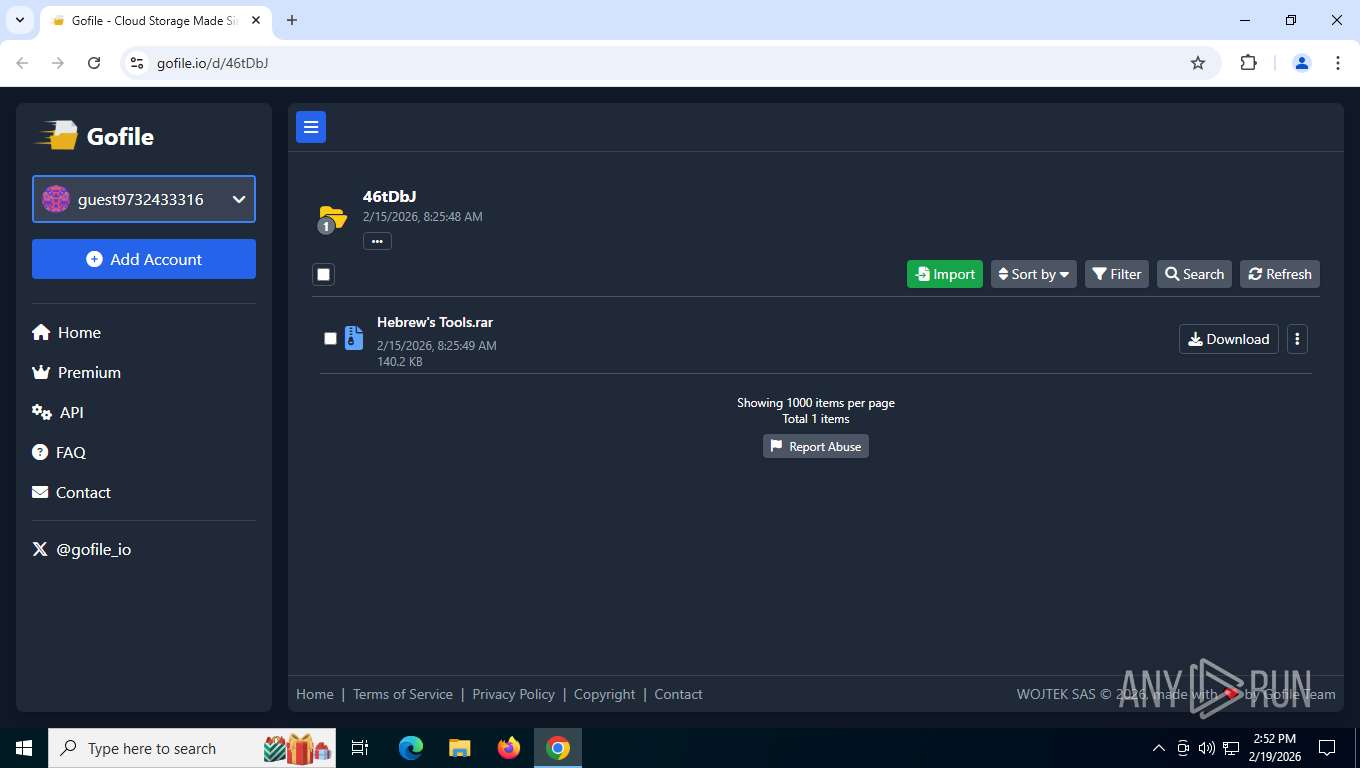
| URL: | https://gofile.io/d/46tDbJ |
| Full analysis: | https://app.any.run/tasks/0bfacec5-6d67-4ad4-8703-5095ebaea52b |
| Verdict: | Malicious activity |
| Analysis date: | February 19, 2026, 19:51:40 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 64F4D2E0E6E3DF4FAC8F1205F7866CEF |
| SHA1: | 02DEDA7D30BEAABC41078F99349A5BF049430DAB |
| SHA256: | D93C5F8141937818DBD4B137AAA7825A23B840B9CD653237105C6F6818C6DC5B |
| SSDEEP: | 3:N8rxL1RjPn:2Zbr |
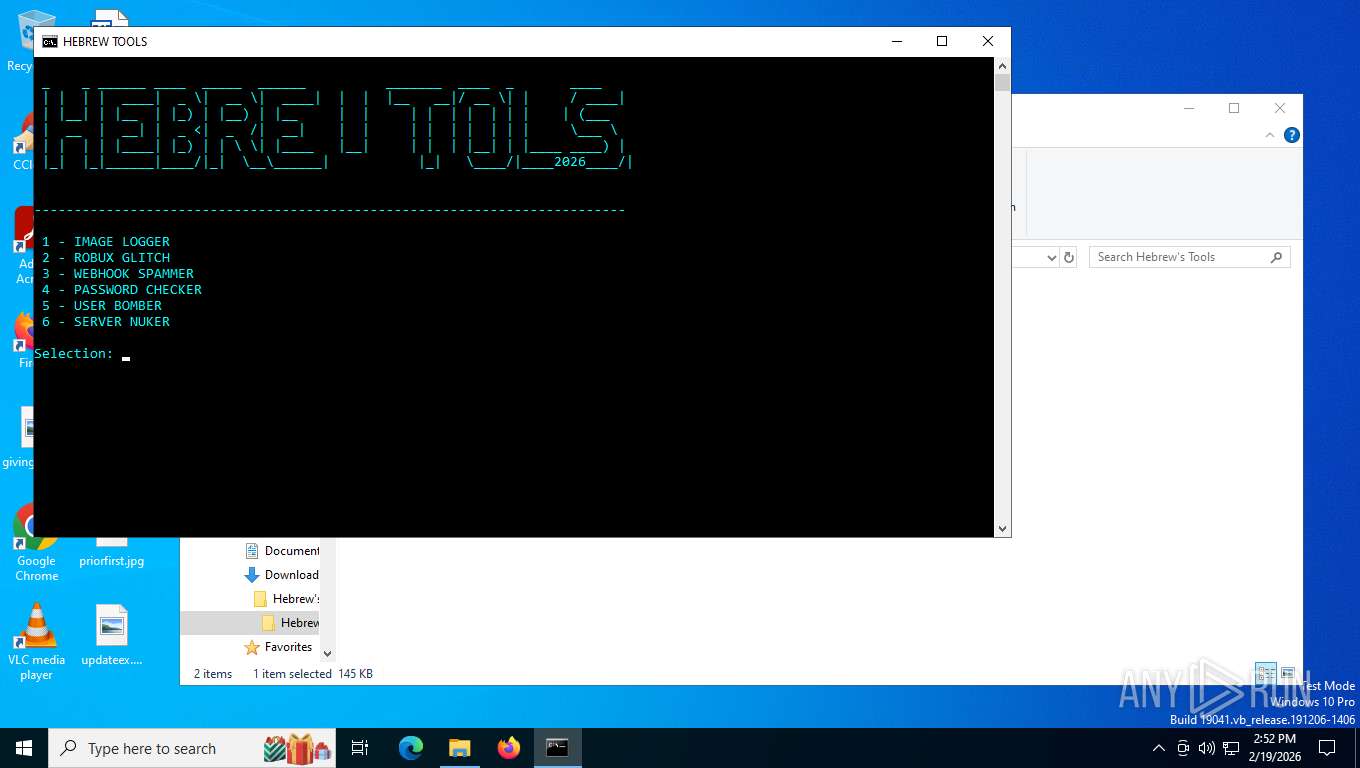
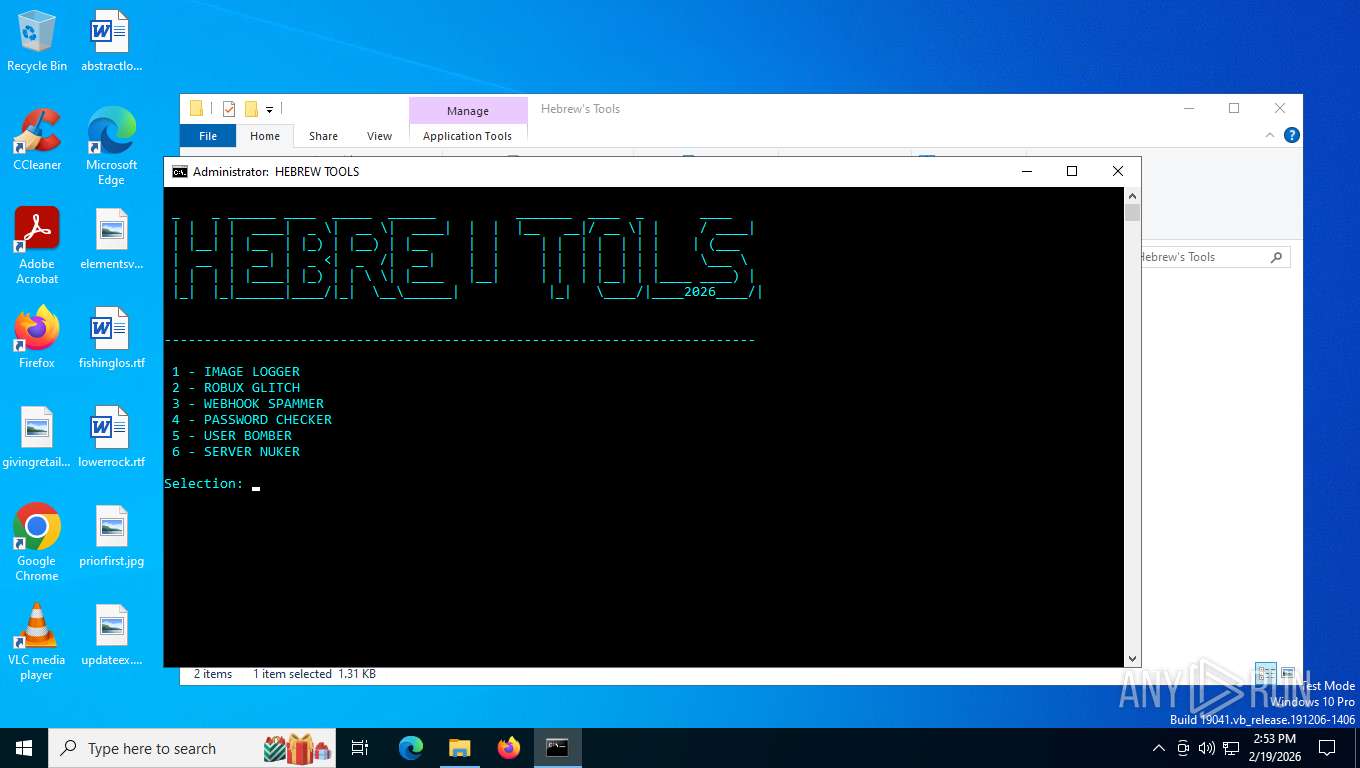
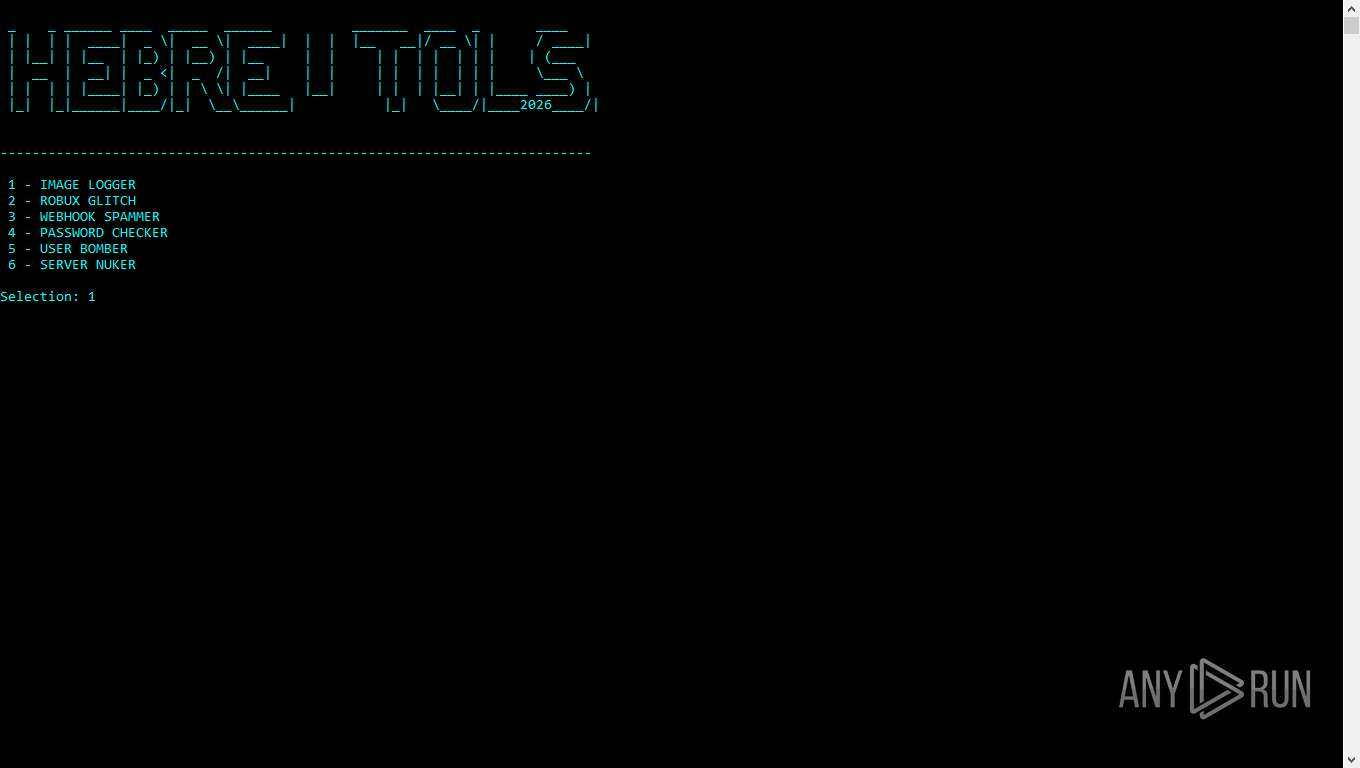
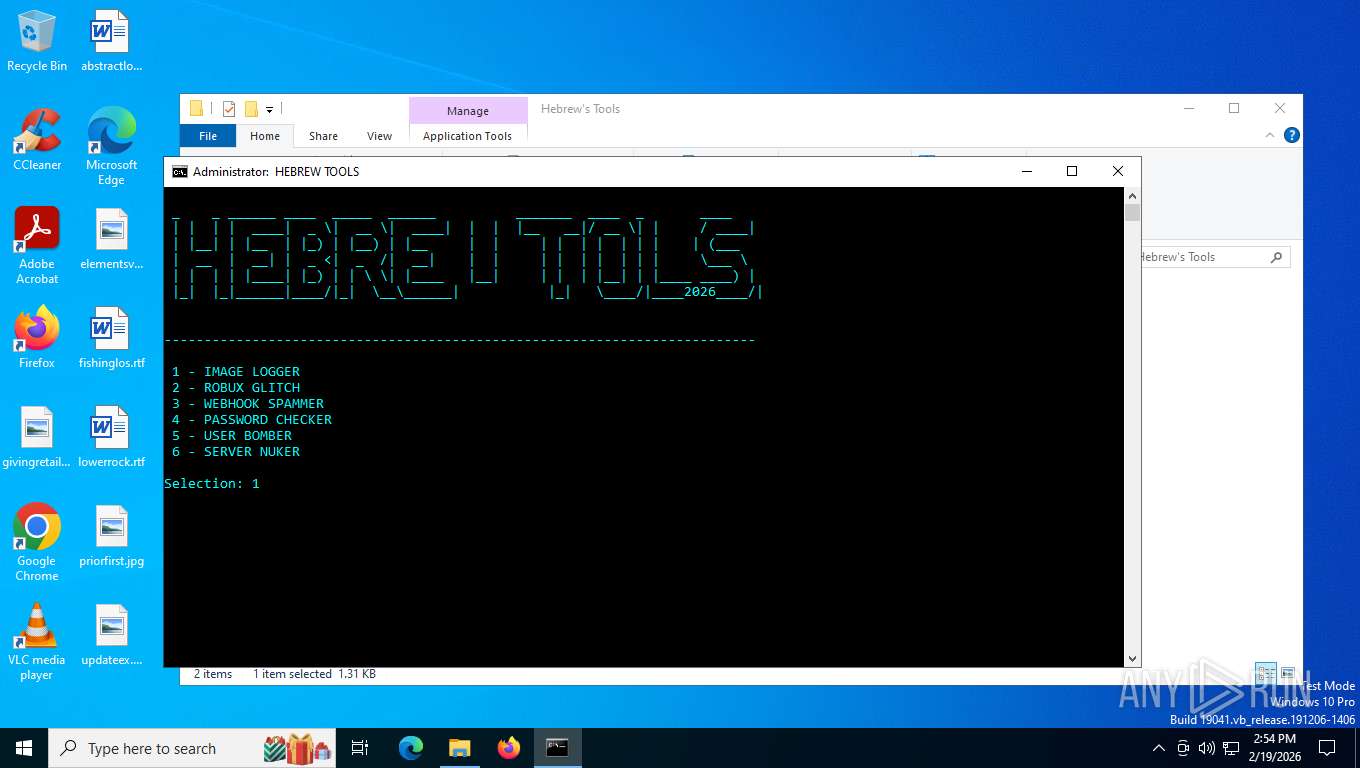
MALICIOUS
Changes the autorun value in the registry
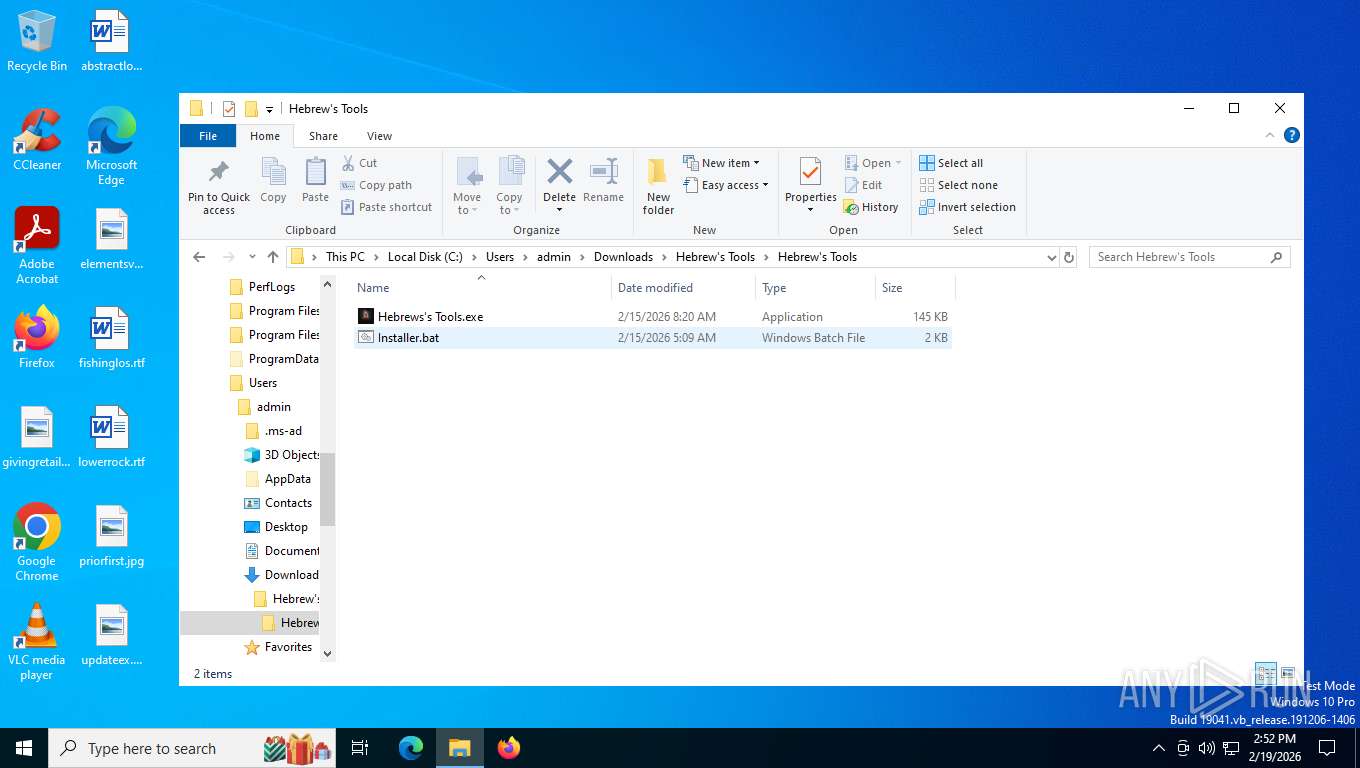
- Hebrews's Tools.exe (PID: 8332)
Create files in the Startup directory
- Hebrews's Tools.exe (PID: 8332)
Uses Task Scheduler to run other applications
- Hebrews's Tools.exe (PID: 8332)
XWORM has been detected
- Hebrews's Tools.exe (PID: 8332)
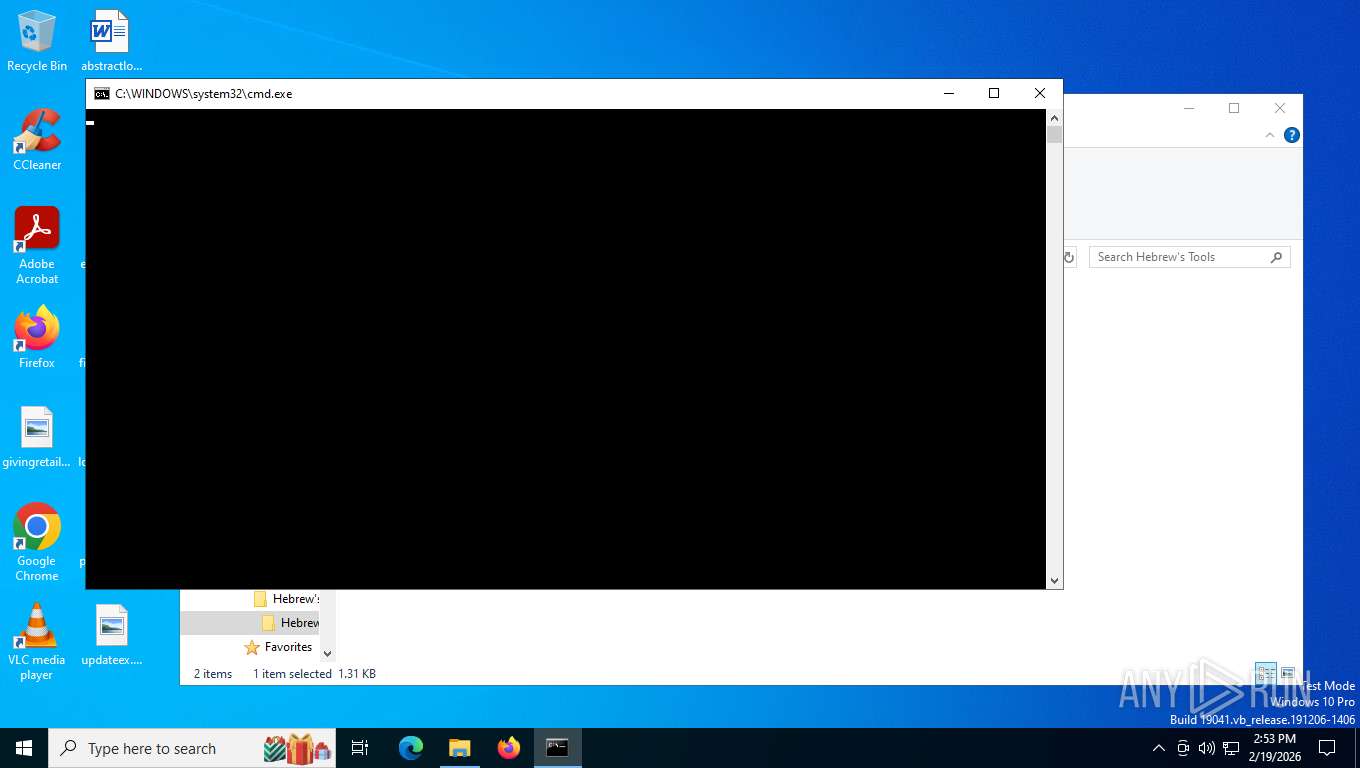
Run PowerShell with an invisible window
- powershell.exe (PID: 5632)
Bypass User Account Control (fodhelper)
- fodhelper.exe (PID: 2368)
Bypass User Account Control (Modify registry)
- reg.exe (PID: 4584)
Adds path to the Windows Defender exclusion list
- cmd.exe (PID: 2328)
Changes Windows Defender settings
- cmd.exe (PID: 2328)
SUSPICIOUS
Reads the date of Windows installation
- Hebrews's Tools.exe (PID: 7780)
- Output.exe (PID: 7344)
- Hebrews's Tools.exe (PID: 8332)
- Hebrews's Tools.exe (PID: 8104)
- Output.exe (PID: 9080)
Executable content was dropped or overwritten
- Hebrews's Tools.exe (PID: 7780)
- Output.exe (PID: 7344)
- Hebrews's Tools.exe (PID: 8332)
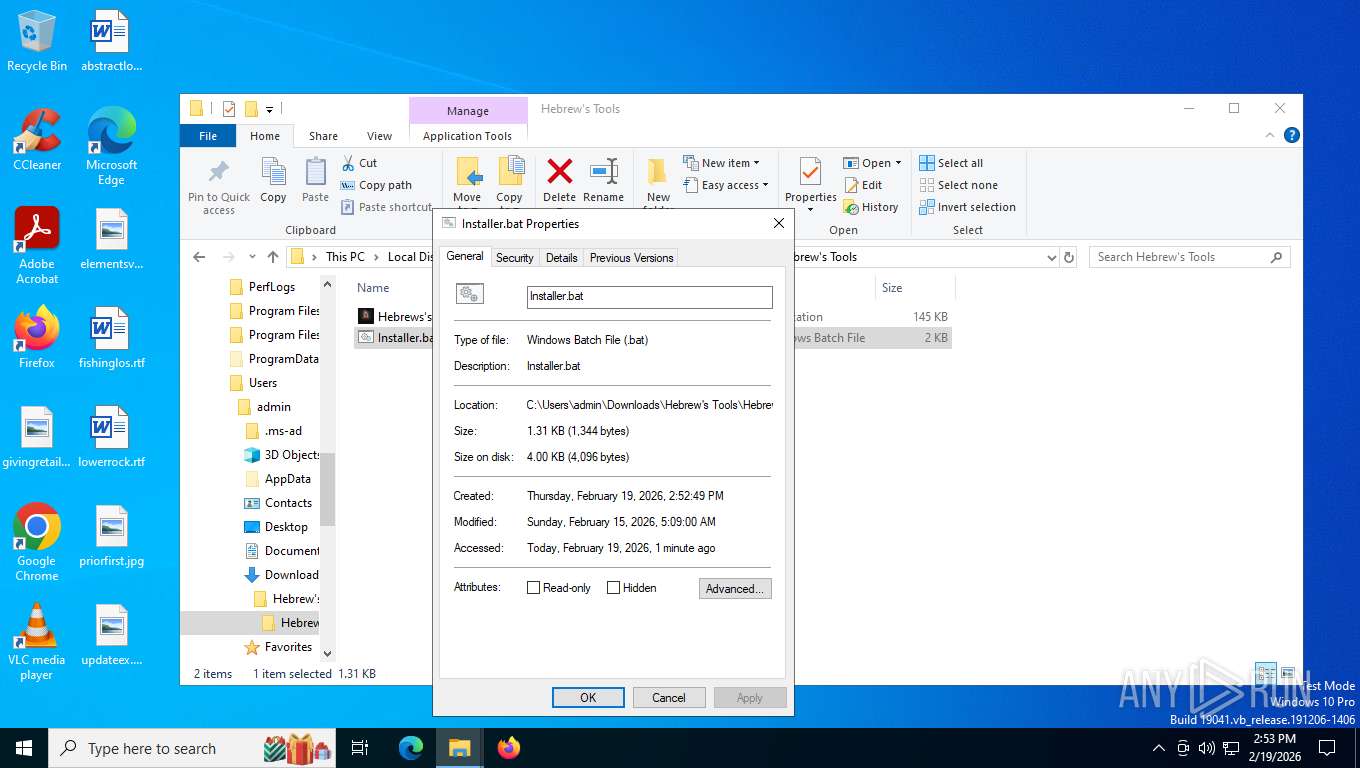
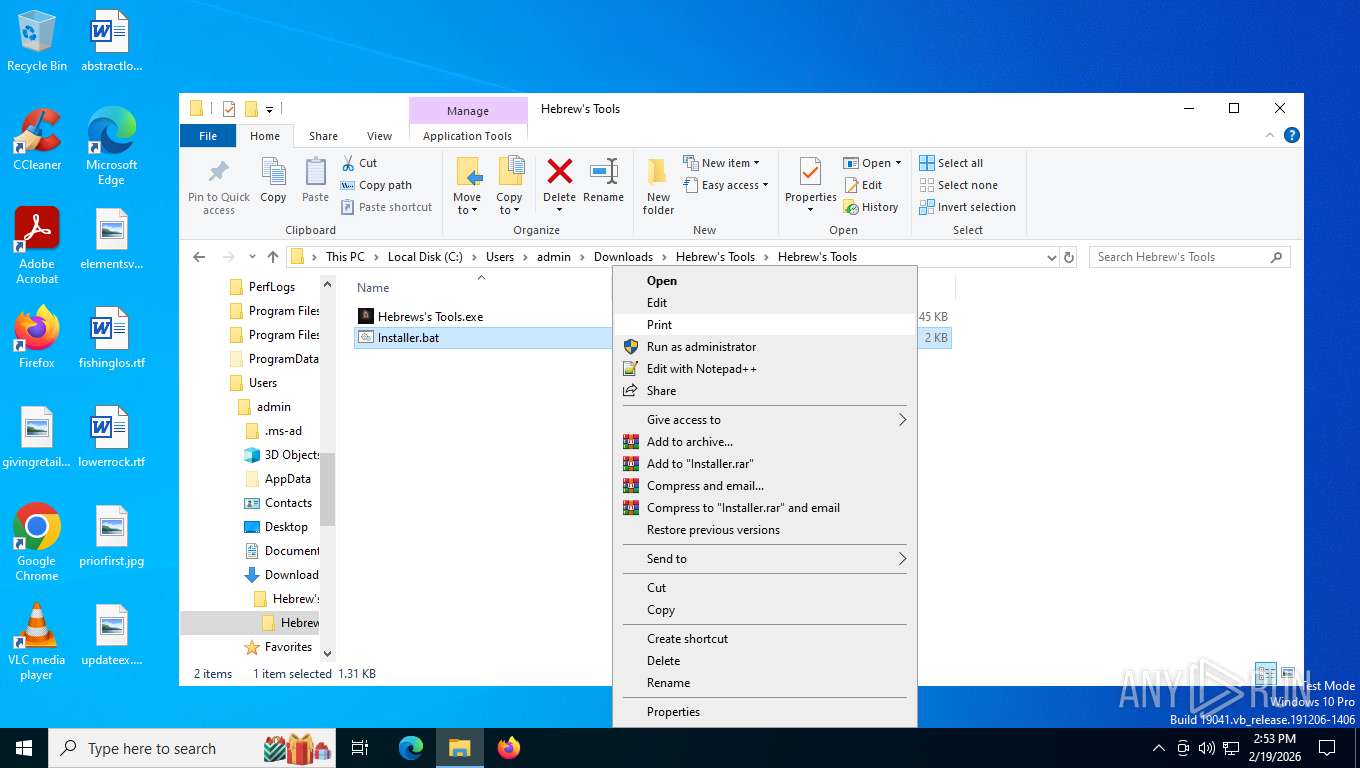
Executing commands from a ".bat" file
- Output.exe (PID: 7344)
- powershell.exe (PID: 5632)
- fodhelper.exe (PID: 2368)
- Output.exe (PID: 9080)
Starts CMD.EXE for commands execution
- Output.exe (PID: 7344)
- powershell.exe (PID: 5632)
- fodhelper.exe (PID: 2368)
- Output.exe (PID: 9080)
Checks for external IP
- svchost.exe (PID: 2292)
- Hebrews's Tools.exe (PID: 8332)
The process creates files with name similar to system file names
- Hebrews's Tools.exe (PID: 8332)
Using short paths in the command line
- powershell.exe (PID: 5632)
- cmd.exe (PID: 6668)
- cmd.exe (PID: 4964)
- fodhelper.exe (PID: 2368)
- cmd.exe (PID: 2328)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 6668)
- cmd.exe (PID: 2328)
Starts process via Powershell
- powershell.exe (PID: 5632)
Starts NET.EXE to display or manage information about active sessions
- cmd.exe (PID: 4964)
- net.exe (PID: 6792)
- net.exe (PID: 8748)
- cmd.exe (PID: 2328)
Delegate execute modification
- reg.exe (PID: 4584)
Uses TIMEOUT.EXE to delay execution
- cmd.exe (PID: 4964)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 4964)
Script adds exclusion path to Windows Defender
- cmd.exe (PID: 2328)
Using the short paths format
- Hebrews's Tools.exe (PID: 8104)
The executable file from the user directory is run by the CMD process
- Hebrews's Tools.exe (PID: 8104)
Changes default file association
- reg.exe (PID: 4584)
The process executes via Task Scheduler
- svchost.exe (PID: 9092)
- svchost.exe (PID: 2148)
- svchost.exe (PID: 8388)
INFO
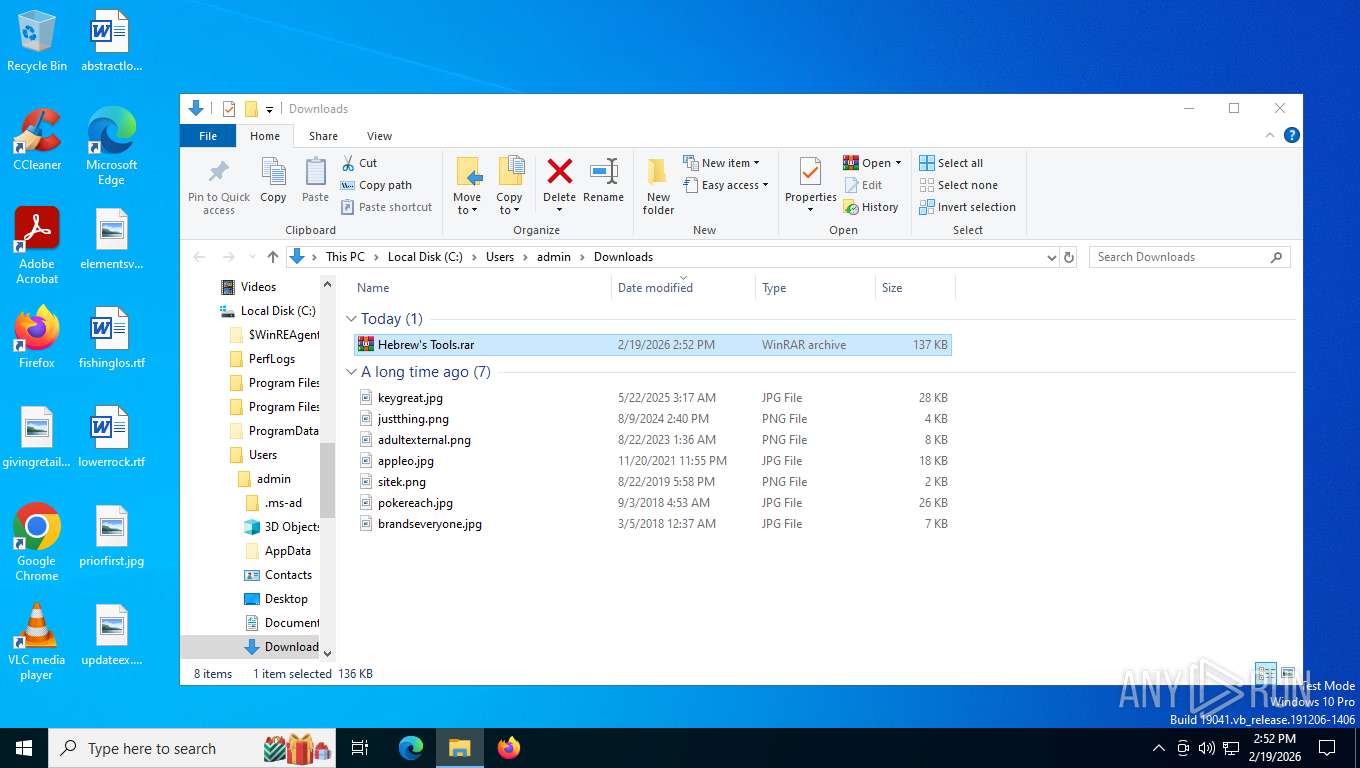
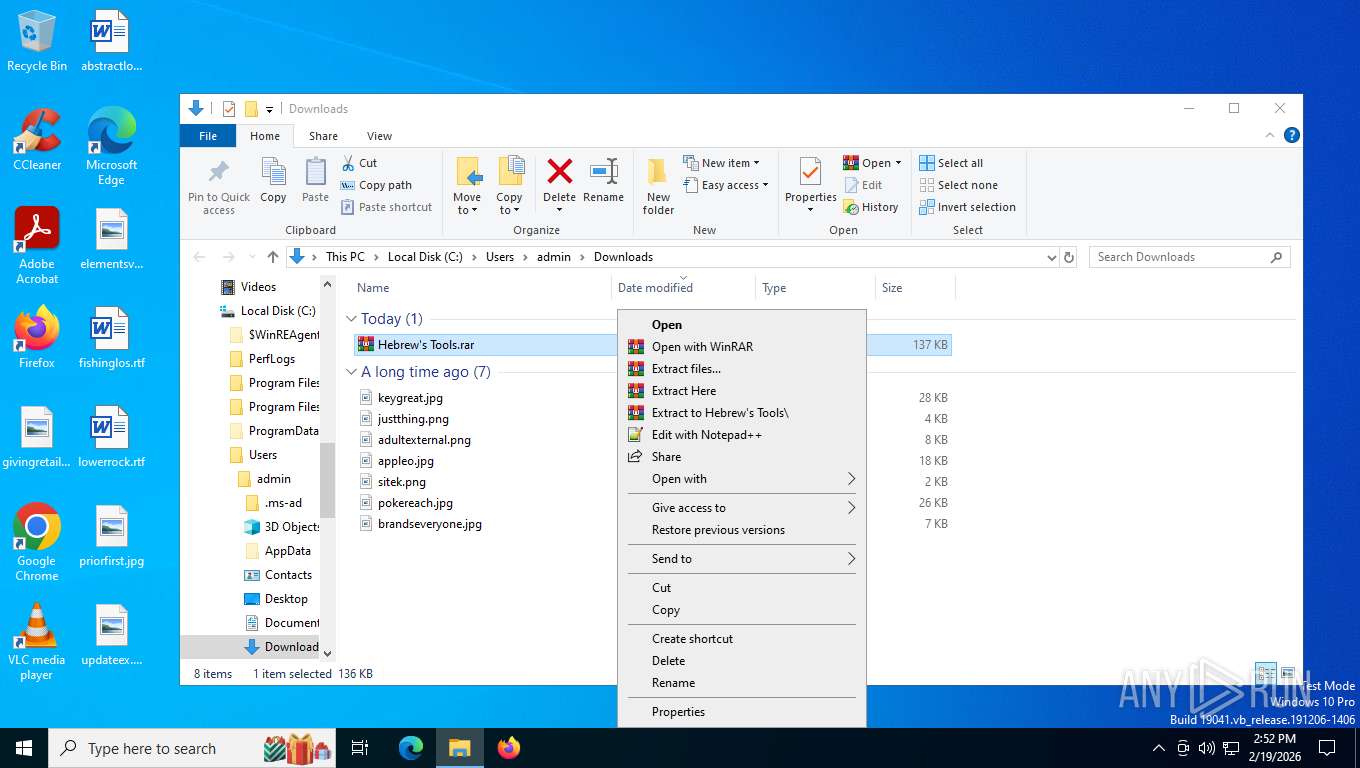
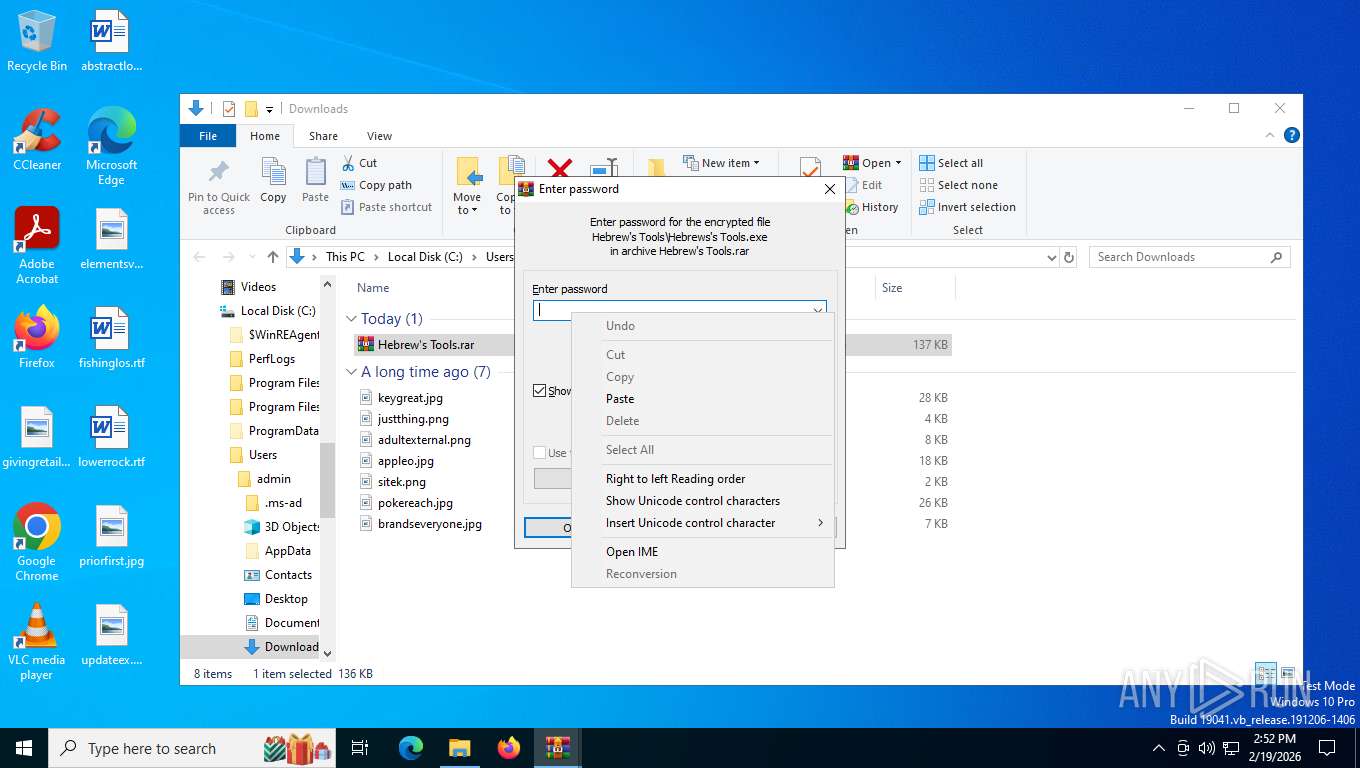
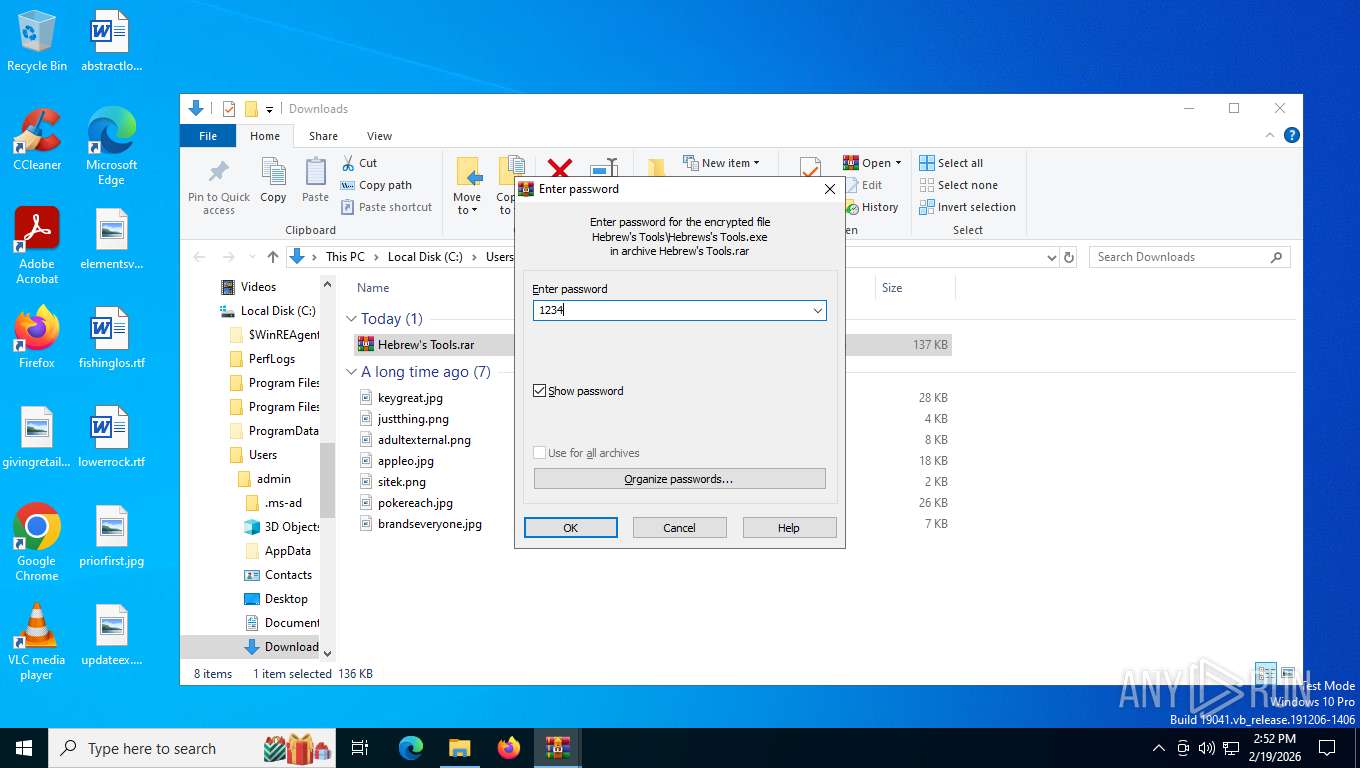
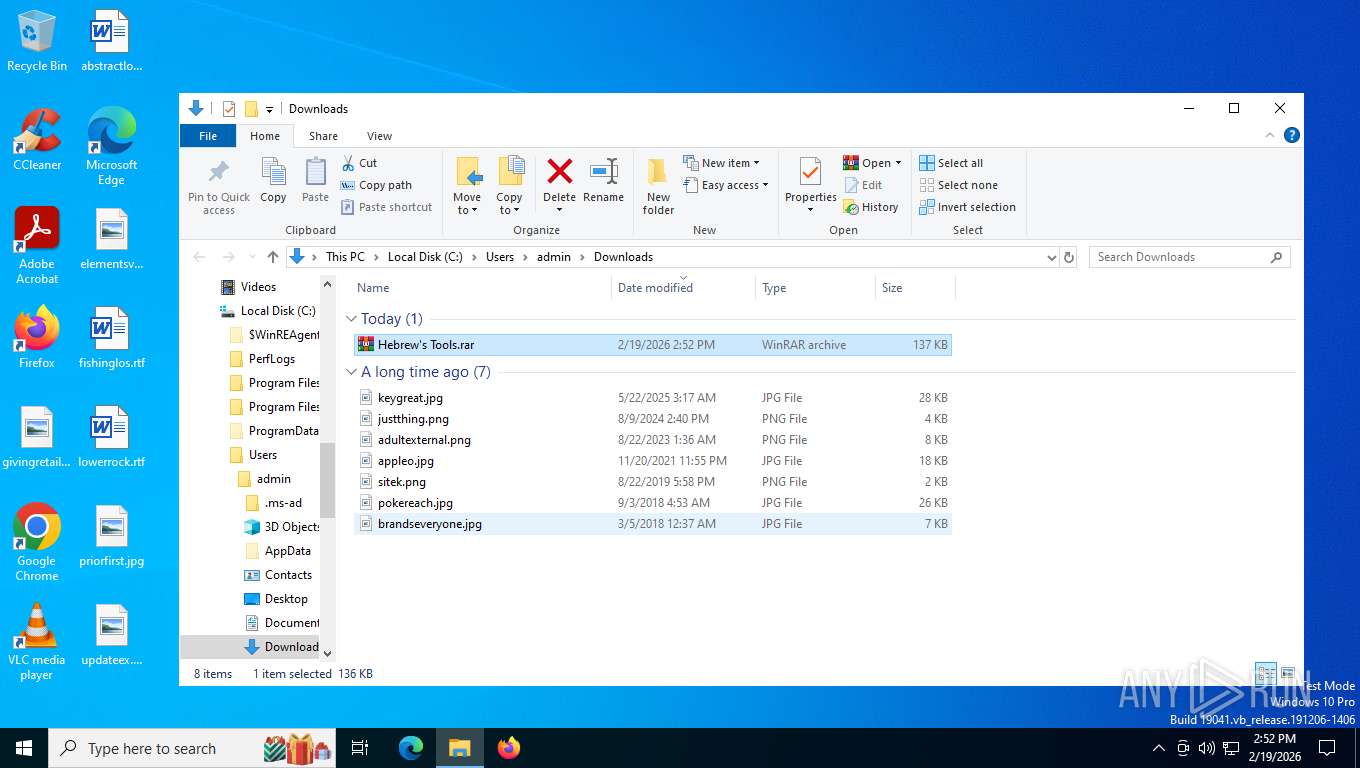
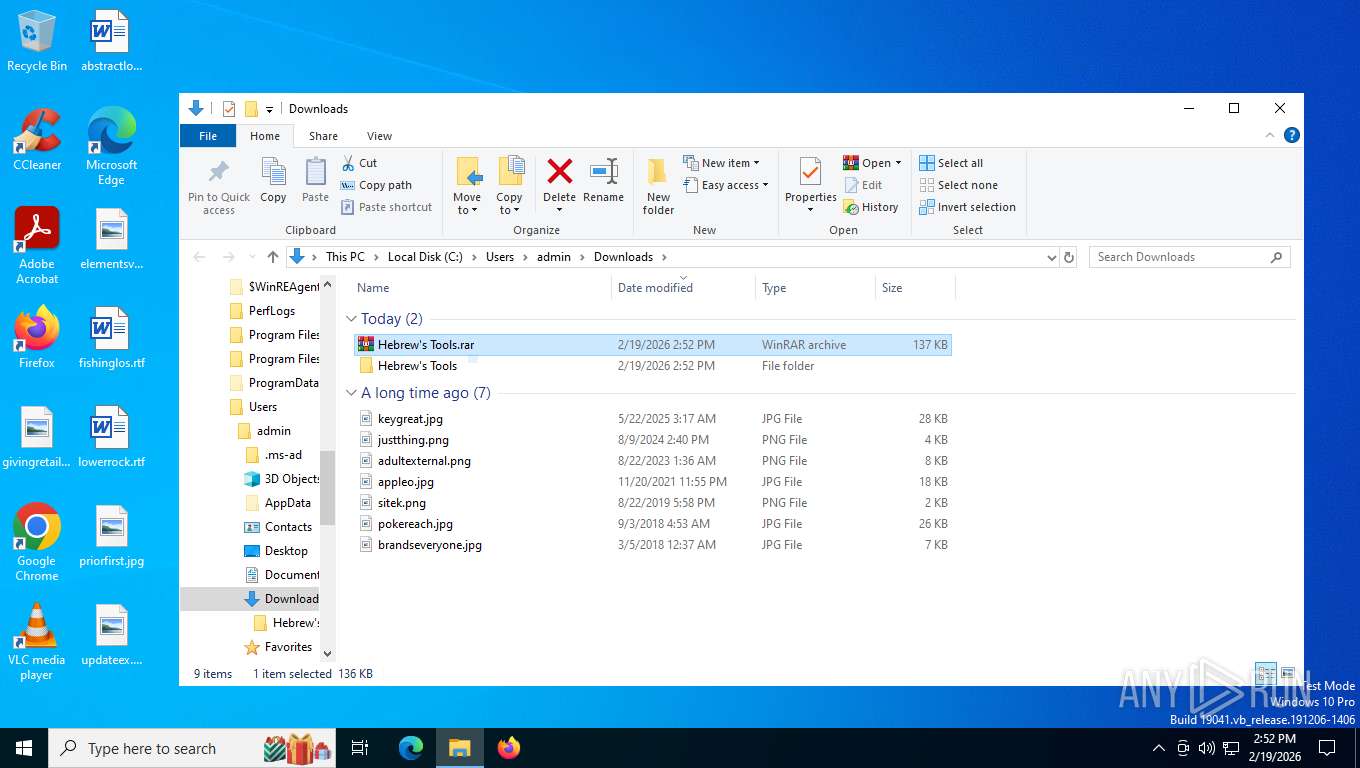
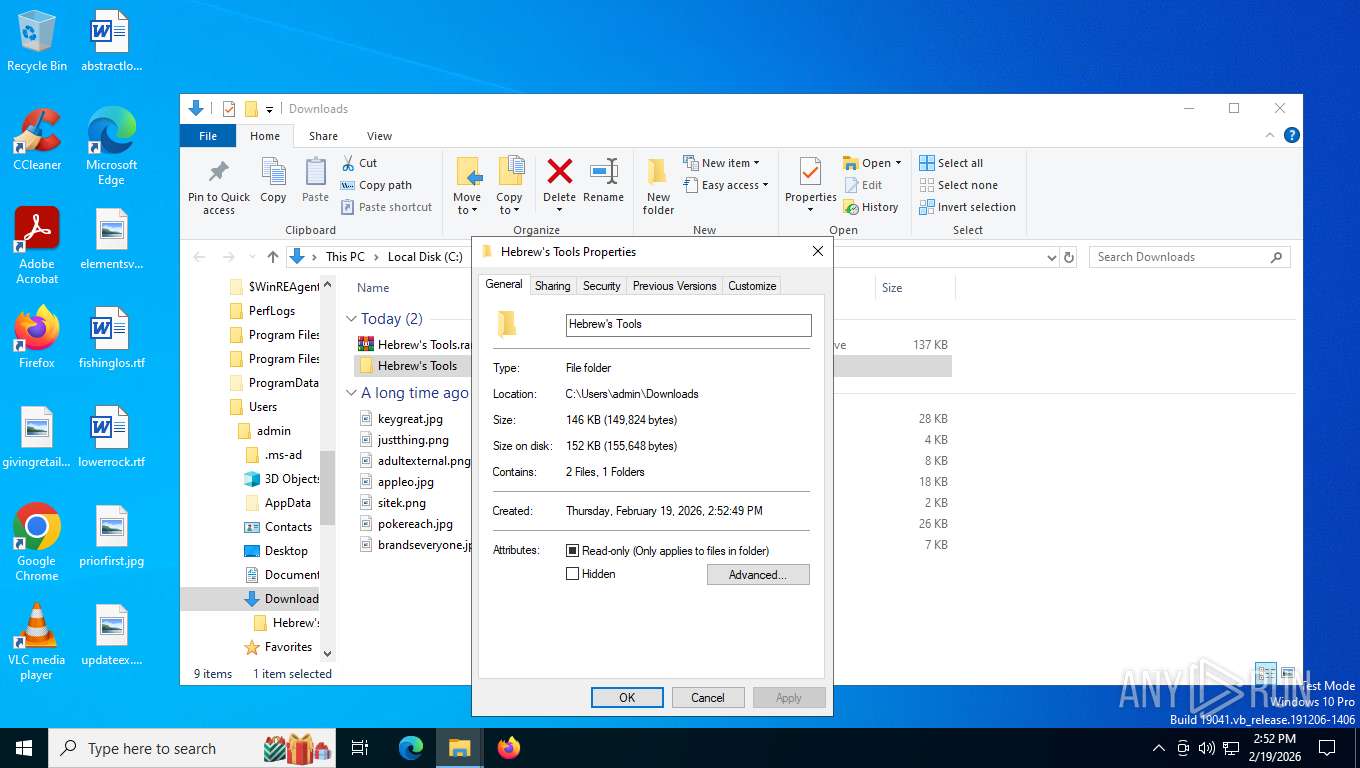
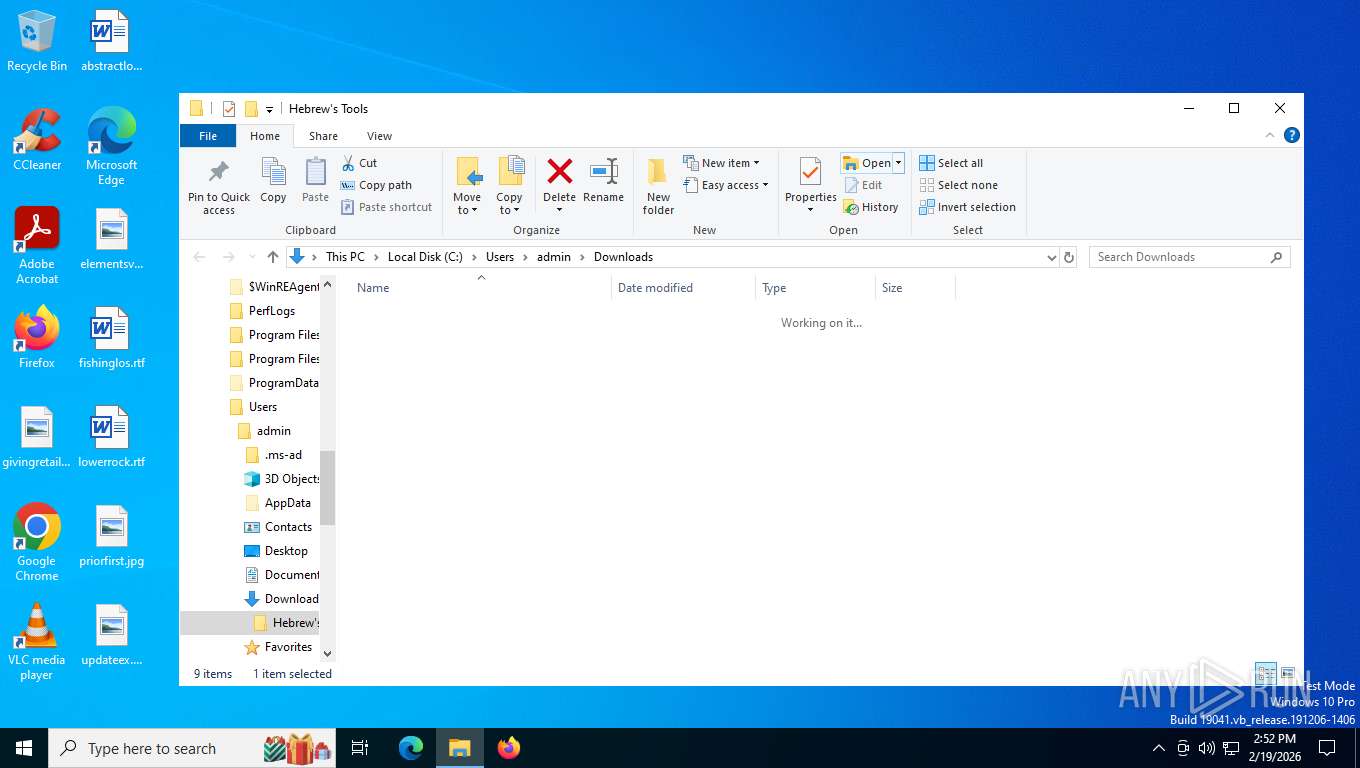
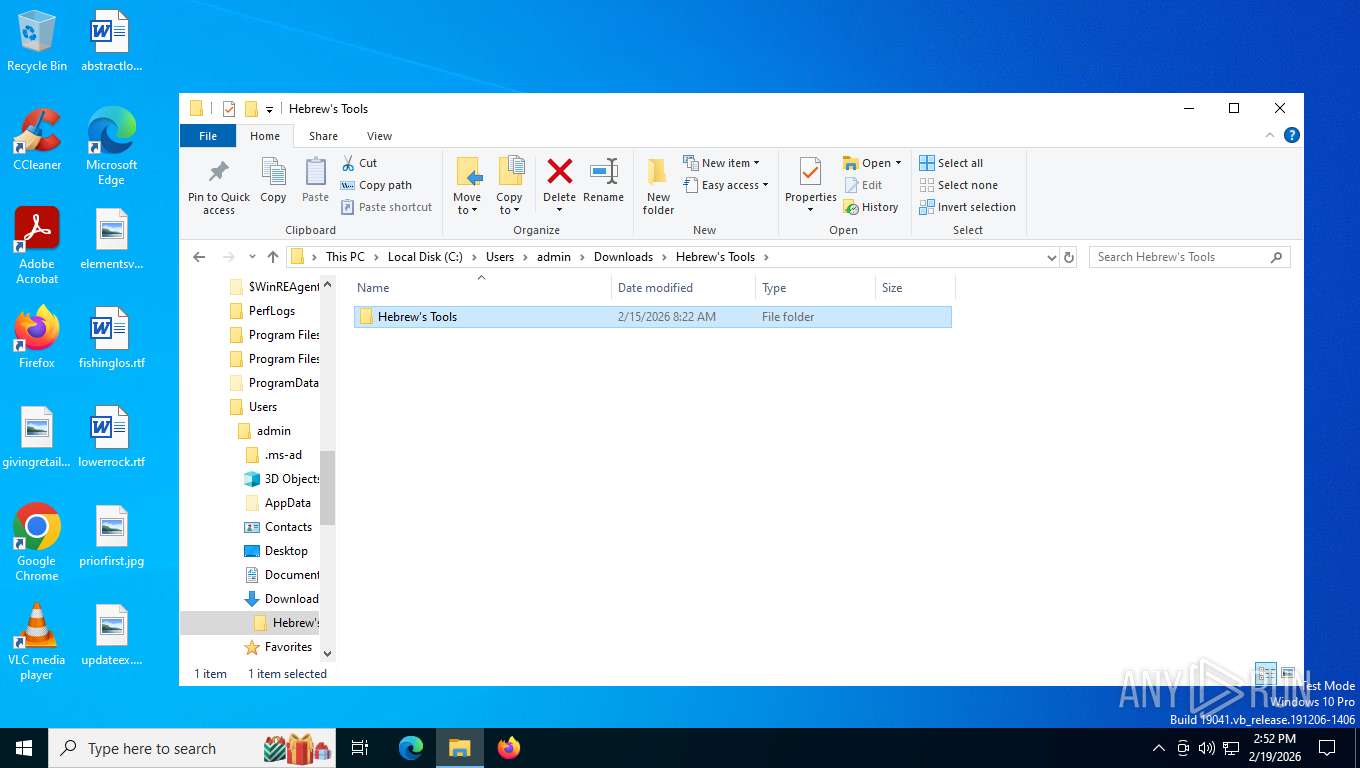
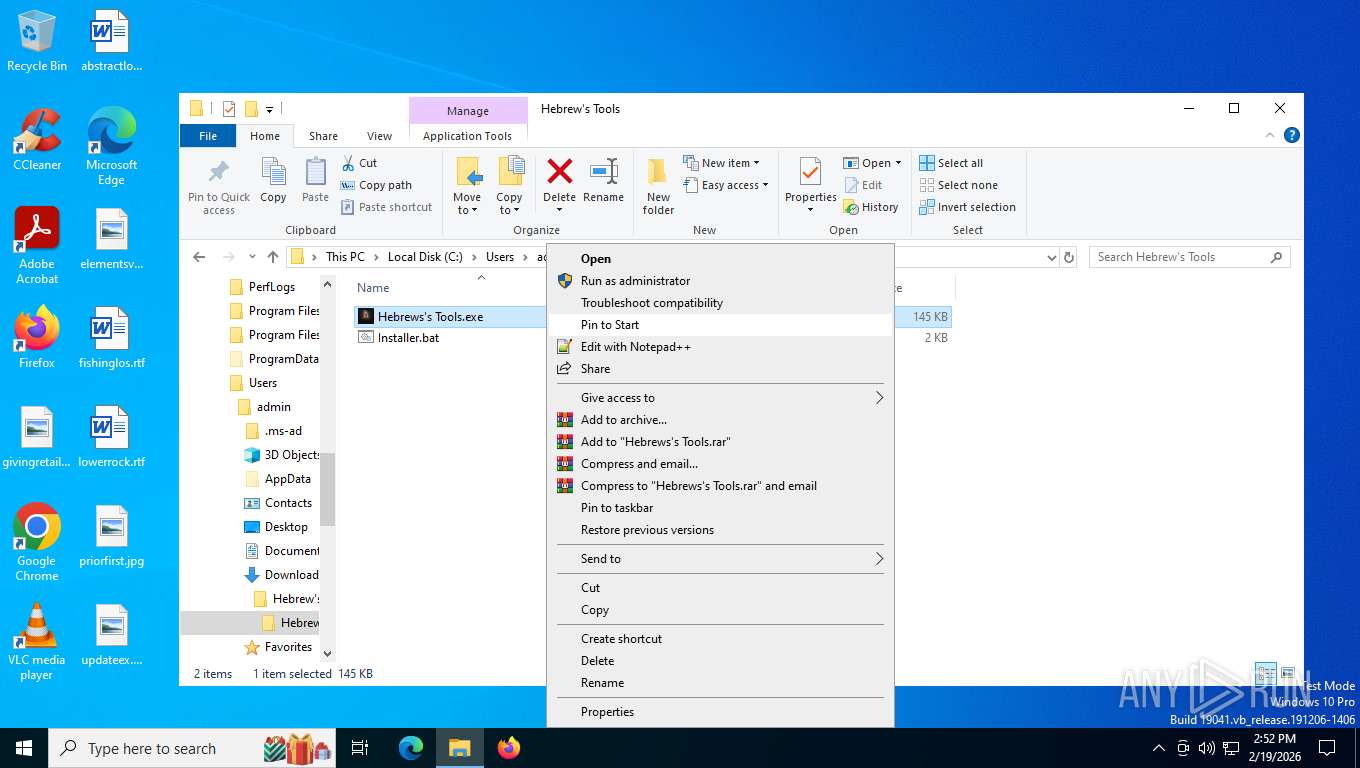
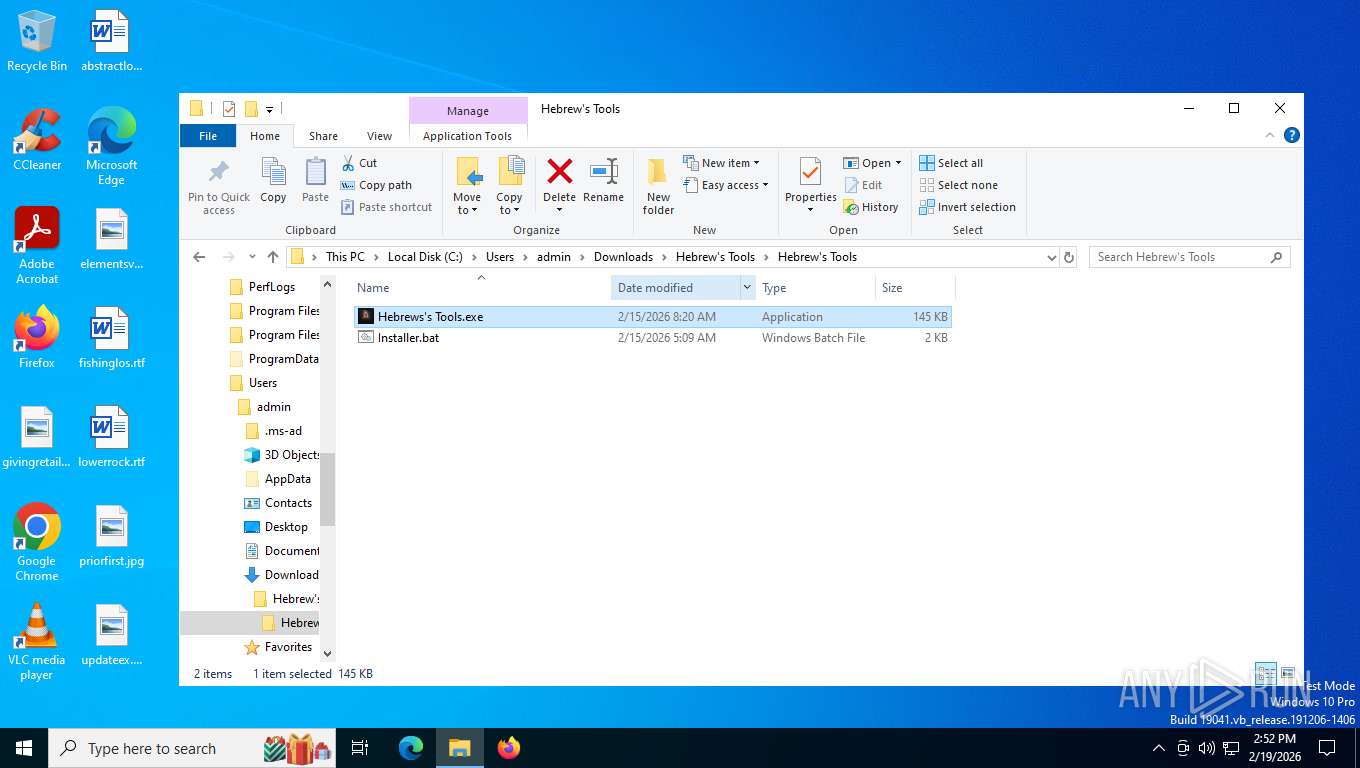
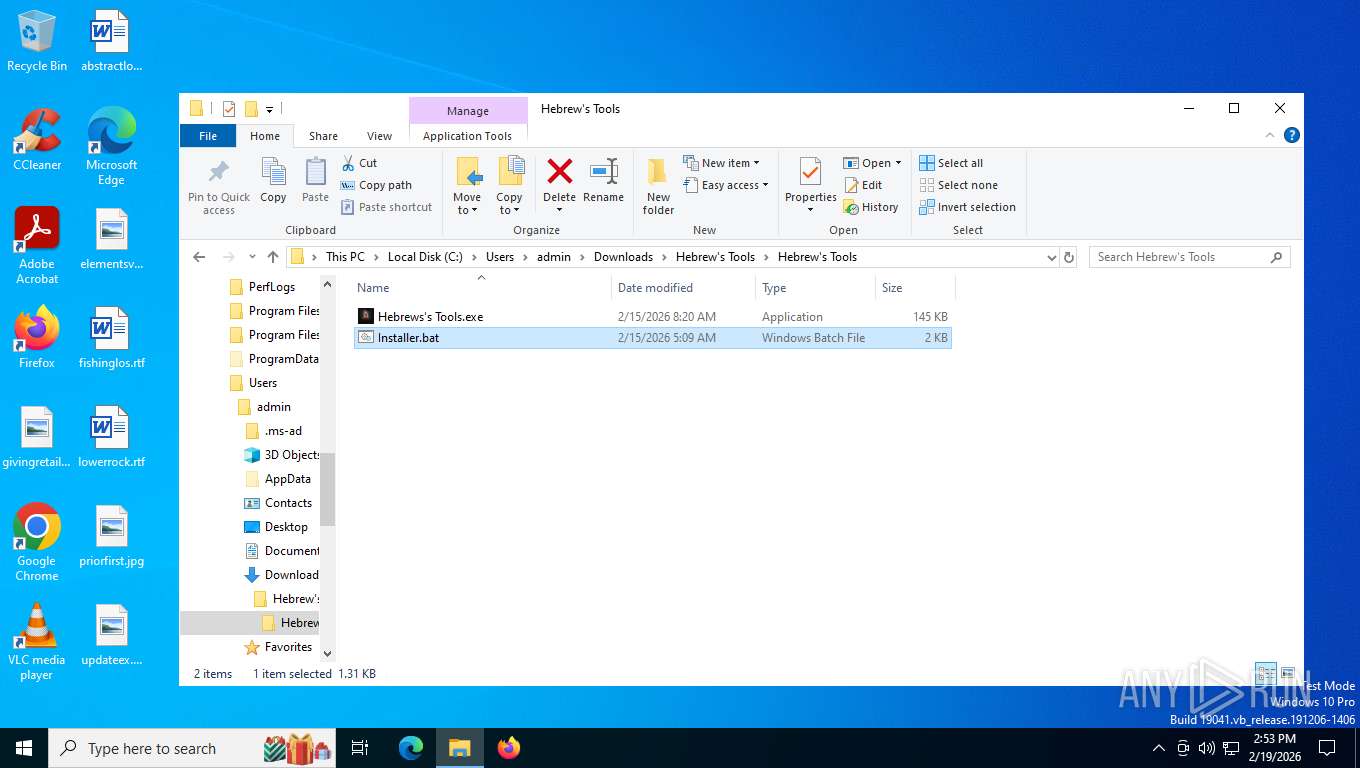
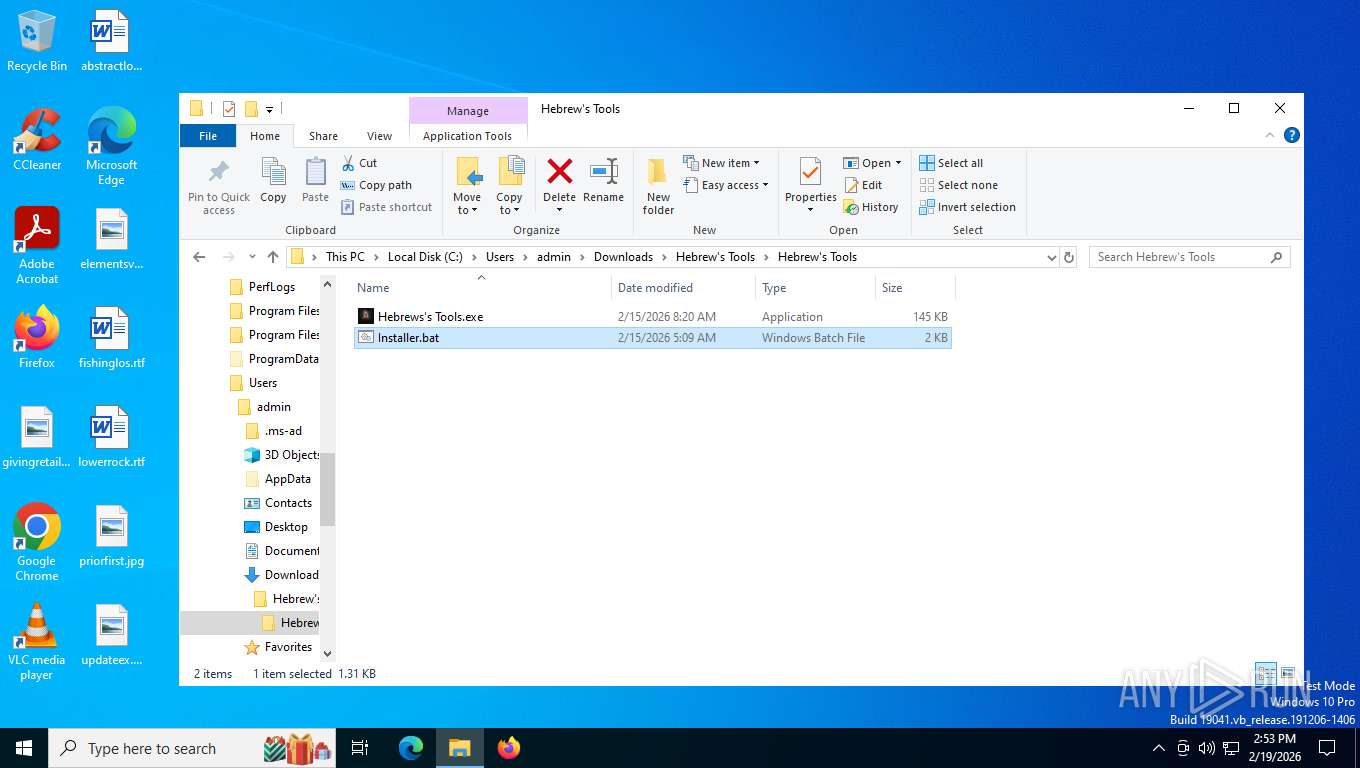
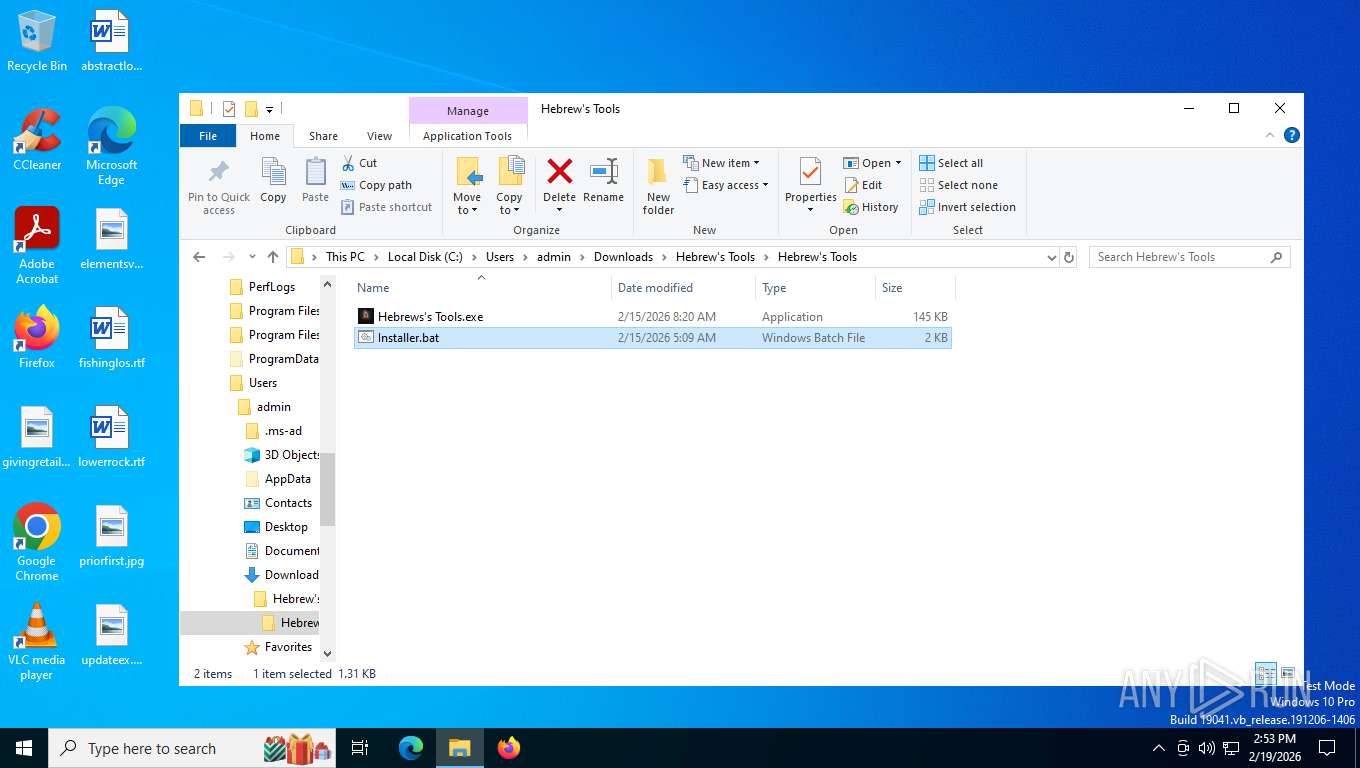
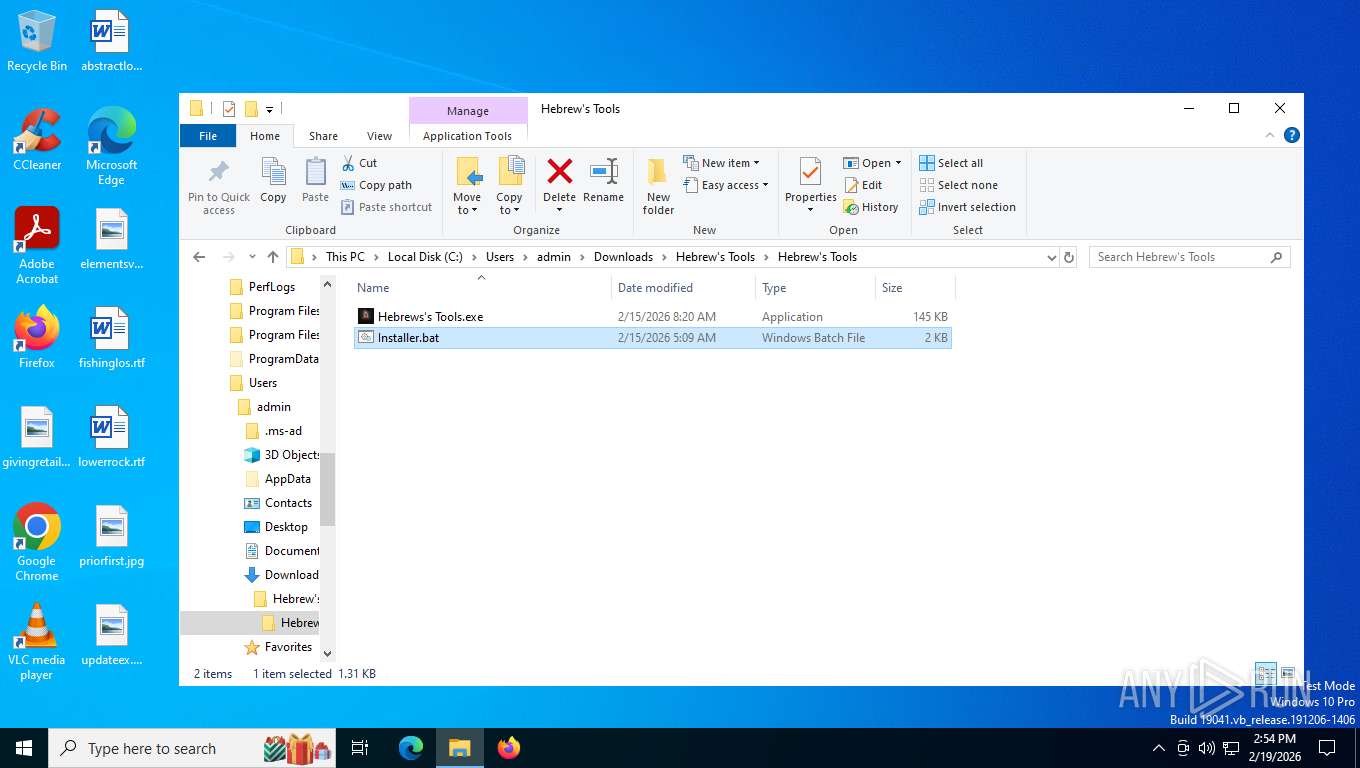
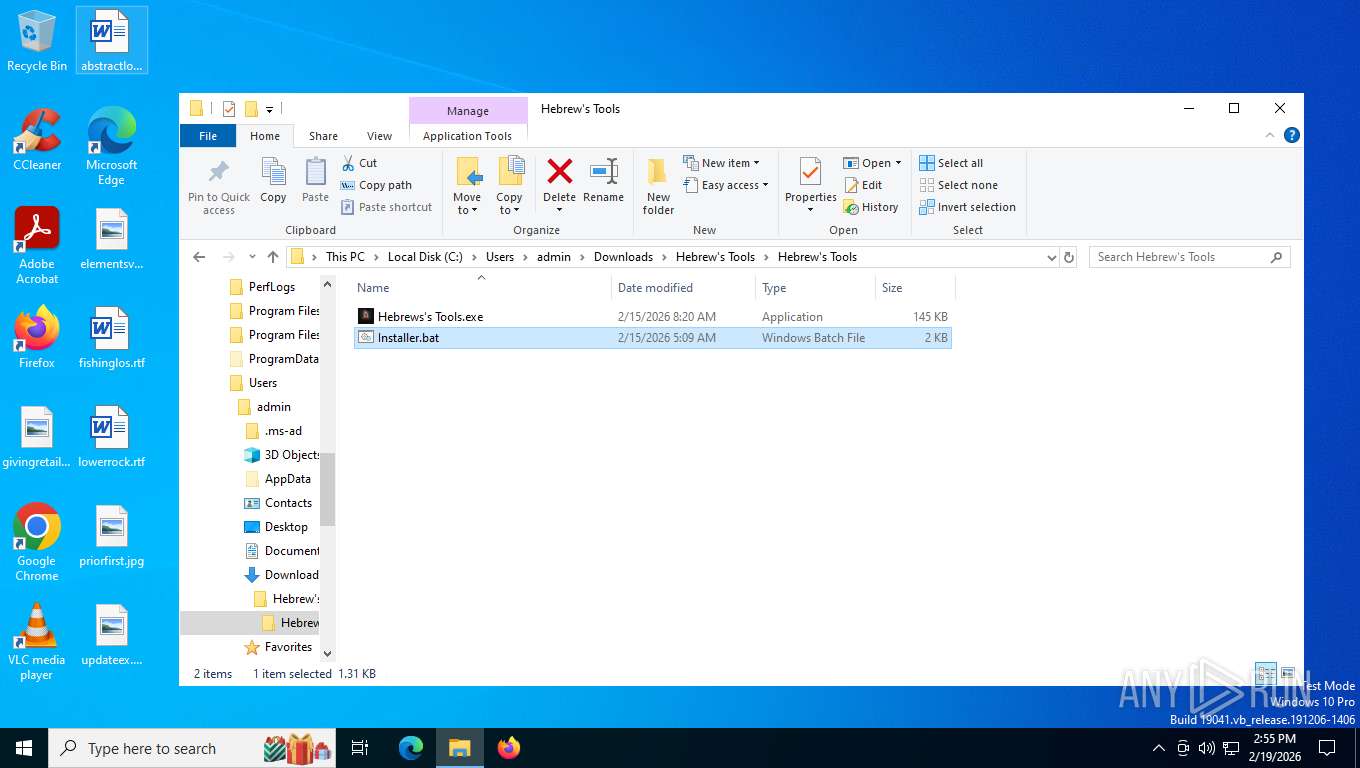
Launching a file from the Downloads directory
- chrome.exe (PID: 8952)
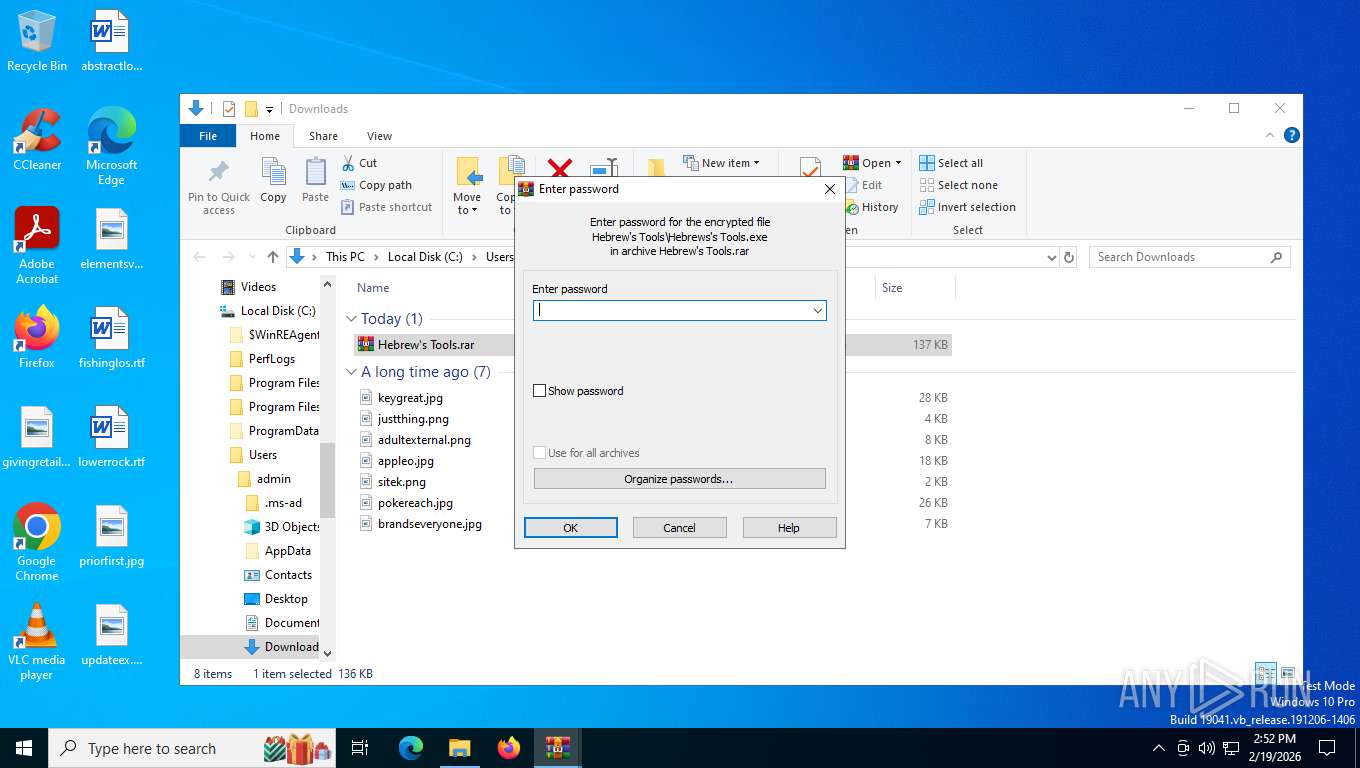
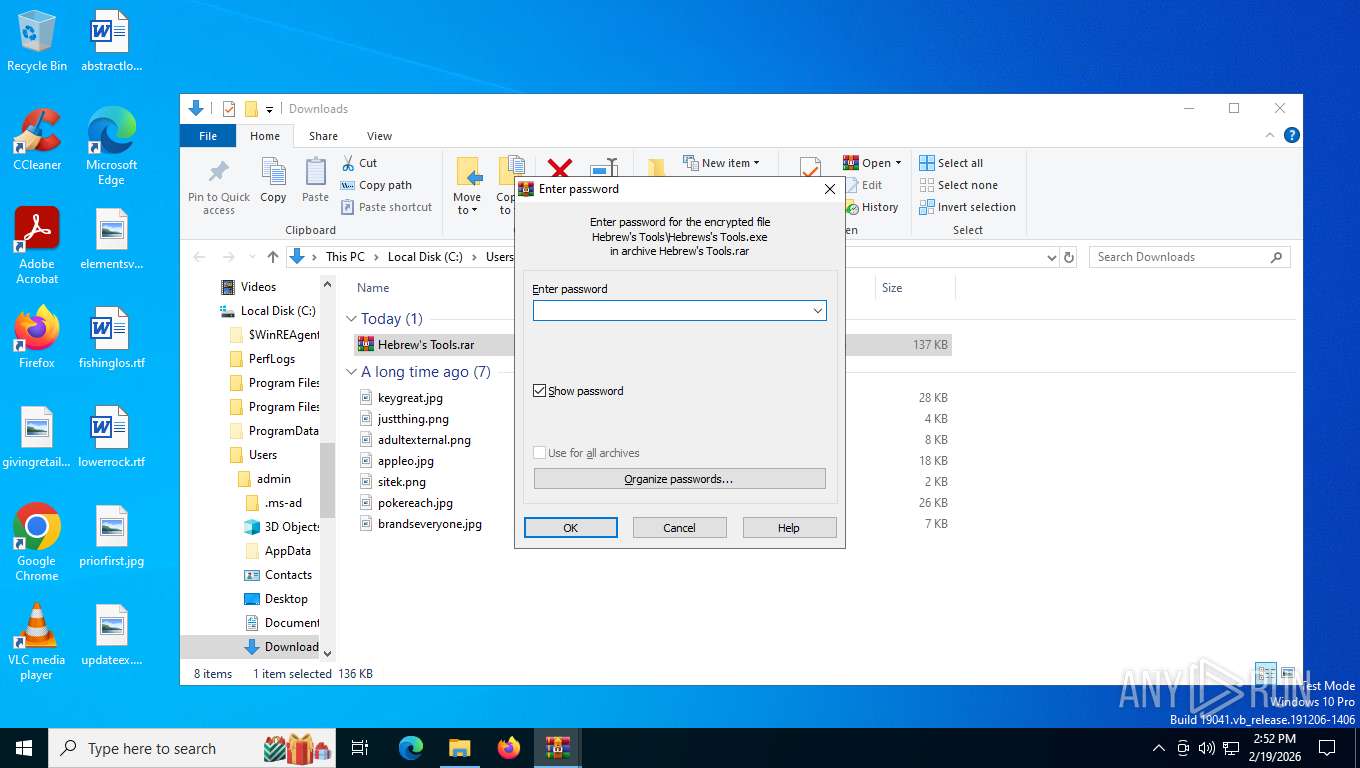
Manual execution by a user
- WinRAR.exe (PID: 2640)
- Hebrews's Tools.exe (PID: 7780)
- cmd.exe (PID: 6668)
Checks supported languages
- Hebrews's Tools.exe (PID: 7780)
- Output.exe (PID: 7344)
- Hebrews's Tools.exe (PID: 8332)
- Hebrews's Tools.exe (PID: 8104)
- Output.exe (PID: 9080)
- Hebrews's Tools.exe (PID: 8080)
- svchost.exe (PID: 2148)
- svchost.exe (PID: 8388)
- svchost.exe (PID: 9092)
Creates files or folders in the user directory
- Hebrews's Tools.exe (PID: 7780)
- Output.exe (PID: 7344)
- Hebrews's Tools.exe (PID: 8332)
Drops script file
- chrome.exe (PID: 8952)
- WinRAR.exe (PID: 2640)
- Output.exe (PID: 7344)
- cmd.exe (PID: 3092)
- cmd.exe (PID: 6668)
- powershell.exe (PID: 5632)
- cmd.exe (PID: 4964)
- cmd.exe (PID: 2328)
- powershell.exe (PID: 8228)
- Output.exe (PID: 9080)
- cmd.exe (PID: 1760)
Reads the computer name
- Hebrews's Tools.exe (PID: 7780)
- Output.exe (PID: 7344)
- Hebrews's Tools.exe (PID: 8332)
- Hebrews's Tools.exe (PID: 8104)
- Output.exe (PID: 9080)
- Hebrews's Tools.exe (PID: 8080)
- svchost.exe (PID: 2148)
- svchost.exe (PID: 8388)
- svchost.exe (PID: 9092)
Reads the machine GUID from the registry
- Hebrews's Tools.exe (PID: 7780)
- Output.exe (PID: 7344)
- Hebrews's Tools.exe (PID: 8332)
- Hebrews's Tools.exe (PID: 8104)
- Output.exe (PID: 9080)
- Hebrews's Tools.exe (PID: 8080)
- svchost.exe (PID: 2148)
- svchost.exe (PID: 8388)
- svchost.exe (PID: 9092)
Application launched itself
- chrome.exe (PID: 8952)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2640)
Reads security settings of Internet Explorer
- Hebrews's Tools.exe (PID: 7780)
- Output.exe (PID: 7344)
- Hebrews's Tools.exe (PID: 8332)
- fodhelper.exe (PID: 2368)
- Hebrews's Tools.exe (PID: 8104)
- Output.exe (PID: 9080)
Process checks computer location settings
- Hebrews's Tools.exe (PID: 7780)
- Output.exe (PID: 7344)
- Hebrews's Tools.exe (PID: 8332)
- Hebrews's Tools.exe (PID: 8104)
- Output.exe (PID: 9080)
Disables trace logs
- Hebrews's Tools.exe (PID: 8332)
Checks proxy server information
- Hebrews's Tools.exe (PID: 8332)
- slui.exe (PID: 1784)
Reads Environment values
- Hebrews's Tools.exe (PID: 8332)
Launching a file from a Registry key
- Hebrews's Tools.exe (PID: 8332)
Launching a file from the Startup directory
- Hebrews's Tools.exe (PID: 8332)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 8228)
Create files in a temporary directory
- Hebrews's Tools.exe (PID: 8332)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
218
Monitored processes
68
Malicious processes
9
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 552 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --field-trial-handle=5728,i,12786430191246565090,7524361713886594296,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version=20251218-201203.402000 --mojo-platform-channel-handle=5780 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 664 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.FileUtilService --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --field-trial-handle=4772,i,12786430191246565090,7524361713886594296,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version=20251218-201203.402000 --mojo-platform-channel-handle=3164 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 680 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 752 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --field-trial-handle=5824,i,12786430191246565090,7524361713886594296,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version=20251218-201203.402000 --mojo-platform-channel-handle=5676 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 1320 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --field-trial-handle=5900,i,12786430191246565090,7524361713886594296,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version=20251218-201203.402000 --mojo-platform-channel-handle=6028 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 1488 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --field-trial-handle=5920,i,12786430191246565090,7524361713886594296,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version=20251218-201203.402000 --mojo-platform-channel-handle=6072 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 1700 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --field-trial-handle=5568,i,12786430191246565090,7524361713886594296,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version=20251218-201203.402000 --mojo-platform-channel-handle=5752 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 1760 | C:\WINDOWS\system32\cmd.exe /c ""C:\Users\admin\AppData\Roaming\omega___.bat" " | C:\Windows\System32\cmd.exe | — | Output.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 3221225786 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1784 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1860 | C:\WINDOWS\system32\net1 session | C:\Windows\System32\net1.exe | — | net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Net Command Exit code: 2 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
16 944
Read events
16 919
Write events
24
Delete events
1
Modification events
| (PID) Process: | (2640) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 1 | |||
| (PID) Process: | (2640) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2640) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2640) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2640) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (8332) Hebrews's Tools.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Hebrews's Tools_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (8332) Hebrews's Tools.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Hebrews's Tools_RASAPI32 |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (8332) Hebrews's Tools.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Hebrews's Tools_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (8332) Hebrews's Tools.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Hebrews's Tools_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: | |||
| (PID) Process: | (8332) Hebrews's Tools.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Hebrews's Tools_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: | |||
Executable files
4
Suspicious files
113
Text files
67
Unknown types
15
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 8952 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old~RF1e4ee9.TMP | — | |
MD5:— | SHA256:— | |||
| 8952 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 8952 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Segmentation Platform\SegmentInfoDB\LOG.old~RF1e4ee9.TMP | — | |
MD5:— | SHA256:— | |||
| 8952 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Segmentation Platform\SegmentInfoDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 8952 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF1e4ee9.TMP | — | |
MD5:— | SHA256:— | |||
| 8952 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\ClientCertificates\LOG.old~RF1e4ef8.TMP | — | |
MD5:— | SHA256:— | |||
| 8952 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 8952 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Segmentation Platform\SignalDB\LOG.old~RF1e4ef8.TMP | — | |
MD5:— | SHA256:— | |||
| 8952 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Segmentation Platform\SignalDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 8952 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\ClientCertificates\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
223
TCP/UDP connections
63
DNS requests
56
Threats
31
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
7376 | chrome.exe | GET | 200 | 51.75.242.210:443 | https://gofile.io/plugins/fontawesome/css/all.min.css | unknown | text | 94.2 Kb | unknown |
7376 | chrome.exe | GET | 200 | 142.250.201.67:443 | https://clientservices.googleapis.com/chrome-variations/seed?osname=win&channel=stable&milestone=133 | unknown | binary | 86.3 Kb | whitelisted |
7376 | chrome.exe | GET | 200 | 51.75.242.210:443 | https://gofile.io/d/46tDbJ | unknown | html | 8.22 Kb | unknown |
7376 | chrome.exe | GET | 200 | 51.75.242.210:443 | https://gofile.io/dist/js/framework.js | unknown | text | 15.8 Kb | unknown |
7376 | chrome.exe | GET | 200 | 142.250.186.46:80 | http://clients2.google.com/time/1/current?cup2key=8:75afSLNWPFgjTLD8cMx8ThKWHgUyVF4ikuVseGkxcAc&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | unknown | — | — | whitelisted |
7376 | chrome.exe | GET | 200 | 142.251.208.10:443 | https://safebrowsingohttpgateway.googleapis.com/v1/ohttp/hpkekeyconfig?key=AIzaSyA2KlwBX3mkFo30om9LUFYQhpqLoa_BNhE | unknown | image | 41 b | whitelisted |
8400 | svchost.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
7376 | chrome.exe | GET | 200 | 51.75.242.210:443 | https://gofile.io/dist/css/output.css | unknown | text | 53.9 Kb | unknown |
7376 | chrome.exe | POST | 200 | 142.251.127.84:443 | https://accounts.google.com/ListAccounts?gpsia=1&source=ChromiumBrowser&json=standard | unknown | text | 17 b | whitelisted |
7376 | chrome.exe | GET | 200 | 51.75.242.210:443 | https://gofile.io/dist/js/profile.js | unknown | text | 24.3 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
8400 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6332 | RUXIMICS.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6768 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7376 | chrome.exe | 142.250.201.67:443 | clientservices.googleapis.com | GOOGLE | US | whitelisted |
7376 | chrome.exe | 142.251.208.10:443 | safebrowsingohttpgateway.googleapis.com | GOOGLE | US | whitelisted |
7376 | chrome.exe | 51.75.242.210:443 | gofile.io | OVH | FR | whitelisted |
7376 | chrome.exe | 142.250.186.46:80 | clients2.google.com | GOOGLE | US | whitelisted |
7376 | chrome.exe | 142.251.127.84:443 | accounts.google.com | GOOGLE | US | whitelisted |
4 | System | 192.168.100.255:138 | — | Not routed | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |
clients2.google.com |
| whitelisted |
gofile.io |
| whitelisted |
safebrowsingohttpgateway.googleapis.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| whitelisted |
update.googleapis.com |
| whitelisted |
www.google.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7376 | chrome.exe | Misc activity | ET FILE_SHARING File Sharing Related Domain in TLS SNI (gofile .io) |
7376 | chrome.exe | Misc activity | ET FILE_SHARING File Sharing Related Domain in TLS SNI (gofile .io) |
7376 | chrome.exe | Potentially Bad Traffic | ET FILE_SHARING Online File Storage Domain in DNS Lookup (gofile .io) |
7376 | chrome.exe | Misc activity | ET FILE_SHARING File Sharing Related Domain in TLS SNI (gofile .io) |
7376 | chrome.exe | Potentially Bad Traffic | ET FILE_SHARING Online File Storage Domain in DNS Lookup (gofile .io) |
7376 | chrome.exe | Misc activity | ET FILE_SHARING File Sharing Related Domain in TLS SNI (gofile .io) |
7376 | chrome.exe | Potentially Bad Traffic | ET FILE_SHARING Online File Storage Domain in DNS Lookup (gofile .io) |
7376 | chrome.exe | Potentially Bad Traffic | ET FILE_SHARING Online File Storage Domain in DNS Lookup (gofile .io) |
7376 | chrome.exe | Misc activity | ET FILE_SHARING File Sharing Related Domain in TLS SNI (gofile .io) |
8400 | svchost.exe | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |