| File name: | ddm.exe |
| Full analysis: | https://app.any.run/tasks/9b3e2bef-3620-416c-a79e-f812d88174ce |
| Verdict: | Malicious activity |
| Analysis date: | August 11, 2021, 15:38:43 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 99FCB4A07A2B38A2DAD00A2BE6635D79 |
| SHA1: | 0C27BDAB508E6AC0371EC9811CF43B67F7B96036 |
| SHA256: | D9C46BCFC8C8648DA8395BA20AE5E1B7BE54CB975DD06C1CC649A36019C6DF65 |
| SSDEEP: | 49152:Ge/eMocSG0c//////vGdvAEYuQngtrZHI6n:Geto+0c//////+dv0jg5ZHI6 |
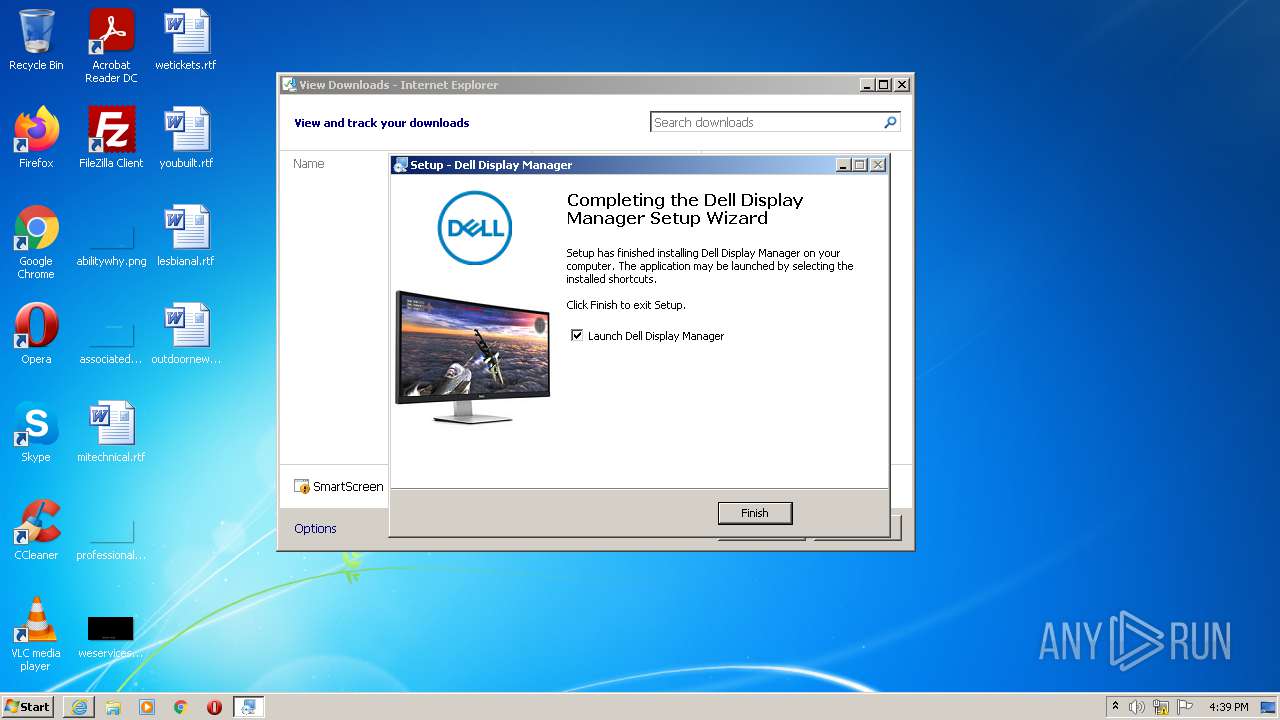
MALICIOUS
Application was dropped or rewritten from another process
- ddmsetup.exe (PID: 3632)
- ddmsetup.exe (PID: 3024)
- ddm.exe (PID: 1868)
- ddm.exe (PID: 876)
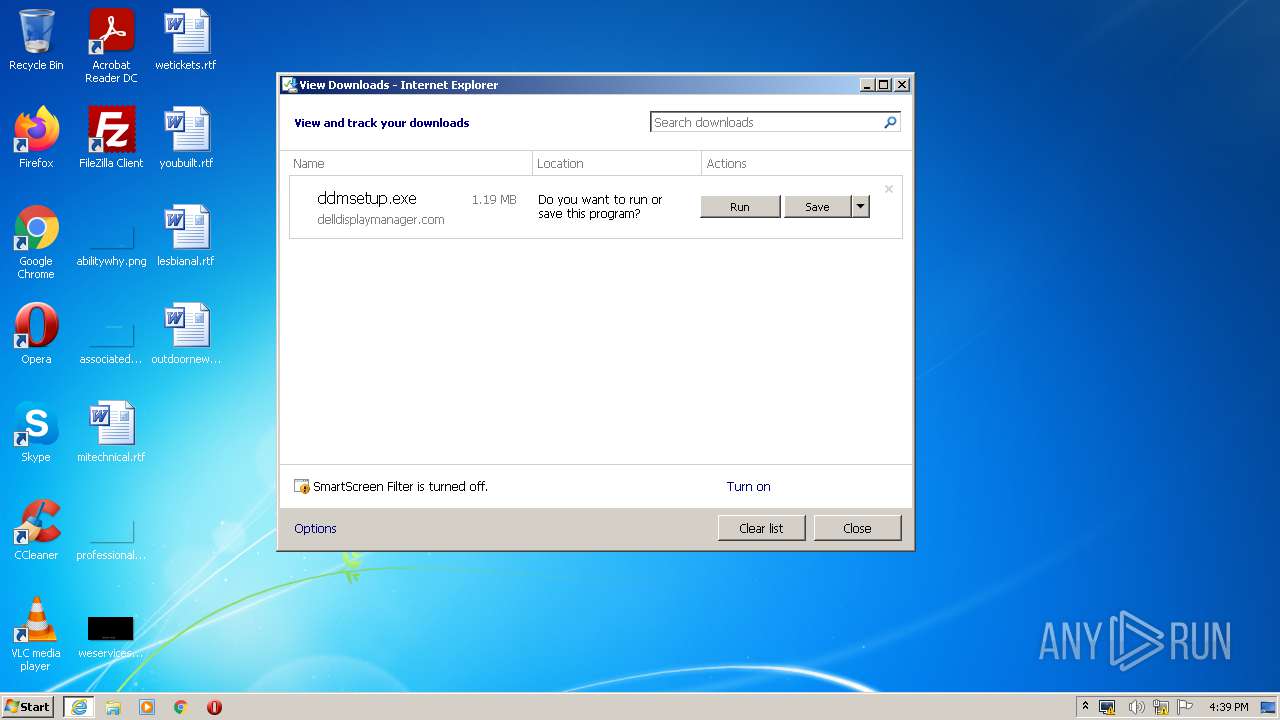
Drops executable file immediately after starts
- ddmsetup.exe (PID: 3632)
- ddmsetup.exe (PID: 3024)
- ddmsetup.tmp (PID: 3356)
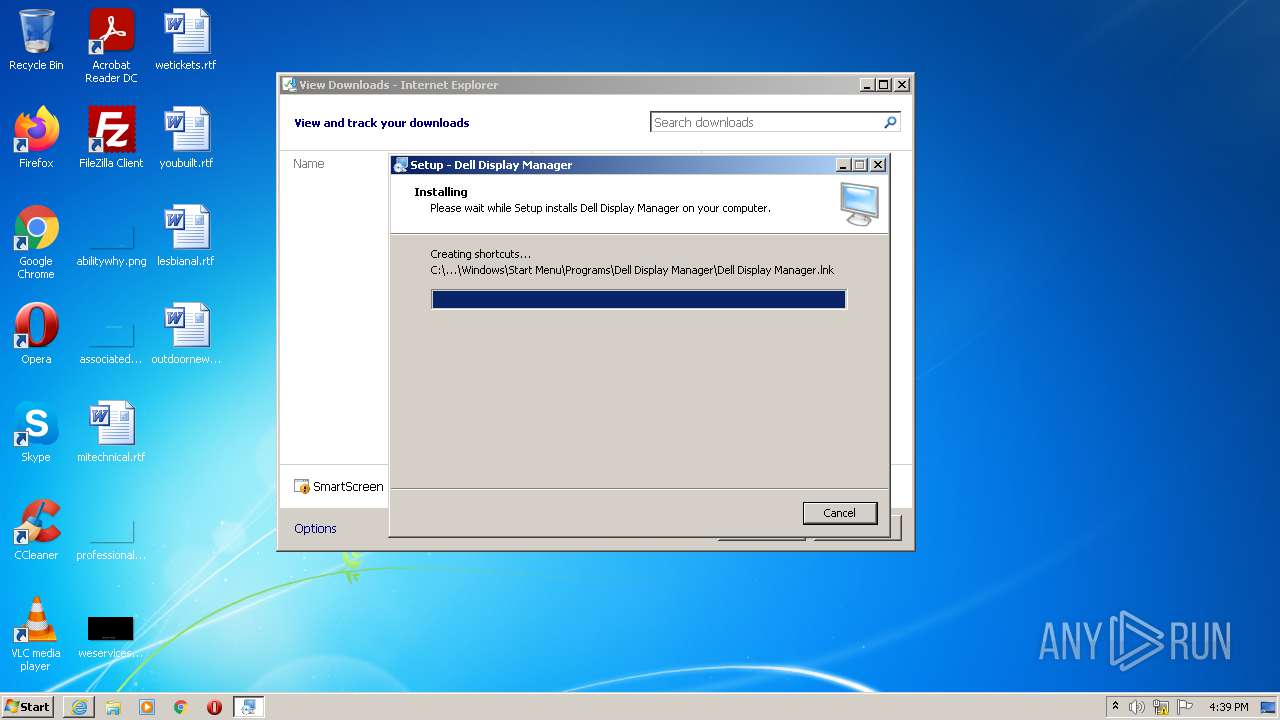
Writes to a start menu file
- ddmsetup.tmp (PID: 3356)
SUSPICIOUS
Checks supported languages
- ddm.exe (PID: 4064)
- ddmsetup.exe (PID: 3632)
- ddmsetup.tmp (PID: 3356)
- ddmcheck.exe (PID: 3760)
- ddmsetup.tmp (PID: 2364)
- ddmsetup.exe (PID: 3024)
- ddm.exe (PID: 1868)
- ddm.exe (PID: 876)
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 1928)
Reads the computer name
- ddm.exe (PID: 4064)
- ddmsetup.tmp (PID: 3356)
- ddmsetup.tmp (PID: 2364)
- ddm.exe (PID: 1868)
Starts Internet Explorer
- ddm.exe (PID: 4064)
Executable content was dropped or overwritten
- iexplore.exe (PID: 3684)
- ddmsetup.exe (PID: 3632)
- iexplore.exe (PID: 1928)
- ddmsetup.exe (PID: 3024)
- ddmsetup.tmp (PID: 3356)
Drops a file with too old compile date
- iexplore.exe (PID: 1928)
- ddmsetup.exe (PID: 3024)
- ddmsetup.tmp (PID: 3356)
- ddmsetup.exe (PID: 3632)
- iexplore.exe (PID: 3684)
Reads Windows owner or organization settings
- ddmsetup.tmp (PID: 3356)
Reads the Windows organization settings
- ddmsetup.tmp (PID: 3356)
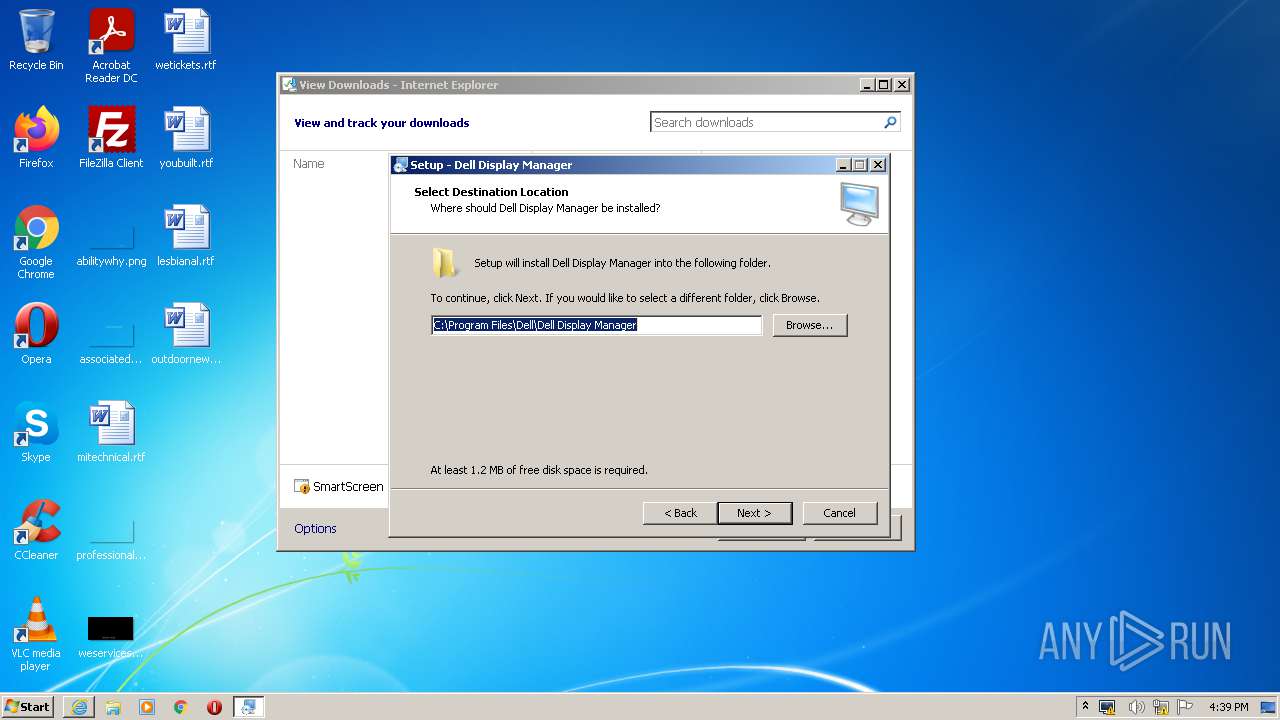
Creates a directory in Program Files
- ddmsetup.tmp (PID: 3356)
Changes default file association
- ddmsetup.tmp (PID: 3356)
INFO
Checks Windows Trust Settings
- ddm.exe (PID: 4064)
- iexplore.exe (PID: 1928)
- iexplore.exe (PID: 3684)
Reads settings of System Certificates
- ddm.exe (PID: 4064)
- iexplore.exe (PID: 3684)
- iexplore.exe (PID: 1928)
Checks supported languages
- iexplore.exe (PID: 3684)
- iexplore.exe (PID: 1928)
- regedit.exe (PID: 304)
Changes internet zones settings
- iexplore.exe (PID: 3684)
Reads the computer name
- iexplore.exe (PID: 3684)
- iexplore.exe (PID: 1928)
Application launched itself
- iexplore.exe (PID: 3684)
Adds / modifies Windows certificates
- iexplore.exe (PID: 3684)
Changes settings of System certificates
- iexplore.exe (PID: 3684)
Reads the date of Windows installation
- iexplore.exe (PID: 3684)
Modifies the phishing filter of IE
- iexplore.exe (PID: 3684)
Application was dropped or rewritten from another process
- ddmsetup.tmp (PID: 2364)
- ddmsetup.tmp (PID: 3356)
- ddmcheck.exe (PID: 3760)
Creates files in the program directory
- ddmsetup.tmp (PID: 3356)
Creates a software uninstall entry
- ddmsetup.tmp (PID: 3356)
Manual execution by user
- ddm.exe (PID: 876)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | InstallShield setup (53.2) |
|---|---|---|
| .exe | | | Win32 Executable Delphi generic (17.5) |
| .scr | | | Windows screen saver (16.1) |
| .exe | | | Win32 Executable (generic) (5.5) |
| .exe | | | Win16/32 Executable Delphi generic (2.5) |
EXIF
EXE
| Comments: | - |
|---|---|
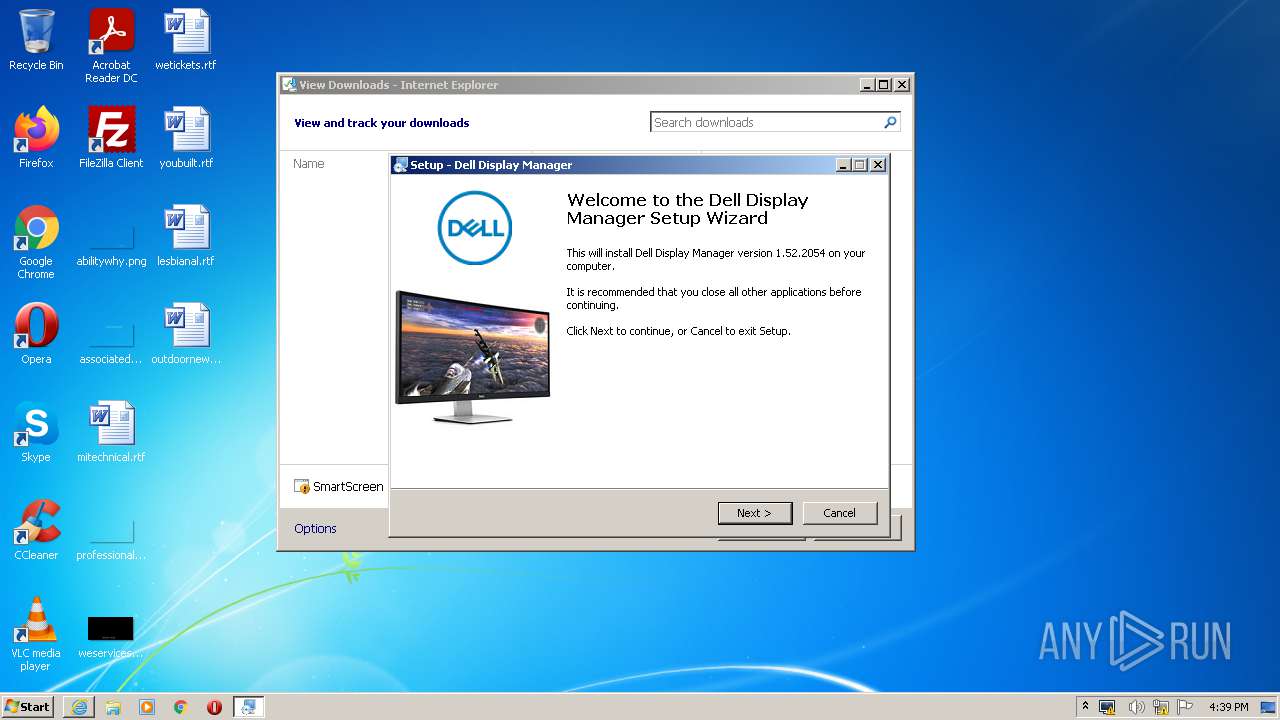
| ProductVersion: | 1.6 |
| ProductName: | Dell Display Manager |
| OriginalFileName: | mControl.exe |
| LegalTrademarks: | - |
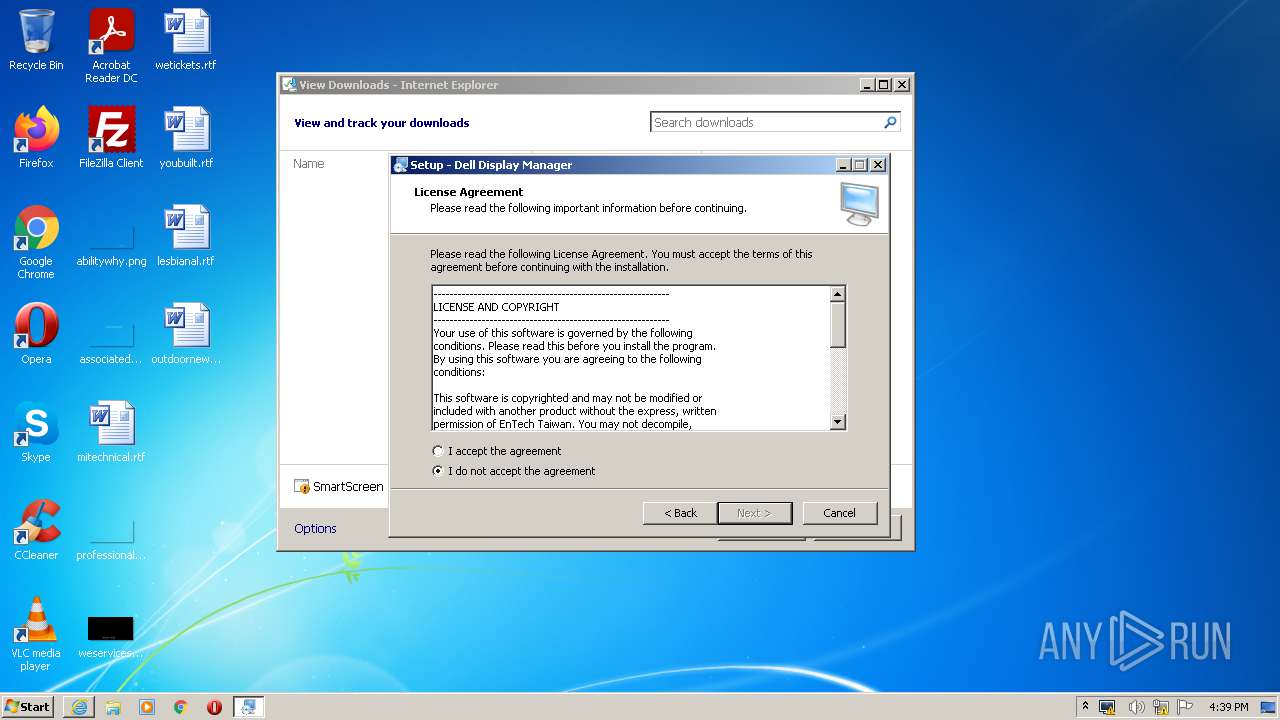
| LegalCopyright: | Copyright (c) EnTech Taiwan, 2007-2021. |
| InternalName: | ddm.exe |
| FileVersion: | 1.51.0.2029 |
| FileDescription: | Dell Display Manager |
| CompanyName: | EnTech Taiwan |
| CharacterSet: | Windows, Latin1 |
| LanguageCode: | English (U.S.) |
| FileSubtype: | - |
| ObjectFileType: | Executable application |
| FileOS: | Win32 |
| FileFlags: | (none) |
| FileFlagsMask: | 0x003f |
| ProductVersionNumber: | 1.51.0.2029 |
| FileVersionNumber: | 1.51.0.2029 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 4 |
| ImageVersion: | - |
| OSVersion: | 4 |
| EntryPoint: | 0x1a4cb4 |
| UninitializedDataSize: | - |
| InitializedDataSize: | 2241024 |
| CodeSize: | 1719808 |
| LinkerVersion: | 2.25 |
| PEType: | PE32 |
| TimeStamp: | 1992:06:20 00:22:17+02:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 19-Jun-1992 22:22:17 |
| Detected languages: |
|
| CompanyName: | EnTech Taiwan |
| FileDescription: | Dell Display Manager |
| FileVersion: | 1.51.0.2029 |
| InternalName: | ddm.exe |
| LegalCopyright: | Copyright (c) EnTech Taiwan, 2007-2021. |
| LegalTrademarks: | - |
| OriginalFilename: | mControl.exe |
| ProductName: | Dell Display Manager |
| ProductVersion: | 1.60 |
| Comments: | - |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 9 |
| Time date stamp: | 19-Jun-1992 22:22:17 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
CODE | 0x00001000 | 0x001A3D58 | 0x001A3E00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.52285 |
DATA | 0x001A5000 | 0x00005DD0 | 0x00005E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.73111 |
BSS | 0x001AB000 | 0x0001014D | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x001BC000 | 0x00003EF6 | 0x00004000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.06453 |
.edata | 0x001C0000 | 0x0000004A | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 0.694563 |
.tls | 0x001C1000 | 0x00000250 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x001C2000 | 0x00000018 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 0.20692 |
.reloc | 0x001C3000 | 0x00019010 | 0x00000000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 0 |
.rsrc | 0x001DD000 | 0x001FFC4F | 0x001FFE00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 2.2862 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.15894 | 1879 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 2.54425 | 2216 | UNKNOWN | English - United States | RT_ICON |
3 | 1.7233 | 1384 | UNKNOWN | English - United States | RT_ICON |
4 | 3.50825 | 2216 | UNKNOWN | UNKNOWN | RT_ICON |
5 | 2.6949 | 308 | UNKNOWN | UNKNOWN | RT_CURSOR |
6 | 2.62527 | 308 | UNKNOWN | UNKNOWN | RT_CURSOR |
7 | 2.91604 | 308 | UNKNOWN | UNKNOWN | RT_CURSOR |
8 | 1.86577 | 308 | UNKNOWN | English - United States | RT_CURSOR |
9 | 1.64003 | 308 | UNKNOWN | English - United States | RT_CURSOR |
10 | 1.64003 | 308 | UNKNOWN | English - United States | RT_CURSOR |
Imports
SetupApi.dll |
advapi32.dll |
cfgmgr32.dll |
comctl32.dll |
comdlg32.dll |
gdi32.dll |
kernel32.dll |
ole32.dll |
oleaut32.dll |
shell32.dll |
Exports
Title | Ordinal | Address |
|---|---|---|
madTraceProcess | 1 | 0x00103B80 |
Total processes
50
Monitored processes
11
Malicious processes
2
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 304 | "C:\Windows\regedit.exe" /s ddmsetup.reg | C:\Windows\regedit.exe | ddmsetup.tmp | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Editor Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 876 | "C:\Program Files\Dell\Dell Display Manager\ddm.exe" | C:\Program Files\Dell\Dell Display Manager\ddm.exe | — | Explorer.EXE | |||||||||||
User: admin Company: EnTech Taiwan Integrity Level: MEDIUM Description: Dell Display Manager Exit code: 0 Version: 1.52.0.2054 Modules
| |||||||||||||||
| 1868 | "C:\Program Files\Dell\Dell Display Manager\ddm.exe" ExpandConstant | C:\Program Files\Dell\Dell Display Manager\ddm.exe | ddmsetup.tmp | ||||||||||||
User: admin Company: EnTech Taiwan Integrity Level: MEDIUM Description: Dell Display Manager Exit code: 0 Version: 1.52.0.2054 Modules
| |||||||||||||||
| 1928 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3684 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2364 | "C:\Users\admin\AppData\Local\Temp\is-GI984.tmp\ddmsetup.tmp" /SL5="$20218,914931,60928,C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\ddmsetup.exe" | C:\Users\admin\AppData\Local\Temp\is-GI984.tmp\ddmsetup.tmp | — | ddmsetup.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Setup/Uninstall Exit code: 0 Version: 51.52.0.0 Modules
| |||||||||||||||
| 3024 | "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\ddmsetup.exe" /SPAWNWND=$20212 /NOTIFYWND=$20218 | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\ddmsetup.exe | ddmsetup.tmp | ||||||||||||
User: admin Company: EnTech Taiwan Integrity Level: HIGH Description: Dell Display Manager Setup Exit code: 0 Version: 1.05 Modules
| |||||||||||||||
| 3356 | "C:\Users\admin\AppData\Local\Temp\is-7MFE4.tmp\ddmsetup.tmp" /SL5="$40216,914931,60928,C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\ddmsetup.exe" /SPAWNWND=$20212 /NOTIFYWND=$20218 | C:\Users\admin\AppData\Local\Temp\is-7MFE4.tmp\ddmsetup.tmp | ddmsetup.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.52.0.0 Modules
| |||||||||||||||
| 3632 | "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\ddmsetup.exe" | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\ddmsetup.exe | iexplore.exe | ||||||||||||
User: admin Company: EnTech Taiwan Integrity Level: MEDIUM Description: Dell Display Manager Setup Exit code: 0 Version: 1.05 Modules
| |||||||||||||||
| 3684 | "C:\Program Files\Internet Explorer\iexplore.exe" https://www.delldisplaymanager.com/ddmsetup.exe | C:\Program Files\Internet Explorer\iexplore.exe | ddm.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3760 | "C:\Users\admin\AppData\Local\Temp\is-573LH.tmp\ddmcheck.exe" | C:\Users\admin\AppData\Local\Temp\is-573LH.tmp\ddmcheck.exe | — | ddmsetup.tmp | |||||||||||
User: admin Company: EnTech Taiwan Integrity Level: HIGH Description: DDM Check Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
Total events
14 086
Read events
13 841
Write events
235
Delete events
10
Modification events
| (PID) Process: | (4064) ddm.exe | Key: | HKEY_CURRENT_USER\Software\EnTech\DDM |
| Operation: | write | Name: | EnumErrorCount |
Value: 0 | |||
| (PID) Process: | (4064) ddm.exe | Key: | HKEY_CURRENT_USER\Software\EnTech\RPC\Out |
| Operation: | write | Name: | (default) |
Value: | |||
| (PID) Process: | (4064) ddm.exe | Key: | HKEY_CURRENT_USER\Software\EnTech\RPC\In |
| Operation: | write | Name: | (default) |
Value: | |||
| (PID) Process: | (4064) ddm.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (4064) ddm.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 460000003B010000090000000000000000000000000000000400000000000000C0E333BBEAB1D3010000000000000000000000000100000002000000C0A80164000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (4064) ddm.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (4064) ddm.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (4064) ddm.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (4064) ddm.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (4064) ddm.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
Executable files
12
Suspicious files
8
Text files
4
Unknown types
11
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4064 | ddm.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\644B8874112055B5E195ECB0E8F243A4 | der | |
MD5:452010DF5190805ECCE2E9F404D43048 | SHA256:B5A129DC56EA03AF0880964265B4537CF70FE00212AB46D2FFB0931434D3CC90 | |||
| 4064 | ddm.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\103621DE9CD5414CC2538780B4B75751 | binary | |
MD5:51050D3CF3A45120AFAC901BF5A5150B | SHA256:2000E730F24859171E1EF3CD3A0C122C2F0015FB32E6650C5E1A71D8F2871C99 | |||
| 4064 | ddm.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\78RFYB7Z\ddm[1].inf | text | |
MD5:E5D2734E9E67FC0121AFA9AE208E312D | SHA256:EB8D7F217B98BF3F6D2B9CDA4381714D5ECDE319933E44D35251A6ABB9D01214 | |||
| 4064 | ddm.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\7F124329ED801D26DE932365AEEB65E9 | der | |
MD5:10166134BE339205E8C22865D6FC077D | SHA256:750187F13AB6AD8A98DC4EE84C7D56808A77F54770CDB07C0A0399047F1B79A1 | |||
| 4064 | ddm.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\7F124329ED801D26DE932365AEEB65E9 | binary | |
MD5:89DFA20FD93A7F66782EBFCF03D8AB8B | SHA256:E316675E4EF23073C068A8139C90F065FB8CD7867913E1450312D0F9F6D14259 | |||
| 1928 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\ddmsetup[1].exe | executable | |
MD5:089780281514F1FF27A2479CBEAFDFF0 | SHA256:1AAA12736AAC19D8D870BCE79C358F126C53552C0959EEA9AD6E52679FEA8CA6 | |||
| 4064 | ddm.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\644B8874112055B5E195ECB0E8F243A4 | binary | |
MD5:FC17C6E407313DB68439ECDAF5C91ACB | SHA256:47BCE8021A5520203E35AA9289A5AA3F801230C7330DC97255365B8C74B53BCE | |||
| 4064 | ddm.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:609C622916F14B00487891A01153EDEE | SHA256:2CFC21DF301A5A9C9CD4A9513EC71322A2E0CDA8B852F98A832B4A83B9B84679 | |||
| 3684 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DFC4084B4644ECBE04.TMP | gmc | |
MD5:D2B945276189294F60DA11751B373837 | SHA256:B9E76A327409B94CFED818A3D254D19ECFAE8EB532D03C90CED5BFFD2F0F646E | |||
| 1928 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\ddmsetup.exe.3i2pnal.partial | executable | |
MD5:0827769DB046F392659102C73A11C006 | SHA256:312C21264481FE19D835277E3C7B75013E589EDB0895E42AD901AC6C196F927F | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
10
DNS requests
5
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4064 | ddm.exe | GET | 200 | 23.55.163.73:80 | http://crl.identrust.com/DSTROOTCAX3CRL.crl | US | der | 1.16 Kb | whitelisted |
4064 | ddm.exe | GET | 200 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?1cf35c21fca03db8 | US | compressed | 4.70 Kb | whitelisted |
4064 | ddm.exe | GET | 200 | 104.117.200.9:80 | http://x1.c.lencr.org/ | US | der | 717 b | whitelisted |
4064 | ddm.exe | GET | 200 | 23.55.163.58:80 | http://r3.o.lencr.org/MFMwUTBPME0wSzAJBgUrDgMCGgUABBRI2smg%2ByvTLU%2Fw3mjS9We3NfmzxAQUFC6zF7dYVsuuUAlA5h%2BvnYsUwsYCEgQvjNlexkNxe3vxkpD2U7GfiQ%3D%3D | US | der | 503 b | shared |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4064 | ddm.exe | 69.89.25.45:443 | www.delldisplaymanager.com | Unified Layer | US | suspicious |
4064 | ddm.exe | 23.55.163.73:80 | crl.identrust.com | Akamai International B.V. | US | unknown |
4064 | ddm.exe | 104.117.200.9:80 | x1.c.lencr.org | TPG Telecom Limited | US | unknown |
4064 | ddm.exe | 93.184.221.240:80 | ctldl.windowsupdate.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
4064 | ddm.exe | 23.55.163.58:80 | r3.o.lencr.org | Akamai International B.V. | US | unknown |
1928 | iexplore.exe | 69.89.25.45:443 | www.delldisplaymanager.com | Unified Layer | US | suspicious |
1868 | ddm.exe | 69.89.25.45:443 | www.delldisplaymanager.com | Unified Layer | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.delldisplaymanager.com |
| suspicious |
ctldl.windowsupdate.com |
| whitelisted |
crl.identrust.com |
| whitelisted |
x1.c.lencr.org |
| whitelisted |
r3.o.lencr.org |
| shared |
Threats
Process | Message |
|---|---|
regedit.exe | REGEDIT: CreateFile failed, GetLastError() = 2
|