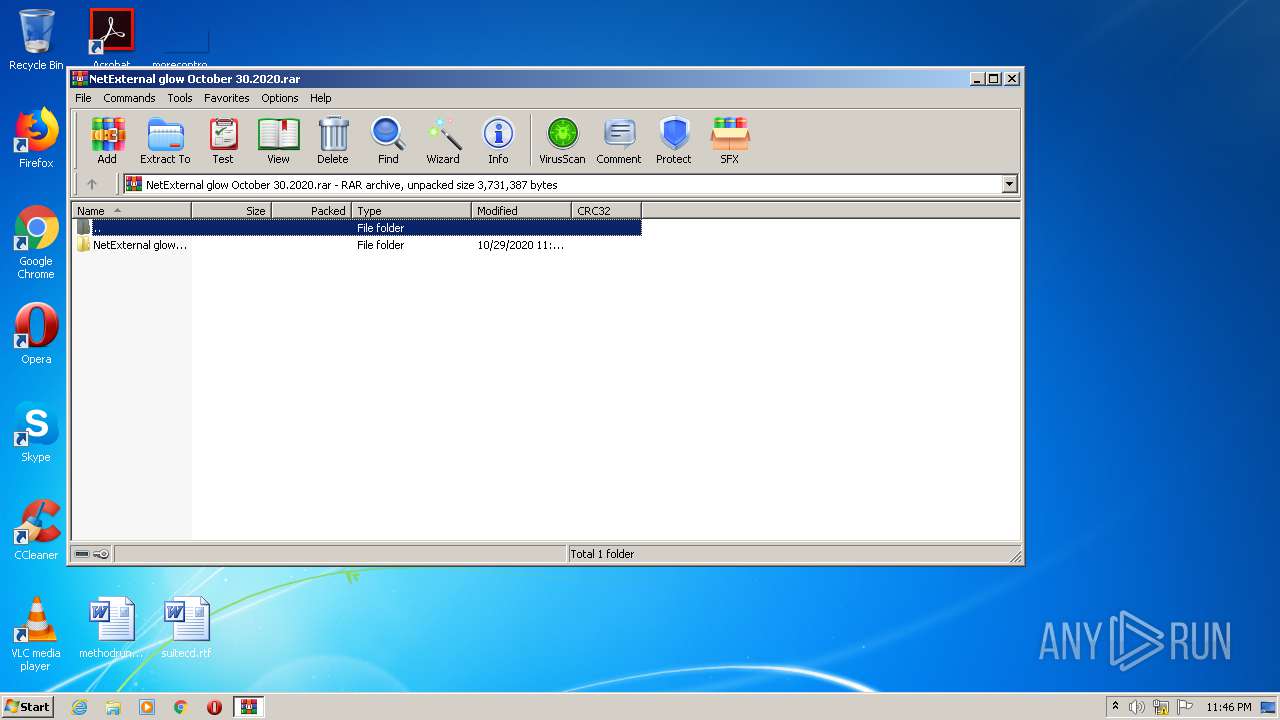
| File name: | NetExternal glow October 30.2020.rar |
| Full analysis: | https://app.any.run/tasks/1a64bc6c-c6a6-434e-aec5-9a02b473fb45 |
| Verdict: | Malicious activity |
| Analysis date: | November 29, 2020, 23:45:59 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | 38C5C9CD08AD56B5AB75CBAF3043028B |
| SHA1: | 84A3B4F92C0FF307B7A9D74ABD1C8068A628ACC7 |
| SHA256: | DA065A4CA3967AB3D09423C32D44F765292B976E78441FDC6A50C18463A39119 |
| SSDEEP: | 49152:rsv0c8aDIWTT6V2TCtEajzrsVlKZnxH61mFqdBKINzNZFoVPobP:JCsQrTXaj4lKt0mEdBKIlNZFoObP |
MALICIOUS
Changes settings of System certificates
- NET-EXTERNAL.exe (PID: 3992)
- DF49.exe (PID: 2532)
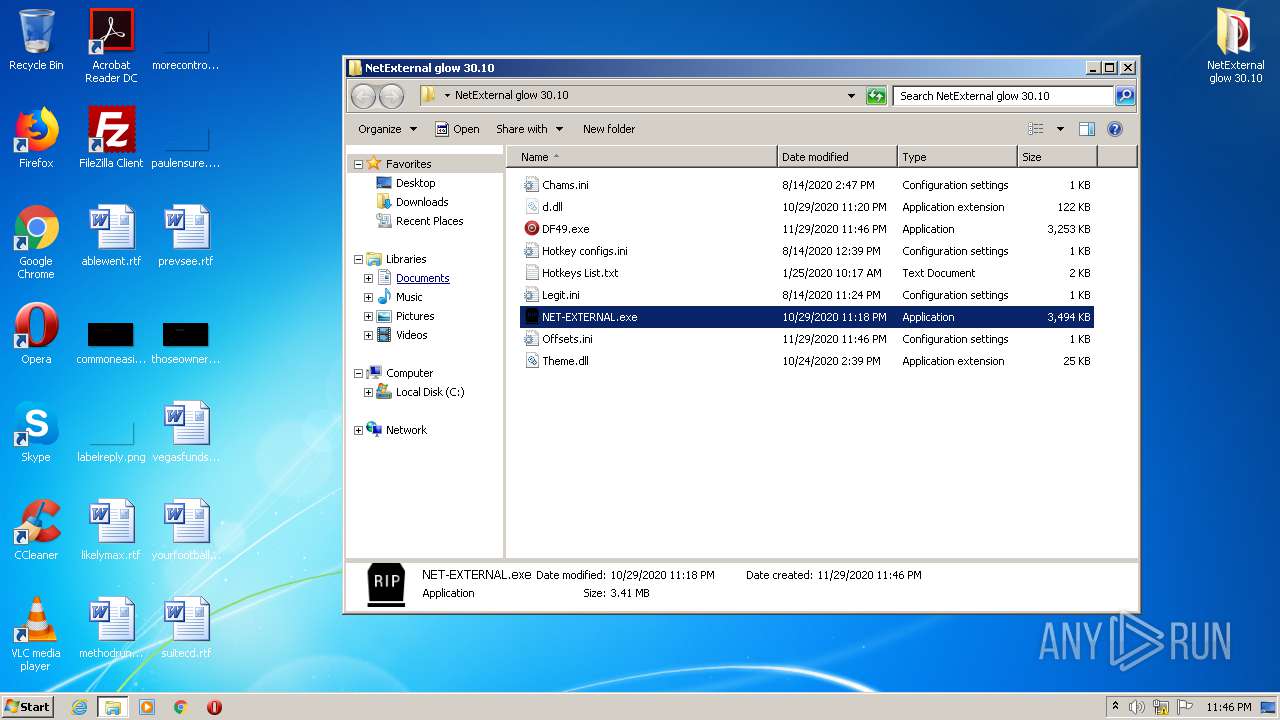
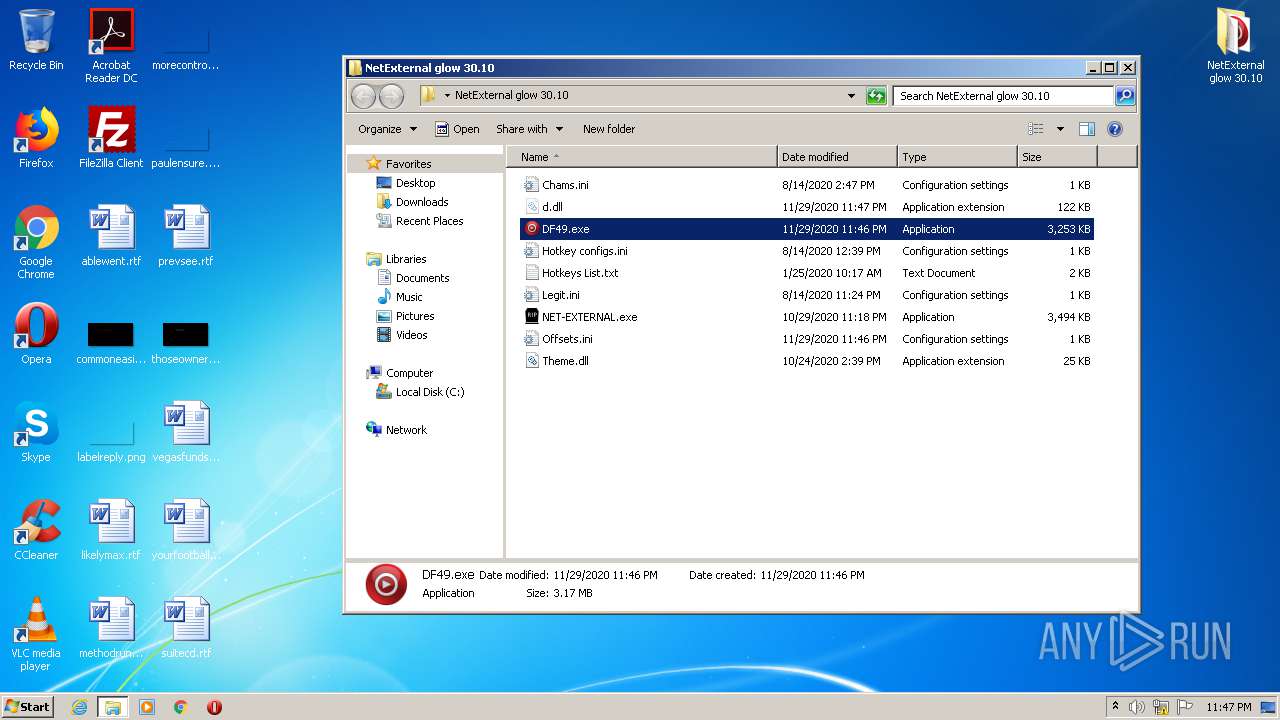
Drops executable file immediately after starts
- DF49.exe (PID: 464)
- DF49.exe (PID: 2532)
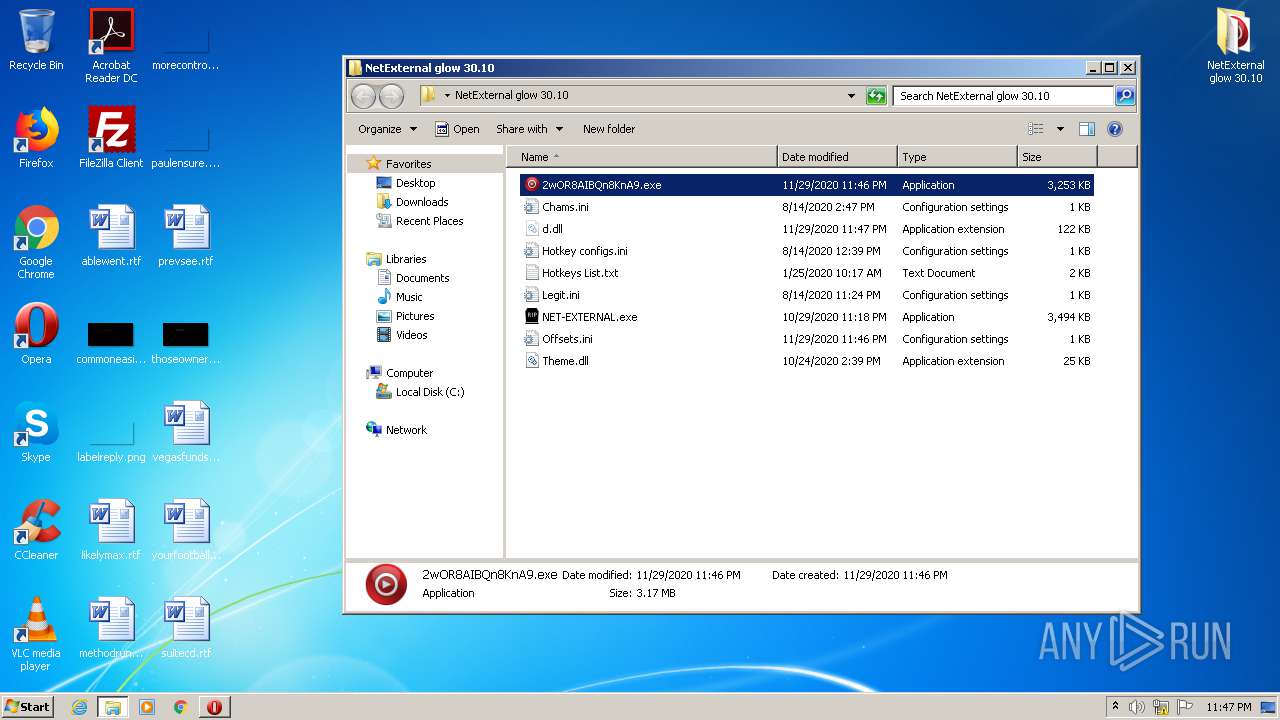
- 2wOR8AIBQn8KnA9.exe (PID: 2612)
- 2wOR8AIBQn8KnA9.exe (PID: 2284)
Application was dropped or rewritten from another process
- DF49.exe (PID: 464)
- DF49.exe (PID: 2532)
- 2wOR8AIBQn8KnA9.exe (PID: 2612)
- 2wOR8AIBQn8KnA9.exe (PID: 2284)
Loads dropped or rewritten executable
- DF49.exe (PID: 2532)
- SearchProtocolHost.exe (PID: 3448)
- DF49.exe (PID: 464)
- 2wOR8AIBQn8KnA9.exe (PID: 2612)
- 2wOR8AIBQn8KnA9.exe (PID: 2284)
SUSPICIOUS
Adds / modifies Windows certificates
- NET-EXTERNAL.exe (PID: 3992)
- DF49.exe (PID: 2532)
Starts Internet Explorer
- NET-EXTERNAL.exe (PID: 3992)
Executable content was dropped or overwritten
- DF49.exe (PID: 464)
- NET-EXTERNAL.exe (PID: 3992)
- DF49.exe (PID: 2532)
- 2wOR8AIBQn8KnA9.exe (PID: 2612)
- 2wOR8AIBQn8KnA9.exe (PID: 2284)
Application launched itself
- DF49.exe (PID: 464)
- 2wOR8AIBQn8KnA9.exe (PID: 2612)
Drops a file that was compiled in debug mode
- DF49.exe (PID: 464)
- DF49.exe (PID: 2532)
- 2wOR8AIBQn8KnA9.exe (PID: 2612)
- 2wOR8AIBQn8KnA9.exe (PID: 2284)
INFO
Reads settings of System Certificates
- NET-EXTERNAL.exe (PID: 3992)
- iexplore.exe (PID: 1260)
- iexplore.exe (PID: 1868)
- DF49.exe (PID: 2532)
- 2wOR8AIBQn8KnA9.exe (PID: 2284)
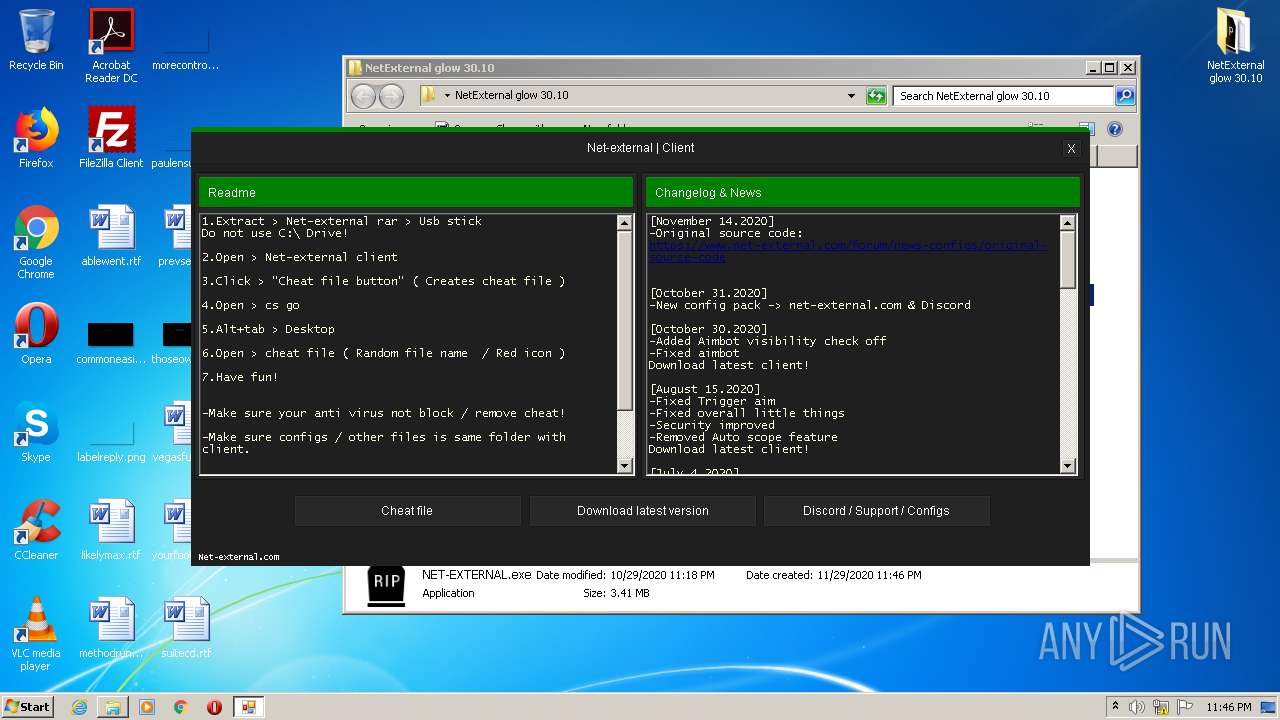
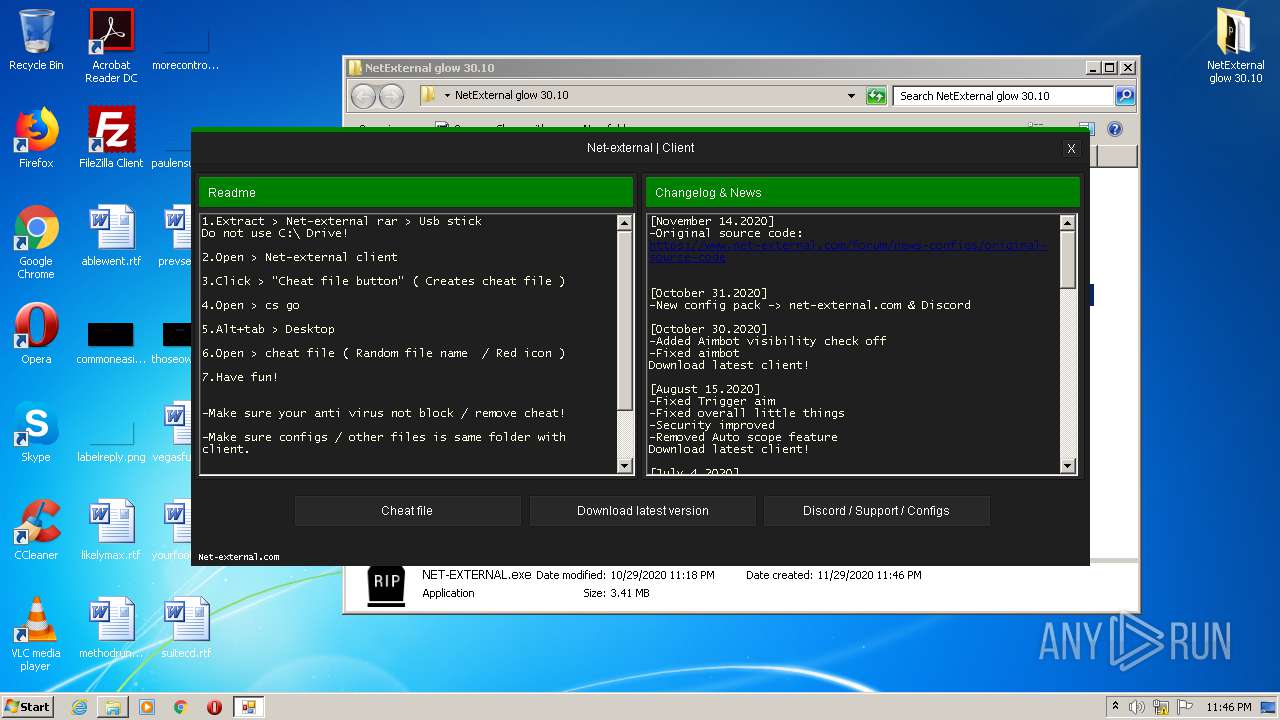
Manual execution by user
- NET-EXTERNAL.exe (PID: 3992)
- DF49.exe (PID: 464)
- 2wOR8AIBQn8KnA9.exe (PID: 2612)
Application launched itself
- iexplore.exe (PID: 1260)
Reads internet explorer settings
- iexplore.exe (PID: 1868)
Changes internet zones settings
- iexplore.exe (PID: 1260)
Changes settings of System certificates
- iexplore.exe (PID: 1260)
Creates files in the user directory
- iexplore.exe (PID: 1868)
Adds / modifies Windows certificates
- iexplore.exe (PID: 1260)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
Total processes
52
Monitored processes
9
Malicious processes
4
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 464 | "C:\Users\admin\Desktop\NetExternal glow 30.10\DF49.exe" | C:\Users\admin\Desktop\NetExternal glow 30.10\DF49.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 4294967295 Version: 2.6.7.2 Modules
| |||||||||||||||
| 1260 | "C:\Program Files\Internet Explorer\iexplore.exe" https://gofile.io/d/gE14Jn | C:\Program Files\Internet Explorer\iexplore.exe | NET-EXTERNAL.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1868 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:1260 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2284 | "C:\Users\admin\Desktop\NetExternal glow 30.10\2wOR8AIBQn8KnA9.exe" | C:\Users\admin\Desktop\NetExternal glow 30.10\2wOR8AIBQn8KnA9.exe | 2wOR8AIBQn8KnA9.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 4294967295 Version: 2.6.7.2 Modules
| |||||||||||||||
| 2532 | "C:\Users\admin\Desktop\NetExternal glow 30.10\DF49.exe" | C:\Users\admin\Desktop\NetExternal glow 30.10\DF49.exe | DF49.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 4294967295 Version: 2.6.7.2 Modules
| |||||||||||||||
| 2612 | "C:\Users\admin\Desktop\NetExternal glow 30.10\2wOR8AIBQn8KnA9.exe" | C:\Users\admin\Desktop\NetExternal glow 30.10\2wOR8AIBQn8KnA9.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 4294967295 Version: 2.6.7.2 Modules
| |||||||||||||||
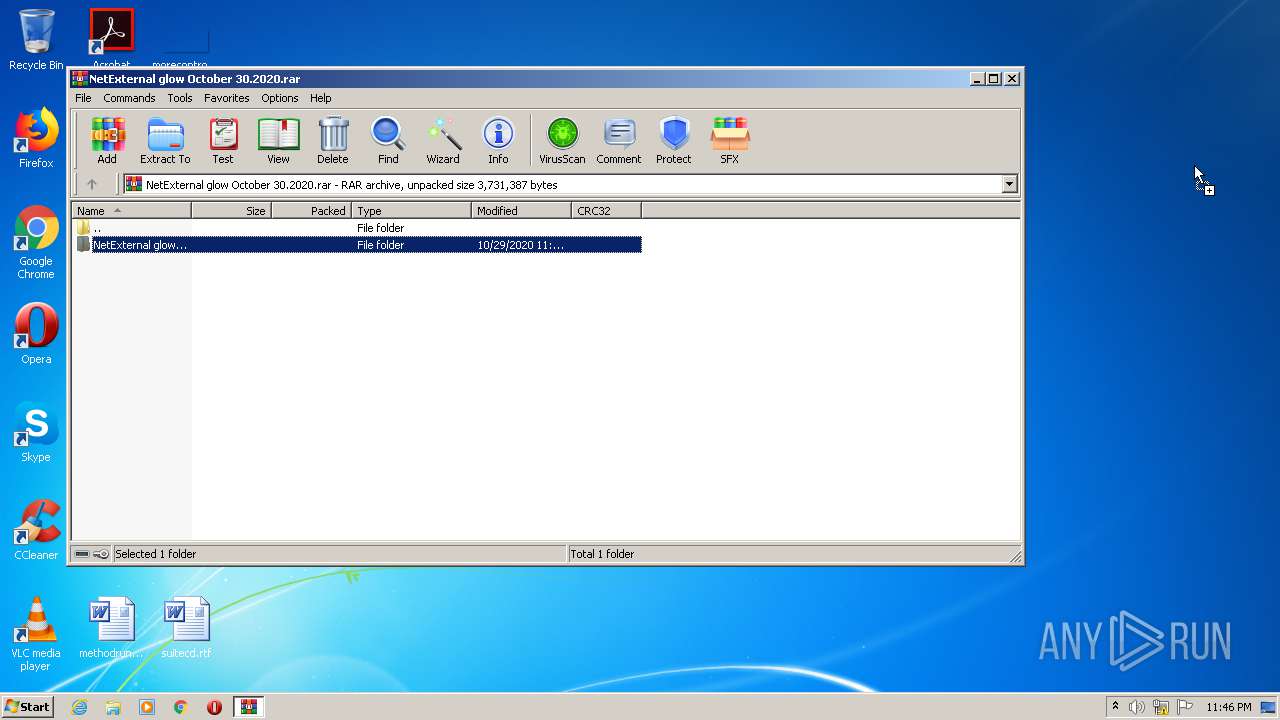
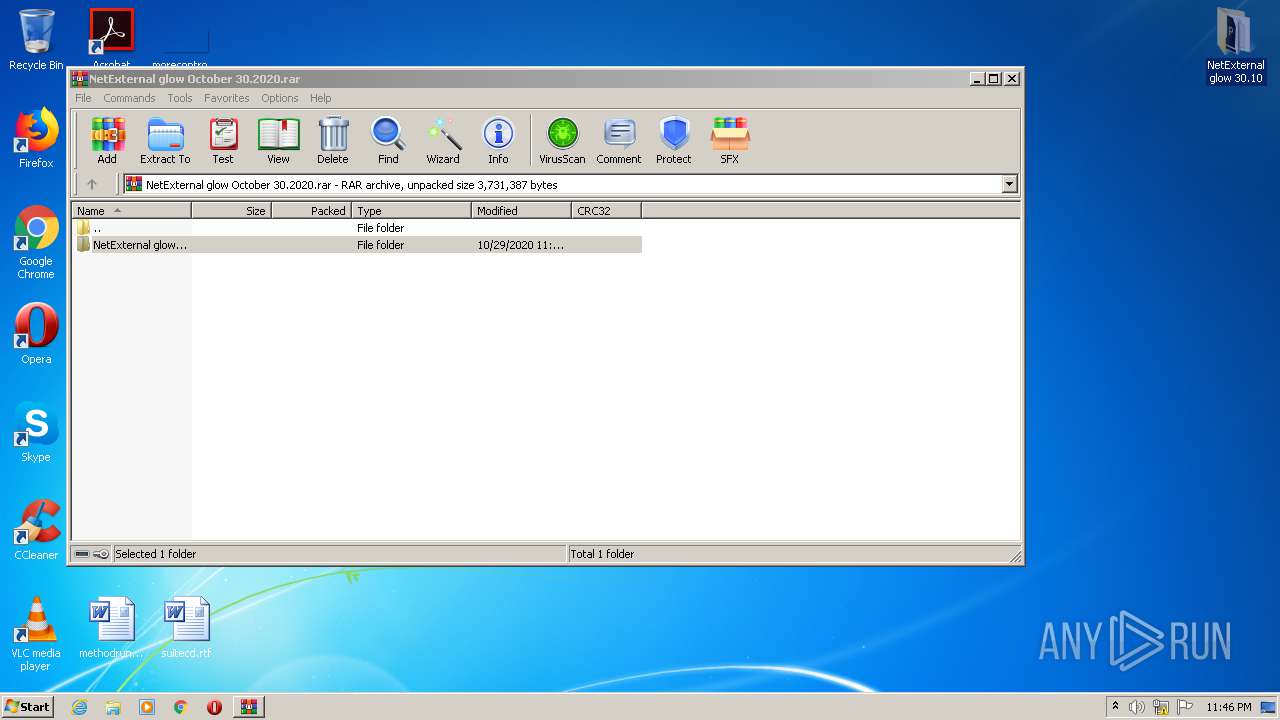
| 2932 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\NetExternal glow October 30.2020.rar" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 3448 | "C:\Windows\system32\SearchProtocolHost.exe" Global\UsGthrFltPipeMssGthrPipe5_ Global\UsGthrCtrlFltPipeMssGthrPipe5 1 -2147483646 "Software\Microsoft\Windows Search" "Mozilla/4.0 (compatible; MSIE 6.0; Windows NT; MS Search 4.0 Robot)" "C:\ProgramData\Microsoft\Search\Data\Temp\usgthrsvc" "DownLevelDaemon" | C:\Windows\System32\SearchProtocolHost.exe | — | SearchIndexer.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Windows Search Protocol Host Exit code: 0 Version: 7.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3992 | "C:\Users\admin\Desktop\NetExternal glow 30.10\NET-EXTERNAL.exe" | C:\Users\admin\Desktop\NetExternal glow 30.10\NET-EXTERNAL.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: NET Exit code: 4294967295 Version: 2.7.3.2 Modules
| |||||||||||||||
Total events
1 647
Read events
1 477
Write events
164
Delete events
6
Modification events
| (PID) Process: | (2932) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2932) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2932) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2932) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\NetExternal glow October 30.2020.rar | |||
| (PID) Process: | (2932) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2932) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2932) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2932) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2932) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF42000000420000000204000037020000 | |||
| (PID) Process: | (2932) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\General |
| Operation: | write | Name: | LastFolder |
Value: C:\Users\admin\AppData\Local\Temp | |||
Executable files
7
Suspicious files
68
Text files
41
Unknown types
38
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
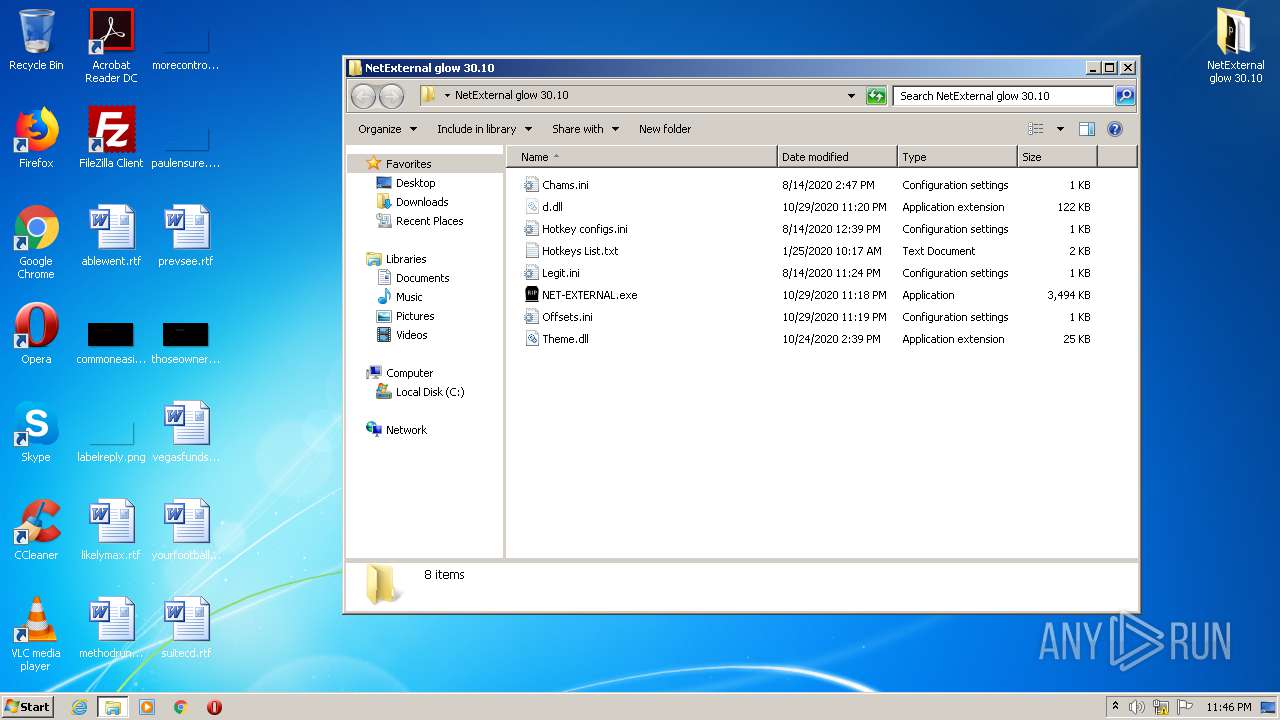
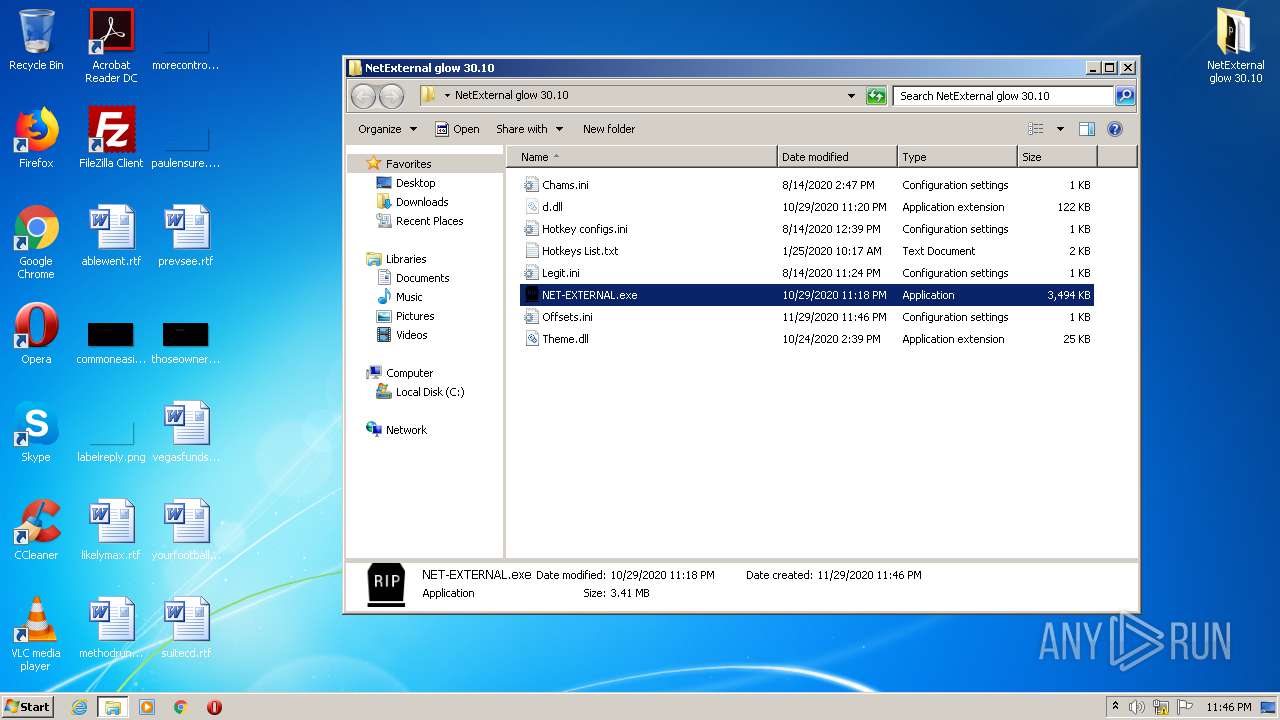
| 2932 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2932.41418\NetExternal glow 30.10\NET-EXTERNAL.exe | — | |
MD5:— | SHA256:— | |||
| 2932 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2932.41418\NetExternal glow 30.10\Theme.dll | — | |
MD5:— | SHA256:— | |||
| 2932 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2932.41418\NetExternal glow 30.10\Legit.ini | — | |
MD5:— | SHA256:— | |||
| 2932 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2932.41418\NetExternal glow 30.10\Chams.ini | — | |
MD5:— | SHA256:— | |||
| 2932 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2932.41418\NetExternal glow 30.10\d.dll | — | |
MD5:— | SHA256:— | |||
| 2932 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2932.41418\NetExternal glow 30.10\Hotkey configs.ini | — | |
MD5:— | SHA256:— | |||
| 2932 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2932.41418\NetExternal glow 30.10\Hotkeys List.txt | — | |
MD5:— | SHA256:— | |||
| 2932 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2932.41418\NetExternal glow 30.10\Offsets.ini | — | |
MD5:— | SHA256:— | |||
| 1868 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Tar305E.tmp | — | |
MD5:— | SHA256:— | |||
| 3992 | NET-EXTERNAL.exe | C:\Users\admin\Documents\offsets.ini | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
34
TCP/UDP connections
64
DNS requests
30
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1868 | iexplore.exe | GET | 200 | 23.55.163.61:80 | http://isrg.trustid.ocsp.identrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRv9GhNQxLSSGKBnMArPUcsHYovpgQUxKexpHsscfrb4UuQdf%2FEFWCFiRACEAoBQUIAAAFThXNqC4Xspwg%3D | US | der | 1.37 Kb | whitelisted |
1868 | iexplore.exe | GET | 200 | 104.18.21.226:80 | http://ocsp.globalsign.com/rootr1/ME8wTTBLMEkwRzAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCDkbwjNvPLFRm7zMB3V80 | US | der | 1.49 Kb | whitelisted |
1868 | iexplore.exe | GET | 200 | 23.55.163.48:80 | http://ocsp.int-x3.letsencrypt.org/MFMwUTBPME0wSzAJBgUrDgMCGgUABBR%2B5mrncpqz%2FPiiIGRsFqEtYHEIXQQUqEpqYwR93brm0Tm3pkVl7%2FOo7KECEgRnv%2FAQseXhKH3izdu0lb5hPA%3D%3D | US | der | 527 b | whitelisted |
1868 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEAo3h2ReX7SMIk79G%2B0UDDw%3D | US | der | 1.47 Kb | whitelisted |
1868 | iexplore.exe | GET | 200 | 104.18.21.226:80 | http://ocsp.globalsign.com/rootr1/ME8wTTBLMEkwRzAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCDkbwjNvPLFRm7zMB3V80 | US | der | 1.49 Kb | whitelisted |
1868 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEAo3h2ReX7SMIk79G%2B0UDDw%3D | US | der | 1.47 Kb | whitelisted |
1868 | iexplore.exe | GET | 200 | 23.55.163.48:80 | http://ocsp.int-x3.letsencrypt.org/MFMwUTBPME0wSzAJBgUrDgMCGgUABBR%2B5mrncpqz%2FPiiIGRsFqEtYHEIXQQUqEpqYwR93brm0Tm3pkVl7%2FOo7KECEgRnv%2FAQseXhKH3izdu0lb5hPA%3D%3D | US | der | 527 b | whitelisted |
1868 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEAo3h2ReX7SMIk79G%2B0UDDw%3D | US | der | 1.47 Kb | whitelisted |
1868 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEAo3h2ReX7SMIk79G%2B0UDDw%3D | US | der | 1.47 Kb | whitelisted |
1868 | iexplore.exe | GET | 200 | 23.55.163.71:80 | http://isrg.trustid.ocsp.identrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRv9GhNQxLSSGKBnMArPUcsHYovpgQUxKexpHsscfrb4UuQdf%2FEFWCFiRACEAoBQUIAAAFThXNqC4Xspwg%3D | US | der | 1.37 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3992 | NET-EXTERNAL.exe | 104.23.98.190:443 | pastebin.com | Cloudflare Inc | US | malicious |
3992 | NET-EXTERNAL.exe | 104.23.99.190:443 | pastebin.com | Cloudflare Inc | US | malicious |
1868 | iexplore.exe | 217.182.142.131:443 | gofile.io | OVH SAS | FR | unknown |
1868 | iexplore.exe | 23.55.163.61:80 | isrg.trustid.ocsp.identrust.com | Akamai International B.V. | US | unknown |
3992 | NET-EXTERNAL.exe | 151.101.64.133:443 | raw.githubusercontent.com | Fastly | US | suspicious |
1868 | iexplore.exe | 23.55.163.71:80 | isrg.trustid.ocsp.identrust.com | Akamai International B.V. | US | suspicious |
1868 | iexplore.exe | 23.55.163.48:80 | ocsp.int-x3.letsencrypt.org | Akamai International B.V. | US | unknown |
1868 | iexplore.exe | 151.101.130.109:443 | cdn.jsdelivr.net | Fastly | US | unknown |
1868 | iexplore.exe | 172.217.11.42:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
1868 | iexplore.exe | 104.22.51.93:443 | cdn.datatables.net | Cloudflare Inc | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
pastebin.com |
| malicious |
raw.githubusercontent.com |
| shared |
gofile.io |
| whitelisted |
isrg.trustid.ocsp.identrust.com |
| whitelisted |
ocsp.int-x3.letsencrypt.org |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
cdn.jsdelivr.net |
| whitelisted |
cdn.buymeacoffee.com |
| whitelisted |
cdn.datatables.net |
| whitelisted |
cdn.rawgit.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1868 | iexplore.exe | Potentially Bad Traffic | ET INFO Observed ZeroSSL SSL/TLS Certificate |
1868 | iexplore.exe | Potentially Bad Traffic | ET INFO Observed ZeroSSL SSL/TLS Certificate |
Process | Message |
|---|---|
DF49.exe | %s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s |
2wOR8AIBQn8KnA9.exe | %s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s |