| File name: | rechnungen.doc |
| Full analysis: | https://app.any.run/tasks/167c7b07-91f3-4e65-b72c-29baa1294213 |
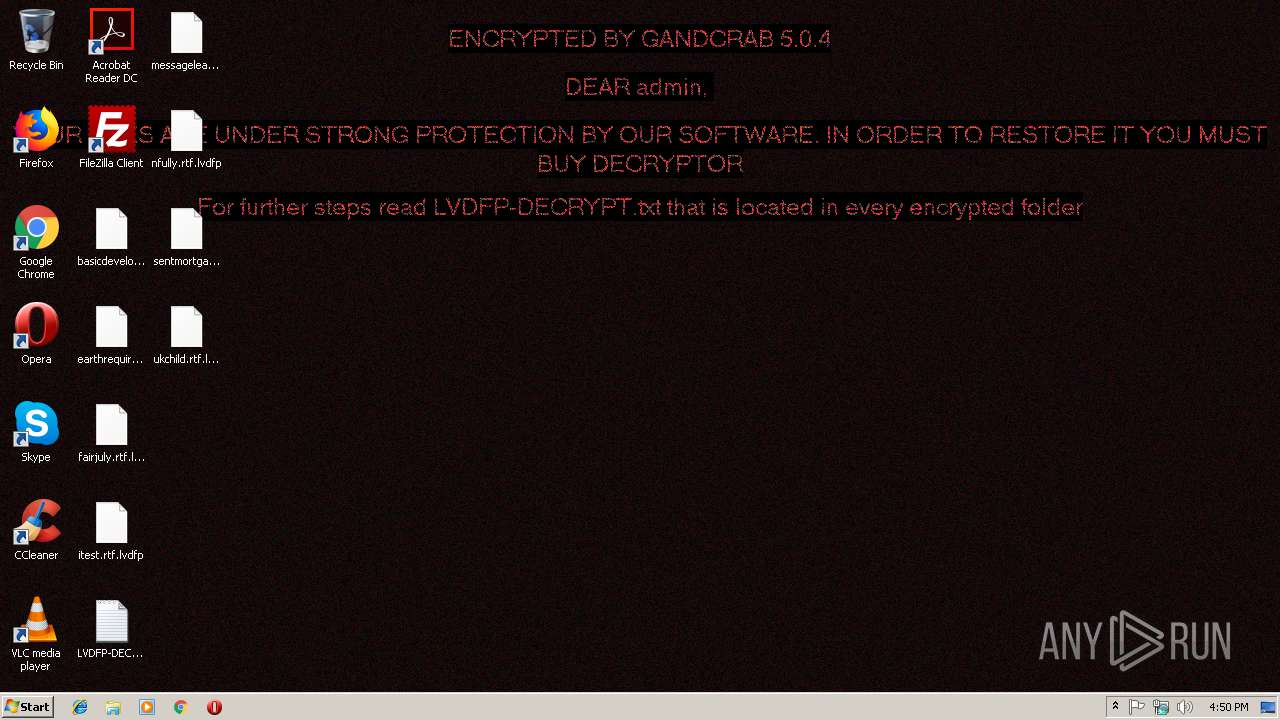
| Verdict: | Malicious activity |
| Threats: | GandCrab is probably one of the most famous Ransomware. A Ransomware is a malware that asks the victim to pay money in order to restore access to encrypted files. If the user does not cooperate the files are forever lost. |
| Analysis date: | January 10, 2019, 16:49:28 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.1, Code page: 1252, Author: Ghost, Template: Normal.dotm, Last Saved By: Ghost, Revision Number: 1, Name of Creating Application: Microsoft Office Word, Create Time/Date: Tue Jan 8 17:22:00 2019, Last Saved Time/Date: Tue Jan 8 17:22:00 2019, Number of Pages: 1, Number of Words: 0, Number of Characters: 0, Security: 0 |
| MD5: | 444749249E358F3C67D0ABC468B8349C |
| SHA1: | CA3C9CA7AB17B1F7E6D5796449DE7C90601B0A04 |
| SHA256: | D9C89E4F9100D4053CFC35F7C7FB9576FB4229E8049CE34CBEC281F14A126621 |
| SSDEEP: | 768:lY+1o93SK815S/FCOhpzJ9BRU/waOxjb3w+byp:lY+a93pO5KUOb/RUIaOpfW |
MALICIOUS
Executable content was dropped or overwritten
- WINWORD.EXE (PID: 3008)
Application was dropped or rewritten from another process
- yeZjqHFMWjXi.exe (PID: 2892)
Requests a remote executable file from MS Office
- WINWORD.EXE (PID: 3008)
Unusual execution from Microsoft Office
- WINWORD.EXE (PID: 3008)
GandCrab keys found
- yeZjqHFMWjXi.exe (PID: 2892)
Writes file to Word startup folder
- yeZjqHFMWjXi.exe (PID: 2892)
Actions looks like stealing of personal data
- yeZjqHFMWjXi.exe (PID: 2892)
Dropped file may contain instructions of ransomware
- yeZjqHFMWjXi.exe (PID: 2892)
Deletes shadow copies
- yeZjqHFMWjXi.exe (PID: 2892)
Renames files like Ransomware
- yeZjqHFMWjXi.exe (PID: 2892)
Connects to CnC server
- yeZjqHFMWjXi.exe (PID: 2892)
SUSPICIOUS
Unusual connect from Microsoft Office
- WINWORD.EXE (PID: 3008)
Reads the cookies of Mozilla Firefox
- yeZjqHFMWjXi.exe (PID: 2892)
Creates files like Ransomware instruction
- yeZjqHFMWjXi.exe (PID: 2892)
Creates files in the user directory
- yeZjqHFMWjXi.exe (PID: 2892)
INFO
Creates files in the user directory
- WINWORD.EXE (PID: 3008)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 3008)
Dropped object may contain TOR URL's
- yeZjqHFMWjXi.exe (PID: 2892)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| Title: | - |
|---|---|
| Subject: | - |
| Author: | Ghost |
| Keywords: | - |
| Comments: | - |
| Template: | Normal.dotm |
| LastModifiedBy: | Ghost |
| RevisionNumber: | 1 |
| Software: | Microsoft Office Word |
| TotalEditTime: | - |
| CreateDate: | 2019:01:08 17:22:00 |
| ModifyDate: | 2019:01:08 17:22:00 |
| Pages: | 1 |
| Words: | - |
| Characters: | - |
| Security: | None |
| CodePage: | Windows Latin 1 (Western European) |
| Company: | - |
| Lines: | - |
| Paragraphs: | - |
| CharCountWithSpaces: | - |
| AppVersion: | 16 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| CompObjUserTypeLen: | 32 |
| CompObjUserType: | Microsoft Word 97-2003 Document |
Total processes
37
Monitored processes
3
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2616 | "C:\Windows\system32\wbem\wmic.exe" shadowcopy delete | C:\Windows\system32\wbem\wmic.exe | — | yeZjqHFMWjXi.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: WMI Commandline Utility Exit code: 2147749908 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2892 | C:\Users\Public\yeZjqHFMWjXi.exe | C:\Users\Public\yeZjqHFMWjXi.exe | WINWORD.EXE | ||||||||||||
