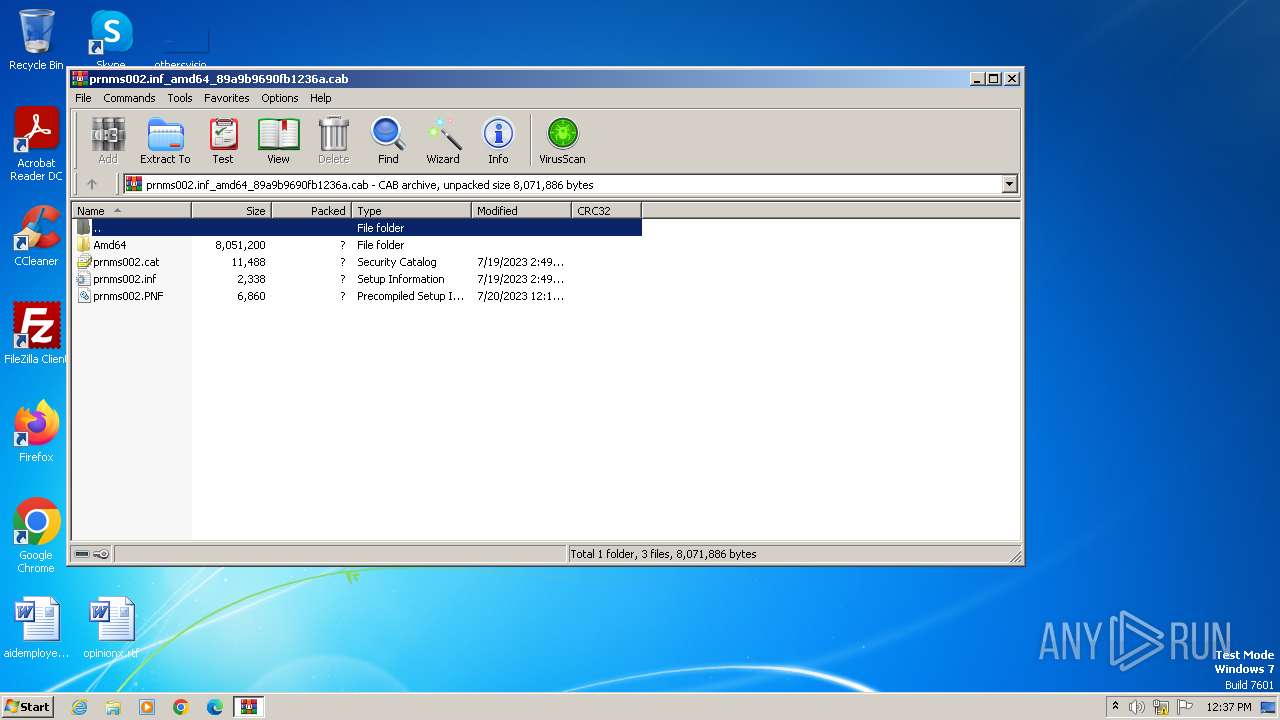
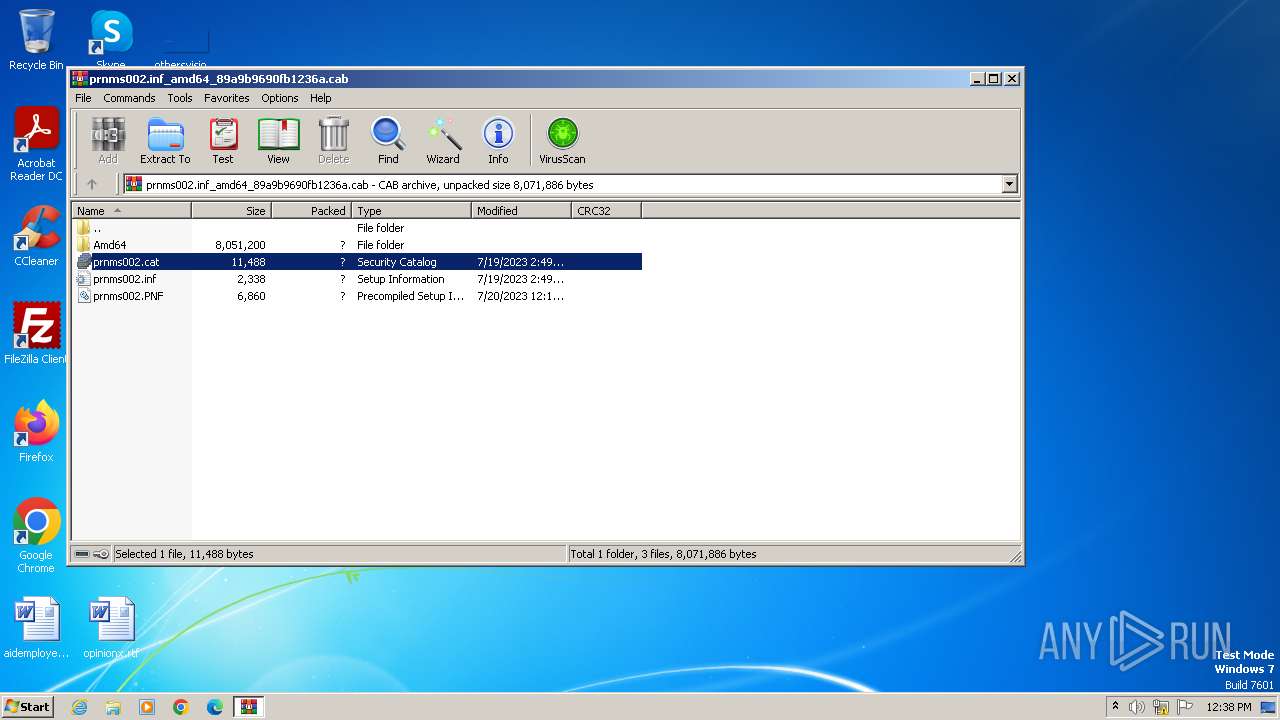
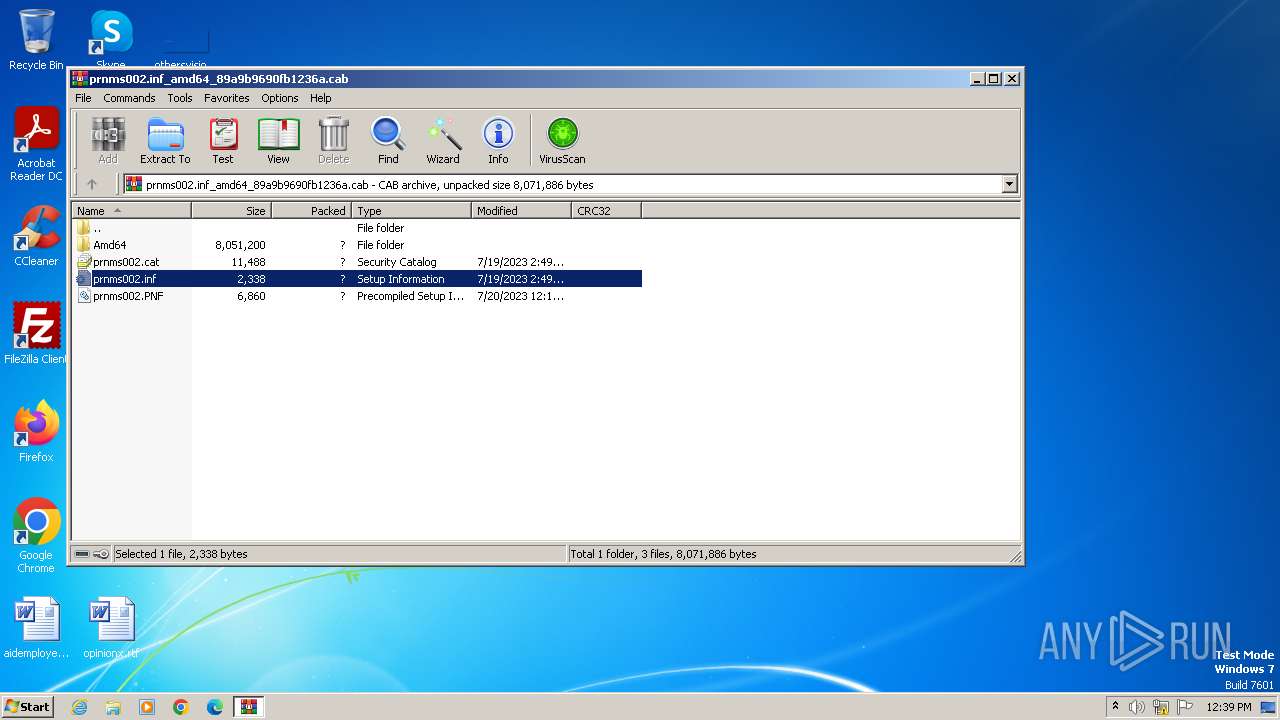
| File name: | prnms002.inf_amd64_89a9b9690fb1236a.cab |
| Full analysis: | https://app.any.run/tasks/0118cd8c-ef8d-42eb-a0a8-d7aff5d21325 |
| Verdict: | Malicious activity |
| Analysis date: | June 05, 2024, 11:37:27 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/vnd.ms-cab-compressed |
| File info: | Microsoft Cabinet archive data, many, 2367451 bytes, 9 files, at 0x2c +A "Amd64\FXSAPI.DLL" +A "Amd64\FXSDRV.DLL", ID 4321, number 1, 247 datablocks, 0x1 compression |
| MD5: | 6E9728EB32CC750C68464D93BB370EB6 |
| SHA1: | A5CB9C0F4A841A90AC4B3471A248E7723698942C |
| SHA256: | D935AC492EB3E90E79F233C3E5950C42B130C8310B3ECEF2999BBD5779609B24 |
| SSDEEP: | 98304:FMaTC8I7unY/OJo6/whohqWQD6Epd2FuiMgVYZI33ZiZwta/kr6KBS0lYZ53eI5M:Ypu9b |
MALICIOUS
No malicious indicators.SUSPICIOUS
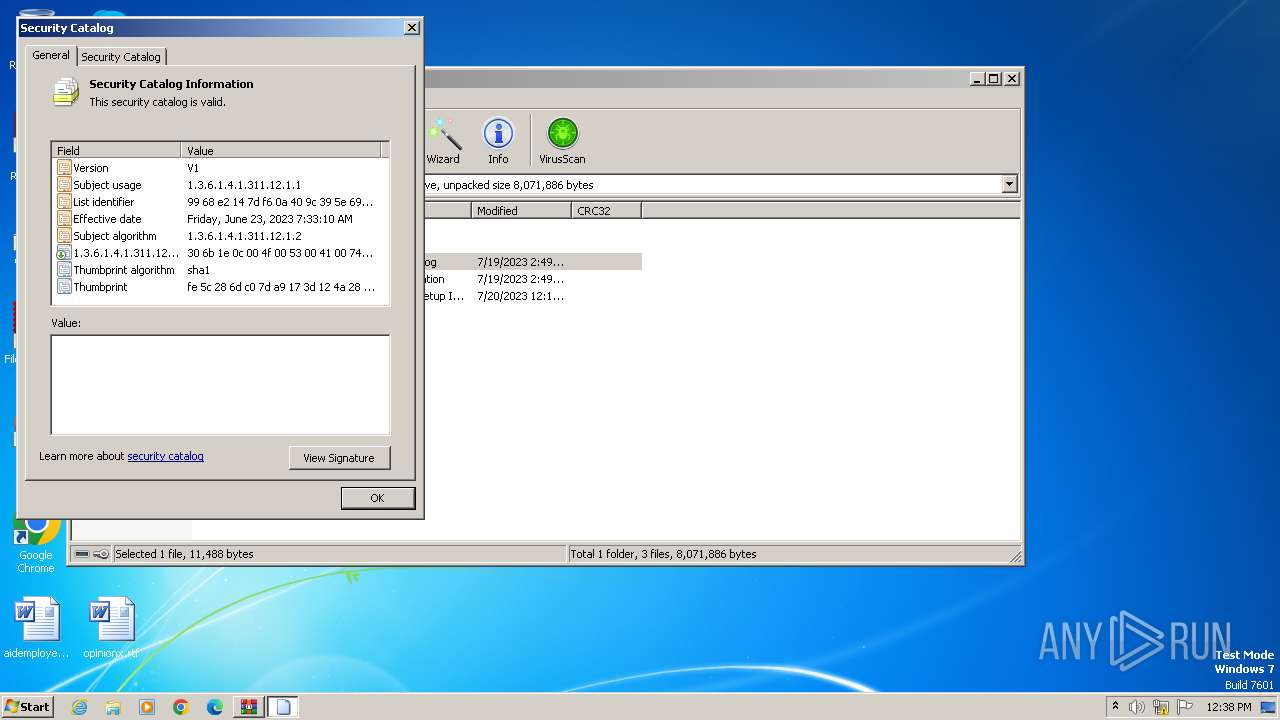
Reads settings of System Certificates
- rundll32.exe (PID: 4048)
Uses RUNDLL32.EXE to load library
- WinRAR.exe (PID: 3968)
Start notepad (likely ransomware note)
- WinRAR.exe (PID: 3968)
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 3968)
INFO
Reads the software policy settings
- rundll32.exe (PID: 4048)
Reads security settings of Internet Explorer
- rundll32.exe (PID: 4048)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .cab | | | Microsoft Cabinet Archive (100) |
|---|
Total processes
34
Monitored processes
3
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
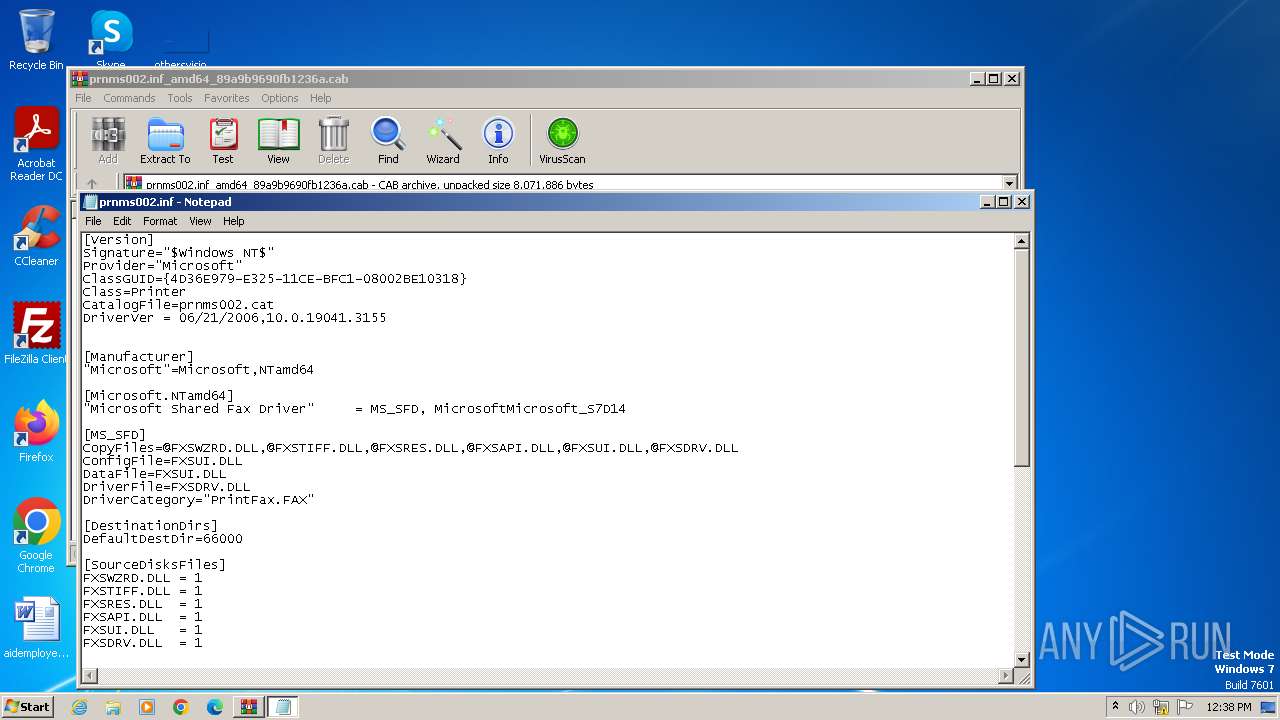
| 1200 | "C:\Windows\system32\NOTEPAD.EXE" C:\Users\admin\AppData\Local\Temp\Rar$DIa3968.33814\prnms002.inf | C:\Windows\System32\notepad.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
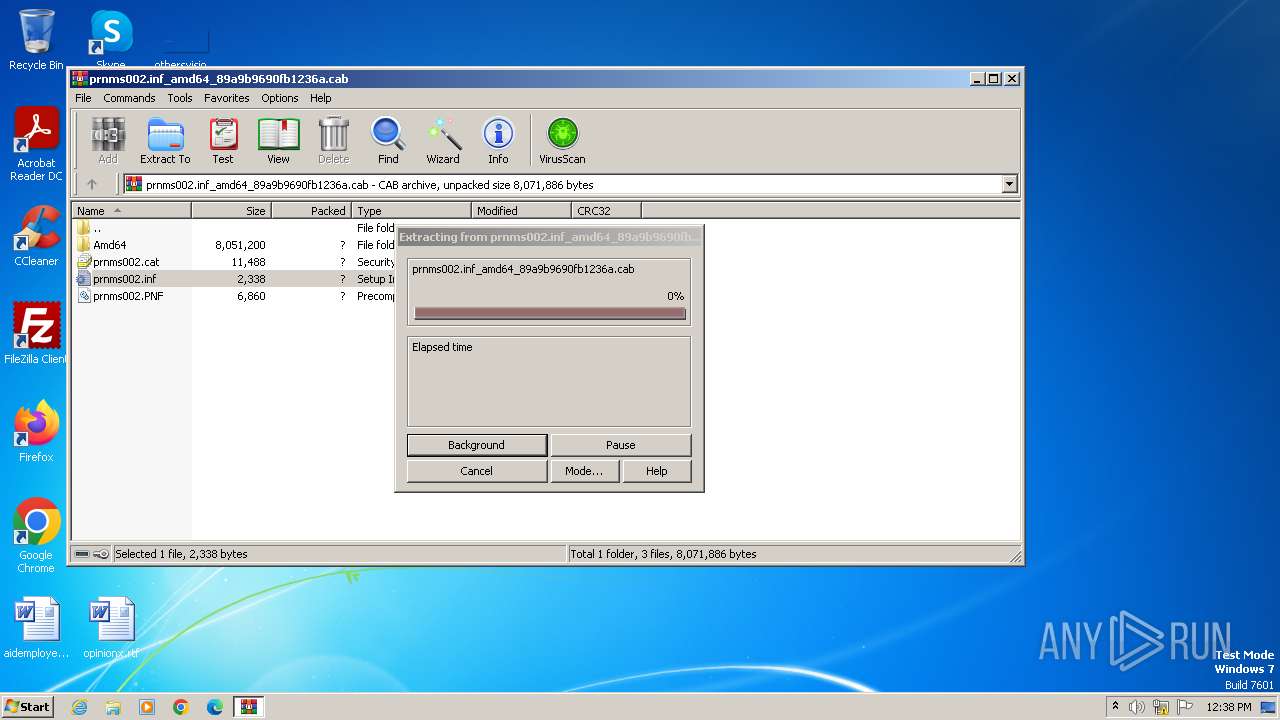
| 3968 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\AppData\Local\Temp\prnms002.inf_amd64_89a9b9690fb1236a.cab | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
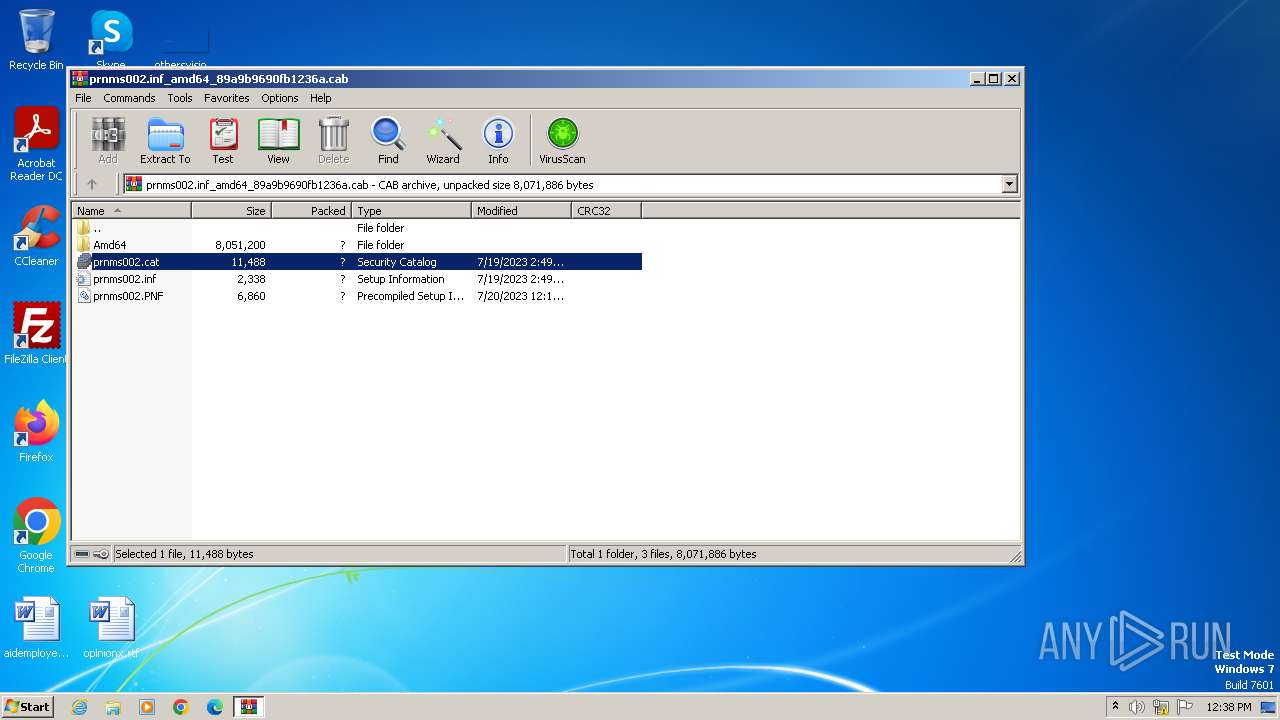
| 4048 | "C:\Windows\system32\rundll32.exe" cryptext.dll,CryptExtOpenCAT C:\Users\admin\AppData\Local\Temp\Rar$DIa3968.32712\prnms002.cat | C:\Windows\System32\rundll32.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
6 760
Read events
6 705
Write events
43
Delete events
12
Modification events
| (PID) Process: | (3968) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3968) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3968) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\182\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3968) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\phacker.zip | |||
| (PID) Process: | (3968) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\Win7-KB3191566-x86.zip | |||
| (PID) Process: | (3968) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\curl-8.5.0_1-win32-mingw.zip | |||
| (PID) Process: | (3968) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\prnms002.inf_amd64_89a9b9690fb1236a.cab | |||
| (PID) Process: | (3968) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3968) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3968) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
Executable files
0
Suspicious files
2
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3968 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DIa3968.32712\prnms002.cat | binary | |
MD5:BF559A7B290125FB406BA3DB57FDB629 | SHA256:03483AE0DD53A499DFB81F355848A610ECBAB32D71FE34051A92B67ABC5095DA | |||
| 3968 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DIa3968.33814\prnms002.inf | binary | |
MD5:E23124B61A9B59BD4ED83949F0AD8925 | SHA256:E8B0AFCB774AE69EB90D0F67F4E5FF9F8856E2A261BA78C8B2CD368169D5F0CC | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
2
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |