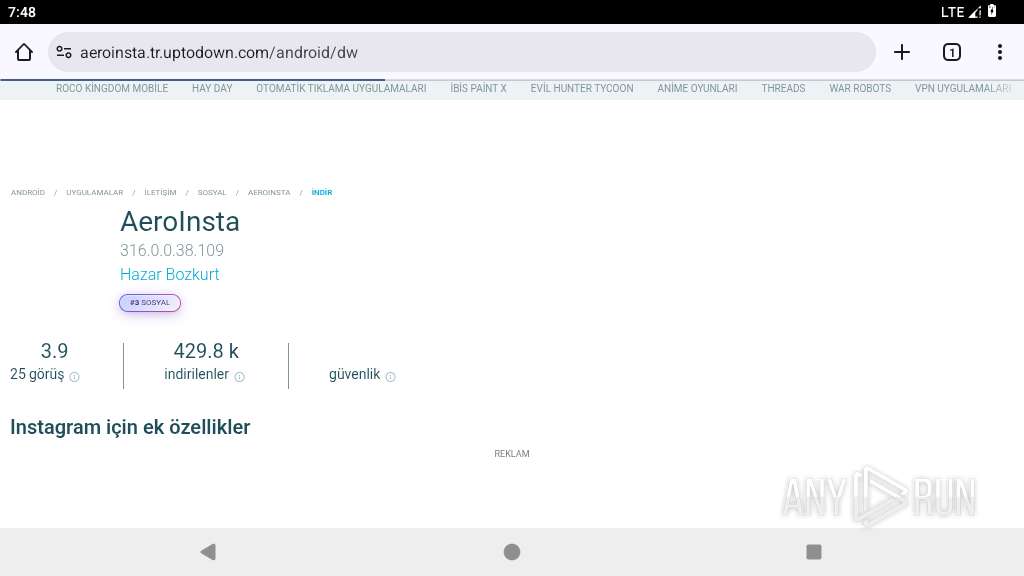
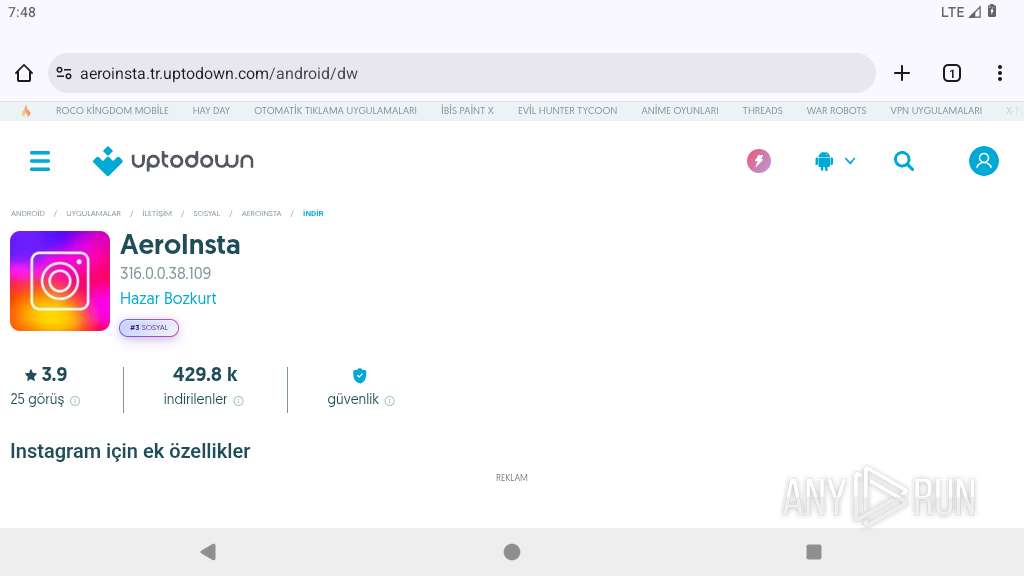
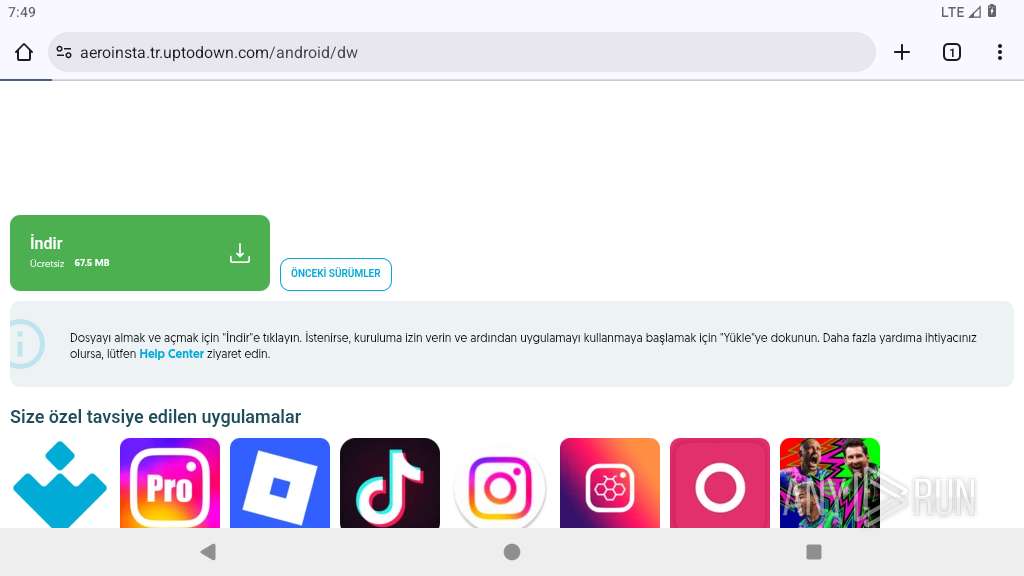
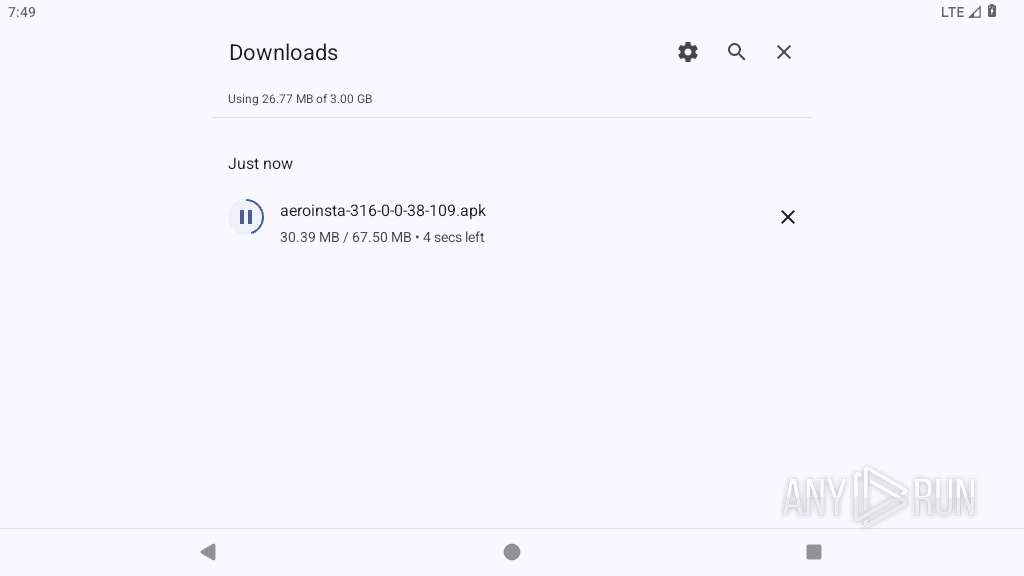
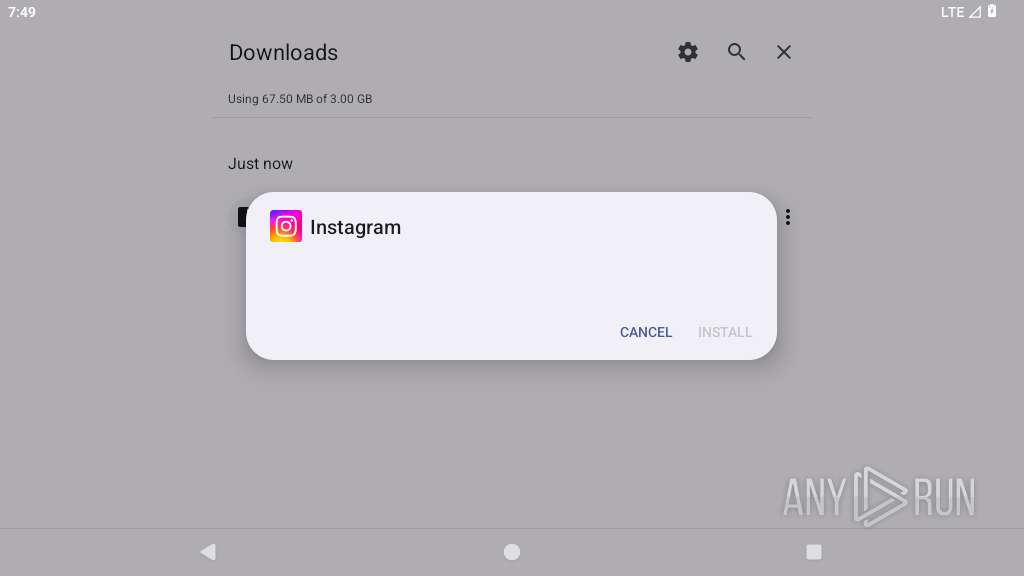
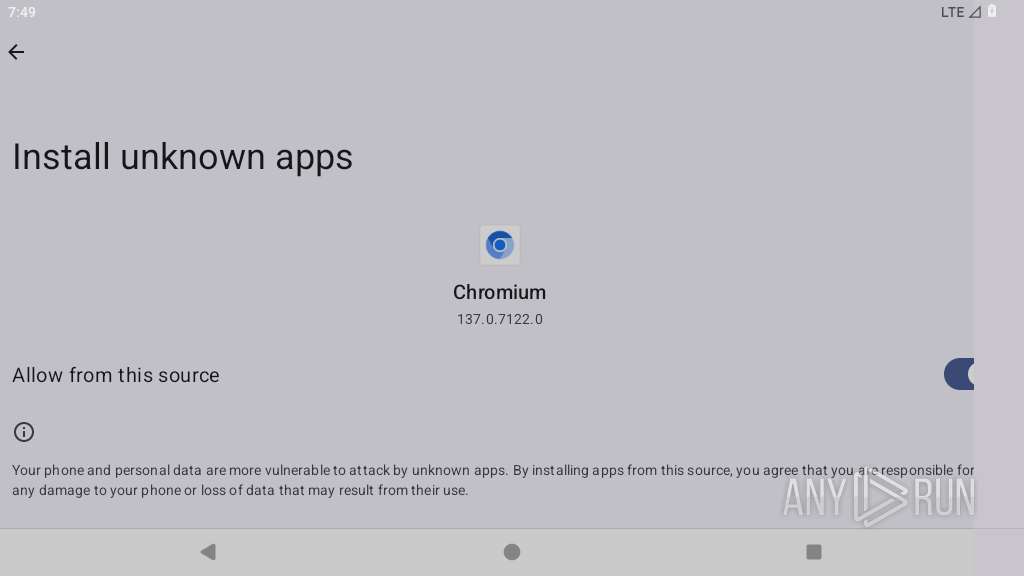
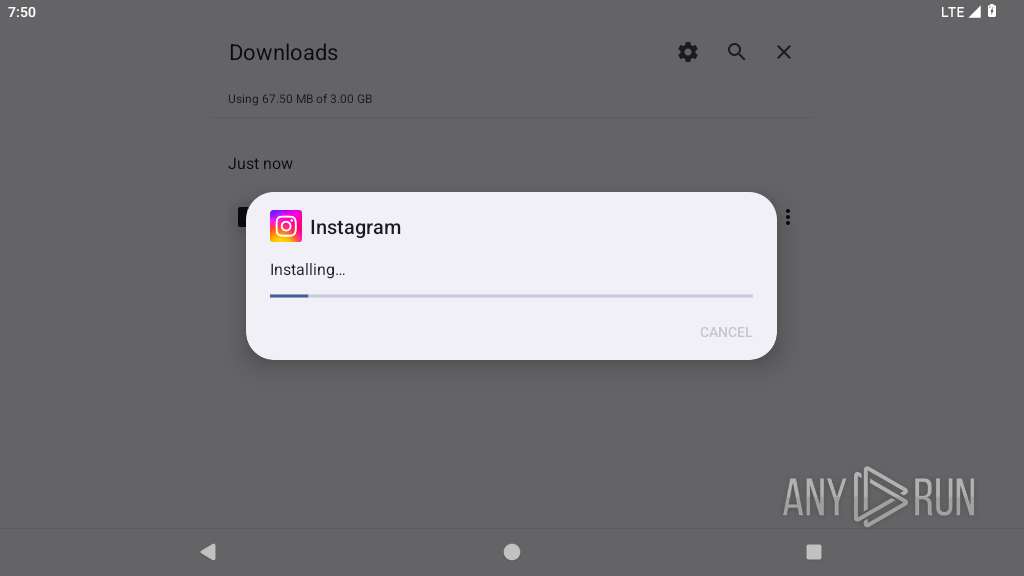
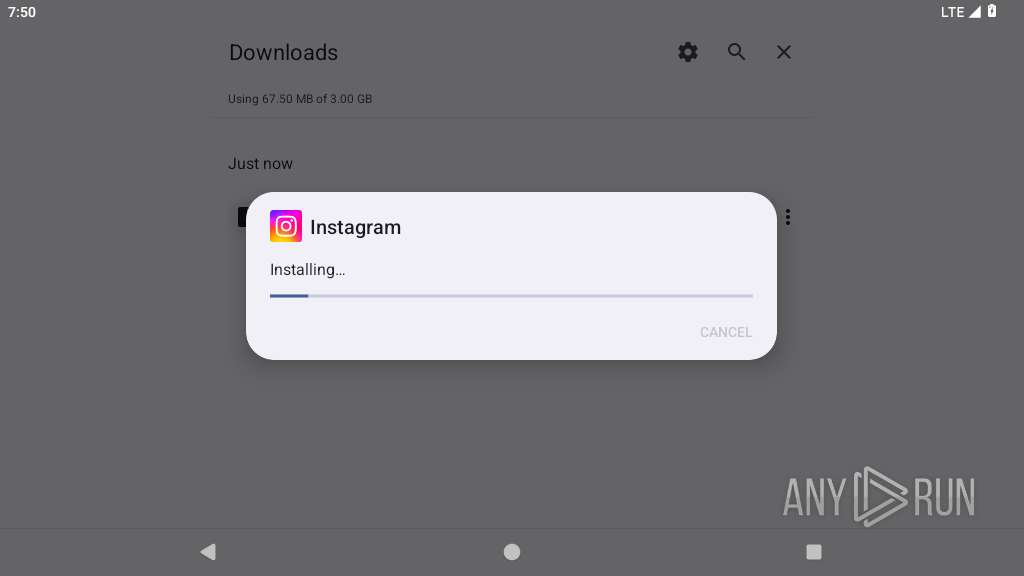
| URL: | https://aeroinsta.tr.uptodown.com/android/dw |
| Full analysis: | https://app.any.run/tasks/f510da7f-a4a0-40de-8b58-6301bb5688d8 |
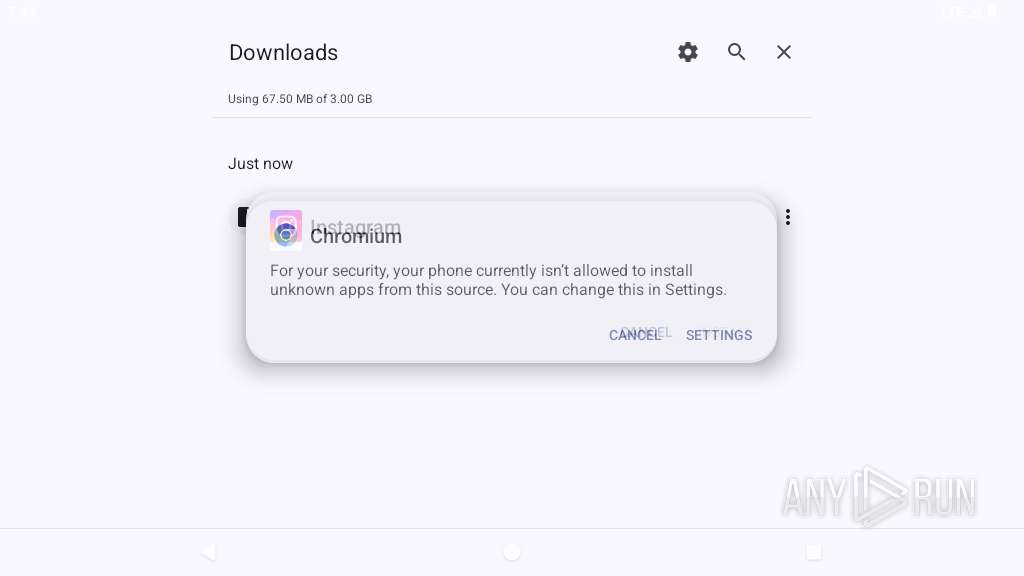
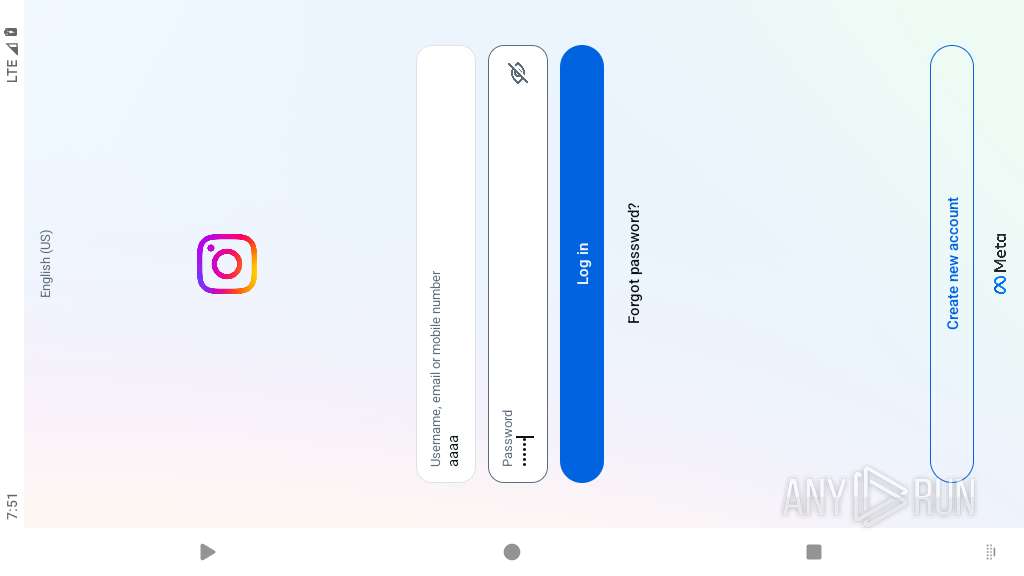
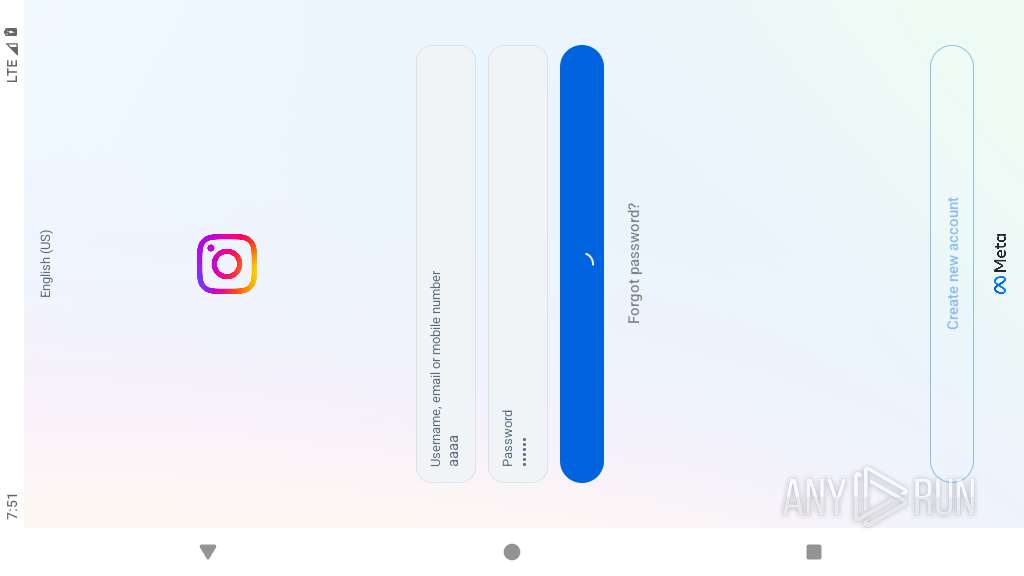
| Verdict: | Malicious activity |
| Analysis date: | April 05, 2026, 19:48:27 |
| OS: | Android 14 |
| Indicators: | |
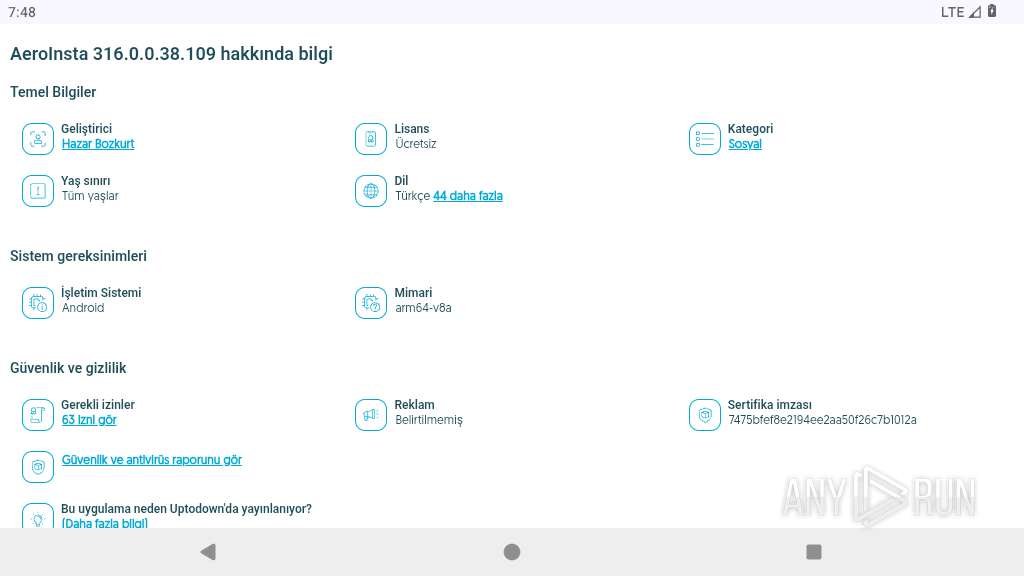
| MD5: | 522F08773B1F63E83A73606C19E69E00 |
| SHA1: | B649497AD41522712CE16B19974A863B3114DBCB |
| SHA256: | D99233EA9CDFB94A6903BE69DA09EFE8EC8D7965AEDFF5914E192195AB101101 |
| SSDEEP: | 3:N8OMXPbd3E1HBZn:2OI3ExBZ |
MALICIOUS
No malicious indicators.SUSPICIOUS
Retrieves a list of running application processes
- app_process64 (PID: 3452)
- app_process64 (PID: 3668)
Collects data about the device's environment (JVM version)
- app_process64 (PID: 3452)
- app_process64 (PID: 3668)
Accesses system-level resources
- app_process64 (PID: 3452)
Establishing a connection
- app_process64 (PID: 3452)
Retrieves Android OS build information
- app_process64 (PID: 3452)
Accesses external device storage files
- app_process64 (PID: 3452)
- app_process64 (PID: 3668)
Scans for popular installed apps
- app_process64 (PID: 3452)
- app_process64 (PID: 3668)
Retrieves the ISO country code of the current SIM card
- app_process64 (PID: 3452)
Accesses memory information
- app_process64 (PID: 3452)
Updates data in the storage of application settings (SharedPreferences)
- app_process64 (PID: 3452)
- app_process64 (PID: 3668)
Launches a new activity
- app_process64 (PID: 3452)
Returns the name of the current network operator
- app_process64 (PID: 3452)
- app_process64 (PID: 3668)
Starts a service
- app_process64 (PID: 3452)
Gets data of saved accounts
- app_process64 (PID: 3452)
INFO
Returns elapsed time since boot
- app_process64 (PID: 3452)
- app_process64 (PID: 3668)
Dynamically inspects or modifies classes, methods, and fields at runtime
- app_process64 (PID: 3452)
- app_process64 (PID: 3668)
Gets file name without full path
- app_process64 (PID: 3452)
- app_process64 (PID: 3668)
Loads a native library into the application
- app_process64 (PID: 3452)
- app_process64 (PID: 3668)
Retrieves data from storage of application settings (SharedPreferences)
- app_process64 (PID: 3452)
- app_process64 (PID: 3668)
Retrieves CPU core information
- app_process64 (PID: 3452)
Retrieves the value of a secure system setting
- app_process64 (PID: 3452)
- app_process64 (PID: 3668)
Verifies whether the device is connected to the internet
- app_process64 (PID: 3452)
- app_process64 (PID: 3668)
Detects device power status
- app_process64 (PID: 3452)
- app_process64 (PID: 3668)
Dynamically registers broadcast event listeners
- app_process64 (PID: 3452)
- app_process64 (PID: 3668)
Gets the display metrics associated with the device's screen
- app_process64 (PID: 3452)
- app_process64 (PID: 3668)
Listens for connection changes
- app_process64 (PID: 3452)
- app_process64 (PID: 3668)
Creates and writes local files
- app_process64 (PID: 3668)
Listens for changes in sensors
- app_process64 (PID: 3452)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
155
Monitored processes
30
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process |
|---|---|---|---|---|
| 2786 | org.chromium.chrome | /system/bin/app_process64 | app_process64 | |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 2844 | org.chromium.chrome_zygote | /system/bin/app_process64 | — | app_process64 |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 2868 | org.chromium.chrome_zygote | /system/bin/app_process64 | — | app_process64 |
User: u0_a72 Integrity Level: UNKNOWN Exit code: 0 | ||||
| 2885 | org.chromium.chrome:privileged_process0 | /system/bin/app_process64 | — | app_process64 |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 2904 | com.android.adservices.api | /system/bin/app_process64 | — | app_process64 |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 2968 | org.chromium.chrome_zygote | /system/bin/app_process64 | — | app_process64 |
User: u0_a72 Integrity Level: UNKNOWN Exit code: 9 | ||||
| 2989 | com.android.providers.partnerbookmarks | /system/bin/app_process64 | — | app_process64 |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 3060 | org.chromium.chrome_zygote | /system/bin/app_process64 | — | app_process64 |
User: u0_a72 Integrity Level: UNKNOWN Exit code: 0 | ||||
| 3087 | /system/bin/dmesgd | /system/bin/dmesgd | — | init |
User: dmesgd Integrity Level: UNKNOWN Exit code: 0 | ||||
| 3088 | dmesg | /system/bin/toybox | — | dmesgd |
User: dmesgd Integrity Level: UNKNOWN Exit code: 0 | ||||
Total events
0
Read events
0
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
430
Text files
26
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3180 | app_process64 | /data/data/org.chromium.chrome/cache/.org.chromium.Chromium.Uj251c/list.pb | binary | |
MD5:— | SHA256:— | |||
| 3180 | app_process64 | /data/data/org.chromium.chrome/cache/.org.chromium.Chromium.Uj251c/manifest.json | text | |
MD5:— | SHA256:— | |||
| 3180 | app_process64 | /data/data/org.chromium.chrome/cache/.org.chromium.Chromium.Uj251c/LICENSE | text | |
MD5:— | SHA256:— | |||
| 3180 | app_process64 | /data/data/org.chromium.chrome/cache/.org.chromium.Chromium.Uj251c/_metadata/verified_contents.json | text | |
MD5:— | SHA256:— | |||
| 3180 | app_process64 | /data/data/org.chromium.chrome/app_chrome/component_crx_cache/cab4d1f0a6a2a1afecae808a520f6690dd2b9d58bf54762877f2dc9715d55461 | binary | |
MD5:— | SHA256:— | |||
| 3199 | app_process64 | /data/data/org.chromium.chrome/cache/.org.chromium.Chromium.j1sBhX/privacy-sandbox-attestations.dat | binary | |
MD5:— | SHA256:— | |||
| 3199 | app_process64 | /data/data/org.chromium.chrome/cache/.org.chromium.Chromium.j1sBhX/manifest.json | text | |
MD5:— | SHA256:— | |||
| 3199 | app_process64 | /data/data/org.chromium.chrome/cache/.org.chromium.Chromium.j1sBhX/_metadata/verified_contents.json | text | |
MD5:— | SHA256:— | |||
| 3199 | app_process64 | /data/data/org.chromium.chrome/app_chrome/component_crx_cache/38c89b12bb20a8f2751c9c7cd2e31c173a47af08c115e1ecccc2f5151a2cf2c6 | binary | |
