| File name: | AnyDesk.exe |
| Full analysis: | https://app.any.run/tasks/ef3c8226-fb83-4590-99a1-0a9d9e52a545 |
| Verdict: | Malicious activity |
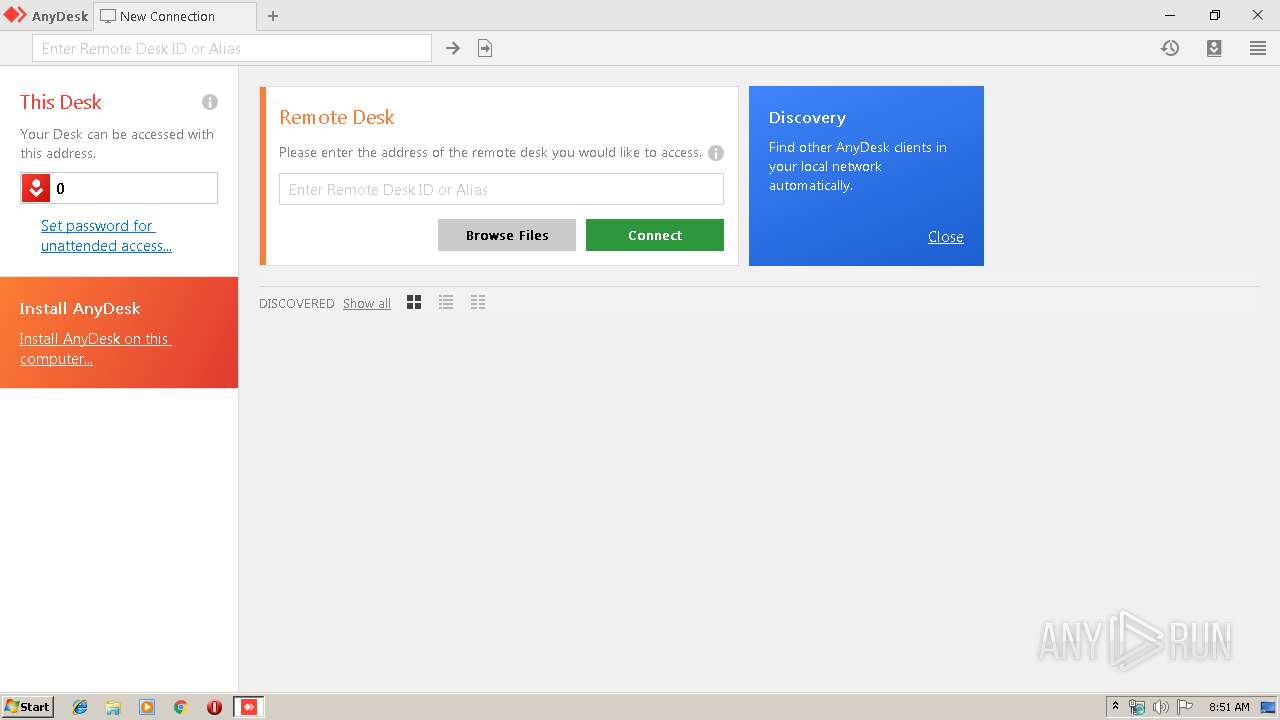
| Analysis date: | July 17, 2019, 07:51:15 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 731ED6D606258B84AC0F943935F0131D |
| SHA1: | 0D952BAD285F1ED906BC49CD1A69B5C1058D6553 |
| SHA256: | D928708B944906E0A97F6A375EB9D85BC00DE5CC217D59A2B60556A3A985DF1E |
| SSDEEP: | 49152:iEPEq4hxCYt7OFfhTcQ4OSbrCRWTZLTPfKFs9daUrdFuN3sbD0N7V+1f9wb9HD47:iEEq4hxZt7KpTcQbSbDTK29pOBptVY1J |
MALICIOUS
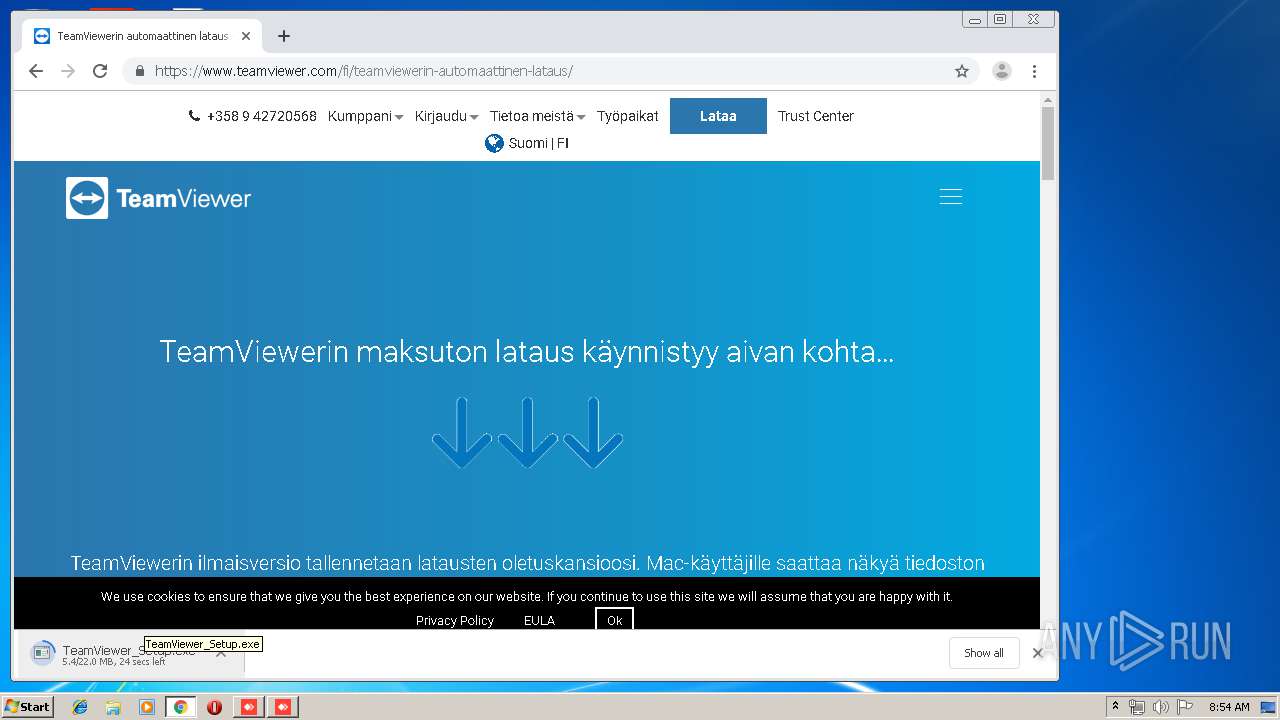
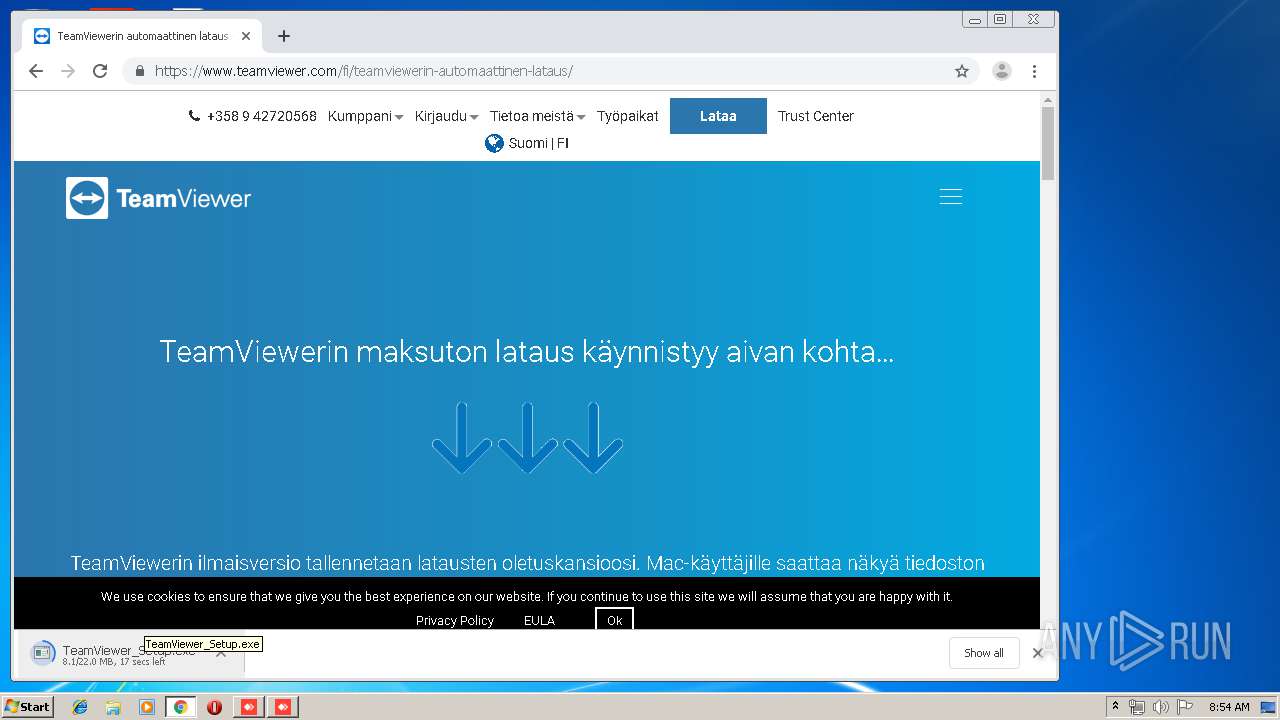
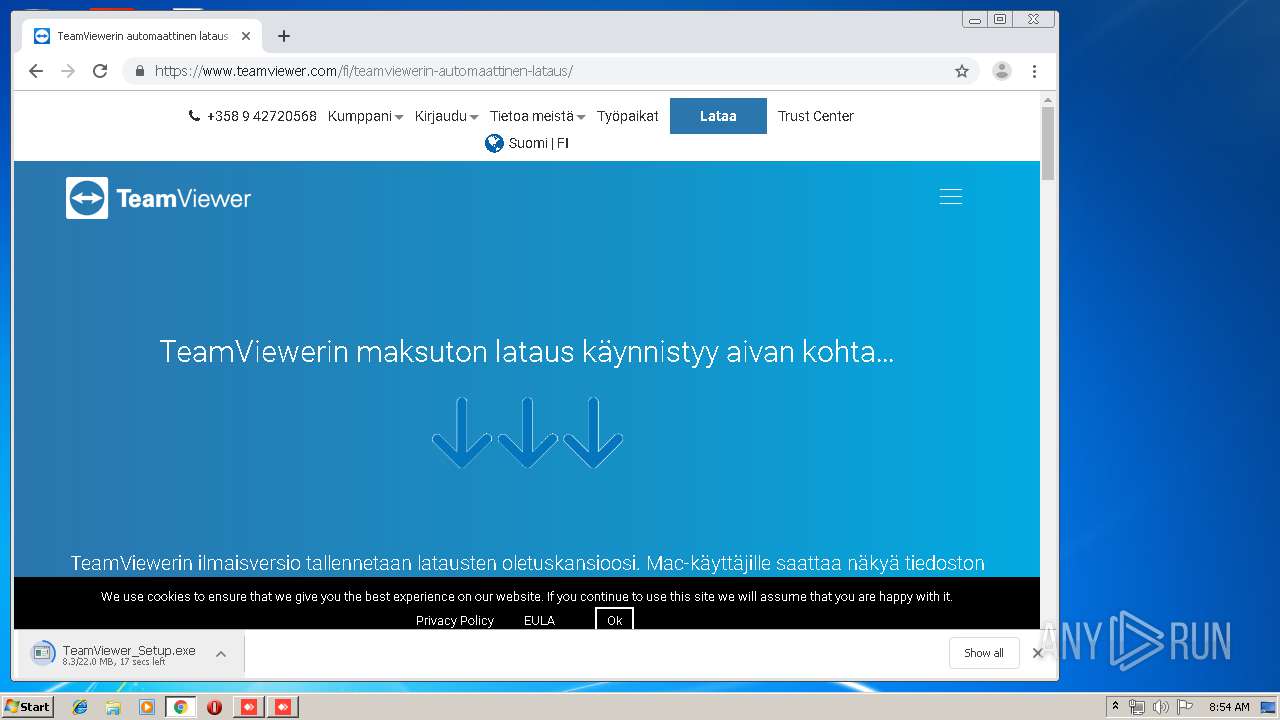
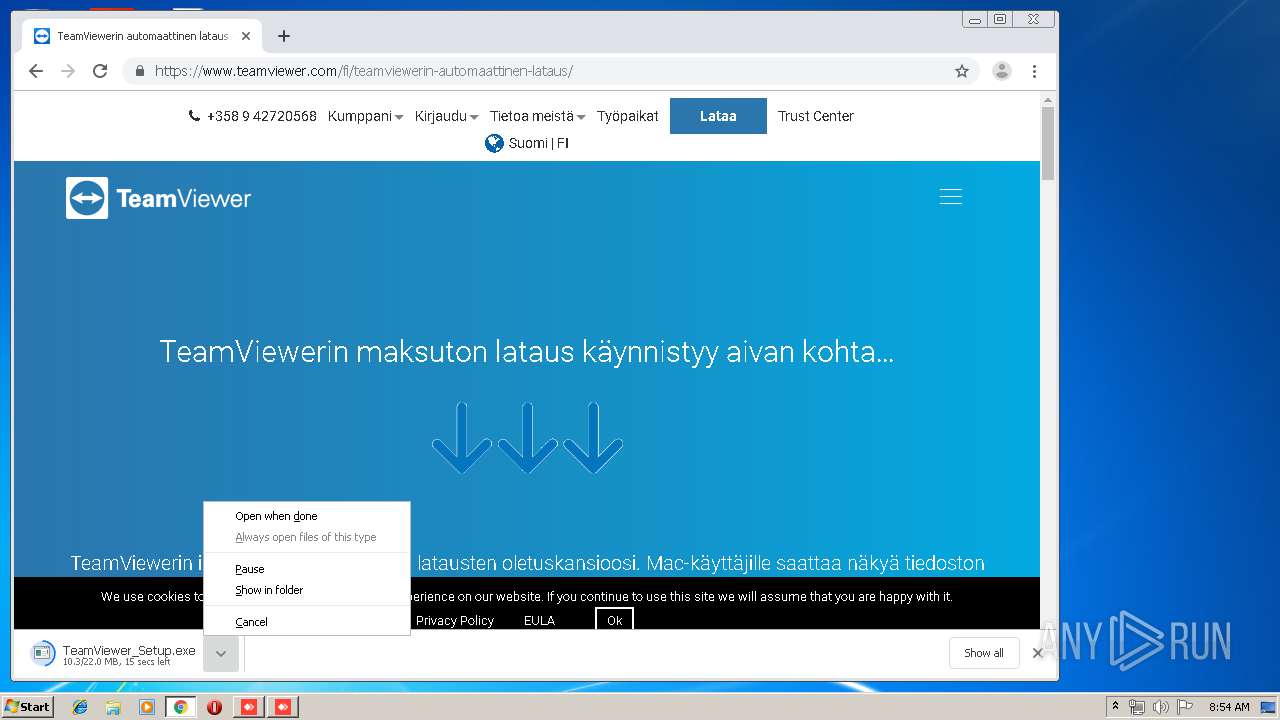
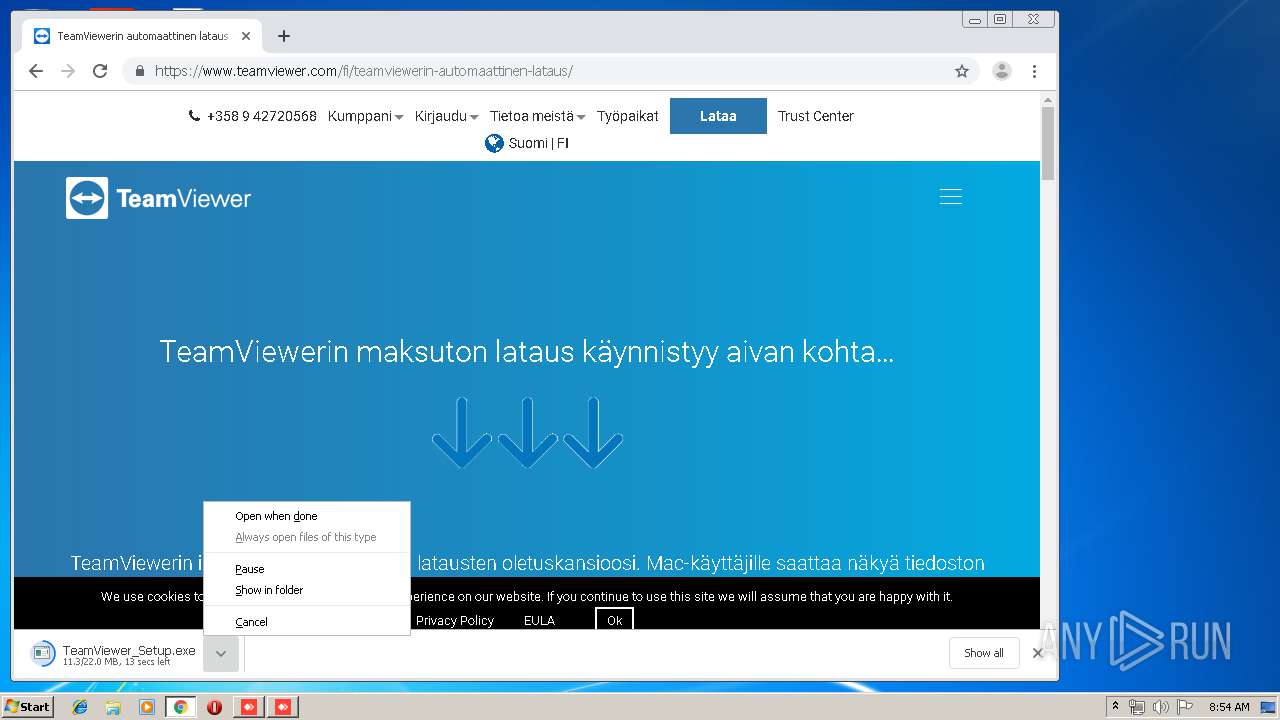
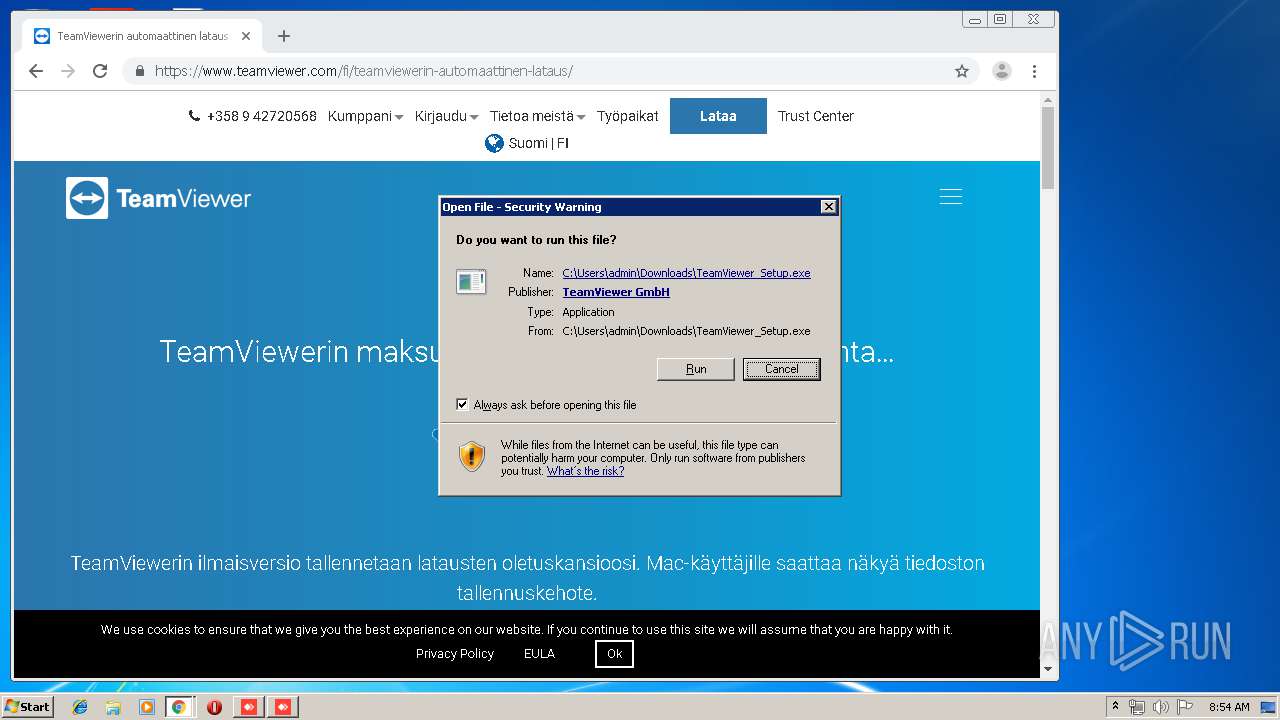
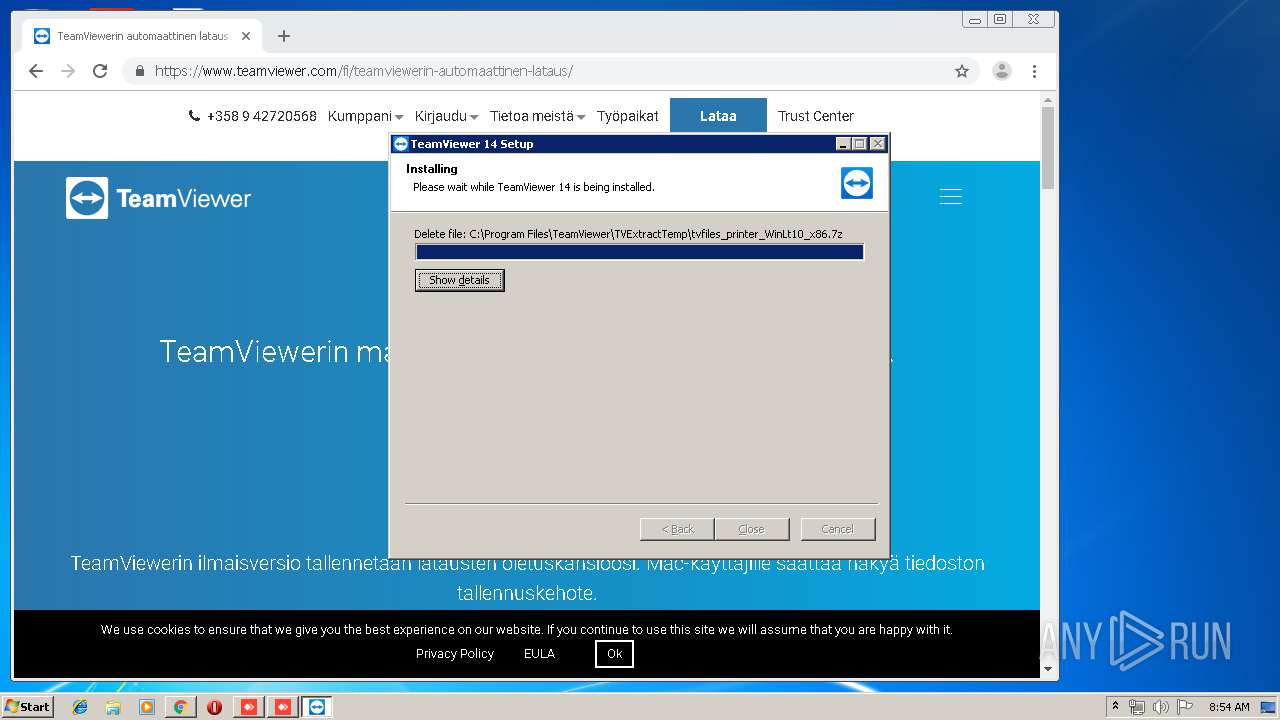
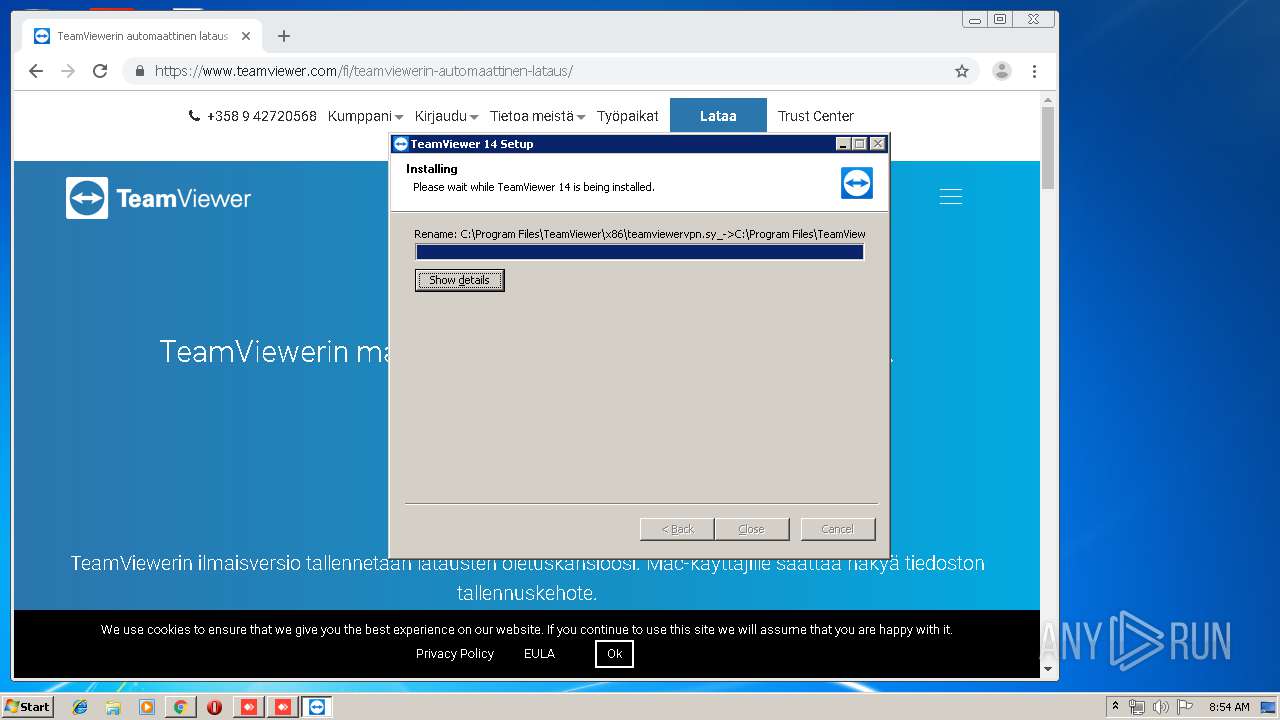
Application was dropped or rewritten from another process
- TeamViewer_Setup.exe (PID: 3176)
- nsCA3C.tmp (PID: 3964)
- ns498.tmp (PID: 4056)
- nsF256.tmp (PID: 3140)
- nsFD54.tmp (PID: 2200)
- TeamViewer_.exe (PID: 3072)
- TeamViewer_.exe (PID: 2360)
- TeamViewer_Service.exe (PID: 2524)
- TeamViewer_Service.exe (PID: 2324)
- tv_w32.exe (PID: 3504)
- ns17B4.tmp (PID: 560)
- TeamViewer_Desktop.exe (PID: 3224)
Loads dropped or rewritten executable
- TeamViewer_.exe (PID: 2360)
- TeamViewer_.exe (PID: 3072)
- TeamViewer_Setup.exe (PID: 3176)
- TeamViewer.exe (PID: 2236)
- regsvr32.exe (PID: 2592)
- tv_w32.exe (PID: 3504)
- TeamViewer_Desktop.exe (PID: 3224)
Loads the Task Scheduler COM API
- schtasks.exe (PID: 2800)
- schtasks.exe (PID: 3504)
Registers / Runs the DLL via REGSVR32.EXE
- ns498.tmp (PID: 4056)
Uses Task Scheduler to run other applications
- ns17B4.tmp (PID: 560)
Changes settings of System certificates
- TeamViewer_Service.exe (PID: 2524)
Uses Task Scheduler to autorun other applications
- nsCA3C.tmp (PID: 3964)
SUSPICIOUS
Creates files in the user directory
- AnyDesk.exe (PID: 3648)
- AnyDesk.exe (PID: 3840)
- TeamViewer_Service.exe (PID: 2524)
- TeamViewer_.exe (PID: 3072)
Application launched itself
- AnyDesk.exe (PID: 3840)
- AnyDesk.exe (PID: 3648)
- TeamViewer_.exe (PID: 2360)
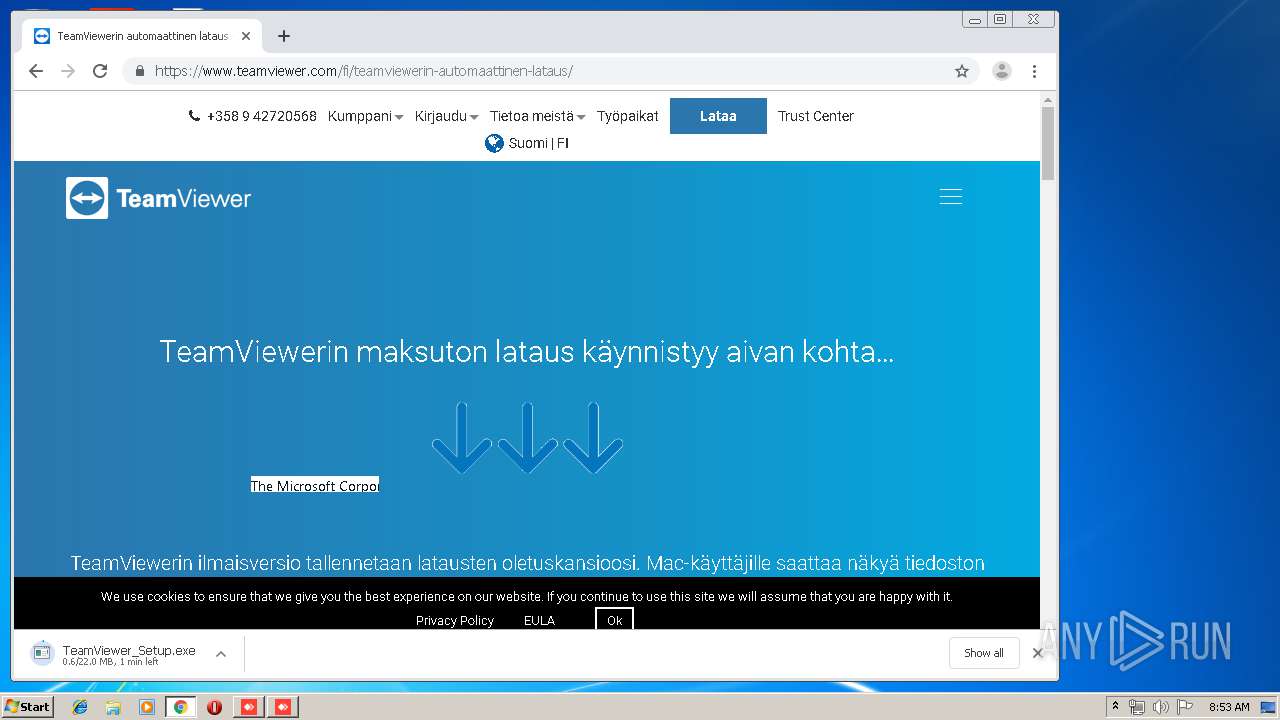
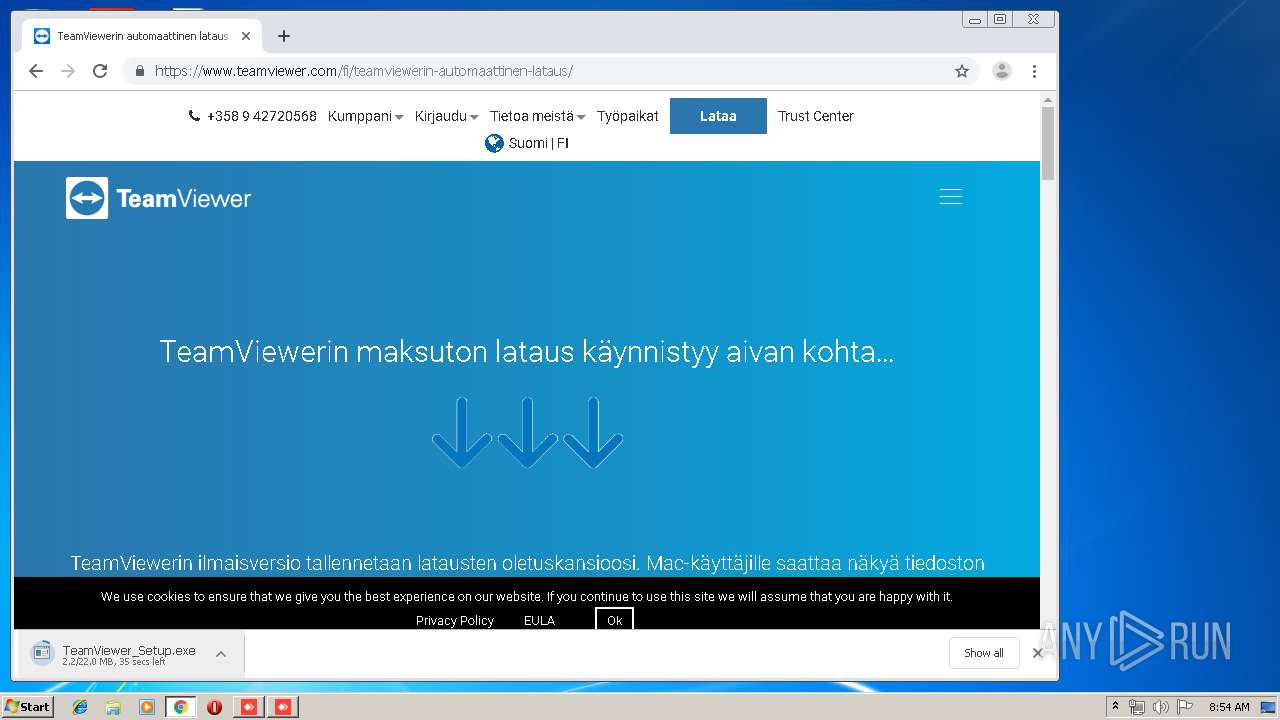
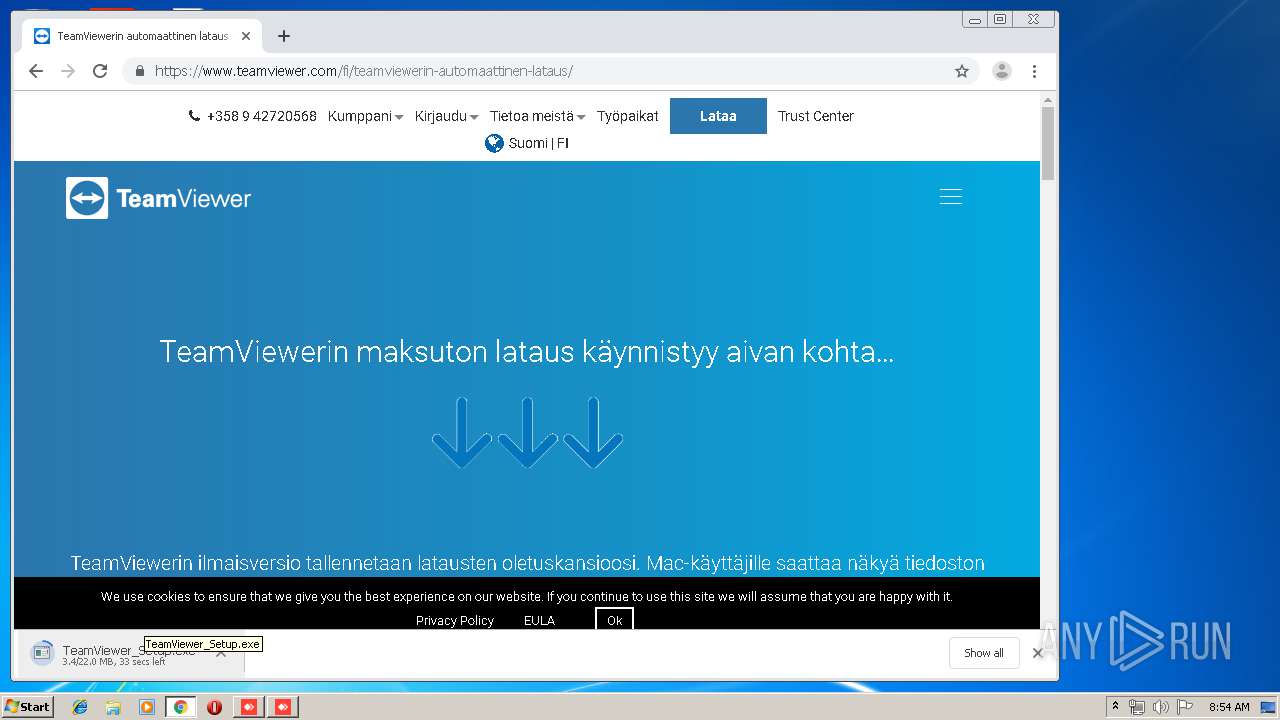
Executable content was dropped or overwritten
- chrome.exe (PID: 2416)
- chrome.exe (PID: 3916)
- TeamViewer_.exe (PID: 2360)
- TeamViewer_Setup.exe (PID: 3176)
- TeamViewer_.exe (PID: 3072)
Modifies files in Chrome extension folder
- chrome.exe (PID: 2416)
Adds / modifies Windows certificates
- TeamViewer_Service.exe (PID: 2524)
Creates files in the program directory
- TeamViewer_.exe (PID: 3072)
- TeamViewer_Service.exe (PID: 2324)
Creates COM task schedule object
- regsvr32.exe (PID: 2592)
Creates a software uninstall entry
- TeamViewer_.exe (PID: 3072)
Starts application with an unusual extension
- TeamViewer_.exe (PID: 3072)
Modifies the open verb of a shell class
- TeamViewer_.exe (PID: 3072)
Starts Internet Explorer
- TeamViewer.exe (PID: 2236)
Executed as Windows Service
- TeamViewer_Service.exe (PID: 2324)
Creates files in the Windows directory
- TeamViewer_.exe (PID: 3072)
INFO
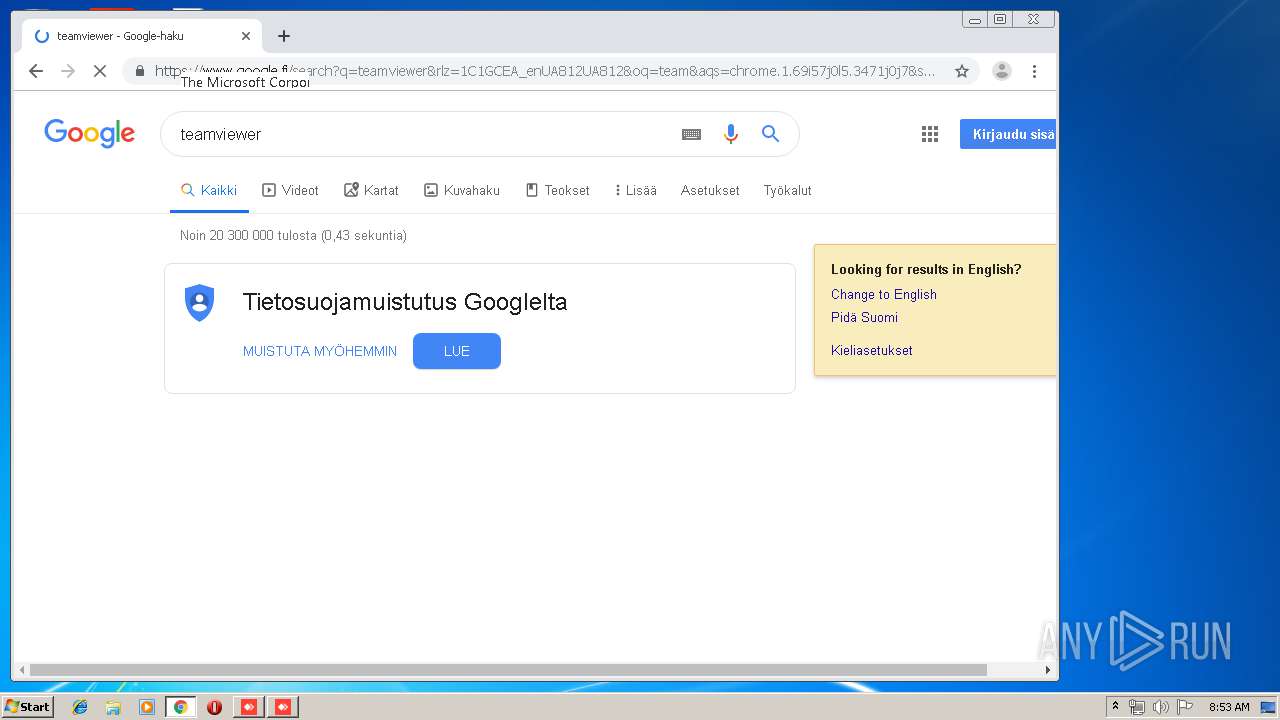
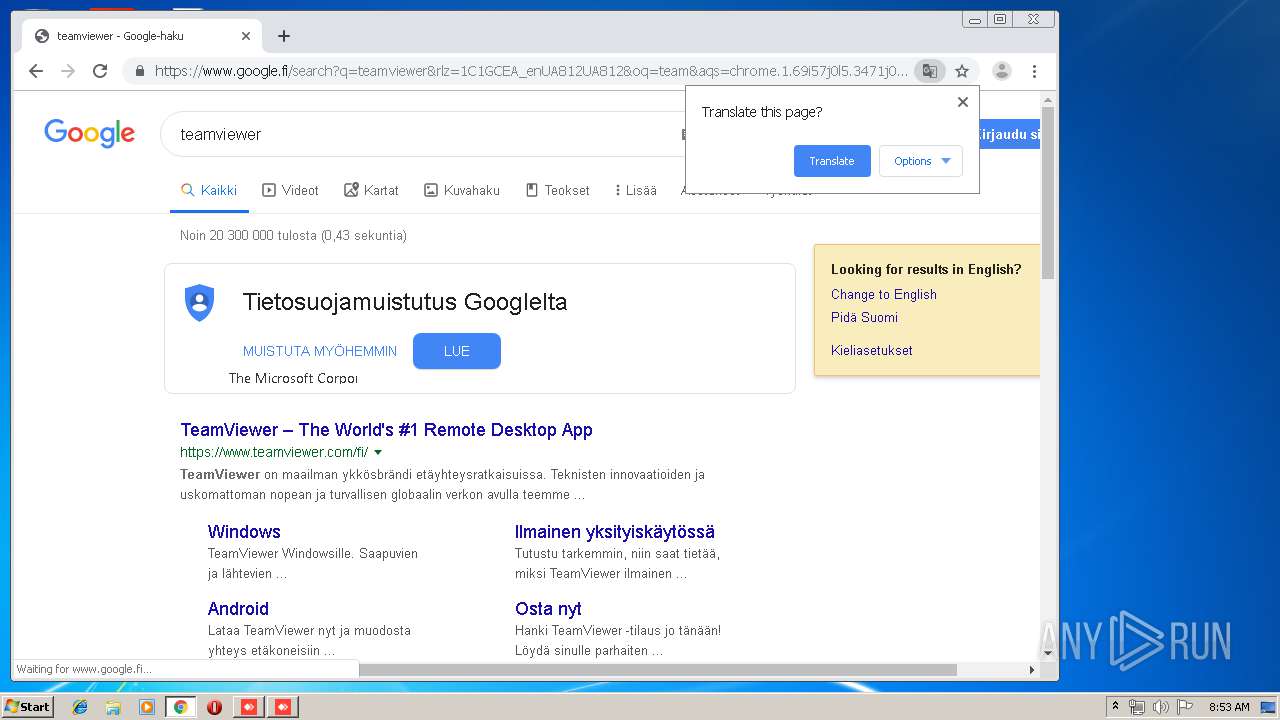
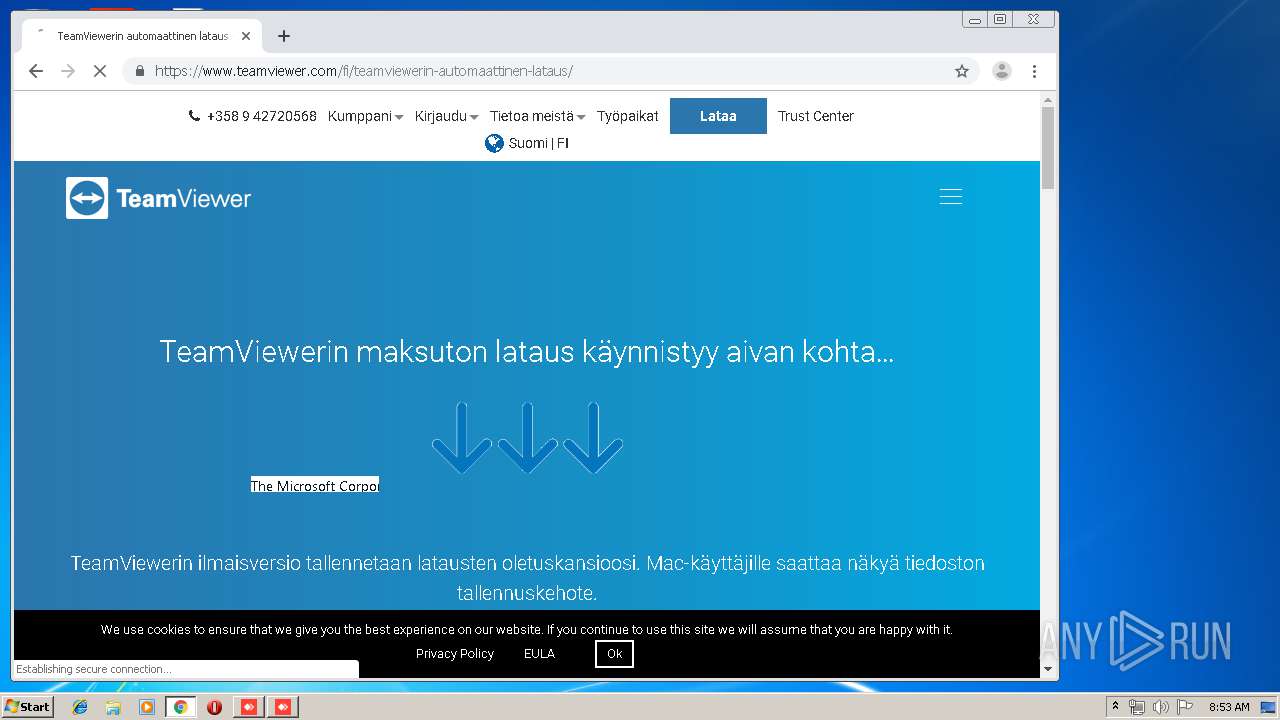
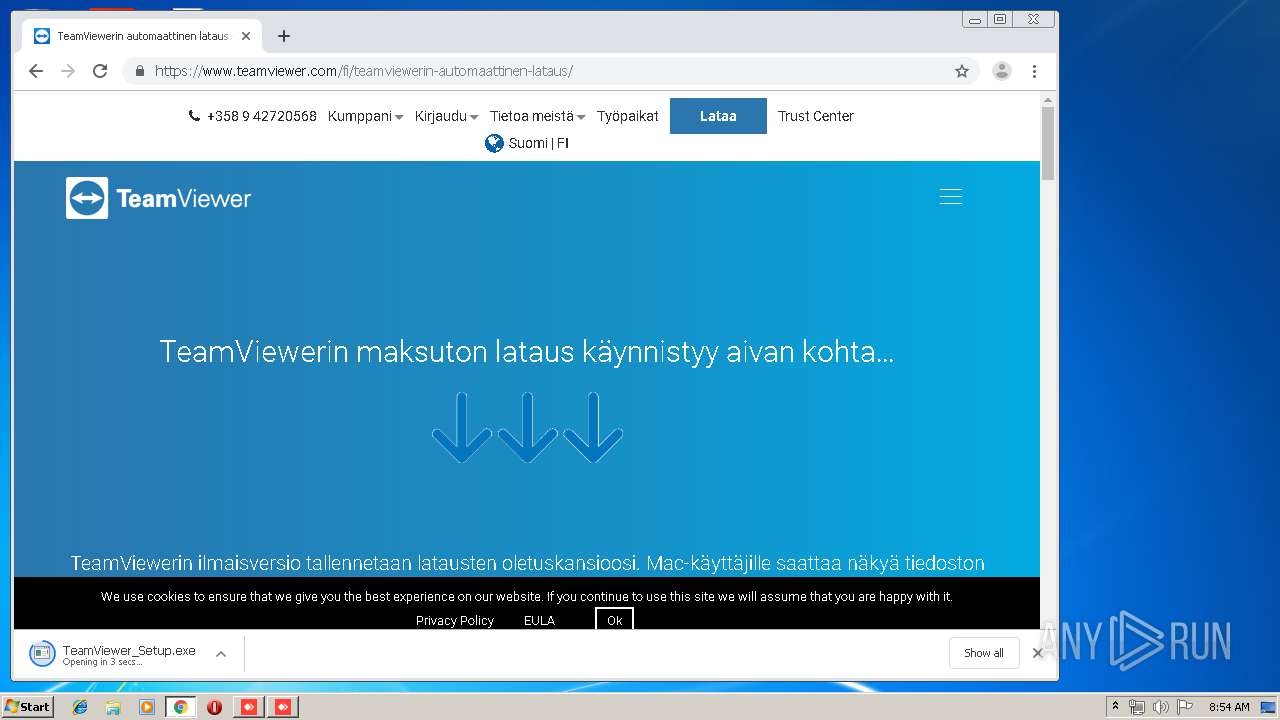
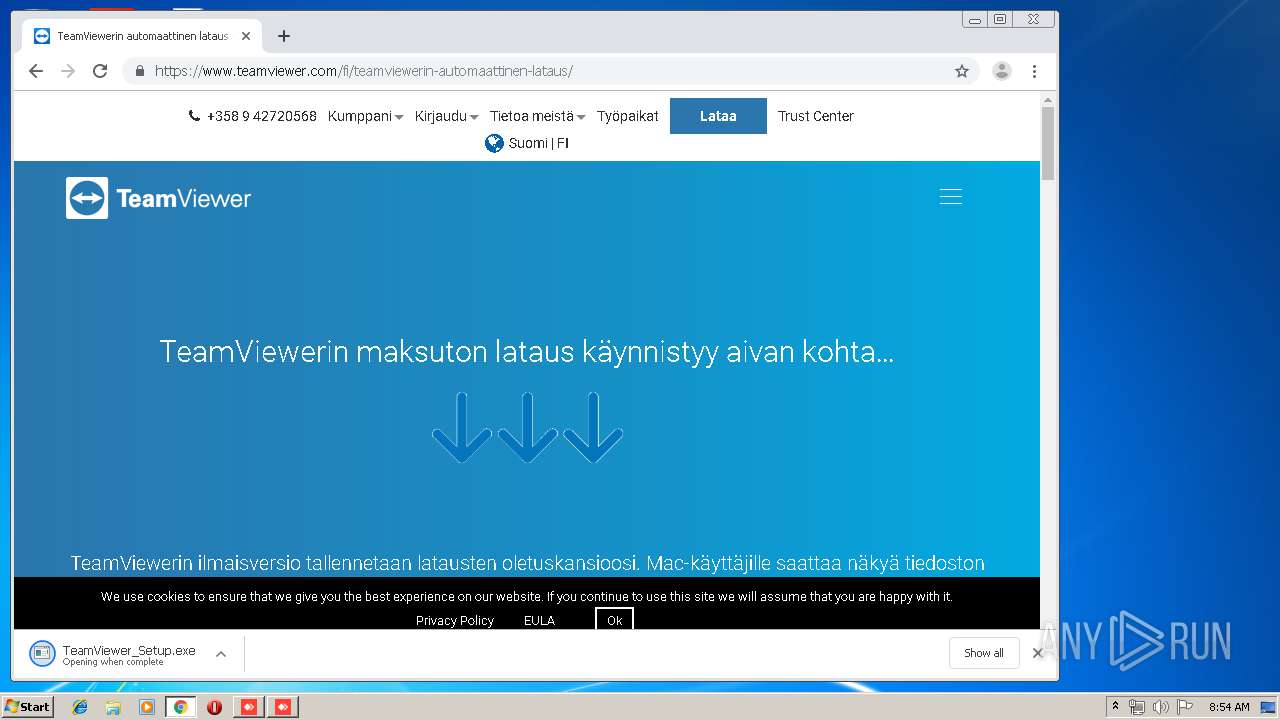
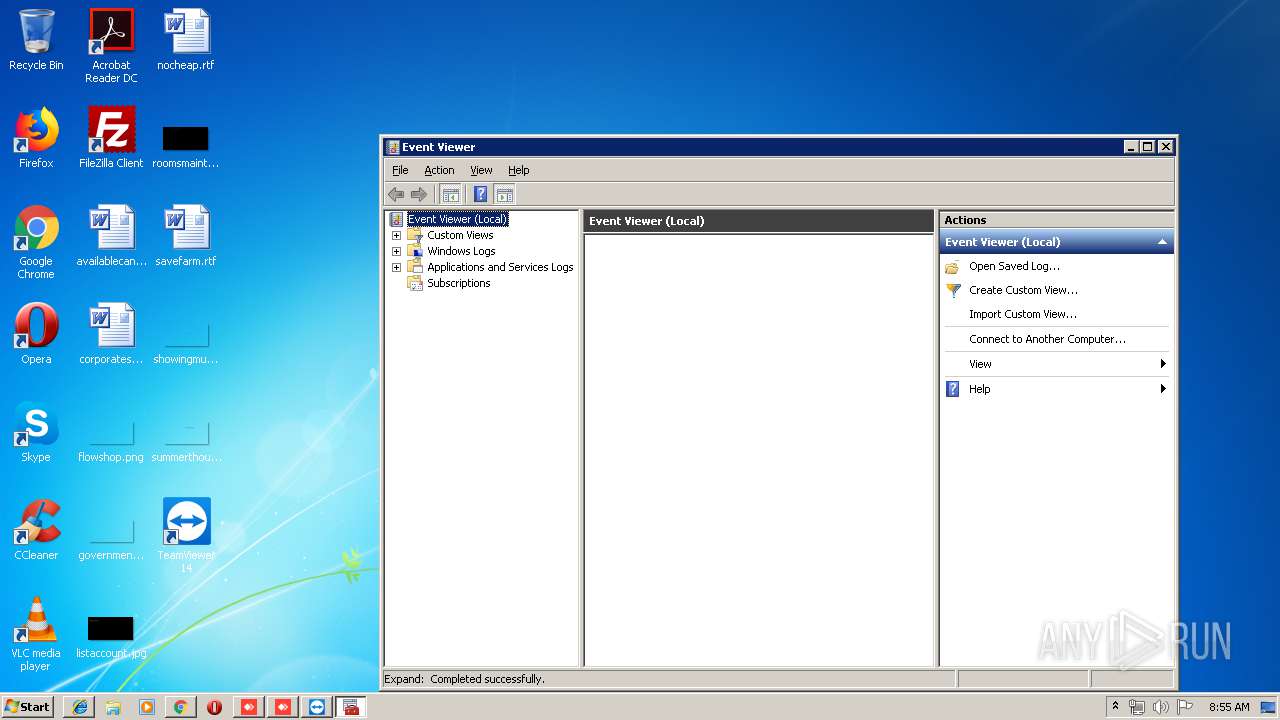
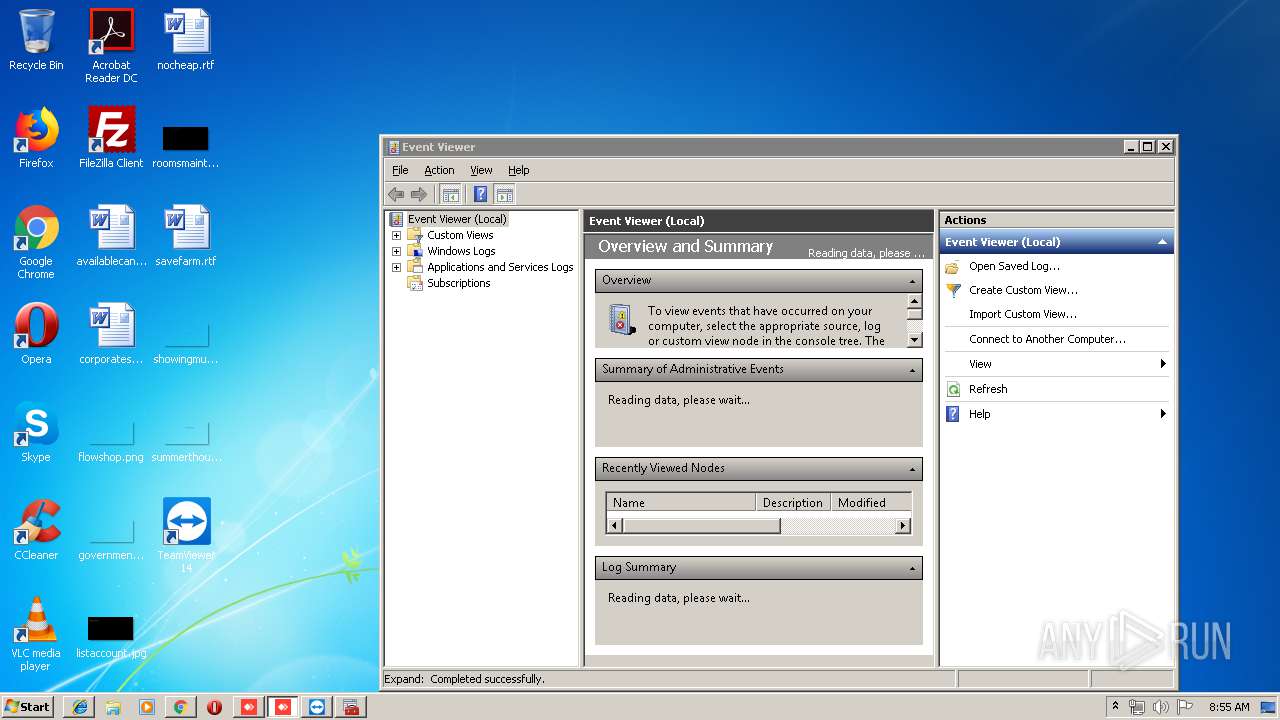
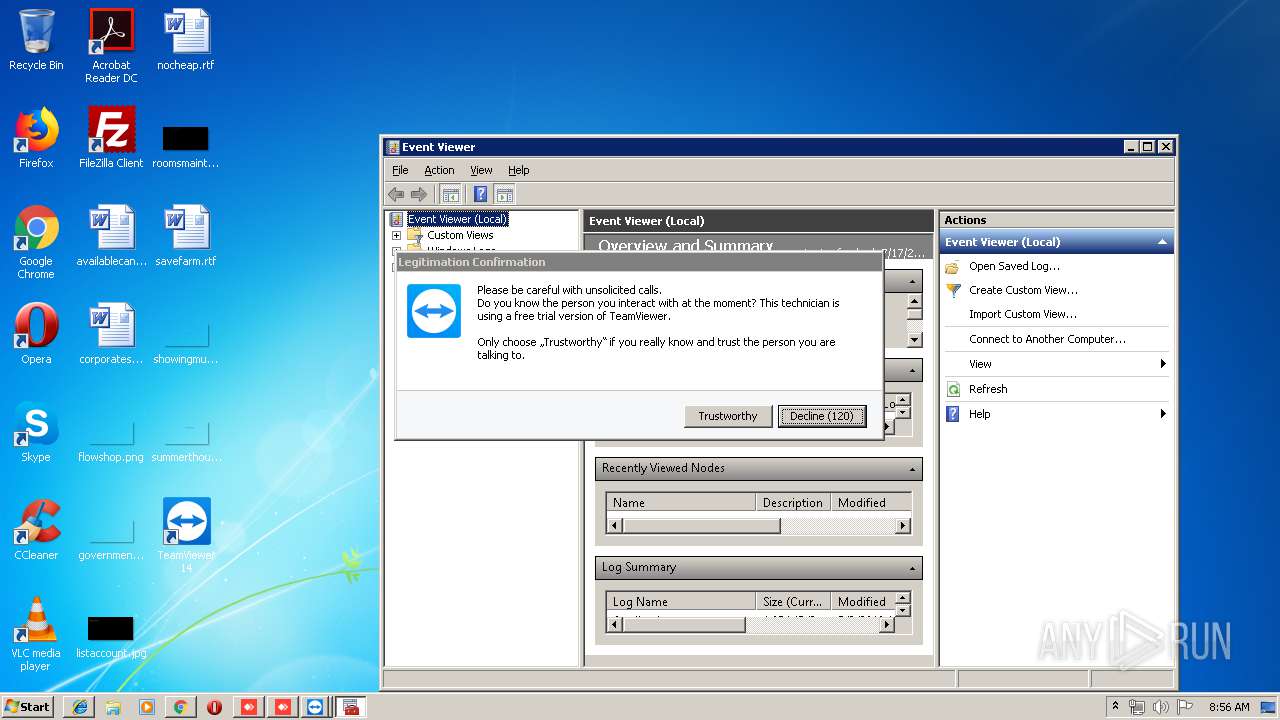
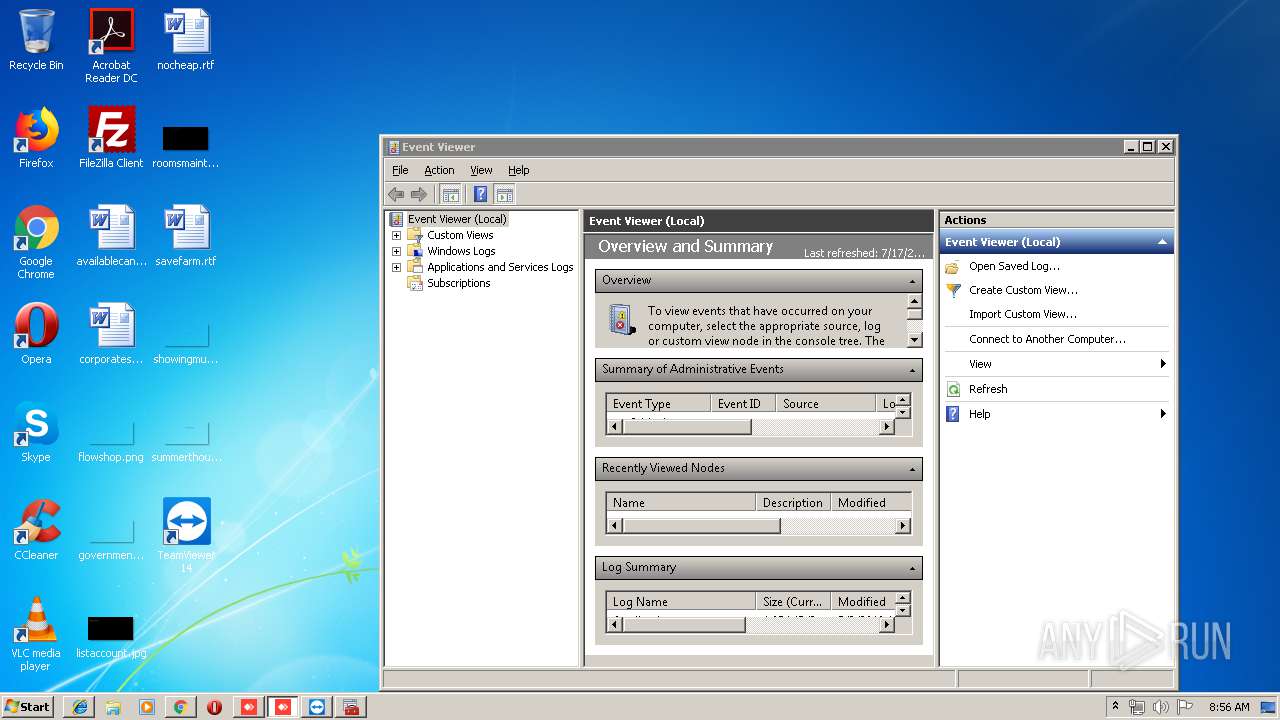
Manual execution by user
- chrome.exe (PID: 2416)
- eventvwr.exe (PID: 560)
- eventvwr.exe (PID: 3576)
Application launched itself
- chrome.exe (PID: 2416)
- iexplore.exe (PID: 252)
Reads Internet Cache Settings
- chrome.exe (PID: 2416)
- iexplore.exe (PID: 2704)
- iexplore.exe (PID: 348)
- iexplore.exe (PID: 252)
Reads settings of System Certificates
- chrome.exe (PID: 2416)
- chrome.exe (PID: 3916)
Creates files in the user directory
- iexplore.exe (PID: 2704)
- iexplore.exe (PID: 348)
- iexplore.exe (PID: 252)
Changes internet zones settings
- iexplore.exe (PID: 252)
Reads internet explorer settings
- iexplore.exe (PID: 348)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (52.9) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (23.5) |
| .exe | | | DOS Executable Generic (23.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:07:12 18:24:22+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 10 |
| CodeSize: | 10752 |
| InitializedDataSize: | 2906112 |
| UninitializedDataSize: | 8975360 |
| EntryPoint: | 0x1ce9 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 5.2.2.0 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Unknown (0) |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| CompanyName: | philandro Software GmbH |
| FileDescription: | AnyDesk |
| FileVersion: | 5.2.2.0 |
| ProductName: | AnyDesk |
| ProductVersion: | 5.2 |
| LegalCopyright: | (C) 2019 philandro Software GmbH |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 12-Jul-2019 16:24:22 |
| Detected languages: |
|
| Debug artifacts: |
|
| CompanyName: | philandro Software GmbH |
| FileDescription: | AnyDesk |
| FileVersion: | 5.2.2.0 |
| ProductName: | AnyDesk |
| ProductVersion: | 5.2 |
| LegalCopyright: | (C) 2019 philandro Software GmbH |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D0 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 6 |
| Time date stamp: | 12-Jul-2019 16:24:22 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00002835 | 0x00002A00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.4881 |
.itext | 0x00004000 | 0x0088F400 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x00894000 | 0x000002E6 | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.52935 |
.data | 0x00895000 | 0x002C1A04 | 0x002C1600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.99994 |
.rsrc | 0x00B57000 | 0x00003290 | 0x00003400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.68329 |
.reloc | 0x00B5B000 | 0x000002F4 | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 1.164 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.38823 | 1540 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 2.29968 | 1640 | UNKNOWN | English - United States | RT_ICON |
3 | 3.6735 | 744 | UNKNOWN | English - United States | RT_ICON |
4 | 2.73746 | 488 | UNKNOWN | English - United States | RT_ICON |
5 | 3.69265 | 296 | UNKNOWN | English - United States | RT_ICON |
1000 | 2.78538 | 76 | UNKNOWN | English - United States | RT_GROUP_ICON |
Total processes
107
Monitored processes
55
Malicious processes
7
Suspicious processes
6
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 252 | "C:\Program Files\Internet Explorer\iexplore.exe" -nohome | C:\Program Files\Internet Explorer\iexplore.exe | TeamViewer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 348 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=996,10886106121909603447,518541568471622218,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=13971643903795635524 --mojo-platform-channel-handle=2672 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 348 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:252 CREDAT:71938 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 356 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=996,10886106121909603447,518541568471622218,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=2848652127029713373 --mojo-platform-channel-handle=2240 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 560 | "C:\Users\admin\AppData\Local\Temp\nspC895.tmp\ns17B4.tmp" C:\Windows\system32\schtasks /Delete /TN TVInstallRestore /F | C:\Users\admin\AppData\Local\Temp\nspC895.tmp\ns17B4.tmp | — | TeamViewer_.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 560 | "C:\Windows\system32\eventvwr.exe" | C:\Windows\system32\eventvwr.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Event Viewer Snapin Launcher Exit code: 3221226540 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 792 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=996,10886106121909603447,518541568471622218,131072 --enable-features=PasswordImport --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=9714381495786265830 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2224 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 856 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=996,10886106121909603447,518541568471622218,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=11282081379993236077 --mojo-platform-channel-handle=720 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 944 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=996,10886106121909603447,518541568471622218,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=4921071143899283405 --mojo-platform-channel-handle=2844 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1236 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=996,10886106121909603447,518541568471622218,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=6570207398724066071 --mojo-platform-channel-handle=3592 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
4 367
Read events
3 306
Write events
1 049
Delete events
12
Modification events
| (PID) Process: | (3096) AnyDesk.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\Advanced |
| Operation: | write | Name: | TaskbarAnimations |
Value: 0 | |||
| (PID) Process: | (2408) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2416-13207823605680625 |
Value: 259 | |||
| (PID) Process: | (2416) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2416) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2416) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2416) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2416) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2416) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2416) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2416) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 1512-13197841398593750 |
Value: 0 | |||
Executable files
126
Suspicious files
154
Text files
381
Unknown types
46
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3648 | AnyDesk.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\0OIN3JSX1469HJB401YQ.temp | — | |
MD5:— | SHA256:— | |||
| 2416 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\3e70e24e-99f3-42f5-97d1-20bf4df8c540.tmp | — | |
MD5:— | SHA256:— | |||
| 2416 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000020.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3840 | AnyDesk.exe | C:\Users\admin\AppData\Roaming\AnyDesk\service.conf | text | |
MD5:— | SHA256:— | |||
| 2416 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2416 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2416 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old~RF12acd2.TMP | text | |
MD5:— | SHA256:— | |||
| 3840 | AnyDesk.exe | C:\Users\admin\AppData\Roaming\AnyDesk\connection_trace.txt | binary | |
MD5:— | SHA256:— | |||
| 2416 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2416 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF12ac74.TMP | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
11
TCP/UDP connections
132
DNS requests
90
Threats
7
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2236 | TeamViewer.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBR8sWZUnKvbRO5iJhat9GV793rVlAQUrb2YejS0Jvf6xCZU7wO94CTLVBoCECdm7lbrSfOOq9dwovyE3iI%3D | US | der | 471 b | whitelisted |
2236 | TeamViewer.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBReAhtobFzTvhaRmVeJ38QUchY9AwQUu69%2BAj36pvE8hI6t7jiY7NkyMtQCECsuburZdTZsFIpu26N8jAc%3D | US | der | 727 b | whitelisted |
3916 | chrome.exe | GET | 200 | 205.185.216.42:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 56.3 Kb | whitelisted |
3916 | chrome.exe | GET | 302 | 172.217.23.174:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 521 b | whitelisted |
3916 | chrome.exe | GET | 200 | 87.245.195.173:80 | http://r2---sn-gxuog0-jx3e.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mip=185.117.118.92&mm=28&mn=sn-gxuog0-jx3e&ms=nvh&mt=1563349937&mv=m&mvi=1&pl=25&shardbypass=yes | RU | crx | 862 Kb | whitelisted |
252 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
2236 | TeamViewer.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.comodoca.com/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBR64T7ooMQqLLQoy%2BemBUYZQOKh6QQUkK9qOpRaC9iQ6hJWc99DtDoo2ucCEQCqAbgx0U87EUkINDCWkQbB | US | der | 472 b | whitelisted |
3916 | chrome.exe | GET | 200 | 52.85.182.185:80 | http://x.ss2.us/x.cer | US | der | 1.27 Kb | whitelisted |
348 | iexplore.exe | GET | 200 | 91.199.212.52:80 | http://crt.usertrust.com/USERTrustRSAAddTrustCA.crt | GB | der | 1.37 Kb | whitelisted |
— | — | GET | 200 | 91.199.212.52:80 | http://crt.comodoca.com/COMODORSAAddTrustCA.crt | GB | der | 1.37 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
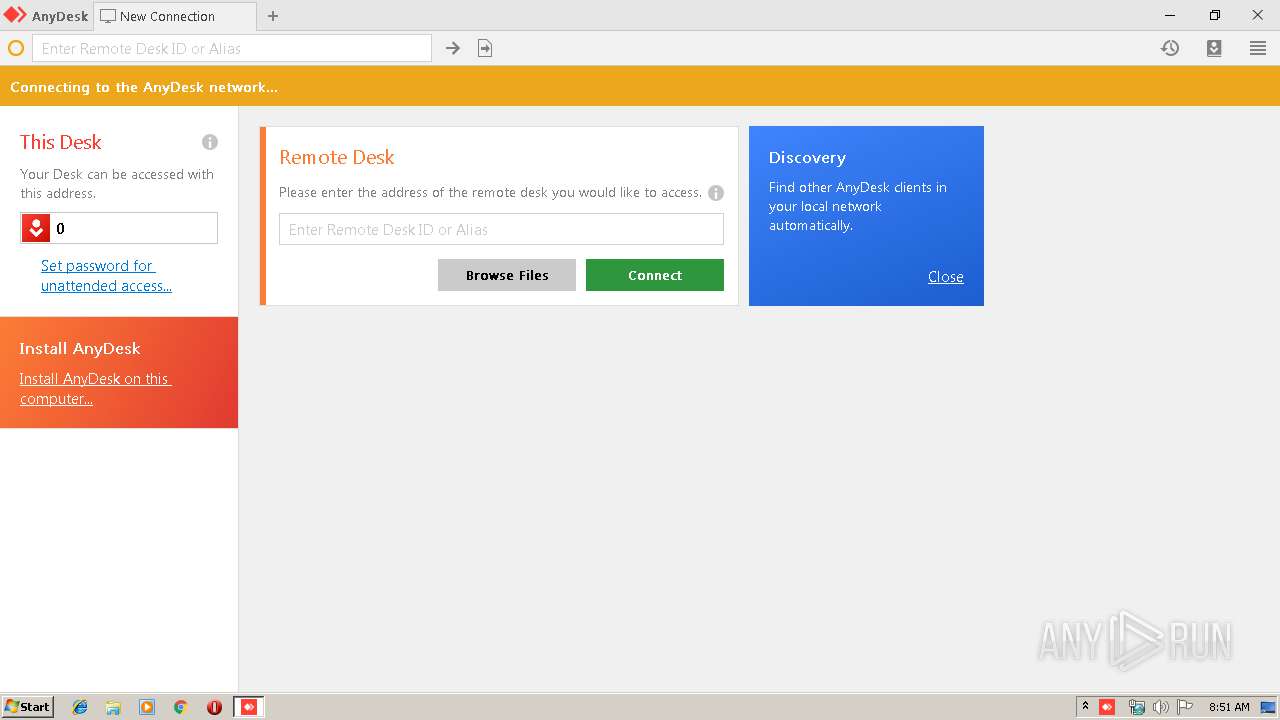
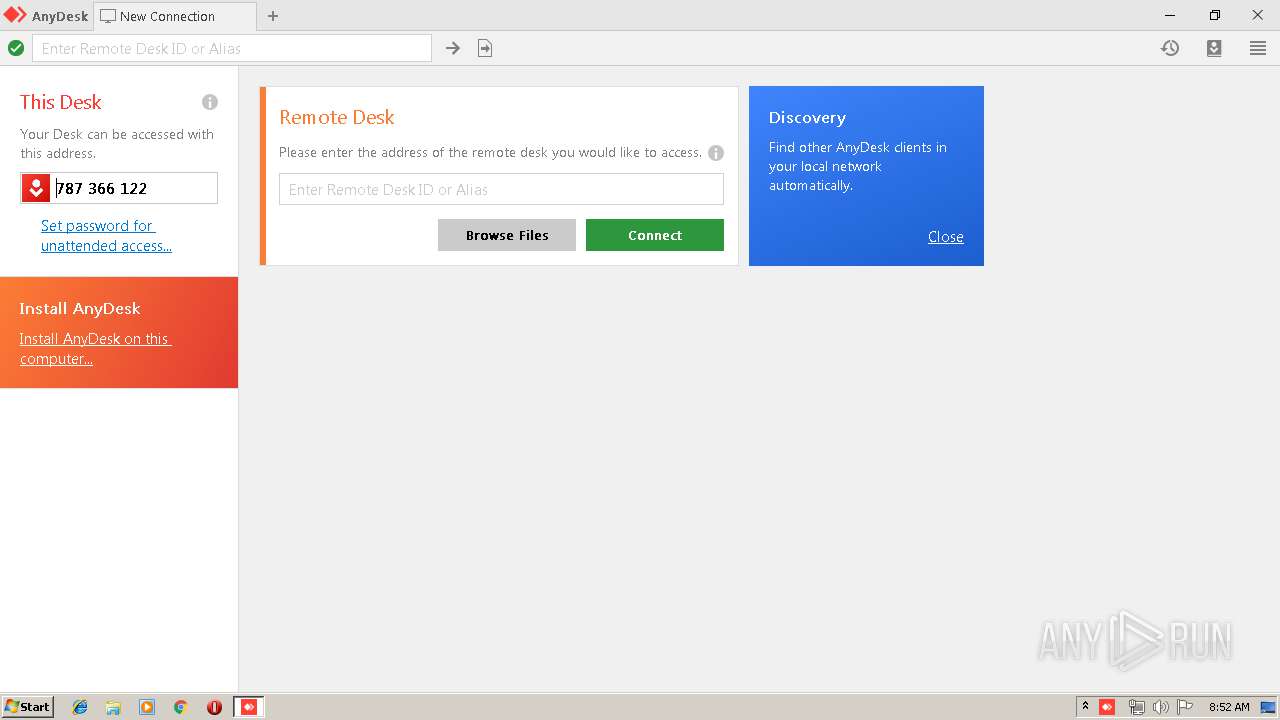
3840 | AnyDesk.exe | 5.9.144.165:443 | boot-01.net.anydesk.com | Hetzner Online GmbH | DE | unknown |
3840 | AnyDesk.exe | 5.9.144.165:6568 | boot-01.net.anydesk.com | Hetzner Online GmbH | DE | unknown |
3840 | AnyDesk.exe | 144.76.156.231:6568 | relay-10497ac9.net.anydesk.com | Hetzner Online GmbH | DE | unknown |
3840 | AnyDesk.exe | 144.76.156.231:80 | relay-10497ac9.net.anydesk.com | Hetzner Online GmbH | DE | unknown |
3840 | AnyDesk.exe | 5.9.144.165:80 | boot-01.net.anydesk.com | Hetzner Online GmbH | DE | unknown |
3840 | AnyDesk.exe | 46.4.119.76:80 | relay-623d48fd.net.anydesk.com | Hetzner Online GmbH | DE | unknown |
3840 | AnyDesk.exe | 46.4.119.76:443 | relay-623d48fd.net.anydesk.com | Hetzner Online GmbH | DE | unknown |
3840 | AnyDesk.exe | 136.0.99.29:50608 | — | Areti Internet Ltd. | US | unknown |
3840 | AnyDesk.exe | 136.0.99.29:7070 | — | Areti Internet Ltd. | US | unknown |
3916 | chrome.exe | 172.217.18.10:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
boot-01.net.anydesk.com |
| whitelisted |
relay-10497ac9.net.anydesk.com |
| unknown |
relay-623d48fd.net.anydesk.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com.ua |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
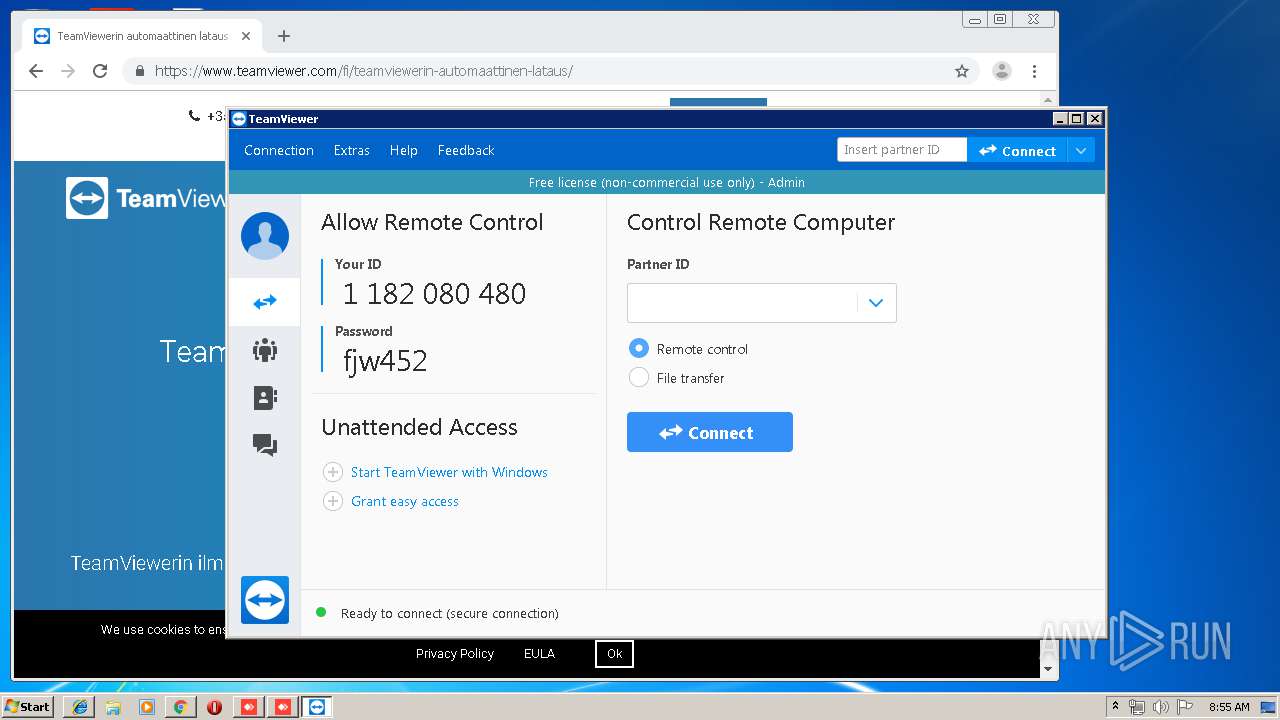
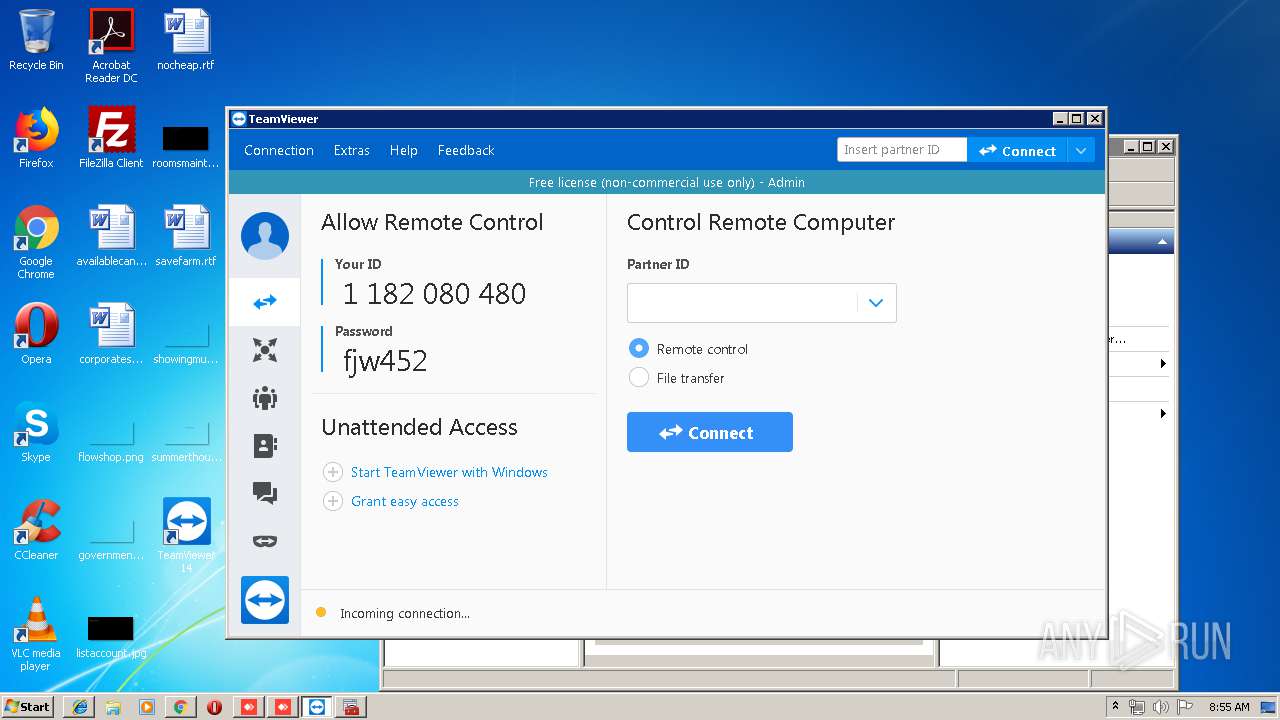
2324 | TeamViewer_Service.exe | Potential Corporate Privacy Violation | POLICY [PTsecurity] TeamViewer connection |
2324 | TeamViewer_Service.exe | Potential Corporate Privacy Violation | POLICY [PTsecurity] TeamViewer negotiation |
2324 | TeamViewer_Service.exe | Potential Corporate Privacy Violation | POLICY [PTsecurity] TeamViewer connection |
2324 | TeamViewer_Service.exe | Potential Corporate Privacy Violation | POLICY [PTsecurity] TeamViewer negotiation |
2324 | TeamViewer_Service.exe | Potential Corporate Privacy Violation | POLICY [PTsecurity] TeamViewer negotiation |
2 ETPRO signatures available at the full report
Process | Message |
|---|---|
mmc.exe | ViewerConfigPath = 'C:\ProgramData\Microsoft\Event Viewer': Microsoft.Windows.ManagementUI.CombinedControls.EventsNode
|
mmc.exe | ViewerViewsFolderPath = 'C:\ProgramData\Microsoft\Event Viewer\Views': Microsoft.Windows.ManagementUI.CombinedControls.EventsNode
|
mmc.exe | ViewerAdminViewsPath = 'C:\ProgramData\Microsoft\Event Viewer\Views\ApplicationViewsRootNode': Microsoft.Windows.ManagementUI.CombinedControls.EventsNode
|
mmc.exe | ViewerExternalLogsPath = 'C:\ProgramData\Microsoft\Event Viewer\ExternalLogs': Microsoft.Windows.ManagementUI.CombinedControls.EventsNode
|
mmc.exe | Failed to get ChannelConfigOwningPublisher -122-The data area passed to a system call is too small
|
mmc.exe | Getting next publisher from enum failed-259-No more data is available
|
mmc.exe | Failed to get ChannelConfigOwningPublisher -122-The data area passed to a system call is too small
|
mmc.exe | ExpandNode:After EventsNode:InsertChildren CountOfChildren = 5
|
mmc.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
mmc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|