| File name: | DPRTSetup.exe |
| Full analysis: | https://app.any.run/tasks/6d2b624f-a8d7-4c4d-91d8-139db1c508d8 |
| Verdict: | Malicious activity |
| Analysis date: | March 19, 2021, 00:55:31 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | 86A218B07B06CE7C6A213EE4298D1128 |
| SHA1: | EB767120023528910573A33887A09C4F5F456277 |
| SHA256: | DA08531A4F28223732601F35F424DE25AD1E972520191D690A8213F0DDFAA920 |
| SSDEEP: | 98304:Br8LuBdVQrlQJdc+sujEdZs/hCBkcTPZ6fOehWzBfUDUmA9akKNay2stwhItm:BrOuAQzcdKEdCoPKOehW/mhVQyIh3 |
MALICIOUS
Changes settings of System certificates
- nos_launcher.exe (PID: 1436)
- nos_setup.exe (PID: 1728)
- nosstarter.npe (PID: 1652)
- nossvc.exe (PID: 2448)
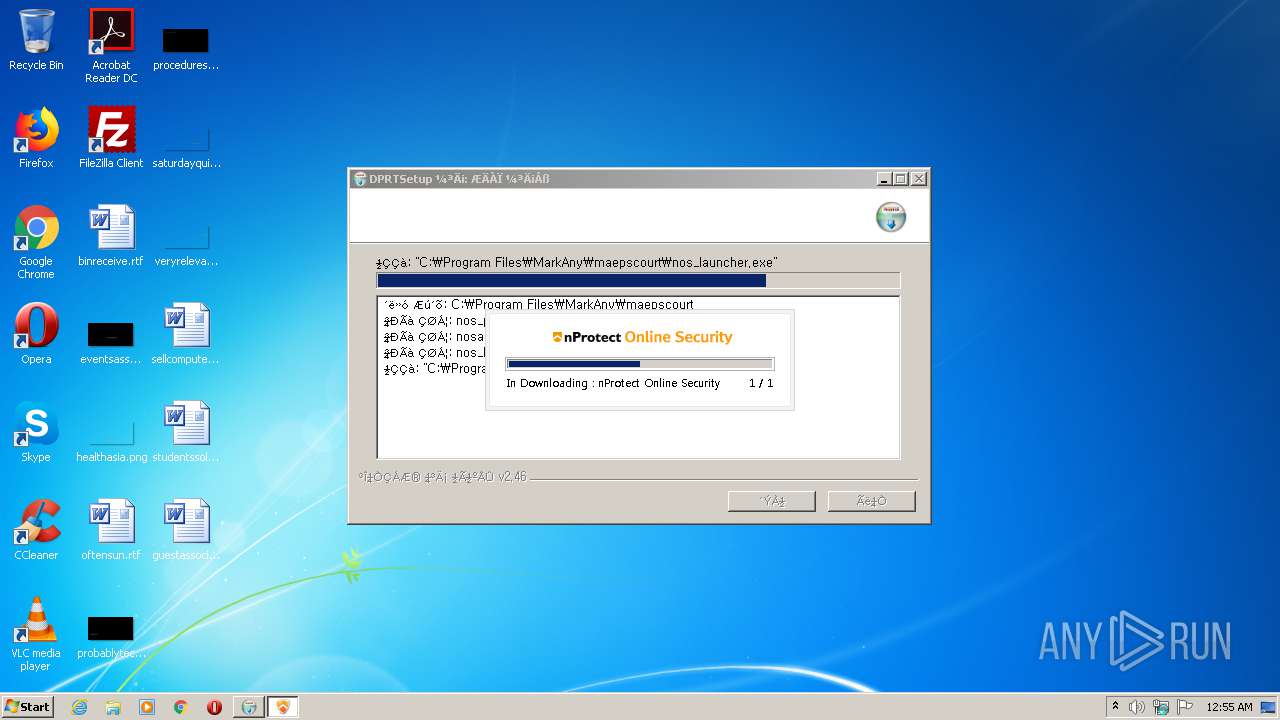
Application was dropped or rewritten from another process
- nos_launcher.exe (PID: 1436)
- certutil.exe (PID: 2808)
- certutil.exe (PID: 3068)
- nos_setup.exe (PID: 1728)
- ns6DF1.tmp (PID: 2344)
- ns6AA4.tmp (PID: 3072)
- ns8812.tmp (PID: 832)
- ns85DF.tmp (PID: 2500)
- ns89D9.tmp (PID: 2064)
- nossvc.exe (PID: 2448)
- nosstarter.npe (PID: 1652)
- certutil.exe (PID: 3804)
- certutil.exe (PID: 3568)
- certutil.exe (PID: 3600)
- nprotect_install.exe (PID: 1676)
- certutil.exe (PID: 952)
- certutil.exe (PID: 3376)
- TrustedSiteCtrl_S.exe (PID: 1748)
Drops executable file immediately after starts
- nos_setup.exe (PID: 1728)
Loads dropped or rewritten executable
- DPRTSetup.exe (PID: 1216)
- nos_setup.exe (PID: 1728)
- certutil.exe (PID: 2808)
- certutil.exe (PID: 3068)
- nossvc.exe (PID: 2448)
- nosstarter.npe (PID: 1652)
- certutil.exe (PID: 3804)
- certutil.exe (PID: 3568)
- certutil.exe (PID: 3600)
- certutil.exe (PID: 3376)
- certutil.exe (PID: 952)
Steals credentials from Web Browsers
- nos_setup.exe (PID: 1728)
- certutil.exe (PID: 2808)
- certutil.exe (PID: 3068)
- certutil.exe (PID: 3568)
- certutil.exe (PID: 3376)
- certutil.exe (PID: 952)
- certutil.exe (PID: 3600)
- nosstarter.npe (PID: 1652)
Actions looks like stealing of personal data
- certutil.exe (PID: 2808)
- nos_setup.exe (PID: 1728)
- certutil.exe (PID: 3068)
- certutil.exe (PID: 3568)
- nosstarter.npe (PID: 1652)
- certutil.exe (PID: 3376)
- certutil.exe (PID: 952)
- certutil.exe (PID: 3600)
Adds new firewall rule via NETSH.EXE
- nos_setup.exe (PID: 1728)
- nosstarter.npe (PID: 1652)
Changes internet zones settings
- TrustedSiteCtrl_S.exe (PID: 1748)
SUSPICIOUS
Executable content was dropped or overwritten
- DPRTSetup.exe (PID: 1216)
- nos_launcher.exe (PID: 1436)
- nos_setup.exe (PID: 1728)
- nprotect_install.exe (PID: 1676)
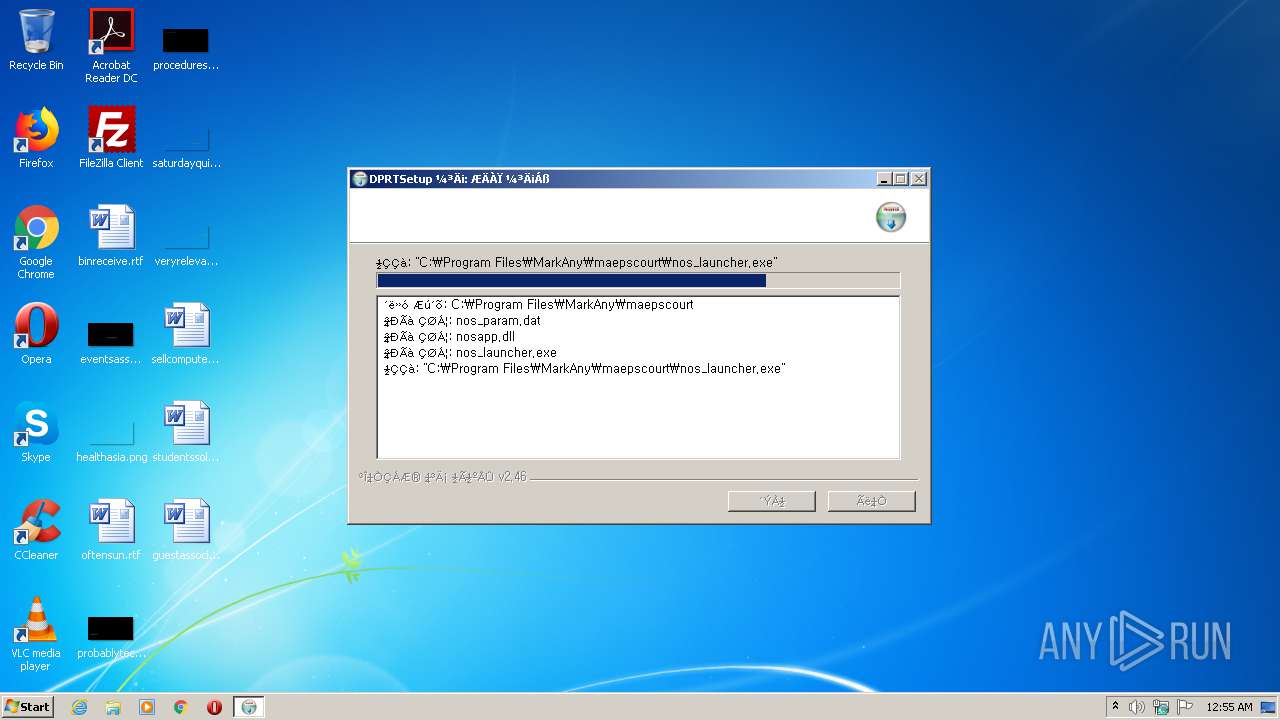
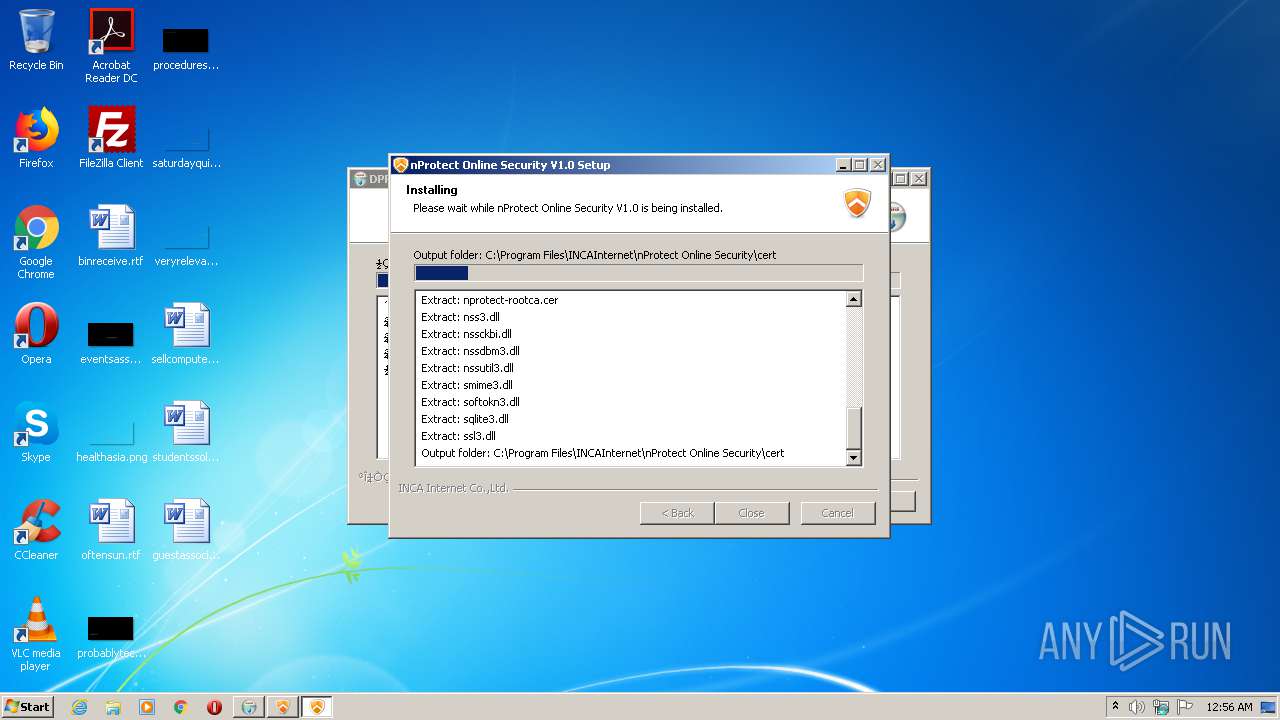
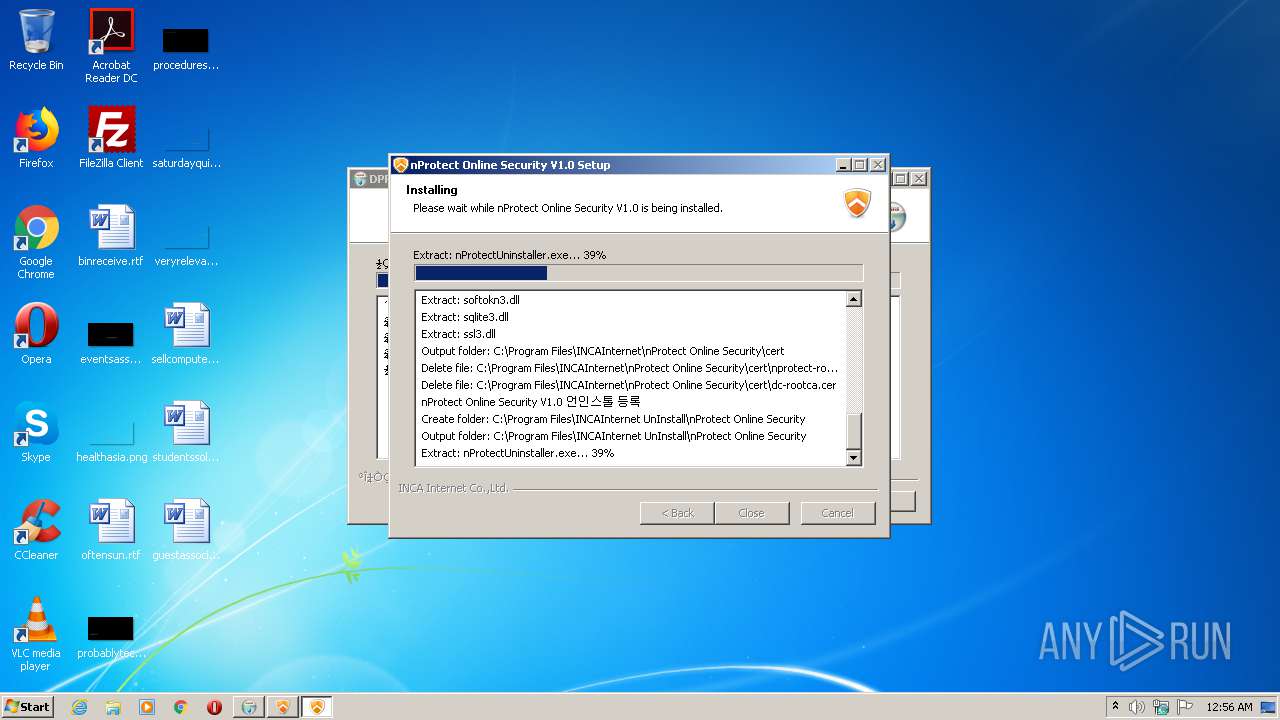
Creates a directory in Program Files
- DPRTSetup.exe (PID: 1216)
- nos_setup.exe (PID: 1728)
Changes default file association
- DPRTSetup.exe (PID: 1216)
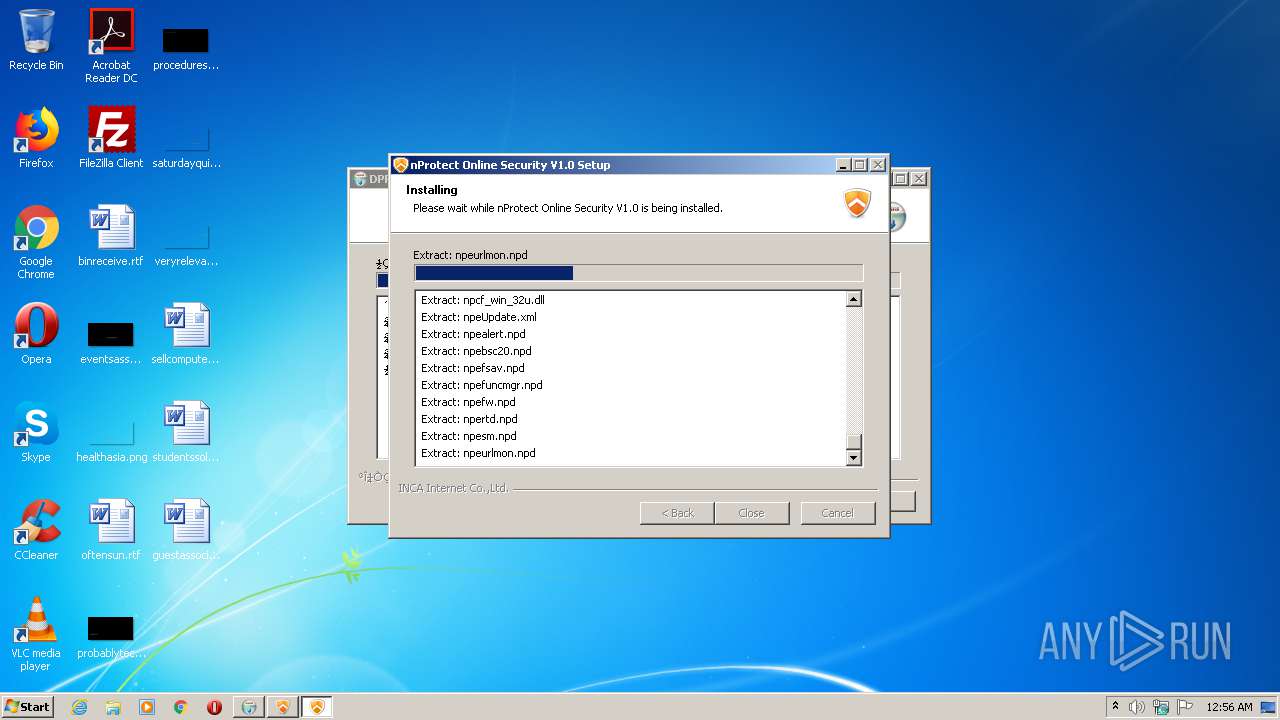
Creates files in the program directory
- DPRTSetup.exe (PID: 1216)
- nos_setup.exe (PID: 1728)
- nprotect_install.exe (PID: 1676)
- nosstarter.npe (PID: 1652)
Drops a file with too old compile date
- DPRTSetup.exe (PID: 1216)
- nos_setup.exe (PID: 1728)
- nprotect_install.exe (PID: 1676)
Drops a file that was compiled in debug mode
- DPRTSetup.exe (PID: 1216)
- nos_setup.exe (PID: 1728)
Creates files in the Windows directory
- nos_setup.exe (PID: 1728)
- nossvc.exe (PID: 2448)
Starts SC.EXE for service management
- ns6AA4.tmp (PID: 3072)
- ns85DF.tmp (PID: 2500)
- ns89D9.tmp (PID: 2064)
- ns8812.tmp (PID: 832)
Adds / modifies Windows certificates
- nos_launcher.exe (PID: 1436)
- nossvc.exe (PID: 2448)
- nosstarter.npe (PID: 1652)
Starts application with an unusual extension
- nos_setup.exe (PID: 1728)
Creates a software uninstall entry
- nos_setup.exe (PID: 1728)
- DPRTSetup.exe (PID: 1216)
Uses NETSH.EXE for network configuration
- nos_setup.exe (PID: 1728)
- nosstarter.npe (PID: 1652)
Creates files in the user directory
- certutil.exe (PID: 3068)
- certutil.exe (PID: 3804)
Removes files from Windows directory
- nos_setup.exe (PID: 1728)
- nossvc.exe (PID: 2448)
Drops a file with a compile date too recent
- nos_setup.exe (PID: 1728)
- DPRTSetup.exe (PID: 1216)
Executed as Windows Service
- nossvc.exe (PID: 2448)
Low-level read access rights to disk partition
- nosstarter.npe (PID: 1652)
Creates or modifies windows services
- nosstarter.npe (PID: 1652)
INFO
Dropped object may contain Bitcoin addresses
- nos_setup.exe (PID: 1728)
Reads the hosts file
- nosstarter.npe (PID: 1652)
Reads settings of System Certificates
- nosstarter.npe (PID: 1652)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | NSIS - Nullsoft Scriptable Install System (94.8) |
|---|---|---|
| .exe | | | Win32 Executable MS Visual C++ (generic) (3.4) |
| .dll | | | Win32 Dynamic Link Library (generic) (0.7) |
| .exe | | | Win32 Executable (generic) (0.5) |
| .exe | | | Generic Win/DOS Executable (0.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2009:12:05 23:50:46+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 23552 |
| InitializedDataSize: | 119808 |
| UninitializedDataSize: | 1024 |
| EntryPoint: | 0x323c |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.6 |
| ProductVersionNumber: | 1.0.0.6 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Windows, Korea (Shift - KSC 5601) |
| CompanyName: | 인터넷등기소 |
| FileVersion: | 1.0.0.6 |
| LegalCopyright: | 인터넷등기소 |
| ProductName: | DPRTSetup |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 05-Dec-2009 22:50:46 |
| Detected languages: |
|
| CompanyName: | 인터넷등기소 |
| FileVersion: | 1.0.0.6 |
| LegalCopyright: | 인터넷등기소 |
| ProductName: | DPRTSetup |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 05-Dec-2009 22:50:46 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00005A5A | 0x00005C00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.4177 |
.rdata | 0x00007000 | 0x00001190 | 0x00001200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.18163 |
.data | 0x00009000 | 0x0001AF98 | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.70903 |
.ndata | 0x00024000 | 0x00009000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x0002D000 | 0x00004258 | 0x00004400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.90304 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.21482 | 958 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 5.9993 | 3752 | UNKNOWN | English - United States | RT_ICON |
3 | 6.24459 | 2216 | UNKNOWN | English - United States | RT_ICON |
4 | 5.01502 | 1384 | UNKNOWN | English - United States | RT_ICON |
5 | 6.16057 | 1128 | UNKNOWN | English - United States | RT_ICON |
6 | 3.34146 | 744 | UNKNOWN | English - United States | RT_ICON |
7 | 3.04232 | 296 | UNKNOWN | English - United States | RT_ICON |
103 | 2.6691 | 104 | UNKNOWN | English - United States | RT_GROUP_ICON |
105 | 2.68176 | 494 | UNKNOWN | English - United States | RT_DIALOG |
106 | 2.86295 | 228 | UNKNOWN | English - United States | RT_DIALOG |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
VERSION.dll |
ole32.dll |
Total processes
78
Monitored processes
26
Malicious processes
13
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 832 | "C:\Users\admin\AppData\Local\Temp\nsx5E3F.tmp\ns8812.tmp" "C:\Windows\system32\sc.exe" description "nossvc" "nProtect Online Security(PFS)" | C:\Users\admin\AppData\Local\Temp\nsx5E3F.tmp\ns8812.tmp | — | nos_setup.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 952 | "C:\Program Files\INCAInternet\nProtect Online Security\cert\certutil.exe" -L -d sql:"C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default" | C:\Program Files\INCAInternet\nProtect Online Security\cert\certutil.exe | nosstarter.npe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 988 | "C:\Windows\system32\sc.exe" control nossvc 200 | C:\Windows\system32\sc.exe | — | ns6AA4.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: A tool to aid in developing services for WindowsNT Exit code: 1060 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1216 | "C:\Users\admin\AppData\Local\Temp\DPRTSetup.exe" | C:\Users\admin\AppData\Local\Temp\DPRTSetup.exe | explorer.exe | ||||||||||||
User: admin Company: 인터넷등기소 Integrity Level: HIGH Exit code: 0 Version: 1.0.0.6 Modules
| |||||||||||||||
| 1436 | "C:\Program Files\MarkAny\maepscourt\nos_launcher.exe" | C:\Program Files\MarkAny\maepscourt\nos_launcher.exe | DPRTSetup.exe | ||||||||||||
User: admin Company: INCA Internet Co., Ltd. Integrity Level: HIGH Description: nProtect Online Security Downloader Exit code: 2 Version: 2017, 4, 4, 1 Modules
| |||||||||||||||
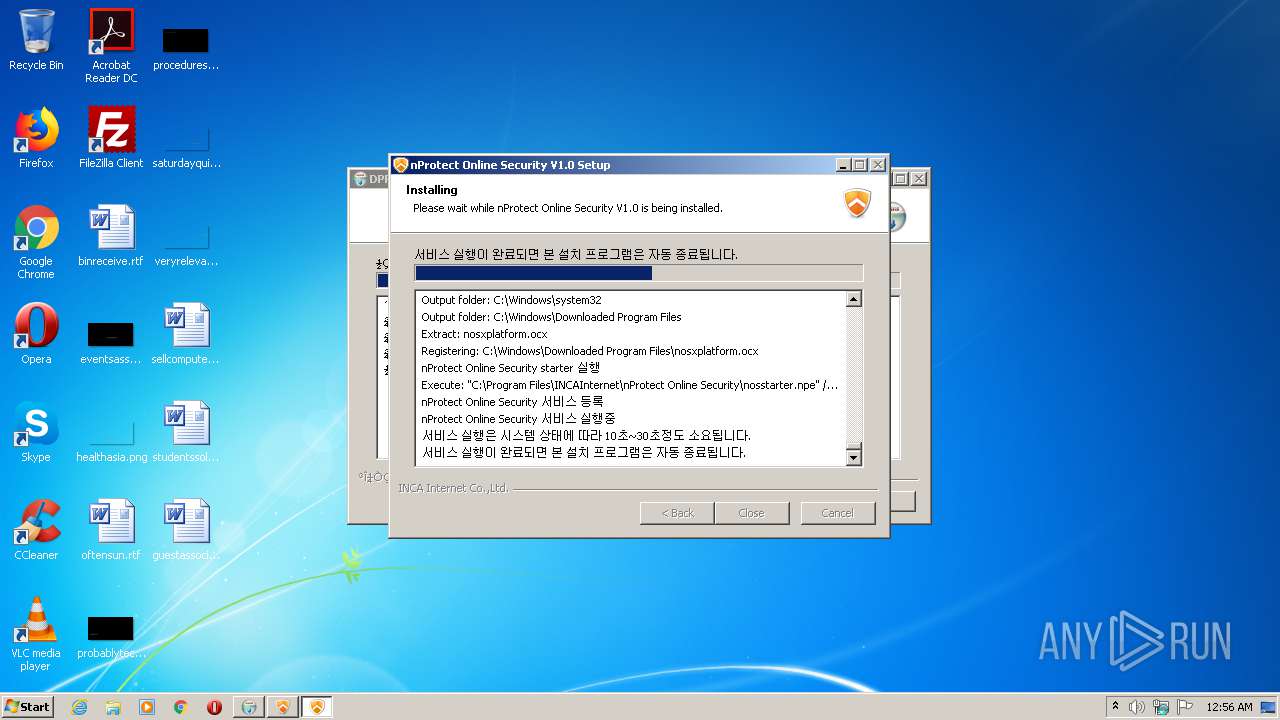
| 1652 | "C:\Program Files\INCAInternet\nProtect Online Security\nosstarter.npe" /SET | C:\Program Files\INCAInternet\nProtect Online Security\nosstarter.npe | nos_setup.exe | ||||||||||||
User: admin Company: INCA Internet Co., Ltd. Integrity Level: HIGH Description: nProtect Online Security Starter Exit code: 0 Version: 2020, 11, 10, 1 Modules
| |||||||||||||||
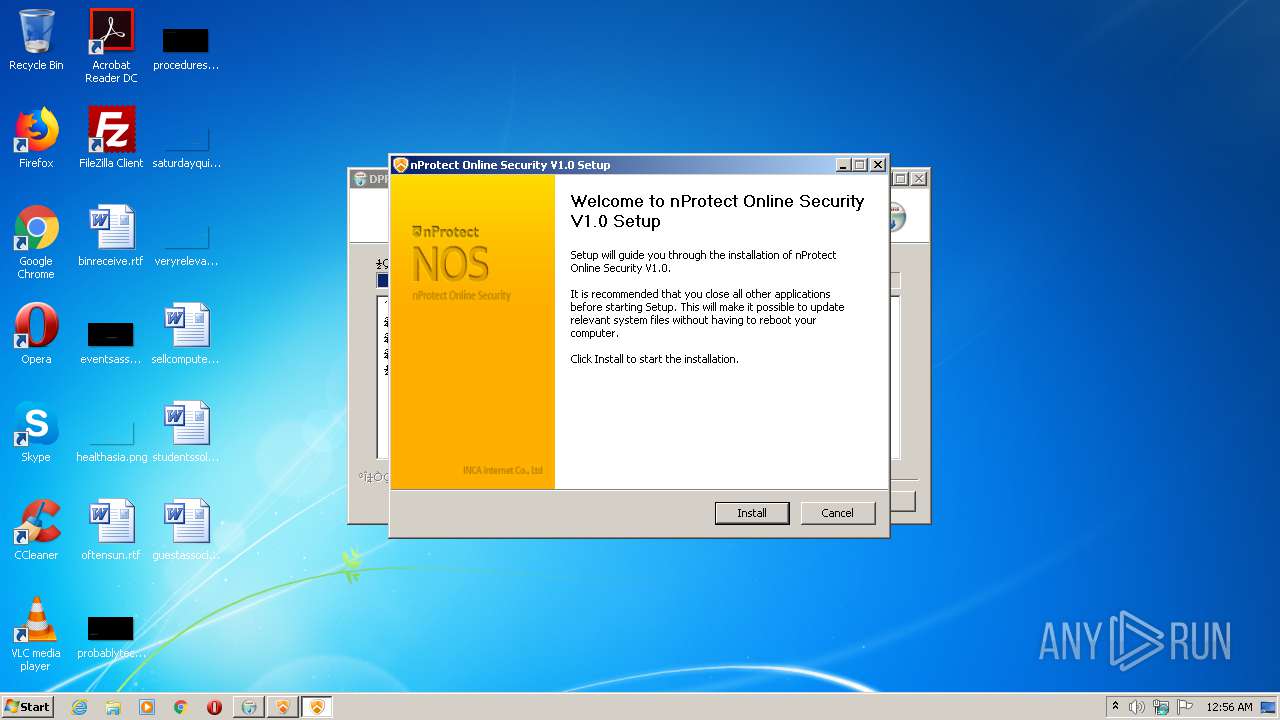
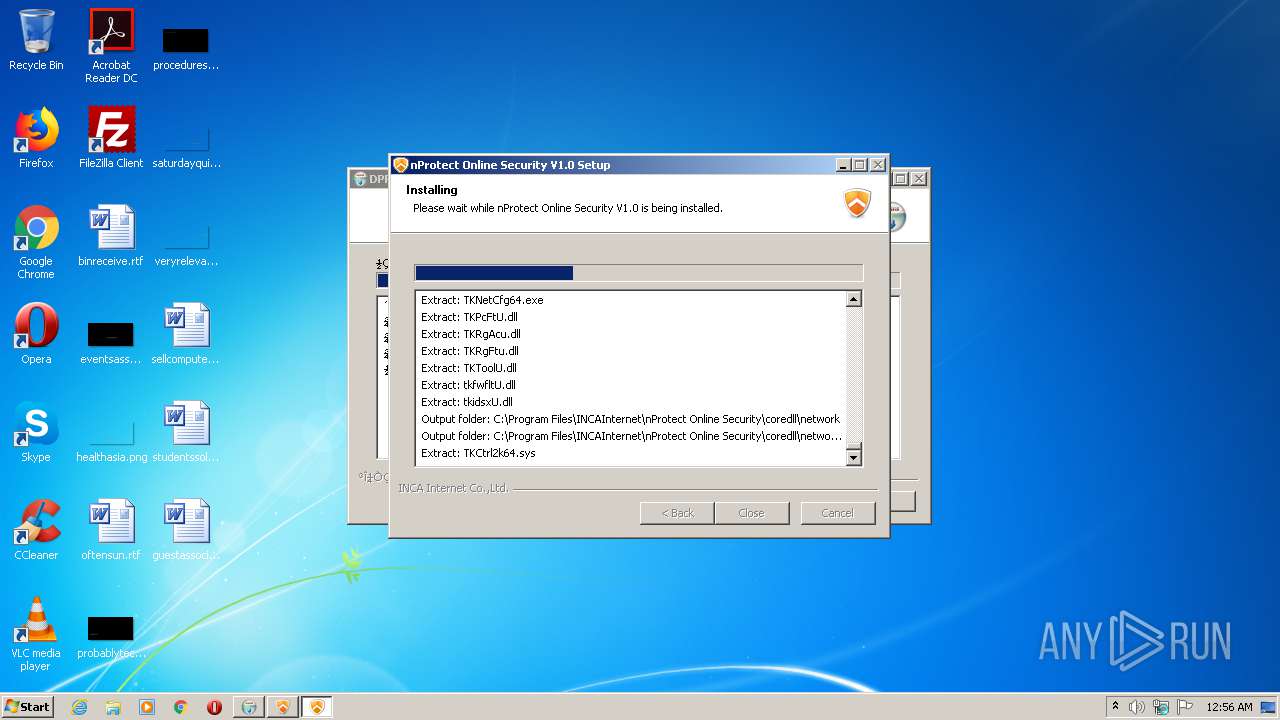
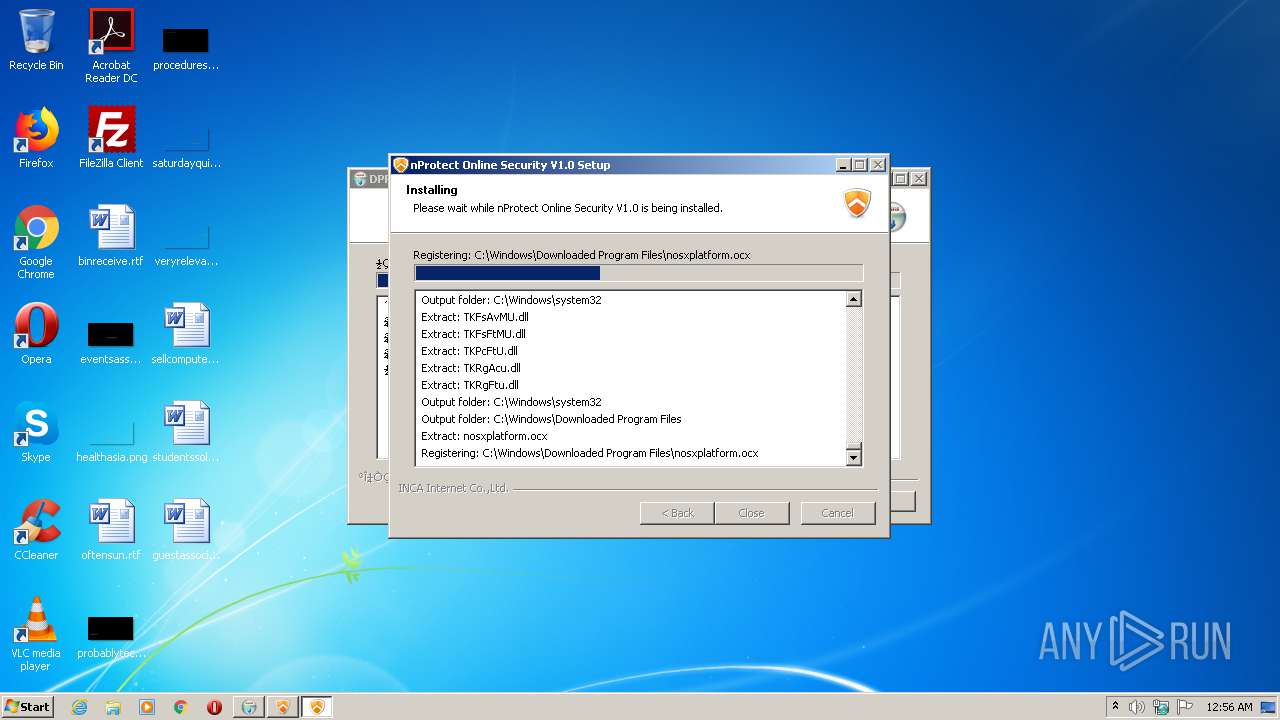
| 1676 | "C:\Program Files\INCAInternet\nProtect Online Security\nprotect_install.exe" /T:c:\temp | C:\Program Files\INCAInternet\nProtect Online Security\nprotect_install.exe | nos_setup.exe | ||||||||||||
User: admin Company: INCA Internet Co.,Ltd. Integrity Level: HIGH Description: nProtect Online Security V1.0 Installer Exit code: 2 Version: 2017.4.12.1 Modules
| |||||||||||||||
| 1728 | C:\Users\admin\AppData\Local\Temp\nos_setup.exe | C:\Users\admin\AppData\Local\Temp\nos_setup.exe | nos_launcher.exe | ||||||||||||
User: admin Company: INCA Internet Co.,Ltd. Integrity Level: HIGH Description: nProtect Online Security V1.0 Installer Exit code: 2 Version: 2021. 3. 18. 1 Modules
| |||||||||||||||
| 1748 | "C:\Program Files\MarkAny\maepscourt\TrustedSiteCtrl_S.exe" | C:\Program Files\MarkAny\maepscourt\TrustedSiteCtrl_S.exe | — | DPRTSetup.exe | |||||||||||
User: admin Company: iros Integrity Level: HIGH Description: TrustedSiteCtrl 응용 프로그램 Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 2064 | "C:\Users\admin\AppData\Local\Temp\nsx5E3F.tmp\ns89D9.tmp" "C:\Windows\system32\sc.exe" start "nossvc" | C:\Users\admin\AppData\Local\Temp\nsx5E3F.tmp\ns89D9.tmp | — | nos_setup.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
Total events
1 074
Read events
817
Write events
257
Delete events
0
Modification events
| (PID) Process: | (1216) DPRTSetup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\dprtregisterxctrl |
| Operation: | write | Name: | (default) |
Value: URL:dprtregisterxctrl Protocol | |||
| (PID) Process: | (1216) DPRTSetup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\dprtregisterxctrl |
| Operation: | write | Name: | URL Protocol |
Value: | |||
| (PID) Process: | (1216) DPRTSetup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\dprtregisterxctrl\shell\open\command |
| Operation: | write | Name: | (default) |
Value: "C:\Program Files\markany\maepscourt\dprtregisterxctrl.exe" "%1" | |||
| (PID) Process: | (1436) nos_launcher.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\INCAInternet |
| Operation: | write | Name: | retDown |
Value: -1 | |||
| (PID) Process: | (1436) nos_launcher.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (1436) nos_launcher.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (1436) nos_launcher.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (1436) nos_launcher.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (1436) nos_launcher.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A5000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (1436) nos_launcher.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
222
Suspicious files
296
Text files
35
Unknown types
356
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1728 | nos_setup.exe | C:\Users\admin\AppData\Local\Temp\nsx5E3F.tmp\ns6AA4.tmp | — | |
MD5:— | SHA256:— | |||
| 1436 | nos_launcher.exe | C:\Users\admin\AppData\LocalLow\nProtect\Log\nos_launcher.exe.npo | txt | |
MD5:— | SHA256:— | |||
| 1728 | nos_setup.exe | C:\Windows\system32\tkfwvt.sys | executable | |
MD5:— | SHA256:— | |||
| 1216 | DPRTSetup.exe | C:\Program Files\MarkAny\maepscourt\nos_param.dat | binary | |
MD5:D2DEEE78DD437C77232BEE973ACA21B9 | SHA256:CEC28B803F34D864662BDBA27F526F951515F84EA2DC421A46A6DD3546A37B88 | |||
| 1728 | nos_setup.exe | C:\Users\admin\AppData\Local\Temp\nsx5E3F.tmp\nppb.dll | executable | |
MD5:59A0F094697AD92BEB7FA7C82543D5BA | SHA256:F09992B46B6690500D6BCA71963F8CAF959E08BD8E14430CD3E4EB84444FE1DB | |||
| 1728 | nos_setup.exe | C:\Users\admin\AppData\Local\Temp\nsx5E3F.tmp\UserInfo.dll | executable | |
MD5:98FF85B635D9114A9F6A0CD7B9B649D0 | SHA256:933F93A30CE44DF96CBC4AC0B56A8B02EE01DA27E4EA665D1D846357A8FCA8DE | |||
| 1728 | nos_setup.exe | C:\Users\admin\AppData\Local\Temp\nsx5E3F.tmp\GetVersion.dll | executable | |
MD5:989672C2DF6AB3BBA092D5CB796C45E0 | SHA256:23E71AC3E977EB1AB8D365E8A66776D002DD81AFB492A8B41120F48BBE0F1C3D | |||
| 1728 | nos_setup.exe | C:\Users\admin\AppData\Local\Temp\nsx5E3F.tmp\npcf_win_32u.dll | executable | |
MD5:9ED934BA36F76BD950B33606F5F48300 | SHA256:E60F5991DF3B70E97FE660D41095D6C93B065D47E4909FD1301B6BB6CF989D6E | |||
| 1728 | nos_setup.exe | C:\Users\admin\AppData\Local\Temp\nsx5E3F.tmp\nsDialogs.dll | executable | |
MD5:48F3E7860E1DE2B4E63EC744A5E9582A | SHA256:6BF9CCCD8A600F4D442EFE201E8C07B49605BA35F49A4B3AB22FA2641748E156 | |||
| 1728 | nos_setup.exe | C:\Users\admin\AppData\Local\Temp\nsx5E3F.tmp\npeNSISUtil.dll | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
10
DNS requests
8
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | — | 23.51.123.27:80 | http://sf.symcd.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTSqZMG5M8TA9rdzkbCnNwuMAd5VgQUz5mp6nsm9EvJjo%2FX8AUm7%2BPSp50CEBAl3Oz5Y4DLk%2FbaIuO25fk%3D | NL | — | — | whitelisted |
2448 | nossvc.exe | GET | 200 | 23.51.123.27:80 | http://ocsp.verisign.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS56bKHAoUD%2BOyl%2B0LhPg9JxyQm4gQUf9Nlp8Ld7LvwMAnzQzn6Aq8zMTMCEFIA5aolVvwahu2WydRLM8c%3D | NL | der | 1.71 Kb | whitelisted |
2448 | nossvc.exe | GET | 200 | 205.185.216.42:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 57.2 Kb | whitelisted |
2448 | nossvc.exe | GET | 304 | 205.185.216.42:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 57.2 Kb | whitelisted |
1652 | nosstarter.npe | GET | 200 | 205.185.216.42:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 57.2 Kb | whitelisted |
1652 | nosstarter.npe | GET | 304 | 205.185.216.42:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 57.2 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1652 | nosstarter.npe | 52.79.75.124:443 | bwtd.nprotect2.net | Amazon.com, Inc. | KR | unknown |
1652 | nosstarter.npe | 205.185.216.42:80 | www.download.windowsupdate.com | Highwinds Network Group, Inc. | US | whitelisted |
2448 | nossvc.exe | 205.185.216.42:80 | www.download.windowsupdate.com | Highwinds Network Group, Inc. | US | whitelisted |
1652 | nosstarter.npe | 61.111.25.114:443 | supdate.nprotect.net | LG DACOM Corporation | KR | unknown |
— | — | 23.205.226.16:443 | supdated.nprotect.net | GTT Communications Inc. | NL | unknown |
1652 | nosstarter.npe | 15.165.198.136:443 | nsrs.nprotect.net | Hewlett-Packard Company | US | unknown |
— | — | 23.51.123.27:80 | ocsp.verisign.com | Akamai Technologies, Inc. | NL | whitelisted |
1436 | nos_launcher.exe | 61.111.25.113:443 | supdate.nprotect.net | LG DACOM Corporation | KR | unknown |
— | — | 15.165.198.136:443 | nsrs.nprotect.net | Hewlett-Packard Company | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
supdate.nprotect.net |
| suspicious |
www.download.windowsupdate.com |
| whitelisted |
supdated.nprotect.net |
| unknown |
bwtd.nprotect2.net |
| unknown |
nsrs.nprotect.net |
| unknown |
ocsp.verisign.com |
| whitelisted |
sf.symcd.com |
| whitelisted |