| File name: | psiphon3(1).exe |
| Full analysis: | https://app.any.run/tasks/9ff353c3-58e2-480a-8952-ef7f6b85261c |
| Verdict: | Malicious activity |
| Analysis date: | December 12, 2020, 14:47:18 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, UPX compressed |
| MD5: | 72DF77223C5C07FF61EB63D651B78D05 |
| SHA1: | AB8E27E07A457FED027581F797E1E49D4E929293 |
| SHA256: | DA043E606F336EE9FB985F35B2B98B27E2B4A3678F99AA9C481717781FB35DE3 |
| SSDEEP: | 98304:p1U2F2G8+bf+pg/nKJ8tn8E8DtGYK61ENrxuthLJ/2Hi9p/FE1Mn/5n:p1U2F2E/K2YGYkMhLJ/RVd |
MALICIOUS
Application was dropped or rewritten from another process
- psiphon-tunnel-core.exe (PID: 832)
SUSPICIOUS
Creates files in the user directory
- psiphon3(1).exe (PID: 2164)
- psiphon-tunnel-core.exe (PID: 832)
Drops a file with too old compile date
- psiphon3(1).exe (PID: 2164)
Reads internet explorer settings
- psiphon3(1).exe (PID: 2164)
Executable content was dropped or overwritten
- psiphon3(1).exe (PID: 2164)
INFO
Reads settings of System Certificates
- psiphon-tunnel-core.exe (PID: 832)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | UPX compressed Win32 Executable (43.5) |
|---|---|---|
| .exe | | | Win32 EXE Yoda's Crypter (42.7) |
| .exe | | | Win32 Executable (generic) (7.2) |
| .exe | | | Generic Win/DOS Executable (3.2) |
| .exe | | | DOS Executable Generic (3.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2020:12:07 23:18:43+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 14 |
| CodeSize: | 7356416 |
| InitializedDataSize: | 90112 |
| UninitializedDataSize: | 14430208 |
| EntryPoint: | 0x14c7b90 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 07-Dec-2020 22:18:43 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000120 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 07-Dec-2020 22:18:43 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
UPX0 | 0x00001000 | 0x00DC3000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
UPX1 | 0x00DC4000 | 0x00704000 | 0x00703E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.92883 |
.rsrc | 0x014C8000 | 0x00016000 | 0x00015E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.47073 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.91161 | 381 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 4.0192 | 744 | UNKNOWN | English - United States | RT_ICON |
3 | 5.62289 | 1384 | UNKNOWN | English - United States | RT_ICON |
4 | 5.86281 | 2216 | UNKNOWN | English - United States | RT_ICON |
5 | 5.32737 | 3752 | UNKNOWN | English - United States | RT_ICON |
6 | 5.87817 | 1128 | UNKNOWN | English - United States | RT_ICON |
7 | 5.62758 | 66 | UNKNOWN | English - United States | RT_STRING |
8 | 4.79539 | 9640 | UNKNOWN | English - United States | RT_ICON |
9 | 7.96592 | 19543 | UNKNOWN | English - United States | RT_ICON |
10 | 7.94804 | 41745 | UNKNOWN | English - United States | RT_ICON |
Imports
ADVAPI32.dll |
COMCTL32.dll |
CRYPT32.dll |
GDI32.dll |
KERNEL32.DLL |
OLEAUT32.dll |
RASAPI32.dll |
SHELL32.dll |
SHLWAPI.dll |
USER32.dll |
Total processes
37
Monitored processes
2
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 832 | C:\Users\admin\AppData\Local\Temp\psiphon-tunnel-core.exe --config "C:\Users\admin\AppData\Roaming\Psiphon3\psiphon.config" --serverList "C:\Users\admin\AppData\Roaming\Psiphon3\server_list.dat" | C:\Users\admin\AppData\Local\Temp\psiphon-tunnel-core.exe | psiphon3(1).exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2164 | "C:\Users\admin\AppData\Local\Temp\psiphon3(1).exe" | C:\Users\admin\AppData\Local\Temp\psiphon3(1).exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
627
Read events
593
Write events
34
Delete events
0
Modification events
| (PID) Process: | (2164) psiphon3(1).exe | Key: | HKEY_CURRENT_USER\Software\Psiphon3 |
| Operation: | write | Name: | SkipProxySettings |
Value: 0 | |||
| (PID) Process: | (2164) psiphon3(1).exe | Key: | HKEY_CURRENT_USER\Software\Psiphon3 |
| Operation: | write | Name: | SkipAutoConnect |
Value: 0 | |||
| (PID) Process: | (2164) psiphon3(1).exe | Key: | HKEY_CURRENT_USER\Software\Psiphon3 |
| Operation: | write | Name: | SSHParentProxyHost |
Value: | |||
| (PID) Process: | (2164) psiphon3(1).exe | Key: | HKEY_CURRENT_USER\Software\Psiphon3 |
| Operation: | write | Name: | SSHParentProxyUsername |
Value: | |||
| (PID) Process: | (2164) psiphon3(1).exe | Key: | HKEY_CURRENT_USER\Software\Psiphon3 |
| Operation: | write | Name: | SSHParentProxyPassword |
Value: | |||
| (PID) Process: | (2164) psiphon3(1).exe | Key: | HKEY_CURRENT_USER\Software\Psiphon3 |
| Operation: | write | Name: | SSHParentProxyDomain |
Value: | |||
| (PID) Process: | (2164) psiphon3(1).exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2164) psiphon3(1).exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2164) psiphon3(1).exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2164) psiphon3(1).exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
Executable files
1
Suspicious files
0
Text files
17
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2164 | psiphon3(1).exe | C:\Users\admin\AppData\Roaming\Psiphon3\psicash\psicashdatastore.prod.temp | — | |
MD5:— | SHA256:— | |||
| 2164 | psiphon3(1).exe | C:\Users\admin\AppData\Roaming\Psiphon3\psicash\psicashdatastore.prod.commit | — | |
MD5:— | SHA256:— | |||
| 2164 | psiphon3(1).exe | C:\Users\admin\AppData\Roaming\Psiphon3\psicash\psicashdatastore.prod | text | |
MD5:— | SHA256:— | |||
| 2164 | psiphon3(1).exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\6Z2BCOUL\main[1] | html | |
MD5:— | SHA256:— | |||
| 2164 | psiphon3(1).exe | C:\Users\admin\AppData\Roaming\Psiphon3\psiphon.config | text | |
MD5:— | SHA256:— | |||
| 2164 | psiphon3(1).exe | C:\Users\admin\AppData\Roaming\Psiphon3\server_list.dat | text | |
MD5:— | SHA256:— | |||
| 2164 | psiphon3(1).exe | C:\Users\admin\AppData\Local\Temp\psiphon-tunnel-core.exe | executable | |
MD5:— | SHA256:— | |||
| 2164 | psiphon3(1).exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\PO2HN1X2\rocket[1] | image | |
MD5:8D890C253C374EA27981CBCA386D69D7 | SHA256:EFE61D586AFF065712F15AB38AC602447B625B0FB21BB8E3FACF14AE453BB431 | |||
| 2164 | psiphon3(1).exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\78RFYB7Z\icomoon[1] | eot | |
MD5:9BA3A958E8254C41E8ACE685E35E8CF1 | SHA256:EDB2DF32F1F406895DB11C56998E1390924CFF7137EC67B83A935019EAF7A928 | |||
| 2164 | psiphon3(1).exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\psicash_coin[1] | image | |
MD5:CBA396707A4339C9EAD9AC6DDE96F93D | SHA256:558CBA644707914E8172333E6D8B8D73EAD464E93C2D1EDE5DD20BD64BD108C8 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
11
TCP/UDP connections
252
DNS requests
155
Threats
81
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
832 | psiphon-tunnel-core.exe | POST | — | 23.215.130.18:80 | http://www.talentcalgsmprofessional.com/ | US | — | — | suspicious |
832 | psiphon-tunnel-core.exe | POST | — | 185.220.70.118:80 | http://185.220.70.118/ | unknown | — | — | suspicious |
832 | psiphon-tunnel-core.exe | POST | — | 82.223.11.221:80 | http://82.223.11.221/ | ES | — | — | unknown |
832 | psiphon-tunnel-core.exe | POST | — | 94.176.148.171:80 | http://www.nyrevsunrisegogreen.com/ | RO | — | — | unknown |
832 | psiphon-tunnel-core.exe | POST | — | 185.189.115.146:80 | http://185.189.115.146/ | CZ | — | — | unknown |
832 | psiphon-tunnel-core.exe | POST | 404 | 88.208.221.16:80 | http://www.patcoastalfoundry.org/ | GB | xml | 341 b | unknown |
832 | psiphon-tunnel-core.exe | POST | 404 | 178.62.235.58:80 | http://frenzycircleseejax.org/ | NL | xml | 341 b | suspicious |
832 | psiphon-tunnel-core.exe | POST | 404 | 23.215.130.16:80 | http://www.vtbestcustom.com/ | US | xml | 341 b | unknown |
832 | psiphon-tunnel-core.exe | POST | — | 23.215.130.10:80 | http://www.retapimaginethereal.com/ | US | — | — | unknown |
832 | psiphon-tunnel-core.exe | POST | 404 | 146.185.157.119:80 | http://fundingslidebrooklynextra.net/ | NL | xml | 341 b | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
832 | psiphon-tunnel-core.exe | 213.171.205.251:554 | — | 1&1 Internet SE | GB | unknown |
832 | psiphon-tunnel-core.exe | 107.161.20.253:22 | — | RamNode LLC | US | unknown |
— | — | 23.215.130.25:443 | a484.na.akamai.net | Akamai International B.V. | US | unknown |
832 | psiphon-tunnel-core.exe | 104.17.229.2:443 | — | Cloudflare Inc | US | shared |
— | — | 104.18.153.190:443 | — | Cloudflare Inc | US | shared |
832 | psiphon-tunnel-core.exe | 185.130.184.94:53 | — | — | — | unknown |
— | — | 2.16.186.41:80 | a262.gd.akamai.net | Akamai International B.V. | — | whitelisted |
— | — | 151.101.0.249:80 | global.prod.fastly.com | Fastly | US | suspicious |
832 | psiphon-tunnel-core.exe | 82.223.43.237:554 | — | 1&1 Internet SE | ES | unknown |
832 | psiphon-tunnel-core.exe | 213.171.197.85:53 | — | 1&1 Internet SE | GB | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
a484.na.akamai.net |
| unknown |
a971.w7.akamai.net |
| suspicious |
global.prod.fastly.com |
| malicious |
a262.gd.akamai.net |
| whitelisted |
cs16.wpc.v0cdn.net |
| unknown |
a780.na.akamai.net |
| suspicious |
prod.global.ssl.fastly.net |
| whitelisted |
| whitelisted | |
a1758.q.akamai.net |
| unknown |
a1852.gd.akamai.net |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
832 | psiphon-tunnel-core.exe | Potential Corporate Privacy Violation | POLICY [PTsecurity] Psiphon3 VPN connection |
832 | psiphon-tunnel-core.exe | Potential Corporate Privacy Violation | POLICY [PTsecurity] Psiphon3 VPN connection |
832 | psiphon-tunnel-core.exe | Potential Corporate Privacy Violation | POLICY [PTsecurity] Psiphon3 VPN connection |
832 | psiphon-tunnel-core.exe | Potential Corporate Privacy Violation | POLICY [PTsecurity] Psiphon3 VPN connection |
832 | psiphon-tunnel-core.exe | Potential Corporate Privacy Violation | POLICY [PTsecurity] Psiphon3 VPN connection |
832 | psiphon-tunnel-core.exe | Potential Corporate Privacy Violation | POLICY [PTsecurity] Psiphon3 VPN connection |
832 | psiphon-tunnel-core.exe | Generic Protocol Command Decode | SURICATA Applayer Mismatch protocol both directions |
832 | psiphon-tunnel-core.exe | Generic Protocol Command Decode | SURICATA HTTP request field missing colon |
832 | psiphon-tunnel-core.exe | Generic Protocol Command Decode | SURICATA HTTP request header invalid |
832 | psiphon-tunnel-core.exe | Generic Protocol Command Decode | SURICATA HTTP URI terminated by non-compliant character |
Process | Message |
|---|---|
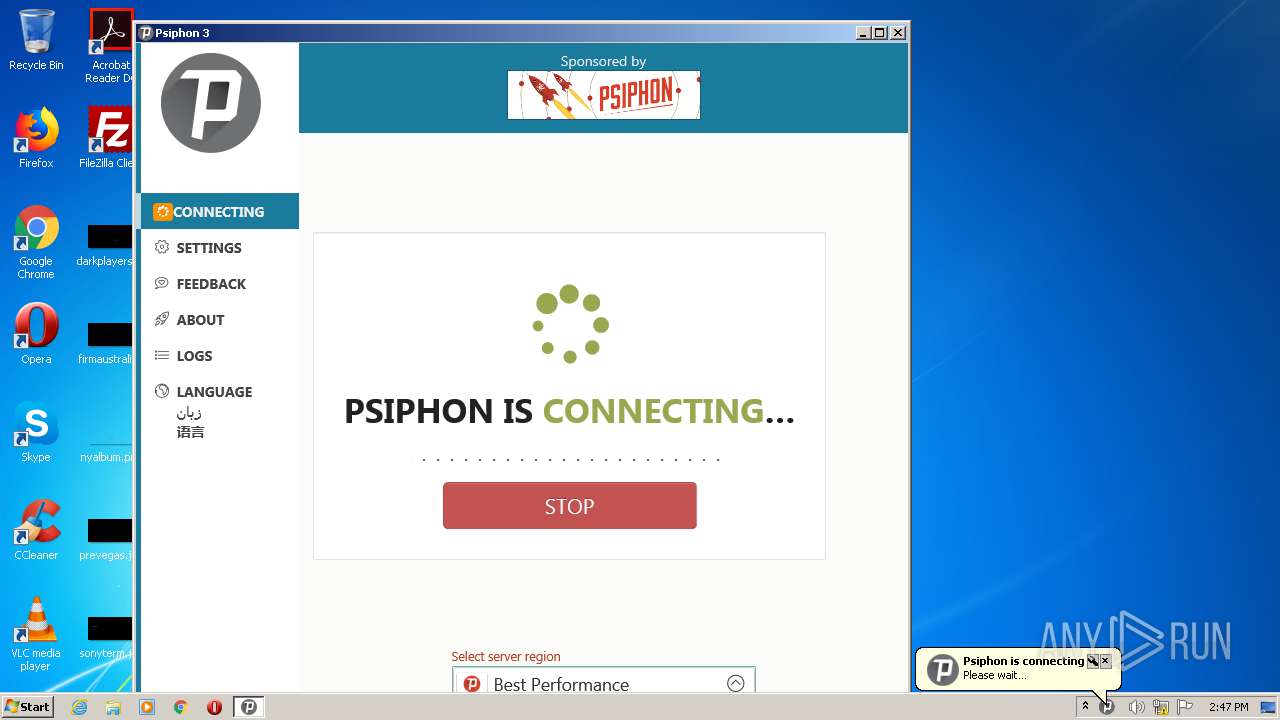
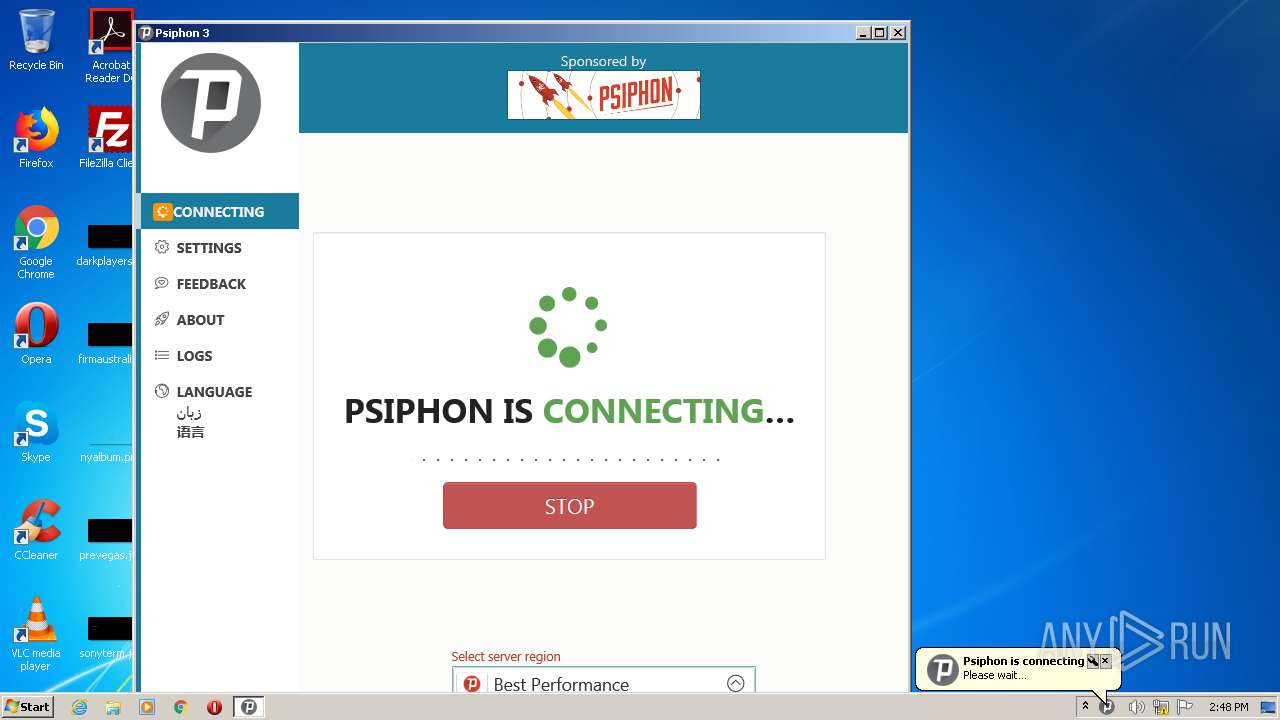
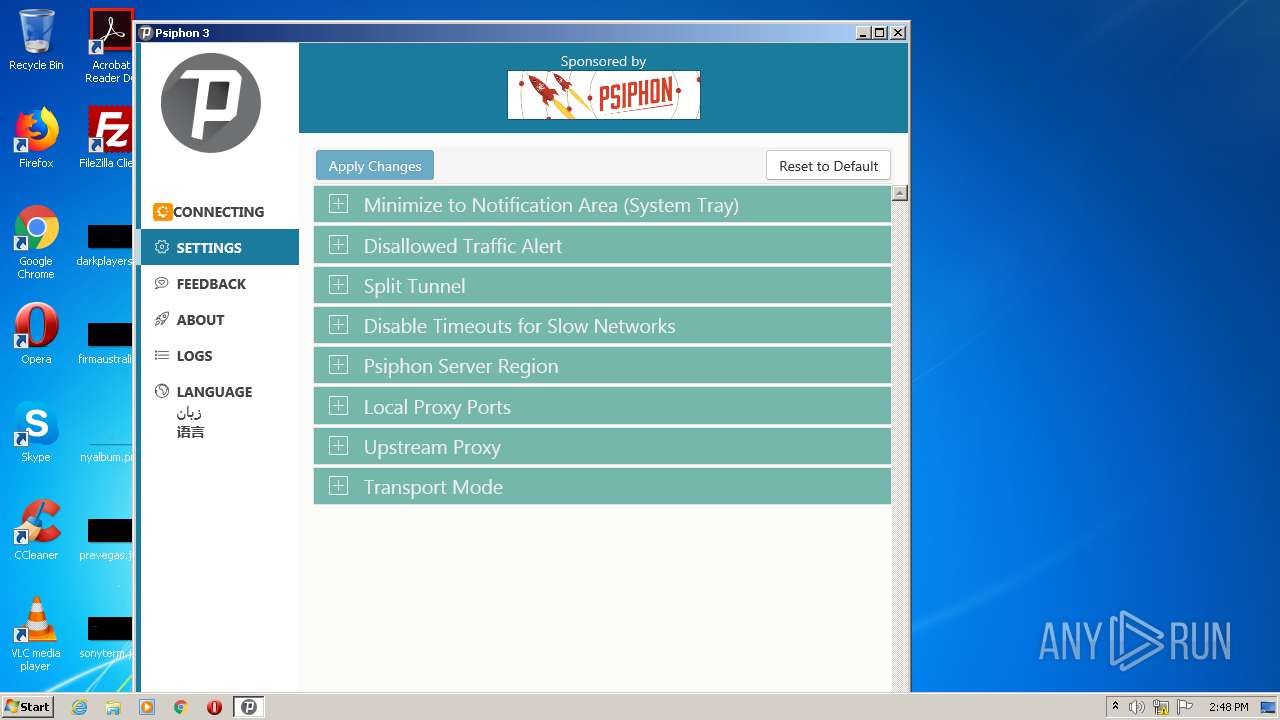
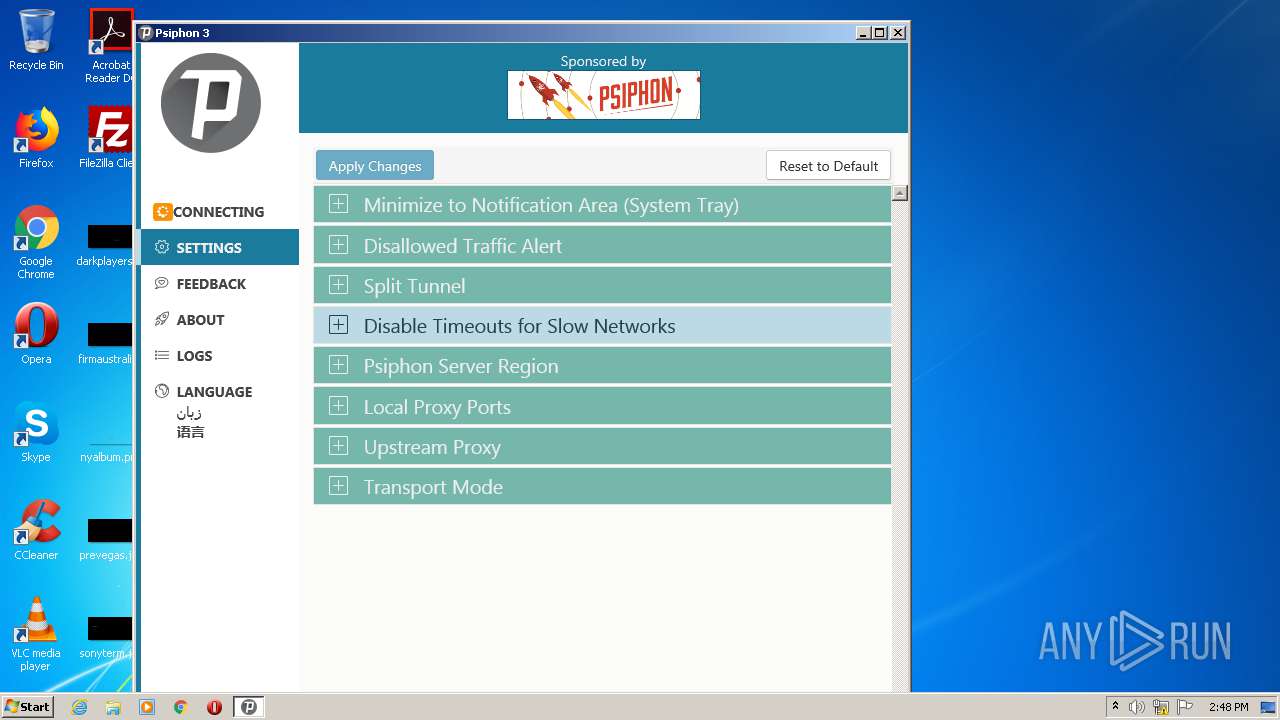
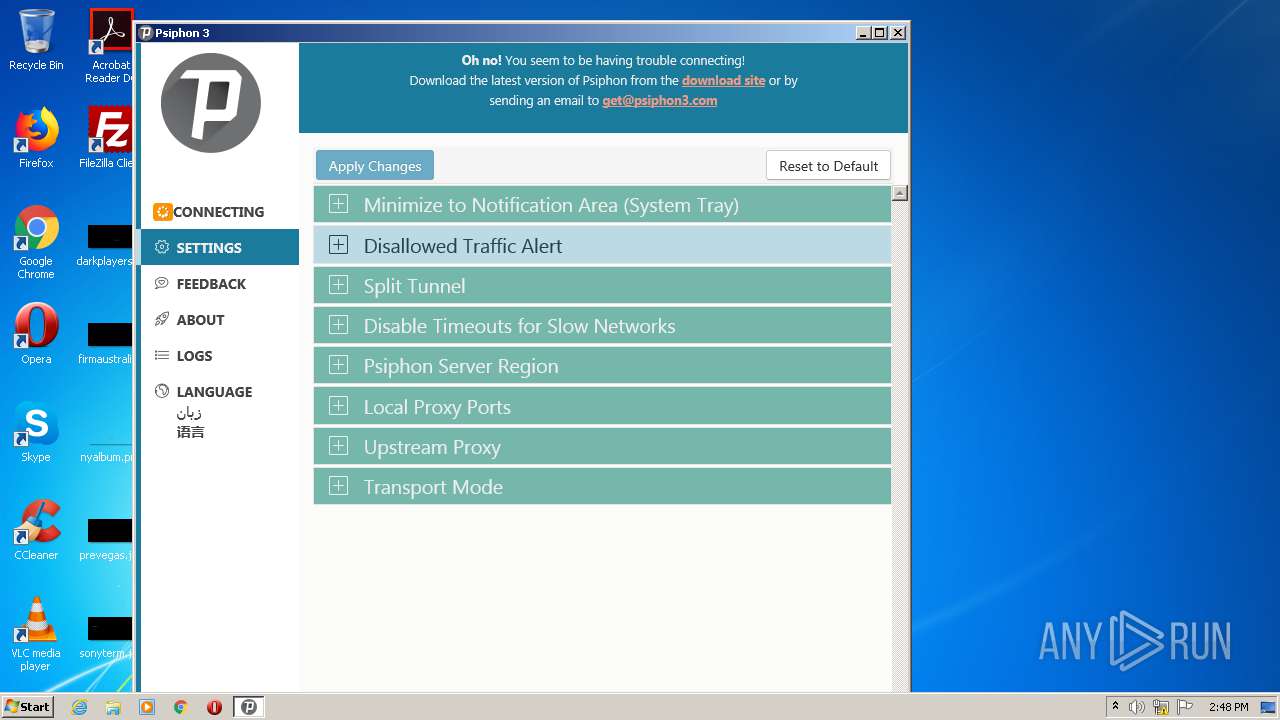
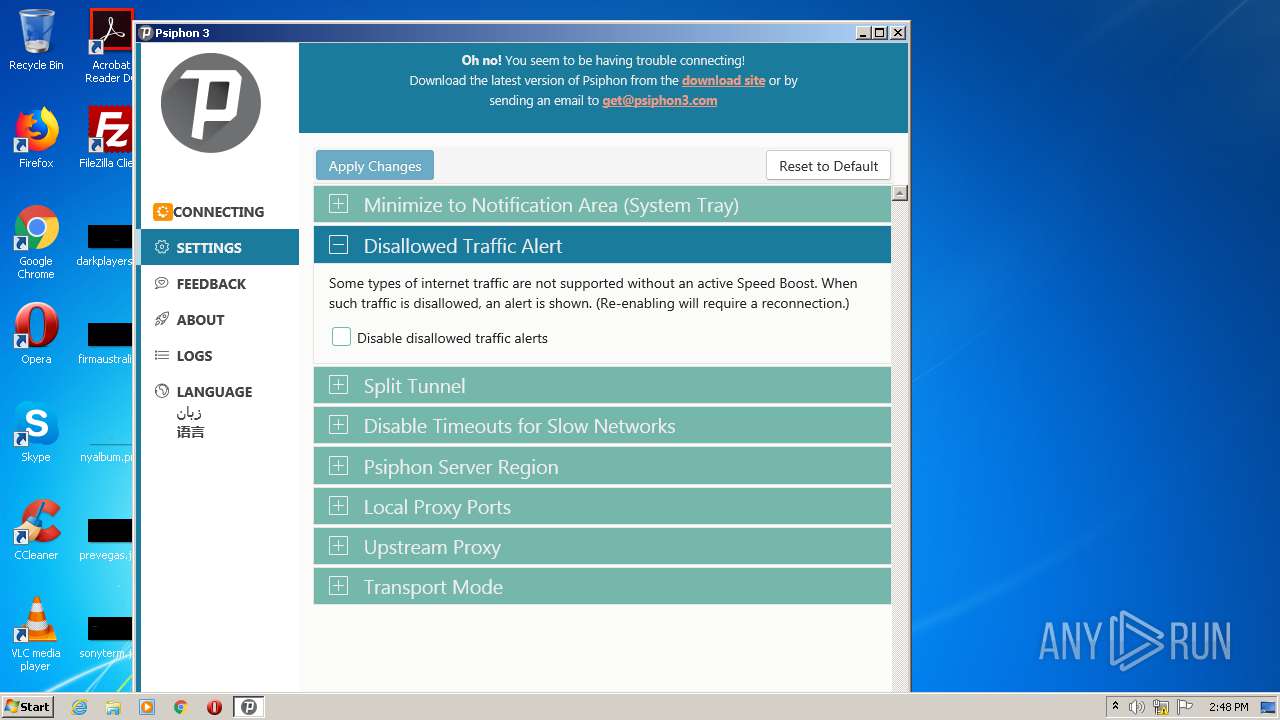
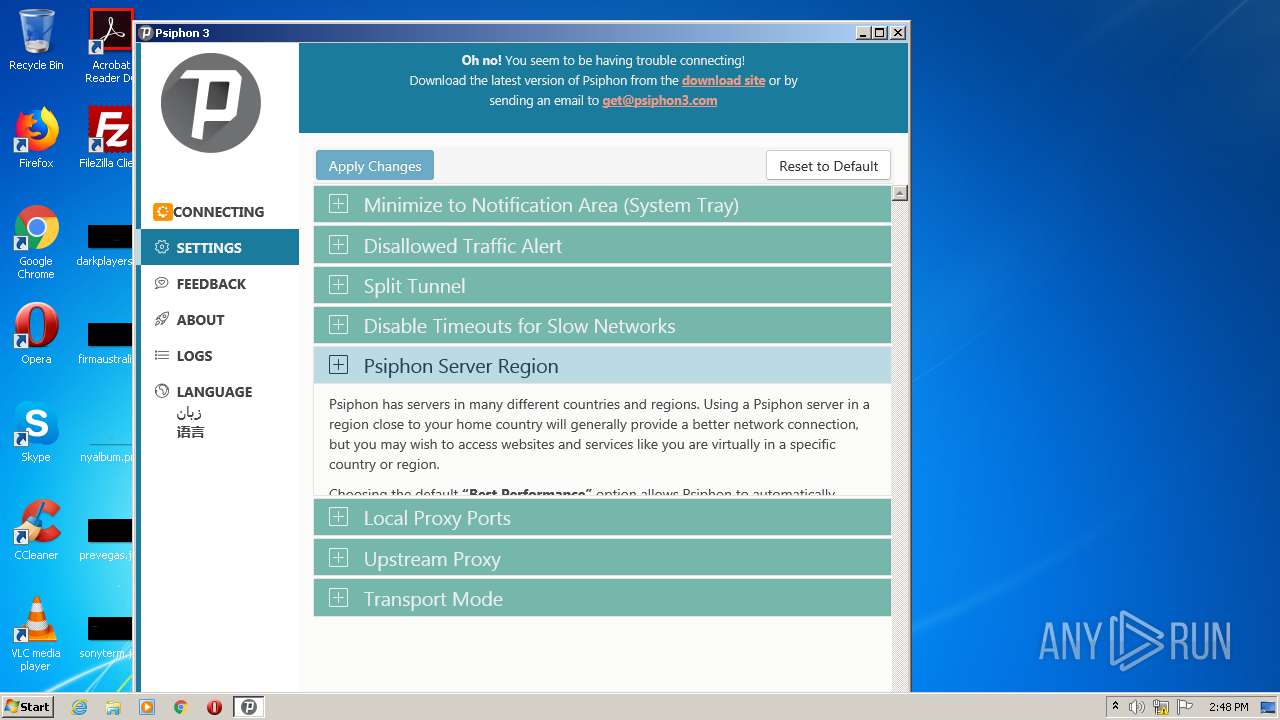
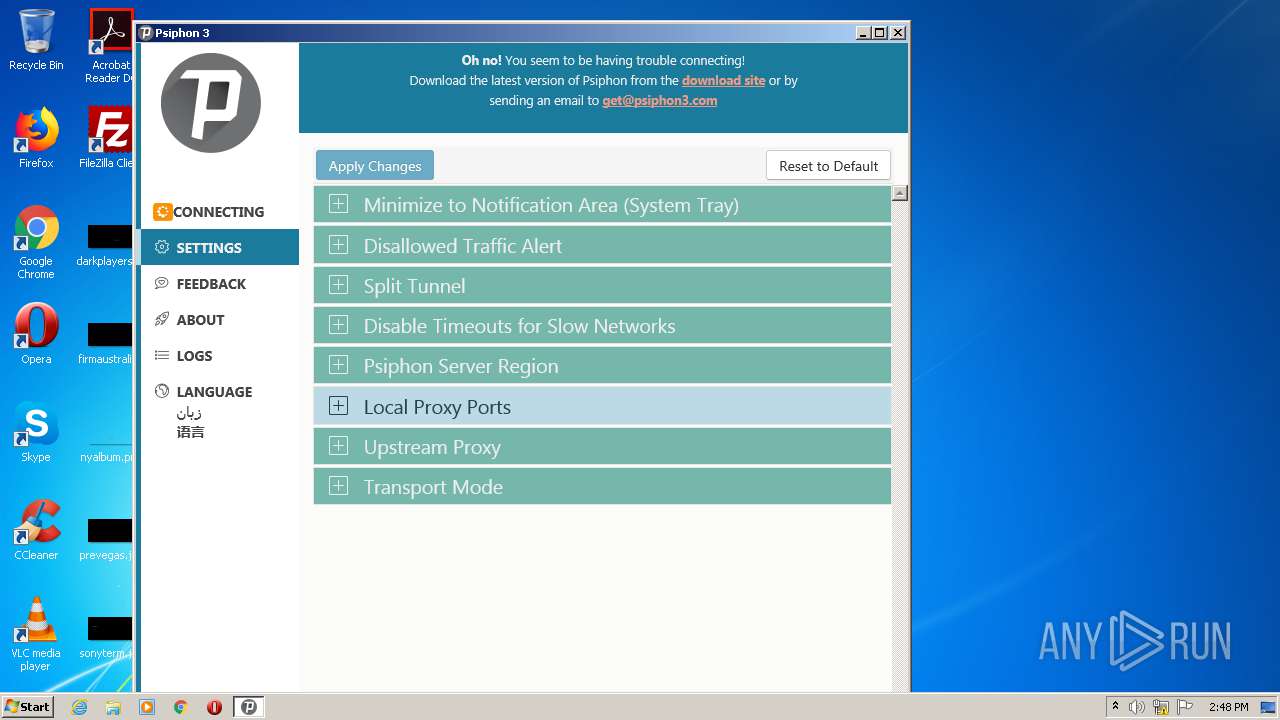
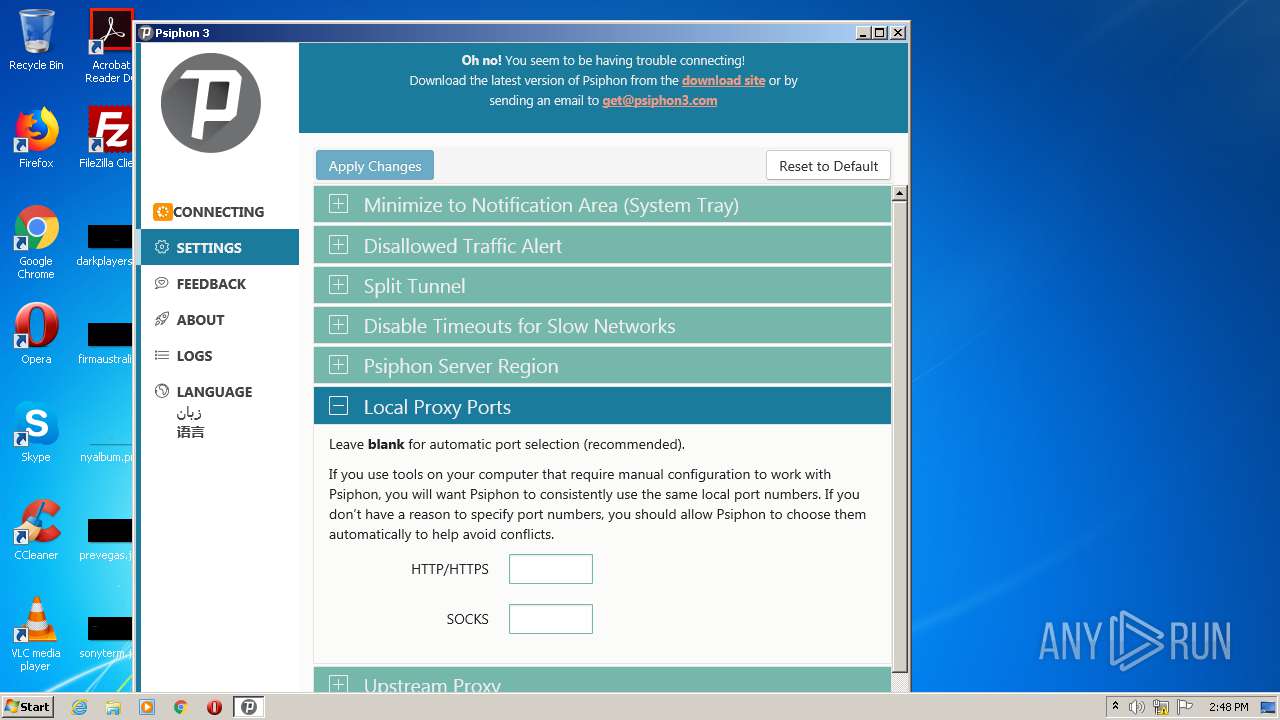
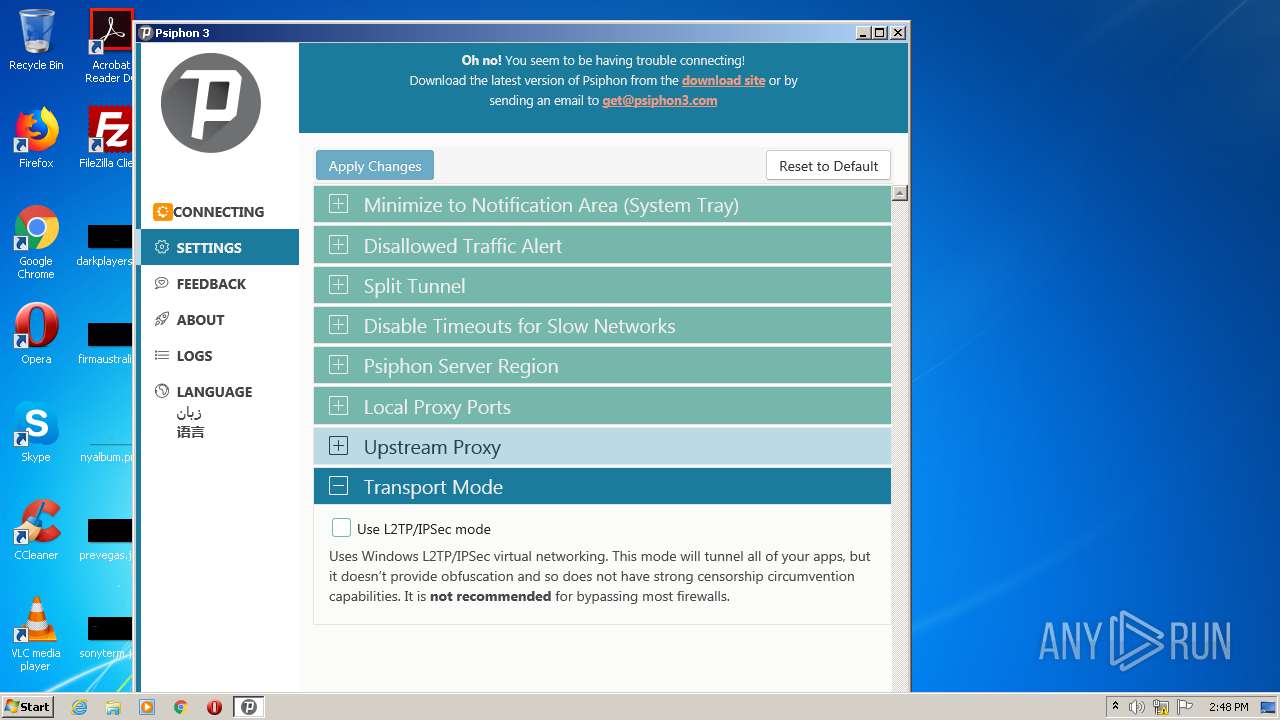
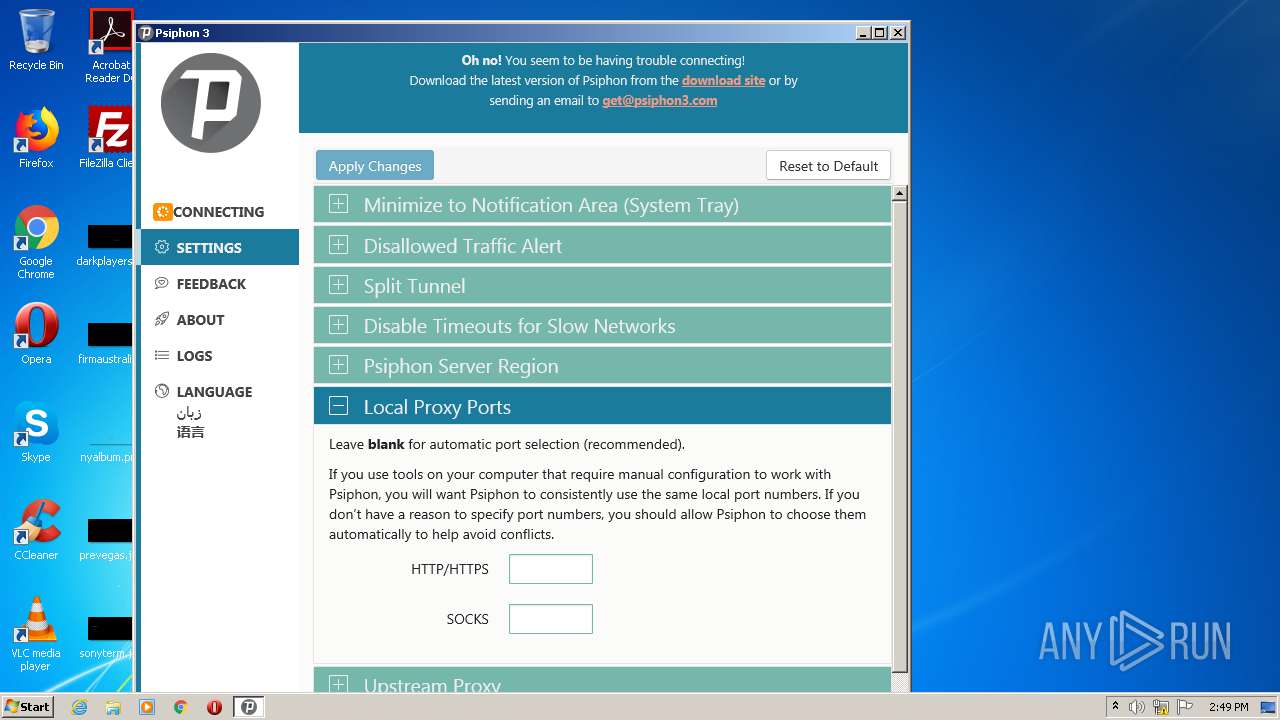
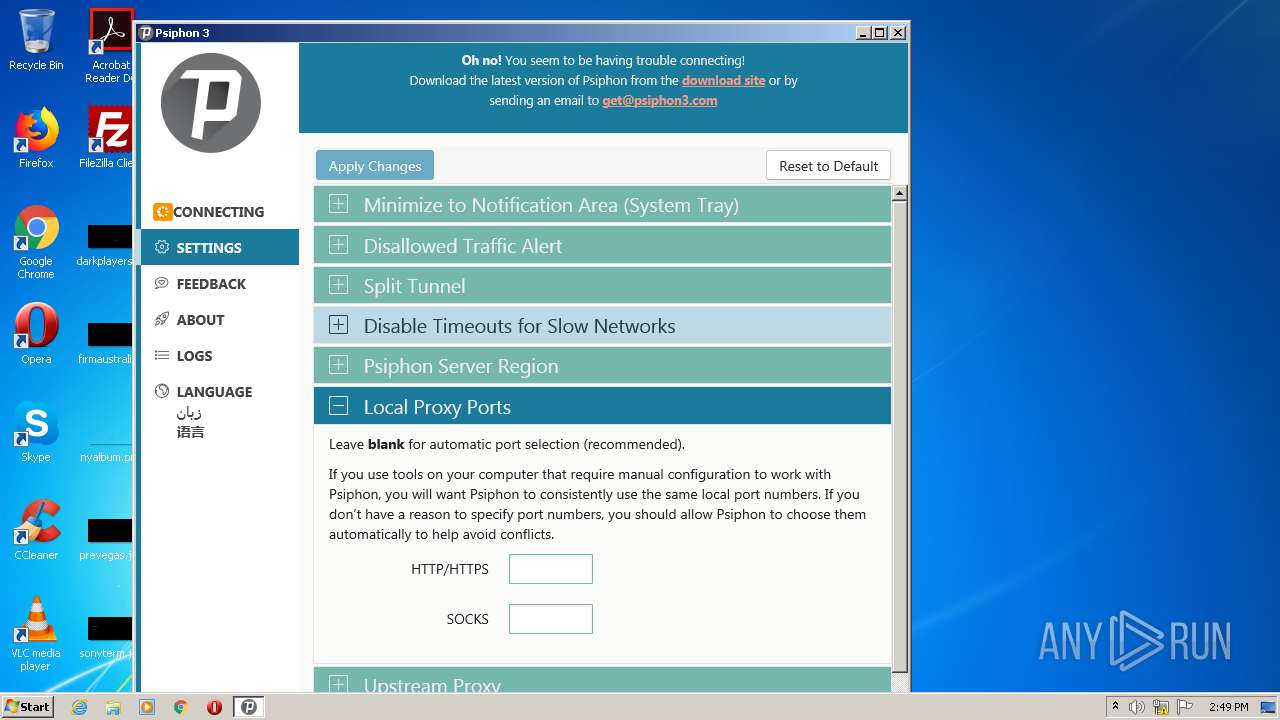
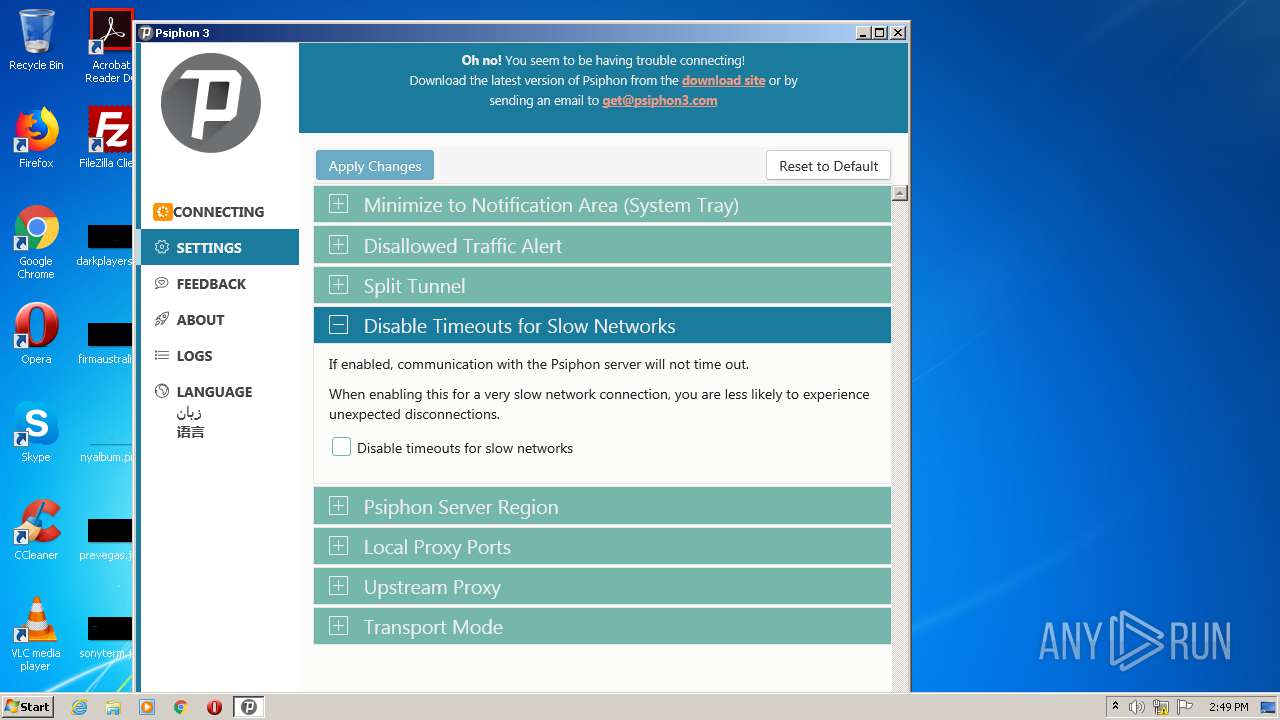
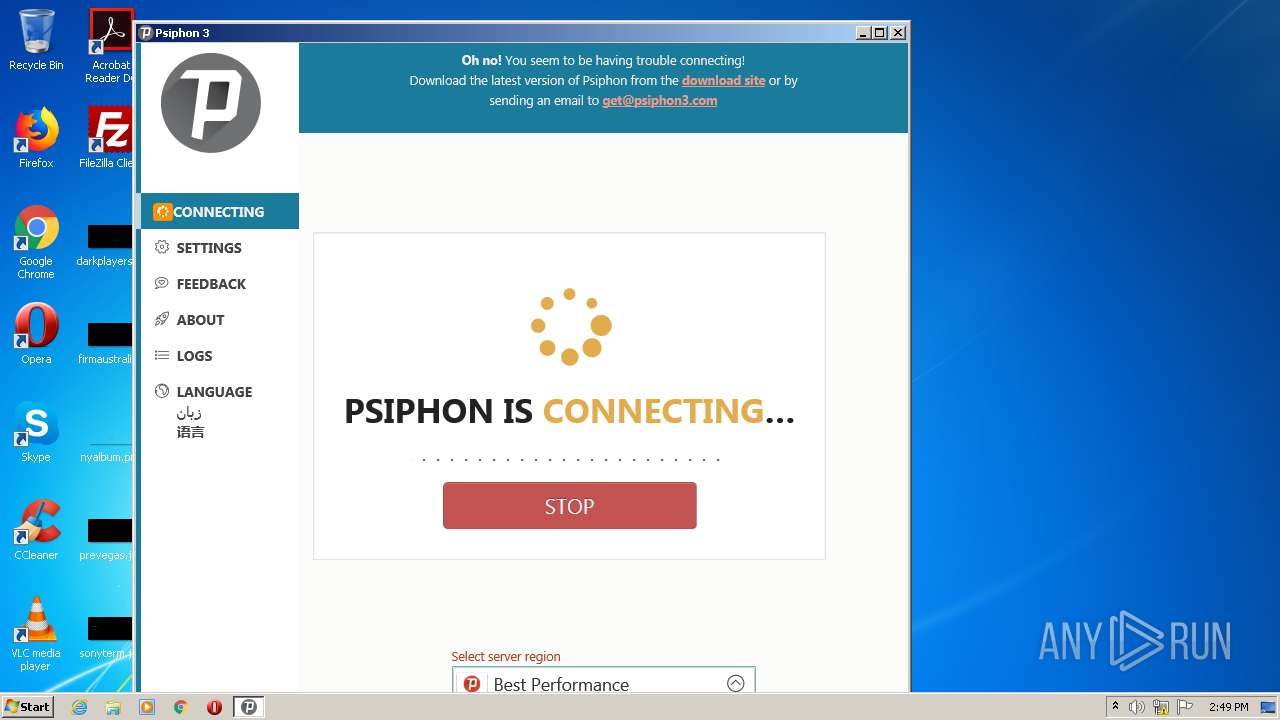
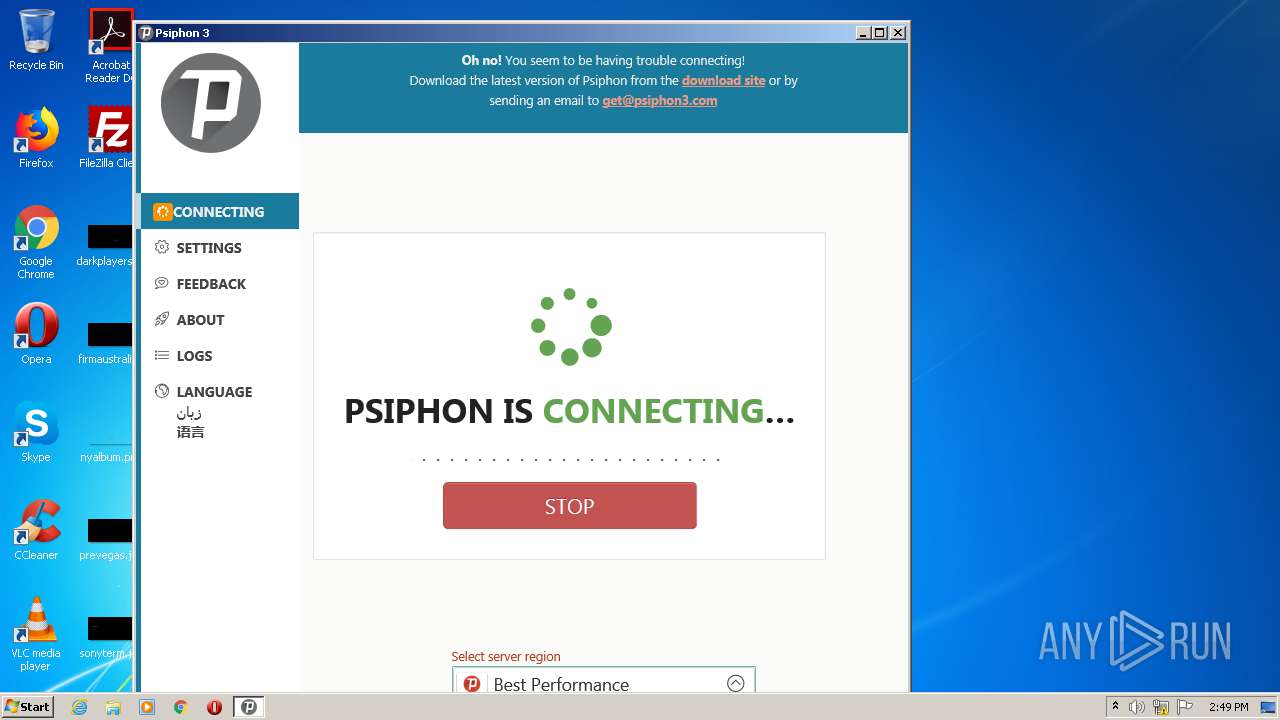
psiphon3(1).exe | 2020-12-12T14:47:43.250Z: |
psiphon3(1).exe | Client Version: 159 |
psiphon3(1).exe | |
psiphon3(1).exe | 2020-12-12T14:47:43.250Z: |
psiphon3(1).exe | Psiphon Tunnel connecting... |
psiphon3(1).exe | |
psiphon3(1).exe | {"data":{"data":{"message":"Config migration: need migration"},"noticeType":"Info","timestamp":"2020-12-12T14:47:43.473Z"},"msg":"CoreNotice","timestamp!!timestamp":"2020-12-12T14:47:43.568Z"}
|
psiphon3(1).exe | |
psiphon3(1).exe | {"data":{"data":{"message":"applied [12] parameters with tag ''"},"noticeType":"Info","timestamp":"2020-12-12T14:47:43.475Z"},"msg":"CoreNotice","timestamp!!timestamp":"2020-12-12T14:47:43.568Z"}
|
psiphon3(1).exe | |