| File name: | uFiler.exe |
| Full analysis: | https://app.any.run/tasks/b15d6ced-4cd0-48a5-9d92-b8f19a20398c |
| Verdict: | Malicious activity |
| Analysis date: | January 20, 2021, 14:09:54 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, UPX compressed |
| MD5: | 7AE50305525802CCD21BFBD548AC32A5 |
| SHA1: | 1BFEB89822F5542BF0368BB0107E0CE89584EE8A |
| SHA256: | DA01B8373BC4963326A28A6E0EB0B88646EFA6B8887C9696EBE6F62C02A7D8B7 |
| SSDEEP: | 196608:IswVKTZhr1BCzHMrovlBooEDCZkU3bzenXpRfIMEdwcrj64:7wVgHr1BCHgodBoJDOX2n56p |
MALICIOUS
Changes the autorun value in the registry
- uFiler.exe (PID: 2276)
Drops executable file immediately after starts
- uFiler.exe (PID: 2276)
Loads dropped or rewritten executable
- uFiler.exe (PID: 2276)
SUSPICIOUS
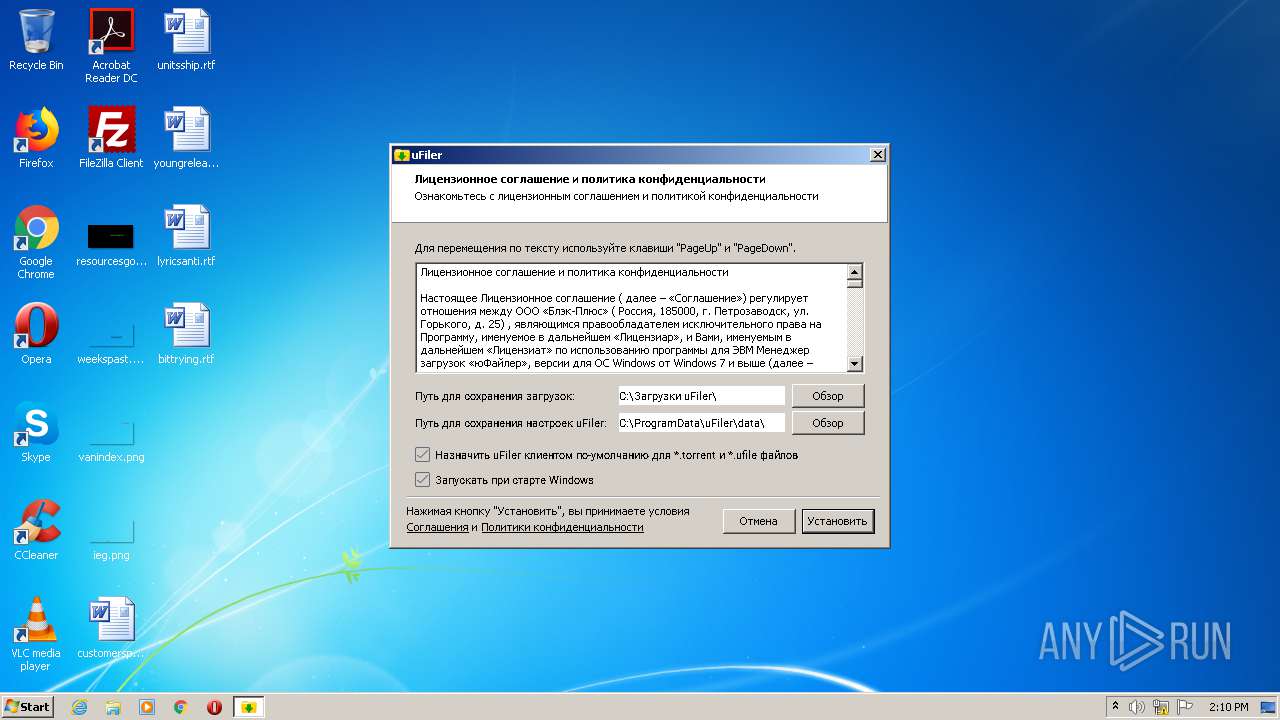
Creates a software uninstall entry
- uFiler.exe (PID: 2144)
Executable content was dropped or overwritten
- uFiler.exe (PID: 2276)
Application launched itself
- uFiler.exe (PID: 2144)
Creates files in the program directory
- uFiler.exe (PID: 2276)
- uFiler.exe (PID: 3436)
Starts CMD.EXE for commands execution
- uFiler.exe (PID: 2276)
