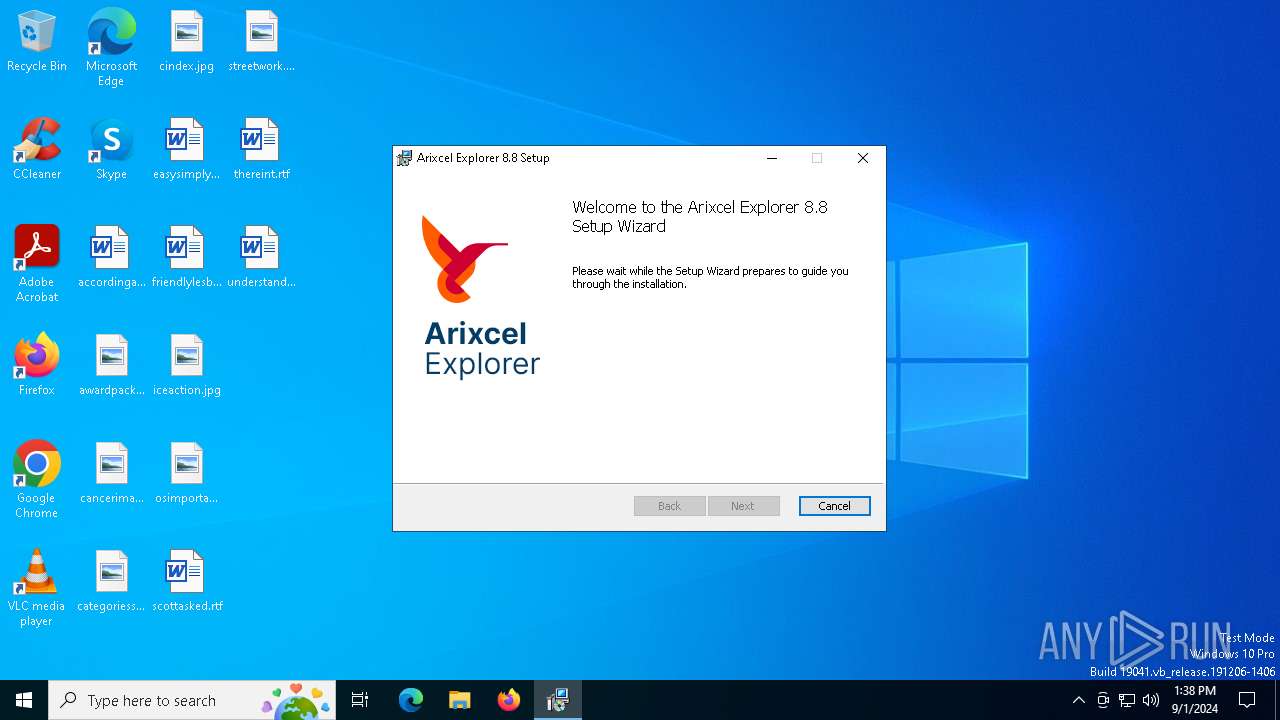
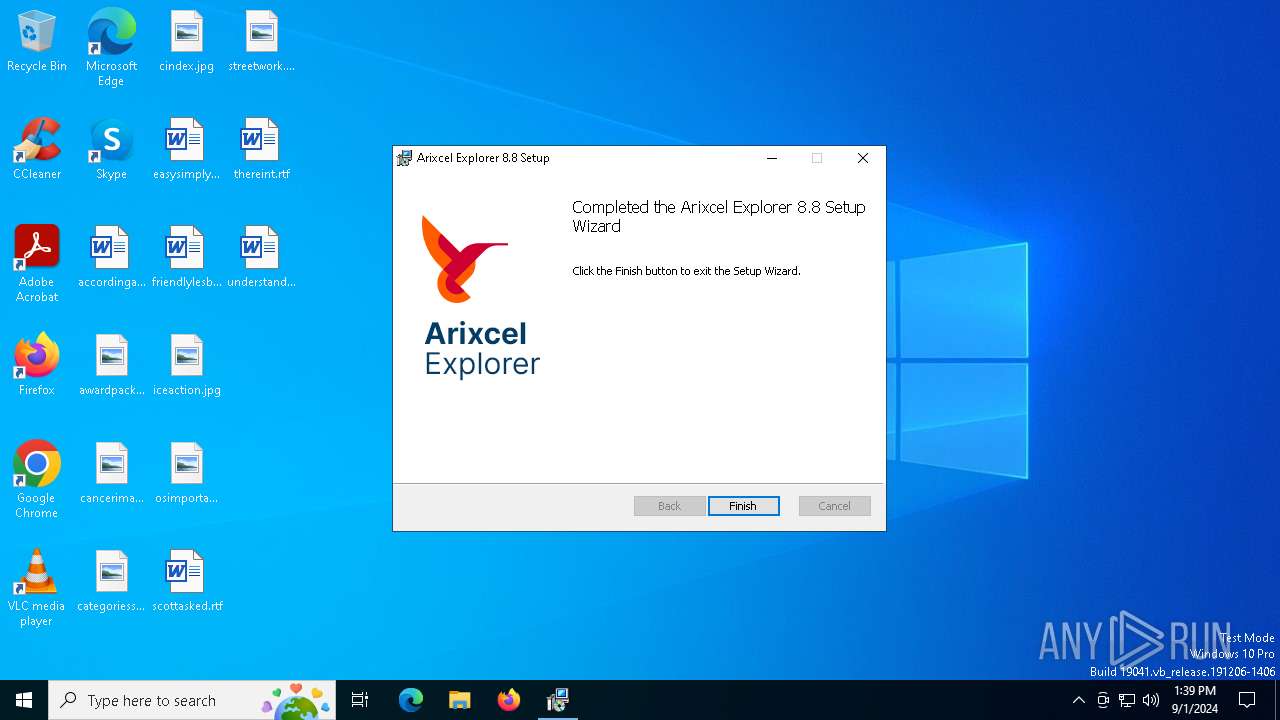
| File name: | Arixcel_Explorer_v8.8.9004.msi |
| Full analysis: | https://app.any.run/tasks/8cdcb7b7-b96c-4e2e-8483-256c514ac34e |
| Verdict: | Malicious activity |
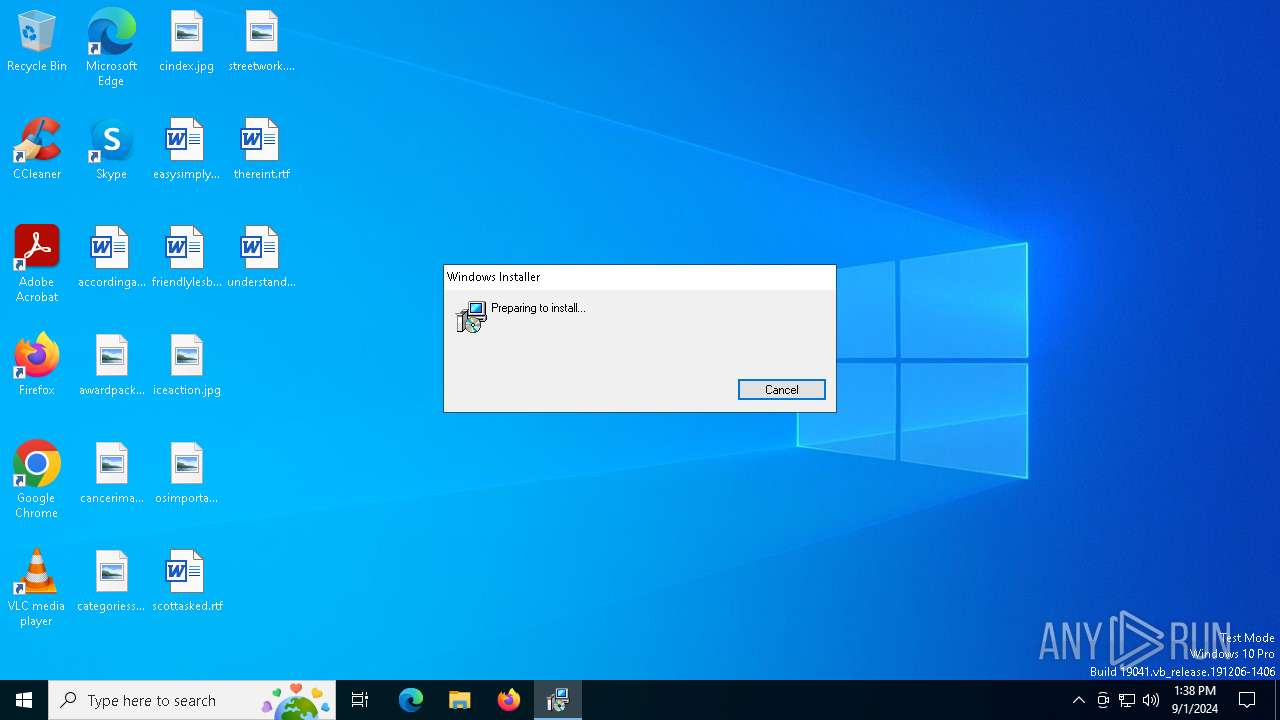
| Analysis date: | September 01, 2024, 13:38:36 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-msi |
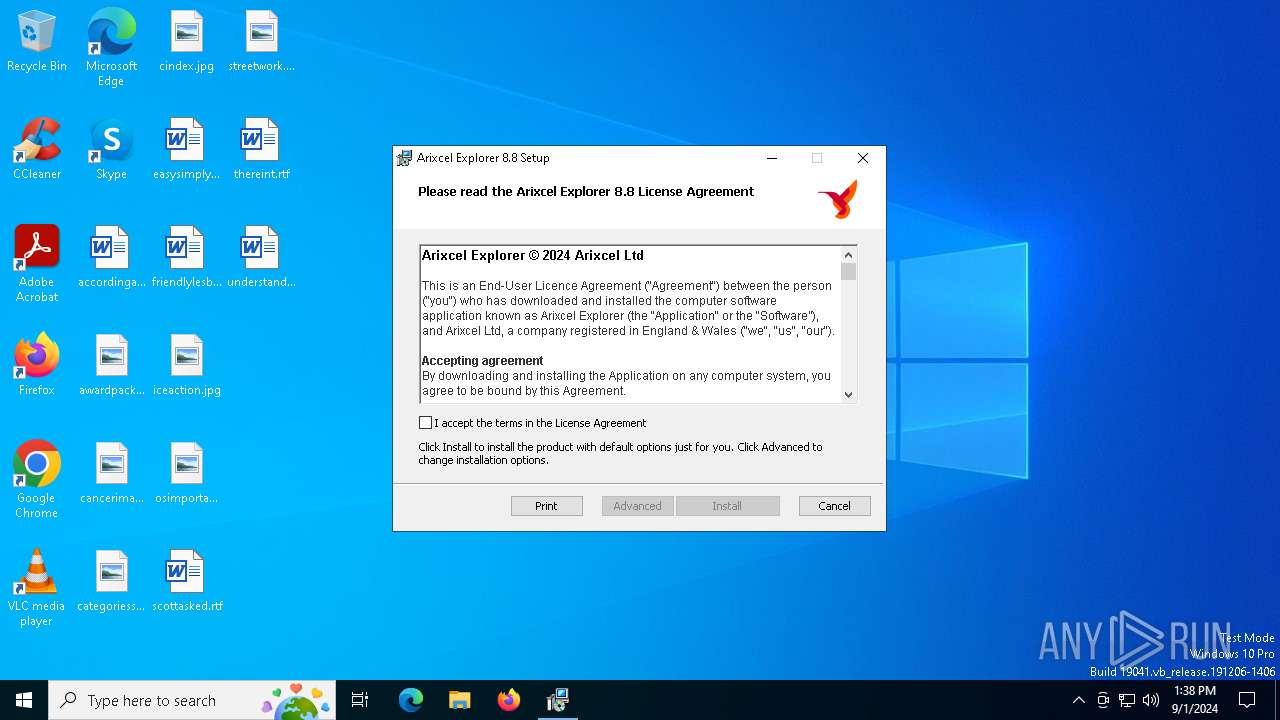
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.2, MSI Installer, Code page: 1252, Title: Installation Database, Subject: Arixcel Explorer Installer, Author: Arixcel Ltd, Keywords: Arixcel Installer, Comments: Arixcel Explorer is a spreadsheet analysis add-in for Microsoft Excel., Template: x64;1033, Revision Number: {58E50600-62F9-417E-9646-2D1E39DE0C4E}, Create Time/Date: Mon Aug 26 20:44:50 2024, Last Saved Time/Date: Mon Aug 26 20:44:50 2024, Number of Pages: 200, Number of Words: 2, Name of Creating Application: Windows Installer XML Toolset (3.14.0.5722), Security: 2 |
| MD5: | 013115D323C7D99EB686A75B46ECC55D |
| SHA1: | F6544344E1063DD6F50F32BD25A3C47822B42821 |
| SHA256: | D9D36B9AE78DF5EE308594219F87D30F68CFF8841D409C68E87D17B6B48A492C |
| SSDEEP: | 98304:sKLHZssiMr0ypgWqk4g8BdEclY65XewtV7xRFQfGl85xH31rysFK6oLPdpkB0a+v:vk |
MALICIOUS
No malicious indicators.SUSPICIOUS
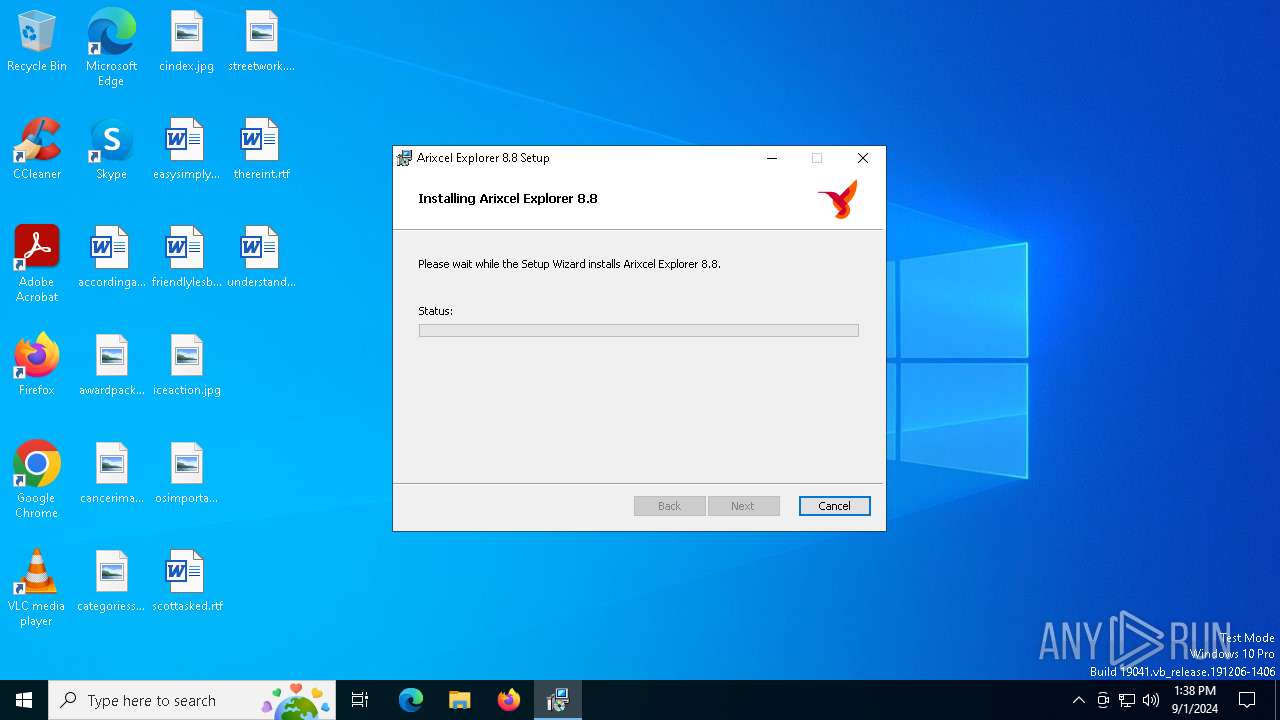
Process drops legitimate windows executable
- msiexec.exe (PID: 6296)
- msiexec.exe (PID: 5000)
Executable content was dropped or overwritten
- rundll32.exe (PID: 5544)
- rundll32.exe (PID: 3812)
- rundll32.exe (PID: 1224)
- rundll32.exe (PID: 3812)
- rundll32.exe (PID: 5544)
Executes as Windows Service
- VSSVC.exe (PID: 2128)
Drops the executable file immediately after the start
- msiexec.exe (PID: 5000)
Checks Windows Trust Settings
- msiexec.exe (PID: 5000)
The process creates files with name similar to system file names
- msiexec.exe (PID: 5000)
Reads the Windows owner or organization settings
- msiexec.exe (PID: 5000)
INFO
Reads the software policy settings
- msiexec.exe (PID: 6296)
- msiexec.exe (PID: 5000)
Reads security settings of Internet Explorer
- msiexec.exe (PID: 6296)
Creates files or folders in the user directory
- msiexec.exe (PID: 6296)
- msiexec.exe (PID: 5000)
Checks proxy server information
- msiexec.exe (PID: 6296)
Reads the computer name
- msiexec.exe (PID: 4680)
- msiexec.exe (PID: 5000)
- msiexec.exe (PID: 1156)
Checks supported languages
- msiexec.exe (PID: 4680)
- msiexec.exe (PID: 5000)
- msiexec.exe (PID: 1156)
Executable content was dropped or overwritten
- msiexec.exe (PID: 6296)
- msiexec.exe (PID: 5000)
Create files in a temporary directory
- rundll32.exe (PID: 5544)
- rundll32.exe (PID: 3812)
- rundll32.exe (PID: 1224)
- rundll32.exe (PID: 5544)
- rundll32.exe (PID: 3812)
Reads Microsoft Office registry keys
- rundll32.exe (PID: 3812)
- msiexec.exe (PID: 5000)
Reads the machine GUID from the registry
- msiexec.exe (PID: 5000)
Creates a software uninstall entry
- msiexec.exe (PID: 5000)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msi | | | Microsoft Windows Installer (93) |
|---|---|---|
