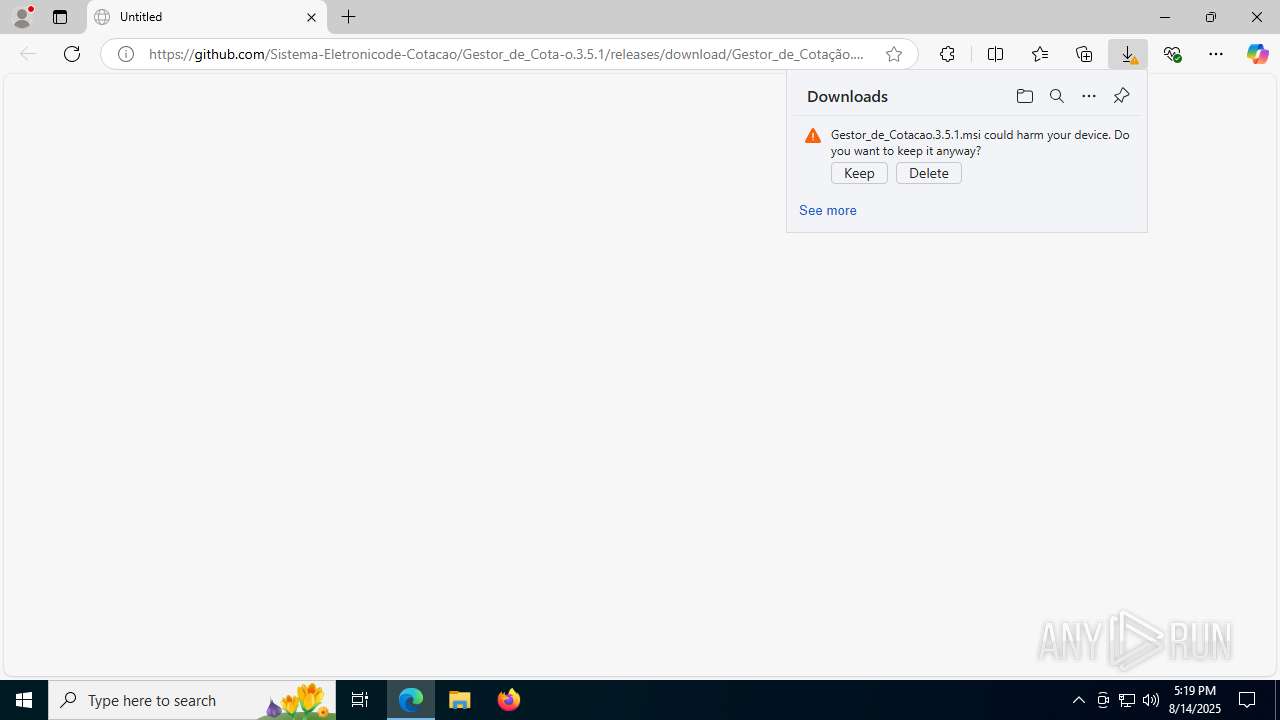
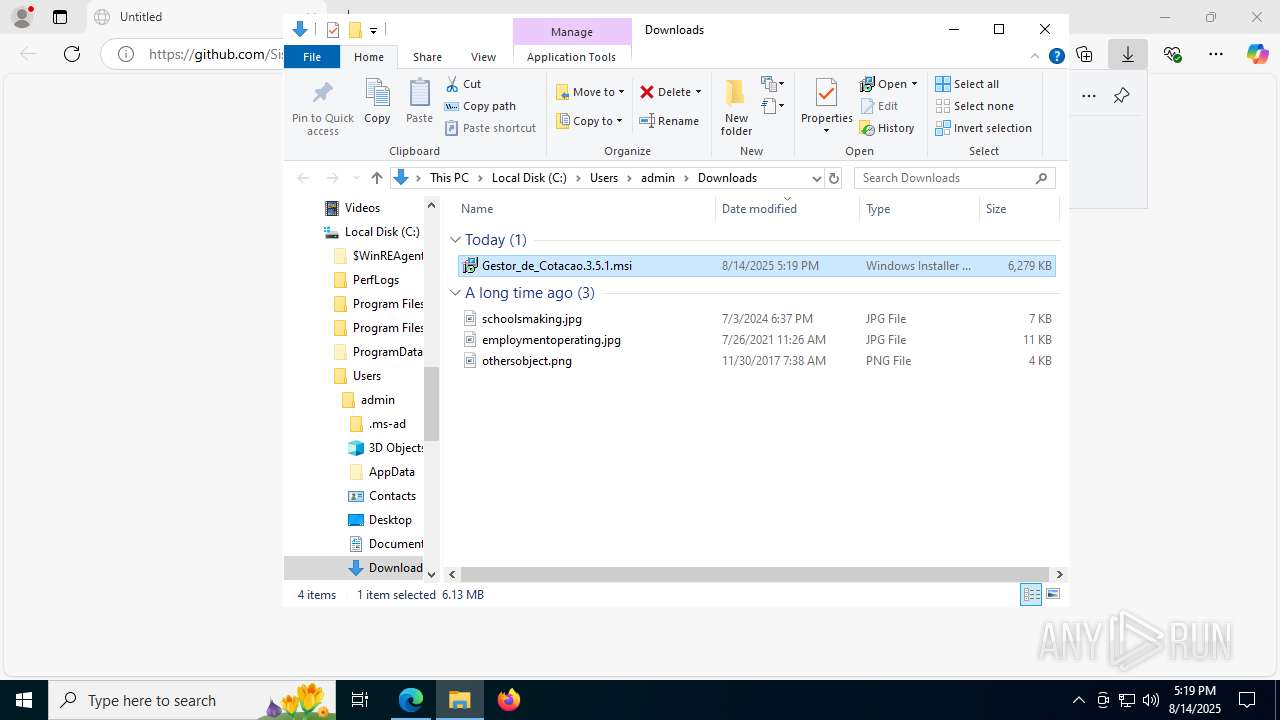
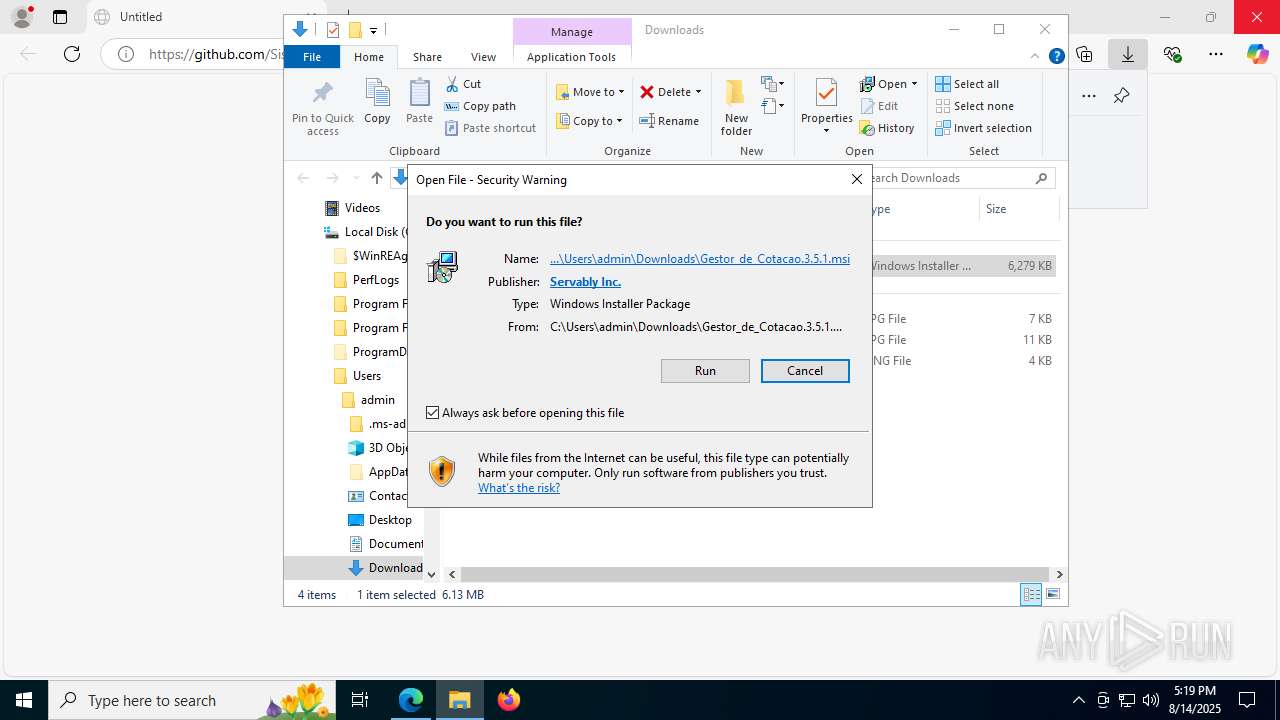
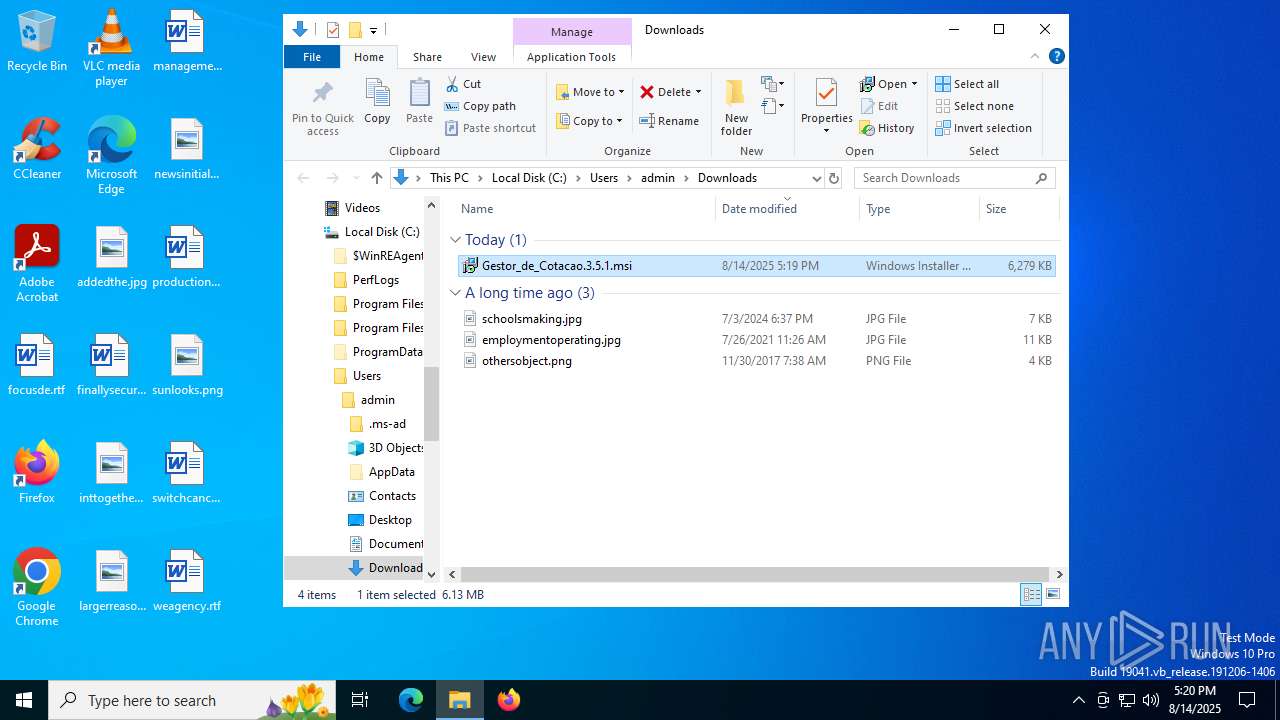
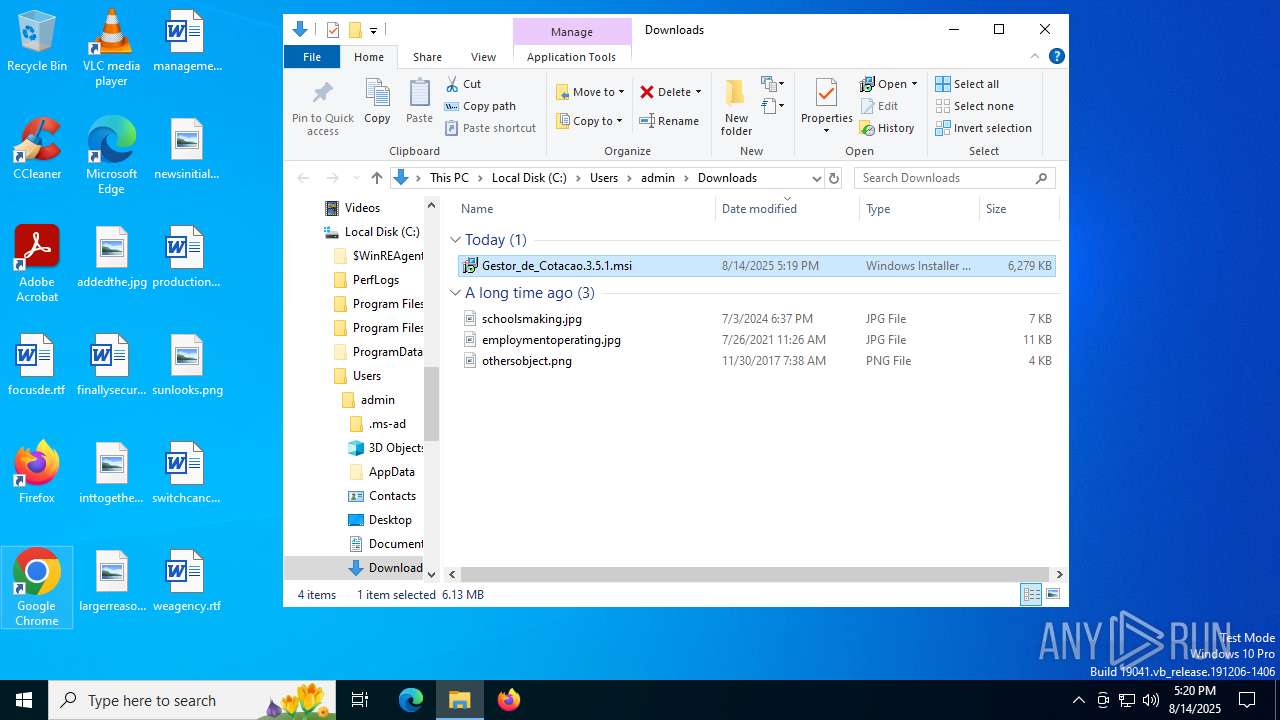
| URL: | https://github.com/Sistema-Eletronicode-Cotacao/Gestor_de_Cota-o.3.5.1/releases/download/Gestor_de_Cota%C3%A7%C3%A3o.3.5.1/Gestor_de_Cotacao.3.5.1.msi |
| Full analysis: | https://app.any.run/tasks/f217e3fc-6002-4624-9306-58cdaceedb0f |
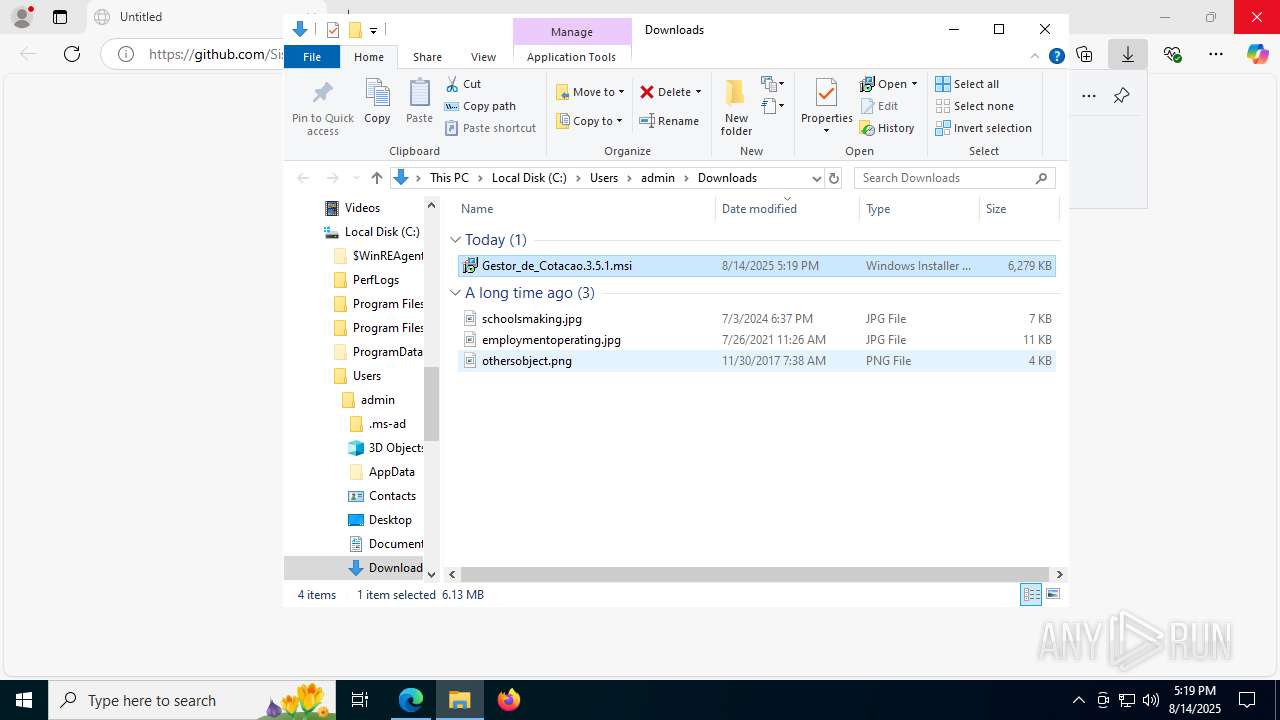
| Verdict: | Malicious activity |
| Analysis date: | August 14, 2025, 17:19:29 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 2C02BAD2DBCDD1F5048D88AAA91EA7D7 |
| SHA1: | D2BCC8F37EC80DAA486DF676AD9A35CFDA0699C9 |
| SHA256: | D99F771F8C99C680B309153A2D01326F95B00EFBECCAB9C242ACC47A13949C2F |
| SSDEEP: | 3:N8tEdSxQa7KqFLcoeUMsMkCjWFL9SAhA/LdL7LmHM:2uoxQlqFooeUMdBkcLd6s |
MALICIOUS
No malicious indicators.SUSPICIOUS
Creates file in the systems drive root
- explorer.exe (PID: 4772)
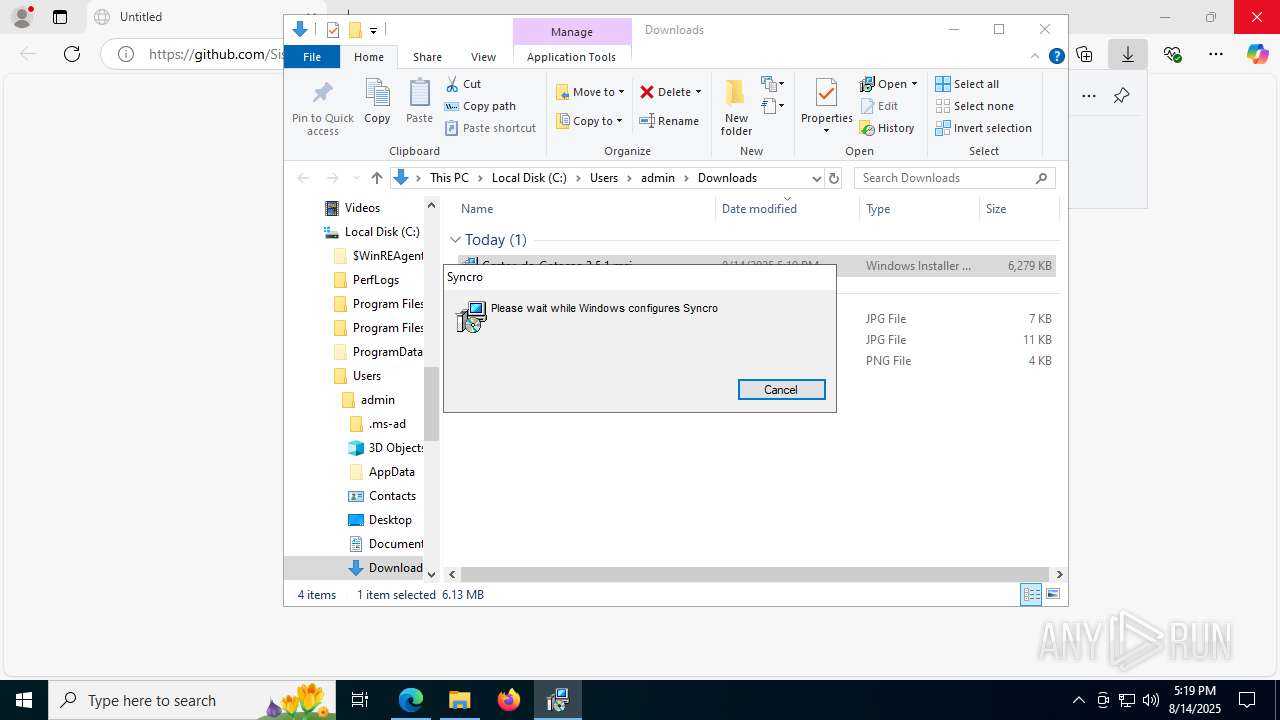
Executes as Windows Service
- VSSVC.exe (PID: 7872)
- Syncro.Service.Runner.exe (PID: 4800)
- WmiApSrv.exe (PID: 3572)
- Syncro.Overmind.Service.exe (PID: 4160)
- SyncroLive.Service.Runner.exe (PID: 6956)
- Syncro.Service.Runner.exe (PID: 7836)
- WmiApSrv.exe (PID: 6840)
Reads the Windows owner or organization settings
- msiexec.exe (PID: 7616)
Executable content was dropped or overwritten
- rundll32.exe (PID: 7548)
- Installer.exe (PID: 4528)
- Syncro.Installer.exe (PID: 1236)
- Syncro.Service.Runner.exe (PID: 4800)
- Syncro.Overmind.Service.exe (PID: 4160)
- Syncro.Service.Runner.exe (PID: 7836)
Reads security settings of Internet Explorer
- Installer.exe (PID: 4528)
- InstallUtil.exe (PID: 1156)
- Syncro.Service.Runner.exe (PID: 4800)
- Syncro.App.Runner.exe (PID: 6408)
- SyncroLive.Service.Runner.exe (PID: 6956)
- Syncro.Service.Runner.exe (PID: 7836)
- SyncroLive.Agent.Runner.exe (PID: 5684)
- Syncro.App.Runner.exe (PID: 2040)
Reads the date of Windows installation
- Installer.exe (PID: 4528)
The process creates files with name similar to system file names
- Syncro.Installer.exe (PID: 1236)
- Syncro.Overmind.Service.exe (PID: 4160)
Process drops legitimate windows executable