Changes default file association
- uFiler.exe (PID: 2276)
Starts itself from another location
- uFiler.exe (PID: 2204)
Drops a file that was compiled in debug mode
- uFiler.exe (PID: 2276)
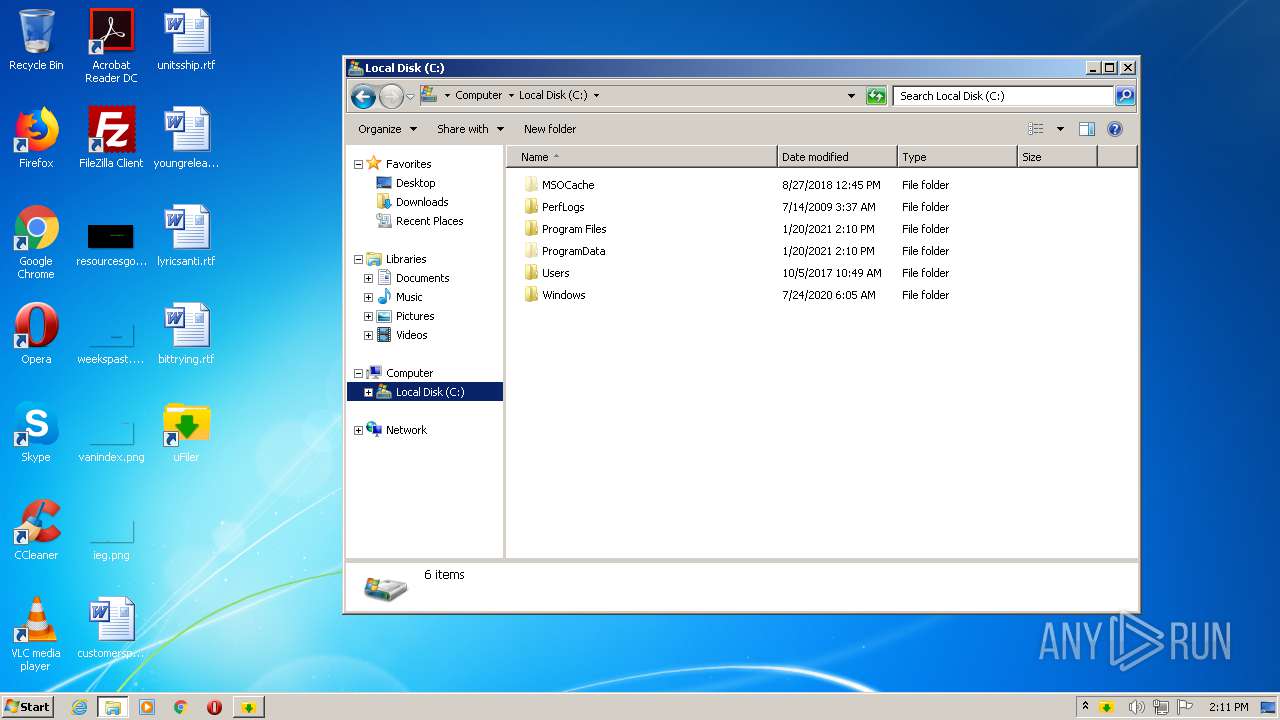
Creates a directory in Program Files
- uFiler.exe (PID: 2276)
INFO
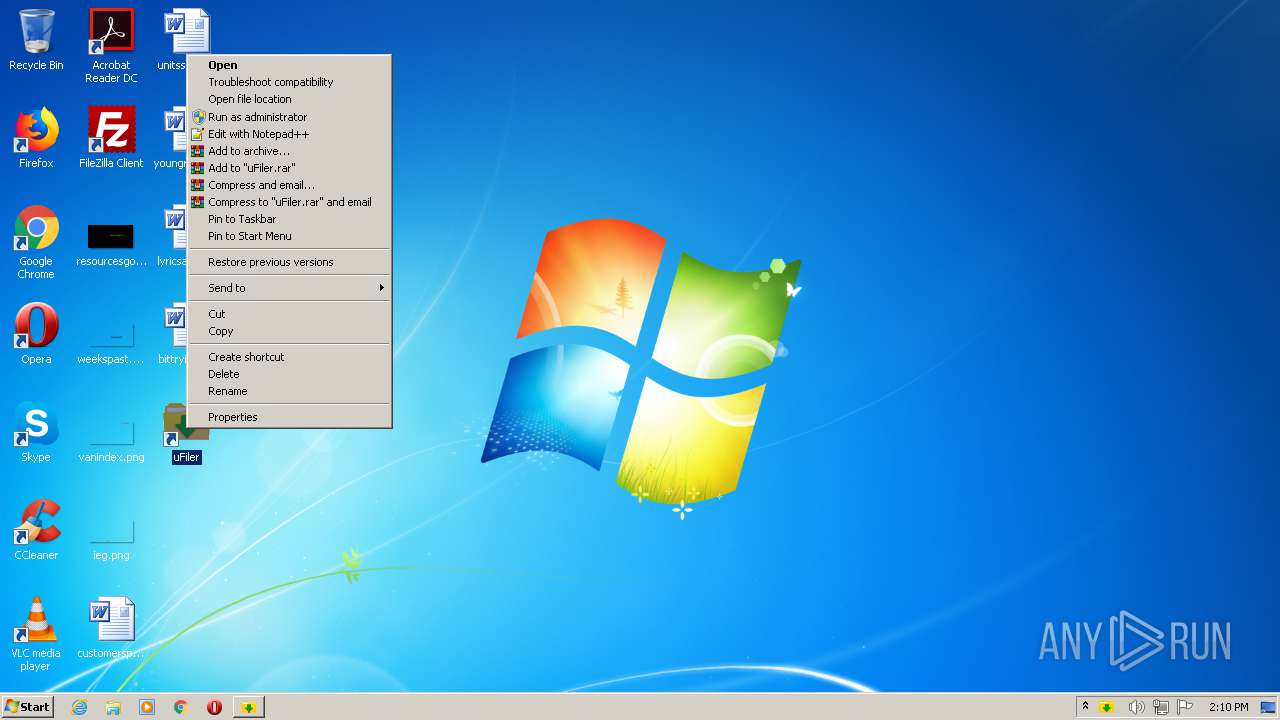
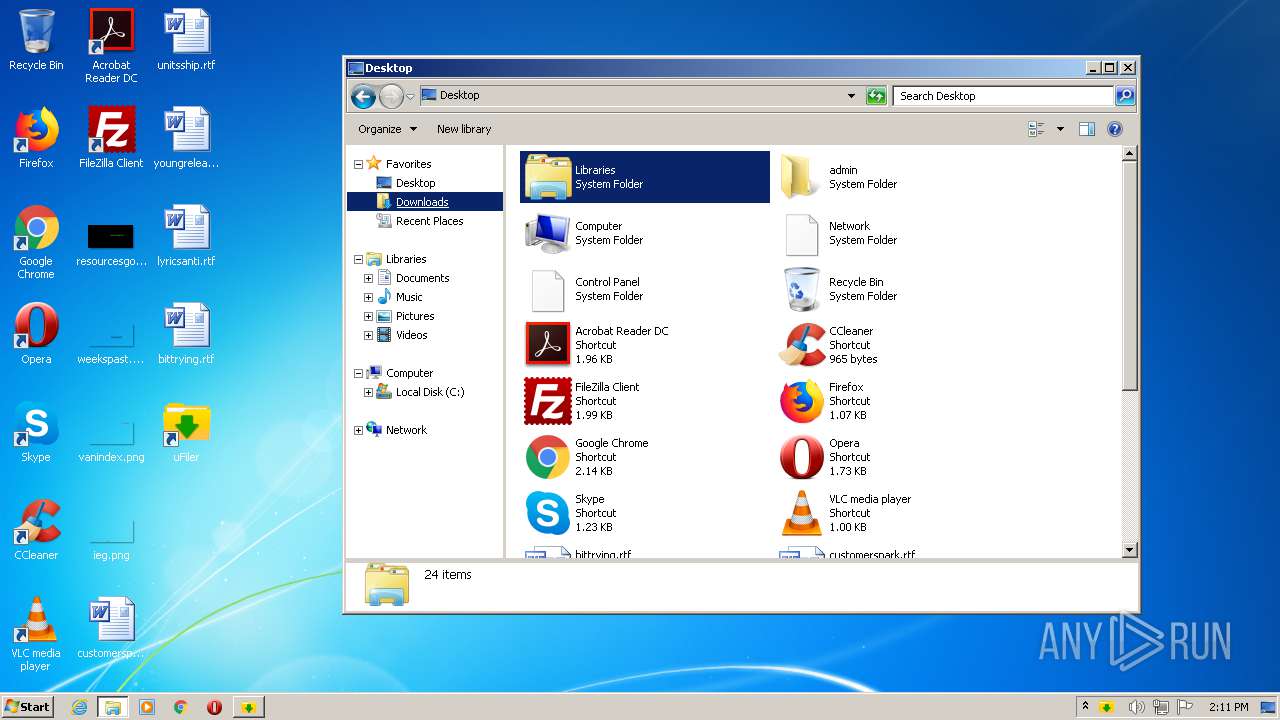
Manual execution by user
- explorer.exe (PID: 2876)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | UPX compressed Win32 Executable (76) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (12.6) |
| .exe | | | Generic Win/DOS Executable (5.6) |
| .exe | | | DOS Executable Generic (5.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2020:10:31 21:20:06+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 8527872 |
| InitializedDataSize: | 131072 |
| UninitializedDataSize: | 17866752 |
| EntryPoint: | 0x192cb00 |
| OSVersion: | 5 |
| ImageVersion: | - |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
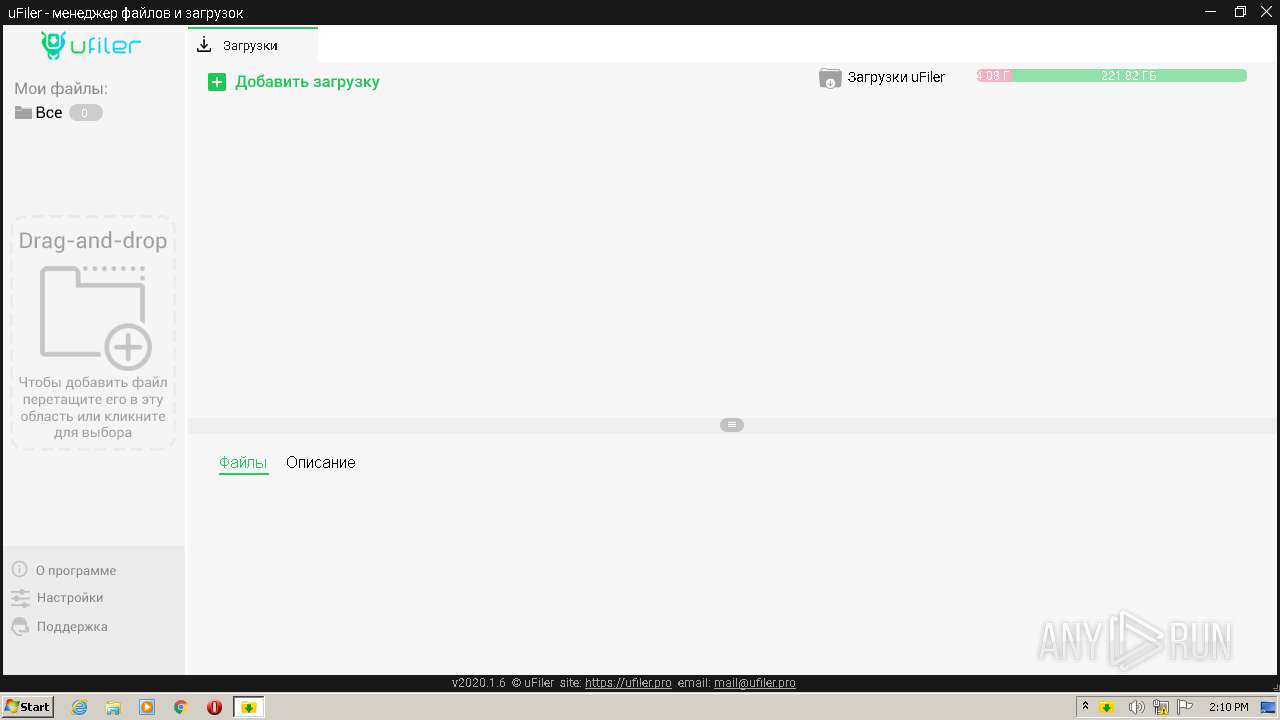
| FileVersionNumber: | 2020.1.6.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| CompanyName: | uFiler.pro |
| FileVersion: | 2020.1.6.0 |
| OriginalFileName: | uFiler.exe |
| ProductName: | uFiler |
| ProductVersion: | 1.0.0 |
| ProgramID: | com.embarcadero.uFiler |
| FileDescription: | uFiler |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 31-Oct-2020 20:20:06 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 31-Oct-2020 20:20:06 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
UPX0 | 0x00001000 | 0x0110A000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
UPX1 | 0x0110B000 | 0x00822000 | 0x00822000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.93484 |
.rsrc | 0x0192D000 | 0x00020000 | 0x0001F800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.36127 |
Imports
KERNEL32.DLL |
PSAPI.dll |
SHFolder.dll |
advapi32.dll |
comctl32.dll |
comdlg32.dll |
d3d9.dll |
gdi32.dll |
mpr.dll |
msvcrt.dll |
Total processes
53
Monitored processes
9
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1940 | "C:\Windows\System32\cmd.exe" /с assoc .ufile=uFiler.ufile | C:\Windows\System32\cmd.exe | — | uFiler.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1988 | "C:\Windows\System32\cmd.exe" /с ftype uFiler.ufile="C:\Program Files\uFiler\uFiler.exe""%1" | C:\Windows\System32\cmd.exe | — | uFiler.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
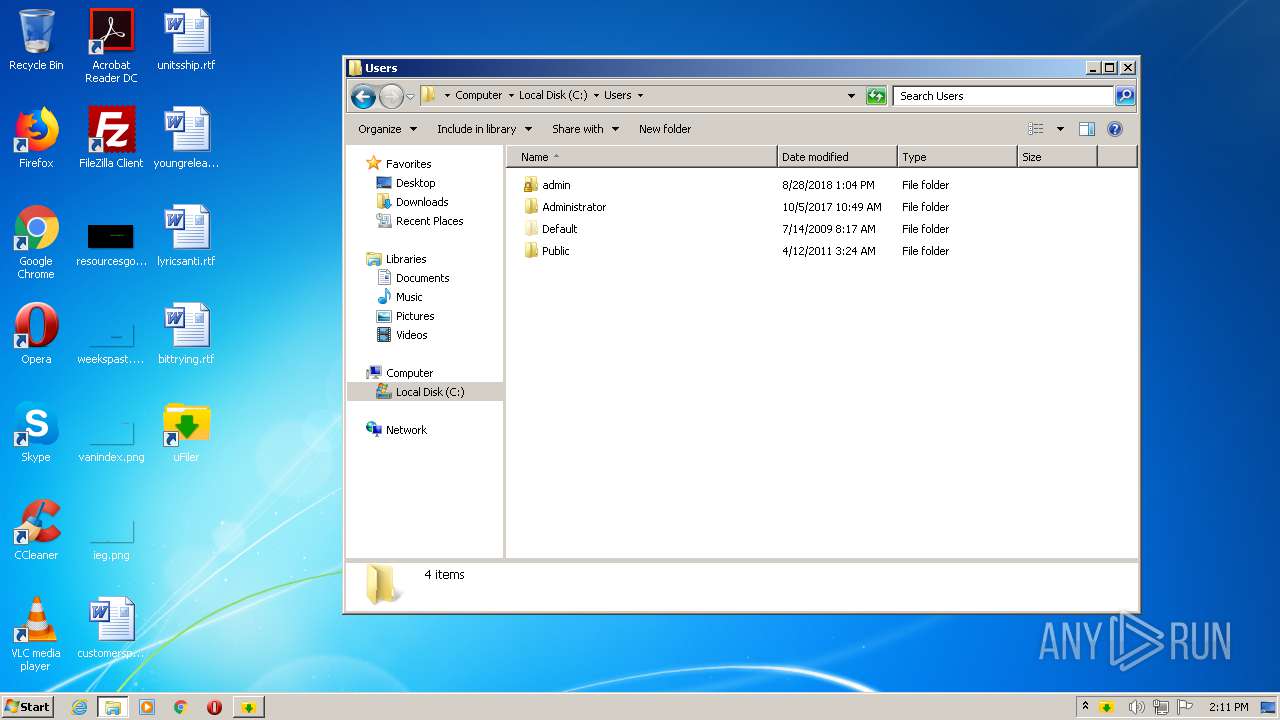
| 2144 | "C:\Users\admin\AppData\Local\Temp\uFiler.exe" | C:\Users\admin\AppData\Local\Temp\uFiler.exe | — | explorer.exe | |||||||||||
User: admin Company: uFiler.pro Integrity Level: MEDIUM Description: uFiler Exit code: 0 Version: 2020.1.6.0 Modules
| |||||||||||||||
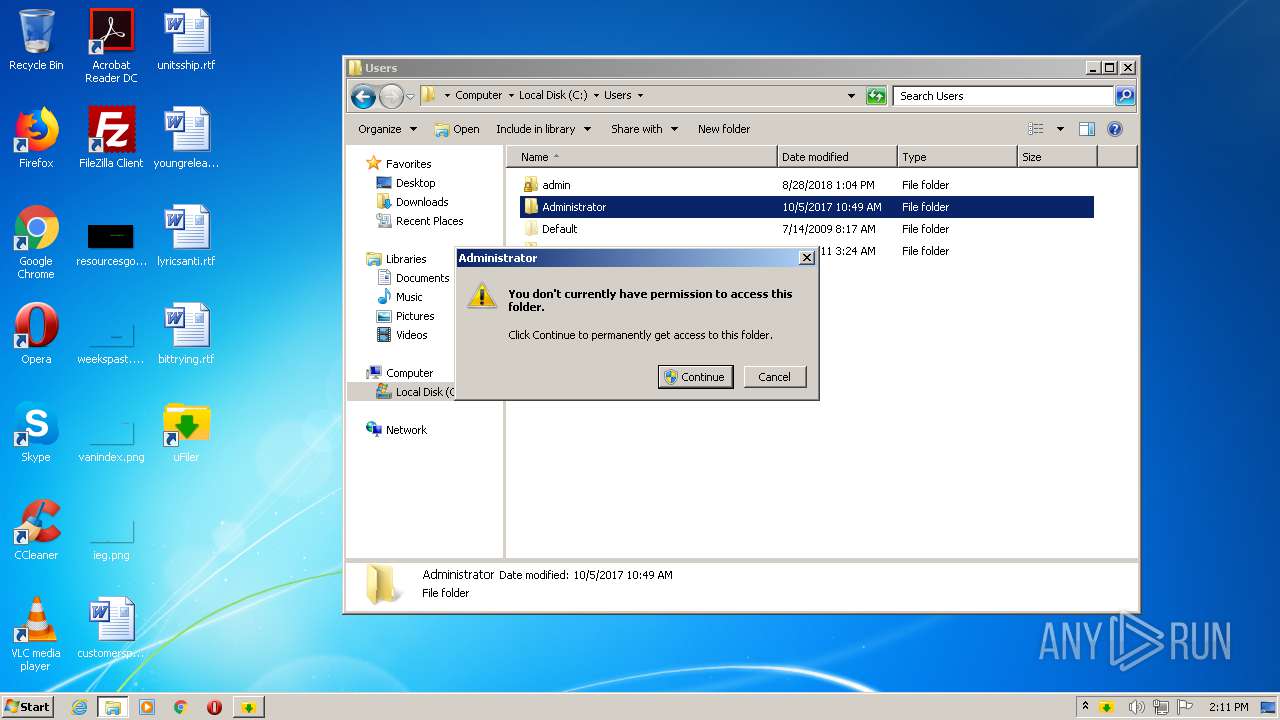
| 2204 | "C:\Users\admin\AppData\Local\Temp\uFiler.exe" | C:\Users\admin\AppData\Local\Temp\uFiler.exe | — | uFiler.exe | |||||||||||
User: admin Company: uFiler.pro Integrity Level: MEDIUM Description: uFiler Exit code: 0 Version: 2020.1.6.0 Modules
| |||||||||||||||
| 2276 | "C:\Users\admin\AppData\Local\Temp\uFiler.exe" -a -pipe | C:\Users\admin\AppData\Local\Temp\uFiler.exe | uFiler.exe | ||||||||||||
User: admin Company: uFiler.pro Integrity Level: HIGH Description: uFiler Exit code: 0 Version: 2020.1.6.0 Modules
| |||||||||||||||