| .msi | | | Microsoft Installer (100) |
EXIF
FlashPix
| CodePage: | Windows Latin 1 (Western European) |
|---|---|
| Title: | Installation Database |
| Subject: | Arixcel Explorer Installer |
| Author: | Arixcel Ltd |
| Keywords: | Arixcel Installer |
| Comments: | Arixcel Explorer is a spreadsheet analysis add-in for Microsoft Excel. |
| Template: | x64;1033 |
| RevisionNumber: | {58E50600-62F9-417E-9646-2D1E39DE0C4E} |
| CreateDate: | 2024:08:26 20:44:50 |
| ModifyDate: | 2024:08:26 20:44:50 |
| Pages: | 200 |
| Words: | 2 |
| Software: | Windows Installer XML Toolset (3.14.0.5722) |
| Security: | Read-only recommended |
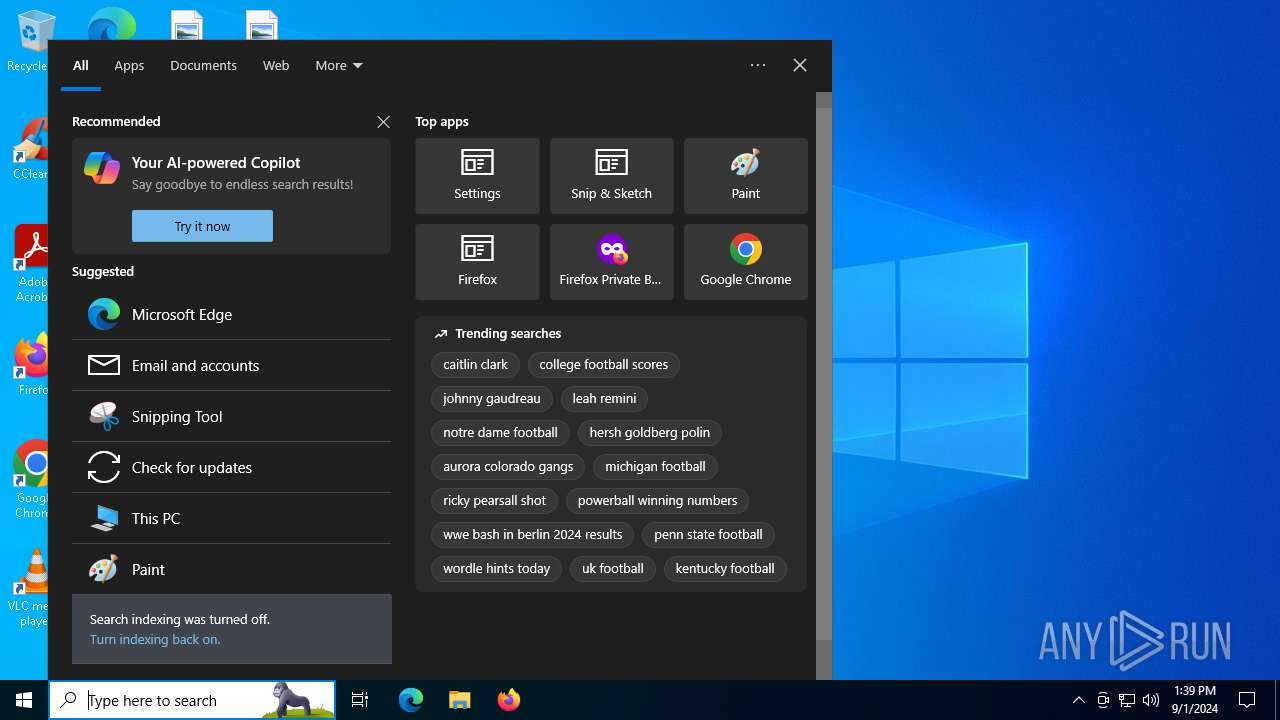
Total processes
147
Monitored processes
15
Malicious processes
1
Suspicious processes
0
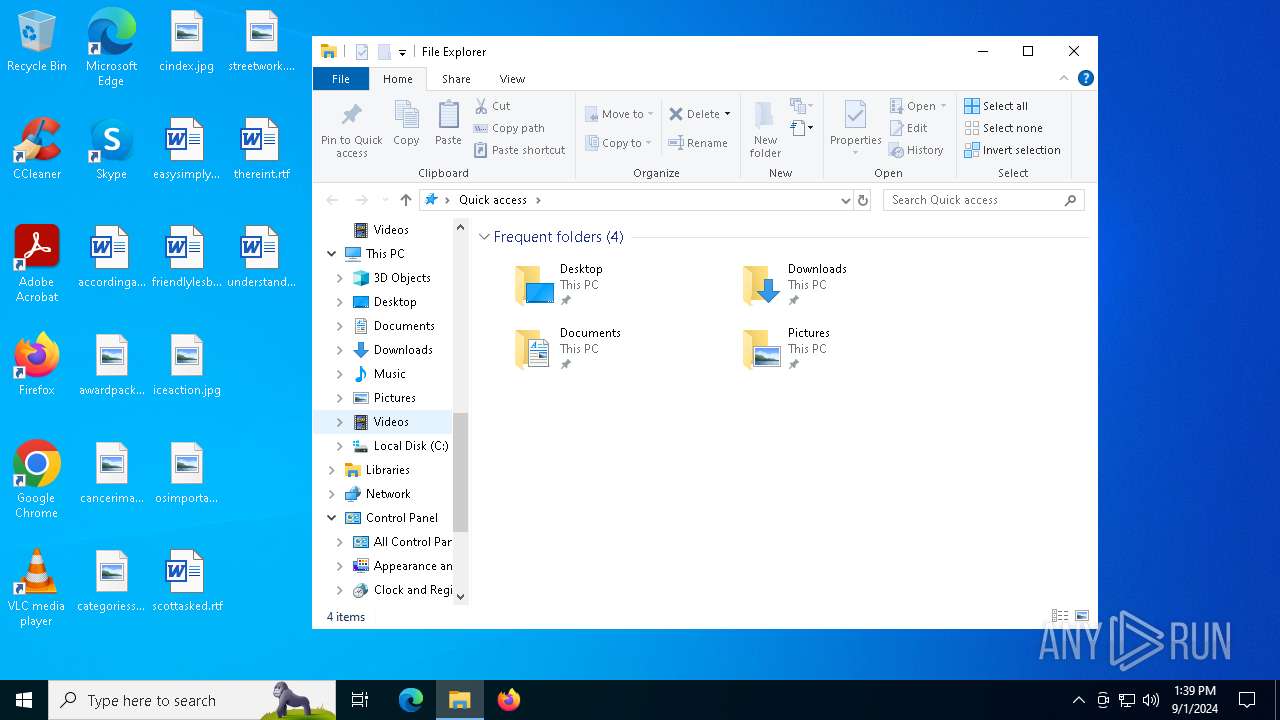
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1116 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | — | SppExtComObj.Exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1156 | C:\Windows\syswow64\MsiExec.exe -Embedding D0E835D98221D46914587E9BB669B674 | C:\Windows\SysWOW64\msiexec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1224 | rundll32.exe "C:\Users\admin\AppData\Local\Temp\MSIA9D8.tmp",zzzzInvokeManagedCustomActionOutOfProc SfxCA_1223125 28 ArixcelSetup!Arixcel.Explorer.Setup.CustomActions.SetDefaultInstallFolders | C:\Windows\SysWOW64\rundll32.exe | msiexec.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1840 | C:\WINDOWS\system32\srtasks.exe ExecuteScopeRestorePoint /WaitForRestorePoint:11 | C:\Windows\System32\SrTasks.