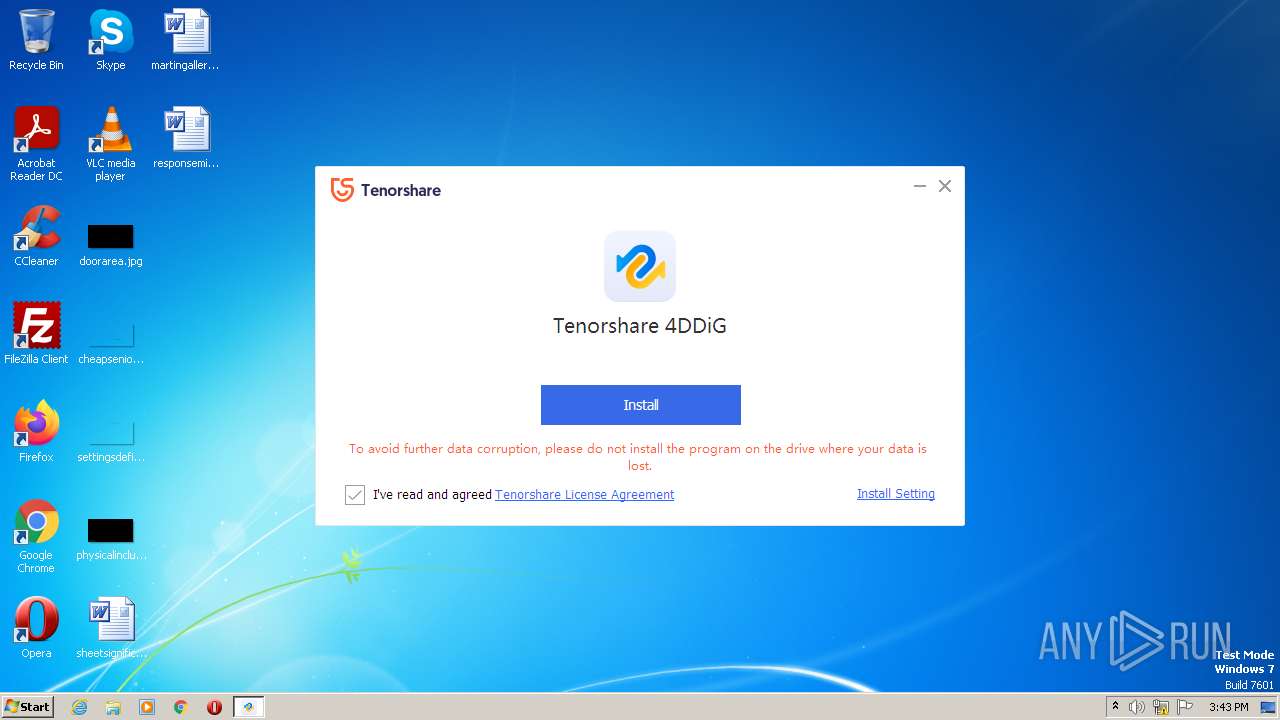
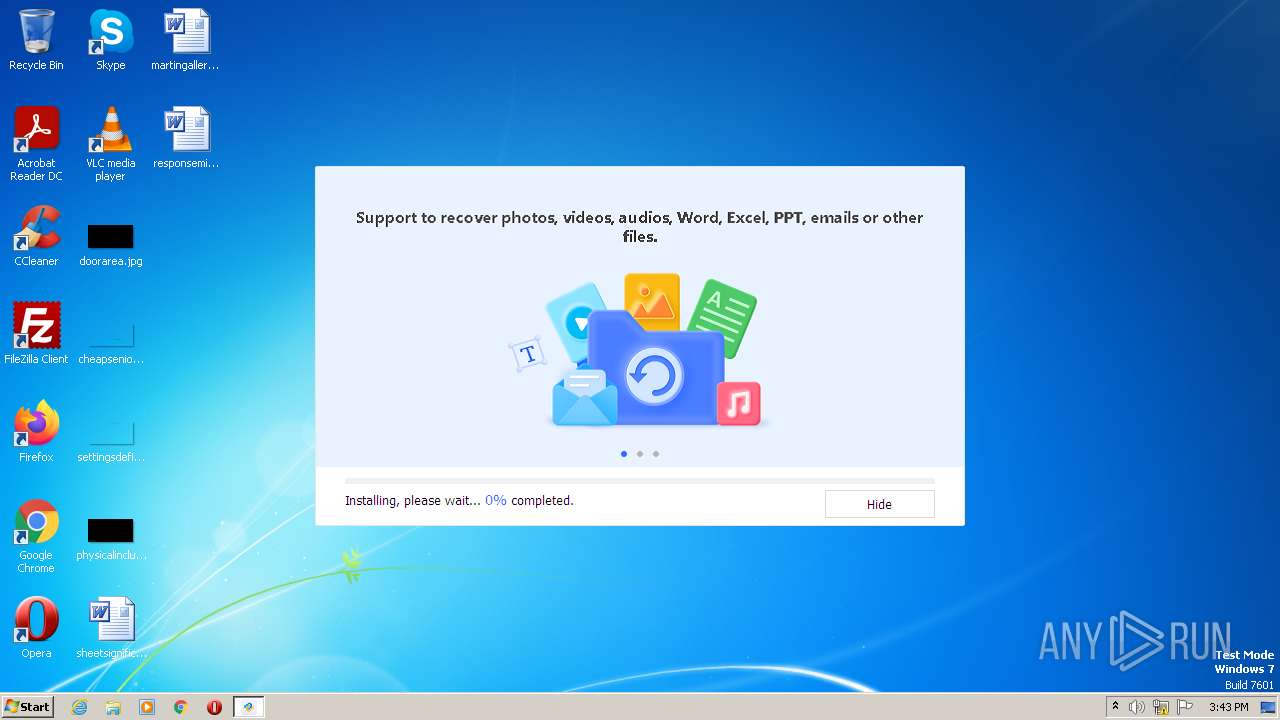
| File name: | tenorshare-4ddig-for-windows.exe |
| Full analysis: | https://app.any.run/tasks/2d6df052-04e3-42a4-bd5b-323d9b75a6dc |
| Verdict: | Malicious activity |
| Analysis date: | March 22, 2023, 15:43:02 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, UPX compressed |
| MD5: | 68B46C56BDF08DDAB45A347441A42DB6 |
| SHA1: | 9C21539F3E1AB37A5F3ADA2F4FCF04880CE44064 |
| SHA256: | D9F6ADEDC7A40DA57ACE46B267318F23532B776446C2FE169038DE4EA81E3F83 |
| SSDEEP: | 49152:CSuGeZU9QdJ5KriX61BG49vWQBowtzmxIca3QySal1uG2iUfpxwGy1f9b1:CSu/W9QnIriEBG49em1tzm6ZQy31r2xu |
MALICIOUS
Connects to the CnC server
- tenorshare-4ddig-for-windows.exe (PID: 3388)
Application was dropped or rewritten from another process
- NetFrameCheck.exe (PID: 2920)
- Tenorshare 4DDiG.exe (PID: 3096)
- Monitor.exe (PID: 2248)
- FrameWorkService.exe (PID: 3064)
- UpdateService.exe (PID: 3648)
SUSPICIOUS
Reads the Internet Settings
- tenorshare-4ddig-for-windows.exe (PID: 3388)
- AnyDataRecovery_net9.4.7.tmp (PID: 2904)
- Tenorshare 4DDiG.exe (PID: 3096)
- NetFrameCheck.exe (PID: 2920)
Reads settings of System Certificates
- tenorshare-4ddig-for-windows.exe (PID: 3388)
- Tenorshare 4DDiG.exe (PID: 3096)
Checks for external IP
- tenorshare-4ddig-for-windows.exe (PID: 3388)
Executable content was dropped or overwritten
- AnyDataRecovery_net9.4.7.exe (PID: 2896)
- AnyDataRecovery_net9.4.7.tmp (PID: 2904)
- Tenorshare 4DDiG.exe (PID: 3096)
- FrameWorkService.exe (PID: 3064)
Reads security settings of Internet Explorer
- tenorshare-4ddig-for-windows.exe (PID: 3388)
- Tenorshare 4DDiG.exe (PID: 3096)
Checks Windows Trust Settings
- tenorshare-4ddig-for-windows.exe (PID: 3388)
- Tenorshare 4DDiG.exe (PID: 3096)
Reads the Windows owner or organization settings
- AnyDataRecovery_net9.4.7.tmp (PID: 2904)
Starts CMD.EXE for commands execution
- AnyDataRecovery_net9.4.7.tmp (PID: 2904)
- Tenorshare 4DDiG.exe (PID: 3096)
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 3216)
- cmd.exe (PID: 2868)
- cmd.exe (PID: 3364)
- cmd.exe (PID: 1936)
- cmd.exe (PID: 2408)
- cmd.exe (PID: 3884)
- cmd.exe (PID: 3896)
- cmd.exe (PID: 1876)
- cmd.exe (PID: 308)
- cmd.exe (PID: 3144)
- cmd.exe (PID: 2320)
- cmd.exe (PID: 3648)
- cmd.exe (PID: 1700)
Uses NETSH.EXE to add a firewall rule or allowed programs
- cmd.exe (PID: 1860)
- cmd.exe (PID: 124)
- cmd.exe (PID: 4048)
- cmd.exe (PID: 2120)
- cmd.exe (PID: 1092)
- cmd.exe (PID: 2272)
- cmd.exe (PID: 4008)
- cmd.exe (PID: 1240)
- cmd.exe (PID: 1468)
- cmd.exe (PID: 1848)
