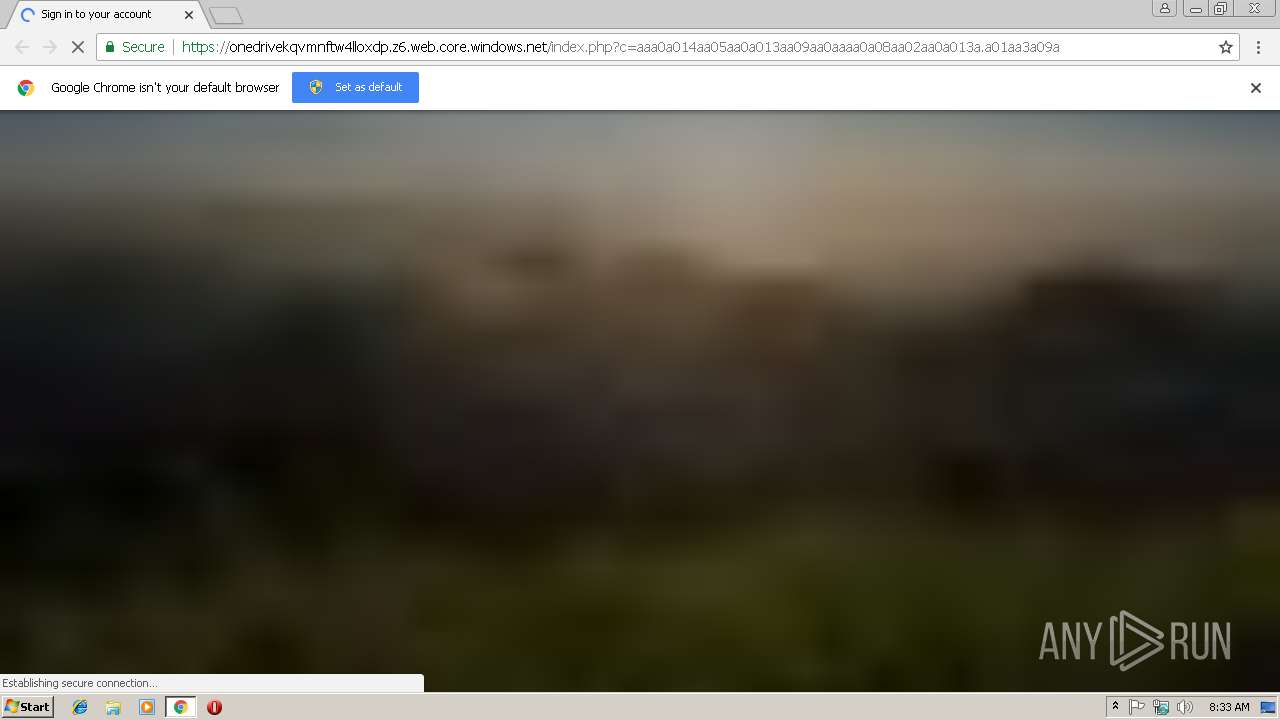
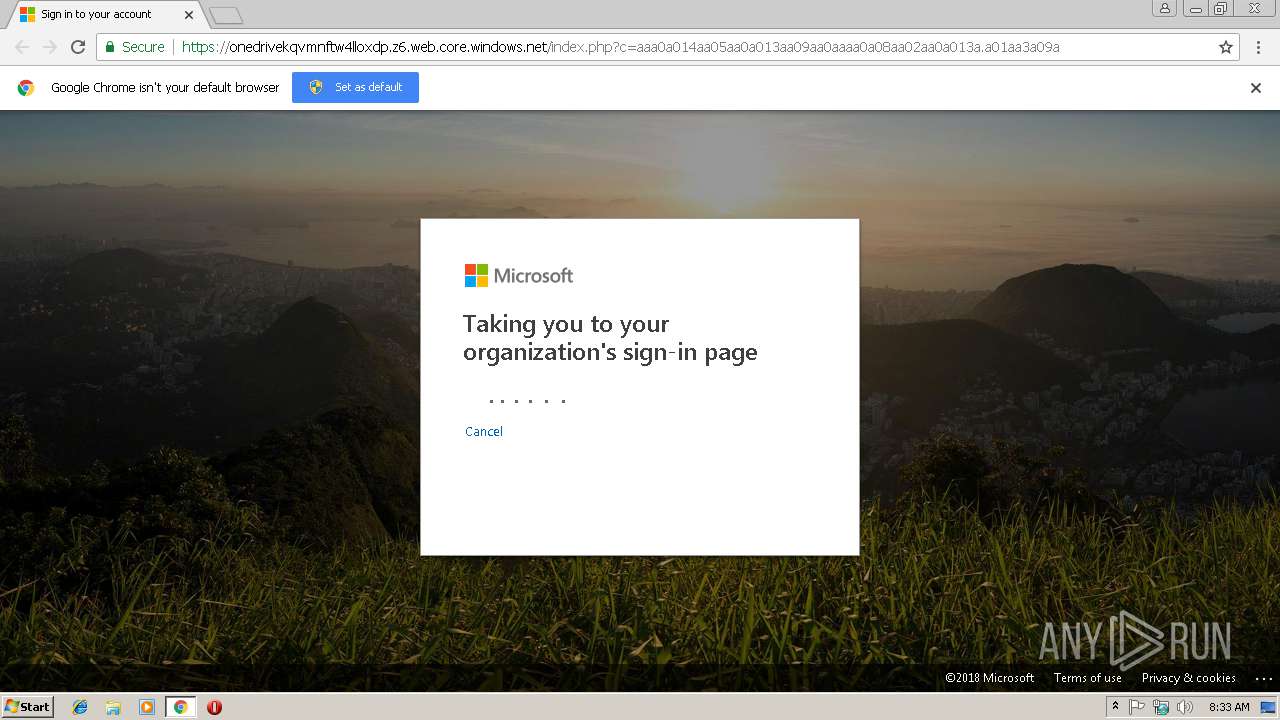
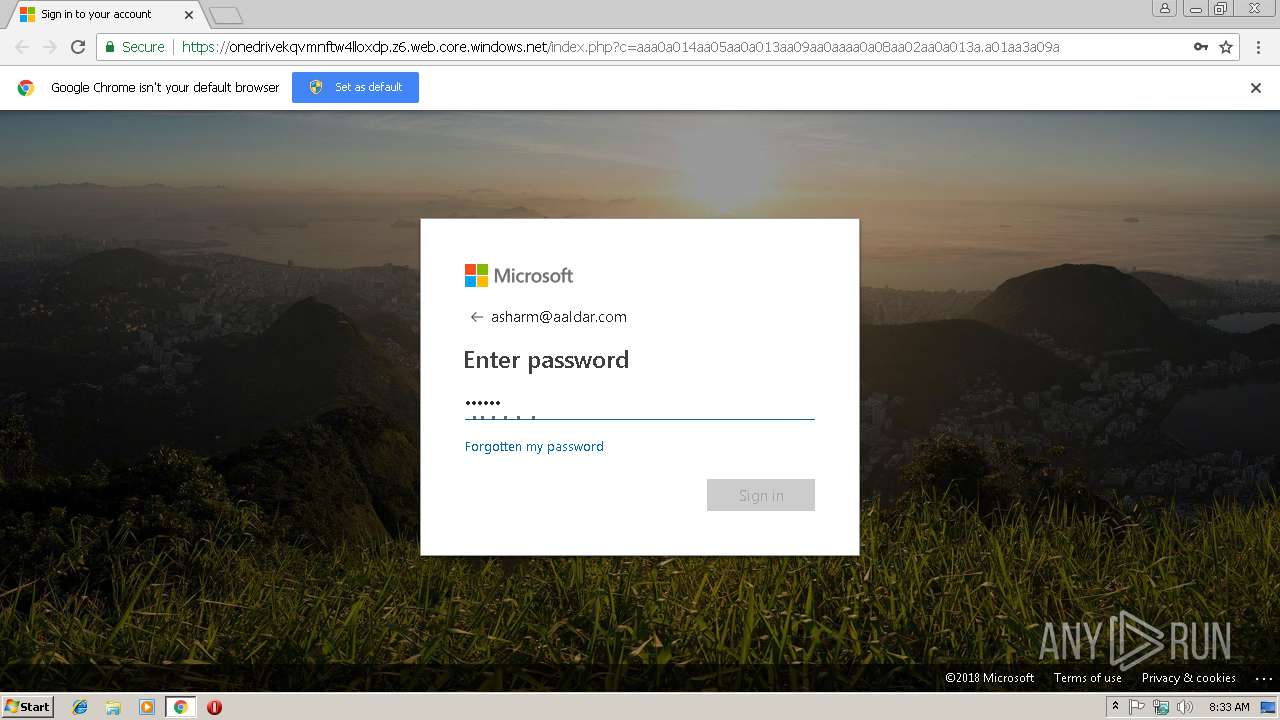
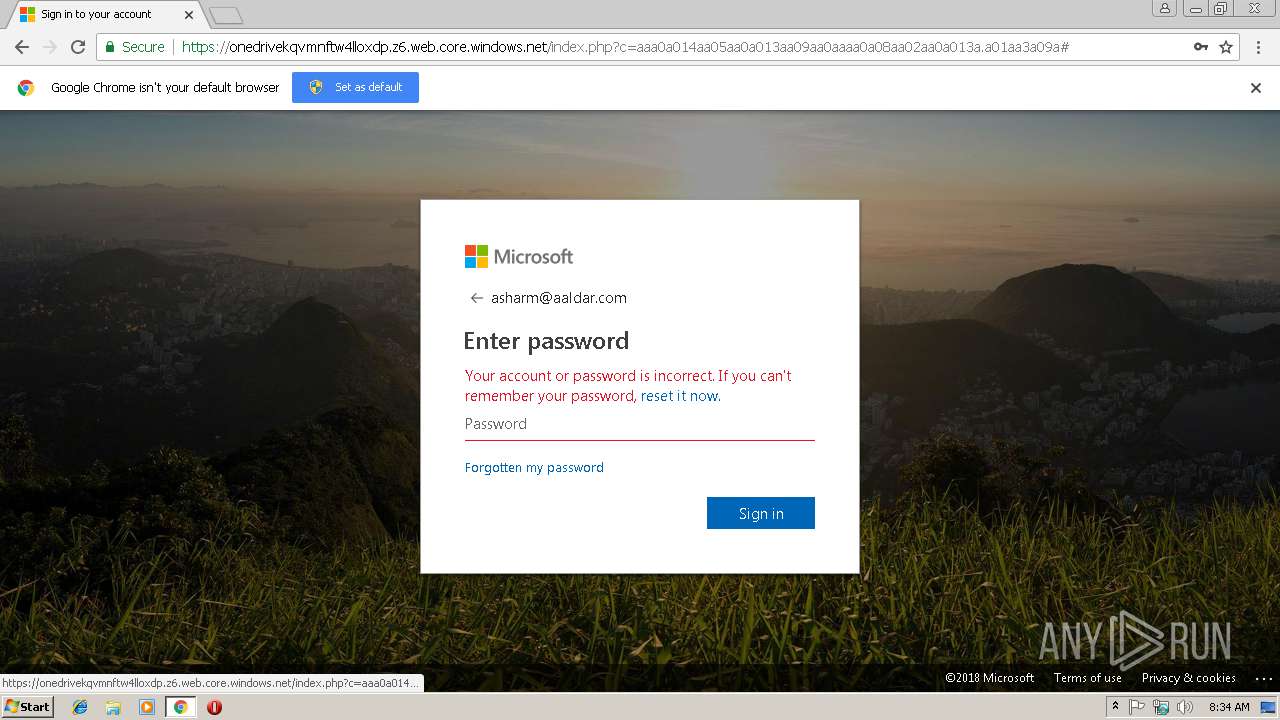
| URL: | https://onedrivekqvmnftw4lloxdp.z6.web.core.windows.net/index.php?c=aaa0a014aa05aa0a013aa09aa0aaaa0a08aa02aa0a013a.a01aa3a09a |
| Full analysis: | https://app.any.run/tasks/a760c84f-4a75-4161-a20d-8c423c3b32aa |
| Verdict: | Malicious activity |
| Analysis date: | February 11, 2019, 08:33:24 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 1B9535FAADC076E7CE436DA84AB1030F |
| SHA1: | 10B66B23AA84F7216383B7DF02AA48B28B598BE0 |
| SHA256: | D906F1505461EA48BE4A746C0C539F36B8B856B5080F64F3793C120DFA9F2601 |
| SSDEEP: | 3:N8Ckyj0sJrSuNfbHNp8EEuV/6pFEmEfVtWW:2Ckyj0sJGutHf8EEaC3Ir |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Application launched itself
- chrome.exe (PID: 2764)
Reads settings of System Certificates
- chrome.exe (PID: 2764)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
36
Monitored processes
8
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2312 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=900,1112433181398300262,13346142530850764726,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=A2DE9FDFBC4A13AF0506AE06DD2EE8B2 --mojo-platform-channel-handle=2284 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2388 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=900,1112433181398300262,13346142530850764726,131072 --enable-features=PasswordImport --disable-gpu-sandbox --gpu-preferences=KAAAAAAAAACAAwBAAQAAAAAAAAAAAGAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAKAAAAEAAAAAAAAAAAAAAACwAAABAAAAAAAAAAAQAAAAoAAAAQAAAAAAAAAAEAAAALAAAA --service-request-channel-token=D3D77D41D600A56240CB5AC749484E6D --mojo-platform-channel-handle=3468 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2584 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=900,1112433181398300262,13346142530850764726,131072 --enable-features=PasswordImport --service-pipe-token=587870EDE714DF2DF9DDF8B0C0206D68 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=587870EDE714DF2DF9DDF8B0C0206D68 --renderer-client-id=4 --mojo-platform-channel-handle=1884 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2764 | "C:\Program Files\Google\Chrome\Application\chrome.exe" https://onedrivekqvmnftw4lloxdp.z6.web.core.windows.net/index.php?c=aaa0a014aa05aa0a013aa09aa0aaaa0a08aa02aa0a013a.a01aa3a09a | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2856 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2768 --on-initialized-event-handle=304 --parent-handle=308 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3260 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=900,1112433181398300262,13346142530850764726,131072 --enable-features=PasswordImport --service-pipe-token=4403F15F4451589A1FF7394D871C375F --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=4403F15F4451589A1FF7394D871C375F --renderer-client-id=3 --mojo-platform-channel-handle=1532 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3612 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=68.0.3440.106 --initial-client-data=0x78,0x7c,0x80,0x74,0x84,0x6f5300b0,0x6f5300c0,0x6f5300cc | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 4016 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=900,1112433181398300262,13346142530850764726,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAACAAwBAAQAAAAAAAAAAAGAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAKAAAAEAAAAAAAAAAAAAAACwAAABAAAAAAAAAAAQAAAAoAAAAQAAAAAAAAAAEAAAALAAAA --service-request-channel-token=33FF2C0AC3CCF2B4F5A9F9DE1C426F58 --mojo-platform-channel-handle=920 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
Total events
500
Read events
456
Write events
41
Delete events
3
Modification events
| (PID) Process: | (2764) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2764) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2764) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2856) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2764-13194347625916000 |
Value: 259 | |||
| (PID) Process: | (2764) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2764) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2764) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3516-13180984670829101 |
Value: 0 | |||
| (PID) Process: | (2764) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (2764) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 2764-13194347625916000 |
Value: 259 | |||
| (PID) Process: | (2764) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
Executable files
0
Suspicious files
7
Text files
49
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2764 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Download Service\EntryDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2764 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\17bc742d-4b1a-414b-b45e-bd4121cf4493.tmp | — | |
MD5:— | SHA256:— | |||
| 2764 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Download Service\EntryDB\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2764 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2764 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\0fe960df-6ef9-4b25-b05c-6e5176b64c6d.tmp | — | |
MD5:— | SHA256:— | |||
| 2764 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:— | SHA256:— | |||
| 2764 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF198c0a.TMP | text | |
MD5:— | SHA256:— | |||
| 2764 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2764 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2764 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Thumbnails\LOG.old | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
9
DNS requests
7
Threats
3
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2764 | chrome.exe | 216.58.208.35:443 | www.gstatic.com | Google Inc. | US | whitelisted |
2764 | chrome.exe | 216.58.206.3:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
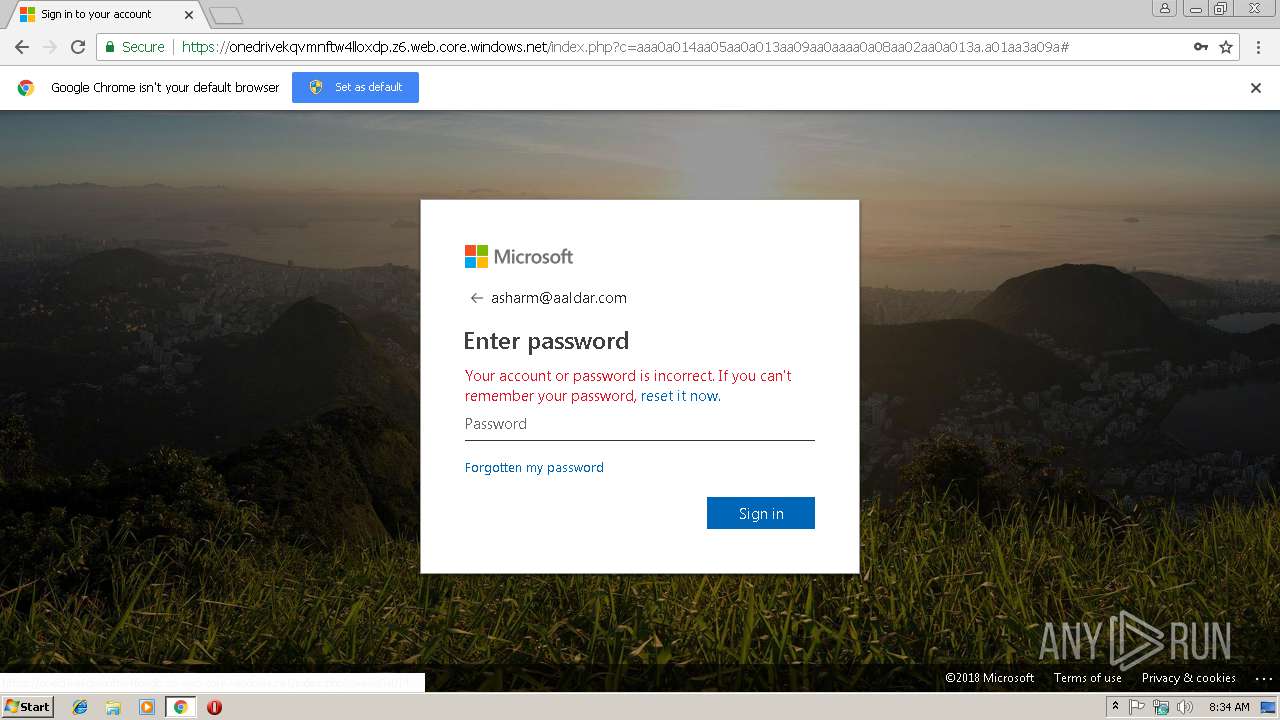
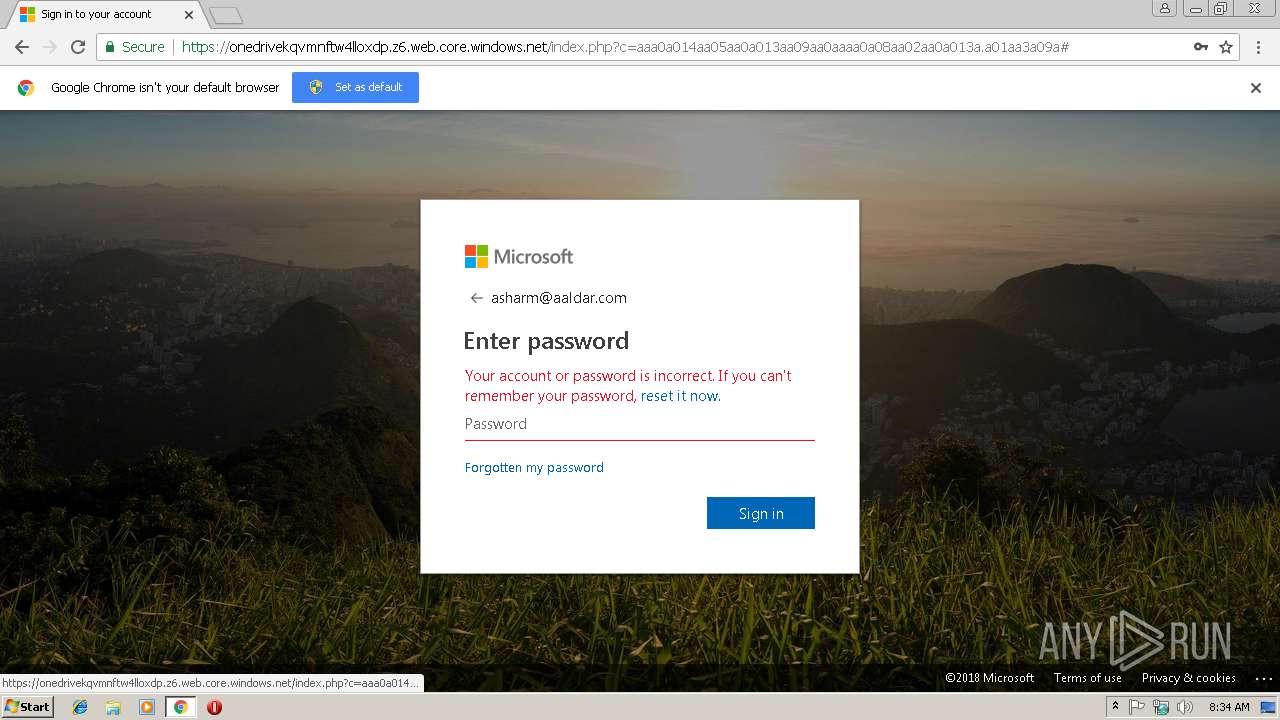
2764 | chrome.exe | 52.174.224.17:443 | onedrivekqvmnftw4lloxdp.z6.web.core.windows.net | Microsoft Corporation | NL | suspicious |
2764 | chrome.exe | 172.217.22.13:443 | accounts.google.com | Google Inc. | US | whitelisted |
2764 | chrome.exe | 172.217.23.131:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
2764 | chrome.exe | 104.27.141.20:443 | authconfig.credlt-suisse.com | Cloudflare Inc | US | shared |
2764 | chrome.exe | 205.185.208.52:443 | code.jquery.com | Highwinds Network Group, Inc. | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
onedrivekqvmnftw4lloxdp.z6.web.core.windows.net |
| unknown |
accounts.google.com |
| shared |
code.jquery.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
authconfig.credlt-suisse.com |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
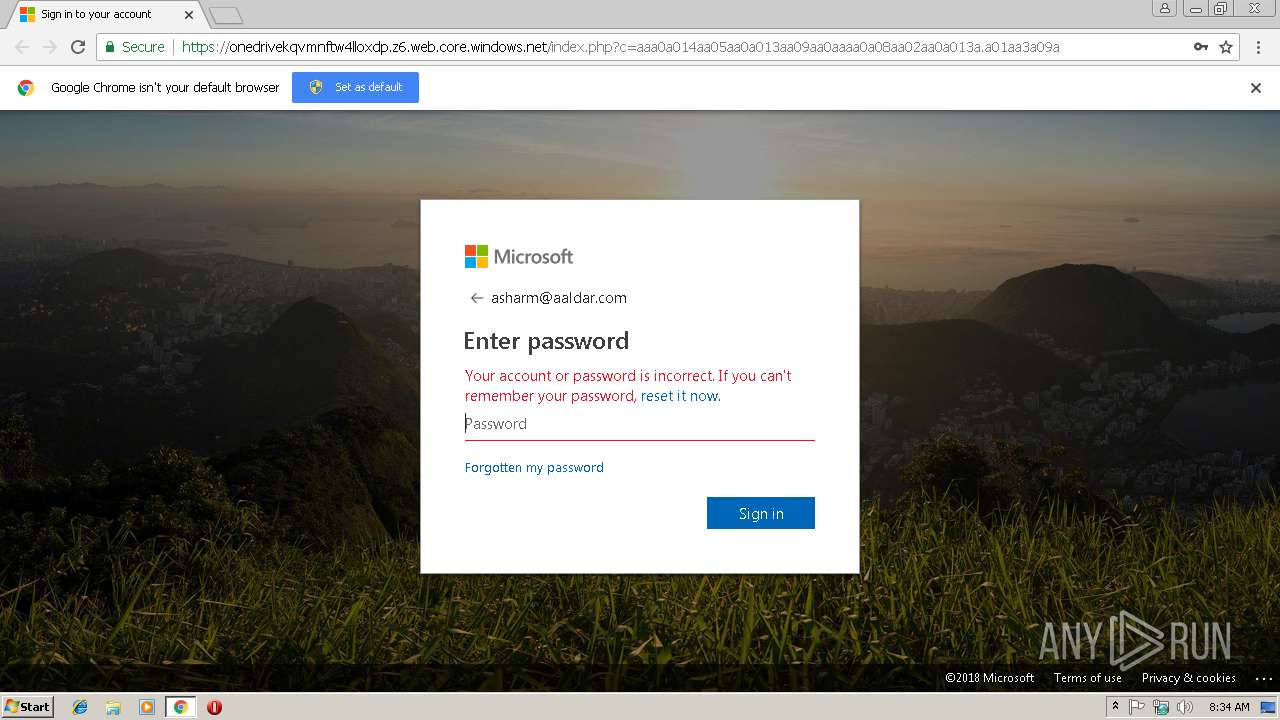
1056 | svchost.exe | Potential Corporate Privacy Violation | ET POLICY DNS Lookup for Possible Common Brand Phishing Hosted on Legitimate Windows Service |
2764 | chrome.exe | Potential Corporate Privacy Violation | ET POLICY Request for Possible Common Brand Phishing Hosted on Legitimate Windows Service |
2764 | chrome.exe | Potential Corporate Privacy Violation | ET POLICY Request for Possible Common Brand Phishing Hosted on Legitimate Windows Service |