| File name: | documento1_410.xls |
| Full analysis: | https://app.any.run/tasks/101080d0-d0a6-4dfe-b224-45cd3a9c251c |
| Verdict: | Malicious activity |
| Analysis date: | October 20, 2020, 04:20:31 |
| OS: | Windows 10 Professional (build: 16299, 64 bit) |
| Indicators: | |
| MIME: | application/vnd.ms-excel |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 10.0, Code page: 1252, Author: dppFJMEcrkUCFZCGUe, Last Saved By: administrator, Name of Creating Application: Microsoft Excel, Create Time/Date: Tue Oct 20 00:28:19 2020, Last Saved Time/Date: Tue Oct 20 00:48:19 2020, Security: 1 |
| MD5: | E2739B11FA9EF4DDEE5F9AB41B1A56FF |
| SHA1: | A10B9A7D05F7E4F04983AED34BA3E52AAC0A8642 |
| SHA256: | D9E458B03EAA69BB9CC9A3950D38C6CC78C4AAC8DF53E0048C7D562E88B61C5F |
| SSDEEP: | 6144:uZKOXZdpjpVBrRWJ+Vl0T2q3T9UnoVEsOUqjLxjn:JOXZHpbrsJS03RUX6G |
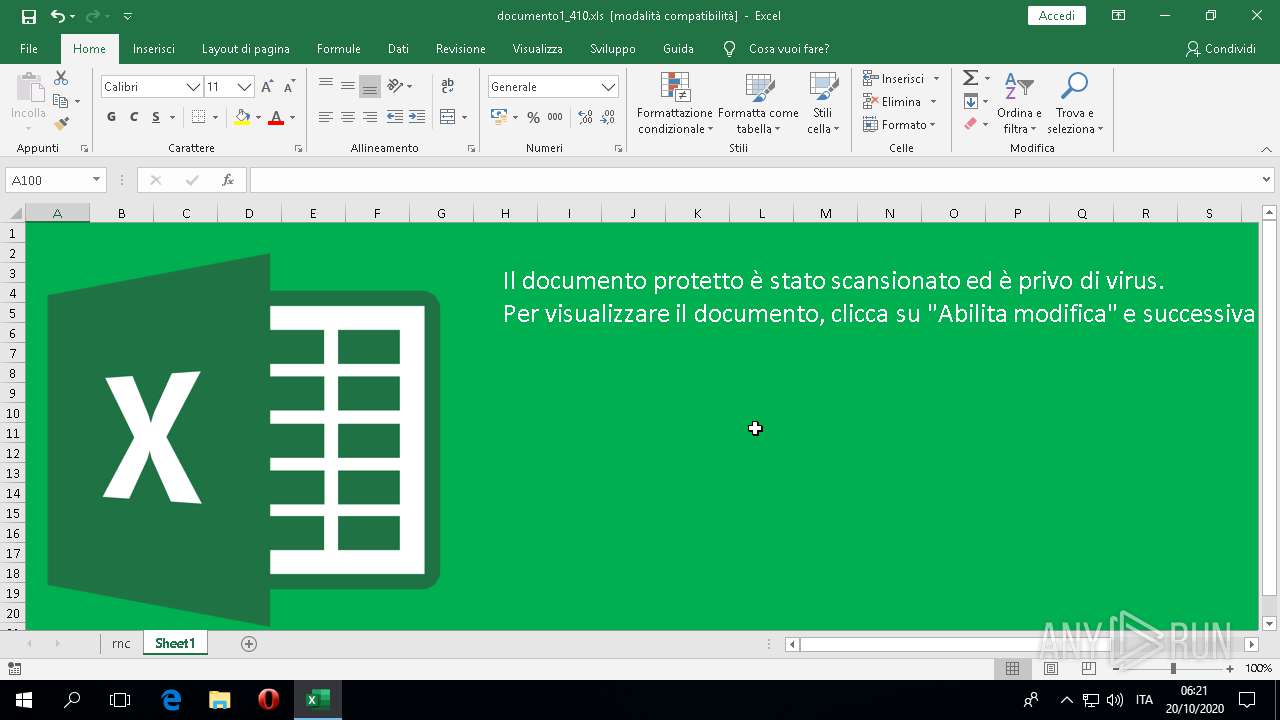
MALICIOUS
Unusual execution from Microsoft Office
- EXCEL.EXE (PID: 576)
Requests a remote executable file from MS Office
- EXCEL.EXE (PID: 576)
SUSPICIOUS
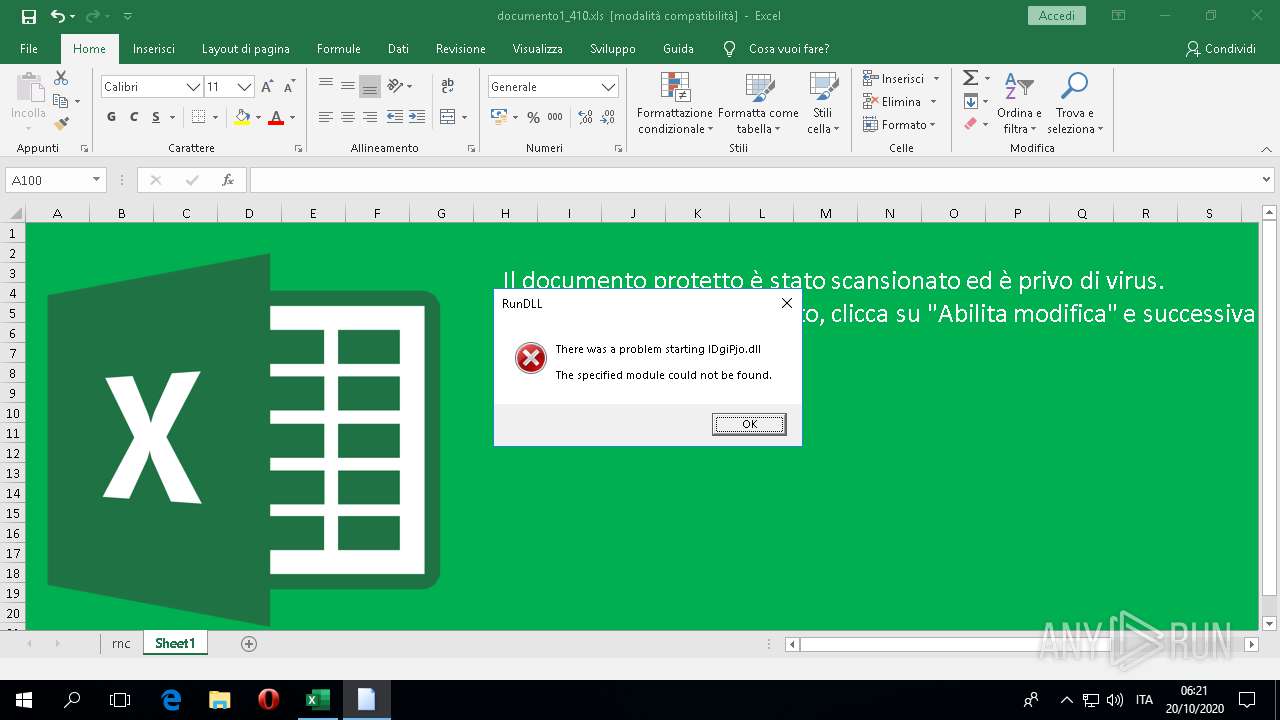
Uses RUNDLL32.EXE to load library
- EXCEL.EXE (PID: 576)
INFO
Creates files in the user directory
- EXCEL.EXE (PID: 576)
Reads the machine GUID from the registry
- EXCEL.EXE (PID: 576)
Reads Environment values
- EXCEL.EXE (PID: 576)
Scans artifacts that could help determine the target
- EXCEL.EXE (PID: 576)
Reads Microsoft Office registry keys
- EXCEL.EXE (PID: 576)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .xls | | | Microsoft Excel sheet (78.9) |
|---|
EXIF
FlashPix
| Author: | dppFJMEcrkUCFZCGUe |
|---|---|
| LastModifiedBy: | administrator |
| Software: | Microsoft Excel |
| CreateDate: | 2020:10:19 23:28:19 |
| ModifyDate: | 2020:10:19 23:48:19 |
| Security: | Password protected |
| CodePage: | Windows Latin 1 (Western European) |
| Company: | - |
| AppVersion: | 16 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: |
|
| HeadingPairs: |
|
Total processes
89
Monitored processes
2
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 576 | "C:\Program Files\Microsoft Office\Root\Office16\EXCEL.EXE" "C:\Users\admin\Desktop\documento1_410.xls" | C:\Program Files\Microsoft Office\Root\Office16\EXCEL.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Excel Exit code: 0 Version: 16.0.12026.20264 Modules
| |||||||||||||||
| 1656 | "C:\Windows\System32\rundll32.exe" IDgiPjo.dll,DllRegisterServer | C:\Windows\System32\rundll32.exe | — | EXCEL.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.16299.15 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
1 368
Read events
1 063
Write events
266
Delete events
39
Modification events
| (PID) Process: | (576) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\Common\ClientTelemetry\Sampling |
| Operation: | write | Name: | 1 |
Value: 01D014000000001000284FFA2E01000000000000000400000000000000 | |||
| (PID) Process: | (576) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\Common\CrashPersistence\EXCEL\576 |
| Operation: | write | Name: | 0 |
Value: 0B0E10A9320435B2A789479840164A08CF59A12300469EBF8BBE86D3A9EB016A0410240044FA5D64A89E01008500A907556E6B6E6F776EC9062E226D2B484F4D616659574A5464337373702B3165327141506A326C775347586F6C4A7635624B6E337449506B3D2200 | |||
| (PID) Process: | (576) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | en-US |
Value: 2 | |||
| (PID) Process: | (576) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | es-es |
Value: 2 | |||
| (PID) Process: | (576) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | de-de |
Value: 2 | |||
| (PID) Process: | (576) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | fr-fr |
Value: 2 | |||
| (PID) Process: | (576) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | it-it |
Value: 2 | |||
| (PID) Process: | (576) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | ja-jp |
Value: 2 | |||
| (PID) Process: | (576) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | ko-kr |
Value: 2 | |||
| (PID) Process: | (576) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | pt-br |
Value: 2 | |||
Executable files
0
Suspicious files
3
Text files
6
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 576 | EXCEL.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\ETZCV79GBIXBYWJXWVTF.temp | — | |
MD5:— | SHA256:— | |||
| 576 | EXCEL.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\YLIW83SDGQCVDFMGFKSK.temp | — | |
MD5:— | SHA256:— | |||
| 576 | EXCEL.EXE | C:\Users\admin\AppData\Local\Microsoft\Office\16.0\WebServiceCache\AllUsers\officeclient.microsoft.com\0DBEA502-8EB6-4649-9A15-5F586D6273F2 | xml | |
MD5:— | SHA256:— | |||
| 576 | EXCEL.EXE | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6BADA8974A10C4BD62CC921D13E43B18_1DC6D7385EA816C957BA2B715AC5C442 | binary | |
MD5:— | SHA256:— | |||
| 576 | EXCEL.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\documento1_410.xls.LNK | lnk | |
MD5:— | SHA256:— | |||
| 576 | EXCEL.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\index.dat | text | |
MD5:— | SHA256:— | |||
| 576 | EXCEL.EXE | C:\Users\admin\AppData\Local\Microsoft\Office\16.0\excel.exe_Rules.xml | xml | |
MD5:— | SHA256:— | |||
| 576 | EXCEL.EXE | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6BADA8974A10C4BD62CC921D13E43B18_1DC6D7385EA816C957BA2B715AC5C442 | der | |
MD5:BC94D23C9480A35FACB5E50F2AB187EF | SHA256:69E4BD5ED06087FBF1FAAA02A868325DE2DA88A33516E285389DE9ECFDB2543A | |||
| 576 | EXCEL.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\b8ab77100df80ab2.customDestinations-ms | binary | |
MD5:E4A1661C2C886EBB688DEC494532431C | SHA256:B76875C50EF704DBBF7F02C982445971D1BBD61AEBE2E4B28DDC58A1D66317D5 | |||
| 576 | EXCEL.EXE | C:\Users\admin\AppData\Local\Microsoft\FontCache\4\Catalog\ListAll.Json | text | |
MD5:DA0BD83A887299F6A4A2B5ACF6C88AF1 | SHA256:4339EF6FC484D48533E9DA01AB8016B060F3C378C63ED58EE5FFD869121FC362 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
16
DNS requests
10
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
576 | EXCEL.EXE | GET | — | 109.248.203.236:80 | http://linksystems.casa/installa.dll | RU | — | — | suspicious |
1076 | svchost.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAH9o%2BtuynXIiEOLckvPvJE%3D | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
576 | EXCEL.EXE | 52.109.76.124:443 | roaming.officeapps.live.com | Microsoft Corporation | IE | whitelisted |
1076 | svchost.exe | 40.90.23.153:443 | login.live.com | Microsoft Corporation | US | unknown |
576 | EXCEL.EXE | 52.109.88.8:443 | officeclient.microsoft.com | Microsoft Corporation | NL | whitelisted |
576 | EXCEL.EXE | 52.109.52.36:443 | messaging.office.com | Microsoft Corporation | JP | unknown |
1076 | svchost.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
576 | EXCEL.EXE | 52.114.159.112:443 | self.events.data.microsoft.com | Microsoft Corporation | US | unknown |
576 | EXCEL.EXE | 52.109.8.19:443 | nexusrules.officeapps.live.com | Microsoft Corporation | US | whitelisted |
— | — | 109.248.203.236:80 | linksystems.casa | Business Consulting LLC | RU | suspicious |
576 | EXCEL.EXE | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
576 | EXCEL.EXE | 104.111.214.95:443 | fs.microsoft.com | Akamai International B.V. | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
officeclient.microsoft.com |
| whitelisted |
roaming.officeapps.live.com |
| whitelisted |
fs.microsoft.com |
| whitelisted |
config.edge.skype.com |
| malicious |
ocsp.digicert.com |
| whitelisted |
login.live.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |
linksystems.casa |
| suspicious |
messaging.office.com |
| whitelisted |
nexusrules.officeapps.live.com |
| whitelisted |