MD5:— | SHA256:— | |||
| 3218 | app_process64 | /data/data/org.chromium.chrome/cache/.org.chromium.Chromium.tUVy4X/decoded_xz | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
109
TCP/UDP connections
90
DNS requests
92
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2786 | app_process64 | GET | 200 | 151.101.195.52:443 | https://aeroinsta.tr.uptodown.com/android/dw | US | html | 142 Kb | unknown |
2786 | app_process64 | GET | 200 | 142.251.36.110:80 | http://clients2.google.com/time/1/current?cup2key=9:DOfRElODUK7fH_w0sNwLBVQb38N8TiYmevLk5OYXeCw&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | US | text | 107 b | whitelisted |
2786 | app_process64 | GET | 200 | 151.101.195.52:443 | https://img.utdstc.com/icon/4f0/532/4f053275616b7dcc22af6231bbe27135989343f4366caa515c87d8d2e4675b13:100 | US | image | 6.38 Kb | unknown |
2786 | app_process64 | GET | 200 | 216.58.206.72:443 | https://www.googletagmanager.com/gtag/js?id=G-DW5XRK7GYT | US | text | 473 Kb | whitelisted |
2786 | app_process64 | GET | 200 | 142.251.141.142:443 | https://fundingchoicesmessages.google.com/i/pub-0337387298854186?ers=1 | US | text | 217 Kb | whitelisted |
2786 | app_process64 | GET | 200 | 142.251.141.142:443 | https://fundingchoicesmessages.google.com/f/AGSKWxXosSA0sn8QV0luAjbXXZsvfA-kwJrjWdkK9szv1e0UWP6P0cU8oFIu6-I_n0cBA4abY9M_u7xcs8fM6aydlF-ajliqG1xolQ9-4g4SNZlY1t56GFAGHirQ_n8gnKd4TEy2XgPIhg==?fccs=W251bGwsbnVsbCxudWxsLG51bGwsbnVsbCxudWxsLFsxNzc1NDE4NTE3LDY3ODAwMDAwMF0sbnVsbCxudWxsLG51bGwsW251bGwsWzddXSwiaHR0cHM6Ly9hZXJvaW5zdGEudHIudXB0b2Rvd24uY29tL2FuZHJvaWQvZHciLG51bGwsW1s4LCI5Y2JGaDB1czlOYyJdLFs5LCJlbi1VUyJdLFsxNiwiWzAsMCwwXSJdLFszNSwiMTc3NTQxODUxNyJdLFsxOSwiMiJdLFsxNywiWzBdIl0sWzI0LCIiXSxbMjksImZhbHNlIl1dXQ | US | text | 2.60 Kb | whitelisted |
2786 | app_process64 | GET | 200 | 151.101.3.52:443 | https://stc.utdstc.com/img/svgs/icon-12-hotlink.svg | US | image | 902 b | unknown |
2786 | app_process64 | GET | 200 | 151.101.3.52:443 | https://stc.utdstc.com/img/svgs/icon-24-turbo2.svg | US | image | 992 b | unknown |
2786 | app_process64 | GET | 200 | 151.101.3.52:443 | https://stc.utdstc.com/img/svgs/logo-uptodown.svg | US | image | 3.51 Kb | unknown |
2786 | app_process64 | GET | 200 | 151.101.195.52:443 | https://www.uptodown.com/cookie-pixel.gif | US | image | 35 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
443 | mdnsd | 224.0.0.251:5353 | — | — | — | whitelisted |
— | — | 142.251.155.119:80 | www.google.com | GOOGLE | US | whitelisted |
— | — | 142.251.157.119:443 | www.google.com | GOOGLE | US | whitelisted |
— | — | 142.251.127.94:80 | connectivitycheck.gstatic.com | GOOGLE | US | whitelisted |
2786 | app_process64 | 142.251.36.110:80 | clients2.google.com | GOOGLE | US | whitelisted |
2786 | app_process64 | 151.101.195.52:443 | aeroinsta.tr.uptodown.com | FASTLY | US | whitelisted |
2786 | app_process64 | 142.251.154.119:443 | www.google.com | GOOGLE | US | whitelisted |
2786 | app_process64 | 142.251.127.84:443 | accounts.google.com | GOOGLE | US | whitelisted |
2786 | app_process64 | 95.85.19.25:443 | geo.cookie-script.com | DIGITALOCEAN-ASN | US | whitelisted |
2786 | app_process64 | 104.26.5.120:443 | scripts.ssm.codes | CLOUDFLARENET | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
clients2.google.com |
| whitelisted |
aeroinsta.tr.uptodown.com |
| unknown |
www.google.com |
| whitelisted |
accounts.google.com |
| whitelisted |
stc.utdstc.com |
| whitelisted |
img.utdstc.com |
| whitelisted |
geo.cookie-script.com |
| whitelisted |
fundingchoicesmessages.google.com |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2786 | app_process64 | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
2786 | app_process64 | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
822 | app_process64 | Misc activity | ET INFO Android Device Connectivity Check |
339 | netd | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |