| File name: | Nursultan Client 1.16.5 CRACK.exe |
| Full analysis: | https://app.any.run/tasks/958f6ecb-300e-482a-a256-ad19f882156c |
| Verdict: | Malicious activity |
| Threats: | DCrat, also known as Dark Crystal RAT, is a remote access trojan (RAT), which was first introduced in 2018. It is a modular malware that can be customized to perform different tasks. For instance, it can steal passwords, crypto wallet information, hijack Telegram and Steam accounts, and more. Attackers may use a variety of methods to distribute DCrat, but phishing email campaigns are the most common. |
| Analysis date: | May 02, 2025, 19:15:55 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows, 3 sections |
| MD5: | 20BE0C0F0FDCC5E6F8254EFCCCB67540 |
| SHA1: | DDE498A4E644A4204F54072BCFF2ACEC4F278098 |
| SHA256: | D8F76A5BC958860507BA2CEA87D16D05F5002B6818FE540A9C233170C2A3240A |
| SSDEEP: | 6144:A+K3sqL7cI07ZkZ8ClmUv2FNc+NadwxF1BEZmYbkrrTv7fO:lXqHcIqZkZ8ClvQ32wxF1gmxrTv |
MALICIOUS
SHEETRAT mutex has been found
- Nursultan Client 1.16.5 CRACK.exe (PID: 6768)
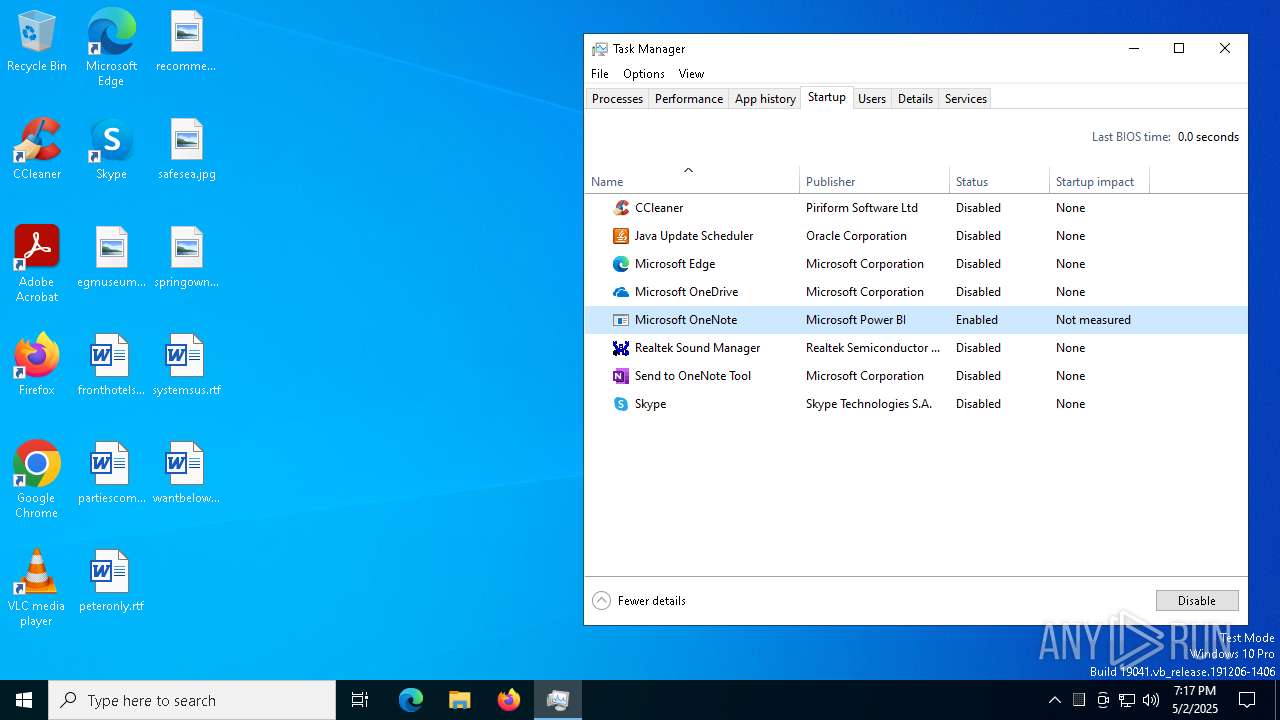
Changes the autorun value in the registry
- Nursultan Client 1.16.5 CRACK.exe (PID: 6768)
Uses Task Scheduler to run other applications
- cmd.exe (PID: 5376)
- cmd.exe (PID: 720)
- cmd.exe (PID: 1328)
- cmd.exe (PID: 6800)
- cmd.exe (PID: 736)
- cmd.exe (PID: 4400)
- cmd.exe (PID: 2980)
- cmd.exe (PID: 2332)
- cmd.exe (PID: 5056)
- cmd.exe (PID: 6800)
- cmd.exe (PID: 2664)
- cmd.exe (PID: 4868)
- cmd.exe (PID: 1328)
- cmd.exe (PID: 1672)
- cmd.exe (PID: 6384)
- cmd.exe (PID: 6800)
- cmd.exe (PID: 3008)
- cmd.exe (PID: 3156)
- cmd.exe (PID: 1912)
- cmd.exe (PID: 632)
- cmd.exe (PID: 3804)
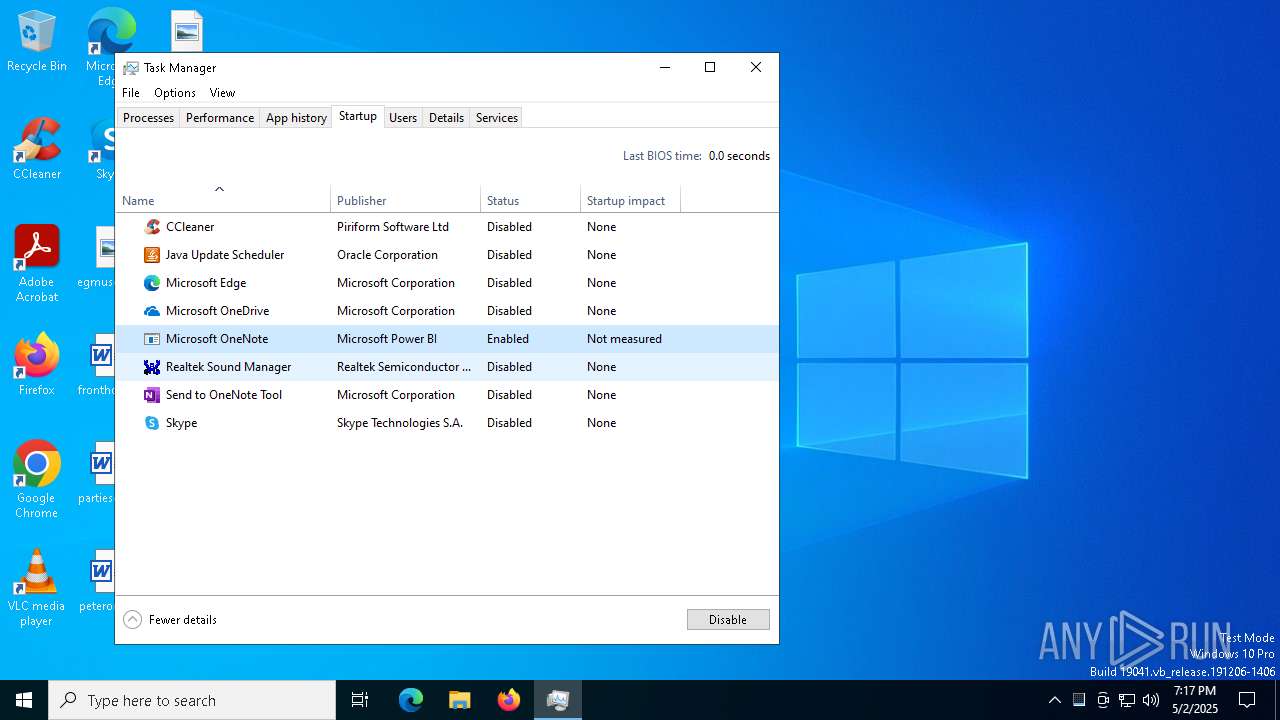
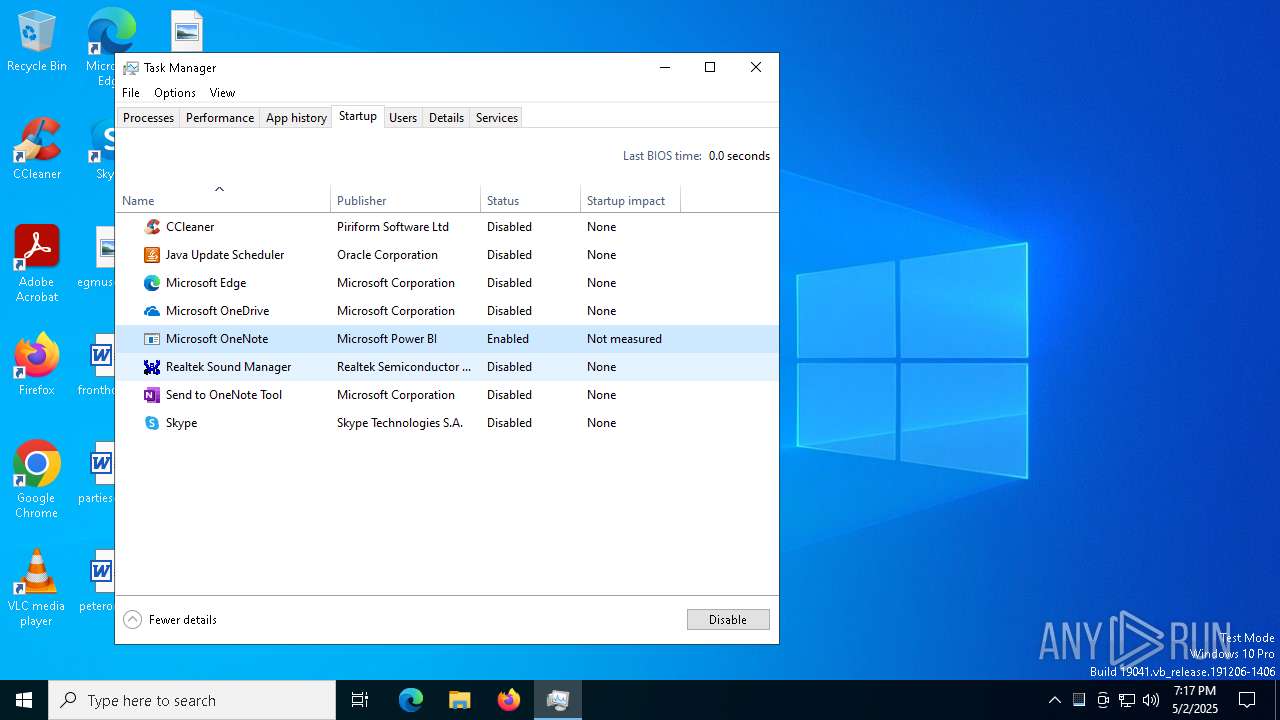
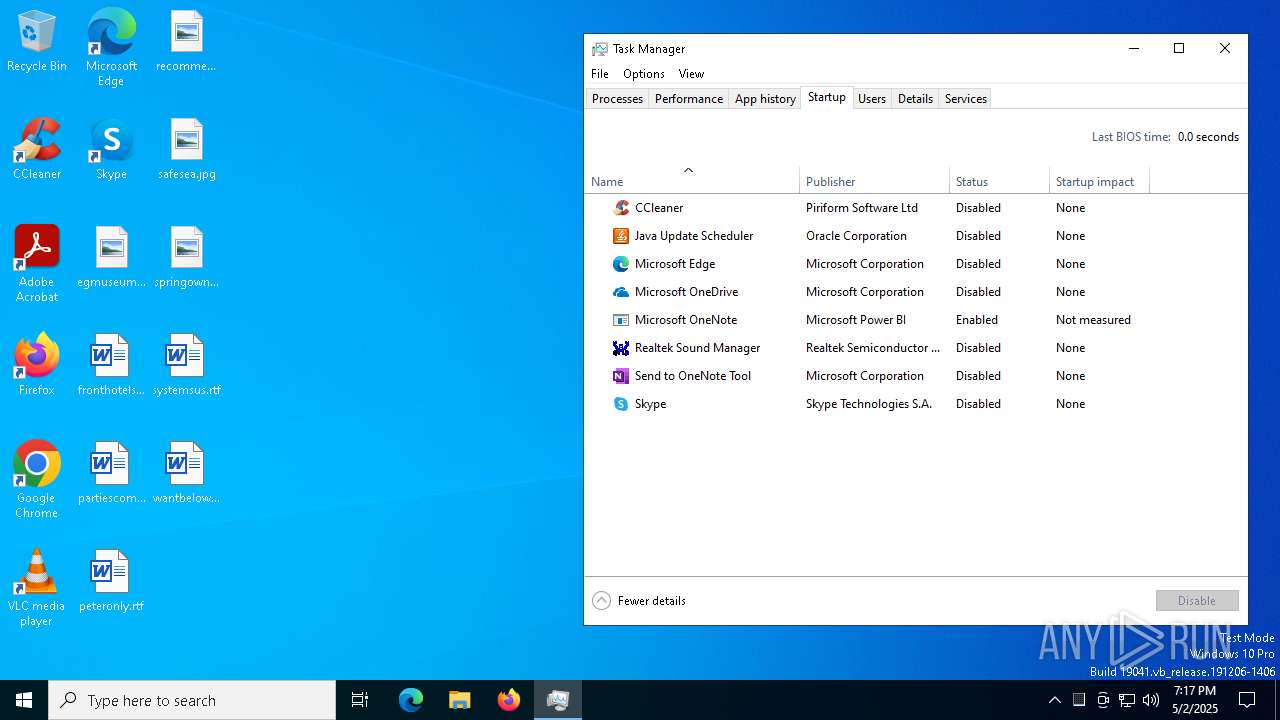
Uses Task Scheduler to autorun other applications
- cmd.exe (PID: 6752)
Changes the login/logoff helper path in the registry
- Nursultan Client 1.16.5 CRACK.exe (PID: 6768)
Changes the AppInit_DLLs value (autorun option)
- Nursultan Client 1.16.5 CRACK.exe (PID: 6768)
DARKCRYSTAL has been detected (SURICATA)
- Nursultan Client 1.16.5 CRACK.exe (PID: 6768)
PURELOGS has been detected (SURICATA)
- Nursultan Client 1.16.5 CRACK.exe (PID: 6768)
Connects to the CnC server
- Nursultan Client 1.16.5 CRACK.exe (PID: 6768)
SHEETRAT has been detected (SURICATA)
- Nursultan Client 1.16.5 CRACK.exe (PID: 6768)
SUSPICIOUS
Reads the date of Windows installation
- Nursultan Client 1.16.5 CRACK.exe (PID: 6640)
Reads security settings of Internet Explorer
- Nursultan Client 1.16.5 CRACK.exe (PID: 6640)
Application launched itself
- Nursultan Client 1.16.5 CRACK.exe (PID: 6640)
Found strings related to reading or modifying Windows Defender settings
- Nursultan Client 1.16.5 CRACK.exe (PID: 6768)
- xdwdMicrosoft SharePoint.exe (PID: 4588)
- xdwdMicrosoft Azure DevOps.exe (PID: 6704)
- xdwdMicrosoft SharePoint.exe (PID: 4264)
- xdwdMicrosoft Azure DevOps.exe (PID: 3812)
Executable content was dropped or overwritten
- Nursultan Client 1.16.5 CRACK.exe (PID: 6768)
Starts CMD.EXE for commands execution
- Nursultan Client 1.16.5 CRACK.exe (PID: 6768)
- xdwdMicrosoft Azure DevOps.exe (PID: 6704)
- xdwdMicrosoft SharePoint.exe (PID: 4588)
- xdwdMicrosoft SharePoint.exe (PID: 4264)
- xdwdMicrosoft Azure DevOps.exe (PID: 3812)
The process checks if it is being run in the virtual environment
- Nursultan Client 1.16.5 CRACK.exe (PID: 6768)
Executes as Windows Service
- WmiApSrv.exe (PID: 2980)
Connects to unusual port
- Nursultan Client 1.16.5 CRACK.exe (PID: 6768)
Contacting a server suspected of hosting an CnC
- Nursultan Client 1.16.5 CRACK.exe (PID: 6768)
The process executes via Task Scheduler
- PLUGScheduler.exe (PID: 4164)
- PLUGScheduler.exe (PID: 4084)
INFO
Checks supported languages
- Nursultan Client 1.16.5 CRACK.exe (PID: 6640)
- Nursultan Client 1.16.5 CRACK.exe (PID: 6768)
Reads the computer name
- Nursultan Client 1.16.5 CRACK.exe (PID: 6640)
- Nursultan Client 1.16.5 CRACK.exe (PID: 6768)
Process checks computer location settings
- Nursultan Client 1.16.5 CRACK.exe (PID: 6640)
Reads the machine GUID from the registry
- Nursultan Client 1.16.5 CRACK.exe (PID: 6640)
- Nursultan Client 1.16.5 CRACK.exe (PID: 6768)
Creates files or folders in the user directory
- Nursultan Client 1.16.5 CRACK.exe (PID: 6768)
Reads CPU info
- Nursultan Client 1.16.5 CRACK.exe (PID: 6768)
Reads the time zone
- Nursultan Client 1.16.5 CRACK.exe (PID: 6768)
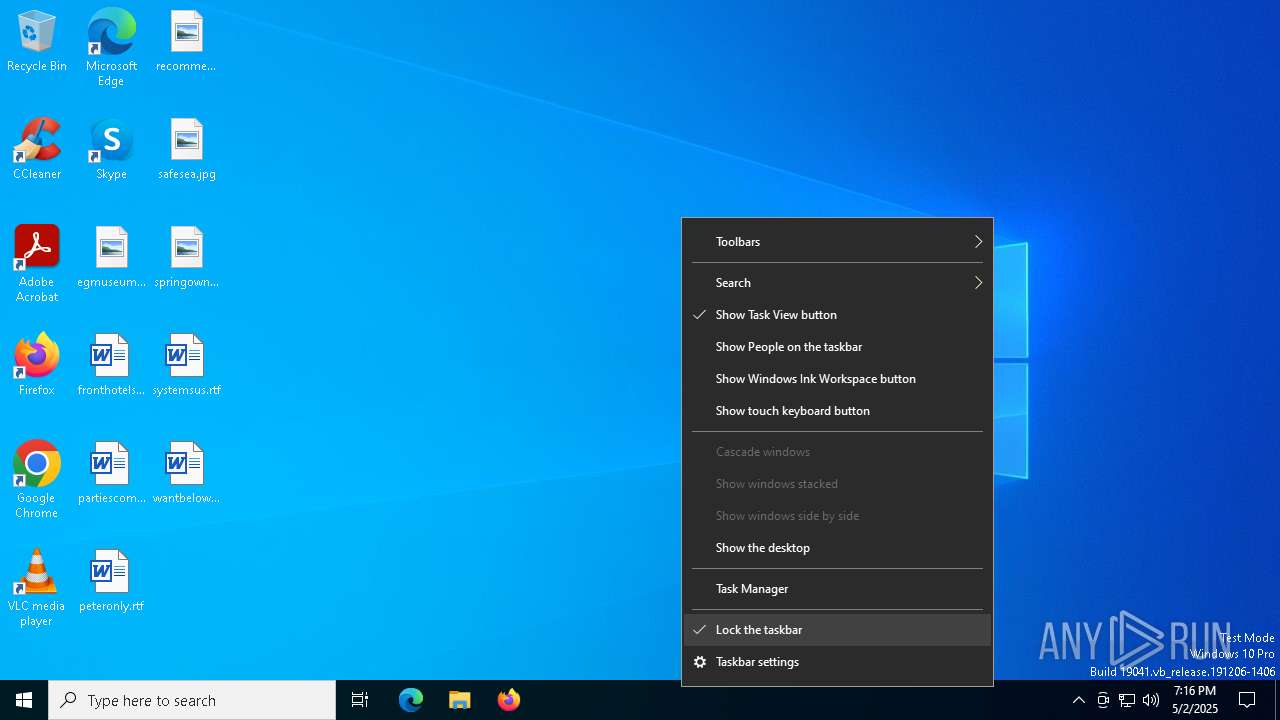
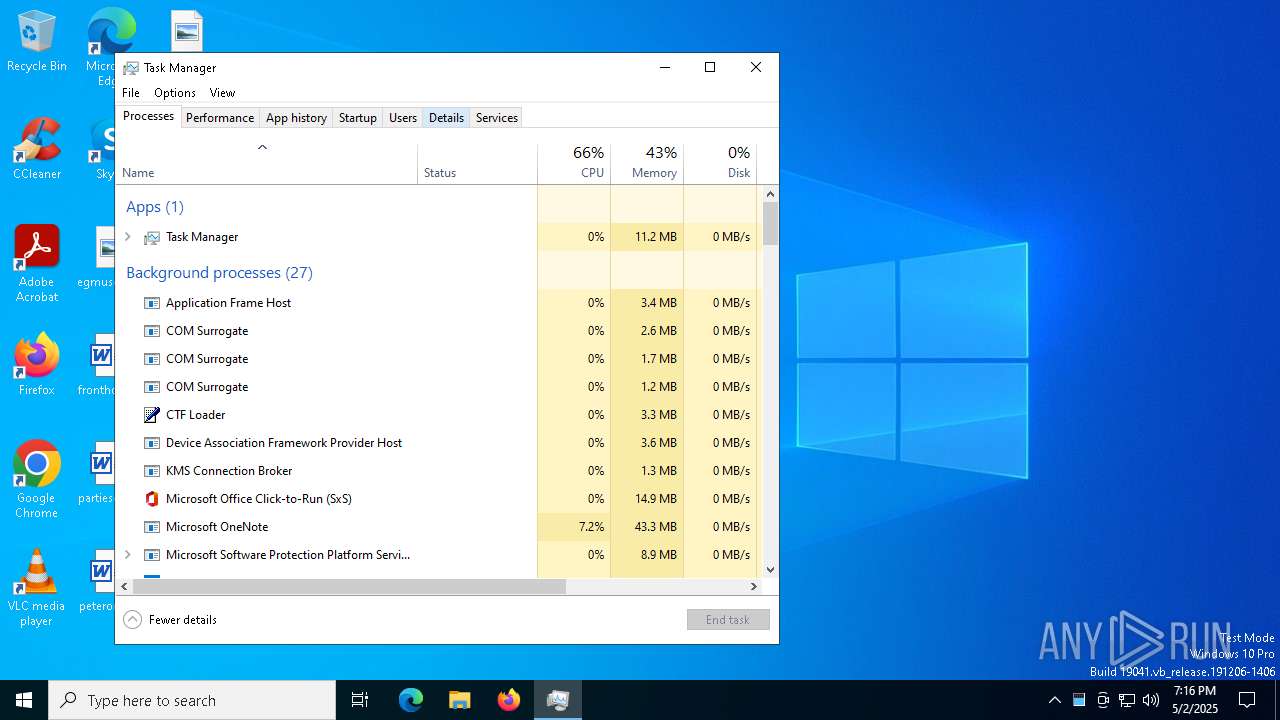
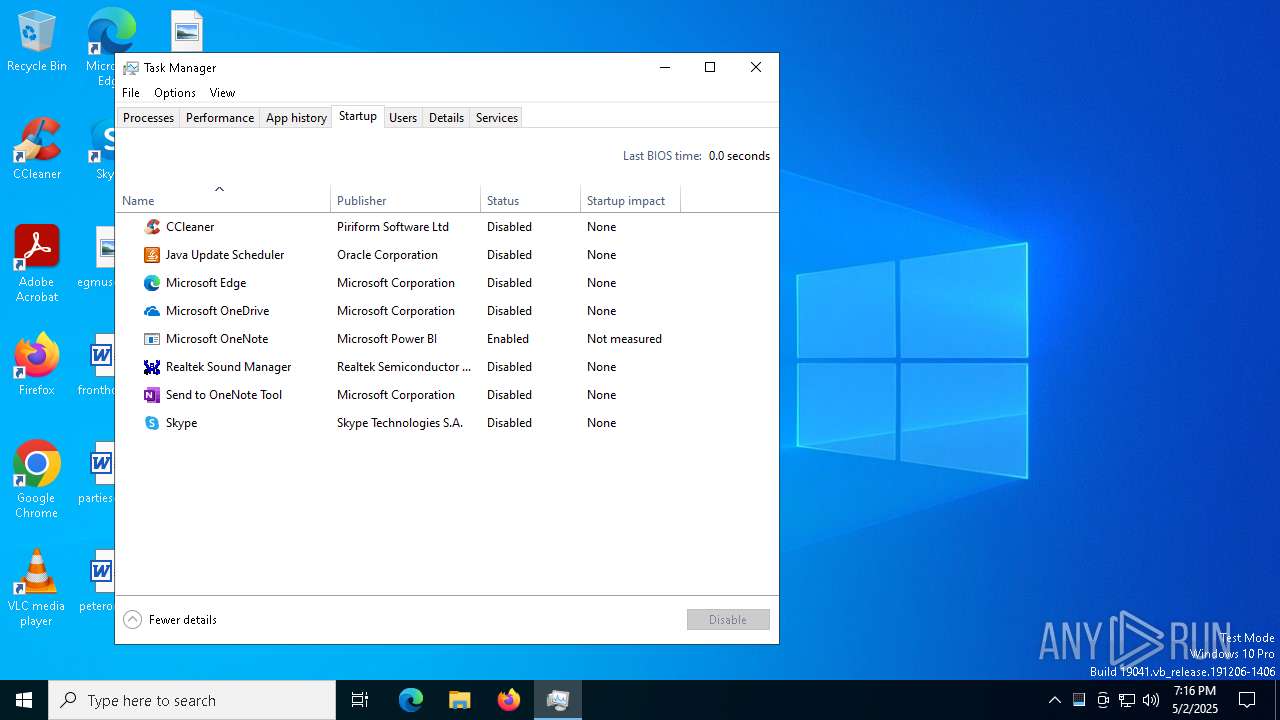
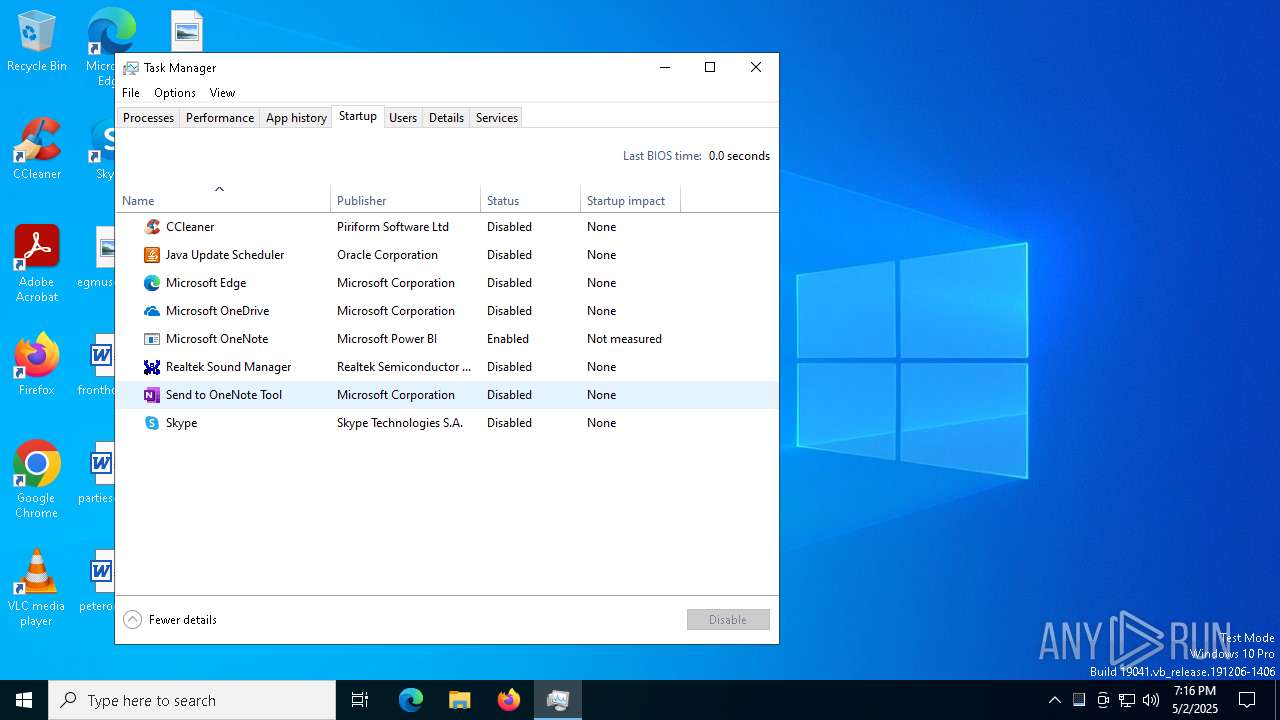
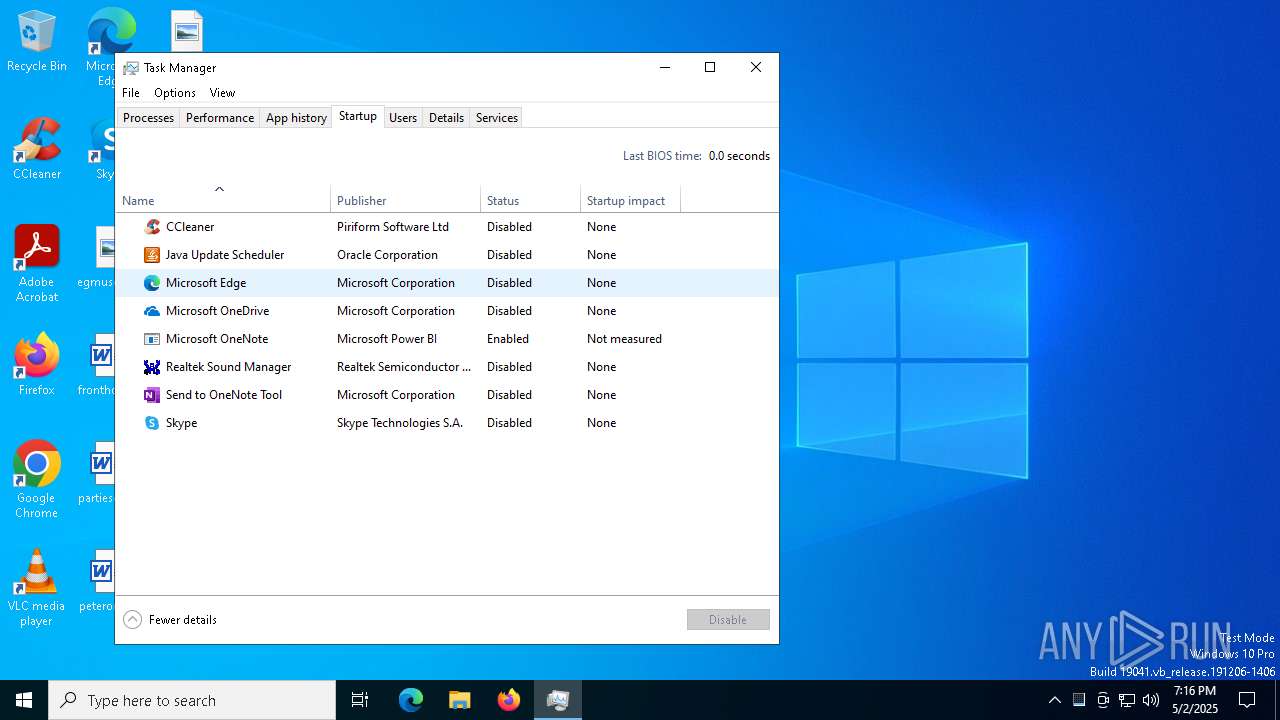
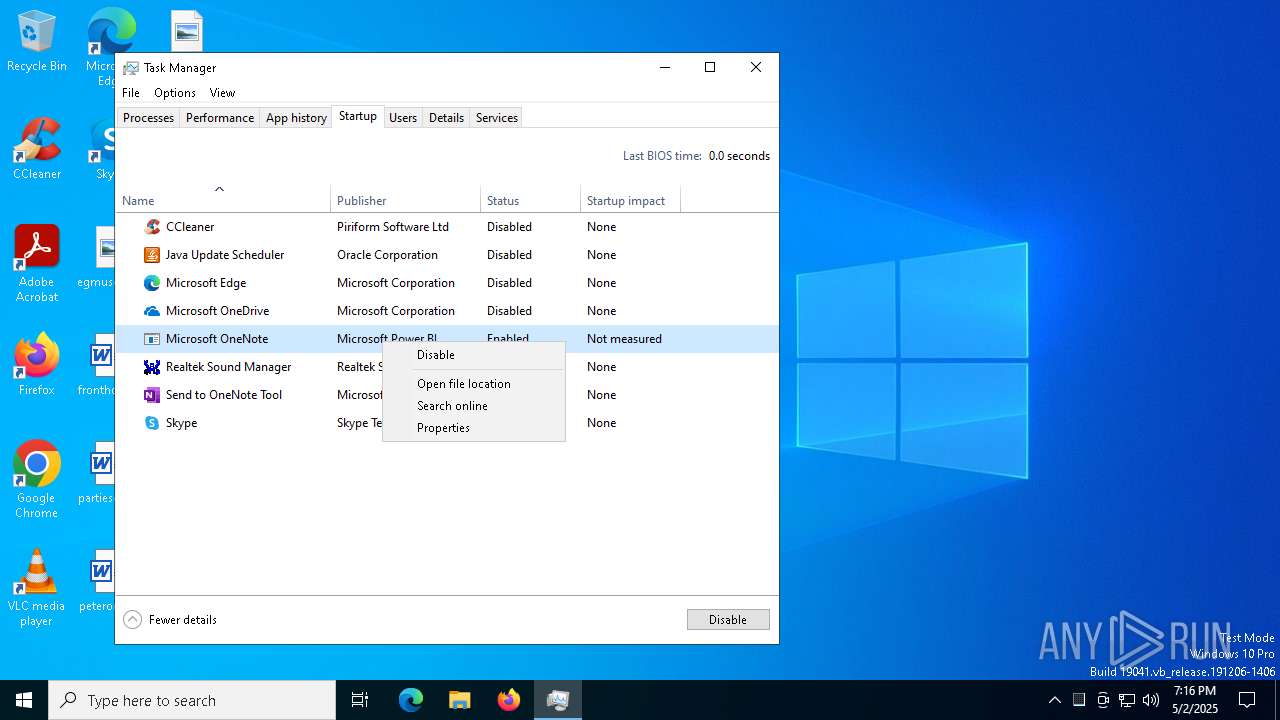
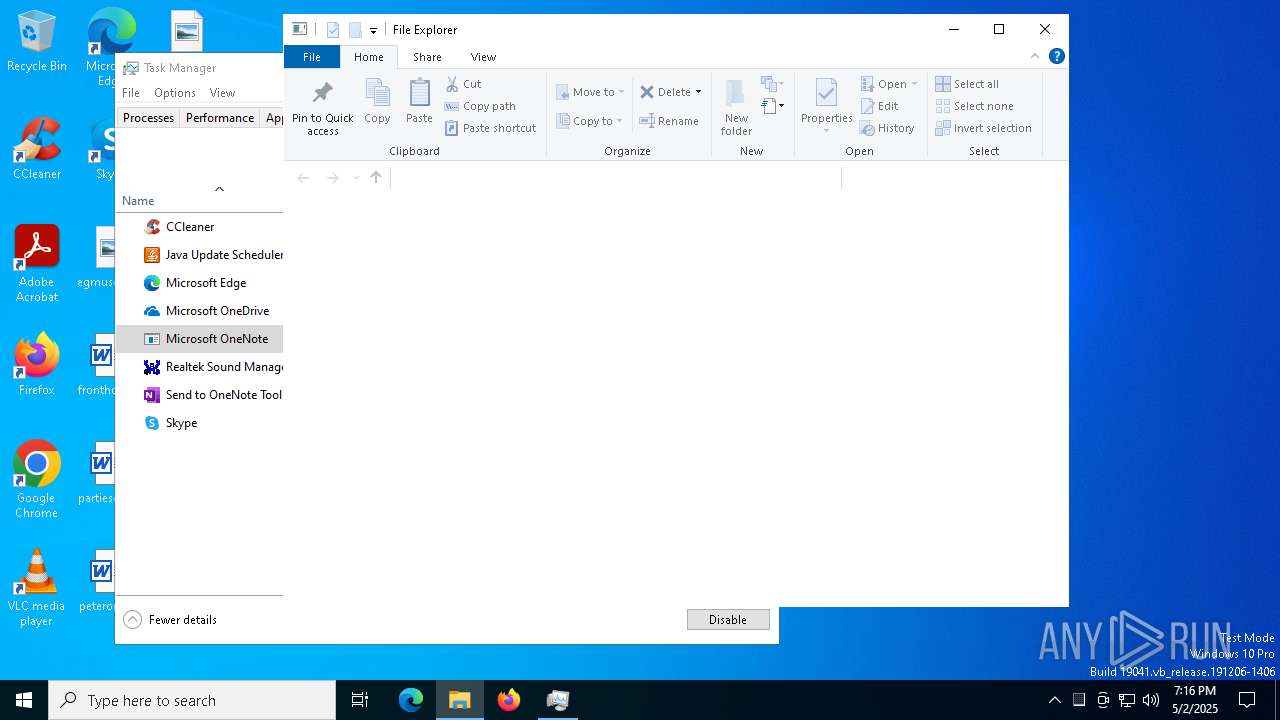
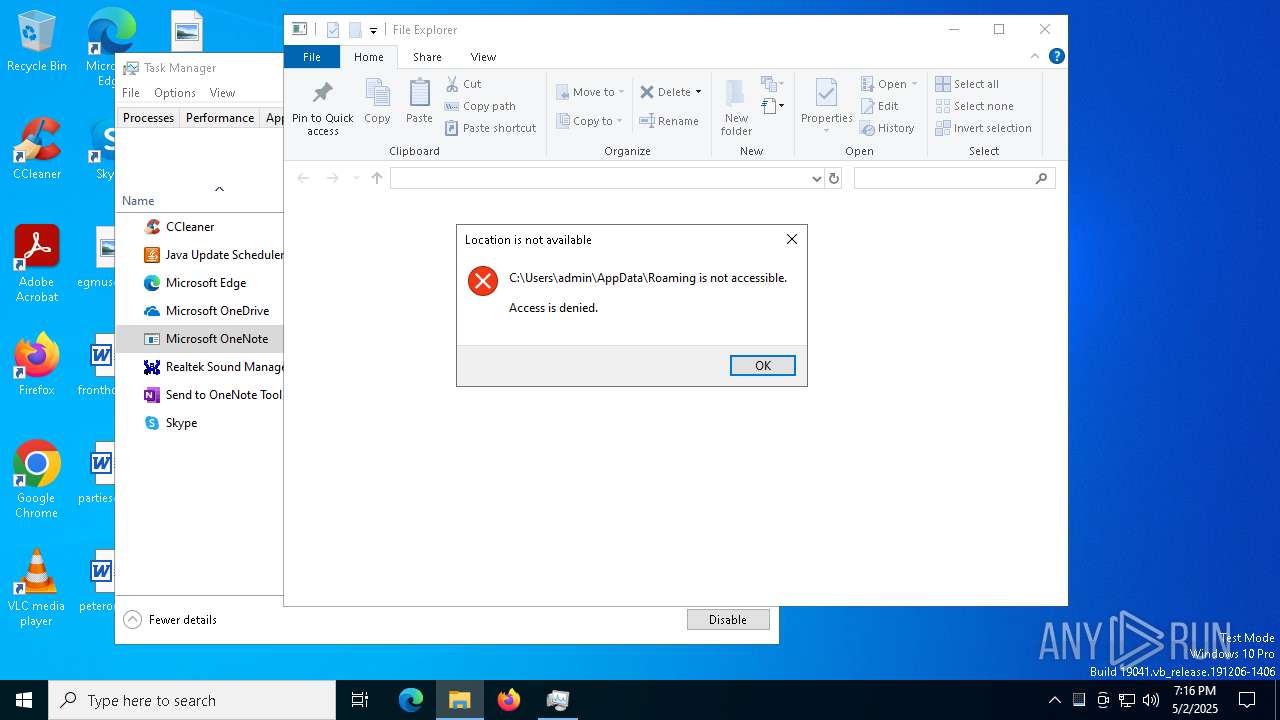
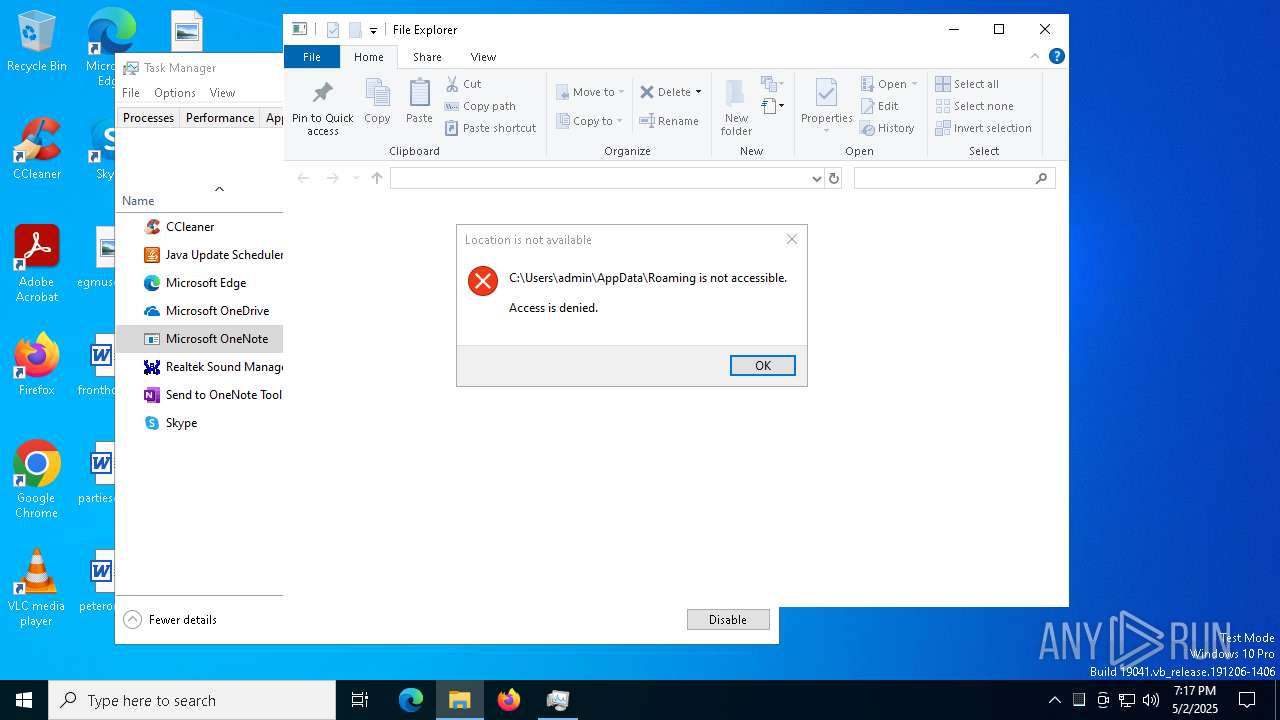
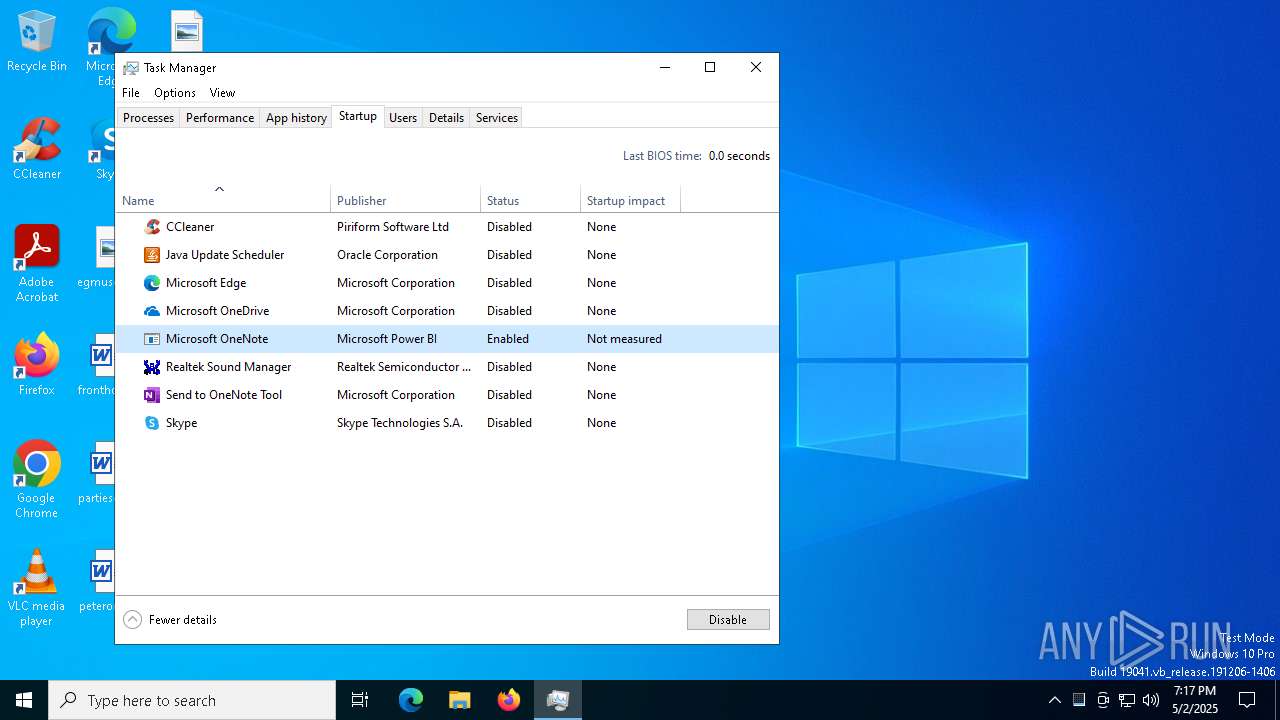
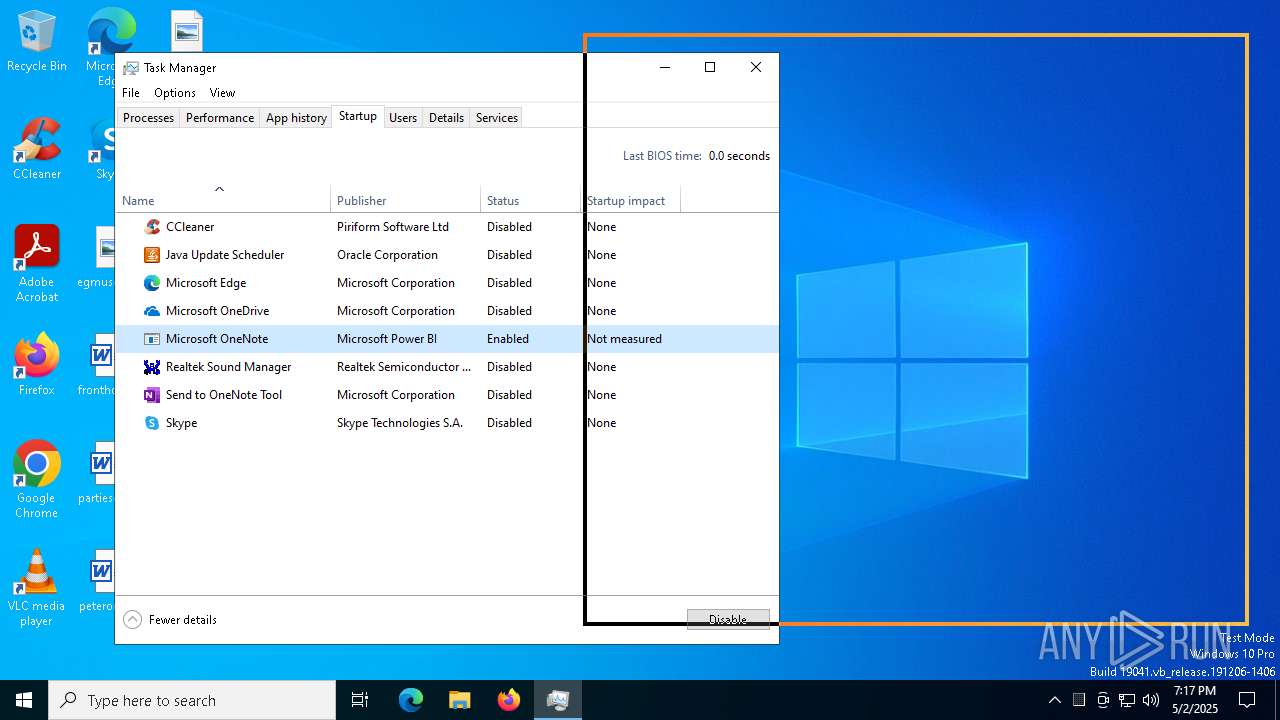
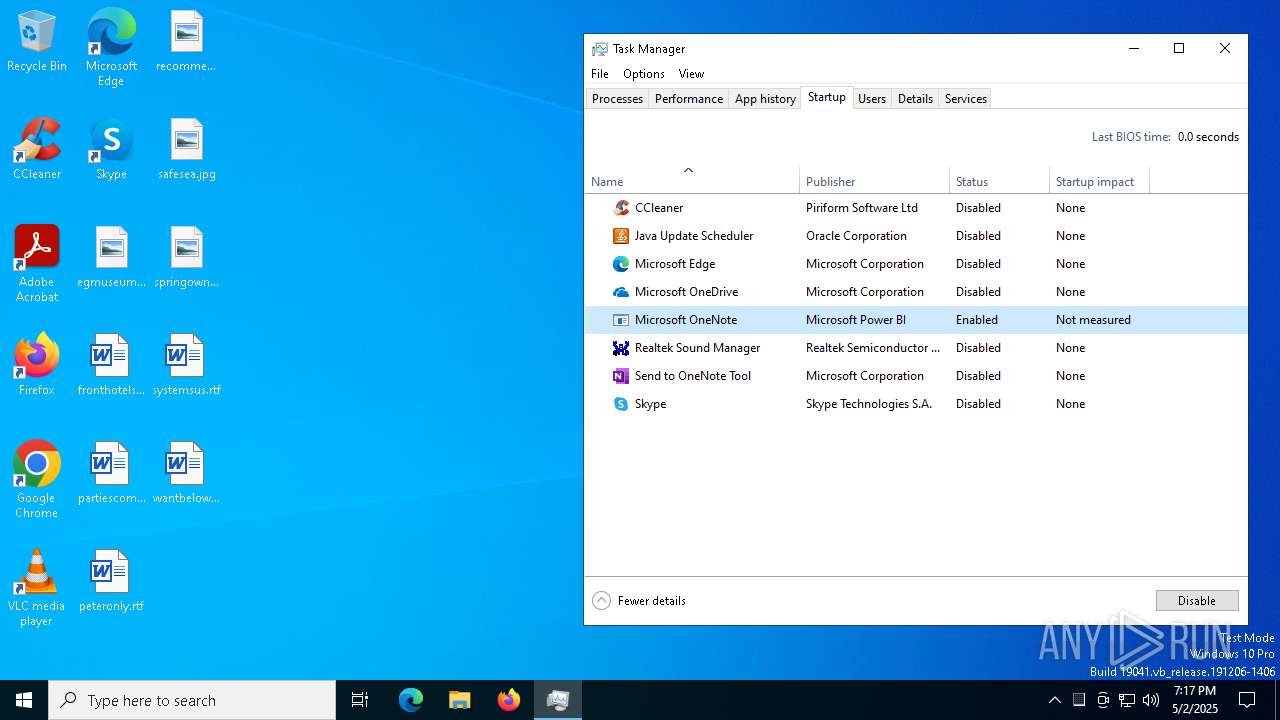
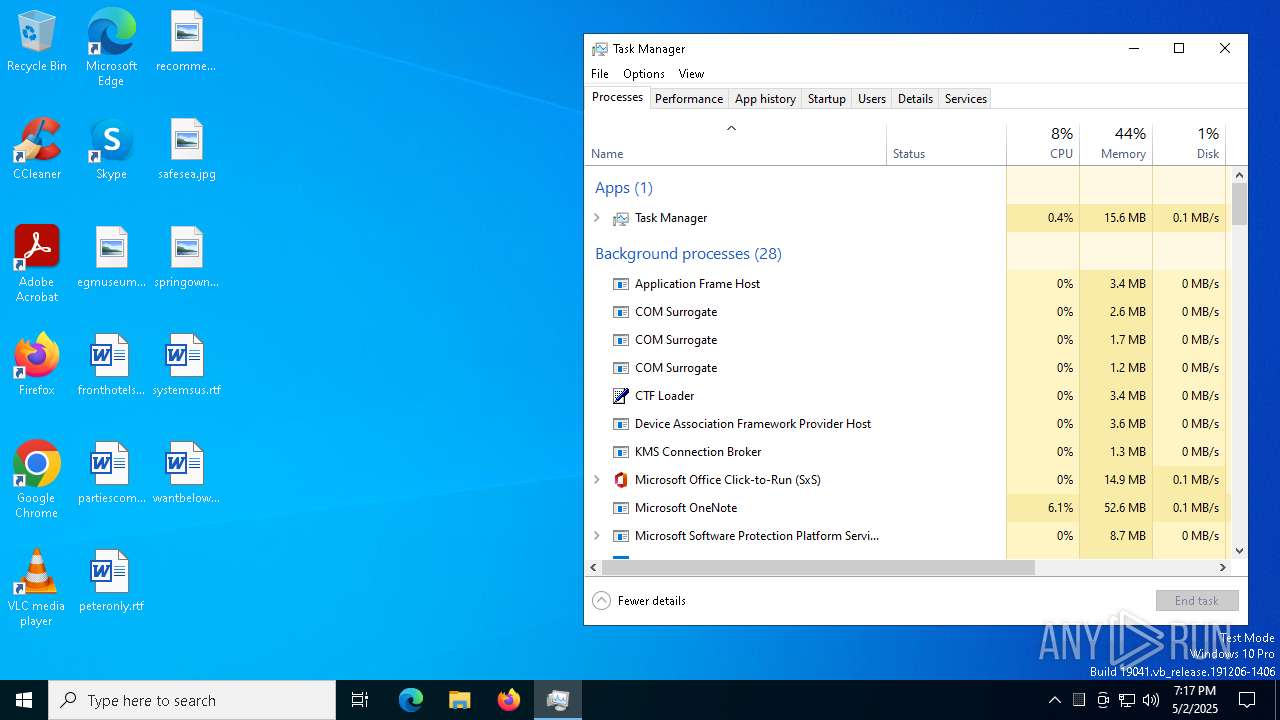
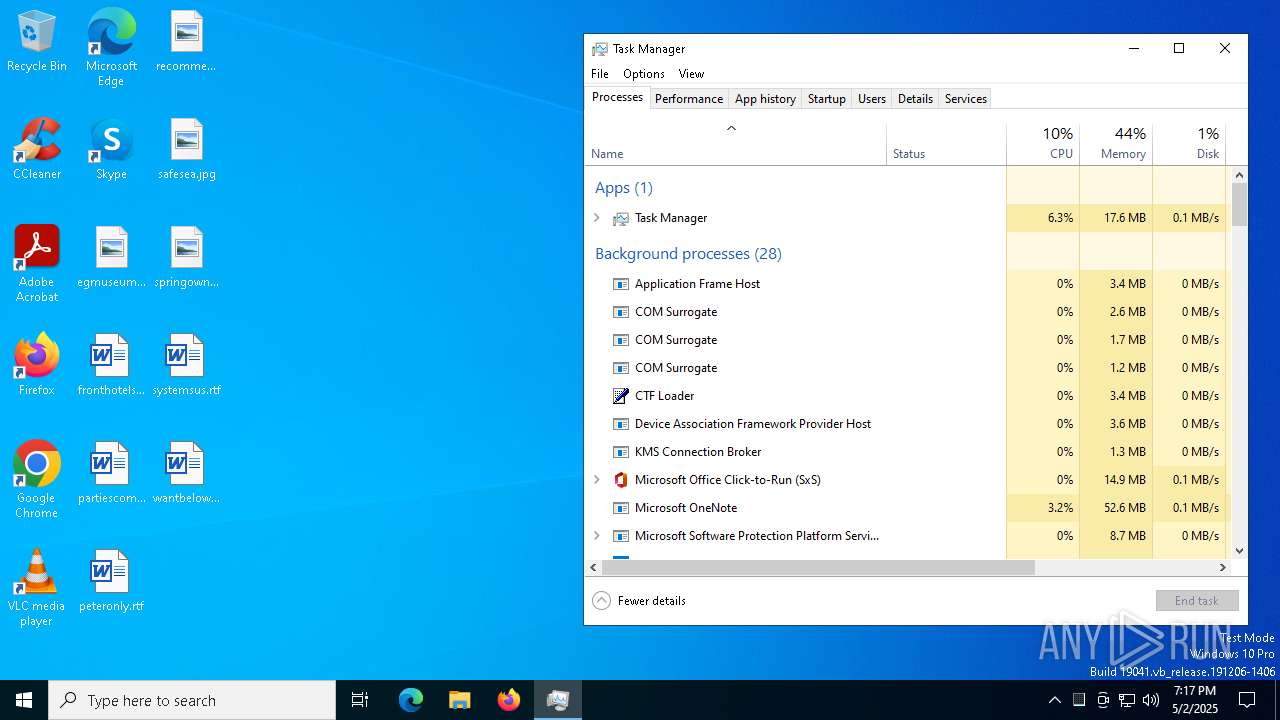
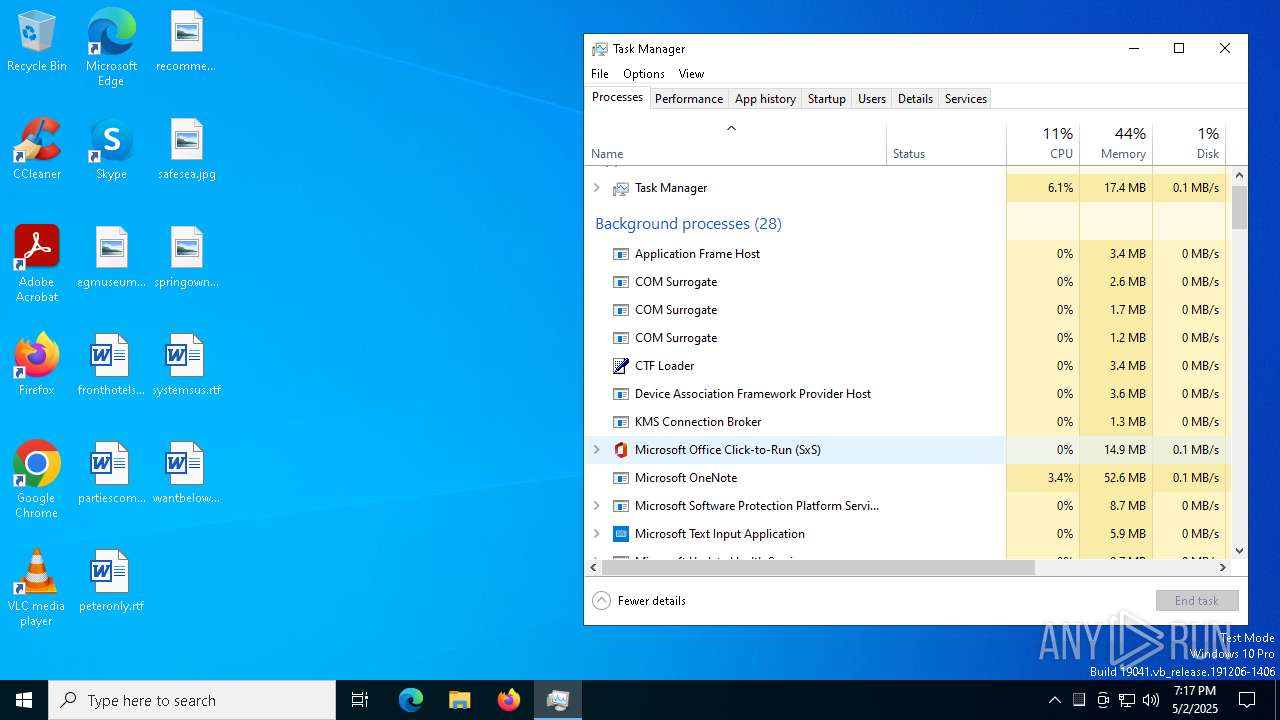
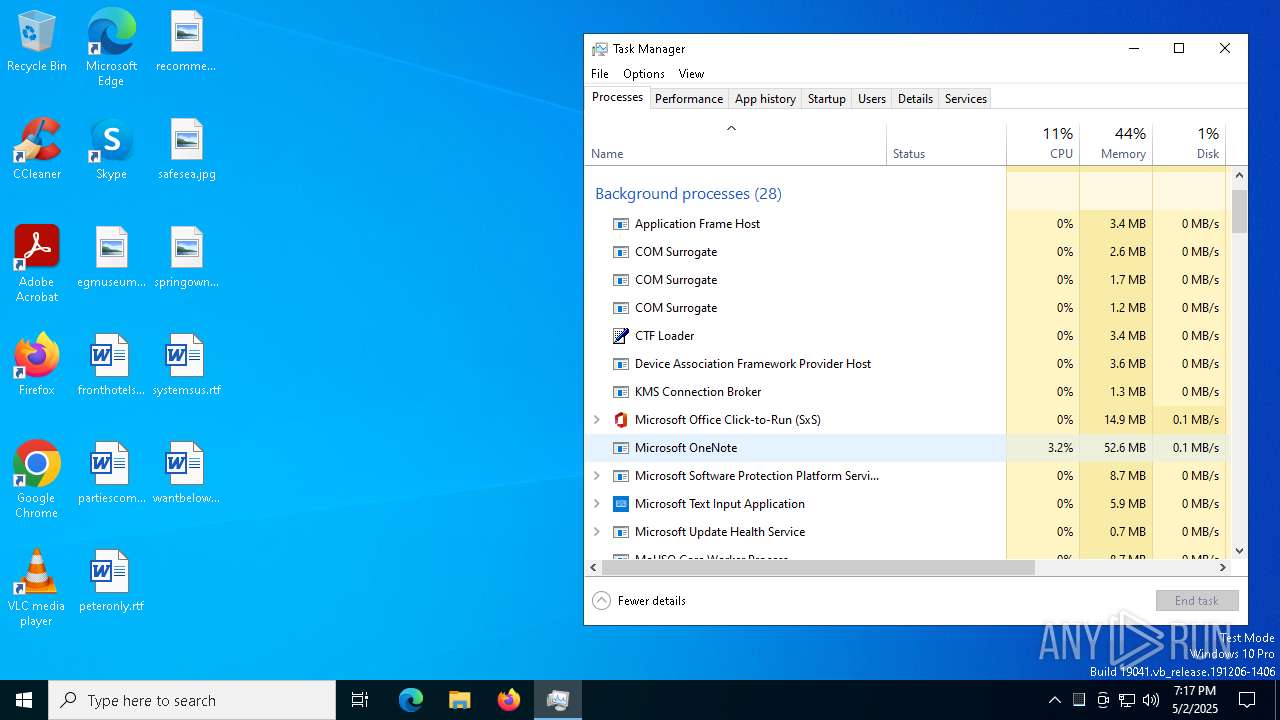
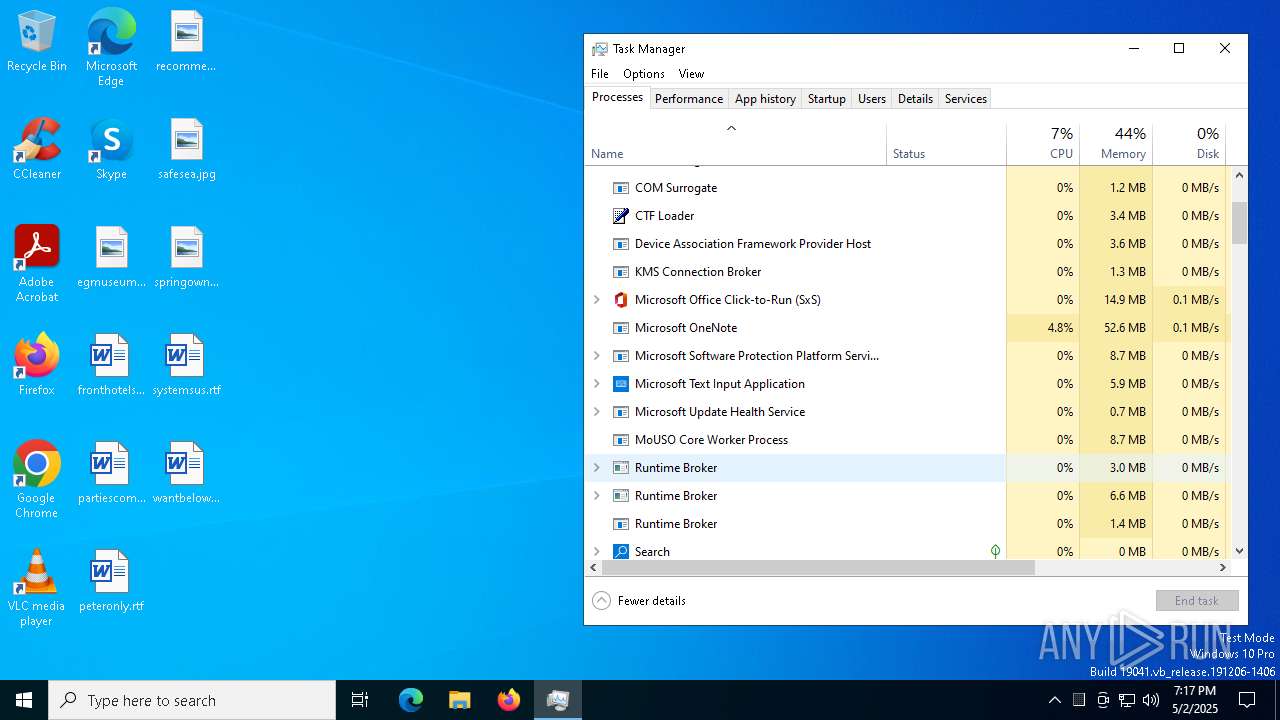
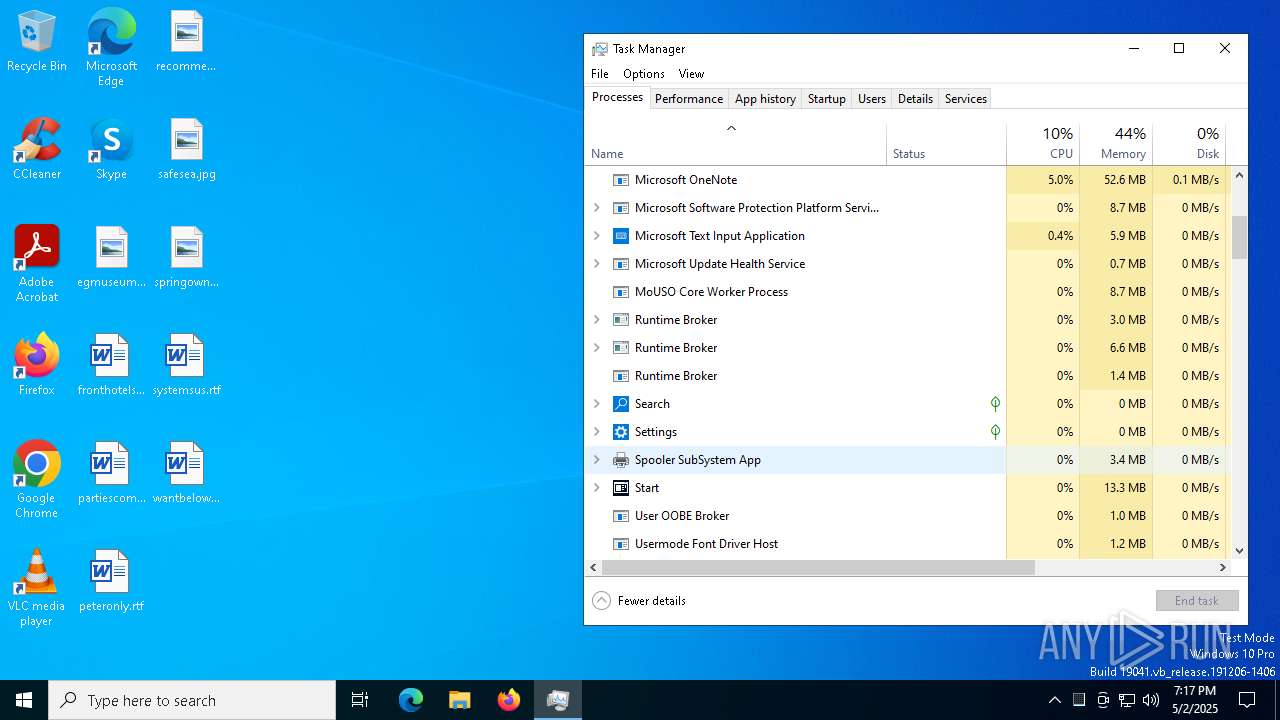
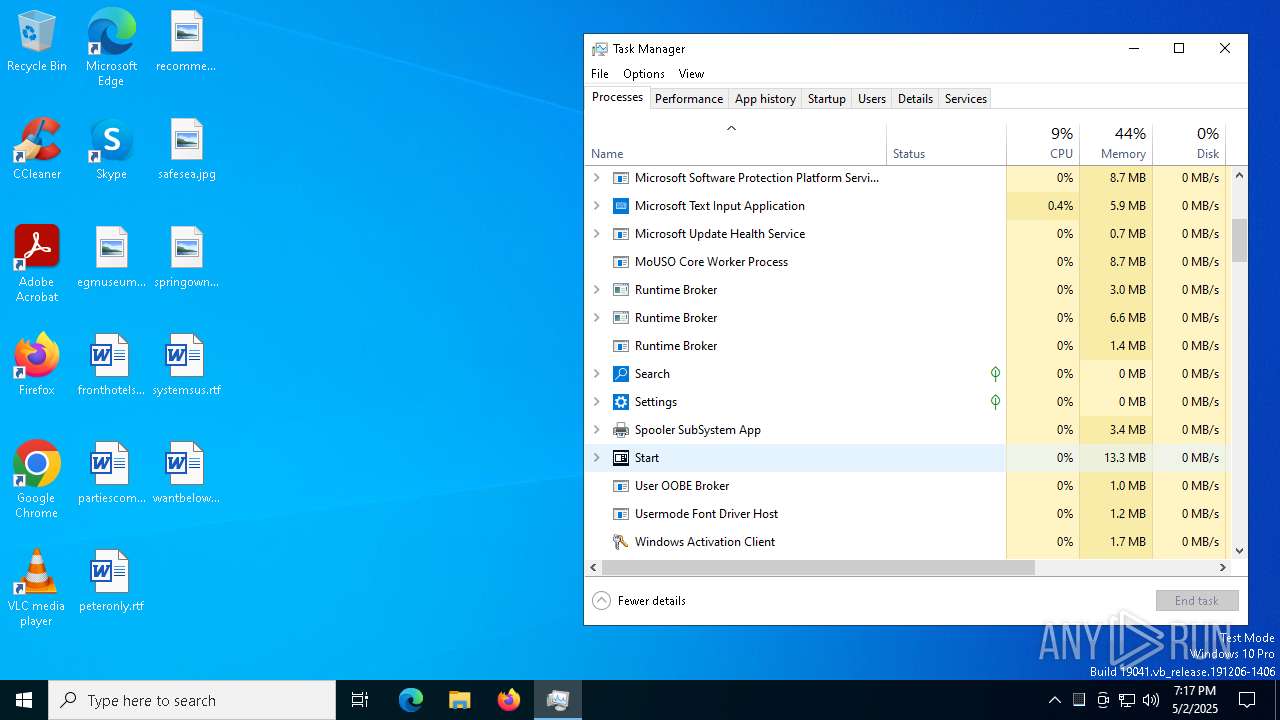
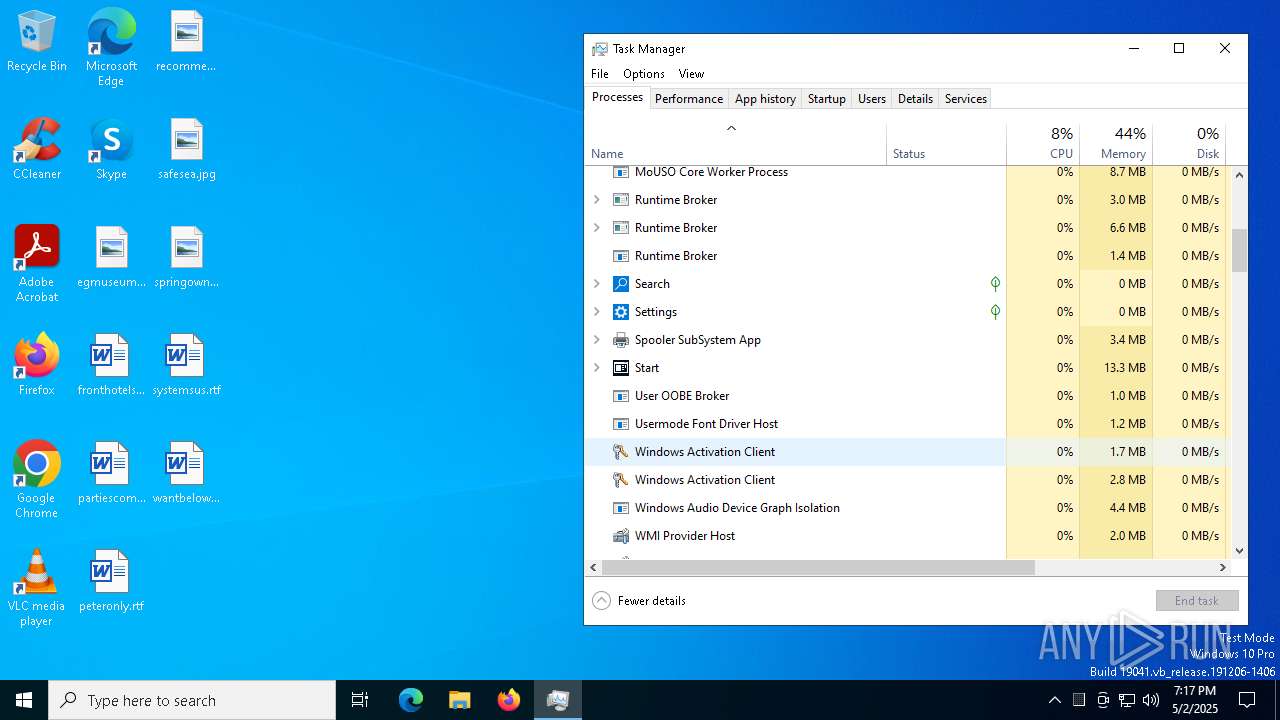
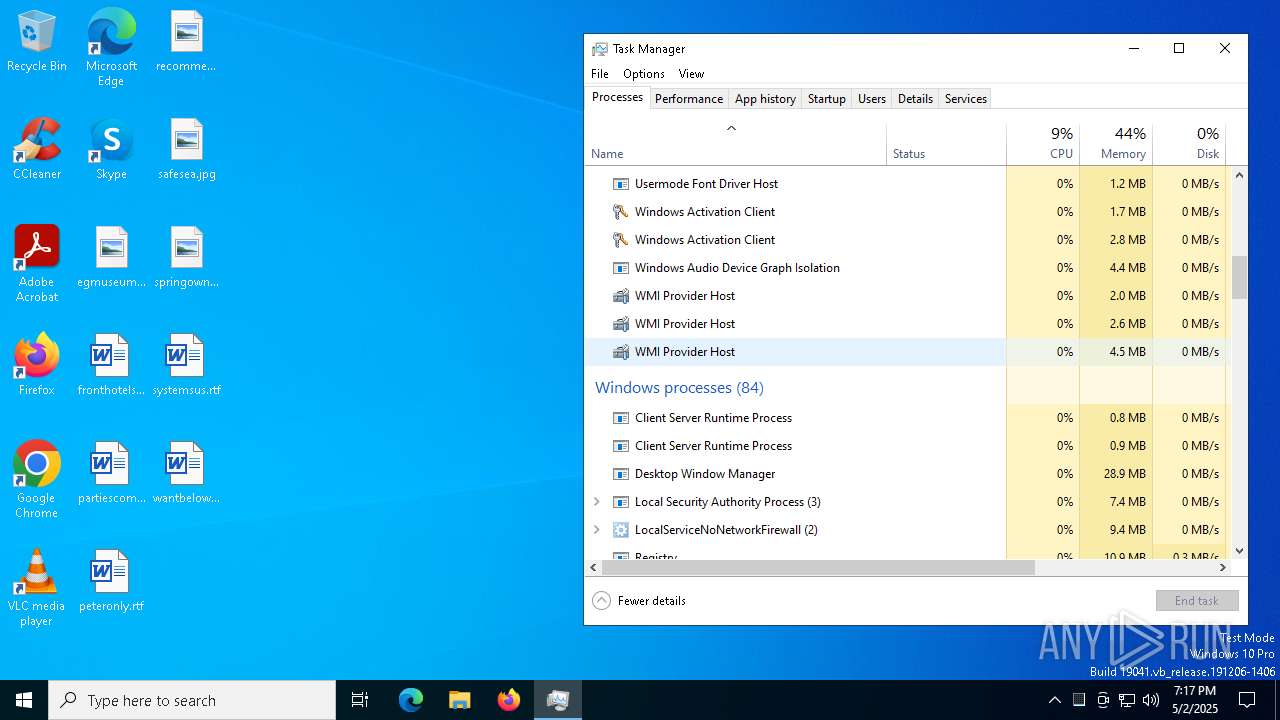
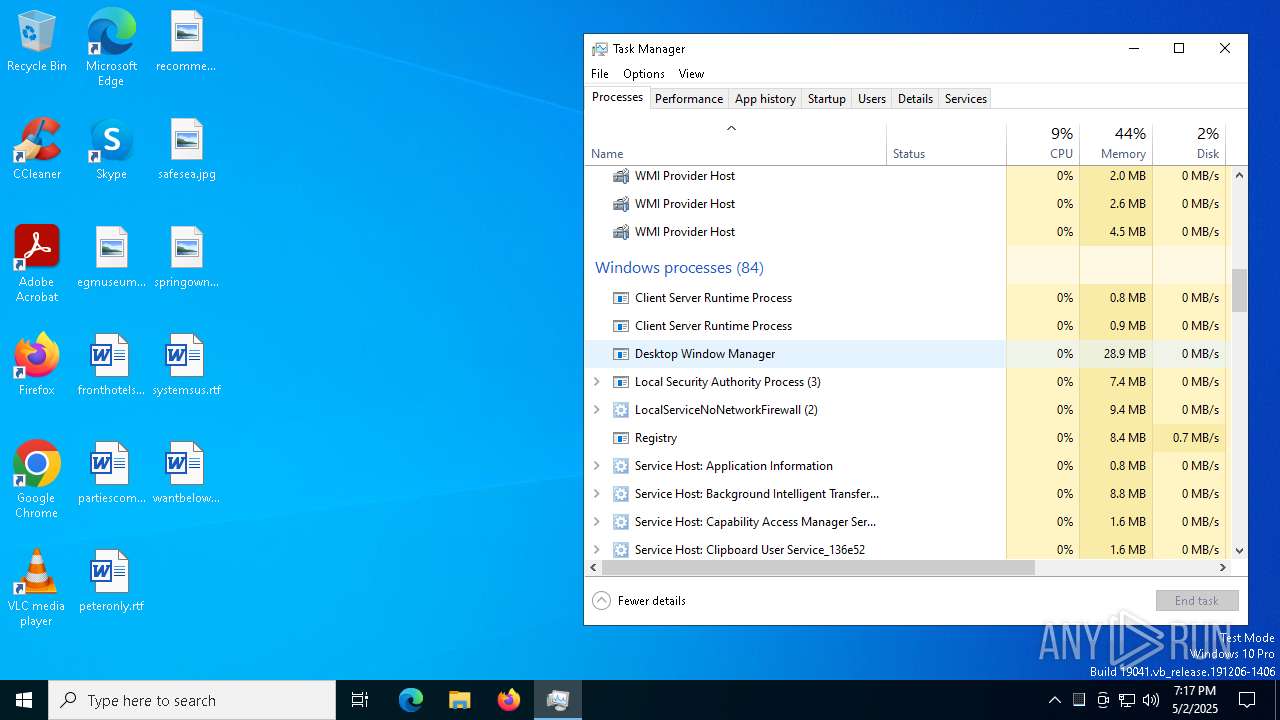
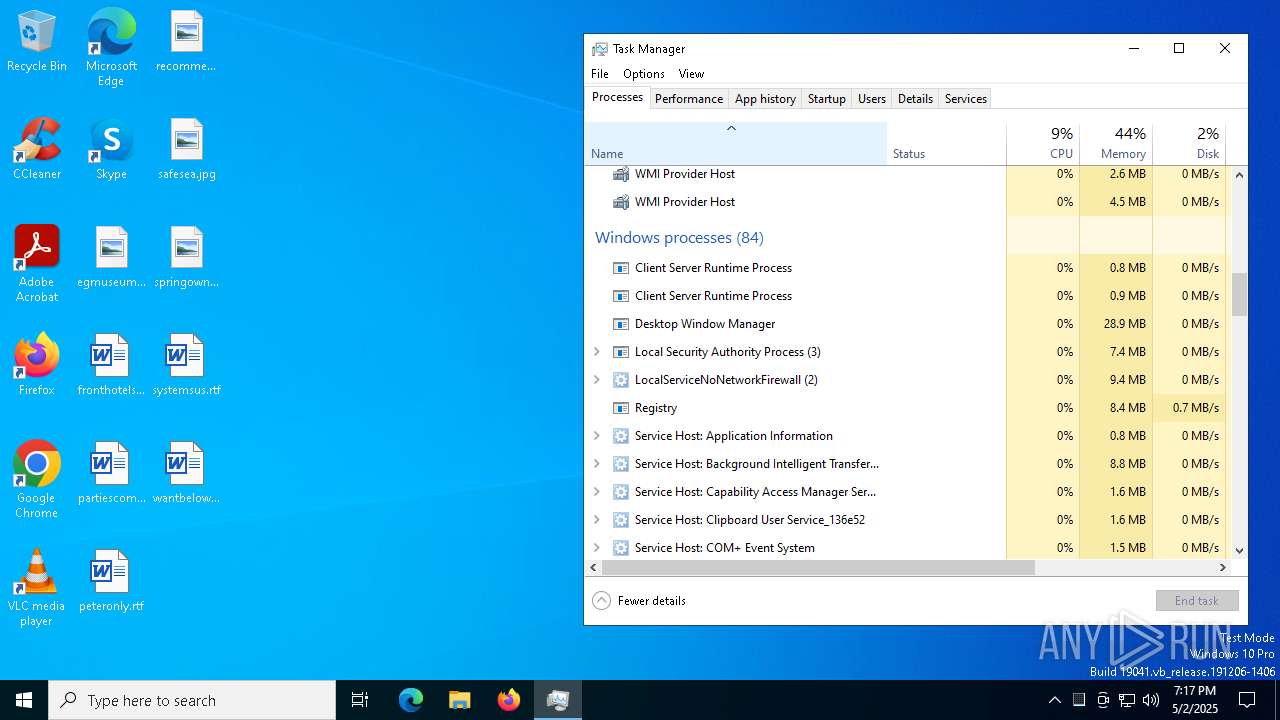
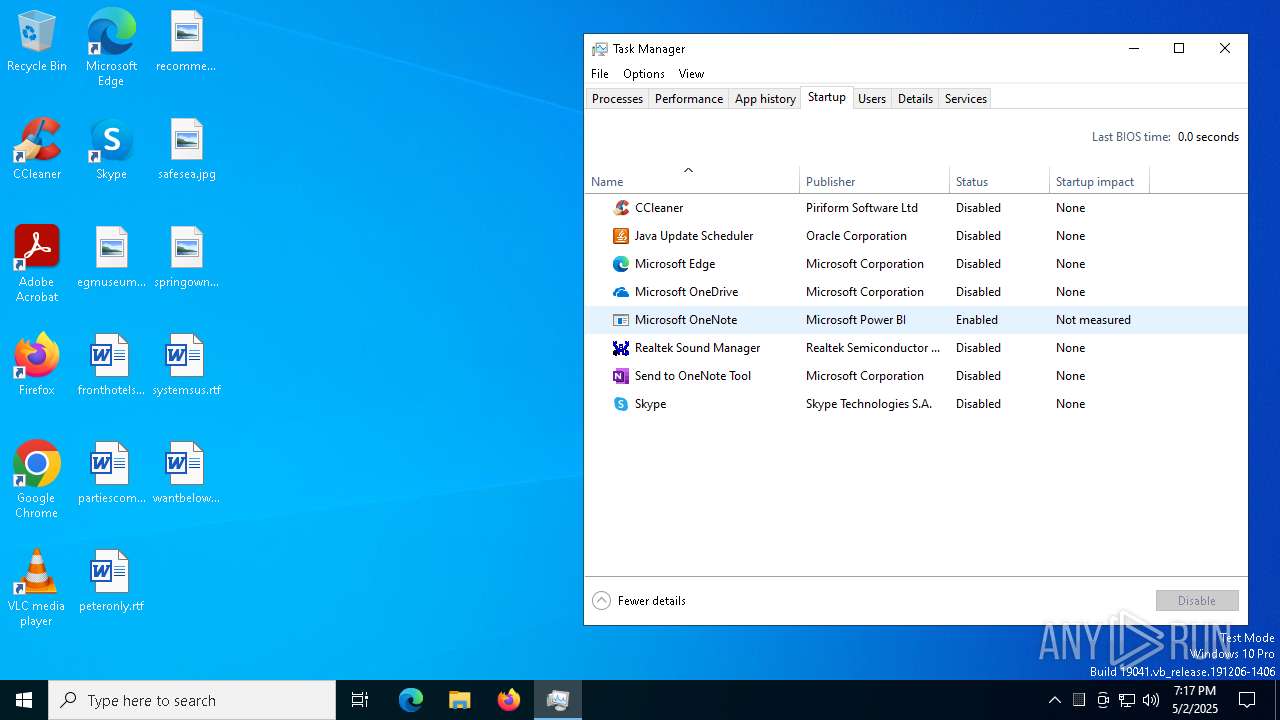
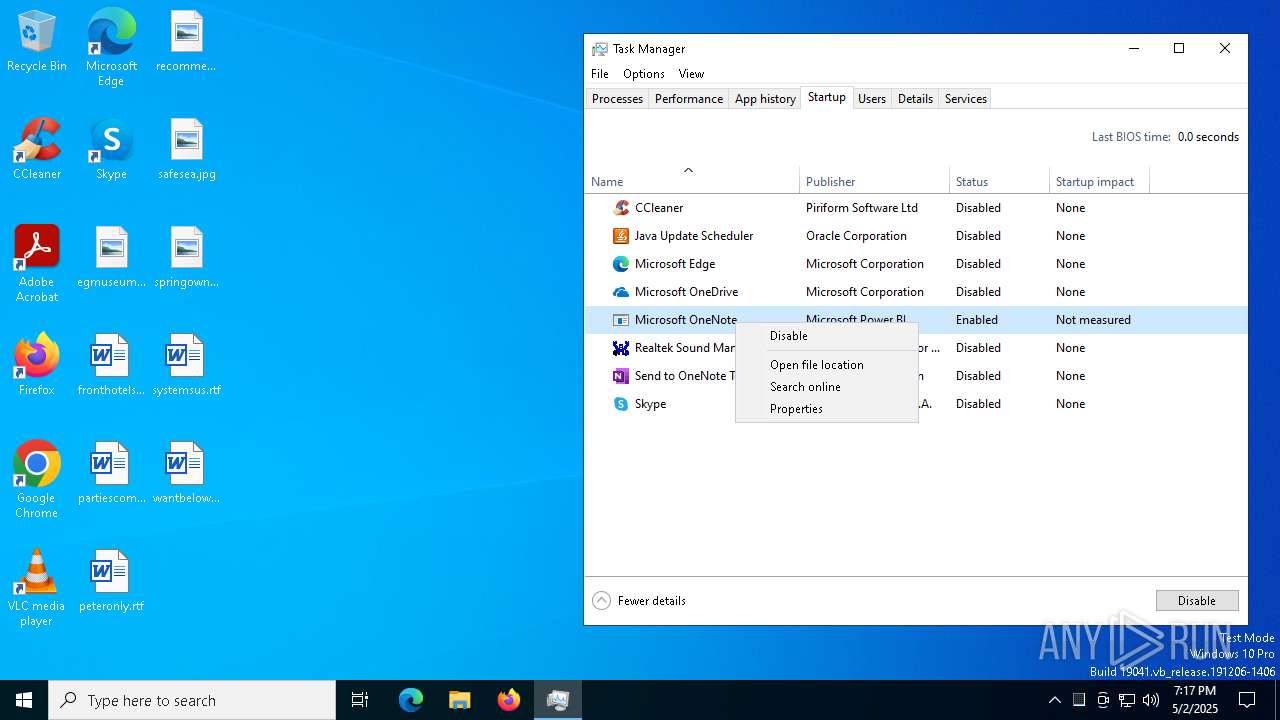
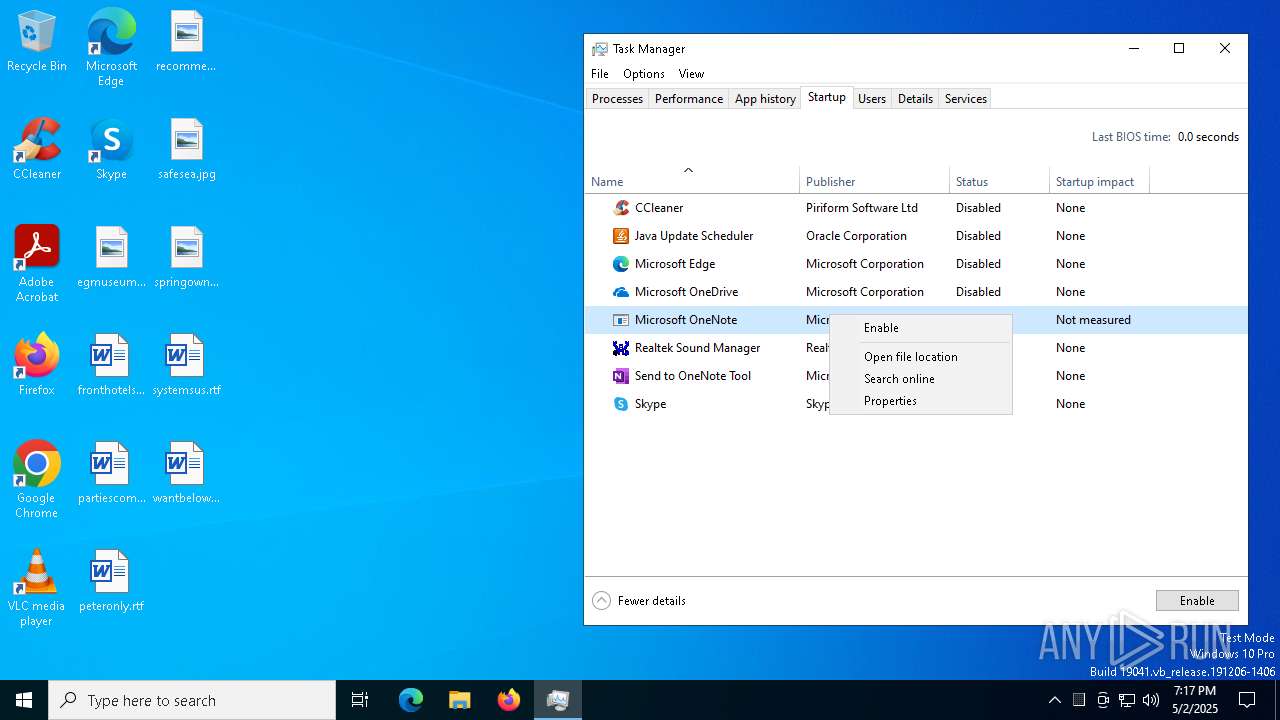
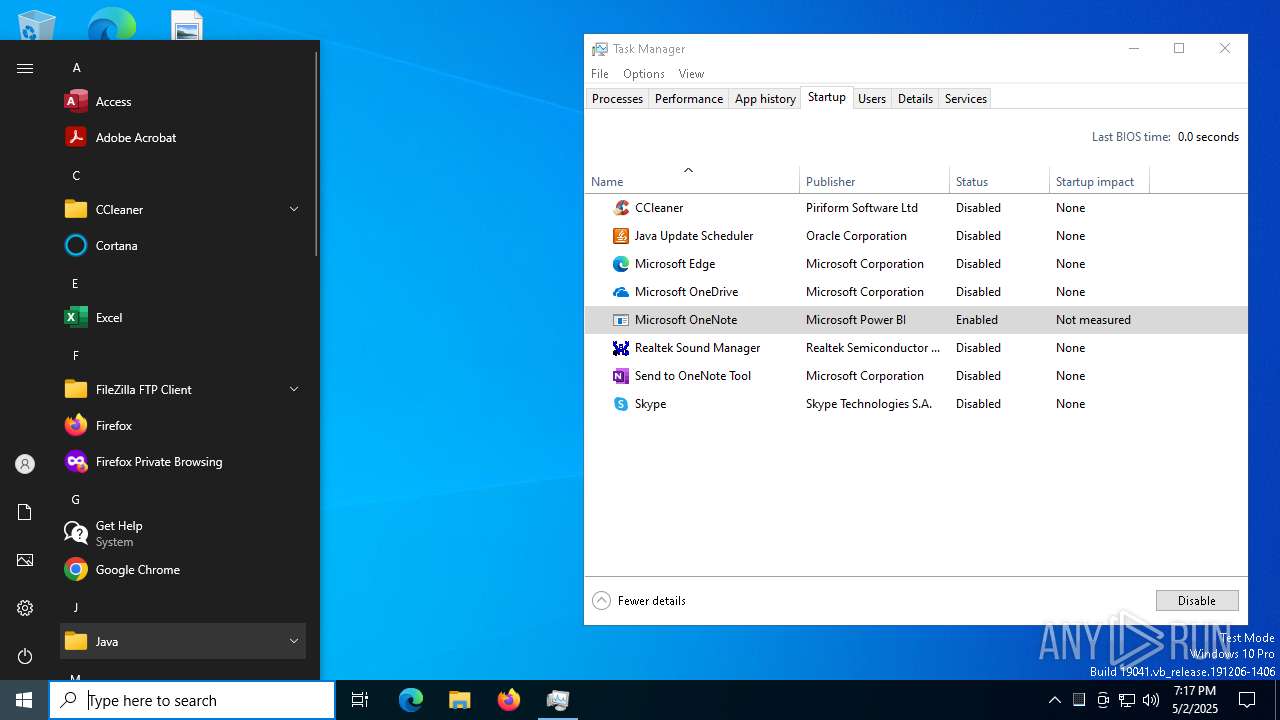
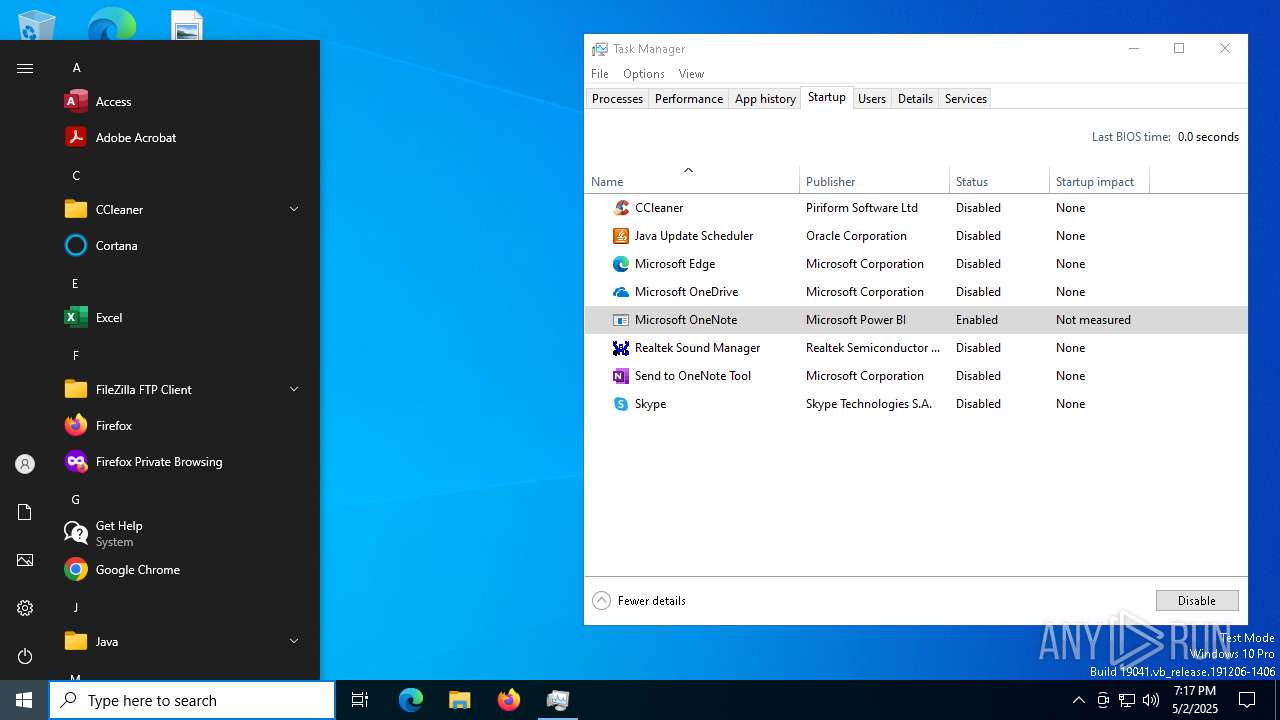
Manual execution by a user
- Taskmgr.exe (PID: 1532)
- Taskmgr.exe (PID: 1040)
- xdwdMicrosoft Azure DevOps.exe (PID: 6704)
- xdwdMicrosoft Azure DevOps.exe (PID: 3812)
Reads security settings of Internet Explorer
- Taskmgr.exe (PID: 1040)
Reads the software policy settings
- slui.exe (PID: 4776)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (72.2) |
|---|---|---|
| .scr | | | Windows screen saver (12.9) |
| .dll | | | Win32 Dynamic Link Library (generic) (6.4) |
| .exe | | | Win32 Executable (generic) (4.4) |
| .exe | | | Generic Win/DOS Executable (1.9) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2100:10:13 03:20:15+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32 |
| LinkerVersion: | 48 |
| CodeSize: | 598016 |
| InitializedDataSize: | 2560 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x93fae |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 188.149.105.180 |
| ProductVersionNumber: | 211.115.130.115 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | - |
| CompanyName: | Microsoft Power BI |
| FileDescription: | Microsoft OneNote |
| FileVersion: | 188.149.105.180 |
| InternalName: | Corel PaintShop Pro.exe |
| LegalCopyright: | Avid Pro Tools |
| LegalTrademarks: | Notepad++ Upgrade |
| OriginalFileName: | Corel PaintShop Pro.exe |
| ProductName: | Google SketchUp |
| ProductVersion: | 211.115.130.115 |
| AssemblyVersion: | 211.115.130.115 |
Total processes
471
Monitored processes
93
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 616 | SchTaSKs /create /f /sc minute /mo -1 /tn "Sage 50" /tr "C:\Users\admin\AppData\Roaming\xdwdMicrosoft SharePoint.exe" /RL HIGHEST | C:\Windows\System32\schtasks.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Task Scheduler Configuration Tool Exit code: 2147500037 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 632 | "CMD" /c SchTaSKs /create /f /sc minute /mo -1 /tn "Sage 50" /tr "C:\Users\admin\AppData\Roaming\xdwdMicrosoft SharePoint.exe" /RL HIGHEST & exit | C:\Windows\System32\cmd.exe | — | Nursultan Client 1.16.5 CRACK.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 2147500037 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 664 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 664 | SchTaSKs /create /f /sc minute /mo -1 /tn "Sage 50" /tr "C:\Users\admin\AppData\Roaming\xdwdMicrosoft SharePoint.exe" /RL HIGHEST | C:\Windows\System32\schtasks.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Task Scheduler Configuration Tool Exit code: 2147500037 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 672 | SchTaSKs /create /f /sc minute /mo 5 /tn "Microsoft Teams Host" /tr "C:\Users\admin\AppData\Roaming\xdwdMicrosoft Azure DevOps.exe" /RL HIGHEST | C:\Windows\System32\schtasks.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Task Scheduler Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 720 | "CMD" /c SchTaSKs /create /f /sc minute /mo 5 /tn "Microsoft Teams Host" /tr "C:\Users\admin\AppData\Roaming\xdwdMicrosoft Azure DevOps.exe" /RL HIGHEST & exit | C:\Windows\System32\cmd.exe | — | Nursultan Client 1.16.5 CRACK.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 736 | "CMD" /c SchTaSKs /create /f /sc minute /mo -1 /tn "Sage 50" /tr "C:\Users\admin\AppData\Roaming\xdwdMicrosoft SharePoint.exe" /RL HIGHEST & exit | C:\Windows\System32\cmd.exe | — | Nursultan Client 1.16.5 CRACK.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 2147500037 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 776 | SchTaSKs /create /f /sc minute /mo -1 /tn "Sage 50" /tr "C:\Users\admin\AppData\Roaming\xdwdMicrosoft SharePoint.exe" /RL HIGHEST | C:\Windows\System32\schtasks.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Task Scheduler Configuration Tool Exit code: 2147500037 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 924 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1040 | "C:\WINDOWS\system32\taskmgr.exe" /4 | C:\Windows\System32\Taskmgr.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Task Manager Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
9 672
Read events
9 630
Write events
41
Delete events
1
Modification events
| (PID) Process: | (6640) Nursultan Client 1.16.5 CRACK.exe | Key: | HKEY_CURRENT_USER\SOFTWARE |
| Operation: | write | Name: | hwid |
Value: MUFFQ0EyRTVDODhDMzgzNkJFQkZBM0M= | |||
| (PID) Process: | (6768) Nursultan Client 1.16.5 CRACK.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\.NET Memory Cache 4.0\Linkage |
| Operation: | write | Name: | Export |
Value: .NET Memory Cache 4.0 | |||
| (PID) Process: | (6768) Nursultan Client 1.16.5 CRACK.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\MSDTC Bridge 3.0.0.0\Linkage |
| Operation: | write | Name: | Export |
Value: MSDTC Bridge 3.0.0.0 | |||
| (PID) Process: | (6768) Nursultan Client 1.16.5 CRACK.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\MSDTC Bridge 4.0.0.0\Linkage |
| Operation: | write | Name: | Export |
Value: MSDTC Bridge 4.0.0.0 | |||
| (PID) Process: | (6768) Nursultan Client 1.16.5 CRACK.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\ServiceModelEndpoint 3.0.0.0\Linkage |
| Operation: | write | Name: | Export |
Value: ServiceModelEndpoint 3.0.0.0 | |||
| (PID) Process: | (6768) Nursultan Client 1.16.5 CRACK.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\ServiceModelOperation 3.0.0.0\Linkage |
| Operation: | write | Name: | Export |
Value: ServiceModelOperation 3.0.0.0 | |||
| (PID) Process: | (6768) Nursultan Client 1.16.5 CRACK.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\ServiceModelService 3.0.0.0\Linkage |
| Operation: | write | Name: | Export |
Value: ServiceModelService 3.0.0.0 | |||
| (PID) Process: | (6768) Nursultan Client 1.16.5 CRACK.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\SMSvcHost 3.0.0.0\Linkage |
| Operation: | write | Name: | Export |
Value: SMSvcHost 3.0.0.0 | |||
| (PID) Process: | (6768) Nursultan Client 1.16.5 CRACK.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\SMSvcHost 4.0.0.0\Linkage |
| Operation: | write | Name: | Export |
Value: SMSvcHost 4.0.0.0 | |||
| (PID) Process: | (6768) Nursultan Client 1.16.5 CRACK.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\Windows Workflow Foundation 3.0.0.0\Linkage |
| Operation: | write | Name: | Export |
Value: Windows Workflow Foundation 3.0.0.0 | |||
Executable files
3
Suspicious files
75
Text files
1
Unknown types
13
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6768 | Nursultan Client 1.16.5 CRACK.exe | C:\Users\admin\AppData\Roaming\xdwdMicrosoft SharePoint.exe | executable | |
MD5:20BE0C0F0FDCC5E6F8254EFCCCB67540 | SHA256:D8F76A5BC958860507BA2CEA87D16D05F5002B6818FE540A9C233170C2A3240A | |||
| 1040 | Taskmgr.exe | C:\Users\admin\AppData\Local\D3DSCache\3534848bb9f4cb71\F4EB2D6C-ED2B-4BDD-AD9D-F913287E6768.lock | text | |
MD5:F49655F856ACB8884CC0ACE29216F511 | SHA256:7852FCE59C67DDF1D6B8B997EAA1ADFAC004A9F3A91C37295DE9223674011FBA | |||
| 4164 | PLUGScheduler.exe | C:\ProgramData\PLUG\Logs\RUXIMLog.046.etl | binary | |
MD5:A7A21FBC9D00F33F186B34A50E170C13 | SHA256:64CAC91E46D4FC832958232A658431CBF9D8D9F265653ACA2BEB32428D4688EC | |||
| 4164 | PLUGScheduler.exe | C:\ProgramData\PLUG\Logs\RUXIMLog.038.etl | binary | |
MD5:F9485F2BA891697F8B6CF8FB1E7F42C0 | SHA256:69146D4AAEFB8609745B6CA780B48ABC66054AA3CDB8061248CF7B32F3B32617 | |||
| 4164 | PLUGScheduler.exe | C:\ProgramData\PLUG\Logs\RUXIMLog.035.etl | binary | |
MD5:2FC3641AD4F7A4A3C83C9F3014B0F0A5 | SHA256:92C3D62BC45E1DDFC77DA511ACE5E47D021D69BA625D2766AF91E376102F11AC | |||
| 4164 | PLUGScheduler.exe | C:\ProgramData\PLUG\Logs\RUXIMLog.034.etl | binary | |
MD5:DCB94F822B793FF178C7332174A89DFB | SHA256:4AB418FA76DFA333D37F7401B40B0B0F0E806876C79AB2F36CD3FD7CCAD8665B | |||
| 4164 | PLUGScheduler.exe | C:\ProgramData\PLUG\Logs\RUXIMLog.045.etl | binary | |
MD5:89BD161BF7B46C9078937CF832786737 | SHA256:2B83DF5532E9F54ED301C8F82E2CDD489799C8D5222A2D44C97DCB151A96FAA9 | |||
| 4164 | PLUGScheduler.exe | C:\ProgramData\PLUG\Logs\RUXIMLog.047.etl | binary | |
MD5:FED961067F664B5381B65A534B7AB728 | SHA256:652F31A8284AE812D1D9D24192BC800976BF74C240591C6AC443A28C4709FB7C | |||
| 4164 | PLUGScheduler.exe | C:\ProgramData\PLUG\Logs\RUXIMLog.050.etl | etl | |
MD5:C8834D365FAE073DEDE1F1620454CE71 | SHA256:C6DD793EEE1D5551CA507A3C5BFFECA82DD3E29C63C2C6DD218A7D4BFB37046B | |||
| 6768 | Nursultan Client 1.16.5 CRACK.exe | C:\Windows\xdwd.dll | executable | |
MD5:16E5A492C9C6AE34C59683BE9C51FA31 | SHA256:35C8D022E1D917F1AABDCEAE98097CCC072161B302F84C768CA63E4B32AC2B66 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
67
DNS requests
40
Threats
39
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2720 | backgroundTaskHost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | DE | binary | 471 b | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.48.23.166:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | DE | binary | 825 b | whitelisted |
2720 | backgroundTaskHost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEA77flR%2B3w%2FxBpruV2lte6A%3D | DE | binary | 471 b | whitelisted |
— | — | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | DE | binary | 868 b | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | DE | binary | 868 b | whitelisted |
6744 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | DE | binary | 407 b | whitelisted |
5452 | SearchApp.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | DE | binary | 313 b | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | DE | binary | 471 b | whitelisted |
6744 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | DE | binary | 419 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2104 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.48.23.166:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
— | — | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
3216 | svchost.exe | 172.211.123.249:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
6544 | svchost.exe | 40.126.31.67:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6544 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
if-detect.gl.at.ply.gg |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | A Network Trojan was detected | MALWARE [ANY.RUN] Suspected domain Associated with Malware Distribution (.ply .gg) |
2196 | svchost.exe | Misc activity | ET TA_ABUSED_SERVICES Tunneling Service in DNS Lookup (* .ply .gg) |
2196 | svchost.exe | Potentially Bad Traffic | ET INFO playit .gg Tunneling Domain in DNS Lookup |
6768 | Nursultan Client 1.16.5 CRACK.exe | A Network Trojan was detected | ET MALWARE PureLogs Backdoor Server GZIP C2 Traffic |
6768 | Nursultan Client 1.16.5 CRACK.exe | A Network Trojan was detected | ET MALWARE DcRAT/Sheet RAT CnC Checkin Using MessagePack |
6768 | Nursultan Client 1.16.5 CRACK.exe | A Network Trojan was detected | ET MALWARE DcRAT/Sheet RAT CnC Checkin Using MessagePack |
6768 | Nursultan Client 1.16.5 CRACK.exe | A Network Trojan was detected | ET MALWARE DcRAT/Sheet RAT CnC Checkin Using MessagePack |
6768 | Nursultan Client 1.16.5 CRACK.exe | A Network Trojan was detected | ET MALWARE DcRAT/Sheet RAT CnC Checkin Using MessagePack |
6768 | Nursultan Client 1.16.5 CRACK.exe | A Network Trojan was detected | ET MALWARE PureLogs Backdoor Client GZIP C2 Traffic |
6768 | Nursultan Client 1.16.5 CRACK.exe | A Network Trojan was detected | ET MALWARE DcRAT/Sheet RAT CnC Checkin Using MessagePack |