| 2480 | "C:\Windows\System32\cmd.exe" /с ftype uFiler.torrent="C:\Program Files\uFiler\uFiler.exe""%1" | C:\Windows\System32\cmd.exe | — | uFiler.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2496 | "C:\Windows\System32\cmd.exe" /с assoc .torrent=uFiler.torrent | C:\Windows\System32\cmd.exe | — | uFiler.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2876 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3436 | "C:\Program Files\uFiler\uFiler.exe" | C:\Program Files\uFiler\uFiler.exe | uFiler.exe | ||||||||||||
User: admin Company: uFiler.pro Integrity Level: MEDIUM Description: uFiler Exit code: 0 Version: 2020.1.6.0 Modules
| |||||||||||||||
Total events
594
Read events
550
Write events
42
Delete events
2
Modification events
| (PID) Process: | (2144) uFiler.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Direct3D\MostRecentApplication |
| Operation: | write | Name: | Name |
Value: uFiler.exe | |||
| (PID) Process: | (2144) uFiler.exe | Key: | HKEY_CURRENT_USER\Software\uFiler\uFiler |
| Operation: | write | Name: | DataPath |
Value: C:\ProgramData\uFiler\data\ | |||
| (PID) Process: | (2144) uFiler.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2144) uFiler.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2276) uFiler.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Direct3D\MostRecentApplication |
| Operation: | write | Name: | Name |
Value: uFiler.exe | |||
| (PID) Process: | (2144) uFiler.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Uninstall\uFiler |
| Operation: | write | Name: | DisplayName |
Value: uFiler | |||
| (PID) Process: | (2144) uFiler.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Uninstall\uFiler |
| Operation: | write | Name: | Publisher |
Value: uFiler.pro | |||
| (PID) Process: | (2144) uFiler.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Uninstall\uFiler |
| Operation: | write | Name: | UninstallString |
Value: C:\Program Files\uFiler\uFiler.exe -Uninstall | |||
| (PID) Process: | (2144) uFiler.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Uninstall\uFiler |
| Operation: | write | Name: | DisplayIcon |
Value: C:\Program Files\uFiler\uFiler.exe,0 | |||
| (PID) Process: | (2144) uFiler.exe | Key: | HKEY_CURRENT_USER\Software\uFiler\uFiler |
| Operation: | write | Name: | DateInstall |
Value: 44216 | |||
Executable files
4
Suspicious files
0
Text files
0
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3436 | uFiler.exe | C:\ProgramData\uFiler\data\uFiler.db-journal | — | |
MD5:— | SHA256:— | |||
| 2276 | uFiler.exe | C:\Program Files\uFiler\uFiler.exe | executable | |
MD5:— | SHA256:— | |||
| 2144 | uFiler.exe | C:\Users\admin\Desktop\uFiler.lnk | lnk | |
MD5:— | SHA256:— | |||
| 3436 | uFiler.exe | C:\ProgramData\uFiler\data\uFiler.db | sqlite | |
MD5:1DFDF4D6ACE71255FF052053E678CEE3 | SHA256:948A2A0DBC342602C3F28451B3B92B69D7243FE30CAF7E12AA15B03EDD3F88BA | |||
| 2276 | uFiler.exe | C:\Program Files\uFiler\modules\ubtorrent\ubtorrent.dll | executable | |
MD5:0B5BCE0814E24D2FECD2E863FF0885C1 | SHA256:5C1B54F5D799B04D391CA3D1A3C3DF91A064D6E08DD0511F529983D42CA06B7E | |||
| 2276 | uFiler.exe | C:\Program Files\uFiler\modules\ssleay32.dll | executable | |
MD5:5D7476F34764F278852406CDB3BEACB6 | SHA256:DF74479FC4CFF960FAAB94C481DB6B962844E1396716FF5E84FD97EB0FCFA661 | |||
| 2276 | uFiler.exe | C:\Program Files\uFiler\modules\libeay32.dll | executable | |
MD5:900DAFE19A17F2E21729BA1AD2A7DDF2 | SHA256:E970087342A29079BFF6B8B37FE58EBF579FD9BF8B5C0815BDC4231B73F9529F | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
91
DNS requests
2
Threats
1
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3436 | uFiler.exe | 185.157.221.247:25401 | dht.libtorrent.org | — | SE | suspicious |
— | — | 76.174.168.91:6881 | — | Time Warner Cable Internet LLC | US | unknown |
— | — | 85.186.184.113:6881 | — | Liberty Global Operations B.V. | RO | unknown |
— | — | 71.162.192.53:6881 | — | MCI Communications Services, Inc. d/b/a Verizon Business | US | unknown |
— | — | 189.71.247.19:54132 | — | Telemar Norte Leste S.A. | BR | unknown |
— | — | 92.100.203.64:13319 | — | PJSC Rostelecom | RU | unknown |
— | — | 103.101.229.80:6881 | — | — | — | unknown |
— | — | 5.104.59.209:6881 | — | TRK Metro LLC | UA | unknown |
— | — | 147.135.154.60:51413 | — | OVH SAS | FR | unknown |
— | — | 1.243.112.67:41087 | — | SK Broadband Co Ltd | KR | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
dht.libtorrent.org |
| suspicious |
client.api.ufiler.pro |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Potential Corporate Privacy Violation | ET P2P BitTorrent DHT ping request |