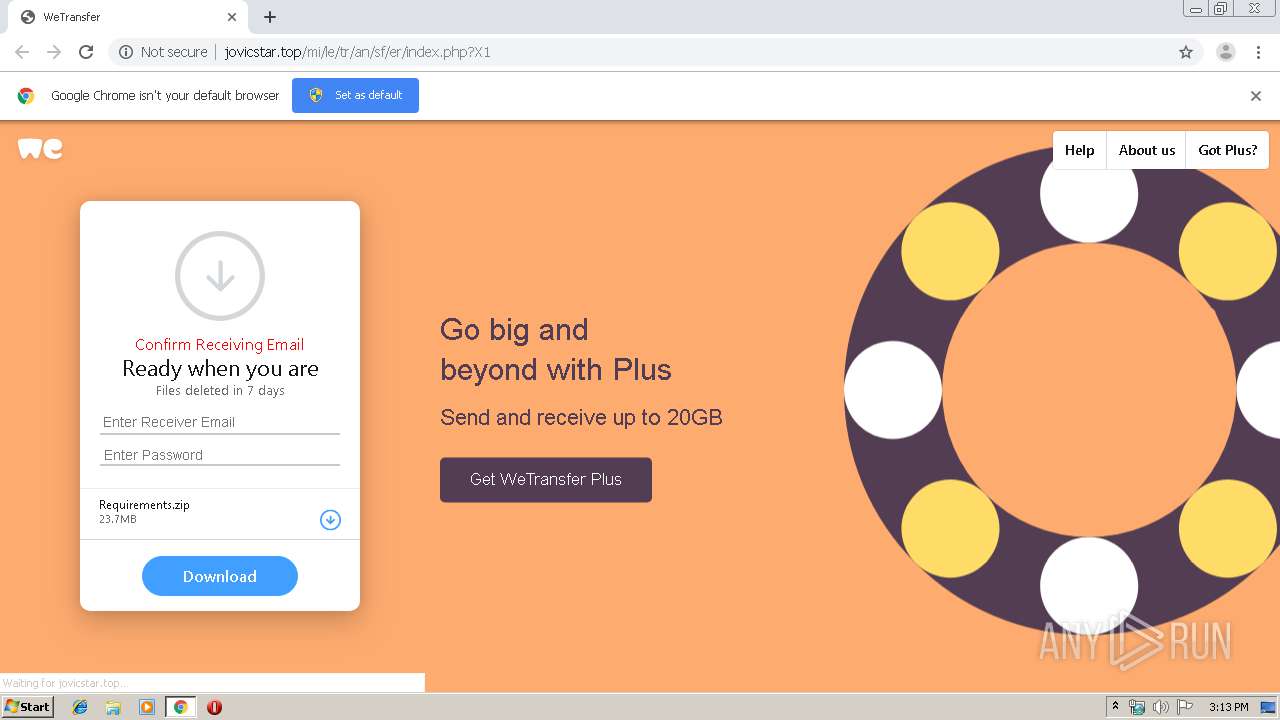
| URL: | http://jovicstar.top/mi/le/tr/an/sf/er/index.php?X1 |
| Full analysis: | https://app.any.run/tasks/1f1de68d-18dc-4e94-b2b7-142a2e8c9b7b |
| Verdict: | Malicious activity |
| Analysis date: | July 11, 2019, 14:12:59 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | CE959E2E3F32E0E4E0962FCBD79AC5CB |
| SHA1: | 6D5C43CDAC5779931DA4C29B025C153EE3FF3562 |
| SHA256: | D8FBB8F8808A5199E211371C0507733F3666E112C4479888AFBBB9E16232753D |
| SSDEEP: | 3:N1KUIMEb1aCHz:CUO1PHz |
MALICIOUS
No malicious indicators.SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 3104)
INFO
Application launched itself
- chrome.exe (PID: 3104)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
55
Monitored processes
20
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1332 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1032,17962473826454419857,8045169081680778509,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=5058837844857036315 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2452 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1900 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1032,17962473826454419857,8045169081680778509,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=12709383517424264929 --mojo-platform-channel-handle=3652 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1996 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1032,17962473826454419857,8045169081680778509,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=6825941864164161957 --mojo-platform-channel-handle=3536 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2180 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1032,17962473826454419857,8045169081680778509,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=9720794653339027564 --mojo-platform-channel-handle=3504 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2252 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1032,17962473826454419857,8045169081680778509,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=11959801087912451943 --mojo-platform-channel-handle=968 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2552 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1032,17962473826454419857,8045169081680778509,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=4922939331700159528 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2232 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2564 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1032,17962473826454419857,8045169081680778509,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=11660352108484198880 --mojo-platform-channel-handle=3516 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2588 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1032,17962473826454419857,8045169081680778509,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=13533193017708474117 --mojo-platform-channel-handle=1596 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2608 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1032,17962473826454419857,8045169081680778509,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=1361346929629996991 --mojo-platform-channel-handle=3640 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2712 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1032,17962473826454419857,8045169081680778509,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=2301942038413146515 --mojo-platform-channel-handle=2784 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
614
Read events
526
Write events
83
Delete events
5
Modification events
| (PID) Process: | (3104) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3104) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3104) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3104) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3104) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3012) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 3104-13207327994408375 |
Value: 259 | |||
| (PID) Process: | (3104) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3104) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3104) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (3104) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 1512-13197841398593750 |
Value: 0 | |||
Executable files
0
Suspicious files
12
Text files
140
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3104 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\837de2b9-4de1-4ac0-bcfa-02afa48b5ba2.tmp | — | |
MD5:— | SHA256:— | |||
| 3104 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000020.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3104 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF100baa.TMP | text | |
MD5:— | SHA256:— | |||
| 3104 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3104 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3104 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF100baa.TMP | text | |
MD5:— | SHA256:— | |||
| 3104 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:9C016064A1F864C8140915D77CF3389A | SHA256:0E7265D4A8C16223538EDD8CD620B8820611C74538E420A88E333BE7F62AC787 | |||
| 3104 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 3104 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF100be9.TMP | text | |
MD5:— | SHA256:— | |||
| 3104 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\AvailabilityDB\LOG.old | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
28
TCP/UDP connections
22
DNS requests
13
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2588 | chrome.exe | GET | 404 | 91.234.99.225:80 | http://jovicstar.top/mi/le/tr/an/sf/er/wallpaper-toolbox-0.4.0.js.html | NL | html | 366 b | suspicious |
2588 | chrome.exe | GET | 404 | 91.234.99.225:80 | http://jovicstar.top/mi/le/tr/an/sf/er/images/texture.html | NL | html | 354 b | suspicious |
2588 | chrome.exe | GET | 404 | 91.234.99.225:80 | http://jovicstar.top/mi/le/tr/an/sf/er/_https_/backgrounds.wetransfer.net/plus/201708/size_orange_v1/images/1px.html | NL | html | 412 b | suspicious |
2588 | chrome.exe | GET | 404 | 91.234.99.225:80 | http://jovicstar.top/mi/le/tr/an/sf/er/fonts/FreightSans-Pro-Semibold.html | NL | html | 370 b | suspicious |
2588 | chrome.exe | GET | 404 | 91.234.99.225:80 | http://jovicstar.top/mi/le/tr/an/sf/er/jquery.min.js.html | NL | html | 353 b | suspicious |
2588 | chrome.exe | GET | 404 | 91.234.99.225:80 | http://jovicstar.top/mi/le/tr/an/sf/er/WeTransfer_files/analytics.js.html | NL | html | 369 b | suspicious |
2588 | chrome.exe | GET | 200 | 91.234.99.225:80 | http://jovicstar.top/mi/le/tr/an/sf/er/index.php?X1 | NL | html | 8.82 Kb | suspicious |
2588 | chrome.exe | GET | 404 | 91.234.99.225:80 | http://jovicstar.top/mi/le/tr/an/sf/er/WeTransfer_files/bWqOLA69nu2fsMi45LjA.js.html | NL | html | 380 b | suspicious |
2588 | chrome.exe | GET | 404 | 91.234.99.225:80 | http://jovicstar.top/mi/le/tr/an/sf/er/WeTransfer_files/gtm.js.html | NL | html | 363 b | suspicious |
2588 | chrome.exe | GET | 200 | 91.234.99.225:80 | http://jovicstar.top/mi/le/tr/an/sf/er/bg.html | NL | html | 18.1 Kb | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2588 | chrome.exe | 91.234.99.225:80 | jovicstar.top | MAROSNET Telecommunication Company LLC | NL | suspicious |
2588 | chrome.exe | 172.217.23.174:443 | clients1.google.com | Google Inc. | US | whitelisted |
— | — | 172.217.21.193:443 | clients2.googleusercontent.com | Google Inc. | US | whitelisted |
2588 | chrome.exe | 216.58.206.3:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2588 | chrome.exe | 216.58.208.45:443 | accounts.google.com | Google Inc. | US | whitelisted |
2588 | chrome.exe | 54.192.94.125:443 | cdn.wetransfer.net | Amazon.com, Inc. | US | whitelisted |
2588 | chrome.exe | 205.185.216.10:80 | www.download.windowsupdate.com | Highwinds Network Group, Inc. | US | whitelisted |
2588 | chrome.exe | 52.85.182.94:80 | x.ss2.us | Amazon.com, Inc. | US | whitelisted |
2588 | chrome.exe | 172.217.23.142:443 | clients2.google.com | Google Inc. | US | whitelisted |
2588 | chrome.exe | 172.217.22.36:443 | www.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
jovicstar.top |
| suspicious |
accounts.google.com |
| shared |
clients1.google.com |
| whitelisted |
cdn.wetransfer.net |
| whitelisted |
x.ss2.us |
| whitelisted |
www.download.windowsupdate.com |
| whitelisted |
clients2.google.com |
| whitelisted |
www.google.com |
| malicious |
ssl.gstatic.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1044 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a *.top domain - Likely Hostile |
2588 | chrome.exe | Potentially Bad Traffic | ET INFO HTTP Request to a *.top domain |
2588 | chrome.exe | A Network Trojan was detected | ET INFO Possible Phish - Mirrored Website Comment Observed |