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Windows System Protection background tasks. Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2128 | C:\WINDOWS\system32\vssvc.exe | C:\Windows\System32\VSSVC.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3812 | rundll32.exe "C:\Users\admin\AppData\Local\Temp\MSIA92B.tmp",zzzzInvokeManagedCustomActionOutOfProc SfxCA_1222953 22 ArixcelSetup!Arixcel.Explorer.Setup.CustomActions.ResetAllUsers | C:\Windows\SysWOW64\rundll32.exe | msiexec.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3812 | rundll32.exe "C:\WINDOWS\Installer\MSIFF.tmp",zzzzInvokeManagedCustomActionOutOfProc SfxCA_1245453 8 ArixcelSetup!Arixcel.Explorer.Setup.CustomActions.RegisterVbaAddin | C:\Windows\SysWOW64\rundll32.exe | msiexec.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4080 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | SrTasks.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4680 | C:\Windows\syswow64\MsiExec.exe -Embedding EC117F56D6F8EF68209AFD29229DE726 C | C:\Windows\SysWOW64\msiexec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5000 | C:\WINDOWS\system32\msiexec.exe /V | C:\Windows\System32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Version: 5.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
13 812
Read events
13 504
Write events
289
Delete events
19
Modification events
| (PID) Process: | (5000) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SystemRestore |
| Operation: | write | Name: | SrCreateRp (Enter) |