- Syncro.Installer.exe (PID: 1236)
- Syncro.Overmind.Service.exe (PID: 4160)
Starts CMD.EXE for commands execution
- Syncro.Installer.exe (PID: 1236)
Executing commands from a ".bat" file
- Syncro.Installer.exe (PID: 1236)
Drops 7-zip archiver for unpacking
- Syncro.Installer.exe (PID: 1236)
- Syncro.Overmind.Service.exe (PID: 4160)
Restarts service on failure
- sc.exe (PID: 6264)
Windows service management via SC.EXE
- sc.exe (PID: 1128)
Searches for installed software
- Syncro.Installer.exe (PID: 1236)
- Syncro.Service.Runner.exe (PID: 4800)
- Syncro.Service.Runner.exe (PID: 7836)
Starts SC.EXE for service management
- cmd.exe (PID: 6876)
Creates a software uninstall entry
- Syncro.Service.Runner.exe (PID: 4800)
The process checks if it is being run in the virtual environment
- Syncro.Service.Runner.exe (PID: 4800)
- SyncroLive.Agent.Runner.exe (PID: 5684)
Creates or modifies Windows services
- Syncro.Overmind.Service.exe (PID: 6332)
INFO
Checks supported languages
- identity_helper.exe (PID: 7652)
- msiexec.exe (PID: 7616)
- identity_helper.exe (PID: 4864)
- msiexec.exe (PID: 4224)
- Installer.exe (PID: 4528)
- Syncro.Installer.exe (PID: 1236)
- InstallUtil.exe (PID: 1156)
- Syncro.App.Runner.exe (PID: 6408)
- Syncro.Service.Runner.exe (PID: 4800)
- Syncro.Overmind.Service.exe (PID: 6332)
- Syncro.Overmind.Service.exe (PID: 4160)
- SyncroLive.Service.Runner.exe (PID: 6956)
- SyncroLive.Agent.Runner.exe (PID: 5684)
- Syncro.Service.Runner.exe (PID: 7836)
- Syncro.App.Runner.exe (PID: 2040)
Application launched itself
- msedge.exe (PID: 2972)
- msedge.exe (PID: 7704)
Reads Environment values
- identity_helper.exe (PID: 7652)
- identity_helper.exe (PID: 4864)
- Syncro.Installer.exe (PID: 1236)
- Syncro.Service.Runner.exe (PID: 4800)
- Syncro.Overmind.Service.exe (PID: 6332)
- Syncro.Overmind.Service.exe (PID: 4160)
- SyncroLive.Agent.Runner.exe (PID: 5684)
- Syncro.Service.Runner.exe (PID: 7836)
Reads the computer name
- identity_helper.exe (PID: 7652)
- msiexec.exe (PID: 7616)
- identity_helper.exe (PID: 4864)
- msiexec.exe (PID: 4224)
- Installer.exe (PID: 4528)
- Syncro.Installer.exe (PID: 1236)
- InstallUtil.exe (PID: 1156)
- Syncro.Service.Runner.exe (PID: 4800)
- Syncro.App.Runner.exe (PID: 6408)
- Syncro.Overmind.Service.exe (PID: 6332)
- Syncro.Overmind.Service.exe (PID: 4160)
- SyncroLive.Service.Runner.exe (PID: 6956)
- Syncro.Service.Runner.exe (PID: 7836)
- SyncroLive.Agent.Runner.exe (PID: 5684)
- Syncro.App.Runner.exe (PID: 2040)
Checks proxy server information
- explorer.exe (PID: 4772)
- slui.exe (PID: 7752)
Reads Microsoft Office registry keys
- explorer.exe (PID: 4772)
Reads security settings of Internet Explorer
- explorer.exe (PID: 4772)
- msiexec.exe (PID: 7388)
Creates files or folders in the user directory
- explorer.exe (PID: 4772)
Reads the software policy settings
- msiexec.exe (PID: 7388)
- explorer.exe (PID: 4772)
- msiexec.exe (PID: 7616)
- Syncro.Installer.exe (PID: 1236)
- Syncro.Service.Runner.exe (PID: 4800)
- Syncro.Overmind.Service.exe (PID: 4160)
- slui.exe (PID: 7752)
- SyncroLive.Agent.Runner.exe (PID: 5684)
- Syncro.Service.Runner.exe (PID: 7836)
Manages system restore points
- SrTasks.exe (PID: 7308)
Create files in a temporary directory
- msiexec.exe (PID: 7616)
- rundll32.exe (PID: 7548)
- Installer.exe (PID: 4528)
- Syncro.Installer.exe (PID: 1236)
Executable content was dropped or overwritten
- msiexec.exe (PID: 7616)
Creates files in the program directory
- Installer.exe (PID: 4528)
- Syncro.Installer.exe (PID: 1236)
- InstallUtil.exe (PID: 1156)
- Syncro.Service.Runner.exe (PID: 4800)
- Syncro.App.Runner.exe (PID: 6408)
- Syncro.Overmind.Service.exe (PID: 6332)
- Syncro.Overmind.Service.exe (PID: 4160)
- SyncroLive.Service.Runner.exe (PID: 6956)
- SyncroLive.Agent.Runner.exe (PID: 5684)
- Syncro.Service.Runner.exe (PID: 7836)
Process checks computer location settings
- Installer.exe (PID: 4528)
Reads the machine GUID from the registry
- msiexec.exe (PID: 7616)
- Syncro.Installer.exe (PID: 1236)
- InstallUtil.exe (PID: 1156)
- Syncro.Service.Runner.exe (PID: 4800)
- Syncro.App.Runner.exe (PID: 6408)
- Syncro.Overmind.Service.exe (PID: 6332)
- Syncro.Overmind.Service.exe (PID: 4160)
- SyncroLive.Service.Runner.exe (PID: 6956)
- SyncroLive.Agent.Runner.exe (PID: 5684)
- Syncro.App.Runner.exe (PID: 2040)
- Syncro.Service.Runner.exe (PID: 7836)
Disables trace logs
- Syncro.Installer.exe (PID: 1236)
- Syncro.Service.Runner.exe (PID: 4800)
- Syncro.Overmind.Service.exe (PID: 4160)
SYNCRO has been detected
- Syncro.Installer.exe (PID: 1236)
- cmd.exe (PID: 6876)
- InstallUtil.exe (PID: 1156)
- Syncro.Service.Runner.exe (PID: 4800)
- Syncro.App.Runner.exe (PID: 6408)
- Syncro.Overmind.Service.exe (PID: 4160)
- Syncro.Service.Runner.exe (PID: 7836)
- Syncro.App.Runner.exe (PID: 2040)
- SyncroLive.Agent.Runner.exe (PID: 5684)
The sample compiled with english language support
- Syncro.Installer.exe (PID: 1236)
- Syncro.Overmind.Service.exe (PID: 4160)
Creates a software uninstall entry
- msiexec.exe (PID: 7616)
Reads the time zone
- Syncro.Service.Runner.exe (PID: 4800)
- SyncroLive.Agent.Runner.exe (PID: 5684)
Reads CPU info
- Syncro.Service.Runner.exe (PID: 4800)
- SyncroLive.Agent.Runner.exe (PID: 5684)
Process checks Powershell version
- Syncro.Service.Runner.exe (PID: 4800)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
213
Monitored processes
67
Malicious processes
4
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1128 | sc start Syncro | C:\Windows\System32\sc.exe | — | cmd.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Service Control Manager Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1156 | "C:\WINDOWS\Microsoft.NET\Framework64\v4.0.30319\installutil.exe" /ShowCallStack /LogFile=C:\ProgramData/Syncro/logs/ServiceInstall.log "C:\Program Files\RepairTech\Syncro\Syncro.Service.Runner.exe" | C:\Windows\Microsoft.NET\Framework64\v4.0.30319\InstallUtil.exe | — | cmd.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: .NET Framework installation utility Exit code: 0 Version: 4.8.9037.0 built by: NET481REL1 Modules
| |||||||||||||||
| 1160 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=4064,i,2787492994232913238,9751382556949458411,262144 --variations-seed-version --mojo-platform-channel-handle=4000 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1236 | "C:\Users\admin\AppData\Local\Temp\Syncro.Installer.exe" --msi --key "vhI4BHrbwJt2m1SLmD-35g" --folderid "4581190" --customerid "1697280" --config-json "ewogICJBdXRoVXJsIjogImh0dHBzOi8vYWRtaW4uc3luY3JvYXBpLmNvbSIsCiAgIkthYnV0b1VybCI6ICJodHRwczovL3JtbS5zeW5jcm9tc3AuY29tIiwKICAiU3luY3JvVXJscyI6IFsKICAgICJodHRwczovL3tzdWJkb21haW59LnN5bmNyb2FwaS5jb20iLAogICAgImh0dHBzOi8ve3N1YmRvbWFpbn0uc3luY3JvbXNwLmNvbSJdLAogICJMb2dEdW1wZXJVcmwiOiAiaHR0cHM6Ly9sZC5hdXJlbGl1cy5ob3N0IiwKICAiVXBkYXRlVXJsIjogImh0dHBzOi8vcHJvZHVjdGlvbi5rYWJ1dG9zZXJ2aWNlcy5jb20vc3luY3JvL21haW4vdXBkYXRlcy8iLAogICJPdmVybWluZFVwZGF0ZVVybCI6ICJodHRwczovL3Byb2R1Y3Rpb24ua2FidXRvc2VydmljZXMuY29tL3N5bmNyby9vdmVybWluZC91cGRhdGVzLyIsCiAgIkNob2NvbGF0ZXlJbnN0YWxsZXJVcmwiOiAiaHR0cHM6Ly9wcm9kdWN0aW9uLmthYnV0b3NlcnZpY2VzLmNvbS9jaG9jby9rYWJ1dG9fcGF0Y2hfbWFuYWdlciIsCiAgIldlYlNvY2tldFVybCI6ICJ3c3M6Ly9yZWFsdGltZS5rYWJ1dG9zZXJ2aWNlcy5jb20vc29ja2V0IiwKICAiQ2hhdFVybCI6ICJ3c3M6Ly9jaGF0LWNoYXQuc3luY3JvbXNwLmNvbS9zb2NrZXQiLAogICJfIjogIiIKfQo=" | C:\Users\admin\AppData\Local\Temp\Syncro.Installer.exe | Installer.exe | ||||||||||||
User: SYSTEM Company: Servably, Inc. Integrity Level: SYSTEM Description: Kabuto.Installer Exit code: 0 Version: 1.0.190.17750 Modules
| |||||||||||||||
| 1512 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=2764,i,16908421887919259590,181927550197959176,262144 --variations-seed-version --mojo-platform-channel-handle=2772 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1636 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=2288,i,16908421887919259590,181927550197959176,262144 --variations-seed-version --mojo-platform-channel-handle=2472 /prefetch:3 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | msedge.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1704 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | SyncroLive.Agent.Runner.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2040 | "C:\Program Files\RepairTech\Syncro\Syncro.App.Runner.exe" | C:\Program Files\RepairTech\Syncro\Syncro.App.Runner.exe | — | Syncro.Service.Runner.exe | |||||||||||
User: admin Company: Servably, Inc. Integrity Level: HIGH Description: Syncro.App.Runner Version: 1.0.191.17899 Modules
| |||||||||||||||
| 2200 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2704 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | SrTasks.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
93 586
Read events
92 981
Write events
581
Delete events
24
Modification events
| (PID) Process: | (2972) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2972) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2972) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2972) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (4772) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\SessionInfo\1\ApplicationViewManagement\W32:00000000000D0344 |
| Operation: | write | Name: | VirtualDesktop |
Value: 10000000303044563096AFED4A643448A750FA41CFC7F708 | |||
| (PID) Process: | (2972) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\852804 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {58C4CC18-5BA6-400D-95C2-F52009B4E37E} | |||
| (PID) Process: | (2972) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: B1640DC3EC9A2F00 | |||
| (PID) Process: | (4772) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\SessionInfo\1\ApplicationViewManagement\W32:00000000000B035A |
| Operation: | write | Name: | VirtualDesktop |
Value: 10000000303044563096AFED4A643448A750FA41CFC7F708 | |||
| (PID) Process: | (2972) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\852804 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {EB4C9CF5-4DA5-49A3-8199-349EA3BBAAB5} | |||
| (PID) Process: | (2972) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 9EB91FC3EC9A2F00 | |||
Executable files
370
Suspicious files
311
Text files
166
Unknown types
52
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2972 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF18e27b.TMP | — | |
MD5:— | SHA256:— | |||
| 2972 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2972 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF18e28b.TMP | — | |
MD5:— | SHA256:— | |||
| 2972 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old~RF18e27b.TMP | — | |
MD5:— | SHA256:— | |||
| 2972 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2972 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2972 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF18e29b.TMP | — | |
MD5:— | SHA256:— | |||
| 2972 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2972 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF18e2ba.TMP | — | |
MD5:— | SHA256:— | |||
| 2972 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old~RF18e2c9.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
24
TCP/UDP connections
82
DNS requests
76
Threats
29
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2460 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
1636 | msedge.exe | GET | 200 | 150.171.27.11:80 | http://edge.microsoft.com/browsernetworktime/time/1/current?cup2key=2:jaXe6vxkcylp60KDxuQEuwVwayx_xksVHcnlnfcwkFw&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 23.216.77.4:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4772 | explorer.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBT3xL4LQLXDRDM9P665TW442vrsUQQUReuir%2FSSy4IxLVGLp6chnfNtyA8CEA6bGI750C3n79tQ4ghAGFo%3D | unknown | — | — | whitelisted |
4772 | explorer.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfIs%2BLjDtGwQ09XEB1Yeq%2BtX%2BBgQQU7NfjgtJxXWRM3y5nP%2Be6mK4cD08CEAitQLJg0pxMn17Nqb2Trtk%3D | unknown | — | — | whitelisted |
4772 | explorer.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSRXerF0eFeSWRripTgTkcJWMm7iQQUaDfg67Y7%2BF8Rhvv%2BYXsIiGX0TkICEA361MoYdn9Fs8n8dWU5Vwk%3D | unknown | — | — | whitelisted |
7760 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7760 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
2940 | svchost.exe | GET | 200 | 2.23.197.184:80 | http://x1.c.lencr.org/ | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1268 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2216 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1636 | msedge.exe | 140.82.121.3:443 | github.com | GITHUB | US | whitelisted |
1636 | msedge.exe | 150.171.22.17:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
1636 | msedge.exe | 150.171.27.11:80 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
1636 | msedge.exe | 150.171.27.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
1636 | msedge.exe | 92.123.104.45:443 | copilot.microsoft.com | Akamai International B.V. | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
github.com |
| whitelisted |
copilot.microsoft.com |
| whitelisted |
release-assets.githubusercontent.com |
| whitelisted |
update.googleapis.com |
| whitelisted |
www.bing.com |
| whitelisted |
clients2.googleusercontent.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1636 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access release user assets on GitHub |
— | — | Potentially Bad Traffic | ET INFO Possible Chrome Plugin install |
— | — | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |
2200 | svchost.exe | Potentially Bad Traffic | ET REMOTE_ACCESS Observed Remote Management Software Domain in DNS Lookup (syncromsp .com) |
1236 | Syncro.Installer.exe | Potentially Bad Traffic | ET REMOTE_ACCESS Observed Remote Management Software Domain (syncromsp .com in TLS SNI) |
2200 | svchost.exe | Misc activity | ET REMOTE_ACCESS Observed SyncroMSP Remote Management Software Domain in DNS Lookup (kabutoservices .com) |
— | — | Misc activity | ET INFO SyncroMSP Remote Remote Management Software Install Registration |
1236 | Syncro.Installer.exe | Potentially Bad Traffic | ET REMOTE_ACCESS Observed SyncroMSP Remote Management Software Domain (kabutoservices .com in TLS SNI) |
1236 | Syncro.Installer.exe | Potentially Bad Traffic | ET REMOTE_ACCESS Observed Remote Management Software Domain (syncromsp .com in TLS SNI) |
1236 | Syncro.Installer.exe | Potentially Bad Traffic | ET REMOTE_ACCESS Observed Remote Management Software Domain (syncromsp .com in TLS SNI) |
Process | Message |
|---|---|
SyncroLive.Service.Runner.exe | Topshelf.HostFactory Information: 0 : |
SyncroLive.Service.Runner.exe | Configuration Result:
[Success] Name SyncroLive
[Success] Description The server that powers SyncroLive Cloud
[Success] ServiceName SyncroLive
|
SyncroLive.Service.Runner.exe | Topshelf.HostConfigurators.HostConfiguratorImpl Information: 0 : |
SyncroLive.Service.Runner.exe | Topshelf v4.3.0.0, .NET Framework 4.8.9181.0 (4.0.30319.42000)
|
SyncroLive.Service.Runner.exe | Topshelf.Runtime.Windows.WindowsServiceHost Information: 0 : |
SyncroLive.Service.Runner.exe | Starting as a Windows service
|
SyncroLive.Service.Runner.exe | Topshelf.Runtime.Windows.WindowsServiceHost Information: 0 : |
SyncroLive.Service.Runner.exe | [Topshelf] Starting
|
SyncroLive.Service.Runner.exe | Topshelf.Runtime.Windows.WindowsServiceHost Information: 0 : |
SyncroLive.Service.Runner.exe | [Topshelf] Started
|