User: admin Company: Abbott Laboratories Integrity Level: MEDIUM Description: Succession Directoryshell Exit code: 0 Modules
| |||||||||||||||
| 3008 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\rechnungen.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
Total events
1 326
Read events
897
Write events
424
Delete events
5
Modification events
| (PID) Process: | (3008) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | &., |
Value: 262E2C00C00B0000010000000000000000000000 | |||
| (PID) Process: | (3008) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (3008) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (3008) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1311375383 | |||
| (PID) Process: | (3008) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1311375504 | |||
| (PID) Process: | (3008) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1311375505 | |||
| (PID) Process: | (3008) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word |
| Operation: | write | Name: | MTTT |
Value: C00B000020852C7D04A9D40100000000 | |||
| (PID) Process: | (3008) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | ?/, |
Value: 3F2F2C00C00B000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (3008) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | delete value | Name: | ?/, |
Value: 3F2F2C00C00B000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (3008) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
2
Suspicious files
277
Text files
227
Unknown types
12
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3008 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVREA06.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3008 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DFB1A3790111E2CF63.TMP | — | |
MD5:— | SHA256:— | |||
| 3008 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DF298F016DBE48DD26.TMP | — | |
MD5:— | SHA256:— | |||
| 3008 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DF2293A6EC8EAC38F8.TMP | — | |
MD5:— | SHA256:— | |||
| 2892 | yeZjqHFMWjXi.exe | C:\Users\admin\.oracle_jre_usage\90737d32e3abaa4.timestamp | — | |
MD5:— | SHA256:— | |||
| 3008 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$chnungen.doc | pgc | |
MD5:— | SHA256:— | |||
| 2892 | yeZjqHFMWjXi.exe | C:\Users\admin\AppData\Roaming\Adobe\Acrobat\DC\JSCache\GlobData | — | |
MD5:— | SHA256:— | |||
| 3008 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRF{34548643-48F5-4E33-9EB0-FCD0B1D44F93}.tmp | binary | |
MD5:— | SHA256:— | |||
| 2892 | yeZjqHFMWjXi.exe | C:\Users\admin\AppData\Roaming\Adobe\Acrobat\DC\JSCache\GlobSettings | — | |
MD5:— | SHA256:— | |||
| 3008 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\VBE\MSForms.exd | tlb | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
68
TCP/UDP connections
126
DNS requests
58
Threats
30
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2892 | yeZjqHFMWjXi.exe | GET | — | 78.46.77.98:80 | http://www.2mmotorsport.biz/ | DE | — | — | suspicious |
2892 | yeZjqHFMWjXi.exe | GET | — | 217.26.53.161:80 | http://www.haargenau.biz/ | CH | — | — | malicious |
2892 | yeZjqHFMWjXi.exe | GET | 302 | 192.185.159.253:80 | http://www.pizcam.com/ | US | — | — | malicious |
2892 | yeZjqHFMWjXi.exe | GET | — | 212.59.186.61:80 | http://www.hotelweisshorn.com/ | CH | — | — | malicious |
2892 | yeZjqHFMWjXi.exe | GET | 301 | 83.138.82.107:80 | http://www.swisswellness.com/ | DE | — | — | whitelisted |
2892 | yeZjqHFMWjXi.exe | GET | 301 | 83.166.138.7:80 | http://www.whitepod.com/ | CH | — | — | whitelisted |
2892 | yeZjqHFMWjXi.exe | GET | — | 217.26.53.37:80 | http://www.hrk-ramoz.com/ | CH | — | — | malicious |
2892 | yeZjqHFMWjXi.exe | GET | 301 | 104.24.22.22:80 | http://www.belvedere-locarno.com/ | US | — | — | shared |
2892 | yeZjqHFMWjXi.exe | GET | 301 | 212.59.186.61:80 | http://www.morcote-residenza.com/ | CH | — | — | malicious |
2892 | yeZjqHFMWjXi.exe | GET | 301 | 80.244.187.247:80 | http://www.hotelfarinet.com/ | GB | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2892 | yeZjqHFMWjXi.exe | 104.24.22.22:443 | www.belvedere-locarno.com | Cloudflare Inc | US | shared |
2892 | yeZjqHFMWjXi.exe | 78.46.77.98:80 | www.2mmotorsport.biz | Hetzner Online GmbH | DE | suspicious |
3008 | WINWORD.EXE | 94.73.146.109:80 | karbonkoko.com | Cizgi Telekomunikasyon Anonim Sirketi | TR | suspicious |
2892 | yeZjqHFMWjXi.exe | 78.46.77.98:443 | www.2mmotorsport.biz | Hetzner Online GmbH | DE | suspicious |
2892 | yeZjqHFMWjXi.exe | 217.26.53.161:80 | www.haargenau.biz | Hostpoint AG | CH | malicious |
2892 | yeZjqHFMWjXi.exe | 74.220.215.73:80 | www.bizziniinfissi.com | Unified Layer | US | malicious |
2892 | yeZjqHFMWjXi.exe | 136.243.13.215:80 | www.holzbock.biz | Hetzner Online GmbH | DE | suspicious |
2892 | yeZjqHFMWjXi.exe | 138.201.162.99:80 | www.fliptray.biz | Hetzner Online GmbH | DE | malicious |
2892 | yeZjqHFMWjXi.exe | 138.201.162.99:443 | www.fliptray.biz | Hetzner Online GmbH | DE | malicious |
2892 | yeZjqHFMWjXi.exe | 192.185.159.253:80 | www.pizcam.com | CyrusOne LLC | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
karbonkoko.com |
| suspicious |
www.2mmotorsport.biz |
| unknown |
www.haargenau.biz |
| unknown |
www.bizziniinfissi.com |
| malicious |
www.holzbock.biz |
| unknown |
www.fliptray.biz |
| malicious |
www.pizcam.com |
| unknown |
www.swisswellness.com |
| whitelisted |
www.hotelweisshorn.com |
| unknown |
www.whitepod.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3008 | WINWORD.EXE | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
2892 | yeZjqHFMWjXi.exe | A Network Trojan was detected | ET TROJAN [eSentire] Win32/GandCrab v4/5 Ransomware CnC Activity |
2892 | yeZjqHFMWjXi.exe | A Network Trojan was detected | MALWARE [PTsecurity] Win32/GandCrab Ransomware CnC Activity |
2892 | yeZjqHFMWjXi.exe | A Network Trojan was detected | MALWARE [PTsecurity] GandCrab Ransomware HTTP |
2892 | yeZjqHFMWjXi.exe | A Network Trojan was detected | MALWARE [PTsecurity] Win32/GandCrab Ransomware CnC Activity |
2892 | yeZjqHFMWjXi.exe | A Network Trojan was detected | MALWARE [PTsecurity] GandCrab Ransomware HTTP |
2892 | yeZjqHFMWjXi.exe | A Network Trojan was detected | MALWARE [PTsecurity] Win32/GandCrab Ransomware CnC Activity |
2892 | yeZjqHFMWjXi.exe | A Network Trojan was detected | MALWARE [PTsecurity] GandCrab Ransomware HTTP |
2892 | yeZjqHFMWjXi.exe | A Network Trojan was detected | ET POLICY Data POST to an image file (gif) |
2892 | yeZjqHFMWjXi.exe | A Network Trojan was detected | MALWARE [PTsecurity] Win32/GandCrab Ransomware CnC Activity |