Value: 4800000000000000DF57464874FCDA0188130000FC130000D50700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (5000) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Enter) |
Value: 4800000000000000DF57464874FCDA0188130000FC130000D20700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (5000) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Leave) |
Value: 48000000000000003E868B4874FCDA0188130000FC130000D20700000100000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (5000) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppEnumGroups (Enter) |
Value: 4800000000000000BDE98D4874FCDA0188130000FC130000D10700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (5000) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppEnumGroups (Leave) |
Value: 4800000000000000924E904874FCDA0188130000FC130000D10700000100000000000000010000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (5000) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppCreate (Enter) |
Value: 4800000000000000C8B1924874FCDA0188130000FC130000D00700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (5000) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SPP |
| Operation: | write | Name: | LastIndex |
Value: 11 | |||
| (PID) Process: | (5000) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGatherWriterMetadata (Enter) |
Value: 48000000000000002C64134974FCDA0188130000FC130000D30700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (5000) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\VssapiPublisher |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4800000000000000B0C7154974FCDA0188130000280C0000E8030000010000000000000000000000BA4D045B304FE24D95D8F38977229BC000000000000000000000000000000000 | |||
| (PID) Process: | (2128) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\Registry Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4800000000000000DBBA214974FCDA01500800003C0F0000E80300000100000001000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
33
Suspicious files
24
Text files
10
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6296 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\MSIA4D4.tmp | executable | |
MD5:2ED0557A2E2EB2690FBCCCBD2471D5DF | SHA256:27976425F7A1F98F79D96E7838403E01EFCA8369CEB50FC5B217ED2B78E4F3B5 | |||
| 6296 | msiexec.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\8EC9B1D0ABBD7F98B401D425828828CE_8B6426B6690101B521CAF68DCFDCB929 | binary | |
MD5:DFC4C036BC2A097429491430F8CA84AA | SHA256:4CDCF1AFD4DD9A3F145EF8C00818F1C5340D512B13FCBA7D9193F9E3080CFF41 | |||
| 5000 | msiexec.exe | C:\System Volume Information\SPP\metadata-2 | — | |
MD5:— | SHA256:— | |||
| 5544 | rundll32.exe | C:\Users\admin\AppData\Local\Temp\MSIA4D4.tmp-\Microsoft.Deployment.WindowsInstaller.dll | executable | |
MD5:C591EF33FEAD6C99DDB6A3138E8BC58F | SHA256:F0BAB56DA3E3D1793668AD6A5C3A1117A07ACB0997C095BA41C7FB0D9C793E7E | |||
| 6296 | msiexec.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\698460A0B6E60F2F602361424D832905_8BB23D43DE574E82F2BEE0DF0EC47EEB | der | |
MD5:2CE3D39222D618BF5596652E33E58BAF | SHA256:C5A5D9F55EEE596175BF6BAFF15C9D2D6A45248E18ECB2EF465A44BD7E753289 | |||
| 6296 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\MSIA9D8.tmp | executable | |
MD5:2ED0557A2E2EB2690FBCCCBD2471D5DF | SHA256:27976425F7A1F98F79D96E7838403E01EFCA8369CEB50FC5B217ED2B78E4F3B5 | |||
| 3812 | rundll32.exe | C:\Users\admin\AppData\Local\Temp\MSIA92B.tmp-\CustomAction.config | xml | |
MD5:82FACDCE498CD0F186C355760C5CF0EC | SHA256:B46DB7ED88826F9D30C4DBDA37BA5C021C94A16A144FF889E1D5BBD77B0B0D71 | |||
| 1224 | rundll32.exe | C:\Users\admin\AppData\Local\Temp\MSIA9D8.tmp-\CustomAction.config | xml | |
MD5:82FACDCE498CD0F186C355760C5CF0EC | SHA256:B46DB7ED88826F9D30C4DBDA37BA5C021C94A16A144FF889E1D5BBD77B0B0D71 | |||
| 1224 | rundll32.exe | C:\Users\admin\AppData\Local\Temp\MSIA9D8.tmp-\Microsoft.Deployment.WindowsInstaller.dll | executable | |
MD5:C591EF33FEAD6C99DDB6A3138E8BC58F | SHA256:F0BAB56DA3E3D1793668AD6A5C3A1117A07ACB0997C095BA41C7FB0D9C793E7E | |||
| 5000 | msiexec.exe | C:\System Volume Information\SPP\snapshot-2 | binary | |
MD5:BC2C53DD4117BB905588CD10D6B8F6C6 | SHA256:1B5B2099CA361A8BC3760979D45FCF687D2C24A6376CA690472B9606081A6DAB | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
10
TCP/UDP connections
56
DNS requests
25
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6296 | msiexec.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBT3xL4LQLXDRDM9P665TW442vrsUQQUReuir%2FSSy4IxLVGLp6chnfNtyA8CEA6bGI750C3n79tQ4ghAGFo%3D | unknown | — | — | whitelisted |
6296 | msiexec.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfIs%2BLjDtGwQ09XEB1Yeq%2BtX%2BBgQQU7NfjgtJxXWRM3y5nP%2Be6mK4cD08CEAitQLJg0pxMn17Nqb2Trtk%3D | unknown | — | — | whitelisted |
6296 | msiexec.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSRXerF0eFeSWRripTgTkcJWMm7iQQUaDfg67Y7%2BF8Rhvv%2BYXsIiGX0TkICEAEzhWDJk%2Fozlbna9gYAnv0%3D | unknown | — | — | whitelisted |
1752 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6592 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
5336 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
6592 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
5336 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEA77flR%2B3w%2FxBpruV2lte6A%3D | unknown | — | — | whitelisted |
5336 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEApDqVCbATUviZV57HIIulA%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 163.181.92.233:80 | http://ocsp.digicert.cn/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEA%2FgMquETQMxBsUMjhPIsGg%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4760 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6424 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2120 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6296 | msiexec.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
4760 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3260 | svchost.exe | 40.113.110.67:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1752 | svchost.exe | 20.190.160.20:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1752 | svchost.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
4820 | svchost.exe | 23.218.210.69:443 | go.microsoft.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |