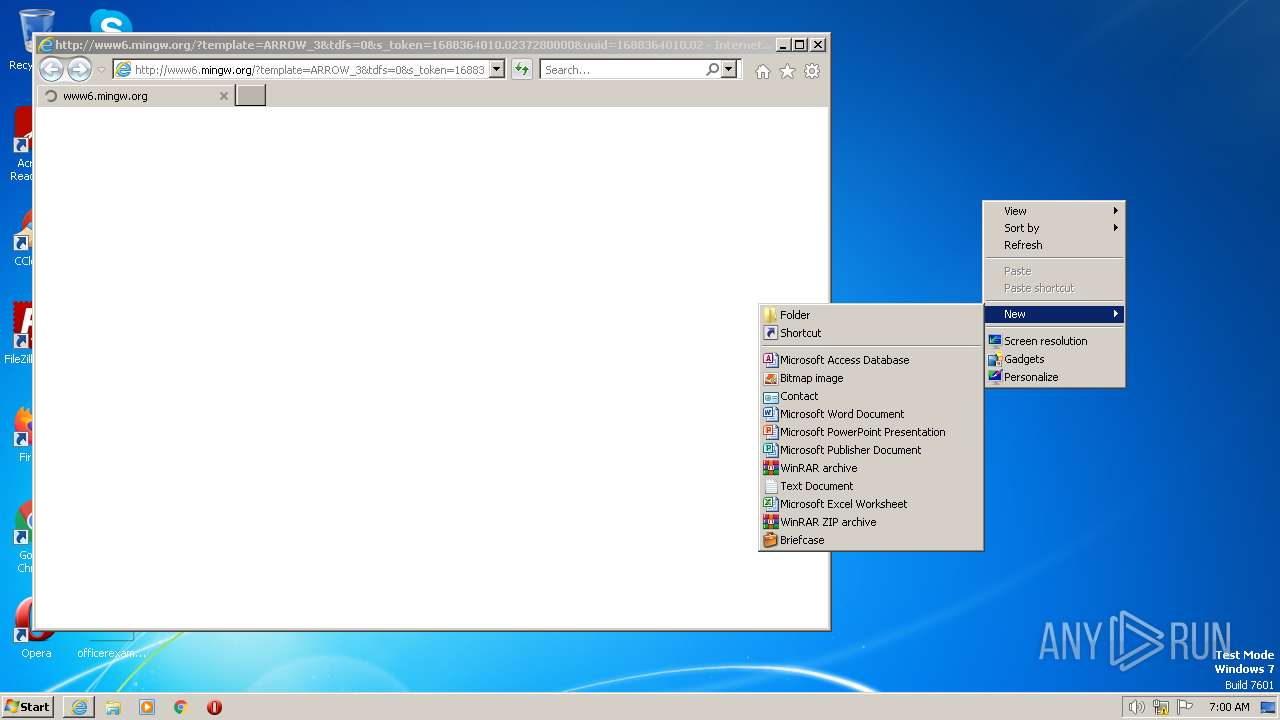
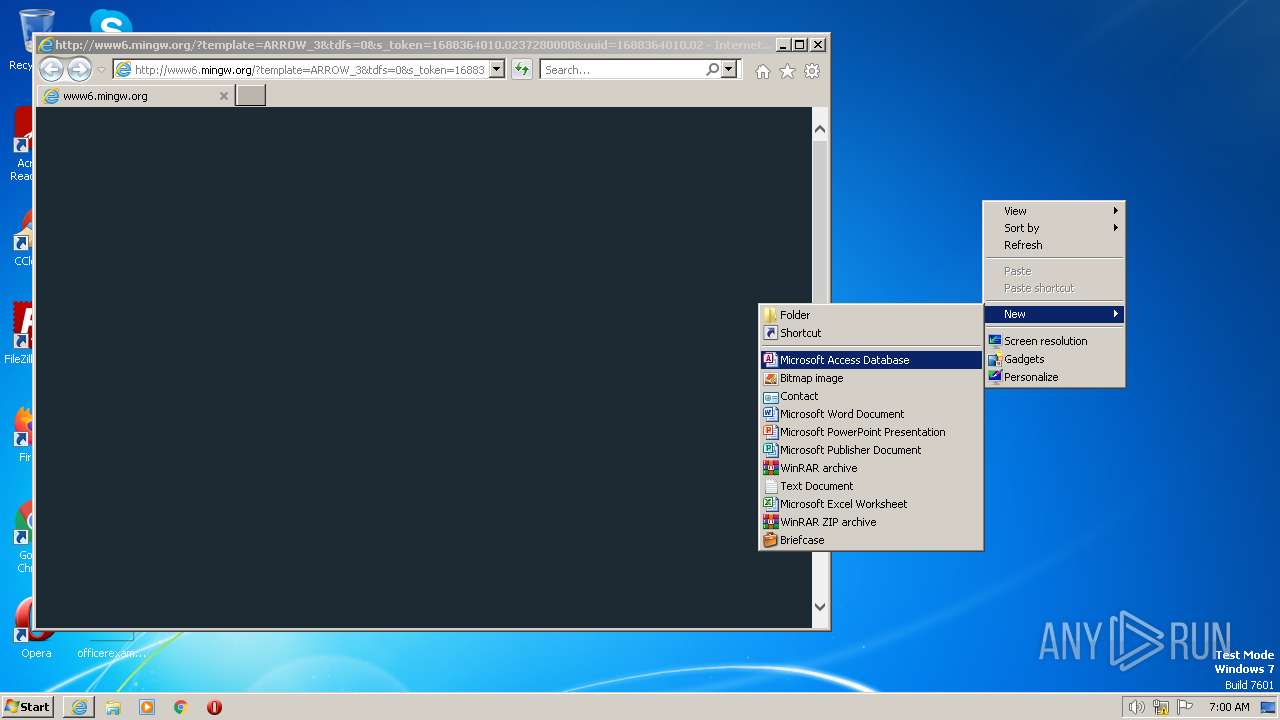
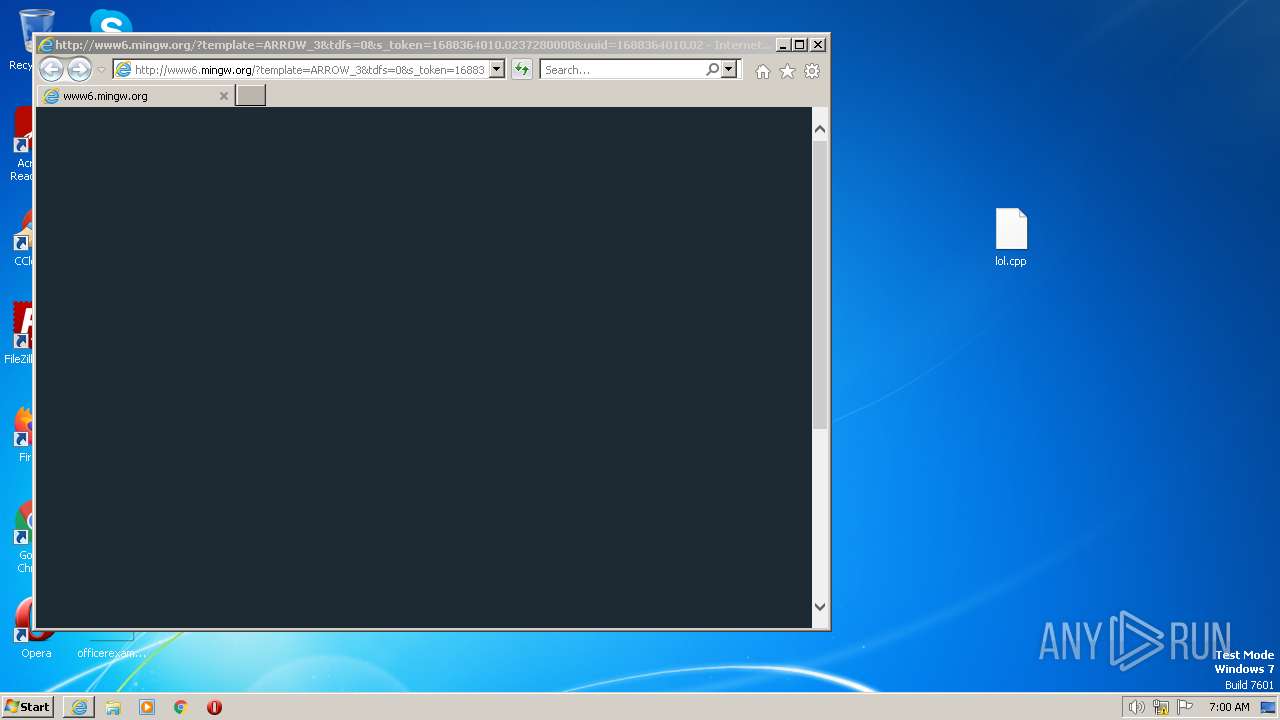
| URL: | https://mingw.org |
| Full analysis: | https://app.any.run/tasks/121f642e-8627-49f4-8c7a-8891cfcbd158 |
| Verdict: | Malicious activity |
| Analysis date: | July 03, 2023, 05:59:35 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 742448B57B0399203E0F618620075E87 |
| SHA1: | BF63FF8773DEE1DEDCF28C7FB170A1FCEC83DA3C |
| SHA256: | D907AAAB185FC0E33ABF25B9FEC899088E254C9B4DFBFF516FBD7AA22962DFA4 |
| SSDEEP: | 3:N8gS:2gS |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
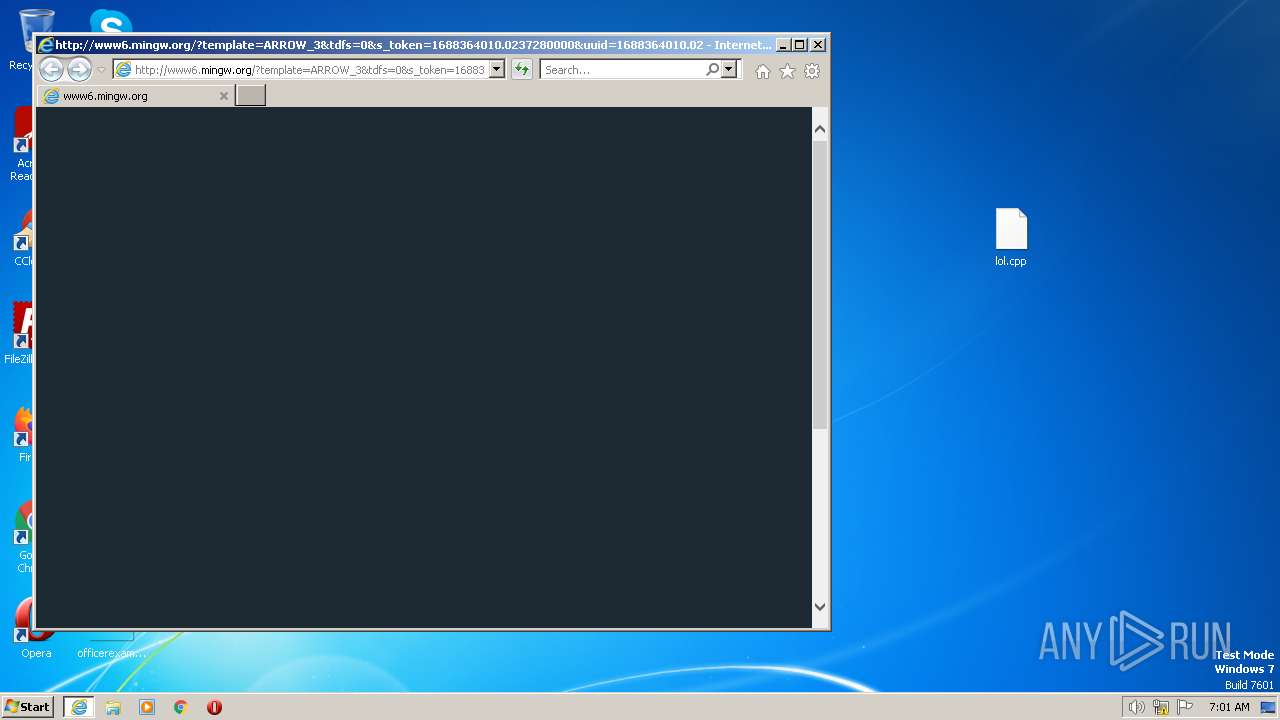
Application launched itself
- iexplore.exe (PID: 3532)
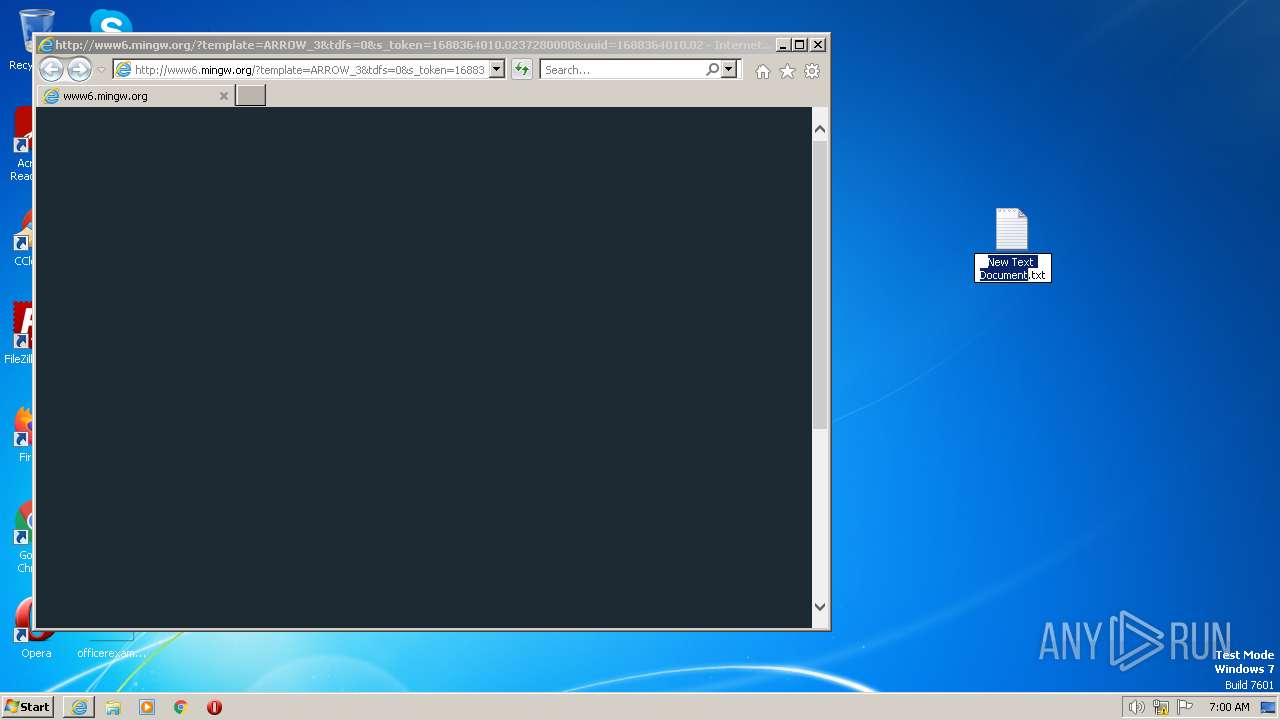
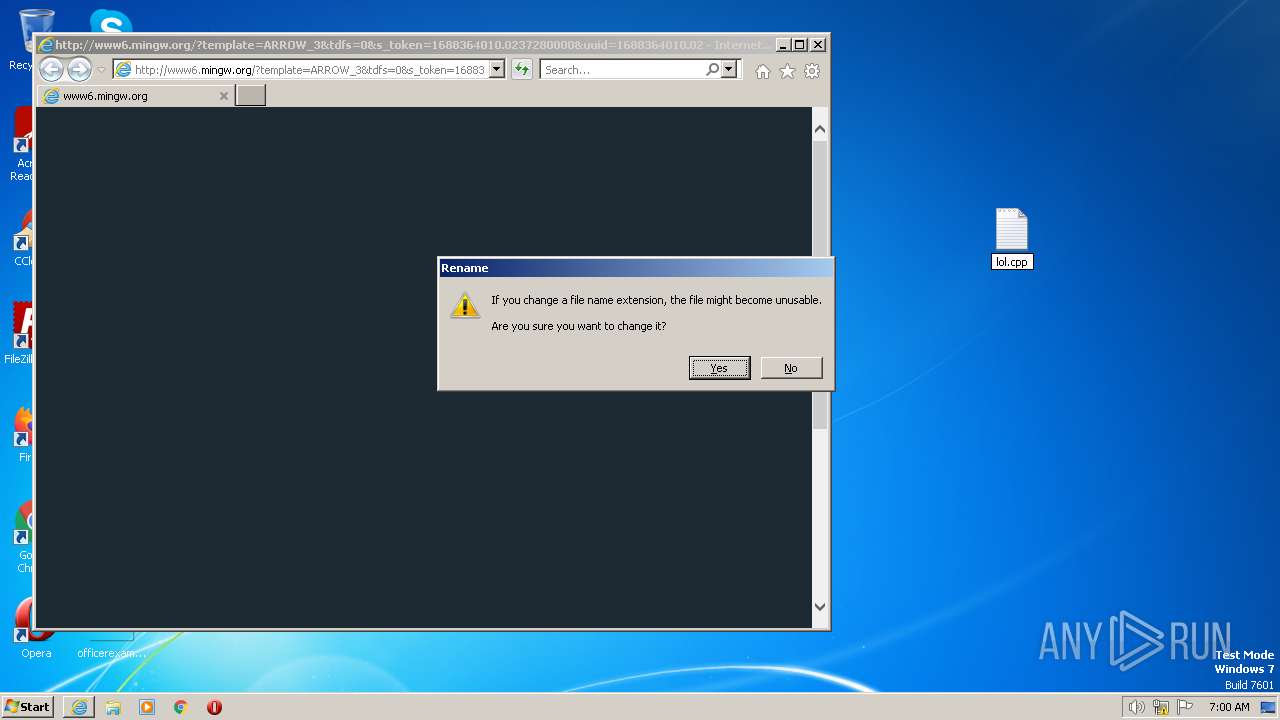
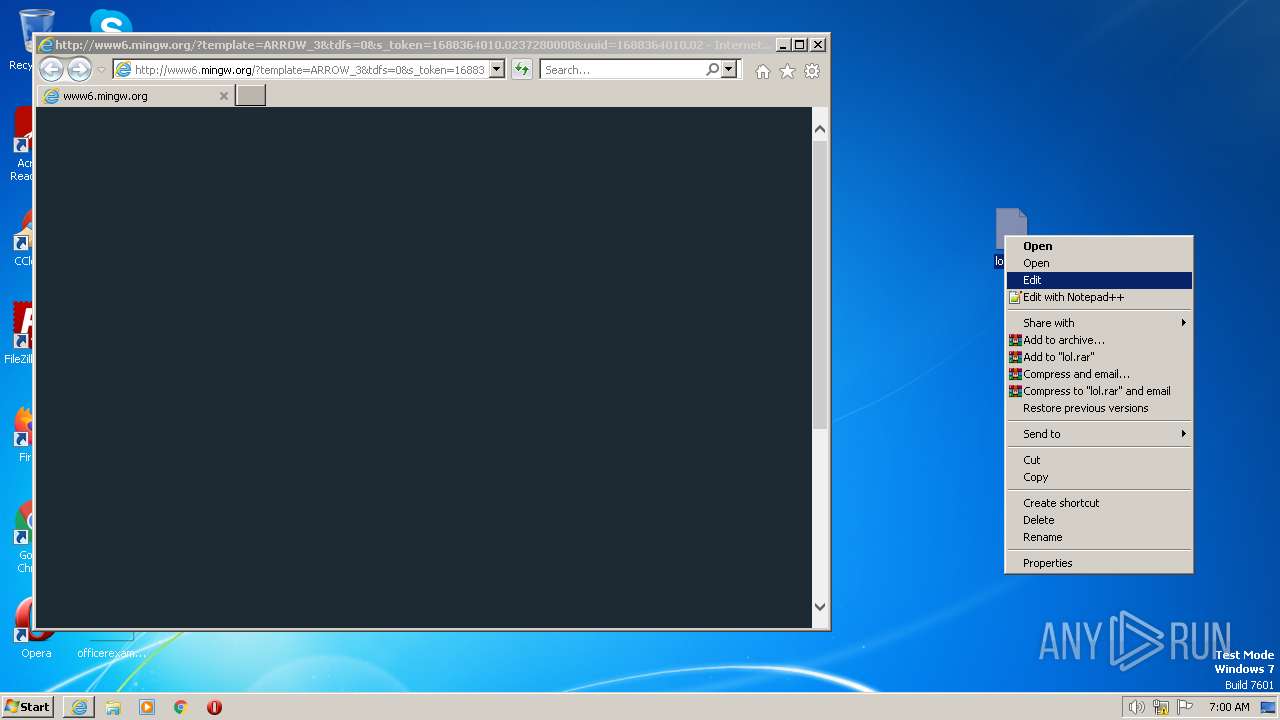
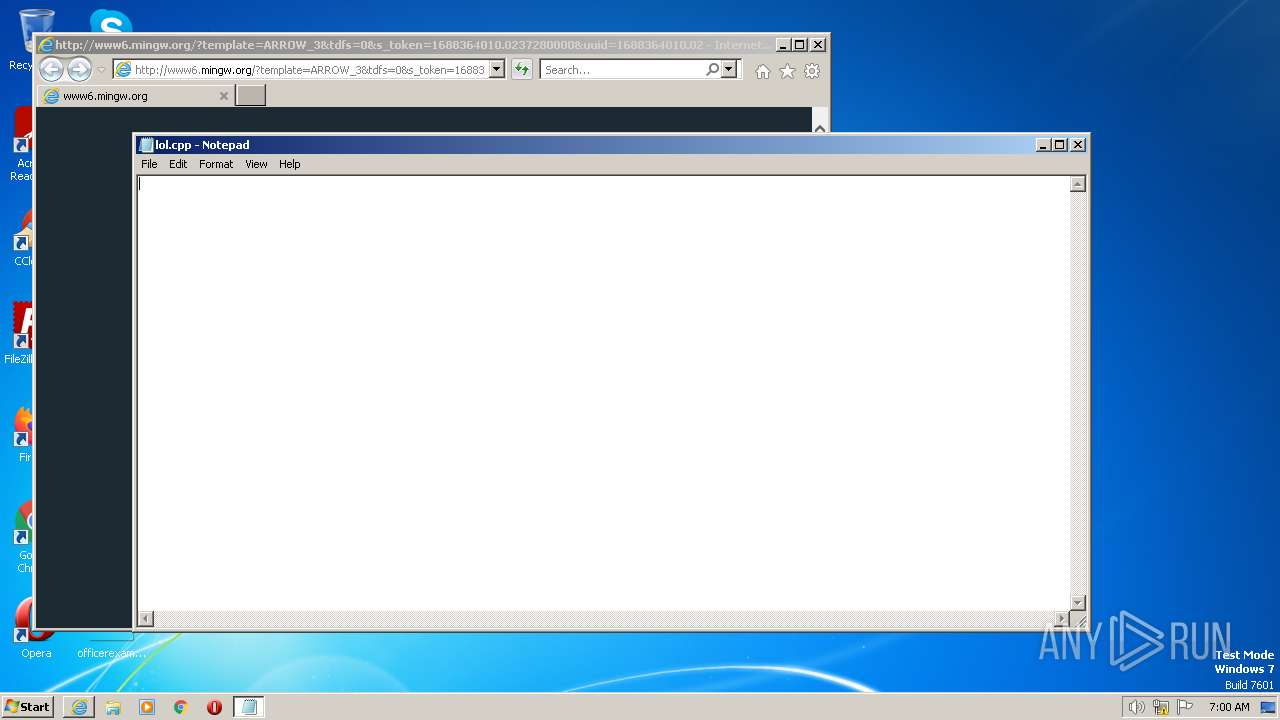
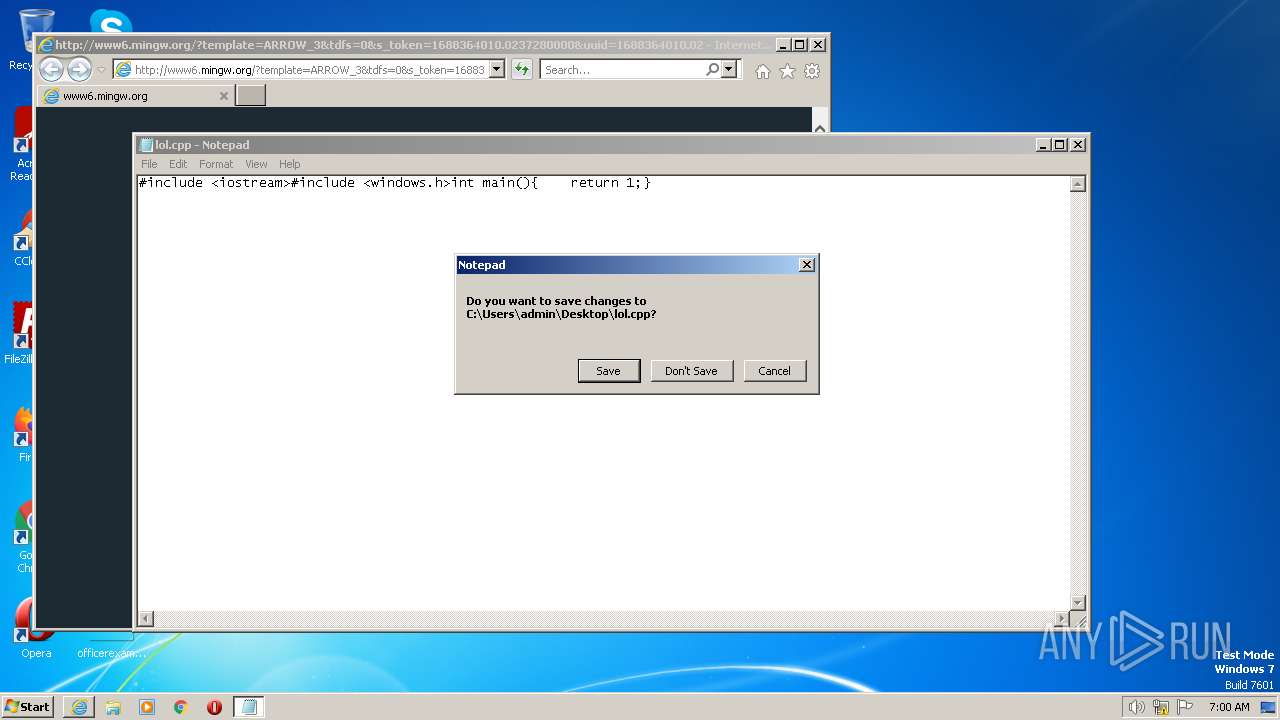
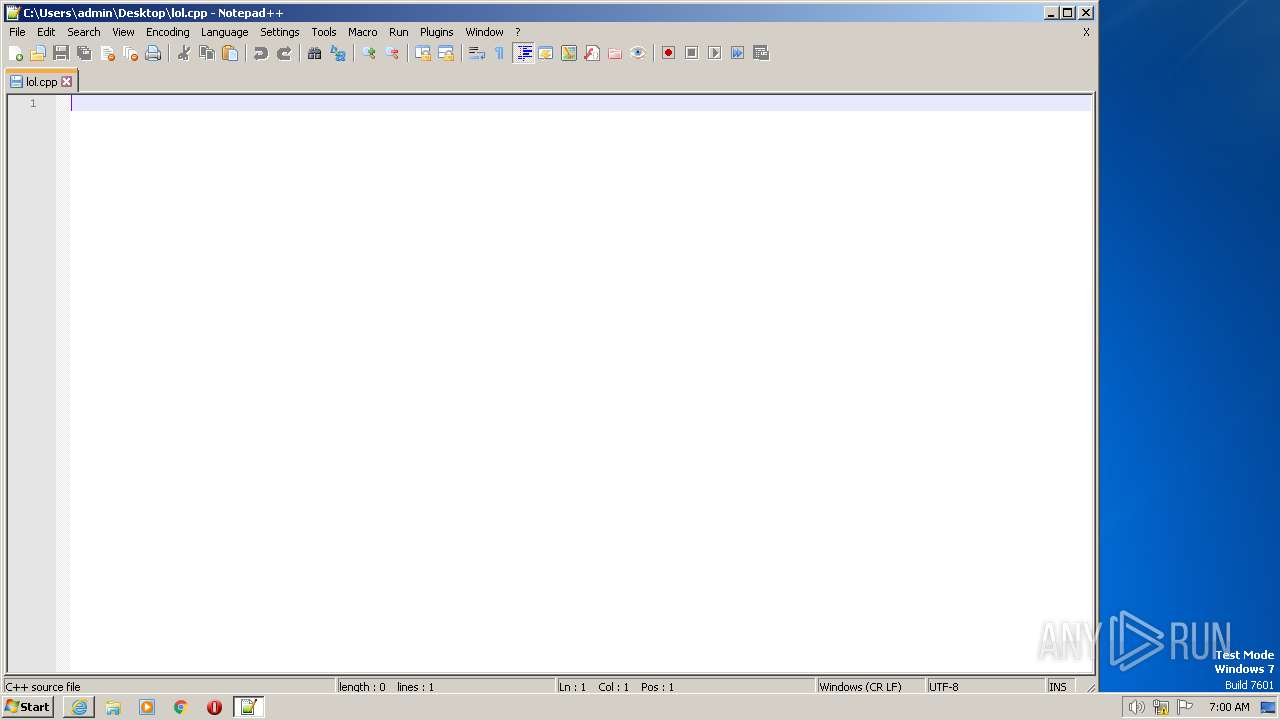
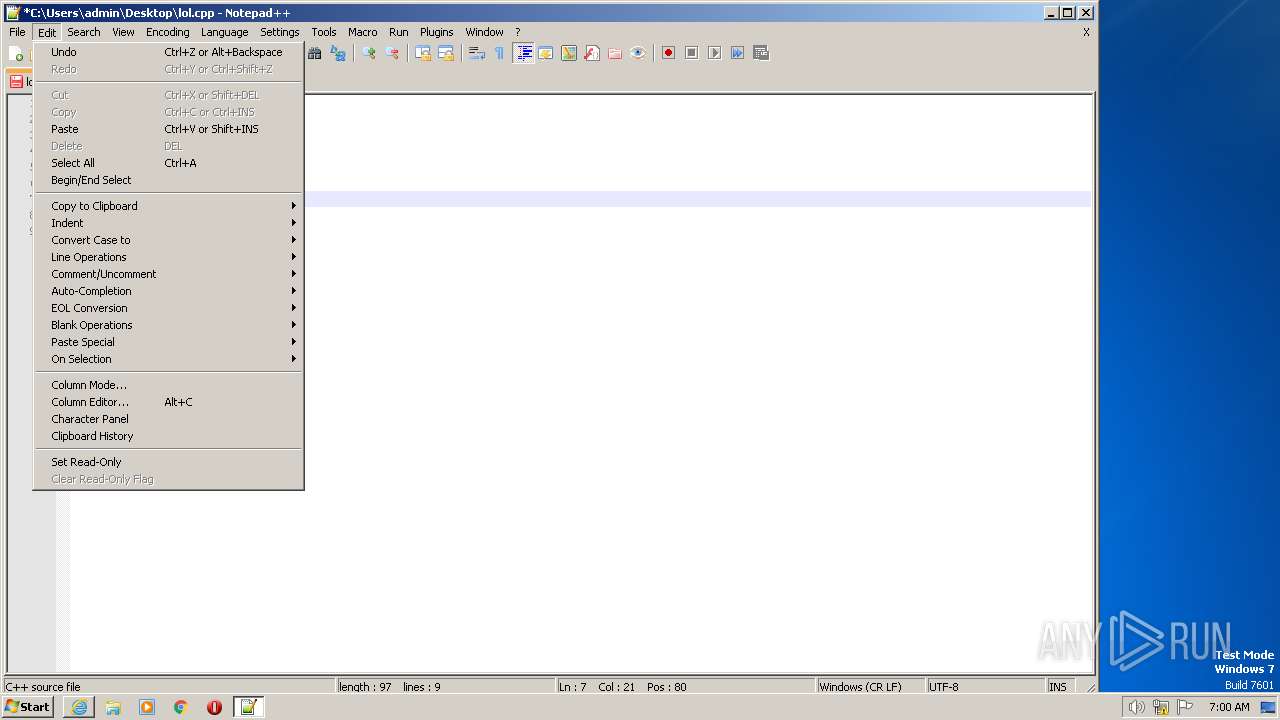
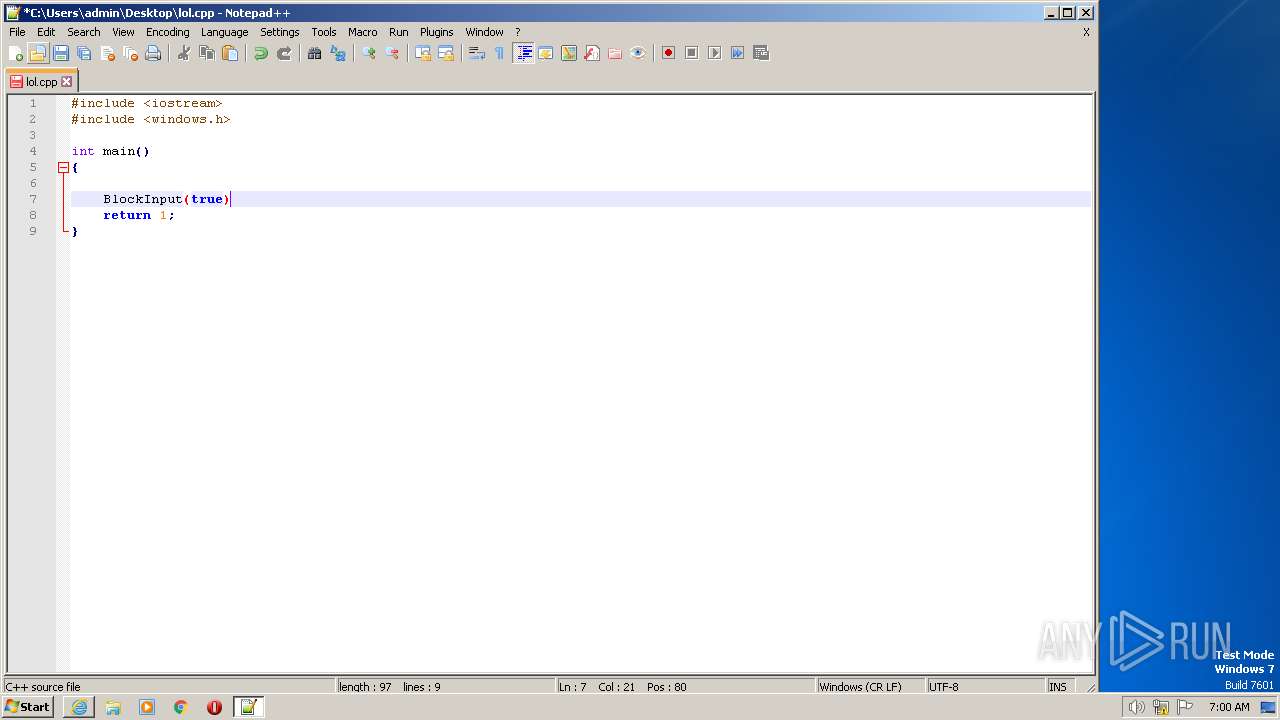
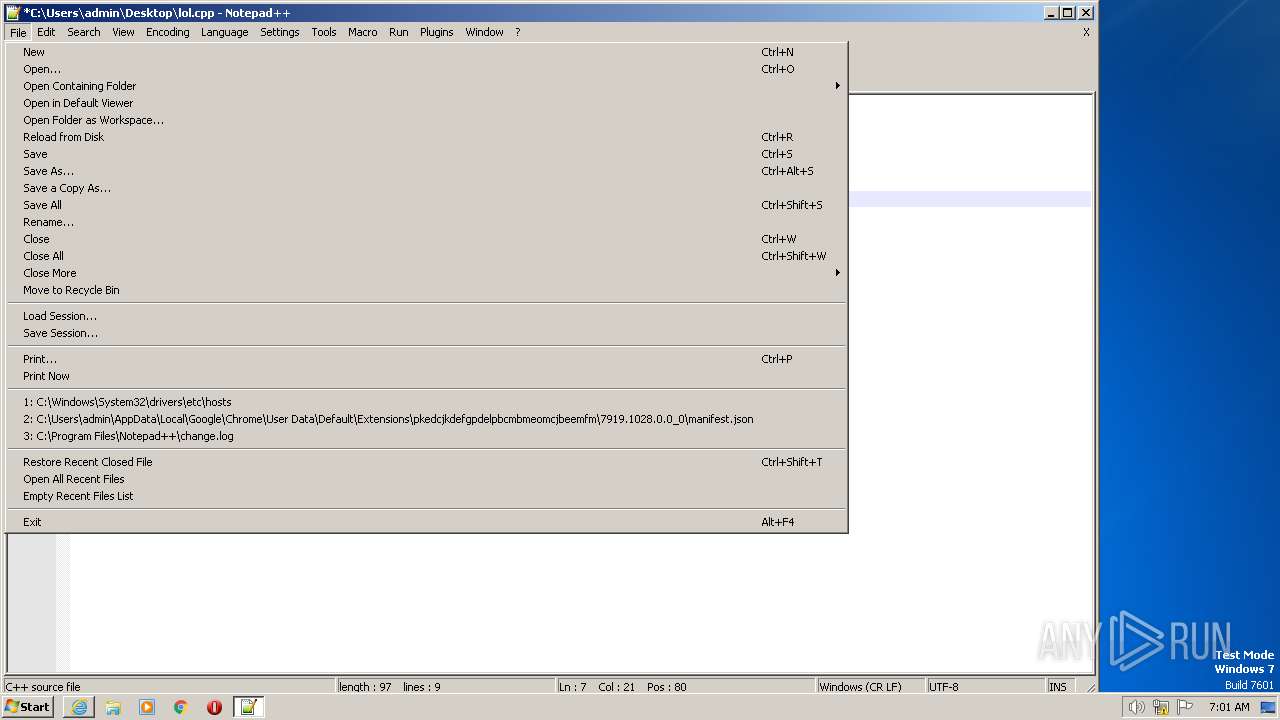
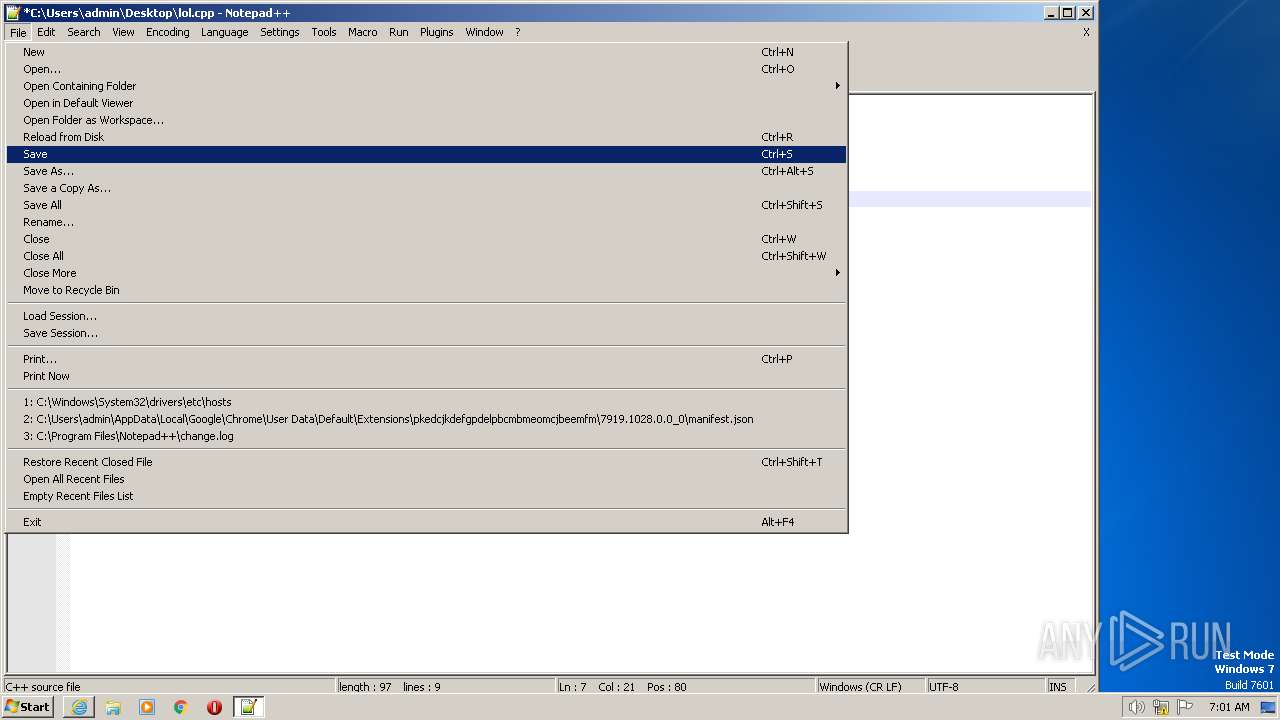
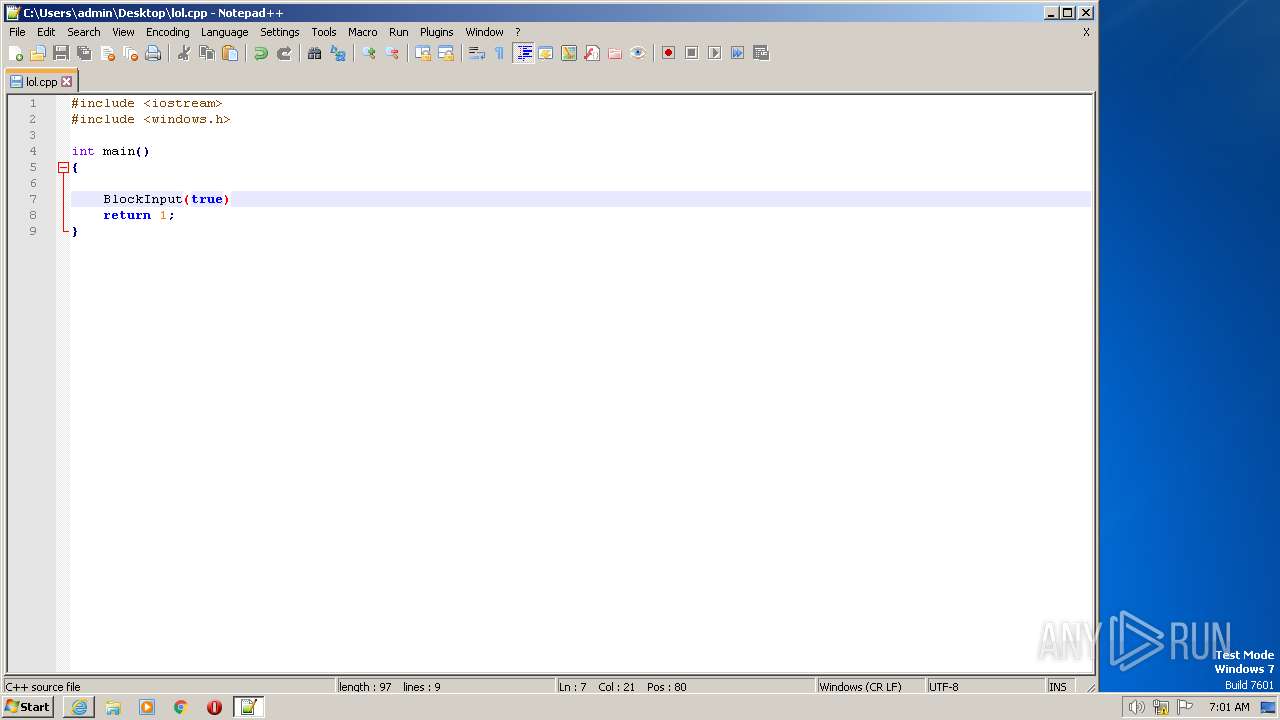
Manual execution by a user
- notepad.exe (PID: 3788)
- notepad++.exe (PID: 2028)
The process checks LSA protection
- notepad++.exe (PID: 2028)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
47
Monitored processes
4
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
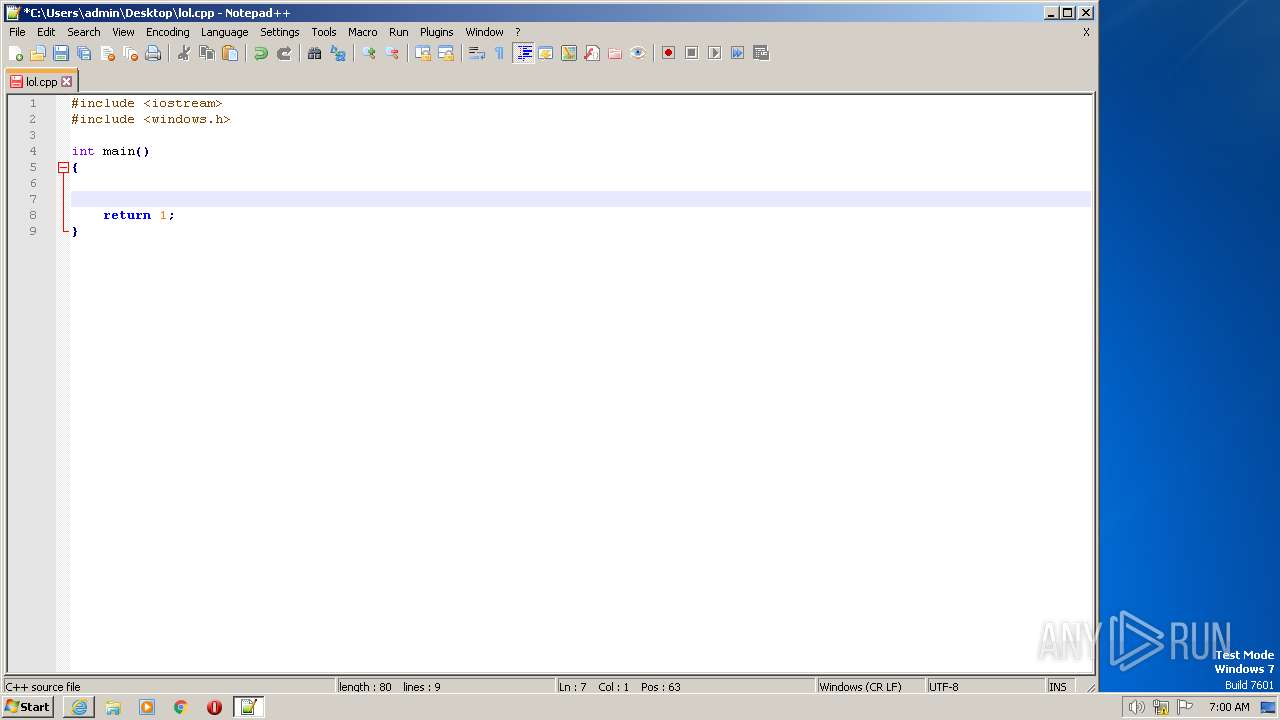
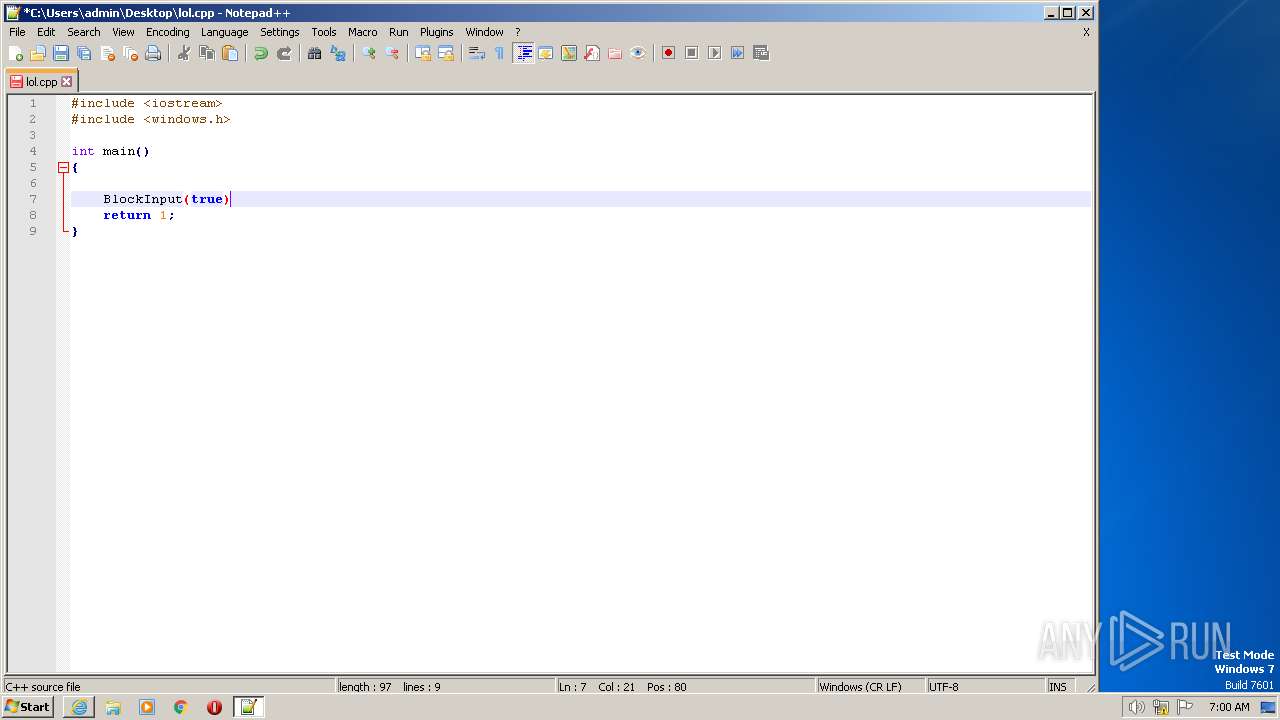
| 2028 | "C:\Program Files\Notepad++\notepad++.exe" "C:\Users\admin\Desktop\lol.cpp" | C:\Program Files\Notepad++\notepad++.exe | explorer.exe | ||||||||||||
User: admin Company: Don HO don.h@free.fr Integrity Level: MEDIUM Description: Notepad++ : a free (GNU) source code editor Exit code: 0 Version: 7.91 Modules
| |||||||||||||||
| 3532 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://mingw.org" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3600 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3532 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3788 | "C:\Windows\system32\NOTEPAD.EXE" C:\Users\admin\Desktop\lol.cpp | C:\Windows\System32\notepad.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
18 307
Read events
18 181
Write events
123
Delete events
3
Modification events
| (PID) Process: | (3532) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 0 | |||
| (PID) Process: | (3532) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30847387 | |||
| (PID) Process: | (3532) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30847437 | |||
| (PID) Process: | (3532) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3532) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3532) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3532) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3532) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3532) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3532) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
Executable files
0
Suspicious files
49
Text files
41
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3532 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | compressed | |
MD5:F7DCB24540769805E5BB30D193944DCE | SHA256:6B88C6AC55BBD6FEA0EBE5A760D1AD2CFCE251C59D0151A1400701CB927E36EA | |||
| 3600 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\77EC63BDA74BD0D0E0426DC8F8008506 | compressed | |
MD5:3AC860860707BAAF32469FA7CC7C0192 | SHA256:D015145D551ECD14916270EFAD773BBC9FD57FAD2228D2C24559F696C961D904 | |||
| 3532 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\82CB34DD3343FE727DF8890D352E0D8F | binary | |
MD5:A786D98FAC4B086CAED1B90BE7B958B2 | SHA256:50ABE1A73EE4A6792000A26DF70537B6D4A65ADA015856C2DED0F54DC9AF1675 | |||
| 3532 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\PO2HN1X2\favicon[1].ico | image | |
MD5:DA597791BE3B6E732F0BC8B20E38EE62 | SHA256:5B2C34B3C4E8DD898B664DBA6C3786E2FF9869EFF55D673AA48361F11325ED07 | |||
| 3600 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\77EC63BDA74BD0D0E0426DC8F8008506 | binary | |
MD5:130A39A94641A6EC270713D12EB05CC1 | SHA256:E47809693B7B00E4F90D09D2883554E5727981E0223E12268F5CE3456168EA28 | |||
| 3600 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\CabF99F.tmp | compressed | |
MD5:3AC860860707BAAF32469FA7CC7C0192 | SHA256:D015145D551ECD14916270EFAD773BBC9FD57FAD2228D2C24559F696C961D904 | |||
| 3532 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:1ADE04204960DA6E7FBD5FFA890F66BB | SHA256:BA4B02FFF7B7E1D8AD8B8AD4E7A06DB9D94EA4E5135D13B064EFC69CBE63C51C | |||
| 3532 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | image | |
MD5:DA597791BE3B6E732F0BC8B20E38EE62 | SHA256:5B2C34B3C4E8DD898B664DBA6C3786E2FF9869EFF55D673AA48361F11325ED07 | |||
| 3600 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\1D5A8F38B7D9520646A6864F3EEEB234 | binary | |
MD5:43FEE4056C38C998669E95BB4E5A08BC | SHA256:3DC14C5562A9E678915570F7C08D4C0563E98901B554722FCB732CFF38D3C7F7 | |||
| 3600 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\px[1].js | text | |
MD5:D2183968F9080B37BABFEBA3CCF10DF2 | SHA256:4D9B83714539F82372E1E0177924BCB5180B75148E22D6725468FD2FB6F96BCC | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
22
TCP/UDP connections
47
DNS requests
25
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3600 | iexplore.exe | GET | 302 | 96.126.123.244:80 | http://mingw.org/?gp=1&js=1&uuid=1688364009.0066357014&other_args=eyJ1cmkiOiAiLyIsICJhcmdzIjogIiIsICJyZWZlcmVyIjogIiIsICJhY2NlcHQiOiAidGV4dC9odG1sLCBhcHBsaWNhdGlvbi94aHRtbCt4bWwsICovKiJ9 | US | — | — | whitelisted |
3600 | iexplore.exe | GET | 200 | 96.126.123.244:80 | http://mingw.org/ | US | compressed | 483 b | whitelisted |
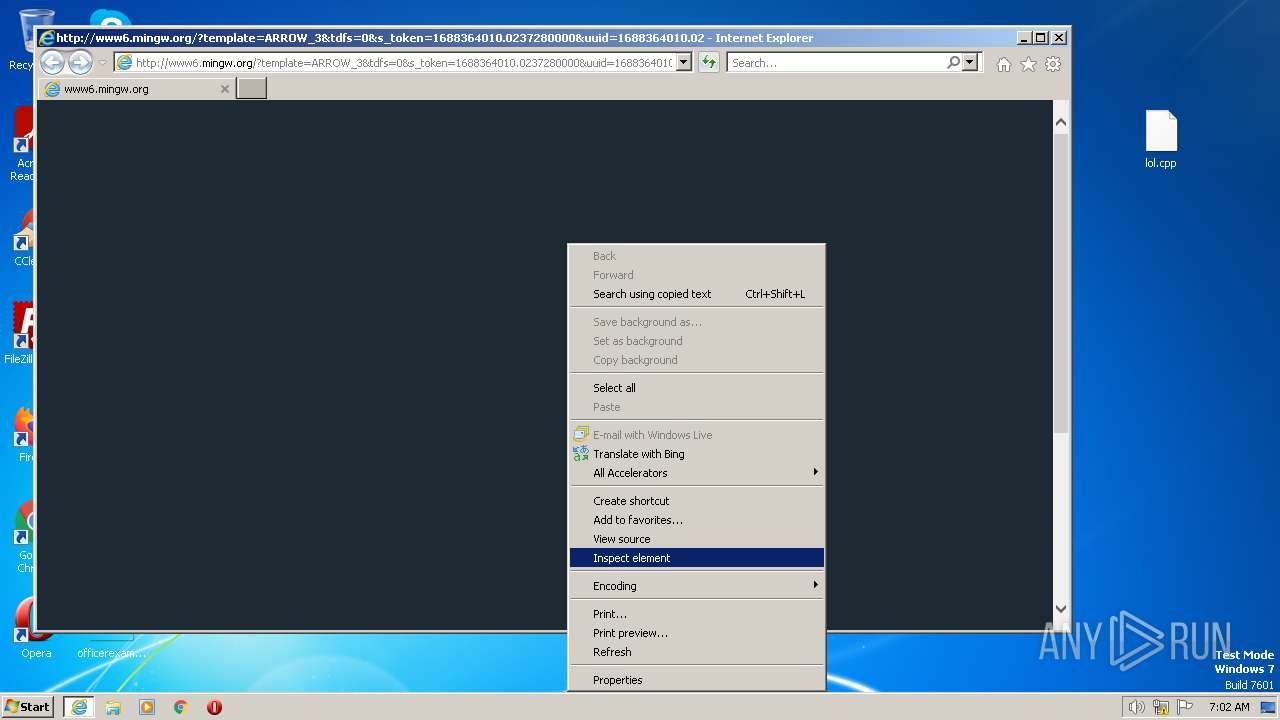
3600 | iexplore.exe | GET | 200 | 35.186.238.101:80 | http://www6.mingw.org/?template=ARROW_3&tdfs=0&s_token=1688364010.0237280000&uuid=1688364010.0237280000&term=GCC%20Compiler&term=C%20Language%20Compiler&term=Test%20Code%20Online&searchbox=0&showDomain=0&backfill=0 | US | html | 2.76 Kb | whitelisted |
3600 | iexplore.exe | GET | 200 | 192.124.249.36:80 | http://ocsp.godaddy.com//MEowSDBGMEQwQjAJBgUrDgMCGgUABBS2CA1fbGt26xPkOKX4ZguoUjM0TgQUQMK9J47MNIMwojPX%2B2yz8LQsgM4CCQCYI13lSyP8mw%3D%3D | US | binary | 2.06 Kb | whitelisted |
3600 | iexplore.exe | GET | 200 | 142.250.185.67:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQCk5jlVaBWoDgp0KKGknUTO | US | binary | 472 b | whitelisted |
3600 | iexplore.exe | GET | 200 | 35.186.238.101:80 | http://www6.mingw.org/px.js?ch=2&abp=1 | US | text | 476 b | whitelisted |
3600 | iexplore.exe | GET | 200 | 142.250.185.67:80 | http://ocsp.pki.goog/gsr1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCEHe9DWzbNvka6iEPxPBY0w0%3D | US | binary | 1.41 Kb | whitelisted |
3600 | iexplore.exe | GET | 200 | 35.186.238.101:80 | http://www6.mingw.org/px.js?ch=1&abp=1 | US | text | 476 b | whitelisted |
3600 | iexplore.exe | GET | 200 | 192.124.249.41:80 | http://ocsp.starfieldtech.com//MEIwQDA%2BMDwwOjAJBgUrDgMCGgUABBQUwPiEZQ6%2FsVZNPaFToNfxx8ZwqAQUfAwyH6fZMH%2FEfWijYqihzqsHWycCAQc%3D | US | binary | 2.05 Kb | whitelisted |
3532 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | binary | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3600 | iexplore.exe | 72.14.178.174:443 | mingw.org | Linode, LLC | US | malicious |
2744 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
3532 | iexplore.exe | 104.126.37.131:443 | www.bing.com | Akamai International B.V. | DE | suspicious |
3532 | iexplore.exe | 93.184.221.240:80 | ctldl.windowsupdate.com | EDGECAST | GB | whitelisted |
3600 | iexplore.exe | 93.184.221.240:80 | ctldl.windowsupdate.com | EDGECAST | GB | whitelisted |
3600 | iexplore.exe | 23.56.202.135:80 | x1.c.lencr.org | AKAMAI-AS | GB | suspicious |
3532 | iexplore.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
3600 | iexplore.exe | 96.126.123.244:443 | mingw.org | Linode, LLC | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
mingw.org |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
x1.c.lencr.org |
| whitelisted |
crl3.digicert.com |
| whitelisted |
r3.o.lencr.org |
| shared |
www6.mingw.org |
| whitelisted |
www.google.com |
| malicious |
Threats
Process | Message |
|---|---|
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\SciLexer.dll
|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | ED255D9151912E40DF048A56288E969A8D0DAFA3
|
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\updater\gup.exe
|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | ED255D9151912E40DF048A56288E969A8D0DAFA3
|
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\plugins\Config\nppPluginList.dll
|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | ED255D9151912E40DF048A56288E969A8D0DAFA3
|
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\updater\gup.exe
|