| File name: | geek.exe |
| Full analysis: | https://app.any.run/tasks/03832376-3b75-461d-92bb-470daf6e010b |
| Verdict: | Malicious activity |
| Analysis date: | January 29, 2024, 06:32:05 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | EF78997488E6121971404A3F25686FEE |
| SHA1: | 53A260990106E5271CB525F87BE008E299BEAA85 |
| SHA256: | D96DF1051E62AA40BAEFD51235BE45F8038745582A5D3428B63123FD2CED60DB |
| SSDEEP: | 98304:2AArUCQYWwxKVsAQK9BY1g7NYQzEsXLQdcAXSvEnf7J6PGyTVQgRcEzUWyW+91d2:FB |
MALICIOUS
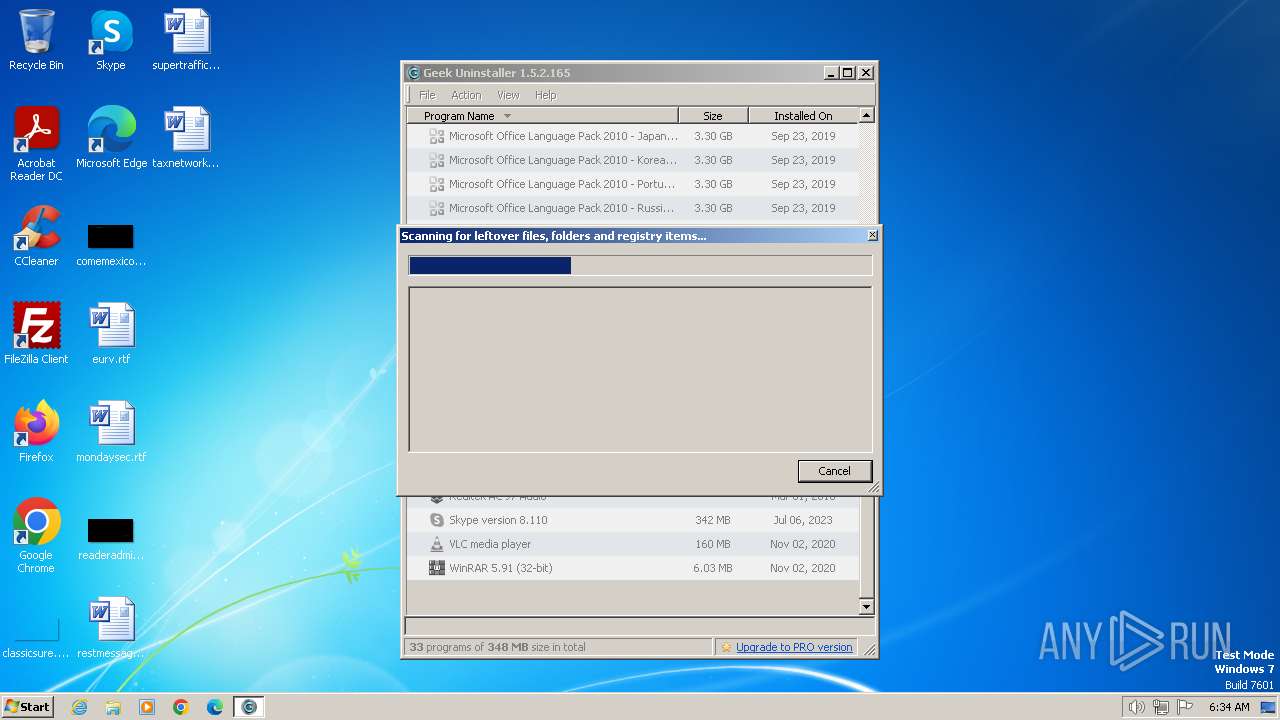
Drops the executable file immediately after the start
- geek.exe (PID: 2484)
- vcredist_x86.exe (PID: 3816)
- vcredist_x86.exe (PID: 3728)
Actions looks like stealing of personal data
- geek.exe (PID: 2484)
SUSPICIOUS
Reads the Internet Settings
- geek.exe (PID: 2484)
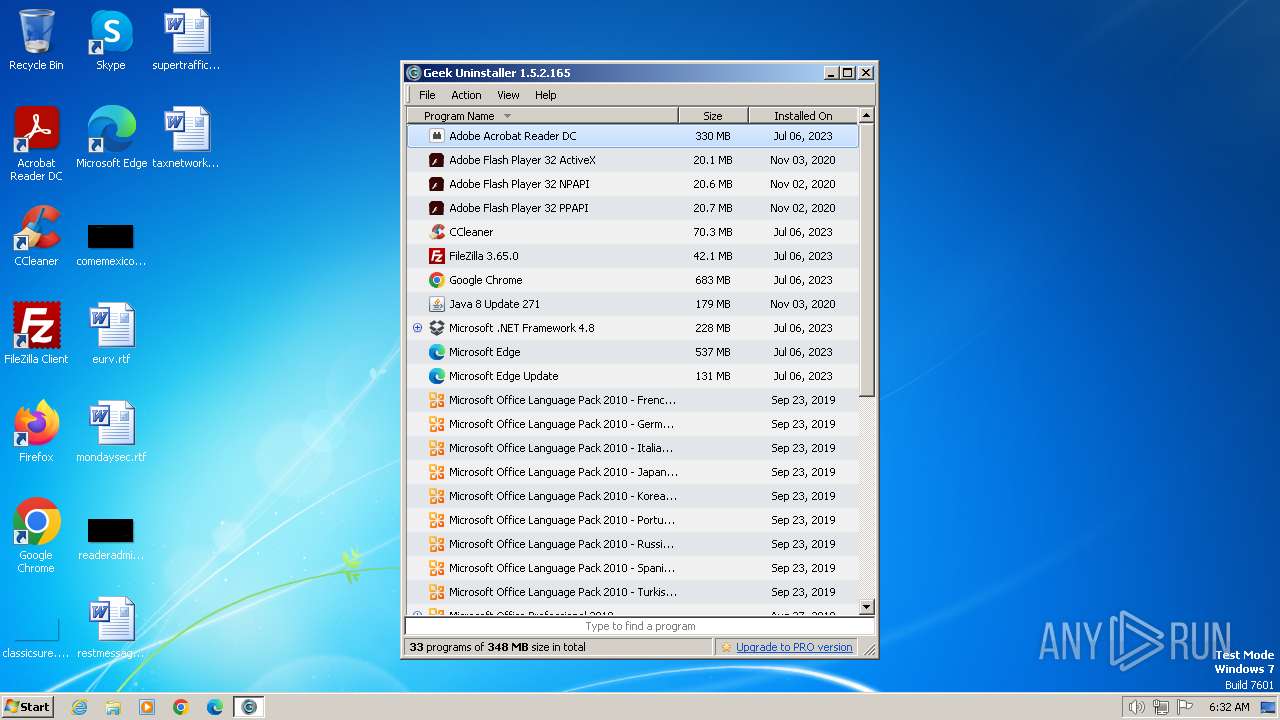
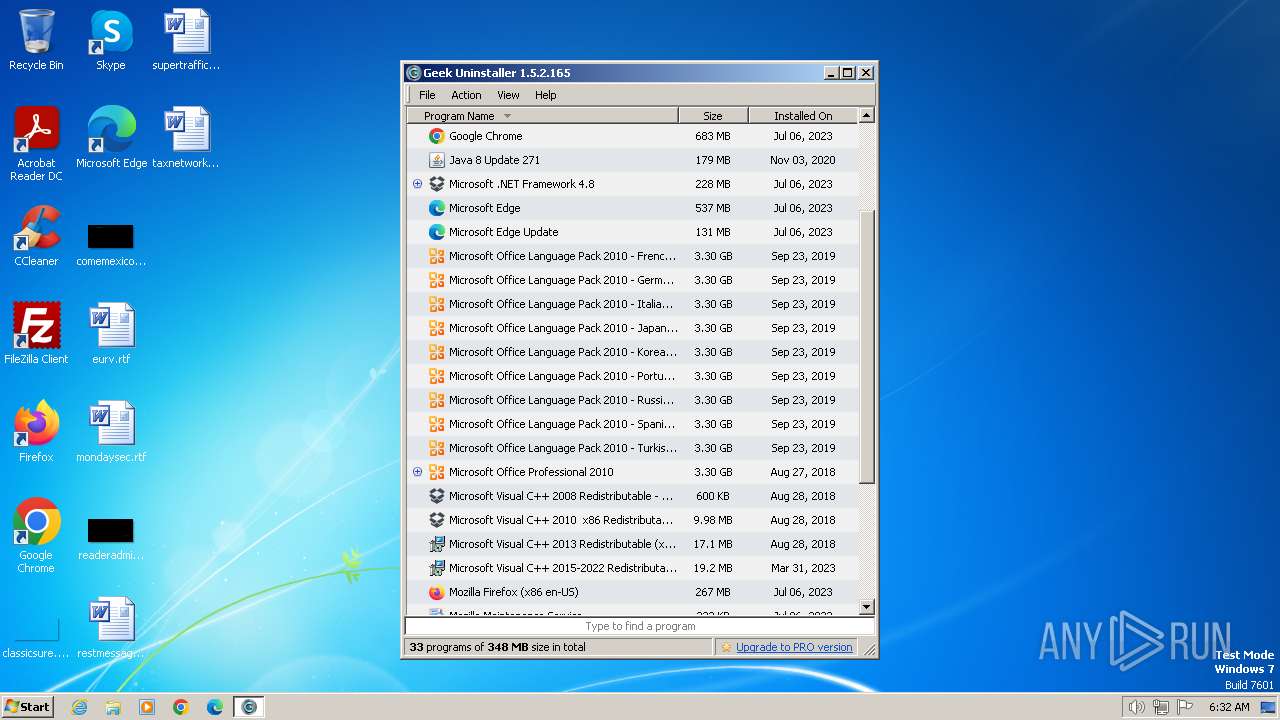
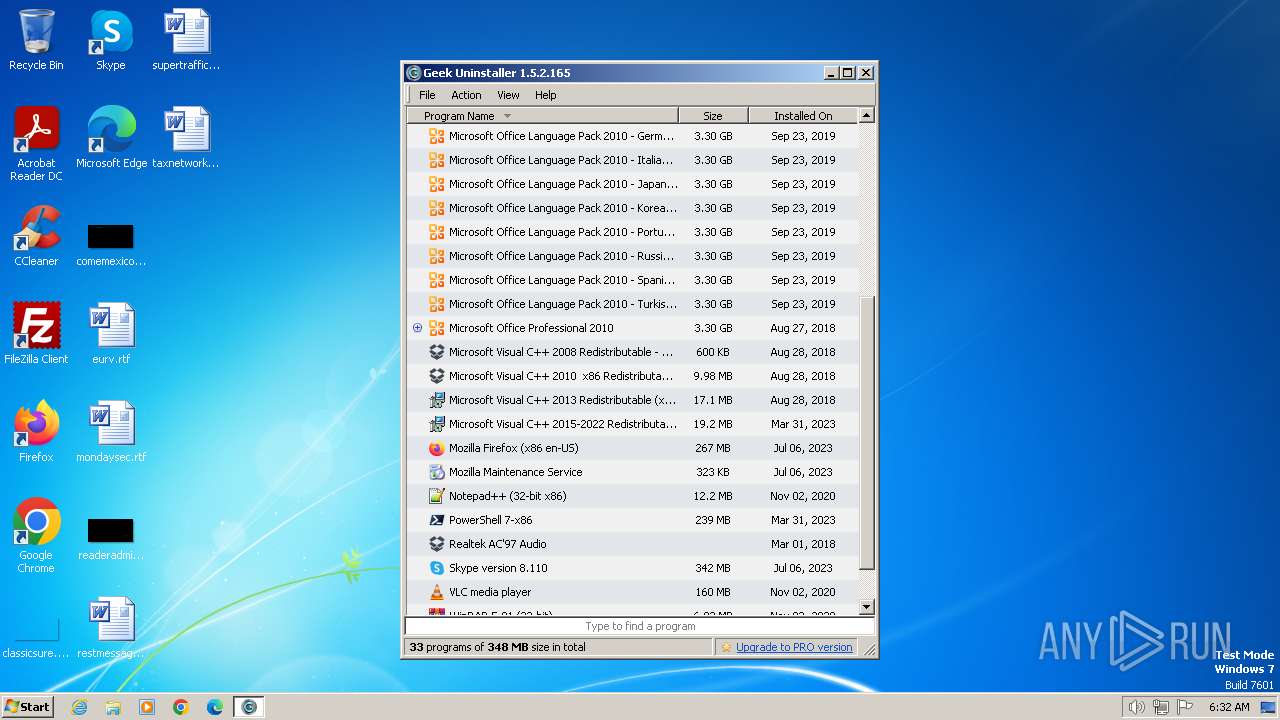
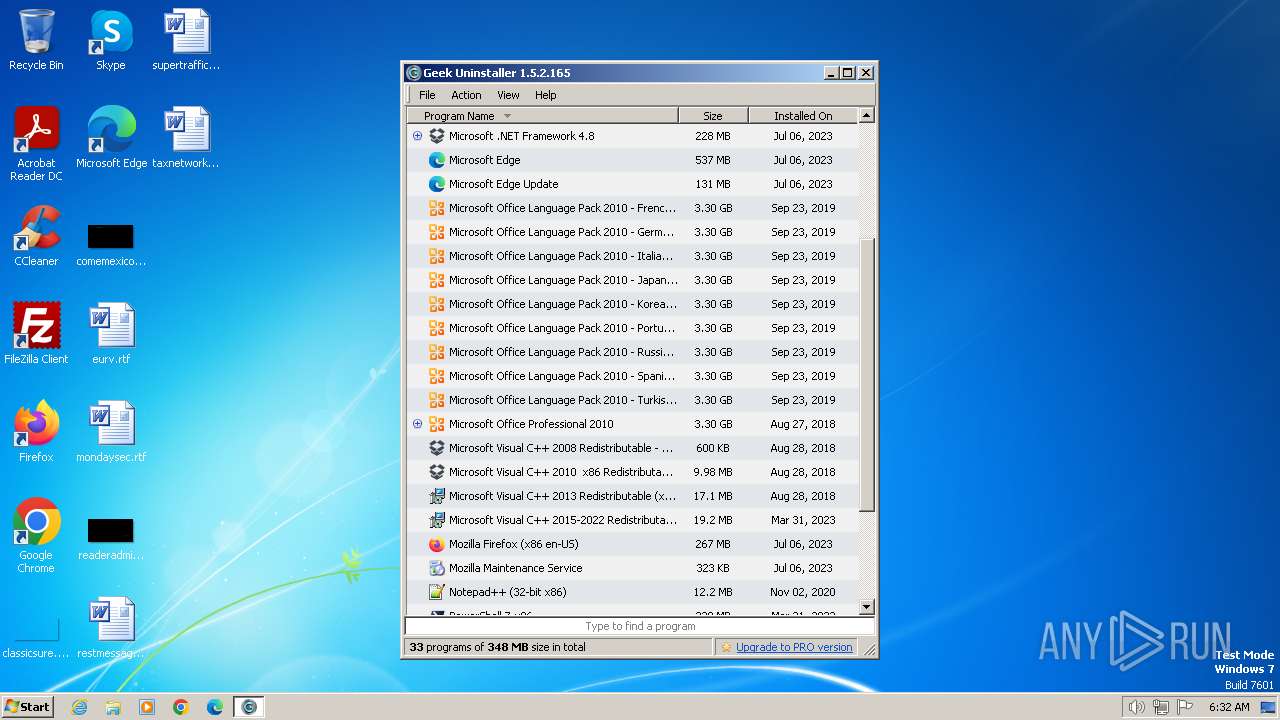
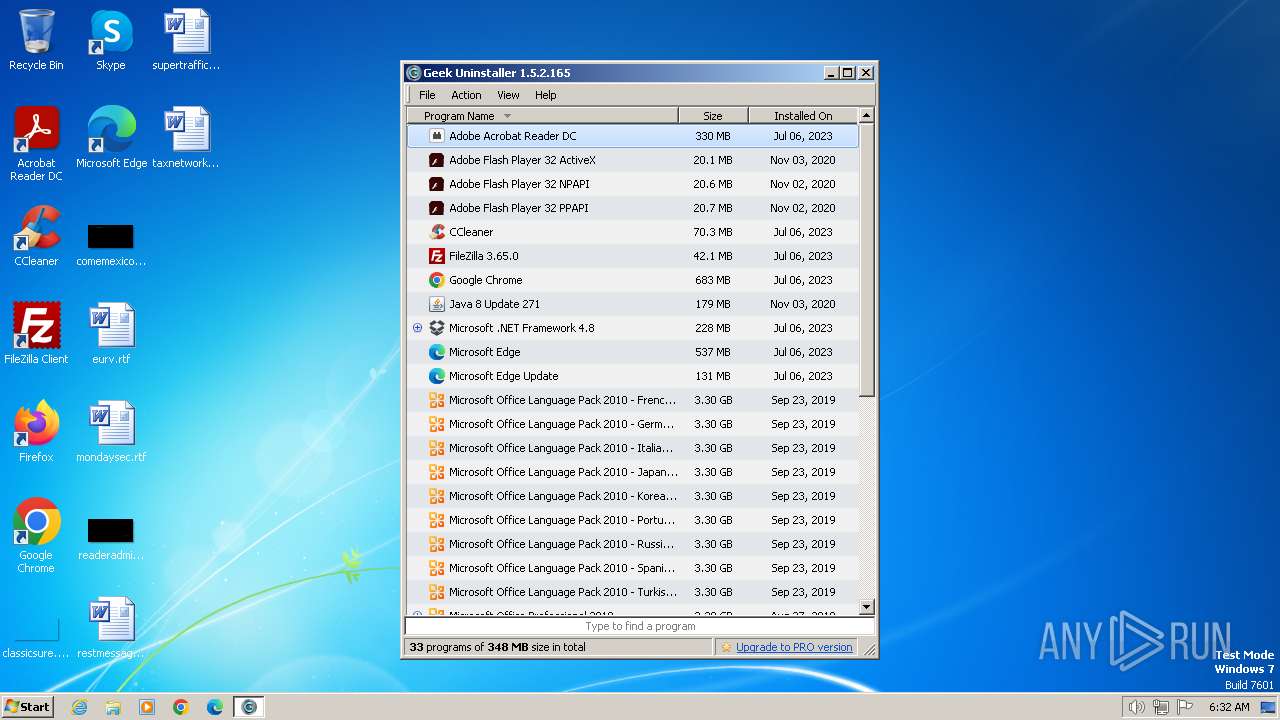
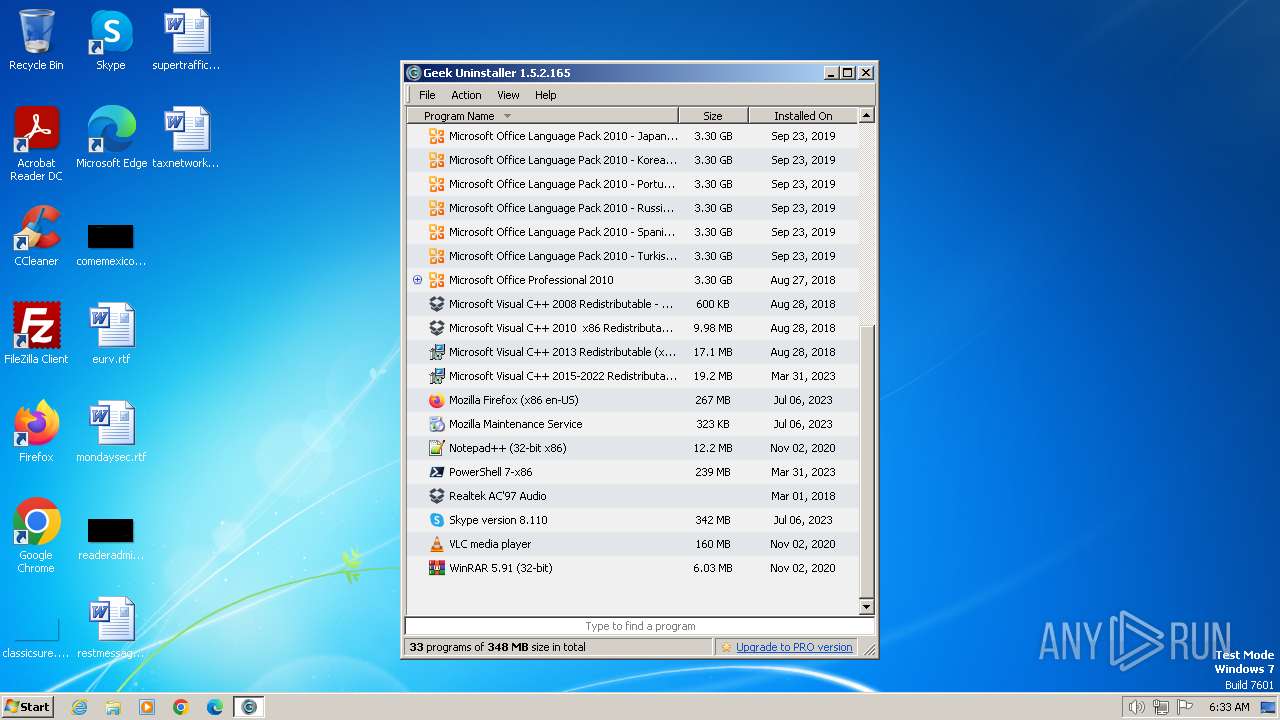
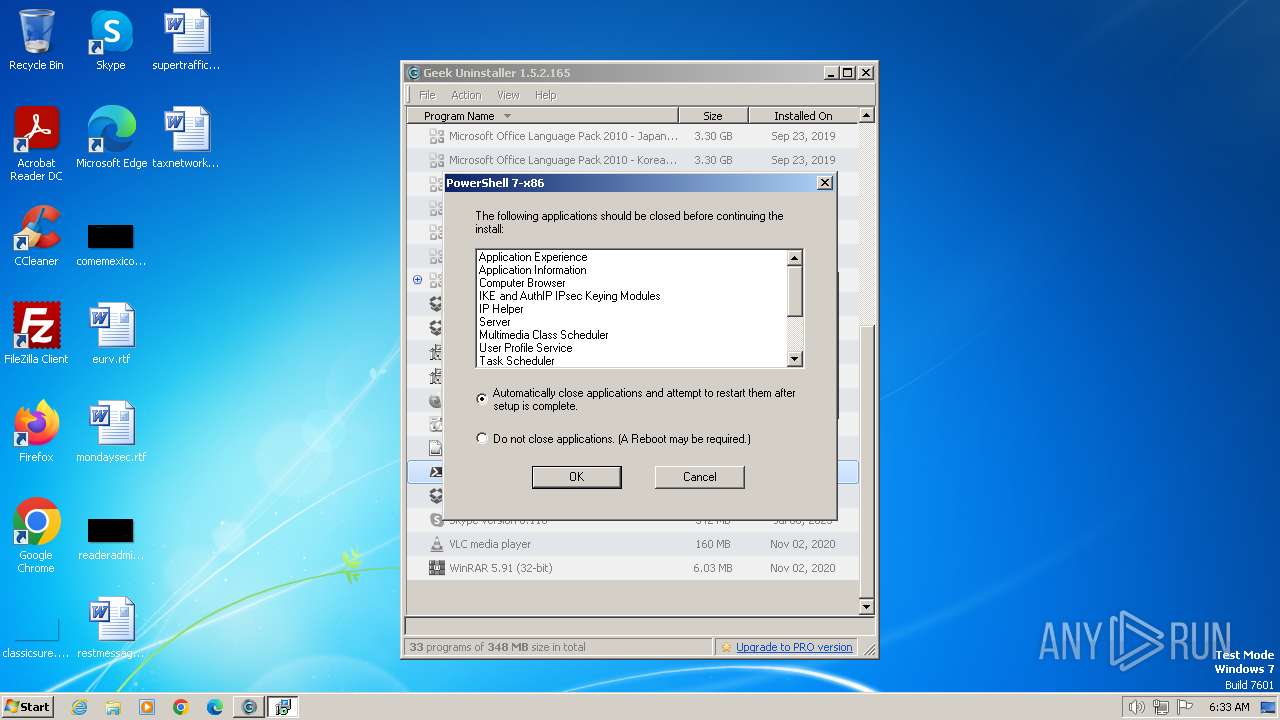
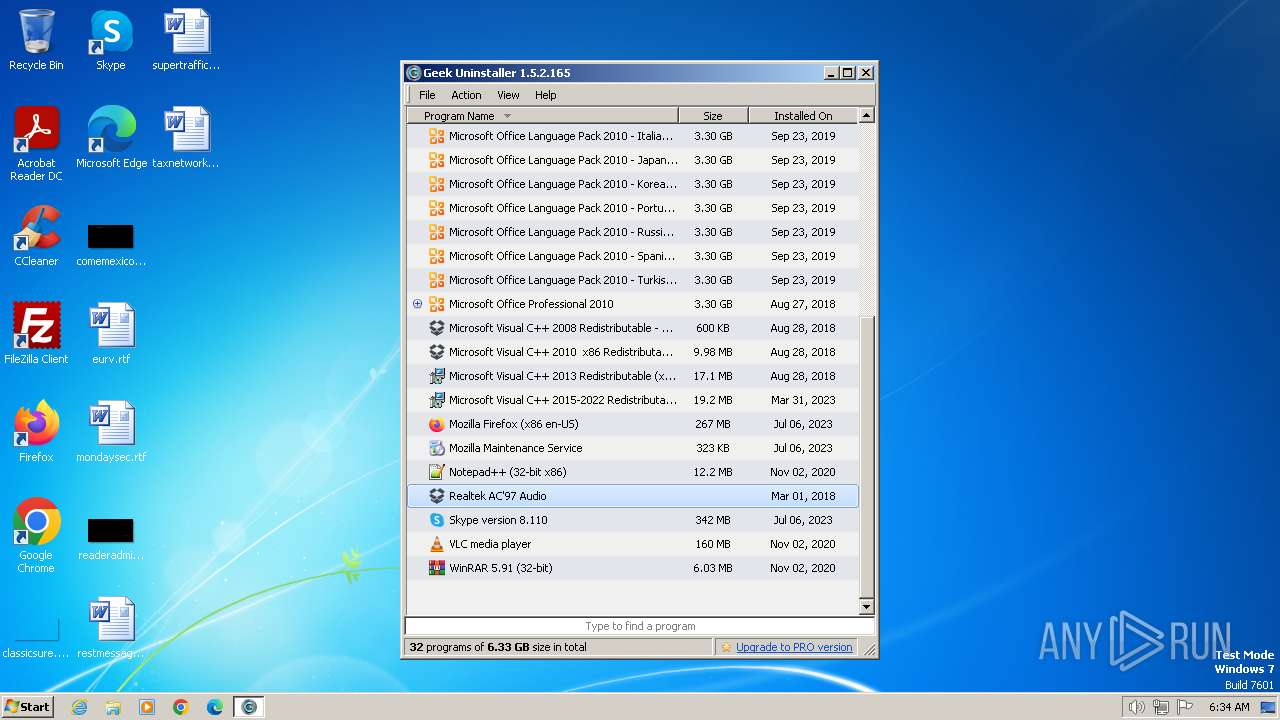
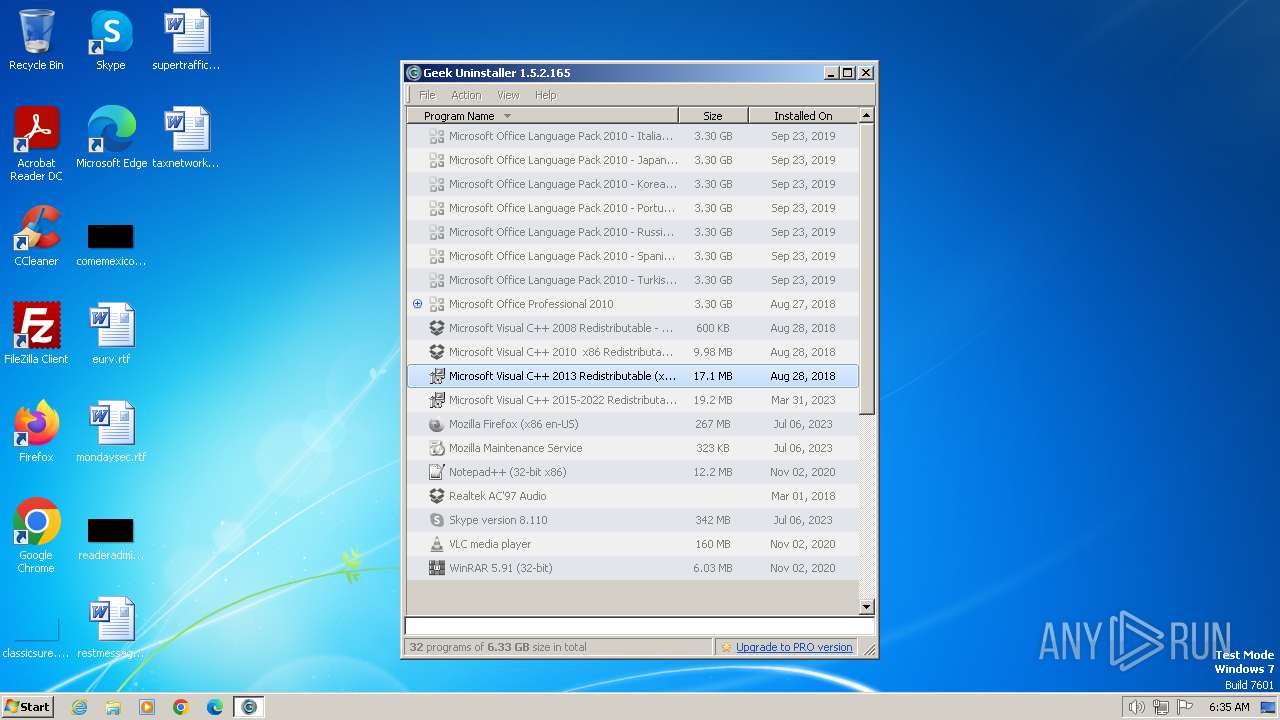
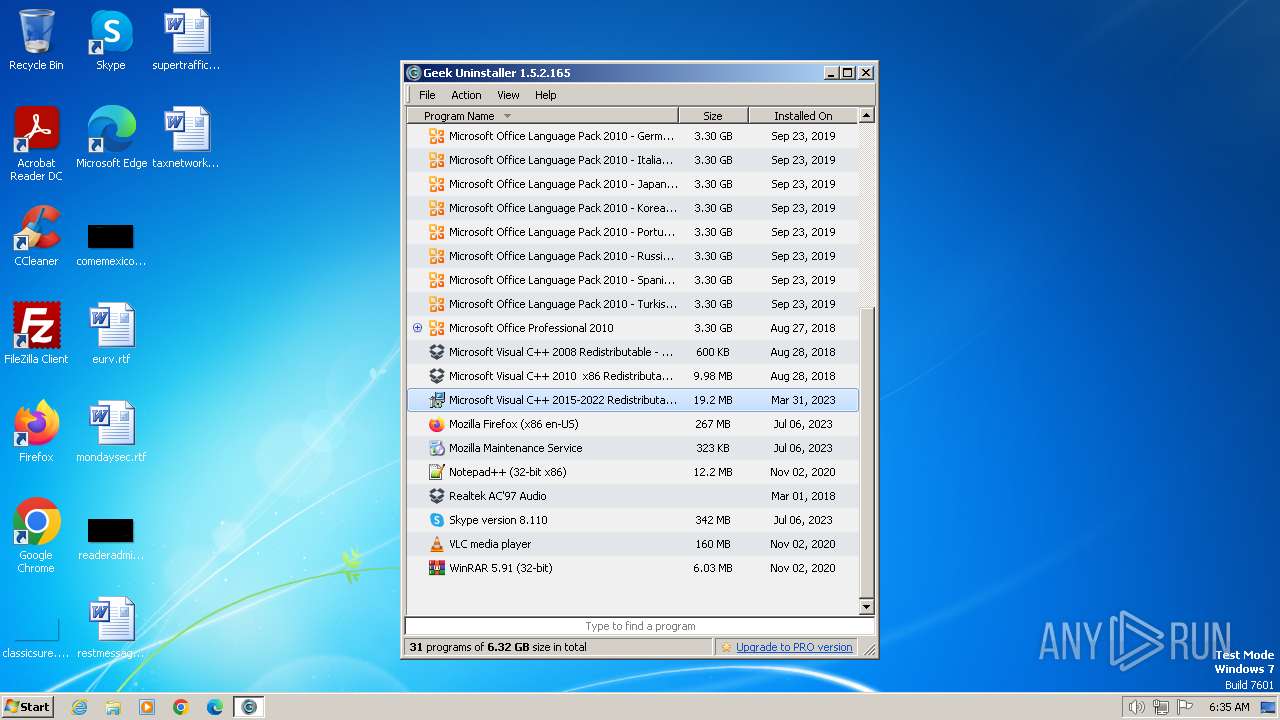
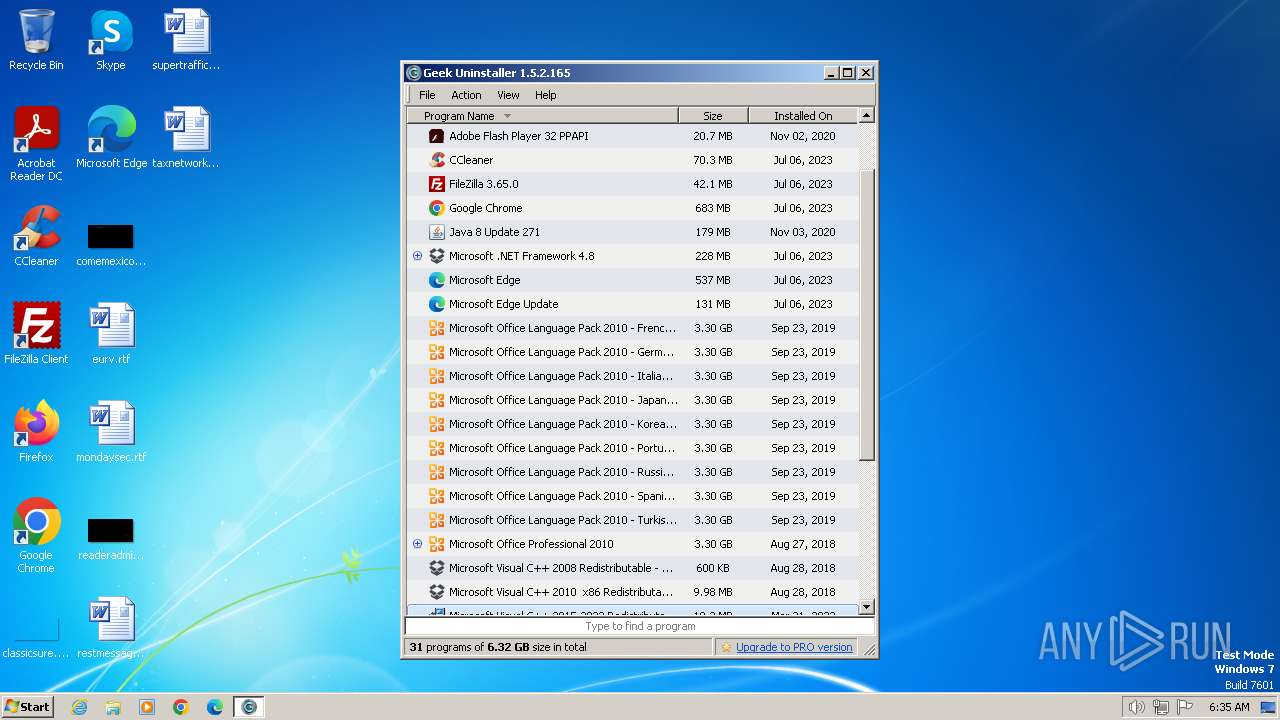
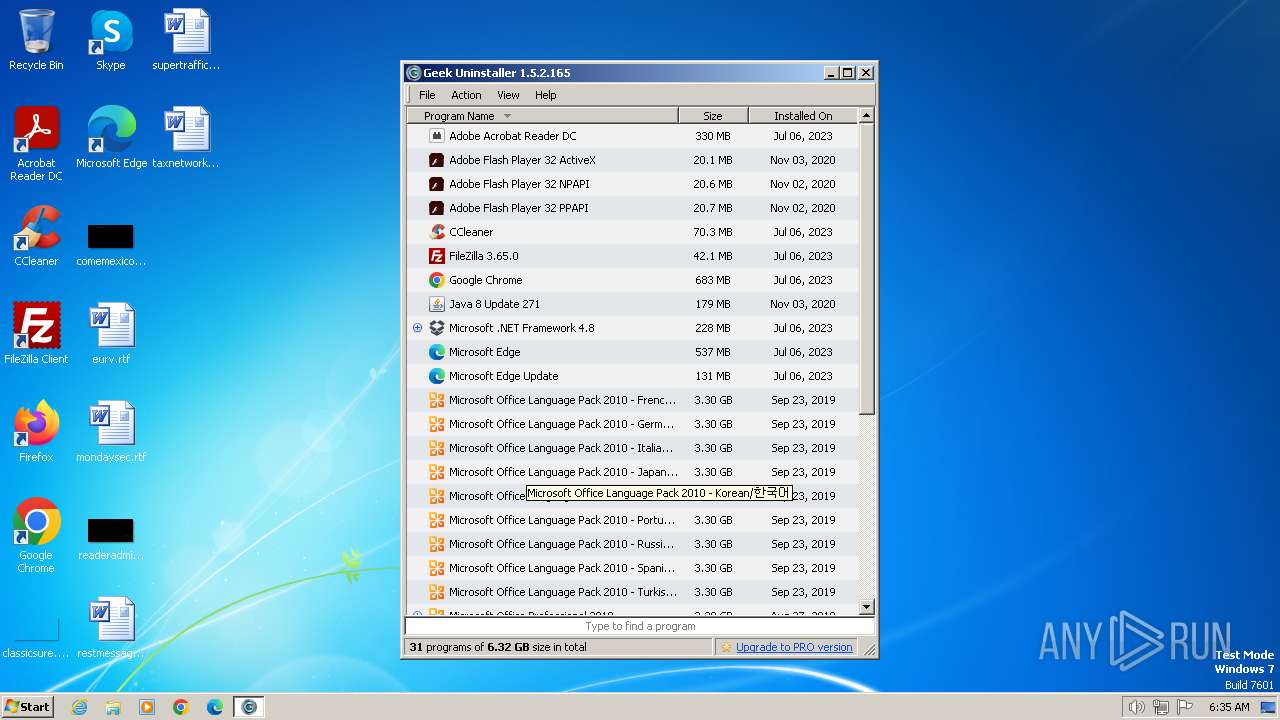
