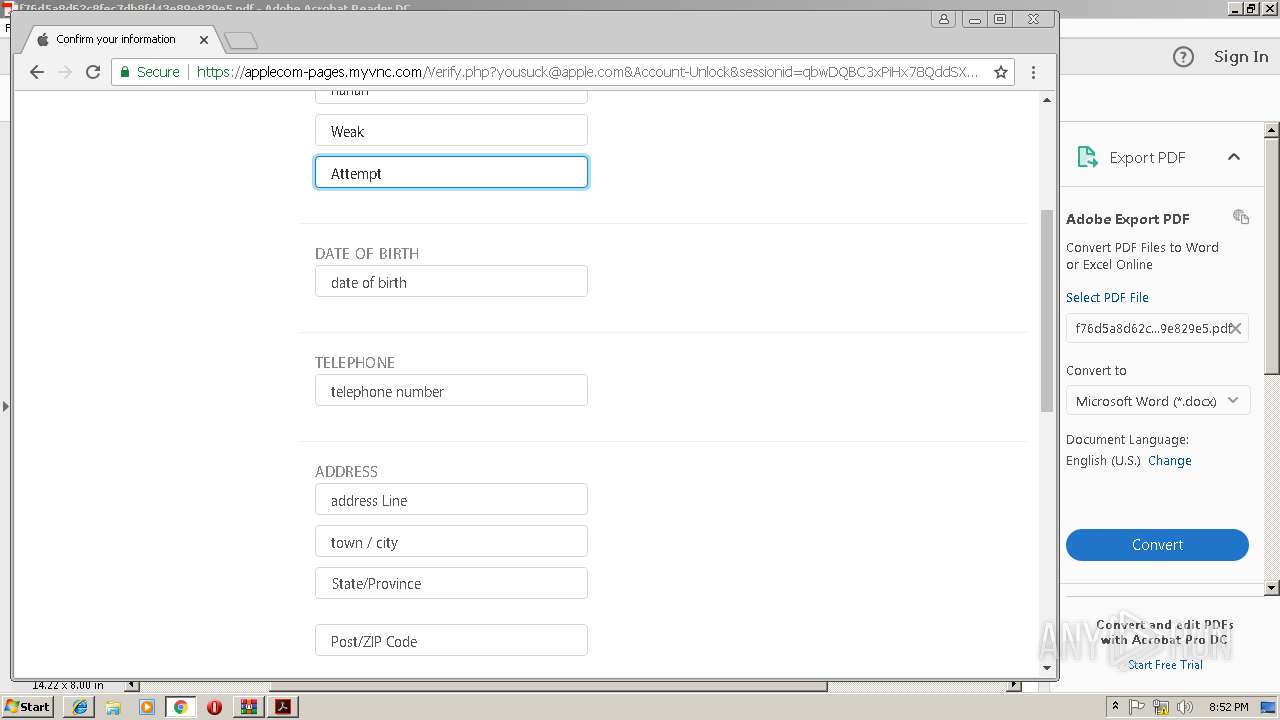
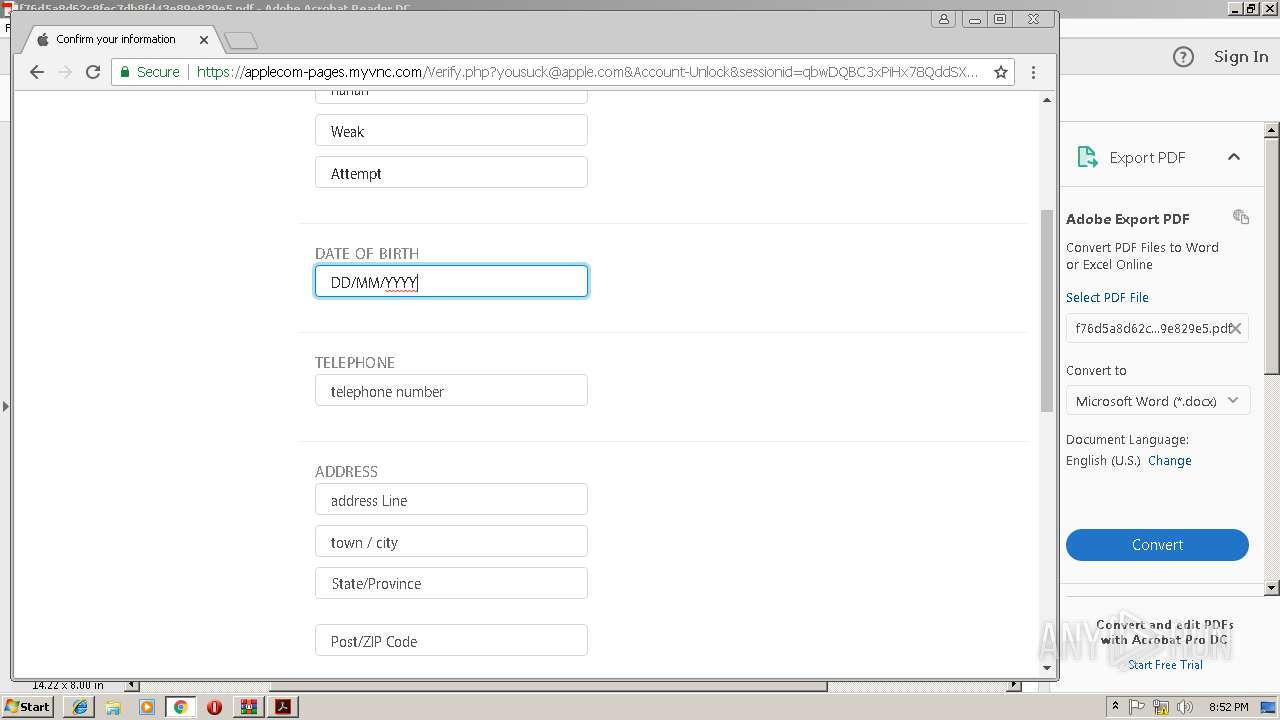
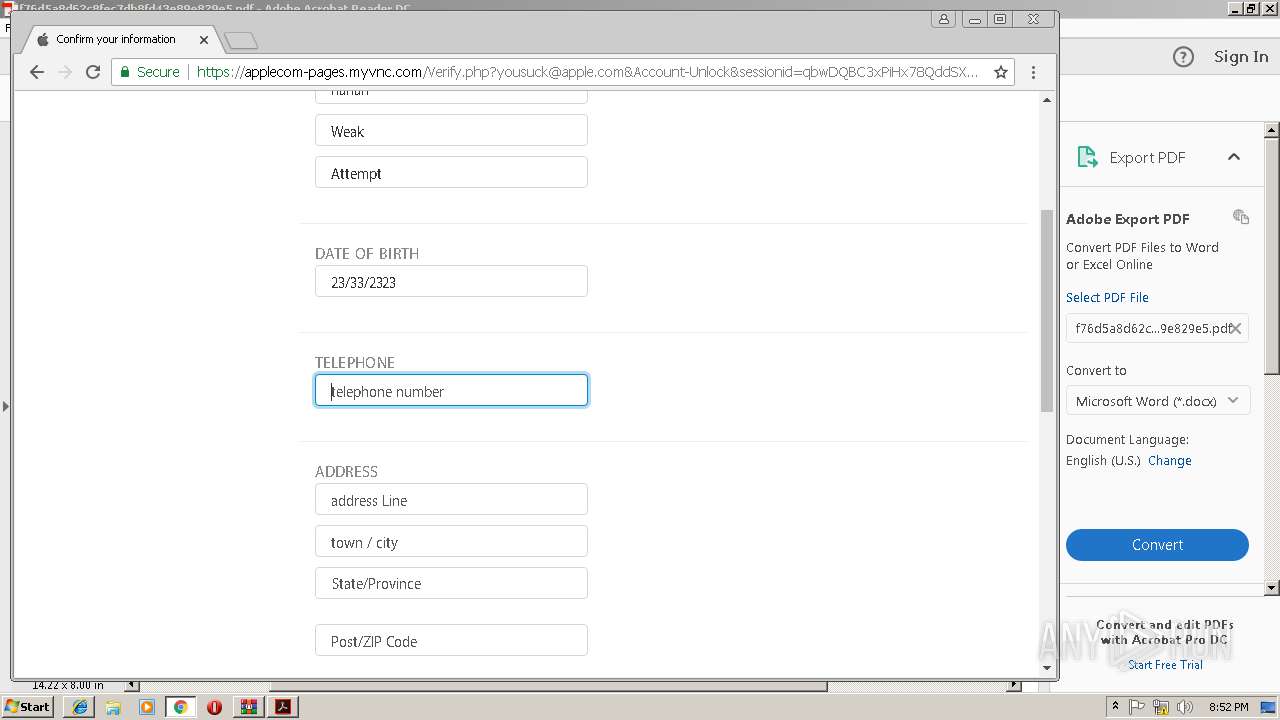
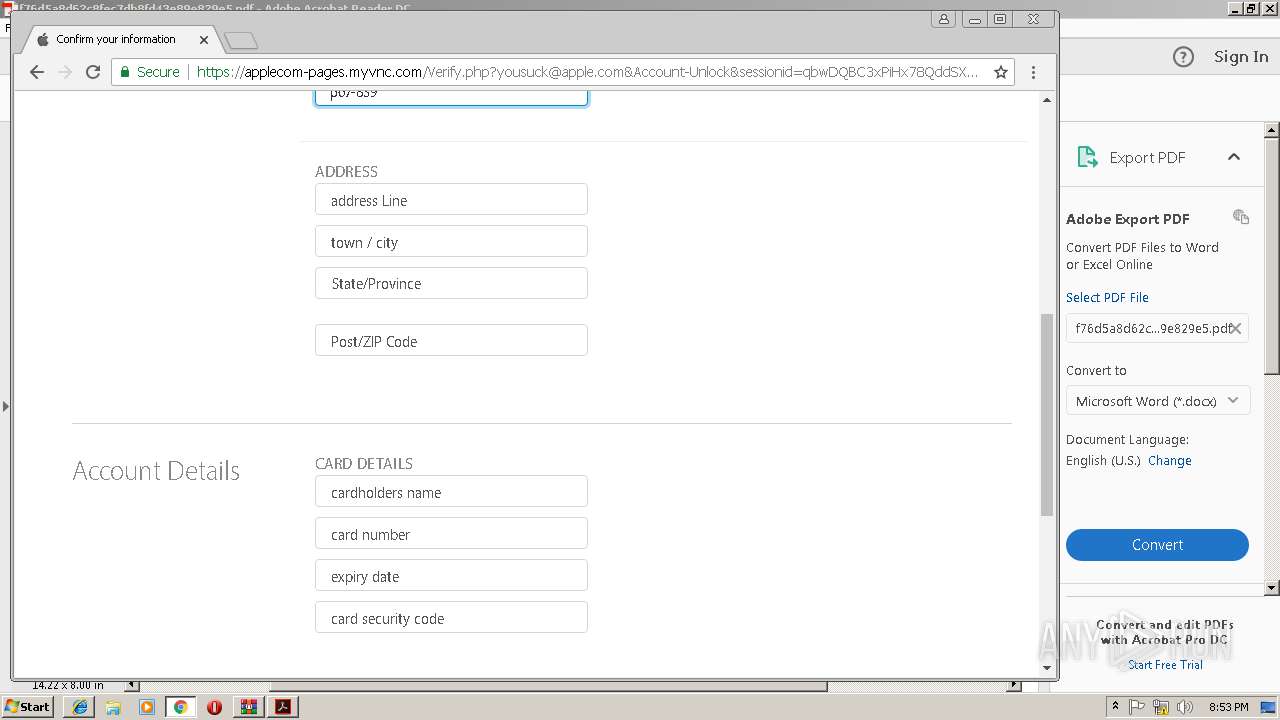
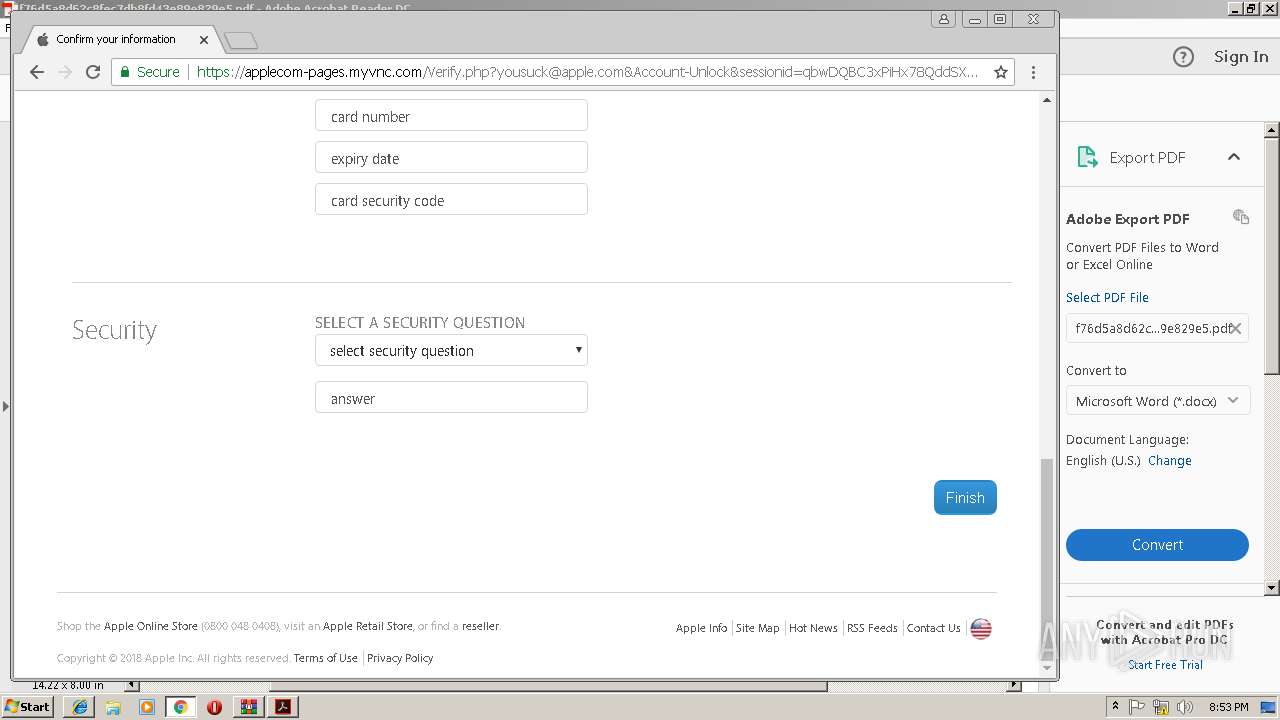
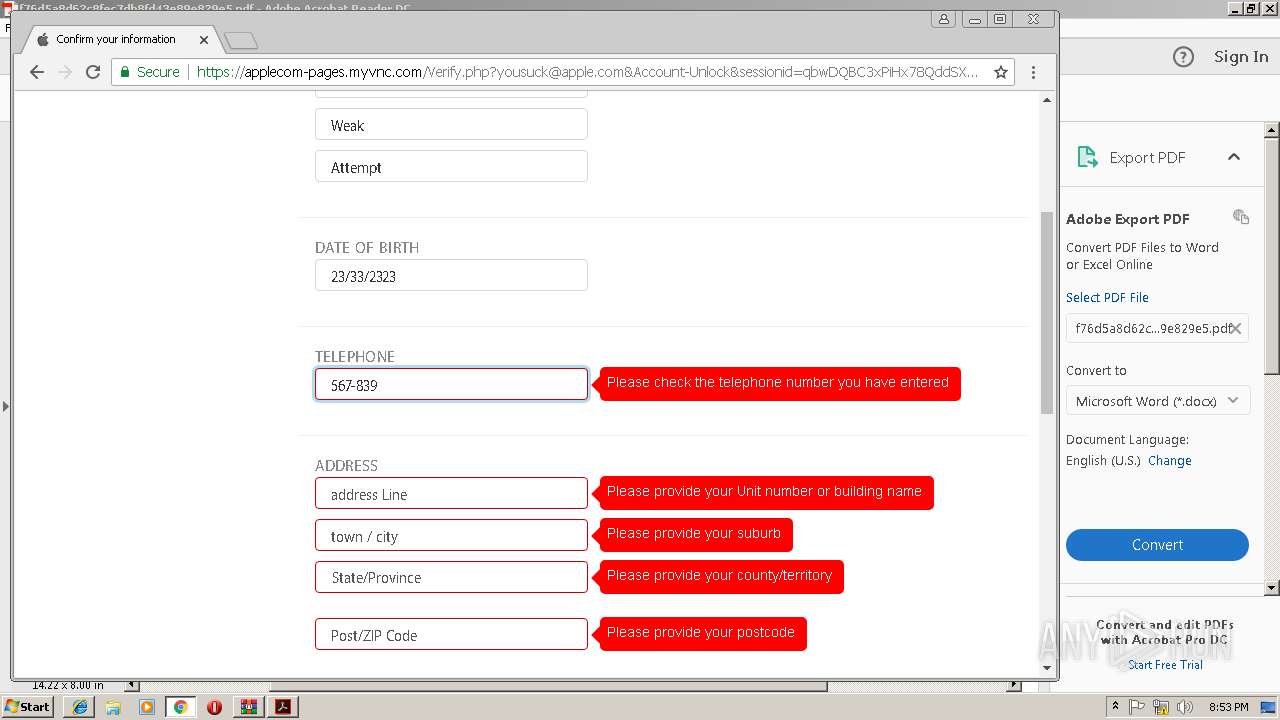
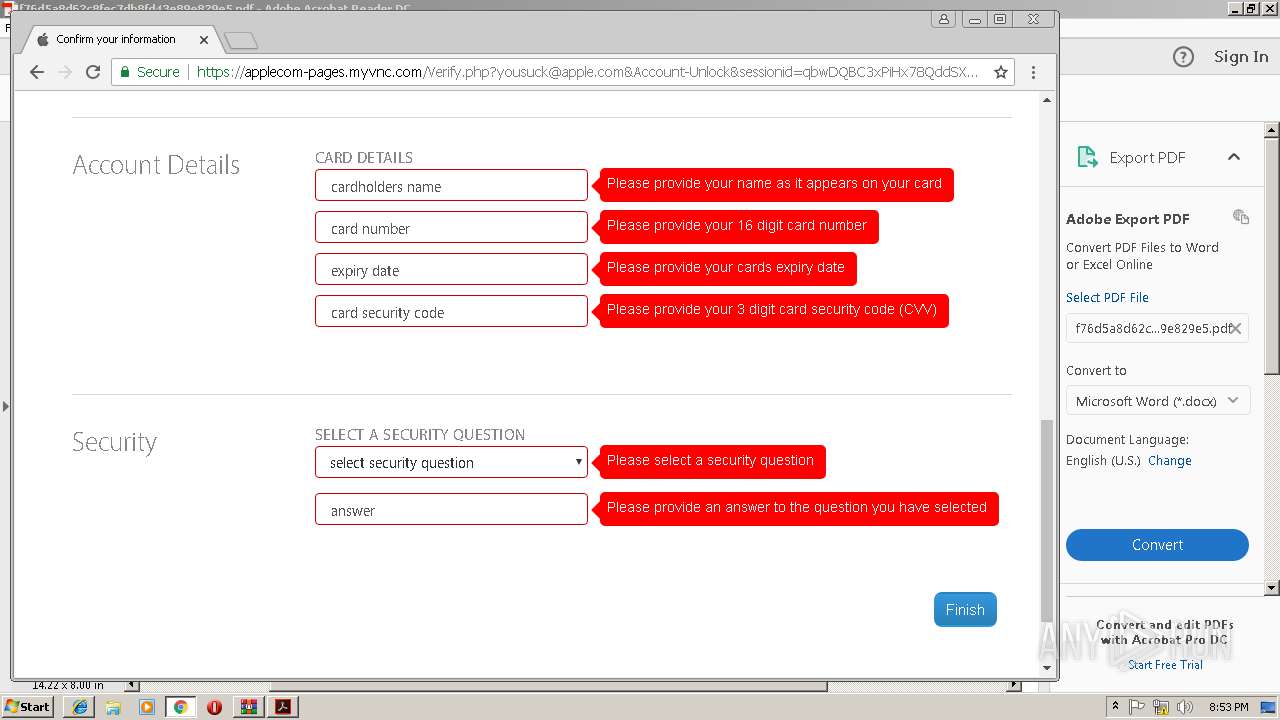
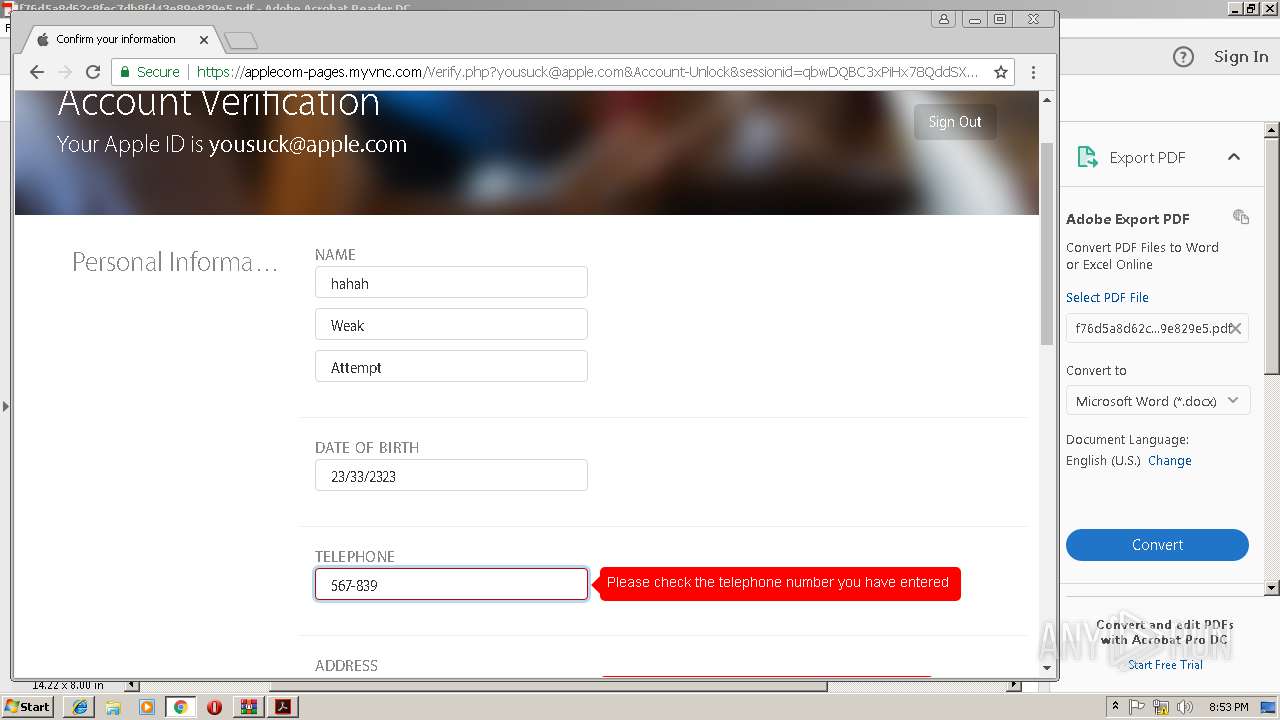
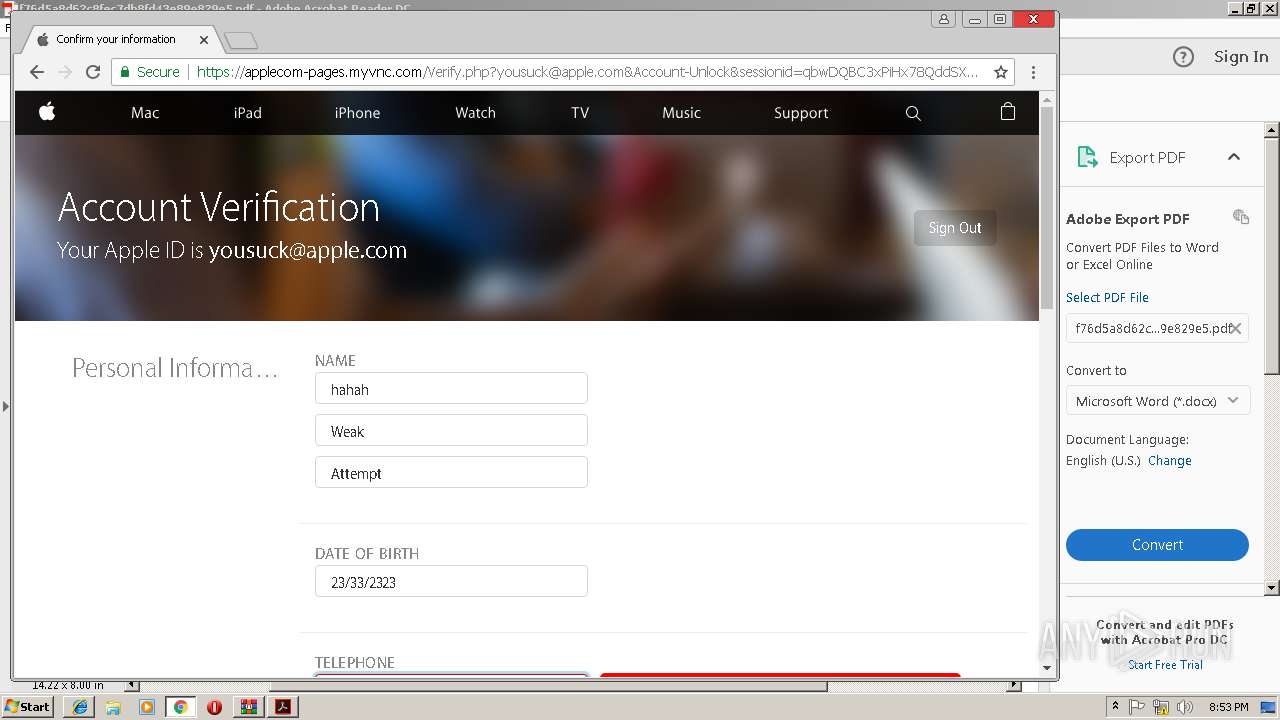
2144 | iexplore.exe | 193.42.118.13:443 | applecom-pages.myvnc.com | — | — | unknown |
3540 | chrome.exe | 172.217.17.35:443 | www.google.de | Google Inc. | US | whitelisted |
3540 | chrome.exe | 172.217.168.35:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3540 | chrome.exe | 172.217.168.45:443 | accounts.google.com | Google Inc. | US | whitelisted |
3540 | chrome.exe | 216.58.215.234:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
3540 | chrome.exe | 172.217.168.3:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
3540 | chrome.exe | 172.217.168.14:443 | apis.google.com | Google Inc. | US | whitelisted |
— | — | 2.18.233.74:443 | armmf.adobe.com | Akamai International B.V. | — | whitelisted |
3540 | chrome.exe | 172.217.168.228:443 | www.google.com | Google Inc. | US | whitelisted |
3540 | chrome.exe | 193.42.118.13:443 | applecom-pages.myvnc.com | — | — | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
acroipm2.adobe.com |
| whitelisted |
armmf.adobe.com |
| whitelisted |
www.bing.com |
| whitelisted |
applecom-pages.myvnc.com |
| unknown |
clientservices.googleapis.com |
| whitelisted |
www.google.de |
| whitelisted |
www.gstatic.com |
| whitelisted |
safebrowsing.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
ssl.gstatic.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Generic Protocol Command Decode | SURICATA STREAM excessive retransmissions |
— | — | unknown | SURICATA TCPv4 invalid checksum |