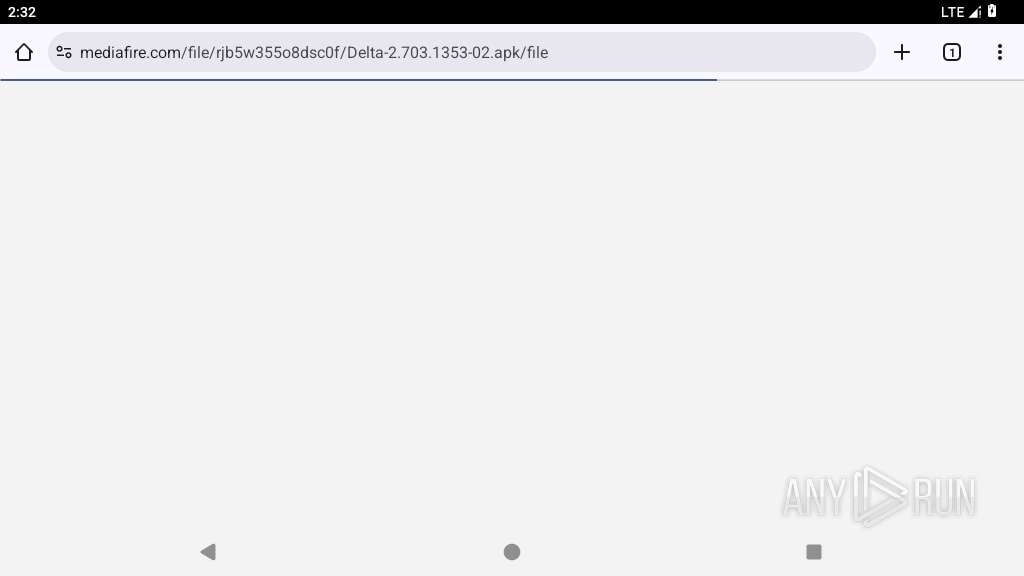
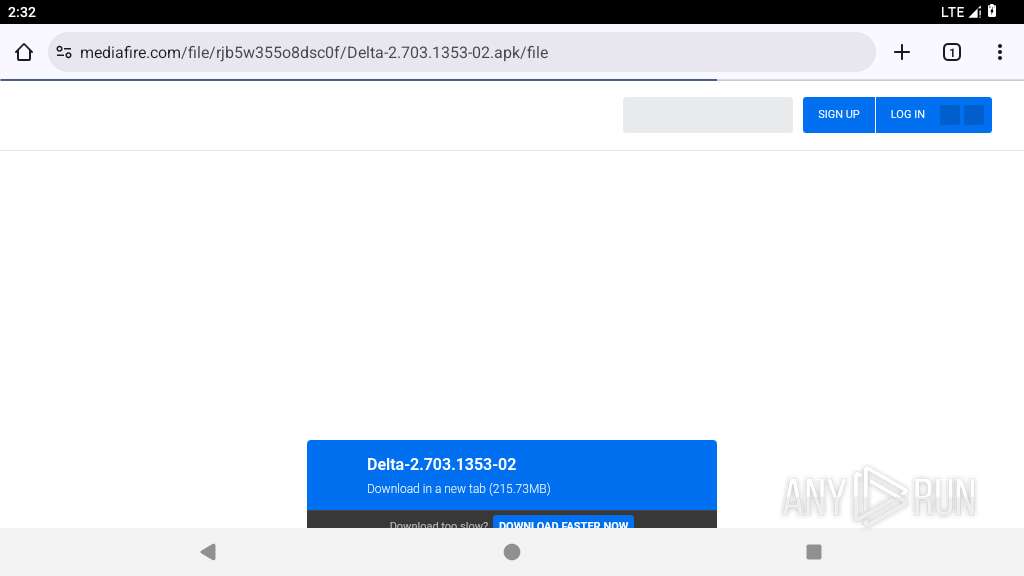
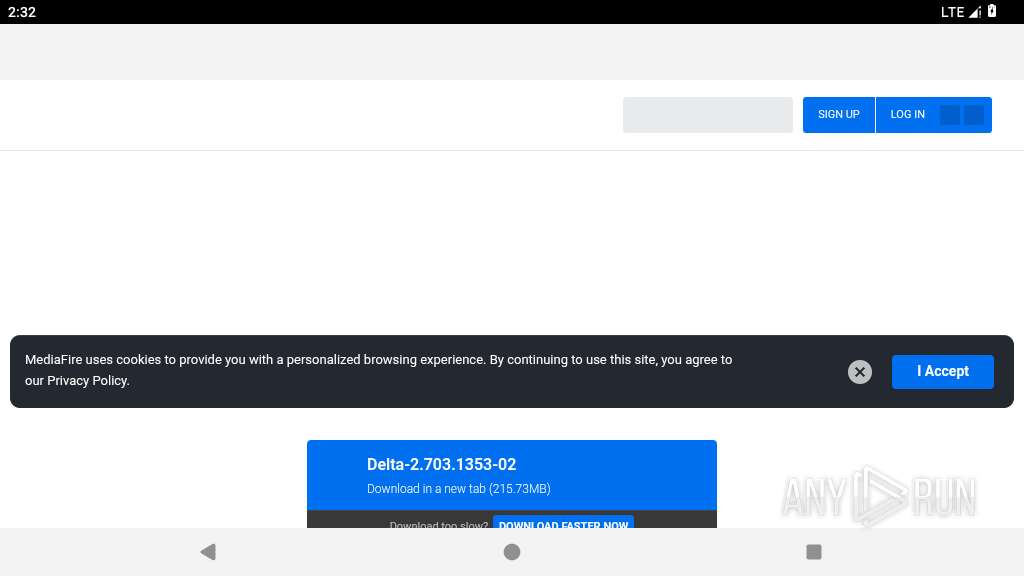
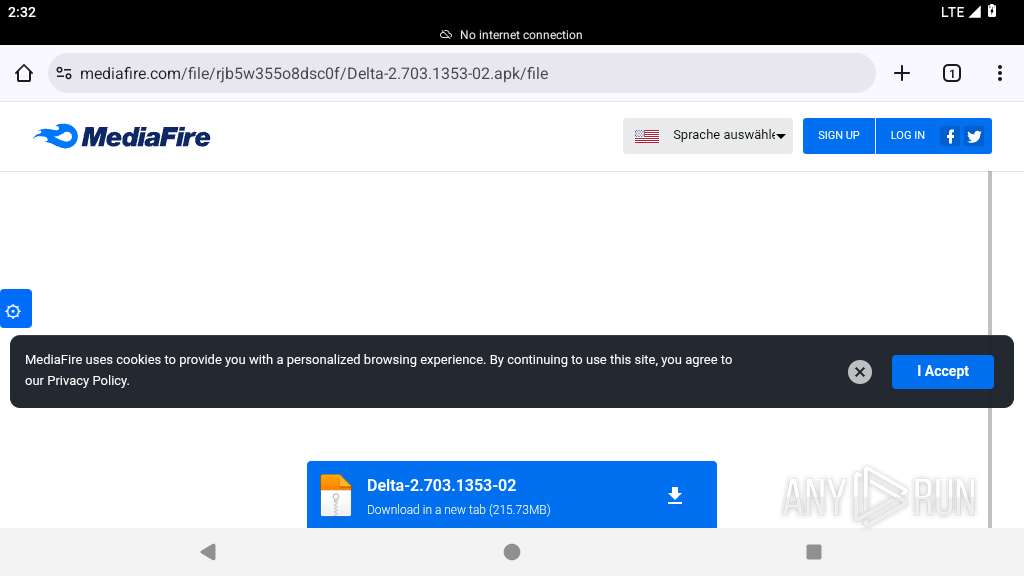
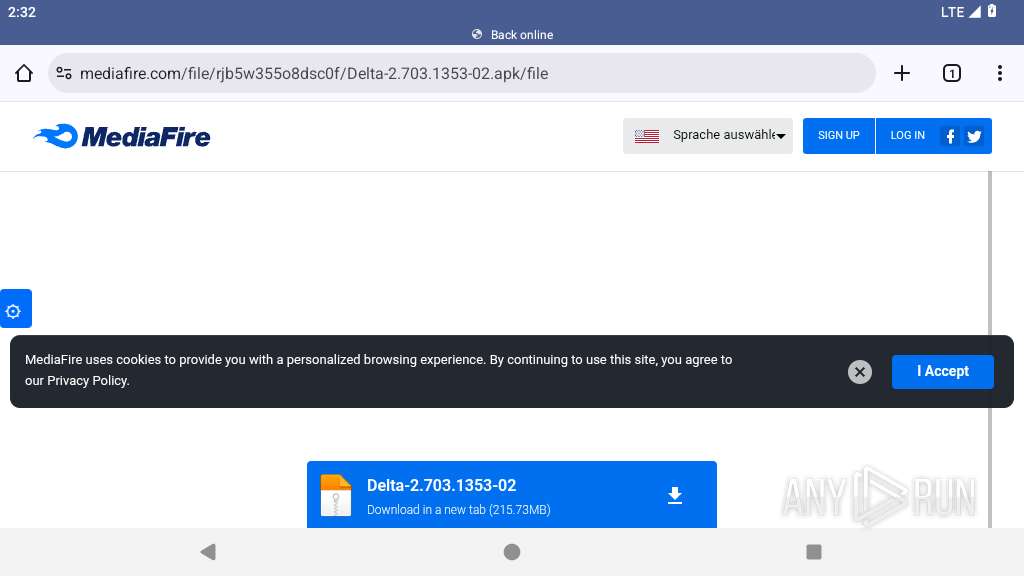
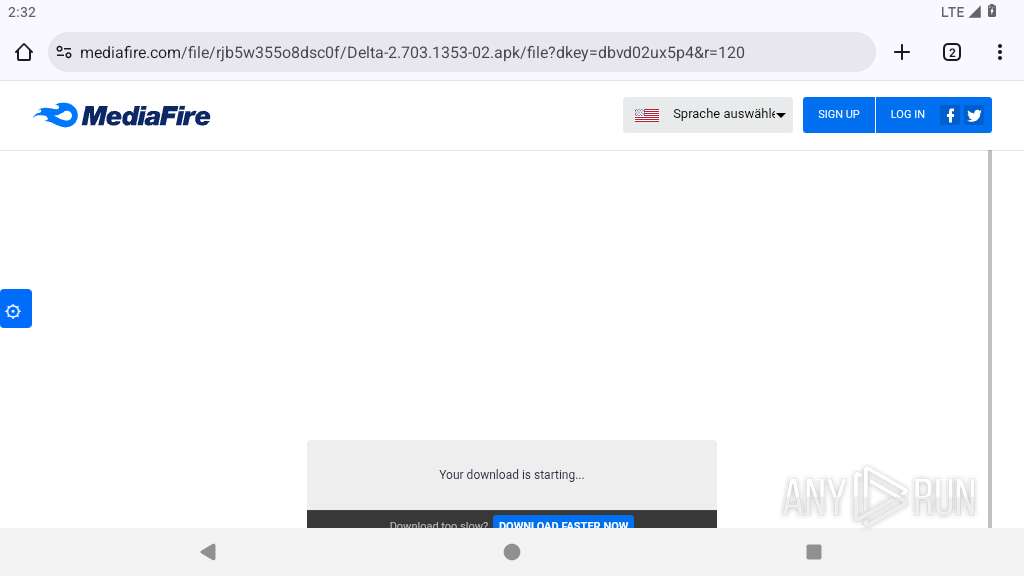
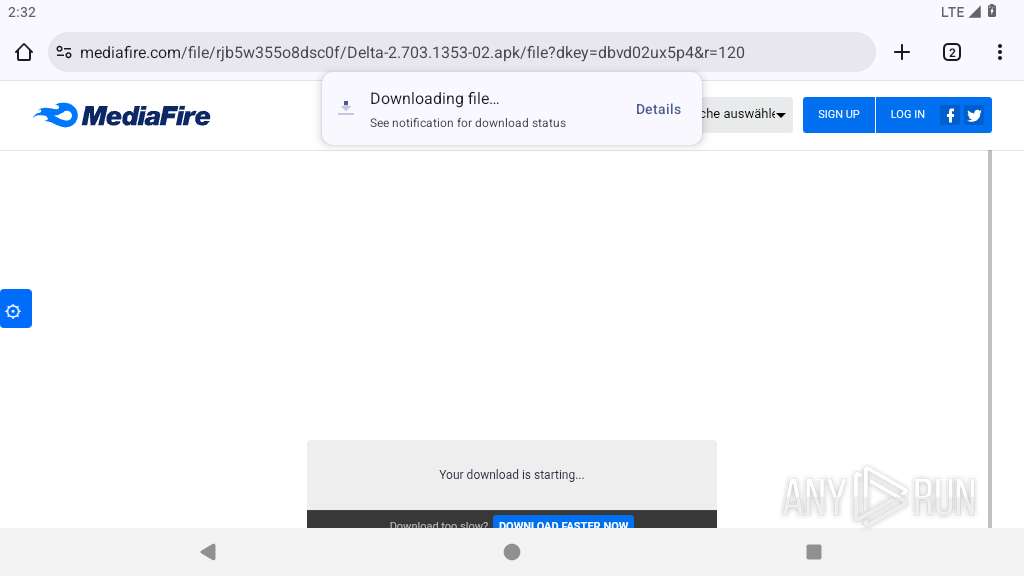
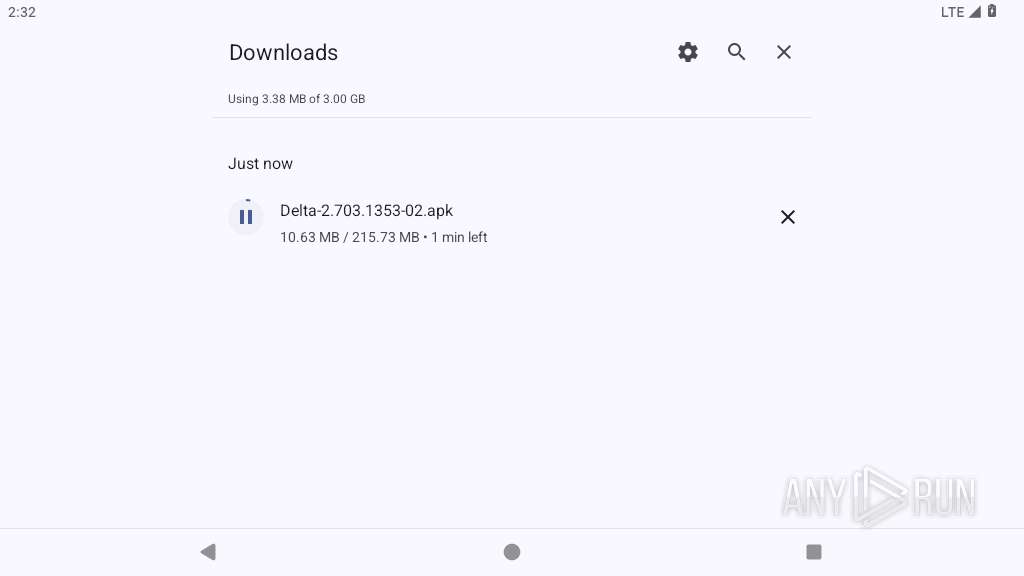
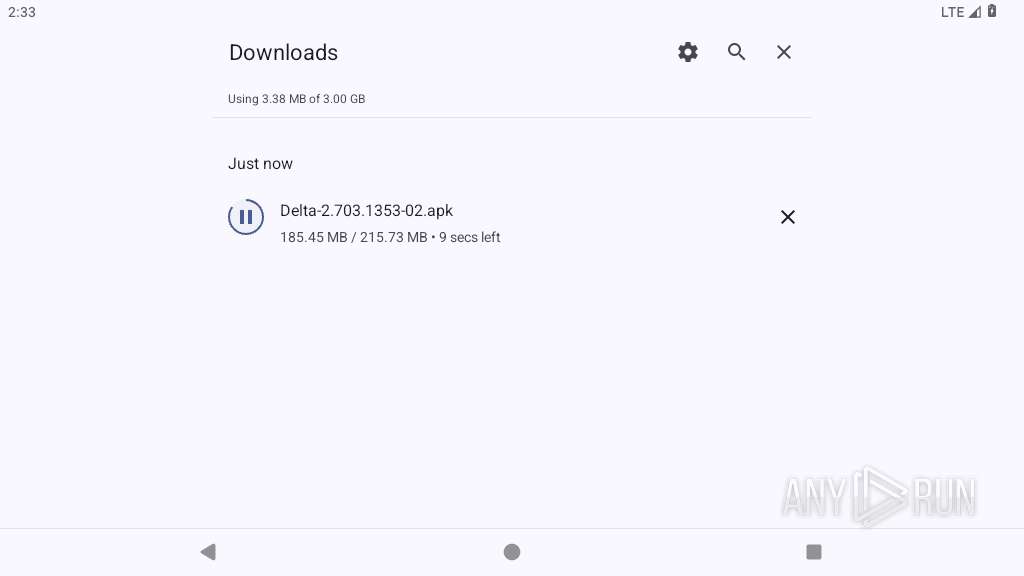
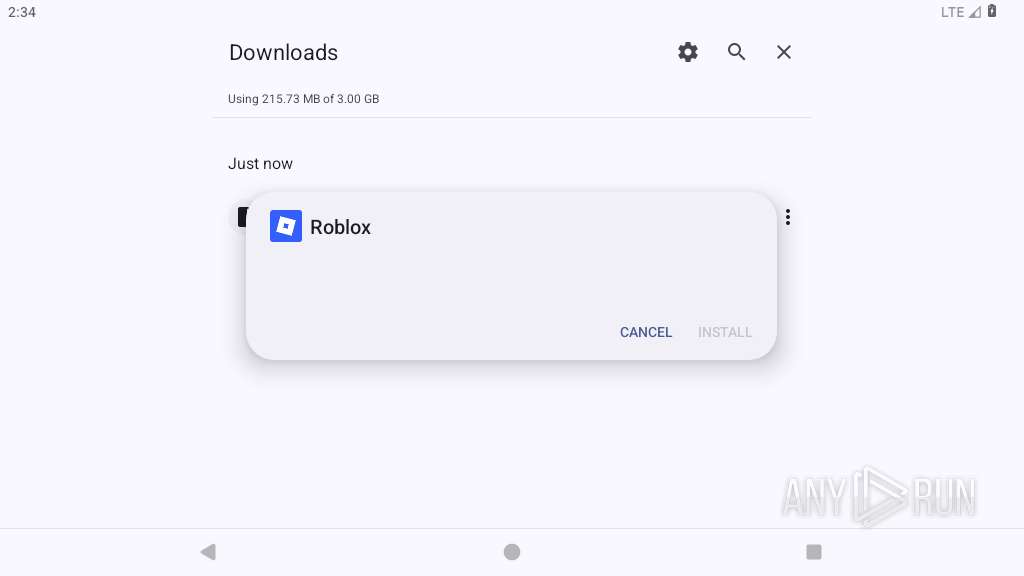
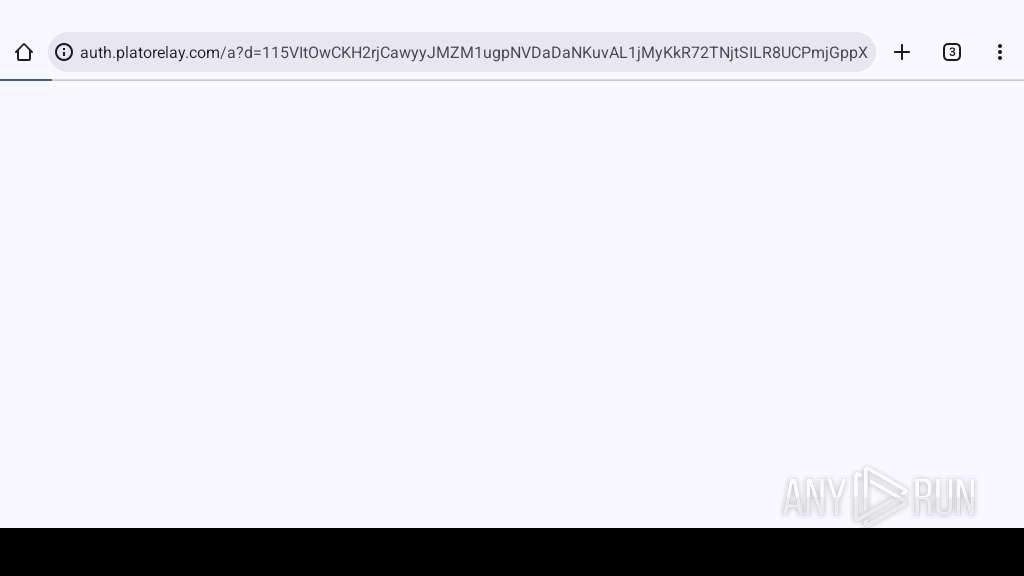
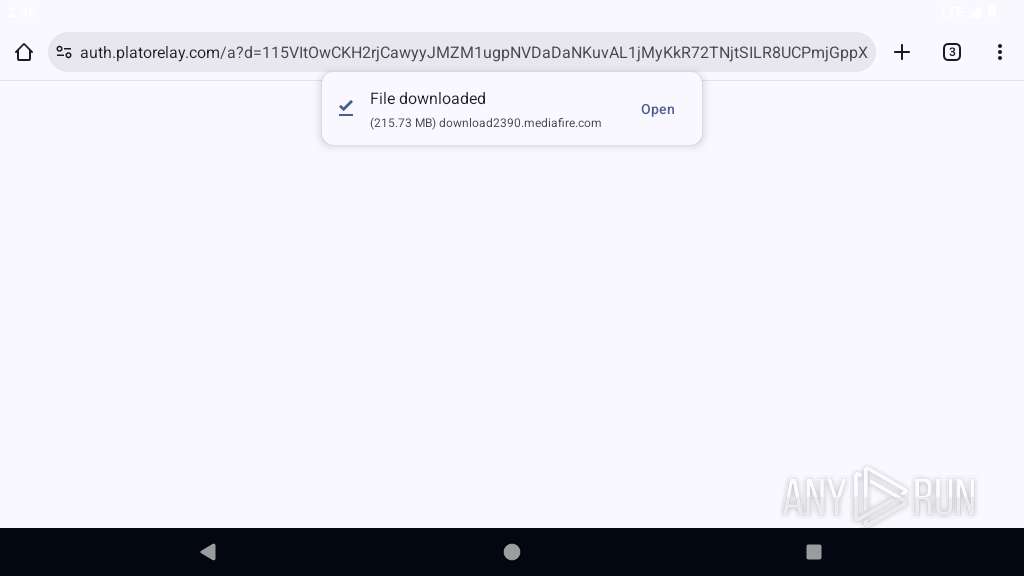
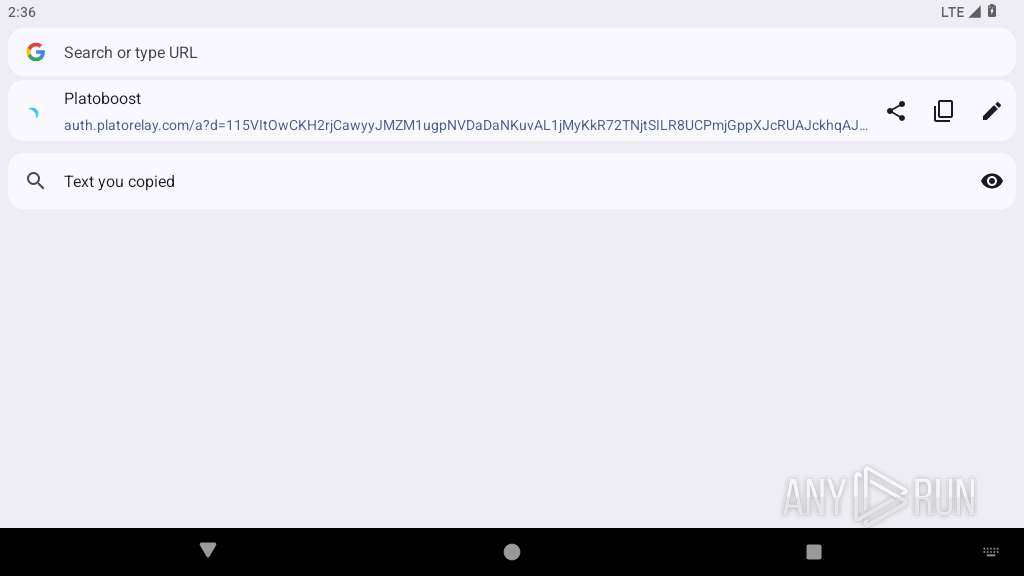
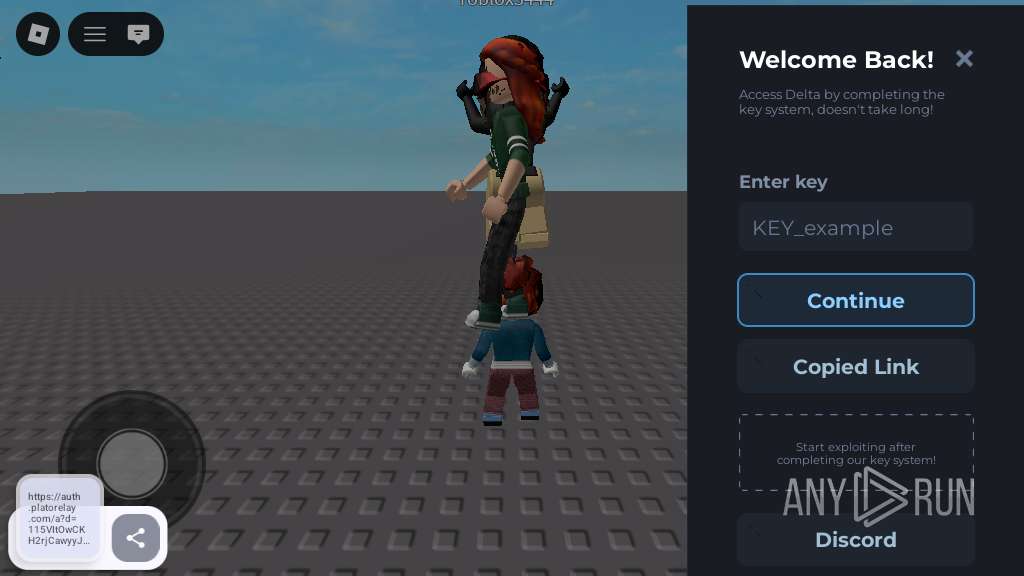
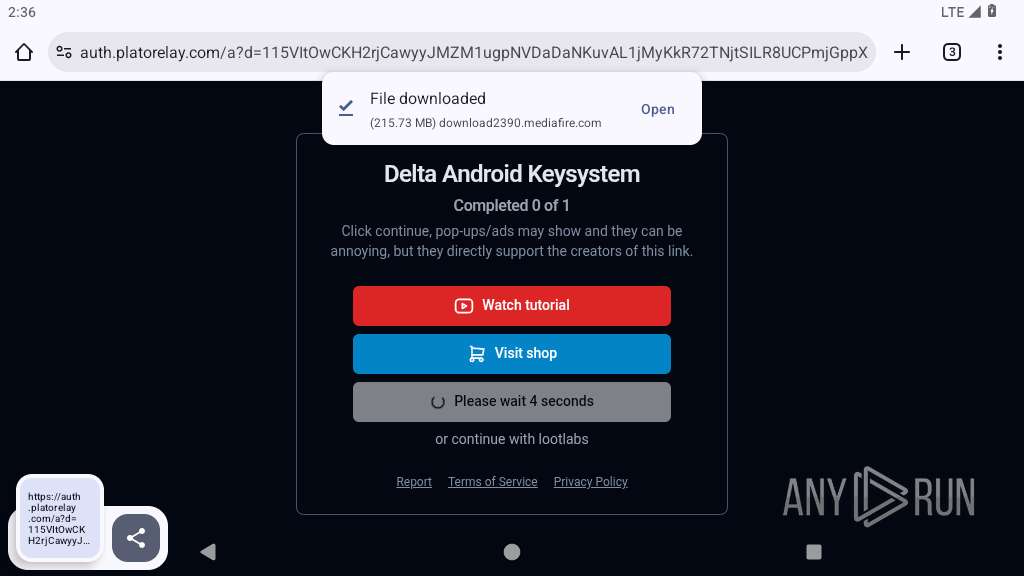
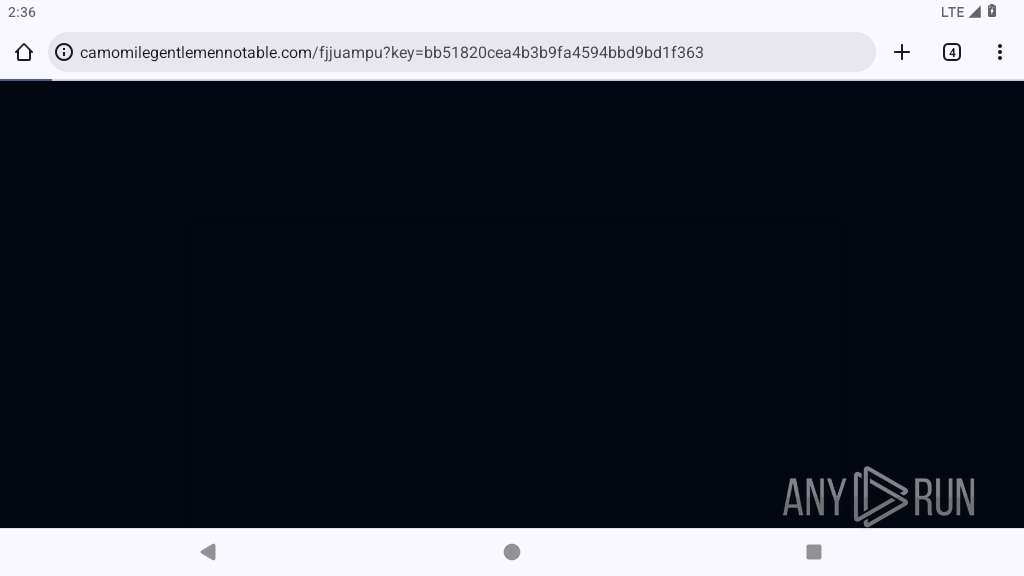
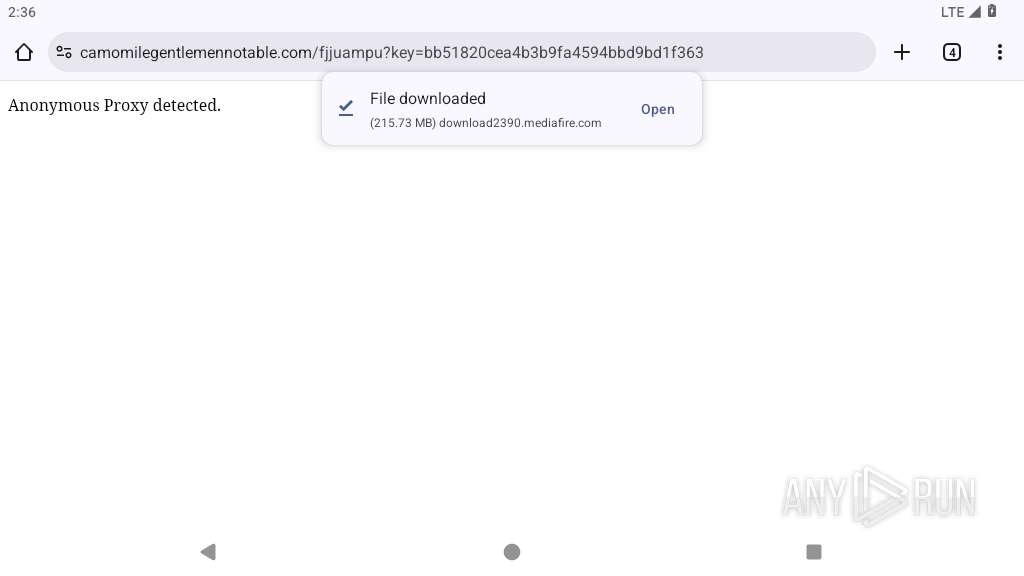
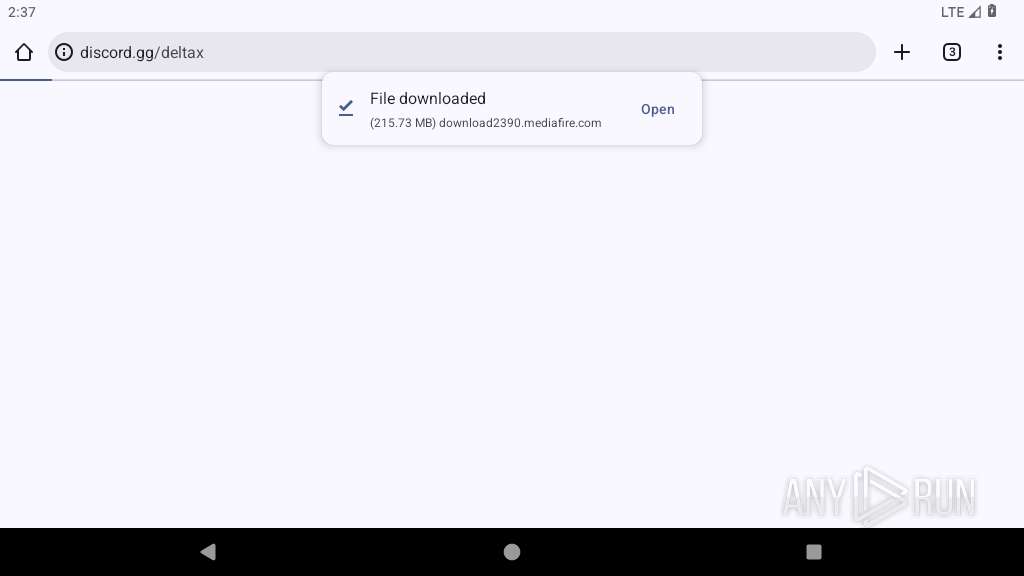
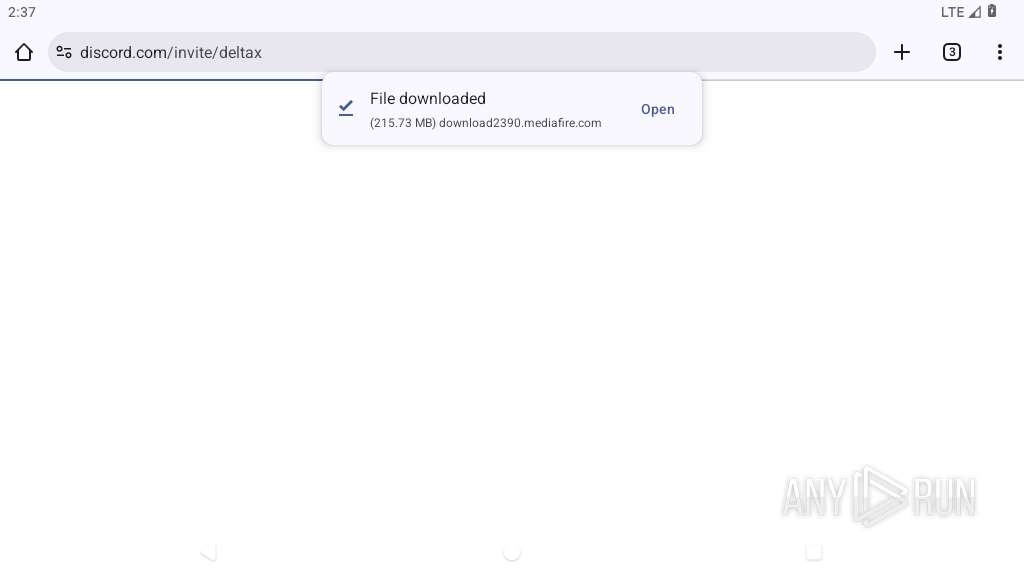
| URL: | https://www.mediafire.com/file/rjb5w355o8dsc0f/Delta-2.703.1353-02.apk/file |
| Full analysis: | https://app.any.run/tasks/3d0da14c-5b64-4e56-8fd4-946437fc4ada |
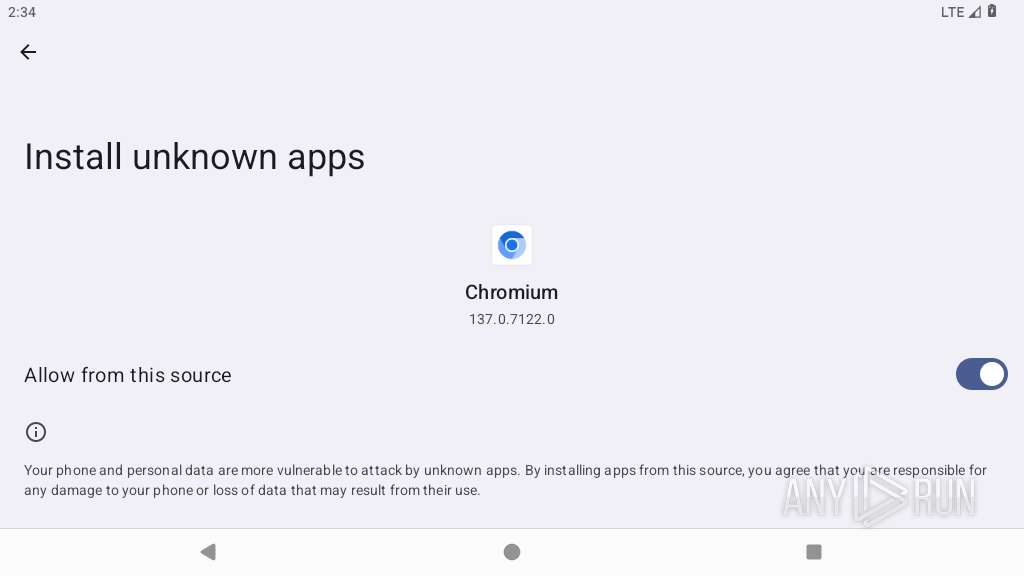
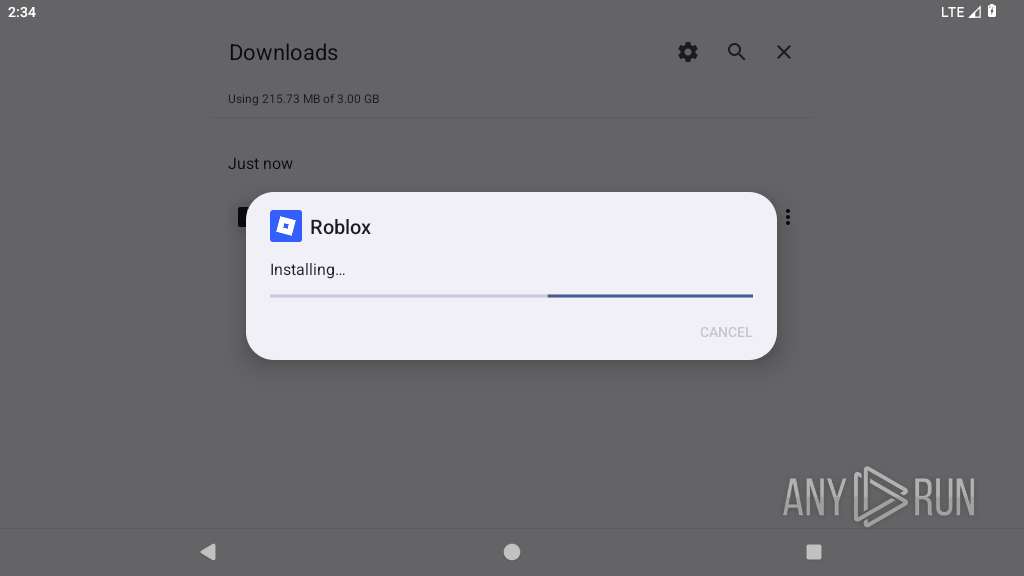
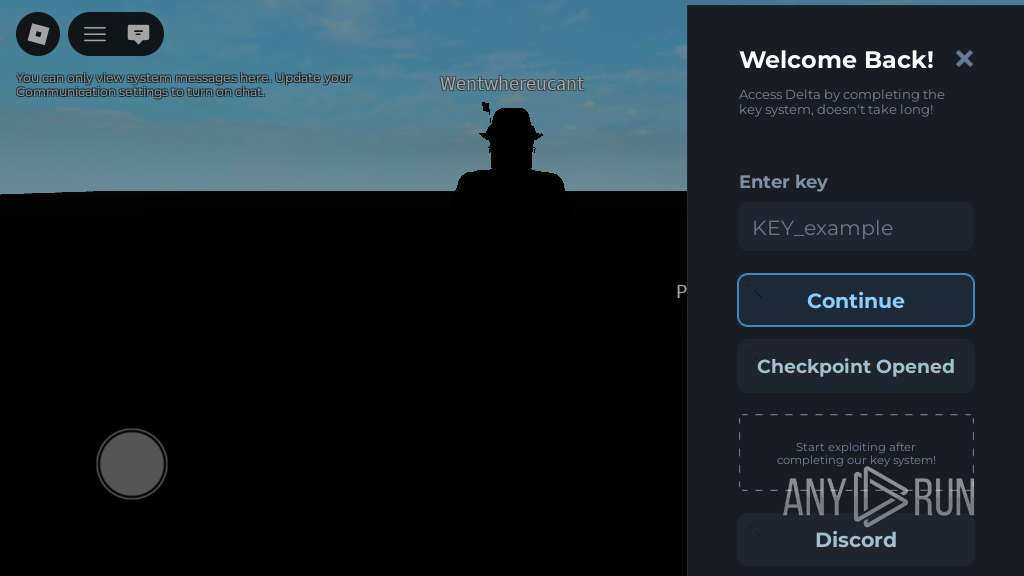
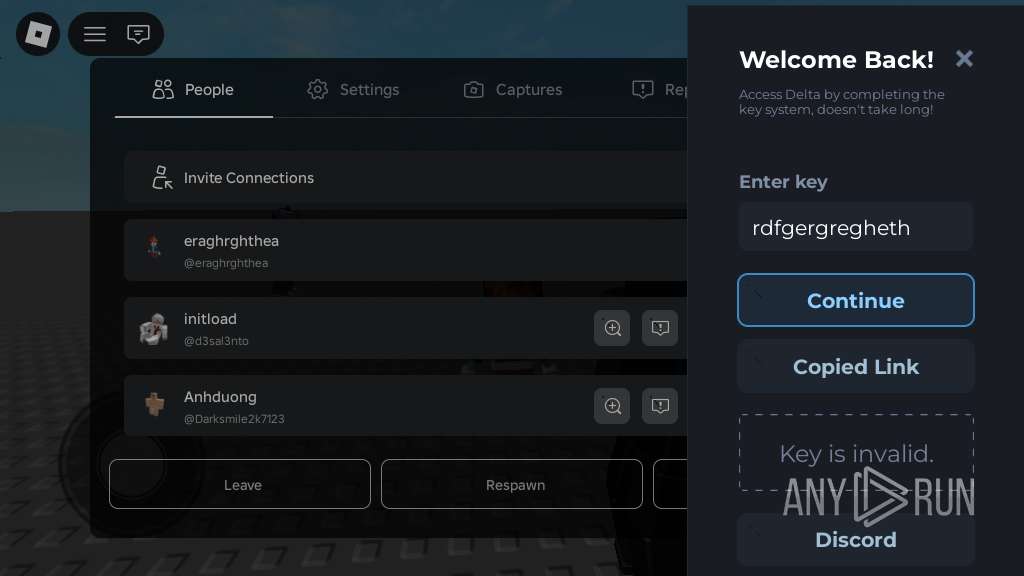
| Verdict: | Malicious activity |
| Analysis date: | January 17, 2026, 14:32:09 |
| OS: | Android 14 |
| Tags: | |
| Indicators: | |
| MD5: | 1BB7908F349991DE9DABB792A224FF36 |
| SHA1: | 99BB6DE9B0FD21F48FED264A807E914920F85570 |