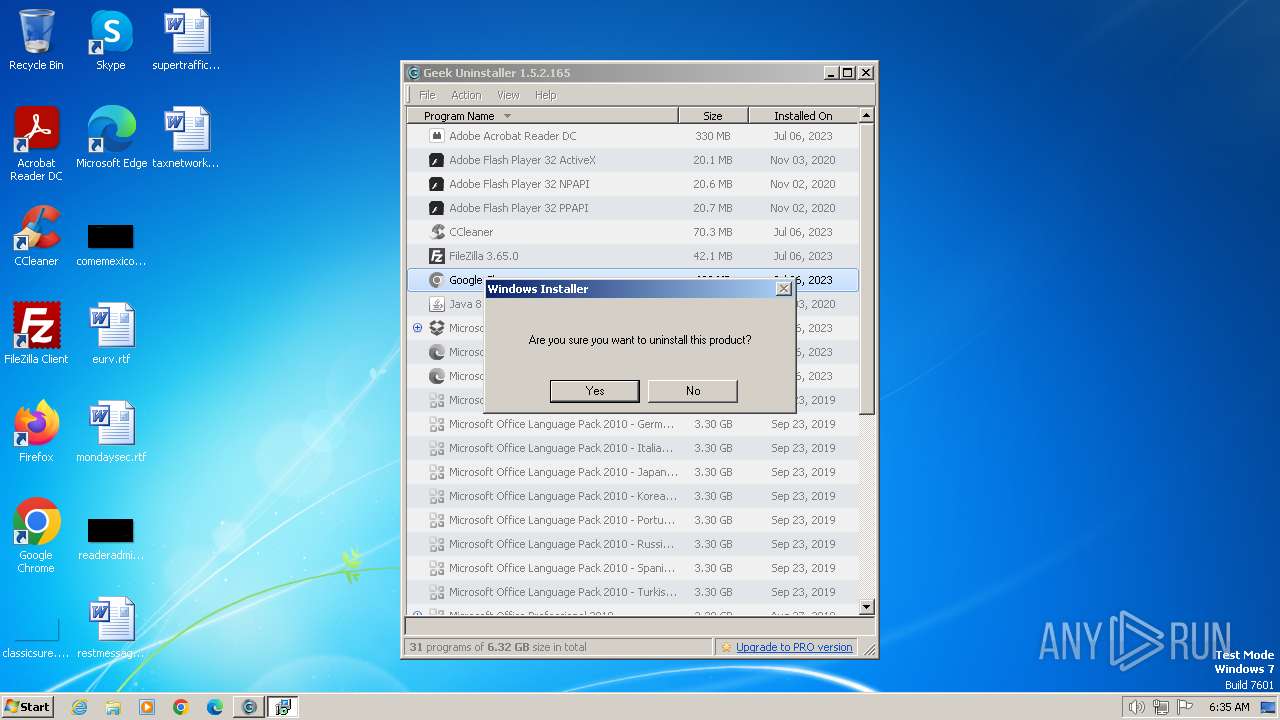
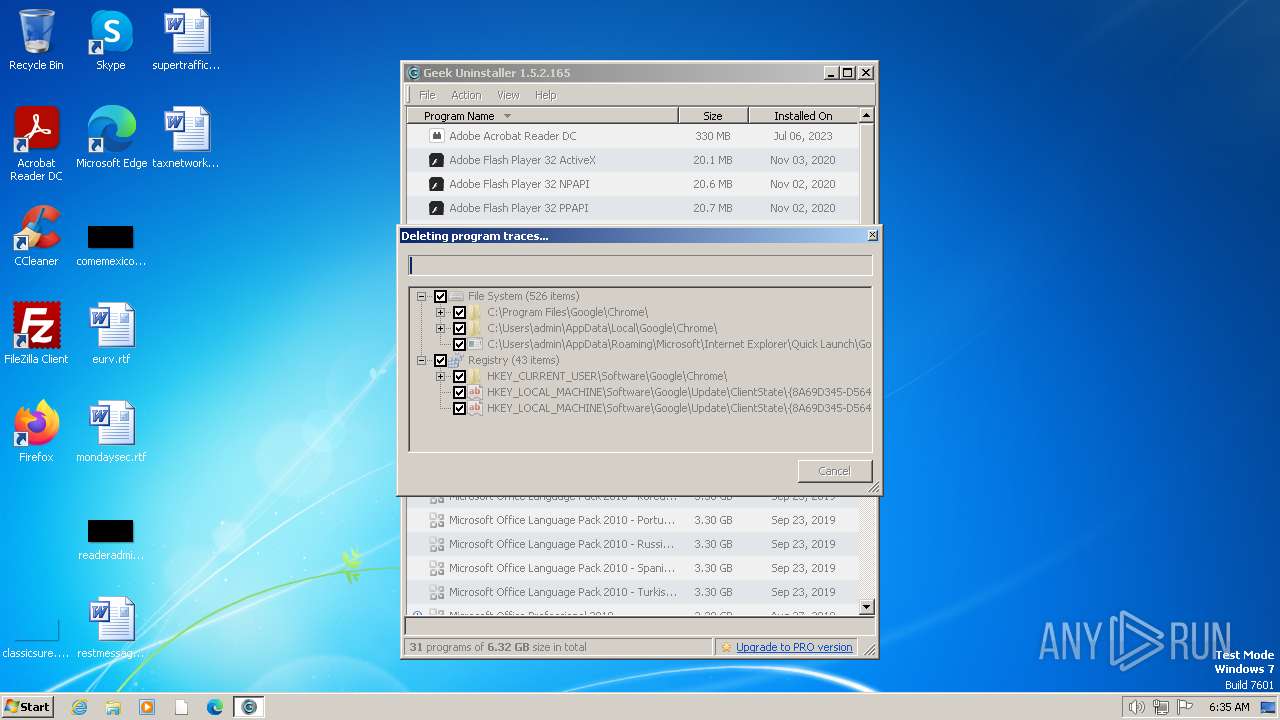
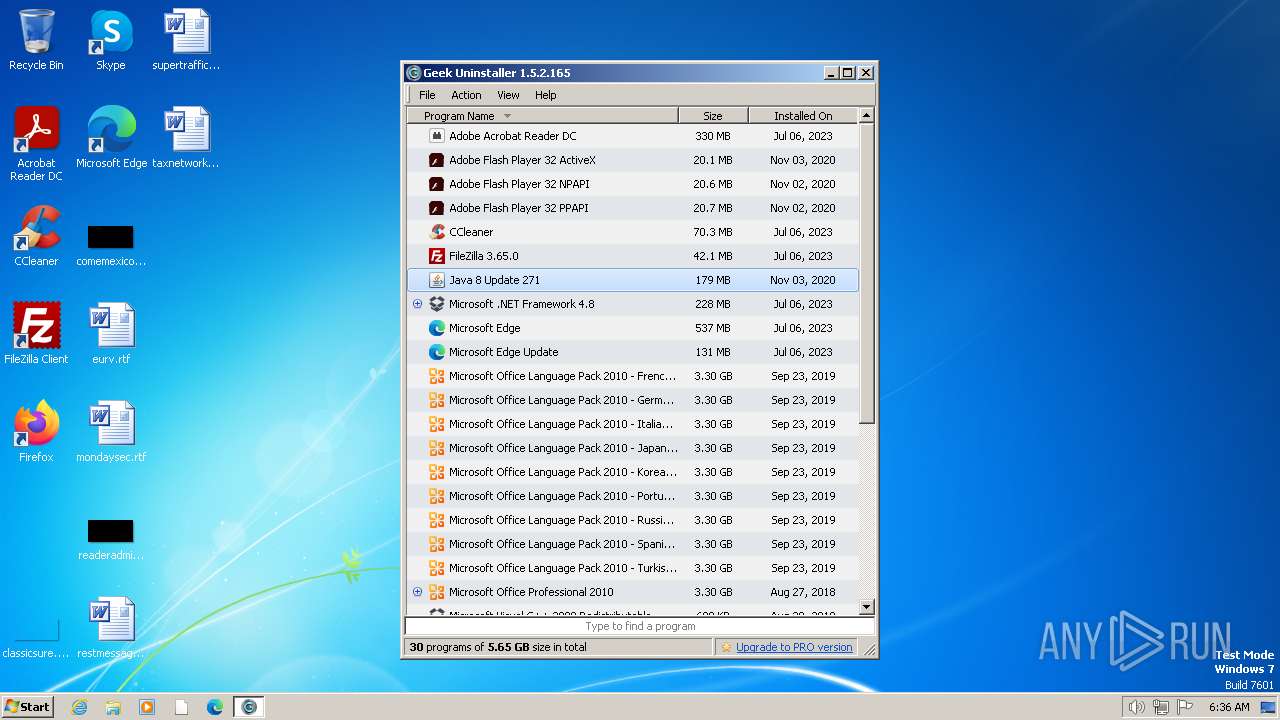
Searches for installed software
- geek.exe (PID: 2484)
Checks Windows Trust Settings
- geek.exe (PID: 2484)
Reads settings of System Certificates
- geek.exe (PID: 2484)
Reads security settings of Internet Explorer
- geek.exe (PID: 2484)
Adds/modifies Windows certificates
- geek.exe (PID: 2484)
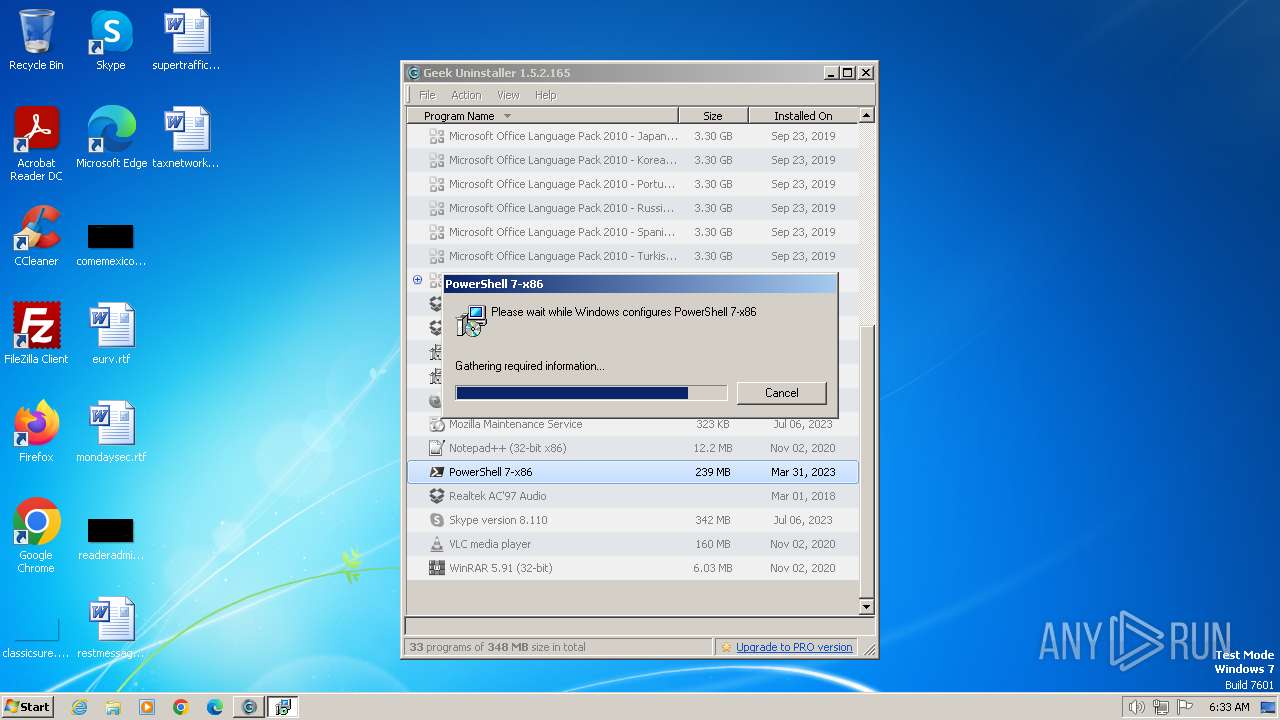
Application launched itself
- vcredist_x86.exe (PID: 3728)
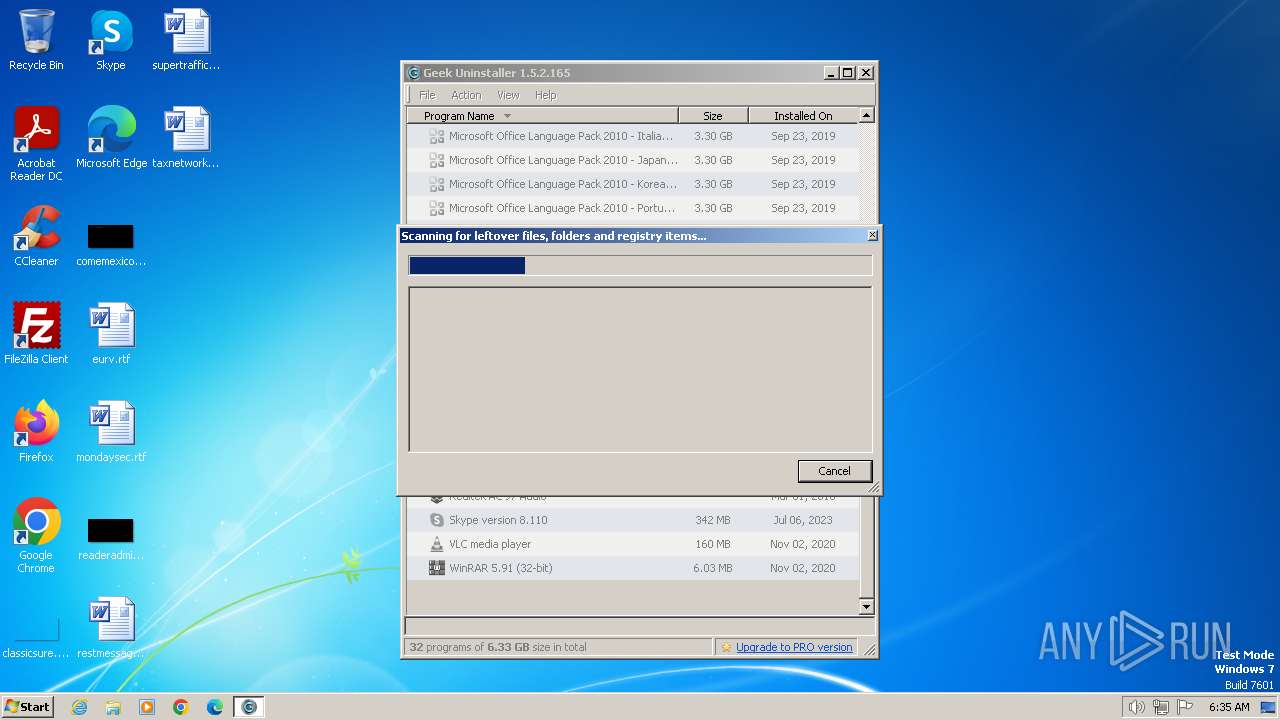
Executable content was dropped or overwritten
- vcredist_x86.exe (PID: 3816)
- vcredist_x86.exe (PID: 3728)
Process drops legitimate windows executable
- vcredist_x86.exe (PID: 3816)
- vcredist_x86.exe (PID: 3728)
INFO
Reads the machine GUID from the registry
- geek.exe (PID: 2484)
Checks proxy server information
- geek.exe (PID: 2484)
Checks supported languages
- geek.exe (PID: 2484)
Reads the computer name
- geek.exe (PID: 2484)
Create files in a temporary directory
- geek.exe (PID: 2484)
Creates files or folders in the user directory
- geek.exe (PID: 2484)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (76.4) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (12.4) |
| .exe | | | Generic Win/DOS Executable (5.5) |
| .exe | | | DOS Executable Generic (5.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2023:09:07 10:12:22+02:00 |
| ImageFileCharacteristics: | No relocs, Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 14.29 |
| CodeSize: | 1999872 |
| InitializedDataSize: | 5018624 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x199f84 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.5.2.165 |
| ProductVersionNumber: | 1.5.2.165 |
| FileFlagsMask: | 0x001f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Windows, Latin1 |
| CompanyName: | Geek Uninstaller |
| Comments: | https://geekuninstaller.com |
| FileDescription: | Geek Uninstaller |
| FileVersion: | 1.5.2.165 |
| InternalName: | Geek Uninstaller |
| LegalCopyright: | Copyright (C) 2012-2023 Geek Uninstaller |
| OriginalFileName: | geek.exe |
| ProductName: | Geek-Uninstaller |
| ProductVersion: | 1.5.2.165 |
Total processes
53
Monitored processes
6
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
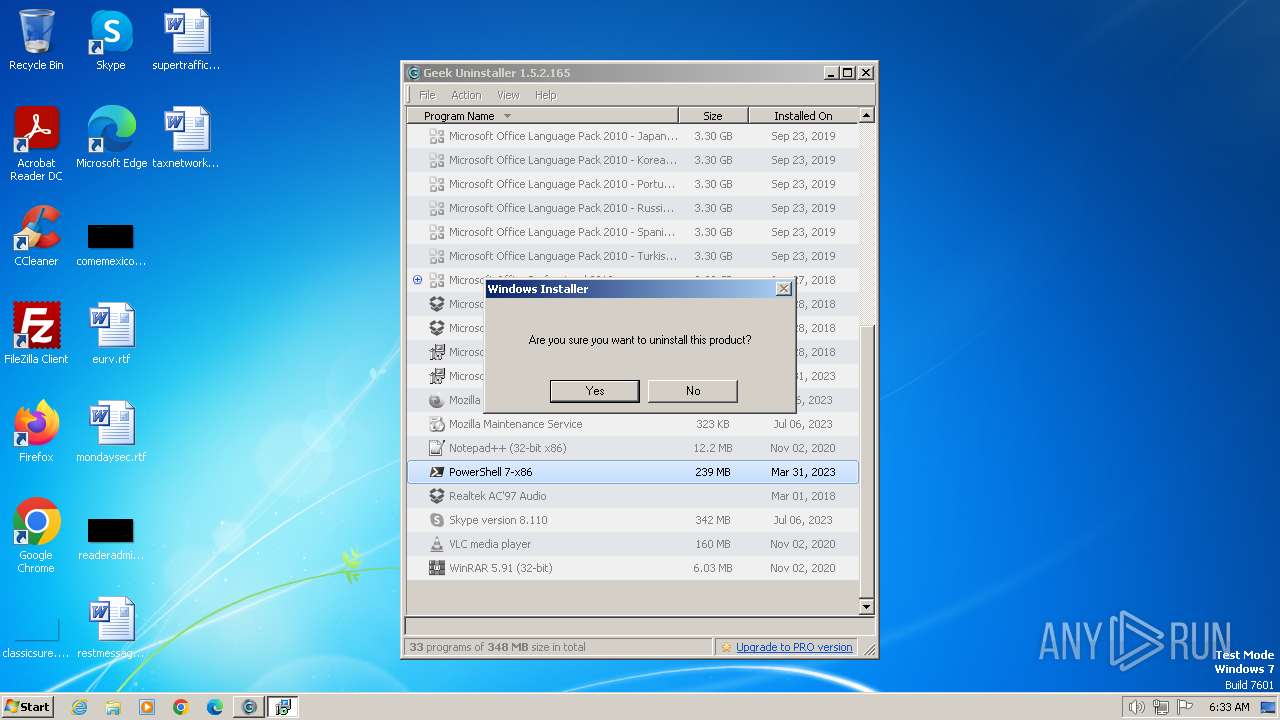
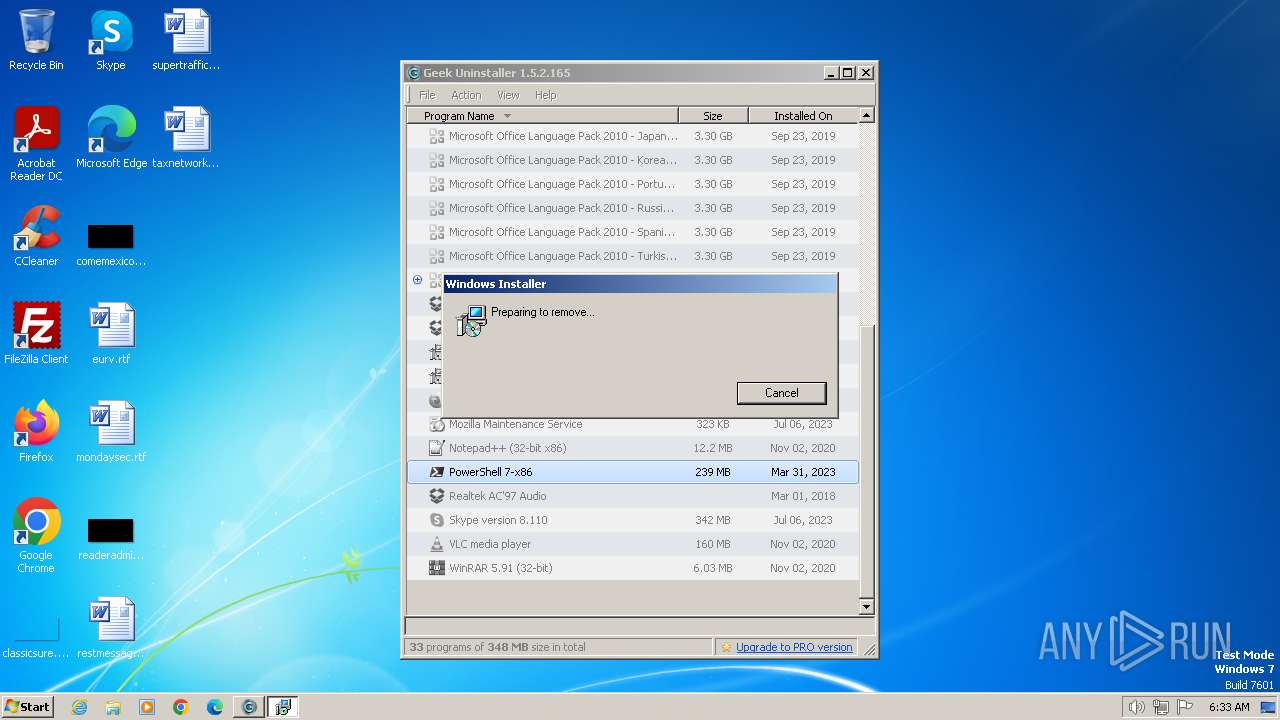
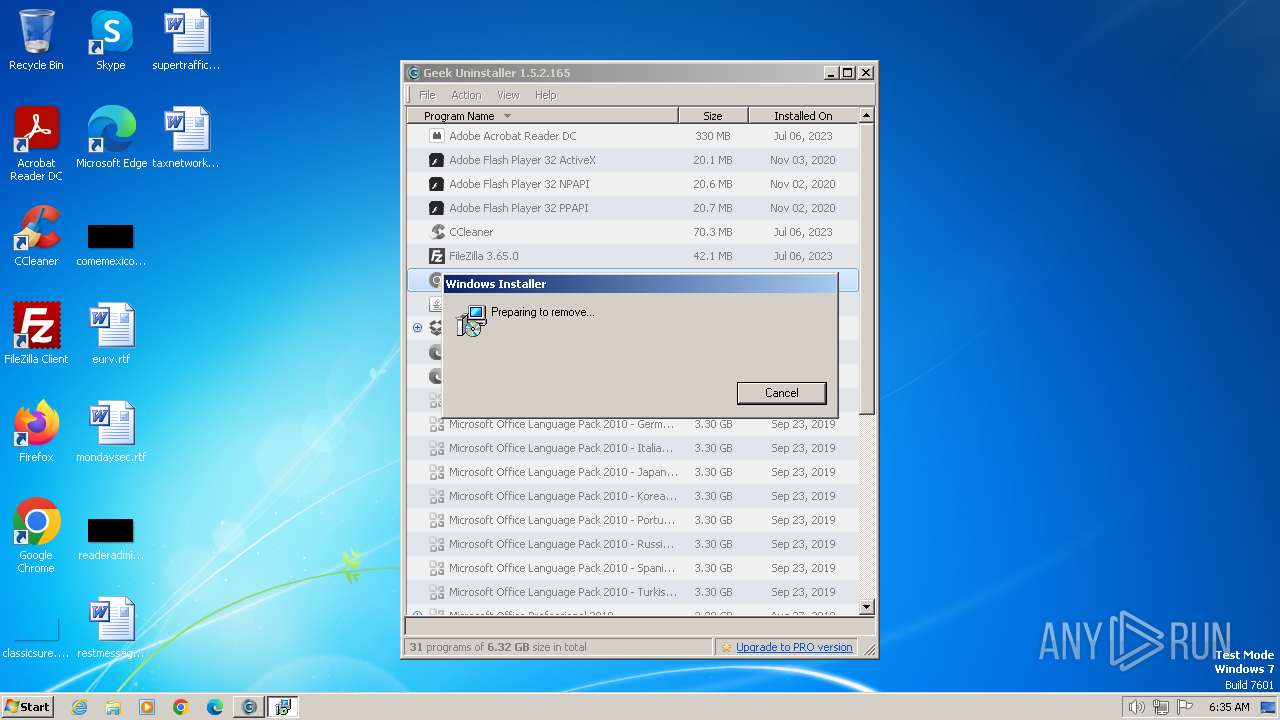
| 2036 | MsiExec.exe /X{AF7532D8-19DC-304C-9BF0-776ACA514F30} | C:\Windows\System32\msiexec.exe | — | geek.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) | |||||||||||||||
| 2396 | "C:\Users\admin\AppData\Local\Temp\geek.exe" | C:\Users\admin\AppData\Local\Temp\geek.exe | — | explorer.exe | |||||||||||
User: admin Company: Geek Uninstaller Integrity Level: MEDIUM Description: Geek Uninstaller Exit code: 3221226540 Version: 1.5.2.165 Modules
| |||||||||||||||
| 2484 | "C:\Users\admin\AppData\Local\Temp\geek.exe" | C:\Users\admin\AppData\Local\Temp\geek.exe | explorer.exe | ||||||||||||
User: admin Company: Geek Uninstaller Integrity Level: HIGH Description: Geek Uninstaller Exit code: 0 Version: 1.5.2.165 Modules
| |||||||||||||||
| 3324 | MsiExec.exe /X{9B99CA21-B296-4C2D-9EBA-DCD1E0C59612} | C:\Windows\System32\msiexec.exe | — | geek.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
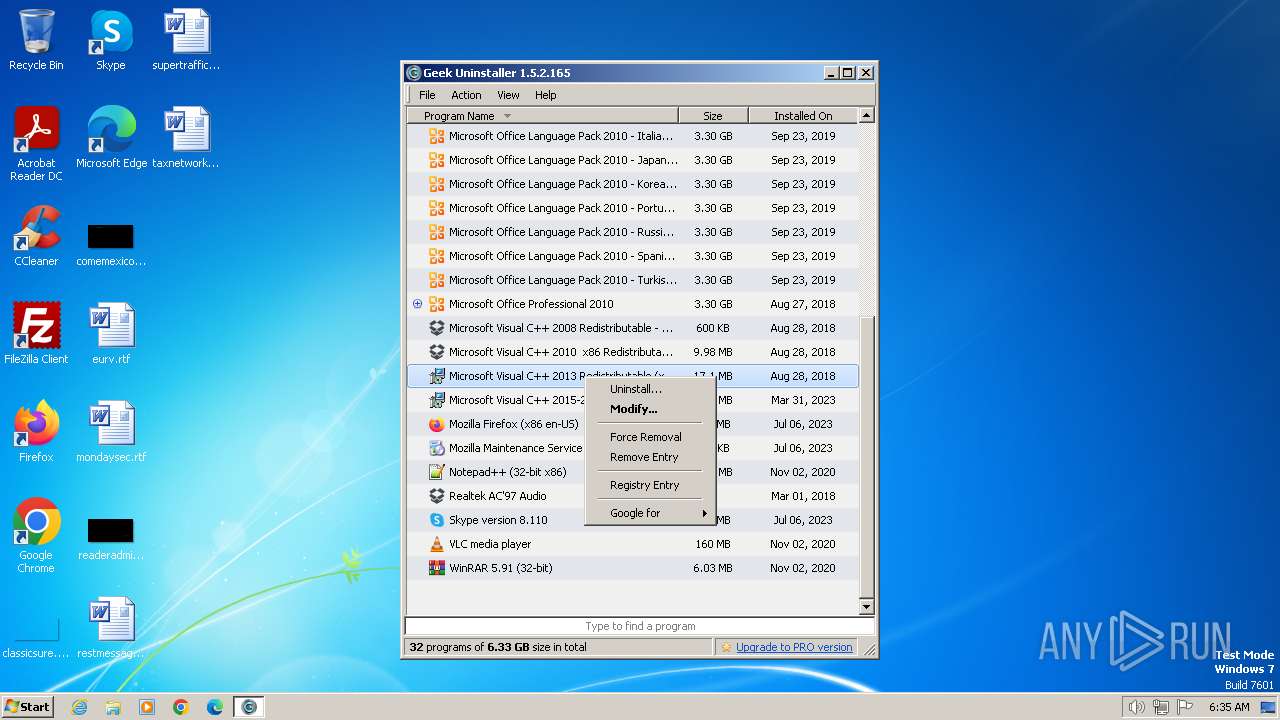
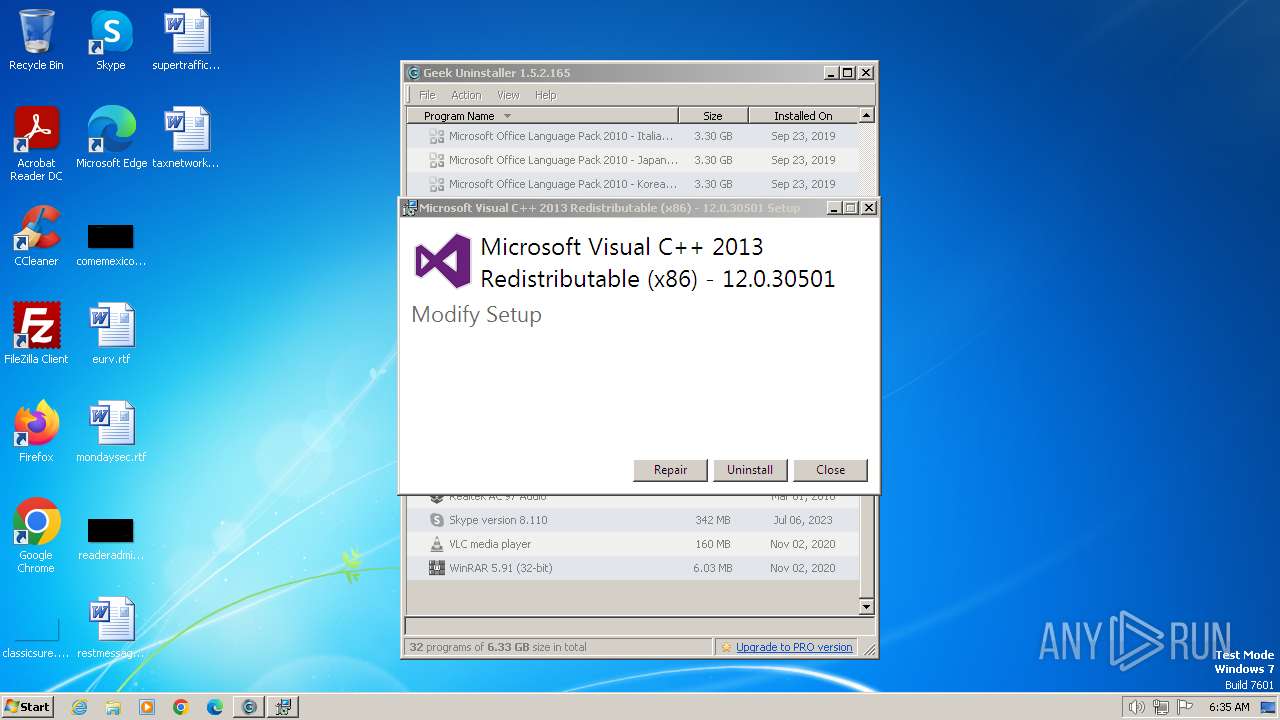
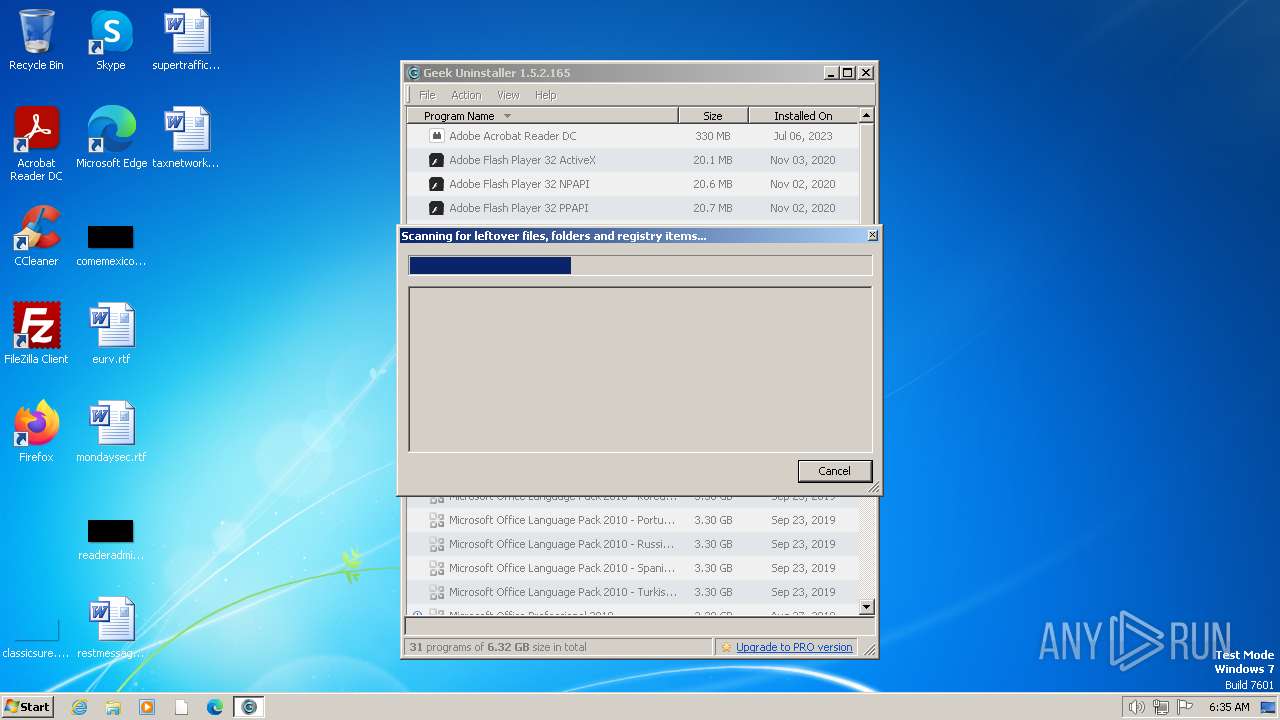
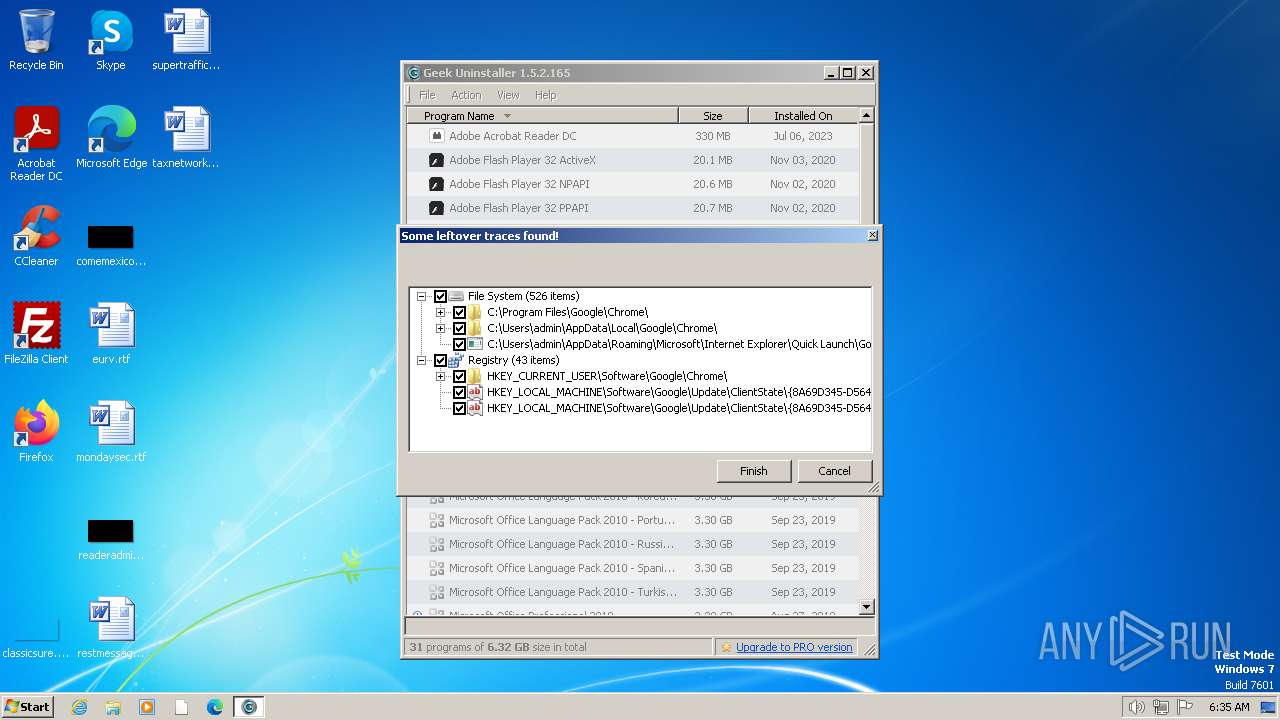
| 3728 | "C:\ProgramData\Package Cache\{f65db027-aff3-4070-886a-0d87064aabb1}\vcredist_x86.exe" /uninstall | C:\ProgramData\Package Cache\{f65db027-aff3-4070-886a-0d87064aabb1}\vcredist_x86.exe | geek.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Visual C++ 2013 Redistributable (x86) - 12.0.30501 Exit code: 0 Version: 12.0.30501.0 Modules
| |||||||||||||||
| 3816 | "C:\ProgramData\Package Cache\{f65db027-aff3-4070-886a-0d87064aabb1}\vcredist_x86.exe" /uninstall -burn.unelevated BurnPipe.{5E555E57-26AE-4420-A410-03D93A6EE689} {485993A5-B364-4DC9-940E-83C06A5FB531} 3728 | C:\ProgramData\Package Cache\{f65db027-aff3-4070-886a-0d87064aabb1}\vcredist_x86.exe | vcredist_x86.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Visual C++ 2013 Redistributable (x86) - 12.0.30501 Exit code: 0 Version: 12.0.30501.0 Modules
| |||||||||||||||
Total events
45 630
Read events
45 575
Write events
49
Delete events
6
Modification events
| (PID) Process: | (2484) geek.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2484) geek.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 460000005B010000090000000000000000000000000000000400000000000000C0E333BBEAB1D3010000000000000000000000000100000002000000C0A8016B000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2484) geek.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2484) geek.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2484) geek.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2484) geek.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2484) geek.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (2484) geek.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (2484) geek.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Wpad\{FCC67766-6201-4AD1-A6B8-2F4553C93D47} |
| Operation: | write | Name: | WpadDecisionReason |
Value: 1 | |||
| (PID) Process: | (2484) geek.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Wpad\{FCC67766-6201-4AD1-A6B8-2F4553C93D47} |
| Operation: | write | Name: | WpadDecisionTime |
Value: 0EE520E67C52DA01 | |||
Executable files
2
Suspicious files
13
Text files
8
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3728 | vcredist_x86.exe | C:\System Volume Information\SPP\metadata-2 | — | |
MD5:— | SHA256:— | |||
| 2484 | geek.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\77EC63BDA74BD0D0E0426DC8F8008506 | compressed | |
MD5:AC05D27423A85ADC1622C714F2CB6184 | SHA256:C6456E12E5E53287A547AF4103E0397CB9697E466CF75844312DC296D43D144D | |||
| 2484 | geek.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\PO2HN1X2\update[1].txt | text | |
MD5:83838B4289E8C584CFD2A53EF414D33D | SHA256:72727B107B79962C08A14D80FFA925387E83CD9ACACFBAB7C7F5DA679B5BDD91 | |||
| 3816 | vcredist_x86.exe | C:\Users\admin\AppData\Local\Temp\{f65db027-aff3-4070-886a-0d87064aabb1}\.ba1\logo.png | image | |
MD5:D6BD210F227442B3362493D046CEA233 | SHA256:335A256D4779EC5DCF283D007FB56FD8211BBCAF47DCD70FE60DED6A112744EF | |||
| 3816 | vcredist_x86.exe | C:\Users\admin\AppData\Local\Temp\{f65db027-aff3-4070-886a-0d87064aabb1}\.ba1\thm.wxl | xml | |
MD5:FBFCBC4DACC566A3C426F43CE10907B6 | SHA256:70400F181D00E1769774FF36BCD8B1AB5FBC431418067D31B876D18CC04EF4CE | |||
| 3728 | vcredist_x86.exe | C:\System Volume Information\SPP\snapshot-2 | binary | |
MD5:9E57CC589D99BB58C75AF7DDBC0056B8 | SHA256:1E9F208401EF4BB0D7F769565212F4525D7829F21BA6EA240FF040861A92FFEA | |||
| 2484 | geek.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\77EC63BDA74BD0D0E0426DC8F8008506 | binary | |
MD5:B9816CC76F9B98ED2B00166029DFF3CE | SHA256:116BD098F71303C526415C1A541B231597471700AAAE629D444C6BCDC6614C70 | |||
| 2484 | geek.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\103621DE9CD5414CC2538780B4B75751 | der | |
MD5:60FE01DF86BE2E5331B0CDBE86165686 | SHA256:C08CCBC876CD5A7CDFA9670F9637DA57F6A1282198A9BC71FC7D7247A6E5B7A8 | |||
| 2484 | geek.exe | C:\Users\admin\AppData\Local\Temp\Cab999E.tmp | compressed | |
MD5:AC05D27423A85ADC1622C714F2CB6184 | SHA256:C6456E12E5E53287A547AF4103E0397CB9697E466CF75844312DC296D43D144D | |||
| 2484 | geek.exe | C:\Users\admin\AppData\Local\Temp\Tar999F.tmp | cat | |
MD5:9C0C641C06238516F27941AA1166D427 | SHA256:4276AF3669A141A59388BC56A87F6614D9A9BDDDF560636C264219A7EB11256F | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
12
DNS requests
4
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2484 | geek.exe | GET | 304 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?1ea1eae1fa4d6740 | unknown | — | — | unknown |
2484 | geek.exe | GET | 200 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?234f22c6067116dc | unknown | compressed | 65.2 Kb | unknown |
2484 | geek.exe | GET | 200 | 69.192.161.44:80 | http://x1.c.lencr.org/ | unknown | binary | 717 b | unknown |
2484 | geek.exe | GET | 200 | 95.101.54.107:80 | http://r3.o.lencr.org/MFMwUTBPME0wSzAJBgUrDgMCGgUABBRI2smg%2ByvTLU%2Fw3mjS9We3NfmzxAQUFC6zF7dYVsuuUAlA5h%2BvnYsUwsYCEgQloXxw7SRy%2BF2phayuh6Pleg%3D%3D | unknown | binary | 503 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 173.230.144.164:443 | geekuninstaller.com | Linode, LLC | US | unknown |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
2484 | geek.exe | 93.184.221.240:80 | ctldl.windowsupdate.com | EDGECAST | GB | unknown |
2484 | geek.exe | 69.192.161.44:80 | x1.c.lencr.org | AKAMAI-AS | DE | unknown |
2484 | geek.exe | 95.101.54.107:80 | r3.o.lencr.org | Akamai International B.V. | DE | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
geekuninstaller.com |
| unknown |
ctldl.windowsupdate.com |
| whitelisted |
x1.c.lencr.org |
| whitelisted |
r3.o.lencr.org |
| shared |