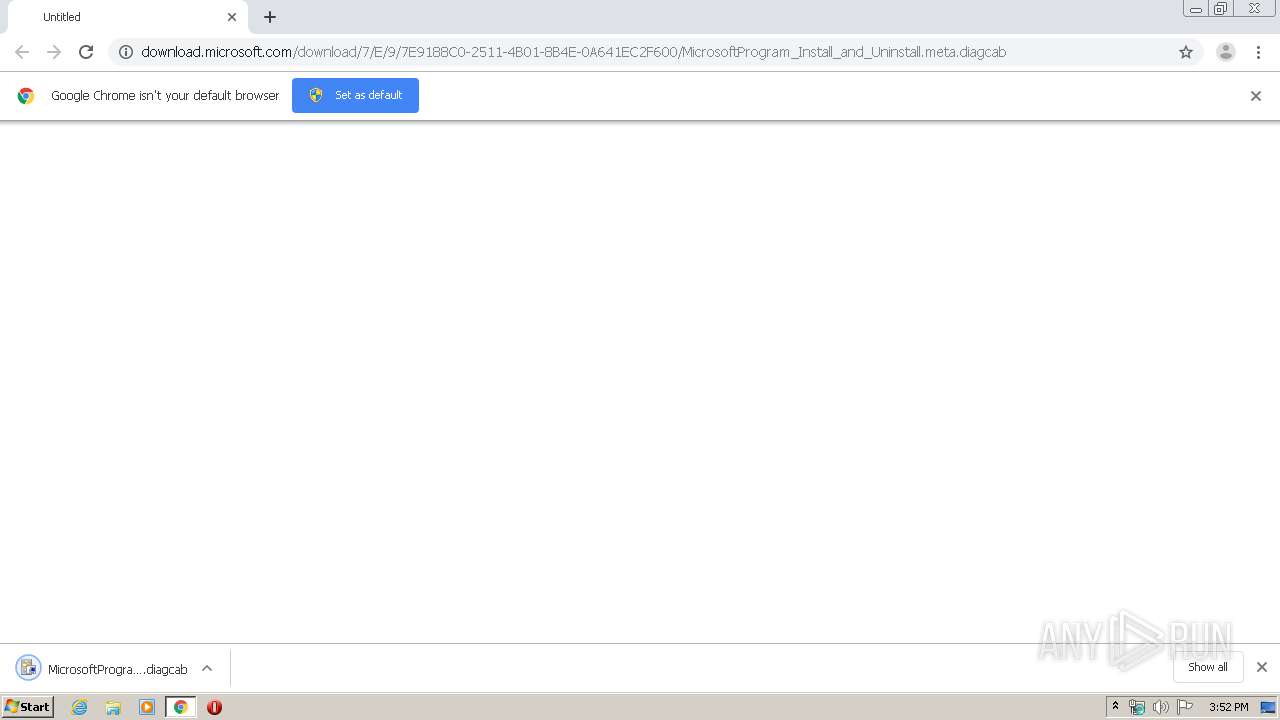
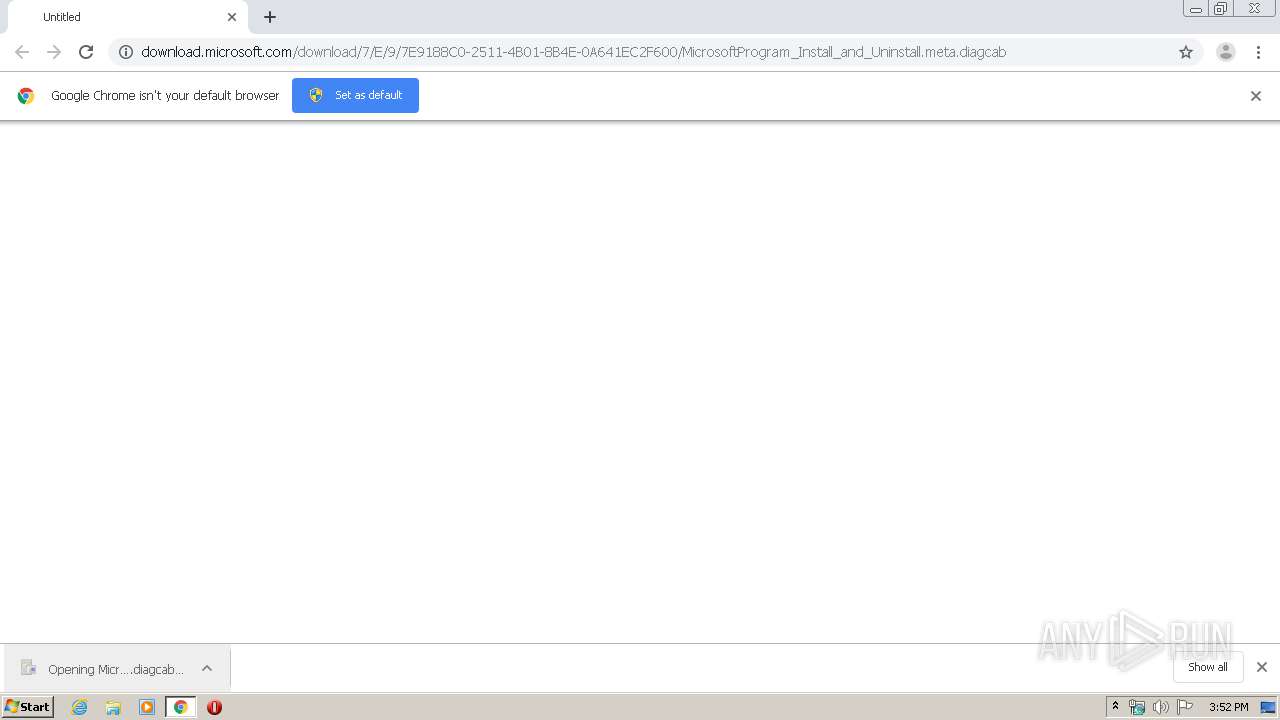
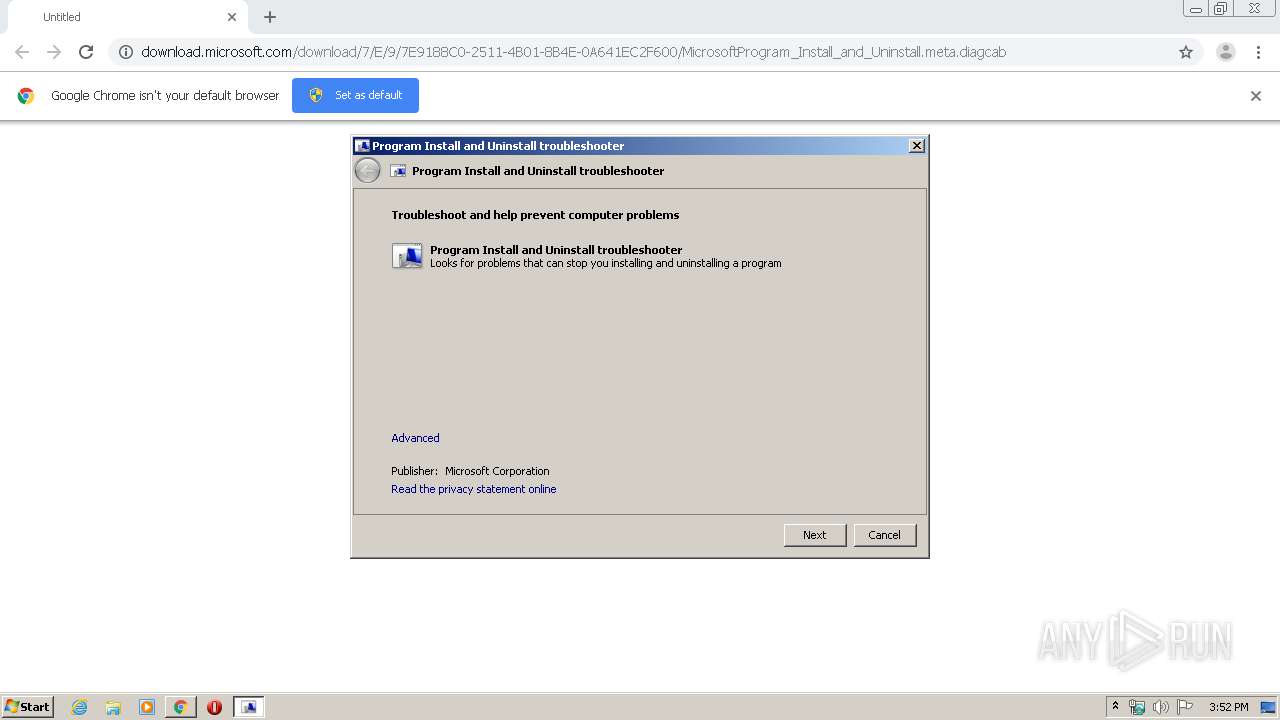
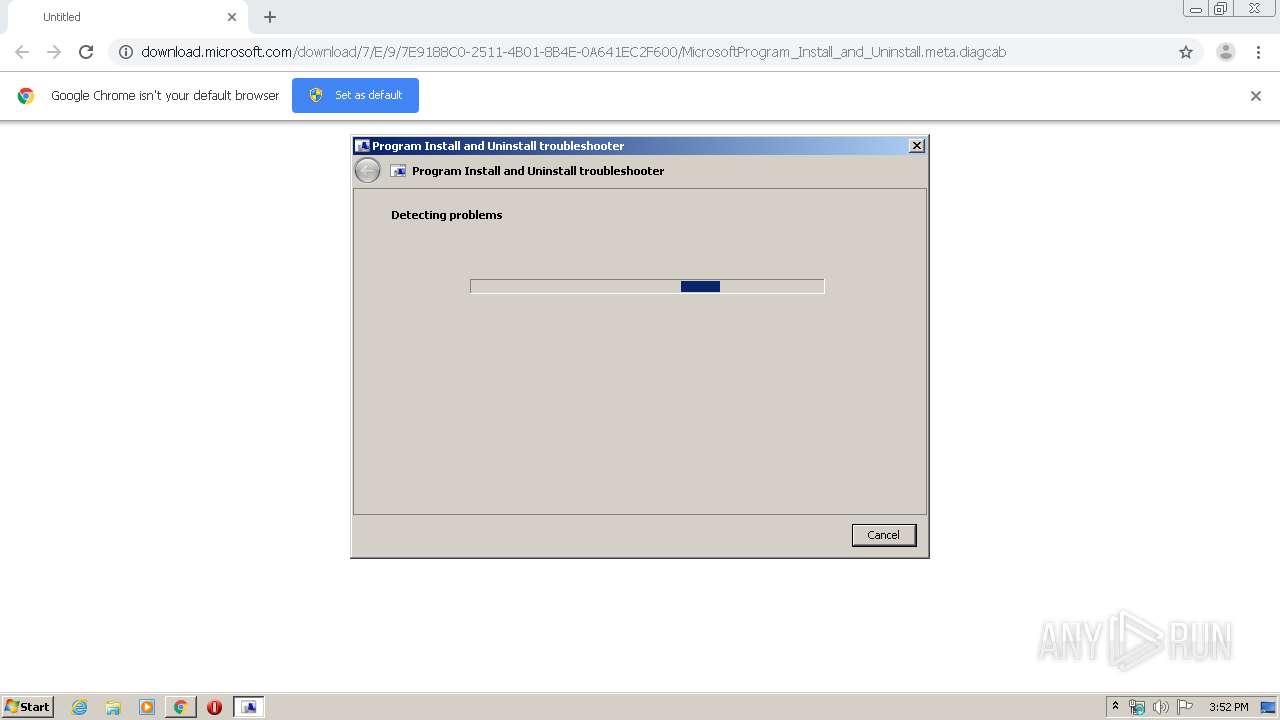
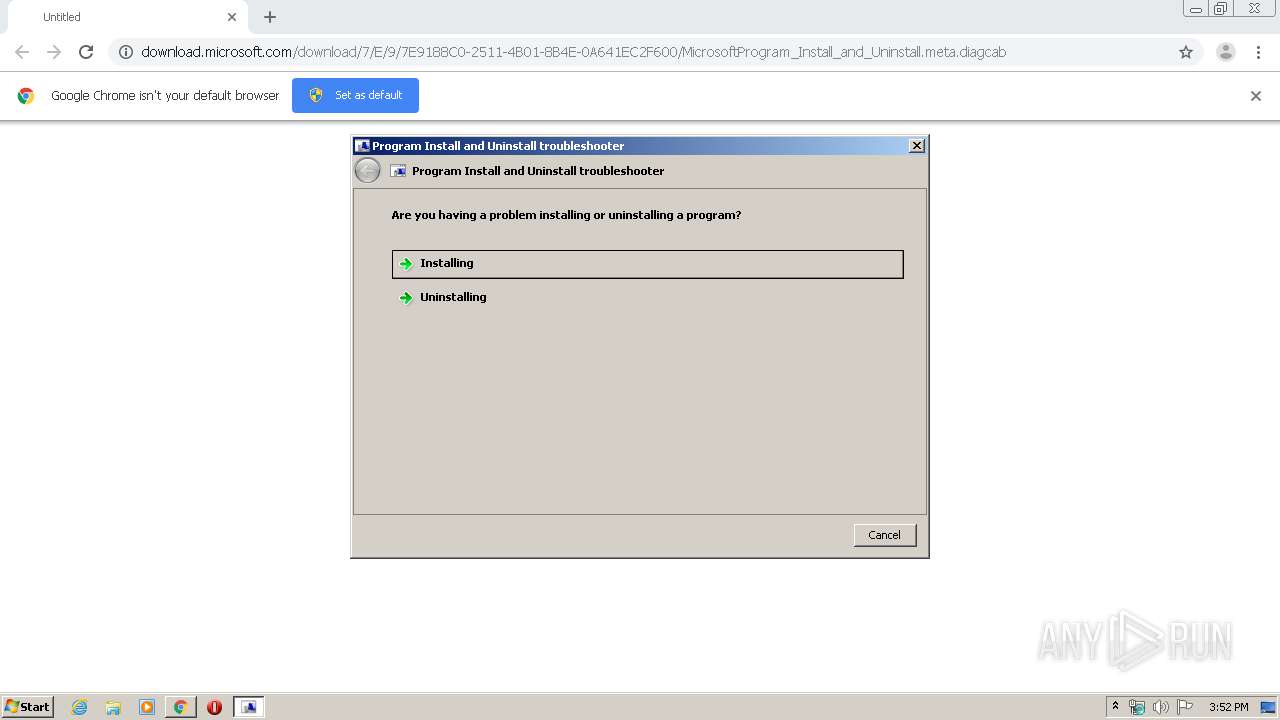
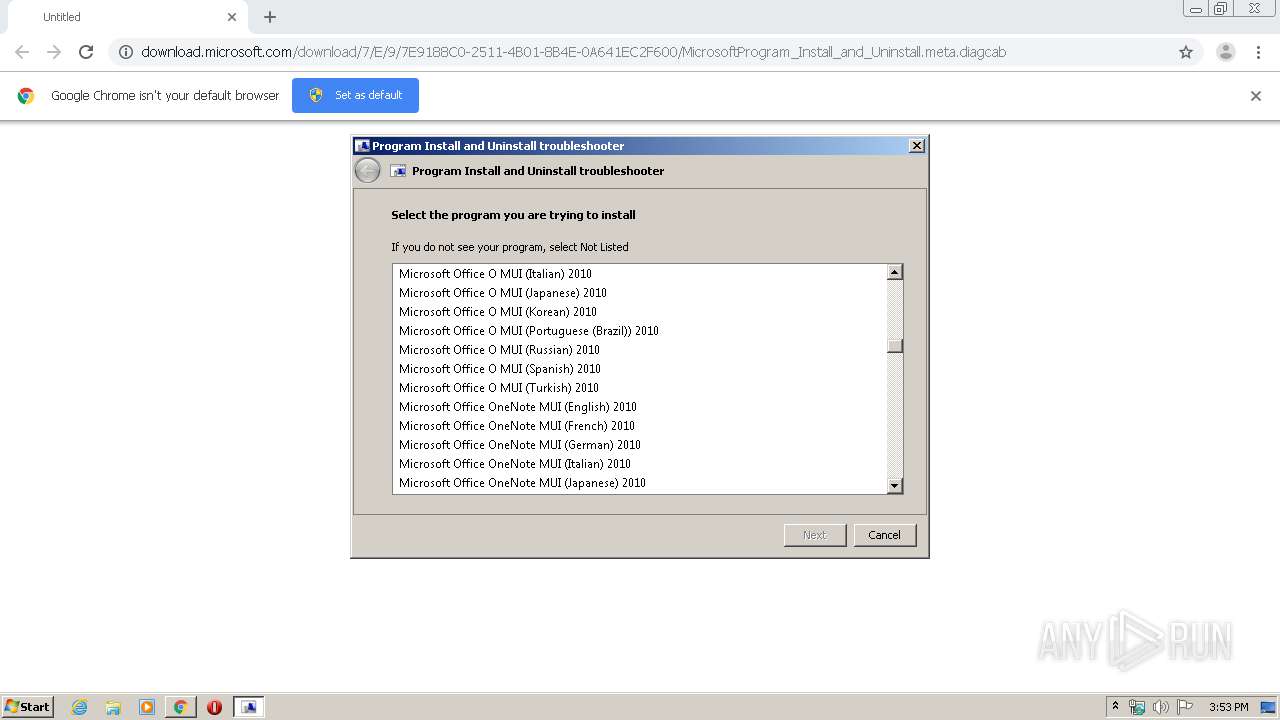
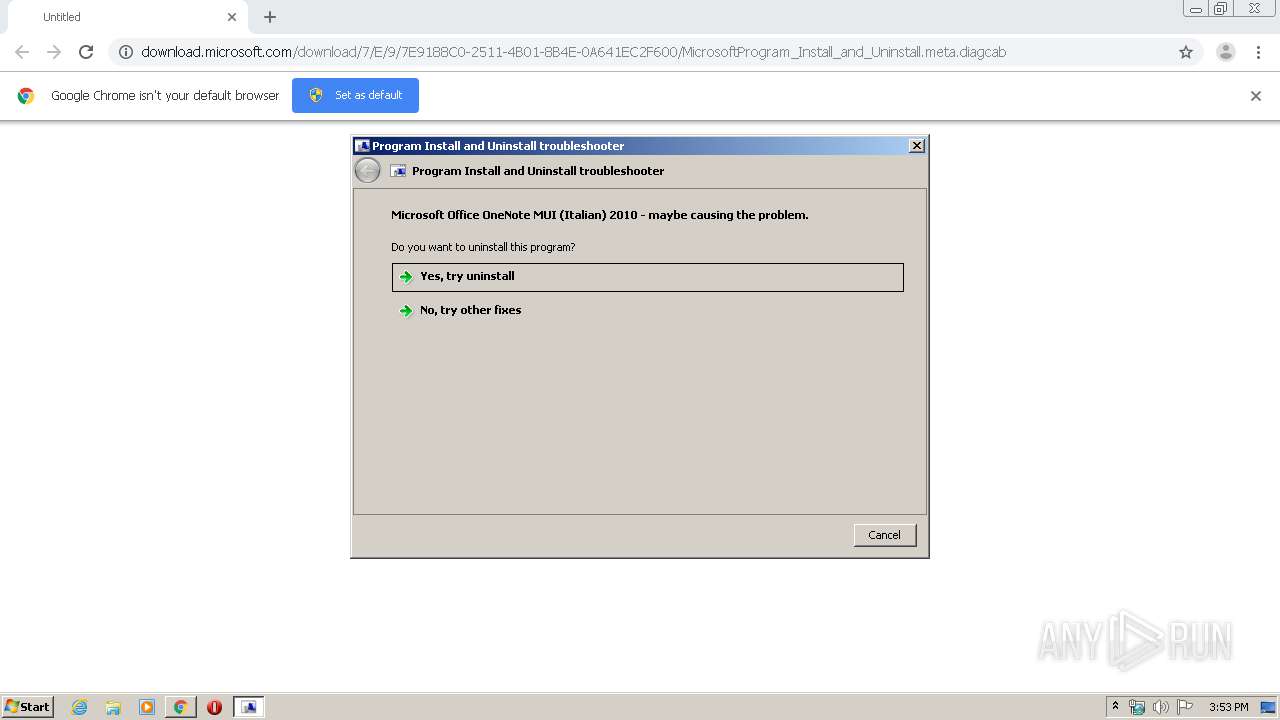
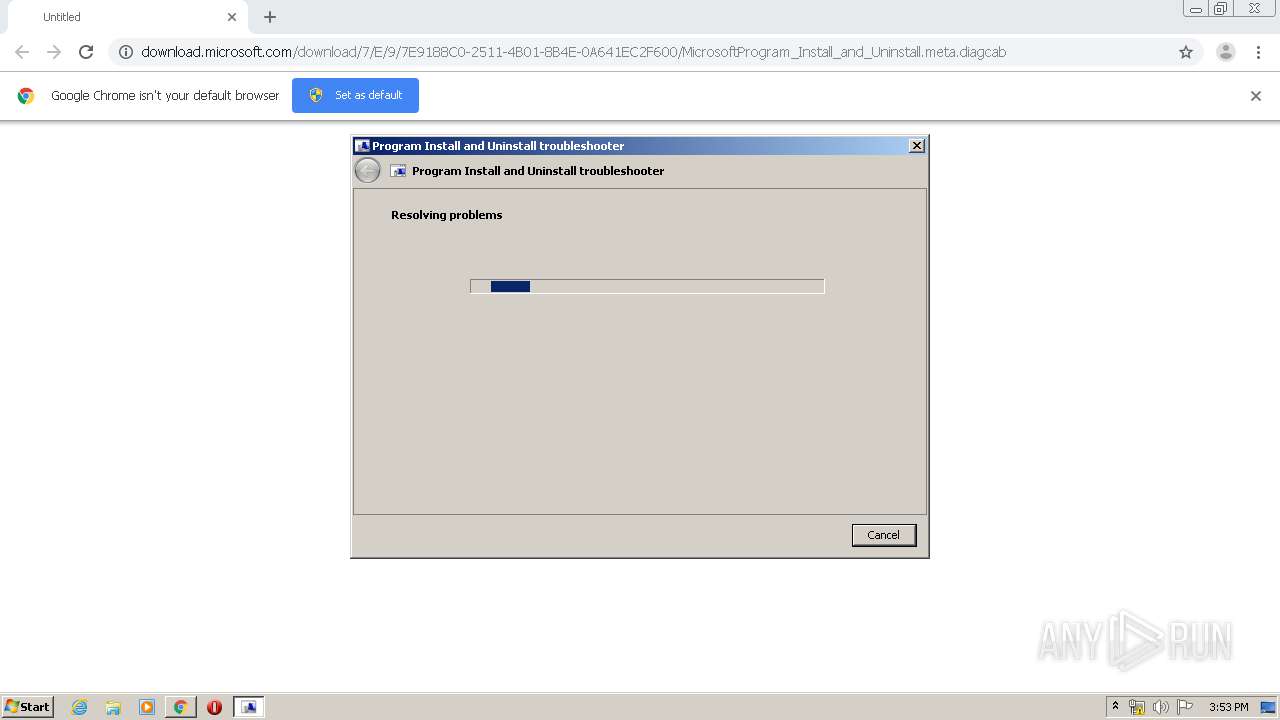
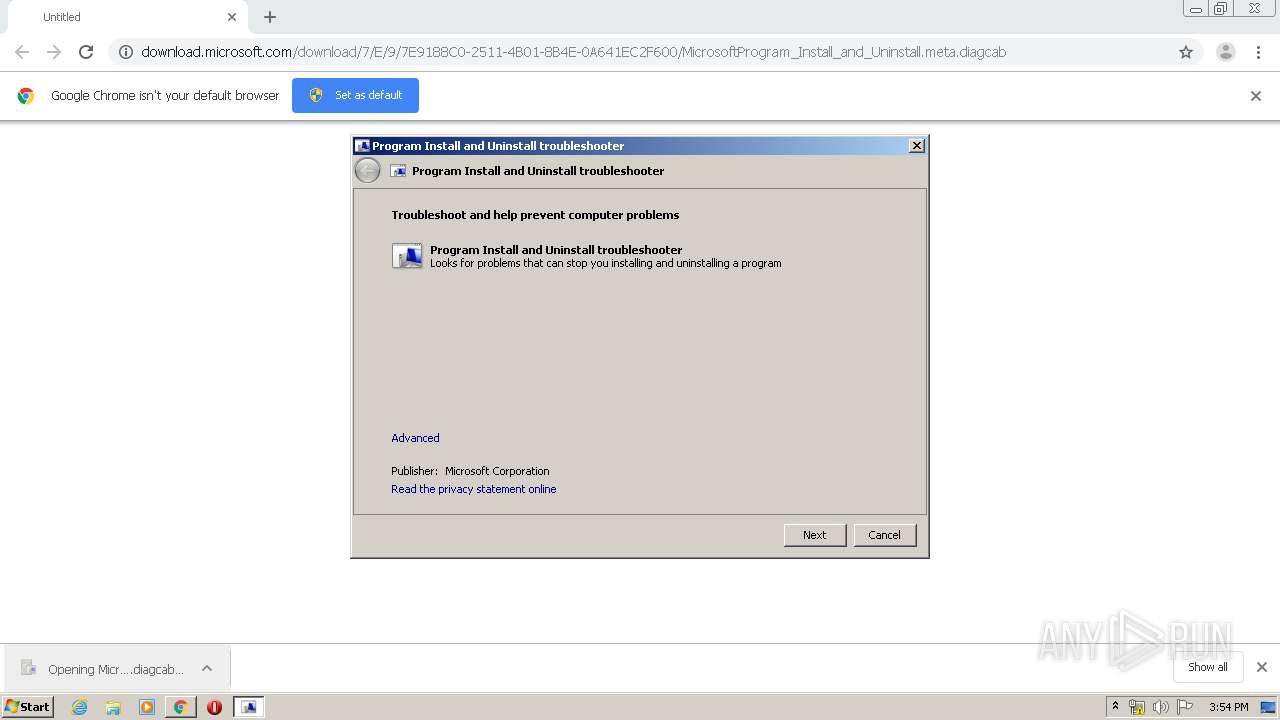
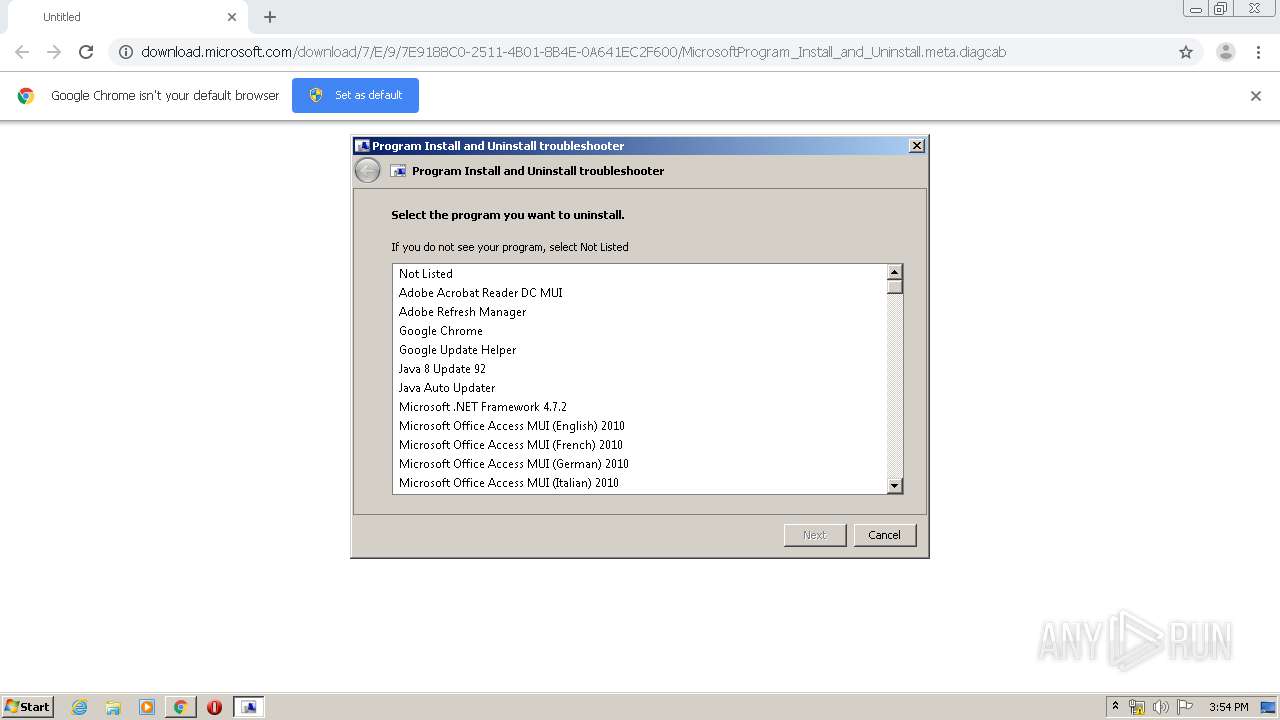
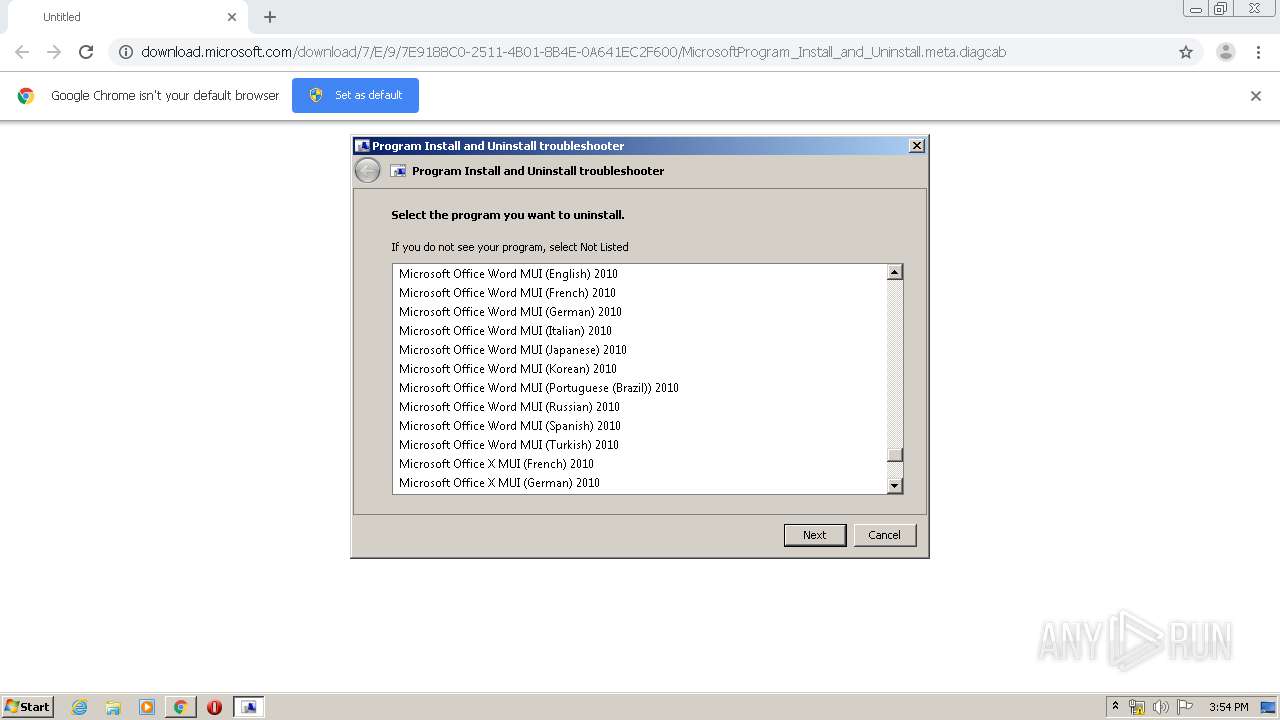
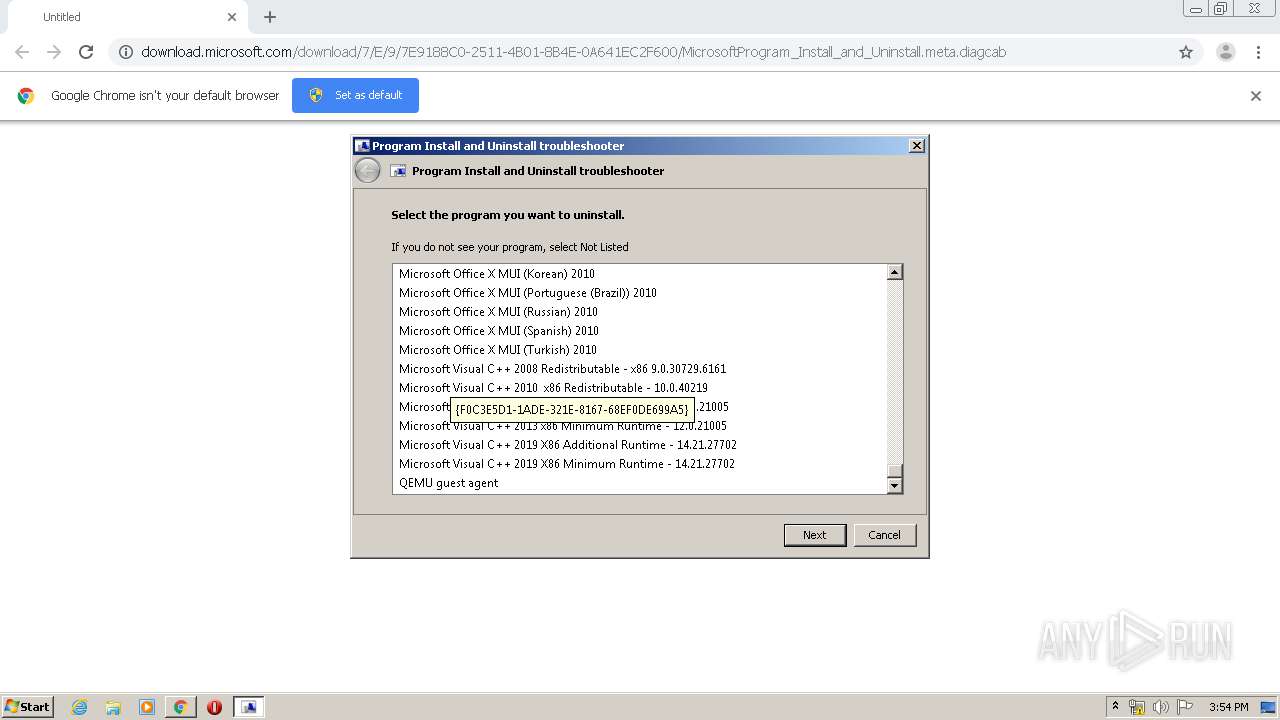
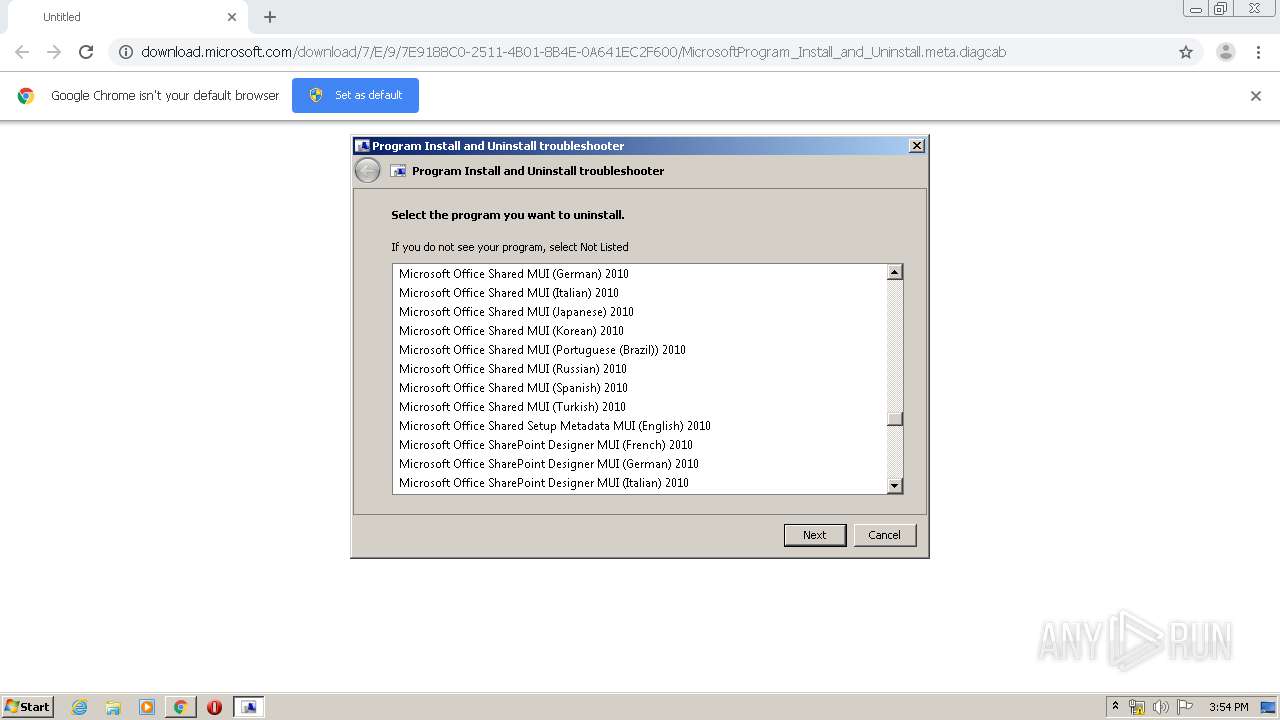
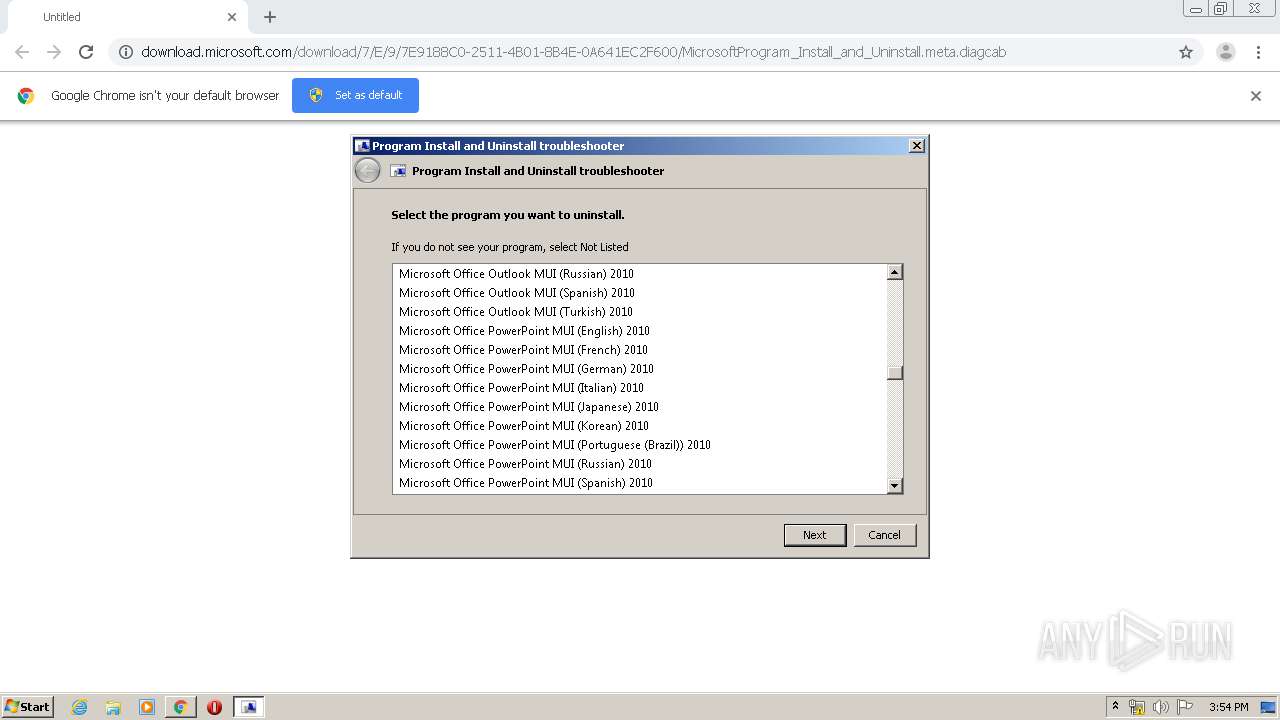
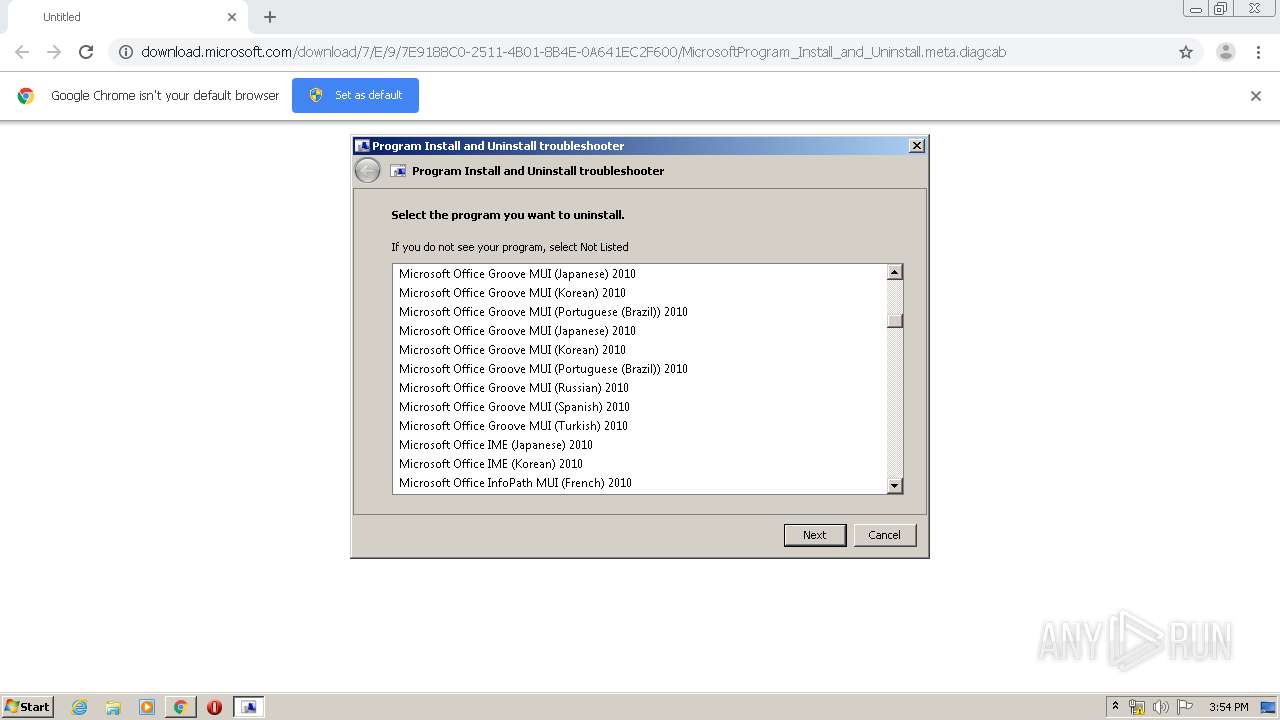
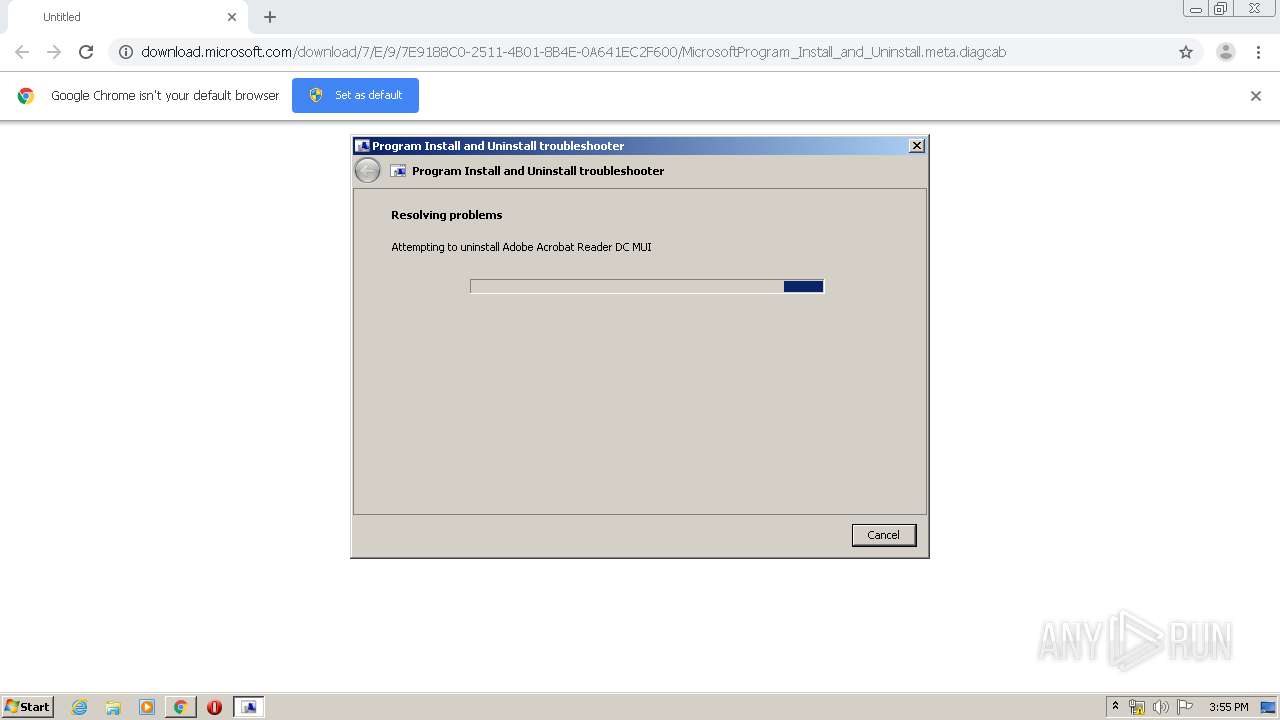
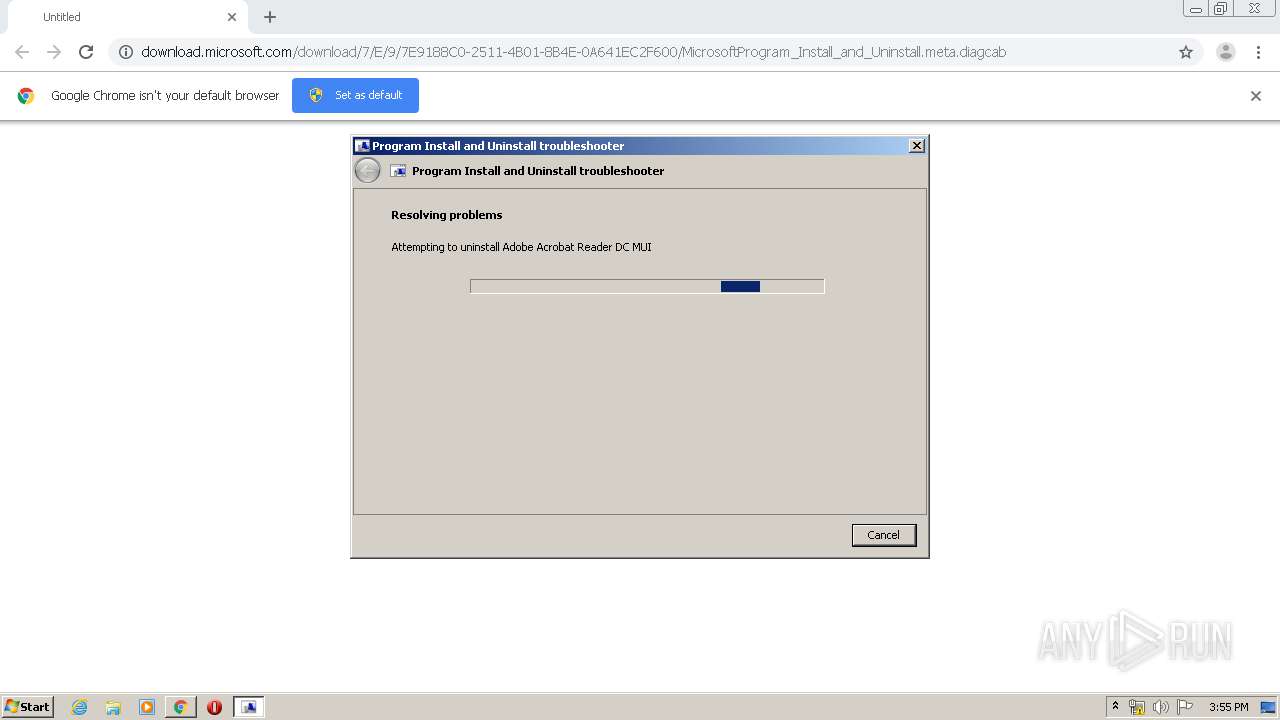
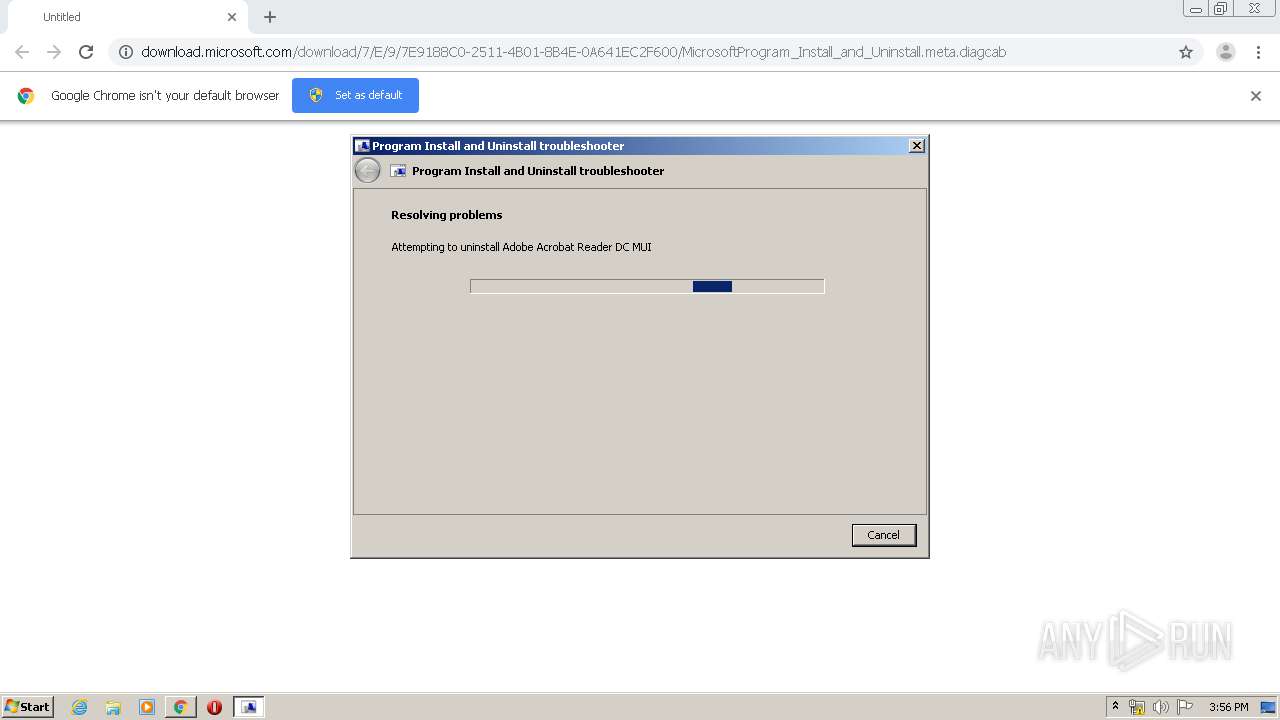
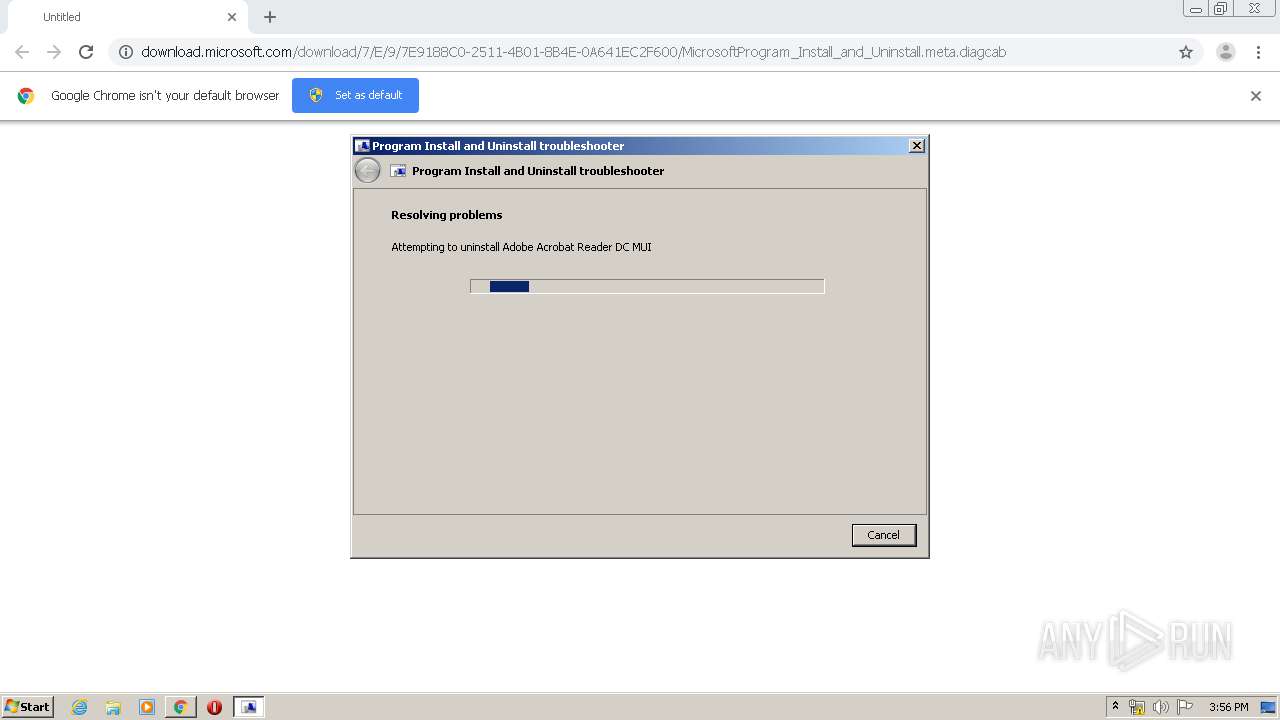
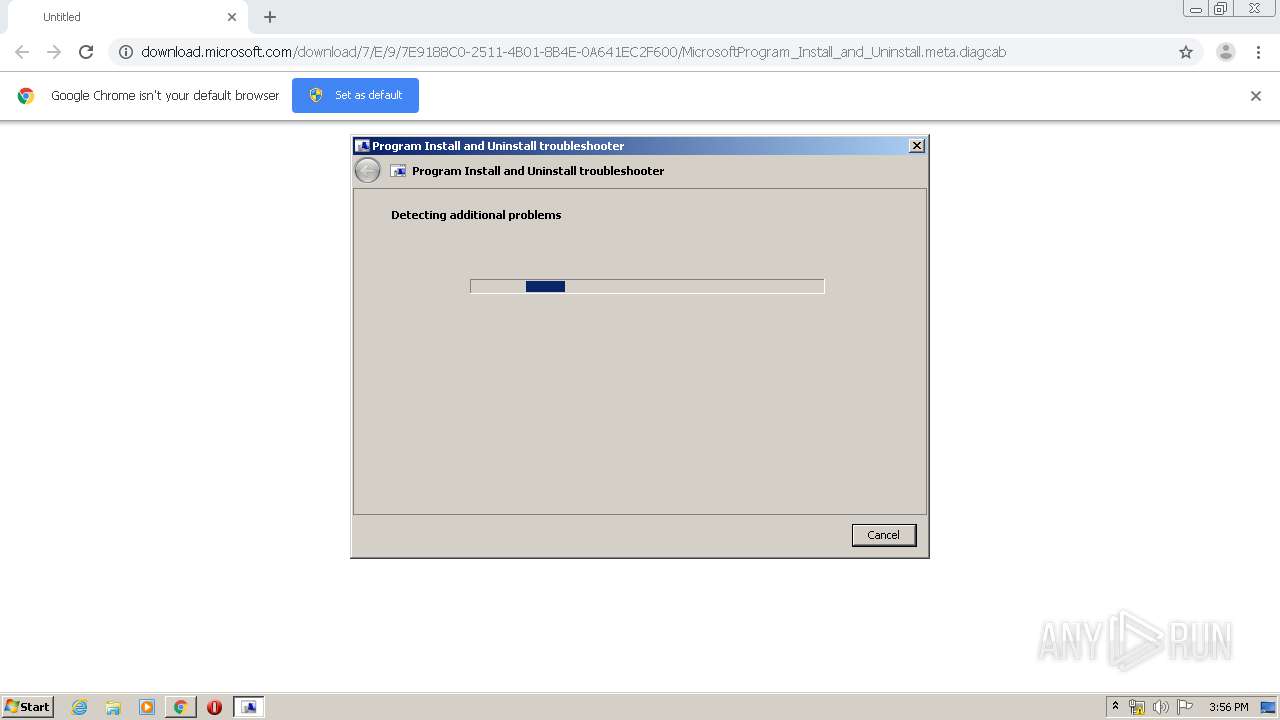
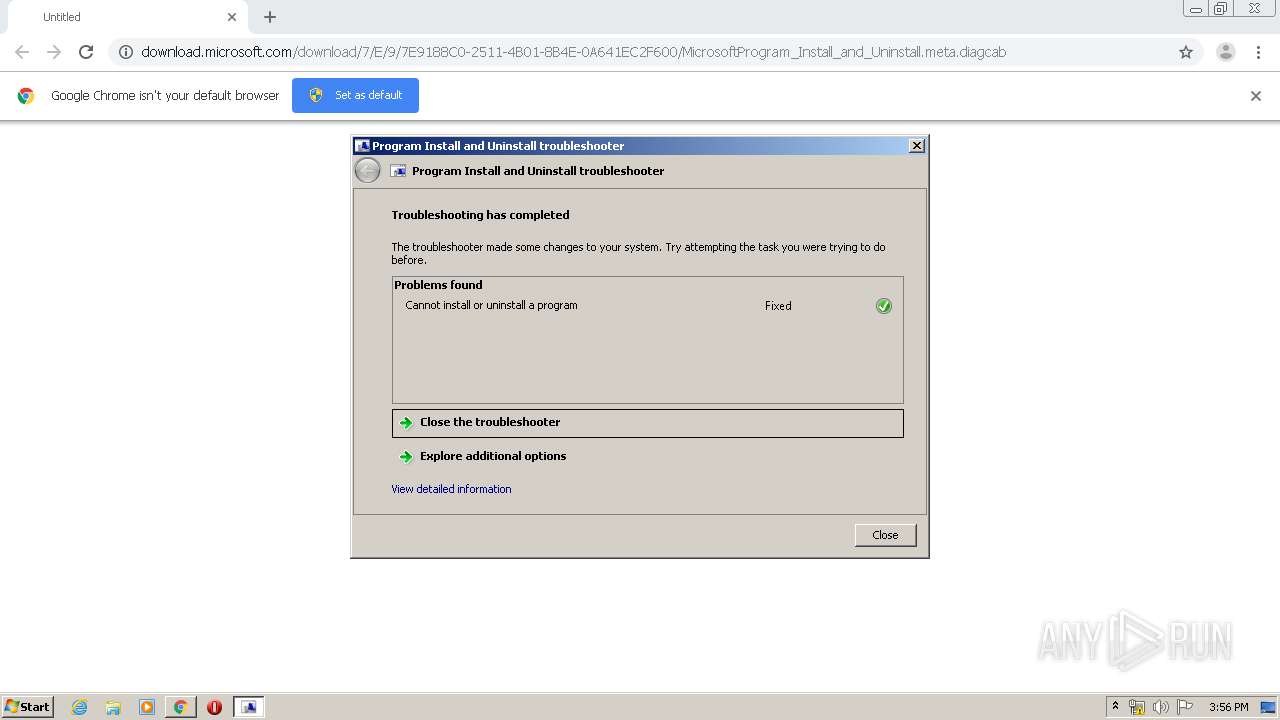
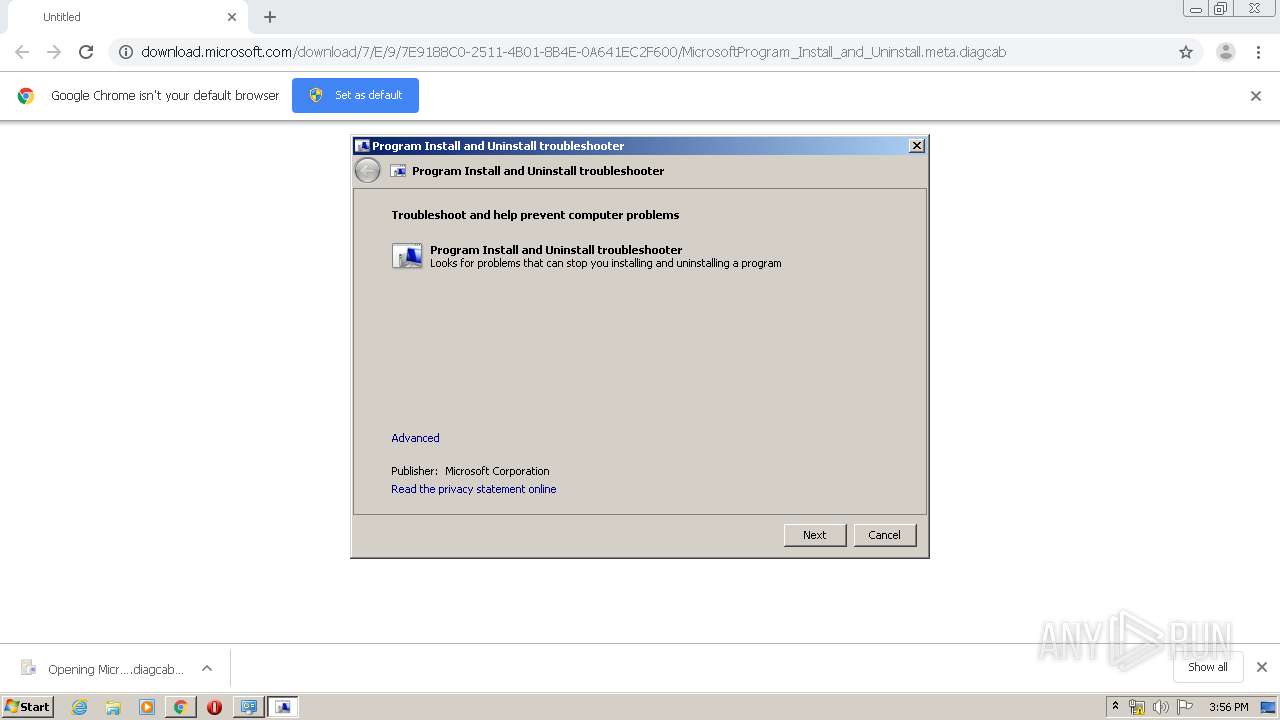
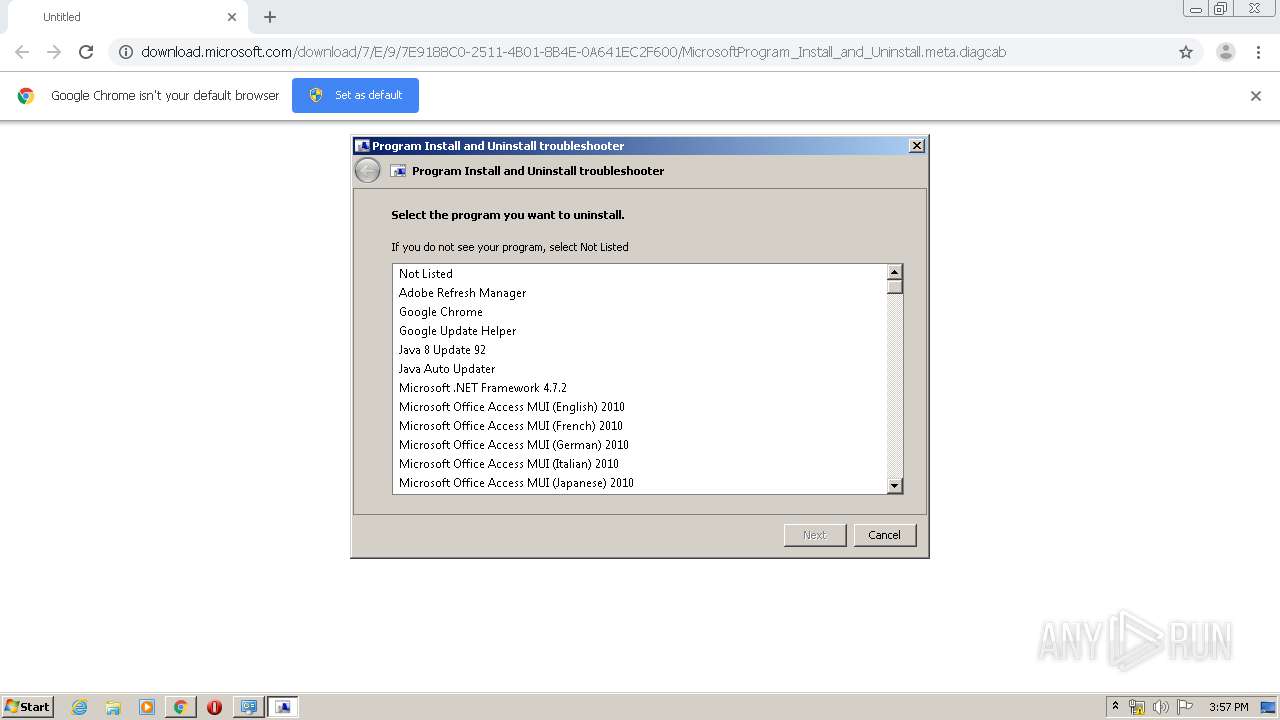
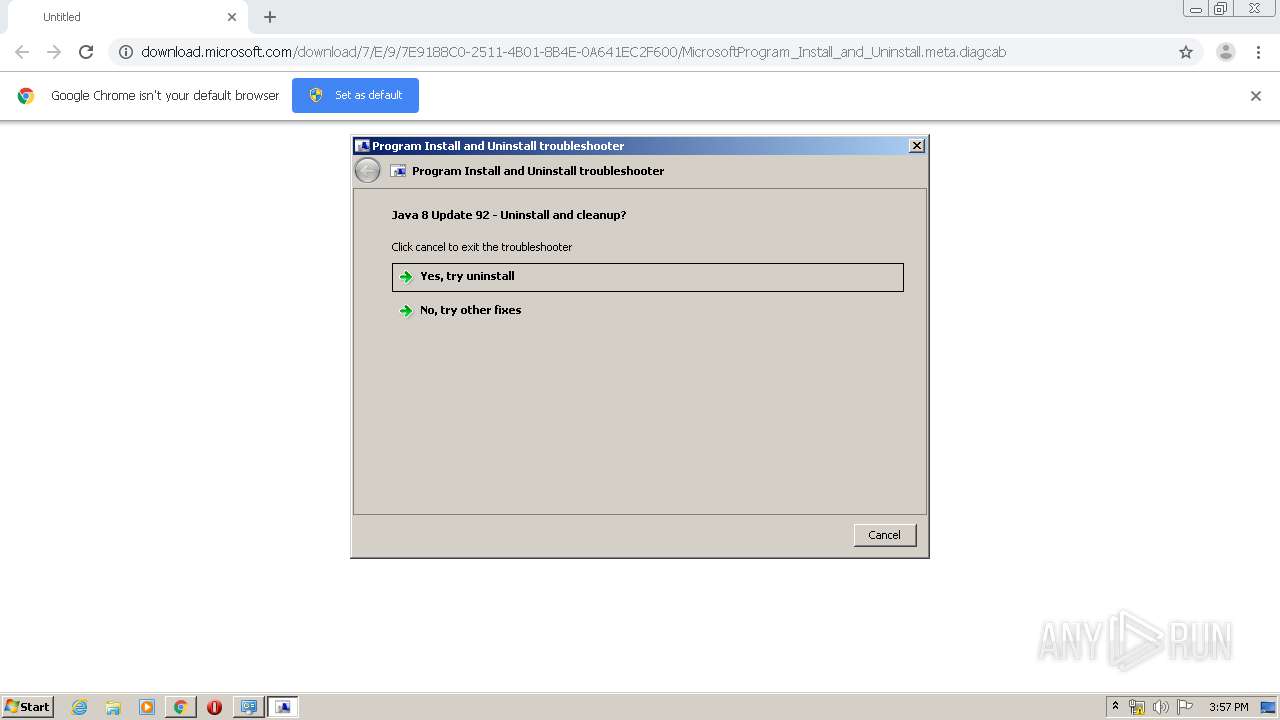
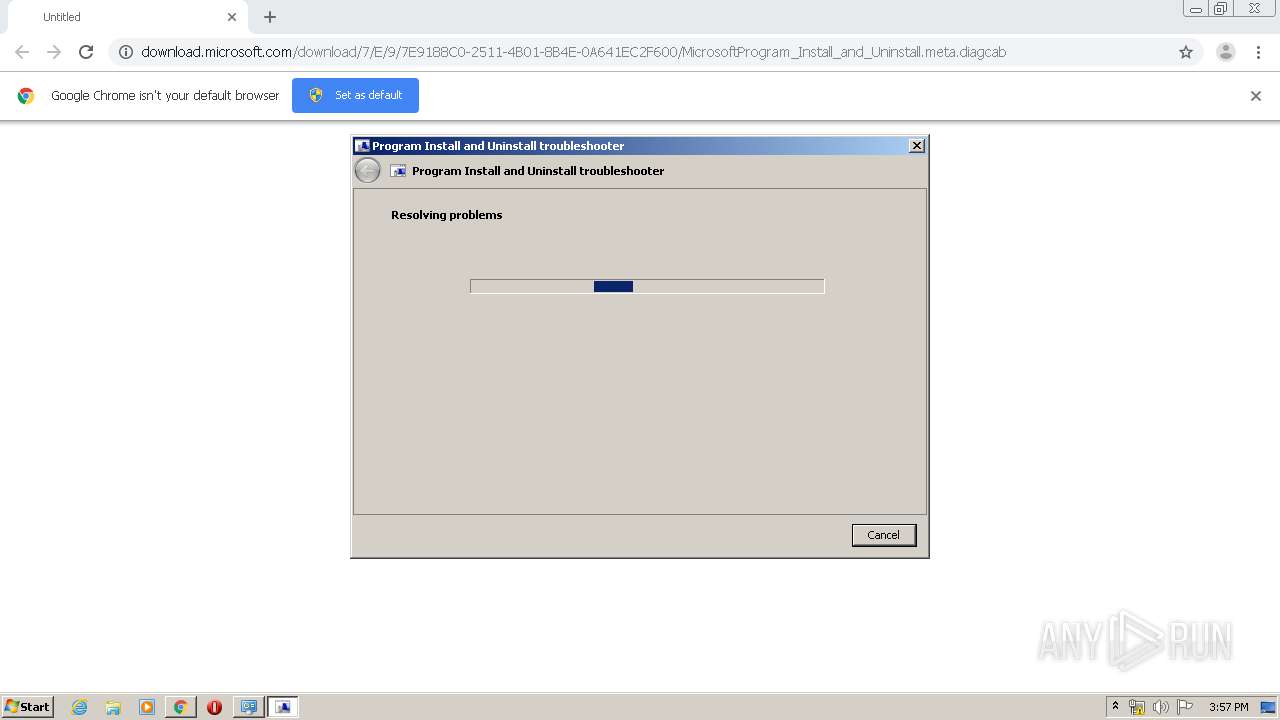
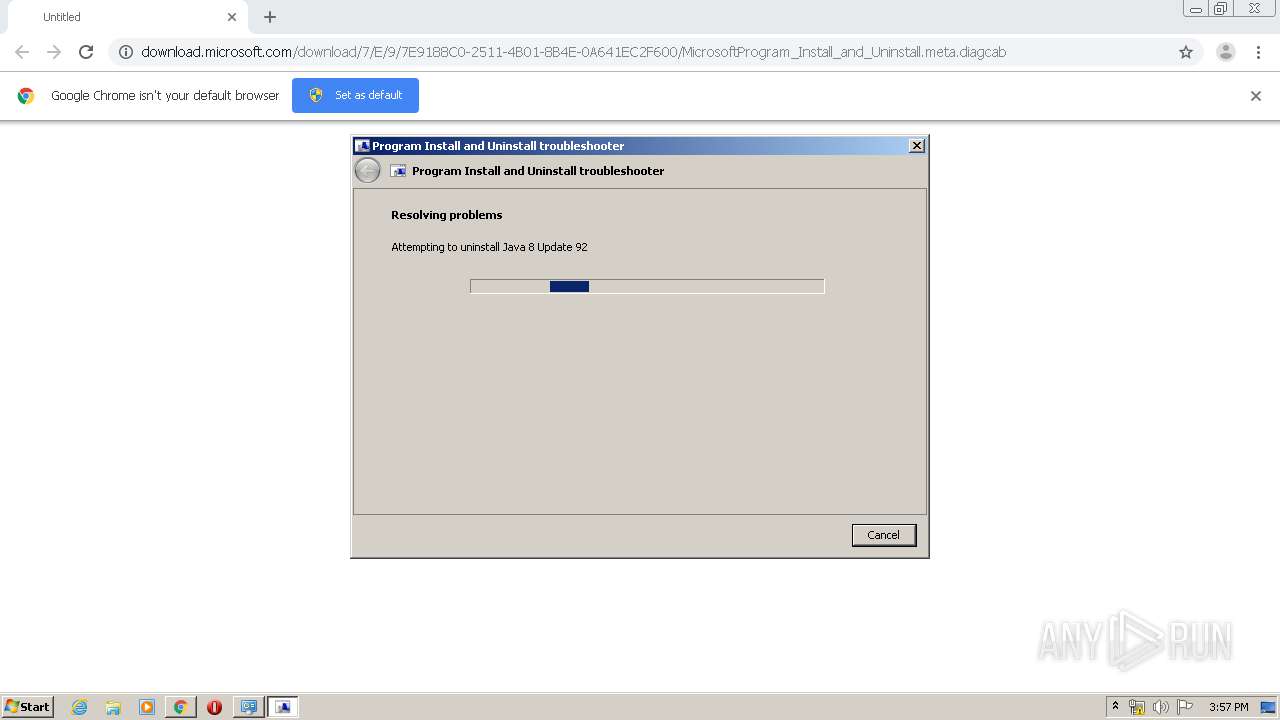
| URL: | http://download.microsoft.com/download/7/E/9/7E9188C0-2511-4B01-8B4E-0A641EC2F600/MicrosoftProgram_Install_and_Uninstall.meta.diagcab |
| Full analysis: | https://app.any.run/tasks/da7f4a76-7fa8-4513-85a4-704184e0b372 |
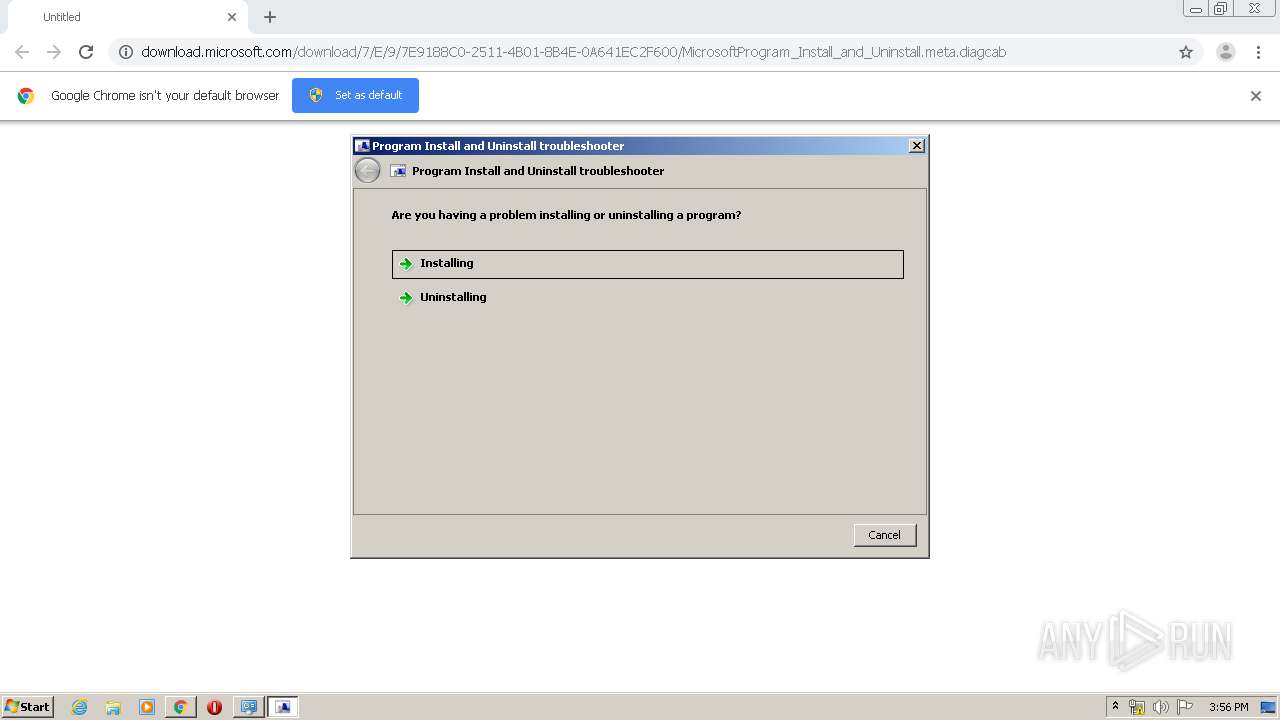
| Verdict: | Malicious activity |
| Analysis date: | February 21, 2020, 15:52:11 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | DC0DF85750C8E0B0C2F120311DFE01A2 |
| SHA1: | 7D8C53E62179AFD612A63C95FEF279BC25B9C1D4 |
| SHA256: | D906486B86DF8DD5A5A088A36363B351C86B1DD289ABC048A021DEEAFDAB6E64 |
| SSDEEP: | 3:N1KaKElyKRtR8LSOcYd5XBUI34UgmXvr3uTXuZzXrWBM3:Ca5TD8mOH54UjabutyM3 |
MALICIOUS
Starts Visual C# compiler
- sdiagnhost.exe (PID: 2856)
- sdiagnhost.exe (PID: 3312)
- sdiagnhost.exe (PID: 2352)
- sdiagnhost.exe (PID: 3660)
- sdiagnhost.exe (PID: 944)
Changes settings of System certificates
- msiexec.exe (PID: 3924)
- msdt.exe (PID: 1156)
SUSPICIOUS
Executable content was dropped or overwritten
- msdt.exe (PID: 3324)
- msdt.exe (PID: 1156)
- MsiExec.exe (PID: 3484)
- csc.exe (PID: 676)
- msdt.exe (PID: 2112)
- msdt.exe (PID: 3100)
- csc.exe (PID: 3876)
- msdt.exe (PID: 3772)
- msdt.exe (PID: 4084)
- msiexec.exe (PID: 3924)
Application launched itself
- msdt.exe (PID: 3324)
- msdt.exe (PID: 2112)
Creates files in the Windows directory
- msdt.exe (PID: 1156)
- sdiagnhost.exe (PID: 2856)
- sdiagnhost.exe (PID: 3312)
- sdiagnhost.exe (PID: 2352)
- MsiExec.exe (PID: 3000)
- msdt.exe (PID: 3100)
- sdiagnhost.exe (PID: 3660)
- msdt.exe (PID: 3772)
- sdiagnhost.exe (PID: 944)
Executed via COM
- sdiagnhost.exe (PID: 2856)
- DllHost.exe (PID: 2376)
- DllHost.exe (PID: 1500)
- DllHost.exe (PID: 3708)
- sdiagnhost.exe (PID: 3312)
- sdiagnhost.exe (PID: 2352)
- DllHost.exe (PID: 3392)
- DllHost.exe (PID: 3716)
- sdiagnhost.exe (PID: 3660)
- sdiagnhost.exe (PID: 944)
- DllHost.exe (PID: 180)
- DllHost.exe (PID: 3208)
- DllHost.exe (PID: 2244)
Executed as Windows Service
- vssvc.exe (PID: 3336)
- SearchIndexer.exe (PID: 1748)
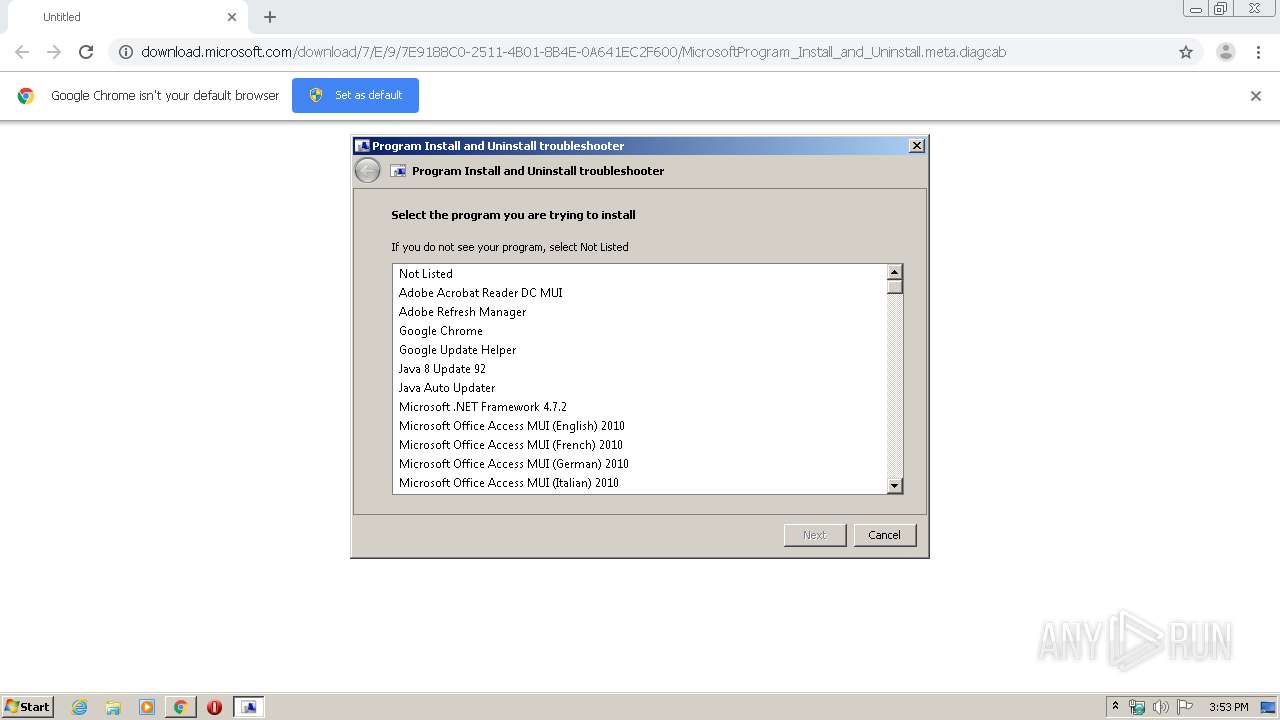
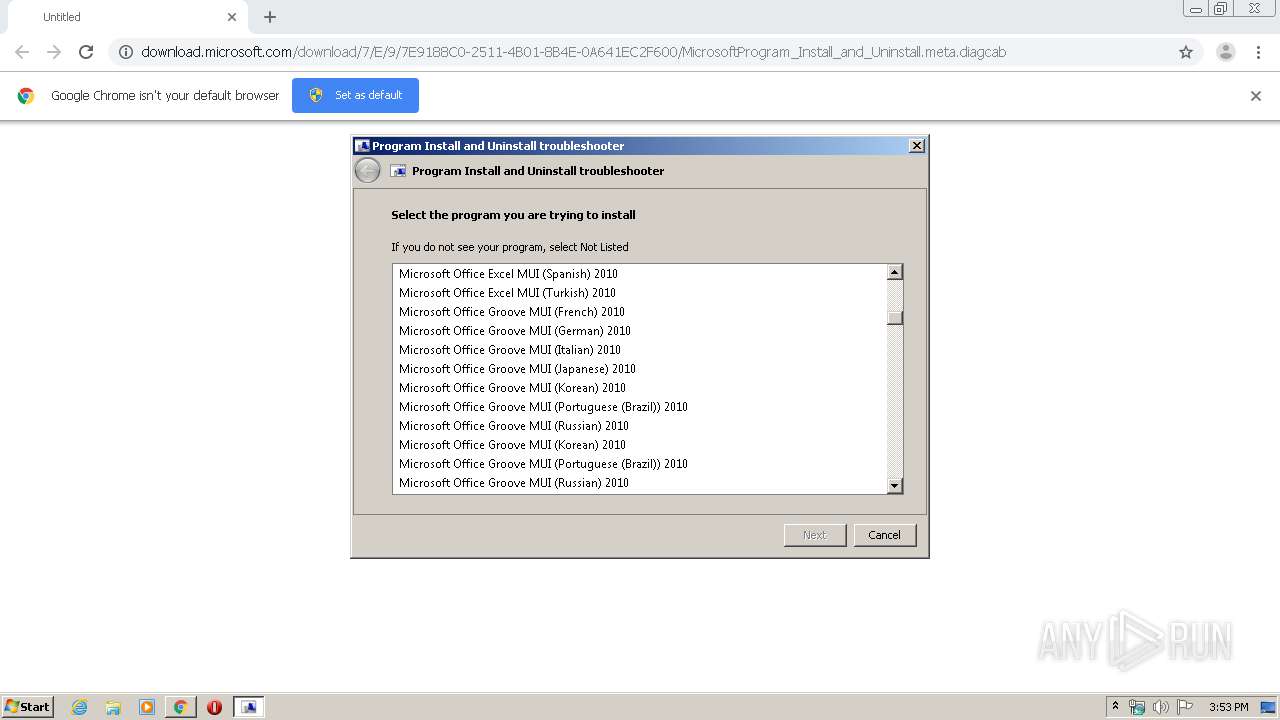
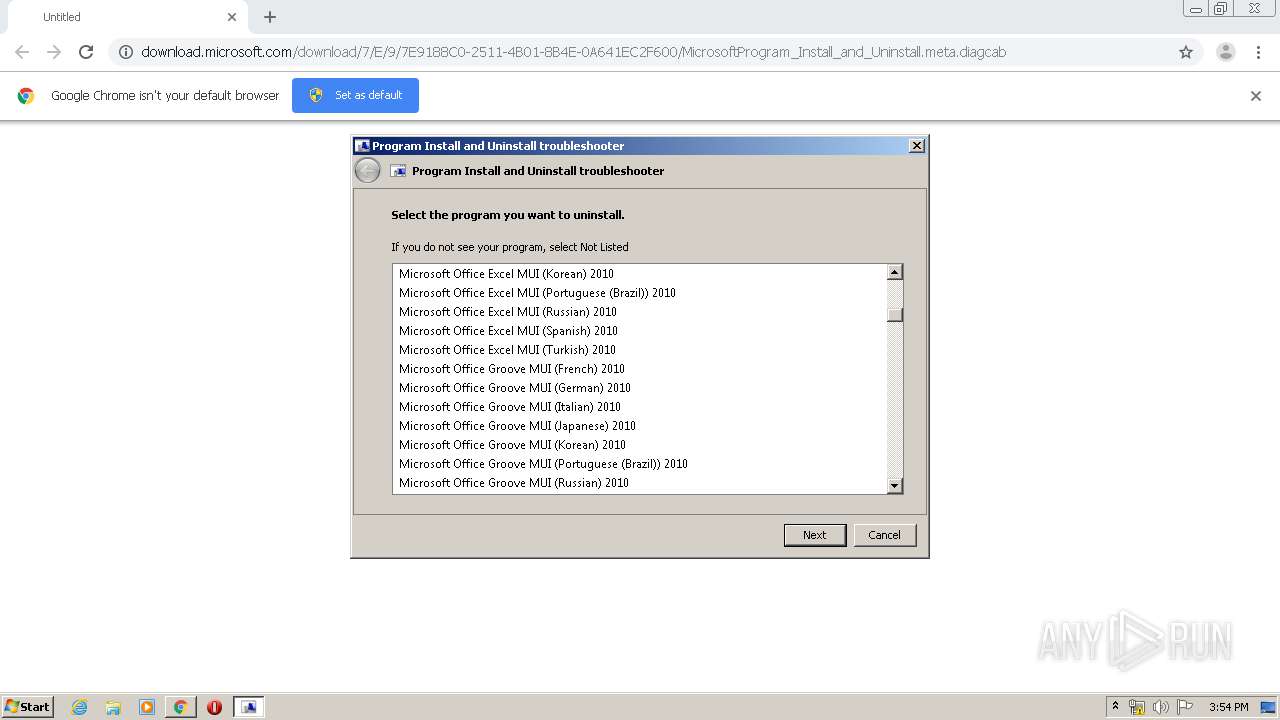
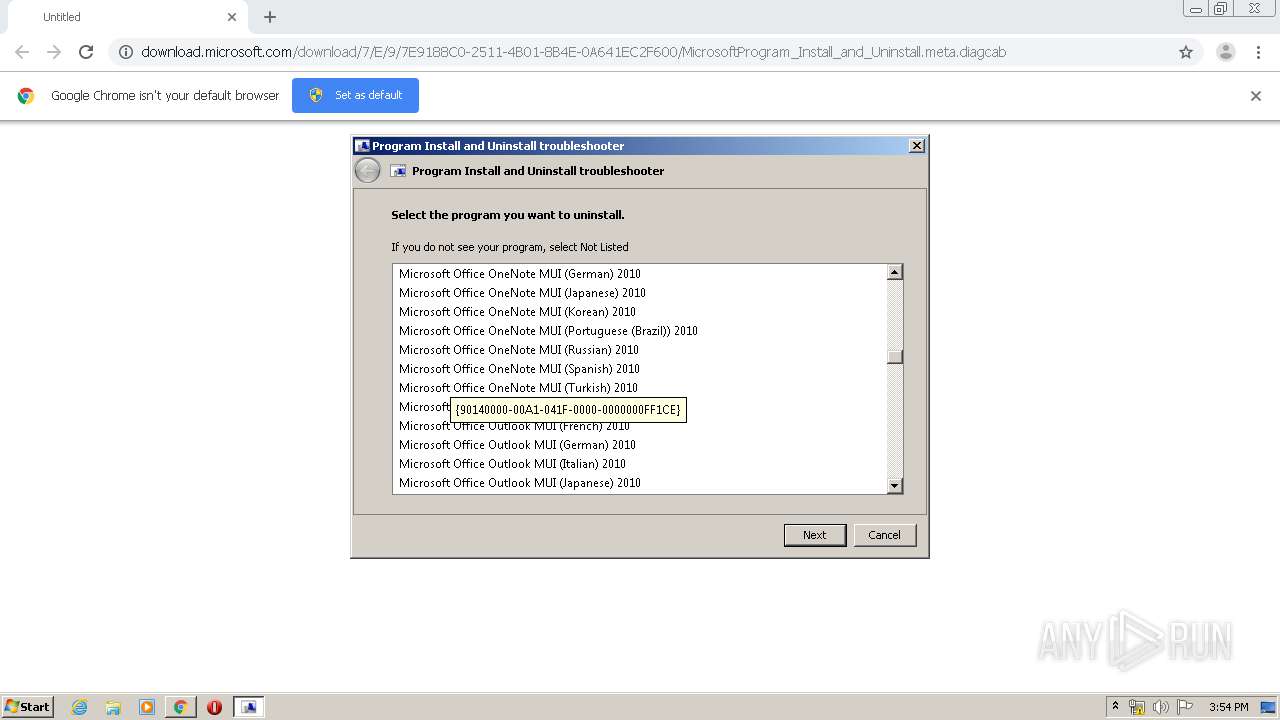
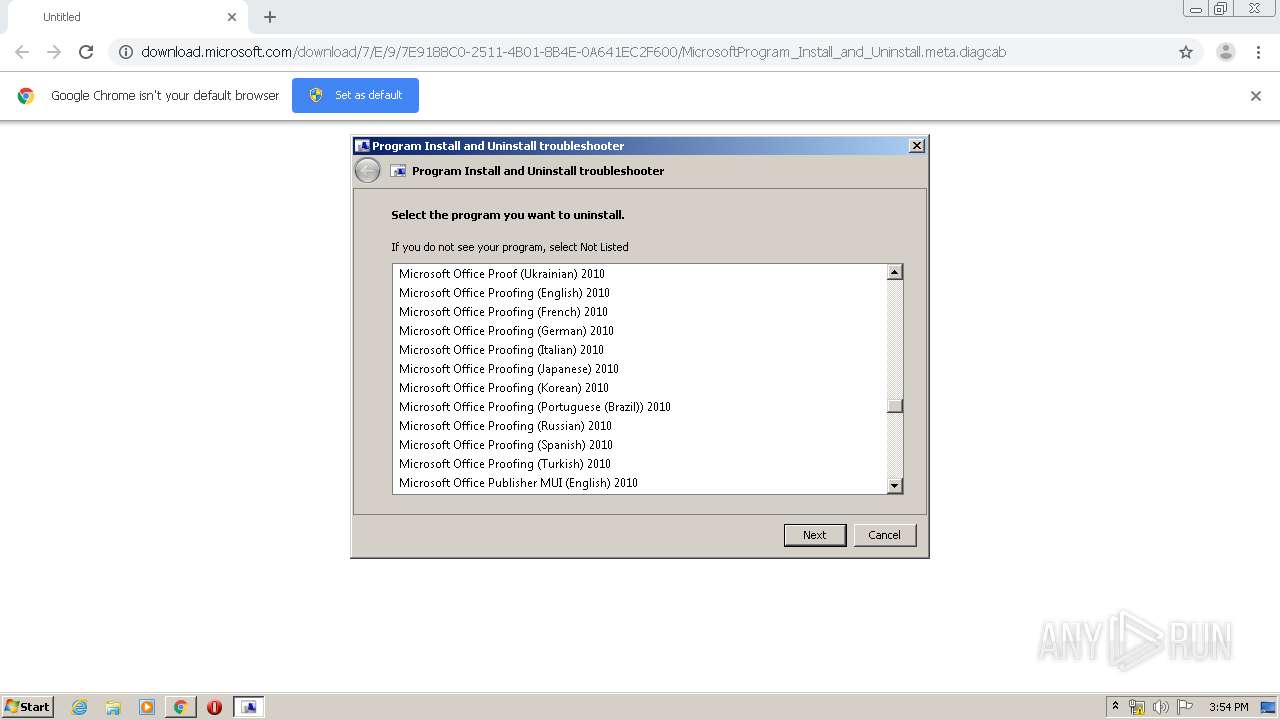
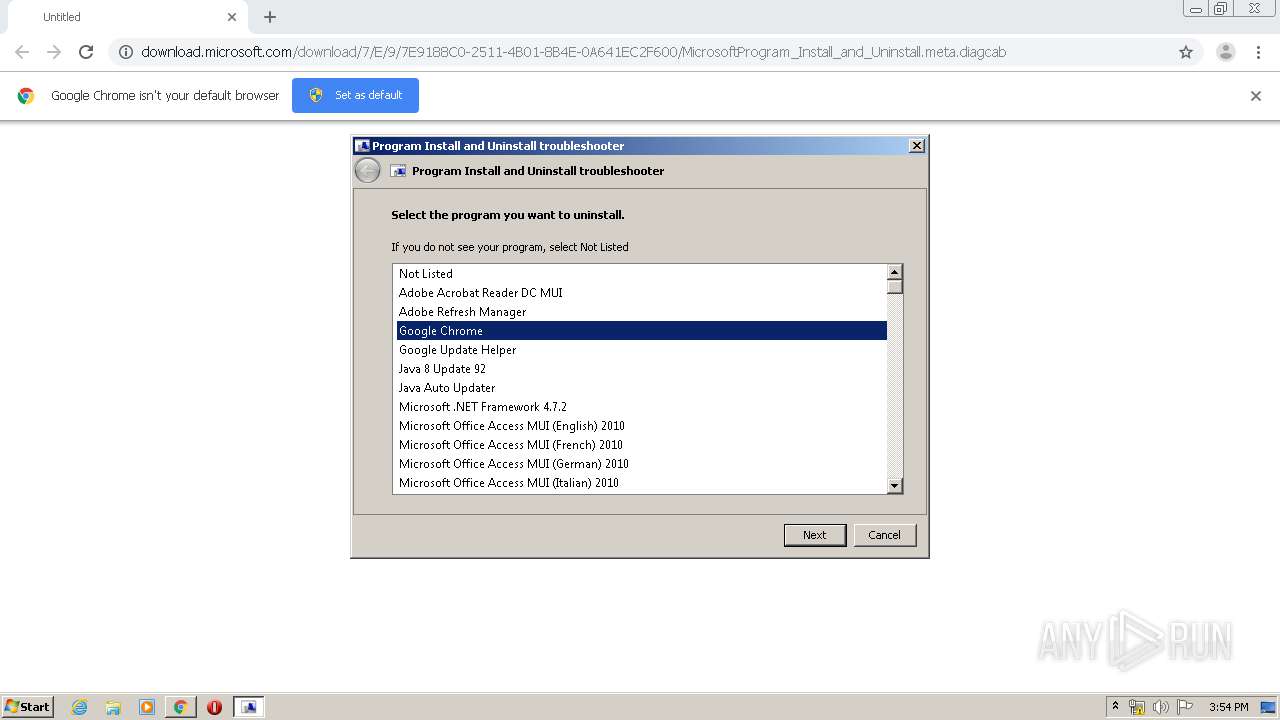
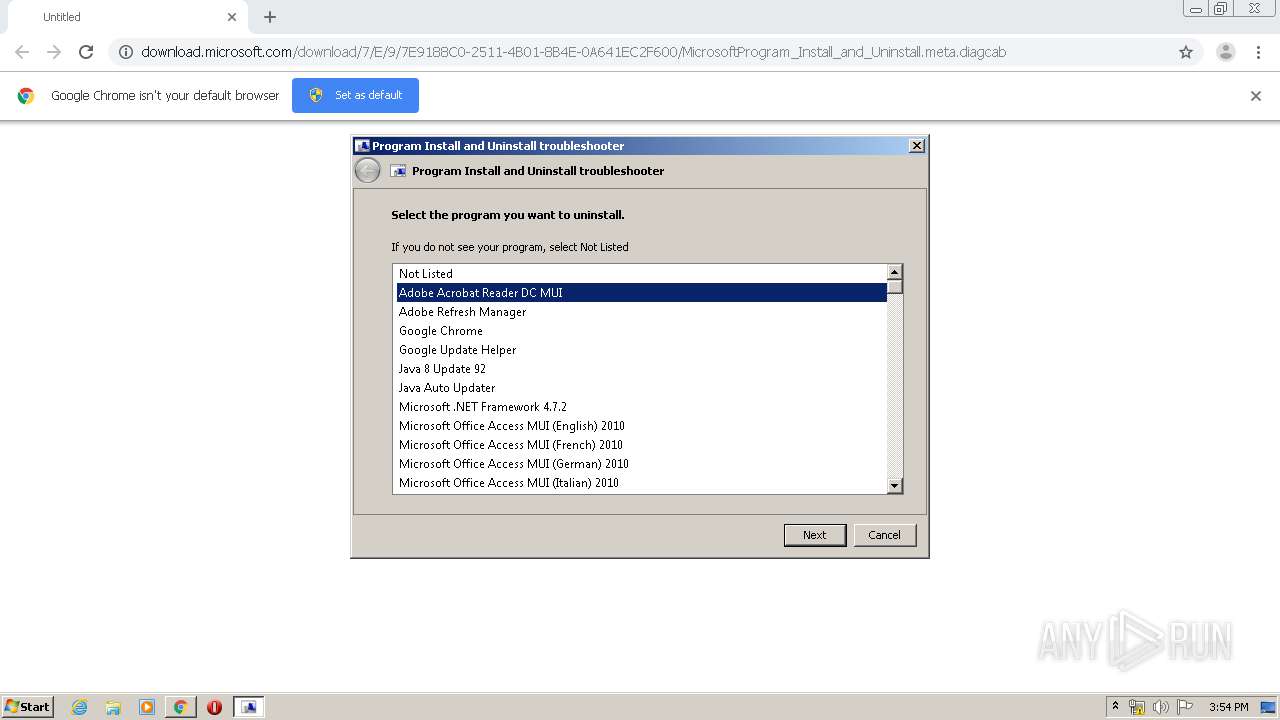
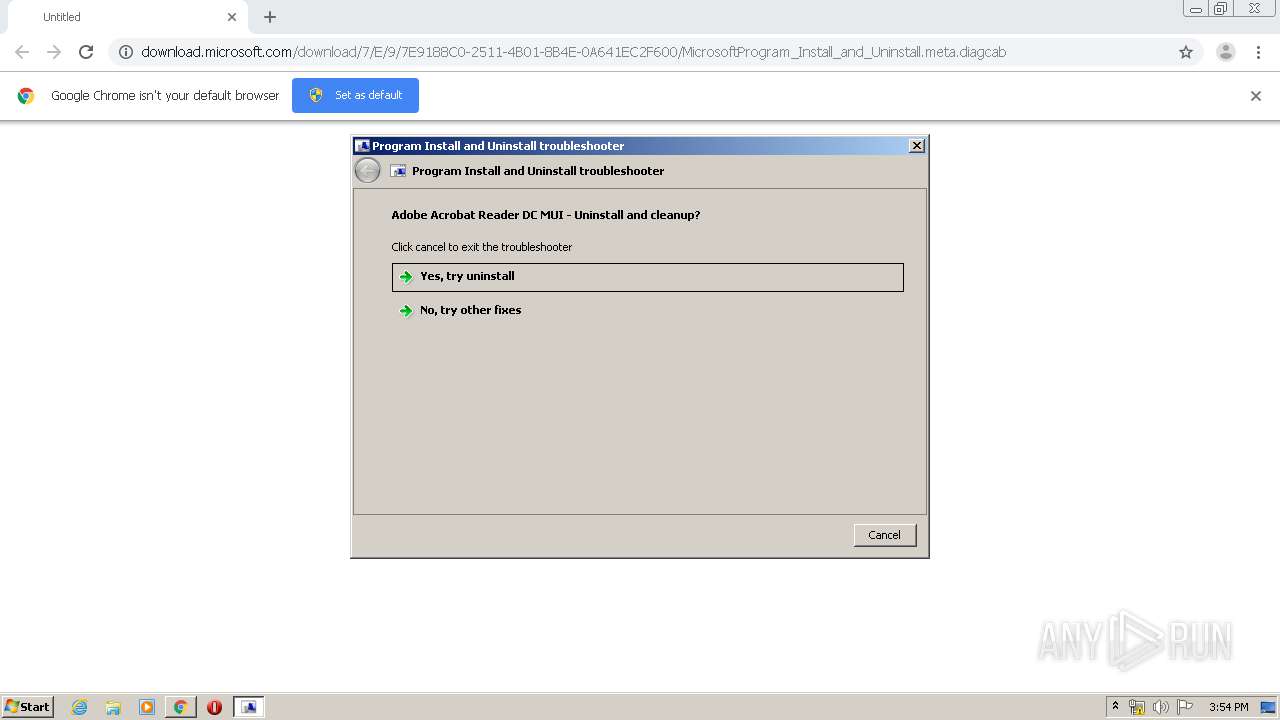
Searches for installed software
- sdiagnhost.exe (PID: 2856)
- sdiagnhost.exe (PID: 2352)
Removes files from Windows directory
- msdt.exe (PID: 1156)
- MsiExec.exe (PID: 3000)
- msdt.exe (PID: 3100)
- MSIE2C1.tmp (PID: 1116)
Adds / modifies Windows certificates
- msiexec.exe (PID: 3924)
- msdt.exe (PID: 1156)
Modifies files in Chrome extension folder
- chrome.exe (PID: 1544)
Creates files in the program directory
- SearchIndexer.exe (PID: 1748)
Creates COM task schedule object
- MSIE2C1.tmp (PID: 1116)
INFO
Reads the hosts file
- chrome.exe (PID: 1544)
- chrome.exe (PID: 3148)
Reads Internet Cache Settings
- chrome.exe (PID: 1544)
Application launched itself
- chrome.exe (PID: 1544)
- msiexec.exe (PID: 3924)
Low-level read access rights to disk partition
- vssvc.exe (PID: 3336)
Reads settings of System Certificates
- msdt.exe (PID: 1156)
- sdiagnhost.exe (PID: 3312)
- sdiagnhost.exe (PID: 2856)
- sdiagnhost.exe (PID: 2352)
- msiexec.exe (PID: 3924)
- sdiagnhost.exe (PID: 3660)
- sdiagnhost.exe (PID: 944)
Loads dropped or rewritten executable
- MsiExec.exe (PID: 2184)
- MsiExec.exe (PID: 3000)
- MsiExec.exe (PID: 3084)
Creates files in the program directory
- MsiExec.exe (PID: 2184)
Starts application with an unusual extension
- msiexec.exe (PID: 3924)
Application was dropped or rewritten from another process
- MSIDCE8.tmp (PID: 2668)
- MSIE2C1.tmp (PID: 1116)
Dropped object may contain Bitcoin addresses
- msiexec.exe (PID: 3924)
Manual execution by user
- rundll32.exe (PID: 1092)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
212
Monitored processes
159
Malicious processes
12
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 180 | C:\Windows\system32\DllHost.exe /Processid:{F32D97DF-E3E5-4CB9-9E3E-0EB5B4E49801} | C:\Windows\system32\DllHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 316 | "C:\Windows\system32\SearchProtocolHost.exe" Global\UsGthrFltPipeMssGthrPipe_S-1-5-21-1302019708-1500728564-335382590-10002_ Global\UsGthrCtrlFltPipeMssGthrPipe_S-1-5-21-1302019708-1500728564-335382590-10002 1 -2147483646 "Software\Microsoft\Windows Search" "Mozilla/4.0 (compatible; MSIE 6.0; Windows NT; MS Search 4.0 Robot)" "C:\ProgramData\Microsoft\Search\Data\Temp\usgthrsvc" "DownLevelDaemon" "1" | C:\Windows\system32\SearchProtocolHost.exe | — | SearchIndexer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Windows Search Protocol Host Exit code: 0 Version: 7.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 404 | C:\Windows\Microsoft.NET\Framework\v2.0.50727\cvtres.exe /NOLOGO /READONLY /MACHINE:IX86 "/OUT:C:\Users\admin\AppData\Local\Temp\RES18F6.tmp" "c:\Users\admin\AppData\Local\Temp\CSC18F5.tmp" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\cvtres.exe | — | csc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft® Resource File To COFF Object Conversion Utility Exit code: 0 Version: 8.00.50727.4940 (Win7SP1.050727-5400) Modules
| |||||||||||||||
| 548 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1020,8207175108809653409,16631101827843906530,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=16555591807914721691 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2248 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 576 | "C:\Windows\Microsoft.NET\Framework\v2.0.50727\csc.exe" /noconfig /fullpaths @"C:\Users\admin\AppData\Local\Temp\gdgt27nt.cmdline" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\csc.exe | sdiagnhost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Visual C# Command Line Compiler Exit code: 0 Version: 8.0.50727.4927 (NetFXspW7.050727-4900) Modules
| |||||||||||||||
| 580 | C:\Windows\Microsoft.NET\Framework\v2.0.50727\cvtres.exe /NOLOGO /READONLY /MACHINE:IX86 "/OUT:C:\Users\admin\AppData\Local\Temp\RES80FC.tmp" "c:\Users\admin\AppData\Local\Temp\CSC80EB.tmp" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\cvtres.exe | — | csc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft® Resource File To COFF Object Conversion Utility Exit code: 0 Version: 8.00.50727.4940 (Win7SP1.050727-5400) Modules
| |||||||||||||||
| 620 | "C:\Windows\Microsoft.NET\Framework\v2.0.50727\csc.exe" /noconfig /fullpaths @"C:\Users\admin\AppData\Local\Temp\lbfpaltq.cmdline" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\csc.exe | sdiagnhost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Visual C# Command Line Compiler Exit code: 0 Version: 8.0.50727.4927 (NetFXspW7.050727-4900) Modules
| |||||||||||||||
| 676 | "C:\Windows\Microsoft.NET\Framework\v2.0.50727\csc.exe" /noconfig /fullpaths @"C:\Users\admin\AppData\Local\Temp\9ua3zrkf.cmdline" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\csc.exe | sdiagnhost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Visual C# Command Line Compiler Exit code: 0 Version: 8.0.50727.4927 (NetFXspW7.050727-4900) Modules
| |||||||||||||||
| 856 | "C:\Windows\Microsoft.NET\Framework\v2.0.50727\csc.exe" /noconfig /fullpaths @"C:\Users\admin\AppData\Local\Temp\__yotn0d.cmdline" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\csc.exe | sdiagnhost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Visual C# Command Line Compiler Exit code: 0 Version: 8.0.50727.4927 (NetFXspW7.050727-4900) Modules
| |||||||||||||||
| 856 | C:\Windows\Microsoft.NET\Framework\v2.0.50727\cvtres.exe /NOLOGO /READONLY /MACHINE:IX86 "/OUT:C:\Users\admin\AppData\Local\Temp\RESFC4C.tmp" "c:\Users\admin\AppData\Local\Temp\CSCFC4B.tmp" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\cvtres.exe | — | csc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft® Resource File To COFF Object Conversion Utility Exit code: 0 Version: 8.00.50727.4940 (Win7SP1.050727-5400) Modules
| |||||||||||||||
Total events
12 514
Read events
4 229
Write events
2 272
Delete events
6 013
Modification events
| (PID) Process: | (2636) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 1544-13226773946473000 |
Value: 259 | |||
| (PID) Process: | (1544) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1544) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (1544) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (1544) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (1544) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1544) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (1544) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (1544) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3120-13213713943555664 |
Value: 0 | |||
| (PID) Process: | (1544) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
1 755
Suspicious files
238
Text files
2 031
Unknown types
471
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1544 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5E4FFCBA-608.pma | — | |
MD5:— | SHA256:— | |||
| 1544 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000028.dbtmp | — | |
MD5:— | SHA256:— | |||
| 1544 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\f5ba415a-333d-4478-ab9e-0989dde5b5cf.tmp | — | |
MD5:— | SHA256:— | |||
| 3632 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\CrashpadMetrics.pma | binary | |
MD5:9543068B6751E1F3E11F91D72EE78D95 | SHA256:D060AD21AE6E04CB58668CAA52ADFCA573E018102CC07554D2ED3EAE11AB7785 | |||
| 1544 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RFa66c01.TMP | text | |
MD5:— | SHA256:— | |||
| 1544 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 1544 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 1544 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RFa66c20.TMP | text | |
MD5:— | SHA256:— | |||
| 1544 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1544 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RFa66d78.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
20
DNS requests
14
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3148 | chrome.exe | GET | 302 | 172.217.23.110:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 514 b | whitelisted |
3148 | chrome.exe | GET | 302 | 172.217.23.110:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 509 b | whitelisted |
3148 | chrome.exe | GET | 200 | 23.210.248.197:80 | http://download.microsoft.com/download/7/E/9/7E9188C0-2511-4B01-8B4E-0A641EC2F600/MicrosoftProgram_Install_and_Uninstall.meta.diagcab | NL | compressed | 216 Kb | whitelisted |
3148 | chrome.exe | GET | 200 | 173.194.139.6:80 | http://r1---sn-aigzrn7k.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx?cms_redirect=yes&mip=185.43.110.12&mm=28&mn=sn-aigzrn7k&ms=nvh&mt=1582300462&mv=m&mvi=0&pl=27&shardbypass=yes | US | crx | 293 Kb | whitelisted |
3148 | chrome.exe | GET | 200 | 173.194.139.6:80 | http://r1---sn-aigzrn7k.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mip=185.43.110.12&mm=28&mn=sn-aigzrn7k&ms=nvh&mt=1582300462&mv=m&mvi=0&pl=27&shardbypass=yes | US | crx | 862 Kb | whitelisted |
3148 | chrome.exe | GET | 304 | 23.210.248.197:80 | http://download.microsoft.com/download/7/E/9/7E9188C0-2511-4B01-8B4E-0A641EC2F600/MicrosoftProgram_Install_and_Uninstall.meta.diagcab | NL | compressed | 216 Kb | whitelisted |
3148 | chrome.exe | GET | 304 | 23.210.248.197:80 | http://download.microsoft.com/download/7/E/9/7E9188C0-2511-4B01-8B4E-0A641EC2F600/MicrosoftProgram_Install_and_Uninstall.meta.diagcab | NL | compressed | 216 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3148 | chrome.exe | 172.217.22.99:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3148 | chrome.exe | 23.210.248.197:80 | download.microsoft.com | Akamai International B.V. | NL | whitelisted |
3148 | chrome.exe | 216.58.207.36:443 | www.google.com | Google Inc. | US | whitelisted |
3148 | chrome.exe | 172.217.18.163:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
3148 | chrome.exe | 172.217.16.195:443 | www.gstatic.com | Google Inc. | US | whitelisted |
3148 | chrome.exe | 172.217.21.234:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
3148 | chrome.exe | 172.217.23.109:443 | accounts.google.com | Google Inc. | US | suspicious |
3148 | chrome.exe | 173.194.139.6:80 | r1---sn-aigzrn7k.gvt1.com | Google Inc. | US | whitelisted |
3148 | chrome.exe | 172.217.23.110:80 | redirector.gvt1.com | Google Inc. | US | whitelisted |
3148 | chrome.exe | 172.217.23.97:443 | clients2.googleusercontent.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
download.microsoft.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com |
| malicious |
ssl.gstatic.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
clients1.google.com |
| whitelisted |
clients2.google.com |
| whitelisted |
redirector.gvt1.com |
| whitelisted |
r1---sn-aigzrn7k.gvt1.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3148 | chrome.exe | Generic Protocol Command Decode | SURICATA HTTP unable to match response to request |
3148 | chrome.exe | Generic Protocol Command Decode | SURICATA HTTP unable to match response to request |
3148 | chrome.exe | Generic Protocol Command Decode | SURICATA HTTP unable to match response to request |
Process | Message |
|---|---|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
csc.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|