| SHA256: | DA1B6FB899E23250C8B326BDF4587358434CACCA1F865ABE91BD1F9B2D5B45CA |
| SSDEEP: | 3:N8DSLw3eGUoIKLjJR9SV3+cAn:2OLw3eGztbx |
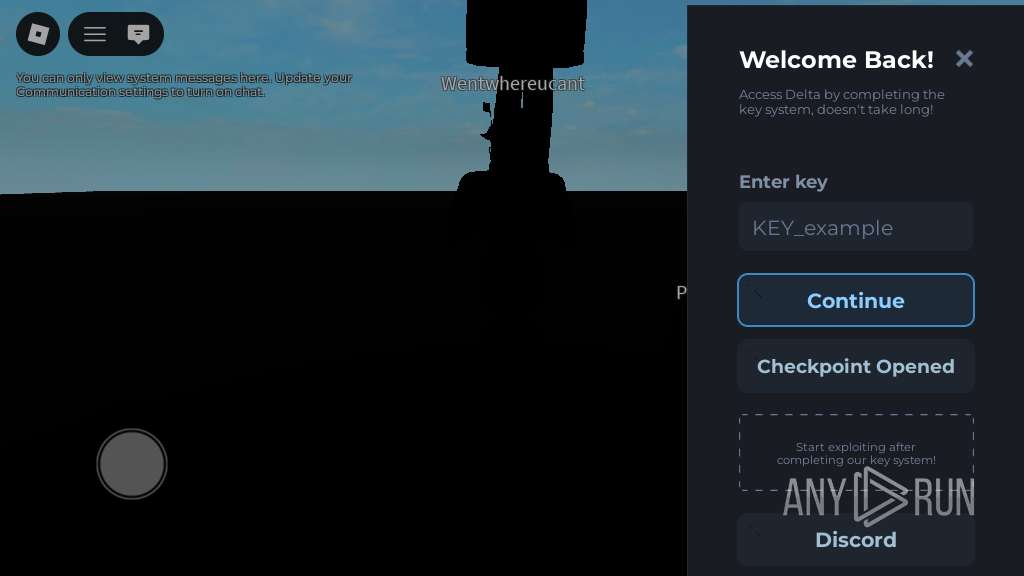
MALICIOUS
Detects root access on device
- app_process64 (PID: 3250)
Executes system commands or scripts
- app_process64 (PID: 3250)
SUSPICIOUS
Accesses system-level resources
- app_process64 (PID: 3250)
Collects data about the device's environment (JVM version)
- app_process64 (PID: 3250)
Reads device serial number identifier
- app_process64 (PID: 3250)
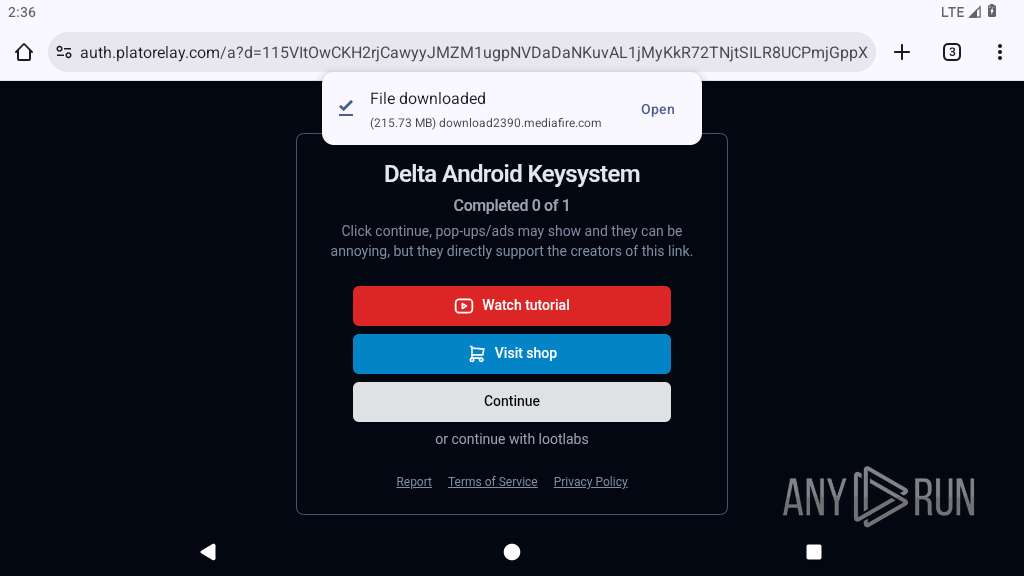
Establishing a connection
- app_process64 (PID: 3250)
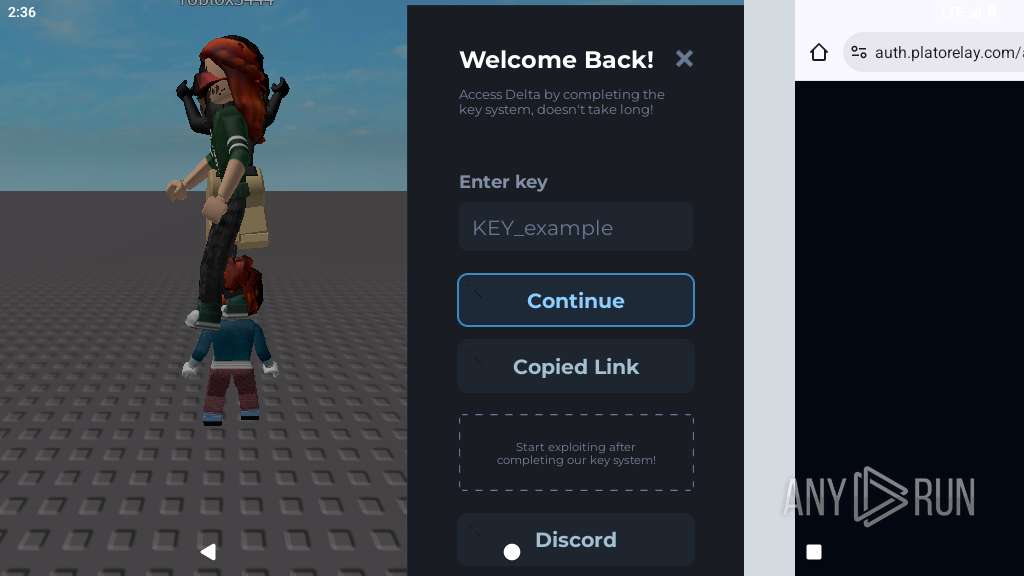
Updates data in the storage of application settings (SharedPreferences)
- app_process64 (PID: 3250)
Accesses memory information
- app_process64 (PID: 3250)
Retrieves Android OS build information
- app_process64 (PID: 3250)
Retrieves a list of running application processes
- app_process64 (PID: 3250)
Launches a new activity
- app_process64 (PID: 3250)
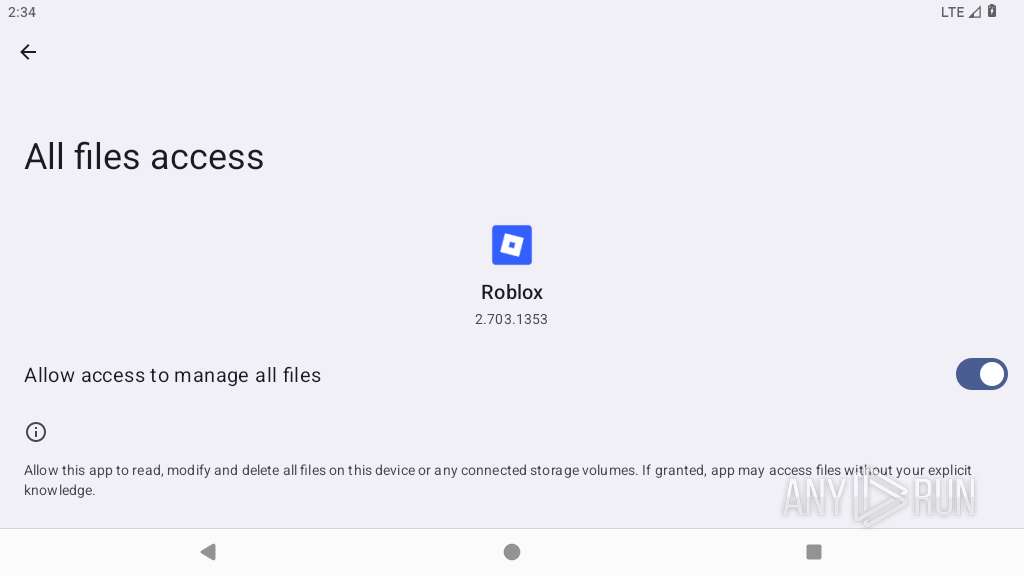
Accesses external device storage files
- app_process64 (PID: 3250)
Connects to unusual port
- app_process64 (PID: 3250)
Checks Bluetooth audio routing status
- app_process64 (PID: 3250)
INFO
Retrieves the value of a secure system setting
- app_process64 (PID: 3250)
Retrieves data from storage of application settings (SharedPreferences)
- app_process64 (PID: 3250)
Returns elapsed time since boot
- app_process64 (PID: 3250)
Dynamically inspects or modifies classes, methods, and fields at runtime
- app_process64 (PID: 3250)
Dynamically registers broadcast event listeners
- app_process64 (PID: 3250)
Gets file name without full path
- app_process64 (PID: 3250)
Loads a native library into the application
- app_process64 (PID: 3250)
Gets the display metrics associated with the device's screen
- app_process64 (PID: 3250)
Verifies whether the device is connected to the internet
- app_process64 (PID: 3250)
Stores data using SQLite database
- app_process64 (PID: 3250)
Handles throwable exceptions in the app
- app_process64 (PID: 3250)
Dynamically loads a class in Java
- app_process64 (PID: 3250)
Detects if debugger is connected
- app_process64 (PID: 3250)
Attempting to use instant messaging service
- app_process64 (PID: 2787)
Detects device power status
- app_process64 (PID: 3250)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
146
Monitored processes
21
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process |
|---|---|---|---|---|
| 2787 | org.chromium.chrome | /system/bin/app_process64 | app_process64 | |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 2847 | org.chromium.chrome_zygote | /system/bin/app_process64 | — | app_process64 |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 2865 | org.chromium.chrome_zygote | /system/bin/app_process64 | — | app_process64 |
User: u0_a72 Integrity Level: UNKNOWN Exit code: 0 | ||||
| 2877 | org.chromium.chrome:privileged_process0 | /system/bin/app_process64 | — | app_process64 |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 2898 | com.android.adservices.api | /system/bin/app_process64 | — | app_process64 |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 2966 | org.chromium.chrome_zygote | /system/bin/app_process64 | — | app_process64 |
User: u0_a72 Integrity Level: UNKNOWN Exit code: 0 | ||||
| 2988 | com.android.providers.partnerbookmarks | /system/bin/app_process64 | — | app_process64 |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 3086 | /system/bin/dmesgd | /system/bin/dmesgd | — | init |
User: dmesgd Integrity Level: UNKNOWN Exit code: 0 | ||||
| 3087 | dmesg | /system/bin/toybox | — | dmesgd |
User: dmesgd Integrity Level: UNKNOWN Exit code: 0 | ||||
| 3088 | org.chromium.chrome_zygote | /system/bin/app_process64 | — | app_process64 |
User: u0_a72 Integrity Level: UNKNOWN Exit code: 0 | ||||
Total events
0
Read events
0
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
478
Text files
197
Unknown types
29
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3250 | app_process64 | /data/data/com.roblox.client/shared_modules/50285346aa69312f47862ddc81a3edcd/gloopversioncache.txt | text | |
MD5:— | SHA256:— | |||
| 3250 | app_process64 | /data/data/com.roblox.client/shared_prefs/com.google.firebase.messaging.xml | xml | |
MD5:— | SHA256:— | |||
| 3250 | app_process64 | /data/data/com.roblox.client/shared_prefs/com.google.android.gms.measurement.prefs.xml | xml | |
MD5:— | SHA256:— | |||
| 3250 | app_process64 | /data/data/com.roblox.client/files/PersistedInstallation4605519451882698226tmp | text | |
MD5:— | SHA256:— | |||
| 3250 | app_process64 | /data/data/com.roblox.client/files/PersistedInstallation.W0RFRkFVTFRd+MToxMDAxNTUzMjA5MDk6YW5kcm9pZDphMmU0ODY1MDVhZDQzNGY1.json | text | |
MD5:— | SHA256:— | |||
| 3250 | app_process64 | /data/data/com.roblox.client/cache/journal.tmp | text | |
MD5:— | SHA256:— | |||
| 3250 | app_process64 | /data/data/com.roblox.client/databases/google_app_measurement_local.db | binary | |
MD5:— | SHA256:— | |||
| 3250 | app_process64 | /data/data/com.roblox.client/shared_prefs/prefs.xml | xml | |
MD5:— | SHA256:— | |||
| 3250 | app_process64 | /data/data/com.roblox.client/no_backup/androidx.work.workdb-journal | binary | |
MD5:— | SHA256:— | |||
| 3250 | app_process64 | /data/data/com.roblox.client/no_backup/androidx.work.workdb-wal | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
522
TCP/UDP connections
280
DNS requests
373
Threats
21
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
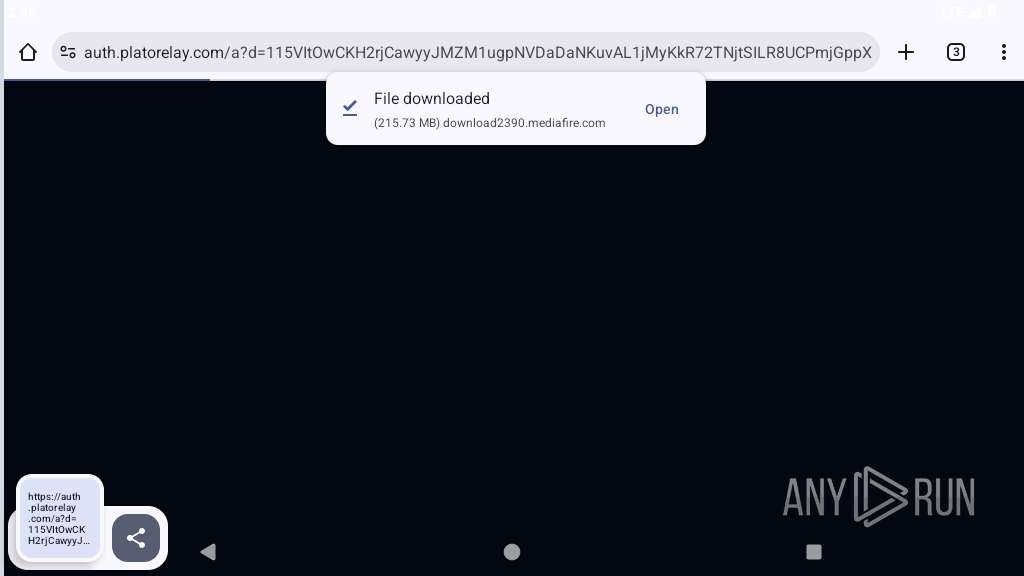
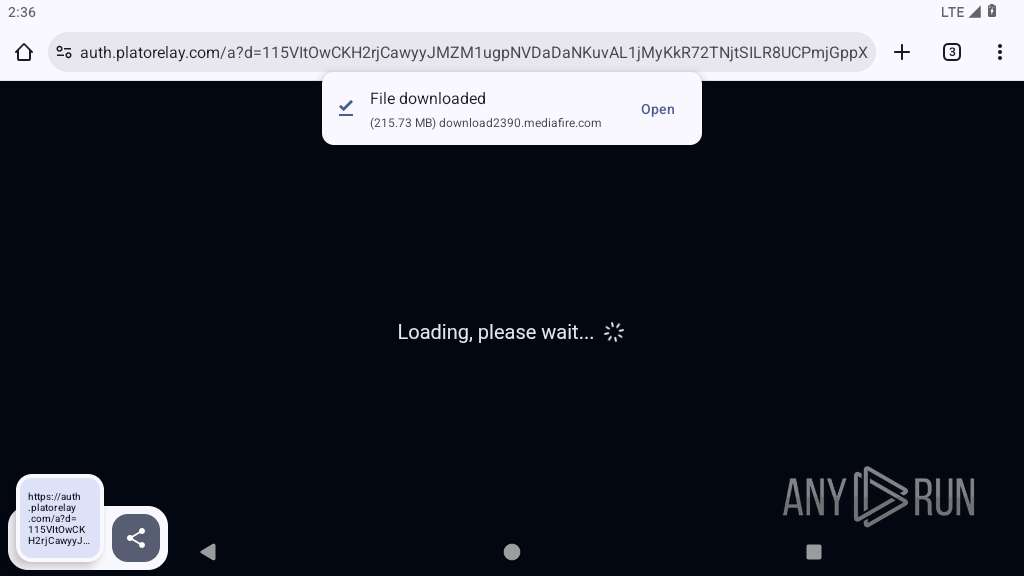
2787 | app_process64 | GET | 302 | 104.17.148.83:443 | https://www.mediafire.com/cdn-cgi/challenge-platform/scripts/jsd/main.js | unknown | — | — | unknown |
— | — | GET | 204 | 216.58.206.68:80 | http://www.google.com/gen_204 | unknown | — | — | whitelisted |
822 | app_process64 | GET | 204 | 142.251.141.67:80 | http://connectivitycheck.gstatic.com/generate_204 | unknown | — | — | whitelisted |
2787 | app_process64 | GET | 200 | 104.17.148.83:443 | https://www.mediafire.com/file/rjb5w355o8dsc0f/Delta-2.703.1353-02.apk/file | unknown | html | 128 Kb | unknown |
2787 | app_process64 | GET | 200 | 104.17.148.83:443 | https://static.mediafire.com/images/filetype/file-zip-v3.png | unknown | image | 1.83 Kb | unknown |
2787 | app_process64 | GET | 200 | 142.250.186.174:80 | http://clients2.google.com/time/1/current?cup2key=9:7Nq6rRIUSsGrc57BvUu4EyrleyySYuCVQUPFNYMN7Bc&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | unknown | — | — | whitelisted |
2787 | app_process64 | GET | 200 | 104.17.148.83:443 | https://static.mediafire.com/images/backgrounds/header/mf_logo_full_color.svg | unknown | image | 3.28 Kb | unknown |
2787 | app_process64 | GET | 200 | 104.17.148.83:443 | https://www.mediafire.com/images/flags_svg/usa.svg | unknown | image | 1.44 Kb | unknown |
2787 | app_process64 | GET | 200 | 104.17.148.83:443 | https://static.mediafire.com/images/icons/svg_light/twitter.svg | unknown | image | 949 b | unknown |
2787 | app_process64 | GET | 200 | 104.17.148.83:443 | https://static.mediafire.com/images/icons/svg_light/facebook.svg | unknown | image | 401 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
443 | mdnsd | 224.0.0.251:5353 | — | — | — | whitelisted |
— | — | 216.58.206.68:80 | www.google.com | GOOGLE | US | whitelisted |
— | — | 216.58.206.68:443 | www.google.com | GOOGLE | US | whitelisted |
— | — | 142.251.141.67:80 | connectivitycheck.gstatic.com | GOOGLE | US | whitelisted |
2787 | app_process64 | 142.250.186.174:80 | clients2.google.com | GOOGLE | US | whitelisted |
2787 | app_process64 | 104.17.148.83:443 | www.mediafire.com | CLOUDFLARENET | US | whitelisted |
2787 | app_process64 | 216.58.206.68:443 | www.google.com | GOOGLE | US | whitelisted |
2787 | app_process64 | 64.233.184.84:443 | accounts.google.com | GOOGLE | US | whitelisted |
2787 | app_process64 | 104.21.42.32:443 | cmp.gatekeeperconsent.com | CLOUDFLARENET | US | whitelisted |
2787 | app_process64 | 172.67.199.186:443 | cmp.gatekeeperconsent.com | CLOUDFLARENET | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
www.google.com |
| whitelisted |
clients2.google.com |
| whitelisted |
www.mediafire.com |
| whitelisted |
accounts.google.com |
| whitelisted |
cmp.gatekeeperconsent.com |
| whitelisted |
the.gatekeeperconsent.com |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
privacy.gatekeeperconsent.com |
| whitelisted |
static.mediafire.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2787 | app_process64 | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain (www .mediafire .com) in DNS Lookup |
2787 | app_process64 | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain (www .mediafire .com) in DNS Lookup |
2787 | app_process64 | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
2787 | app_process64 | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
822 | app_process64 | Misc activity | ET INFO Android Device Connectivity Check |
2787 | app_process64 | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |
2787 | app_process64 | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |
2787 | app_process64 | Potentially Bad Traffic | ET FILE_SHARING File Sharing Related Domain in DNS Lookup (download .mediafire .com) |
2787 | app_process64 | Potentially Bad Traffic | ET FILE_SHARING File Sharing Related Domain in DNS Lookup (download .mediafire .com) |
2787 | app_process64 | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |