| File name: | firefox.exe |
| Full analysis: | https://app.any.run/tasks/5823b9a5-ee8e-4b51-b11d-9fc4b97a9bfc |
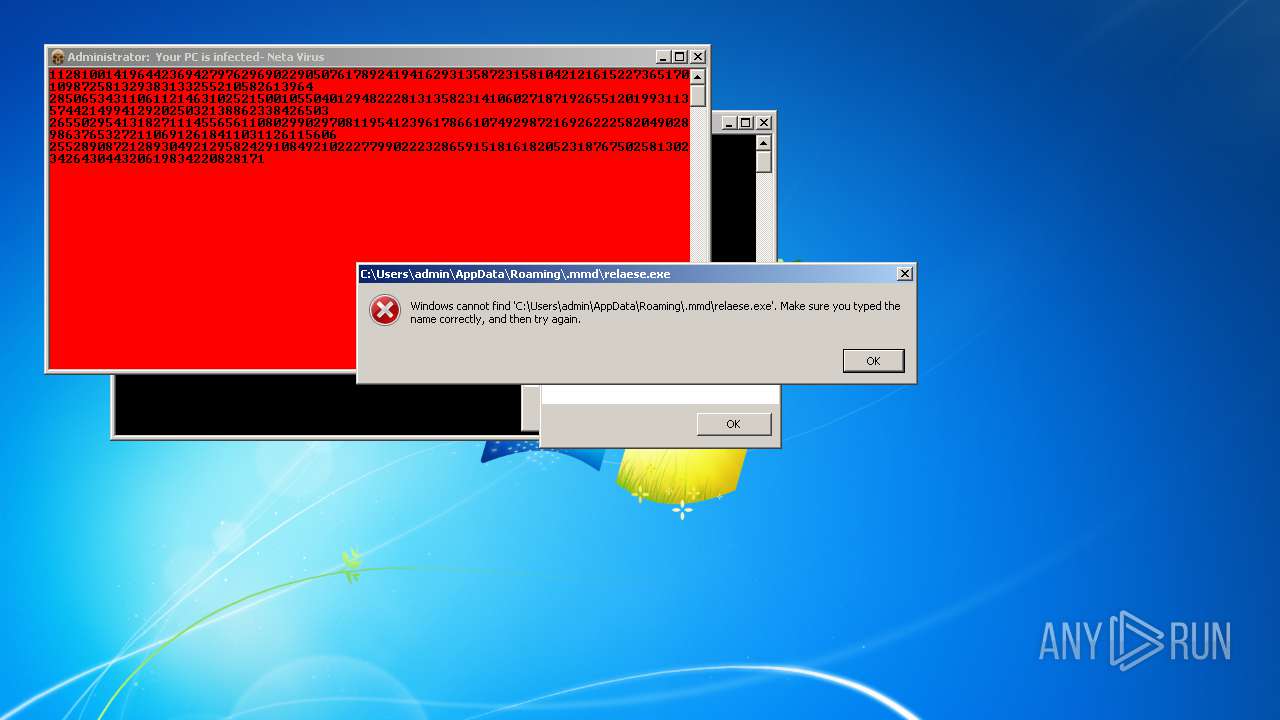
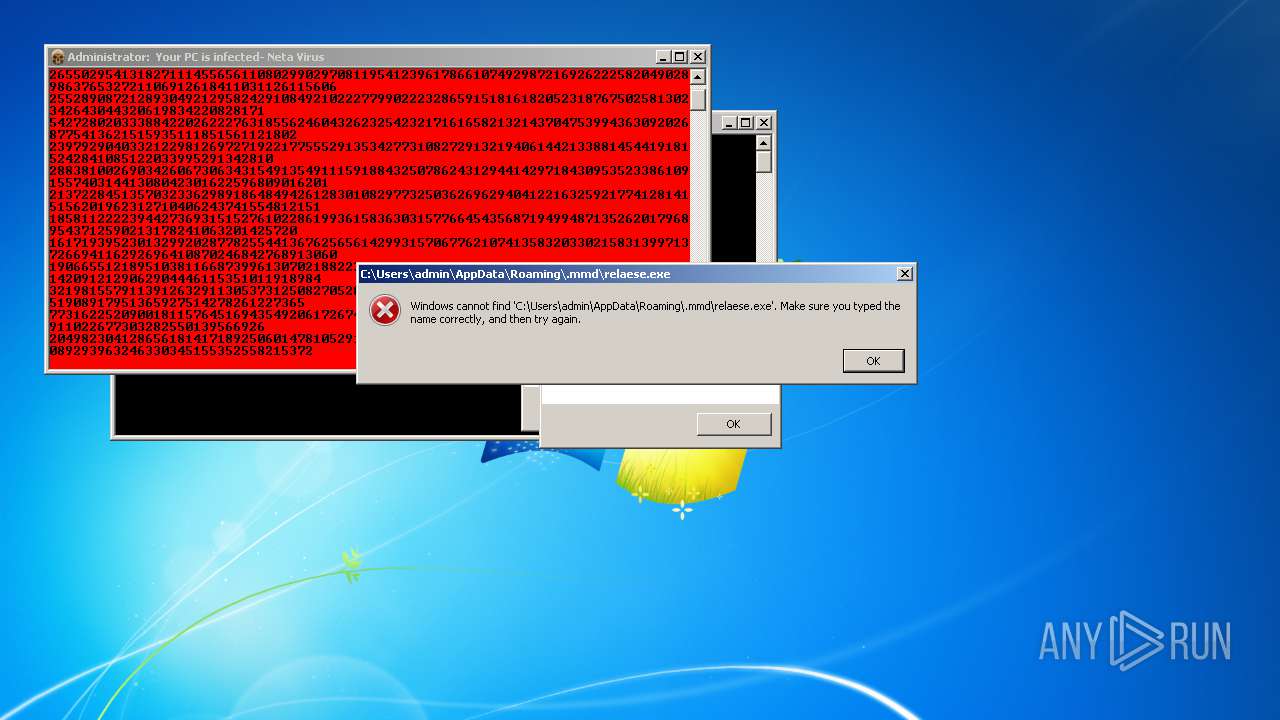
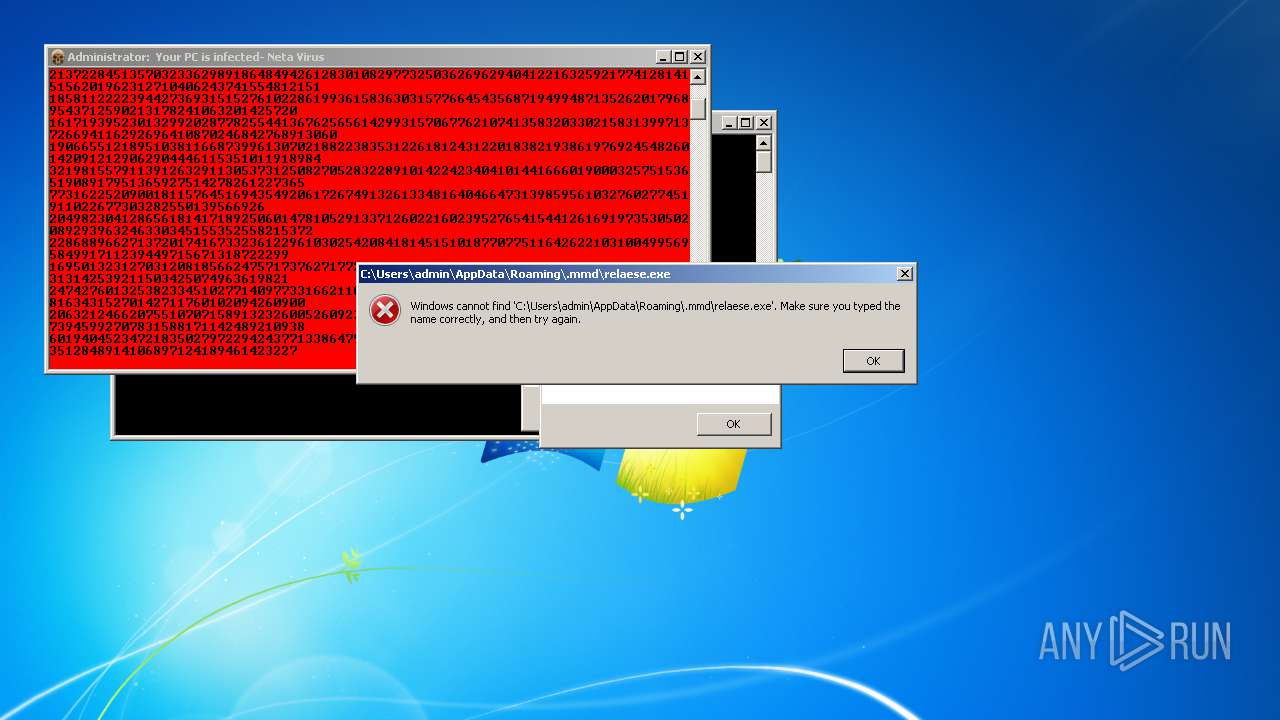
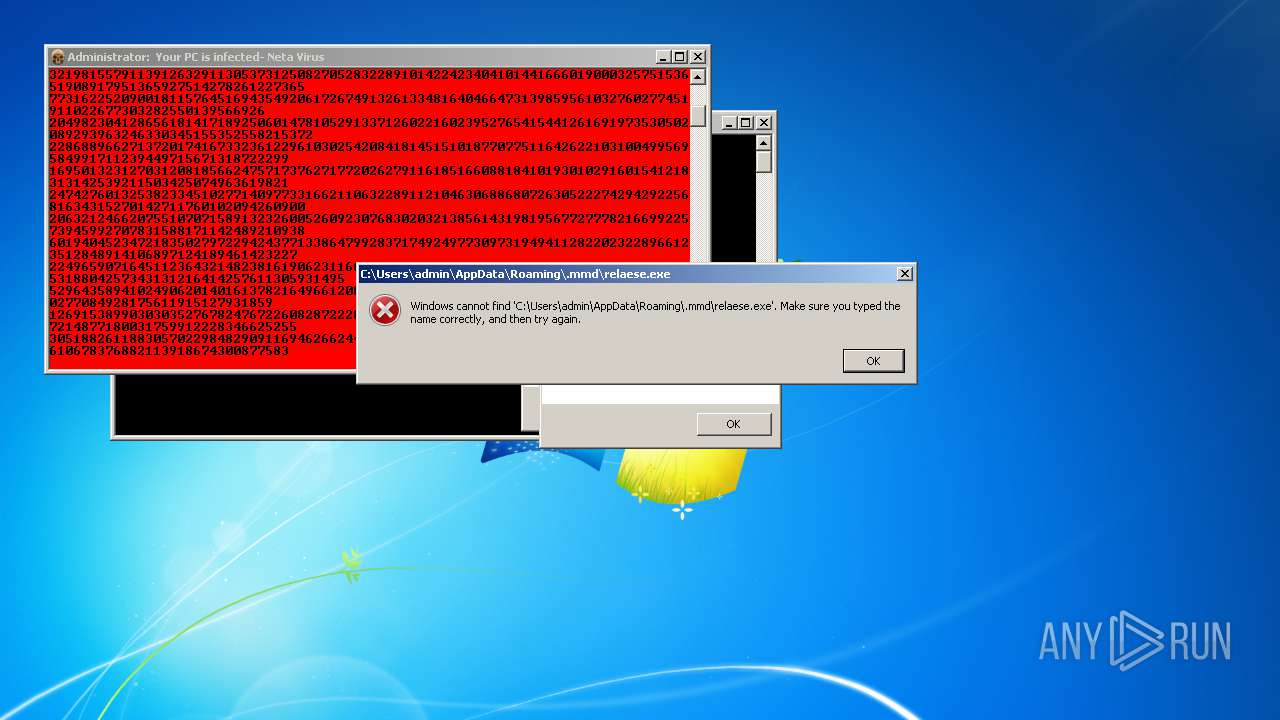
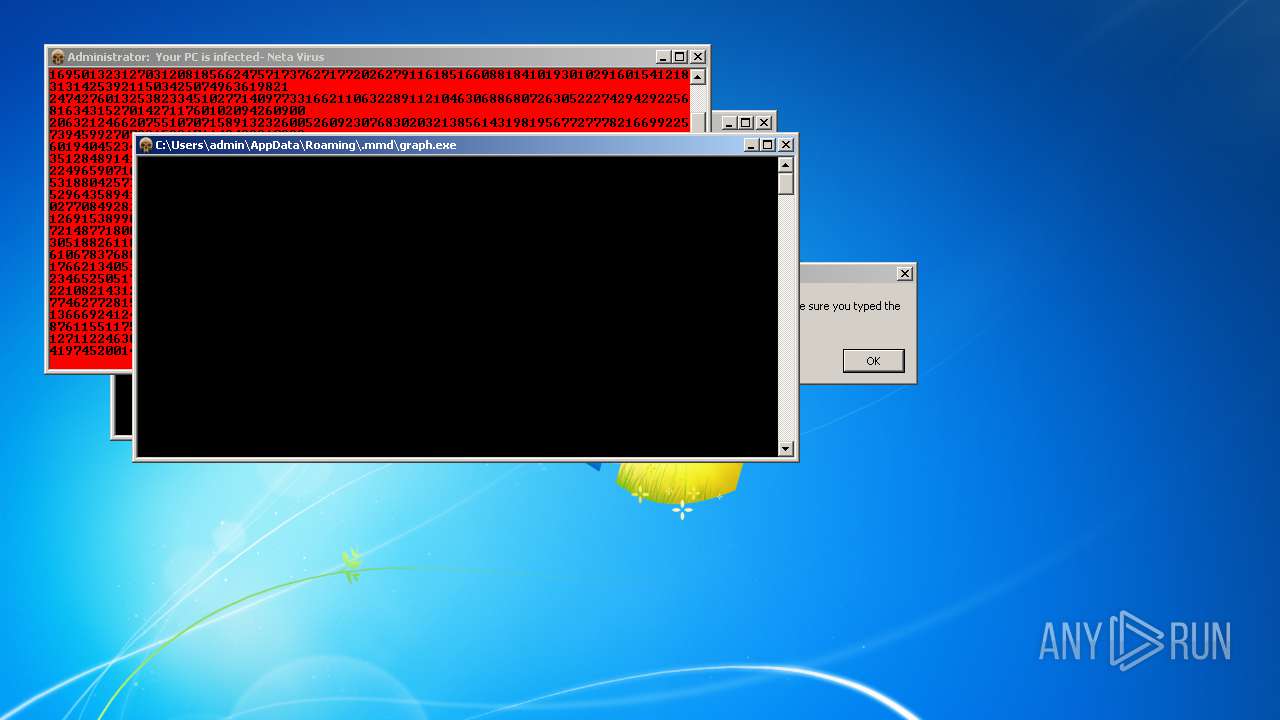
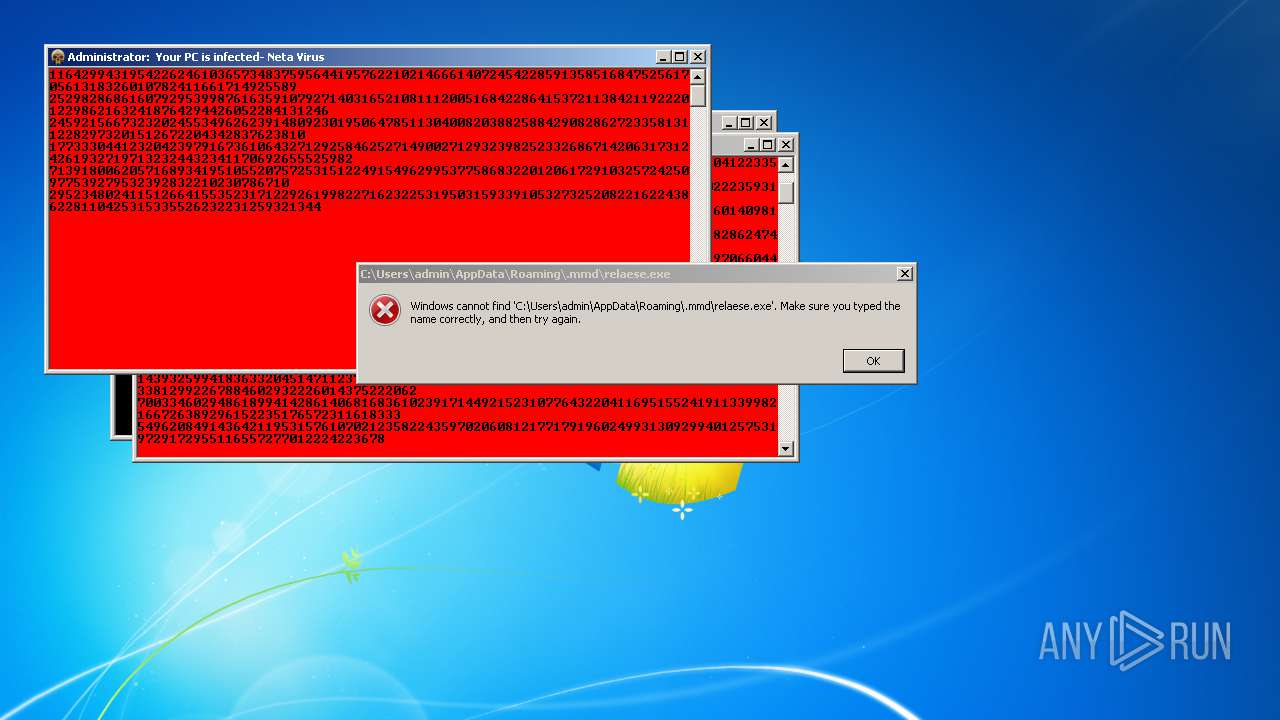
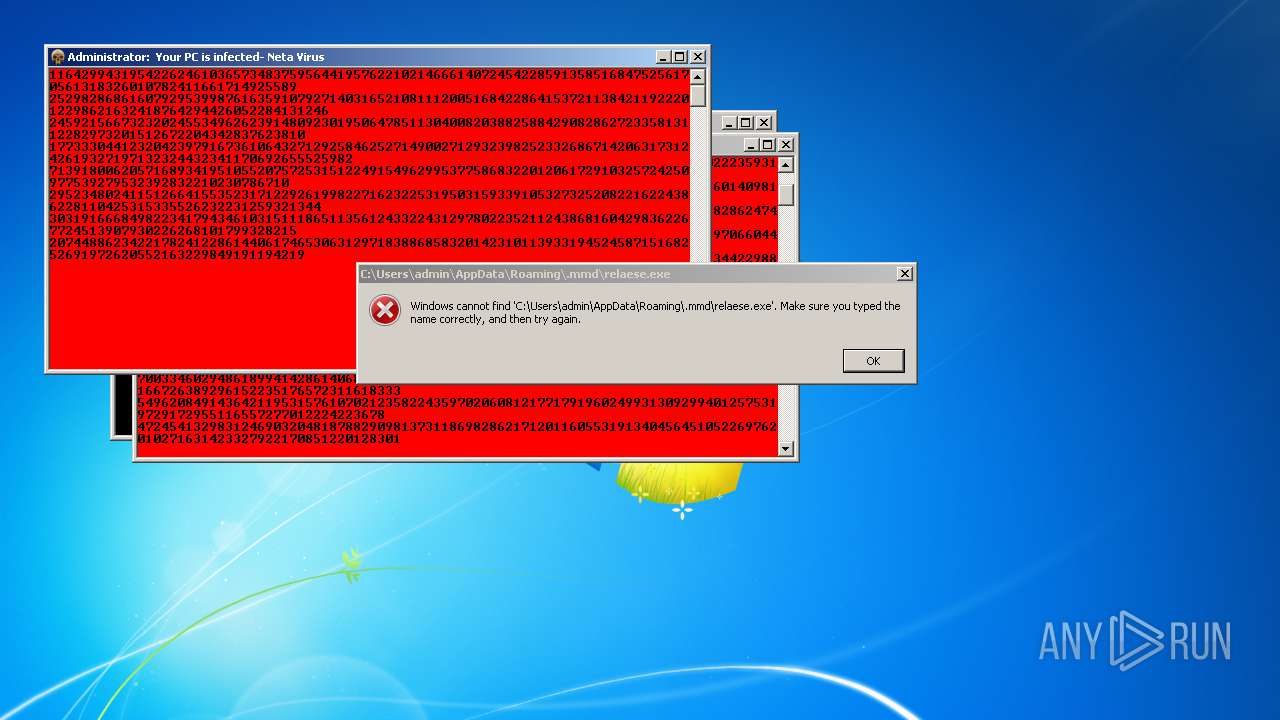
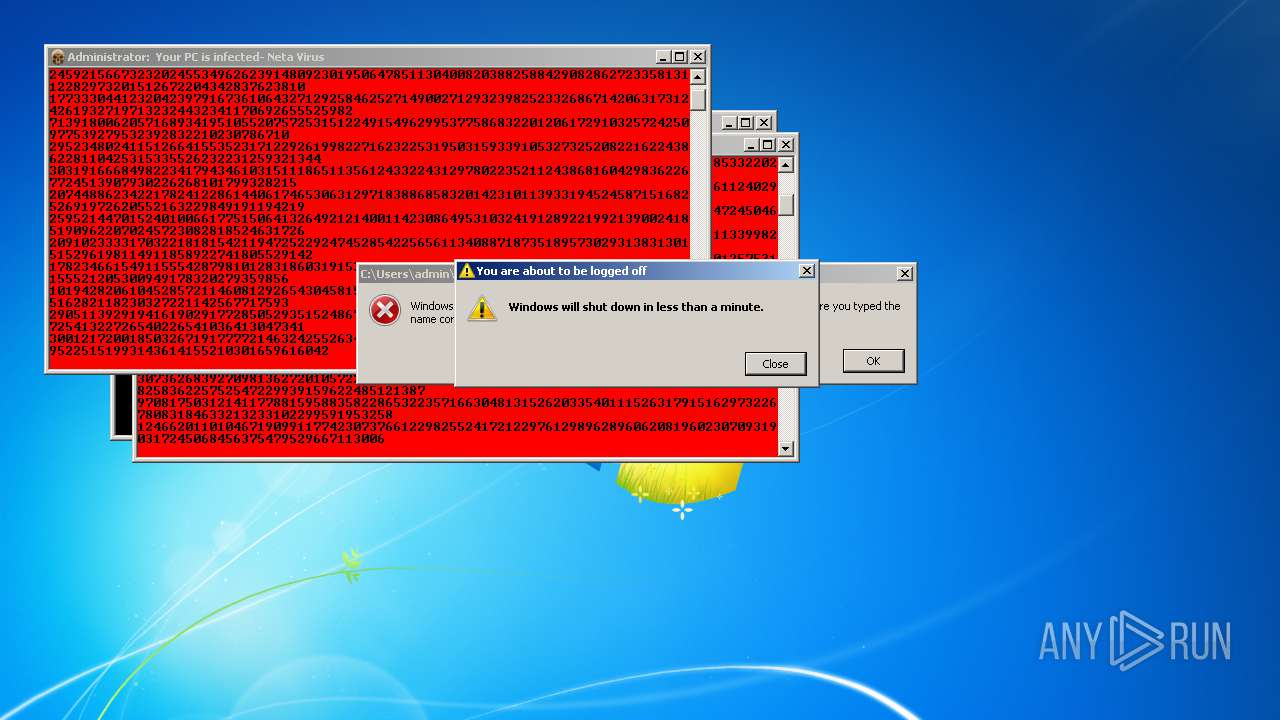
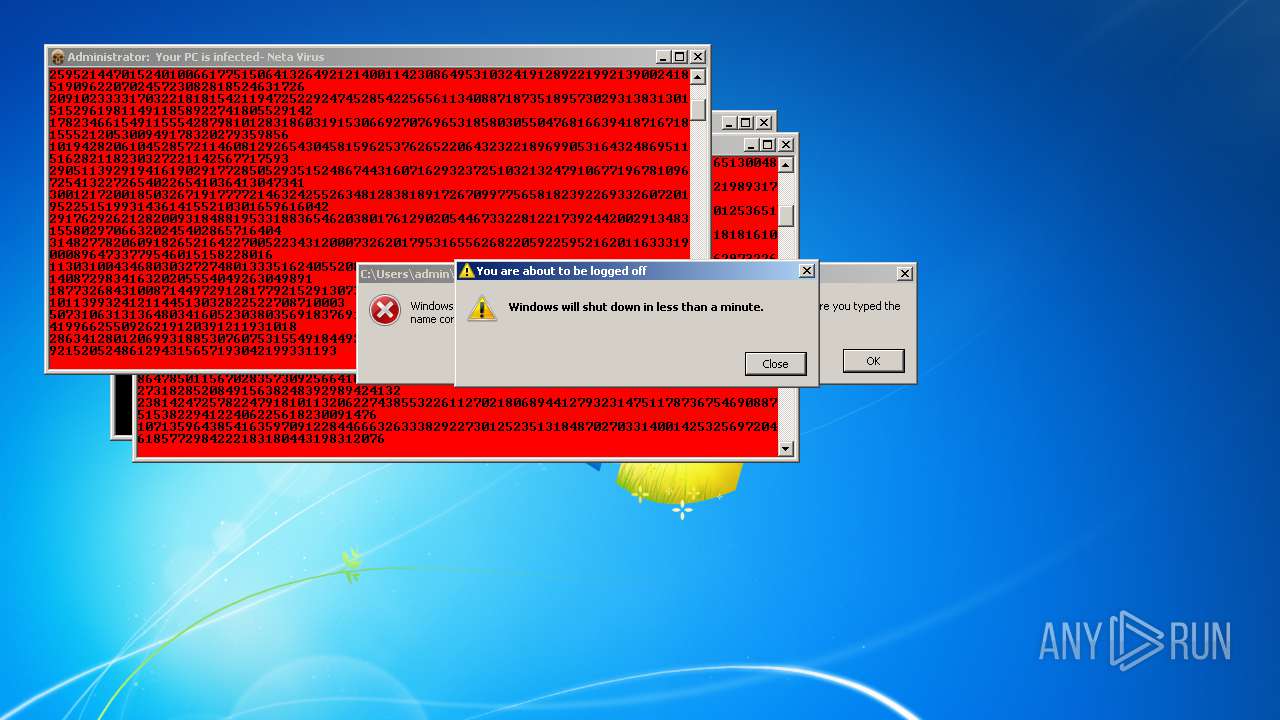
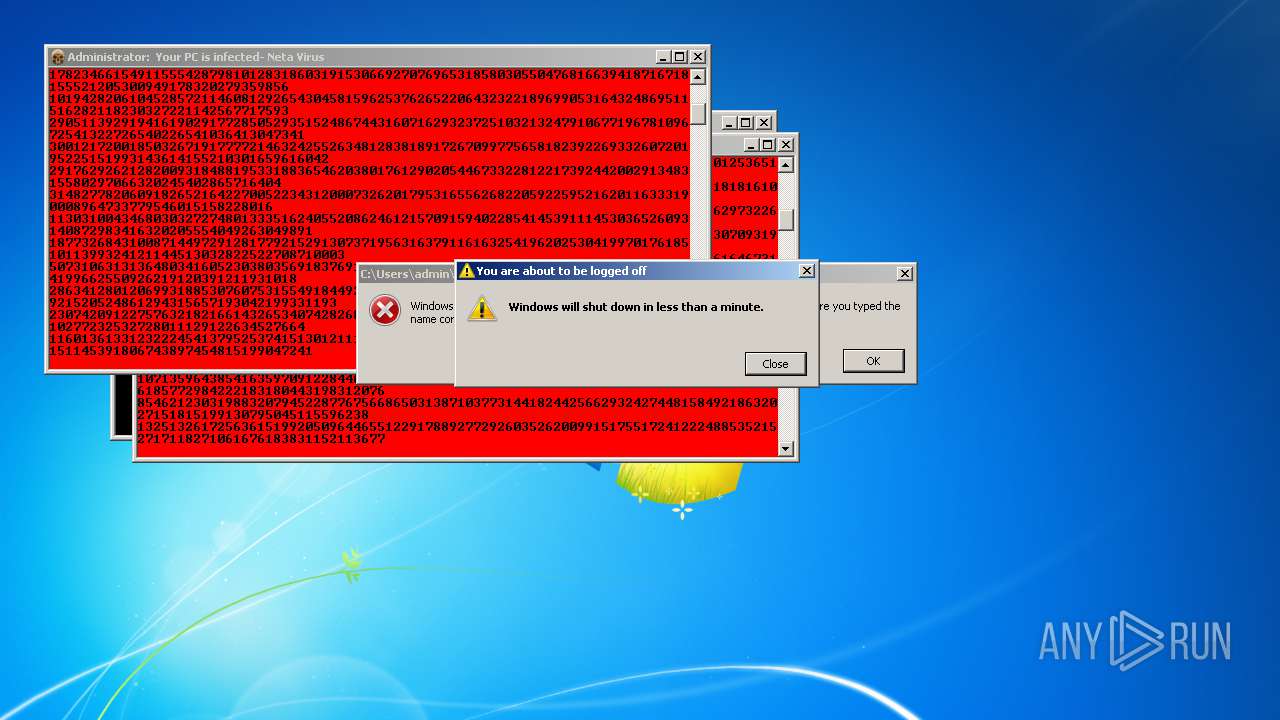
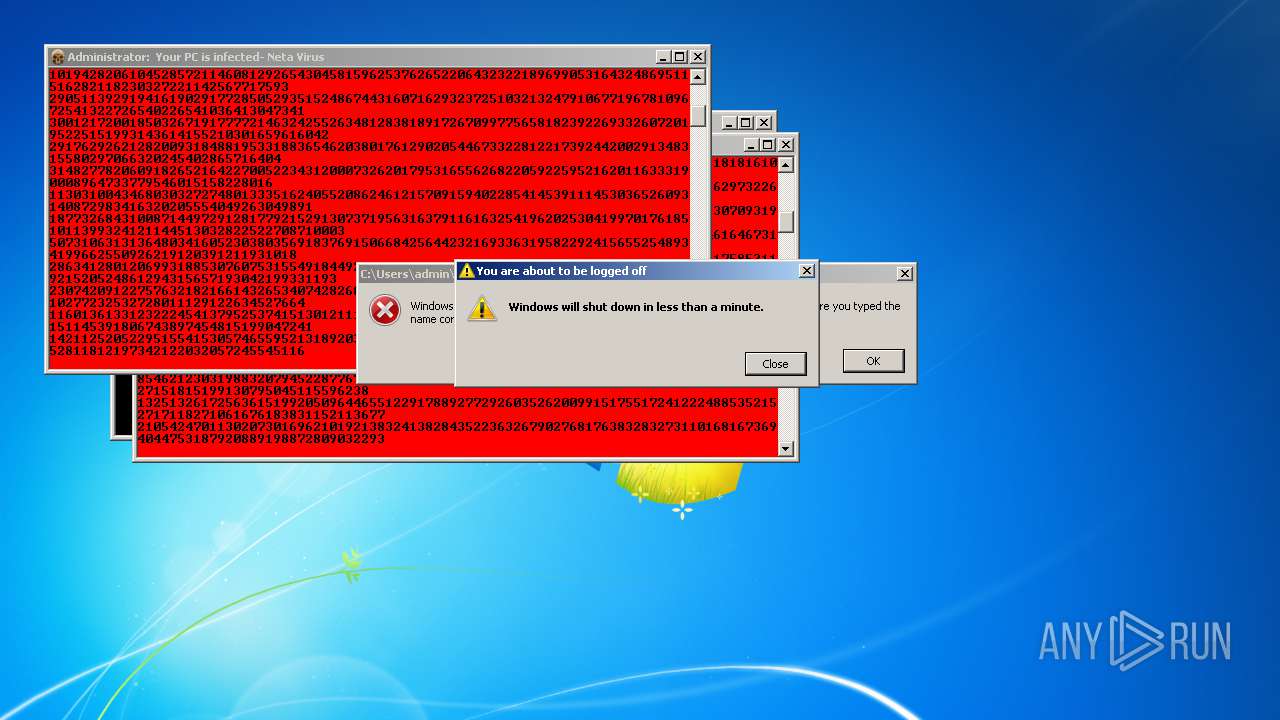
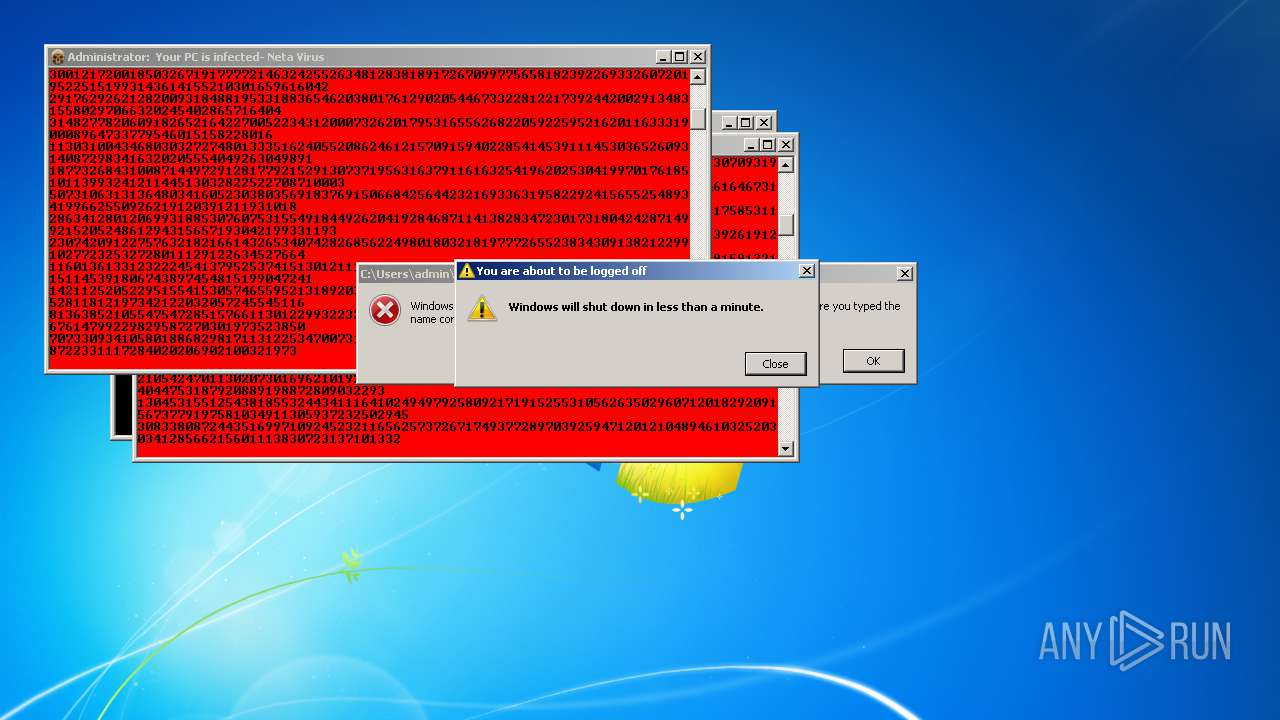
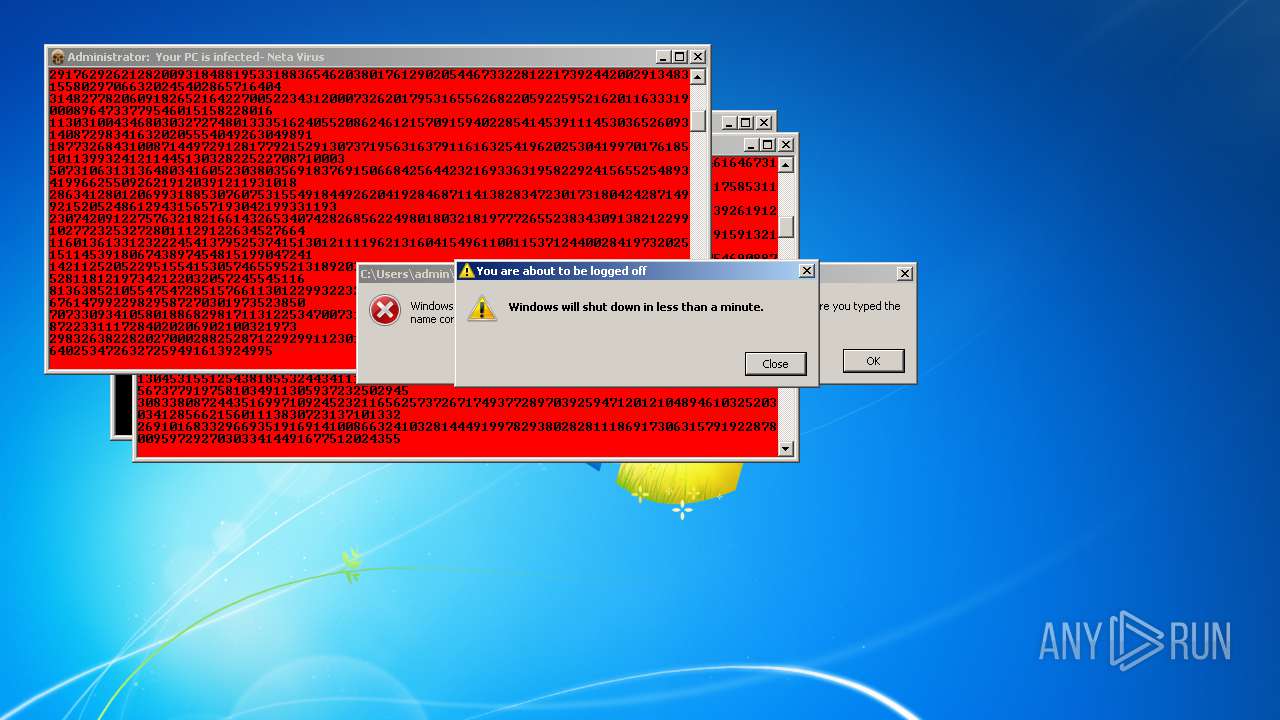
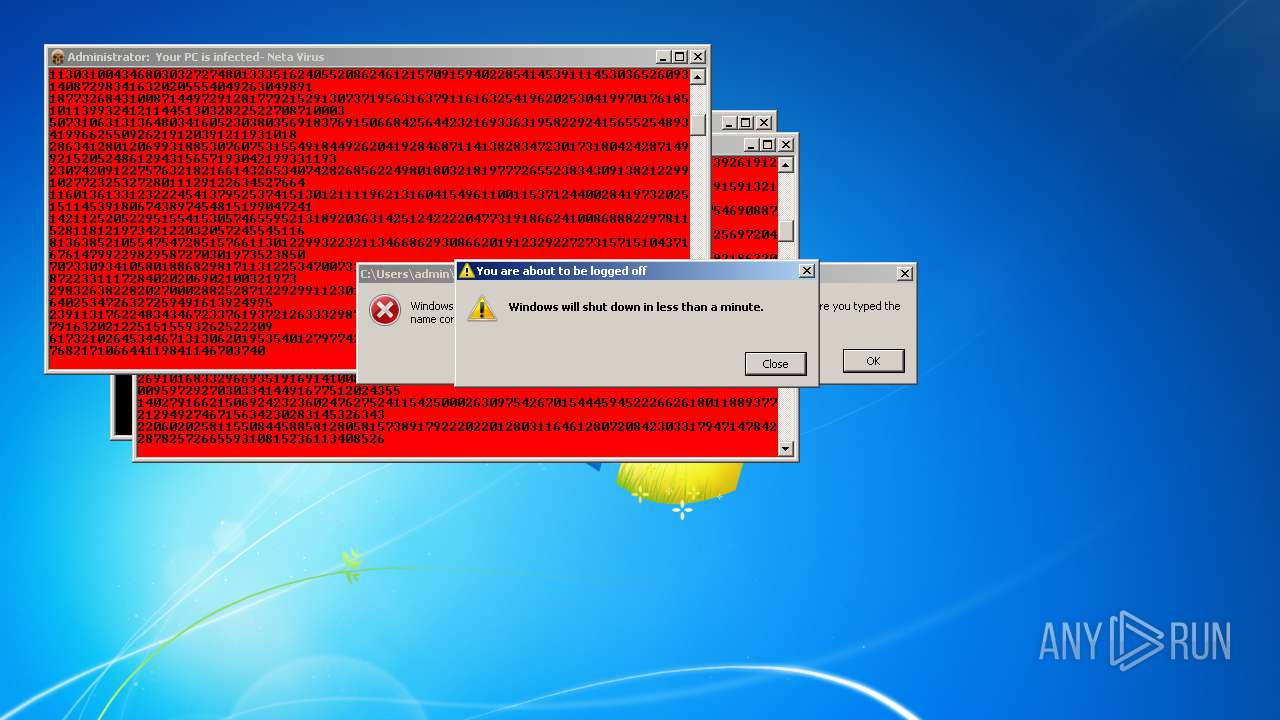
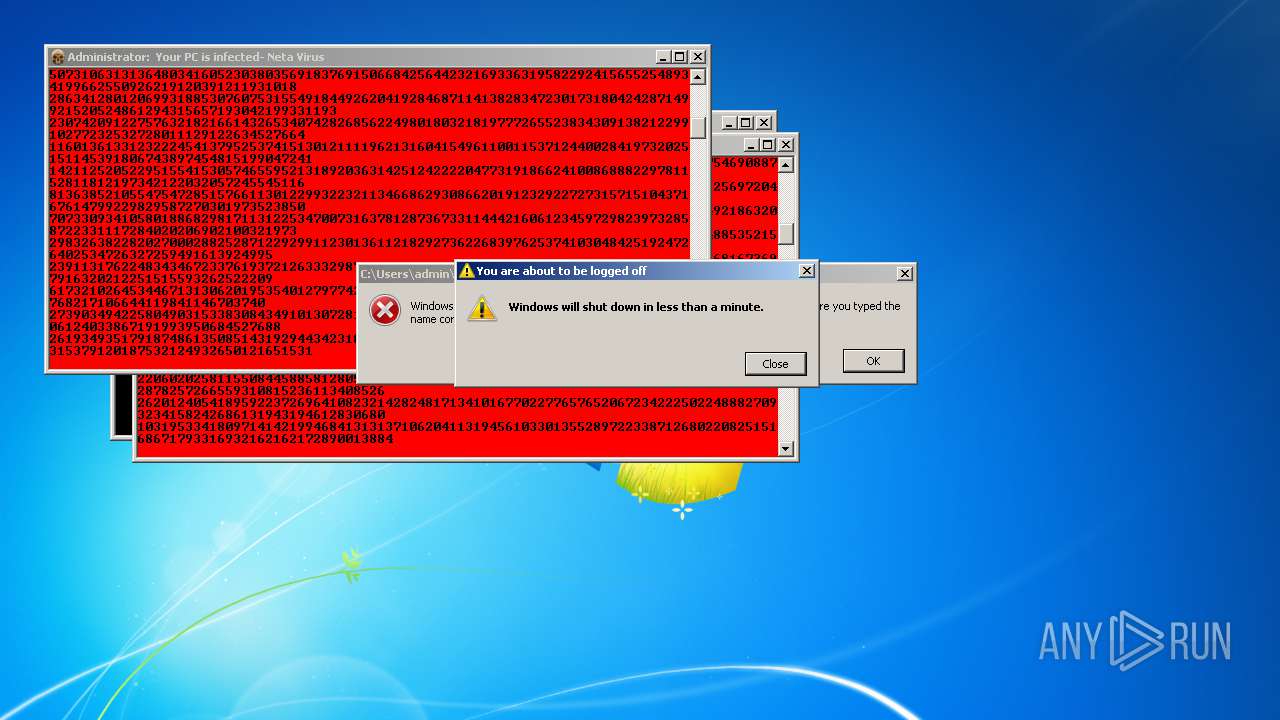
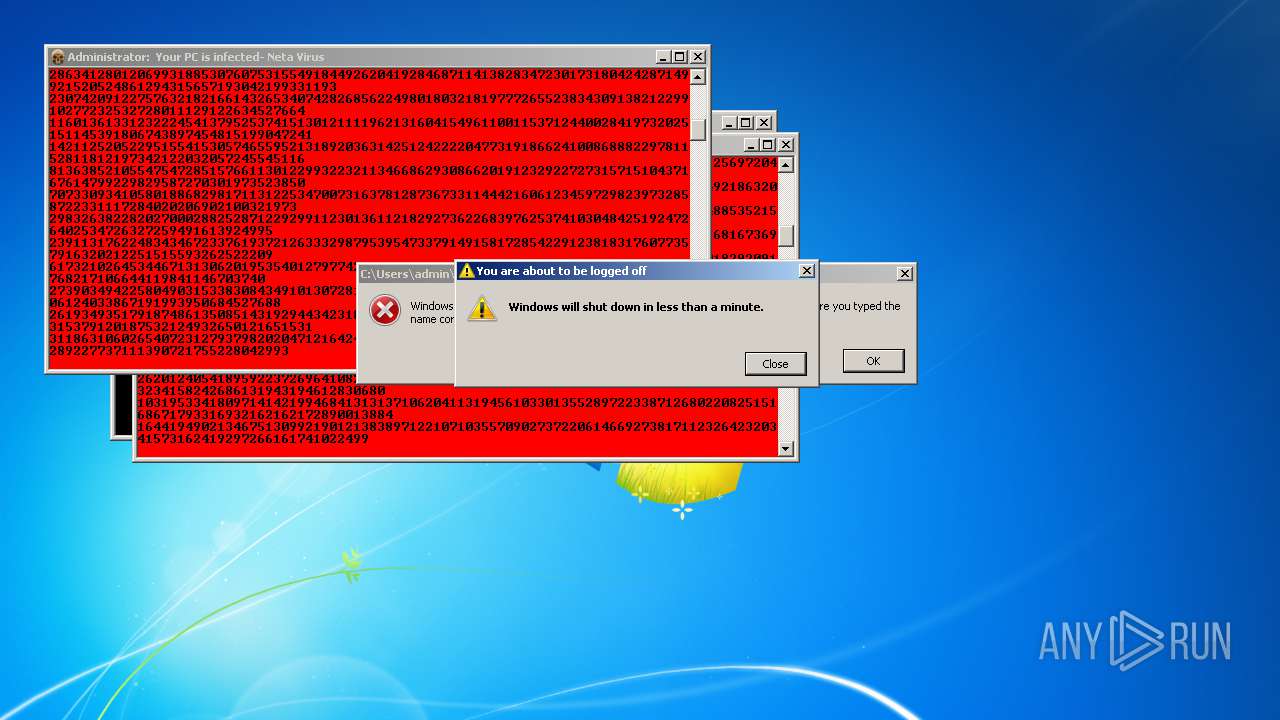
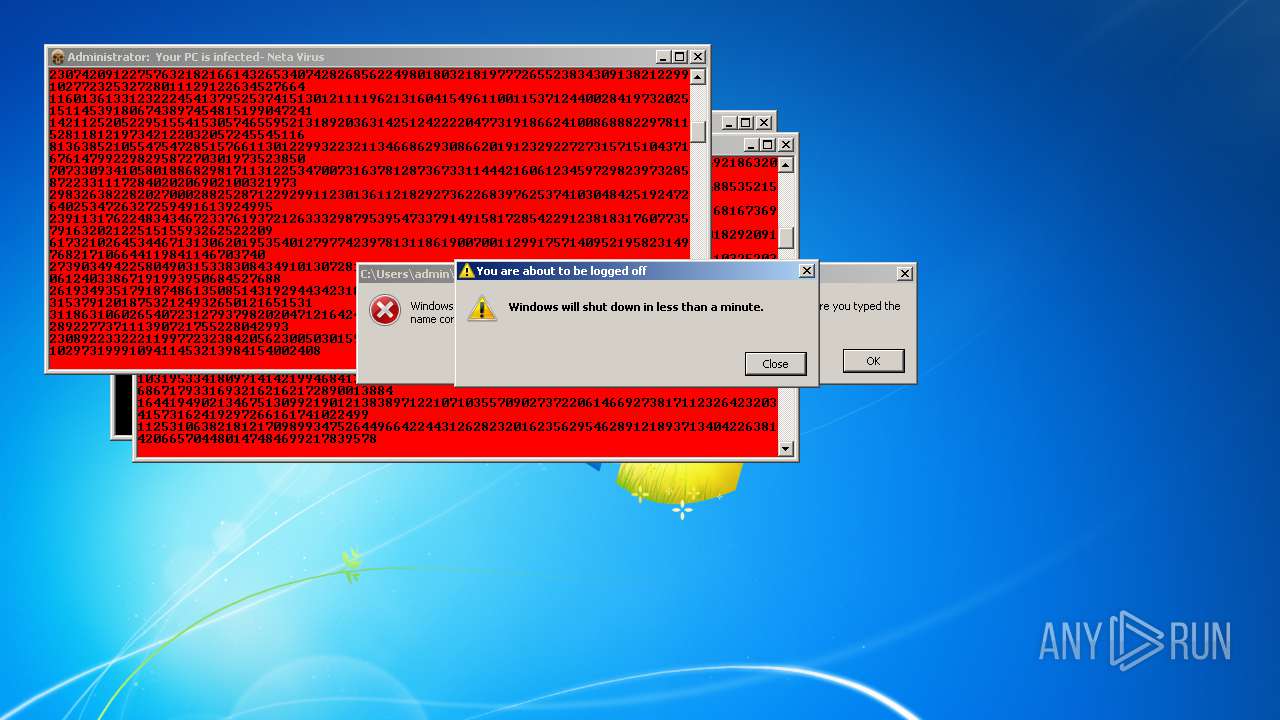
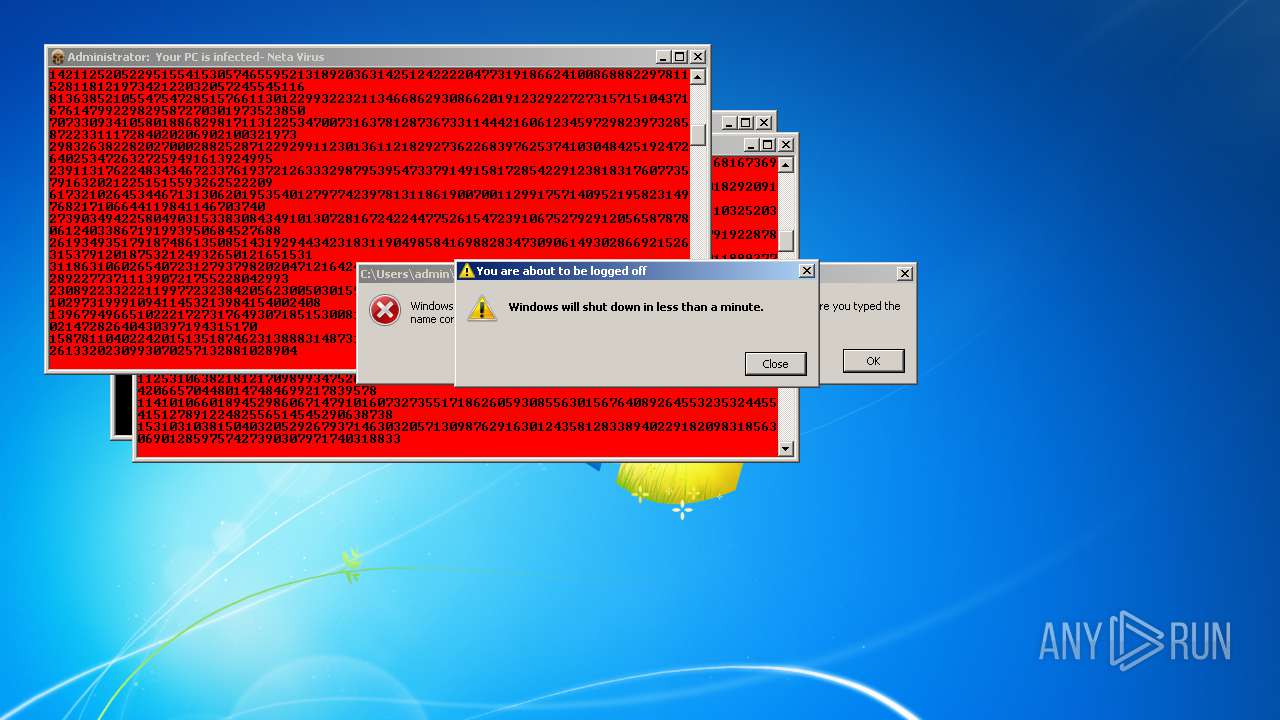
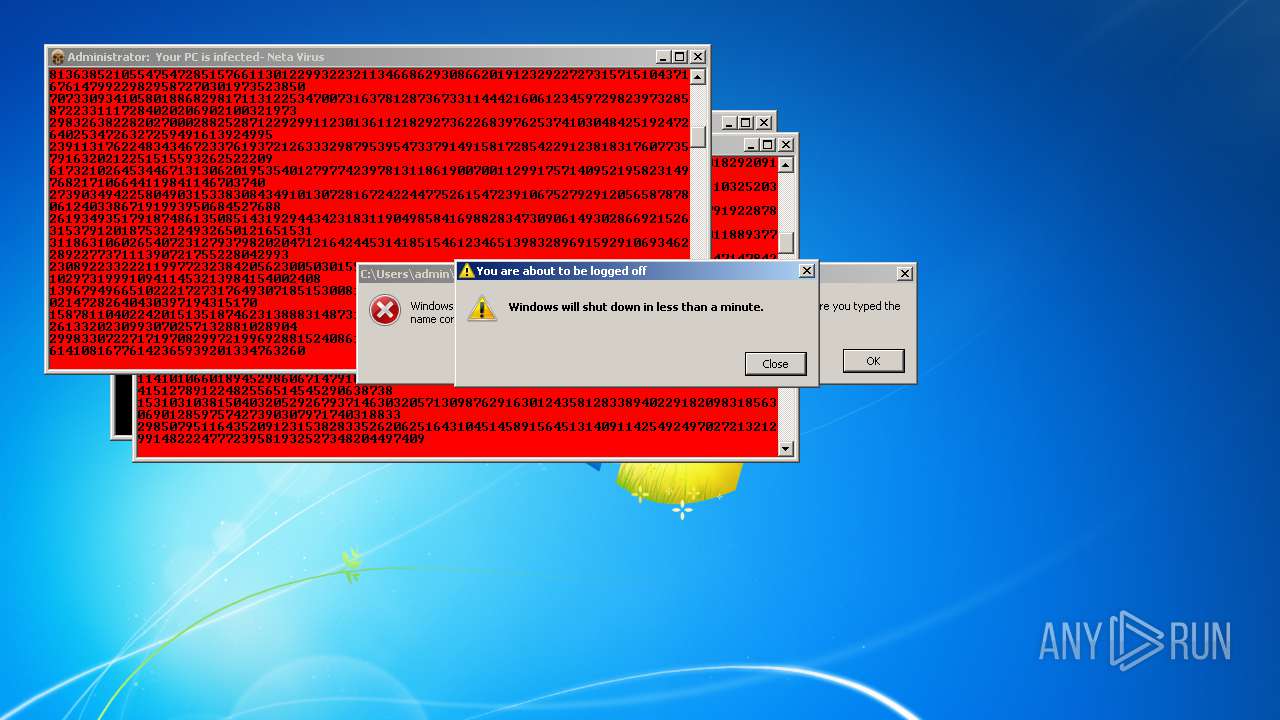
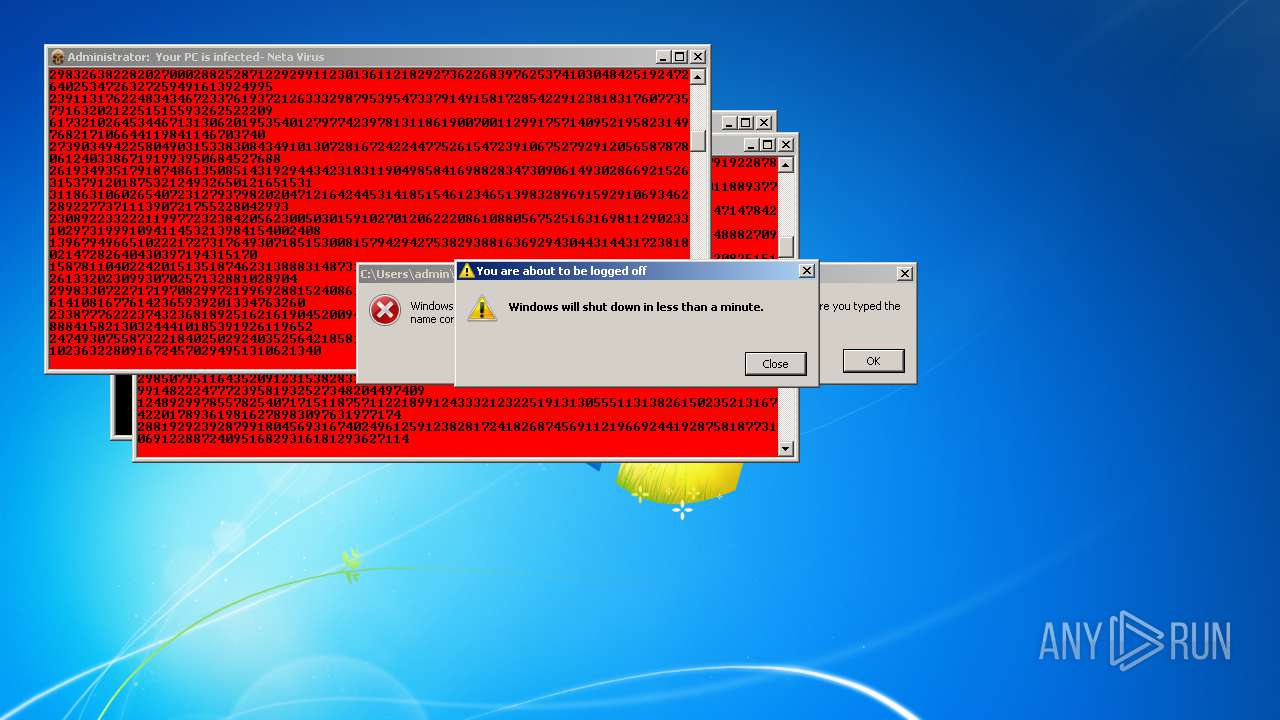
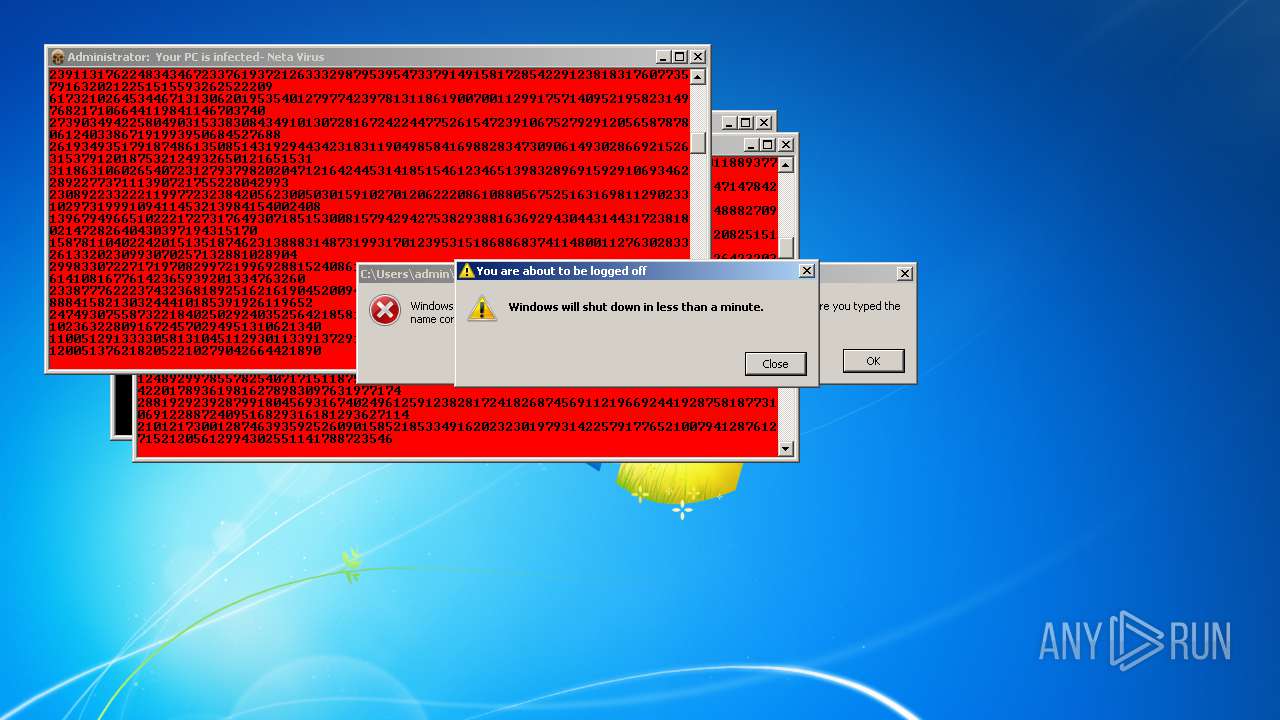
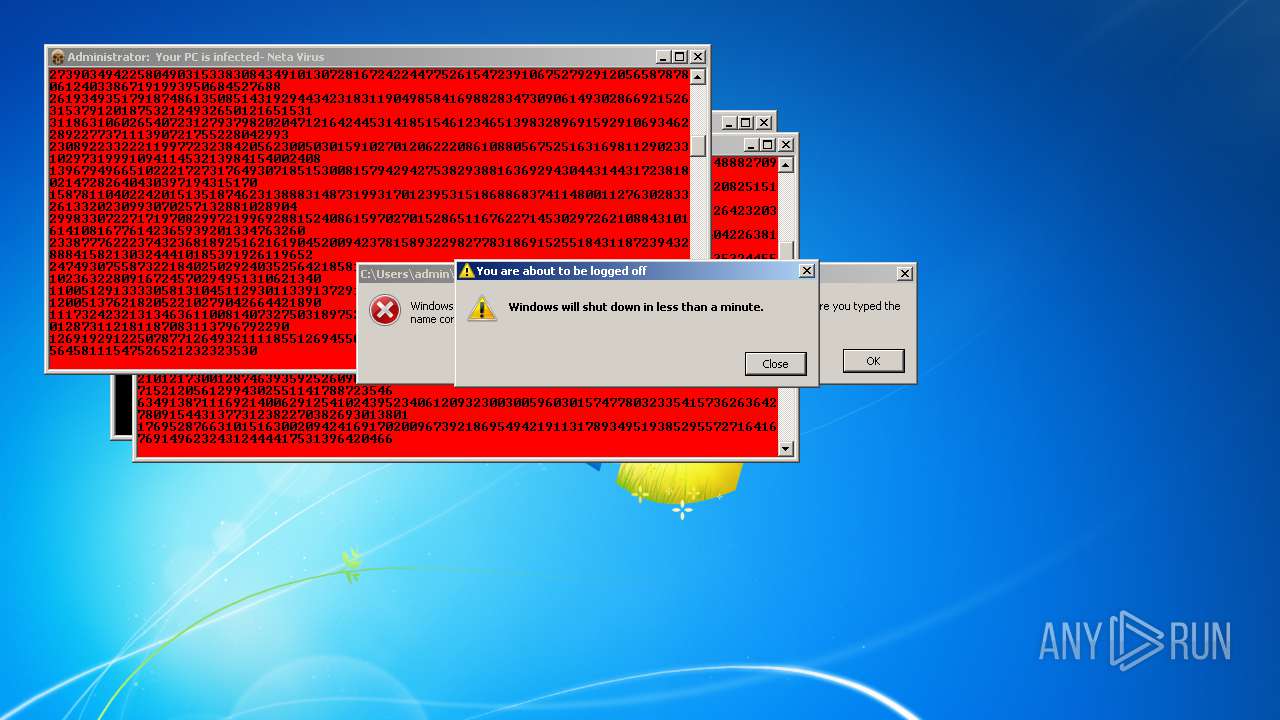
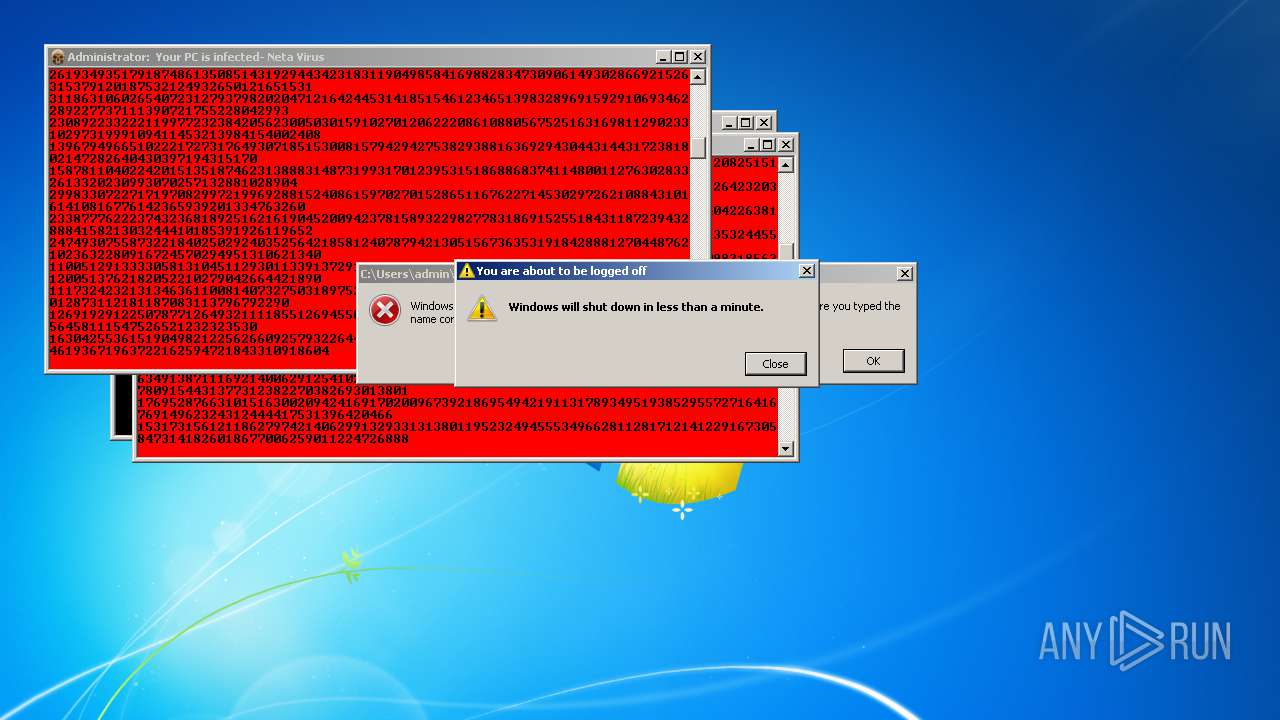
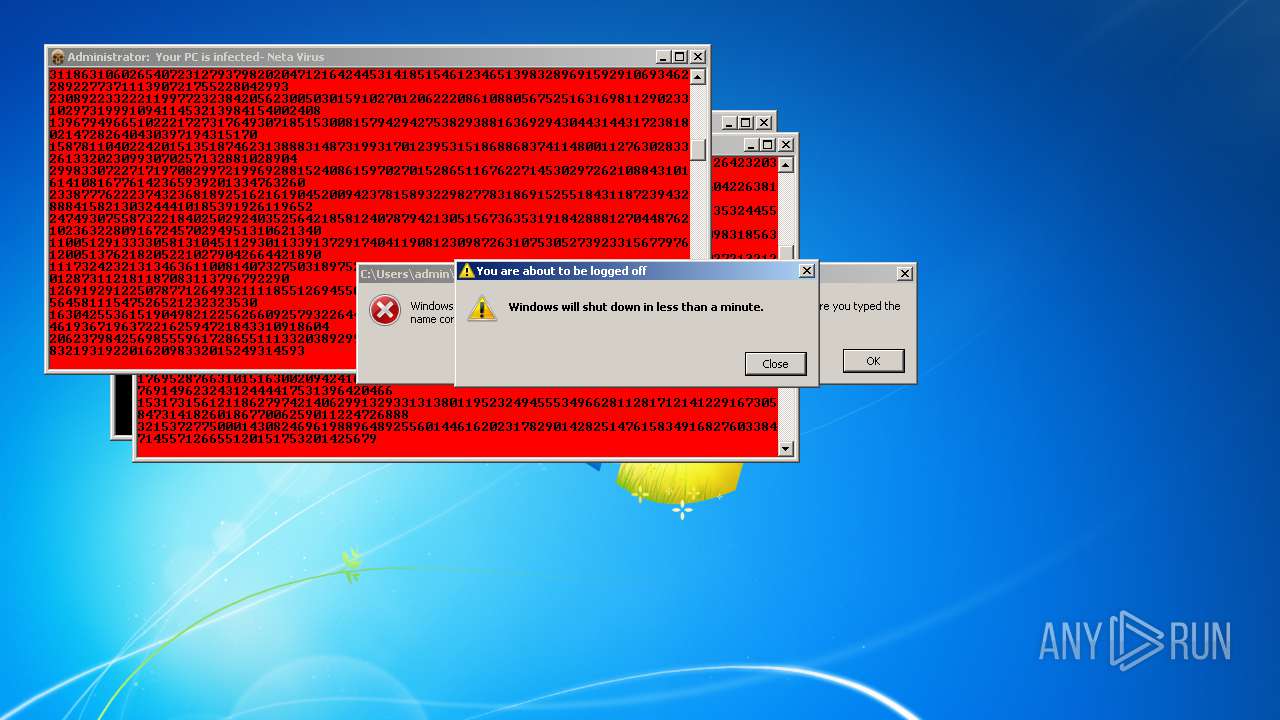
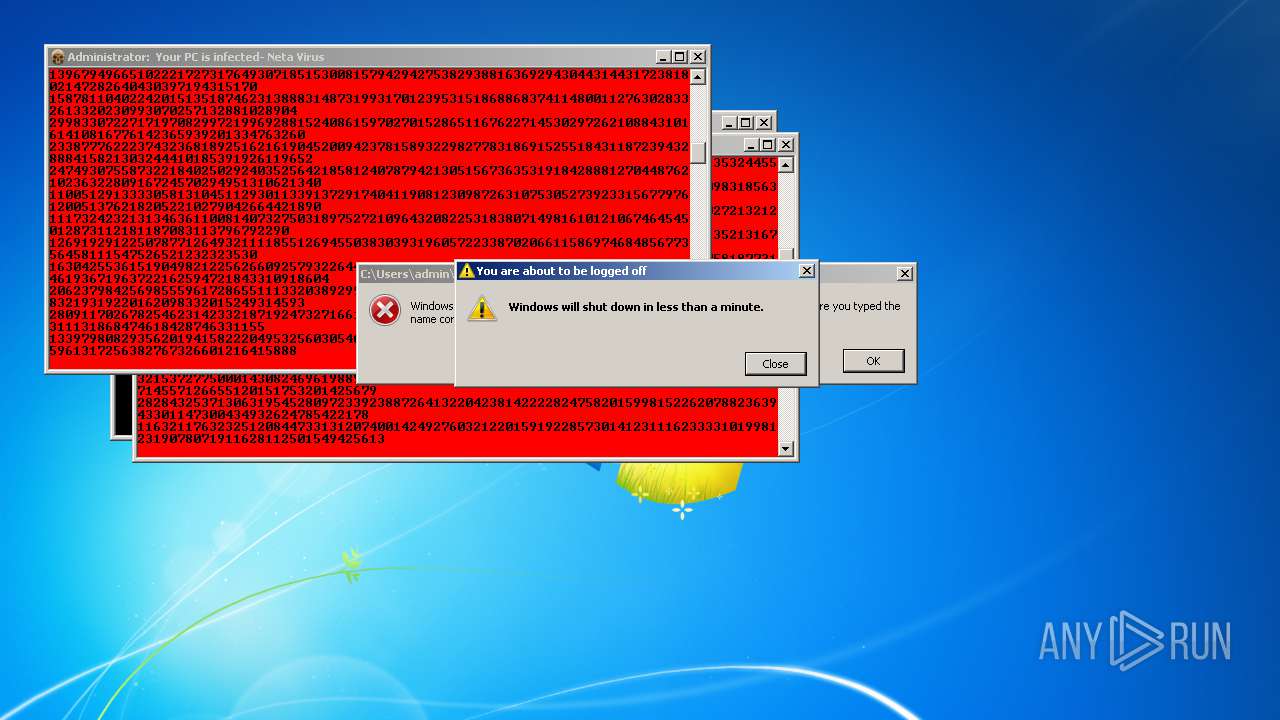
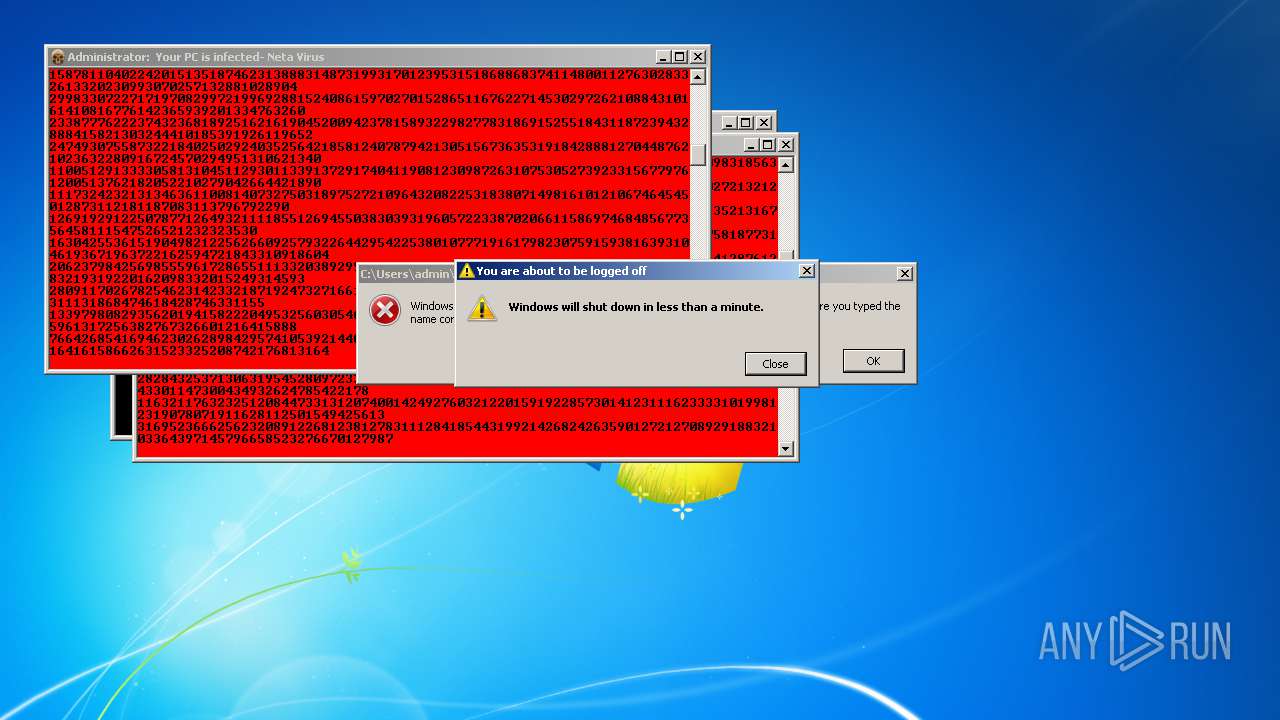
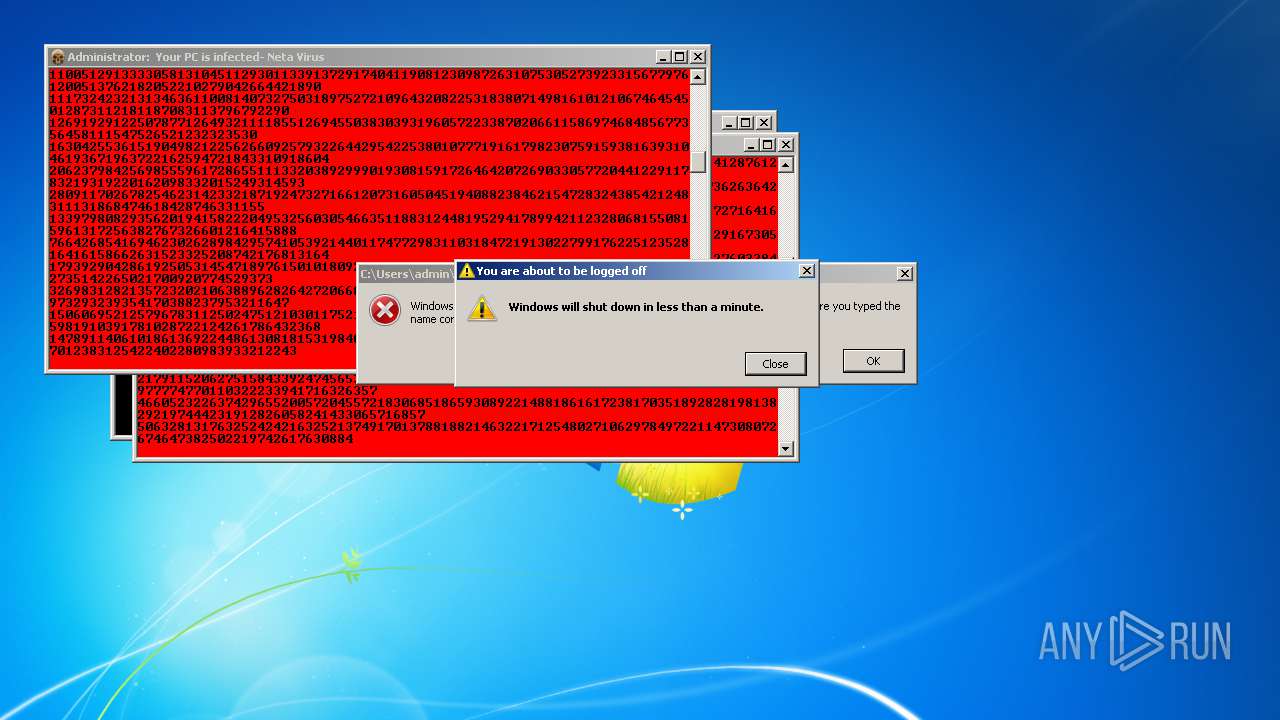
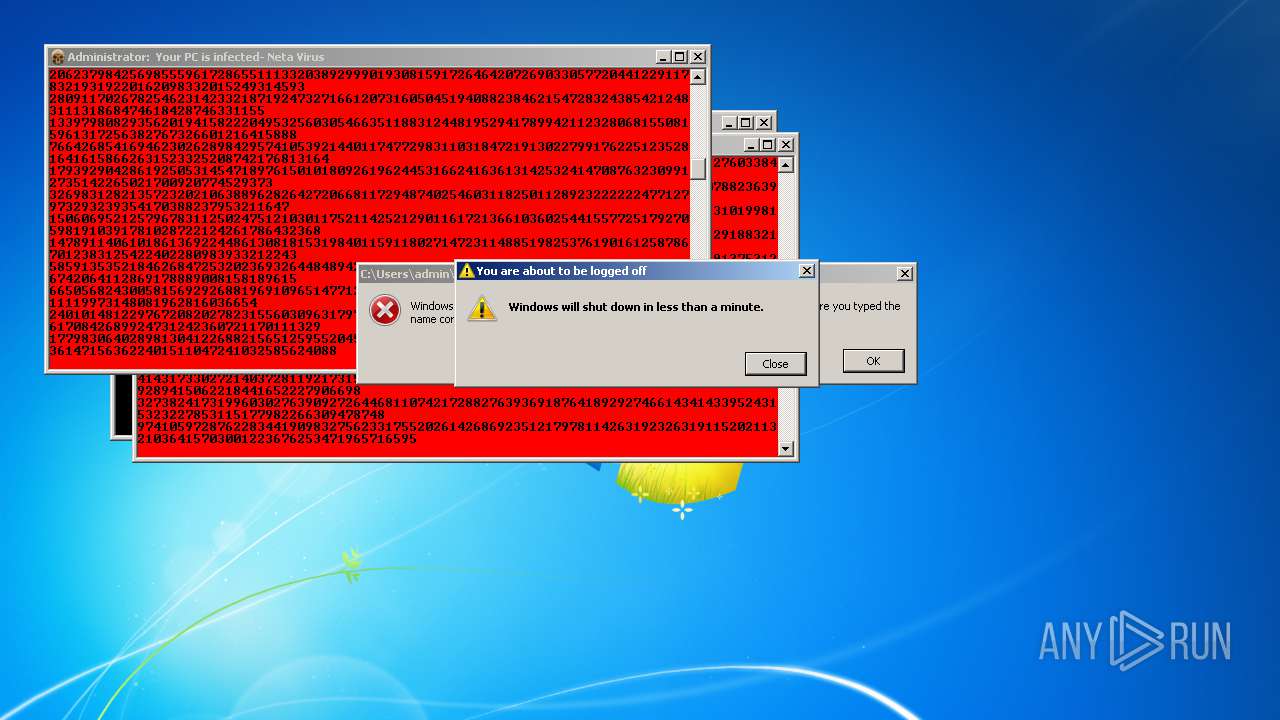
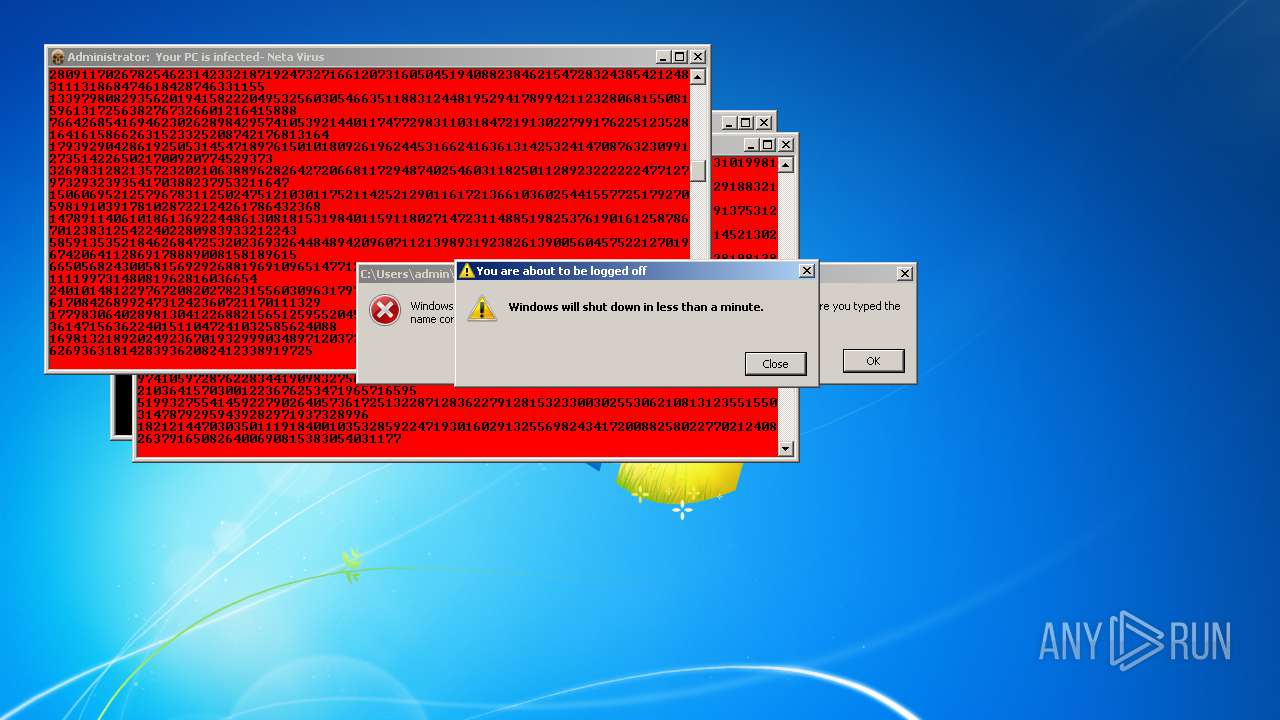
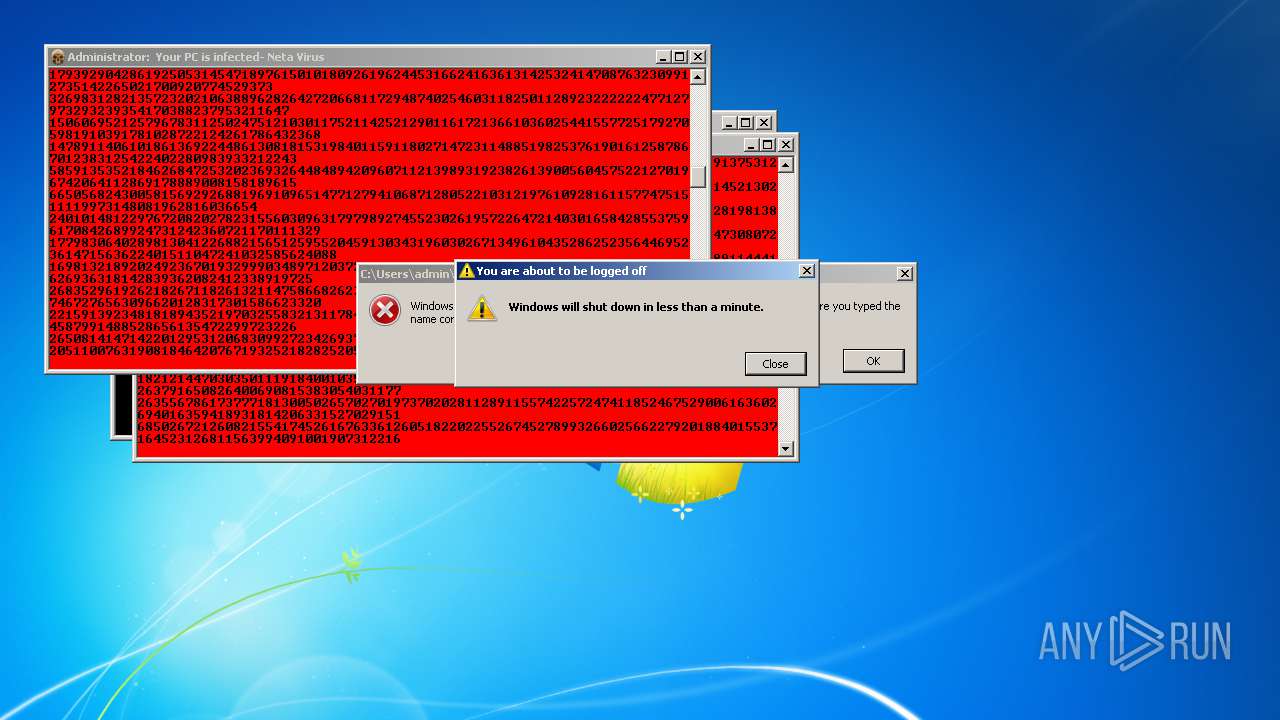
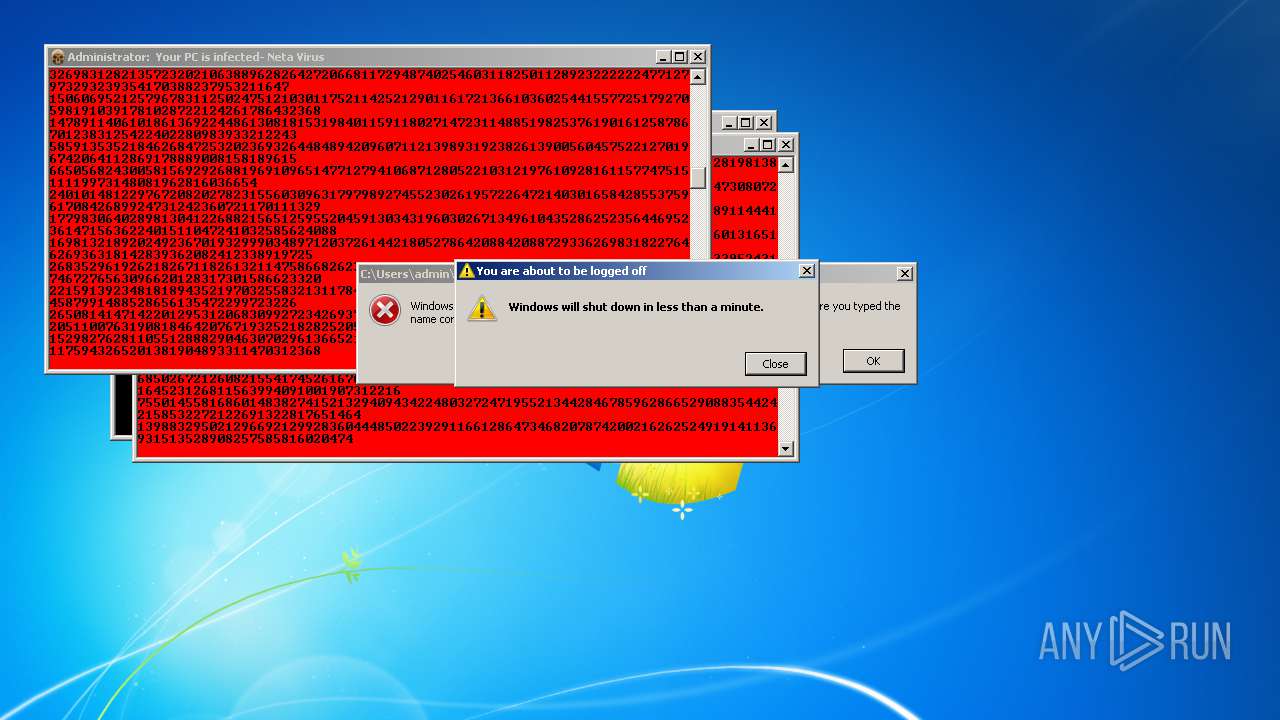
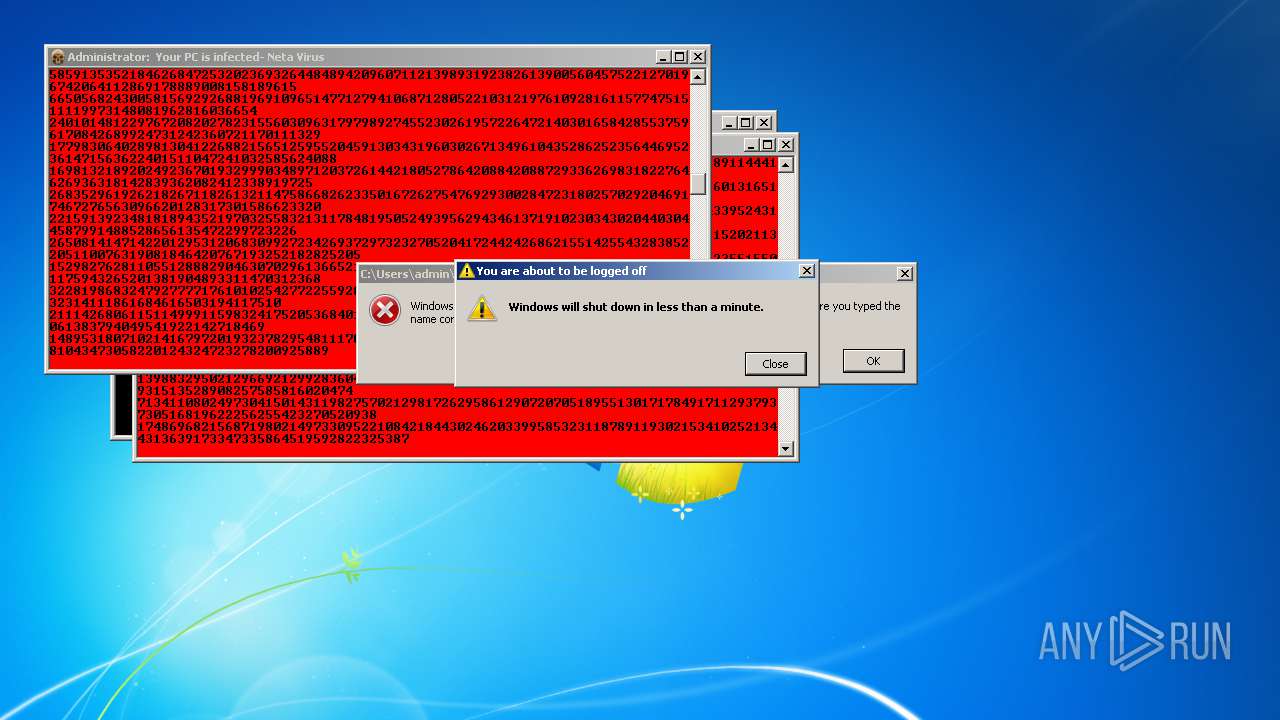
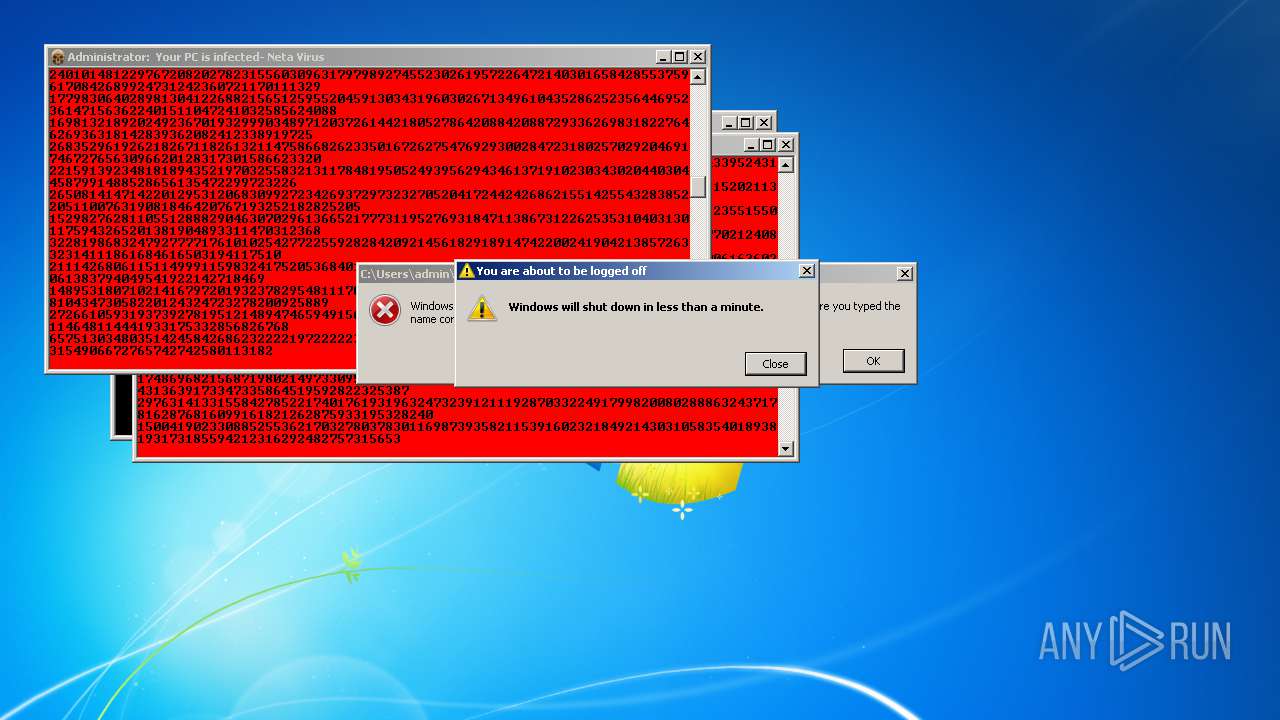
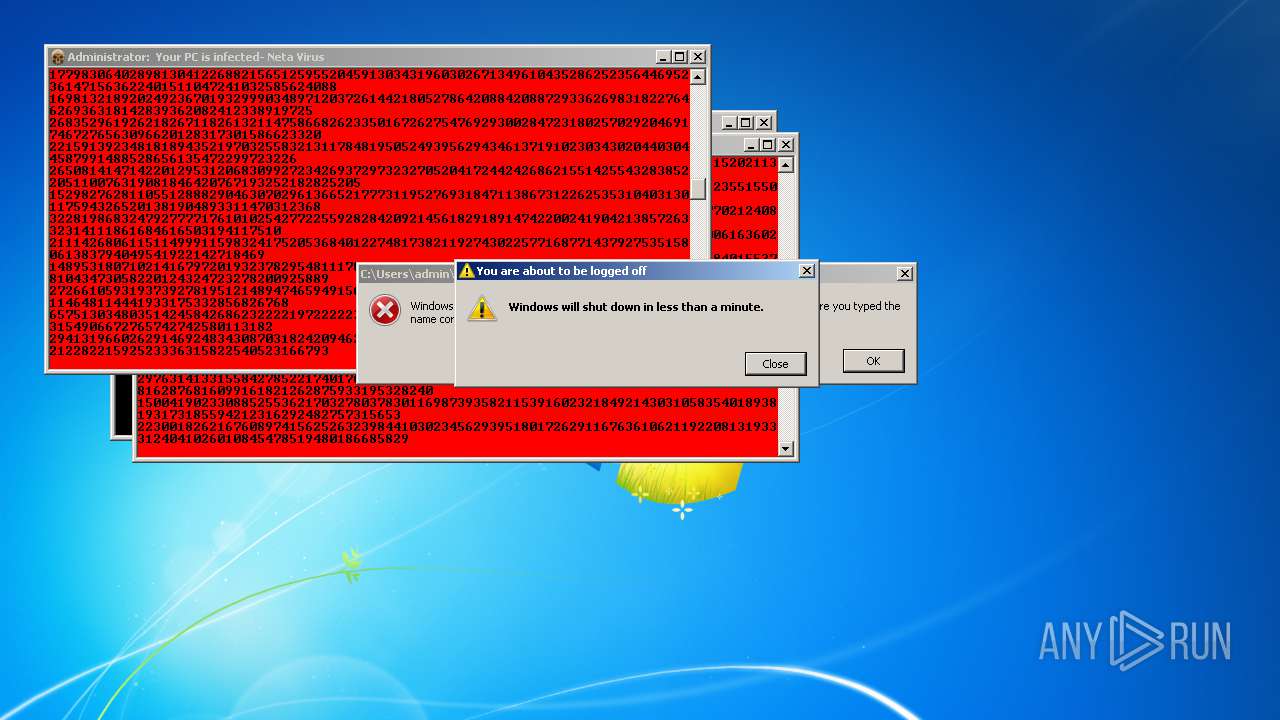
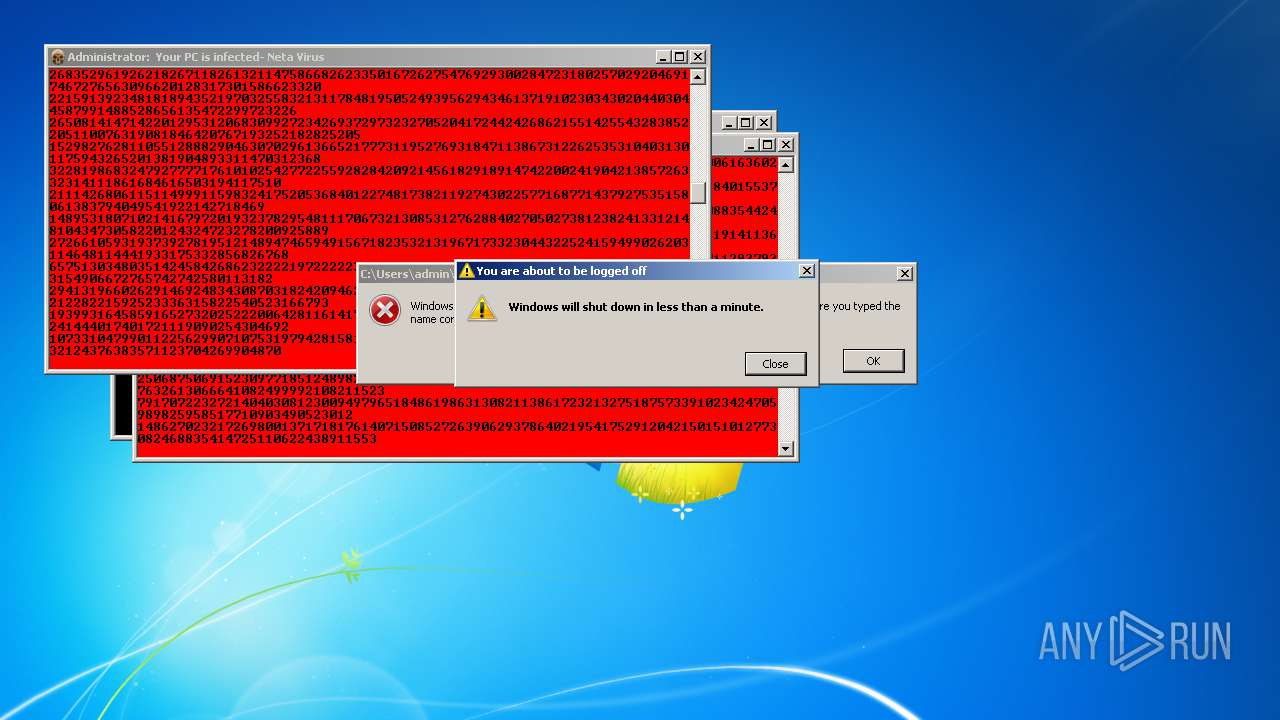
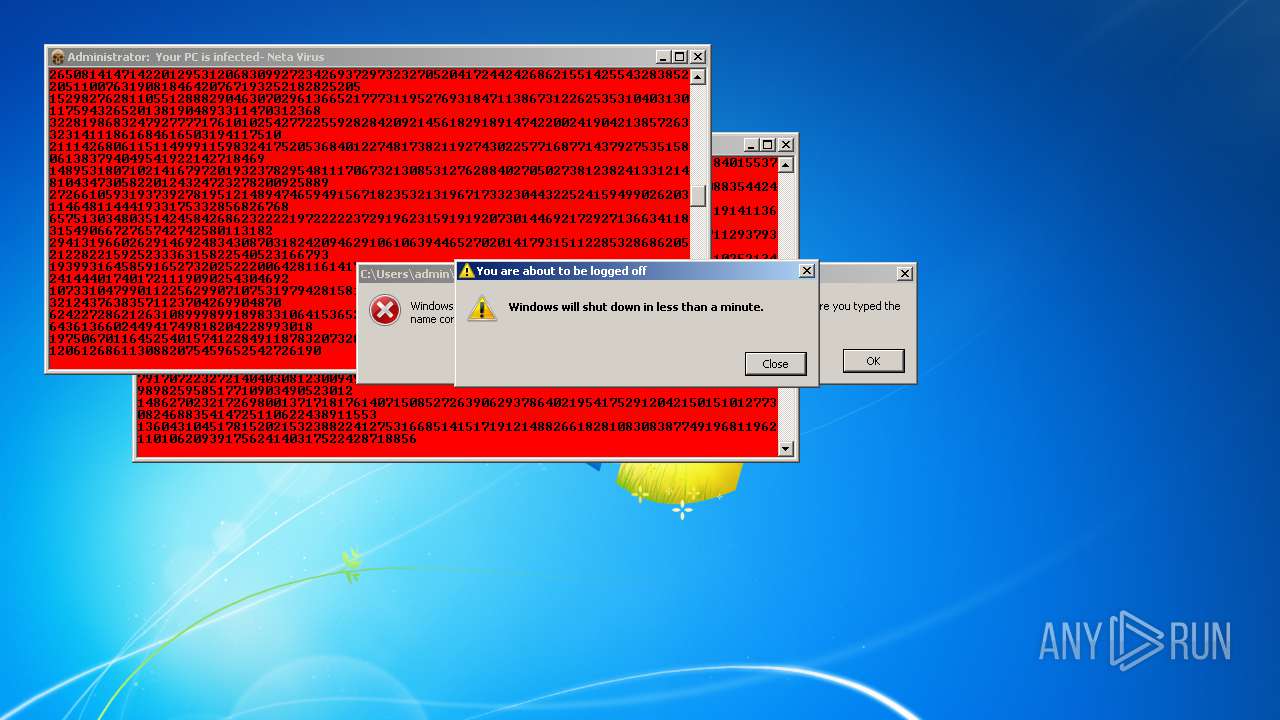
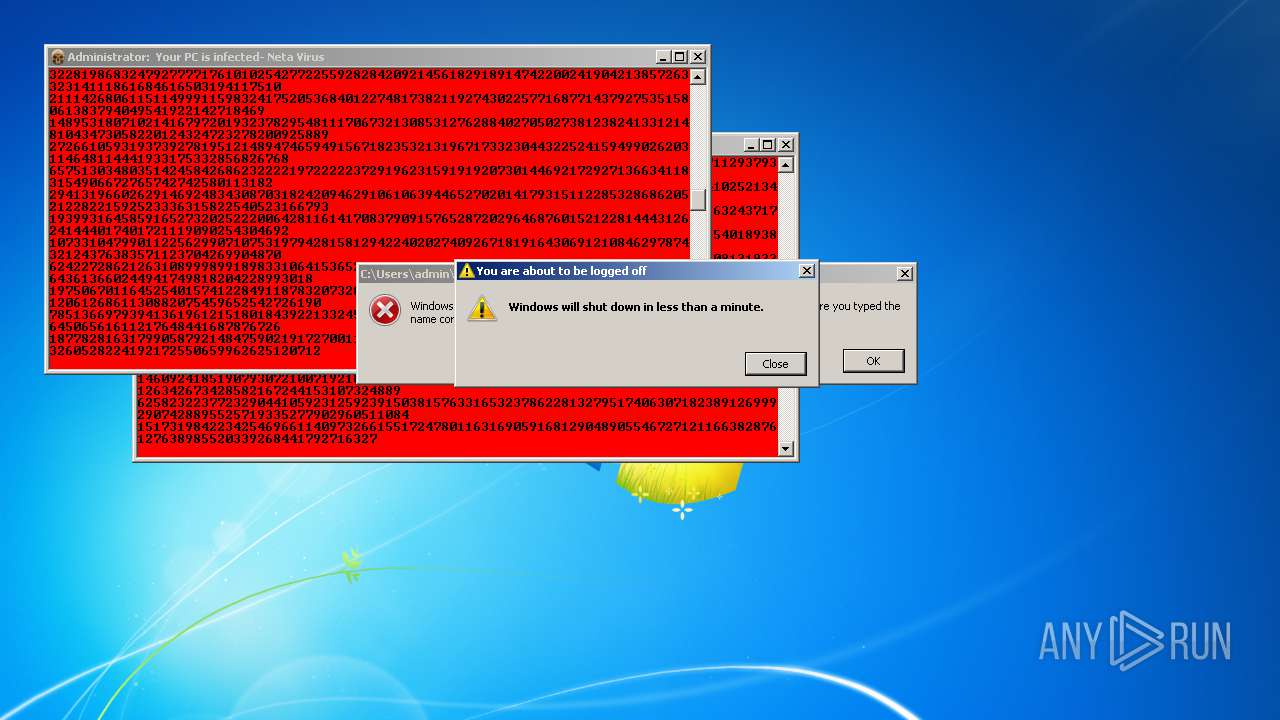
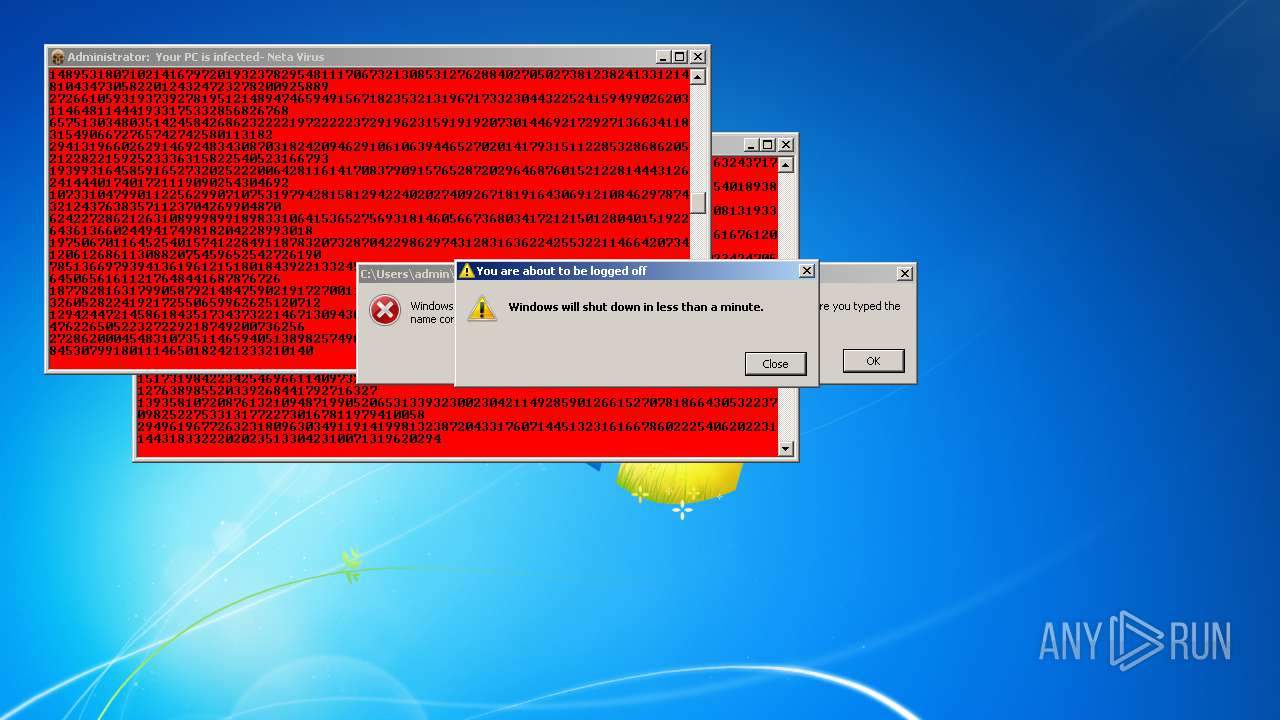
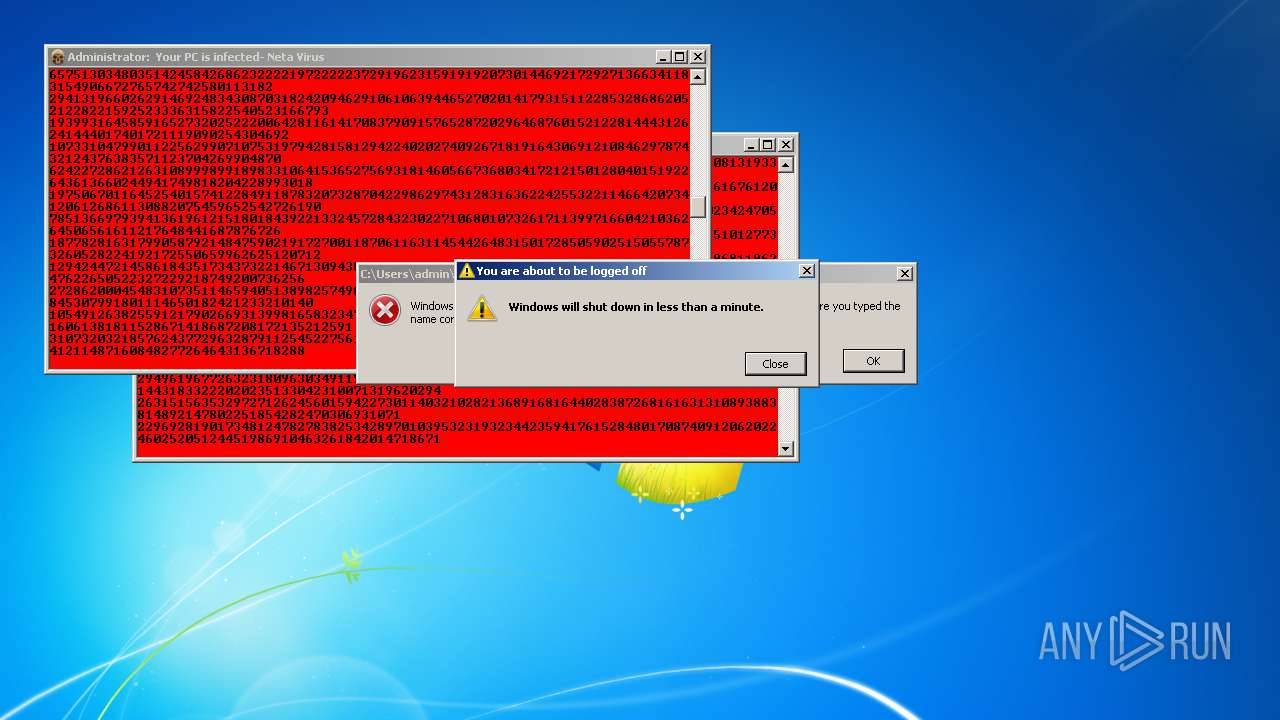
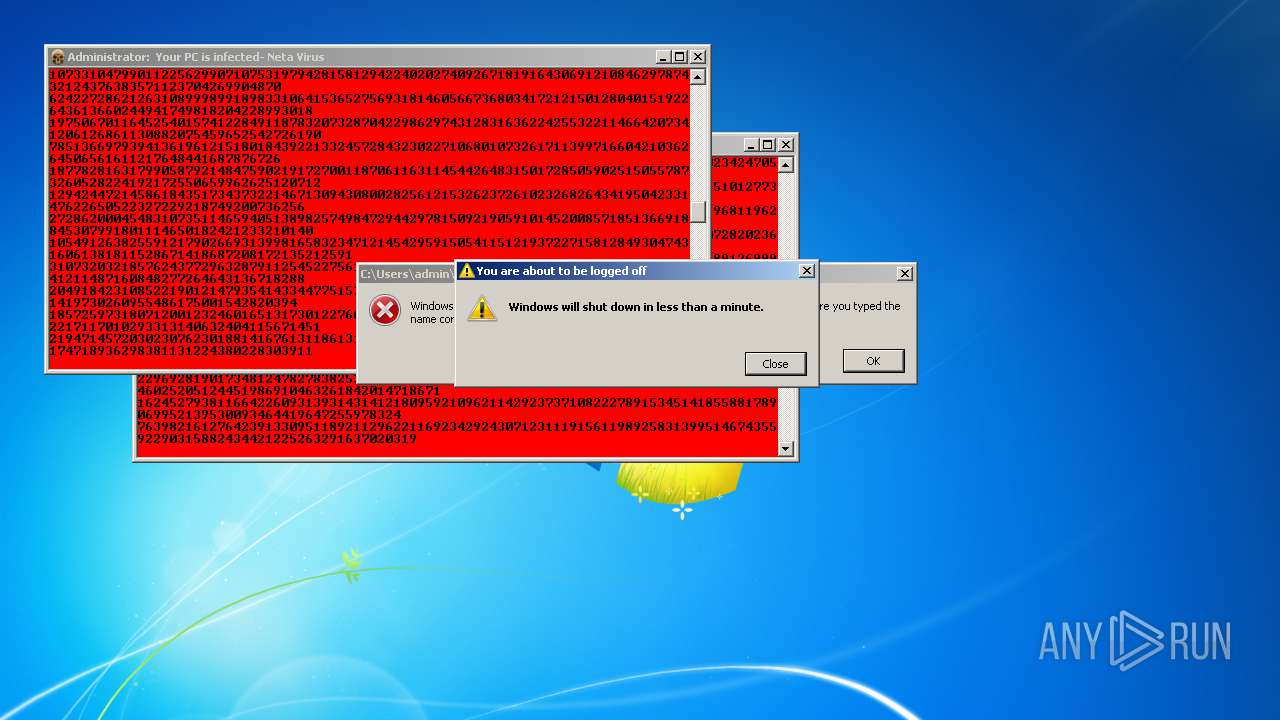
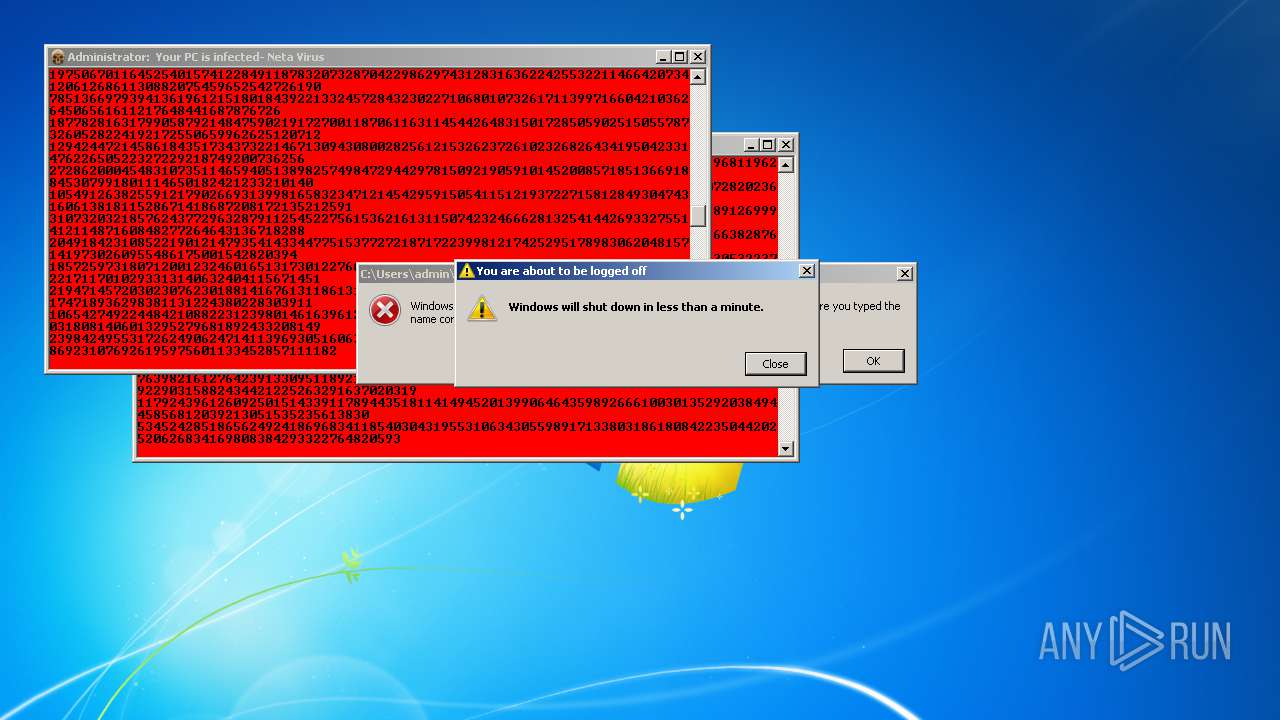
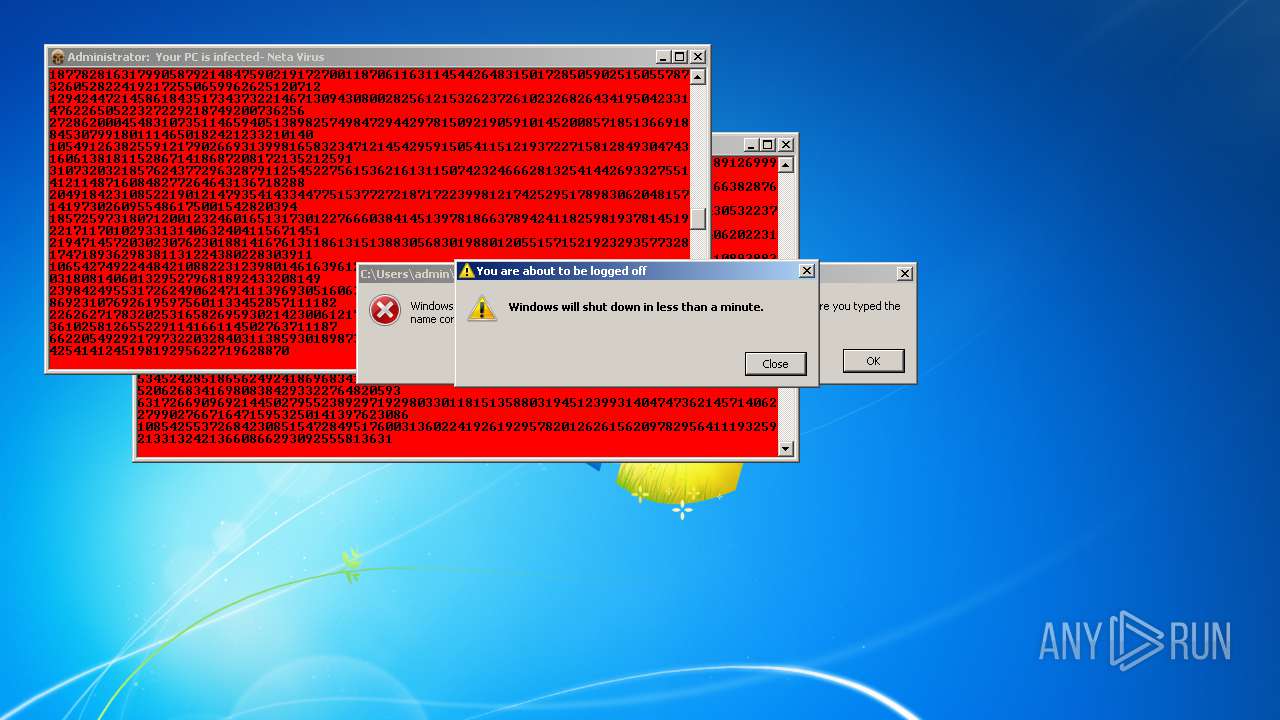
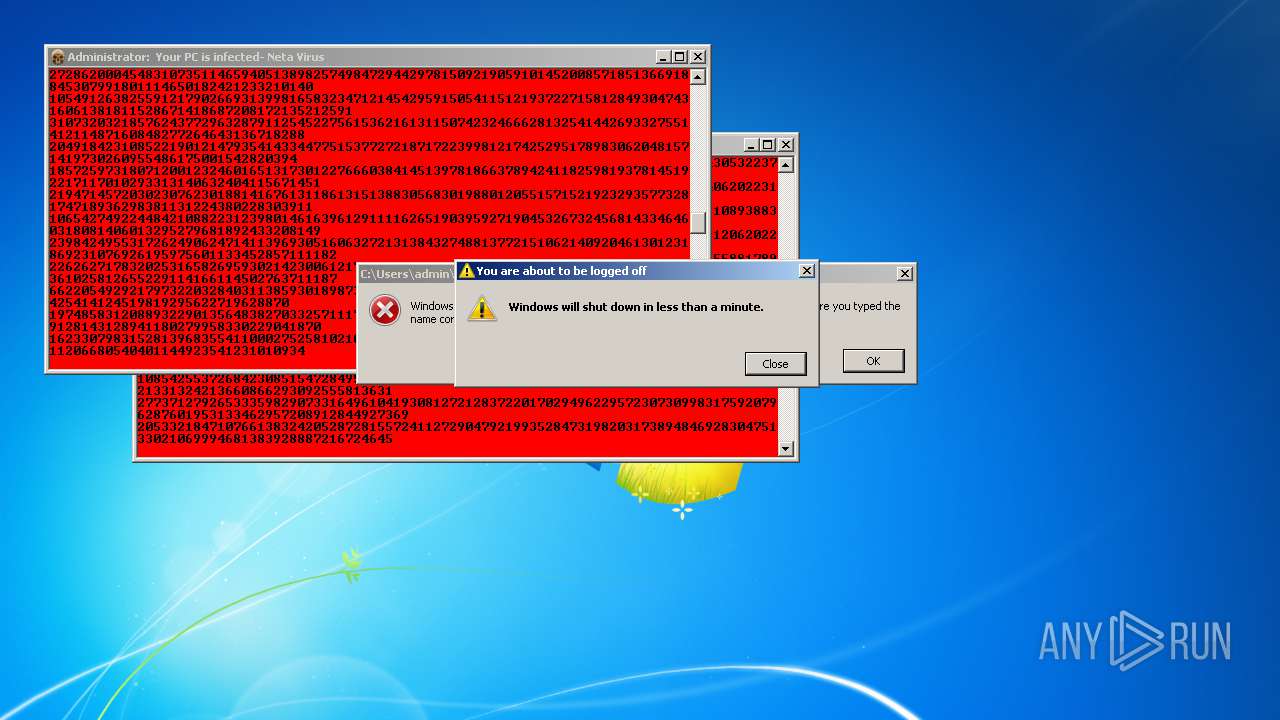
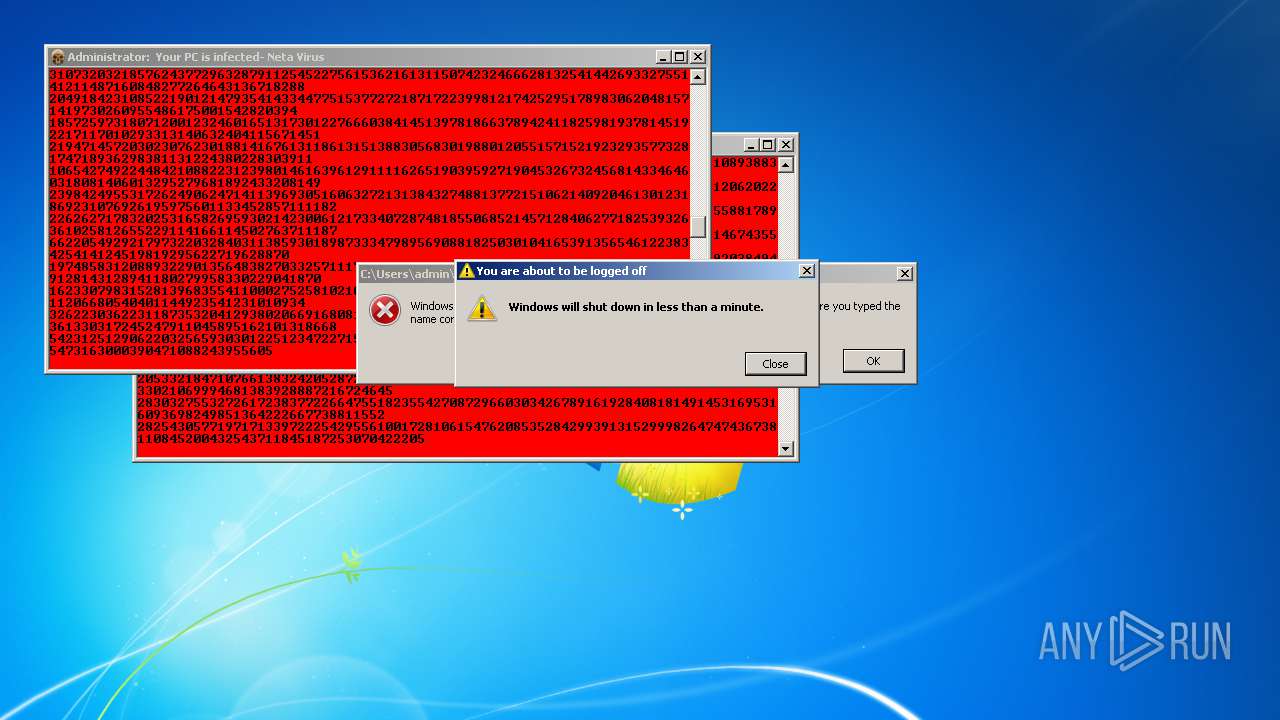
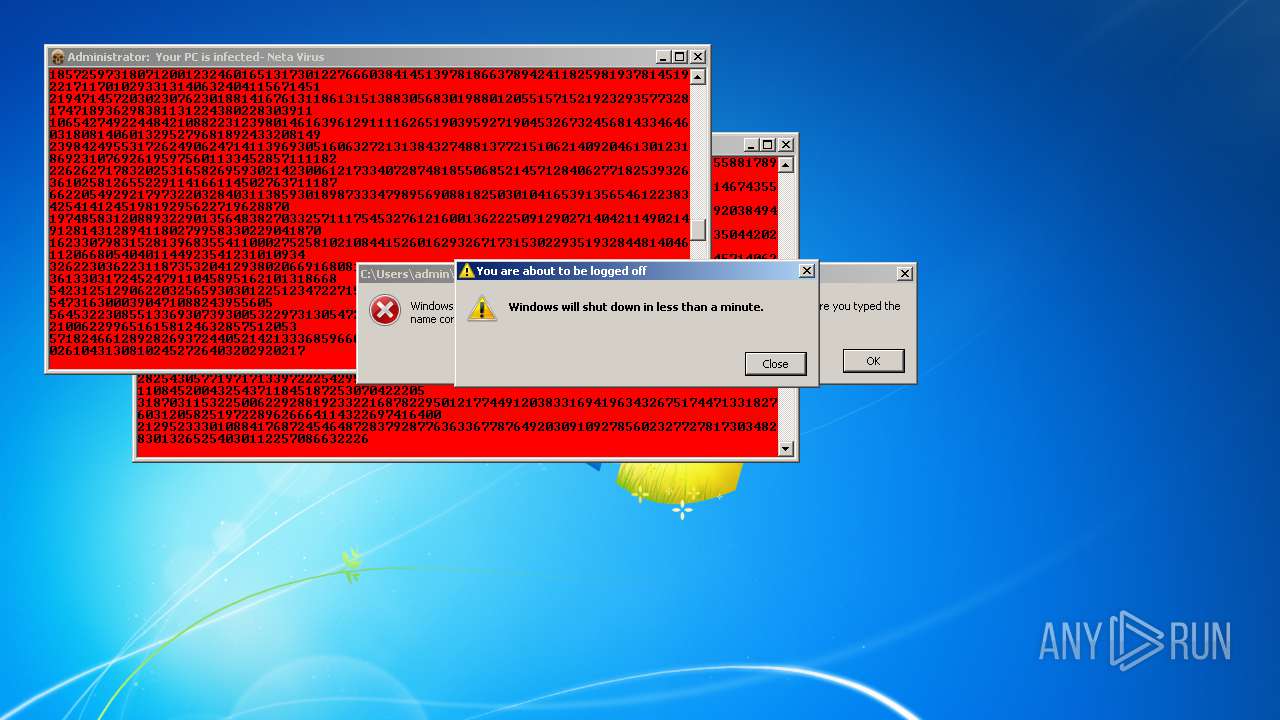
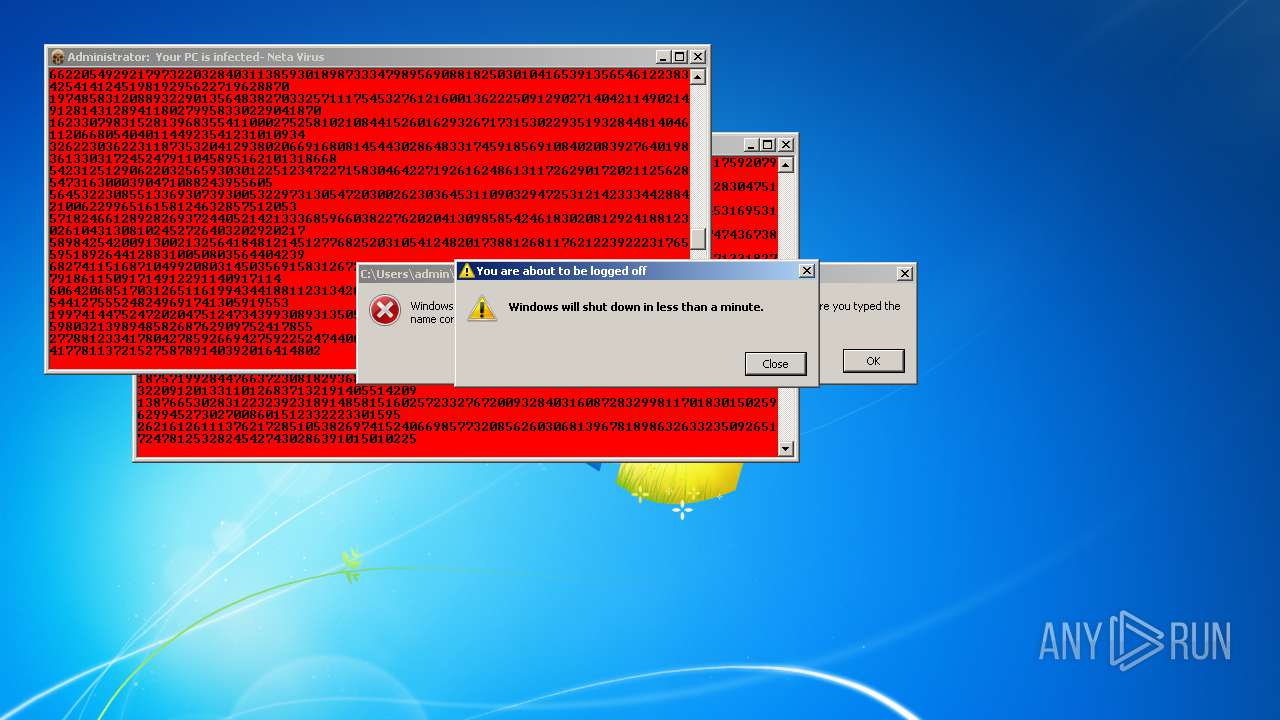
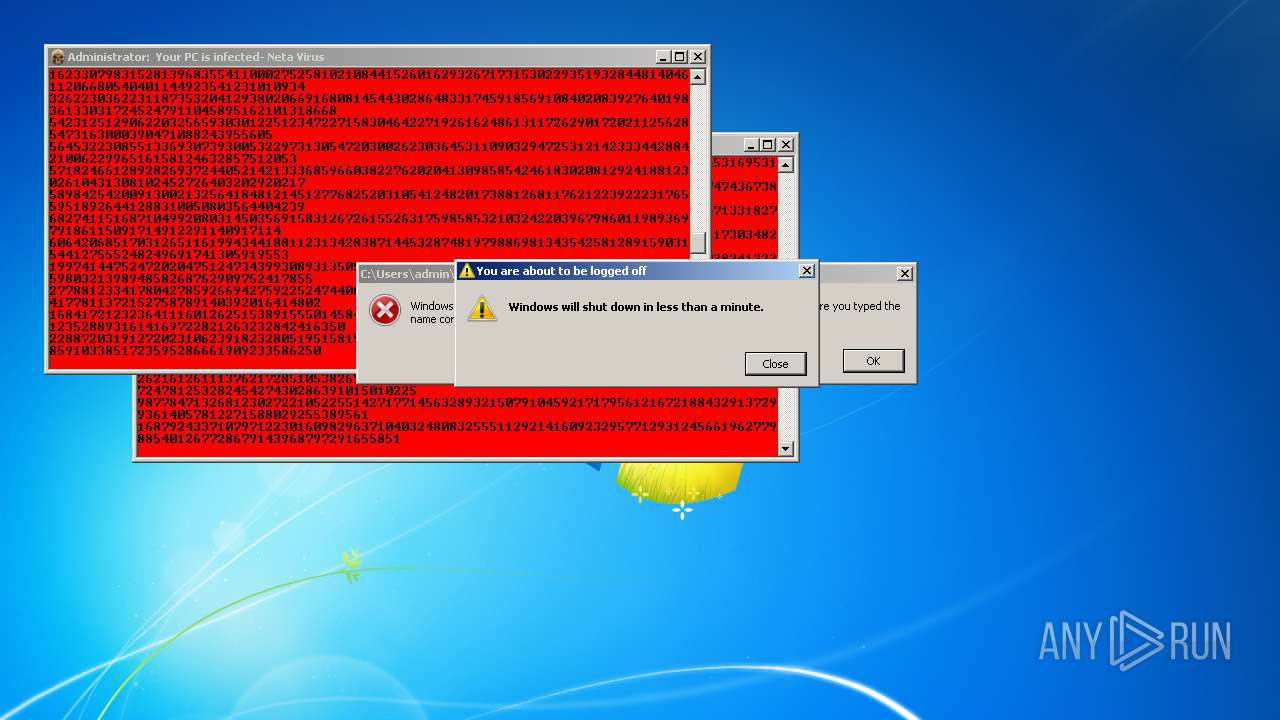
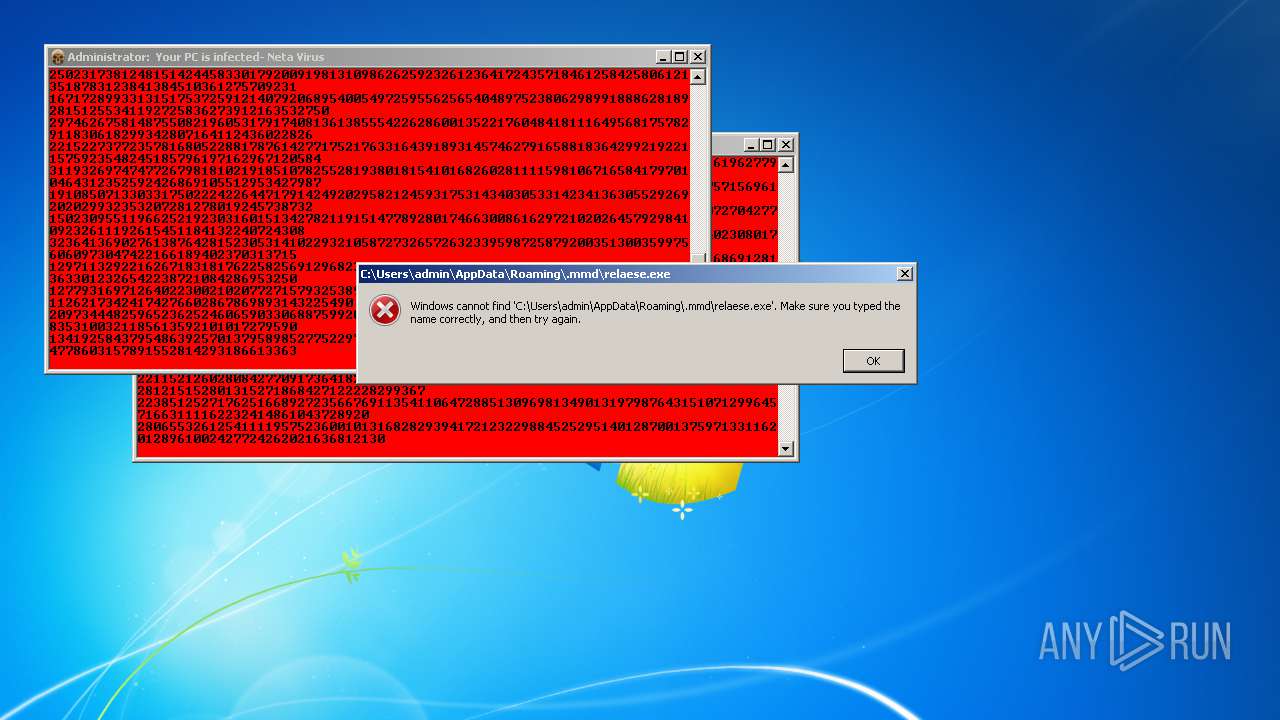
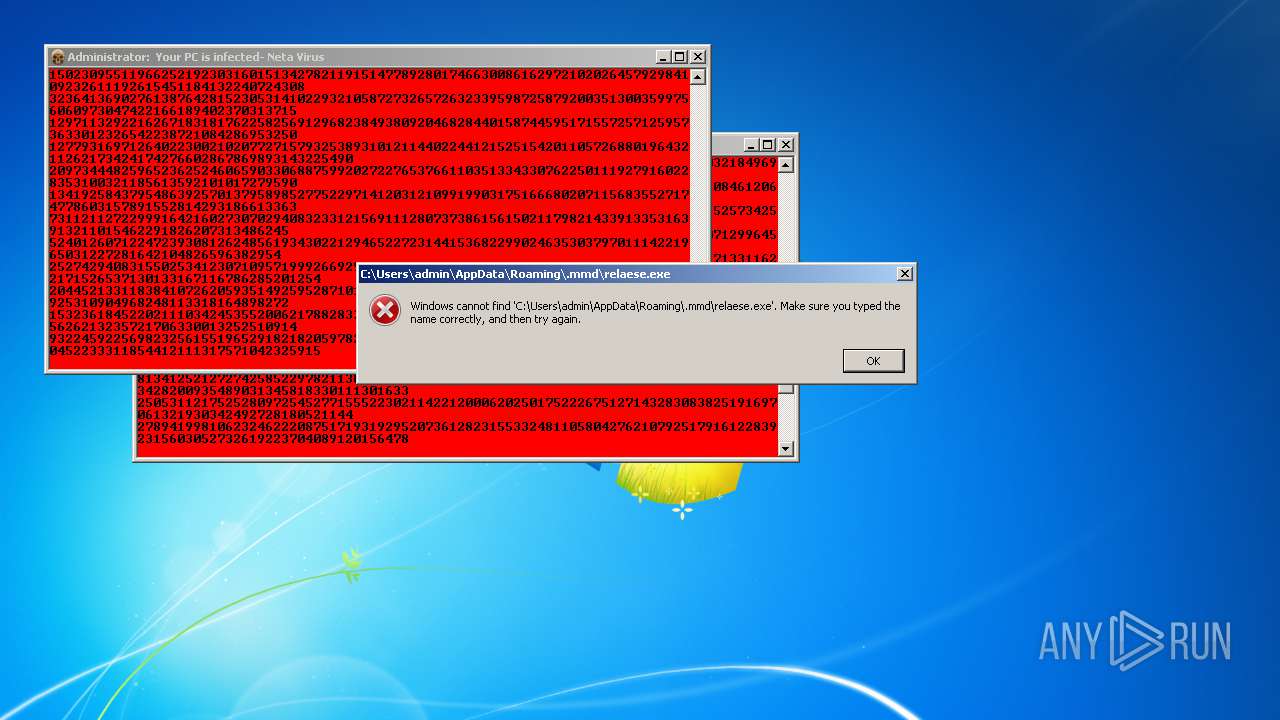
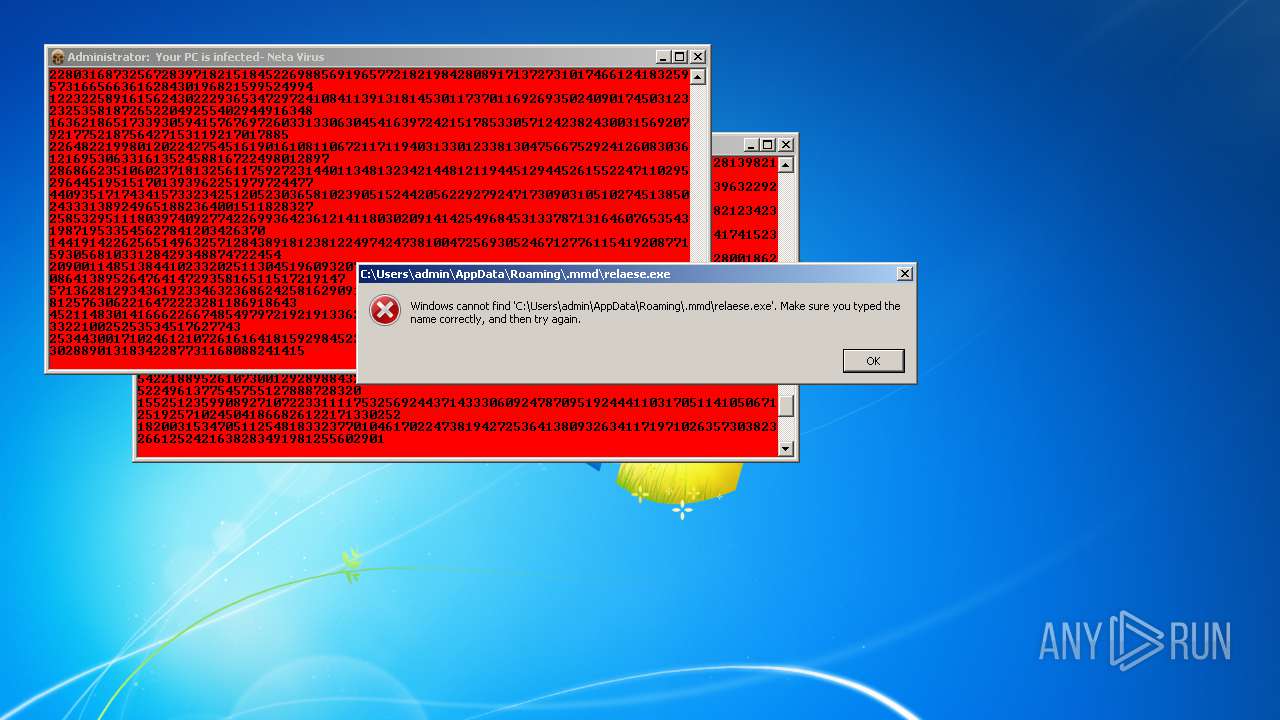
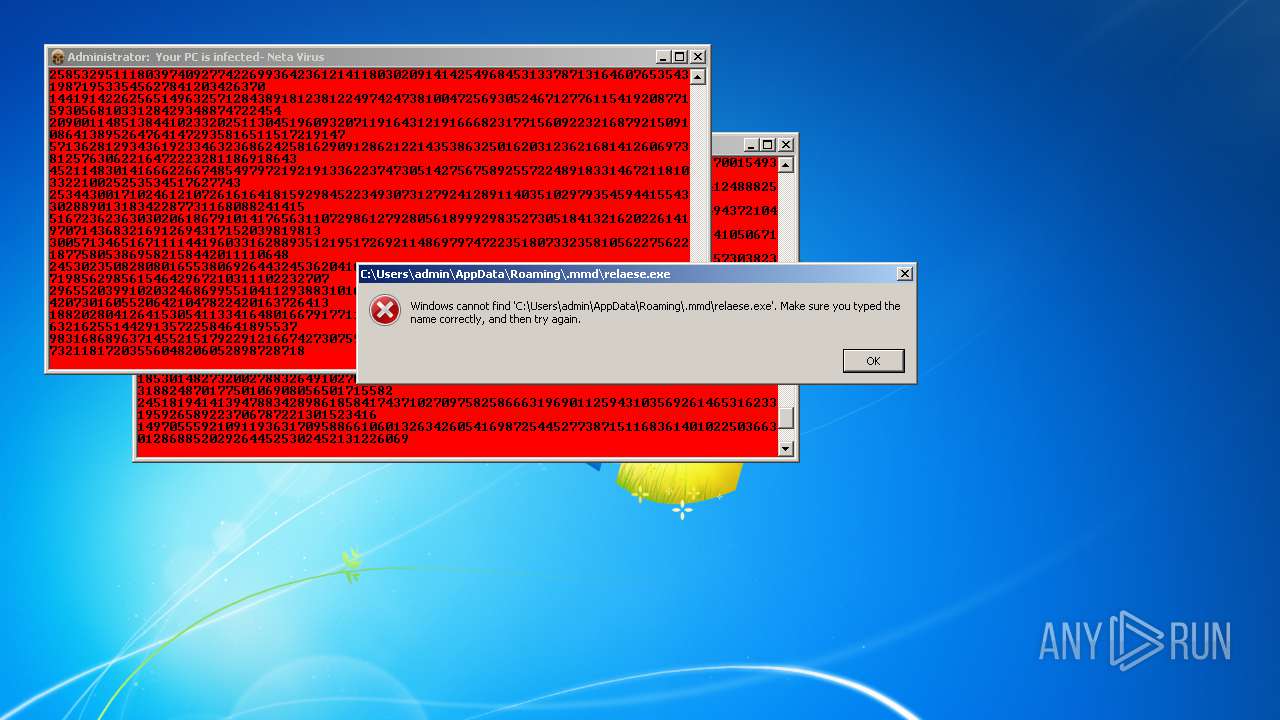
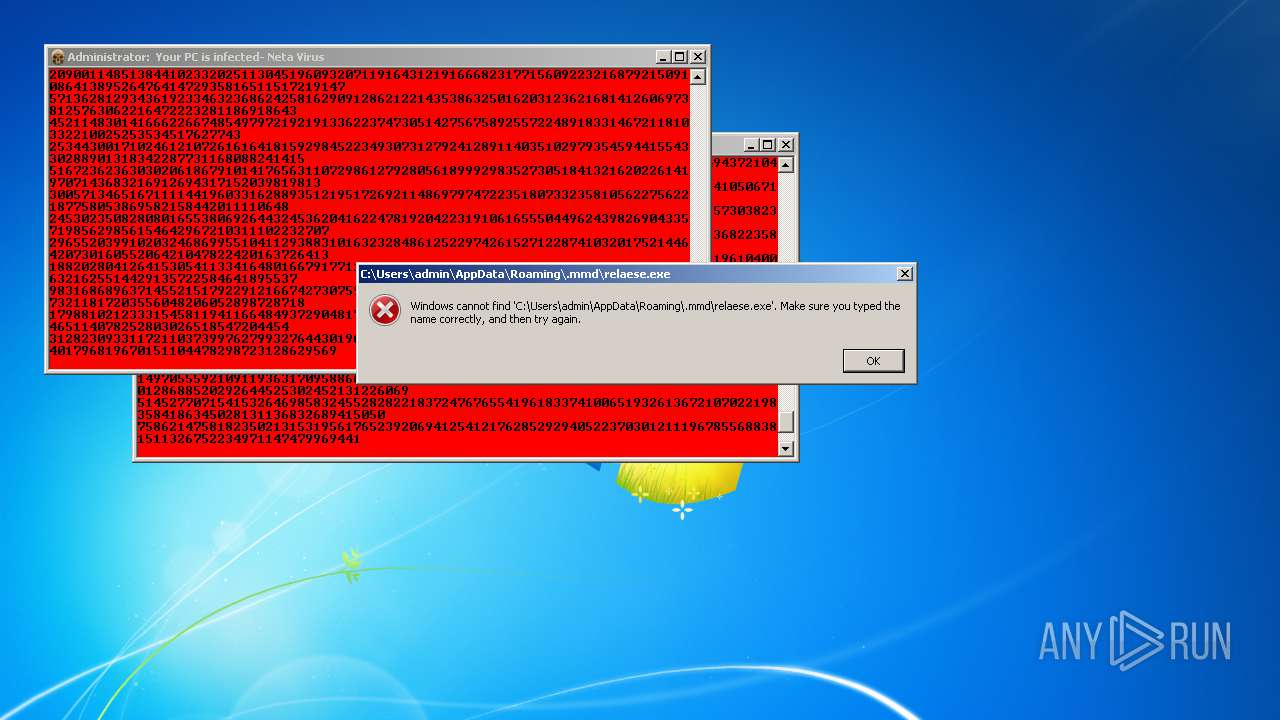
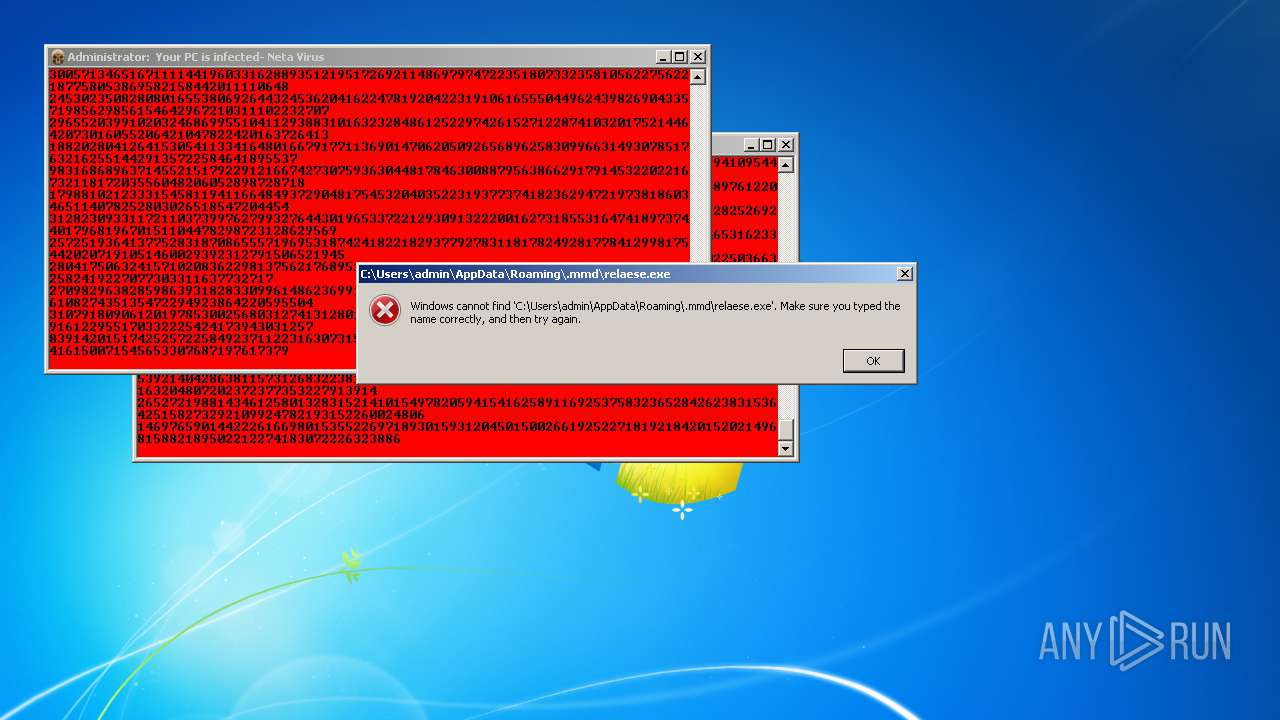
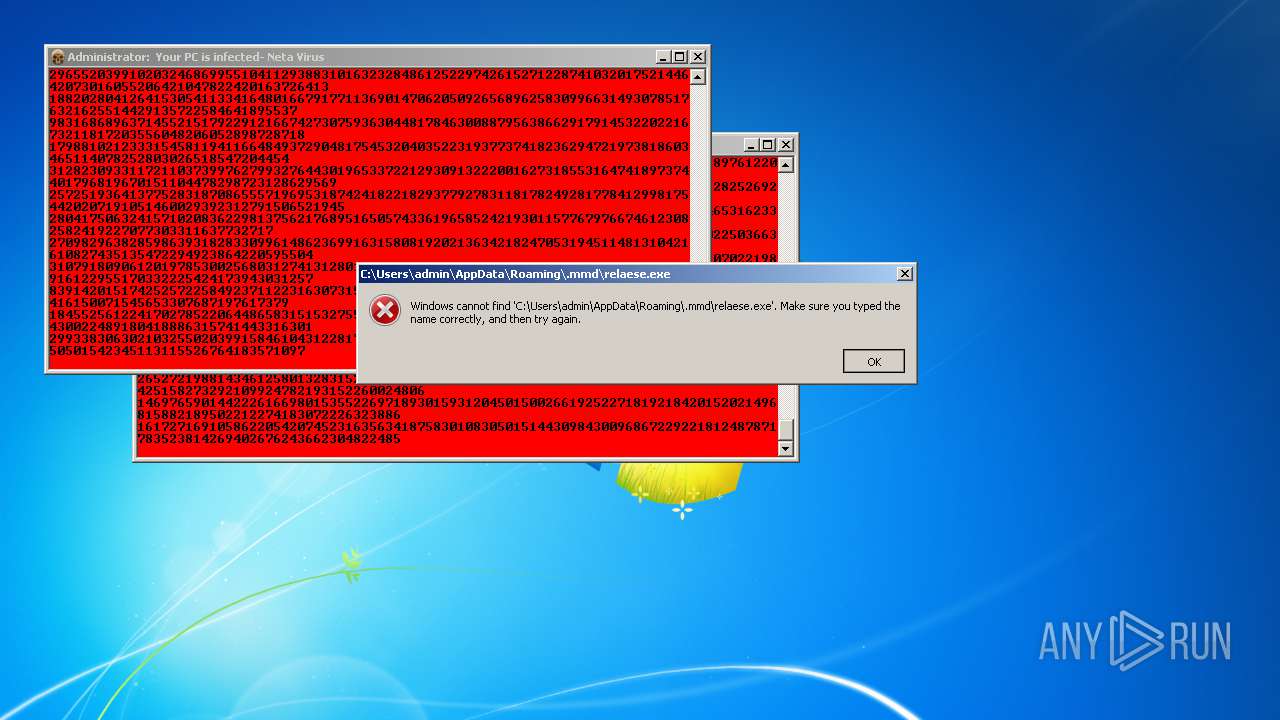
| Verdict: | Malicious activity |
| Analysis date: | March 14, 2019, 18:07:21 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | FE693D55B6C2A3C6C989774082A89013 |
| SHA1: | C46A7F383474074B2CFA821E9138C3F3587D654E |
| SHA256: | DA04C0ACBA4F49083BC54663F75963C49DB55649F457218DBA406ECF218DEA9A |
| SSDEEP: | 24576:HTTKrJ/LV+Mehh8rjwOkF3kNtsT6Db84GzVT2EScj6HdtQ3fYD7ELQQnO:zT8ZMMehqrjwOm/2QxTpScj6MgoLQN |
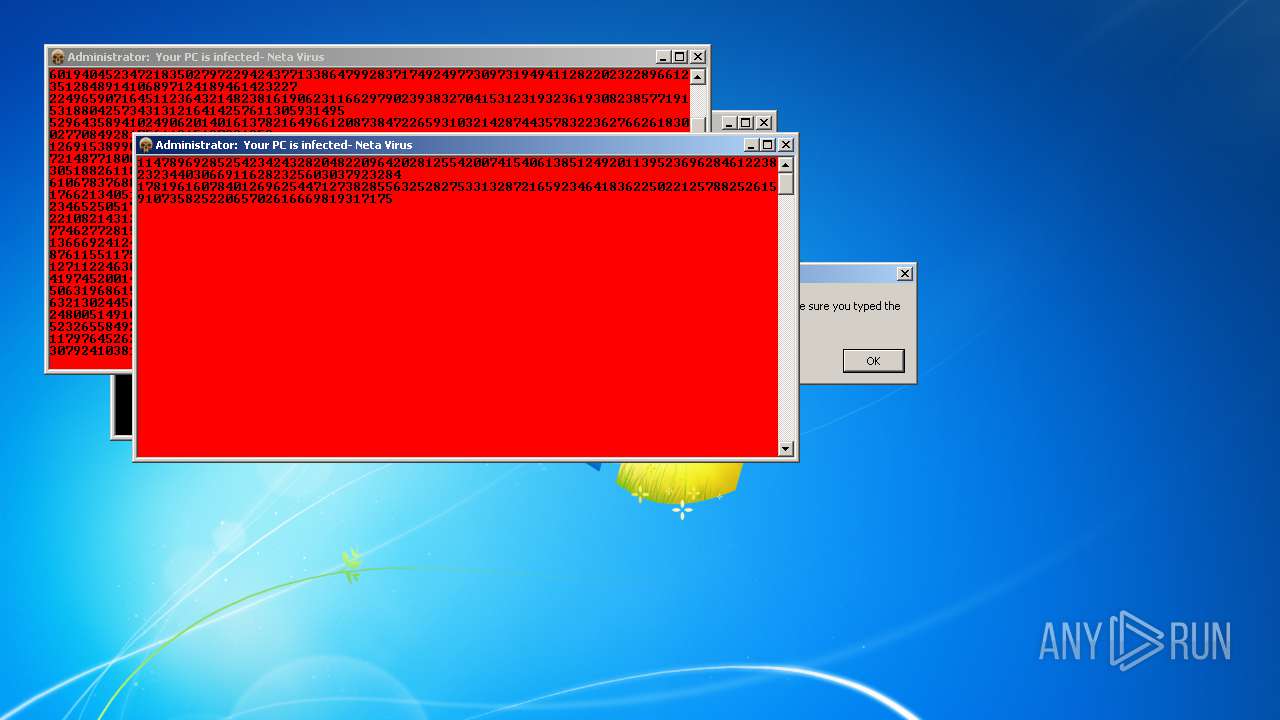
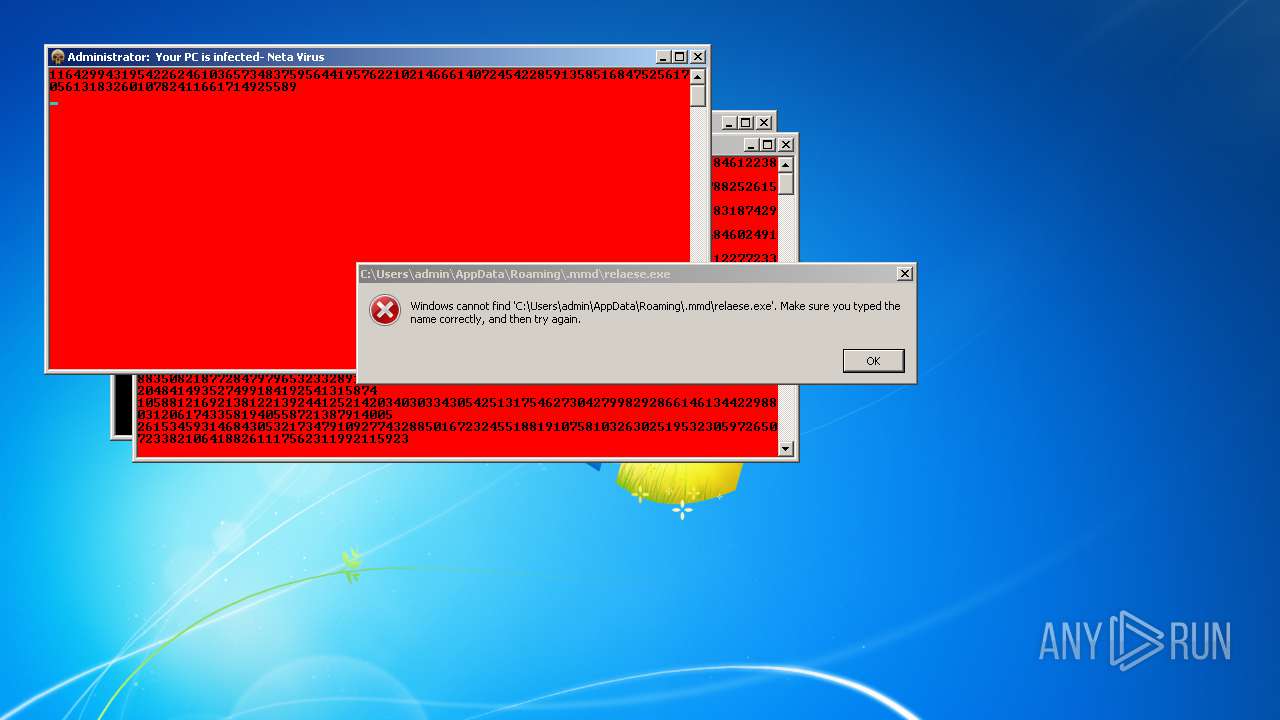
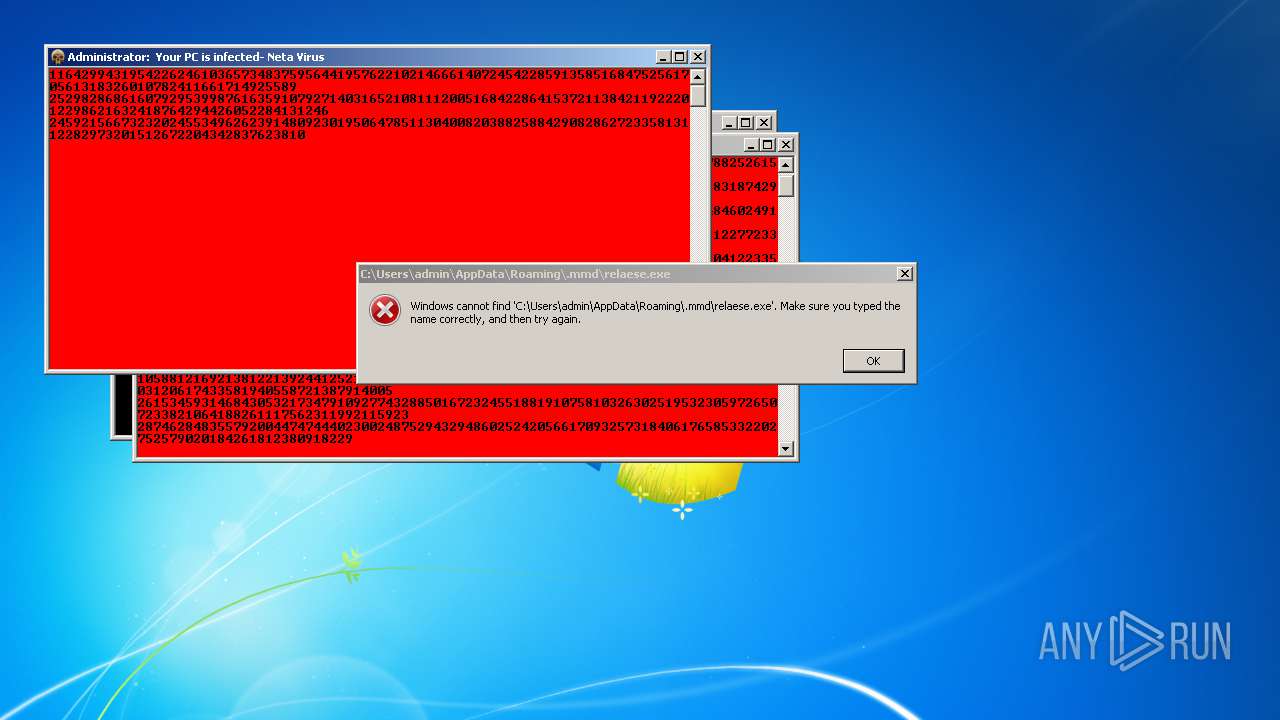
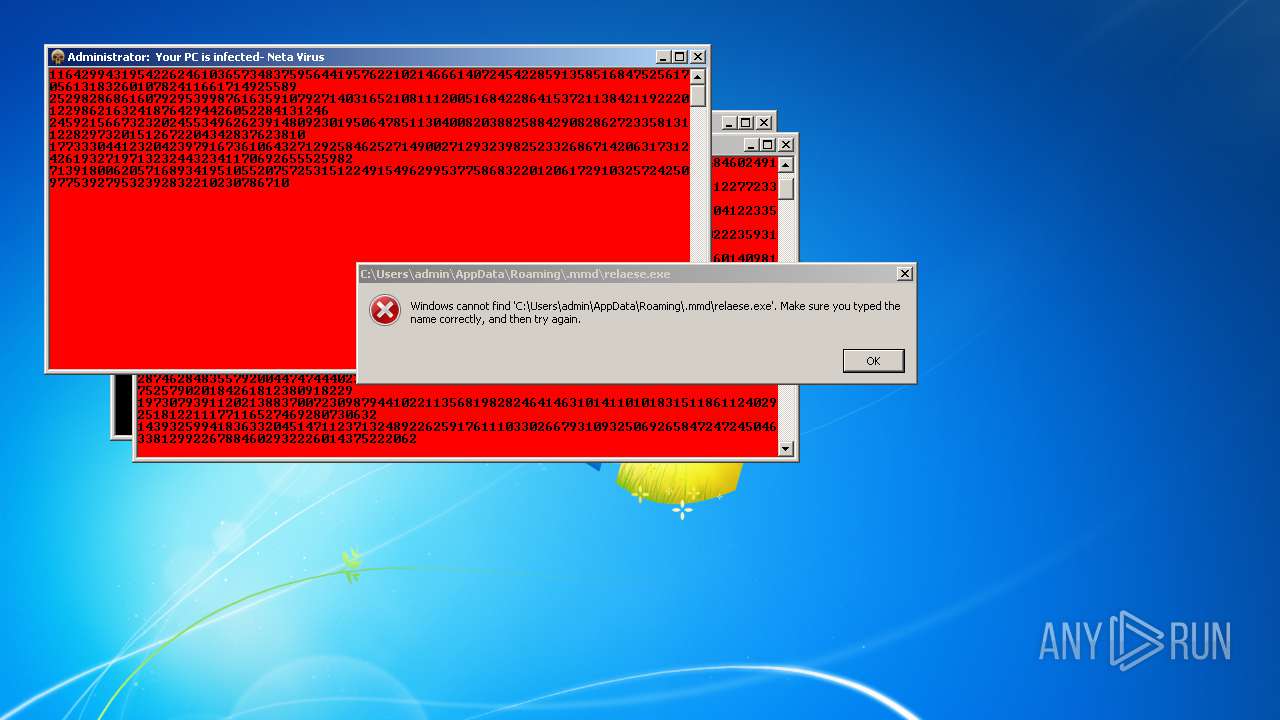
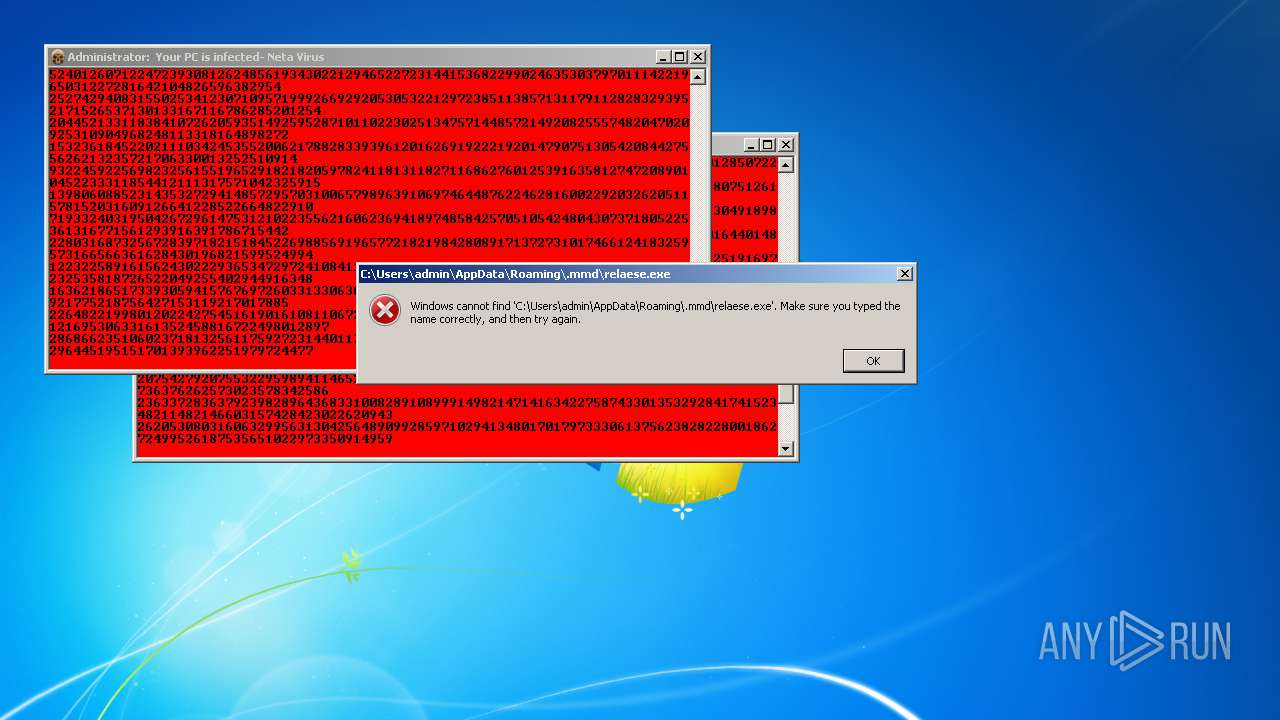
MALICIOUS
Runs PING.EXE for delay simulation
- cmd.exe (PID: 2440)
- cmd.exe (PID: 3868)
- cmd.exe (PID: 3076)
- cmd.exe (PID: 3624)
- cmd.exe (PID: 3408)
- cmd.exe (PID: 1100)
- cmd.exe (PID: 2336)
- cmd.exe (PID: 3468)
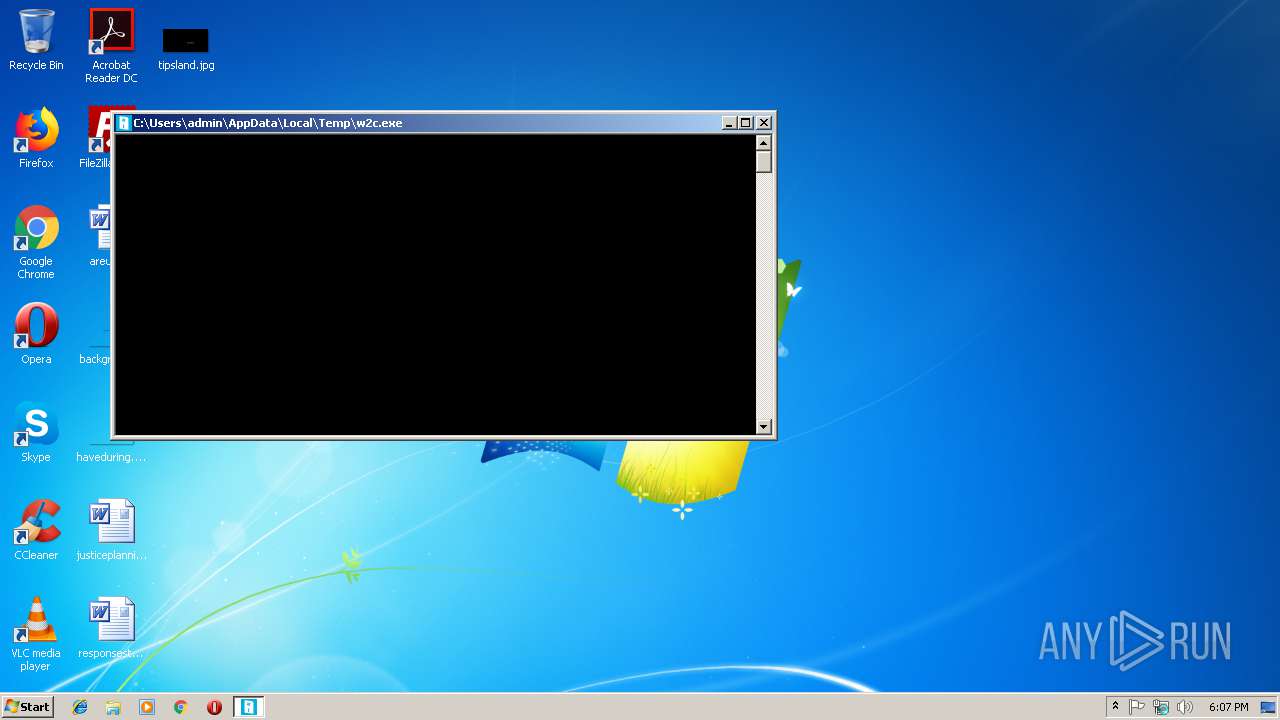
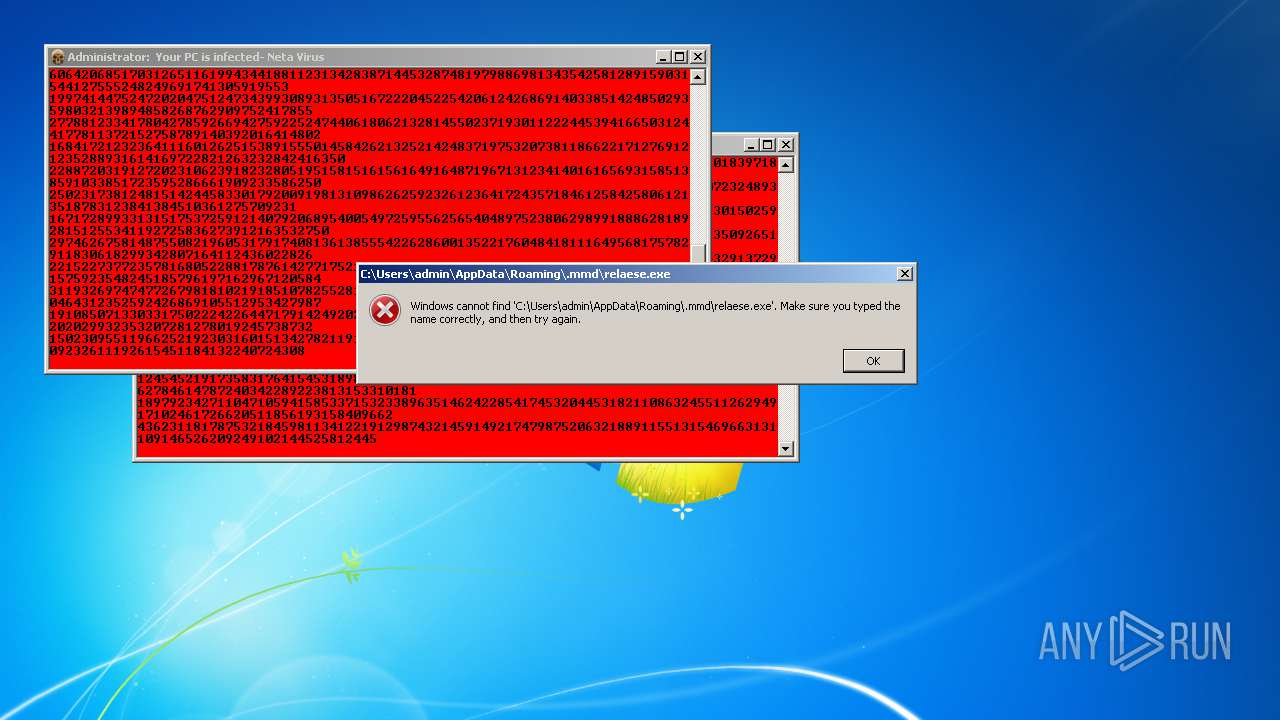
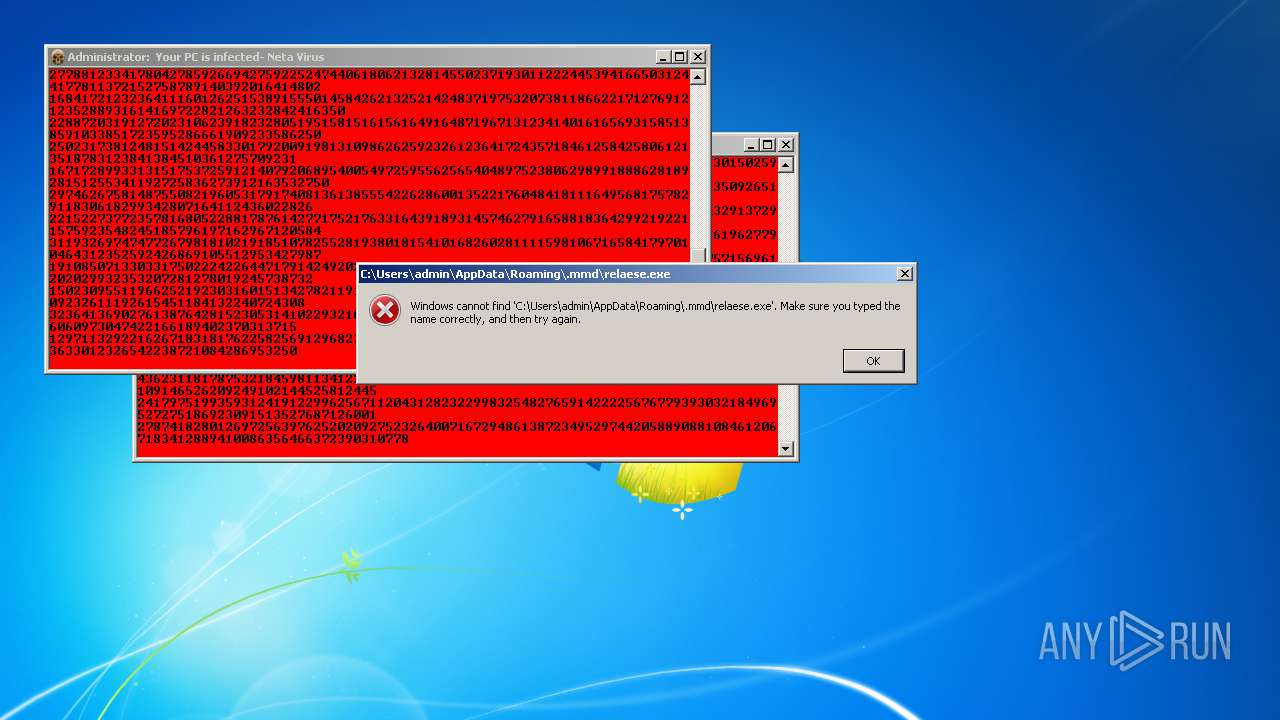
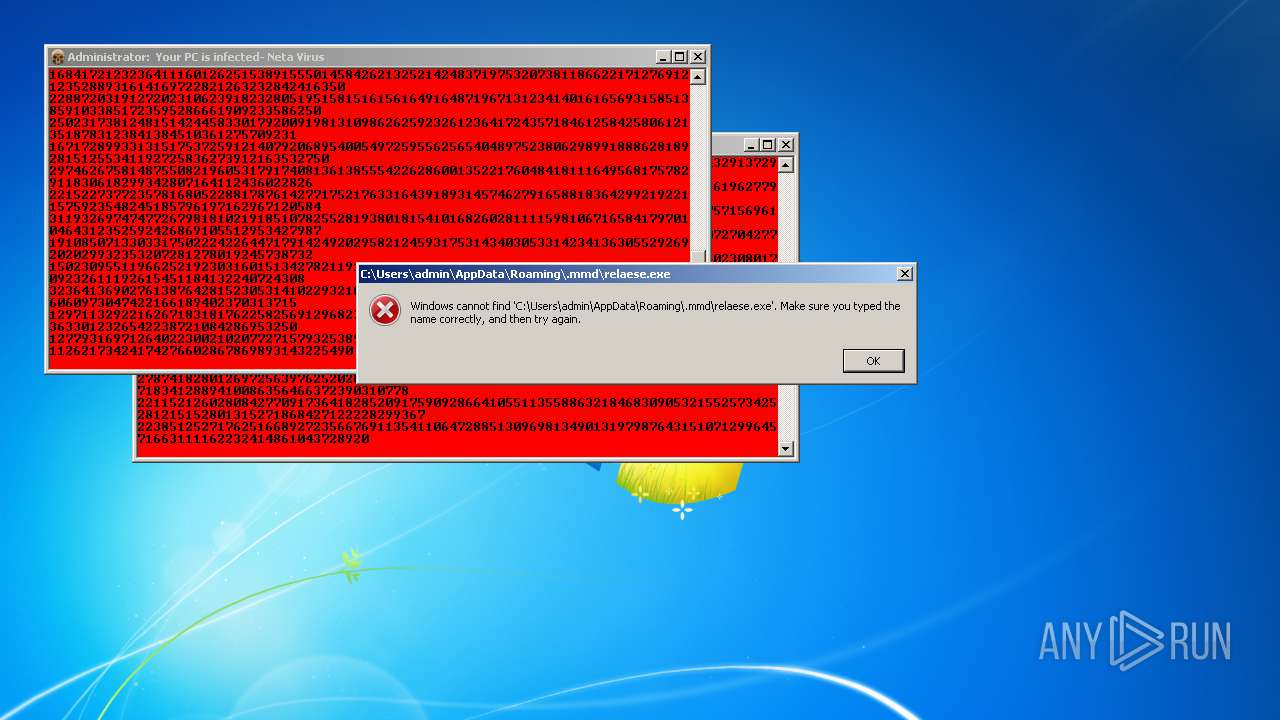
Application was dropped or rewritten from another process
- cort.exe (PID: 3668)
- w2c.exe (PID: 3028)
- down.exe (PID: 2768)
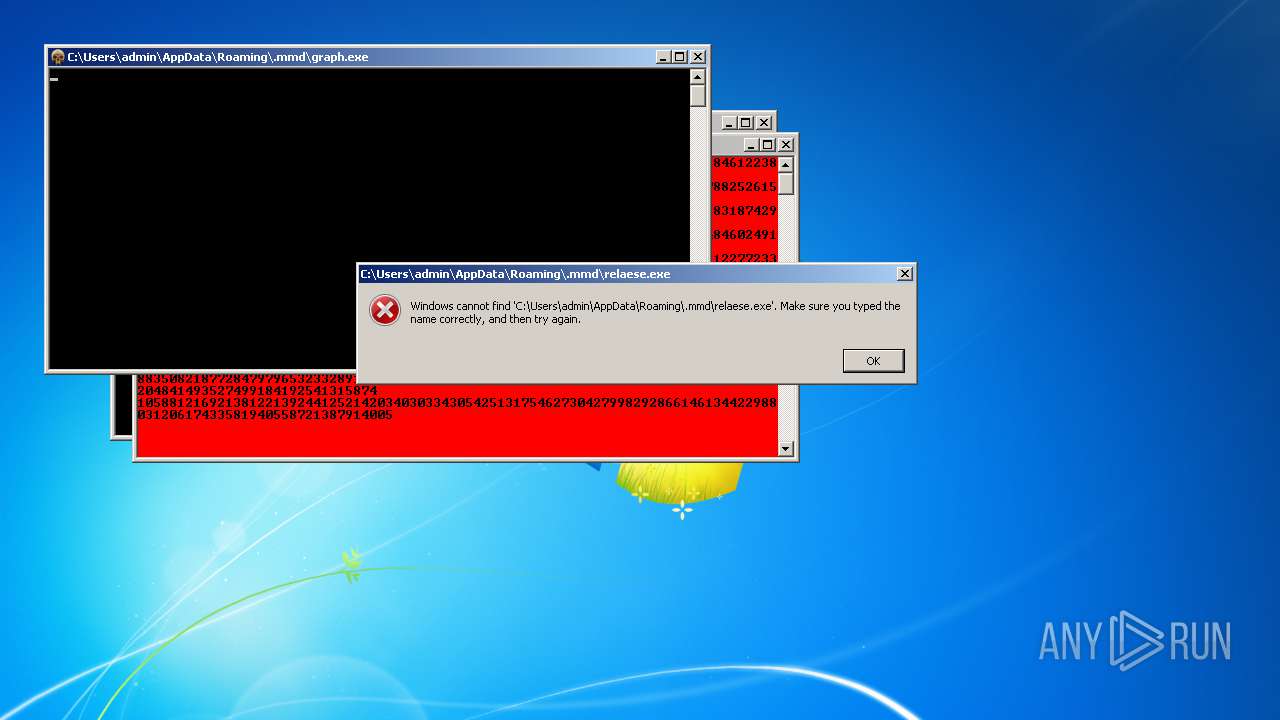
- graph.exe (PID: 1204)
- cort.exe (PID: 3984)
- writo.exe (PID: 4012)
- down.exe (PID: 3264)
- cort.exe (PID: 2244)
- graph.exe (PID: 2272)
- writo.exe (PID: 3804)
- graph.exe (PID: 3548)
- cort.exe (PID: 3924)
- writo.exe (PID: 1012)
Starts NET.EXE to view/add/change user profiles
- cmd.exe (PID: 2432)
SUSPICIOUS
Creates files in the user directory
- xcopy.exe (PID: 3392)
- xcopy.exe (PID: 3560)
- xcopy.exe (PID: 3656)
- cmd.exe (PID: 2432)
Starts CMD.EXE for commands execution
- w2c.exe (PID: 3028)
- cort.exe (PID: 3668)
- firefox.exe (PID: 2372)
- graph.exe (PID: 1204)
- cort.exe (PID: 3984)
- graph.exe (PID: 2272)
- writo.exe (PID: 3804)
- cort.exe (PID: 2244)
- writo.exe (PID: 4012)
- firefox.exe (PID: 1368)
- graph.exe (PID: 3548)
- writo.exe (PID: 1012)
- firefox.exe (PID: 3392)
- cort.exe (PID: 3924)
- firefox.exe (PID: 3528)
Creates files in the Windows directory
- xcopy.exe (PID: 2380)
- xcopy.exe (PID: 2916)
- cmd.exe (PID: 384)
- cmd.exe (PID: 3224)
- cmd.exe (PID: 2808)
Executable content was dropped or overwritten
- xcopy.exe (PID: 2916)
- xcopy.exe (PID: 2380)
- firefox.exe (PID: 3528)
- xcopy.exe (PID: 3392)
Uses TASKKILL.EXE to kill Browsers
- cmd.exe (PID: 3868)
- cmd.exe (PID: 3624)
- cmd.exe (PID: 2336)
- cmd.exe (PID: 3468)
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 3868)
- cmd.exe (PID: 3624)
- cmd.exe (PID: 2336)
- cmd.exe (PID: 3468)
- cmd.exe (PID: 2432)
Executes scripts
- cmd.exe (PID: 2432)
Uses REG.EXE to modify Windows registry
- cmd.exe (PID: 2432)
Changes the desktop background image
- reg.exe (PID: 3024)
- reg.exe (PID: 2548)
- reg.exe (PID: 3284)
- reg.exe (PID: 3360)
Uses RUNDLL32.EXE to load library
- cmd.exe (PID: 2432)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (41) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (36.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.6) |
| .exe | | | Win32 Executable (generic) (5.9) |
| .exe | | | Win16/32 Executable Delphi generic (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:02:01 21:18:00+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.5 |
| CodeSize: | 67584 |
| InitializedDataSize: | 1498112 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1000 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 0.0.0.0 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | Debug, Pre-release, Private build |
| FileOS: | Windows 16-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| FileVersion: | 12.23.72 |
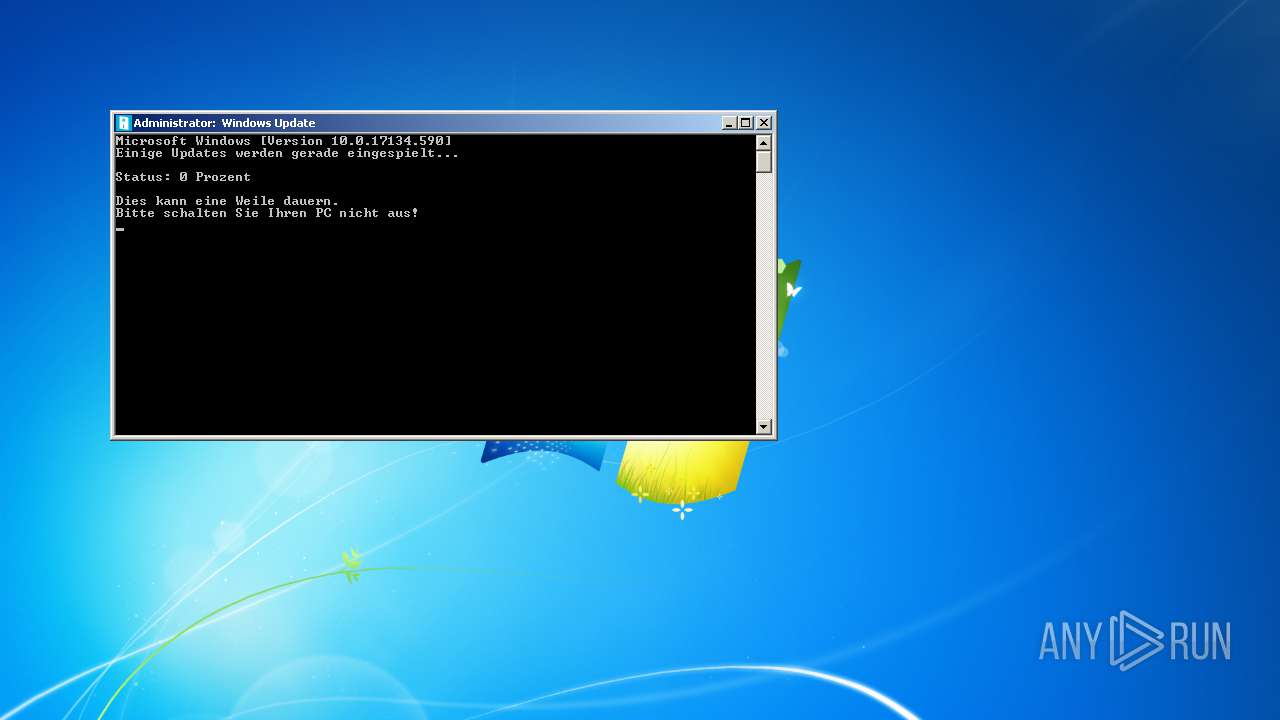
| ProductName: | Windows Update Service |
| OriginalFileName: | wus.exe |
| FileDescription: | Windows Update Service |
| CompanyName: | Microsoft Corp. |
| LegalCopyright: | (c) Microsoft Corp. 2019 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 01-Feb-2018 20:18:00 |
| Detected languages: |
|
| FileVersion: | 12.23.72 |
| ProductName: | Windows Update Service |
| OriginalFilename: | wus.exe |
| FileDescription: | Windows Update Service |
| CompanyName: | Microsoft Corp. |
| LegalCopyright: | (c) Microsoft Corp. 2019 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 01-Feb-2018 20:18:00 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.code | 0x00001000 | 0x000037F0 | 0x00003800 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.61236 |
.text | 0x00005000 | 0x0000CFA2 | 0x0000D000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.58582 |
.rdata | 0x00012000 | 0x000033A0 | 0x00003400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.11024 |
.data | 0x00016000 | 0x00001724 | 0x00001200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.93705 |
.rsrc | 0x00018000 | 0x001694B8 | 0x00169600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.86421 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.08821 | 672 | Latin 1 / Western European | UNKNOWN | RT_MANIFEST |
2 | 5.00696 | 67624 | Latin 1 / Western European | UNKNOWN | RT_ICON |
3 | 5.07409 | 38056 | Latin 1 / Western European | UNKNOWN | RT_ICON |
4 | 5.07276 | 21640 | Latin 1 / Western European | UNKNOWN | RT_ICON |
5 | 5.09169 | 16936 | Latin 1 / Western European | UNKNOWN | RT_ICON |
6 | 5.16097 | 9640 | Latin 1 / Western European | UNKNOWN | RT_ICON |
7 | 5.27367 | 4264 | Latin 1 / Western European | UNKNOWN | RT_ICON |
8 | 5.36761 | 2440 | Latin 1 / Western European | UNKNOWN | RT_ICON |
9 | 5.452 | 1128 | Latin 1 / Western European | UNKNOWN | RT_ICON |
06F1319348 | 0 | 1 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
Imports
COMCTL32.DLL |
GDI32.DLL |
KERNEL32.dll |
MSVCRT.dll |
OLE32.DLL |
SHELL32.DLL |
SHLWAPI.DLL |
USER32.DLL |
WINMM.DLL |
Total processes
345
Monitored processes
296
Malicious processes
29
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 256 | ping localhost -n 1 | C:\Windows\system32\PING.EXE | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: TCP/IP Ping Command Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 304 | taskkill /im firefox.exe /f | C:\Windows\system32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 384 | "C:\Windows\system32\cmd.exe" /c "C:\Users\admin\AppData\Local\Temp\1721.tmp\1732.tmp\1733.bat C:\Users\admin\AppData\Roaming\.mmd\writo.exe" | C:\Windows\system32\cmd.exe | — | writo.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 388 | ping localhost -n 1 | C:\Windows\system32\PING.EXE | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: TCP/IP Ping Command Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 456 | ping localhost -n 1 | C:\Windows\system32\PING.EXE | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: TCP/IP Ping Command Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 456 | ping localhost -n 1 | C:\Windows\system32\PING.EXE | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: TCP/IP Ping Command Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 608 | ping localhost -n 1 | C:\Windows\system32\PING.EXE | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: TCP/IP Ping Command Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 608 | ping localhost -n 1 | C:\Windows\system32\PING.EXE | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: TCP/IP Ping Command Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 632 | ping localhost -n 1 | C:\Windows\system32\PING.EXE | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: TCP/IP Ping Command Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
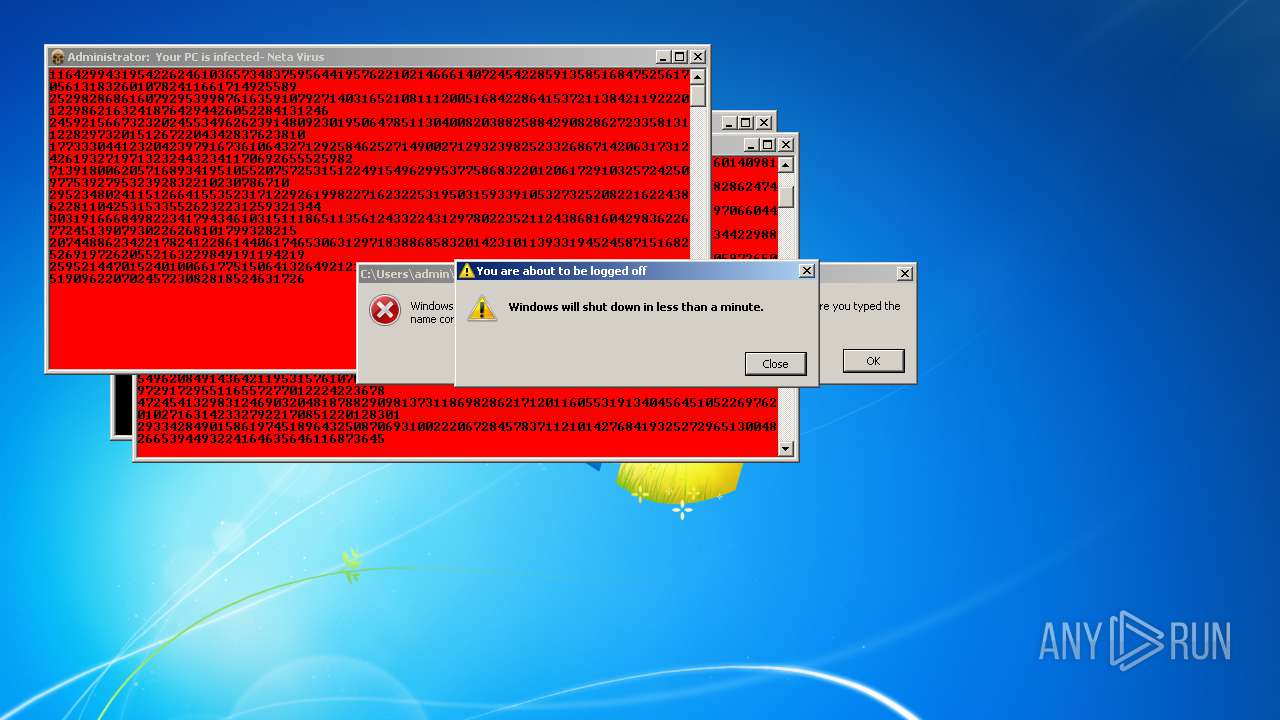
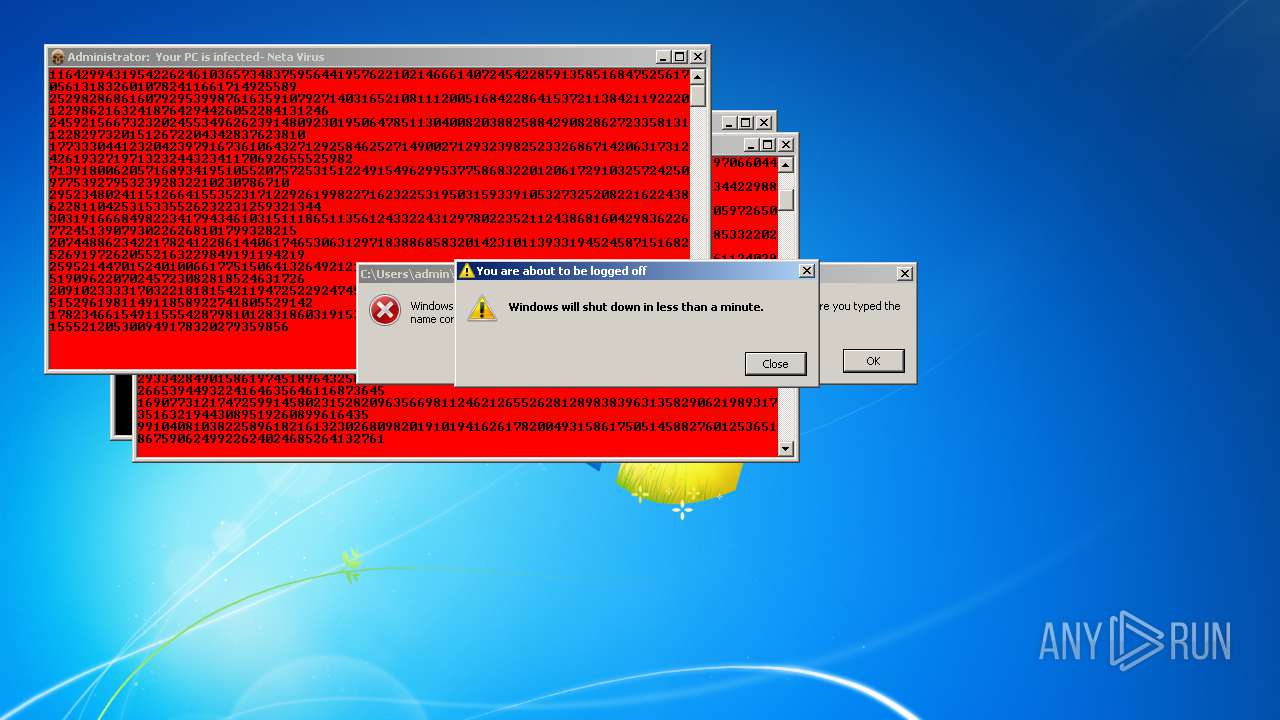
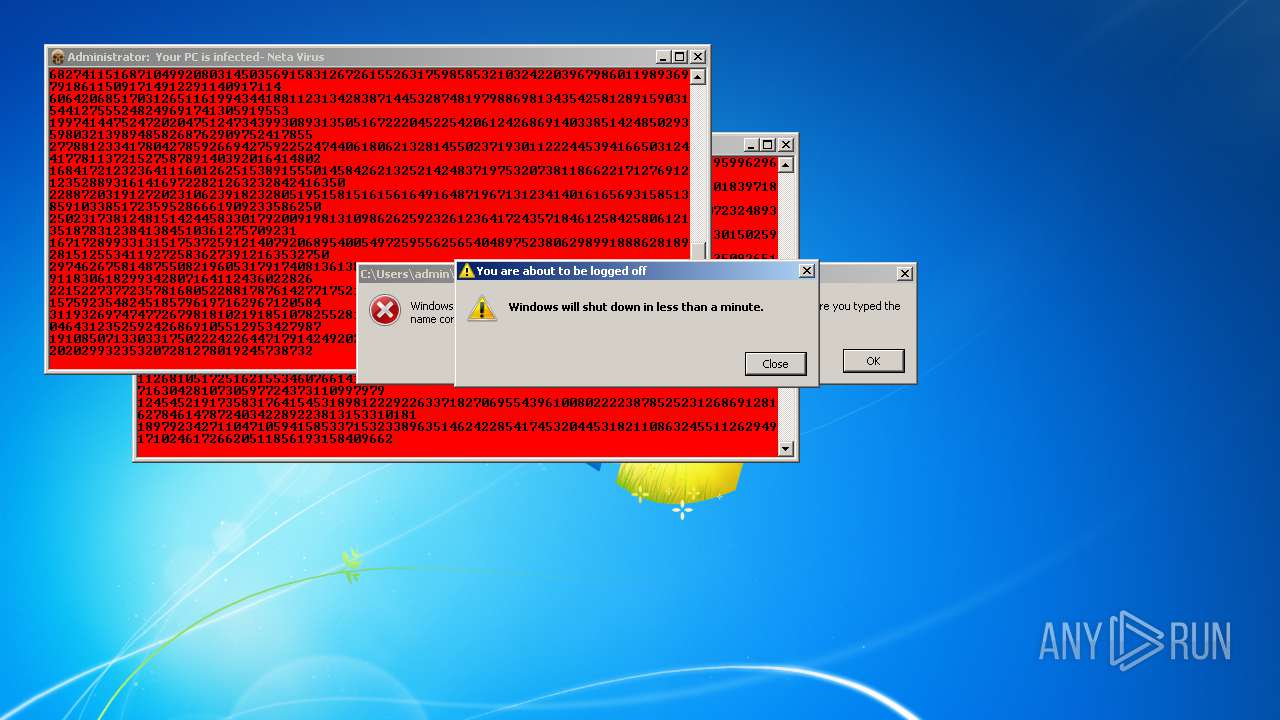
| 696 | shutdown /r /f | C:\Windows\system32\shutdown.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Shutdown and Annotation Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
2 082
Read events
2 026
Write events
56
Delete events
0
Modification events
| (PID) Process: | (3528) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3528) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3668) cort.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3668) cort.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3284) reg.exe | Key: | HKEY_CURRENT_USER\Control Panel\Desktop |
| Operation: | write | Name: | WallpaperStyle |
Value: 2 | |||
| (PID) Process: | (2548) reg.exe | Key: | HKEY_CURRENT_USER\Control Panel\Desktop |
| Operation: | write | Name: | TileWallpaper |
Value: 0 | |||
| (PID) Process: | (3360) reg.exe | Key: | HKEY_CURRENT_USER\Control Panel\Desktop |
| Operation: | write | Name: | Wallpaper |
Value: \pic.bmp | |||
| (PID) Process: | (3024) reg.exe | Key: | HKEY_CURRENT_USER\Control Panel\Desktop |
| Operation: | write | Name: | Wallpaper |
Value: \pic.bmp | |||
| (PID) Process: | (2432) cmd.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2432) cmd.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
19
Suspicious files
25
Text files
47 918
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3528 | firefox.exe | C:\Users\admin\AppData\Local\Temp\cort.exe | executable | |
MD5:— | SHA256:— | |||
| 3528 | firefox.exe | C:\Users\admin\AppData\Local\Temp\E8AE.tmp\E8AF.tmp\E8B0.bat | text | |
MD5:— | SHA256:— | |||
| 3528 | firefox.exe | C:\Users\admin\AppData\Local\Temp\down.exe | executable | |
MD5:— | SHA256:— | |||
| 3528 | firefox.exe | C:\Users\admin\AppData\Local\Temp\graph.exe | executable | |
MD5:— | SHA256:— | |||
| 3528 | firefox.exe | C:\Users\admin\AppData\Local\Temp\writo.exe | executable | |
MD5:— | SHA256:— | |||
| 3392 | xcopy.exe | C:\Users\admin\AppData\Roaming\.mmd\01q1kbjs.z2t | binary | |
MD5:— | SHA256:— | |||
| 3392 | xcopy.exe | C:\Users\admin\AppData\Roaming\.mmd\4nsl0xcm.niy | binary | |
MD5:— | SHA256:— | |||
| 3028 | w2c.exe | C:\Users\admin\AppData\Local\Temp\E9D7.tmp\E9D8.tmp\E9D9.bat | text | |
MD5:— | SHA256:— | |||
| 3392 | xcopy.exe | C:\Users\admin\AppData\Roaming\.mmd\4brm0q0k.abl | binary | |
MD5:— | SHA256:— | |||
| 3392 | xcopy.exe | C:\Users\admin\AppData\Roaming\.mmd\AdobeARM_NotLocked.log | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
12
DNS requests
11
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 188.121.36.239:80 | http://ocsp.godaddy.com//MEQwQjBAMD4wPDAJBgUrDgMCGgUABBTkIInKBAzXkF0Qh0pel3lfHJ9GPAQU0sSw0pHUTBFxs2HLPaH%2B3ahq1OMCAxvnFQ%3D%3D | NL | der | 1.66 Kb | whitelisted |
— | — | GET | 200 | 188.121.36.239:80 | http://ocsp.godaddy.com//MEIwQDA%2BMDwwOjAJBgUrDgMCGgUABBQdI2%2BOBkuXH93foRUj4a7lAr4rGwQUOpqFBxBnKLbv9r0FQW4gwZTaD94CAQc%3D | NL | der | 1.69 Kb | whitelisted |
— | — | GET | 200 | 13.33.96.186:80 | http://o.ss2.us//MEowSDBGMEQwQjAJBgUrDgMCGgUABBSLwZ6EW5gdYc9UaSEaaLjjETNtkAQUv1%2B30c7dH4b0W1Ws3NcQwg6piOcCCQCnDkpMNIK3fw%3D%3D | US | der | 1.70 Kb | whitelisted |
— | — | GET | 200 | 2.16.186.56:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | unknown | compressed | 55.2 Kb | whitelisted |
— | — | GET | 200 | 13.33.96.211:80 | http://ocsp.rootg2.amazontrust.com/MFQwUjBQME4wTDAJBgUrDgMCGgUABBSIfaREXmfqfJR3TkMYnD7O5MhzEgQUnF8A36oB1zArOIiiuG1KnPIRkYMCEwZ%2FlEoqJ83z%2BsKuKwH5CO65xMY%3D | US | der | 1.51 Kb | whitelisted |
— | — | GET | 200 | 13.33.96.203:80 | http://ocsp.sca1b.amazontrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQz9arGHWbnBV0DFzpNHz4YcTiFDQQUWaRmBlKge5WSPKOUByeWdFv5PdACEAI4jOA483M30CpSgcAmdHE%3D | US | der | 471 b | whitelisted |
— | — | GET | 200 | 13.33.96.227:80 | http://x.ss2.us/x.cer | US | der | 1.27 Kb | whitelisted |
— | — | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAH9o%2BtuynXIiEOLckvPvJE%3D | US | der | 471 b | whitelisted |
— | — | GET | 200 | 13.33.96.138:80 | http://ocsp.rootca1.amazontrust.com/MFQwUjBQME4wTDAJBgUrDgMCGgUABBRPWaOUU8%2B5VZ5%2Fa9jFTaU9pkK3FAQUhBjMhTTsvAyUlC4IWZzHshBOCggCEwZ%2FlFeFh%2Bisd96yUzJbvJmLVg0%3D | US | der | 1.39 Kb | shared |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3264 | down.exe | 192.0.77.2:443 | i1.wp.com | Automattic, Inc | US | suspicious |
— | — | 188.121.36.239:80 | ocsp.godaddy.com | GoDaddy.com, LLC | NL | unknown |
2768 | down.exe | 52.52.55.181:443 | www.reverbnation.com | Amazon.com, Inc. | US | unknown |
— | — | 13.33.96.227:80 | x.ss2.us | Amazon.com, Inc. | US | unknown |
— | — | 2.16.186.56:80 | www.download.windowsupdate.com | Akamai International B.V. | — | whitelisted |
— | — | 13.33.96.186:80 | o.ss2.us | Amazon.com, Inc. | US | unknown |
— | — | 13.33.96.211:80 | ocsp.rootg2.amazontrust.com | Amazon.com, Inc. | US | whitelisted |
2768 | down.exe | 68.232.34.237:443 | c2lo.reverbnation.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
— | — | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
— | — | 13.33.96.203:80 | ocsp.sca1b.amazontrust.com | Amazon.com, Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
i1.wp.com |
| whitelisted |
ocsp.godaddy.com |
| whitelisted |
www.reverbnation.com |
| unknown |
x.ss2.us |
| whitelisted |
www.download.windowsupdate.com |
| whitelisted |
o.ss2.us |
| whitelisted |
ocsp.rootg2.amazontrust.com |
| whitelisted |
ocsp.rootca1.amazontrust.com |
| shared |
ocsp.sca1b.amazontrust.com |
| whitelisted |
c2lo.reverbnation.com |
| unknown |