| File name: | CAMSCANNER-1805.2023.exe |
| Full analysis: | https://app.any.run/tasks/d3832542-f5e9-42f7-a4f6-0feb20eb35bc |
| Verdict: | Malicious activity |
| Analysis date: | May 19, 2023, 09:35:45 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 64 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32+ executable (GUI) x86-64 Mono/.Net assembly, for MS Windows |
| MD5: | 3B65E95F9A43B837254CA66788EB0BC3 |
| SHA1: | C0FEF342D4398CB7656C4723E7E4F88341AA3996 |
| SHA256: | D9811E872A9CA7C1677B003630980C86079DA627723497363920E7870D103246 |
| SSDEEP: | 12288:Pe2EyN+Mm/A5uWjTdnWY8Xw3R7aw5+V3E00KfLZvHrIKX2uc7htL9U8pVThyvdlw:PiWd/Lb+3B2McisHy759/yOwZoc |
MALICIOUS
Adds path to the Windows Defender exclusion list
- svchost.exe (PID: 2396)
SUSPICIOUS
Reads the BIOS version
- CAMSCANNER-1805.2023.exe (PID: 2616)
- svchost.exe (PID: 2396)
The process checks if it is being run in the virtual environment
- CAMSCANNER-1805.2023.exe (PID: 2616)
- svchost.exe (PID: 2396)
Starts CMD.EXE for commands execution
- CAMSCANNER-1805.2023.exe (PID: 2616)
Creates executable files that already exist in Windows
- CAMSCANNER-1805.2023.exe (PID: 2616)
The process creates files with name similar to system file names
- CAMSCANNER-1805.2023.exe (PID: 2616)
Executable content was dropped or overwritten
- CAMSCANNER-1805.2023.exe (PID: 2616)
Executing commands from a ".bat" file
- CAMSCANNER-1805.2023.exe (PID: 2616)
Uses TIMEOUT.EXE to delay execution
- cmd.exe (PID: 1164)
Reads the Internet Settings
- svchost.exe (PID: 2396)
- powershell.exe (PID: 1824)
Starts POWERSHELL.EXE for commands execution
- svchost.exe (PID: 2396)
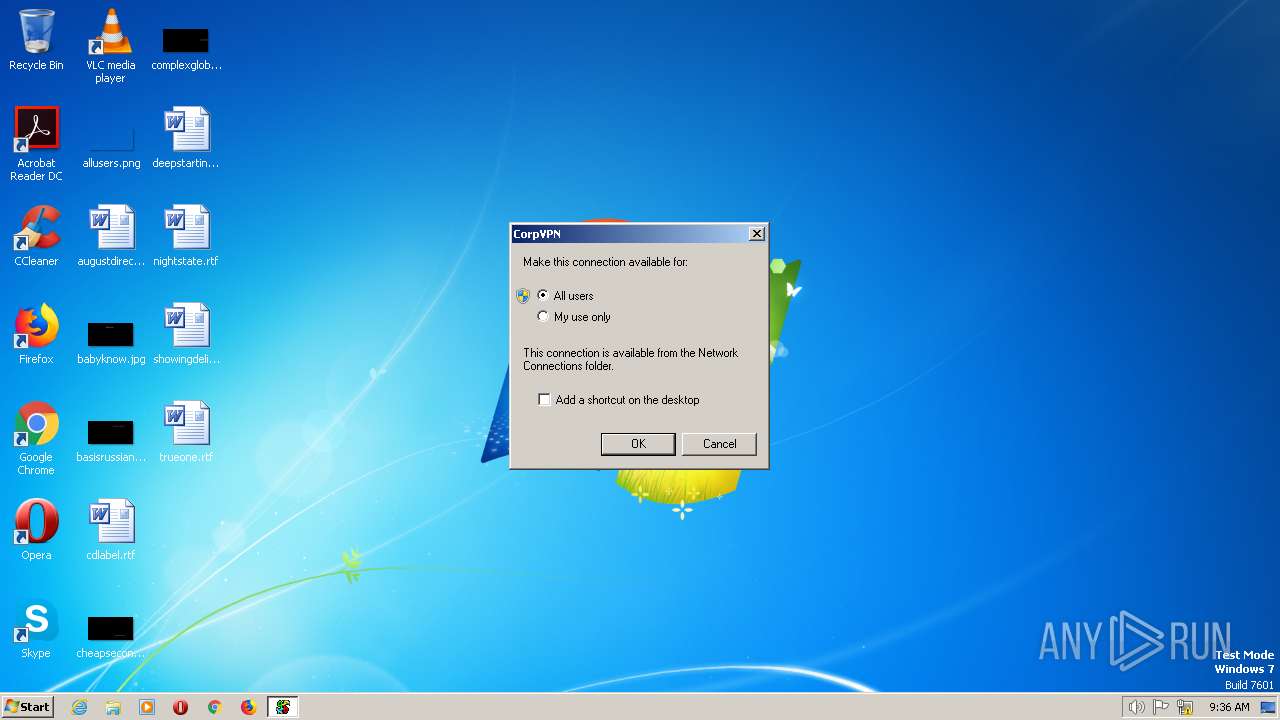
Probably UAC bypass using CMSTP.exe (Connection Manager service profile)
- svchost.exe (PID: 2396)
Script adds exclusion path to Windows Defender
- svchost.exe (PID: 2396)
INFO
The process checks LSA protection
- CAMSCANNER-1805.2023.exe (PID: 2616)
- svchost.exe (PID: 2396)
- cmstp.exe (PID: 2768)
- dllhost.exe (PID: 2016)
Reads the computer name
- CAMSCANNER-1805.2023.exe (PID: 2616)
- svchost.exe (PID: 2396)
- jsc.exe (PID: 2976)
Reads the machine GUID from the registry
- CAMSCANNER-1805.2023.exe (PID: 2616)
- svchost.exe (PID: 2396)
Checks supported languages
- CAMSCANNER-1805.2023.exe (PID: 2616)
- svchost.exe (PID: 2396)
- jsc.exe (PID: 2976)
Create files in a temporary directory
- CAMSCANNER-1805.2023.exe (PID: 2616)
- powershell.exe (PID: 1824)
Creates files or folders in the user directory
- CAMSCANNER-1805.2023.exe (PID: 2616)
The executable file from the user directory is run by the CMD process
- svchost.exe (PID: 2396)
Process checks computer location settings
- jsc.exe (PID: 2976)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic Win/DOS Executable (50) |
|---|---|---|
| .exe | | | DOS Executable Generic (49.9) |
EXIF
EXE
| AssemblyVersion: | 1.0.0.0 |
|---|---|
| ProductVersion: | 1.0.0.0 |
| ProductName: | WindowsFormsApplication2 |
| OriginalFileName: | WindowsFormsApplication2.exe |
| LegalTrademarks: | - |
| LegalCopyright: | Copyright © 2014 |
| InternalName: | WindowsFormsApplication2.exe |
| FileVersion: | 1.0.0.0 |
| FileDescription: | WindowsFormsApplication2 |
| CompanyName: | - |
| Comments: | - |
| CharacterSet: | Unicode |
| LanguageCode: | Neutral |
| FileSubtype: | - |
| ObjectFileType: | Executable application |
| FileOS: | Win32 |
| FileFlags: | (none) |
| FileFlagsMask: | 0x003f |
| ProductVersionNumber: | 1.0.0.0 |
| FileVersionNumber: | 1.0.0.0 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 4 |
| ImageVersion: | - |
| OSVersion: | 4 |
| EntryPoint: | 0x0000 |
| UninitializedDataSize: | - |
| InitializedDataSize: | 1574 |
| CodeSize: | 1243280 |
| LinkerVersion: | 48 |
| PEType: | PE32+ |
| ImageFileCharacteristics: | Executable, Large address aware |
| TimeStamp: | 2023:05:18 07:25:55+00:00 |
| MachineType: | AMD AMD64 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_AMD64 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 18-May-2023 07:25:55 |
| Comments: | - |
| CompanyName: | - |
| FileDescription: | WindowsFormsApplication2 |
| FileVersion: | 1.0.0.0 |
| InternalName: | WindowsFormsApplication2.exe |
| LegalCopyright: | Copyright © 2014 |
| LegalTrademarks: | - |
| OriginalFilename: | WindowsFormsApplication2.exe |
| ProductName: | WindowsFormsApplication2 |
| ProductVersion: | 1.0.0.0 |
| Assembly Version: | 1.0.0.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_AMD64 |
| Number of sections: | 2 |
| Time date stamp: | 18-May-2023 07:25:55 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00F0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00002000 | 0x0012F890 | 0x0012FA00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 4.08801 |
.rsrc | 0x00132000 | 0x00000626 | 0x00000800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 3.47309 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.00112 | 490 | UNKNOWN | UNKNOWN | RT_MANIFEST |
Total processes
52
Monitored processes
17
Malicious processes
3
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1164 | C:\Windows\system32\cmd.exe /c ""C:\Users\admin\AppData\Local\Temp\tmp3ACE.tmp.bat"" | C:\Windows\System32\cmd.exe | — | CAMSCANNER-1805.2023.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1824 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" Add-MpPreference -ExclusionPath "C:\Users\admin\AppData\Roaming\svchost.exe" -Force | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
| 2016 | C:\Windows\system32\DllHost.exe /Processid:{3E5FC7F9-9A51-4367-9063-A120244FBEC7} | C:\Windows\System32\dllhost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2256 | timeout 3 | C:\Windows\System32\timeout.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: timeout - pauses command processing Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2396 | "C:\Users\admin\AppData\Roaming\svchost.exe" | C:\Users\admin\AppData\Roaming\svchost.exe | — | cmd.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: WindowsFormsApplication2 Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 2452 | "C:\Windows\Microsoft.NET\Framework64\v4.0.30319\aspnet_wp.exe" | C:\Windows\Microsoft.NET\Framework64\v4.0.30319\aspnet_wp.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: aspnet_wp.exe Exit code: 4294967295 Version: 4.7.2558.0 built by: NET471REL1 Modules
| |||||||||||||||
| 2508 | "C:\Windows\Microsoft.NET\Framework64\v4.0.30319\RegAsm.exe" | C:\Windows\Microsoft.NET\Framework64\v4.0.30319\RegAsm.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft .NET Assembly Registration Utility Exit code: 4294967295 Version: 4.7.2558.0 built by: NET471REL1 Modules
| |||||||||||||||
| 2552 | "C:\Windows\Microsoft.NET\Framework64\v4.0.30319\aspnet_compiler.exe" | C:\Windows\Microsoft.NET\Framework64\v4.0.30319\aspnet_compiler.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: aspnet_compiler.exe Exit code: 4294967295 Version: 4.7.2558.0 built by: NET471REL1 Modules
| |||||||||||||||
| 2616 | "C:\Users\admin\AppData\Local\Temp\CAMSCANNER-1805.2023.exe" | C:\Users\admin\AppData\Local\Temp\CAMSCANNER-1805.2023.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: WindowsFormsApplication2 Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 2640 | "C:\Windows\Microsoft.NET\Framework64\v4.0.30319\ServiceModelReg.exe" | C:\Windows\Microsoft.NET\Framework64\v4.0.30319\ServiceModelReg.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: WCF Generic Command for Vista Setup Exit code: 4294967295 Version: 4.7.2558.0 built by: NET471REL1 Modules
| |||||||||||||||
Total events
1 943
Read events
1 913
Write events
30
Delete events
0
Modification events
| (PID) Process: | (2396) svchost.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2396) svchost.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2396) svchost.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (2396) svchost.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (1824) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (1824) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (1824) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (1824) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (1824) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\14C\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
Executable files
2
Suspicious files
3
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1824 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:446DD1CF97EABA21CF14D03AEBC79F27 | SHA256:A7DE5177C68A64BD48B36D49E2853799F4EBCFA8E4761F7CC472F333DC5F65CF | |||
| 1824 | powershell.exe | C:\Users\admin\AppData\Local\Temp\boctciih.lyy.ps1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 1824 | powershell.exe | C:\Users\admin\AppData\Local\Temp\isdsd5pp.y2d.psm1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 2396 | svchost.exe | C:\windows\temp\po45zz5t.inf | text | |
MD5:91FF0F895DCD1B50DFD03DAF52121C4E | SHA256:7719987FFDA436D9A0D354E237FC7B6B52F559FD945C718859850E8F2E705C4C | |||
| 2616 | CAMSCANNER-1805.2023.exe | C:\Users\admin\AppData\Local\Temp\tmp3ACE.tmp.bat | text | |
MD5:ABC0C975E4E1E74BDCFECD4292B08796 | SHA256:CB5273D1D6CA7ED7F9E642C934406569D88B7C774691FB2AF0133B30A5959F8C | |||
| 2616 | CAMSCANNER-1805.2023.exe | C:\Users\admin\AppData\Roaming\svchost.exe | executable | |
MD5:3B65E95F9A43B837254CA66788EB0BC3 | SHA256:D9811E872A9CA7C1677B003630980C86079DA627723497363920E7870D103246 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
4
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
328 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |