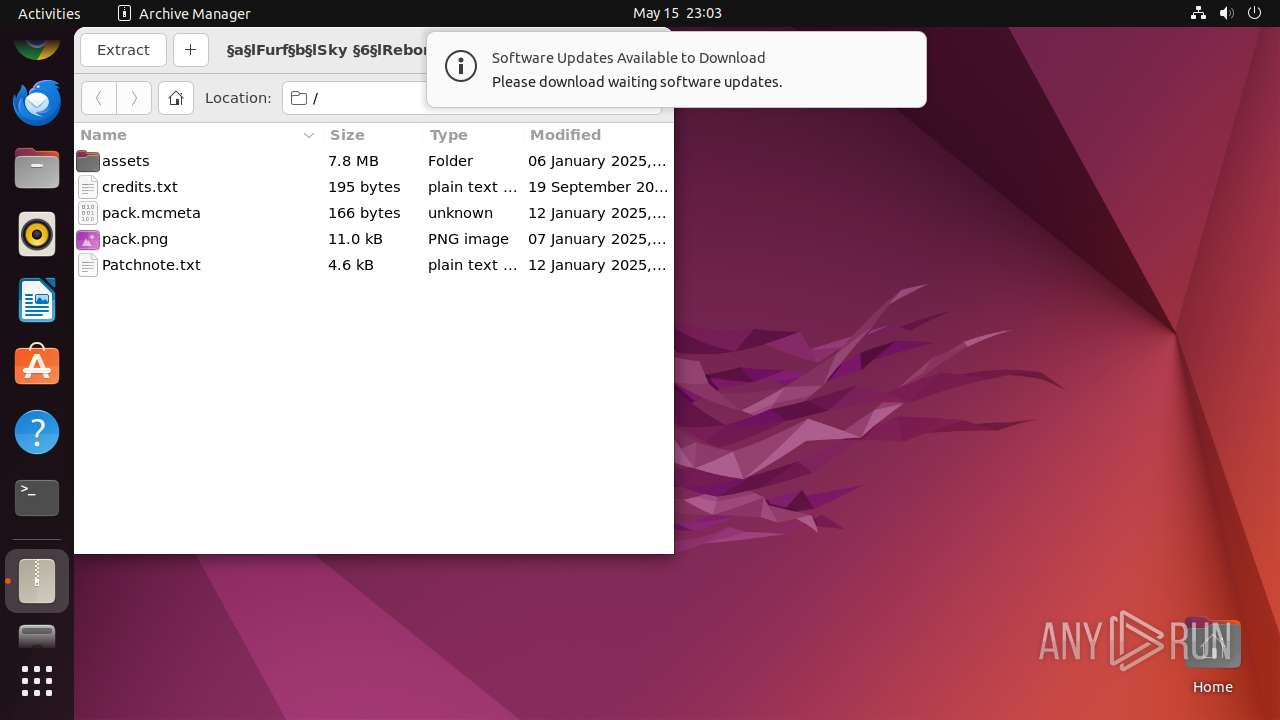
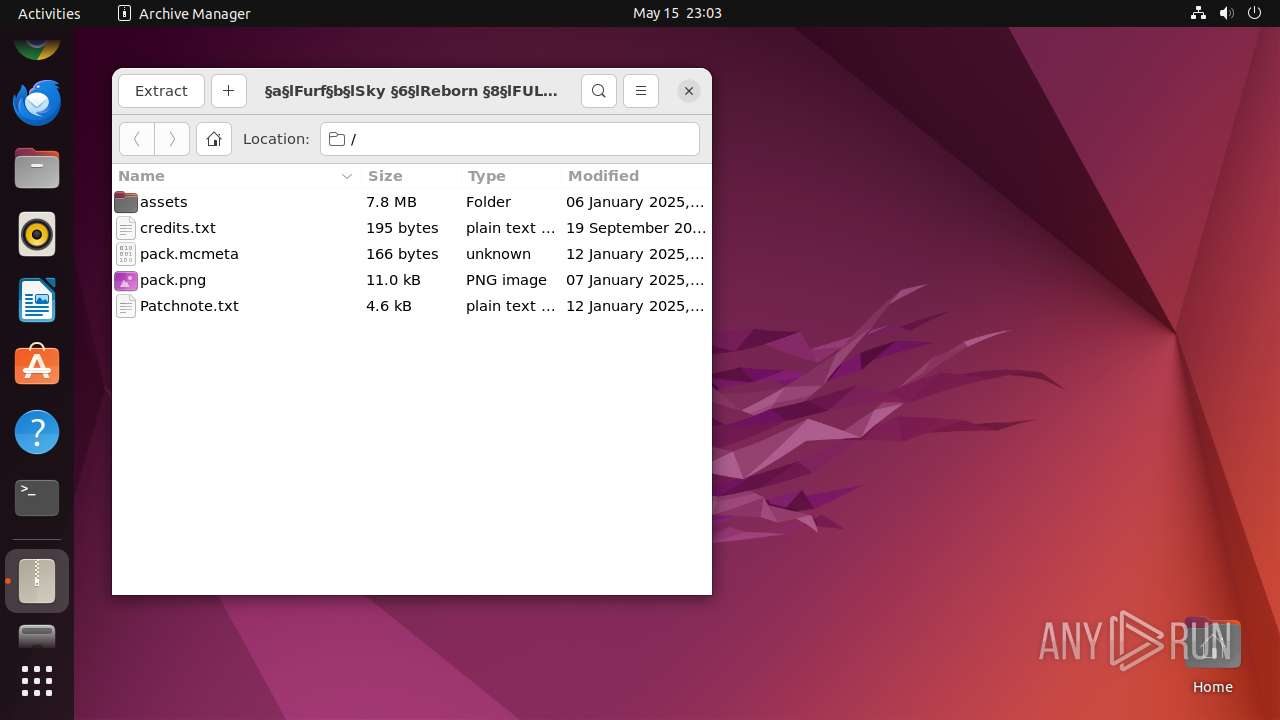
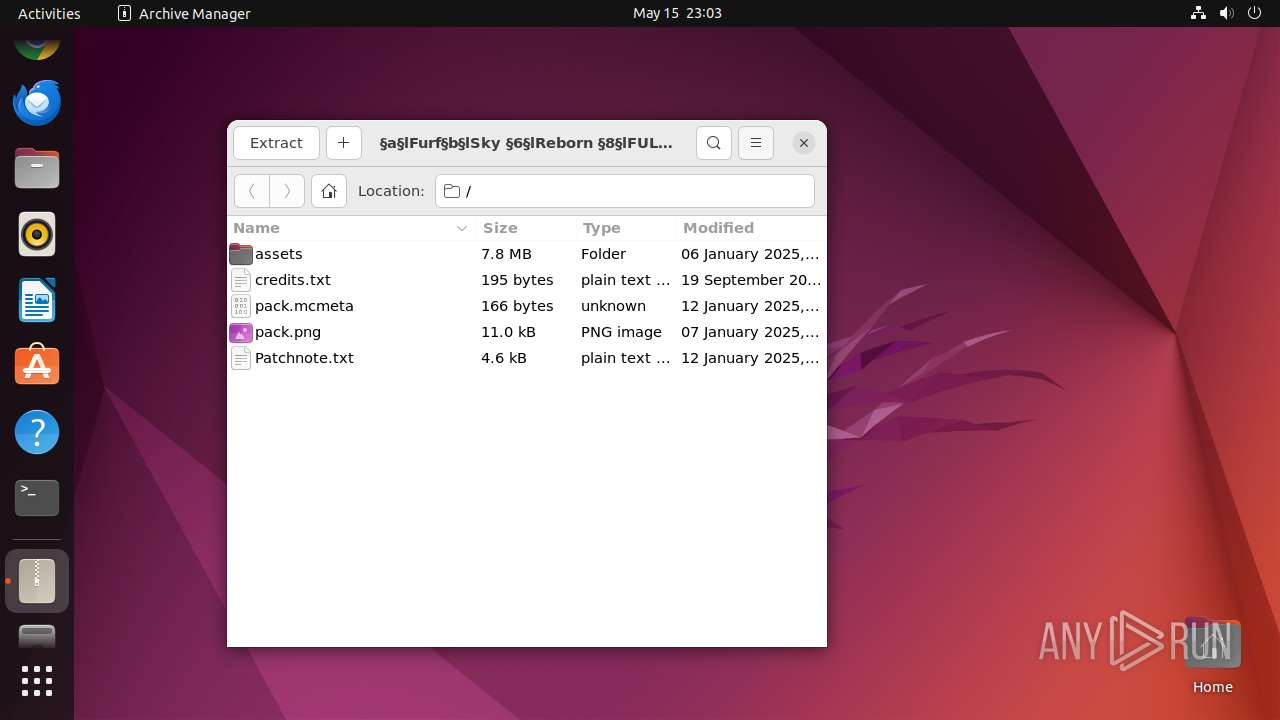
| File name: | §a§lFurf§b§lSky §6§lReborn §8§lFULL.zip |
| Full analysis: | https://app.any.run/tasks/a197d986-3fdb-45bb-a8ea-1d5b1d3df4f1 |
| Verdict: | Malicious activity |
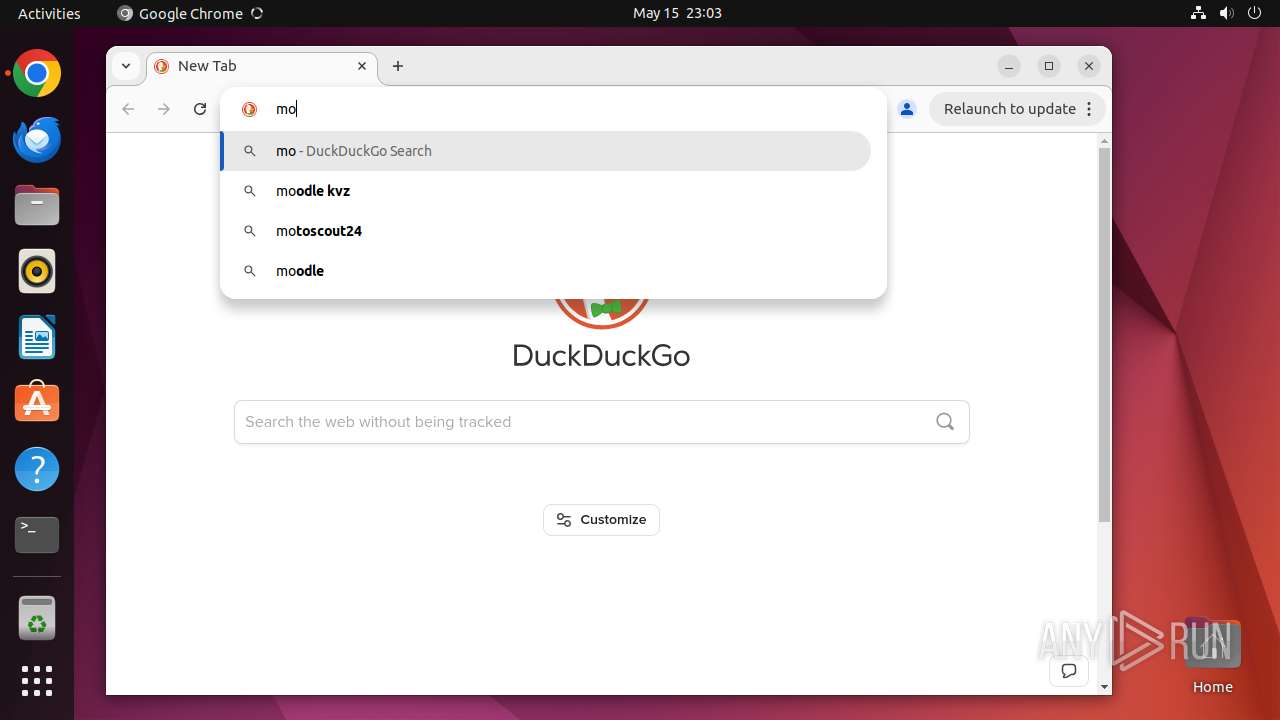
| Analysis date: | May 15, 2025, 22:03:07 |
| OS: | Ubuntu 22.04.2 |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=store |
| MD5: | 693F5A312CB357E523EF82D910F3D5FF |
| SHA1: | 18043C3B7FF329329660CDDC48EEBB98FAE7BE88 |
| SHA256: | D92CD0A84585B6BE7E874F89C29EC704BADE597DFF7C3C70AC4DB14F2530ED1B |
| SSDEEP: | 98304:ixtdrwGLMOz8ZB0o4DtrdBo4zOcry7mCUW8BhRju8bsv7+pjLiynK1SU7c1nm3tI:eNuIMuKI |
MALICIOUS
No malicious indicators.SUSPICIOUS
Executes commands using command-line interpreter
- sudo (PID: 40665)
- chrome (PID: 40682)
Reads profile file
- file-roller (PID: 40666)
Reads passwd file
- file-roller (PID: 40666)
INFO
Checks timezone
- 7z (PID: 40681)
- file-roller (PID: 40666)
- chrome (PID: 40682)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2025:01:06 06:03:54 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | - |
| ZipUncompressedSize: | - |
| ZipFileName: | assets/ |
Total processes
321
Monitored processes
95
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process |
|---|---|---|---|---|
| 40664 | /bin/sh -c "DISPLAY=:0 sudo -iu user file-roller \"/tmp/§a§lFurf§b§lSky §6§lReborn §8§lFULL\.zip\" " | /usr/bin/dash | — | any-guest-agent |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 40665 | sudo -iu user file-roller "/tmp/§a§lFurf§b§lSky §6§lReborn §8§lFULL\.zip" | /usr/bin/sudo | — | dash |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 40666 | file-roller "/tmp/§a§lFurf§b§lSky §6§lReborn §8§lFULL\.zip" | /usr/bin/file-roller | — | sudo |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 40667 | /usr/bin/locale-check C.UTF-8 | /usr/bin/locale-check | — | file-roller |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 40681 | /usr/lib/p7zip/7z l -slt -bd -y -- "/tmp/§a§lFurf§b§lSky §6§lReborn §8§lFULL\.zip" | /usr/lib/p7zip/7z | — | file-roller |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 40682 | /usr/bin/google-chrome-stable | /opt/google/chrome/chrome | — | gnome-shell |
User: user Integrity Level: UNKNOWN | ||||
| 40684 | readlink -f /usr/bin/google-chrome-stable | /usr/bin/readlink | — | chrome |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 40685 | dirname /opt/google/chrome/google-chrome | /usr/bin/dirname | — | chrome |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 40686 | mkdir -p /home/user/.local/share/applications | /usr/bin/mkdir | — | chrome |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 40687 | cat | /usr/bin/cat | — | chrome |
User: user Integrity Level: UNKNOWN | ||||
Executable files
0
Suspicious files
198
Text files
11
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
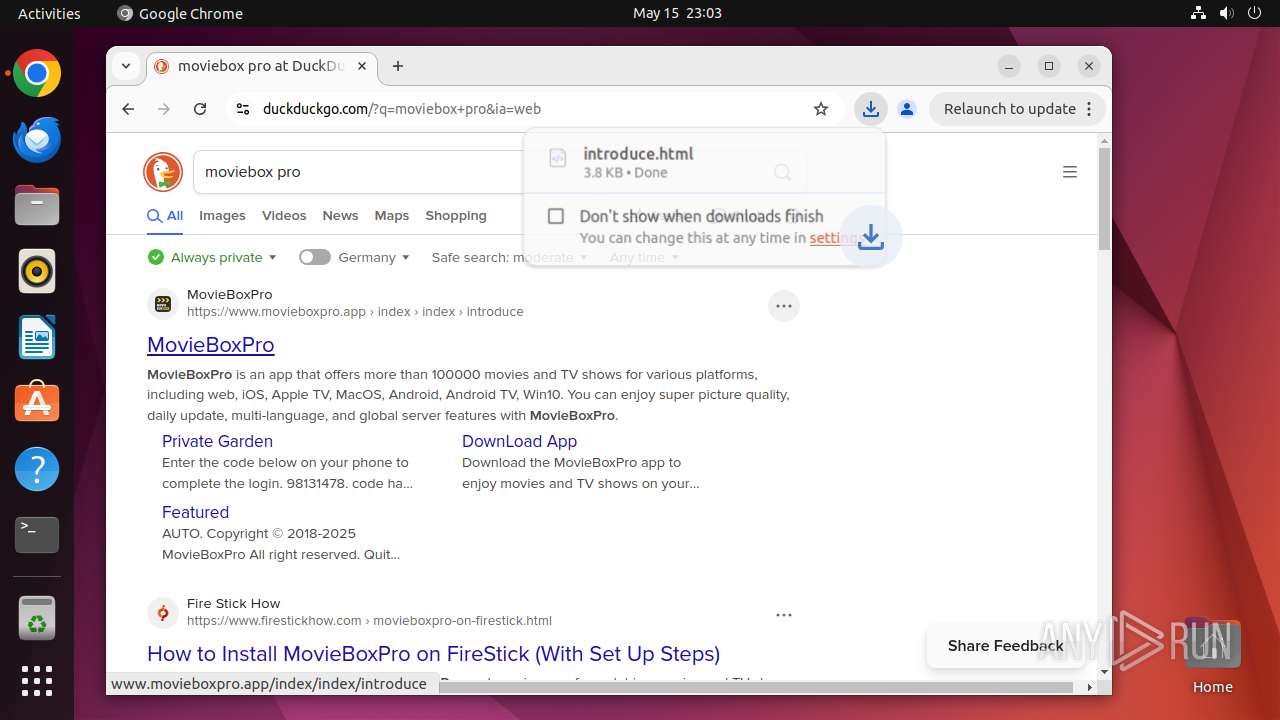
| 40682 | chrome | /home/user/.config/google-chrome/ShaderCache/data_3 | binary | |
MD5:— | SHA256:— | |||
| 40682 | chrome | /home/user/.config/google-chrome/ShaderCache/data_2 | binary | |
MD5:— | SHA256:— | |||
| 40682 | chrome | /home/user/.config/google-chrome/ShaderCache/data_0 | binary | |
MD5:— | SHA256:— | |||
| 40682 | chrome | /home/user/.config/google-chrome/Default/GPUCache/data_3 | binary | |
MD5:— | SHA256:— | |||
| 40682 | chrome | /home/user/.config/google-chrome/Default/GPUCache/data_2 | binary | |
MD5:— | SHA256:— | |||
| 40682 | chrome | /home/user/.config/google-chrome/Default/GPUCache/data_0 | binary | |
MD5:— | SHA256:— | |||
| 40725 | chrome | /home/user/.cache/mesa_shader_cache/index | binary | |
MD5:— | SHA256:— | |||
| 40824 | chrome | /home/user/.cache/mesa_shader_cache/index | binary | |
MD5:— | SHA256:— | |||
| 40848 | chrome | /home/user/.cache/mesa_shader_cache/index | binary | |
MD5:— | SHA256:— | |||
| 40682 | chrome | /home/user/.config/google-chrome/Default/History | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
30
DNS requests
39
Threats
24
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 204 | 185.125.190.97:80 | http://connectivity-check.ubuntu.com/ | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 185.125.190.97:80 | connectivity-check.ubuntu.com | Canonical Group Limited | GB | whitelisted |
484 | avahi-daemon | 224.0.0.251:5353 | — | — | — | unknown |
— | — | 169.150.255.184:443 | odrs.gnome.org | — | GB | whitelisted |
— | — | 185.125.188.59:443 | api.snapcraft.io | Canonical Group Limited | GB | whitelisted |
— | — | 185.125.188.57:443 | api.snapcraft.io | Canonical Group Limited | GB | whitelisted |
40731 | chrome | 142.250.185.234:443 | safebrowsingohttpgateway.googleapis.com | GOOGLE | US | whitelisted |
40731 | chrome | 142.250.185.99:443 | clientservices.googleapis.com | GOOGLE | US | whitelisted |
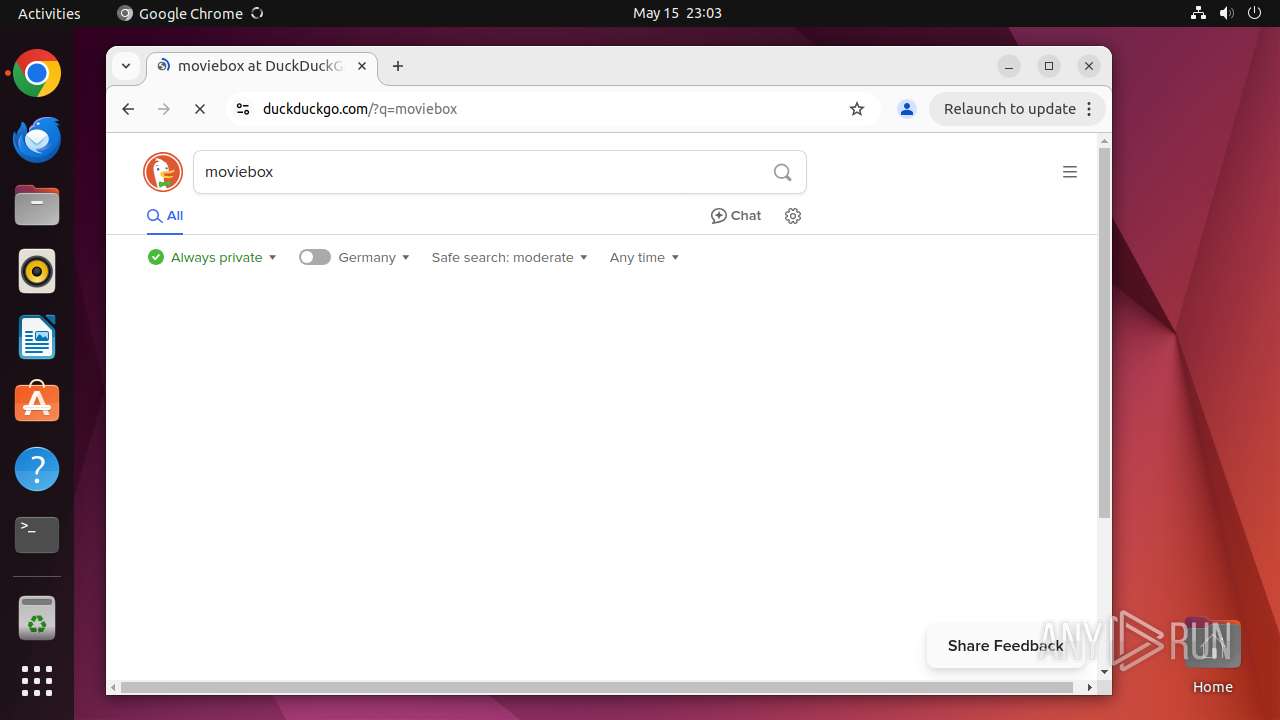
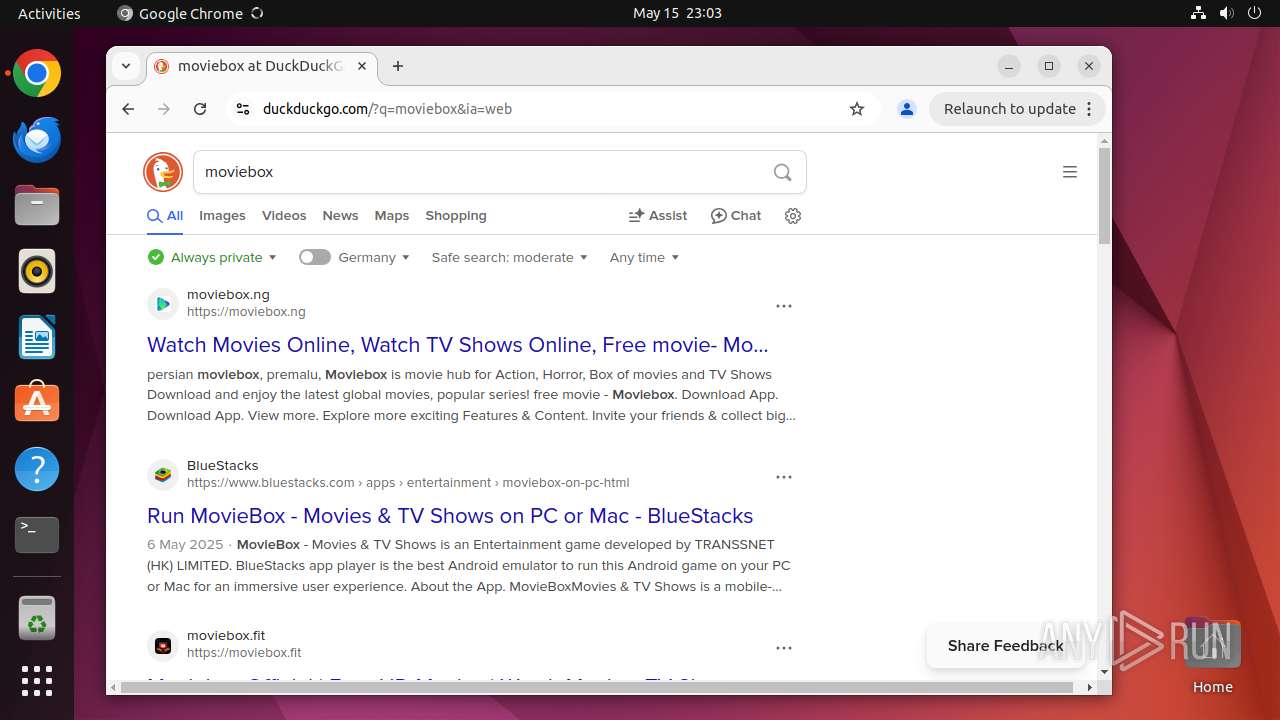
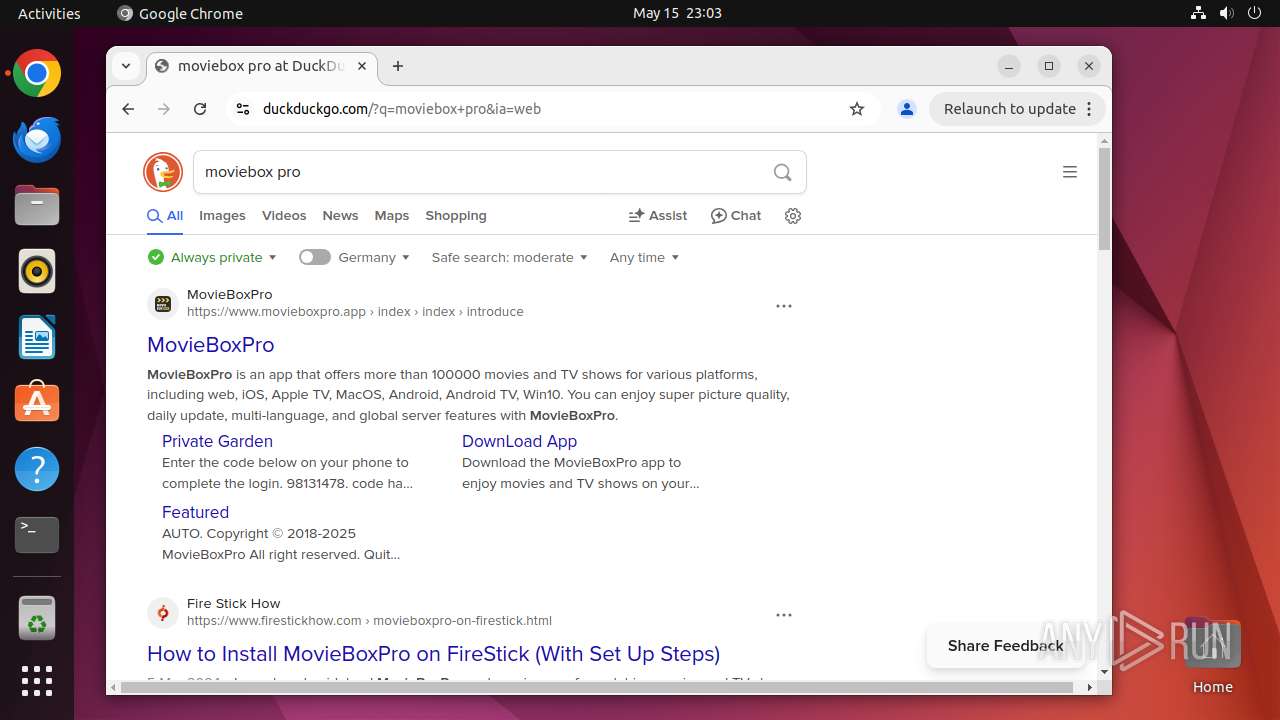
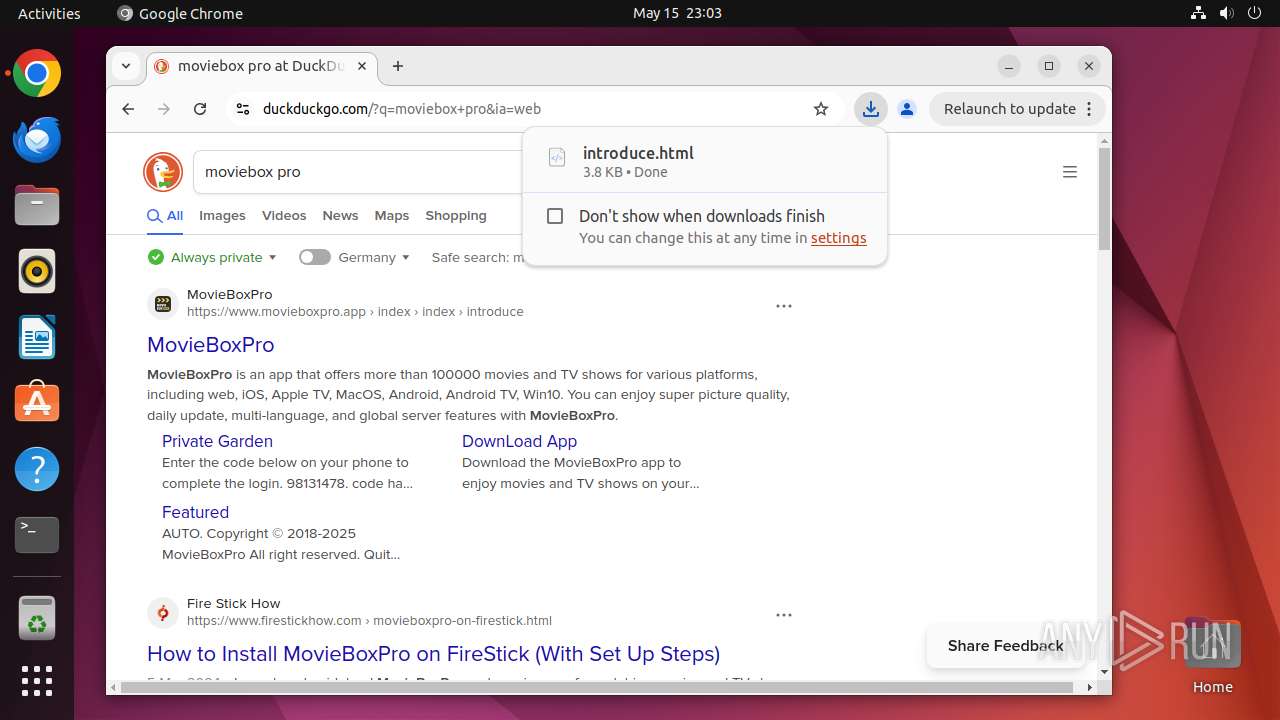
40731 | chrome | 40.114.177.156:443 | duckduckgo.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
40731 | chrome | 173.194.76.84:443 | accounts.google.com | GOOGLE | US | whitelisted |
40731 | chrome | 142.250.186.138:443 | safebrowsing.googleapis.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
connectivity-check.ubuntu.com |
| whitelisted |
odrs.gnome.org |
| whitelisted |
google.com |
| whitelisted |
api.snapcraft.io |
| whitelisted |
6.100.168.192.in-addr.arpa |
| unknown |
safebrowsingohttpgateway.googleapis.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
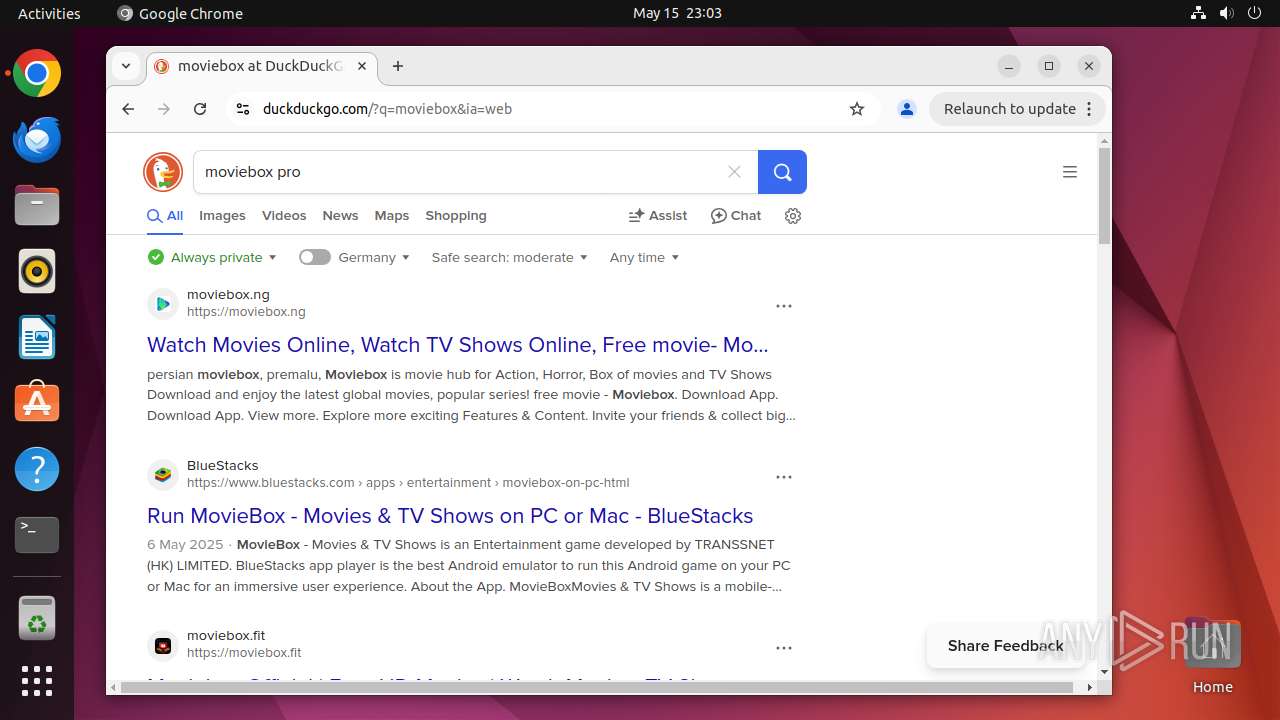
duckduckgo.com |
| whitelisted |
accounts.google.com |
| whitelisted |
safebrowsing.googleapis.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
40731 | chrome | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
40731 | chrome | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
40731 | chrome | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
40731 | chrome | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
40731 | chrome | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
40731 | chrome | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
40731 | chrome | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
40731 | chrome | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
40731 | chrome | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
40731 | chrome | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |