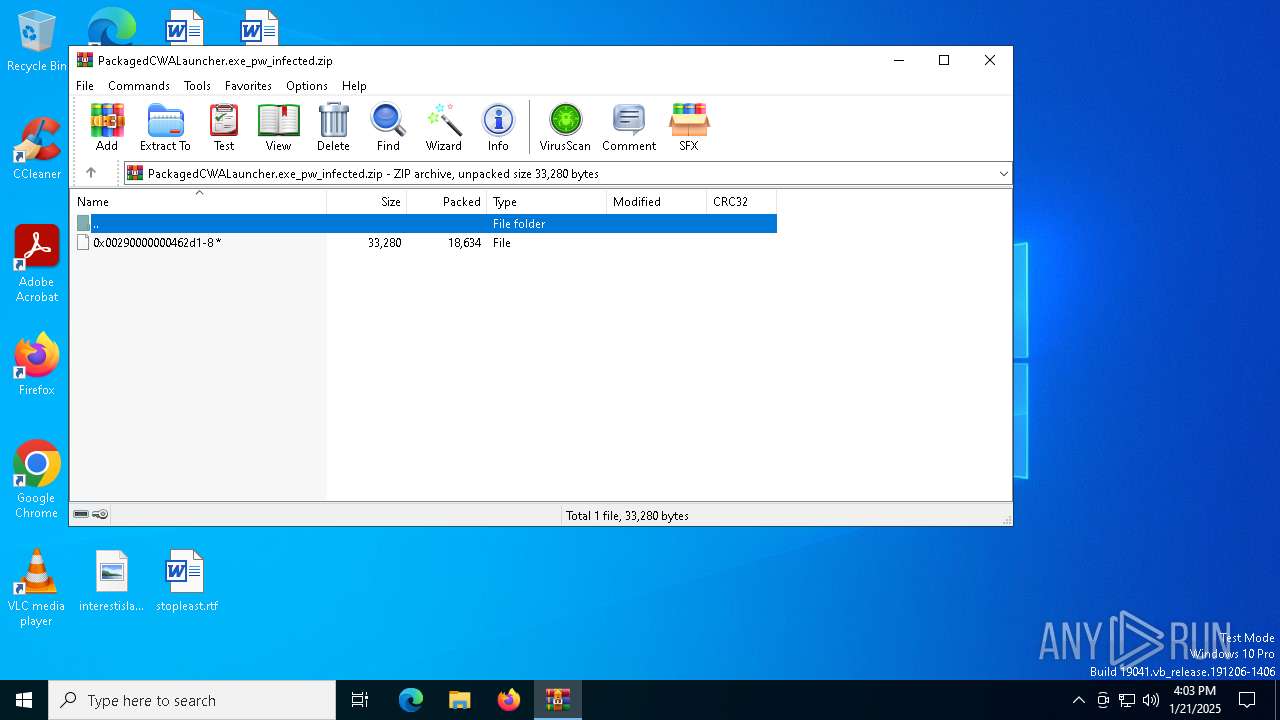
| File name: | PackagedCWALauncher.exe_pw_infected.zip |
| Full analysis: | https://app.any.run/tasks/b40943fa-7d14-4031-b653-de0ae2cdb618 |
| Verdict: | Malicious activity |
| Analysis date: | January 21, 2025, 16:03:08 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/zip |
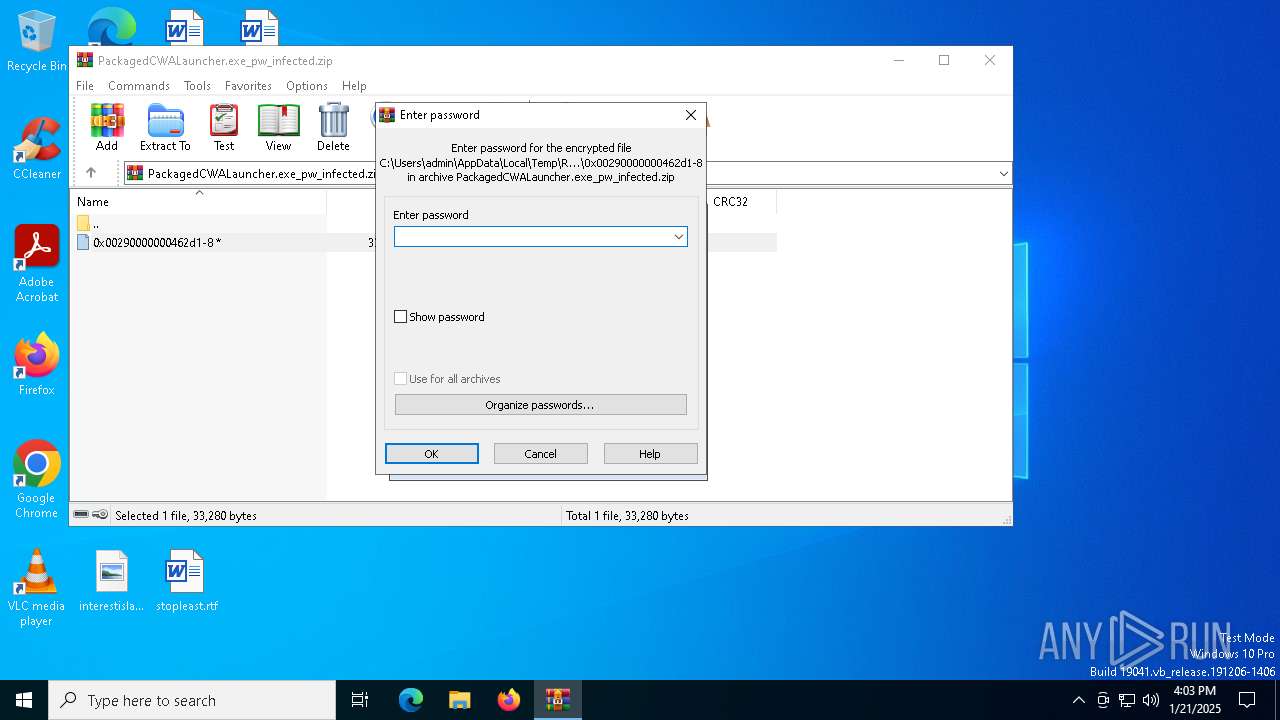
| File info: | Zip archive data, at least v2.0 to extract, compression method=AES Encrypted |
| MD5: | 41E54781E8B721721A91D5830C30F5BC |
| SHA1: | 861C9EBF63715DDBB844CCB54779134D697FC09C |
| SHA256: | D91AB3868C512BE90FD32BBB4059E36CA4EC0CB0FECA53AC3F952F813A80FB23 |
| SSDEEP: | 384:X5fRSoiqggEKAmxKCRW/NIaP+zlYIbXbI3qIAd7dq2ivI6/Vk9SZf5fdK++sx:XOdgEKAmxbqWJYIbXbI3qIAC2kVk9cgA |
MALICIOUS
Starts CMD.EXE for self-deleting
- 0x00290000000462d1-8.exe (PID: 644)
SUSPICIOUS
Process drops legitimate windows executable
- WinRAR.exe (PID: 6648)
- 0x00290000000462d1-8.exe (PID: 644)
Starts a Microsoft application from unusual location
- 0x00290000000462d1-8.exe (PID: 4540)
- 0x00290000000462d1-8.exe (PID: 644)
Executable content was dropped or overwritten
- 0x00290000000462d1-8.exe (PID: 644)
Executes as Windows Service
- net.exe (PID: 6208)
Starts CMD.EXE for commands execution
- 0x00290000000462d1-8.exe (PID: 644)
Reads security settings of Internet Explorer
- 0x00290000000462d1-8.exe (PID: 644)
Hides command output
- cmd.exe (PID: 1328)
Runs PING.EXE to delay simulation
- cmd.exe (PID: 1328)
Sets range of bytes to zero
- fsutil.exe (PID: 6844)
Connects to unusual port
- net.exe (PID: 6208)
INFO
The sample compiled with english language support
- WinRAR.exe (PID: 6648)
- 0x00290000000462d1-8.exe (PID: 644)
The process uses the downloaded file
- WinRAR.exe (PID: 6648)
- dllhost.exe (PID: 2076)
- 0x00290000000462d1-8.exe (PID: 644)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 6648)
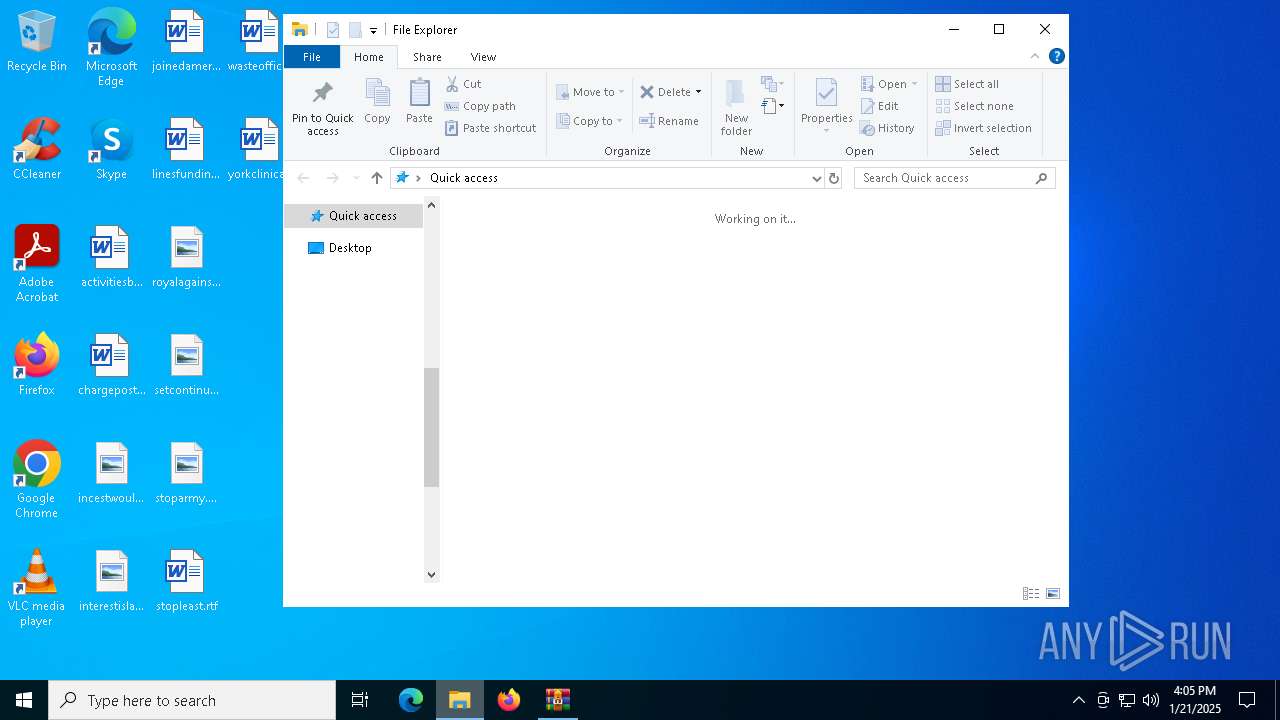
Manual execution by a user
- 0x00290000000462d1-8.exe (PID: 4540)
Reads the computer name
- 0x00290000000462d1-8.exe (PID: 4540)
- 0x00290000000462d1-8.exe (PID: 644)
- net.exe (PID: 6208)
Reads security settings of Internet Explorer
- dllhost.exe (PID: 2076)
Reads the machine GUID from the registry
- 0x00290000000462d1-8.exe (PID: 4540)
- 0x00290000000462d1-8.exe (PID: 644)
- net.exe (PID: 6208)
Checks supported languages
- 0x00290000000462d1-8.exe (PID: 4540)
- 0x00290000000462d1-8.exe (PID: 644)
- net.exe (PID: 6208)
Create files in a temporary directory
- 0x00290000000462d1-8.exe (PID: 644)
Creates files in the program directory
- 0x00290000000462d1-8.exe (PID: 644)
Process checks computer location settings
- 0x00290000000462d1-8.exe (PID: 644)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0009 |
| ZipCompression: | Unknown (99) |
| ZipModifyDate: | 1980:00:00 00:00:00 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | 18634 |
| ZipUncompressedSize: | 33280 |
| ZipFileName: | 0x00290000000462d1-8 |
Total processes
140
Monitored processes
11
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 644 | "C:\Users\admin\Desktop\0x00290000000462d1-8.exe" | C:\Users\admin\Desktop\0x00290000000462d1-8.exe | dllhost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Packaged CWA Launcher Exit code: 0 Version: 10.0.19041.4355 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1328 | "C:\WINDOWS\system32\cmd.exe" /d /c ping -n 2 127.0.0.1 > NUL & fsutil file setzerodata offset=0 length=524288 "C:\Users\admin\Desktop\0x00290000000462d1-8.exe" & del "C:\Users\admin\Desktop\0x00290000000462d1-8.exe" > NUL & exit | C:\Windows\SysWOW64\cmd.exe | — | 0x00290000000462d1-8.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2076 | C:\WINDOWS\SysWOW64\DllHost.exe /Processid:{D2E7041B-2927-42FB-8E9F-7CE93B6DC937} | C:\Windows\SysWOW64\dllhost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4052 | C:\WINDOWS\SysWOW64\DllHost.exe /Processid:{3E5FC7F9-9A51-4367-9063-A120244FBEC7} | C:\Windows\SysWOW64\dllhost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4540 | "C:\Users\admin\Desktop\0x00290000000462d1-8.exe" | C:\Users\admin\Desktop\0x00290000000462d1-8.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Packaged CWA Launcher Exit code: 0 Version: 10.0.19041.4355 (WinBuild.160101.0800) Modules
| |||||||||||||||
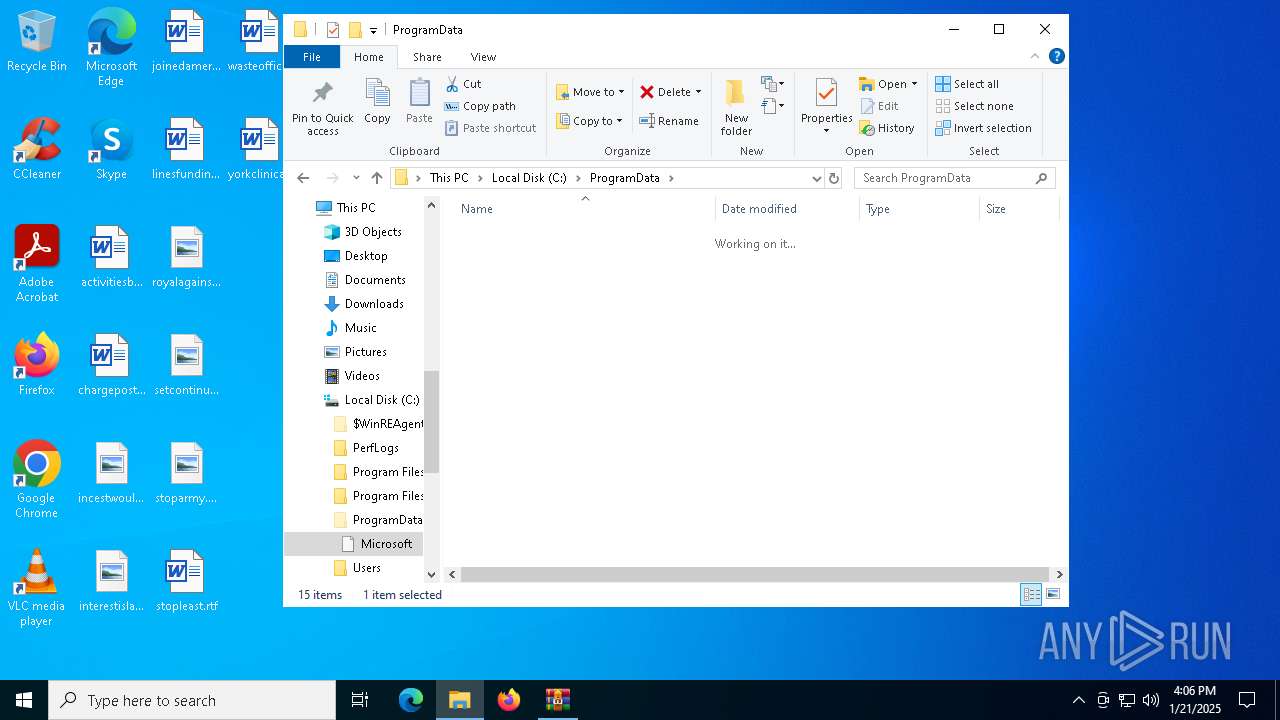
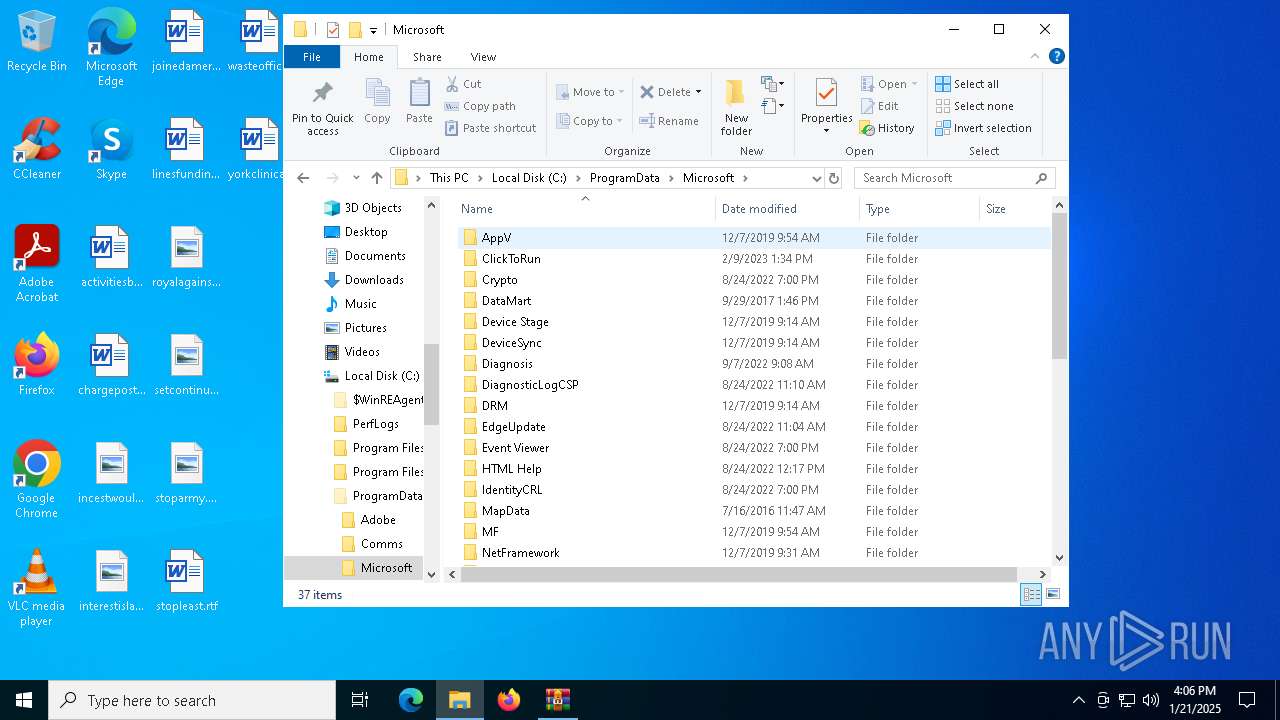
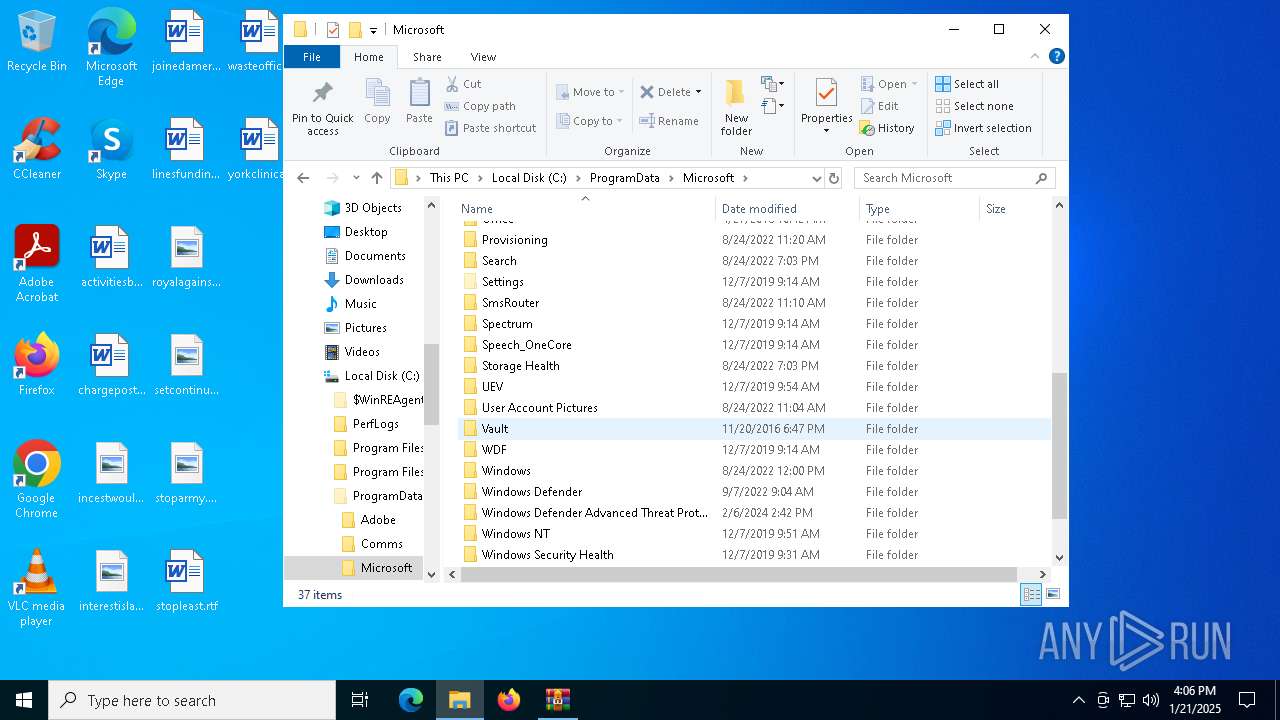
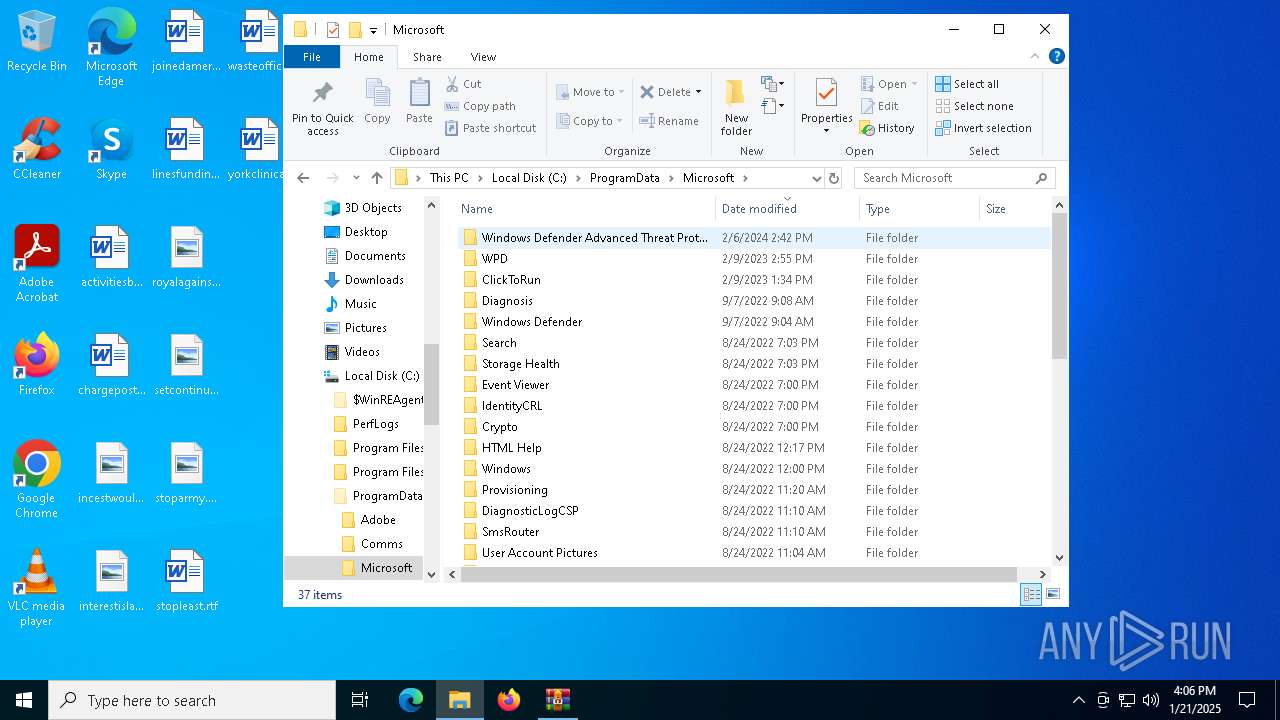
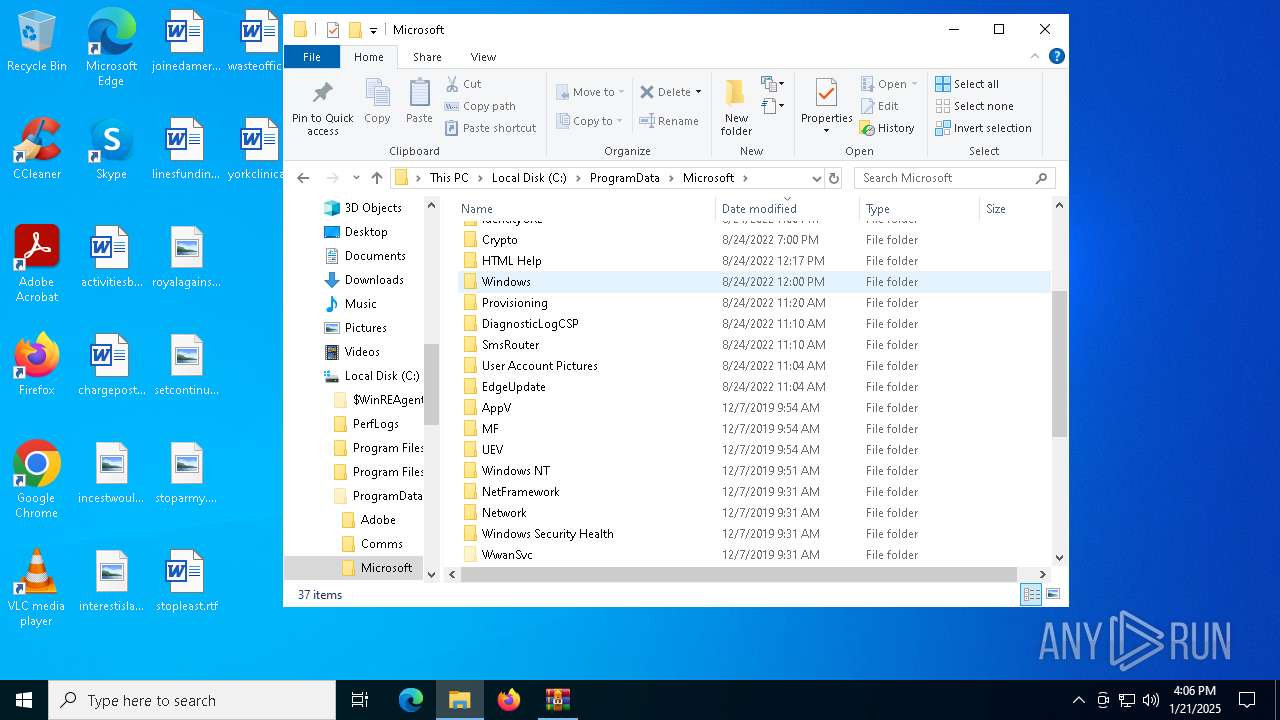
| 6208 | C:\ProgramData\Microsoft\v2.0_2.0.0.0__6cf057e92141bcbb\net.exe | C:\ProgramData\Microsoft\v2.0_2.0.0.0__6cf057e92141bcbb\net.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Net Command Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6248 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
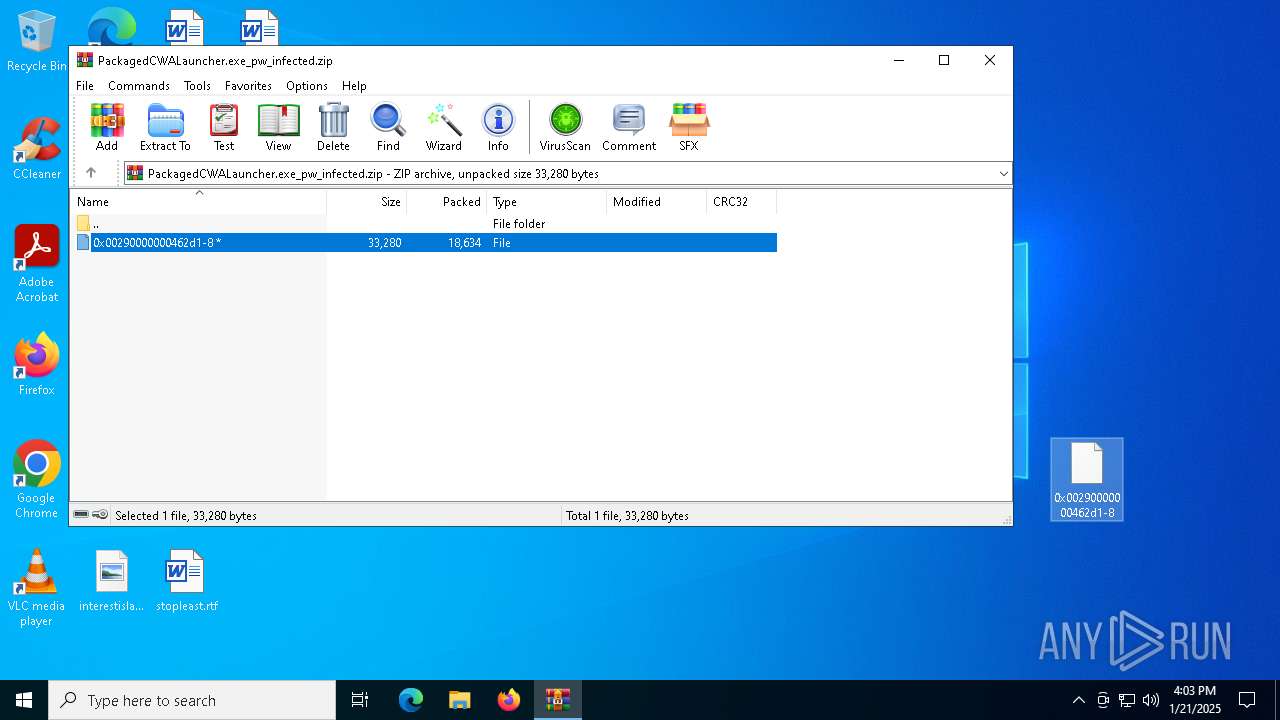
| 6648 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\AppData\Local\Temp\PackagedCWALauncher.exe_pw_infected.zip | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
| 6844 | fsutil file setzerodata offset=0 length=524288 "C:\Users\admin\Desktop\0x00290000000462d1-8.exe" | C:\Windows\SysWOW64\fsutil.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: fsutil.exe Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6880 | ping -n 2 127.0.0.1 | C:\Windows\SysWOW64\PING.EXE | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: TCP/IP Ping Command Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
2 852
Read events
2 841
Write events
10
Delete events
1
Modification events
| (PID) Process: | (6648) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (6648) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (6648) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (6648) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\PackagedCWALauncher.exe_pw_infected.zip | |||
| (PID) Process: | (6648) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (6648) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (6648) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (6648) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (6648) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
| (PID) Process: | (4052) dllhost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows NT\CurrentVersion\ICM\Calibration |
| Operation: | write | Name: | DisplayCalibrator |
Value: C:\Users\admin\Desktop\0x00290000000462d1-8.exe | |||
Executable files
24
Suspicious files
2
Text files
10
Unknown types
0
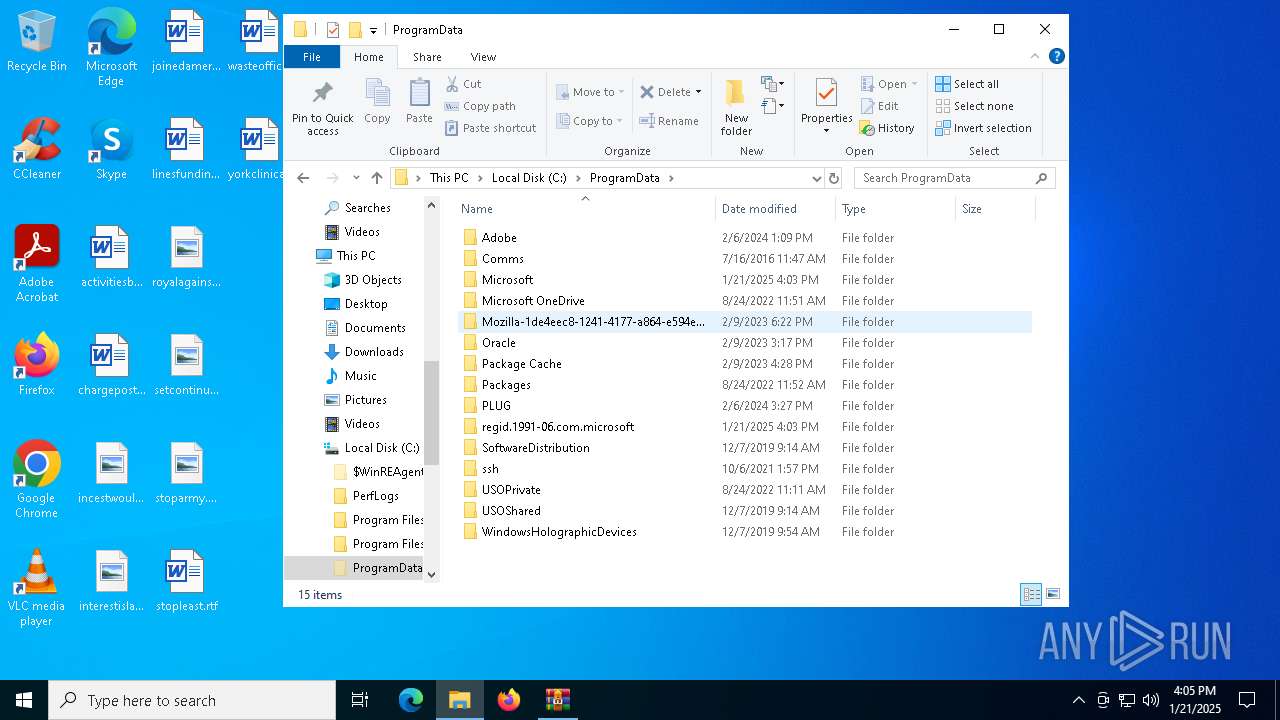
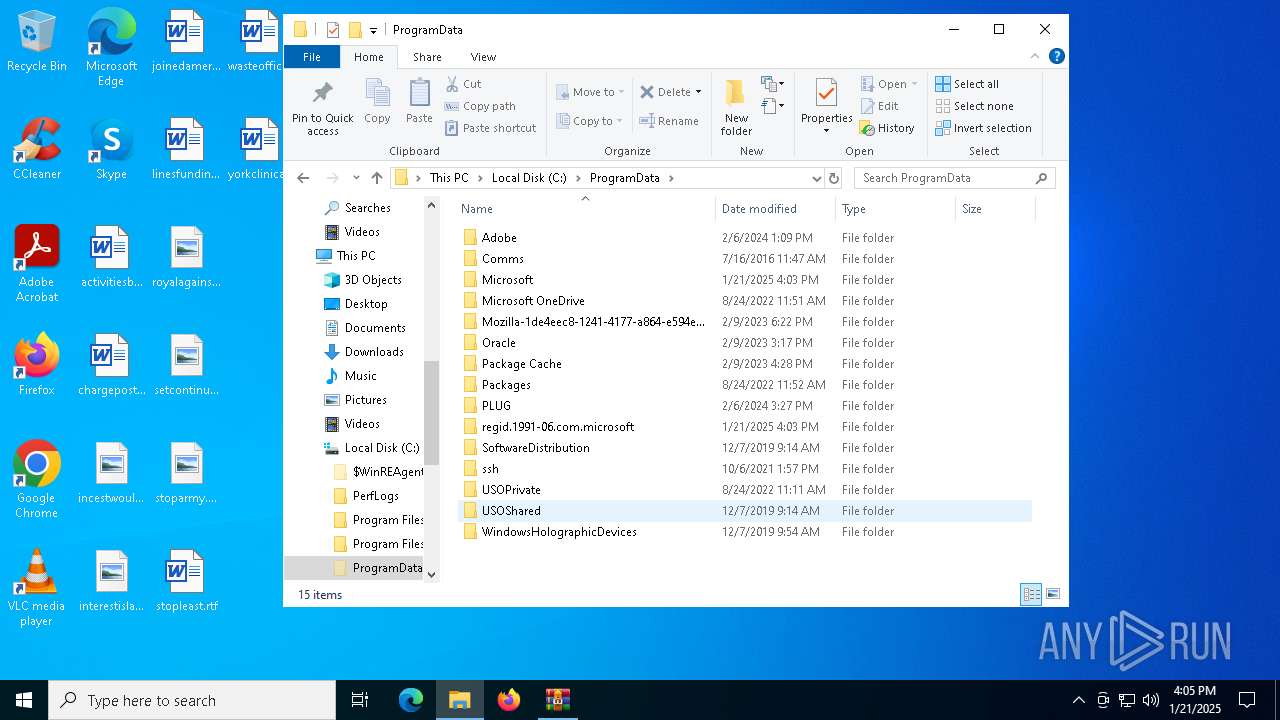
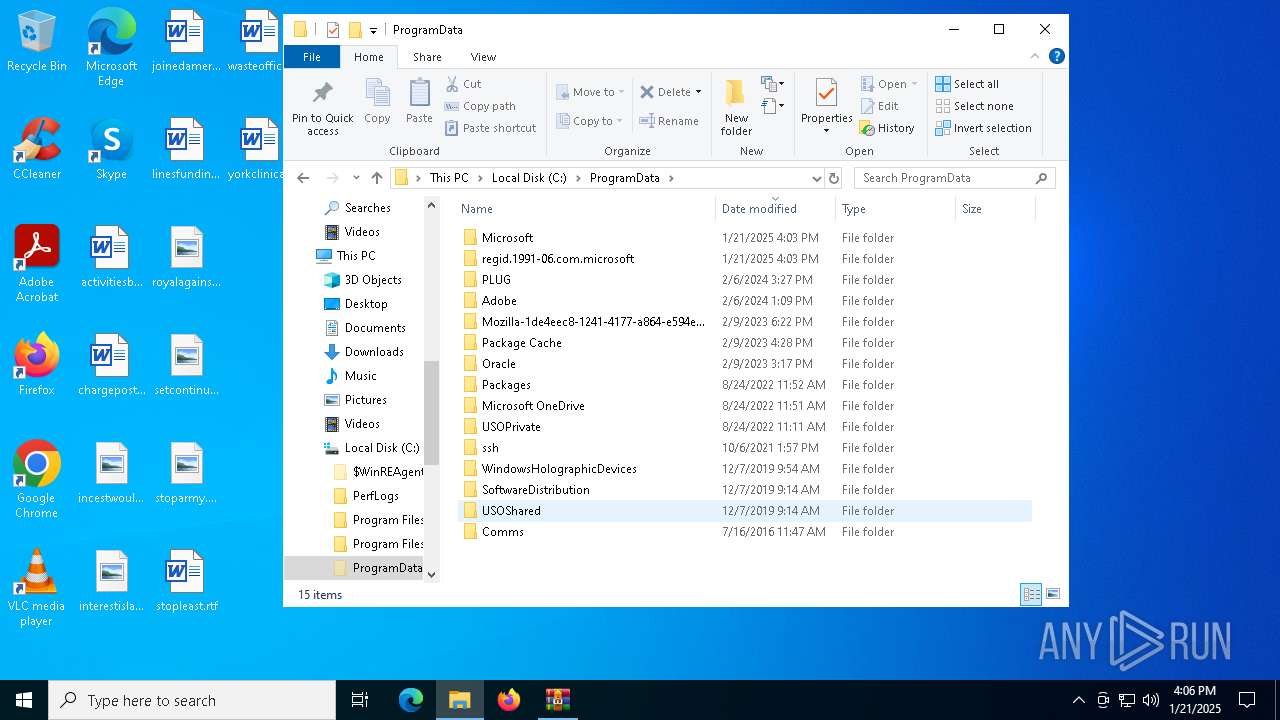
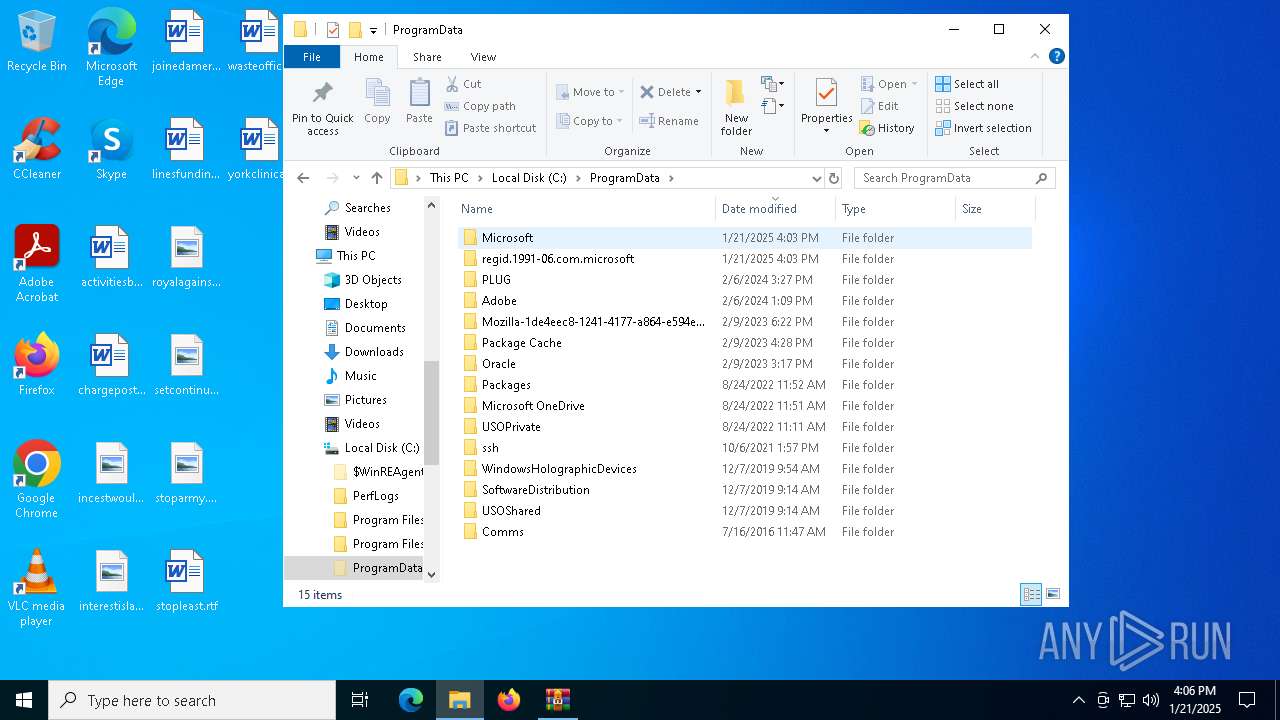
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
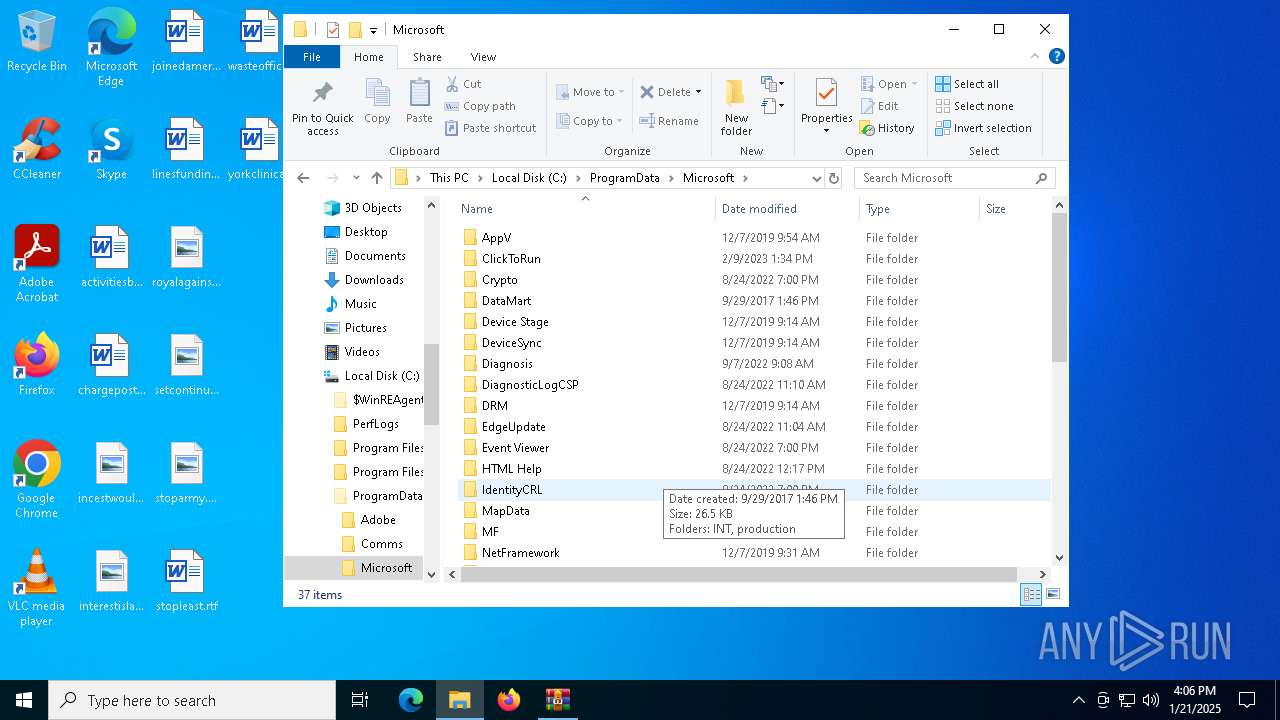
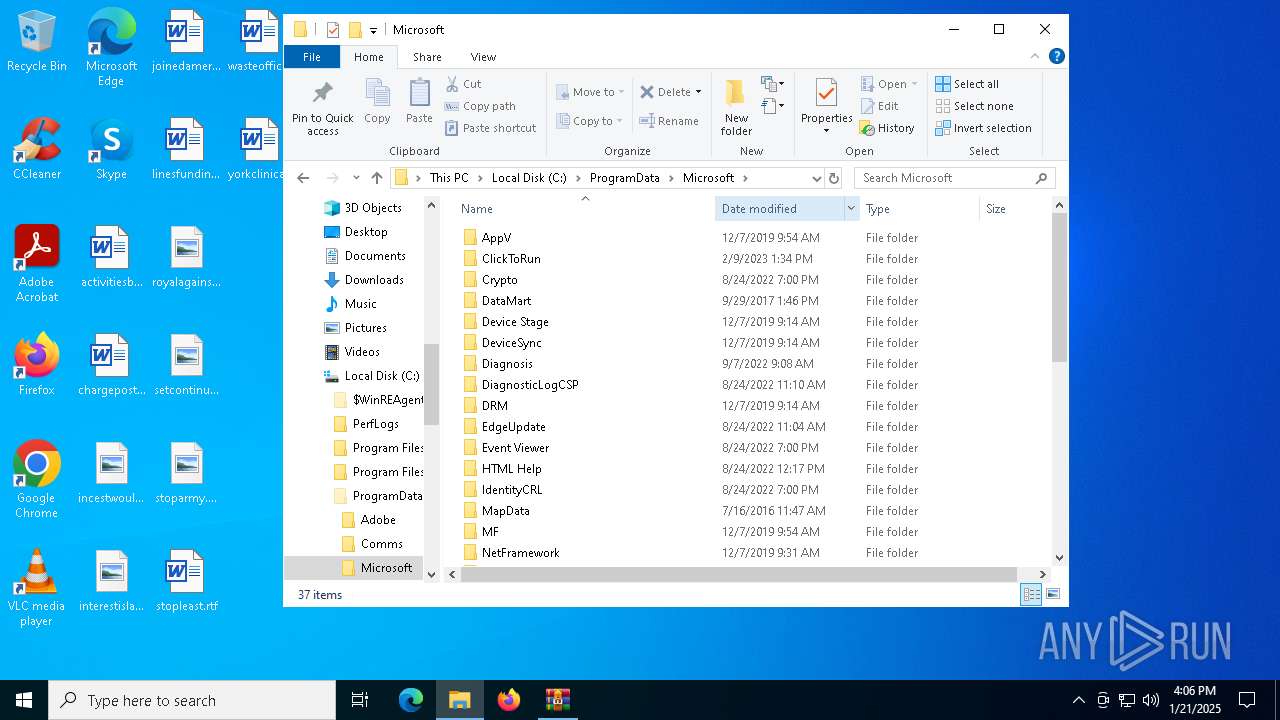
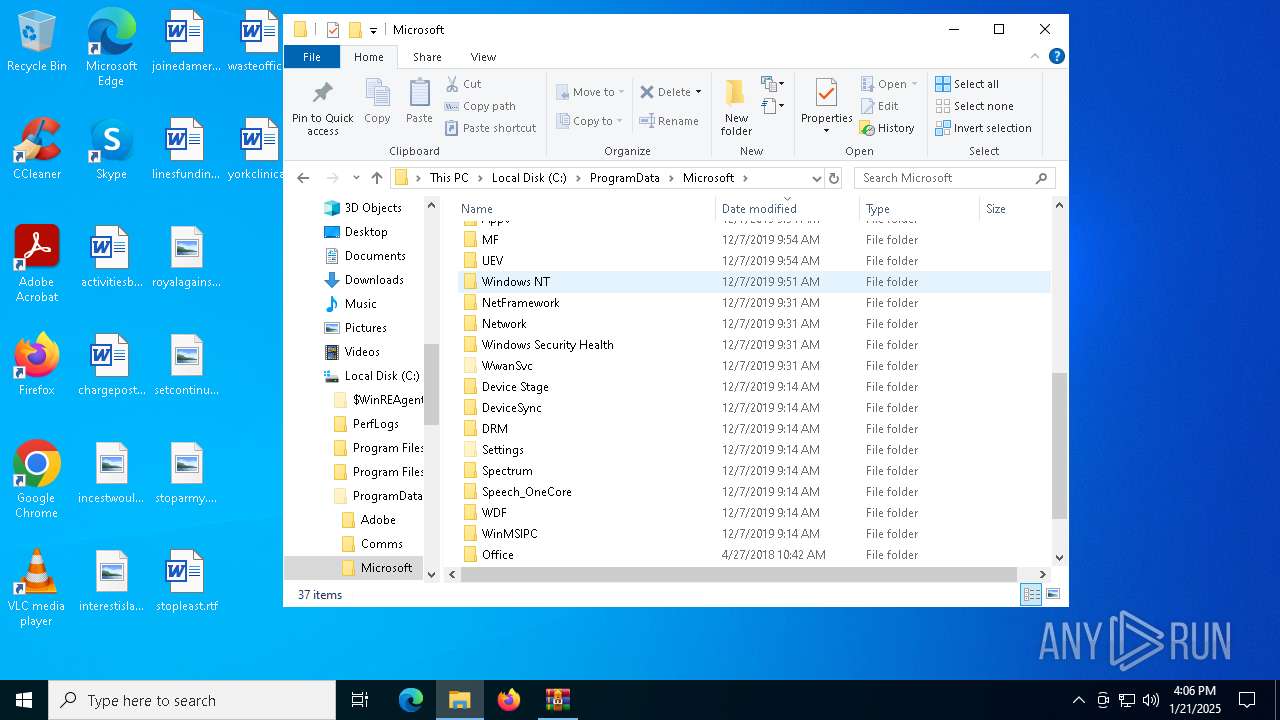
| 644 | 0x00290000000462d1-8.exe | C:\ProgramData\Microsoft\v2.0_2.0.0.0__6cf057e92141bcbb\RCX456.tmp | executable | |
MD5:F1D78962B3E2EB0E65F1C16708283FA9 | SHA256:063BEF606EC4A5719353D8AEF850A3066F07DEDC3B390F75F21F7972B6FE155D | |||
| 644 | 0x00290000000462d1-8.exe | C:\Users\admin\AppData\Local\Temp\tmp444.tmp | executable | |
MD5:BC6F7F9E0C30AE3C0BEF12A115E9558D | SHA256:DE290F2F2A911FD769AD309C8EB8E6574AB8316D3E7CDFCE77983AA50B5BD584 | |||
| 644 | 0x00290000000462d1-8.exe | C:\ProgramData\Microsoft\v2.0_2.0.0.0__6cf057e92141bcbb\wsmanconfig_schemax.xml | text | |
MD5:930423065AB3F5DB52D5726C7FC66385 | SHA256:176FE54ED73D56B0A03F33B6C5997E5701F46BBB0309A46477E9DD256BE50A09 | |||
| 644 | 0x00290000000462d1-8.exe | C:\ProgramData\Microsoft\v2.0_2.0.0.0__6cf057e92141bcbb\net.exe | executable | |
MD5:BC6F7F9E0C30AE3C0BEF12A115E9558D | SHA256:DE290F2F2A911FD769AD309C8EB8E6574AB8316D3E7CDFCE77983AA50B5BD584 | |||
| 644 | 0x00290000000462d1-8.exe | C:\ProgramData\Microsoft\v2.0_2.0.0.0__6cf057e92141bcbb\ndfetwm.dll | executable | |
MD5:469420A1AEA6901E6417D93F016DDC85 | SHA256:ADCBA24AF4805B748CC11E215D2E7DAA3B3859091D55D06F104737123DB5555D | |||
| 6648 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb6648.21937\0x00290000000462d1-8 | executable | |
MD5:BC6F7F9E0C30AE3C0BEF12A115E9558D | SHA256:DE290F2F2A911FD769AD309C8EB8E6574AB8316D3E7CDFCE77983AA50B5BD584 | |||
| 644 | 0x00290000000462d1-8.exe | C:\ProgramData\Microsoft\v2.0_2.0.0.0__6cf057e92141bcbb\sysdms.cpl | executable | |
MD5:D2A49399F8105C848FA50D7CD0CE8193 | SHA256:B5A79DBDEC9105A661E1B495C5FA97A92AFF273B0D87E739760D6DC37273227B | |||
| 644 | 0x00290000000462d1-8.exe | C:\ProgramData\Microsoft\v2.0_2.0.0.0__6cf057e92141bcbb\wscuim.cpl | executable | |
MD5:3EA5429311E92628C2C483F1F65A532F | SHA256:F2C2CF31F7FB8E4399A46E901EE9D4D7AC4967C3B61FA87CB1976E1D89B8AAE8 | |||
| 644 | 0x00290000000462d1-8.exe | C:\ProgramData\Microsoft\v2.0_2.0.0.0__6cf057e92141bcbb\ALSNDMGRm.cpl | executable | |
MD5:4E91776F39821EB81C061C8BA4AE7A3E | SHA256:DE1B542148F47C65776C0BD6643F3CD998B065C9415E6BA7916B39CB33FD3D81 | |||
| 644 | 0x00290000000462d1-8.exe | C:\ProgramData\Microsoft\v2.0_2.0.0.0__6cf057e92141bcbb\AppxProvisionings.xml | xml | |
MD5:3D7FF4B04224F03AF5B3894878B1D33B | SHA256:8D1659B73479A51F5AA891390EB809156AFC52567C309E2462957E1D69B775A3 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
38
DNS requests
20
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4712 | MoUsoCoreWorker.exe | GET | 200 | 23.48.23.147:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
440 | svchost.exe | GET | 200 | 23.48.23.147:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 2.19.217.218:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
440 | svchost.exe | GET | 200 | 2.19.217.218:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
1732 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
1732 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
6392 | backgroundTaskHost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
5064 | SearchApp.exe | 23.212.110.186:443 | — | Akamai International B.V. | CZ | unknown |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
4712 | MoUsoCoreWorker.exe | 23.48.23.147:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
440 | svchost.exe | 23.48.23.147:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4712 | MoUsoCoreWorker.exe | 2.19.217.218:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
440 | svchost.exe | 2.19.217.218:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
1176 | svchost.exe | 40.126.31.71:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1176 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |