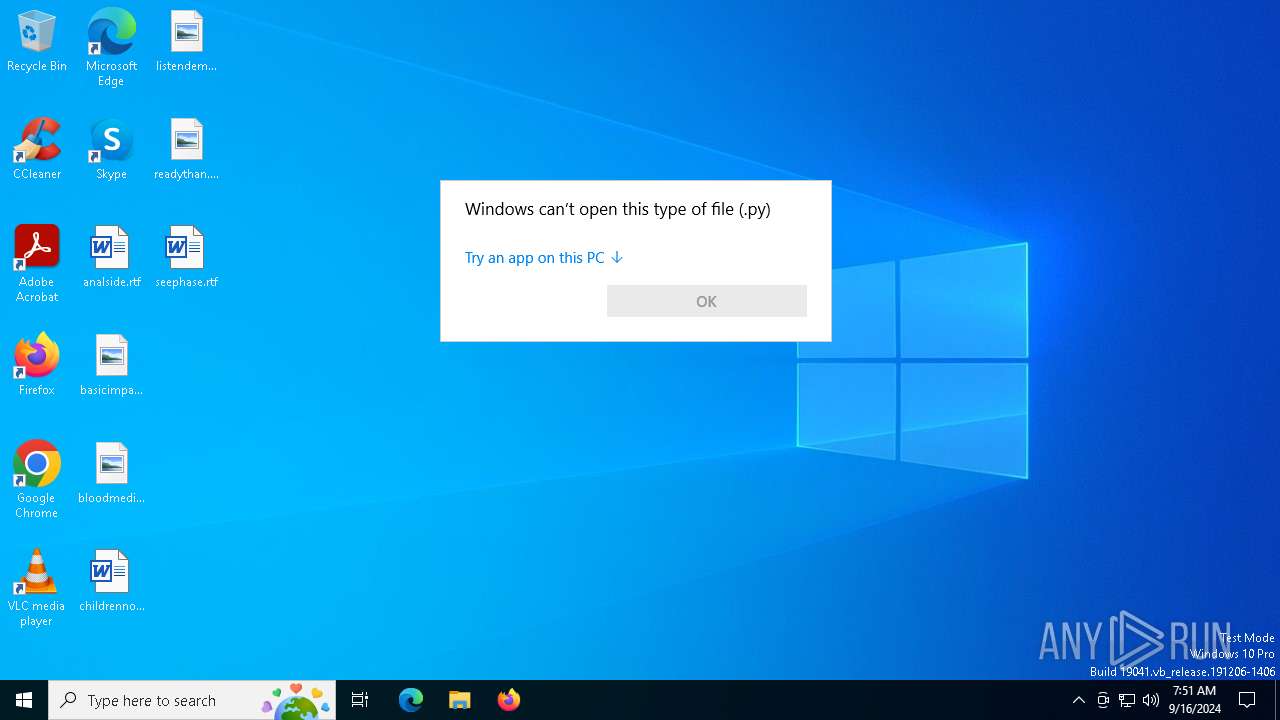
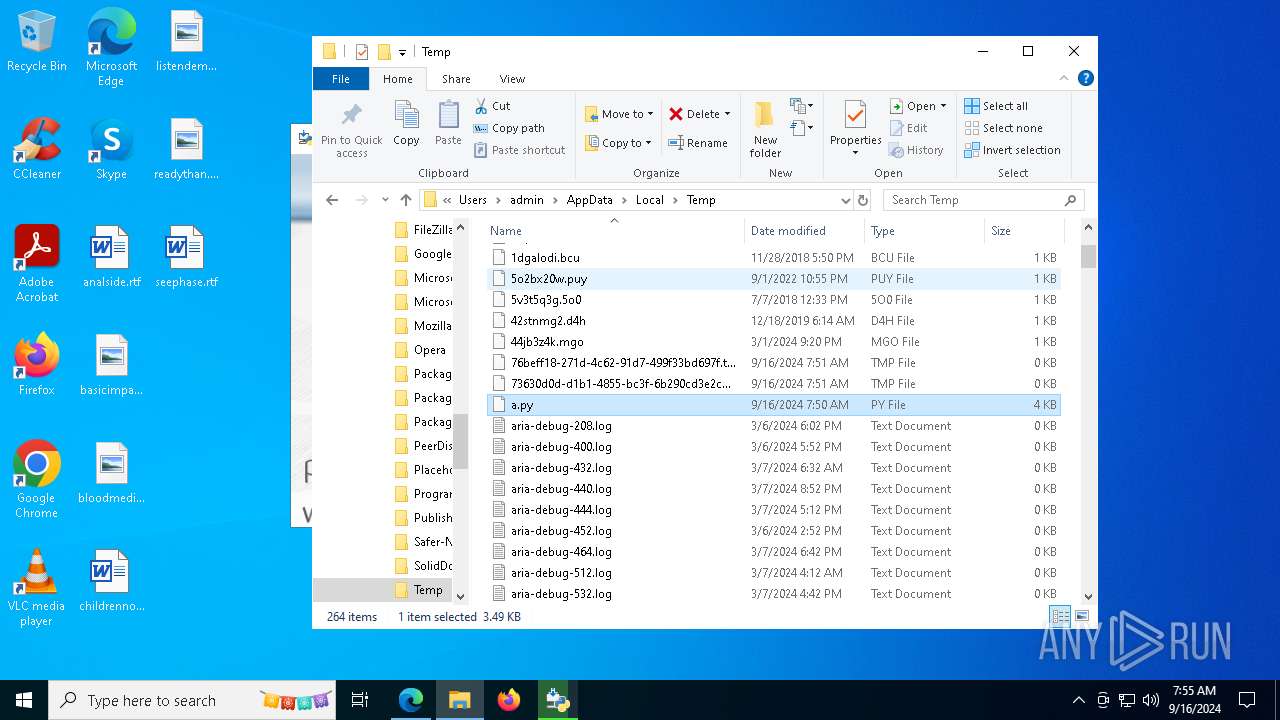
| File name: | a.py |
| Full analysis: | https://app.any.run/tasks/36f10c3e-b543-4b65-a587-ea038204f592 |
| Verdict: | Malicious activity |
| Analysis date: | September 16, 2024, 07:50:53 |
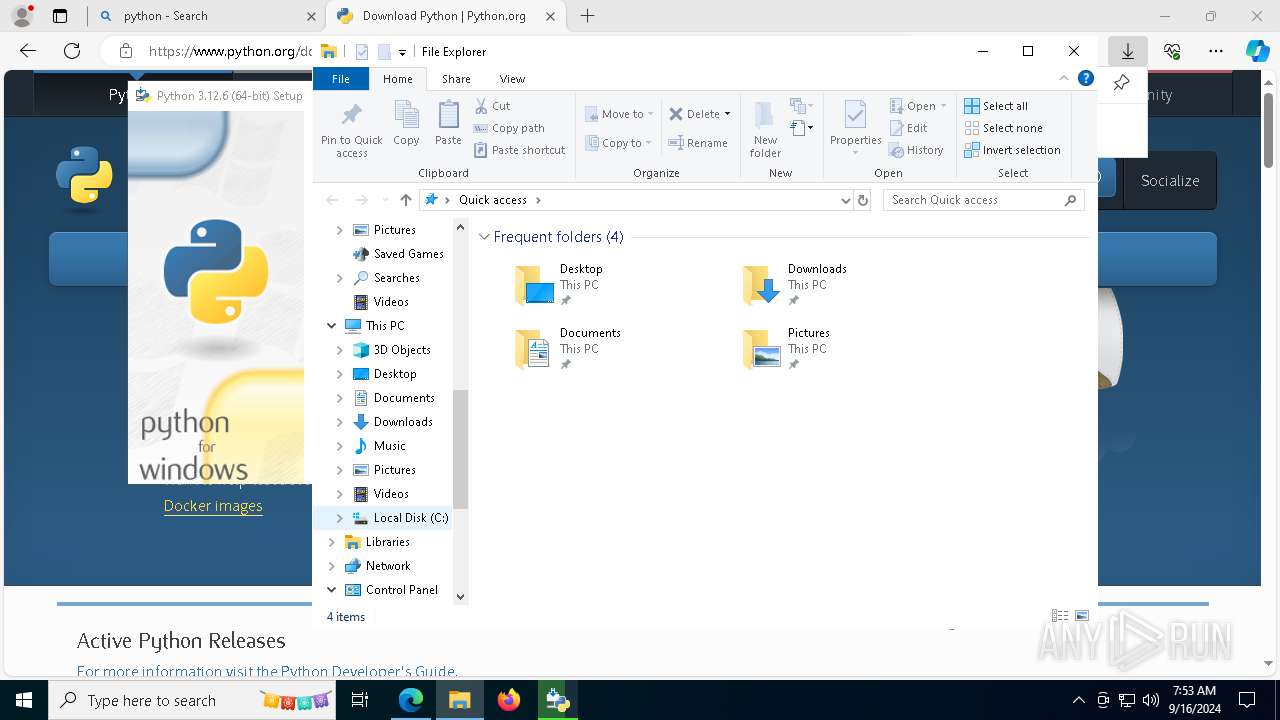
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
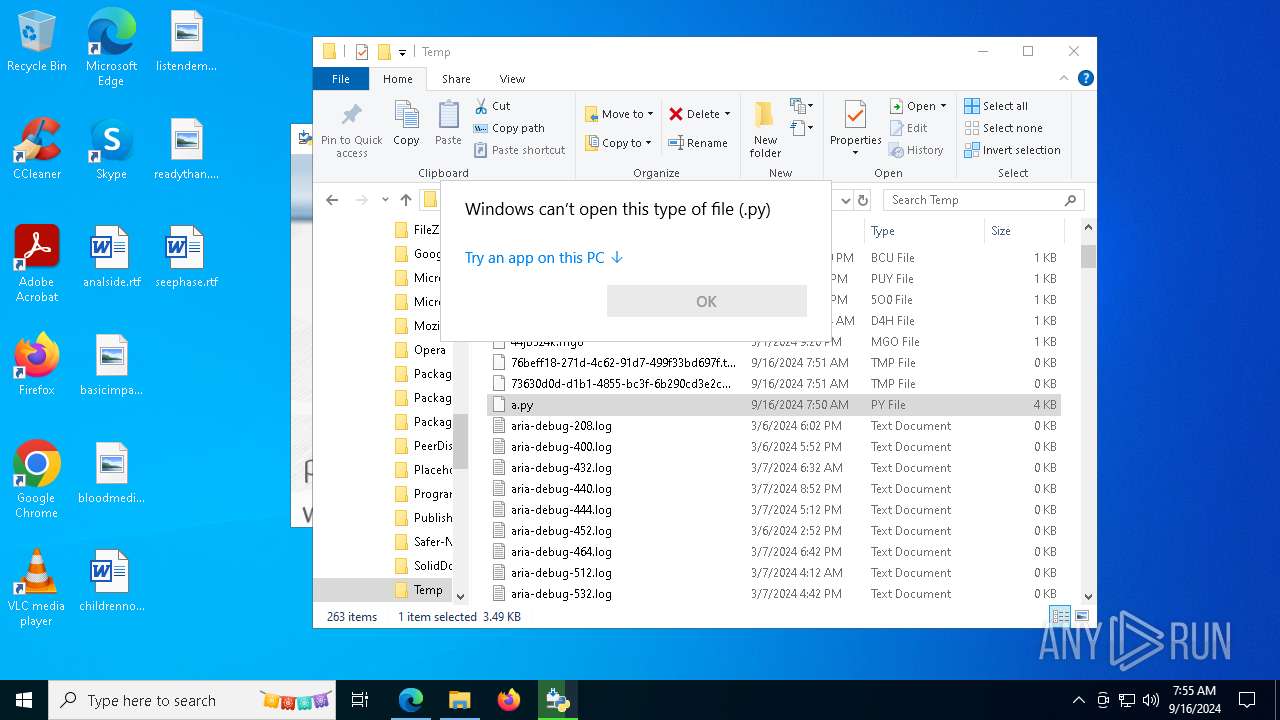
| MIME: | text/x-script.python |
| File info: | Python script, ASCII text executable, with CRLF line terminators |
| MD5: | 4E8313C8A4BB0654BEBDD7A4C6AD2A4F |
| SHA1: | 5F26DA4F13C67EA7A9B8C9DB7BDED62AF7516840 |
| SHA256: | D9E26C19AE9E160A8BE0F43593A560114BA4C7F50FEB76040E950C282A2600AE |
| SSDEEP: | 48:oUvbLGl3/DJD7XURq2E25TBpB97xBR89KjyIJi78u2IB7RsKdEpk0XibbA:ouPGl3/DhURq2FtBzzBR89uNUF+JwA |
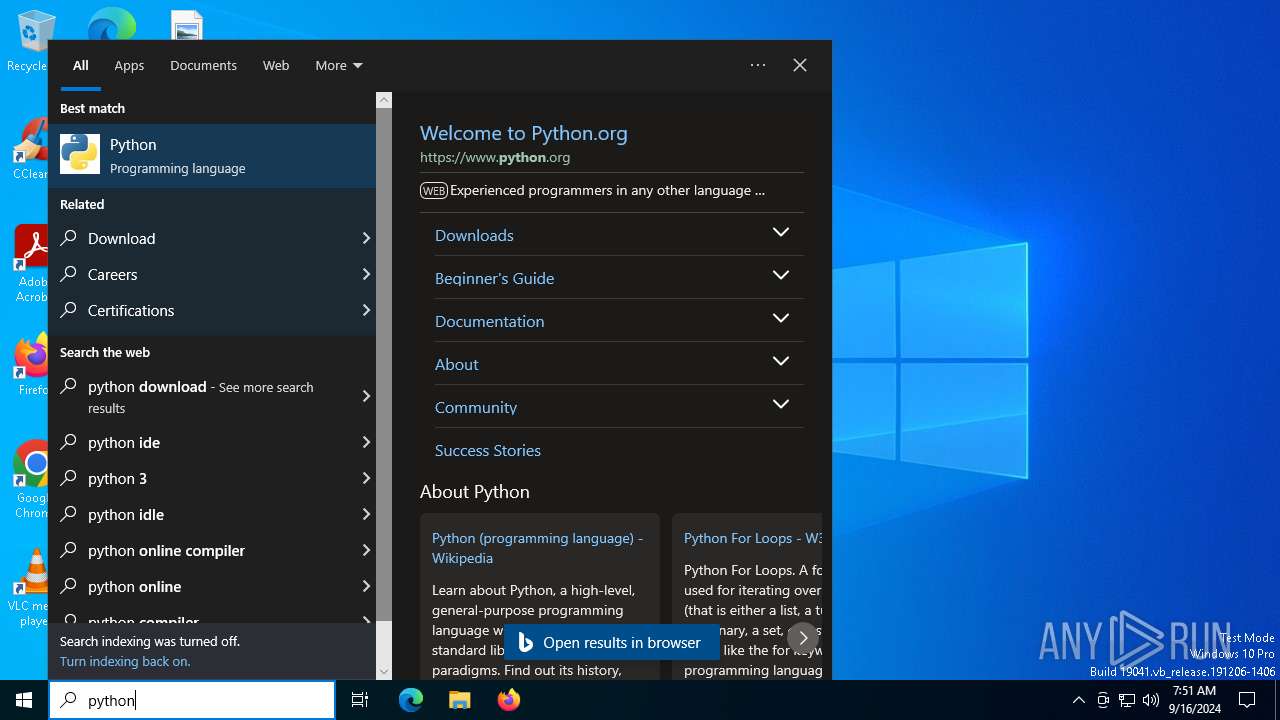
MALICIOUS
Changes the autorun value in the registry
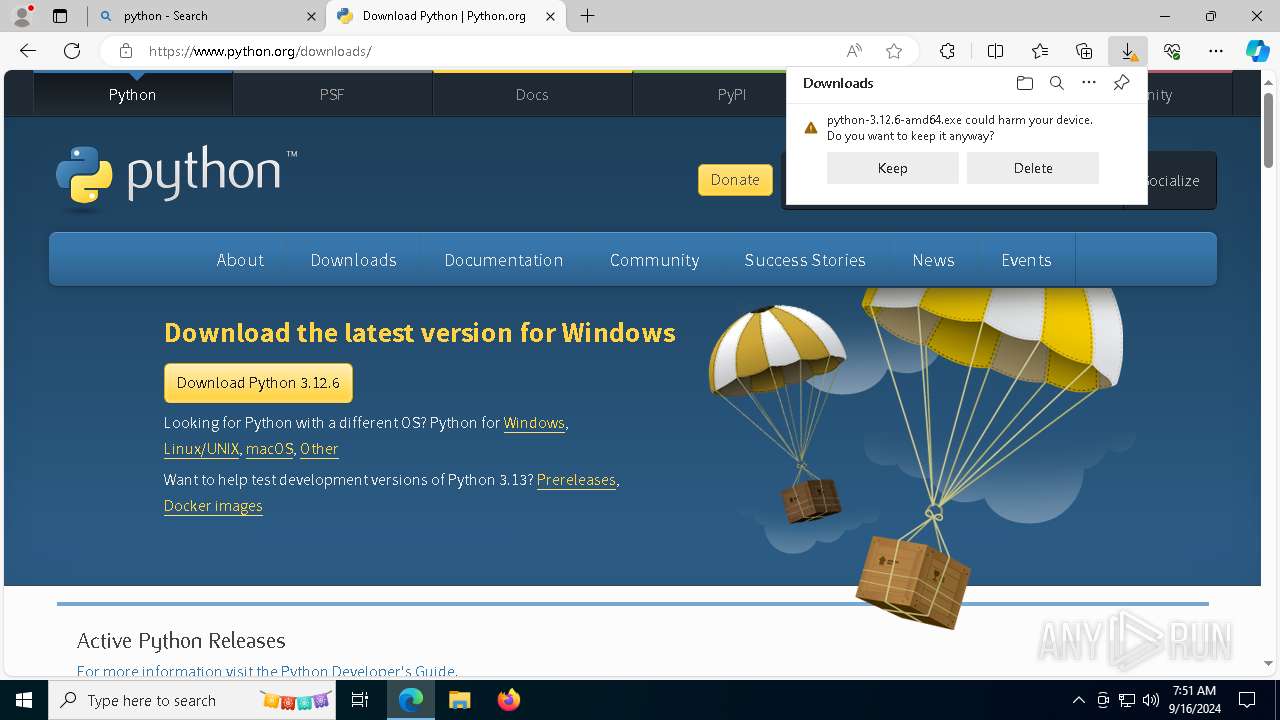
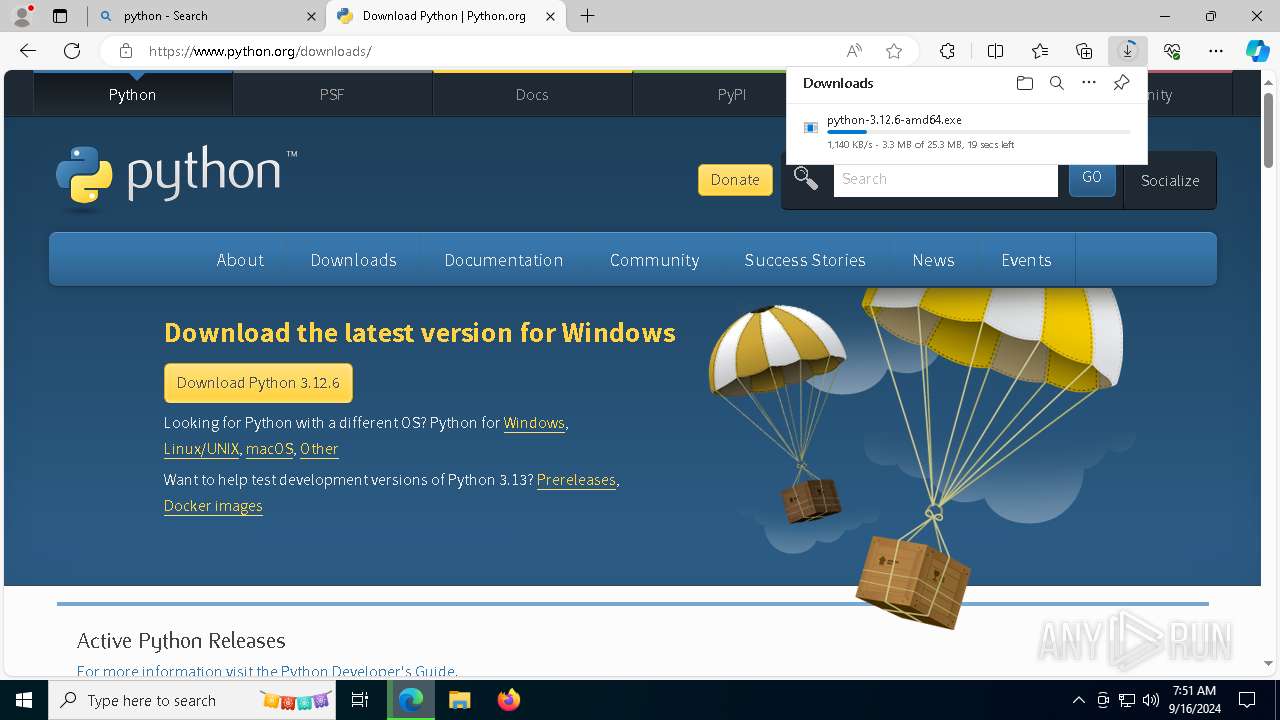
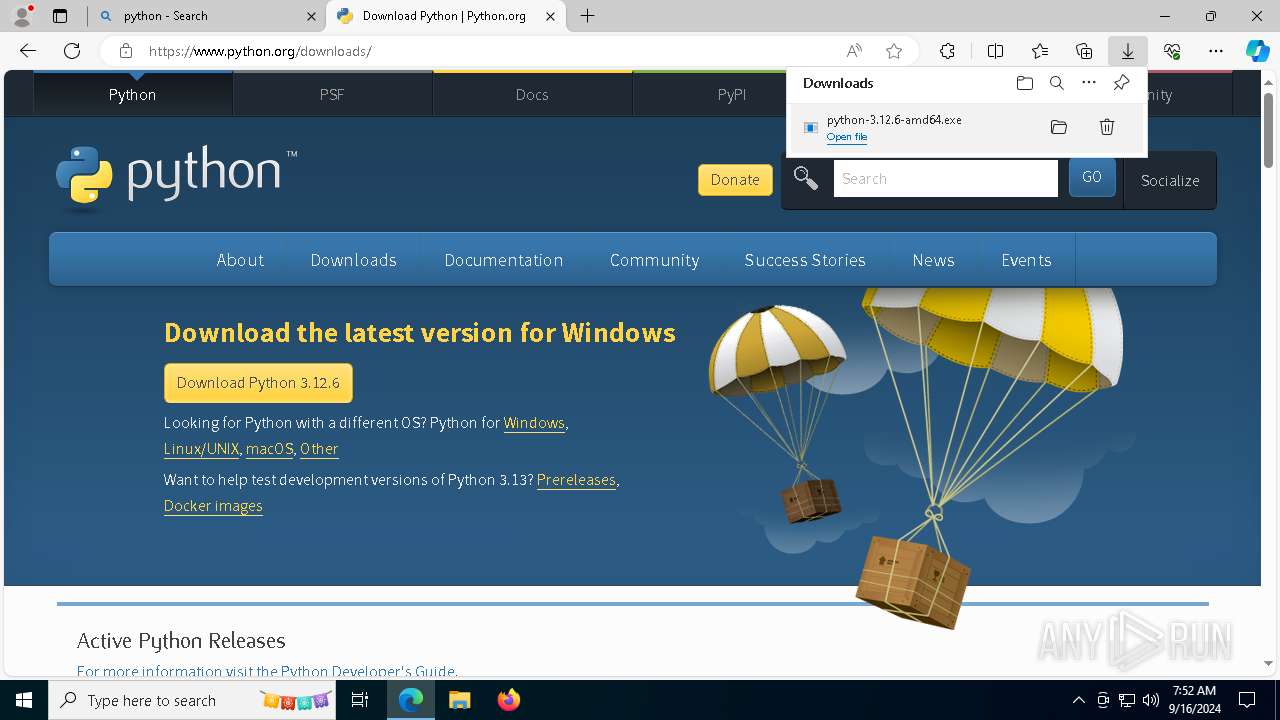
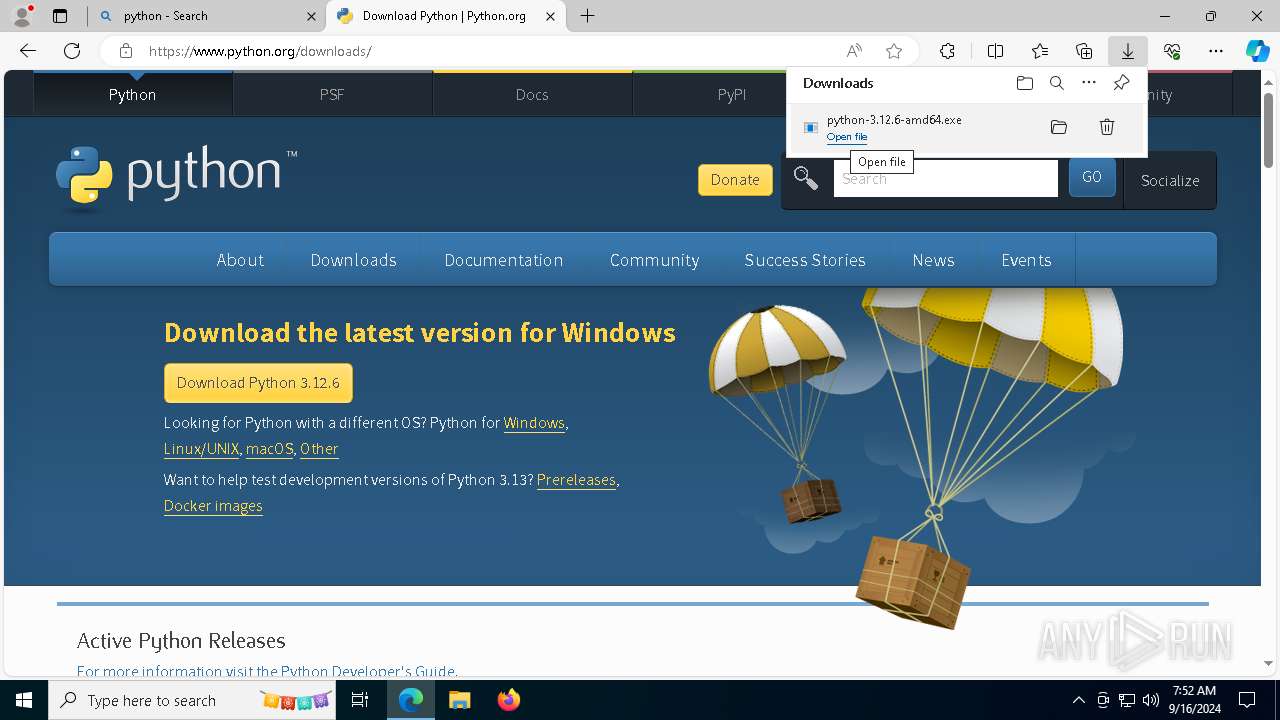
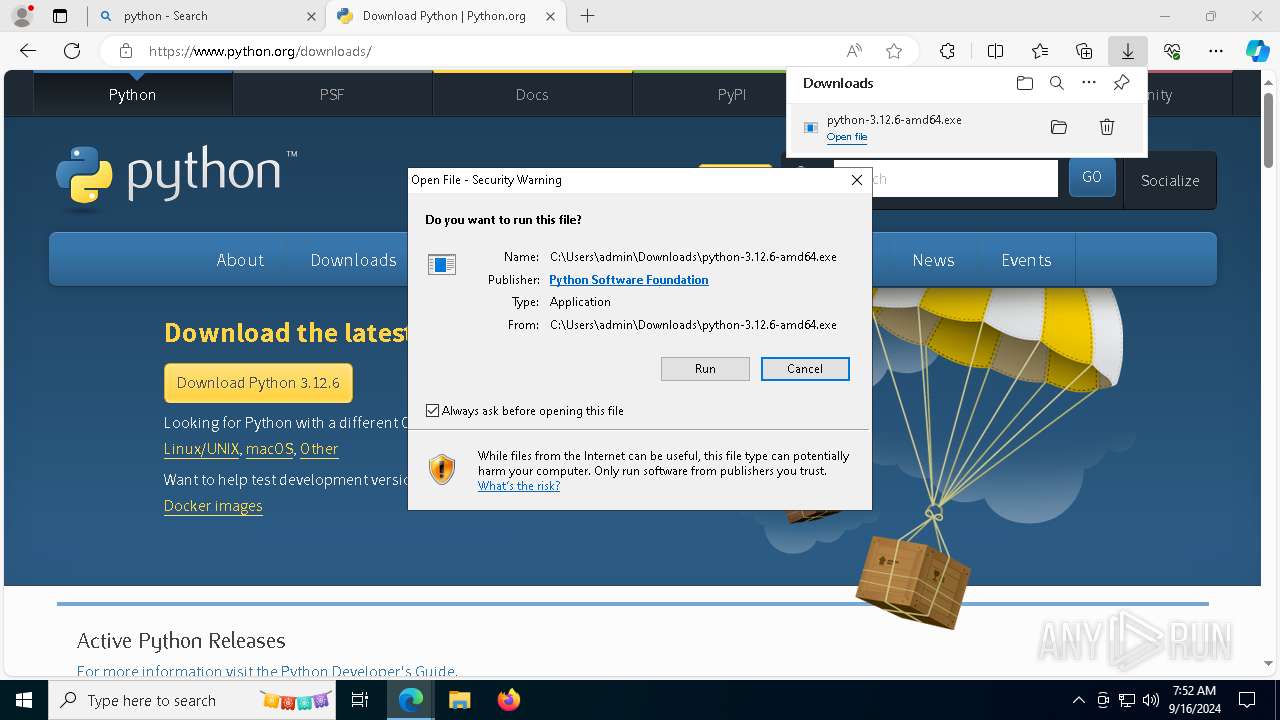
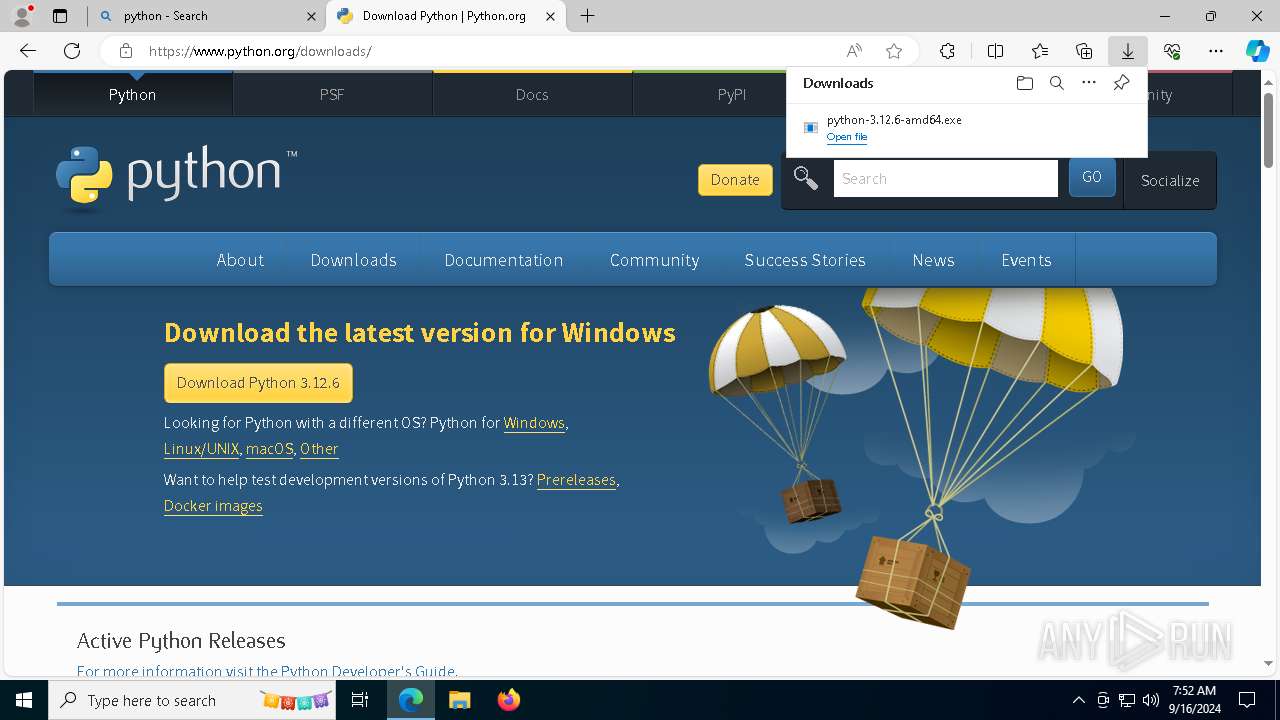
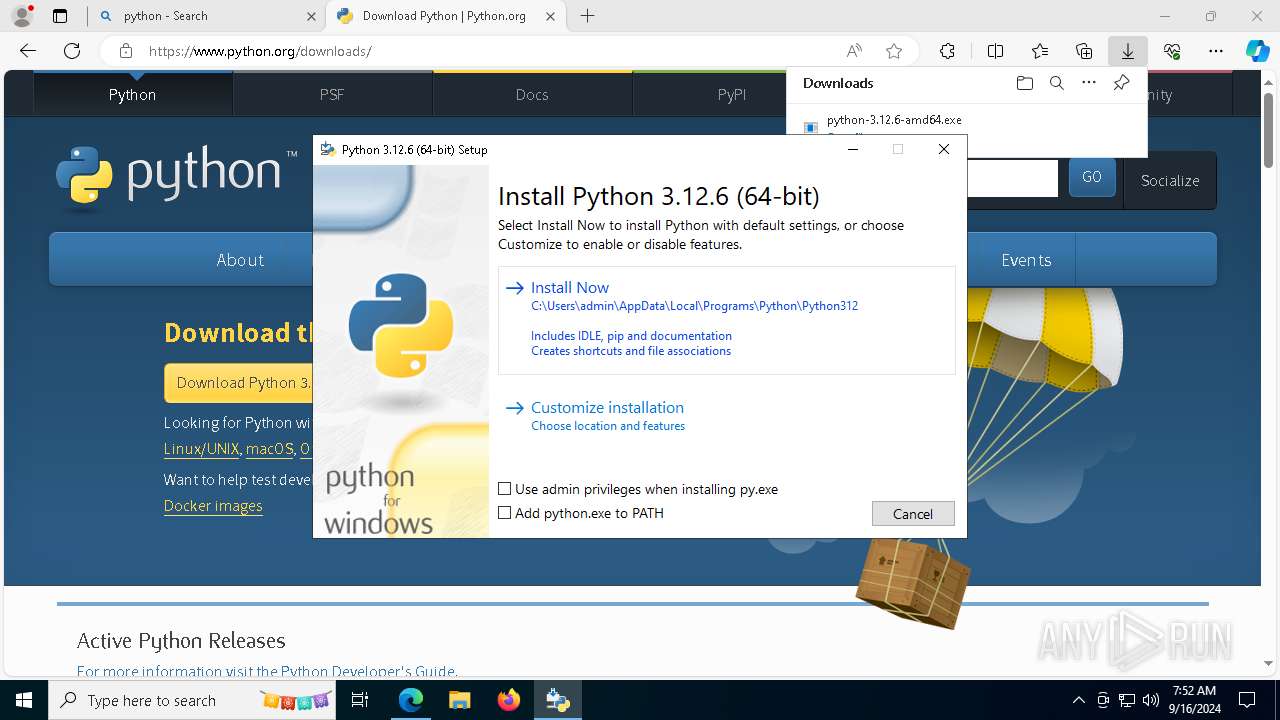
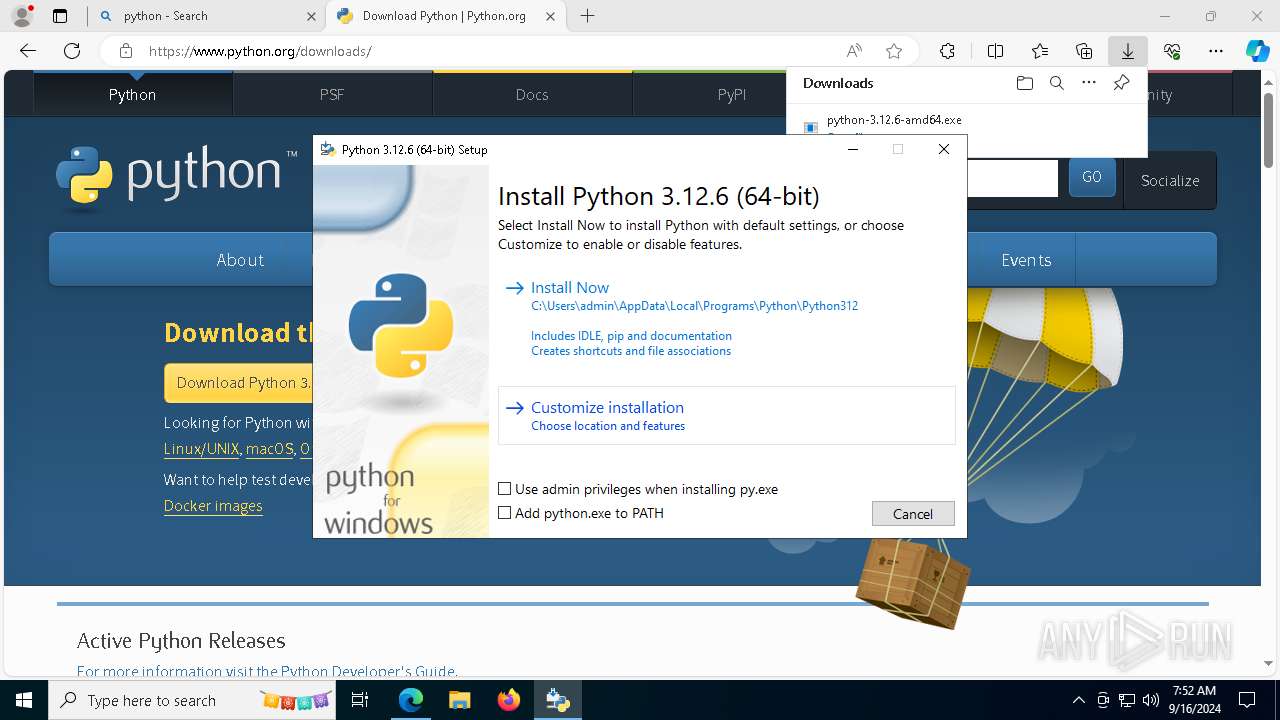
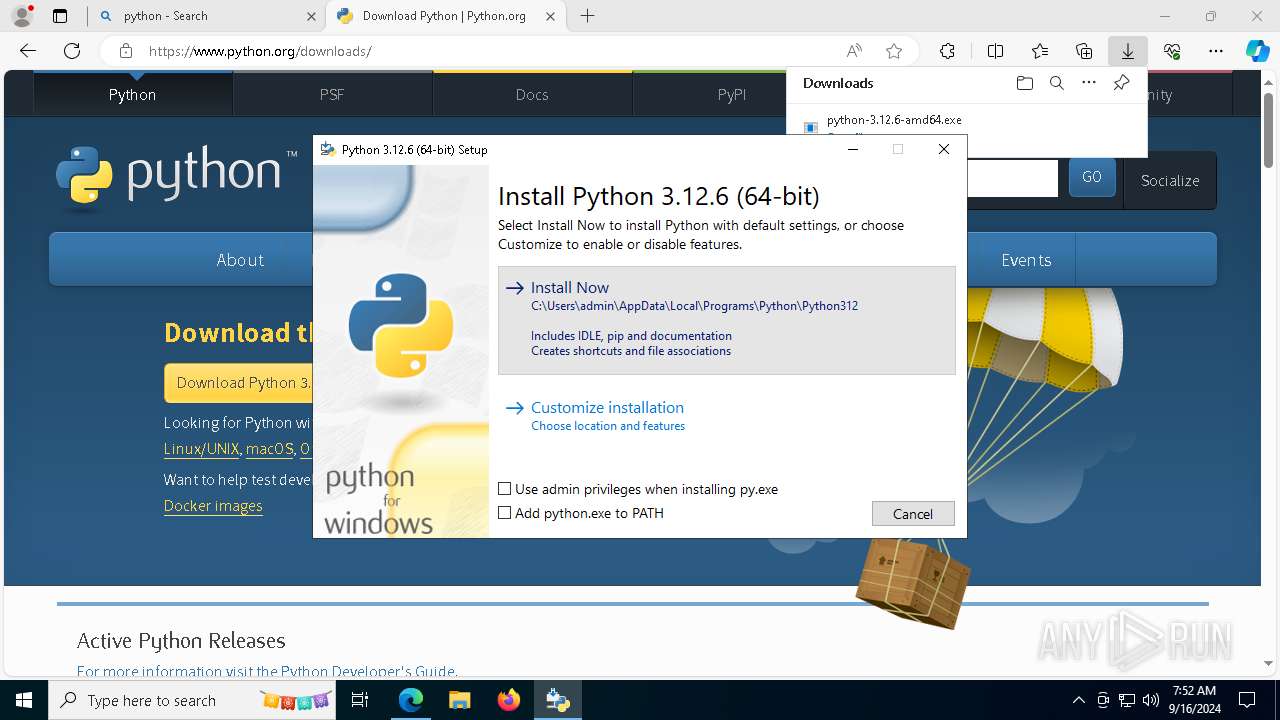
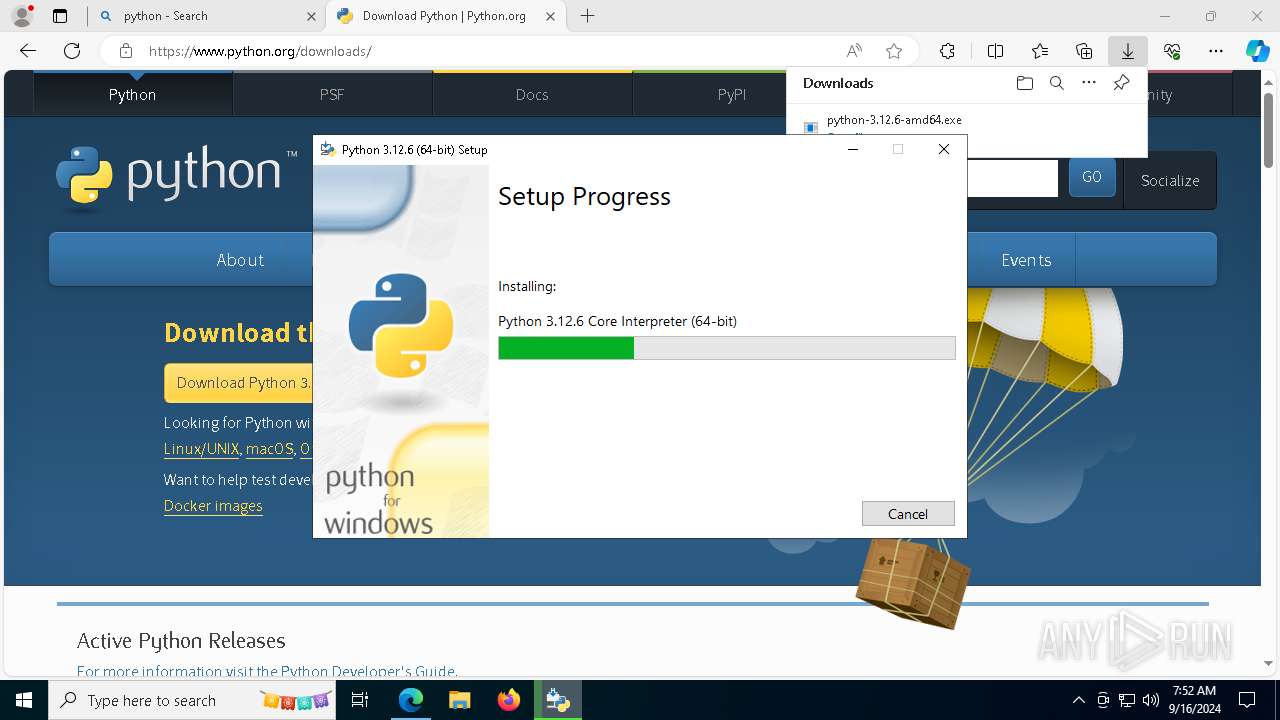
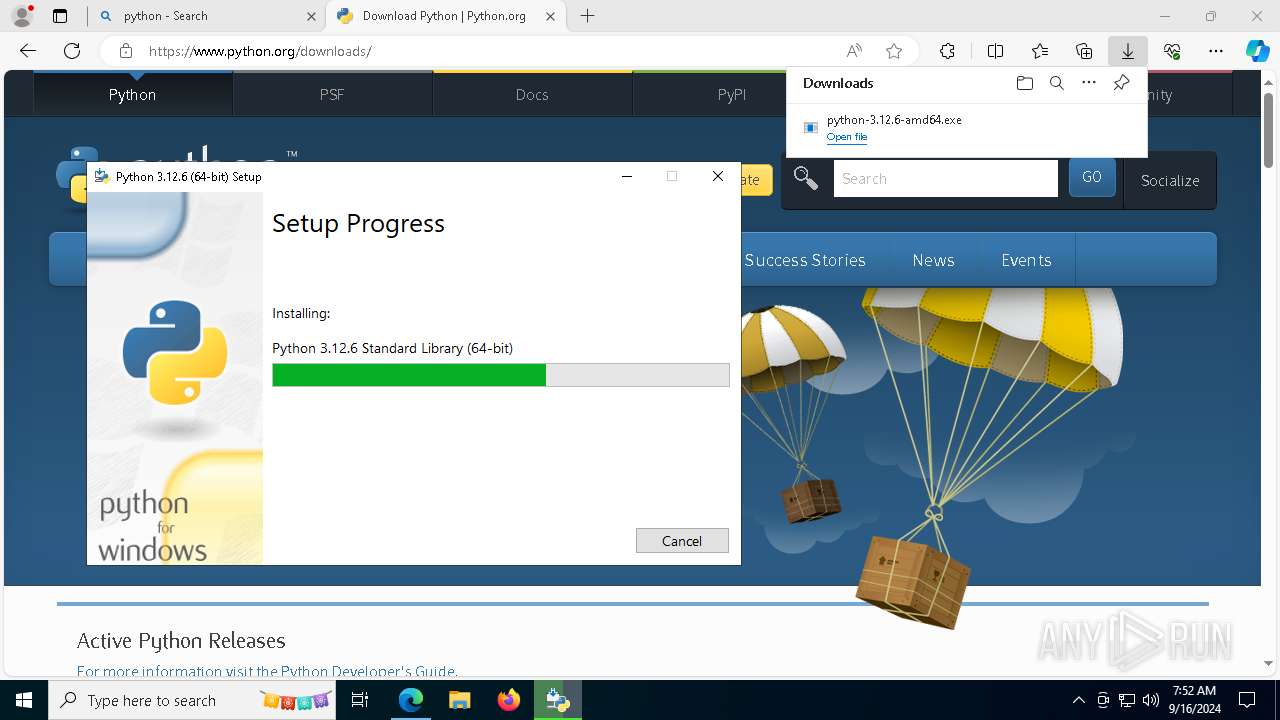
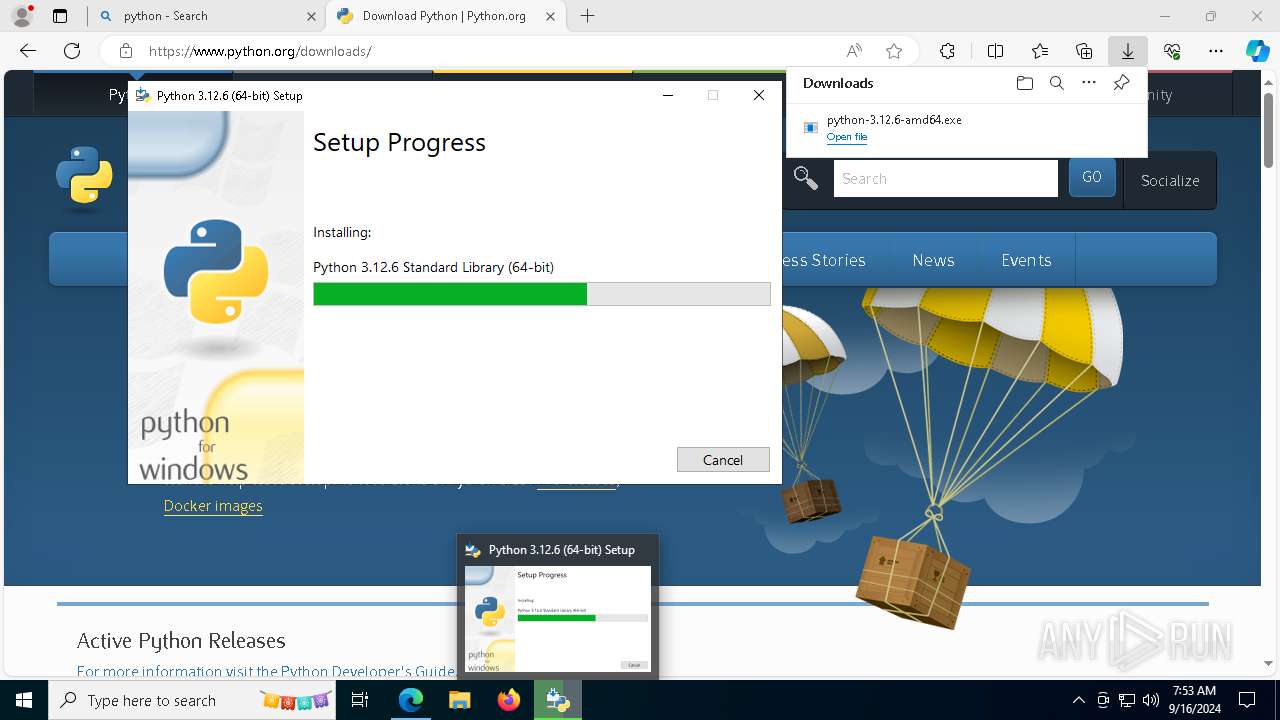
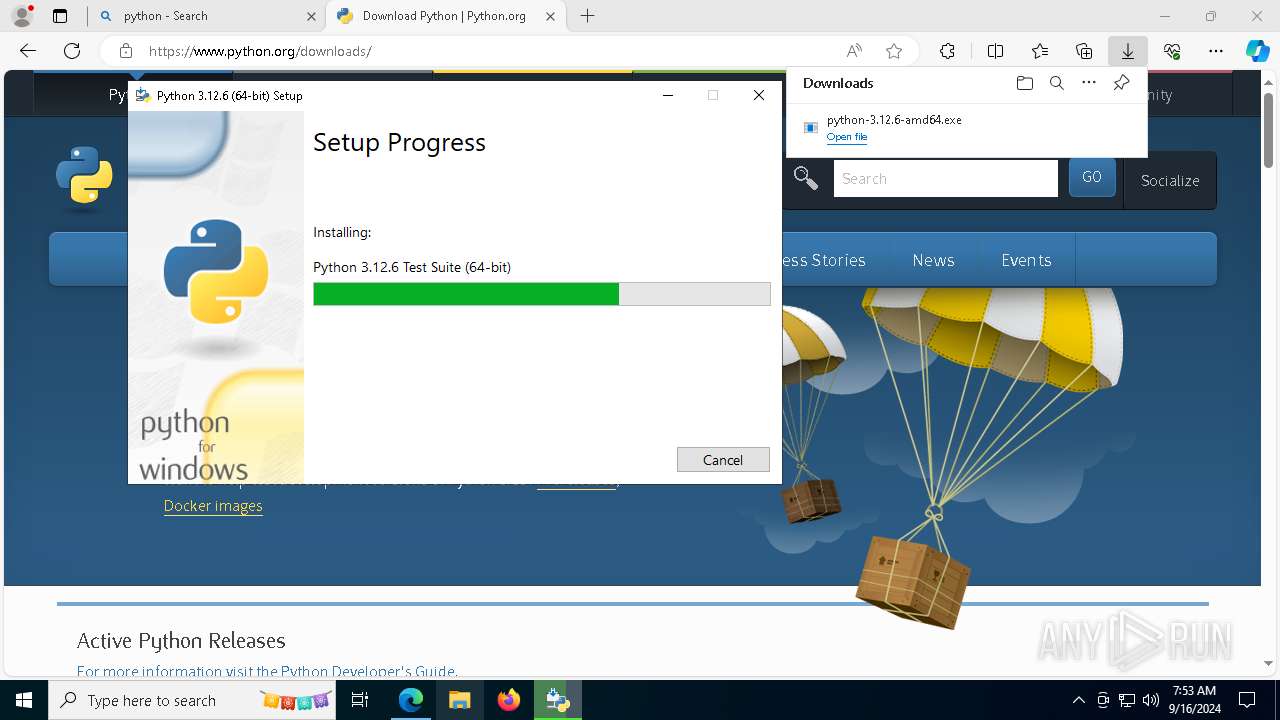
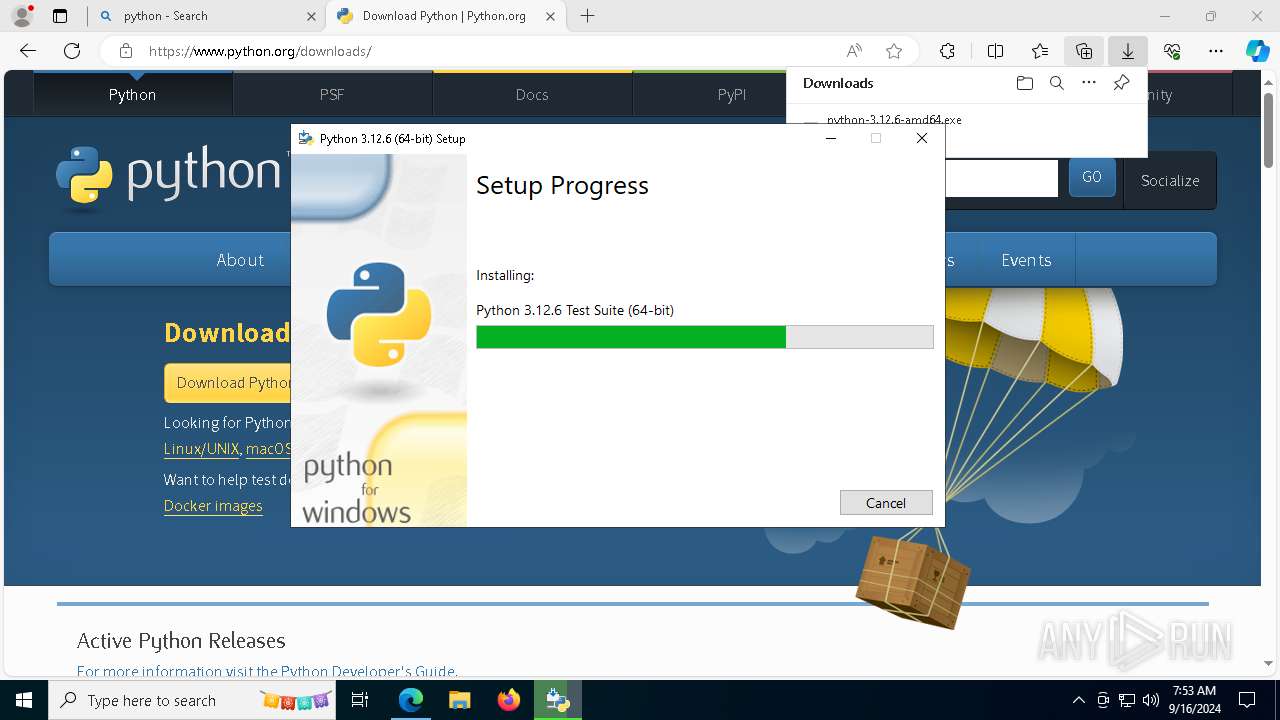
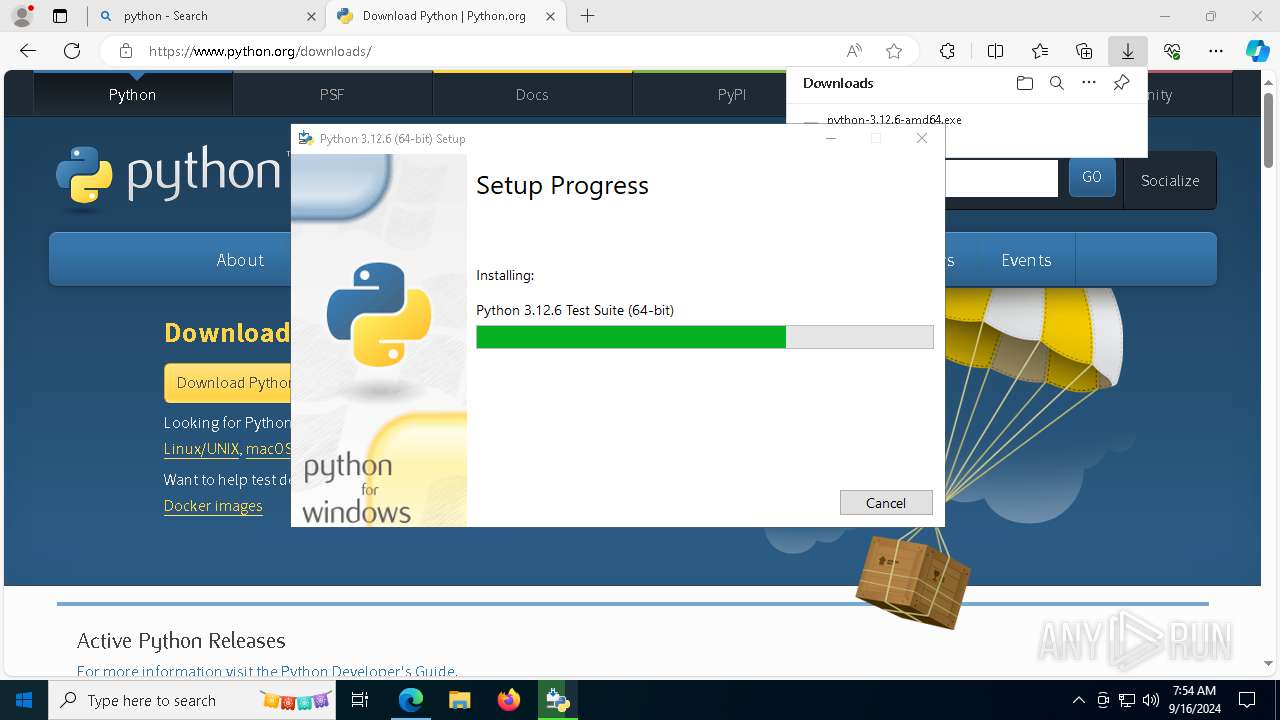
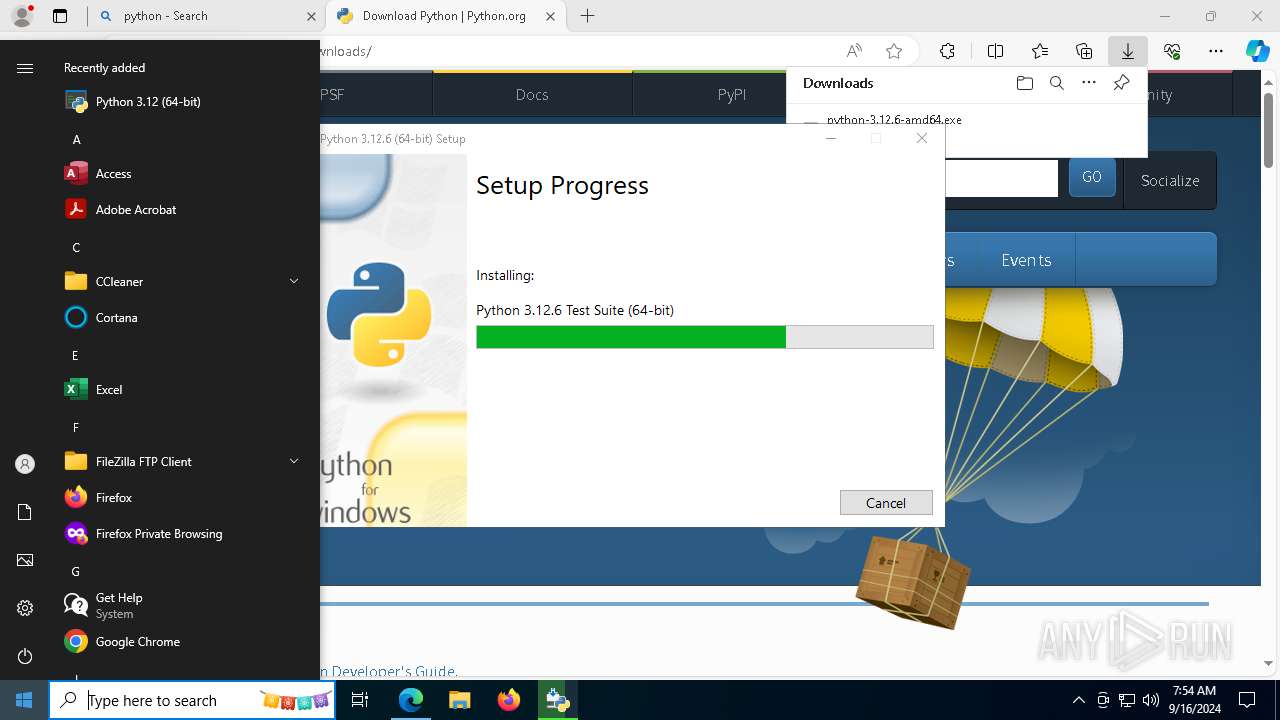
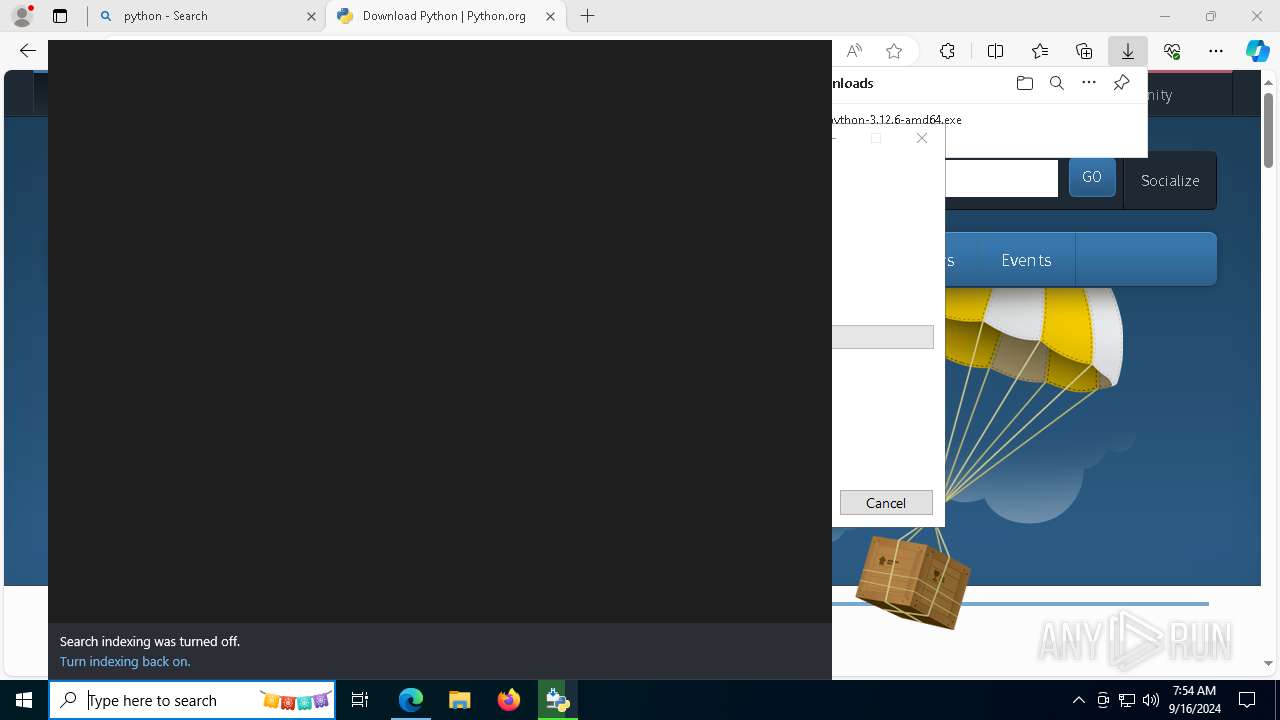
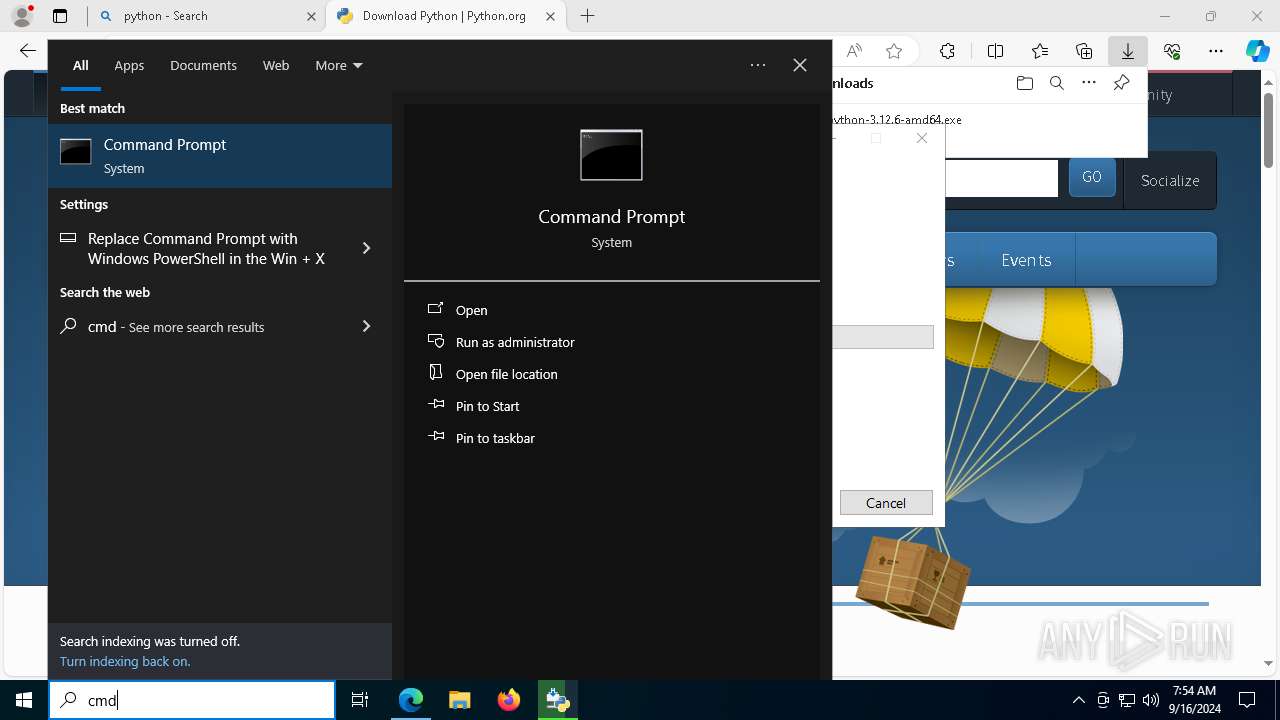
- python-3.12.6-amd64.exe (PID: 8060)
SUSPICIOUS
Executable content was dropped or overwritten
- python-3.12.6-amd64.exe (PID: 8060)
Reads the Windows owner or organization settings
- msiexec.exe (PID: 7244)
Creates a software uninstall entry
- python-3.12.6-amd64.exe (PID: 8060)
Checks Windows Trust Settings
- msiexec.exe (PID: 7244)
Process drops python dynamic module
- msiexec.exe (PID: 7244)
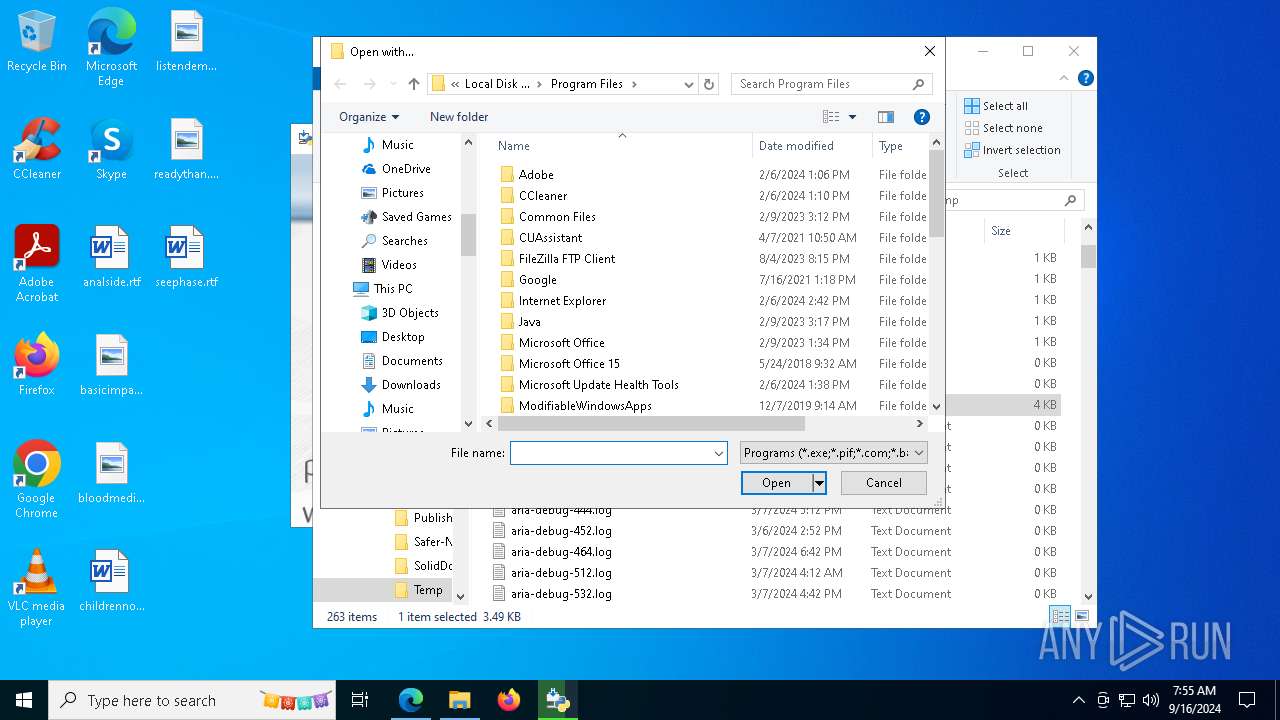
Searches for installed software
- python-3.12.6-amd64.exe (PID: 8060)
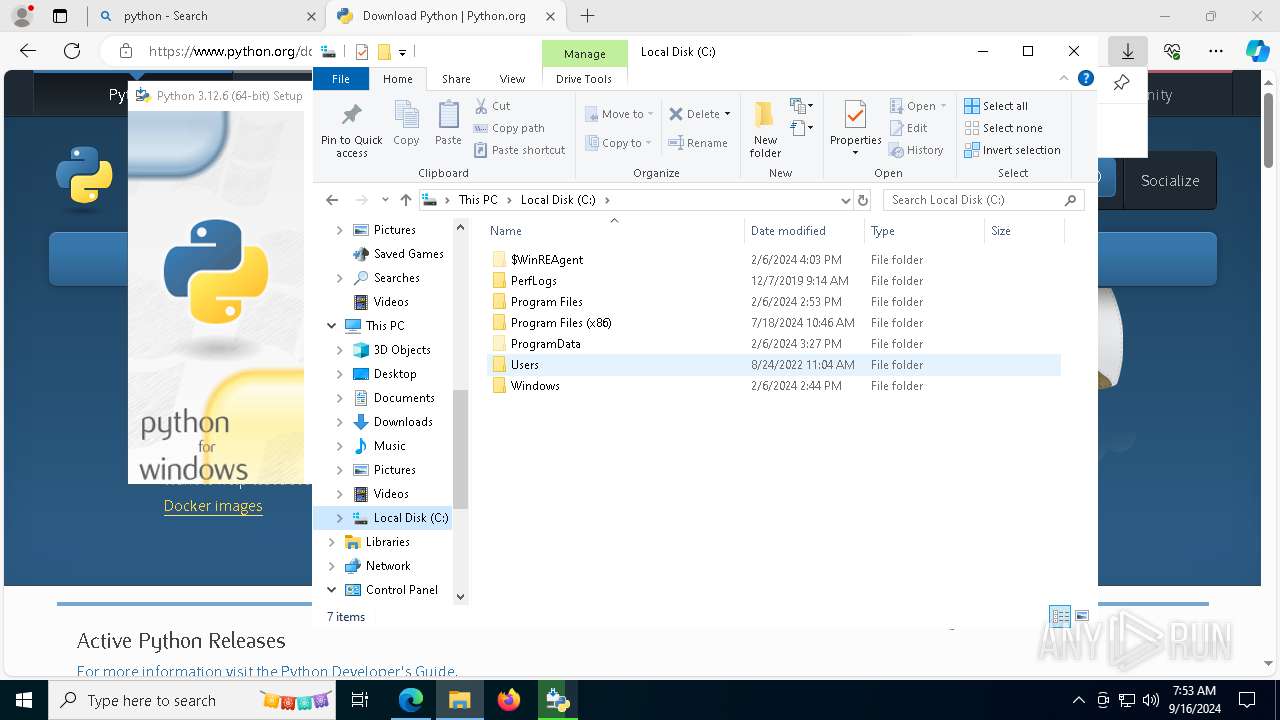
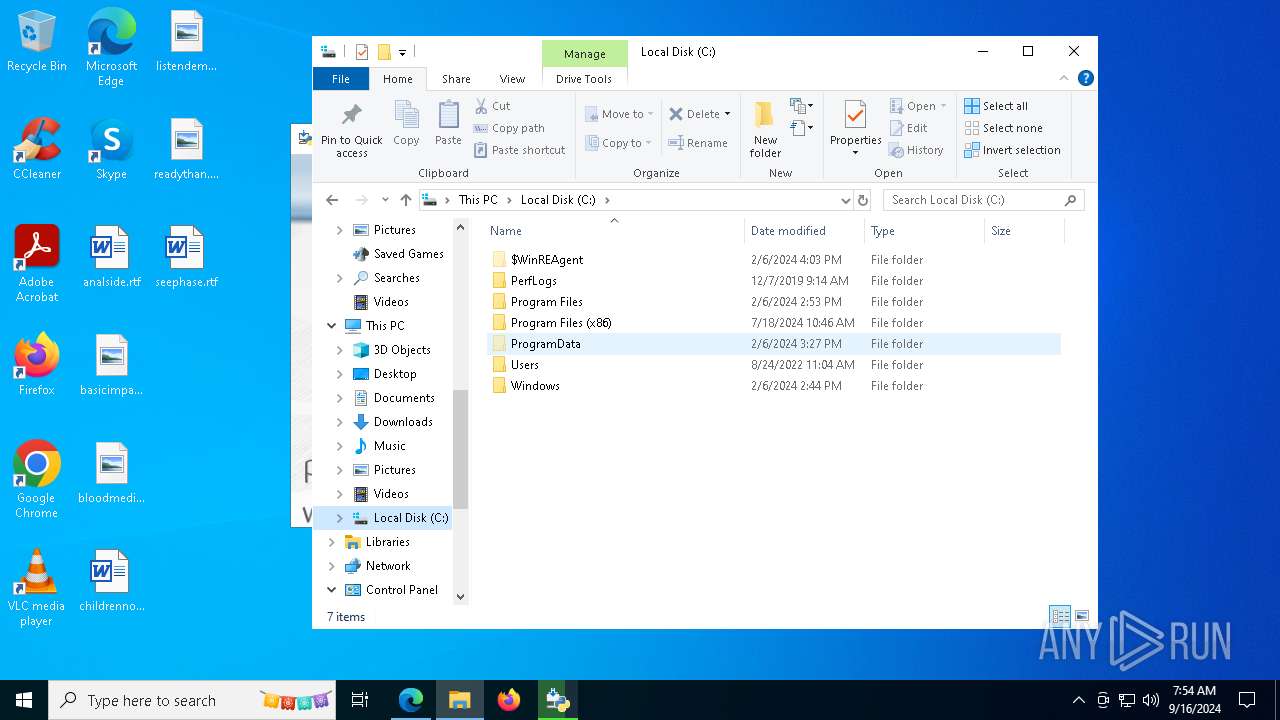
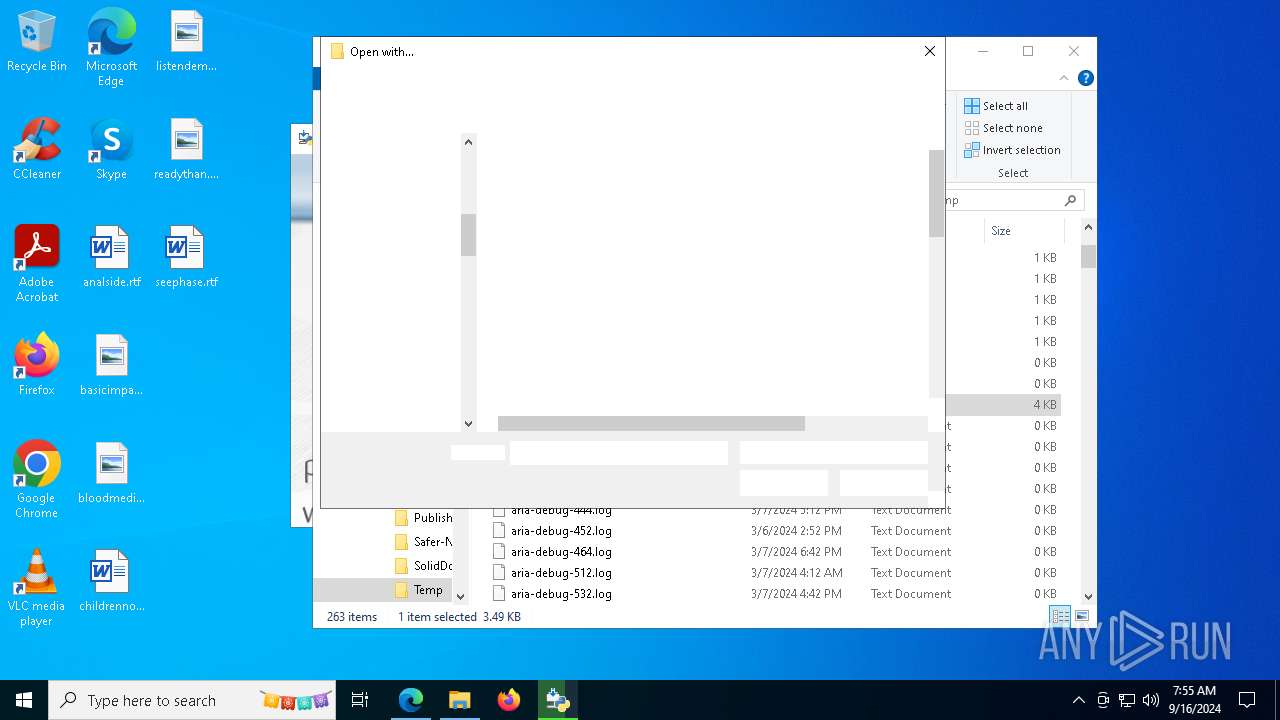
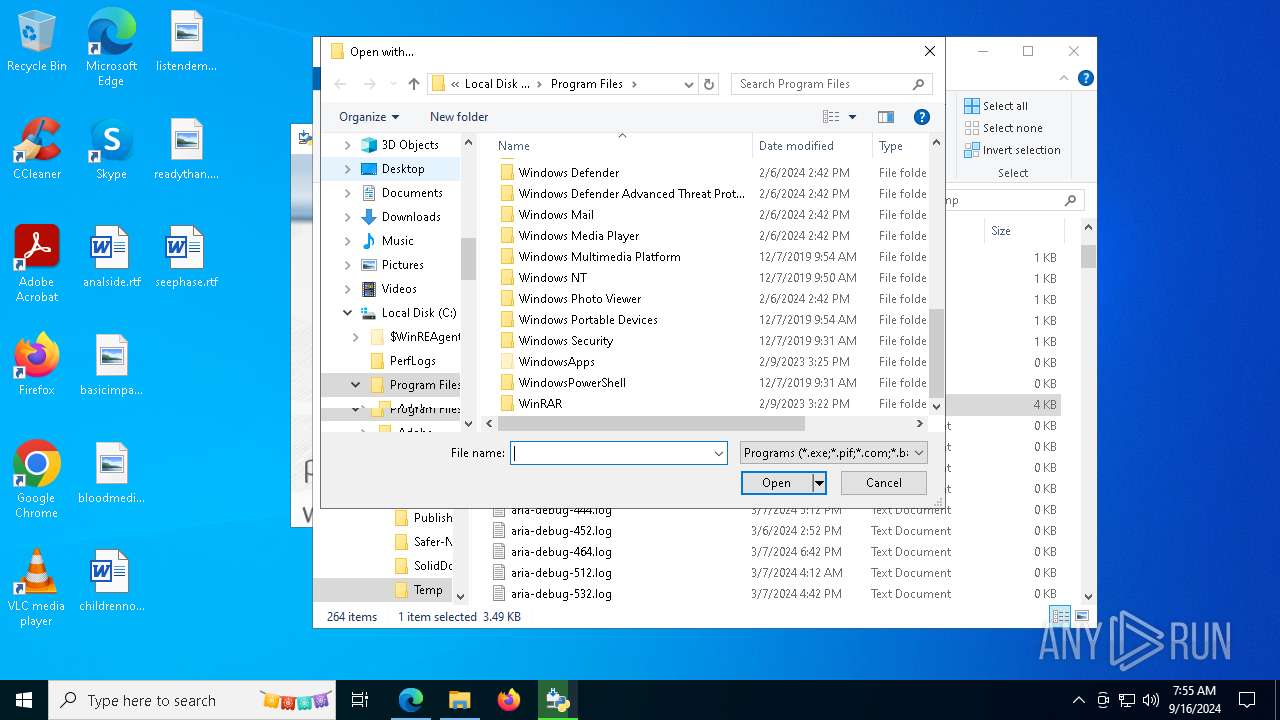
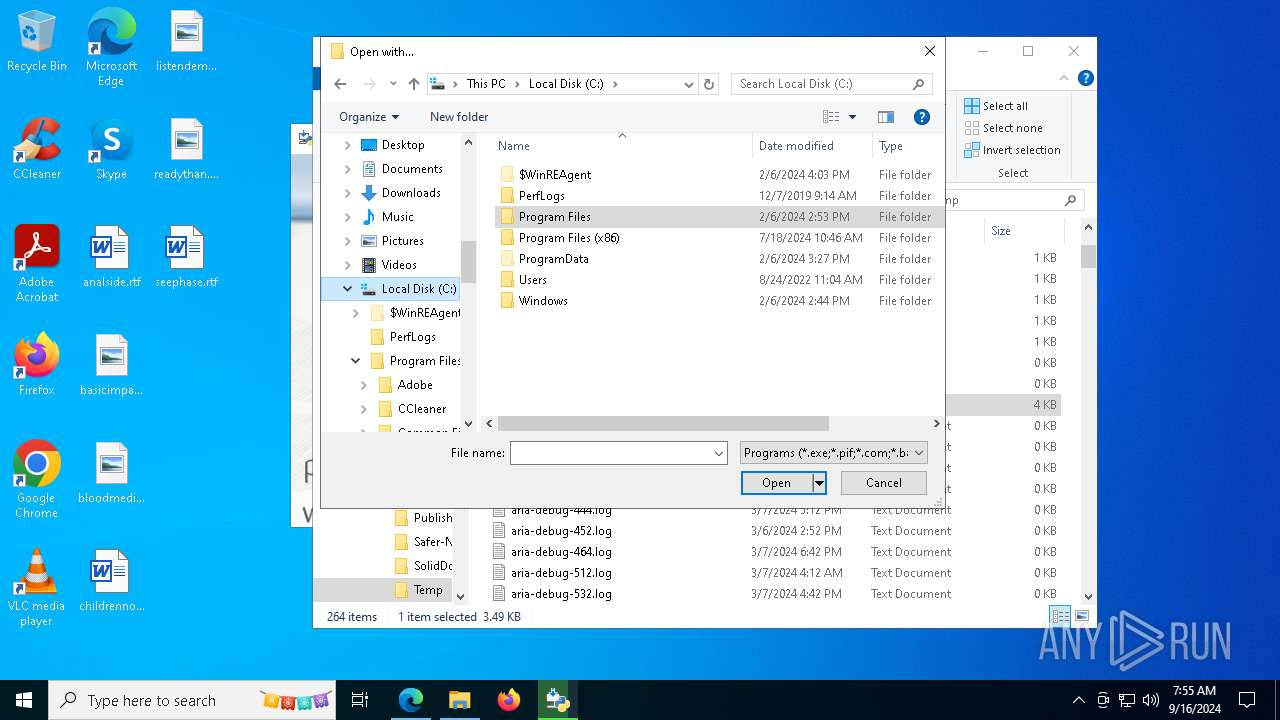
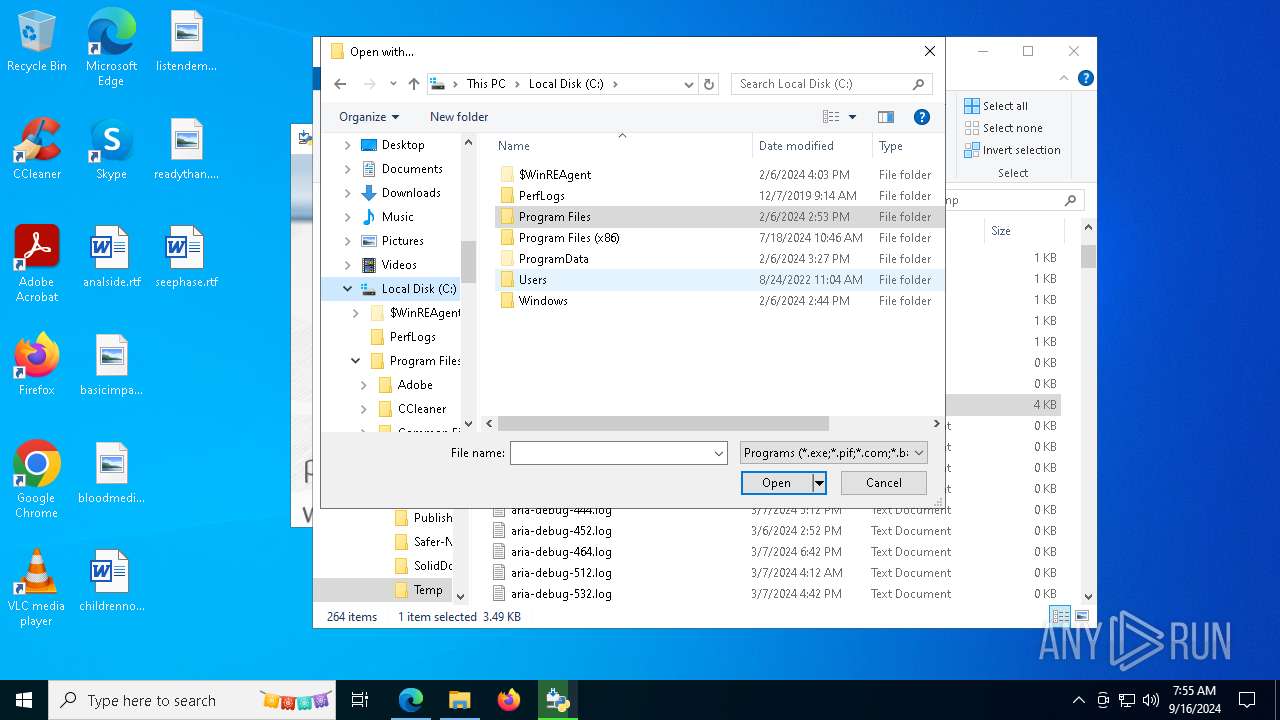
Creates file in the systems drive root
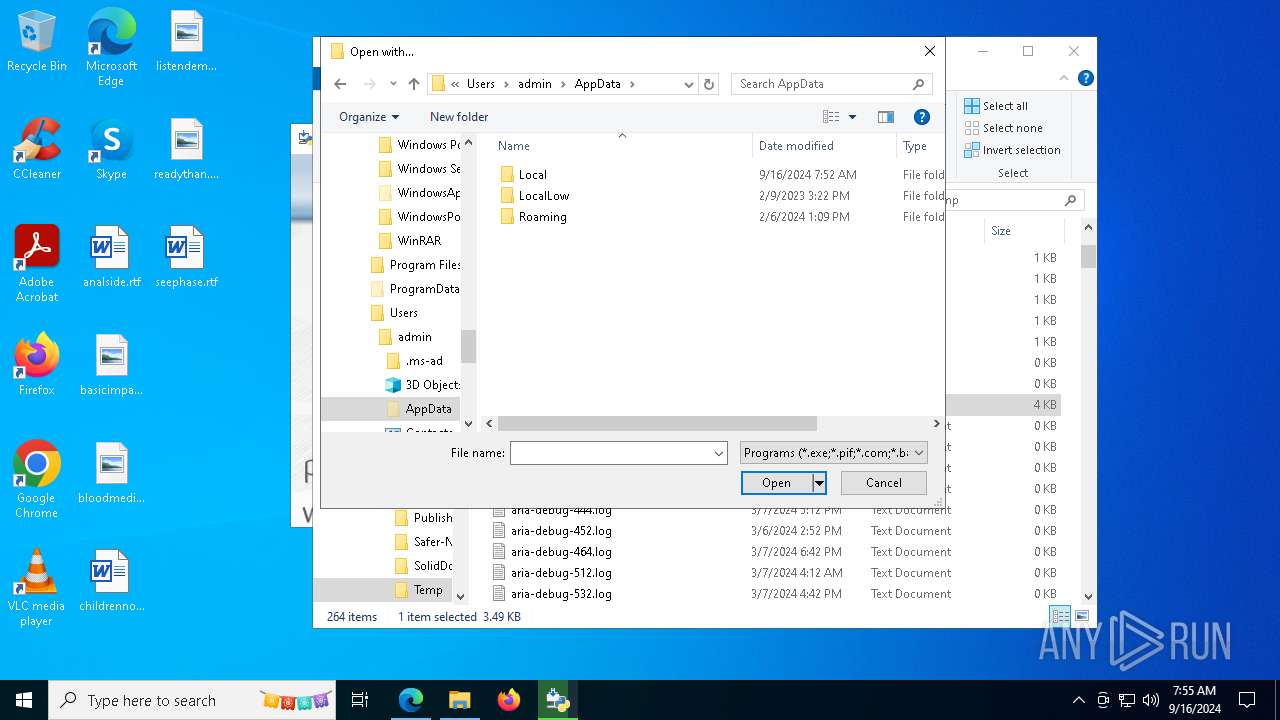
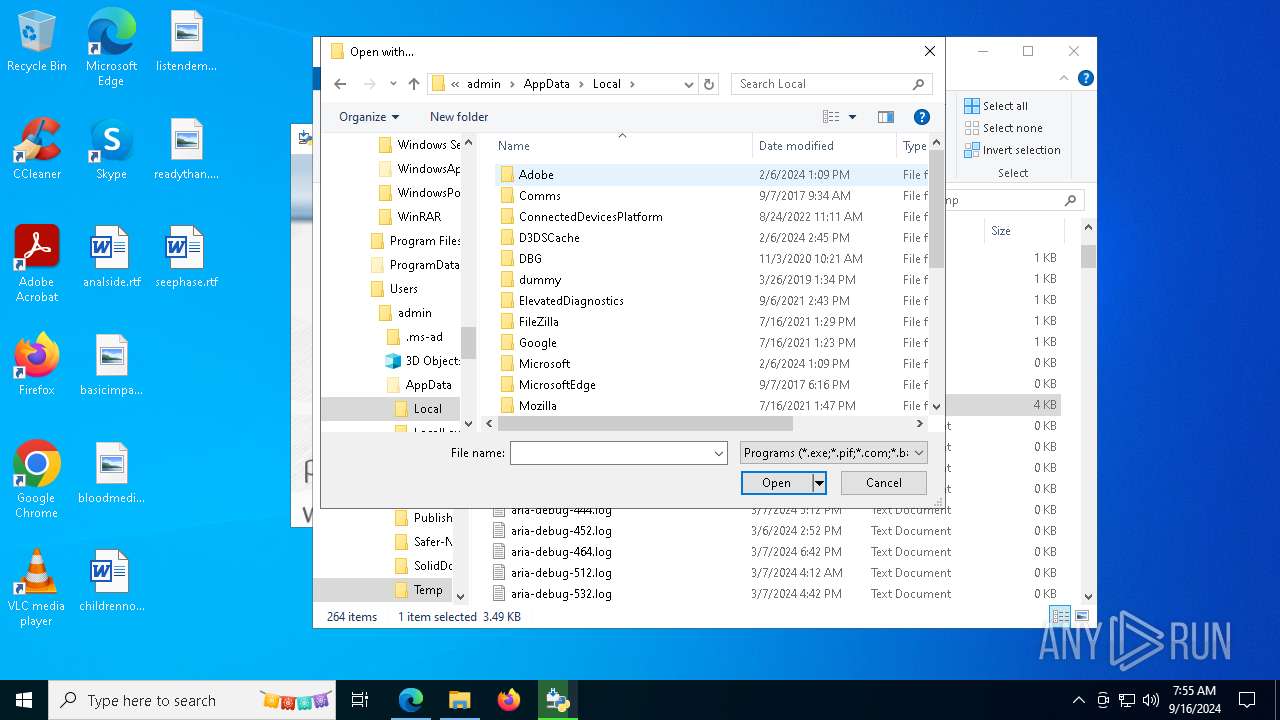
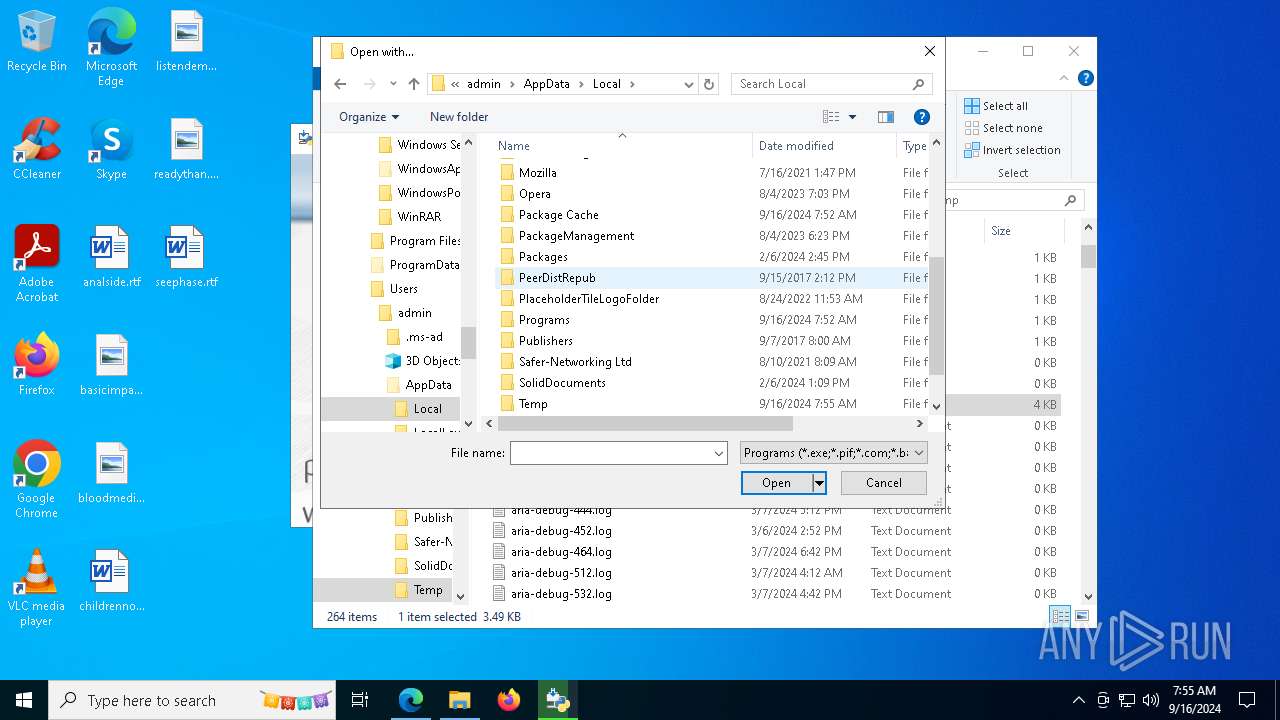
- OpenWith.exe (PID: 7280)
Loads Python modules
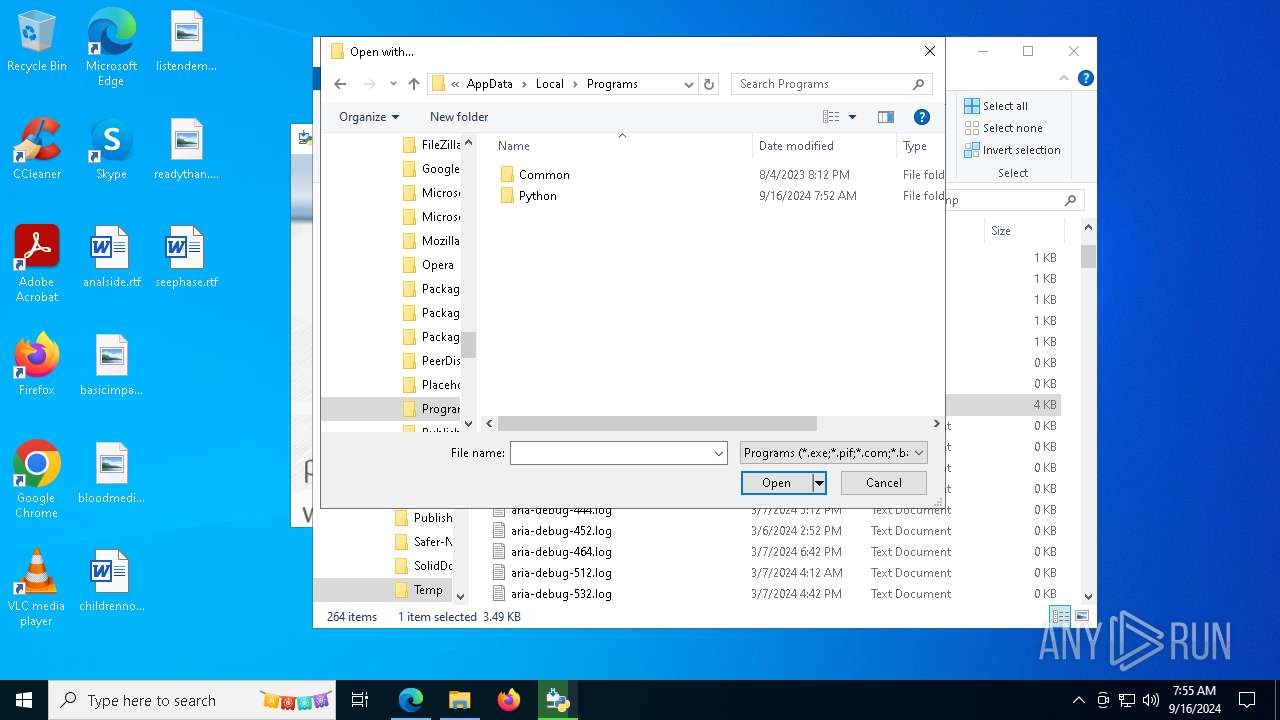
- python.exe (PID: 6964)
INFO
Reads Microsoft Office registry keys
- OpenWith.exe (PID: 7164)
- OpenWith.exe (PID: 7280)
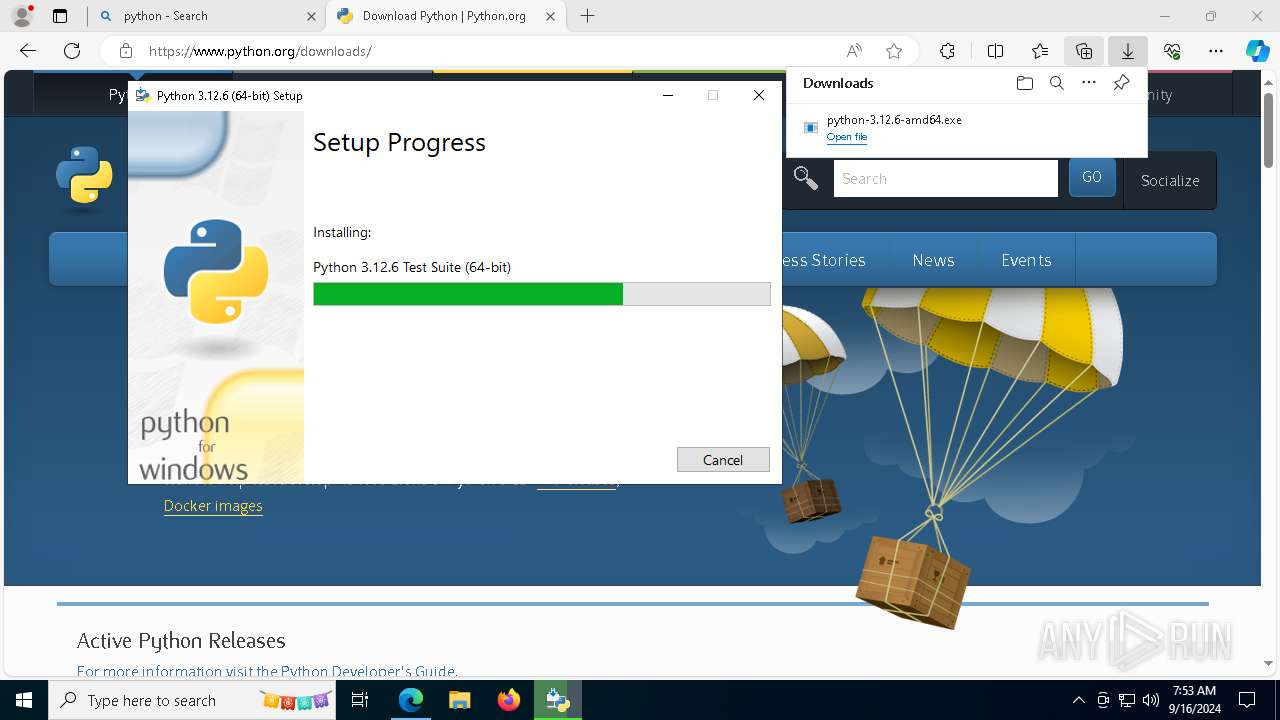
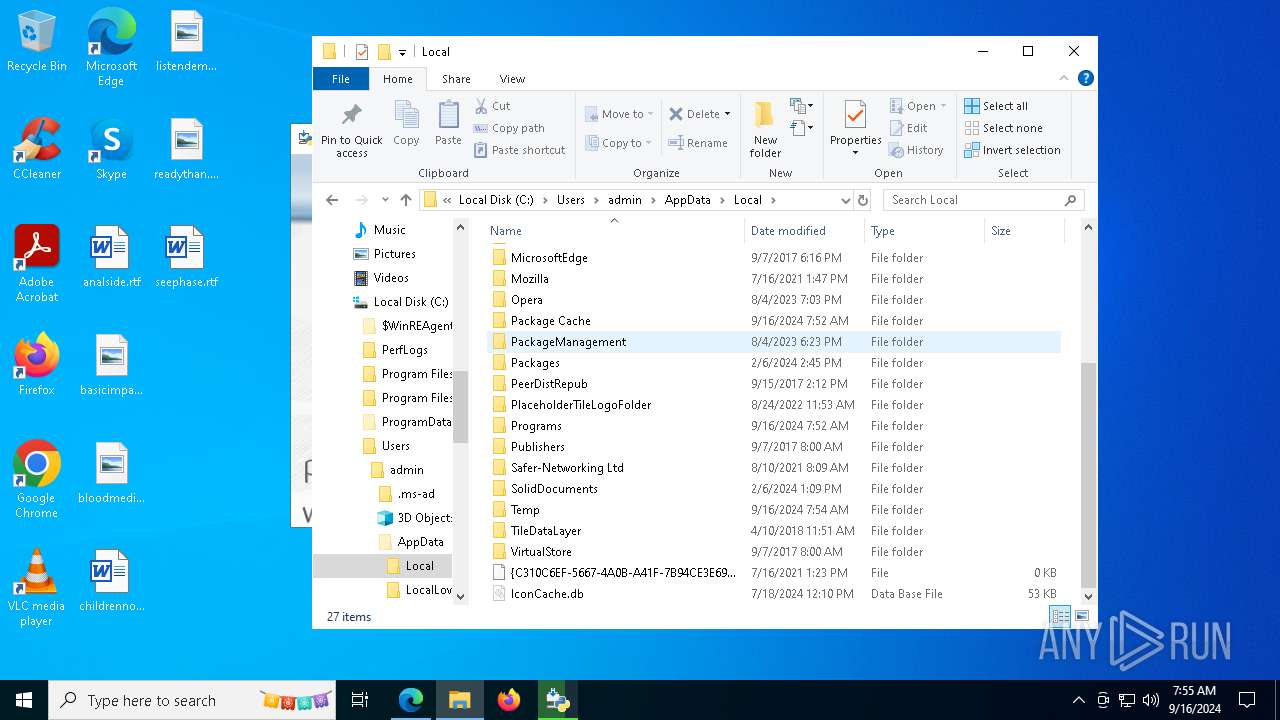
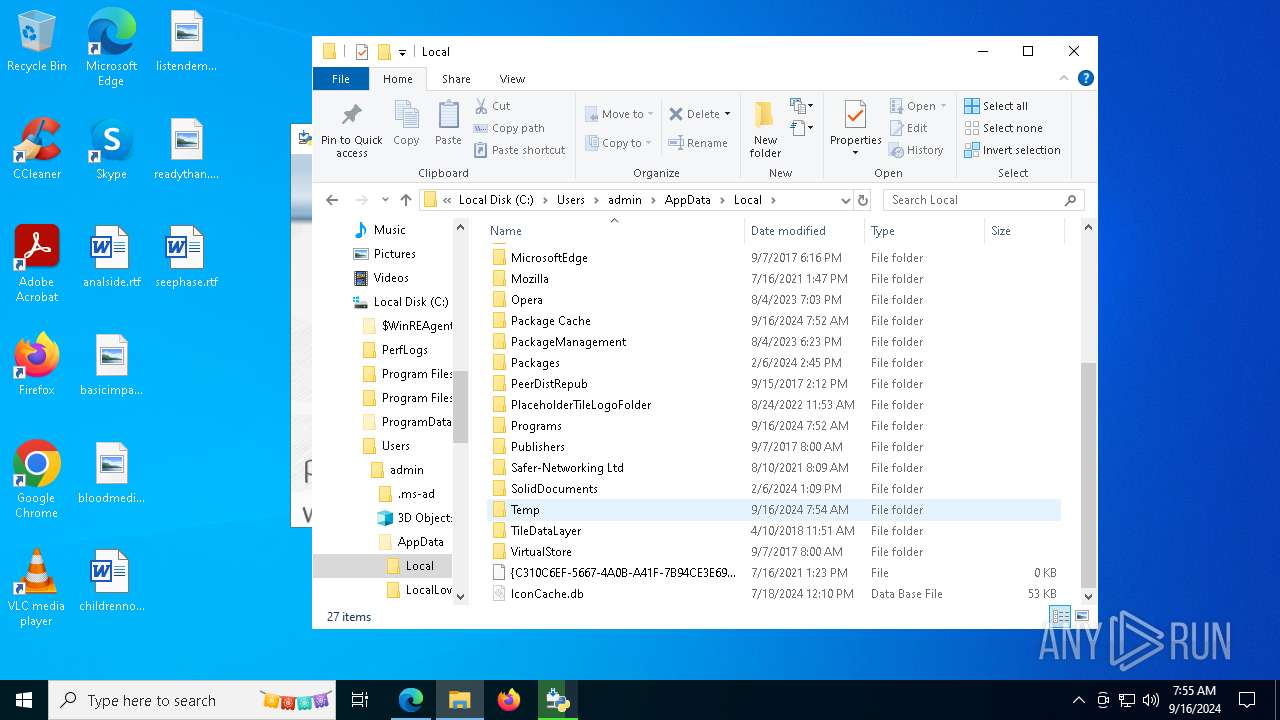
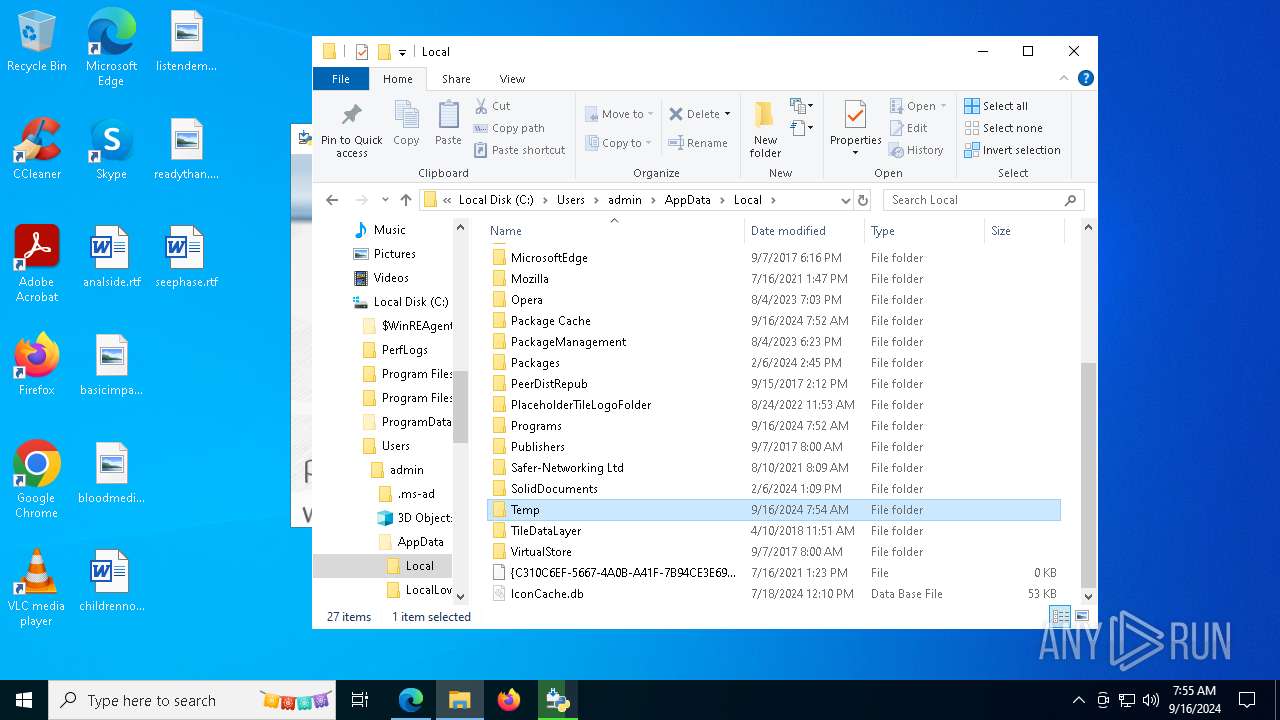
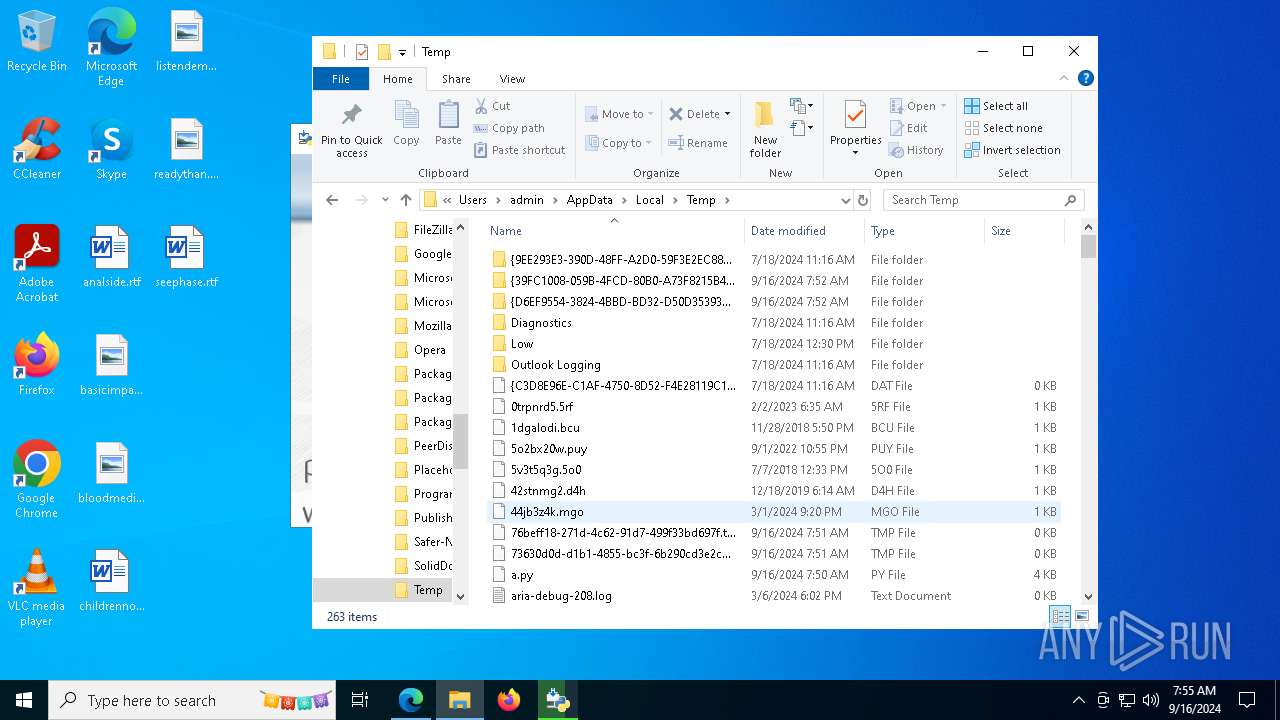
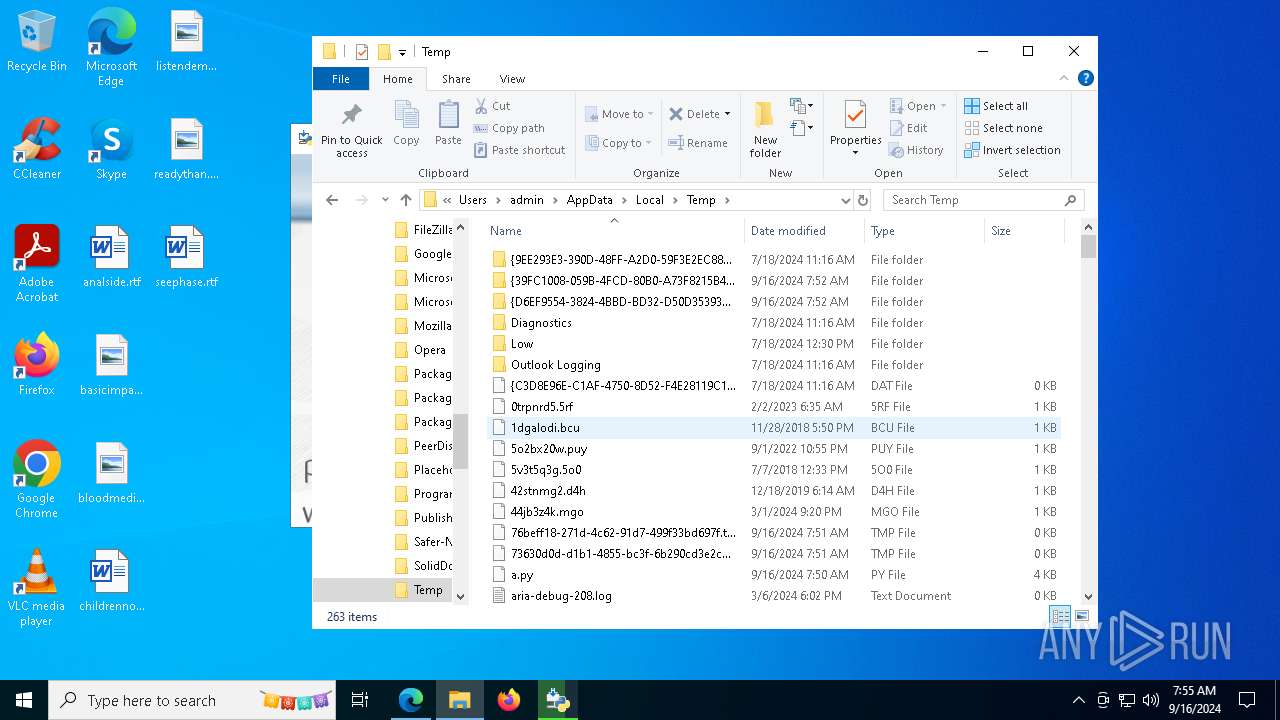
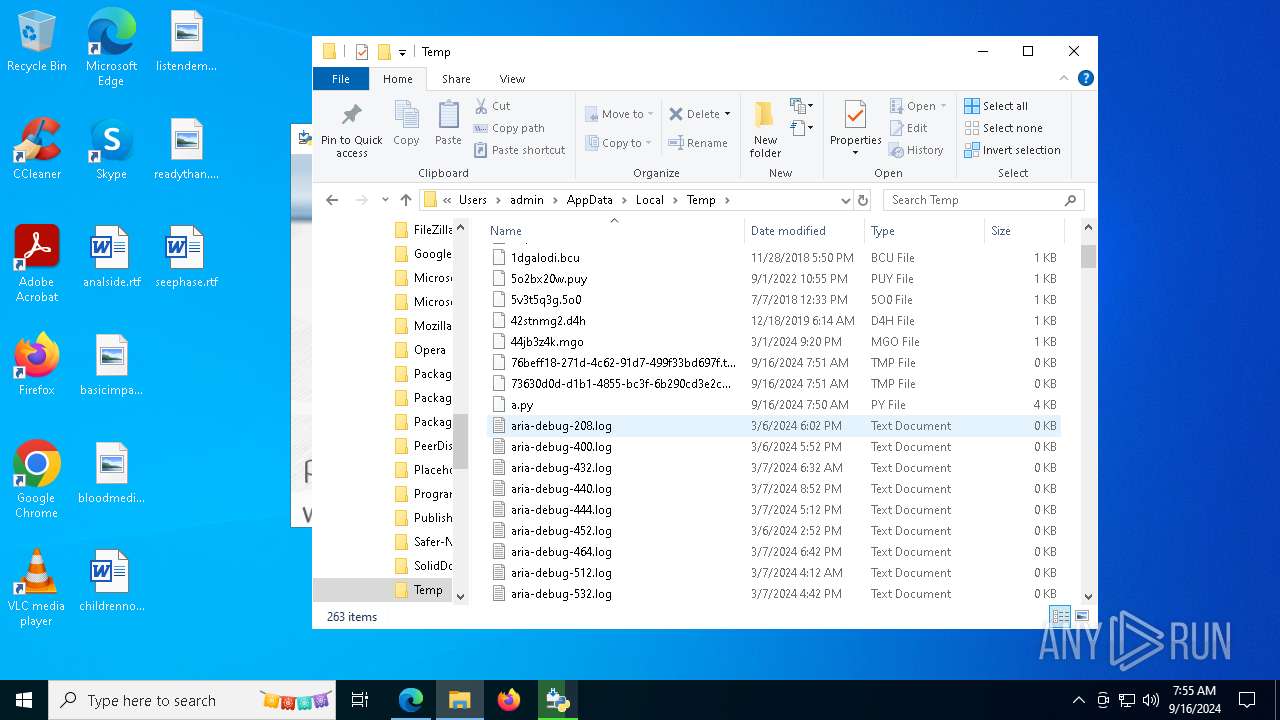
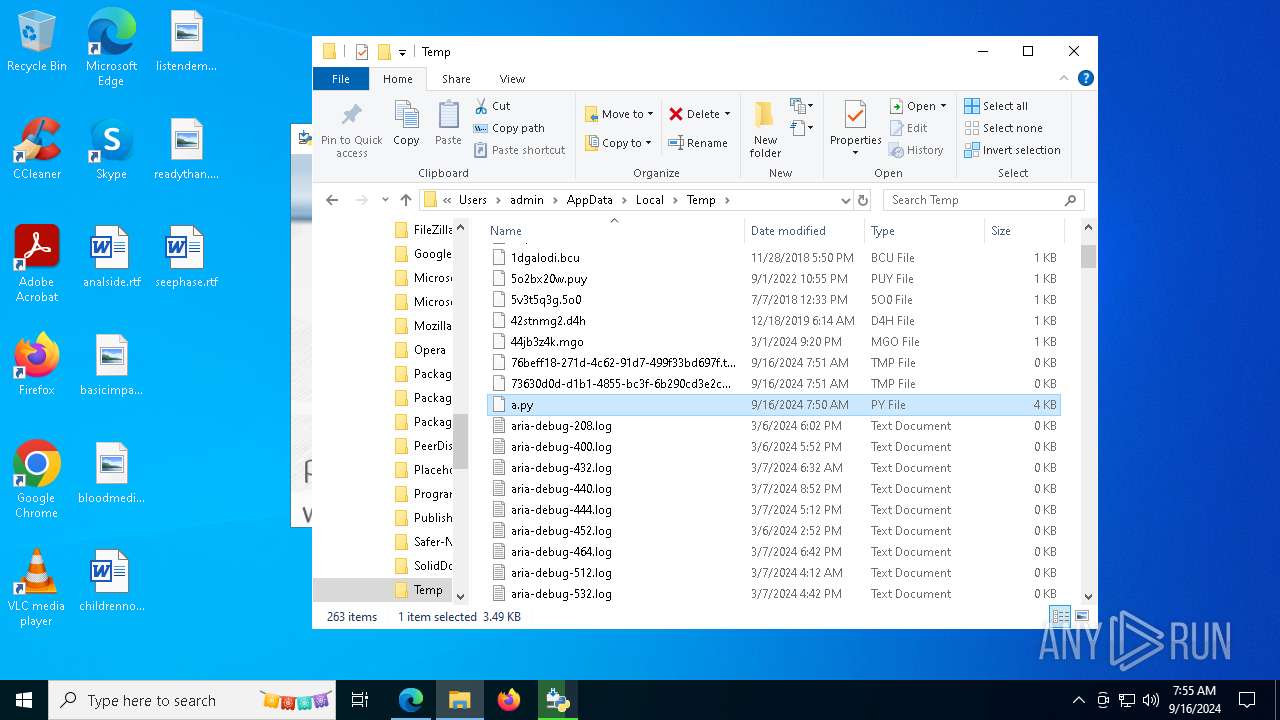
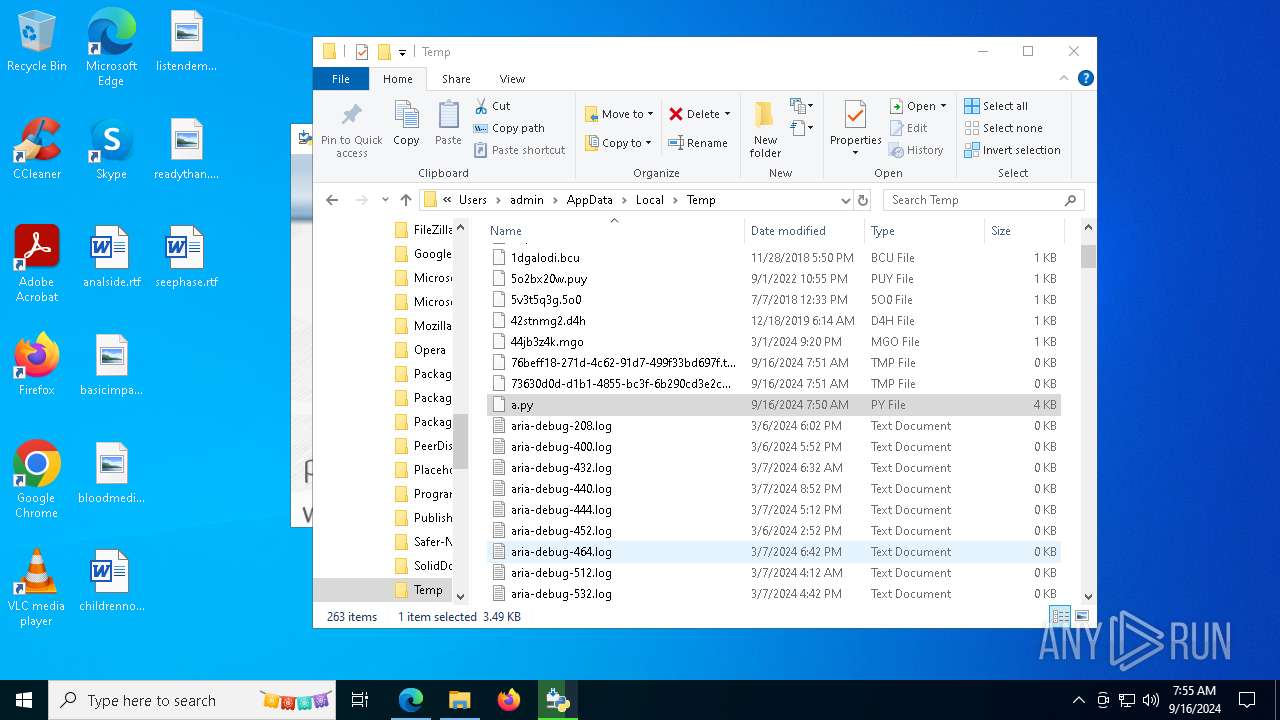
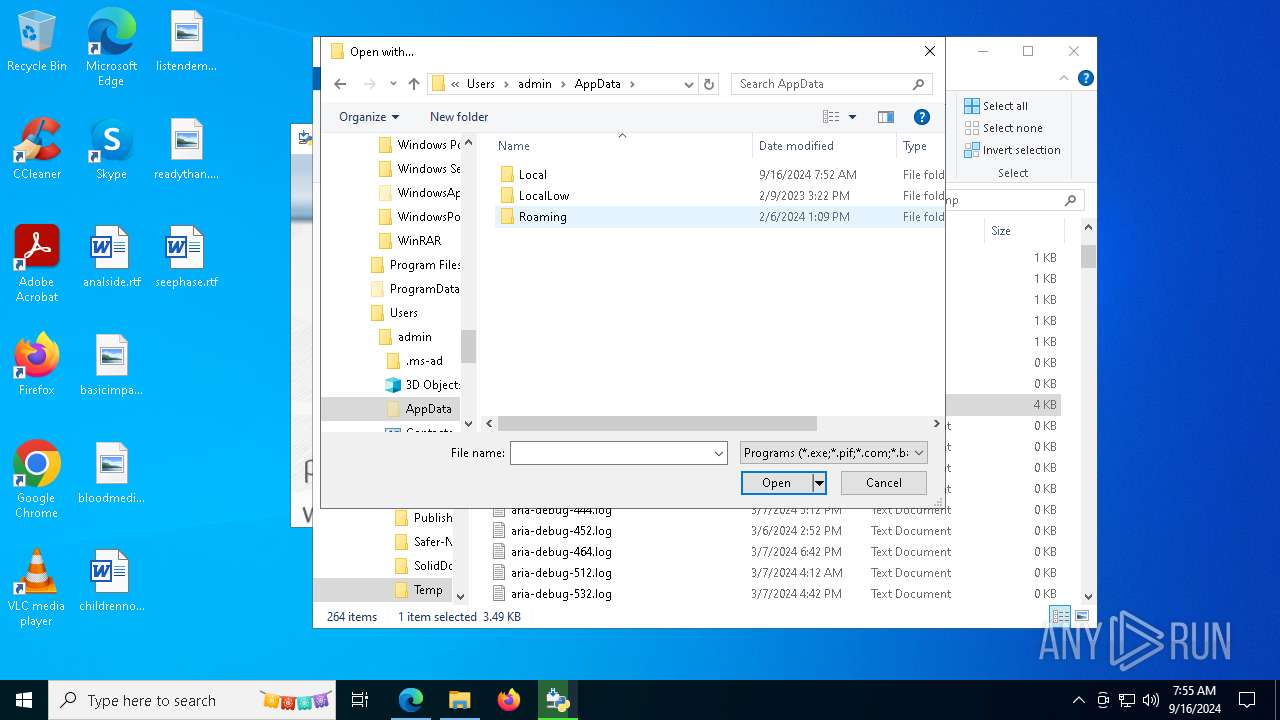
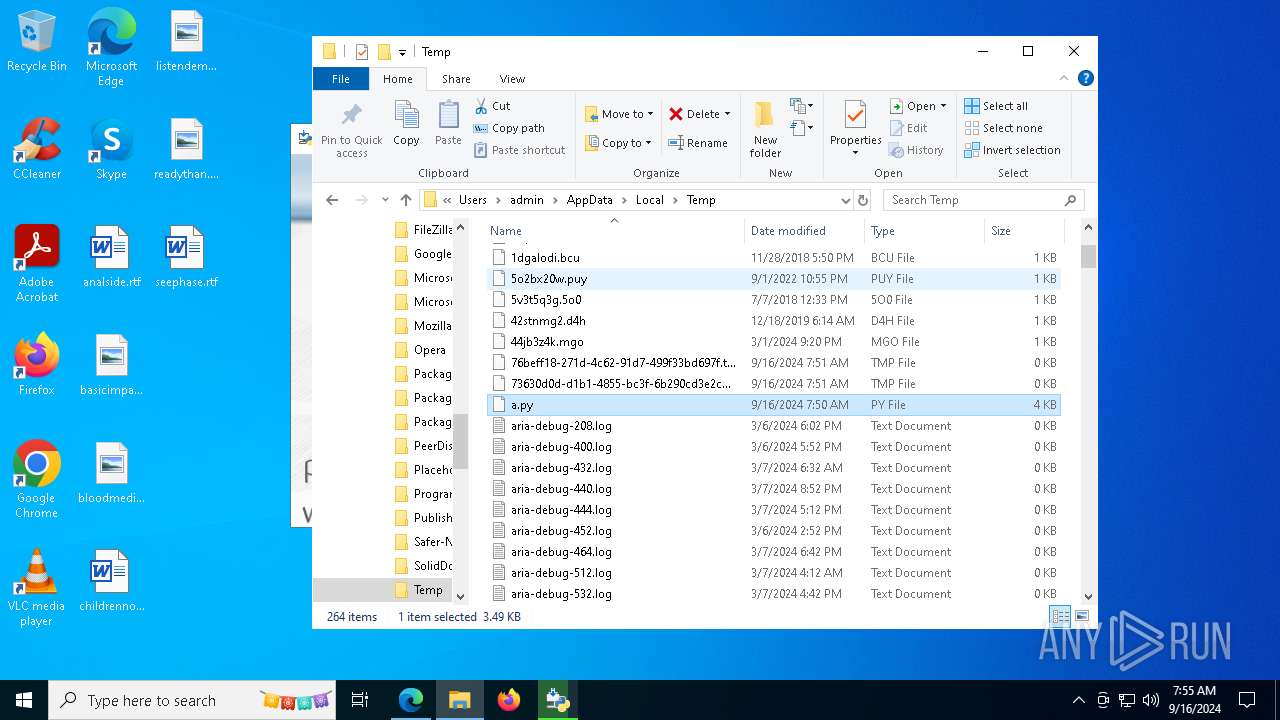
Create files in a temporary directory
- python-3.12.6-amd64.exe (PID: 8060)
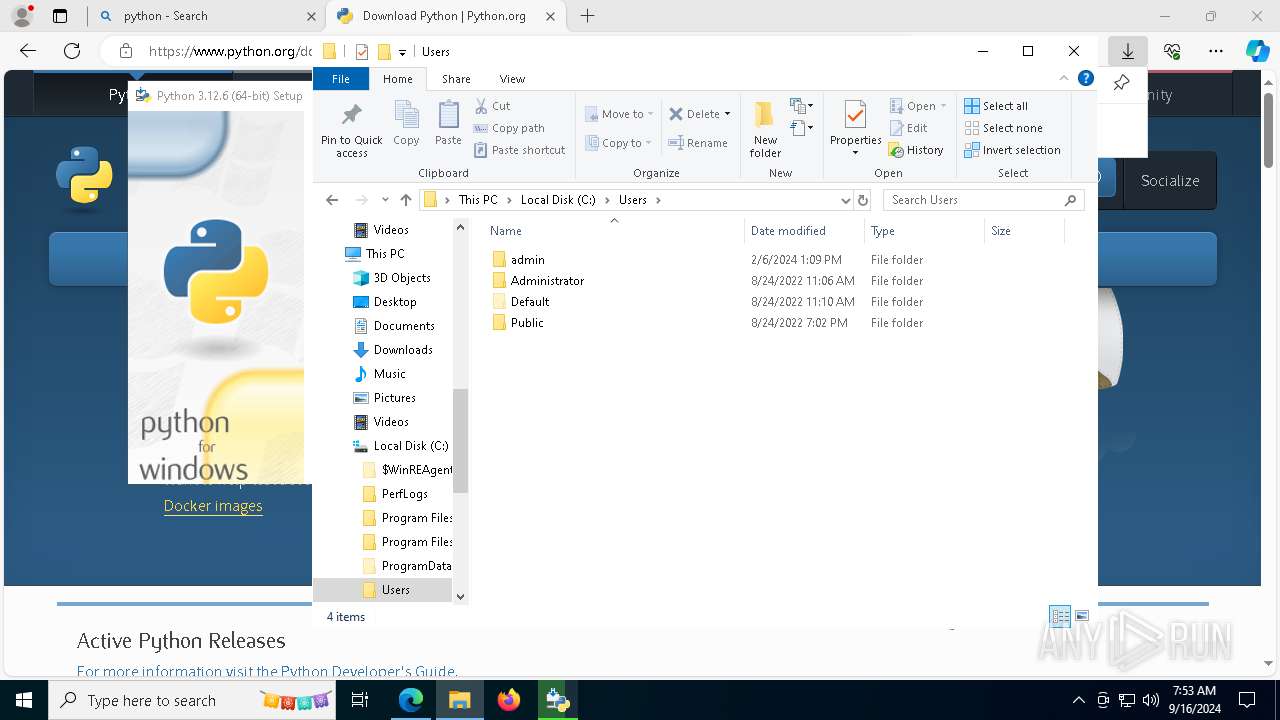
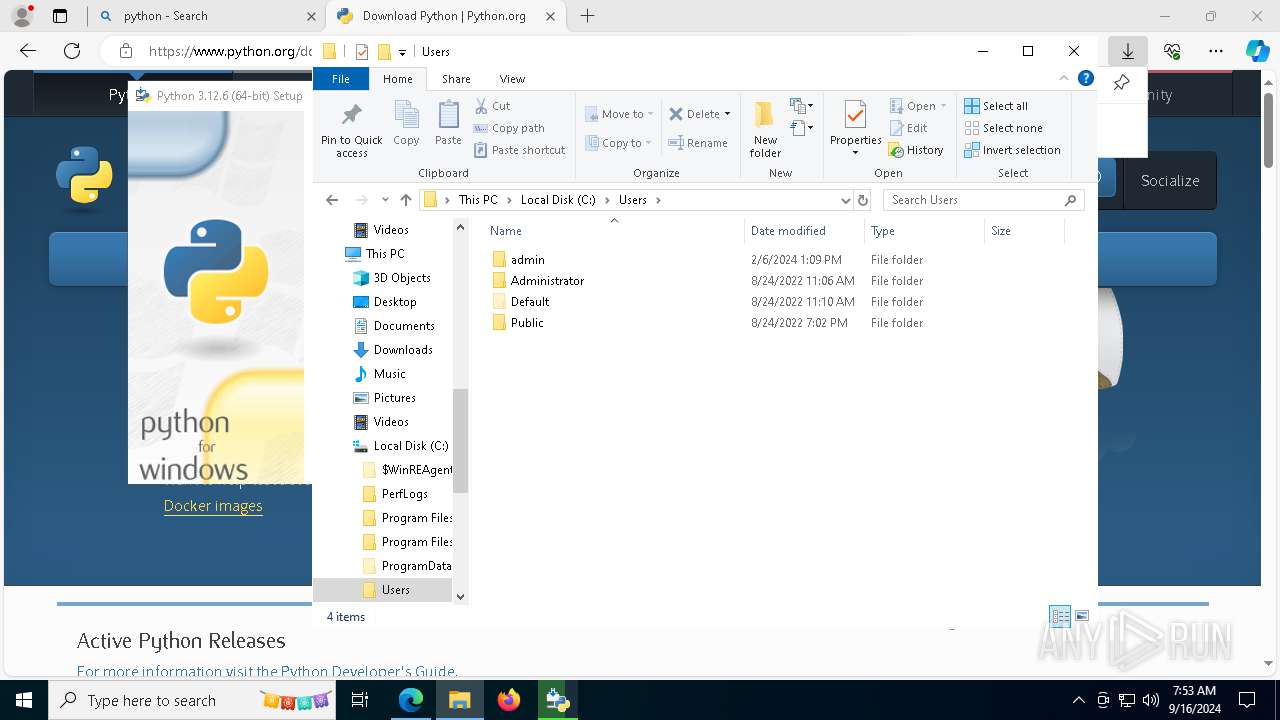
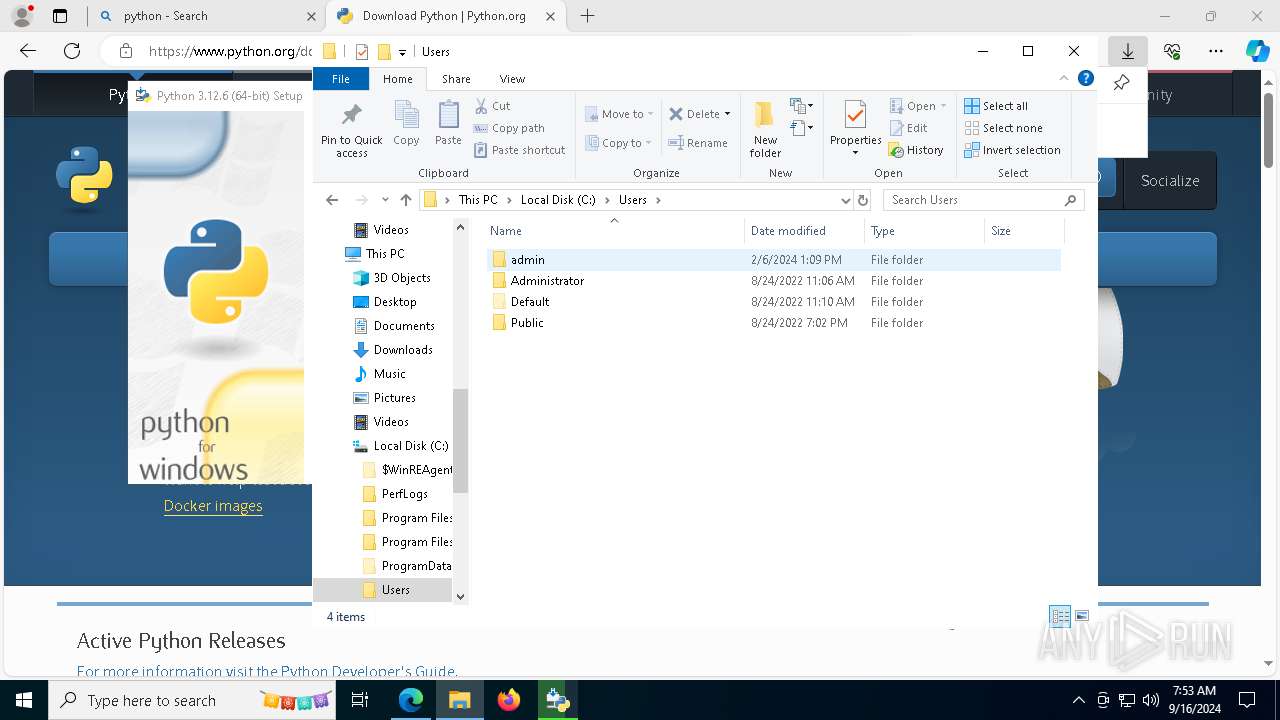
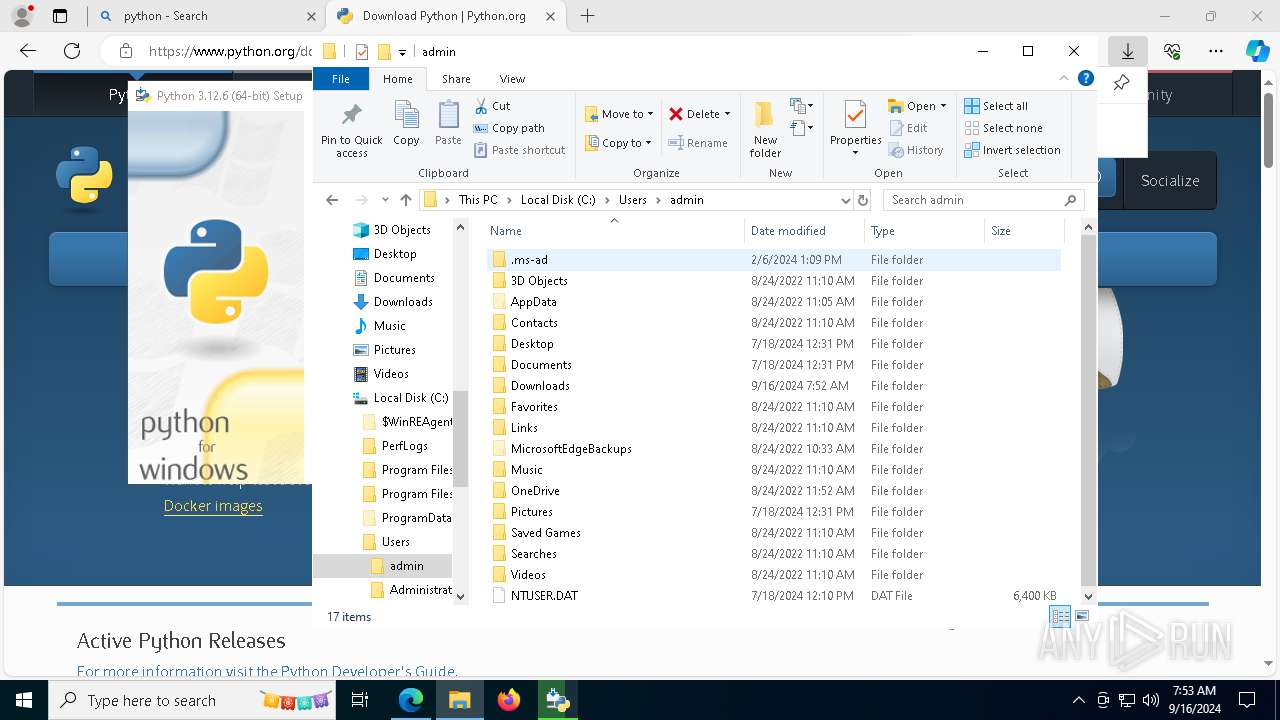
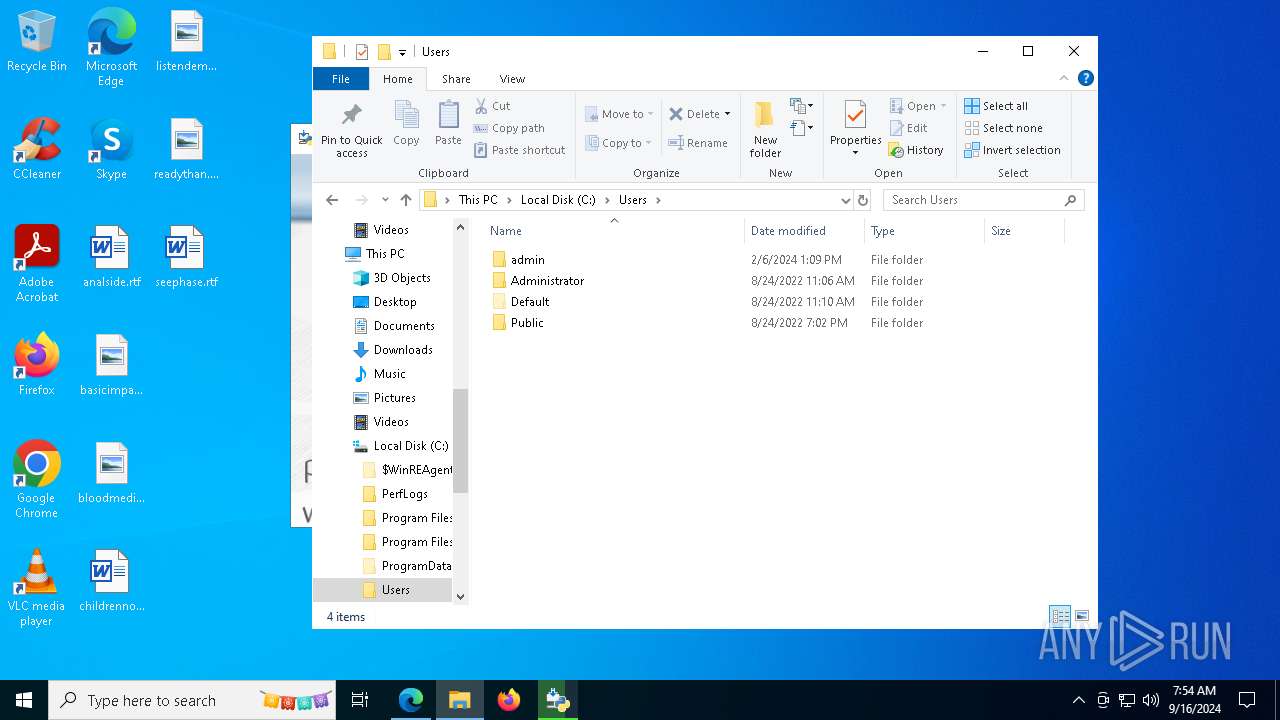
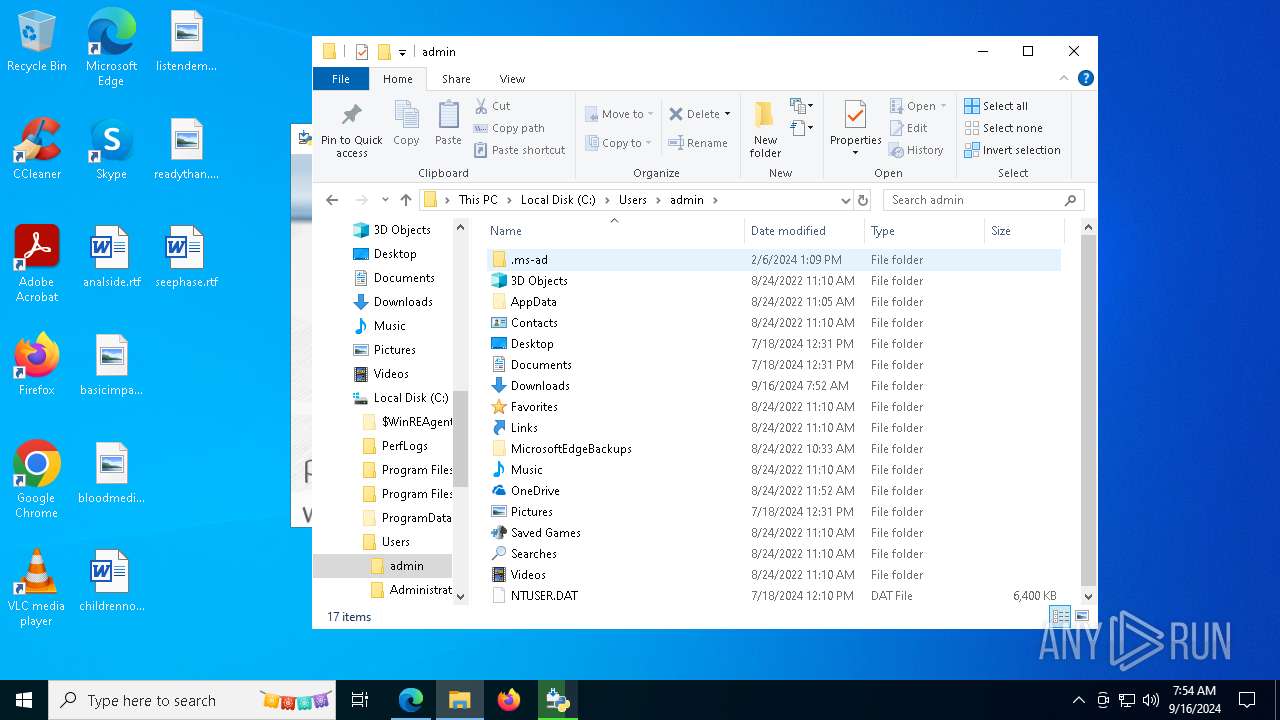
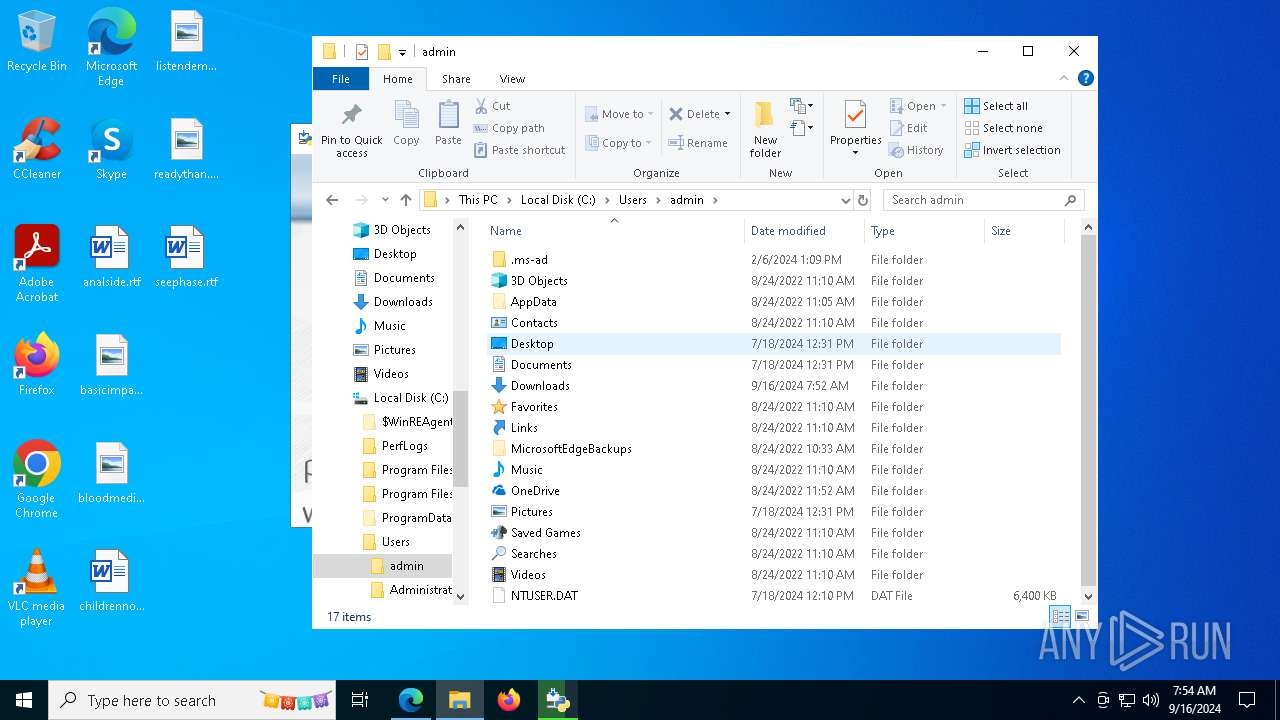
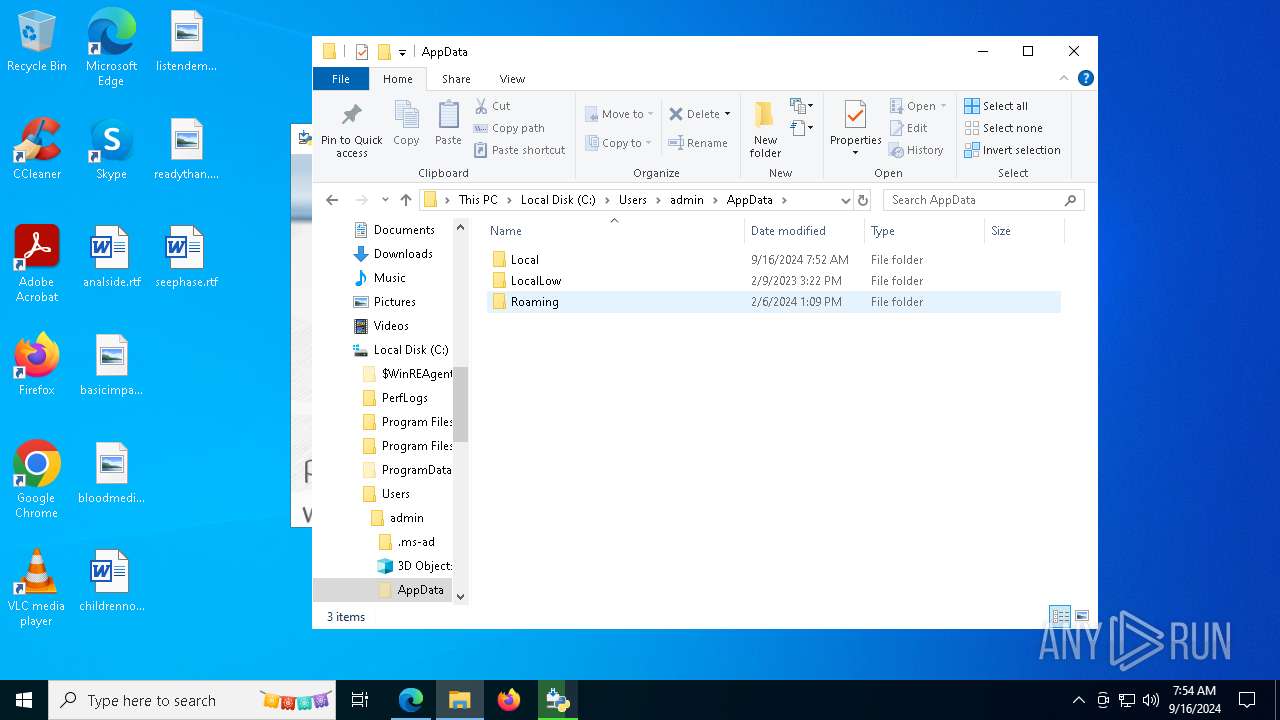
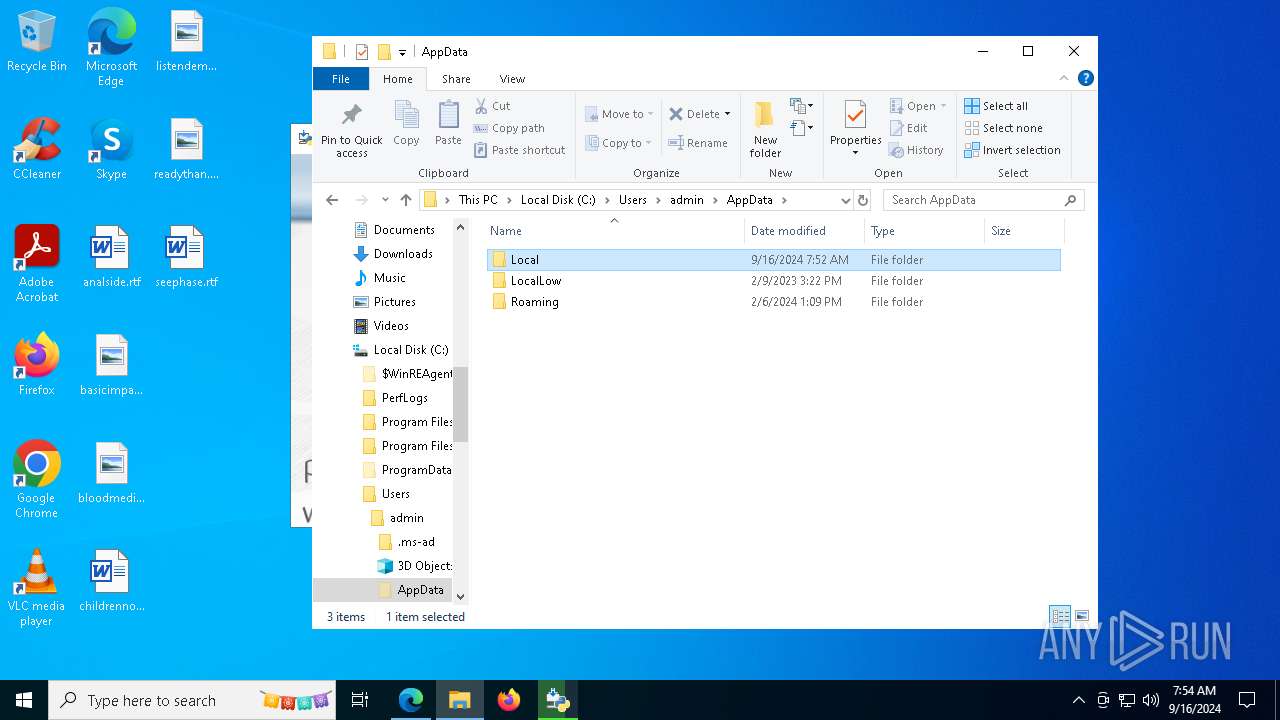
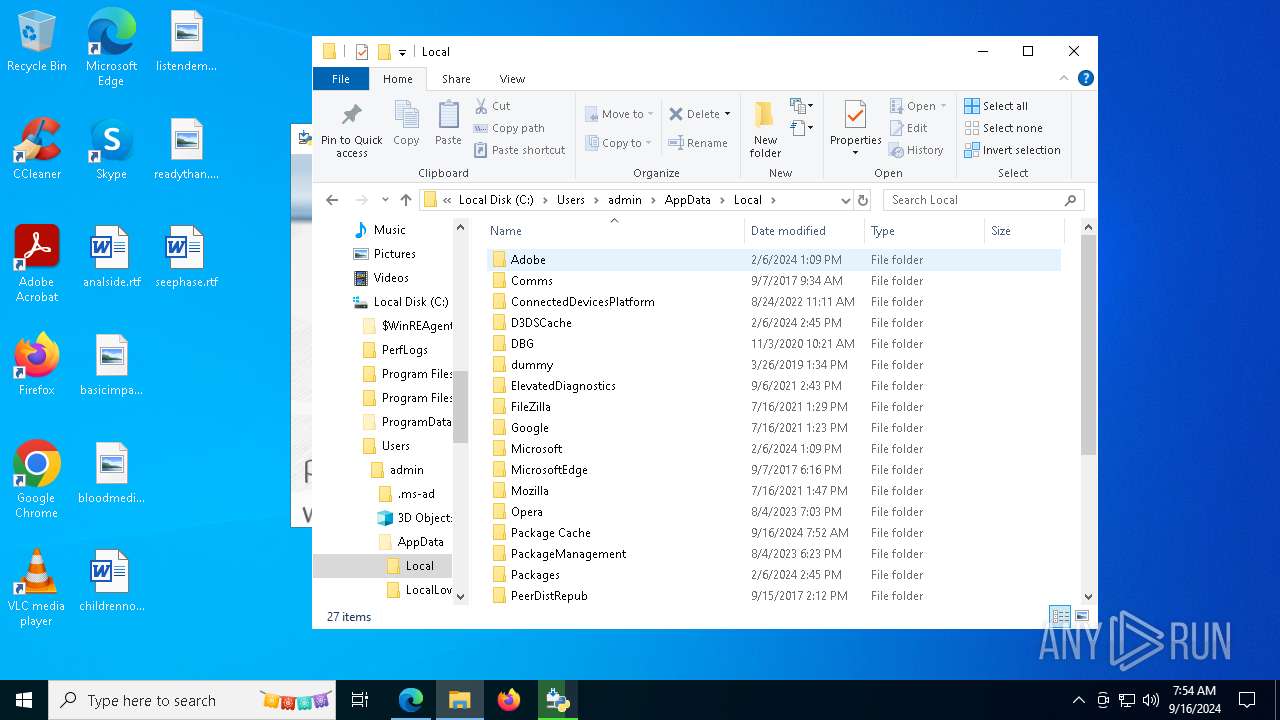
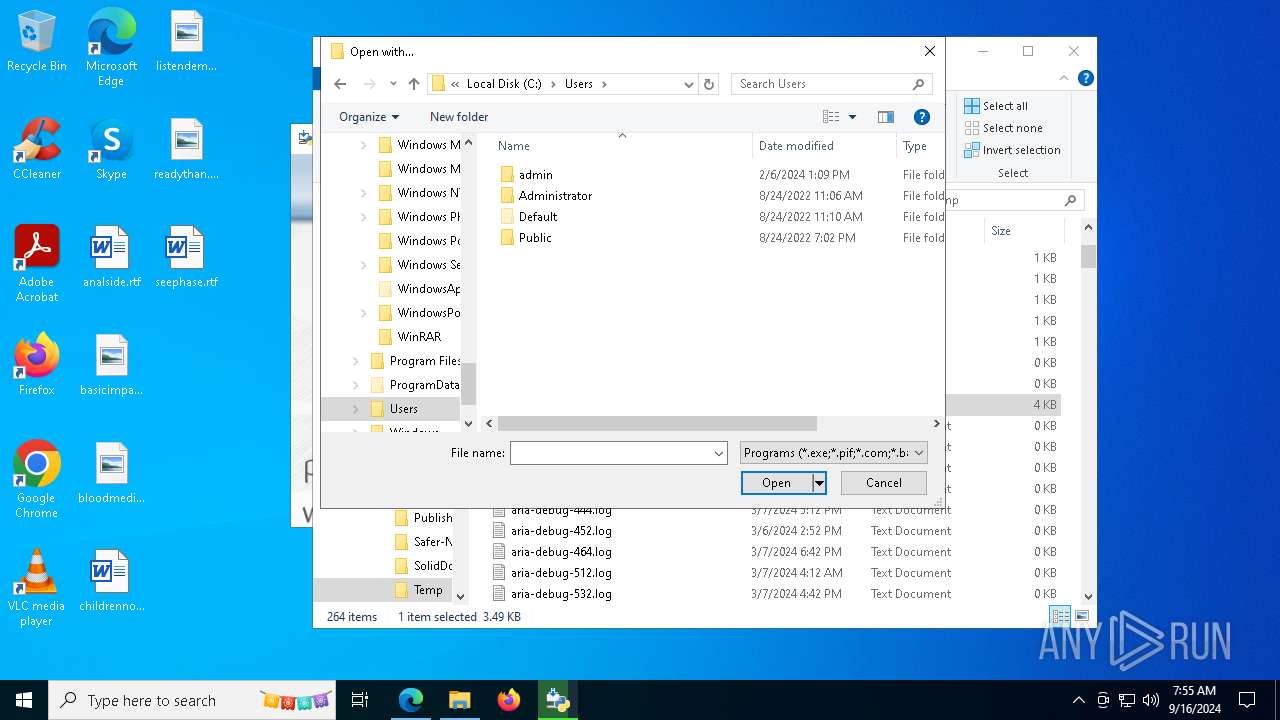
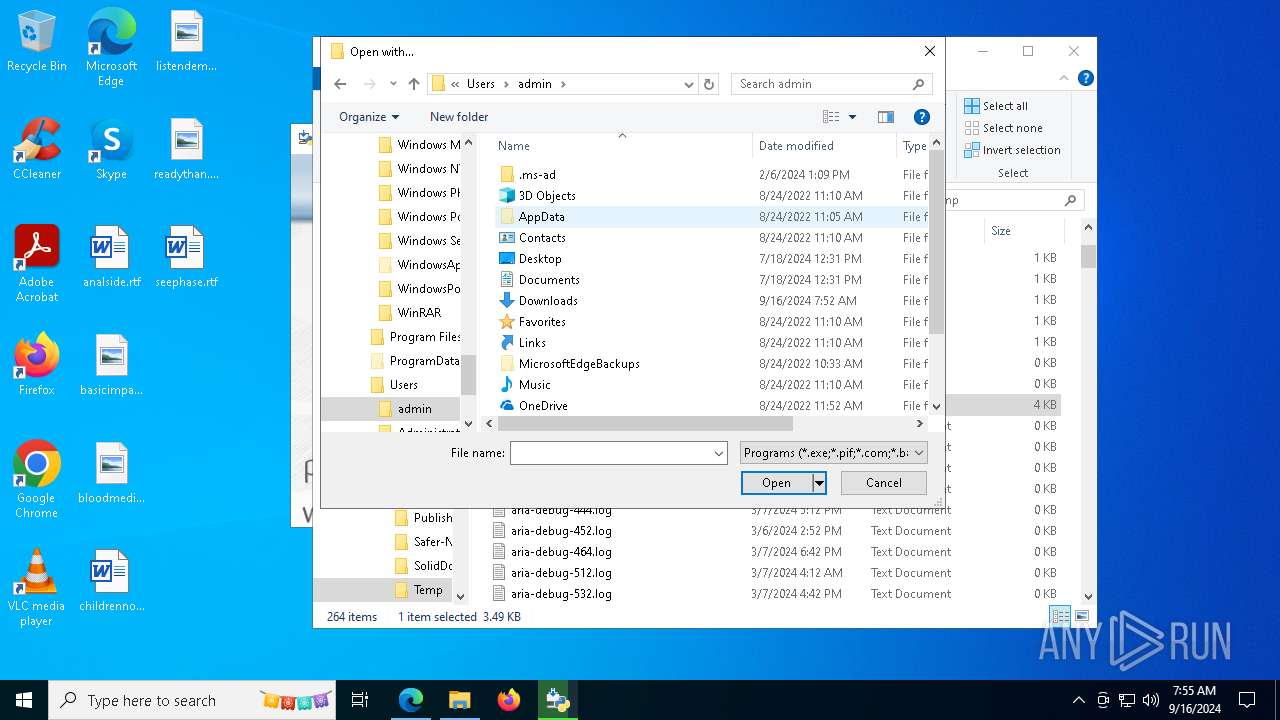
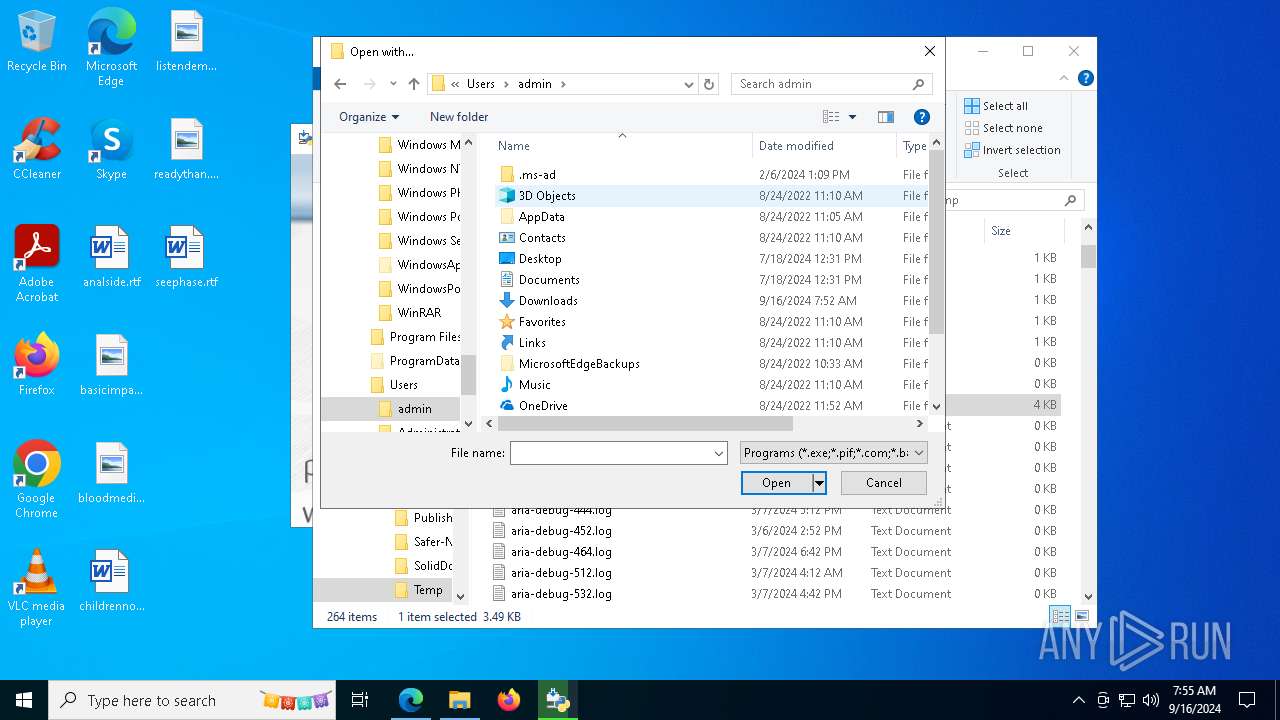
Creates files or folders in the user directory
- python-3.12.6-amd64.exe (PID: 8060)
- msiexec.exe (PID: 7244)
- python.exe (PID: 6964)
Reads the computer name
- python-3.12.6-amd64.exe (PID: 8060)
- msiexec.exe (PID: 7244)
Reads the machine GUID from the registry
- python-3.12.6-amd64.exe (PID: 8060)
- msiexec.exe (PID: 7244)
Reads the software policy settings
- msiexec.exe (PID: 7244)
Checks supported languages
- python-3.12.6-amd64.exe (PID: 8060)
- python.exe (PID: 6964)
- msiexec.exe (PID: 7244)
Executable content was dropped or overwritten
- msiexec.exe (PID: 7244)
The process uses the downloaded file
- OpenWith.exe (PID: 7280)
Reads security settings of Internet Explorer
- OpenWith.exe (PID: 7280)
Creates a software uninstall entry
- msiexec.exe (PID: 7244)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
200
Monitored processes
7
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3708 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | python.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6944 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
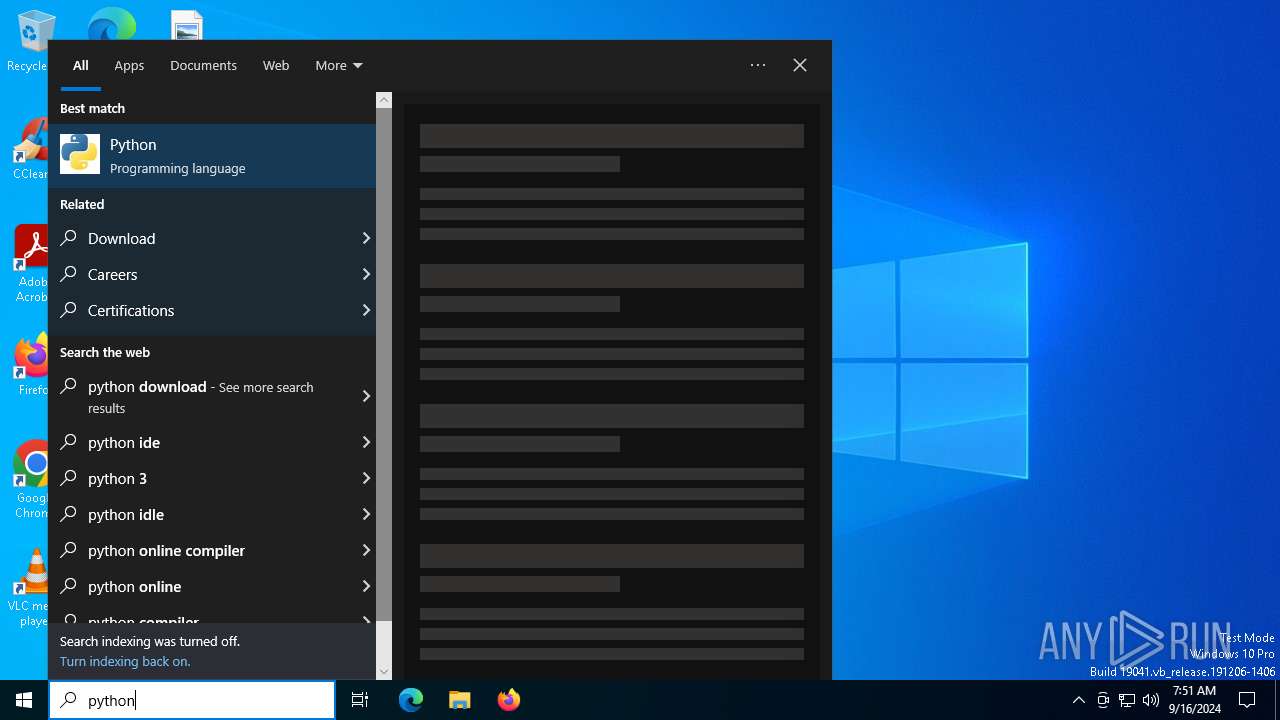
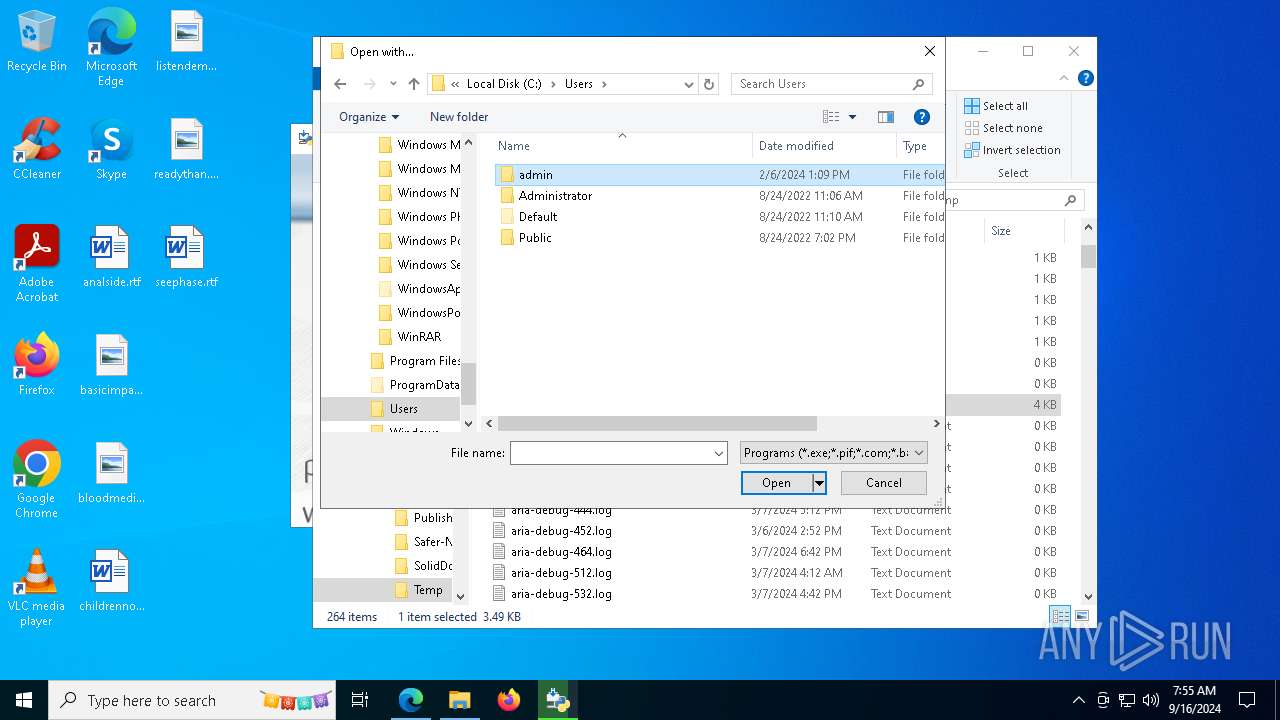
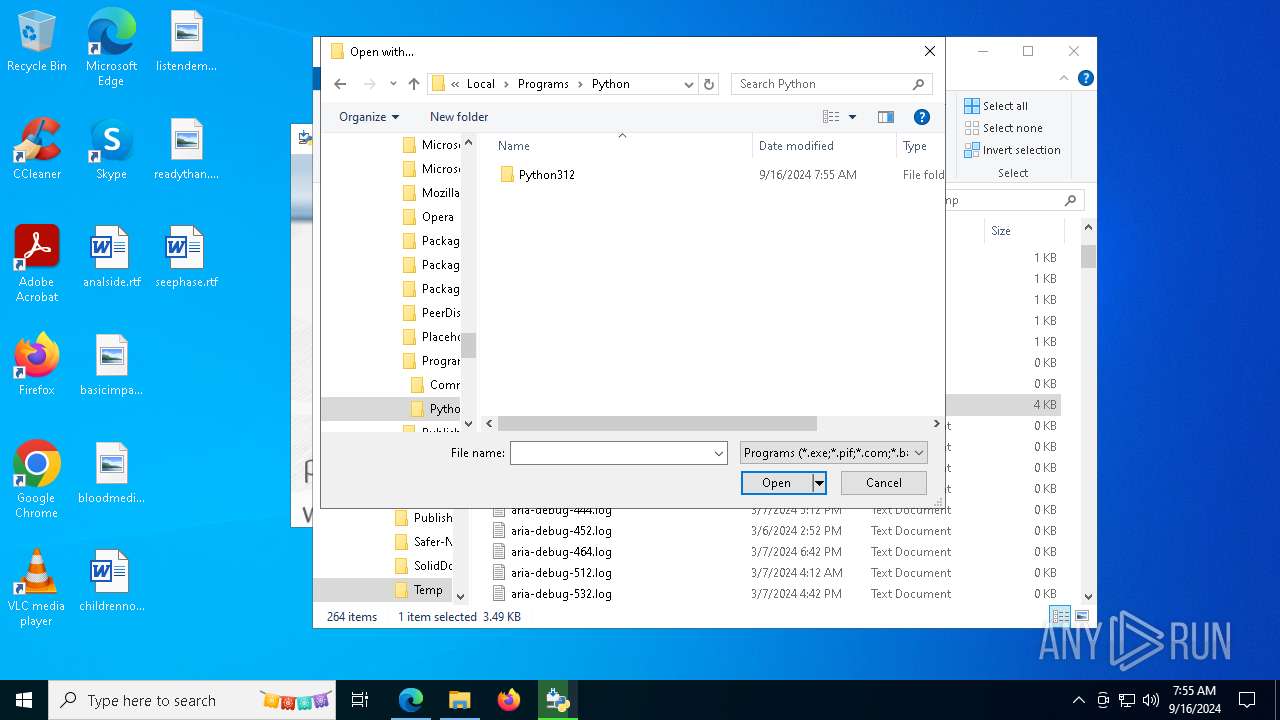
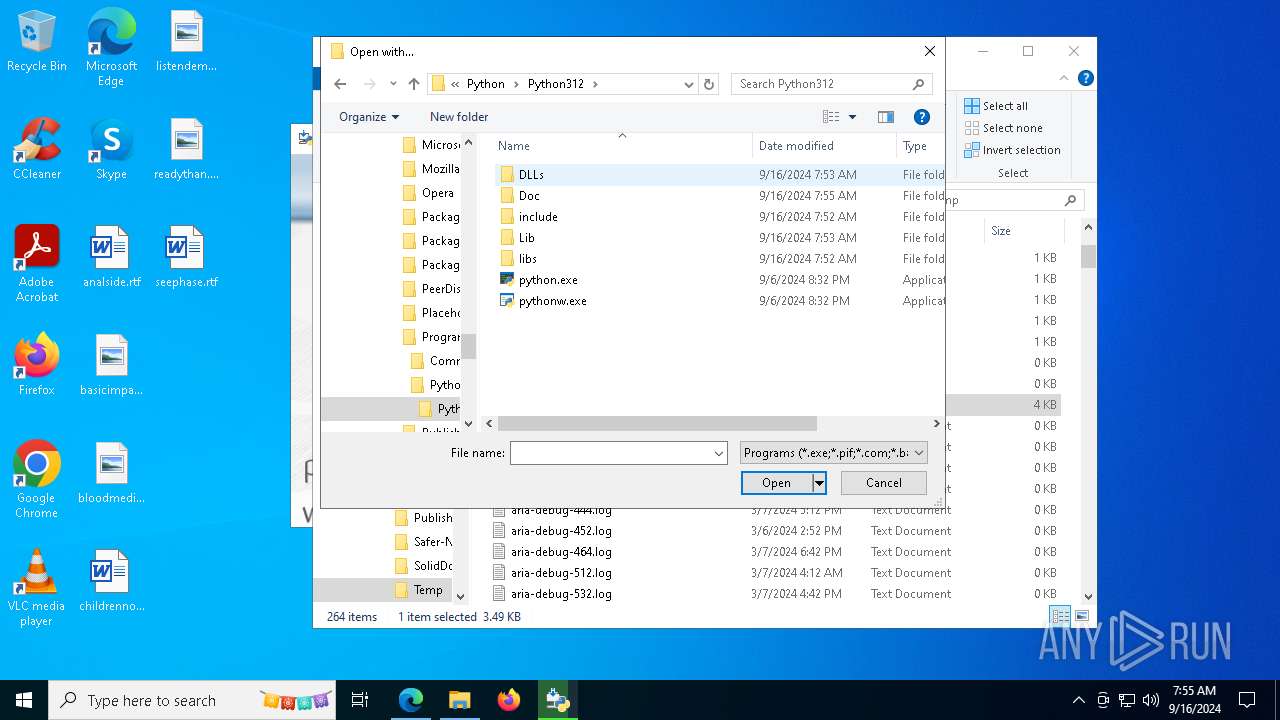
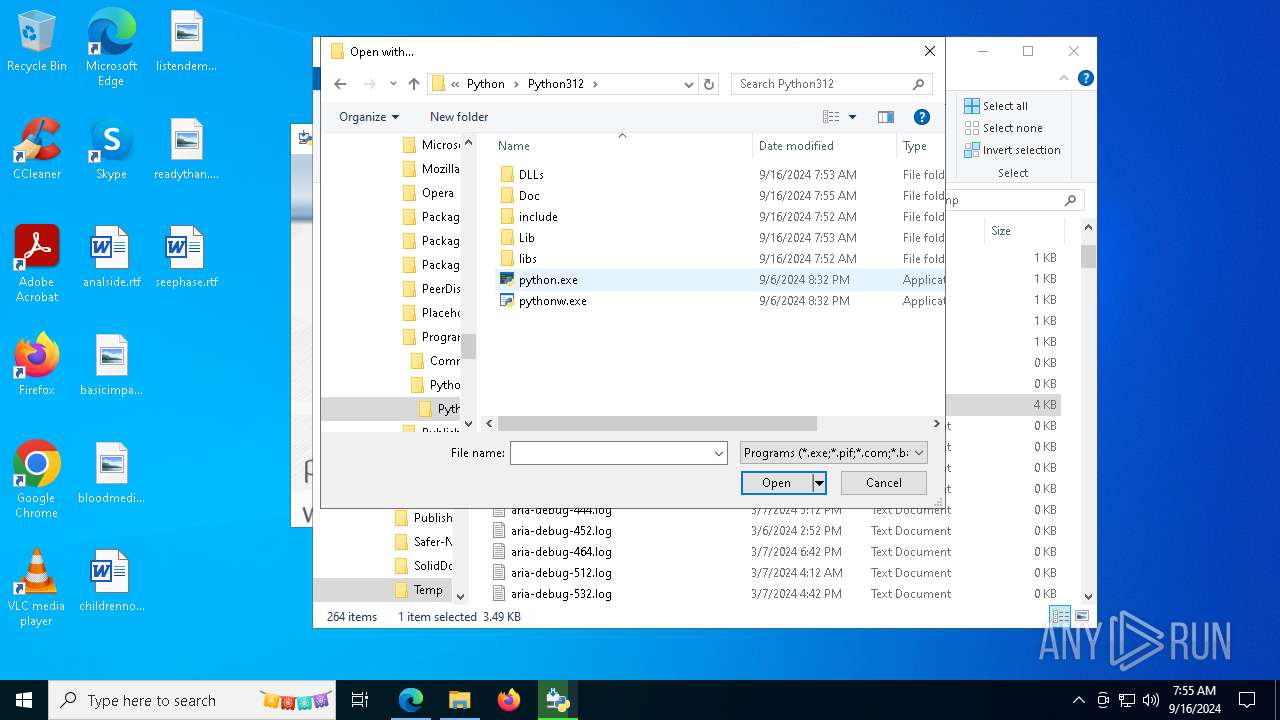
| 6964 | "C:\Users\admin\AppData\Local\Programs\Python\Python312\python.exe" "C:\Users\admin\AppData\Local\Temp\a.py" | C:\Users\admin\AppData\Local\Programs\Python\Python312\python.exe | — | OpenWith.exe | |||||||||||
User: admin Company: Python Software Foundation Integrity Level: MEDIUM Description: Python Exit code: 1 Version: 3.12.6 Modules
| |||||||||||||||
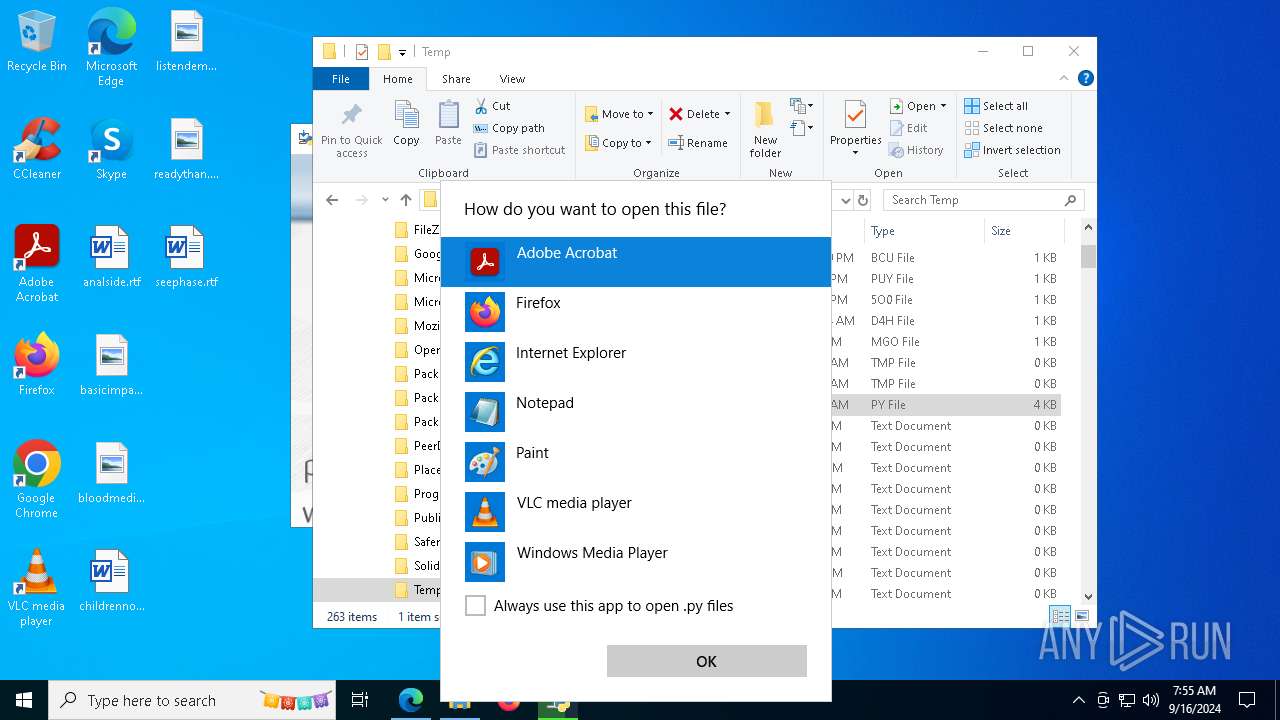
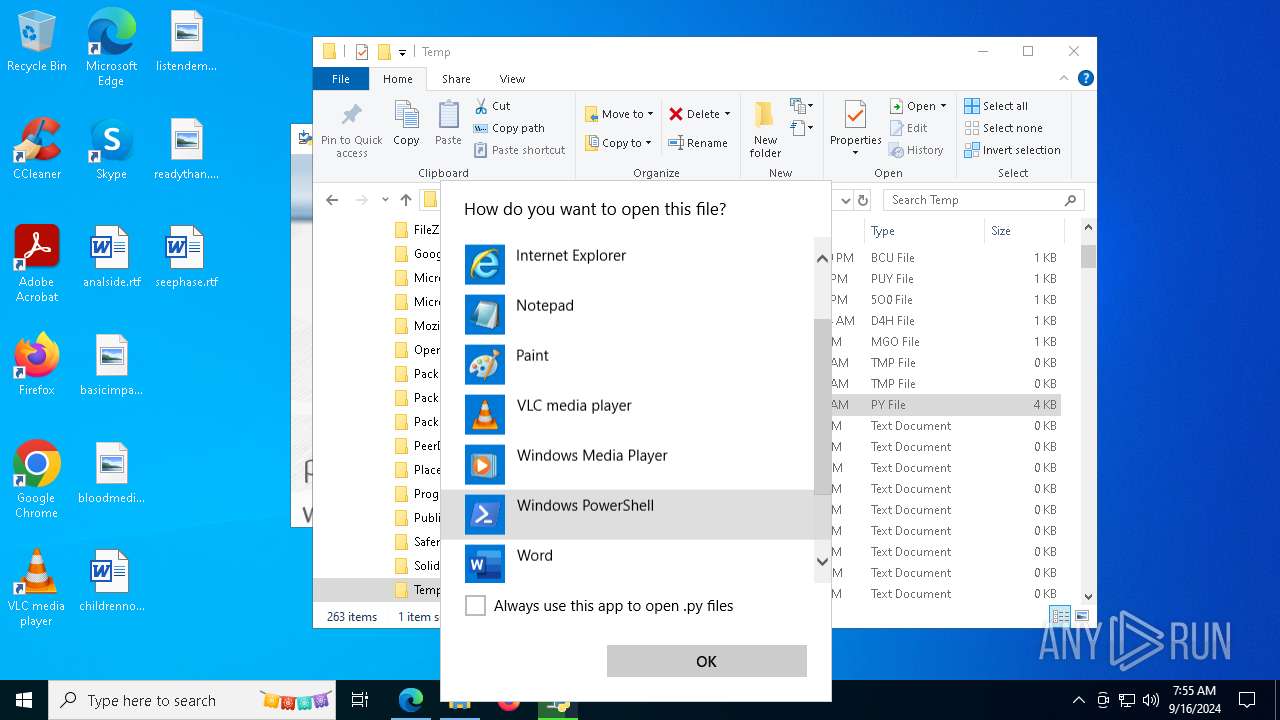
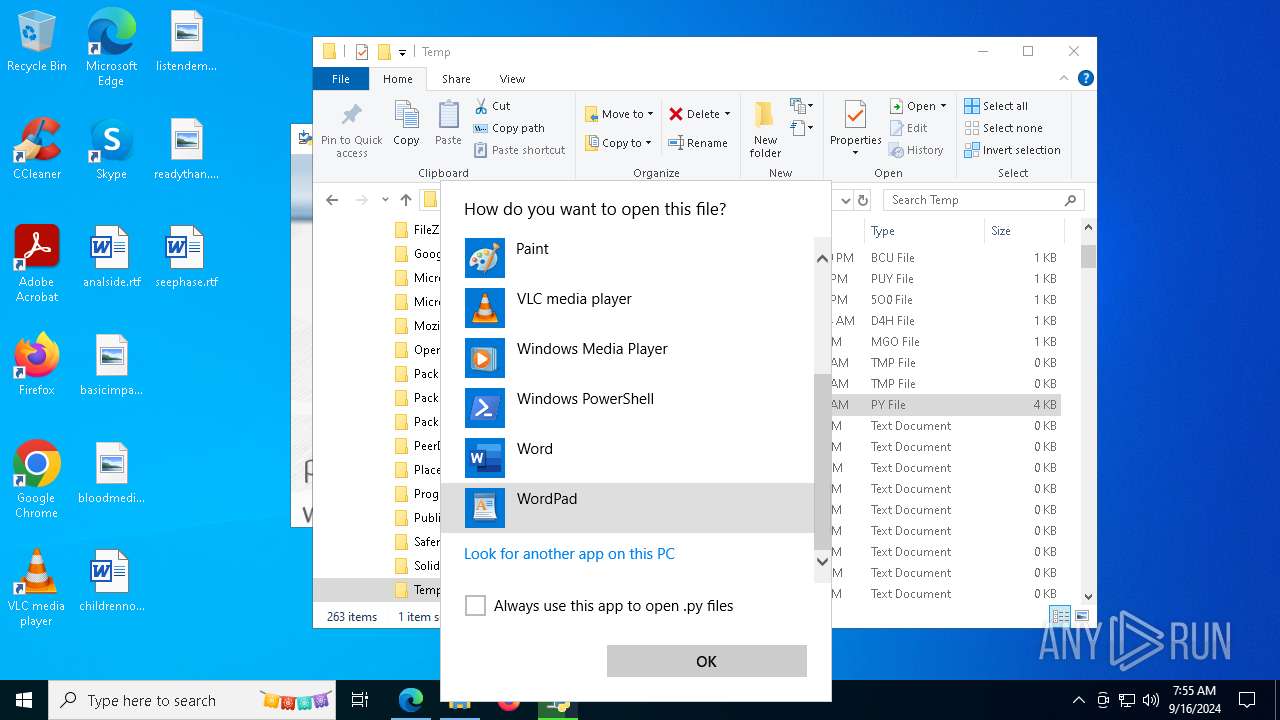
| 7164 | "C:\WINDOWS\System32\OpenWith.exe" C:\Users\admin\AppData\Local\Temp\a.py | C:\Windows\System32\OpenWith.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Pick an app Exit code: 2147943623 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7244 | C:\WINDOWS\system32\msiexec.exe /V | C:\Windows\System32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Version: 5.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7280 | C:\WINDOWS\system32\OpenWith.exe -Embedding | C:\Windows\System32\OpenWith.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Pick an app Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
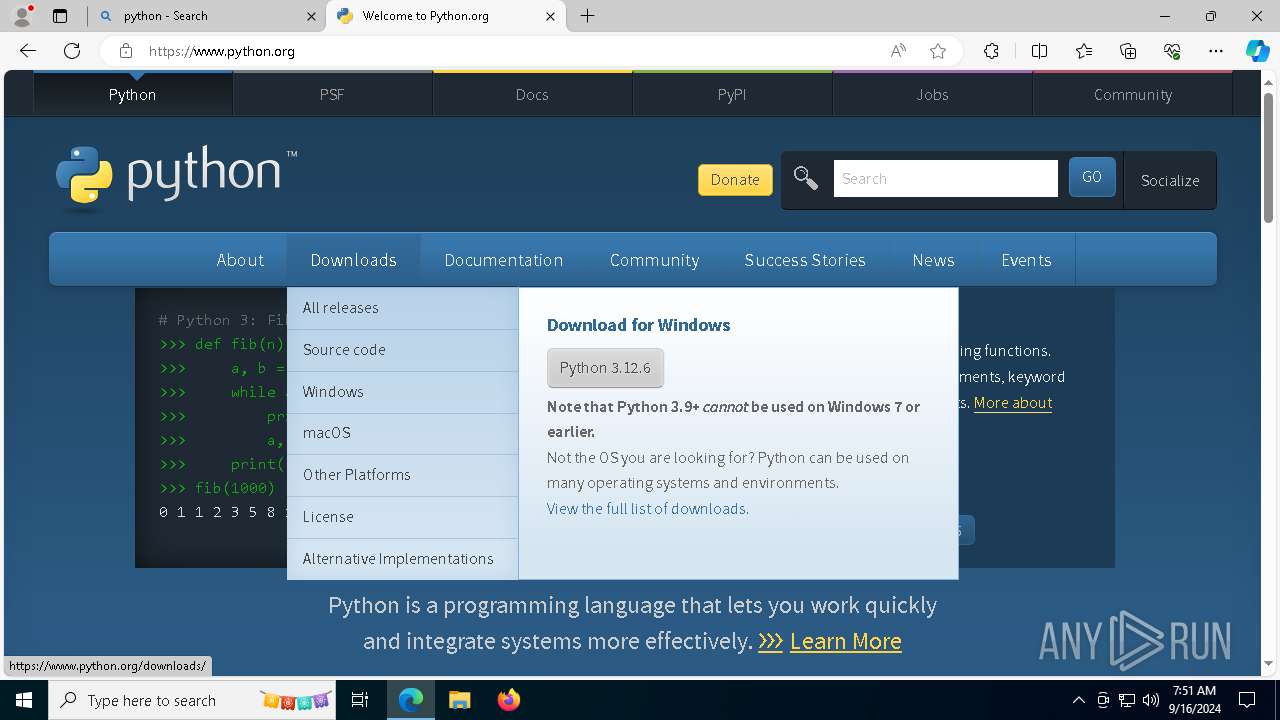
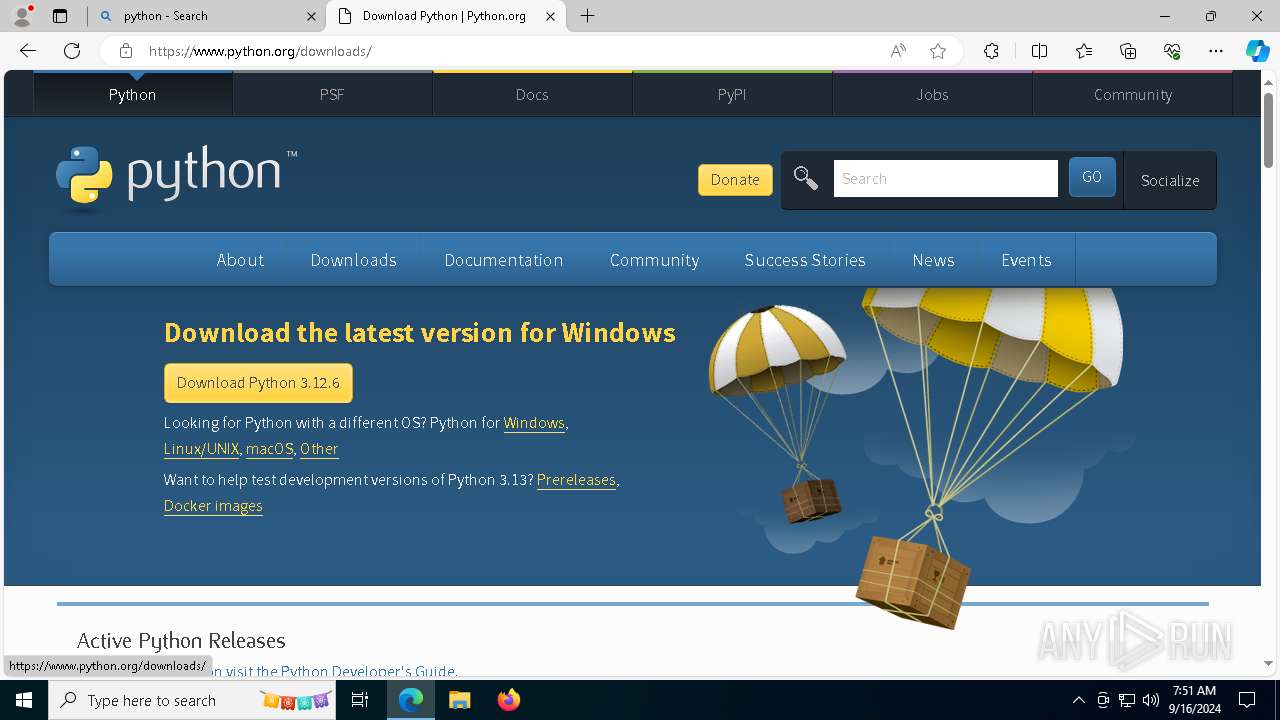
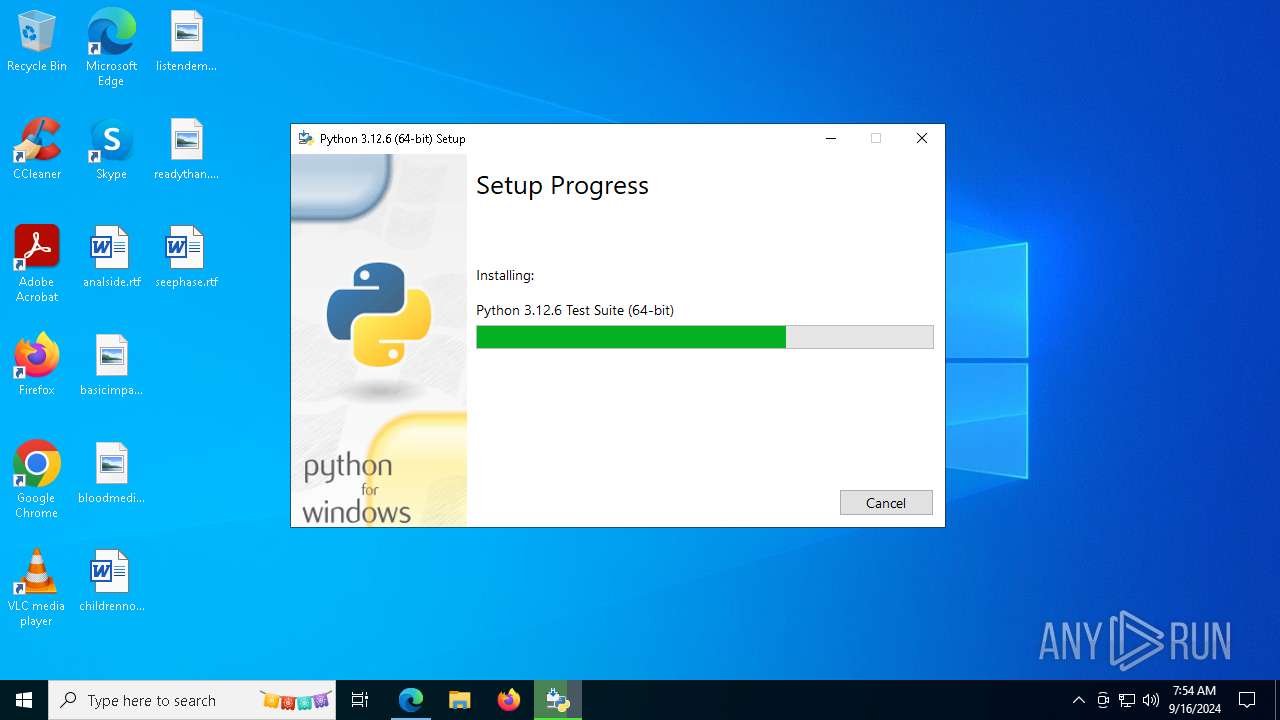
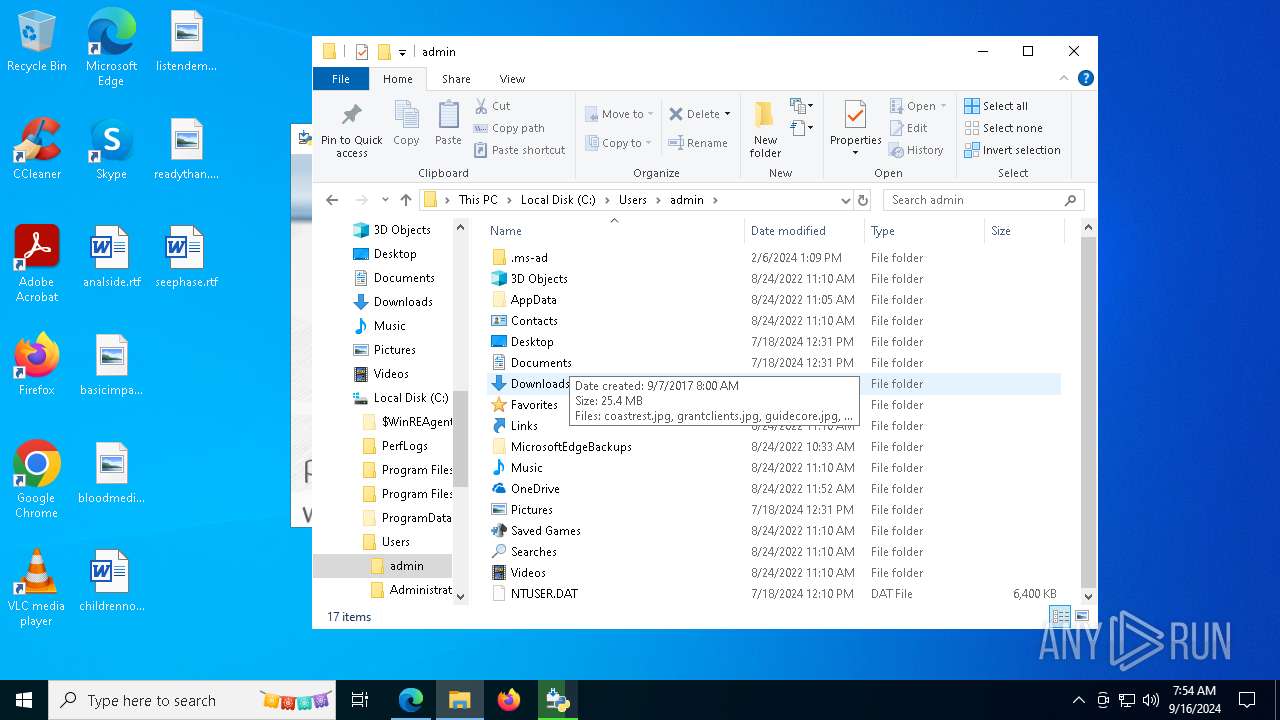
| 8060 | "C:\Users\admin\AppData\Local\Temp\{39FC1008-059B-4FCD-80B0-A73F8215B4C2}\.cr\python-3.12.6-amd64.exe" -burn.clean.room="C:\Users\admin\Downloads\python-3.12.6-amd64.exe" -burn.filehandle.attached=568 -burn.filehandle.self=564 | C:\Users\admin\AppData\Local\Temp\{39FC1008-059B-4FCD-80B0-A73F8215B4C2}\.cr\python-3.12.6-amd64.exe | python-3.12.6-amd64.exe | ||||||||||||
User: admin Company: Python Software Foundation Integrity Level: MEDIUM Description: Python 3.12.6 (64-bit) Version: 3.12.6150.0 Modules
| |||||||||||||||
Total events
35 195
Read events
31 071
Write events
4 057
Delete events
67
Modification events
| (PID) Process: | (8060) python-3.12.6-amd64.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{316e3b12-1191-47df-b9d4-dcf0bf2f6cc4} |
| Operation: | write | Name: | BundleCachePath |
Value: C:\Users\admin\AppData\Local\Package Cache\{316e3b12-1191-47df-b9d4-dcf0bf2f6cc4}\python-3.12.6-amd64.exe | |||
| (PID) Process: | (8060) python-3.12.6-amd64.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{316e3b12-1191-47df-b9d4-dcf0bf2f6cc4} |
| Operation: | write | Name: | BundleUpgradeCode |
Value: {114AEC44-152B-5746-952F-F20CE3CAB54A} | |||
| (PID) Process: | (8060) python-3.12.6-amd64.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{316e3b12-1191-47df-b9d4-dcf0bf2f6cc4} |
| Operation: | write | Name: | BundleAddonCode |
Value: | |||
| (PID) Process: | (8060) python-3.12.6-amd64.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{316e3b12-1191-47df-b9d4-dcf0bf2f6cc4} |
| Operation: | write | Name: | BundleDetectCode |
Value: | |||
| (PID) Process: | (8060) python-3.12.6-amd64.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{316e3b12-1191-47df-b9d4-dcf0bf2f6cc4} |
| Operation: | write | Name: | BundlePatchCode |
Value: | |||
| (PID) Process: | (8060) python-3.12.6-amd64.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{316e3b12-1191-47df-b9d4-dcf0bf2f6cc4} |
| Operation: | write | Name: | BundleVersion |
Value: 3.12.6150.0 | |||
| (PID) Process: | (8060) python-3.12.6-amd64.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{316e3b12-1191-47df-b9d4-dcf0bf2f6cc4} |
| Operation: | write | Name: | VersionMajor |
Value: 3 | |||
| (PID) Process: | (8060) python-3.12.6-amd64.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{316e3b12-1191-47df-b9d4-dcf0bf2f6cc4} |
| Operation: | write | Name: | VersionMinor |
Value: 12 | |||
| (PID) Process: | (8060) python-3.12.6-amd64.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{316e3b12-1191-47df-b9d4-dcf0bf2f6cc4} |
| Operation: | write | Name: | BundleProviderKey |
Value: CPython-3.12 | |||
| (PID) Process: | (8060) python-3.12.6-amd64.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{316e3b12-1191-47df-b9d4-dcf0bf2f6cc4} |
| Operation: | write | Name: | BundleTag |
Value: | |||
Executable files
72
Suspicious files
218
Text files
2 757
Unknown types
44
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 8060 | python-3.12.6-amd64.exe | C:\Users\admin\AppData\Local\Temp\{D6EF9554-3824-4BBD-BD32-D50D35393D45}\lib_JustForMe | — | |
MD5:— | SHA256:— | |||
| 8060 | python-3.12.6-amd64.exe | C:\Users\admin\AppData\Local\Temp\{D6EF9554-3824-4BBD-BD32-D50D35393D45}\test_JustForMe | — | |
MD5:— | SHA256:— | |||
| 8060 | python-3.12.6-amd64.exe | C:\Users\admin\AppData\Local\Temp\{D6EF9554-3824-4BBD-BD32-D50D35393D45}\doc_JustForMe | — | |
MD5:— | SHA256:— | |||
| 8060 | python-3.12.6-amd64.exe | C:\Users\admin\AppData\Local\Temp\{D6EF9554-3824-4BBD-BD32-D50D35393D45}\dev_JustForMe | executable | |
MD5:DC49359C176D731FEF03FC51ED13C959 | SHA256:04F38BDD910EABE114DDE5E321CDCBF831C6373DA9D27D791B96E09CD96F5417 | |||
| 8060 | python-3.12.6-amd64.exe | C:\Users\admin\AppData\Local\Package Cache\.unverified\lib_JustForMe | — | |
MD5:— | SHA256:— | |||
| 8060 | python-3.12.6-amd64.exe | C:\Users\admin\AppData\Local\Package Cache\{1DAEF824-881A-49C6-B91E-1D28877FF18D}v3.12.6150.0\lib.msi | — | |
MD5:— | SHA256:— | |||
| 8060 | python-3.12.6-amd64.exe | C:\Users\admin\AppData\Local\Package Cache\.unverified\test_JustForMe | — | |
MD5:— | SHA256:— | |||
| 8060 | python-3.12.6-amd64.exe | C:\Users\admin\AppData\Local\Package Cache\{3334B843-864F-4F04-A635-5D2FD5840AD5}v3.12.6150.0\test.msi | — | |
MD5:— | SHA256:— | |||
| 8060 | python-3.12.6-amd64.exe | C:\Users\admin\AppData\Local\Package Cache\.unverified\doc_JustForMe | — | |
MD5:— | SHA256:— | |||
| 8060 | python-3.12.6-amd64.exe | C:\Users\admin\AppData\Local\Package Cache\{46673E63-1CA8-43EA-B73B-AC20DDD77C5A}v3.12.6150.0\doc.msi | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
56
TCP/UDP connections
142
DNS requests
129
Threats
6
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5336 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
1764 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6732 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
2120 | MoUsoCoreWorker.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5336 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
3164 | msedge.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBT3xL4LQLXDRDM9P665TW442vrsUQQUReuir%2FSSy4IxLVGLp6chnfNtyA8CEA6bGI750C3n79tQ4ghAGFo%3D | unknown | — | — | whitelisted |
5336 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
3164 | msedge.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfIs%2BLjDtGwQ09XEB1Yeq%2BtX%2BBgQQU7NfjgtJxXWRM3y5nP%2Be6mK4cD08CEAitQLJg0pxMn17Nqb2Trtk%3D | unknown | — | — | whitelisted |
3164 | msedge.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSRXerF0eFeSWRripTgTkcJWMm7iQQUaDfg67Y7%2BF8Rhvv%2BYXsIiGX0TkICEAcfFBuLMA0l8xTrIwzQ0d0%3D | unknown | — | — | whitelisted |
3728 | svchost.exe | HEAD | 200 | 23.48.23.66:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/3f7756bd-b1cc-4d5e-96d8-fd938a5c5bb6?P1=1726549099&P2=404&P3=2&P4=htX2J4ECKCtfy0neF%2f0BAQE8657EM%2forIHH7fhsVjqVSxkz3orsosHaSoHycOe6LiVaTZ6fMhbAsBxVBouJAhw%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
568 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2120 | MoUsoCoreWorker.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3888 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
3260 | svchost.exe | 40.113.103.199:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1764 | svchost.exe | 20.190.159.2:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1764 | svchost.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
5336 | SearchApp.exe | 92.123.104.45:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
www.bing.com |
| whitelisted |
r.bing.com |
| whitelisted |
th.bing.com |
| whitelisted |
www2.bing.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6472 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Hosted Libraries (ajax .googleapis .com) |
6472 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Hosted Libraries (ajax .googleapis .com) |
6472 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Hosted Libraries (ajax .googleapis .com) |
6472 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Hosted Libraries (ajax .googleapis .com) |
6472 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Hosted Libraries (ajax .googleapis .com) |
6472 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Hosted Libraries (ajax .googleapis .com) |