- cmd.exe (PID: 2728)
- cmd.exe (PID: 2372)
- cmd.exe (PID: 2380)
- cmd.exe (PID: 2372)
- cmd.exe (PID: 2780)
- cmd.exe (PID: 584)
- cmd.exe (PID: 3084)
- cmd.exe (PID: 2440)
- cmd.exe (PID: 2428)
- cmd.exe (PID: 3284)
- cmd.exe (PID: 3932)
- cmd.exe (PID: 2916)
Uses NETSH.EXE to delete a firewall rule or allowed programs
- cmd.exe (PID: 2988)
- cmd.exe (PID: 2000)
- cmd.exe (PID: 1164)
- cmd.exe (PID: 3896)
- cmd.exe (PID: 2256)
- cmd.exe (PID: 2060)
- cmd.exe (PID: 2752)
- cmd.exe (PID: 1028)
- cmd.exe (PID: 2772)
- cmd.exe (PID: 3304)
- cmd.exe (PID: 3404)
Searches for installed software
- Tenorshare 4DDiG.exe (PID: 3096)
INFO
The process checks LSA protection
- tenorshare-4ddig-for-windows.exe (PID: 3388)
- AnyDataRecovery_net9.4.7.tmp (PID: 2904)
- taskkill.exe (PID: 3448)
- taskkill.exe (PID: 3504)
- taskkill.exe (PID: 3384)
- taskkill.exe (PID: 600)
- taskkill.exe (PID: 1468)
- taskkill.exe (PID: 2260)
- taskkill.exe (PID: 580)
- taskkill.exe (PID: 936)
- taskkill.exe (PID: 3324)
- taskkill.exe (PID: 952)
- taskkill.exe (PID: 3348)
- netsh.exe (PID: 3408)
- taskkill.exe (PID: 572)
- taskkill.exe (PID: 3524)
- netsh.exe (PID: 2556)
- netsh.exe (PID: 1796)
- netsh.exe (PID: 2820)
- netsh.exe (PID: 1808)
- netsh.exe (PID: 2848)
- netsh.exe (PID: 2484)
- netsh.exe (PID: 2172)
- netsh.exe (PID: 2424)
- netsh.exe (PID: 1744)
- netsh.exe (PID: 2304)
- netsh.exe (PID: 3220)
- netsh.exe (PID: 2512)
- netsh.exe (PID: 2928)
- netsh.exe (PID: 3708)
- netsh.exe (PID: 1896)
- netsh.exe (PID: 2532)
- netsh.exe (PID: 2828)
- netsh.exe (PID: 3460)
- netsh.exe (PID: 3804)
- netsh.exe (PID: 3480)
- netsh.exe (PID: 3020)
- netsh.exe (PID: 4092)
- netsh.exe (PID: 3216)
- netsh.exe (PID: 312)
- netsh.exe (PID: 2788)
- netsh.exe (PID: 3560)
- netsh.exe (PID: 3612)
- netsh.exe (PID: 3616)
- netsh.exe (PID: 1704)
- netsh.exe (PID: 3660)
- netsh.exe (PID: 3348)
- netsh.exe (PID: 3088)
- NetFrameCheck.exe (PID: 2920)
- Tenorshare 4DDiG.exe (PID: 3096)
Checks supported languages
- tenorshare-4ddig-for-windows.exe (PID: 3388)
- AnyDataRecovery_net9.4.7.tmp (PID: 2904)
- AnyDataRecovery_net9.4.7.exe (PID: 2896)
- NetFrameCheck.exe (PID: 2920)
- Tenorshare 4DDiG.exe (PID: 3096)
Reads the computer name
- tenorshare-4ddig-for-windows.exe (PID: 3388)
- AnyDataRecovery_net9.4.7.tmp (PID: 2904)
- NetFrameCheck.exe (PID: 2920)
- Tenorshare 4DDiG.exe (PID: 3096)
Checks proxy server information
- tenorshare-4ddig-for-windows.exe (PID: 3388)
Reads the machine GUID from the registry
- tenorshare-4ddig-for-windows.exe (PID: 3388)
- Tenorshare 4DDiG.exe (PID: 3096)
Creates files in the program directory
- tenorshare-4ddig-for-windows.exe (PID: 3388)
- AnyDataRecovery_net9.4.7.tmp (PID: 2904)
- Tenorshare 4DDiG.exe (PID: 3096)
- NetFrameCheck.exe (PID: 2920)
Reads Environment values
- tenorshare-4ddig-for-windows.exe (PID: 3388)
Create files in a temporary directory
- AnyDataRecovery_net9.4.7.tmp (PID: 2904)
- AnyDataRecovery_net9.4.7.exe (PID: 2896)
- tenorshare-4ddig-for-windows.exe (PID: 3388)
- Tenorshare 4DDiG.exe (PID: 3096)
Creates files or folders in the user directory
- tenorshare-4ddig-for-windows.exe (PID: 3388)
Application was dropped or rewritten from another process
- AnyDataRecovery_net9.4.7.tmp (PID: 2904)
Application launched itself
- iexplore.exe (PID: 3228)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | UPX compressed Win32 Executable (76) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (12.6) |
| .exe | | | Generic Win/DOS Executable (5.6) |
| .exe | | | DOS Executable Generic (5.6) |
EXIF
EXE
| ProductVersion: | 2.6.7.0 |
|---|---|
| ProductName: | 20221104103053 |
| LegalCopyright: | Copyright © 2007-2022 Tenorshare Co.,Ltd. |
| FileVersion: | 2.6.7.0 |
| FileDescription: | Tenorshare 4DDiG |
| CompanyName: | Tenorshare Co., Ltd. |
| CharacterSet: | Windows, Latin1 |
| LanguageCode: | English (U.S.) |
| FileSubtype: | - |
| ObjectFileType: | Executable application |
| FileOS: | Win32 |
| FileFlags: | (none) |
| FileFlagsMask: | 0x003f |
| ProductVersionNumber: | 2.6.7.0 |
| FileVersionNumber: | 2.6.7.0 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 5.1 |
| ImageVersion: | - |
| OSVersion: | 5.1 |
| EntryPoint: | 0x3f0570 |
| UninitializedDataSize: | 2449408 |
| InitializedDataSize: | 630784 |
| CodeSize: | 1679360 |
| LinkerVersion: | 14 |
| PEType: | PE32 |
| ImageFileCharacteristics: | Executable, 32-bit |
| TimeStamp: | 2022:11:04 02:31:17+00:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 04-Nov-2022 02:31:17 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000158 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 04-Nov-2022 02:31:17 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
UPX0 | 0x00001000 | 0x00256000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
UPX1 | 0x00257000 | 0x0019A000 | 0x00199800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.90853 |
.rsrc | 0x003F1000 | 0x0009A000 | 0x00099E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.35595 |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
IMM32.dll |
IPHLPAPI.DLL |
KERNEL32.DLL |
OLEAUT32.dll |
SHELL32.dll |
SHLWAPI.dll |
SensApi.dll |
Total processes
206
Monitored processes
109
Malicious processes
5
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 124 | "C:\Windows\system32\cmd.exe" /c netsh advfirewall firewall add rule name="Tenorshare 4DDiG" dir=out action=allow program="C:\Program Files\Tenorshare\Tenorshare 4DDiG\Tenorshare 4DDiG.exe" enable=yes | C:\Windows\System32\cmd.exe | — | AnyDataRecovery_net9.4.7.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 308 | "C:\Windows\system32\cmd.exe" /c taskkill /f /t /im "FrameWorkService.exe" | C:\Windows\System32\cmd.exe | — | AnyDataRecovery_net9.4.7.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 128 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 312 | netsh advfirewall firewall add rule name="Tenorshare 4DDiG_FrameWorkService" dir=out action=allow program="C:\Program Files\Tenorshare\Tenorshare 4DDiG\FrameWorkService.exe" enable=yes | C:\Windows\System32\netsh.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 572 | taskkill /f /t /im "MediaPlayerService.exe" | C:\Windows\System32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 580 | taskkill /f /t /im "FrameWorkService.exe" | C:\Windows\System32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 584 | "C:\Windows\system32\cmd.exe" /c netsh advfirewall firewall add rule name="Tenorshare 4DDiG_PhotosRepairService" dir=out action=allow program="C:\Program Files\Tenorshare\Tenorshare 4DDiG\PhotosRepairService.exe" enable=yes | C:\Windows\System32\cmd.exe | — | AnyDataRecovery_net9.4.7.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 600 | taskkill /f /t /im "DebugRecord.exe" | C:\Windows\System32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 936 | taskkill /f /t /im "SuperResolution.exe" | C:\Windows\System32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 952 | taskkill /f /t /im "ParseRecord.exe" | C:\Windows\System32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1028 | "C:\Windows\system32\cmd.exe" /c netsh advfirewall firewall delete rule name=all program="C:\Program Files\Tenorshare\Tenorshare 4DDiG\MediaPlayerService.exe" | C:\Windows\System32\cmd.exe | — | AnyDataRecovery_net9.4.7.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
54 605
Read events
51 355
Write events
3 238
Delete events
12
Modification events
| (PID) Process: | (3388) tenorshare-4ddig-for-windows.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3388) tenorshare-4ddig-for-windows.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 460000003D010000090000000000000000000000000000000400000000000000C0E333BBEAB1D3010000000000000000000000000100000002000000C0A80164000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3388) tenorshare-4ddig-for-windows.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3388) tenorshare-4ddig-for-windows.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3388) tenorshare-4ddig-for-windows.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3388) tenorshare-4ddig-for-windows.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (3388) tenorshare-4ddig-for-windows.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3388) tenorshare-4ddig-for-windows.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3388) tenorshare-4ddig-for-windows.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Wpad\{FCC67766-6201-4AD1-A6B8-2F4553C93D47} |
| Operation: | write | Name: | WpadDecisionReason |
Value: 1 | |||
| (PID) Process: | (3388) tenorshare-4ddig-for-windows.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Wpad\{FCC67766-6201-4AD1-A6B8-2F4553C93D47} |
| Operation: | write | Name: | WpadDecisionTime |
Value: 70EC6201D55CD901 | |||
Executable files
1 228
Suspicious files
1 217
Text files
222
Unknown types
60
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3388 | tenorshare-4ddig-for-windows.exe | C:\Users\admin\AppData\Local\Temp\AnyDataRecovery_net\AnyDataRecovery_net9.4.7.exe | — | |
MD5:— | SHA256:— | |||
| 3388 | tenorshare-4ddig-for-windows.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\FBWMIFKC.txt | text | |
MD5:5342B9B1EB4B915B70EEE19A1562F636 | SHA256:FC117BEDBDD02148D74CAF7F4D27ACA3C498D678BC650D312E6CDFA5CA65ED97 | |||
| 3388 | tenorshare-4ddig-for-windows.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\9QYTRNRA.txt | text | |
MD5:1F756F59FA749C0D3A7FD1397DA997A7 | SHA256:63FE35A65B6CC0AFF809C3CAFF140DF9B5FD31F561452285E161DD9C73FAD448 | |||
| 3388 | tenorshare-4ddig-for-windows.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\HCA81DN4.txt | text | |
MD5:83728081F03EC85A99BEFDB237359B61 | SHA256:704B60C5084E1D9C30CA9F18176B15361000BB6CDDF703B4B2BE27D48E16A899 | |||
| 3388 | tenorshare-4ddig-for-windows.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6BADA8974A10C4BD62CC921D13E43B18_28DEA62A0AE77228DD387E155AD0BA27 | binary | |
MD5:625983BA285FD976438AAAB56A83618B | SHA256:CAF9913A88B4626B983ED0C28C262EE23A41B999339555F981BF689BDC526BF6 | |||
| 3388 | tenorshare-4ddig-for-windows.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\80237EE4964FC9C409AAF55BF996A292_FB287BEB63DB9E8D59A799779773B97C | der | |
MD5:519E332DACB0952C2D1D9EF295FE316D | SHA256:BB2FAD41B5B94E9B837675923B67C8680C8A8880006971B990C3E366B0B4C5C8 | |||
| 3388 | tenorshare-4ddig-for-windows.exe | C:\Users\admin\AppData\Local\Temp\TS_GetDownloaderInfo.log | text | |
MD5:D0E8D2442C0C9C09FE5A610F75BA08C8 | SHA256:BB5ABEA5CE2F565461F8A8D454C99F572A635F4763018D4891994DAC8BB60DD9 | |||
| 3388 | tenorshare-4ddig-for-windows.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:71573E592C03BD3DF2803113AD59FE97 | SHA256:C1DA60213D35E23B24BC2A4F8614204CE92EA35F6C5FDDB73DFA3CB9BEBFCCC4 | |||
| 3388 | tenorshare-4ddig-for-windows.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6BADA8974A10C4BD62CC921D13E43B18_28DEA62A0AE77228DD387E155AD0BA27 | der | |
MD5:6425565C73A4AD3508C5754BEF1AFF58 | SHA256:5E89D837C0C0CF3B0C8C6697C7D22C06D7EB9F089706D08A5AA927FFB84B4B49 | |||
| 3388 | tenorshare-4ddig-for-windows.exe | C:\Users\admin\AppData\Local\Temp\AnyDataRecovery_net\AnyDataRecovery_net9.4.7.exe.xml | text | |
MD5:8B4C29F10AD5C6910357F8C4DF3AF821 | SHA256:B3D0C6D374A314707433F59A82CA1E5BD0436D85E2DD58F57641CDACB521ED7F | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
58
TCP/UDP connections
246
DNS requests
26
Threats
15
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3388 | tenorshare-4ddig-for-windows.exe | GET | 200 | 23.216.77.80:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?3db752c774de3db8 | US | compressed | 4.70 Kb | whitelisted |
3388 | tenorshare-4ddig-for-windows.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEAo3h2ReX7SMIk79G%2B0UDDw%3D | US | der | 1.47 Kb | whitelisted |
3388 | tenorshare-4ddig-for-windows.exe | GET | 301 | 104.18.25.249:80 | http://www.tenorshare.com/downloads/service/softwarelog.txt | US | html | 268 b | whitelisted |
3388 | tenorshare-4ddig-for-windows.exe | GET | 301 | 104.18.25.249:80 | http://www.tenorshare.com/downloads/service/softwarelog.txt | US | html | 268 b | whitelisted |
3388 | tenorshare-4ddig-for-windows.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAhflMAthXvozBT%2FU%2B2iPio%3D | US | der | 471 b | whitelisted |
3388 | tenorshare-4ddig-for-windows.exe | GET | 200 | 208.95.112.1:80 | http://ip-api.com/csv | unknown | text | 123 b | malicious |
3388 | tenorshare-4ddig-for-windows.exe | POST | 200 | 142.250.186.142:80 | http://www.google-analytics.com/collect | US | image | 35 b | whitelisted |
3388 | tenorshare-4ddig-for-windows.exe | GET | 301 | 104.18.25.249:80 | http://www.tenorshare.com/downloads/service/softwarelog.txt | US | html | 268 b | whitelisted |
3388 | tenorshare-4ddig-for-windows.exe | POST | 200 | 142.250.186.142:80 | http://www.google-analytics.com/collect | US | image | 35 b | whitelisted |
3388 | tenorshare-4ddig-for-windows.exe | POST | 200 | 142.250.186.142:80 | http://www.google-analytics.com/collect | US | image | 35 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3388 | tenorshare-4ddig-for-windows.exe | 208.95.112.1:80 | ip-api.com | TUT-AS | US | malicious |
3388 | tenorshare-4ddig-for-windows.exe | 104.18.10.138:443 | download.tenorshare.net | CLOUDFLARENET | — | unknown |
3388 | tenorshare-4ddig-for-windows.exe | 104.18.24.30:443 | check.mobie.app | CLOUDFLARENET | — | unknown |
3388 | tenorshare-4ddig-for-windows.exe | 104.18.25.30:443 | check.mobie.app | CLOUDFLARENET | — | suspicious |
— | — | 104.18.25.30:443 | check.mobie.app | CLOUDFLARENET | — | suspicious |
3388 | tenorshare-4ddig-for-windows.exe | 23.216.77.80:80 | ctldl.windowsupdate.com | Akamai International B.V. | DE | suspicious |
3388 | tenorshare-4ddig-for-windows.exe | 104.18.25.249:80 | www.tenorshare.com | CLOUDFLARENET | — | suspicious |
3388 | tenorshare-4ddig-for-windows.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
3388 | tenorshare-4ddig-for-windows.exe | 104.18.11.138:443 | download.tenorshare.net | CLOUDFLARENET | — | unknown |
— | — | 104.18.11.138:443 | download.tenorshare.net | CLOUDFLARENET | — | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
check.mobie.app |
| suspicious |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
www.tenorshare.com |
| whitelisted |
download.tenorshare.net |
| whitelisted |
ip-api.com |
| malicious |
www.google-analytics.com |
| whitelisted |
download.tenorshare.com |
| suspicious |
apiw.tenorshare.com |
| suspicious |
cbs.tenorshare.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3388 | tenorshare-4ddig-for-windows.exe | Potential Corporate Privacy Violation | ET POLICY Unsupported/Fake Windows NT Version 5.0 |
3388 | tenorshare-4ddig-for-windows.exe | Potential Corporate Privacy Violation | ET POLICY Unsupported/Fake Windows NT Version 5.0 |
3388 | tenorshare-4ddig-for-windows.exe | Potential Corporate Privacy Violation | AV POLICY Internal Host Retrieving External IP Address (ip-api. com) |
3388 | tenorshare-4ddig-for-windows.exe | Device Retrieving External IP Address Detected | ET POLICY External IP Lookup ip-api.com |
3388 | tenorshare-4ddig-for-windows.exe | A Network Trojan was detected | ET MALWARE Win32/Neshta.A Checkin |
3388 | tenorshare-4ddig-for-windows.exe | Generic Protocol Command Decode | SURICATA STREAM bad window update |
3388 | tenorshare-4ddig-for-windows.exe | Generic Protocol Command Decode | SURICATA HTTP unable to match response to request |
— | — | Potential Corporate Privacy Violation | ET POLICY Unsupported/Fake Windows NT Version 5.0 |
7 ETPRO signatures available at the full report