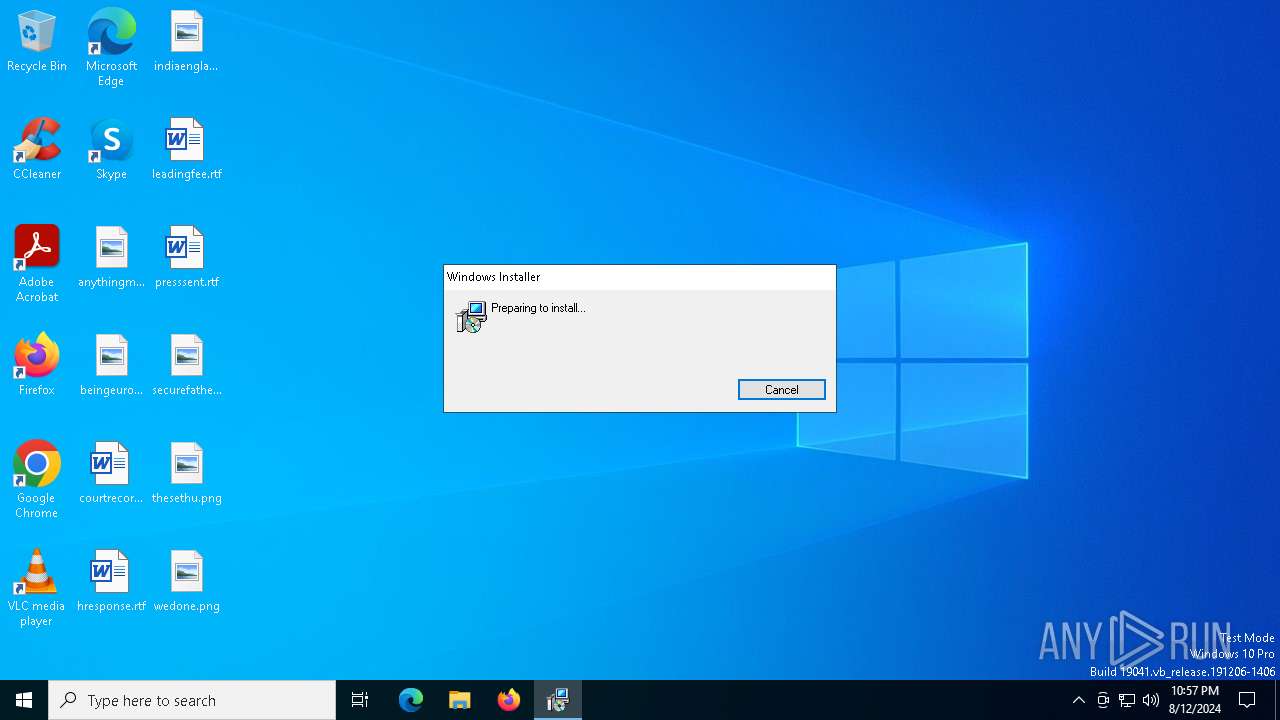
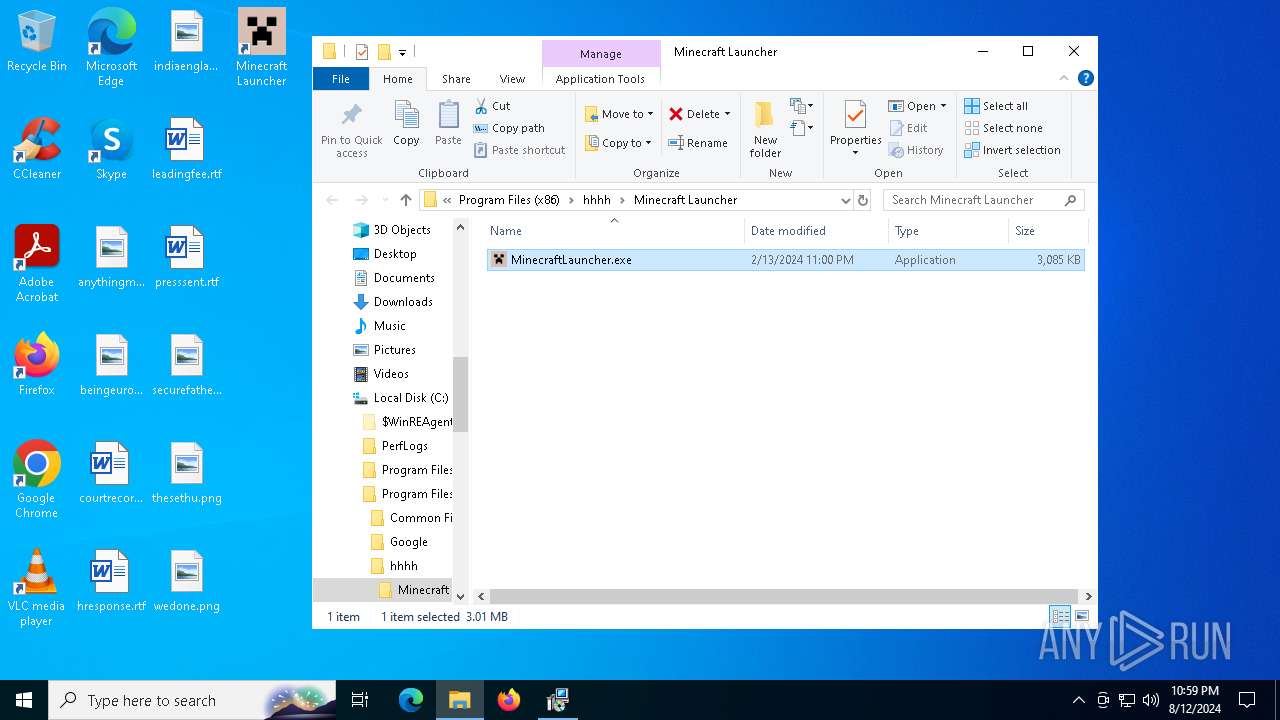
| File name: | MinecraftInstaller.msi |
| Full analysis: | https://app.any.run/tasks/309293db-af8f-4bf2-a590-3a9043b800da |
| Verdict: | Malicious activity |
| Analysis date: | August 12, 2024, 22:57:49 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-msi |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.2, MSI Installer, Code page: 1252, Title: Installation Database, Subject: Minecraft Launcher, Author: Mojang, Keywords: Installer, Comments: This installer database contains the logic and data required to install Minecraft Launcher., Template: Intel;1033, Revision Number: {BC990100-219F-4A7E-BCD6-B88F054547B7}, Create Time/Date: Tue Feb 13 23:03:12 2024, Last Saved Time/Date: Tue Feb 13 23:03:12 2024, Number of Pages: 200, Number of Words: 2, Name of Creating Application: Windows Installer XML Toolset (3.9.1006.0), Security: 2 |
| MD5: | 02D7F8E22149E154487F2FDDDFCEC8C5 |
| SHA1: | 390019B5F2C24F14DD398AB4BA8BEF0183A923AF |
| SHA256: | D9618862A64DA8A5C86F2C9CDE65B48AB92FF8BBC14D5F3C7946539A44E2DB17 |
| SSDEEP: | 98304:RezMF/MeIPrST1vMe5clIIoN2KIZd0O99oU1aikVB8VBlMo/tIB:6y |
MALICIOUS
No malicious indicators.SUSPICIOUS
Executes as Windows Service
- VSSVC.exe (PID: 7028)
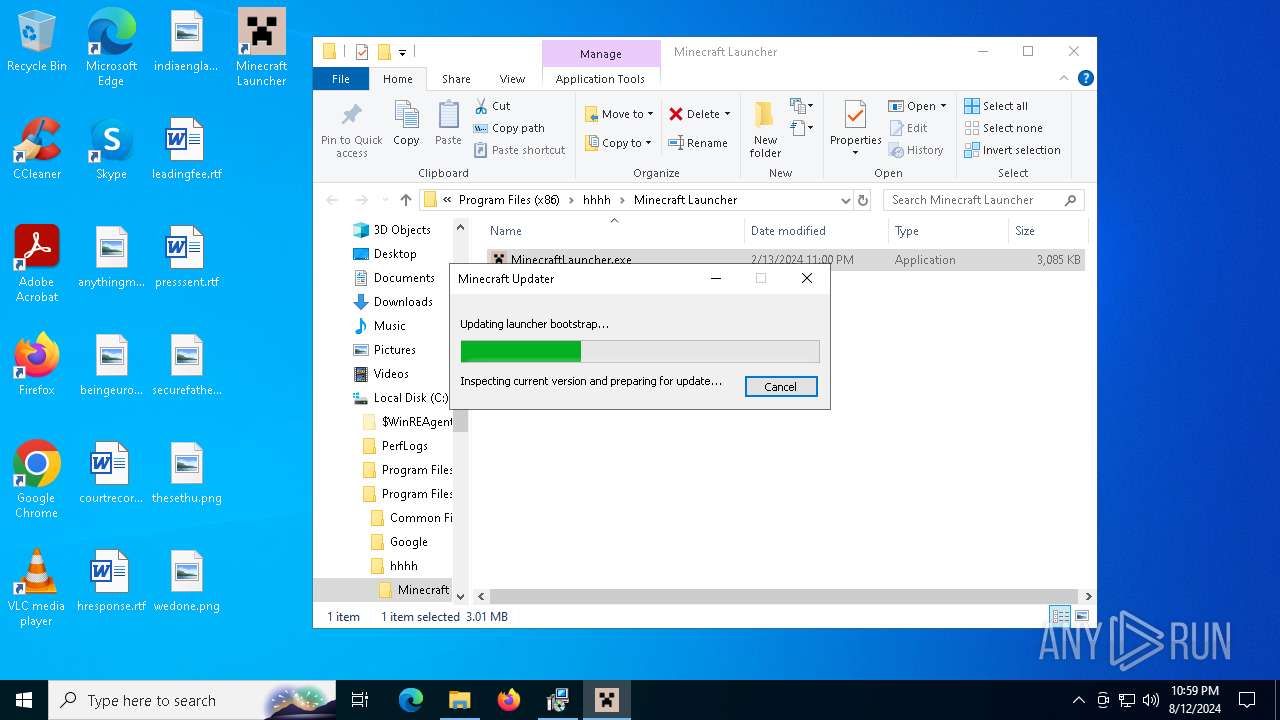
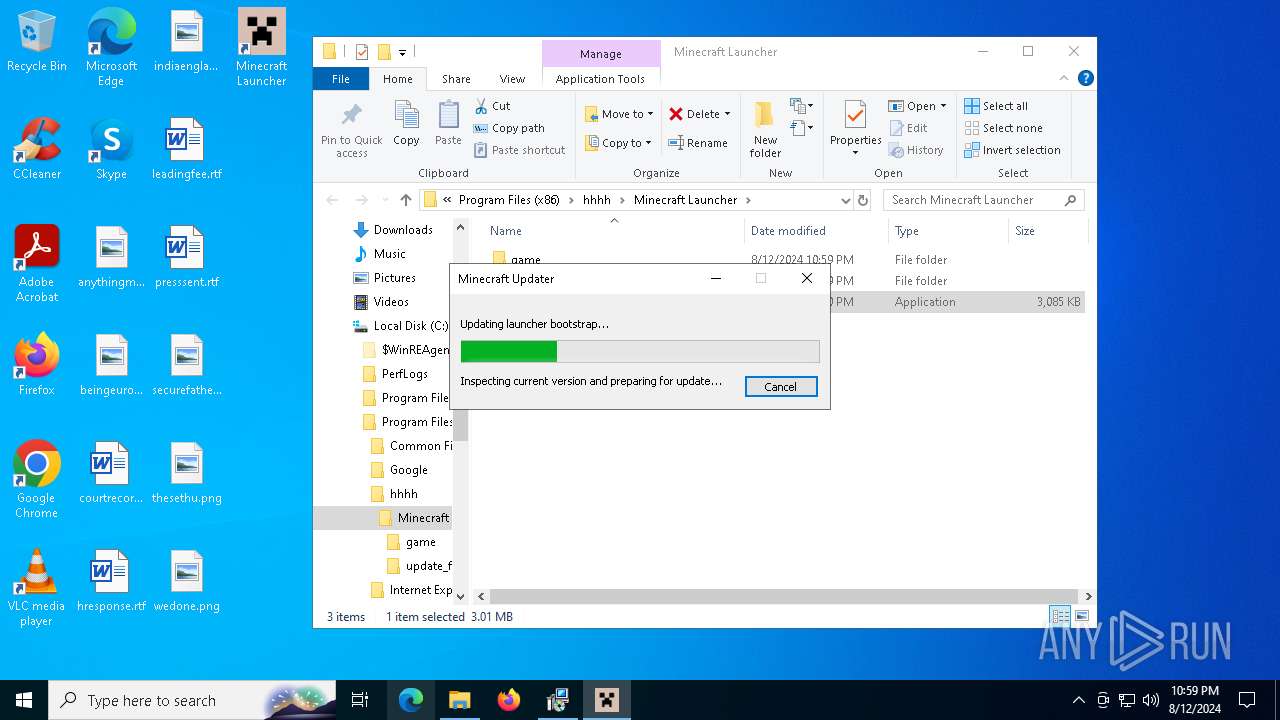
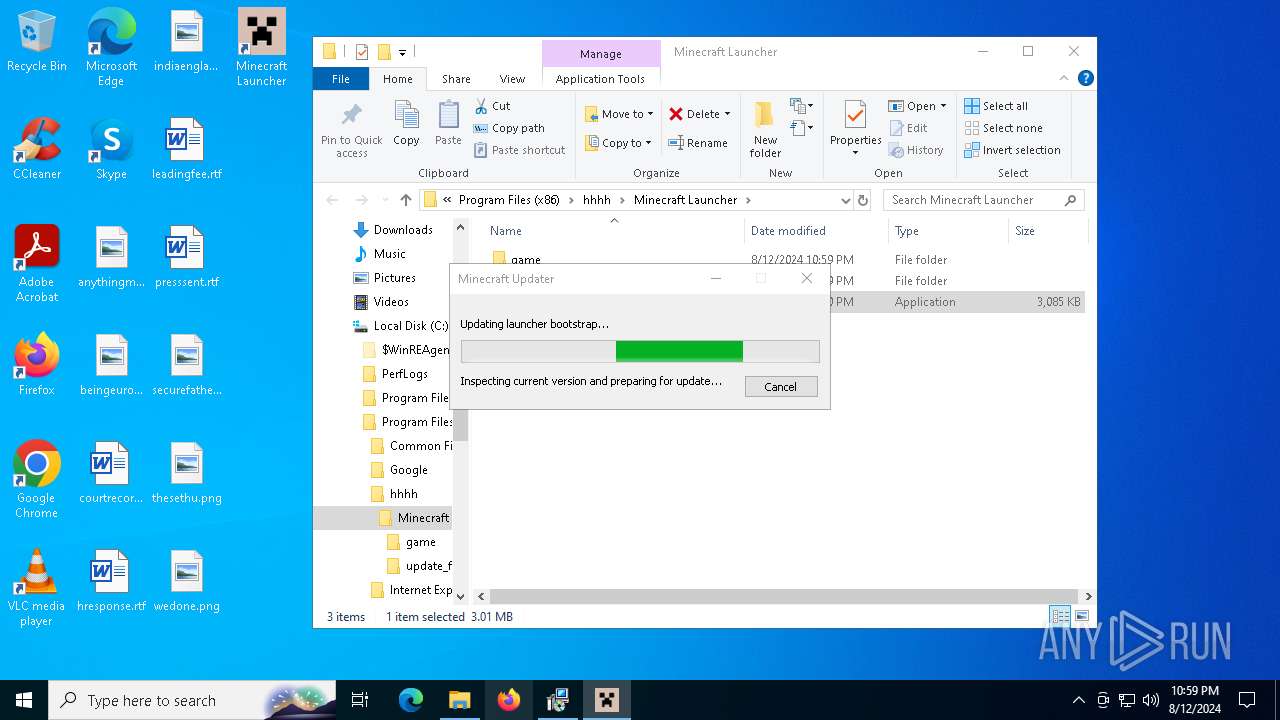
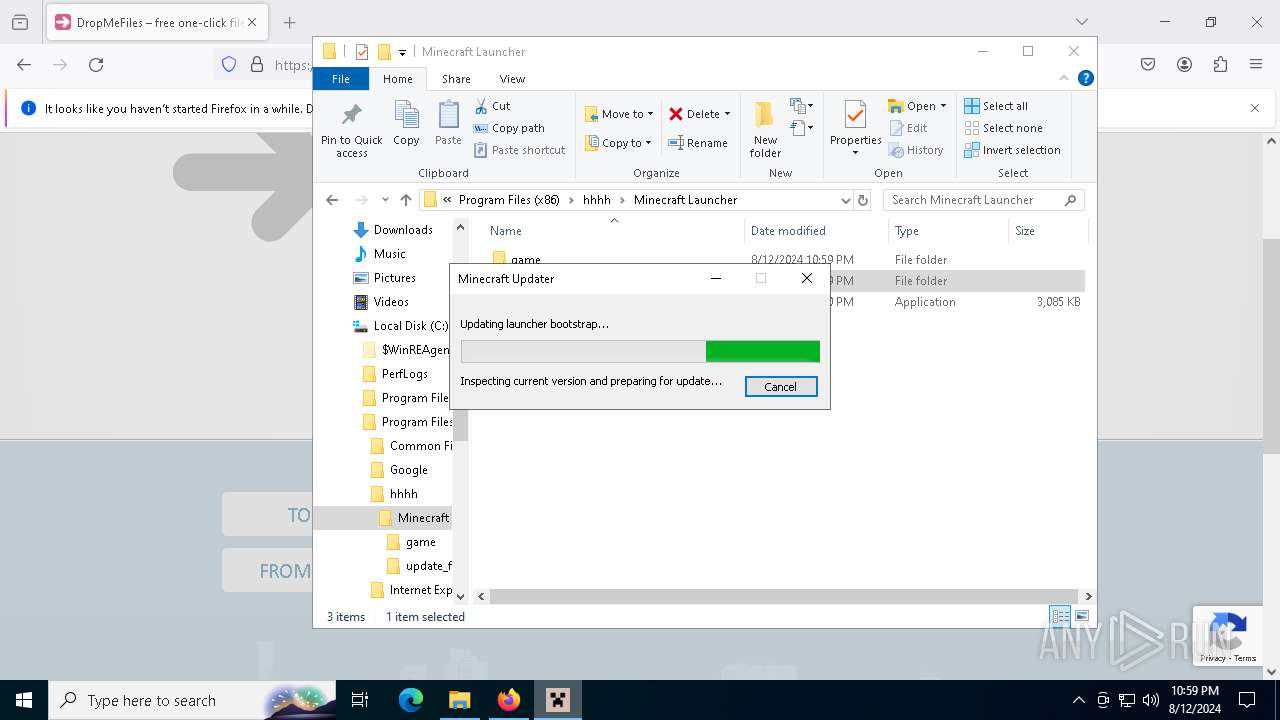
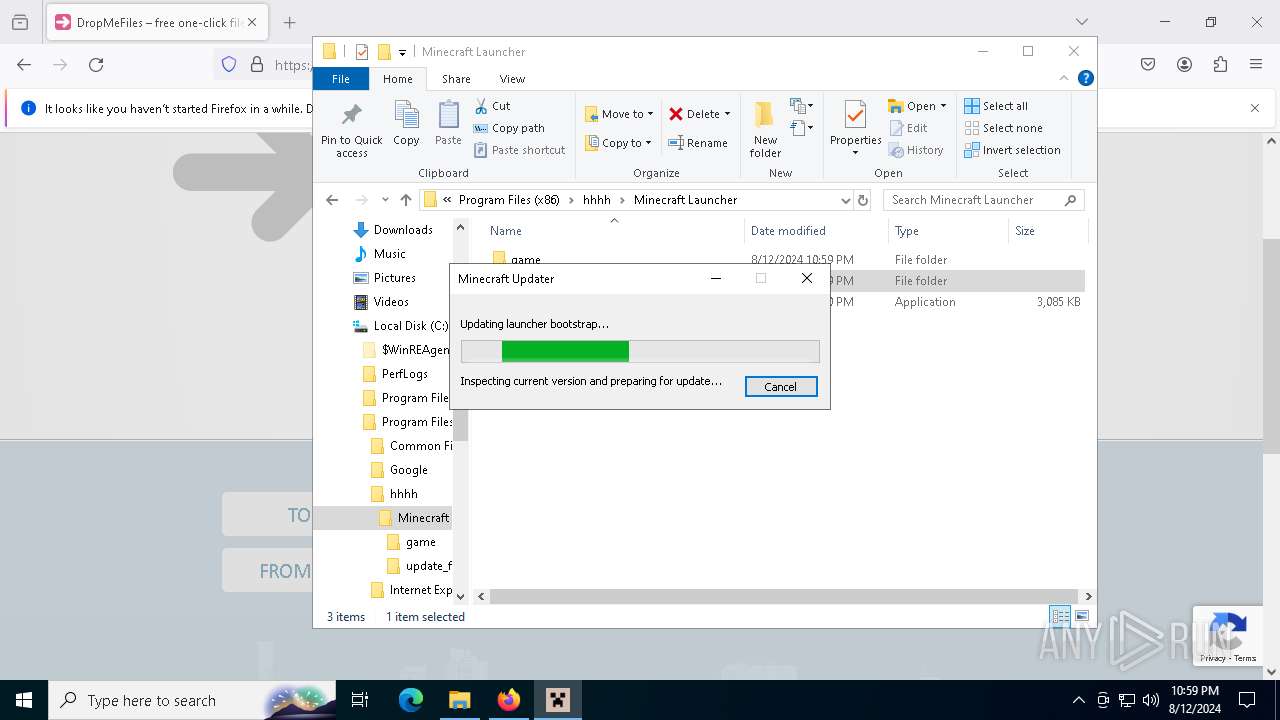
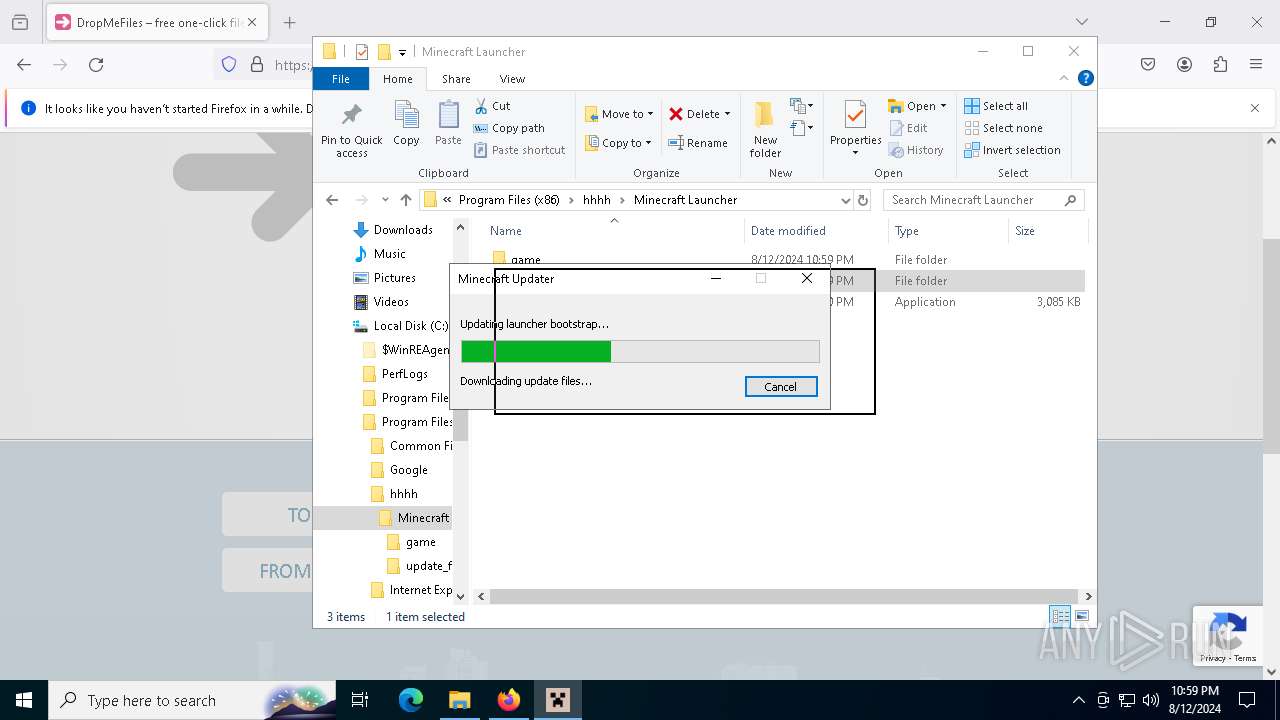
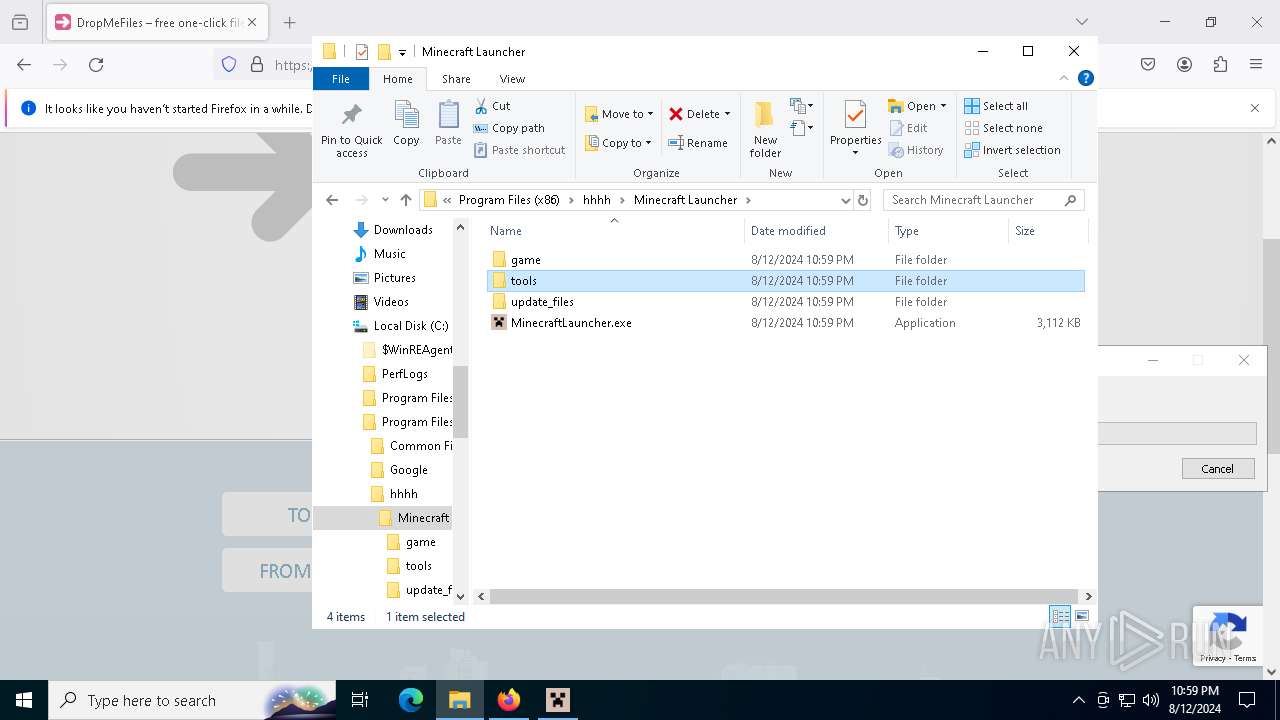
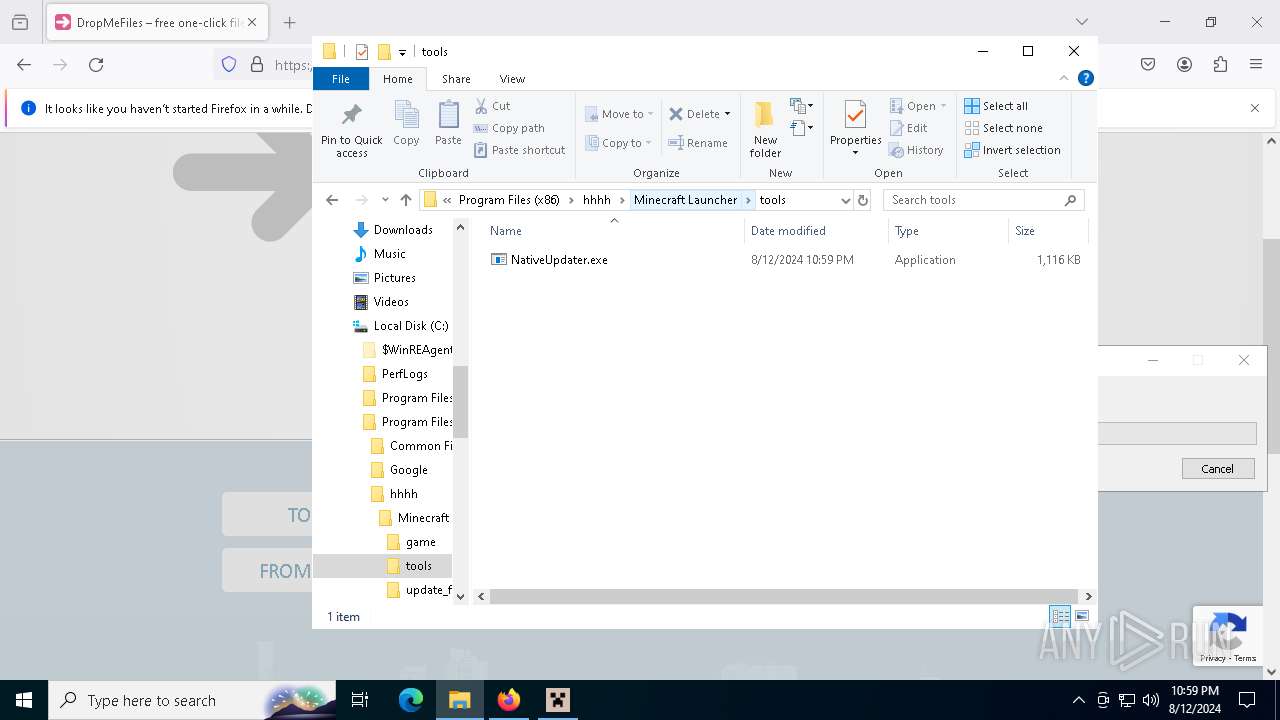
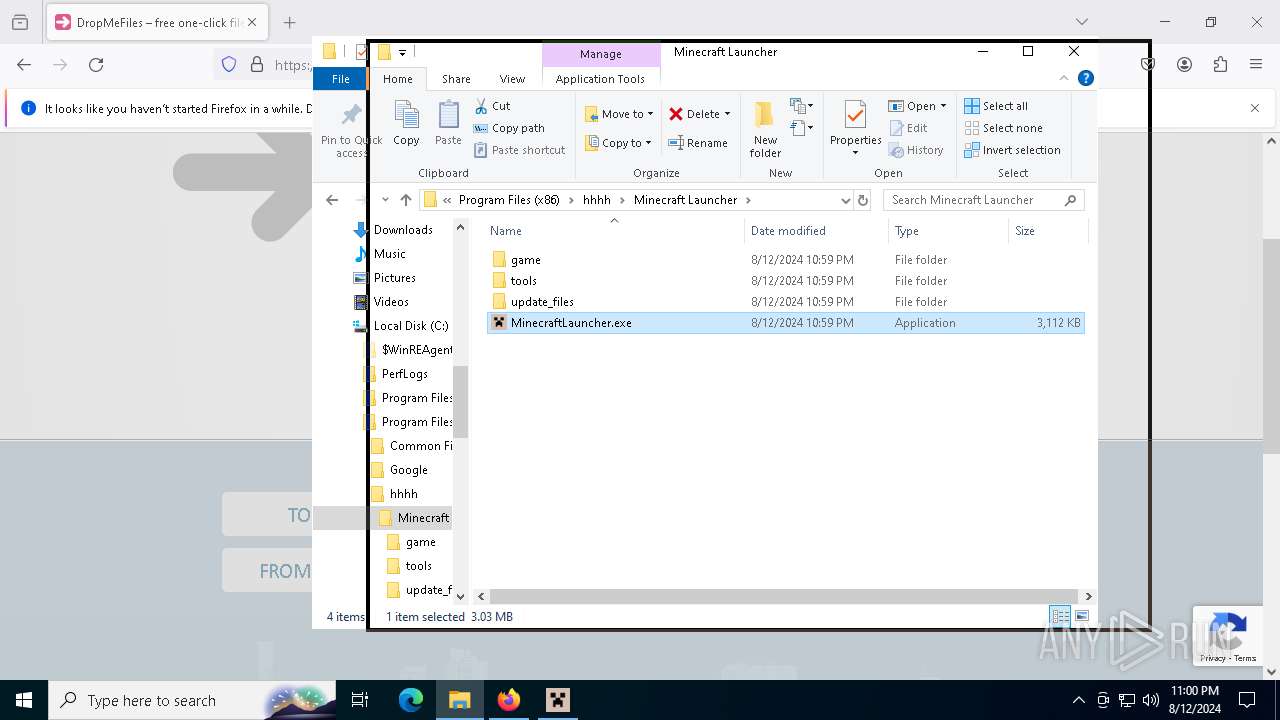
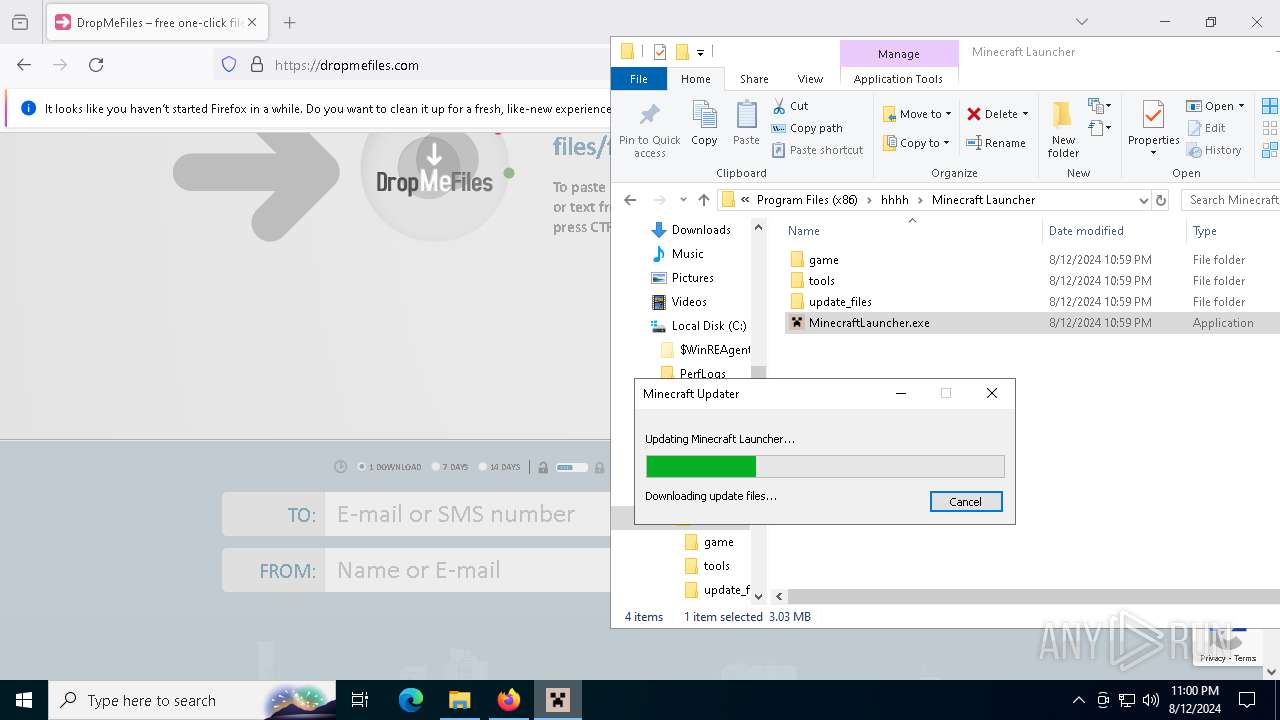
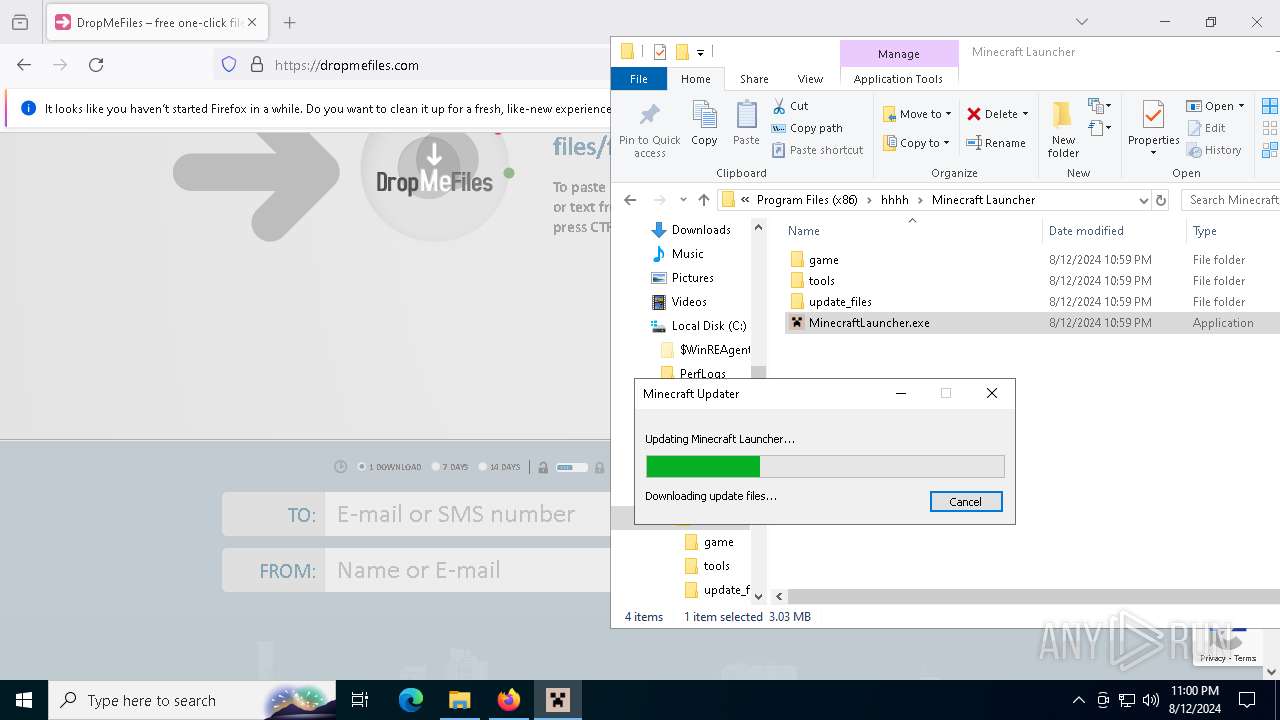
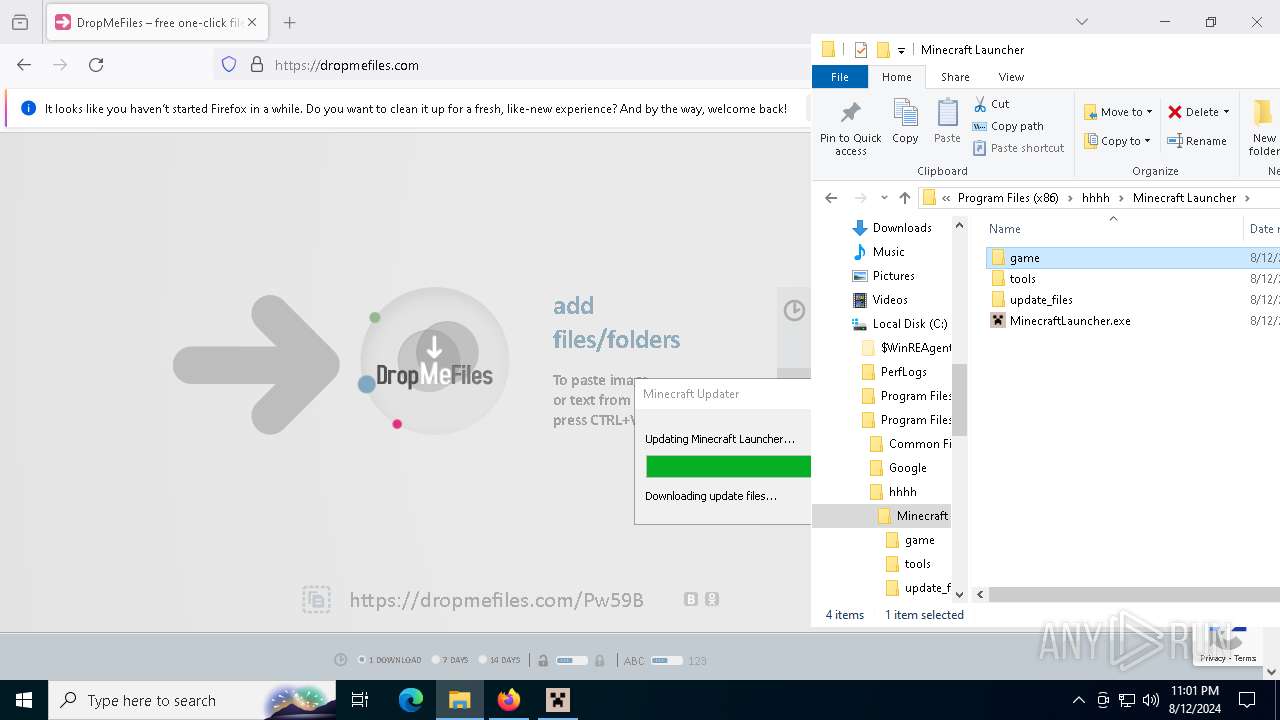
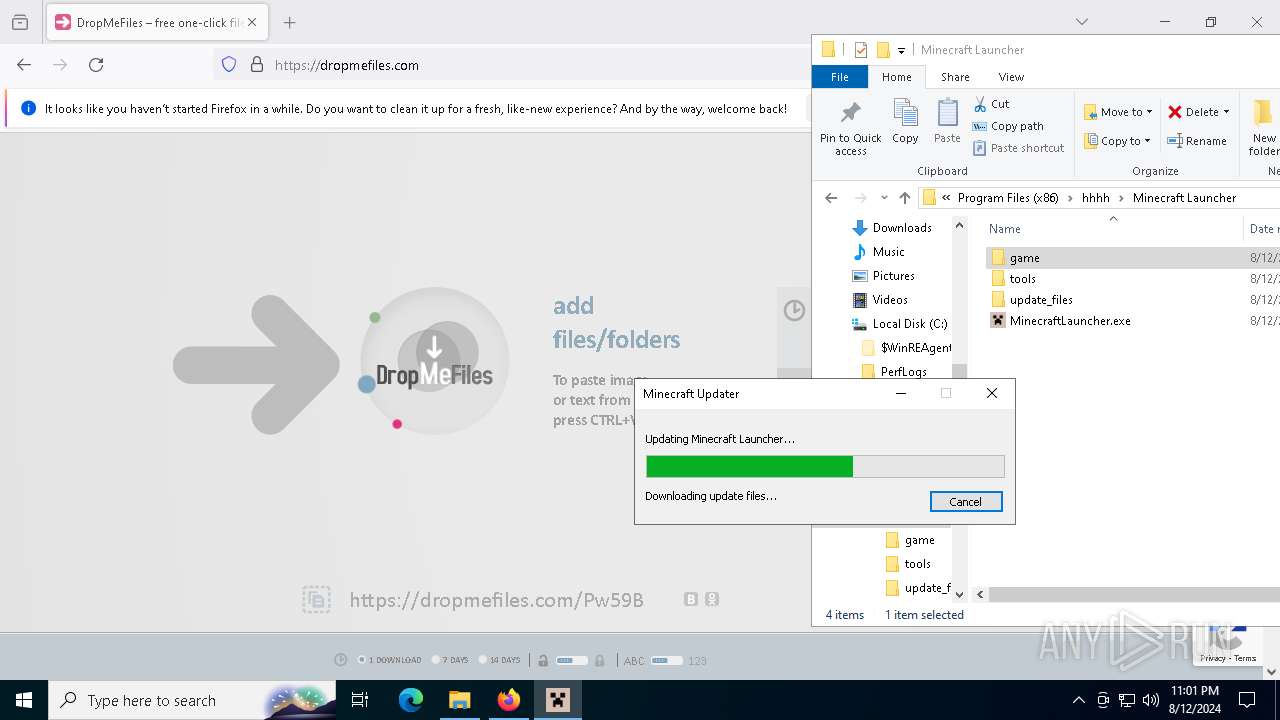
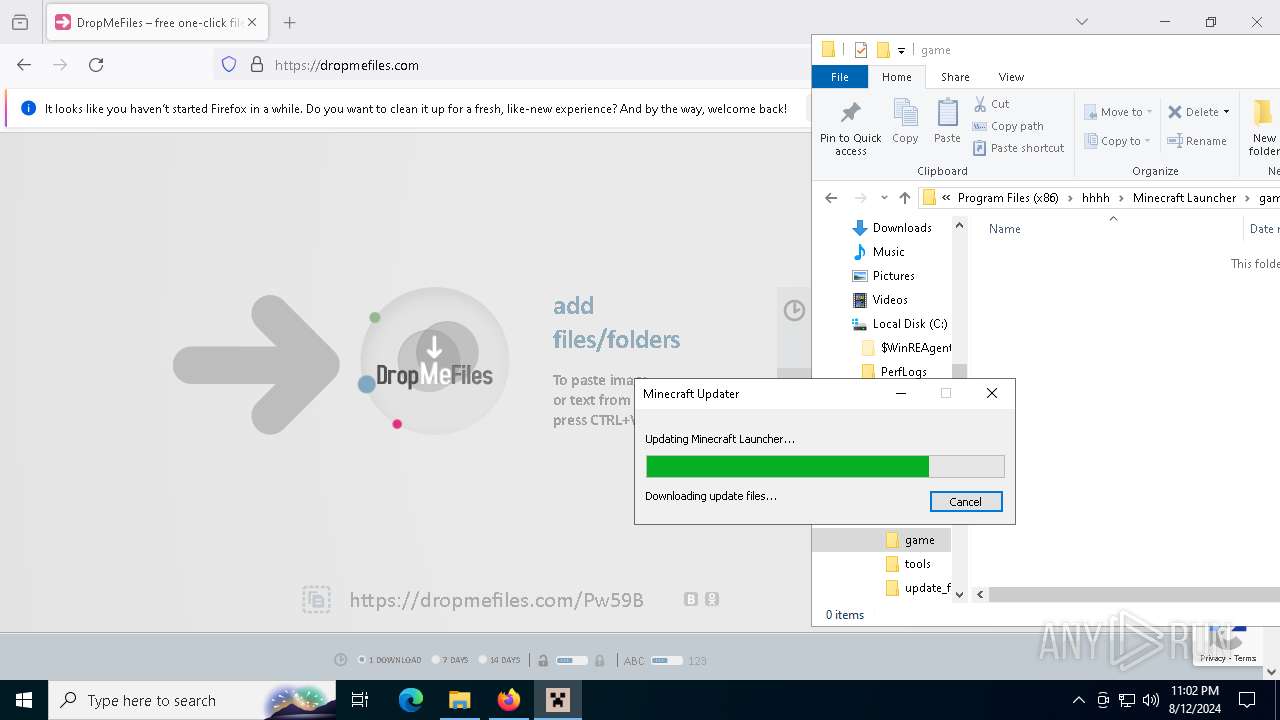
Drops the executable file immediately after the start
- msiexec.exe (PID: 6728)
- msiexec.exe (PID: 6860)
- MinecraftLauncher.exe (PID: 7136)
- NativeUpdater.exe (PID: 7964)
- MinecraftLauncher.exe (PID: 8024)
Checks Windows Trust Settings
- msiexec.exe (PID: 6860)
Reads the Windows owner or organization settings
- msiexec.exe (PID: 6860)
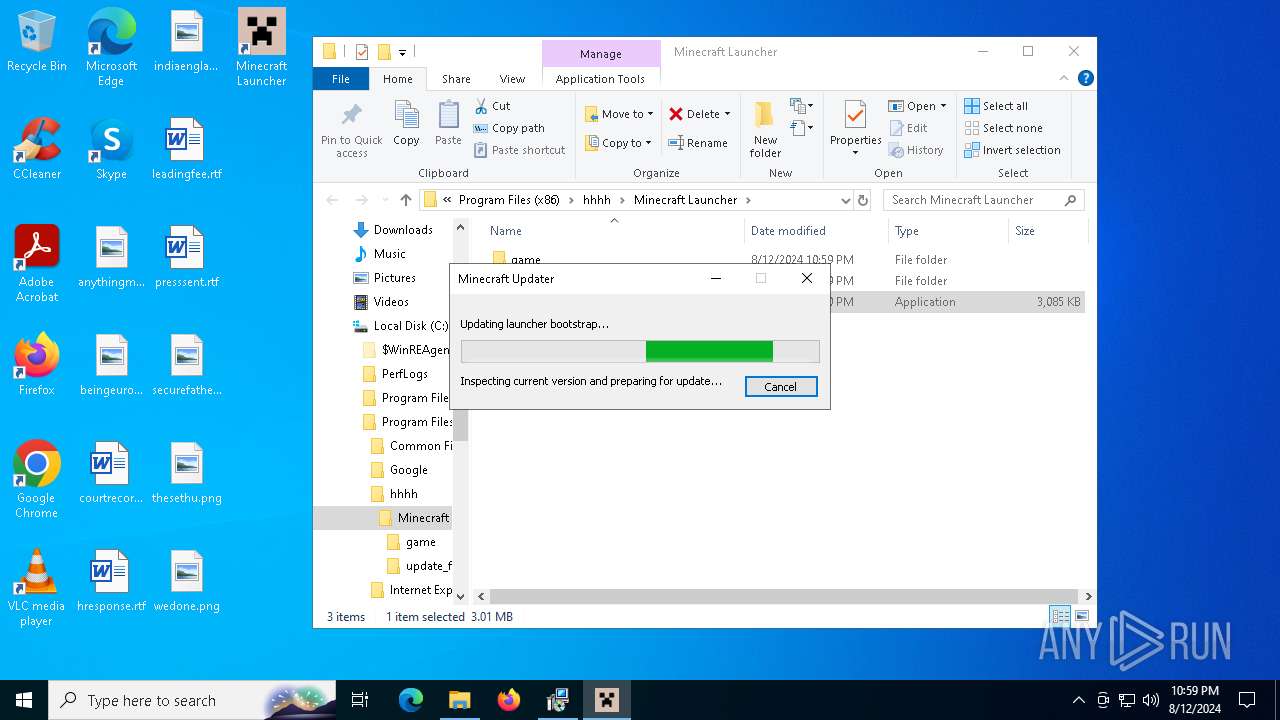
Executable content was dropped or overwritten
- MinecraftLauncher.exe (PID: 7136)
- NativeUpdater.exe (PID: 7964)
- MinecraftLauncher.exe (PID: 8024)
Process drops legitimate windows executable
- MinecraftLauncher.exe (PID: 8024)
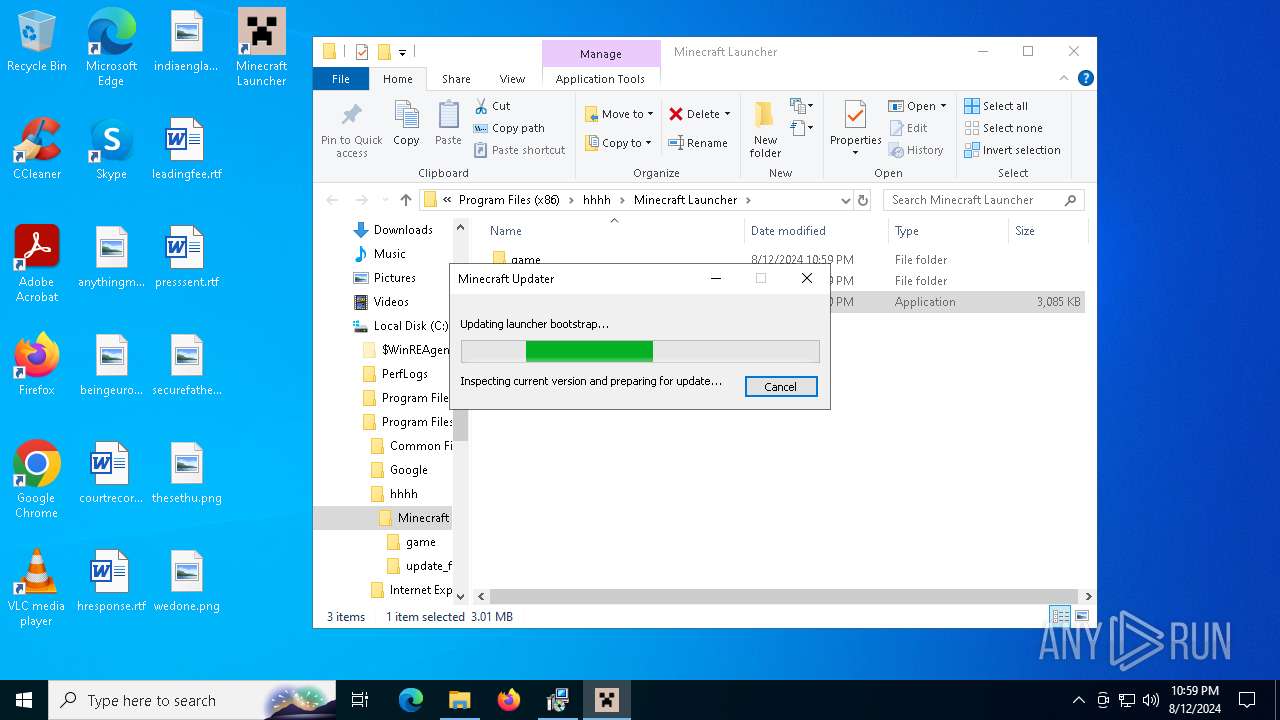
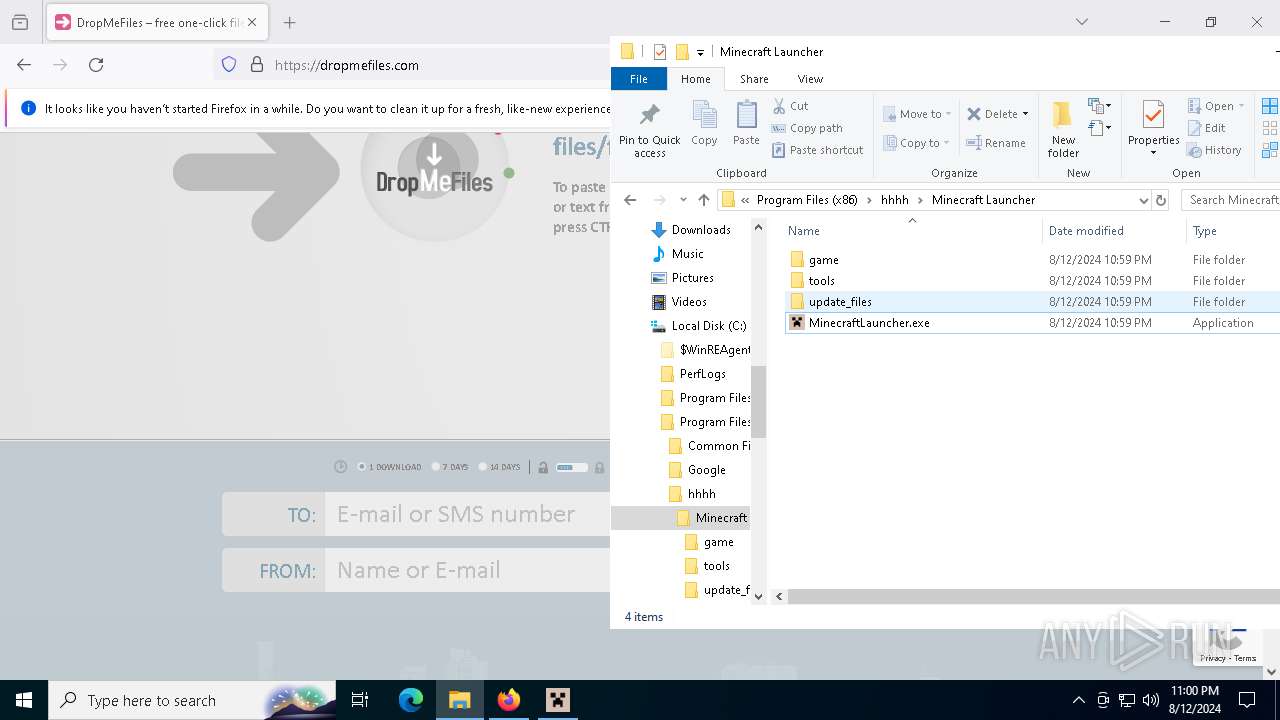
Application launched itself
- MinecraftLauncher.exe (PID: 8024)
INFO
Creates files or folders in the user directory
- msiexec.exe (PID: 6728)
- MinecraftLauncher.exe (PID: 7136)
- NativeUpdater.exe (PID: 7964)
- MinecraftLauncher.exe (PID: 8024)
- MinecraftLauncher.exe (PID: 7572)
Reads security settings of Internet Explorer
- msiexec.exe (PID: 6728)
Reads the computer name
- msiexec.exe (PID: 6724)
- msiexec.exe (PID: 5400)
- msiexec.exe (PID: 6860)
- msiexec.exe (PID: 7092)
- MinecraftLauncher.exe (PID: 7136)
- TextInputHost.exe (PID: 6296)
- MinecraftLauncher.exe (PID: 8024)
- MinecraftLauncher.exe (PID: 3188)
- MinecraftLauncher.exe (PID: 3360)
- MinecraftLauncher.exe (PID: 1048)
- MinecraftLauncher.exe (PID: 6056)
- MinecraftLauncher.exe (PID: 7572)
Checks proxy server information
- msiexec.exe (PID: 6728)
- MinecraftLauncher.exe (PID: 7136)
- MinecraftLauncher.exe (PID: 8024)
- MinecraftLauncher.exe (PID: 3188)
- MinecraftLauncher.exe (PID: 7572)
- MinecraftLauncher.exe (PID: 3360)
- MinecraftLauncher.exe (PID: 1048)
- MinecraftLauncher.exe (PID: 6056)
Checks supported languages
- msiexec.exe (PID: 6724)
- msiexec.exe (PID: 6860)
- msiexec.exe (PID: 7092)
- msiexec.exe (PID: 5400)
- MinecraftLauncher.exe (PID: 7136)
- TextInputHost.exe (PID: 6296)
- NativeUpdater.exe (PID: 7964)
- MinecraftLauncher.exe (PID: 3188)
- MinecraftLauncher.exe (PID: 6056)
- MinecraftLauncher.exe (PID: 8024)
- MinecraftLauncher.exe (PID: 7572)
- MinecraftLauncher.exe (PID: 1048)
- MinecraftLauncher.exe (PID: 3360)
Executable content was dropped or overwritten
- msiexec.exe (PID: 6728)
- msiexec.exe (PID: 6860)
Reads the software policy settings
- msiexec.exe (PID: 6728)
- msiexec.exe (PID: 6860)
- MinecraftLauncher.exe (PID: 8024)
Reads the machine GUID from the registry
- msiexec.exe (PID: 6860)
- MinecraftLauncher.exe (PID: 8024)
Application launched itself
- firefox.exe (PID: 3700)
- firefox.exe (PID: 6868)
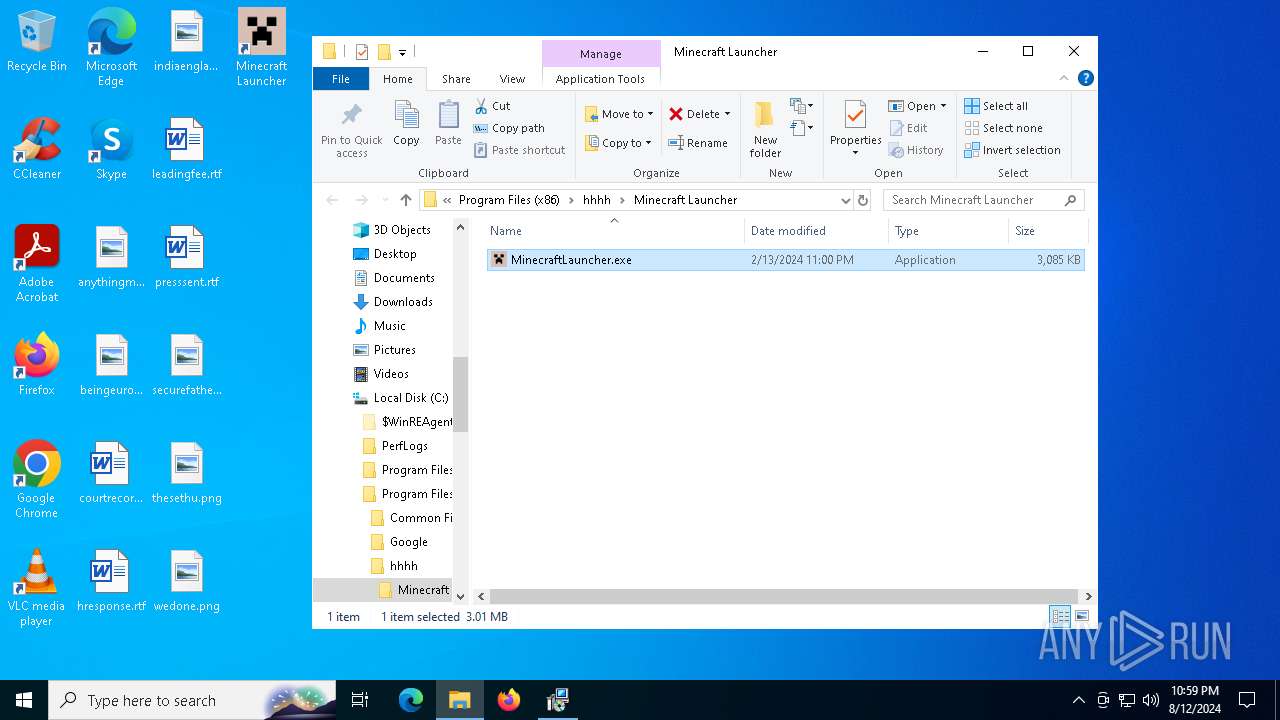
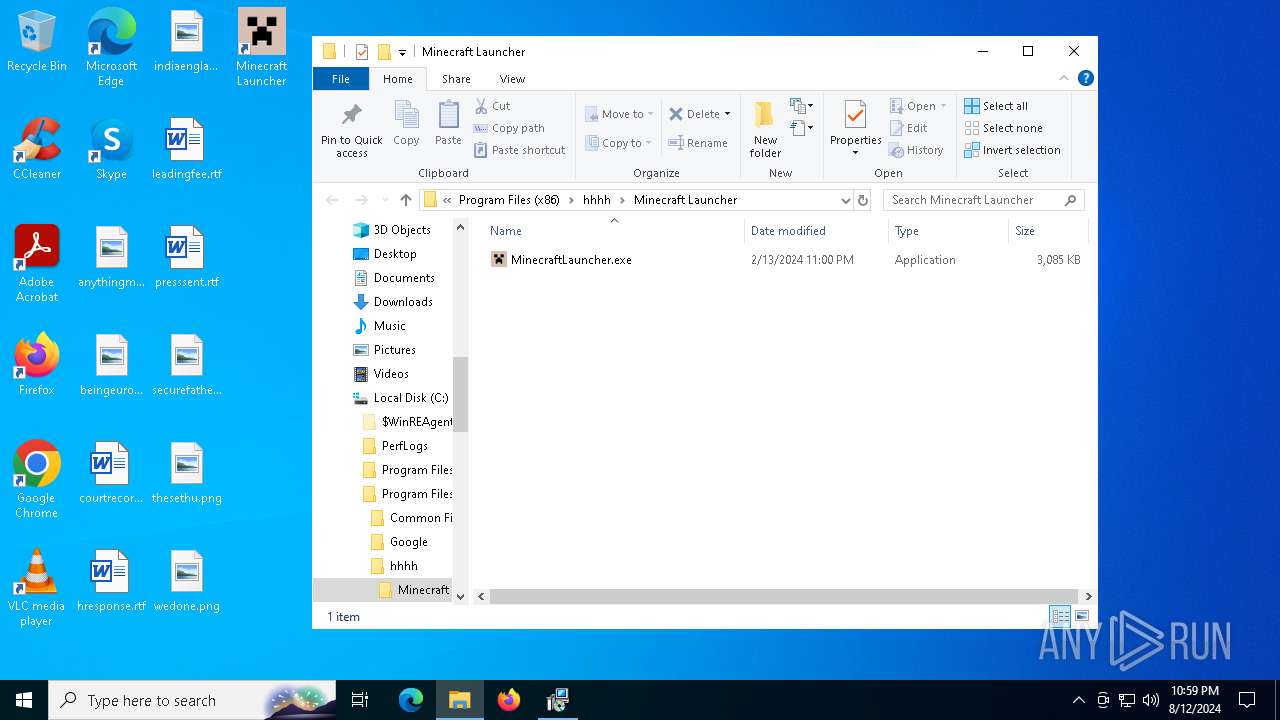
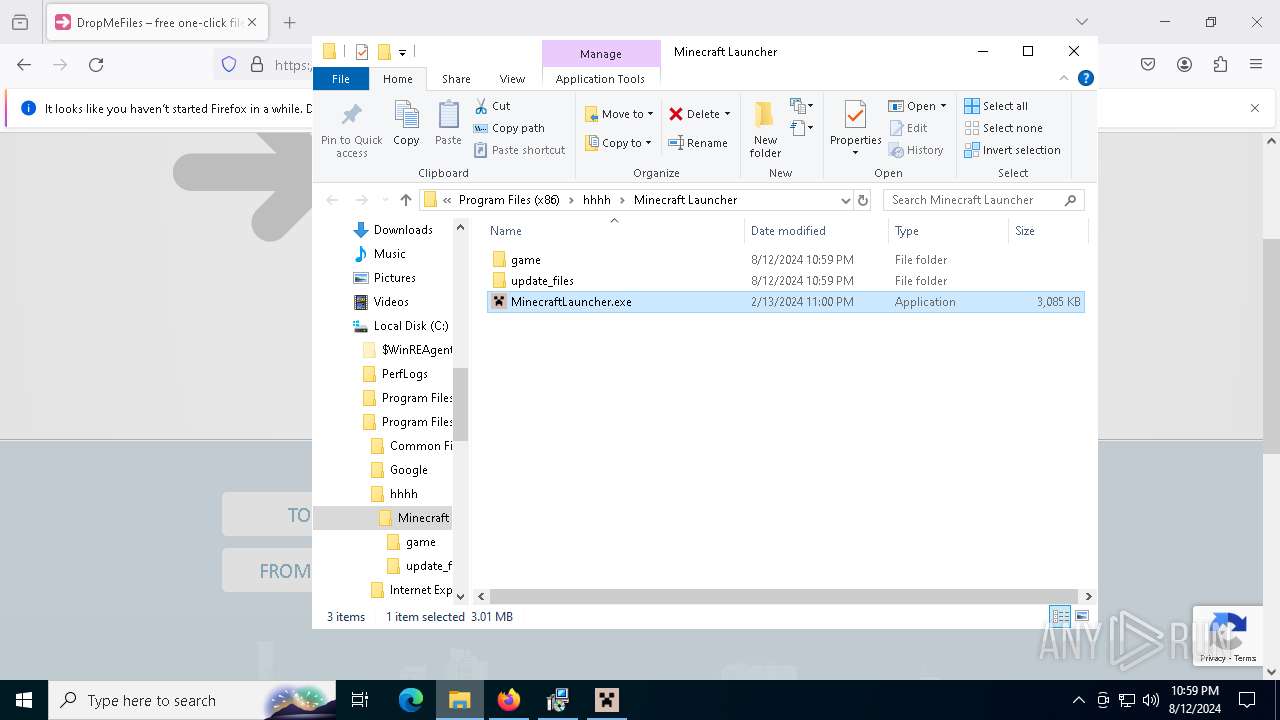
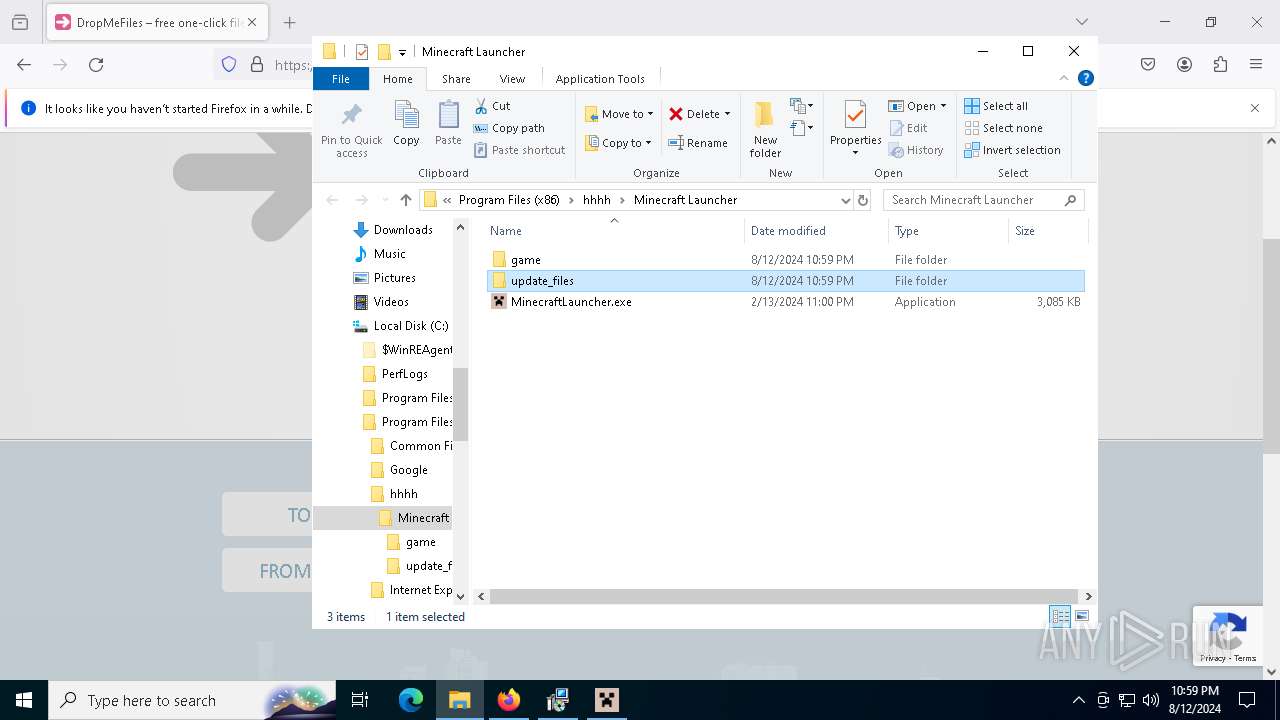
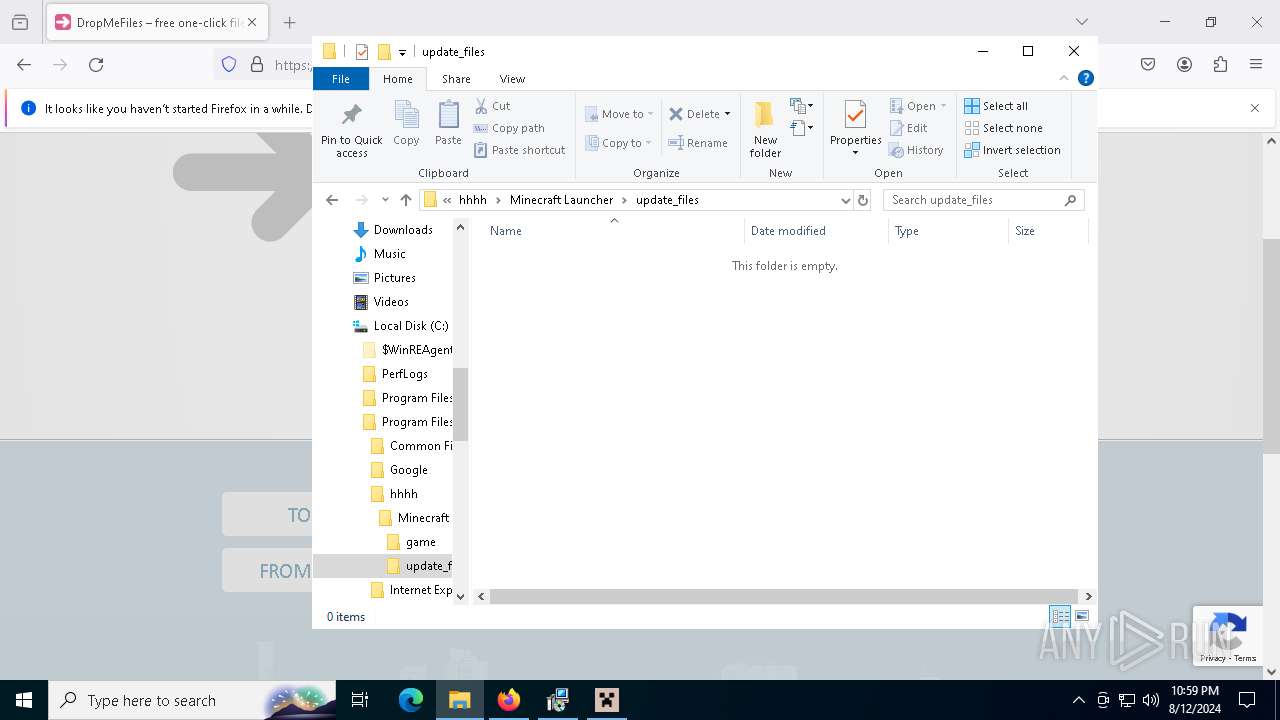
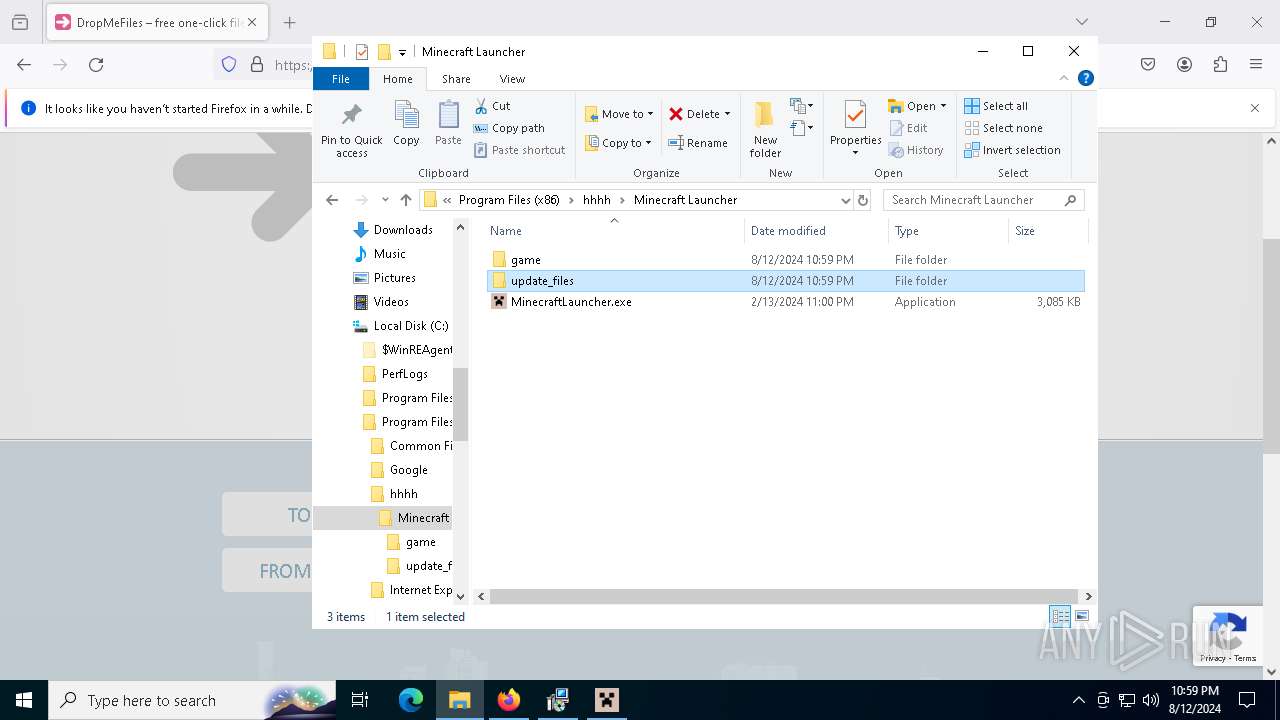
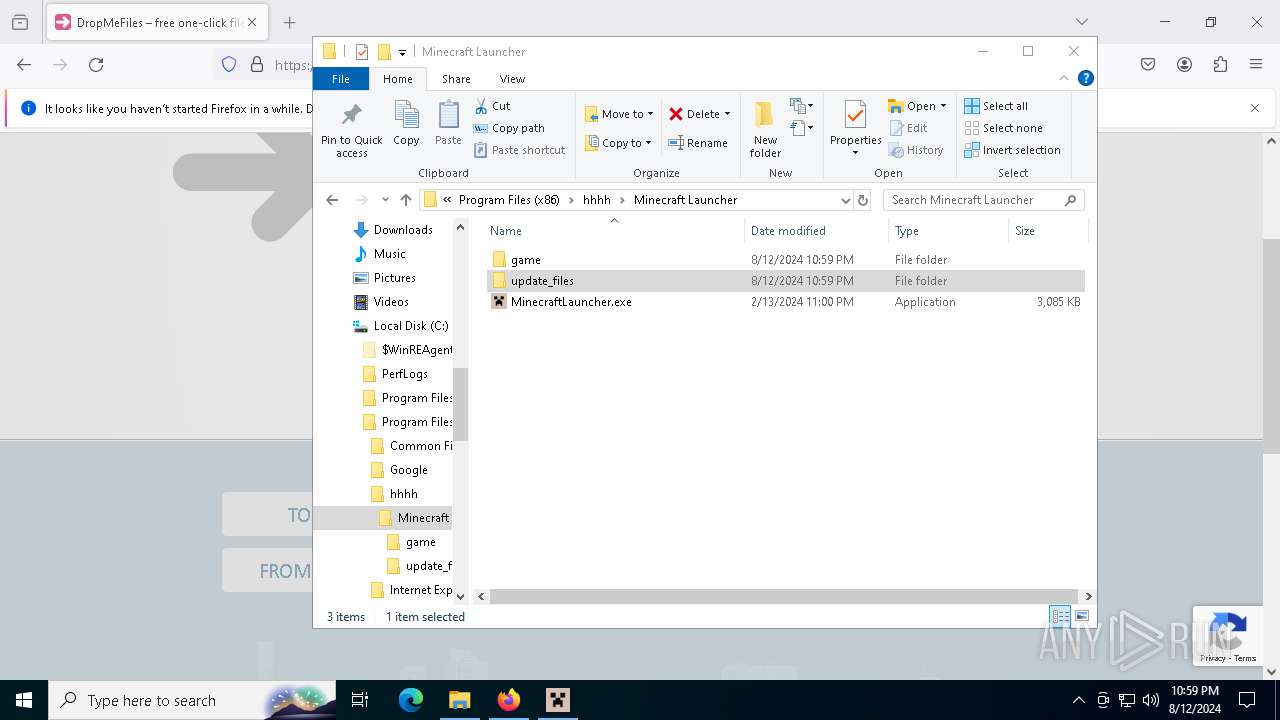
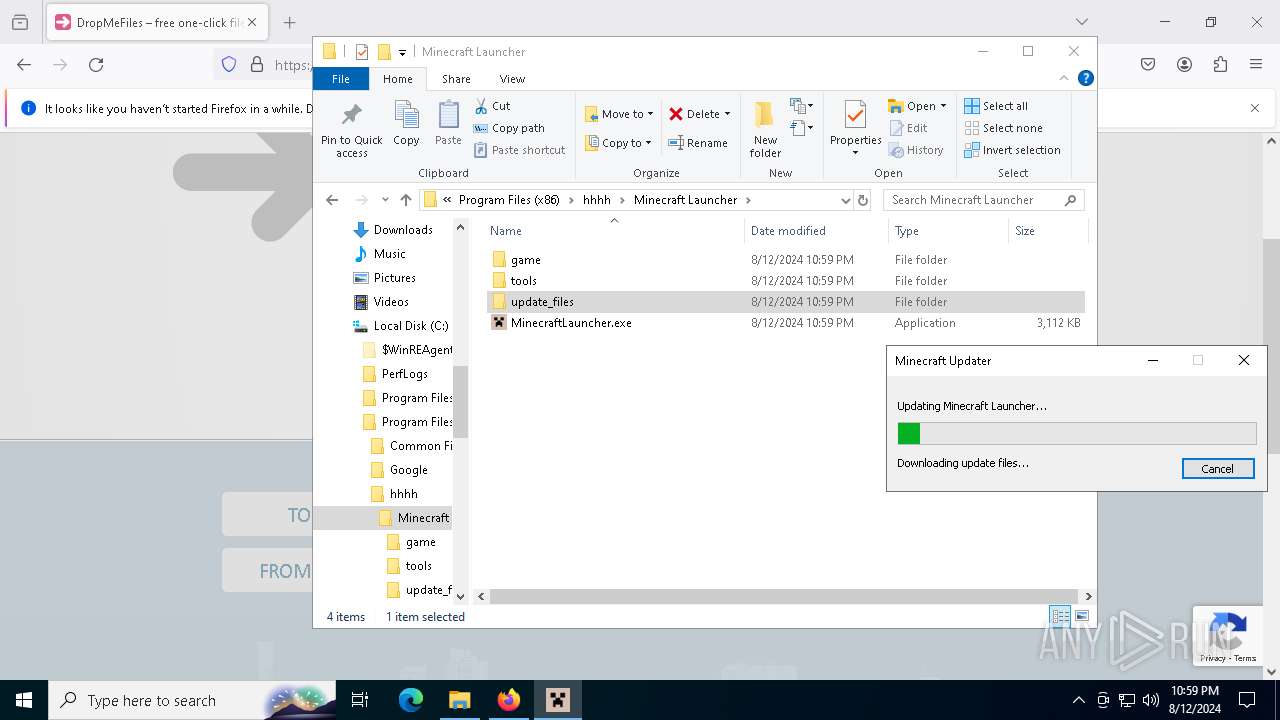
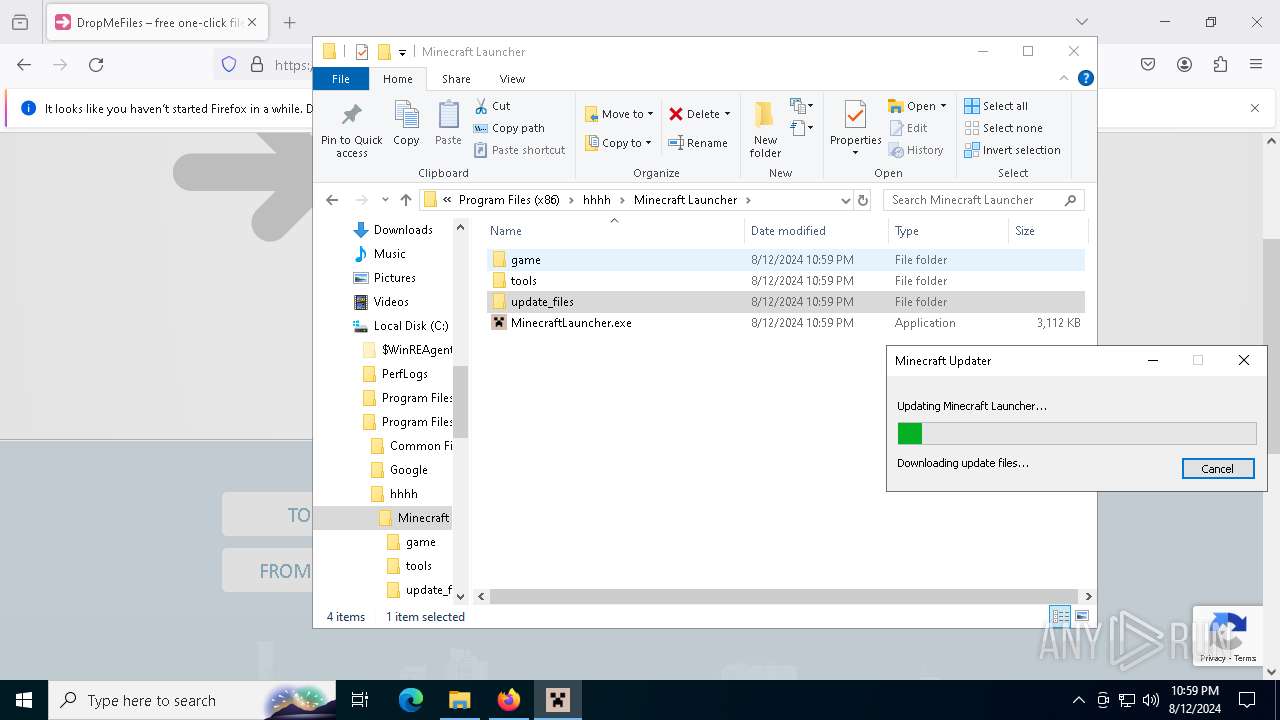
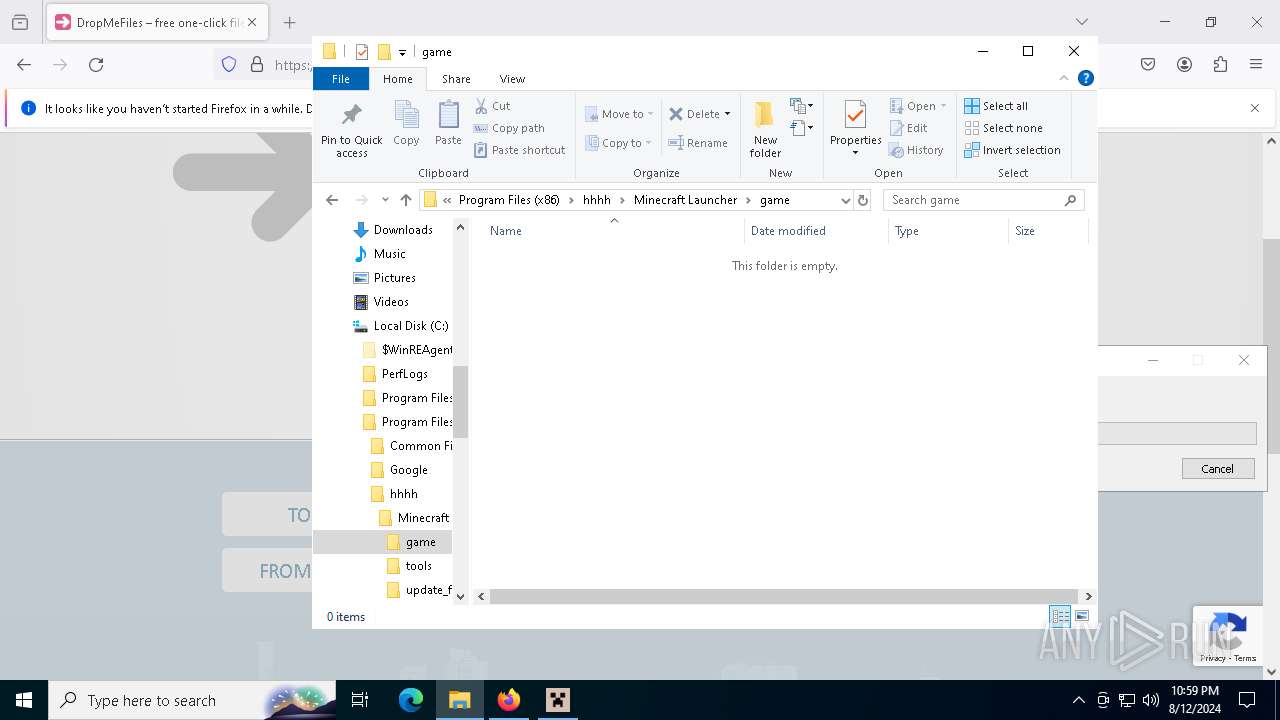
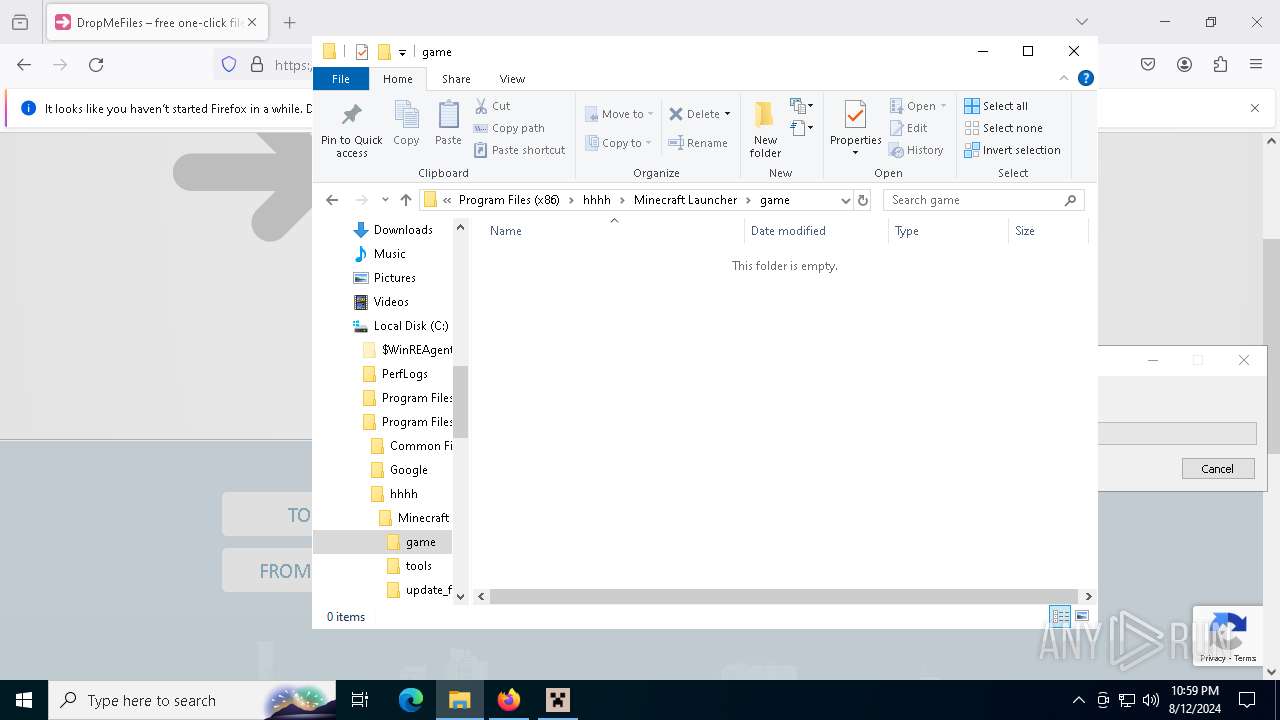
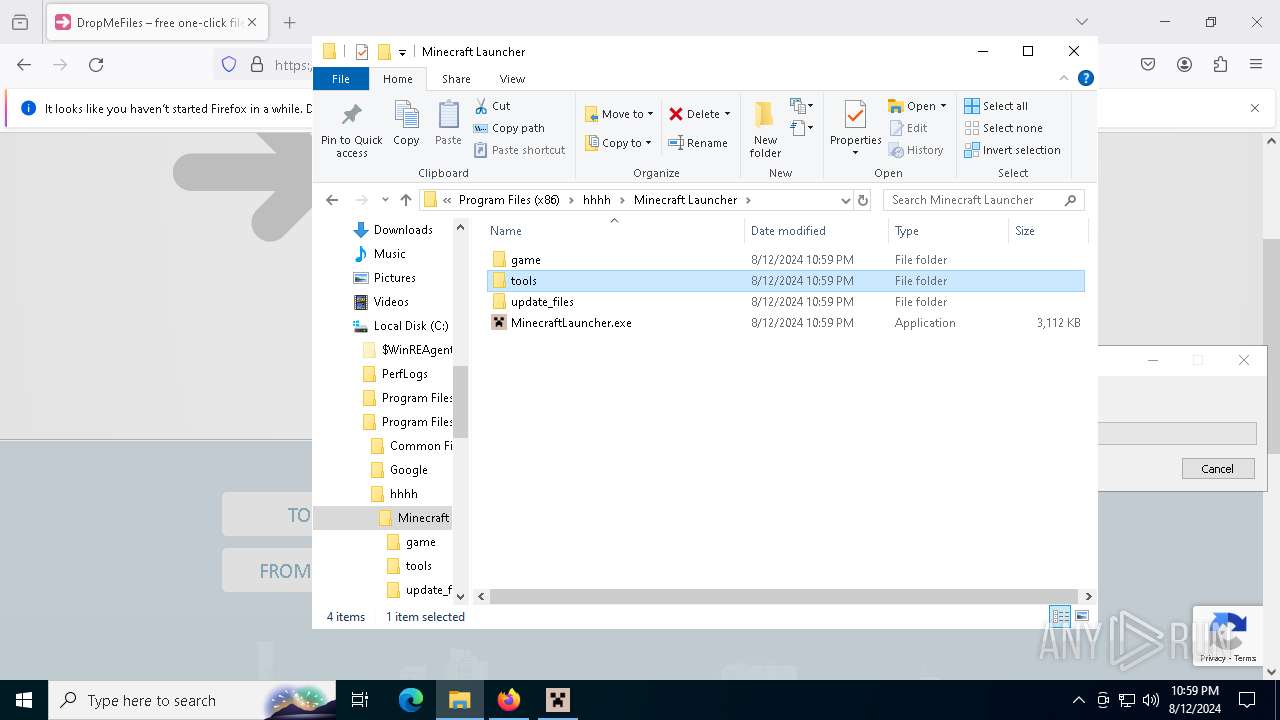
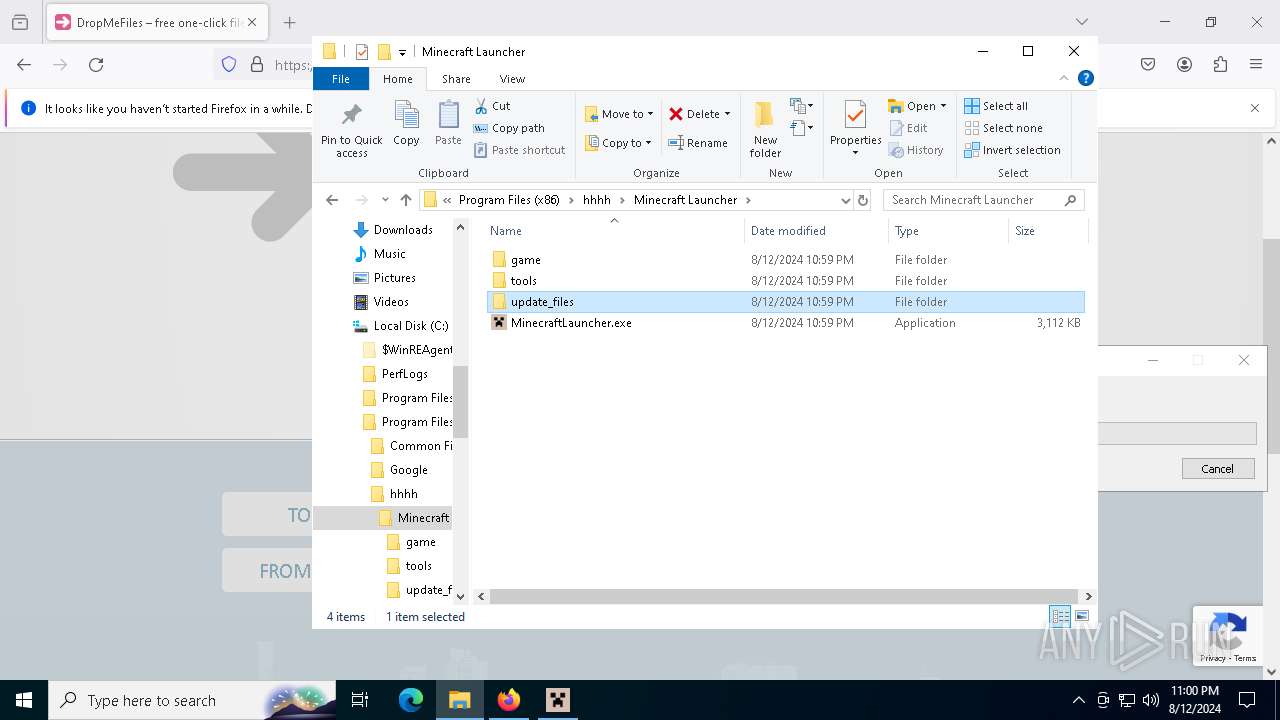
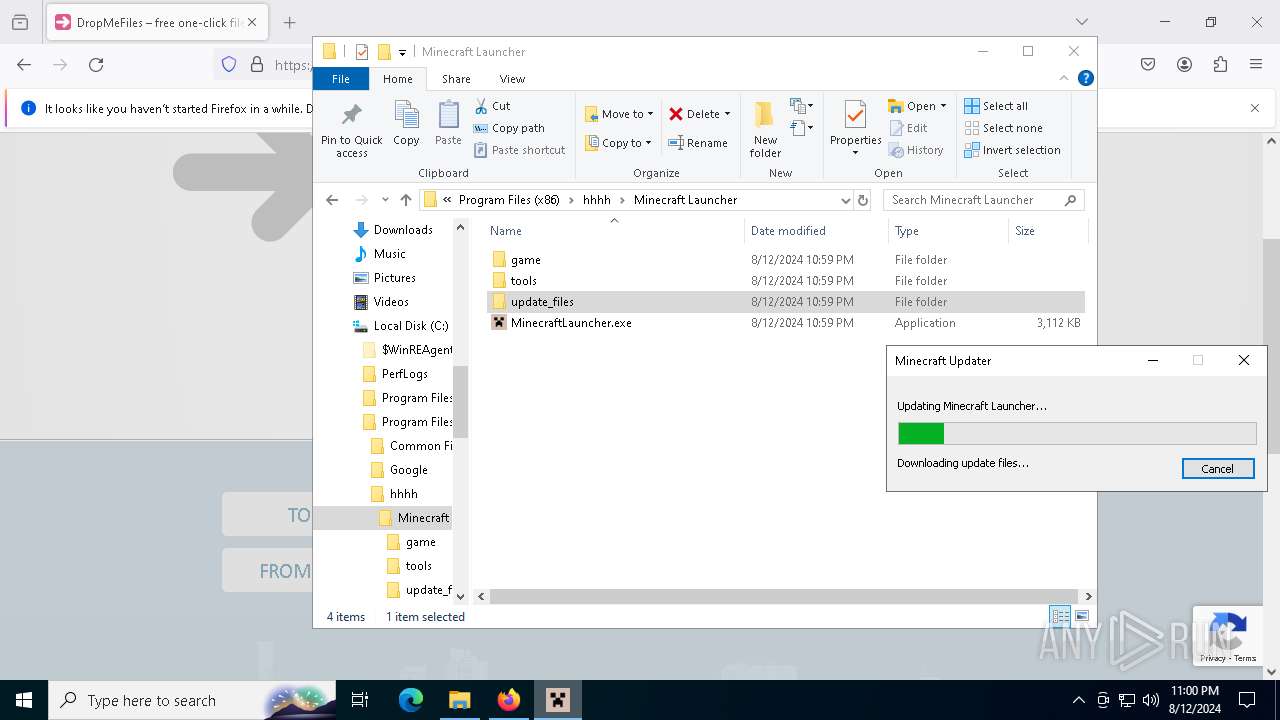
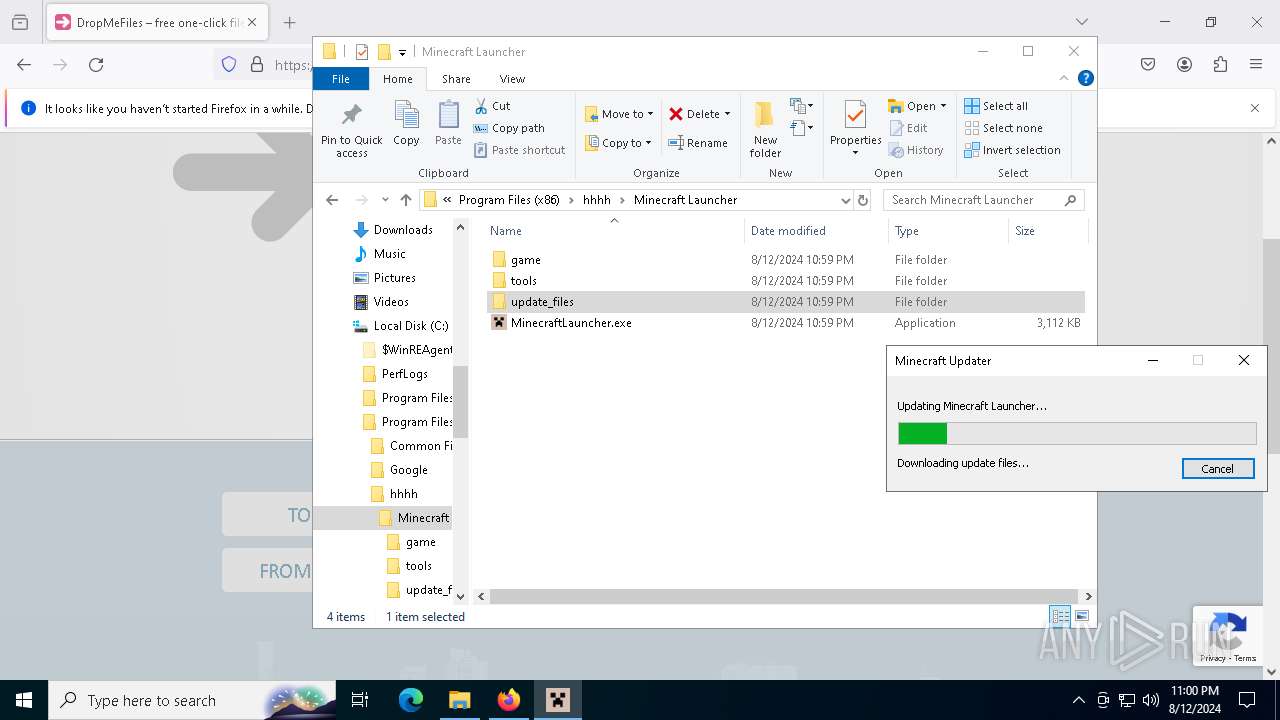
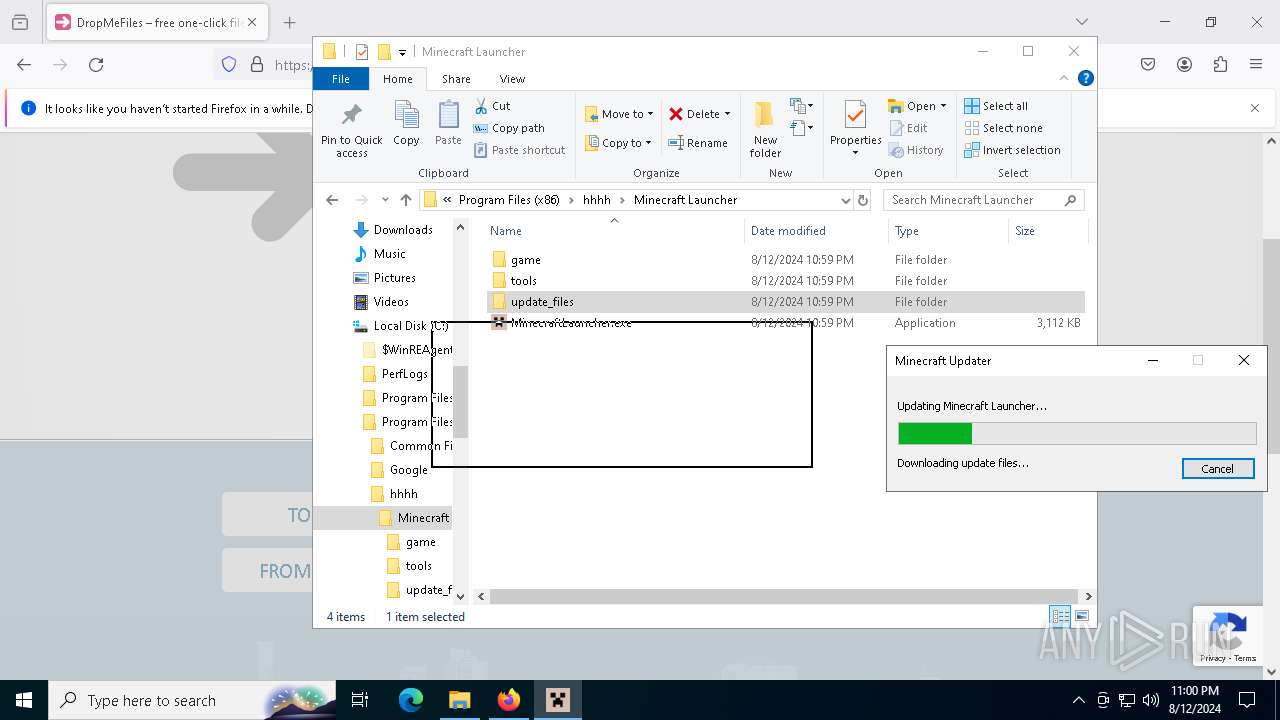
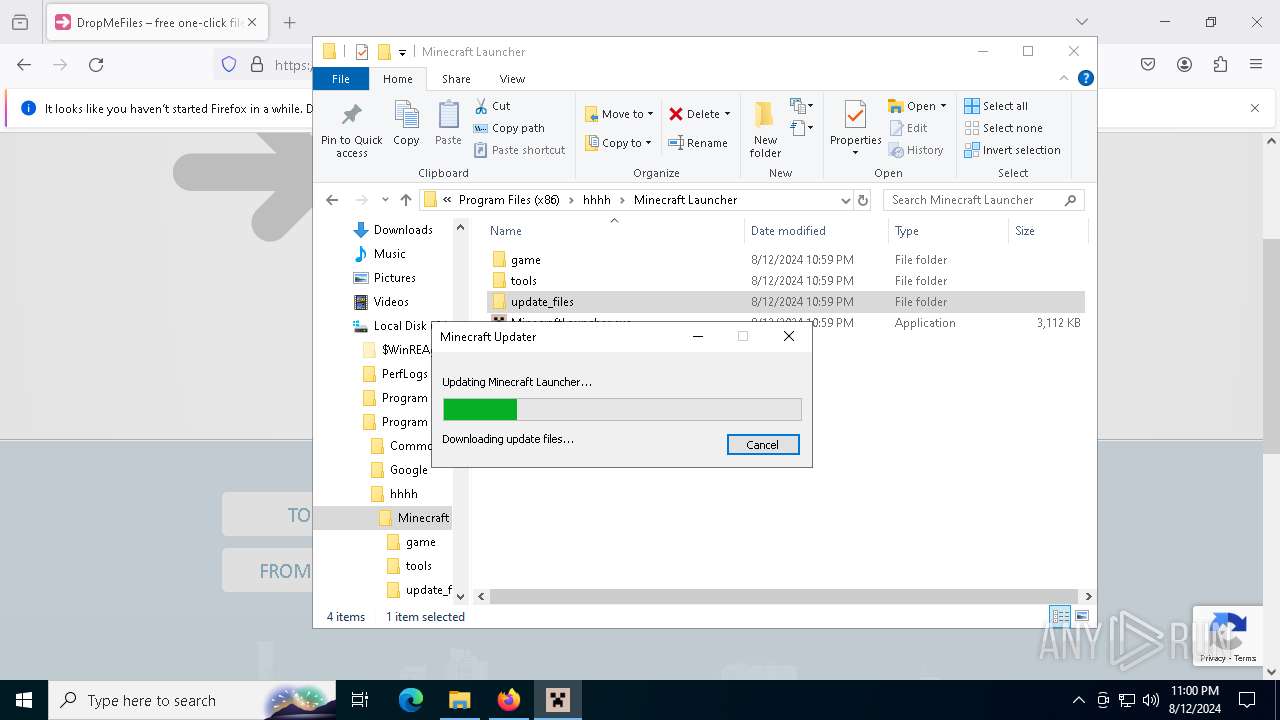
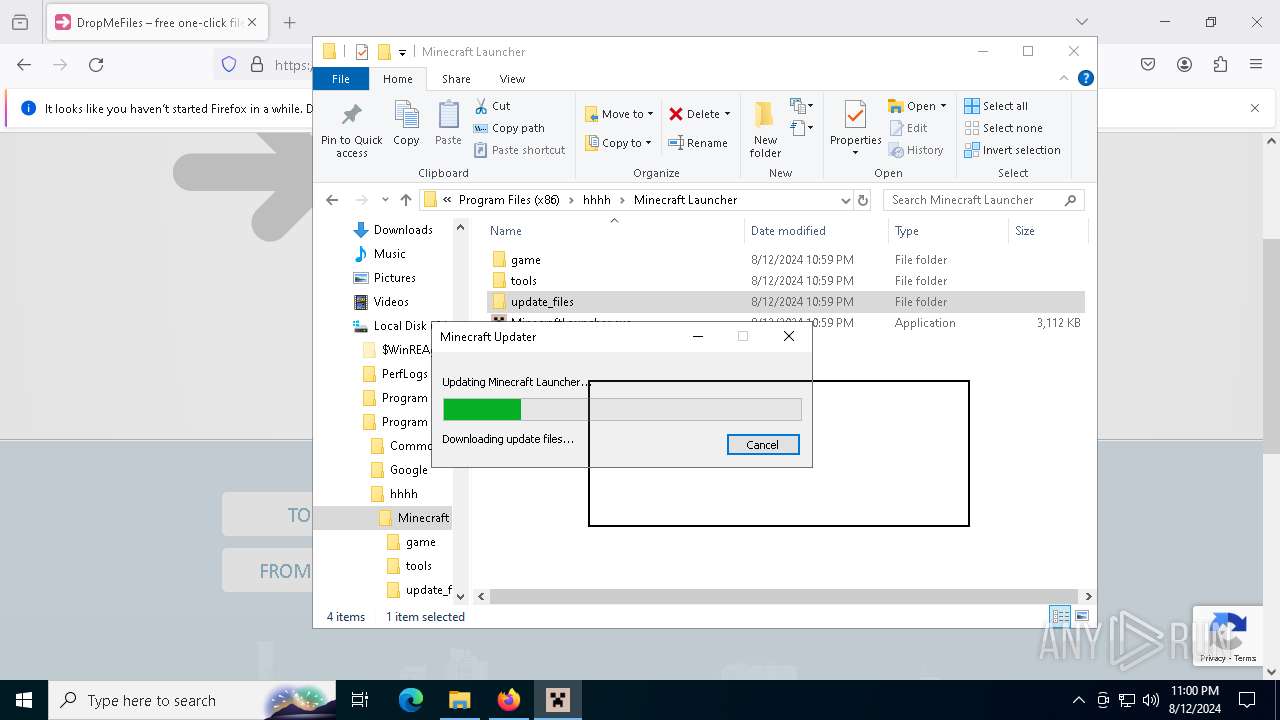
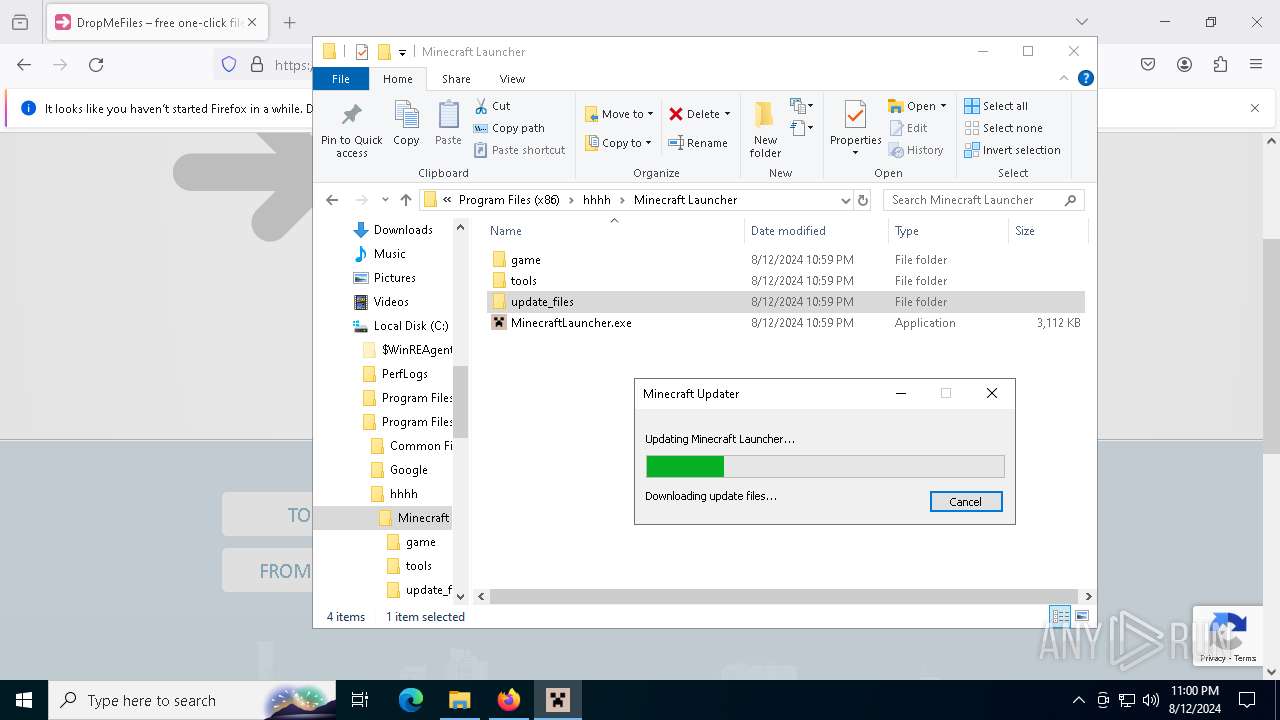
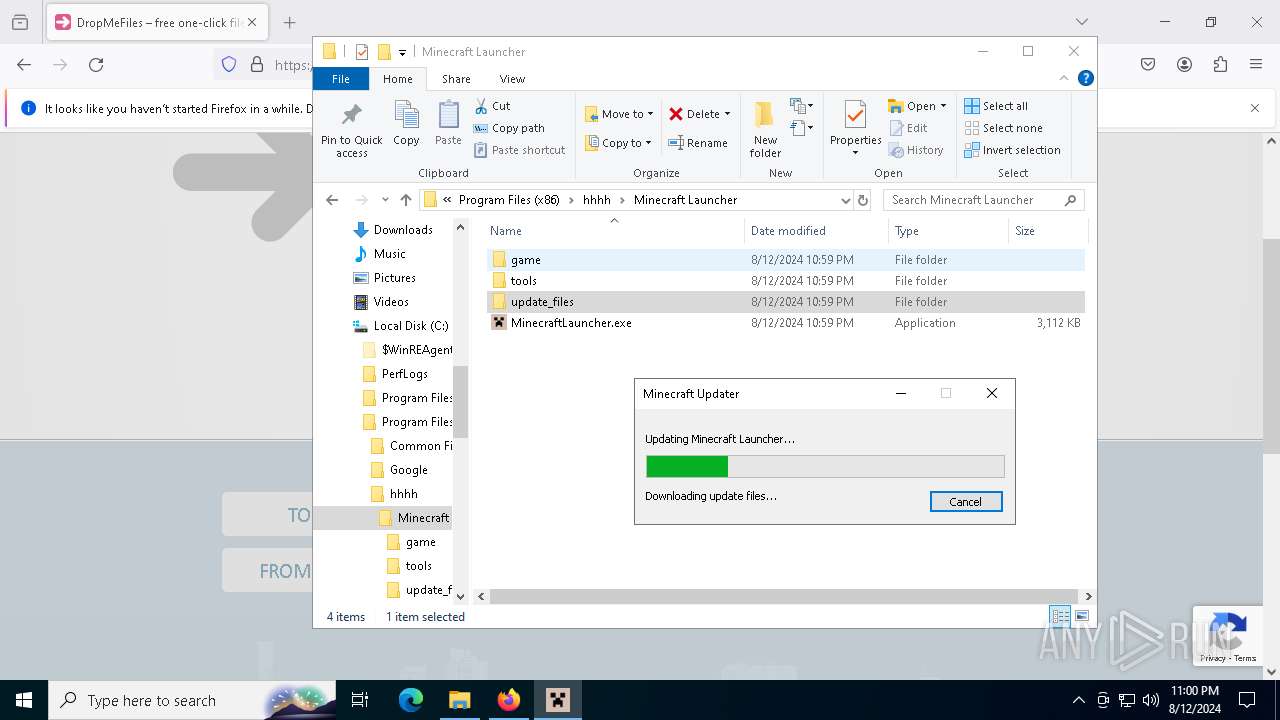
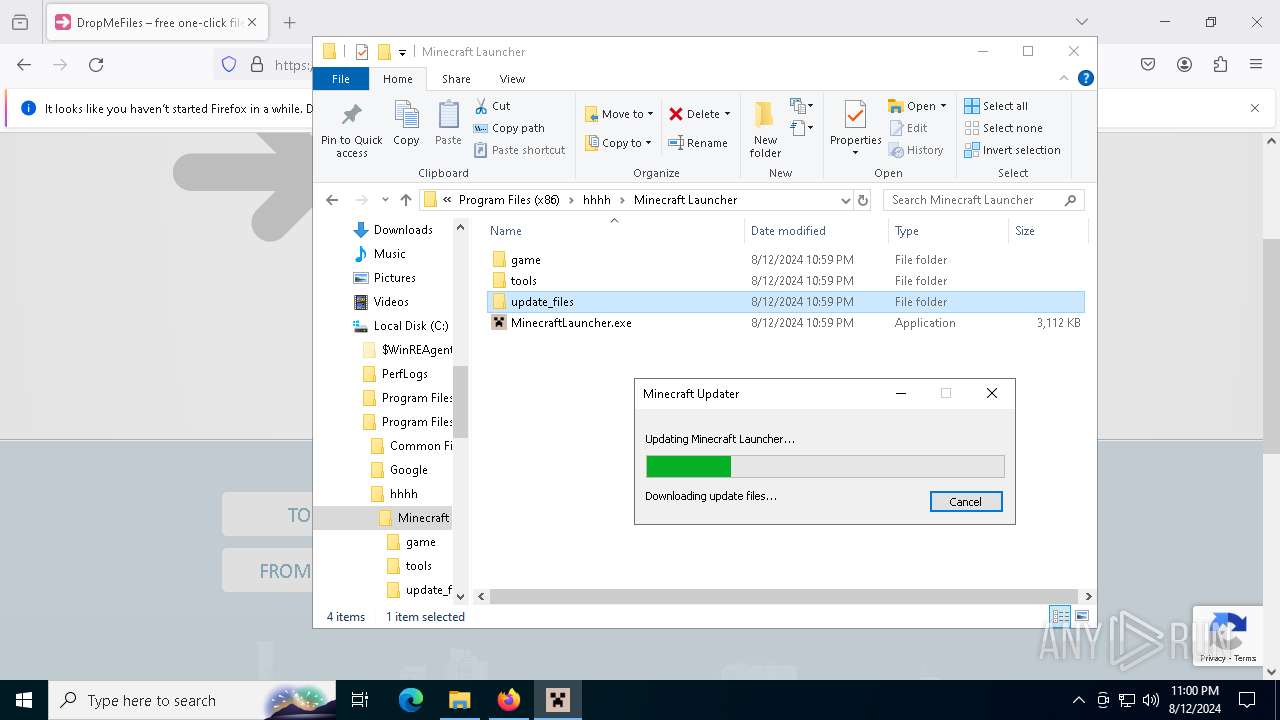
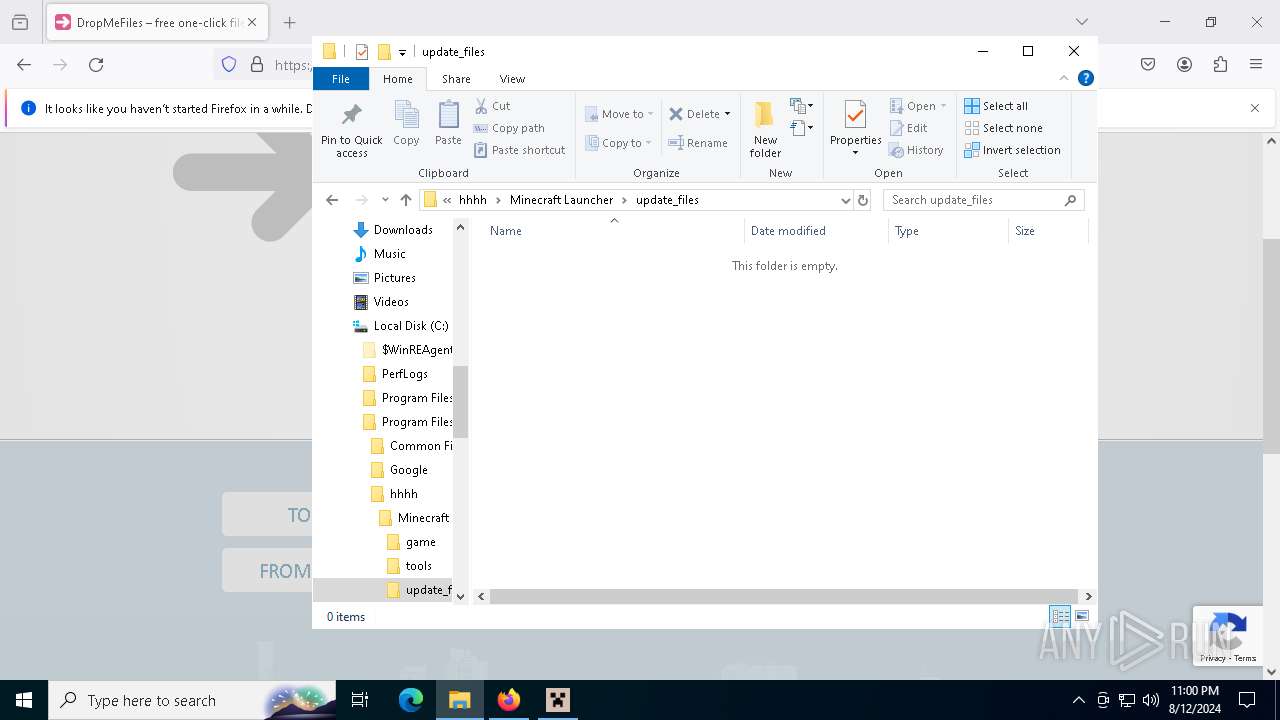
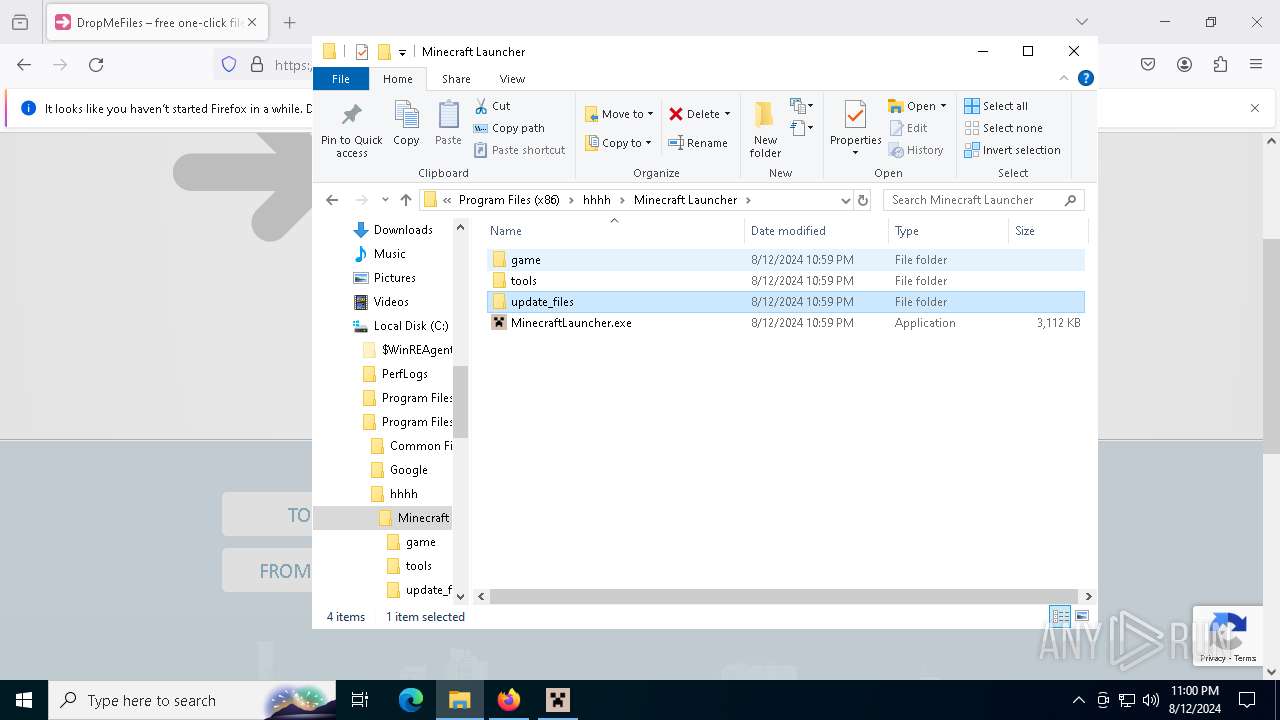
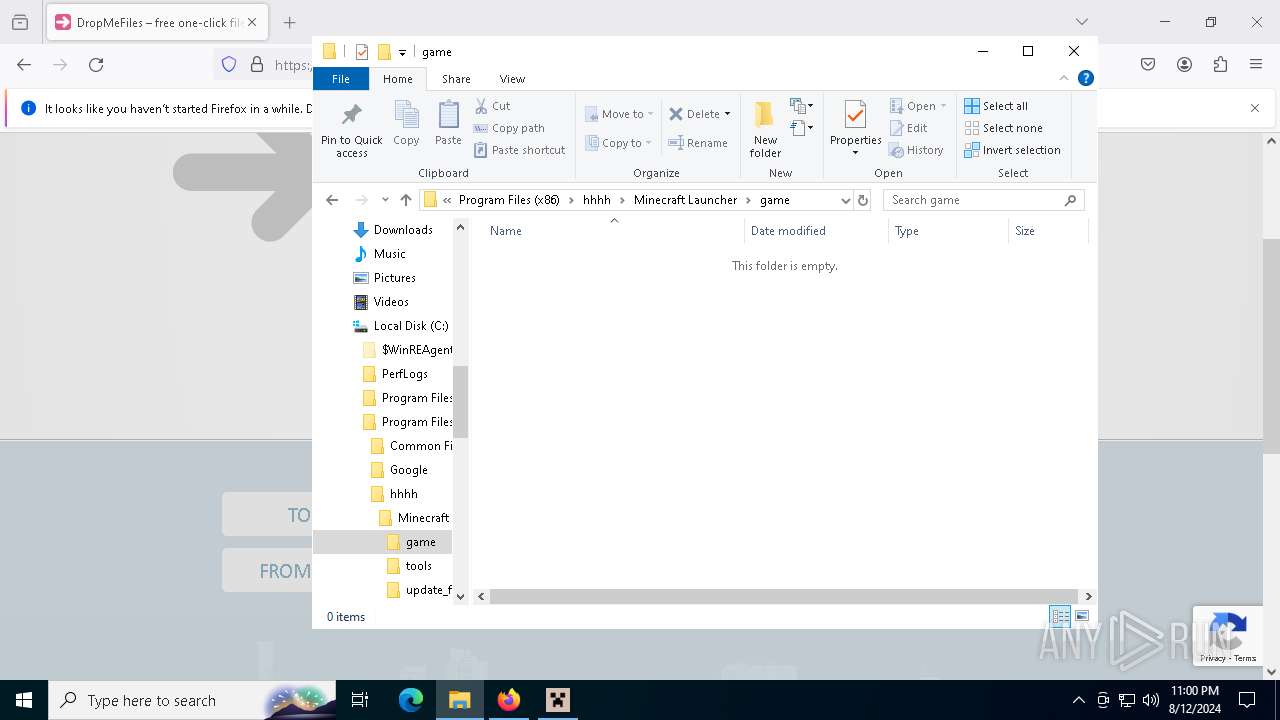
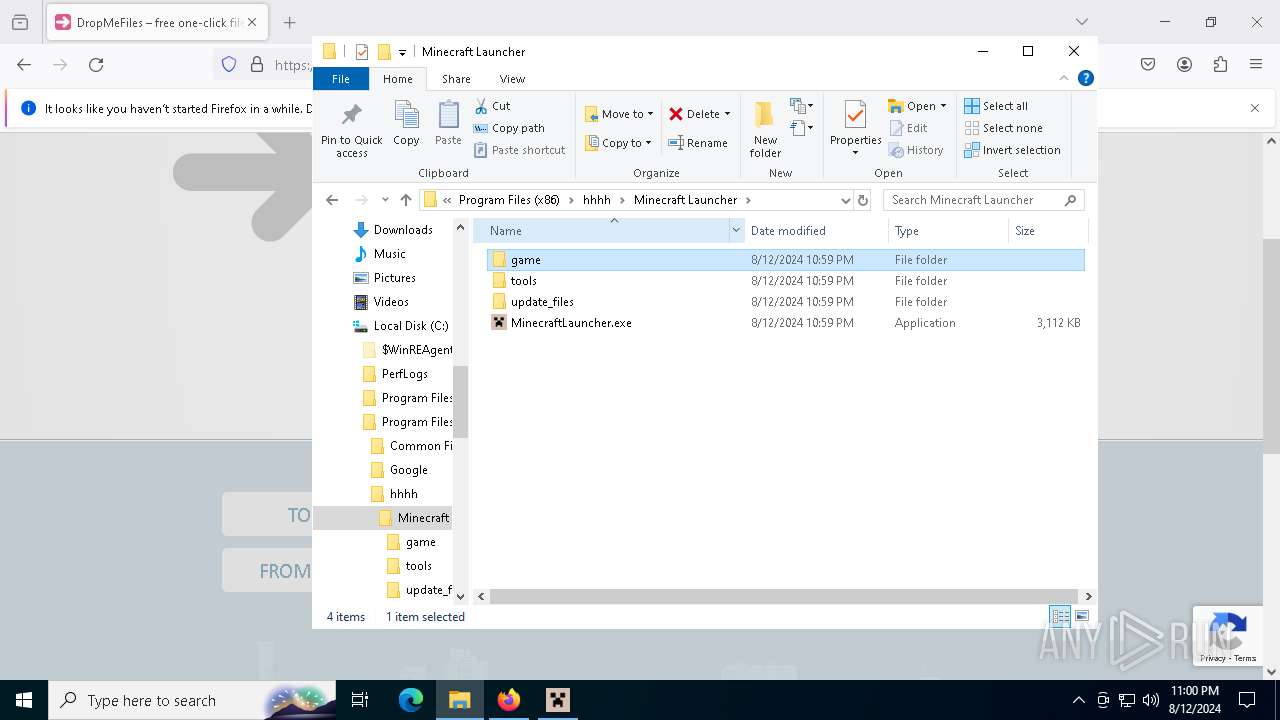
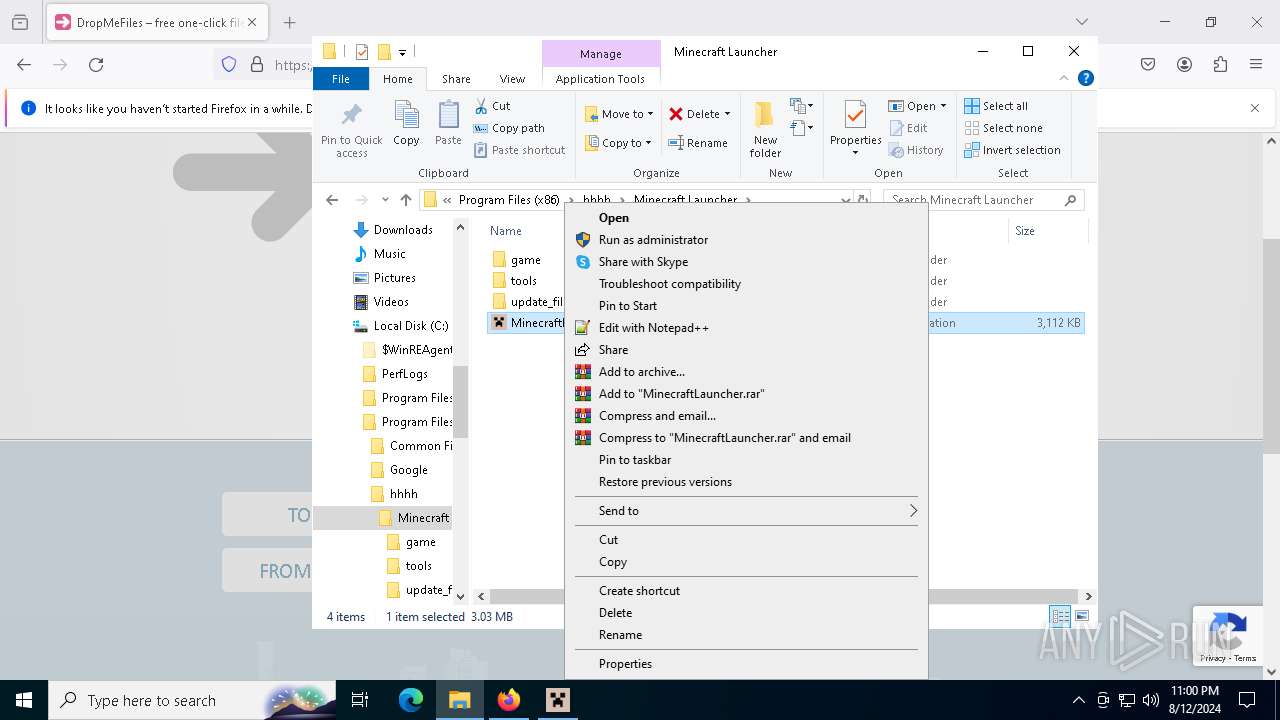
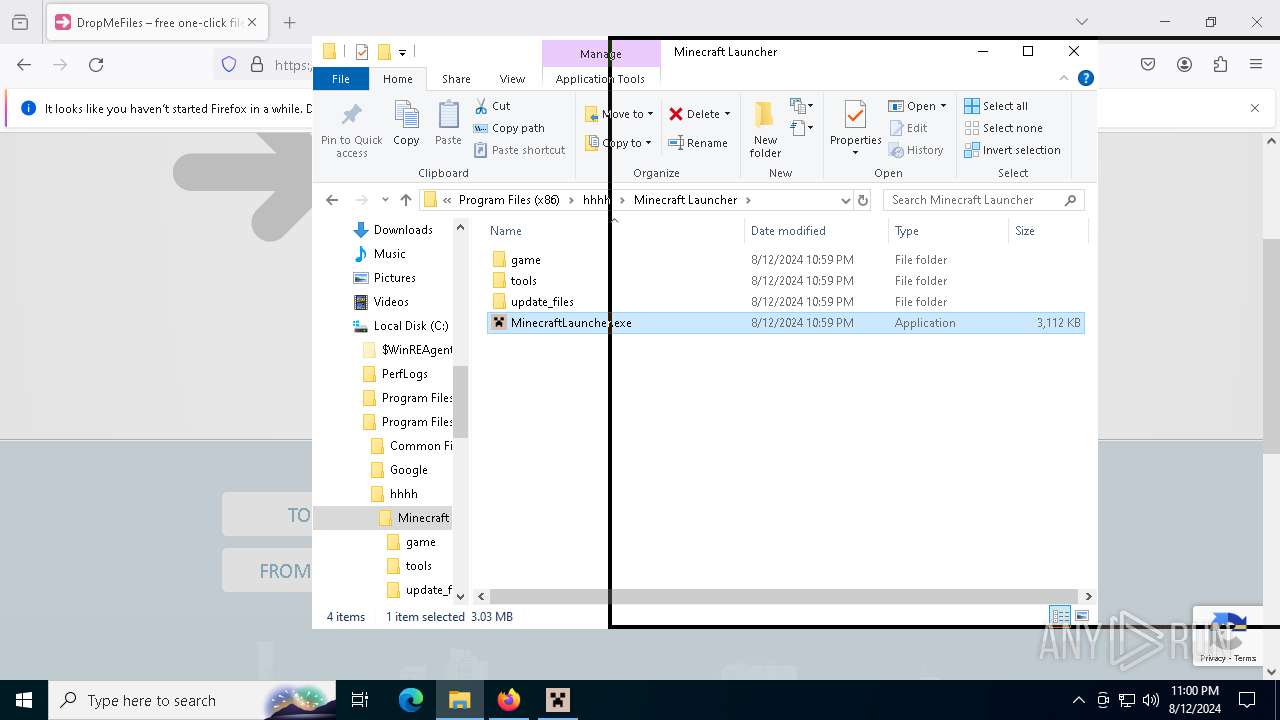
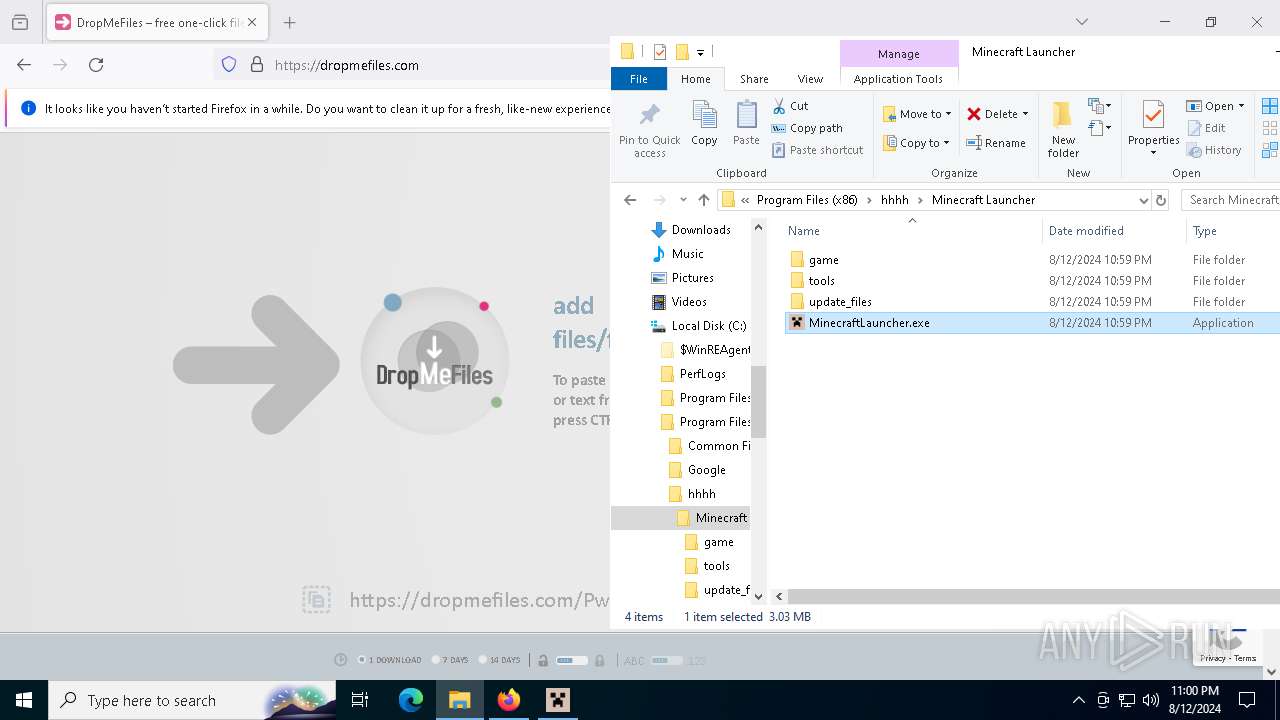
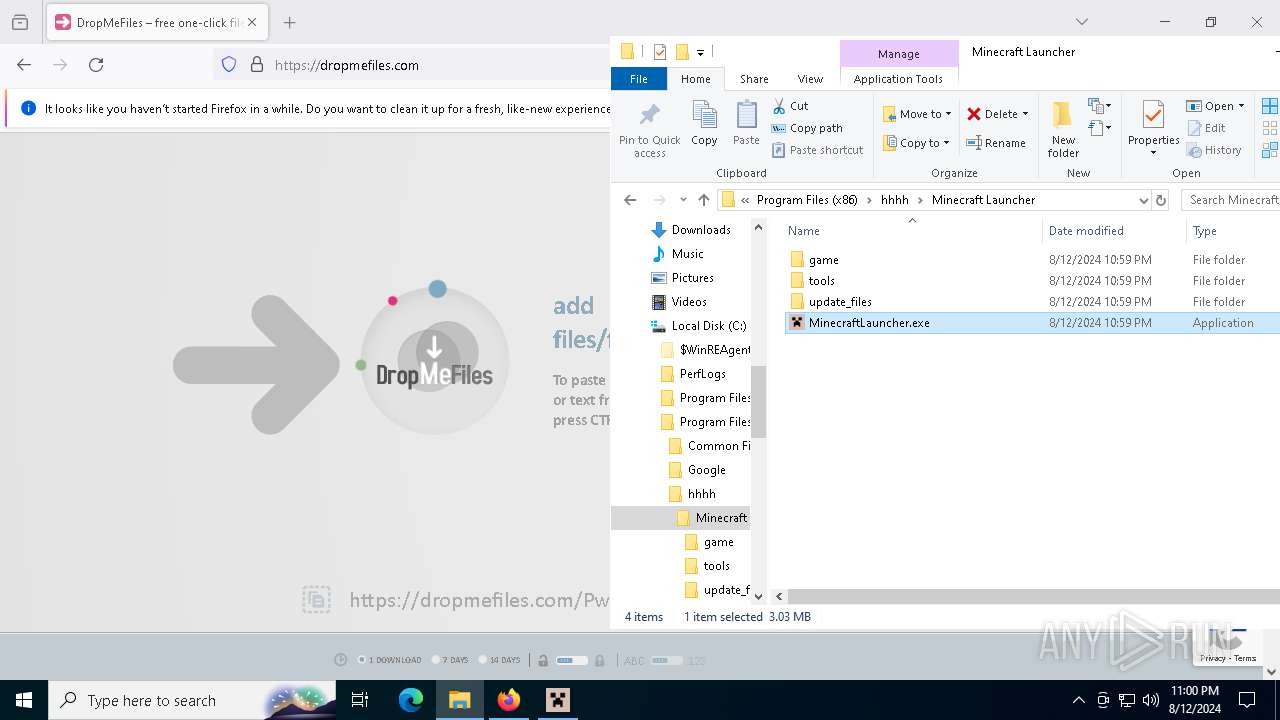
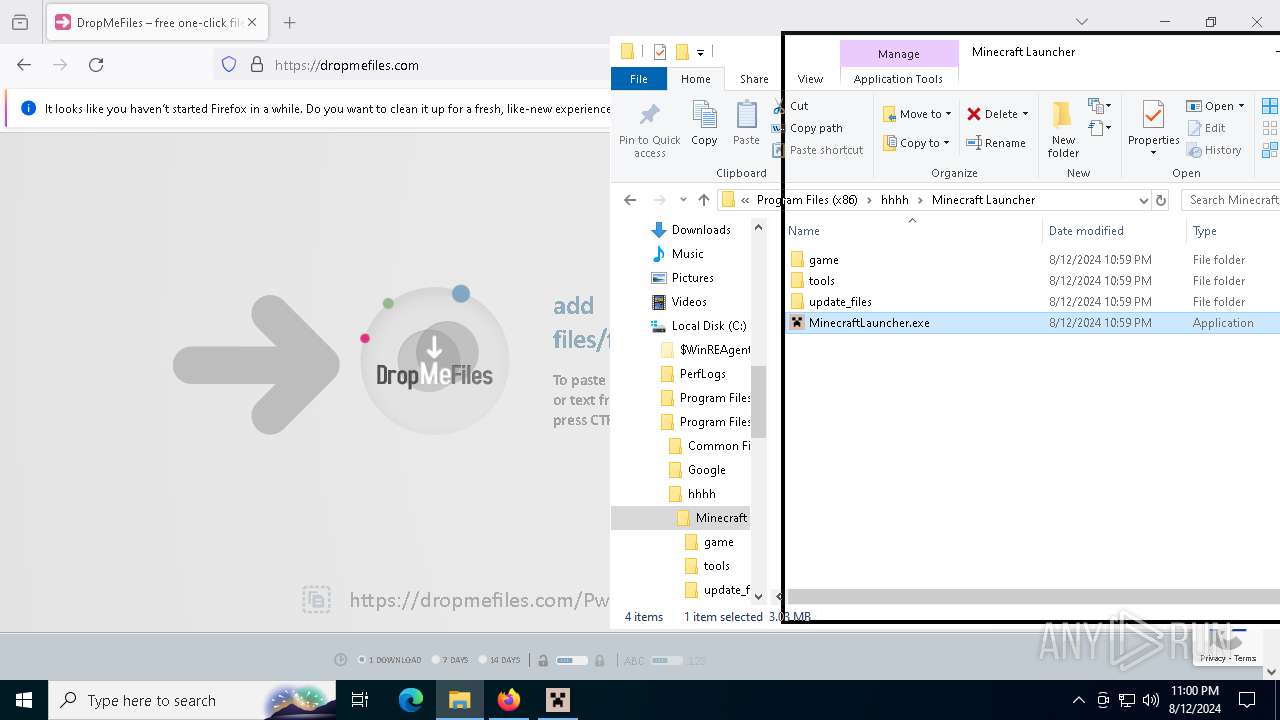
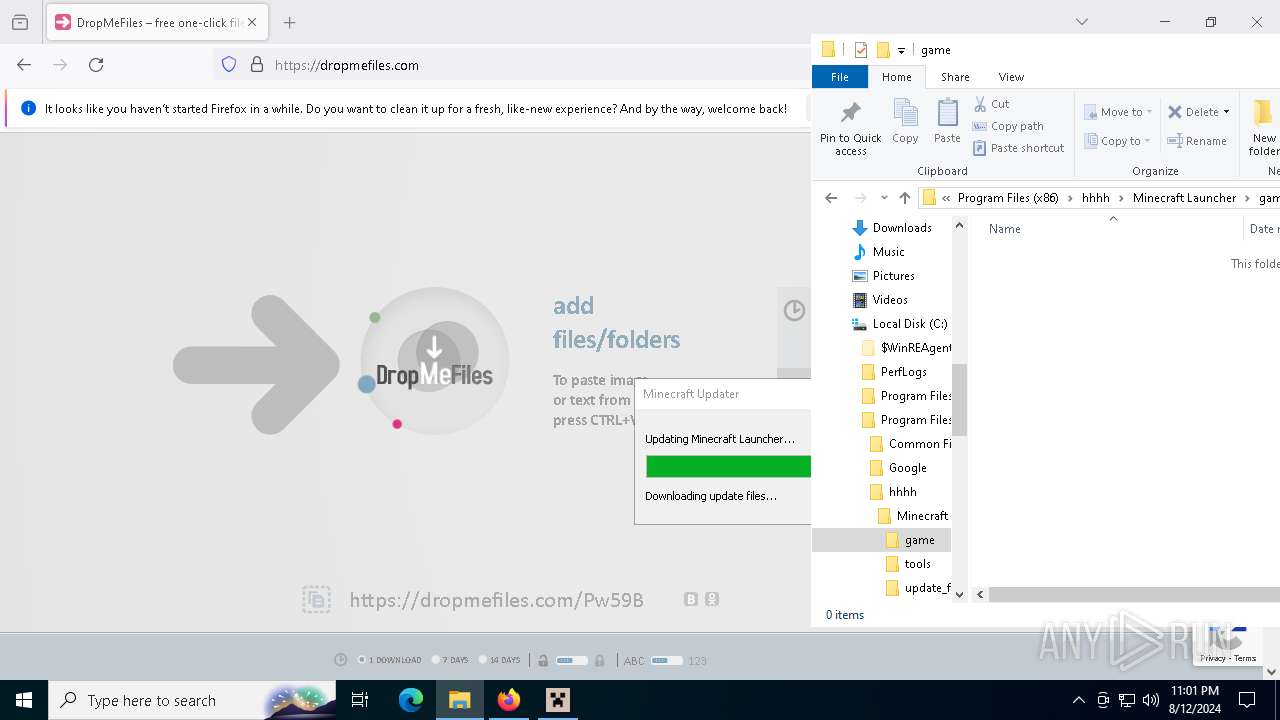
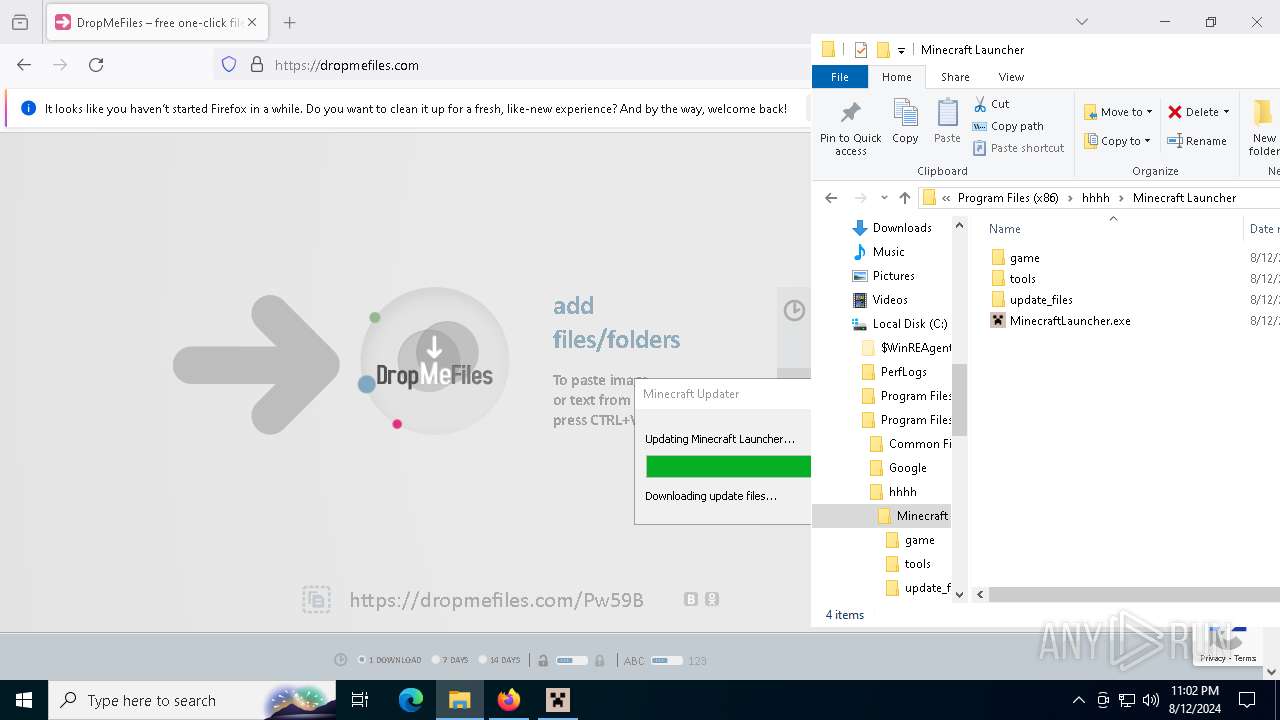
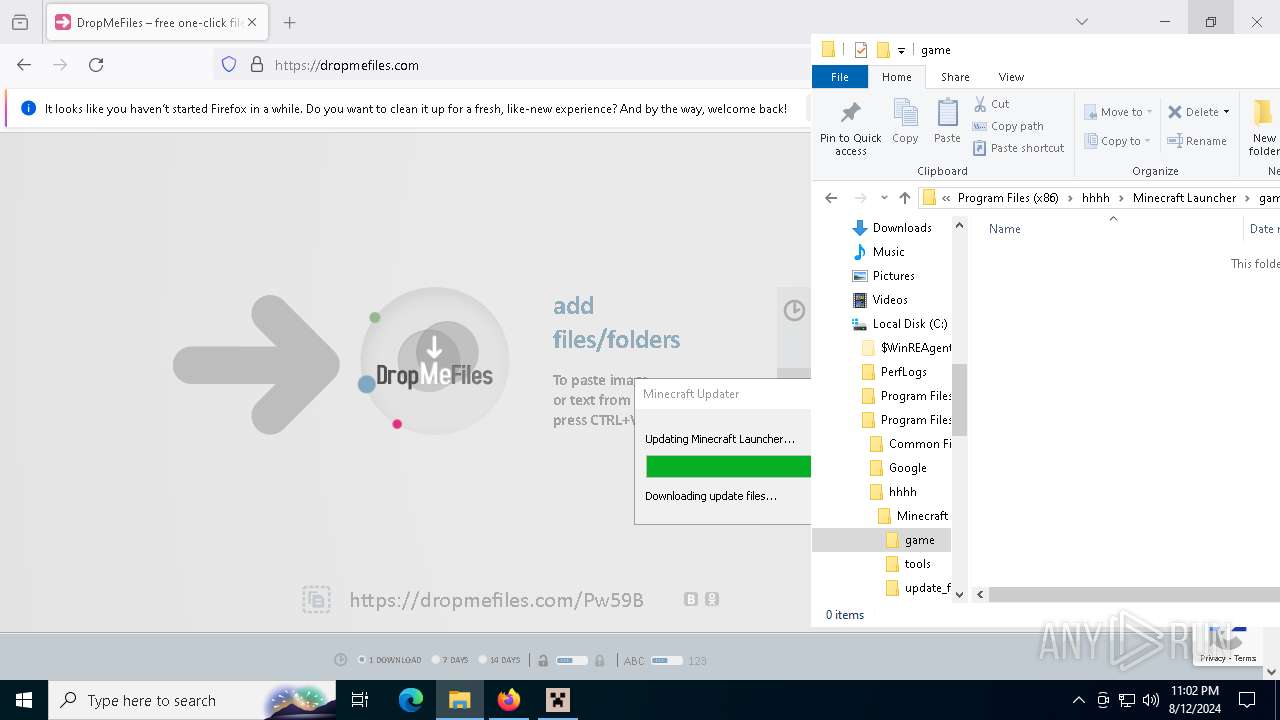
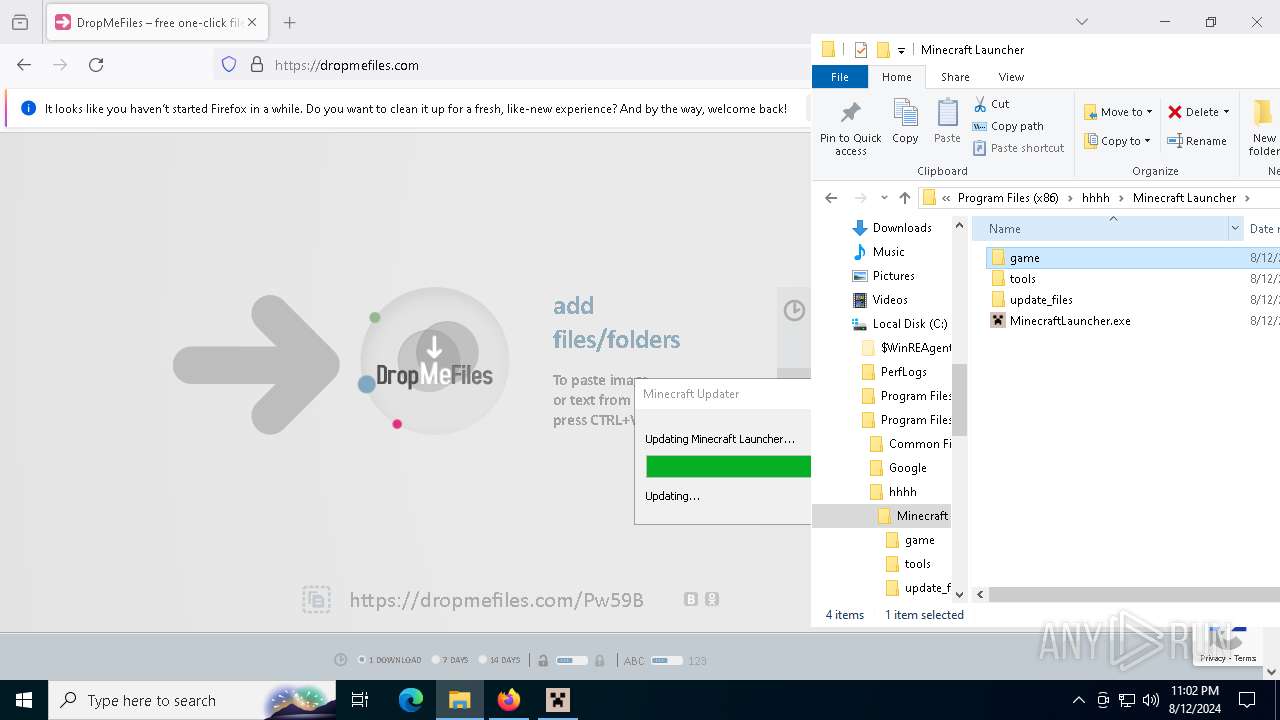
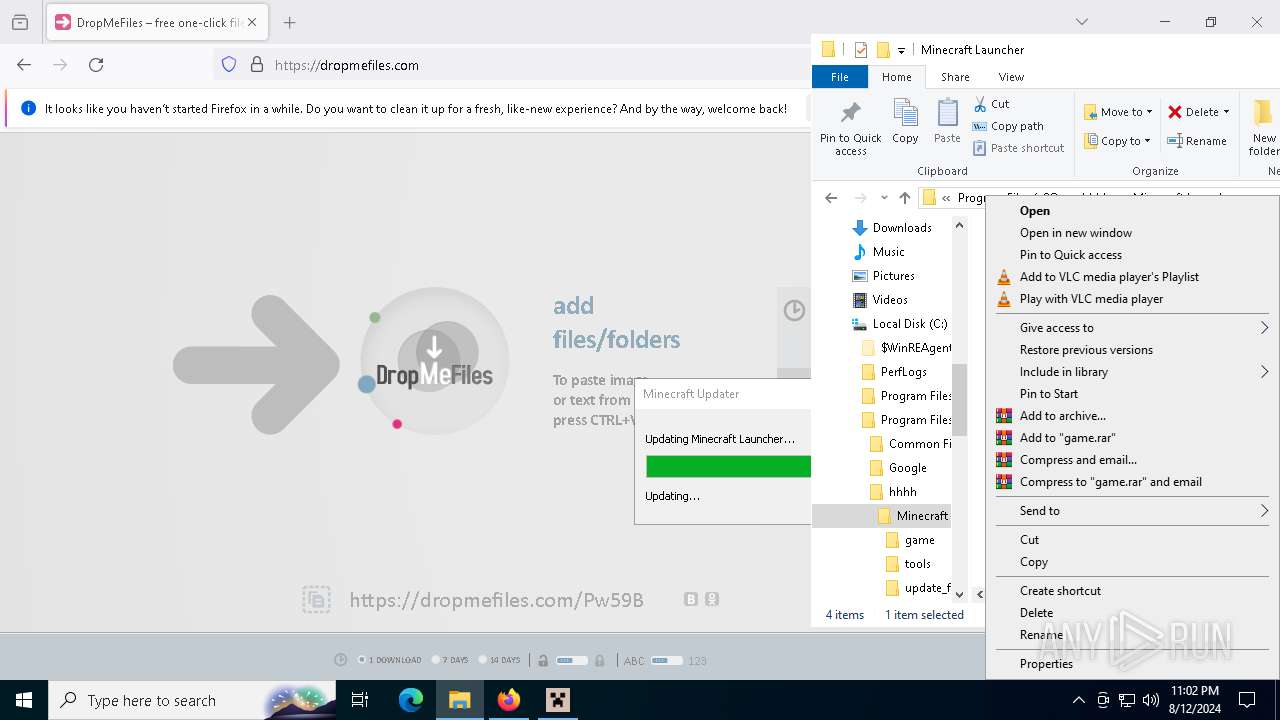
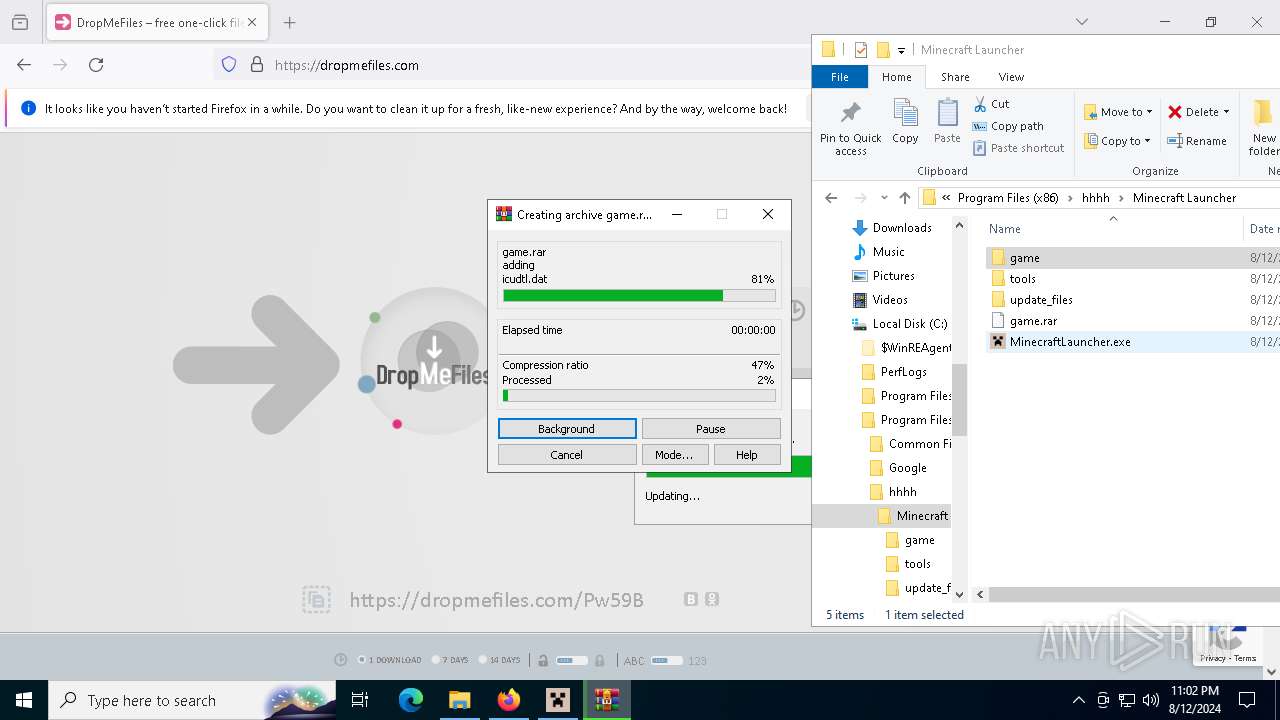
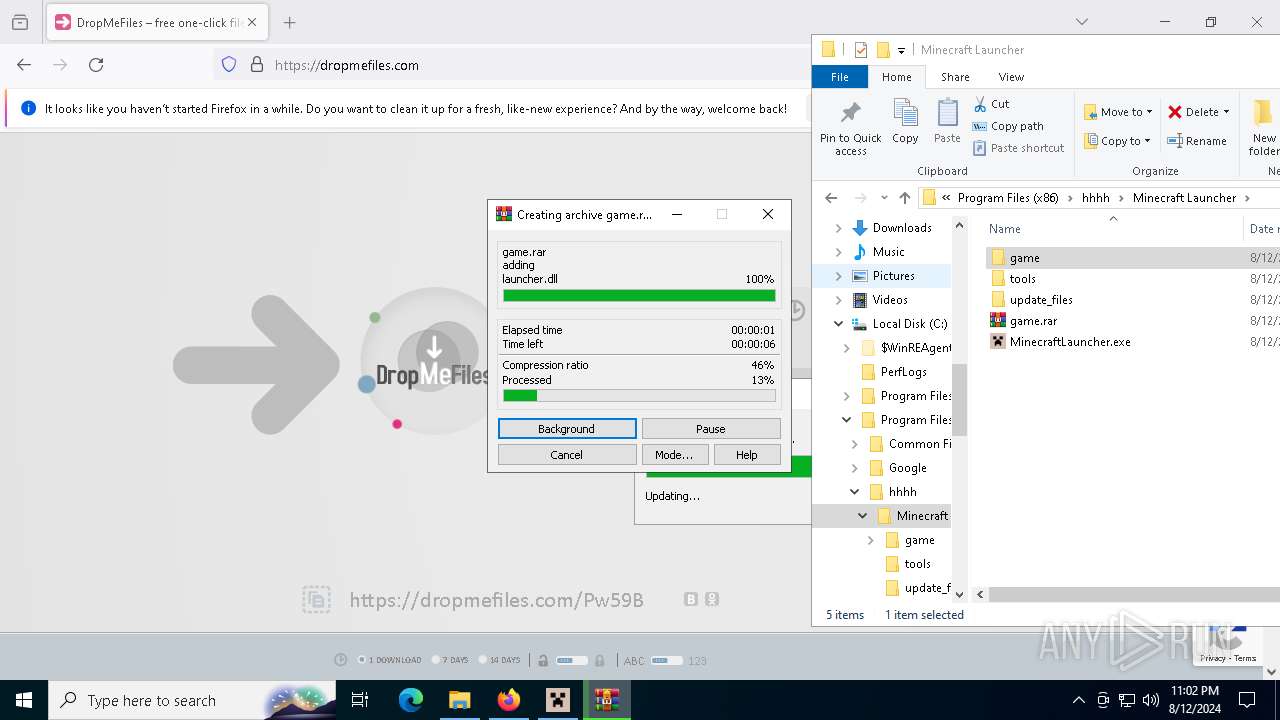
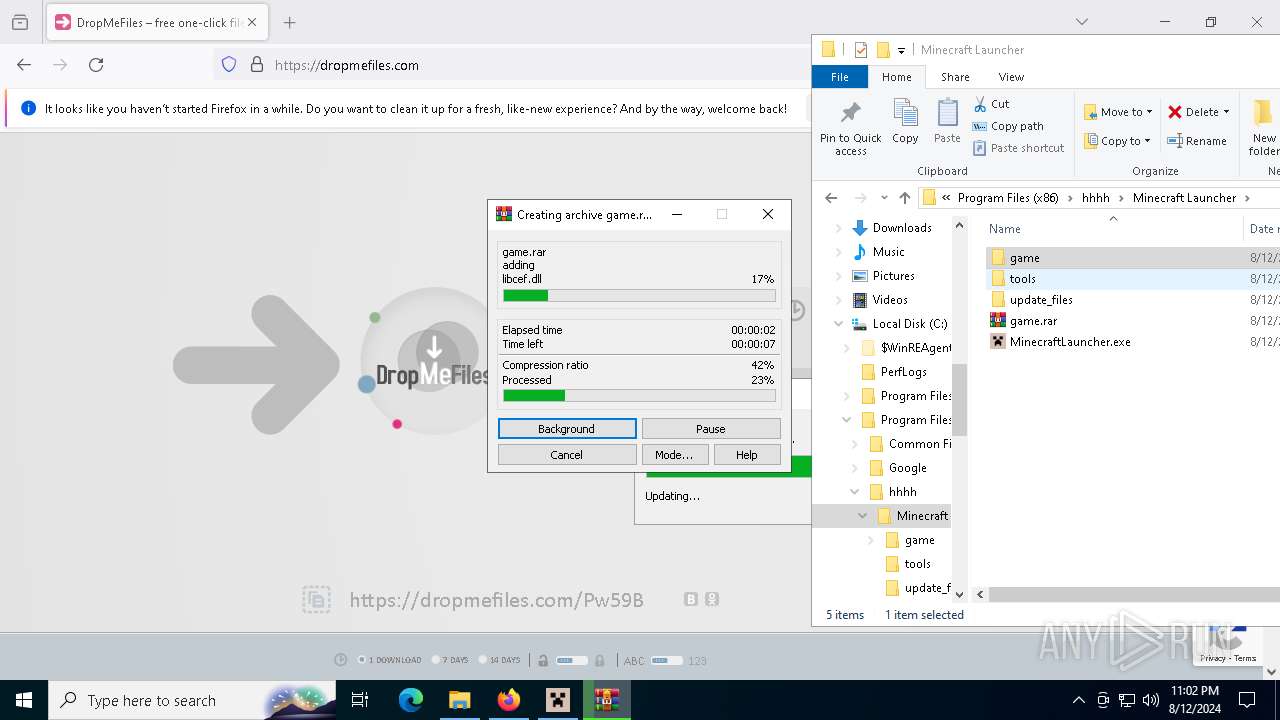
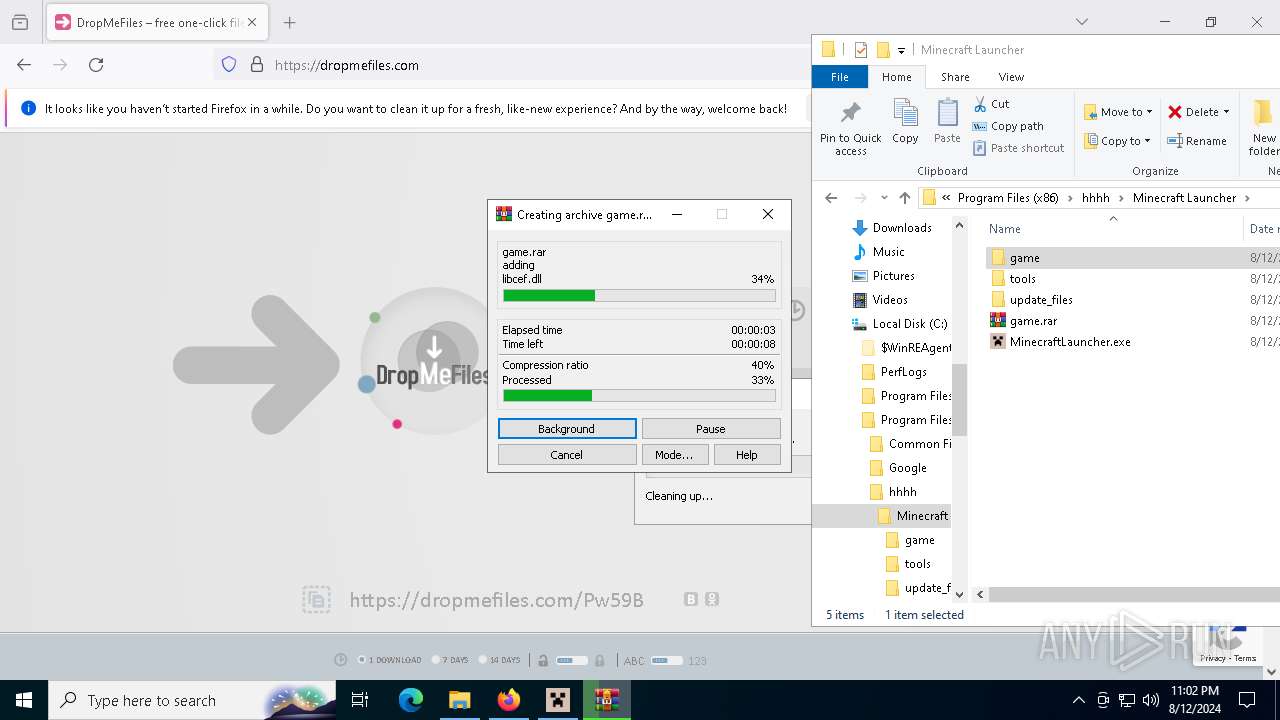
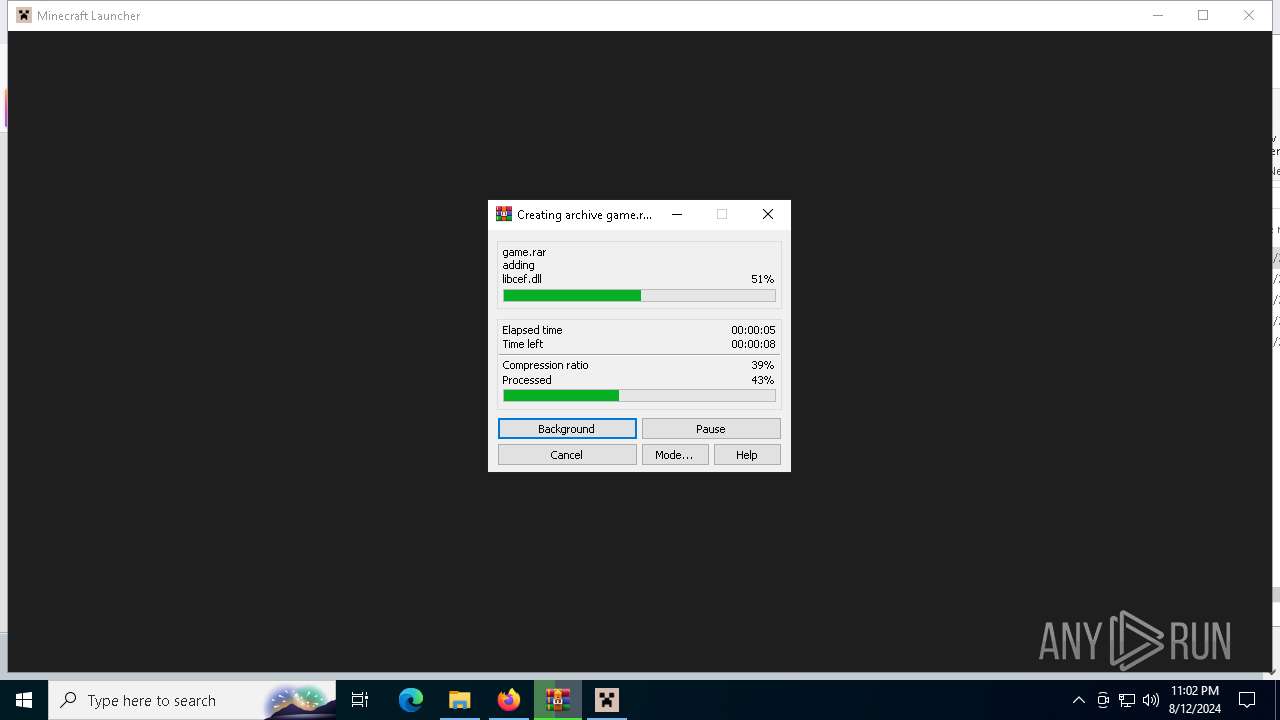
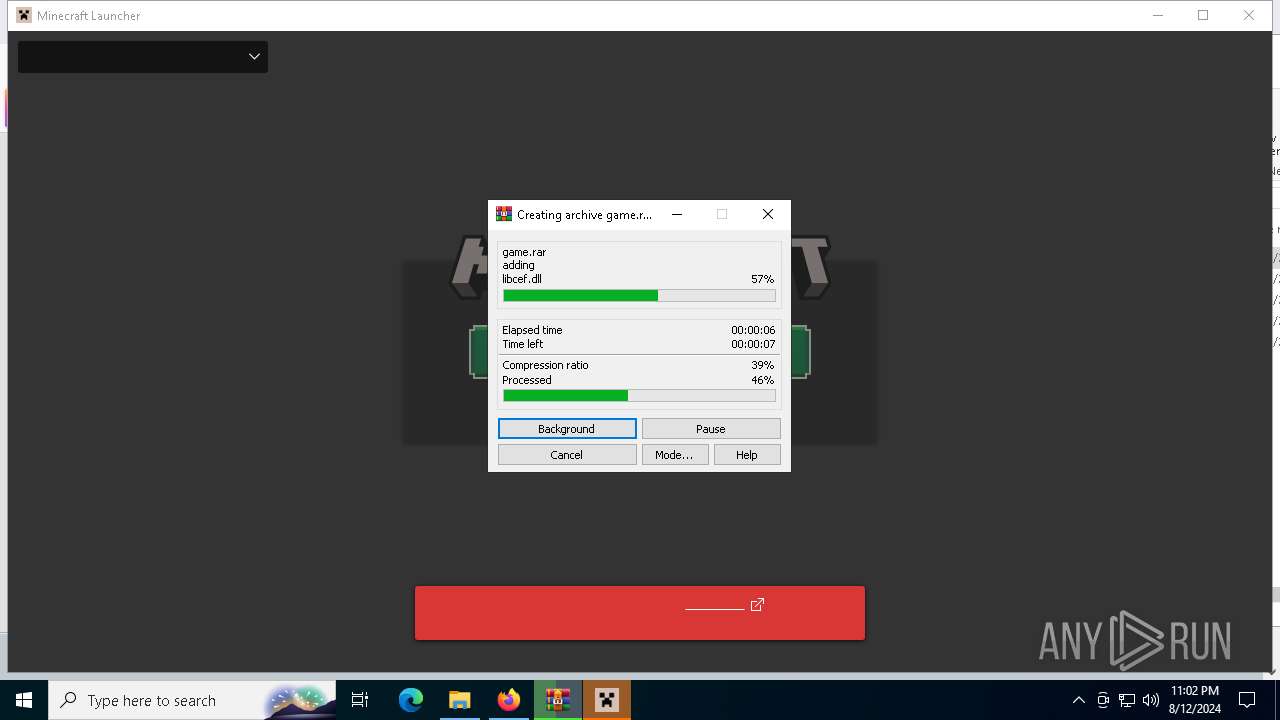
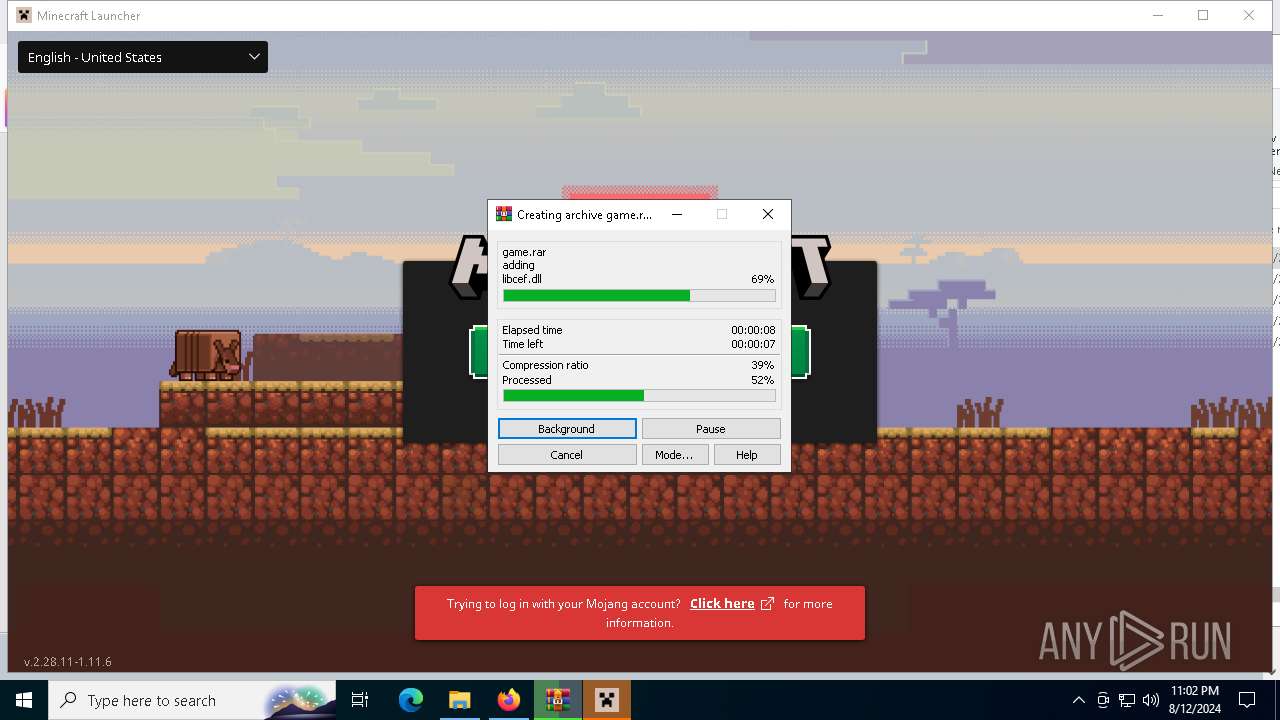
Creates files in the program directory
- MinecraftLauncher.exe (PID: 7136)
- MinecraftLauncher.exe (PID: 8024)
- WinRAR.exe (PID: 6732)
Reads Environment values
- MinecraftLauncher.exe (PID: 7136)
- MinecraftLauncher.exe (PID: 8024)
- MinecraftLauncher.exe (PID: 3188)
- MinecraftLauncher.exe (PID: 6056)
- MinecraftLauncher.exe (PID: 7572)
- MinecraftLauncher.exe (PID: 1048)
- MinecraftLauncher.exe (PID: 3360)
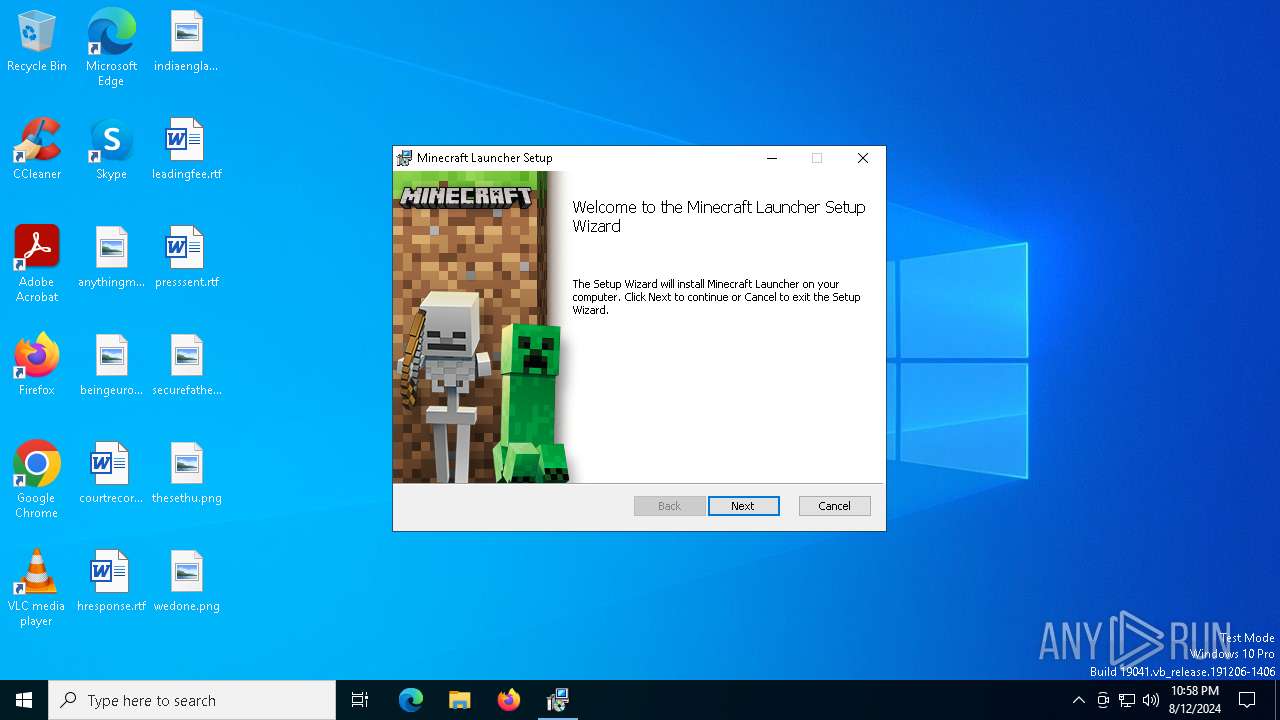
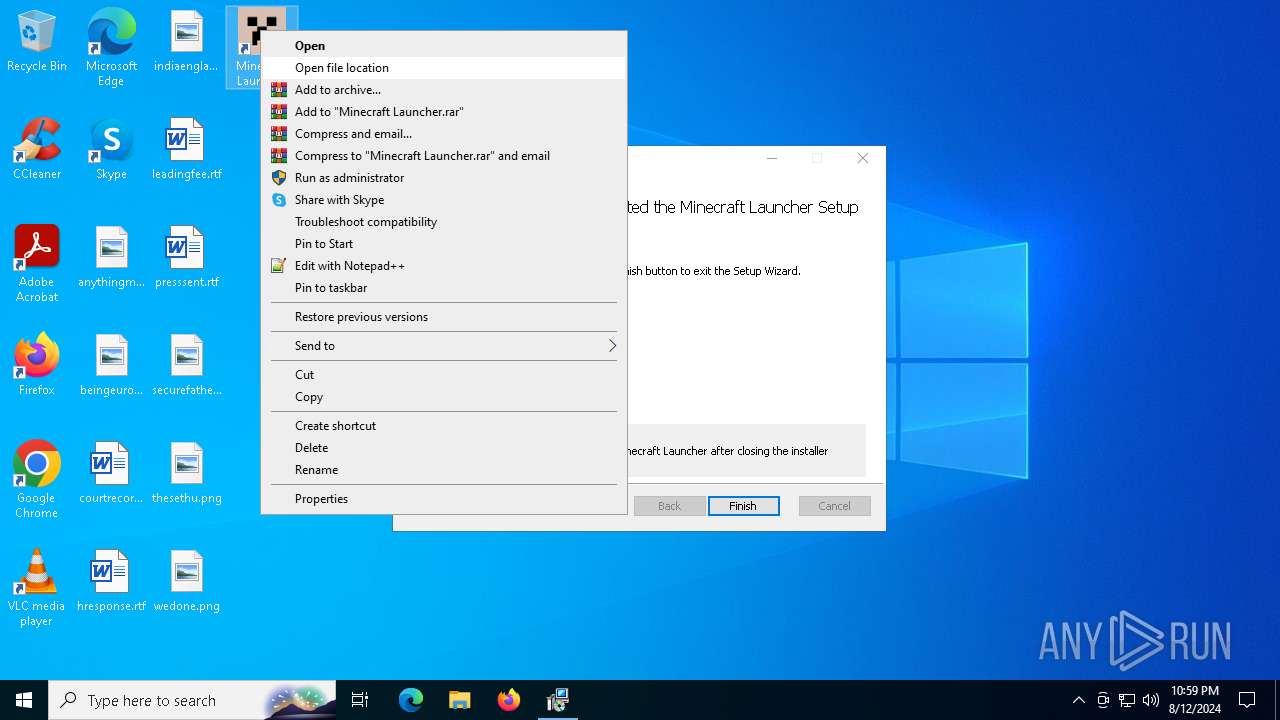
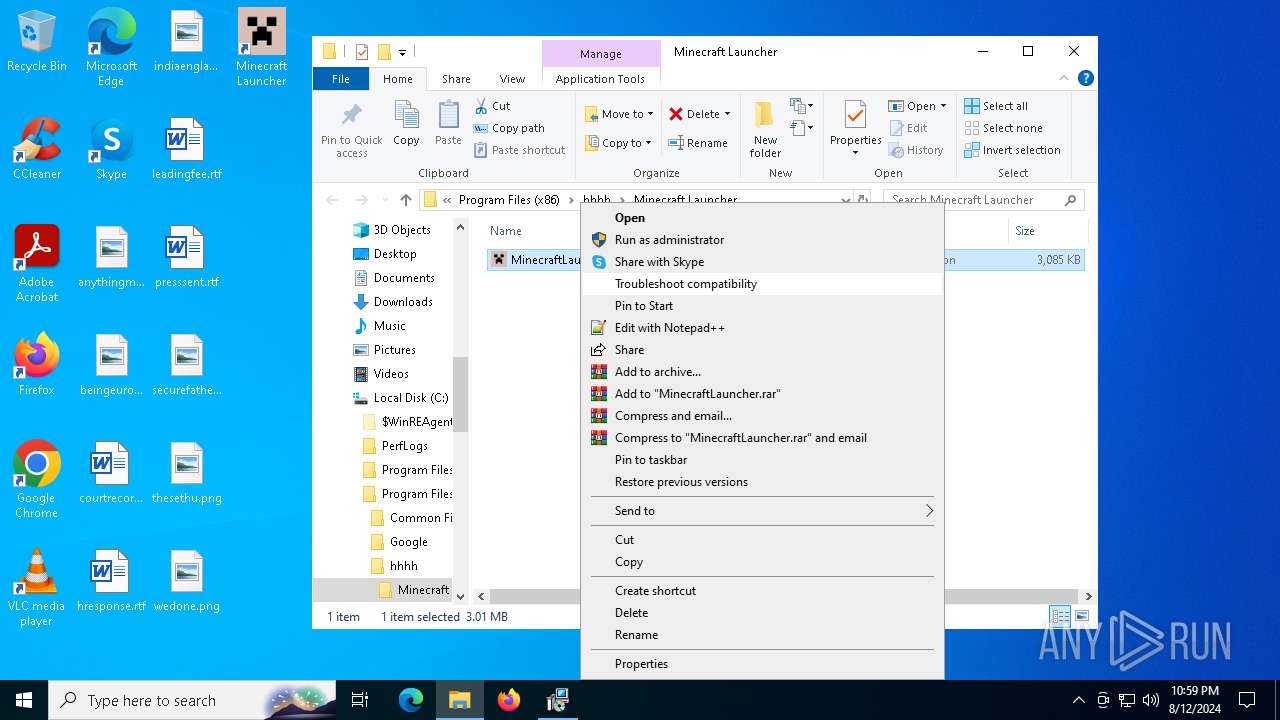
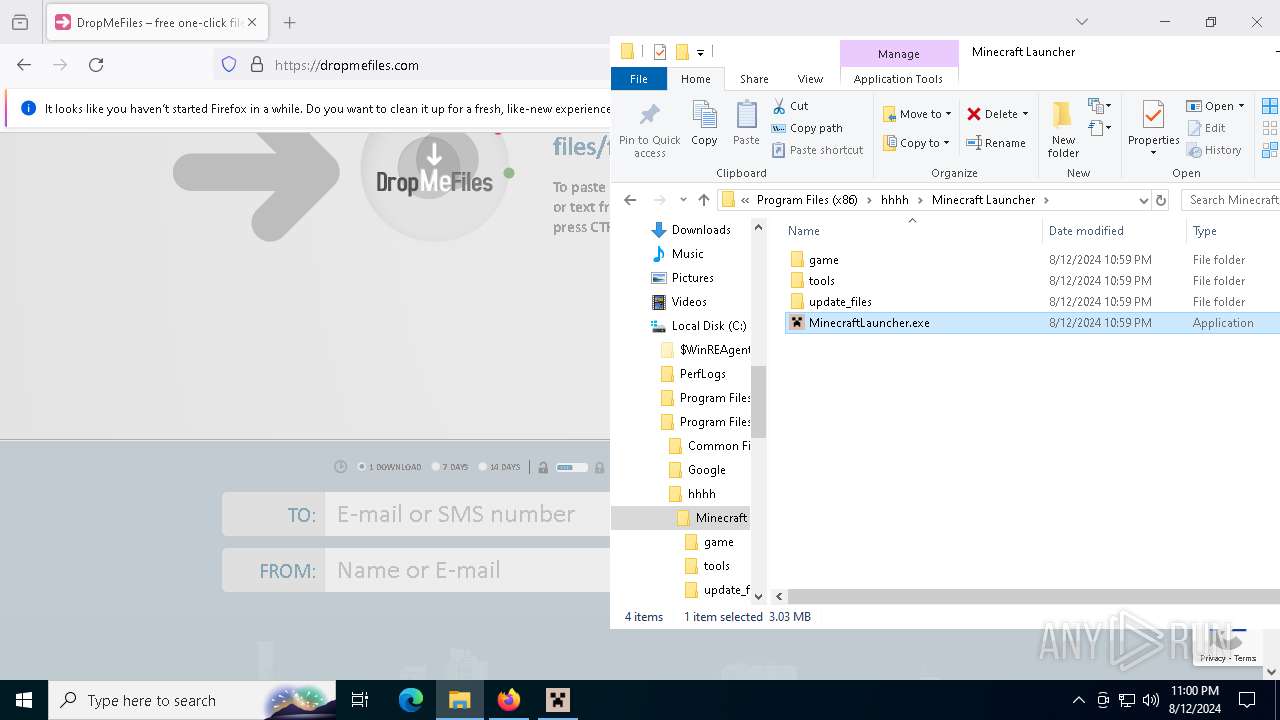
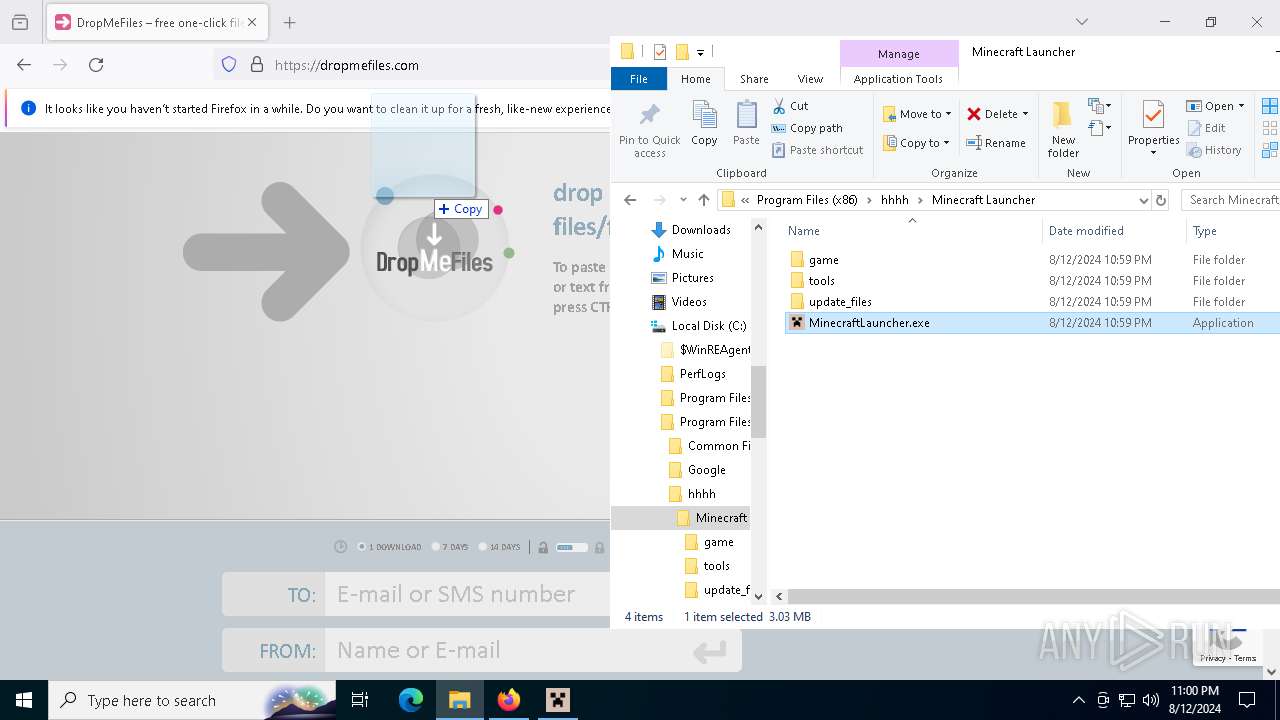
Manual execution by a user
- firefox.exe (PID: 6868)
- WinRAR.exe (PID: 6732)
- MinecraftLauncher.exe (PID: 7136)
Reads Microsoft Office registry keys
- firefox.exe (PID: 3700)
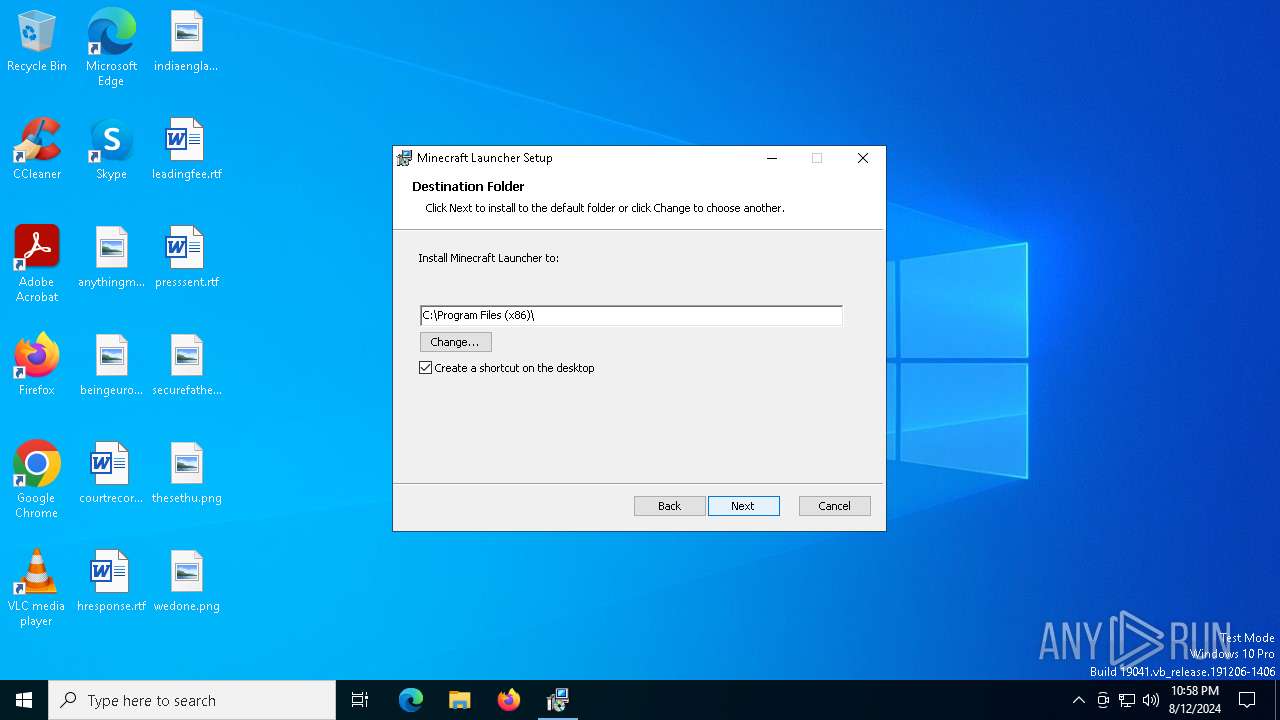
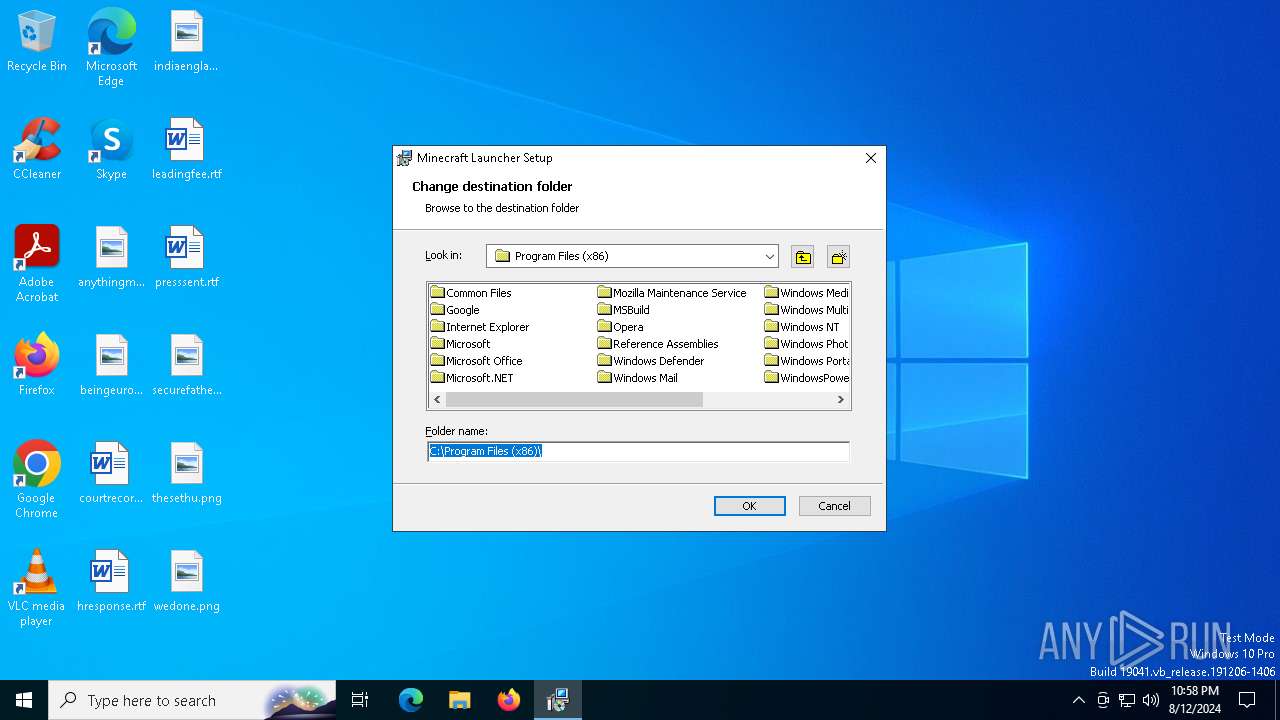
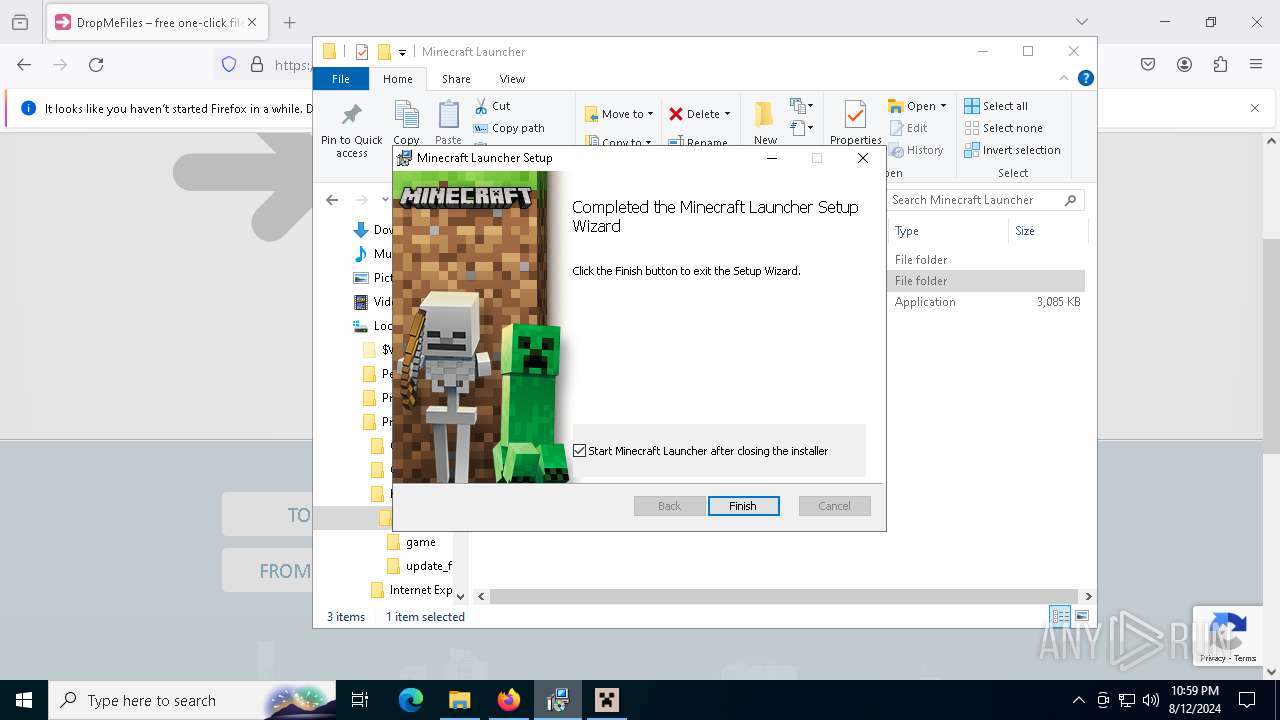
Creates a software uninstall entry
- msiexec.exe (PID: 6860)
Process checks computer location settings
- MinecraftLauncher.exe (PID: 8024)
- MinecraftLauncher.exe (PID: 1048)
- MinecraftLauncher.exe (PID: 3360)
Create files in a temporary directory
- MinecraftLauncher.exe (PID: 8024)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msi | | | Microsoft Windows Installer (95.3) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (3.2) |
| .msi | | | Microsoft Installer (100) |
EXIF
FlashPix
| CodePage: | Windows Latin 1 (Western European) |
|---|---|
| Title: | Installation Database |
| Subject: | Minecraft Launcher |
| Author: | Mojang |
| Keywords: | Installer |
| Comments: | This installer database contains the logic and data required to install Minecraft Launcher. |
| Template: | Intel;1033 |
| RevisionNumber: | {BC990100-219F-4A7E-BCD6-B88F054547B7} |
| CreateDate: | 2024:02:13 23:03:12 |
| ModifyDate: | 2024:02:13 23:03:12 |
| Pages: | 200 |
| Words: | 2 |
| Software: | Windows Installer XML Toolset (3.9.1006.0) |
| Security: | Read-only recommended |
Total processes
173
Monitored processes
35
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1048 | "C:\Program Files (x86)\hhhh\Minecraft Launcher\MinecraftLauncher.exe" --type=renderer --log-severity=info --user-data-dir="C:\Users\admin\AppData\Local\CEF\User Data" --launcherui --workdir="C:\Users\admin\AppData\Roaming\.minecraft" --no-sandbox --log-file="C:\Users\admin\AppData\Roaming\.minecraft\launcher_cef_log.txt" --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --mojo-platform-channel-handle=2872 --field-trial-handle=2328,i,3269271760247734166,12882409912904554043,131072 --disable-features=CalculateNativeWinOcclusion,WinUseBrowserSpellChecker /prefetch:1 | C:\Program Files (x86)\hhhh\Minecraft Launcher\MinecraftLauncher.exe | — | MinecraftLauncher.exe | |||||||||||
User: admin Company: Mojang Integrity Level: MEDIUM Description: Minecraft Launcher Version: 1.0.1.0 Modules
| |||||||||||||||
| 1140 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=6044 -childID 8 -isForBrowser -prefsHandle 6020 -prefMapHandle 6008 -prefsLen 31937 -prefMapSize 244343 -jsInitHandle 1504 -jsInitLen 235124 -parentBuildID 20240213221259 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {2a0c4b83-7031-4849-bc29-de070ff5037c} 3700 "\\.\pipe\gecko-crash-server-pipe.3700" 21b32227d90 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Version: 123.0 Modules
| |||||||||||||||
| 2068 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=2928 -childID 1 -isForBrowser -prefsHandle 2952 -prefMapHandle 2948 -prefsLen 30953 -prefMapSize 244343 -jsInitHandle 1504 -jsInitLen 235124 -parentBuildID 20240213221259 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {fef180f0-ceca-4df1-bca3-258c989440c0} 3700 "\\.\pipe\gecko-crash-server-pipe.3700" 21b2cd68850 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Version: 123.0 Modules
| |||||||||||||||
| 2476 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | SrTasks.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2960 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=1816 -parentBuildID 20240213221259 -prefsHandle 1852 -prefMapHandle 1844 -prefsLen 30537 -prefMapSize 244343 -appDir "C:\Program Files\Mozilla Firefox\browser" - {ef632acf-2bb1-4b1e-854c-5990ed5769e0} 3700 "\\.\pipe\gecko-crash-server-pipe.3700" 21b275e0e10 gpu | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Version: 123.0 Modules
| |||||||||||||||
| 3188 | "C:\Program Files (x86)\hhhh\Minecraft Launcher\MinecraftLauncher.exe" --type=gpu-process --no-sandbox --log-severity=info --lang=en-US --user-data-dir="C:\Users\admin\AppData\Local\CEF\User Data" --launcherui --workdir="C:\Users\admin\AppData\Roaming\.minecraft" --gpu-preferences=UAAAAAAAAADgACAYAAAAAAAAAAAAAAAAAABgAAAAAAAwAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAEgAAAAAAAAASAAAAAAAAAAYAAAAAgAAABAAAAAAAAAAGAAAAAAAAAAQAAAAAAAAAAAAAAAOAAAAEAAAAAAAAAABAAAADgAAAAgAAAAAAAAACAAAAAAAAAA= --log-file="C:\Users\admin\AppData\Roaming\.minecraft\launcher_cef_log.txt" --mojo-platform-channel-handle=2176 --field-trial-handle=2328,i,3269271760247734166,12882409912904554043,131072 --disable-features=CalculateNativeWinOcclusion,WinUseBrowserSpellChecker /prefetch:2 | C:\Program Files (x86)\hhhh\Minecraft Launcher\MinecraftLauncher.exe | — | MinecraftLauncher.exe | |||||||||||
User: admin Company: Mojang Integrity Level: MEDIUM Description: Minecraft Launcher Version: 1.0.1.0 Modules
| |||||||||||||||
| 3360 | "C:\Program Files (x86)\hhhh\Minecraft Launcher\MinecraftLauncher.exe" --type=renderer --log-severity=info --user-data-dir="C:\Users\admin\AppData\Local\CEF\User Data" --launcherui --workdir="C:\Users\admin\AppData\Roaming\.minecraft" --no-sandbox --log-file="C:\Users\admin\AppData\Roaming\.minecraft\launcher_cef_log.txt" --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --mojo-platform-channel-handle=2824 --field-trial-handle=2328,i,3269271760247734166,12882409912904554043,131072 --disable-features=CalculateNativeWinOcclusion,WinUseBrowserSpellChecker /prefetch:1 | C:\Program Files (x86)\hhhh\Minecraft Launcher\MinecraftLauncher.exe | — | MinecraftLauncher.exe | |||||||||||
User: admin Company: Mojang Integrity Level: MEDIUM Description: Minecraft Launcher Version: 1.0.1.0 Modules
| |||||||||||||||
| 3700 | "C:\Program Files\Mozilla Firefox\firefox.exe" | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Version: 123.0 Modules
| |||||||||||||||
| 3992 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5084 | C:\WINDOWS\SysWOW64\DllHost.exe /Processid:{45BA127D-10A8-46EA-8AB7-56EA9078943C} | C:\Windows\SysWOW64\dllhost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: COM Surrogate Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
38 875
Read events
38 554
Write events
301
Delete events
20
Modification events
| (PID) Process: | (6860) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SystemRestore |
| Operation: | write | Name: | SrCreateRp (Enter) |
Value: 480000000000000086DF652C0BEDDA01CC1A00008C1B0000D50700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6860) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Enter) |
Value: 480000000000000086DF652C0BEDDA01CC1A00008C1B0000D20700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6860) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Leave) |
Value: 4800000000000000AFC8CE2C0BEDDA01CC1A00008C1B0000D20700000100000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6860) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppEnumGroups (Enter) |
Value: 4800000000000000AFC8CE2C0BEDDA01CC1A00008C1B0000D10700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6860) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppEnumGroups (Leave) |
Value: 4800000000000000E17CD32C0BEDDA01CC1A00008C1B0000D10700000100000000000000010000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6860) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppCreate (Enter) |
Value: 48000000000000002044D82C0BEDDA01CC1A00008C1B0000D00700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6860) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SPP |
| Operation: | write | Name: | LastIndex |
Value: 11 | |||
| (PID) Process: | (6860) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGatherWriterMetadata (Enter) |
Value: 4800000000000000CC1C4D2D0BEDDA01CC1A00008C1B0000D30700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6860) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\VssapiPublisher |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 480000000000000069804F2D0BEDDA01CC1A000058190000E80300000100000000000000000000001B1013C38CD942488BCB87F3DEA8E2B100000000000000000000000000000000 | |||
| (PID) Process: | (7028) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\COM+ REGDB Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 480000000000000082C15D2D0BEDDA01741B0000FC0C0000E80300000100000001000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
43
Suspicious files
458
Text files
44
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6860 | msiexec.exe | C:\System Volume Information\SPP\metadata-2 | — | |
MD5:— | SHA256:— | |||
| 6728 | msiexec.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\C0018BB1B5834735BFA60CD063B31956 | der | |
MD5:FC1193C6345AC35188AA3DE0F824CEB7 | SHA256:BDFB8FAFF4C0C0A15C642890A5544BD32F930F55CA199470DBD4736A32D6E200 | |||
| 6728 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\MSIF364.tmp | executable | |
MD5:48EAF9D4CCF75BC06BBC5D33E78B7FFF | SHA256:9AE2608EDD49D2C319BB7BCFC24550BD9FB88B2F100FE90222A6FC55CA43C589 | |||
| 6860 | msiexec.exe | C:\System Volume Information\SPP\OnlineMetadataCache\{c313101b-d98c-4842-8bcb-87f3dea8e2b1}_OnDiskSnapshotProp | binary | |
MD5:E270ED61C37CE418FCFF62827A82AD85 | SHA256:6C474B04983E99DF85C2D525989105DE1A8083B94004F53A1AA2BCD0318AD6A3 | |||
| 6860 | msiexec.exe | C:\Windows\Installer\{6A960B34-5197-49DE-AC60-1177DFE24976}\minecraft.ico | image | |
MD5:1D4B0CC64CAFCBC3E70ADFC5DAA2F627 | SHA256:57E3C89D247B4E2E419AE0F9DD3DA075AF8C73281DE26179EF04C1F2C0EF37E2 | |||
| 6728 | msiexec.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\37C951188967C8EB88D99893D9D191FE | binary | |
MD5:FB64A9EBEDF48D3895381D5B7D80743D | SHA256:EA21D495930AD76F267A33A0F593DBF0C7EA75E457FCAE49A29DAAD8BD920F42 | |||
| 6860 | msiexec.exe | C:\Windows\Installer\MSI3F72.tmp | executable | |
MD5:785EE78478D43F00870E91FA96B94646 | SHA256:B8665993CD5F7224E35C122A5C1965F8C4F2B4D9D41F75160B515E66F9AFFC53 | |||
| 6860 | msiexec.exe | C:\Windows\Installer\MSI3F71.tmp | binary | |
MD5:702225F22853B19112DB9AB044F906BC | SHA256:036B1C00CF91BDD88B653688F767E1A3975FACC755ABAEEE59CE779CFA9A5EB4 | |||
| 6860 | msiexec.exe | C:\Windows\Temp\~DFF9E63878F6014C66.TMP | binary | |
MD5:5B29412C09846E158107E8ED39045FD7 | SHA256:97794B14AB0C40983665751D3ABE760AE96E748DEBE5A4F5B76B3C21AB8F7FE8 | |||
| 6860 | msiexec.exe | C:\System Volume Information\SPP\snapshot-2 | binary | |
MD5:E270ED61C37CE418FCFF62827A82AD85 | SHA256:6C474B04983E99DF85C2D525989105DE1A8083B94004F53A1AA2BCD0318AD6A3 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
41
TCP/UDP connections
158
DNS requests
177
Threats
17
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5336 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
2324 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
2324 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6424 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
6728 | msiexec.exe | GET | 200 | 104.79.89.142:80 | http://www.microsoft.com/pkiops/crl/MicCodSigPCA2011_2011-07-08.crl | unknown | — | — | whitelisted |
6484 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
3700 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/canonical.html | unknown | — | — | whitelisted |
3700 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/success.txt?ipv4 | unknown | — | — | whitelisted |
3700 | firefox.exe | POST | 200 | 2.16.202.121:80 | http://r11.o.lencr.org/ | unknown | — | — | unknown |
3700 | firefox.exe | POST | 200 | 2.16.202.121:80 | http://r10.o.lencr.org/ | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 192.168.100.255:138 | — | — | — | whitelisted |
1420 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3888 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
2120 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5336 | SearchApp.exe | 2.23.209.187:443 | www.bing.com | Akamai International B.V. | GB | unknown |
5336 | SearchApp.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
— | — | 40.126.31.67:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2324 | svchost.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
— | — | 40.113.103.199:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
login.live.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
fd.api.iris.microsoft.com |
| whitelisted |
th.bing.com |
| whitelisted |
arc.msn.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
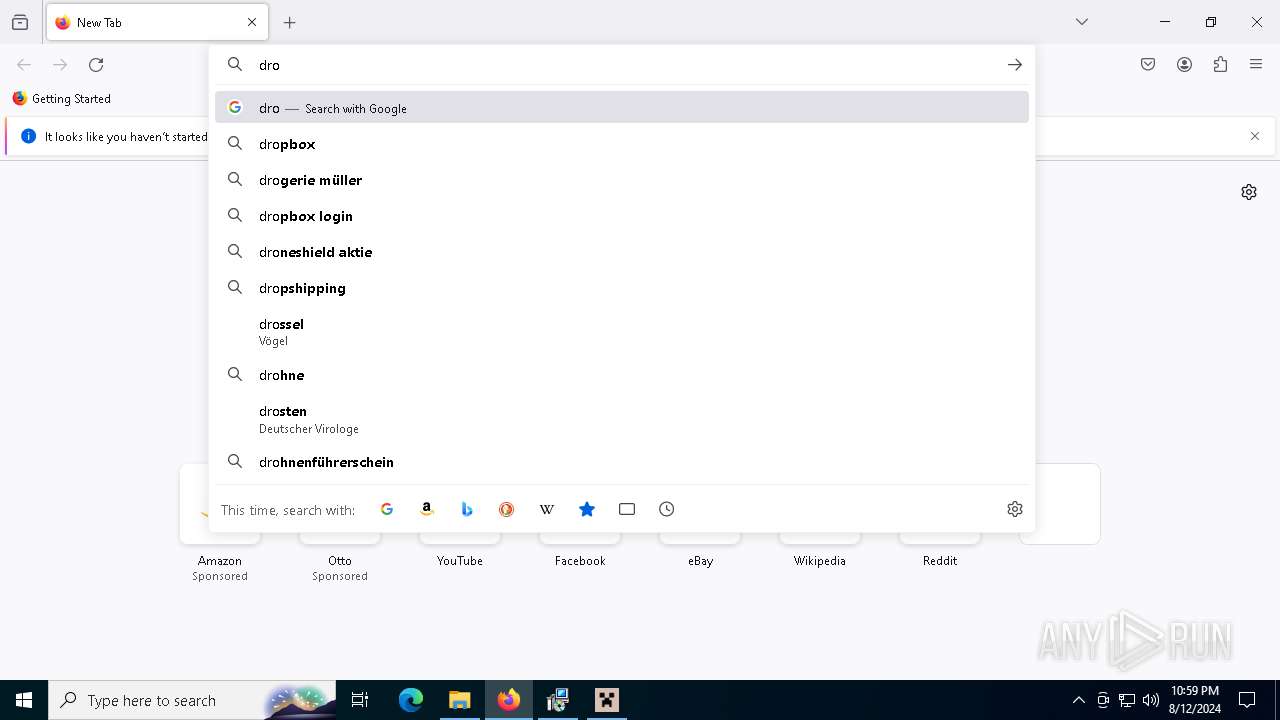
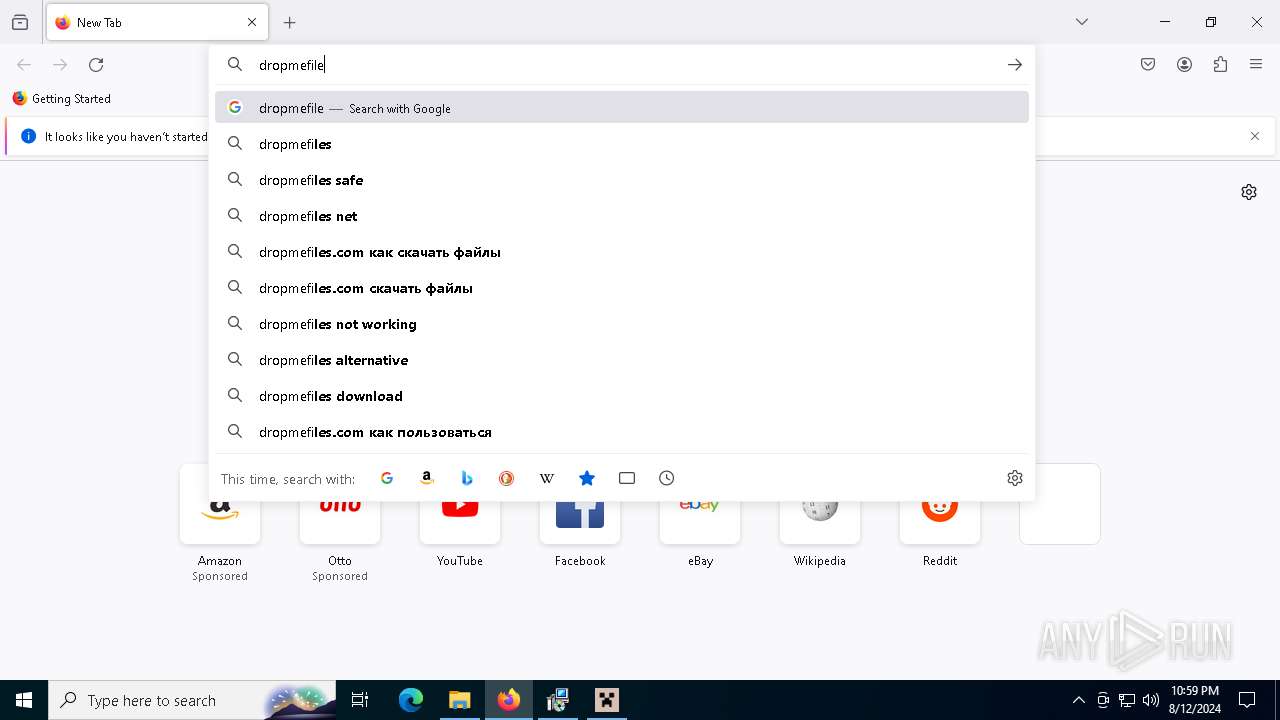
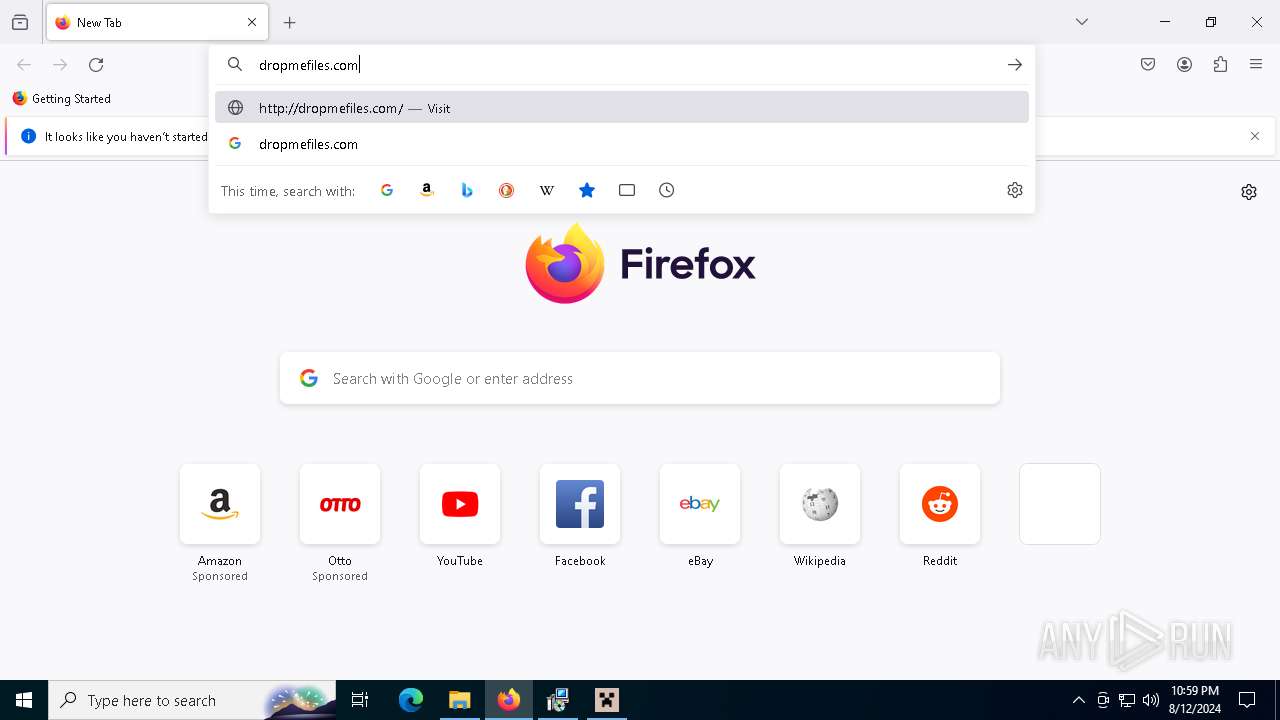
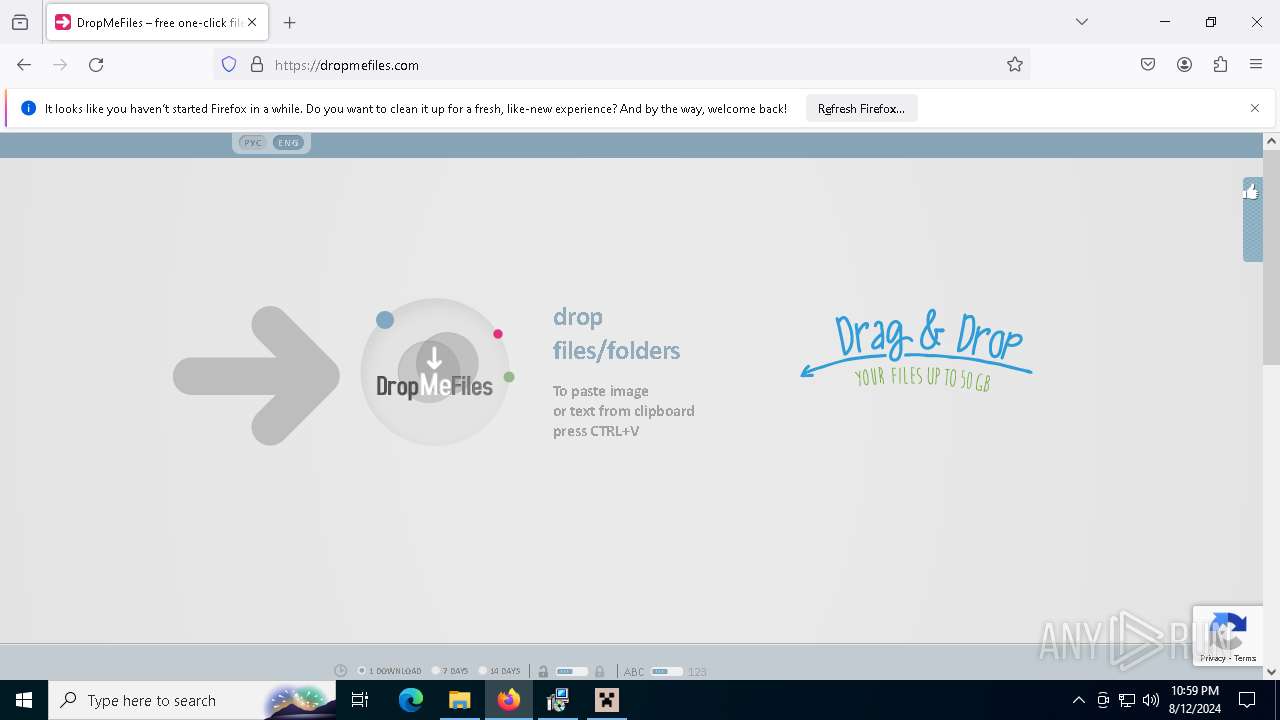
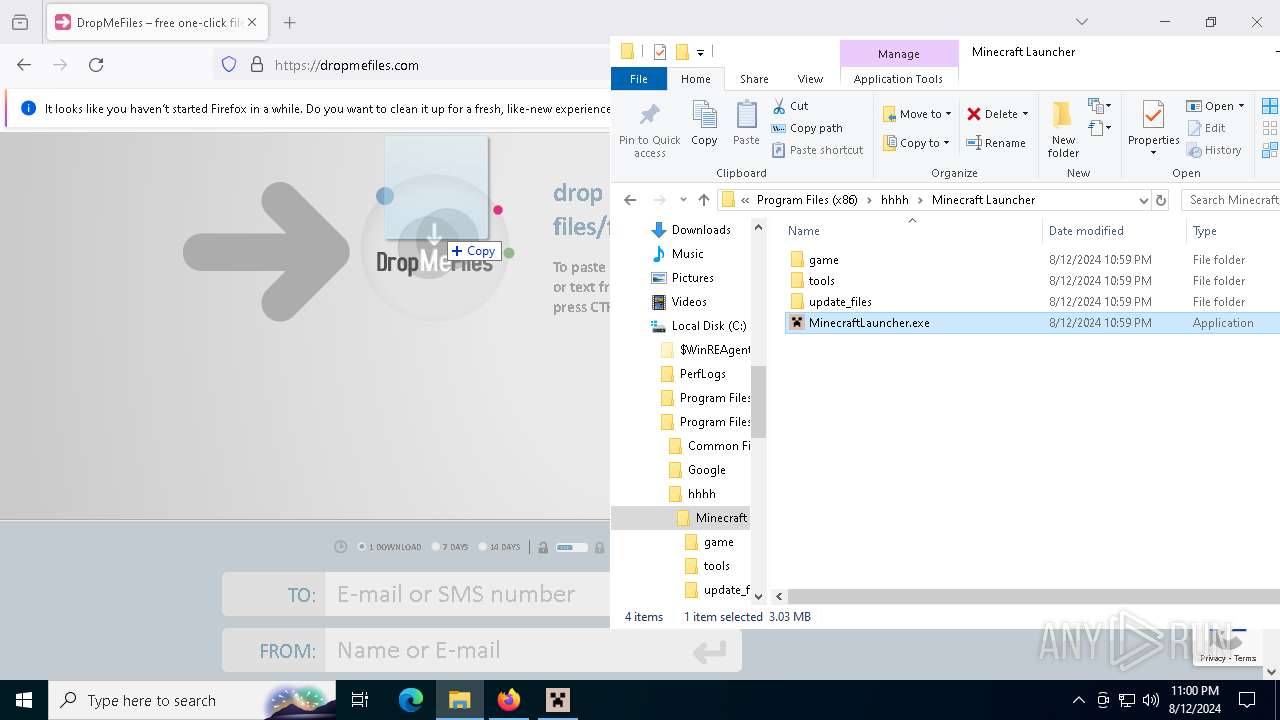
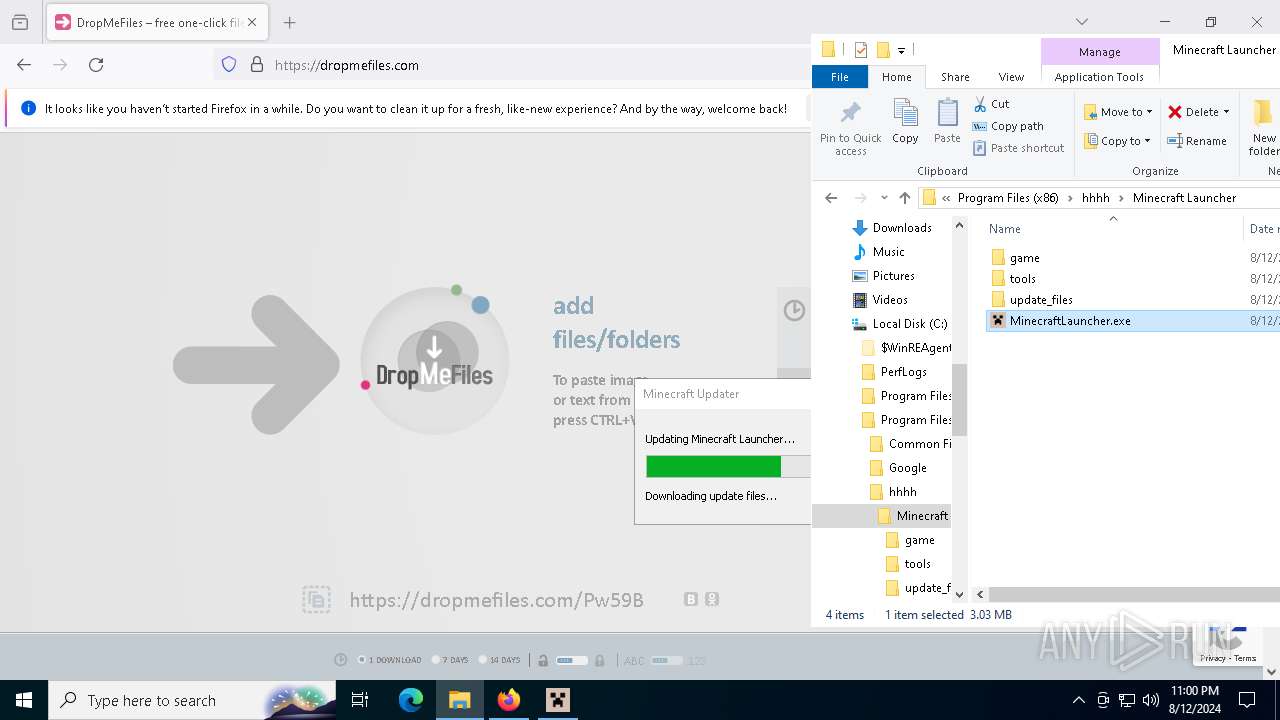
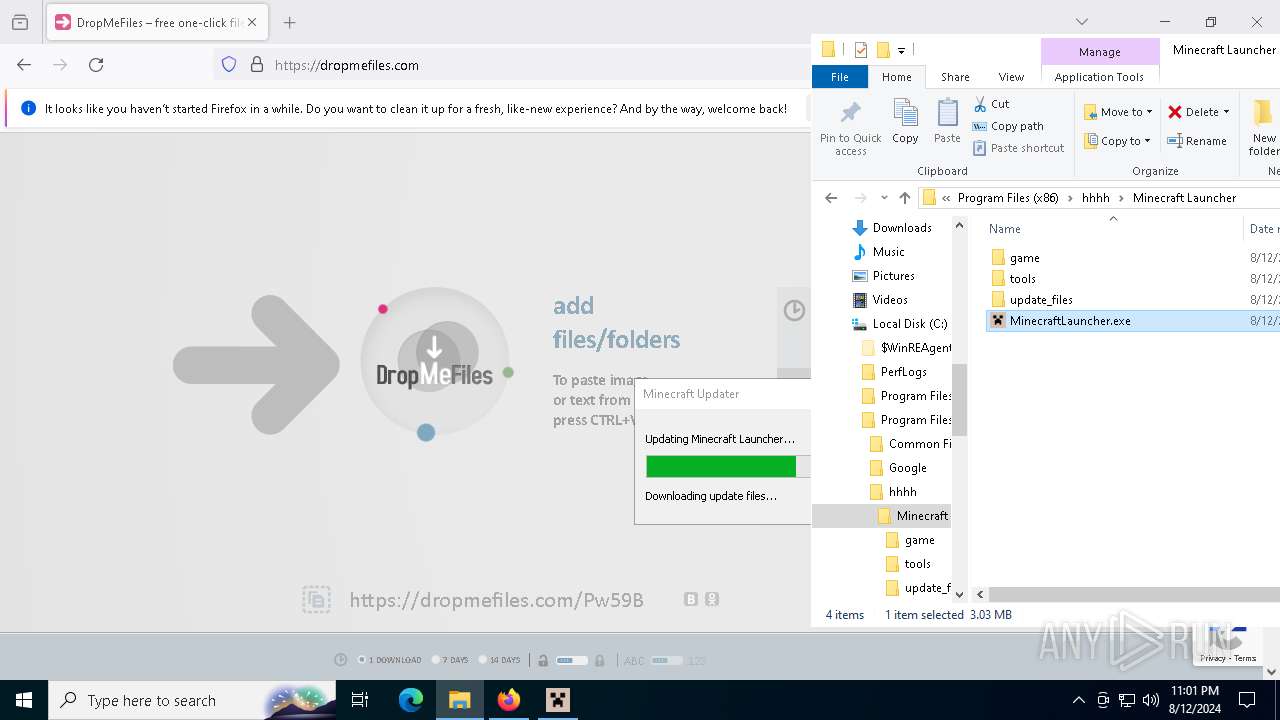
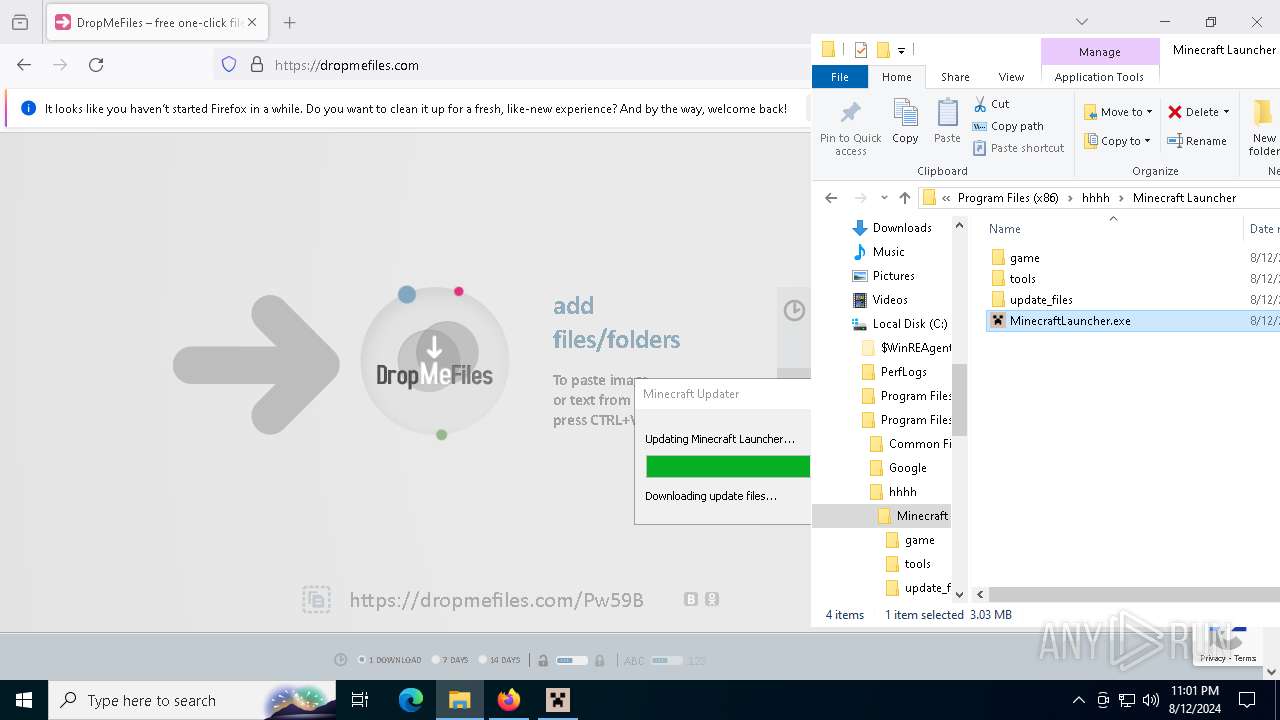
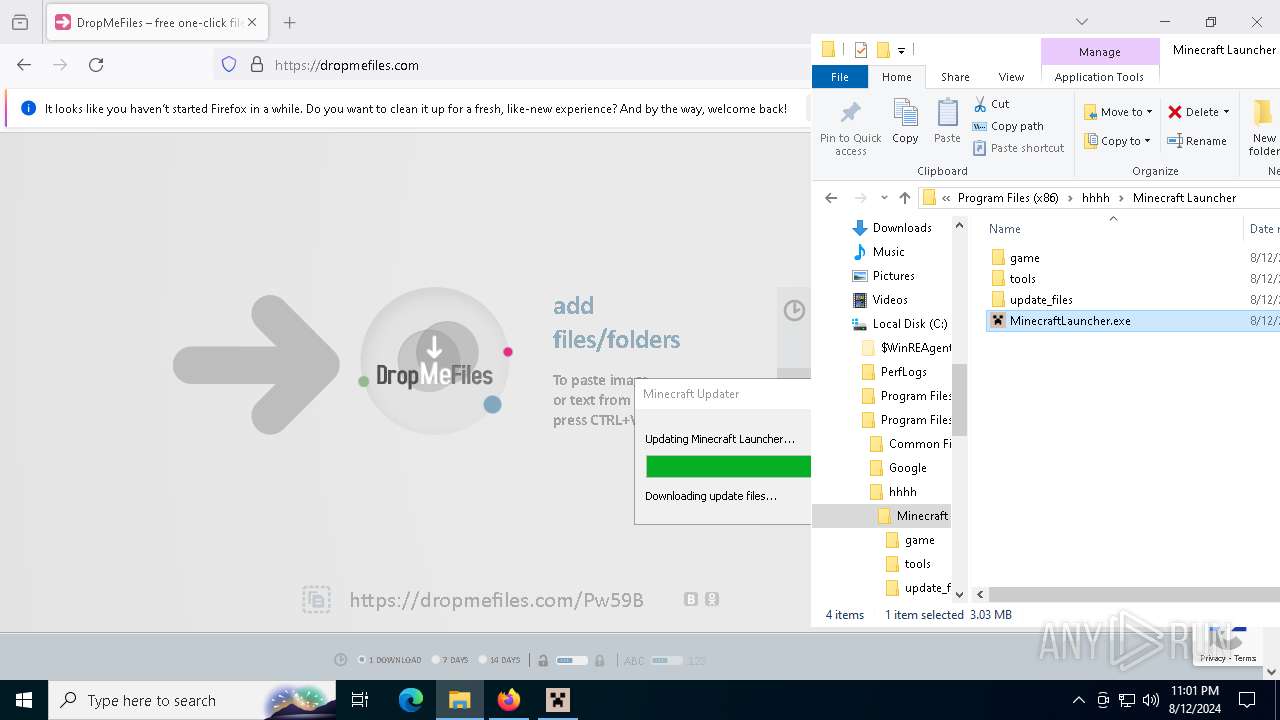
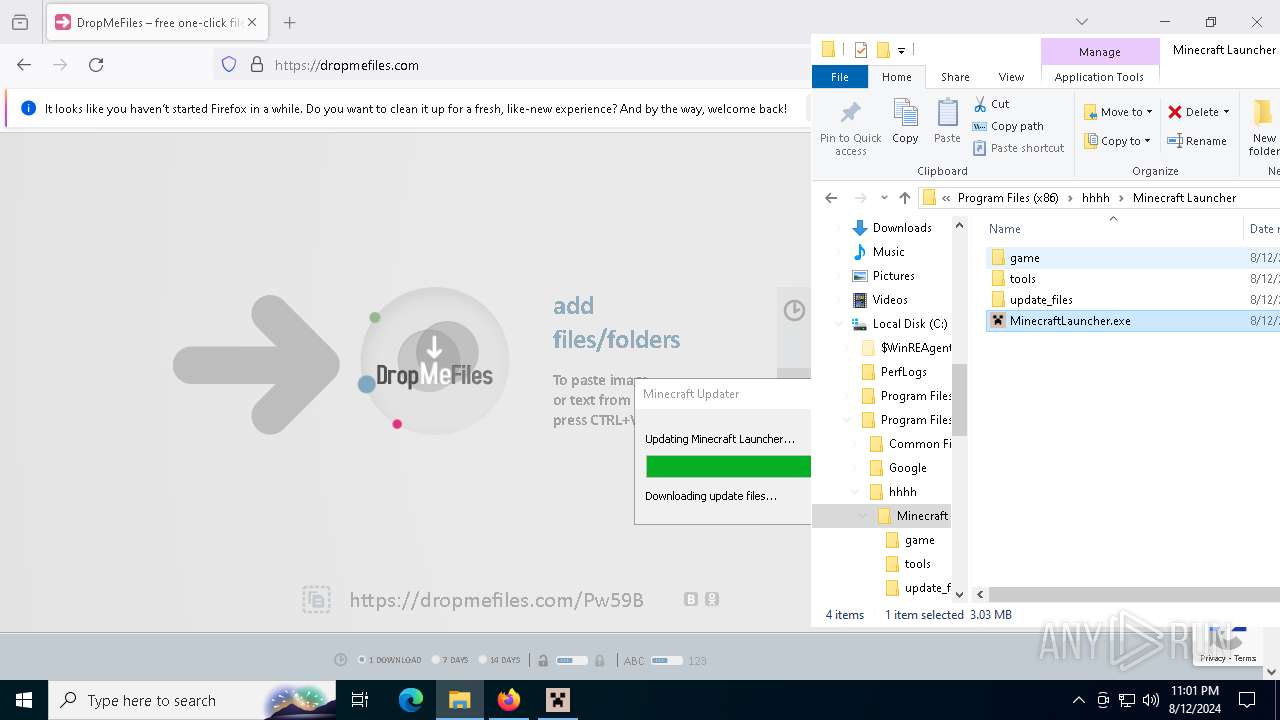
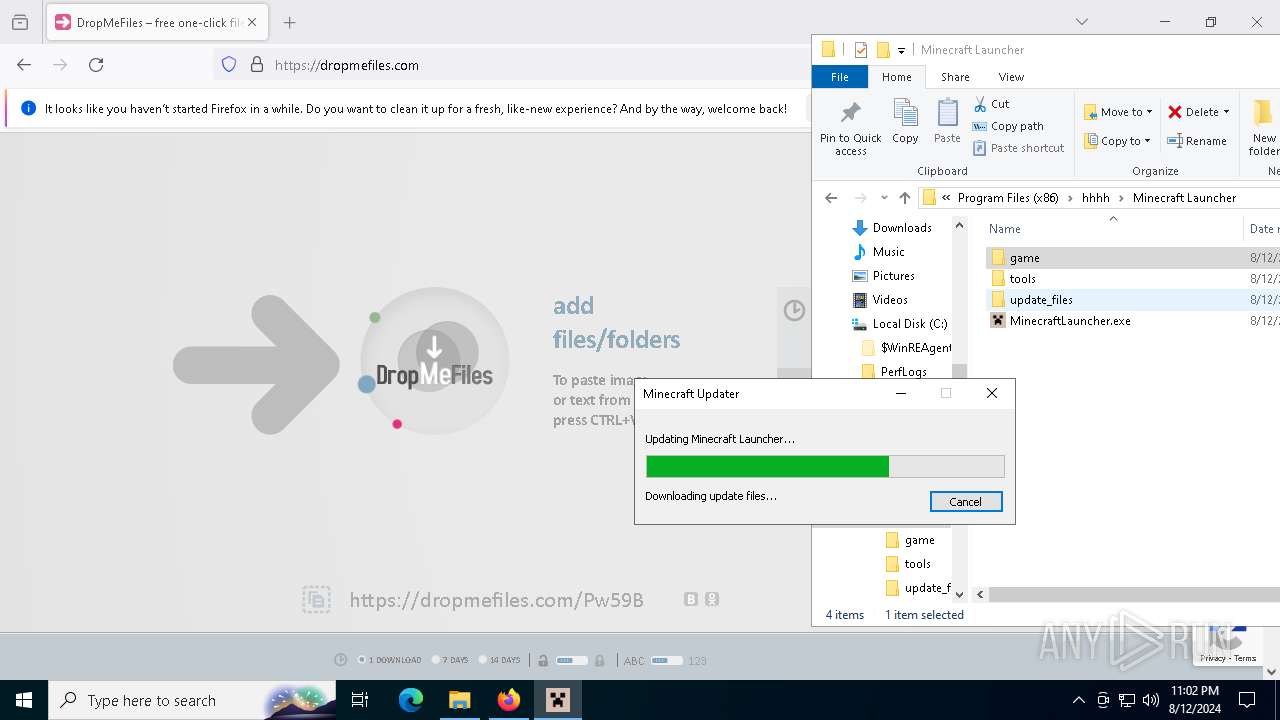
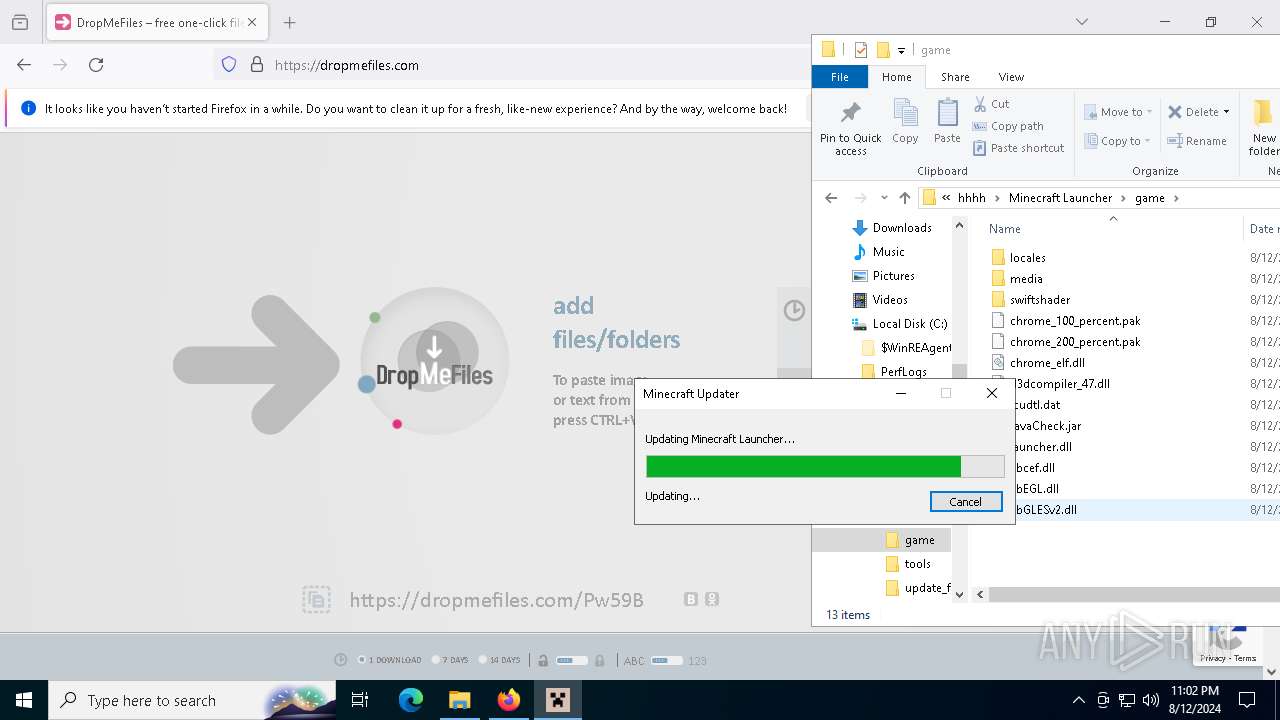
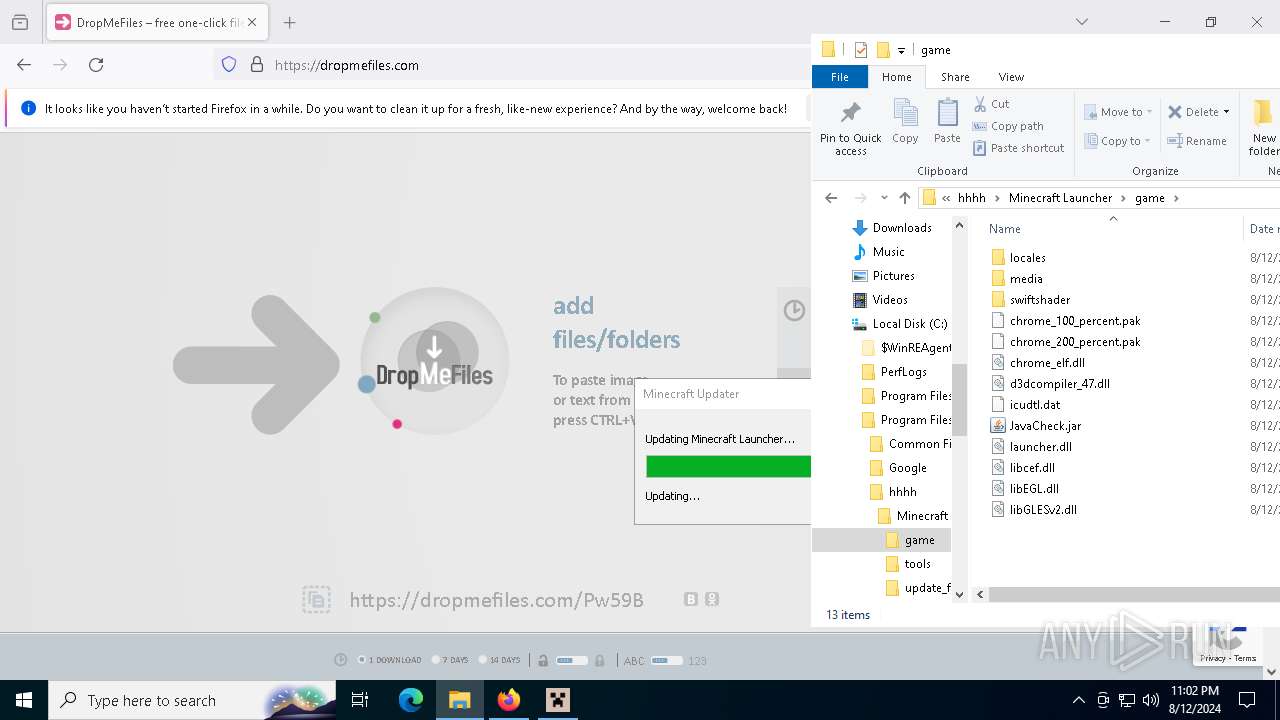
2256 | svchost.exe | Misc activity | ET INFO File Sharing Service Domain in DNS Lookup (dropmefiles .com) |
2256 | svchost.exe | Misc activity | ET INFO File Sharing Service Domain in DNS Lookup (dropmefiles .com) |
2256 | svchost.exe | Misc activity | ET INFO File Sharing Service Domain in DNS Lookup (dropmefiles .com) |
2256 | svchost.exe | Misc activity | ET INFO File Sharing Service Domain in DNS Lookup (dropmefiles .com) |
2256 | svchost.exe | Misc activity | ET INFO File Sharing Service Domain in DNS Lookup (dropmefiles .com) |
3700 | firefox.exe | Misc activity | ET INFO Observed File Sharing Service Domain (dropmefiles .com in TLS SNI) |
3700 | firefox.exe | Misc activity | ET INFO Observed File Sharing Service Domain (dropmefiles .com in TLS SNI) |
3700 | firefox.exe | Misc activity | ET INFO Observed File Sharing Service Domain (dropmefiles .com in TLS SNI) |
3700 | firefox.exe | Misc activity | ET INFO Observed File Sharing Service Domain (dropmefiles .com in TLS SNI) |
3700 | firefox.exe | Misc activity | ET INFO Observed File Sharing Service Domain (dropmefiles .com in TLS SNI) |
Process | Message |
|---|---|
MinecraftLauncher.exe | [0812/230253.921:INFO:main_context.cpp(131)] CEF initialized successfully.
|
MinecraftLauncher.exe | [0812/230253.921:INFO:main_context.cpp(133)] CEF version: 99.2.14+g3f796b8+chromium-99.0.4844.84
|