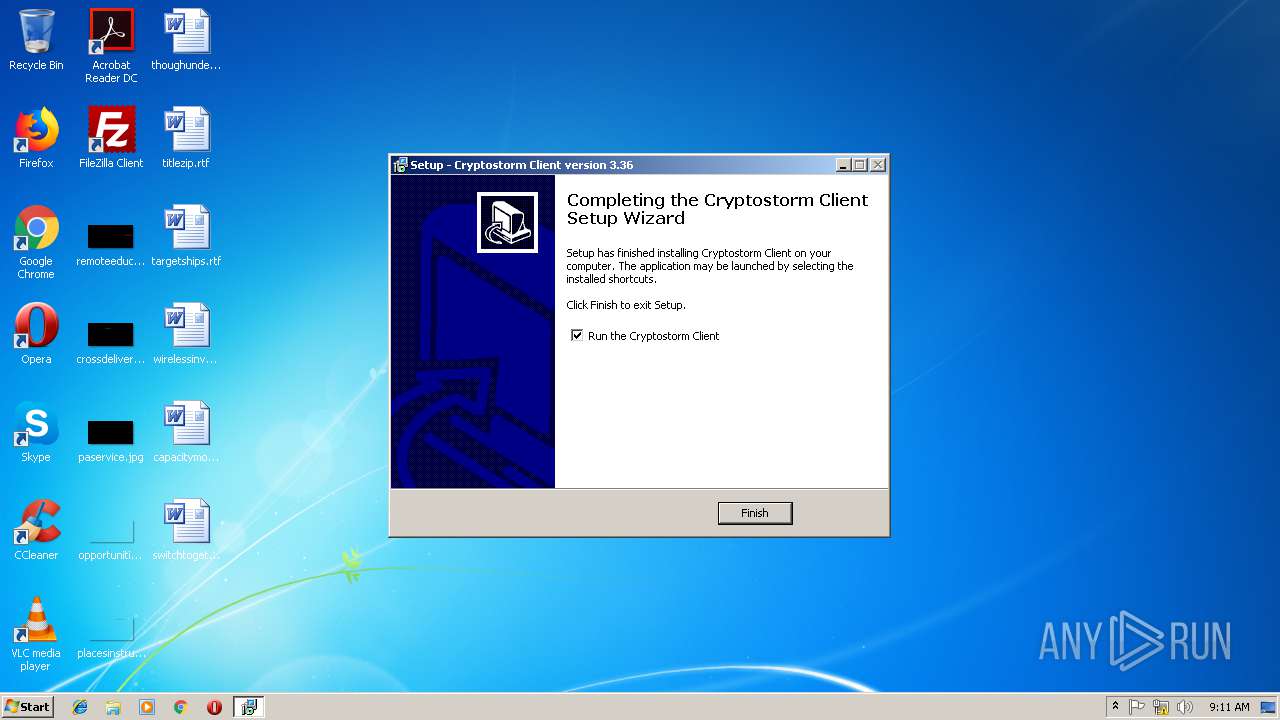
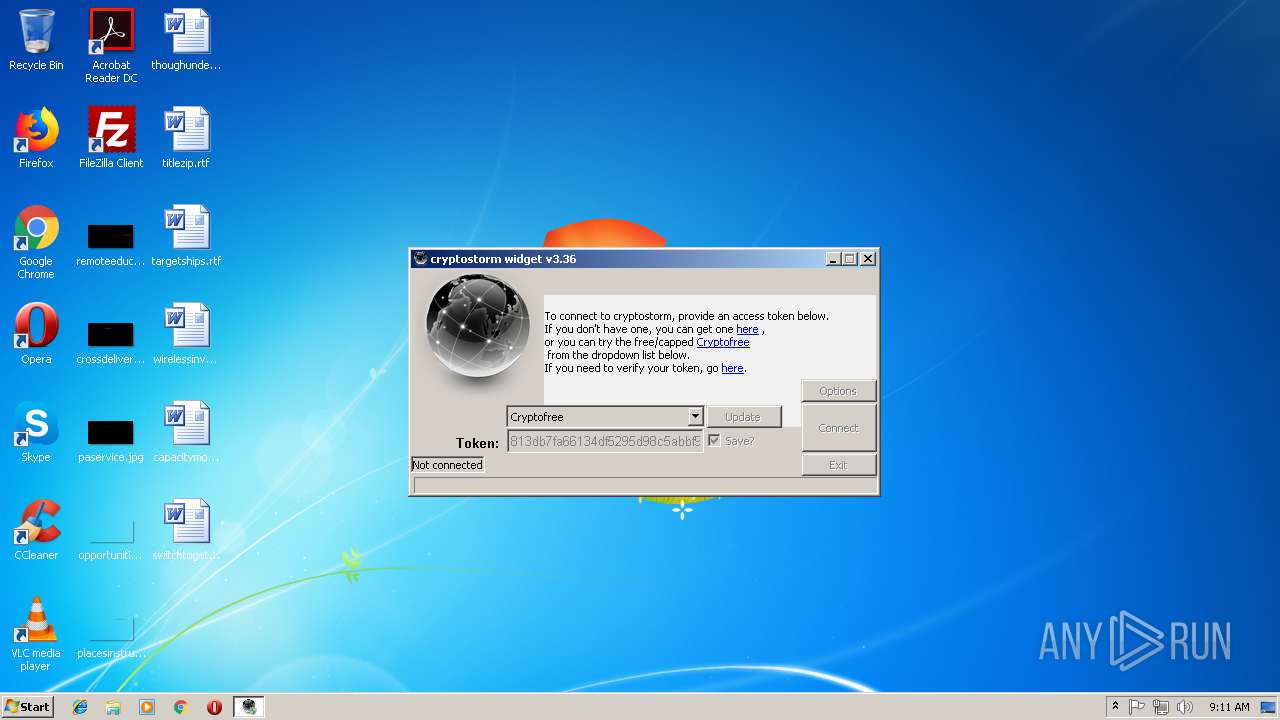
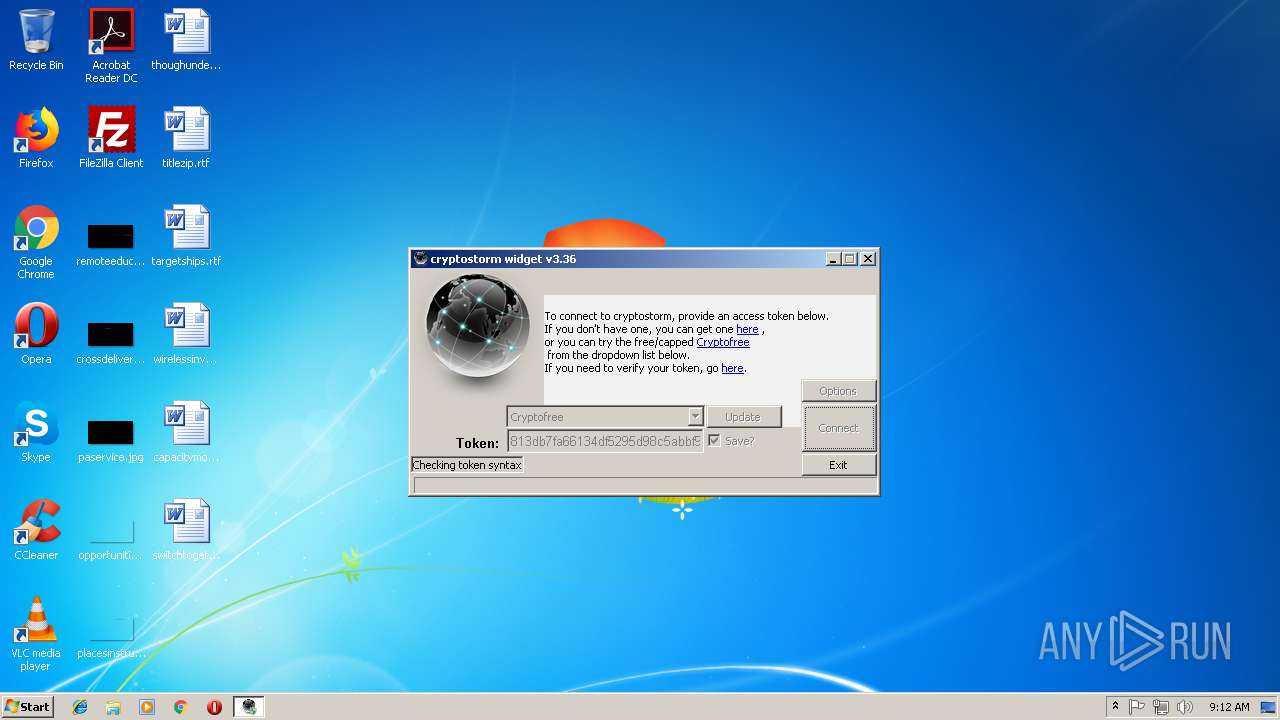
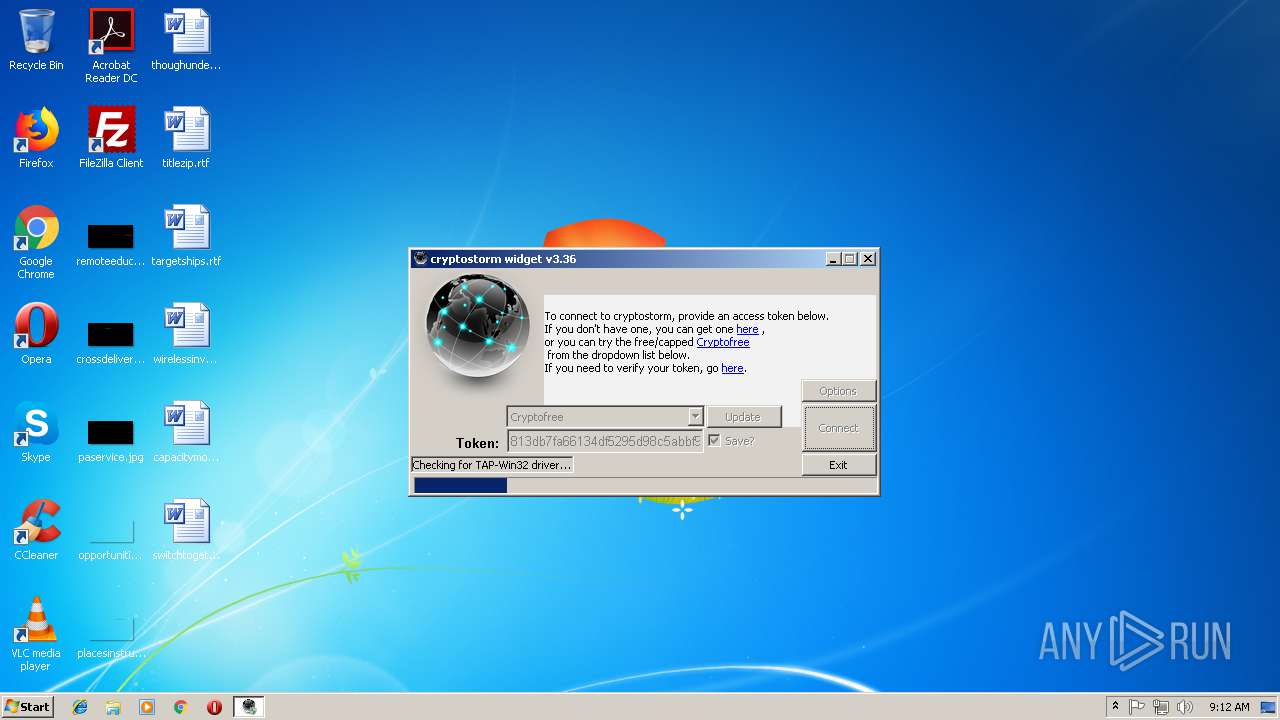
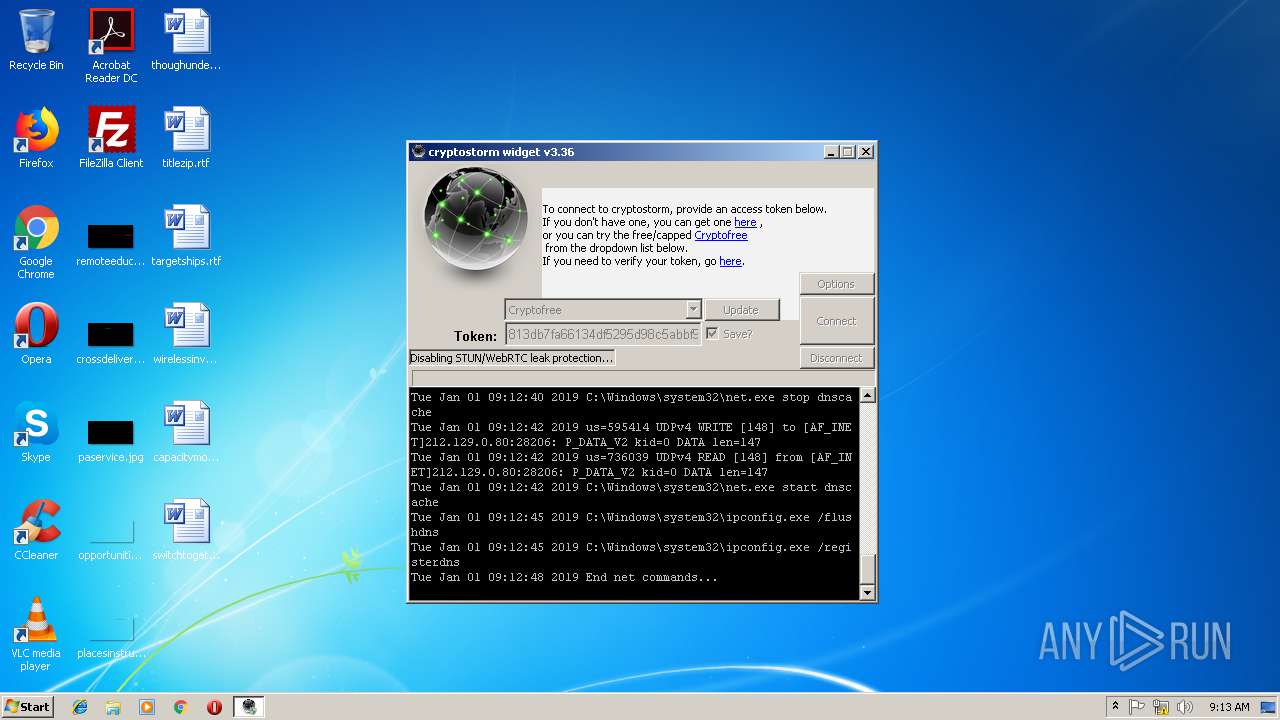
| download: | cryptostorm_setup.exe |
| Full analysis: | https://app.any.run/tasks/964b127c-56a7-4ebf-9eec-339fdba0db46 |
| Verdict: | Malicious activity |
| Analysis date: | January 01, 2019, 09:09:40 |
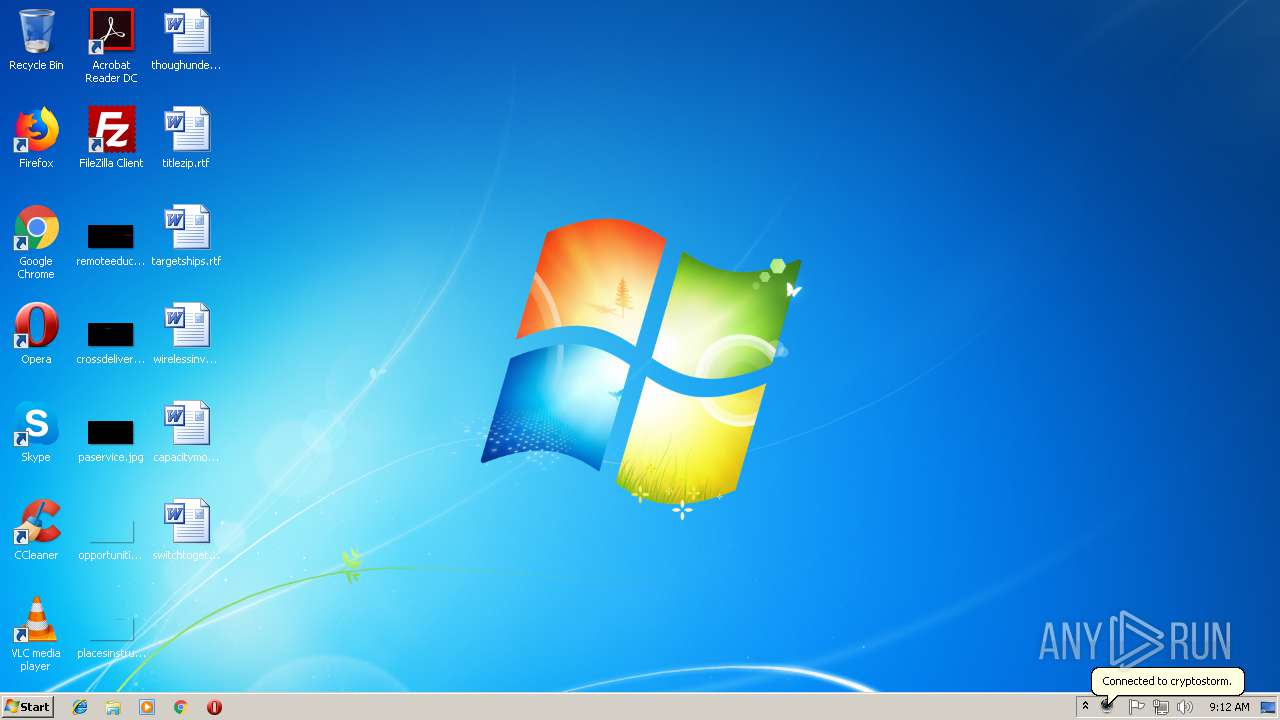
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 0364D6E4FB9BE7490DAE373B38886DE8 |
| SHA1: | EAEF5C6F8B475A2F81657EF80437533E096F5297 |
| SHA256: | D8F4AACE54AECDEBF9BB03D81A93E20813E4CC45C1AFBF04EB1A6723EB4F173E |
| SSDEEP: | 393216:/nwul975xJfPRcUu7rszT1lKBIoZzT7gcn8rN7FfEV0PTMatxVXMo:PF5nKV3ssIMj2FBEOPT5XMo |
MALICIOUS
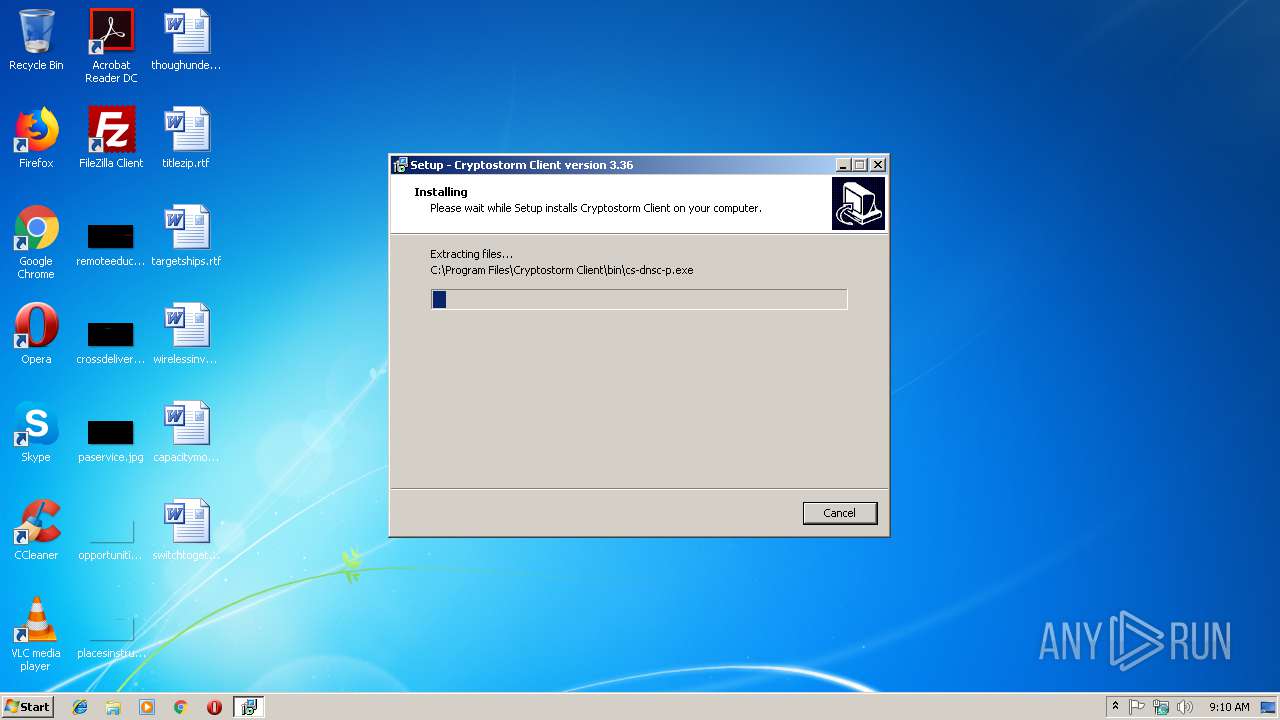
Application was dropped or rewritten from another process
- nsF3BE.tmp (PID: 3700)
- tapinstall.exe (PID: 2548)
- nsF7E6.tmp (PID: 2240)
- tapinstall.exe (PID: 2796)
- client.exe (PID: 2764)
- cpwgui.exe (PID: 3144)
- csvpn32.exe (PID: 2428)
- ossl32.exe (PID: 3332)
- cs-dnsc-p.exe (PID: 1332)
- csvpn32.exe (PID: 2704)
- csvpn32.exe (PID: 3880)
- csvpn32.exe (PID: 1008)
- tap32.exe (PID: 2892)
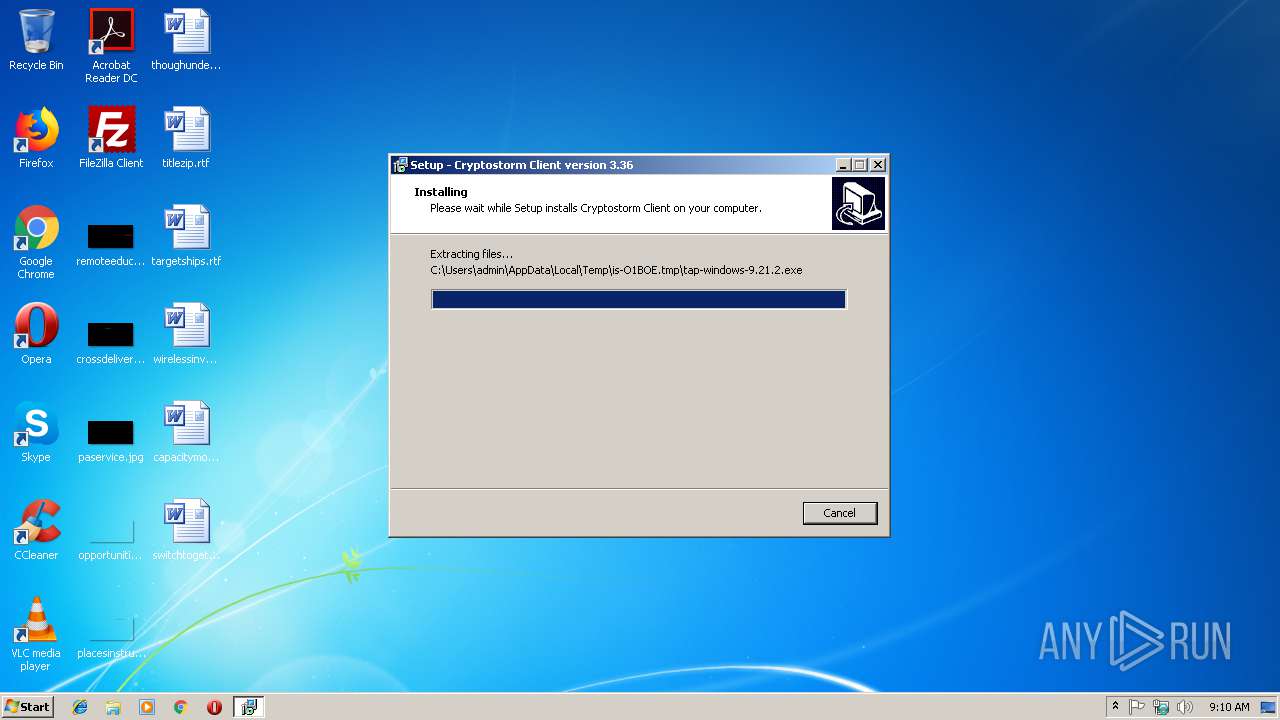
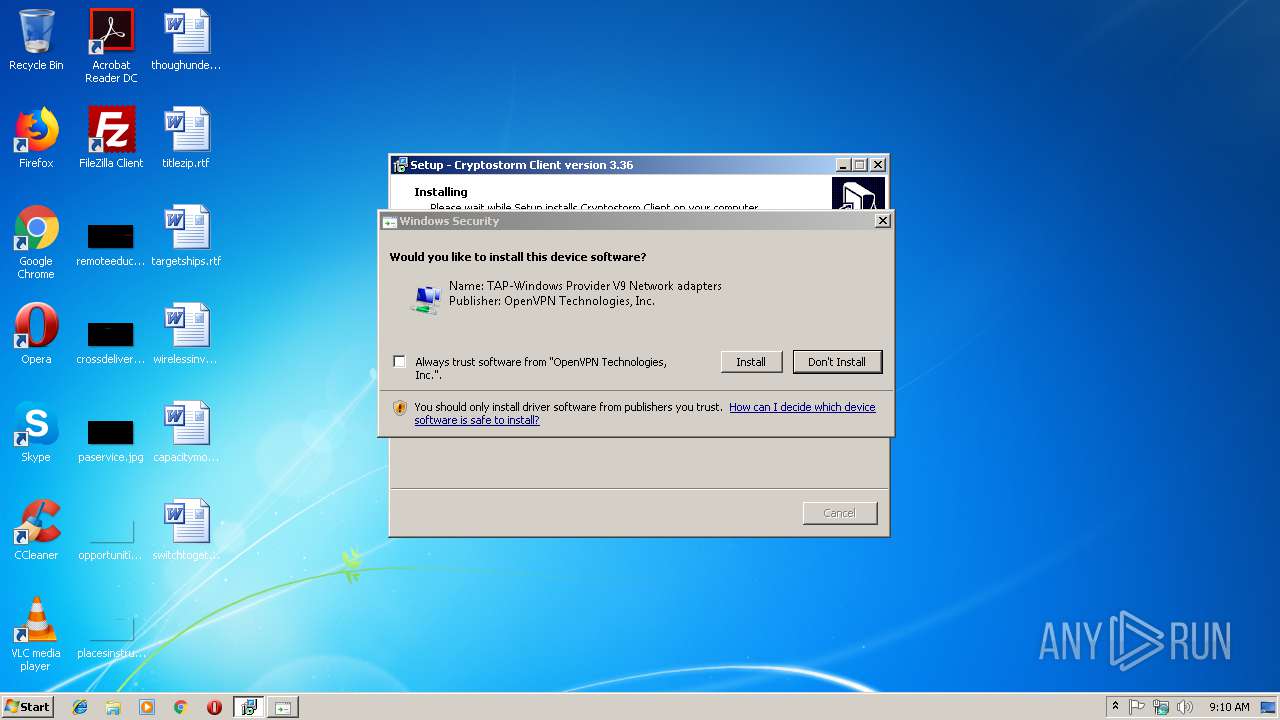
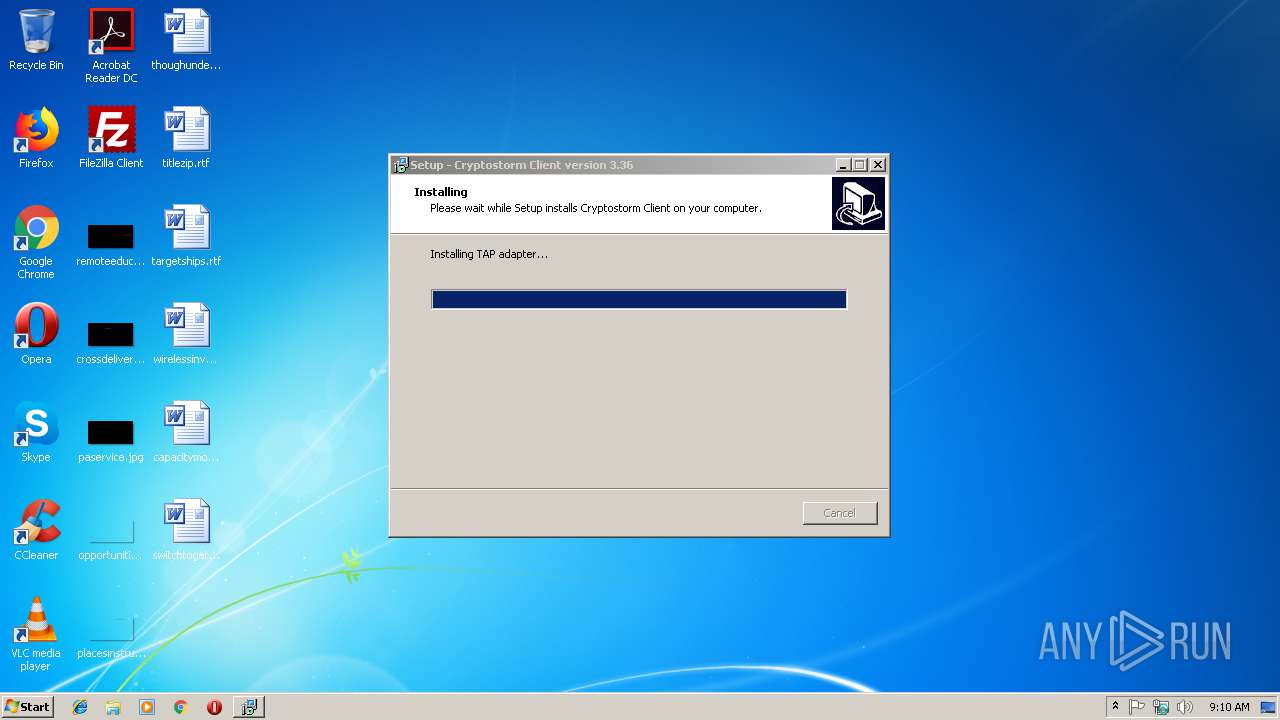
- tap-windows-9.21.2.exe (PID: 3628)
- nsA973.tmp (PID: 2604)
- nsA81A.tmp (PID: 3108)
- tapinstall.exe (PID: 3840)
- tapinstall.exe (PID: 4020)
- csvpn32.exe (PID: 3764)
- csvpn32.exe (PID: 3284)
- csvpn32.exe (PID: 2436)
- csvpn32.exe (PID: 2096)
- cs-dnsc-p.exe (PID: 2320)
- csvpn32.exe (PID: 3224)
- csvpn32.exe (PID: 4092)
- csvpn32.exe (PID: 2500)
- csvpn32.exe (PID: 2728)
- wkillcx.exe (PID: 2292)
- wkillcx.exe (PID: 3568)
- wkillcx.exe (PID: 3780)
- wkillcx.exe (PID: 3616)
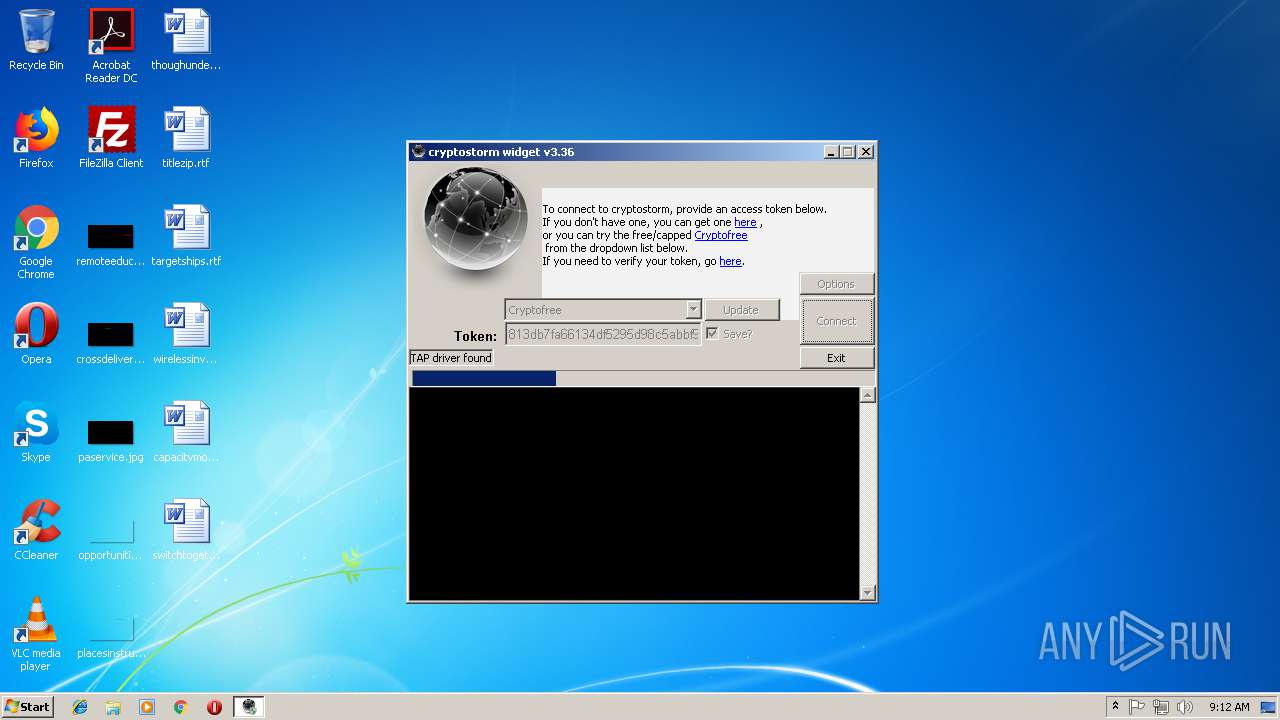
Loads dropped or rewritten executable
- client.exe (PID: 2764)
- csvpn32.exe (PID: 2428)
- ossl32.exe (PID: 3332)
- csvpn32.exe (PID: 1008)
- csvpn32.exe (PID: 3880)
- csvpn32.exe (PID: 2704)
- tap-windows-9.21.2.exe (PID: 3628)
- csvpn32.exe (PID: 3764)
- csvpn32.exe (PID: 2436)
- csvpn32.exe (PID: 2096)
- csvpn32.exe (PID: 3284)
- csvpn32.exe (PID: 4092)
- csvpn32.exe (PID: 3224)
- csvpn32.exe (PID: 2500)
- csvpn32.exe (PID: 2728)
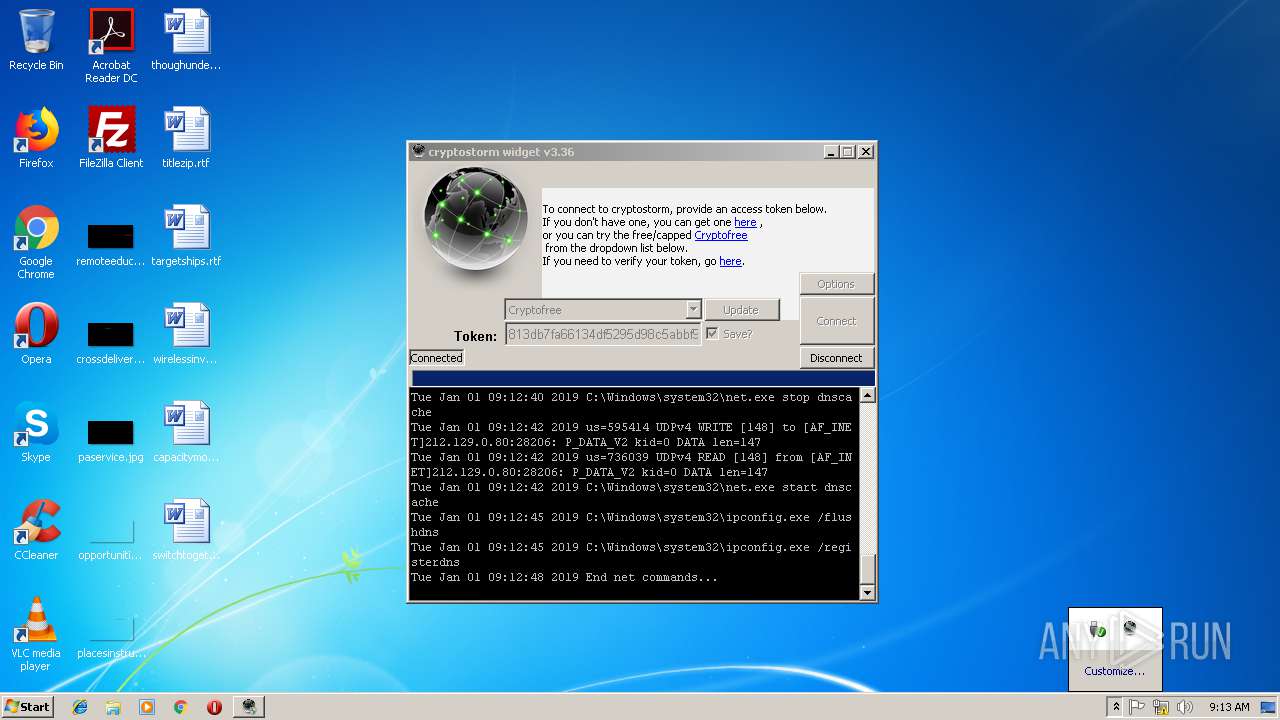
Starts NET.EXE for service management
- csvpn32.exe (PID: 2728)
SUSPICIOUS
Reads Windows owner or organization settings
- cryptostorm_setup.tmp (PID: 2644)
Reads the Windows organization settings
- cryptostorm_setup.tmp (PID: 2644)
Executable content was dropped or overwritten
- cryptostorm_setup.exe (PID: 4048)
- cryptostorm_setup.exe (PID: 3608)
- tap-windows-9.21.2.exe (PID: 3772)
- DrvInst.exe (PID: 2860)
- tapinstall.exe (PID: 2796)
- DrvInst.exe (PID: 2720)
- cryptostorm_setup.tmp (PID: 2644)
- client.exe (PID: 2764)
- tap-windows-9.21.2.exe (PID: 3628)
Starts CMD.EXE for commands execution
- cryptostorm_setup.tmp (PID: 2644)
- client.exe (PID: 2764)
Starts application with an unusual extension
- tap-windows-9.21.2.exe (PID: 3772)
- tap-windows-9.21.2.exe (PID: 3628)
Creates files in the Windows directory
- tapinstall.exe (PID: 2796)
- DrvInst.exe (PID: 2860)
- DrvInst.exe (PID: 2720)
- DrvInst.exe (PID: 2800)
Removes files from Windows directory
- DrvInst.exe (PID: 2860)
- DrvInst.exe (PID: 2720)
- DrvInst.exe (PID: 2800)
Uses RUNDLL32.EXE to load library
- DrvInst.exe (PID: 2860)
Creates files in the driver directory
- DrvInst.exe (PID: 2860)
- DrvInst.exe (PID: 2720)
Searches for installed software
- DrvInst.exe (PID: 2860)
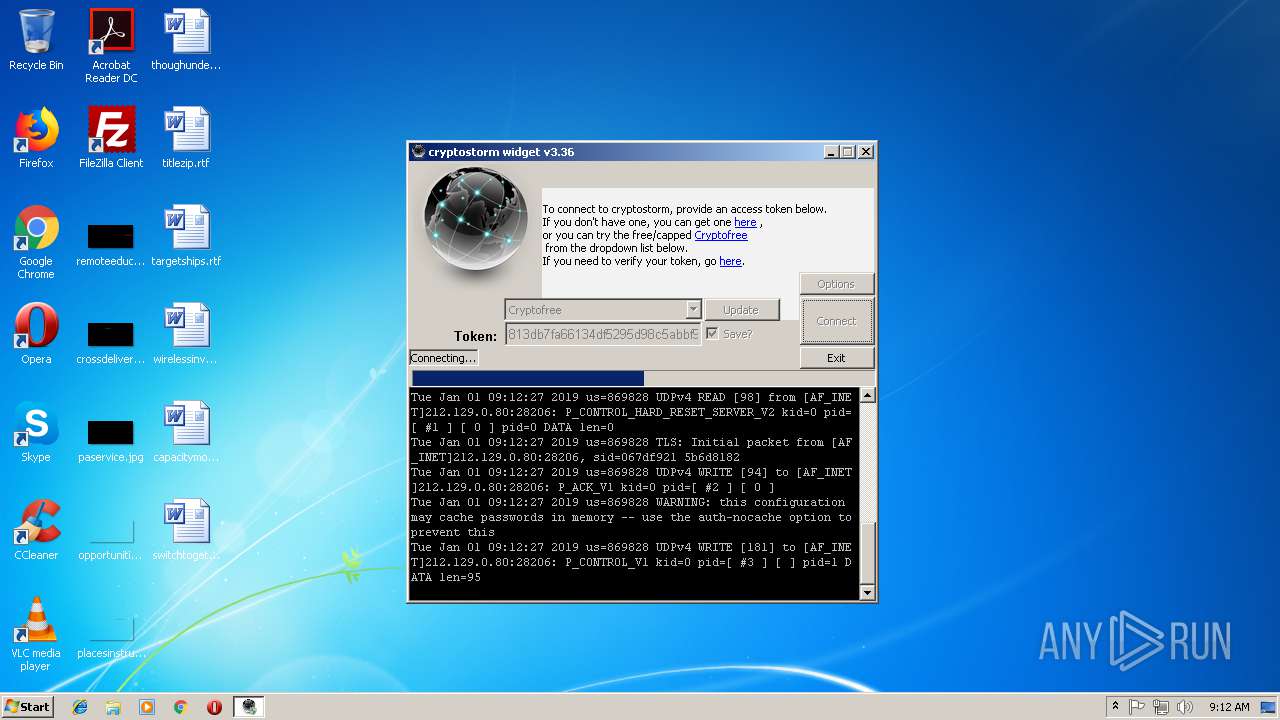
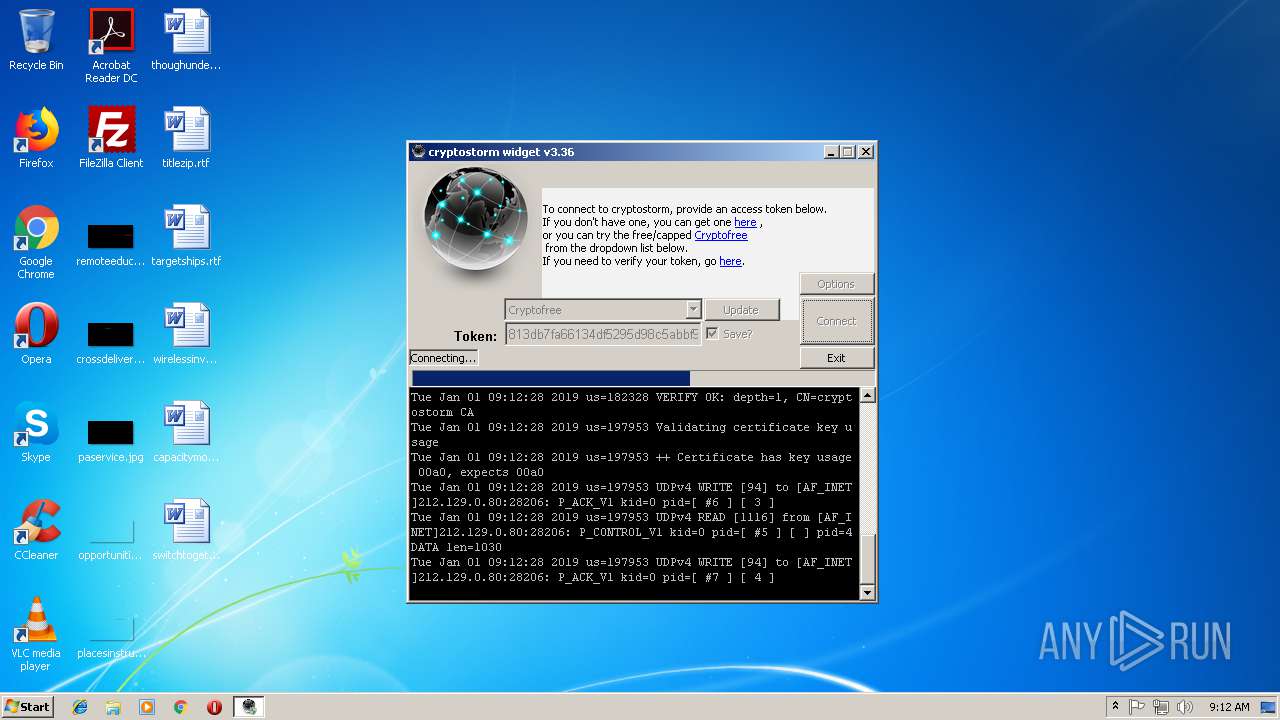
Uses NETSH.EXE for network configuration
- client.exe (PID: 2764)
- cmd.exe (PID: 2428)
- cmd.exe (PID: 3308)
- cmd.exe (PID: 2436)
- cmd.exe (PID: 2360)
- cmd.exe (PID: 2092)
- cmd.exe (PID: 3548)
- cmd.exe (PID: 4056)
Creates files in the program directory
- client.exe (PID: 2764)
- netsh.exe (PID: 3736)
Uses NETSTAT.EXE to discover network connections
- client.exe (PID: 2764)
Creates a software uninstall entry
- tap-windows-9.21.2.exe (PID: 3628)
Uses IPCONFIG.EXE to discover IP address
- csvpn32.exe (PID: 2728)
Application launched itself
- csvpn32.exe (PID: 2500)
INFO
Application was dropped or rewritten from another process
- cryptostorm_setup.tmp (PID: 2568)
- cryptostorm_setup.tmp (PID: 2644)
- tap32.exe (PID: 1428)
- tap-windows-9.21.2.exe (PID: 3772)
Loads dropped or rewritten executable
- tap-windows-9.21.2.exe (PID: 3772)
Dropped object may contain Bitcoin addresses
- cryptostorm_setup.tmp (PID: 2644)
Creates a software uninstall entry
- cryptostorm_setup.tmp (PID: 2644)
- tap-windows-9.21.2.exe (PID: 3772)
Creates files in the program directory
- tap-windows-9.21.2.exe (PID: 3772)
- cryptostorm_setup.tmp (PID: 2644)
Low-level read access rights to disk partition
- vssvc.exe (PID: 3428)
Application launched itself
- chrome.exe (PID: 2336)
Changes settings of System certificates
- chrome.exe (PID: 2336)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable Delphi generic (45.2) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (20.9) |
| .exe | | | Win32 Executable (generic) (14.3) |
| .exe | | | Win16/32 Executable Delphi generic (6.6) |
| .exe | | | Generic Win/DOS Executable (6.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:06:14 15:27:46+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 66560 |
| InitializedDataSize: | 53760 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1181c |
| OSVersion: | 5 |
| ImageVersion: | 6 |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 3.36.0.0 |
| ProductVersionNumber: | 3.36.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
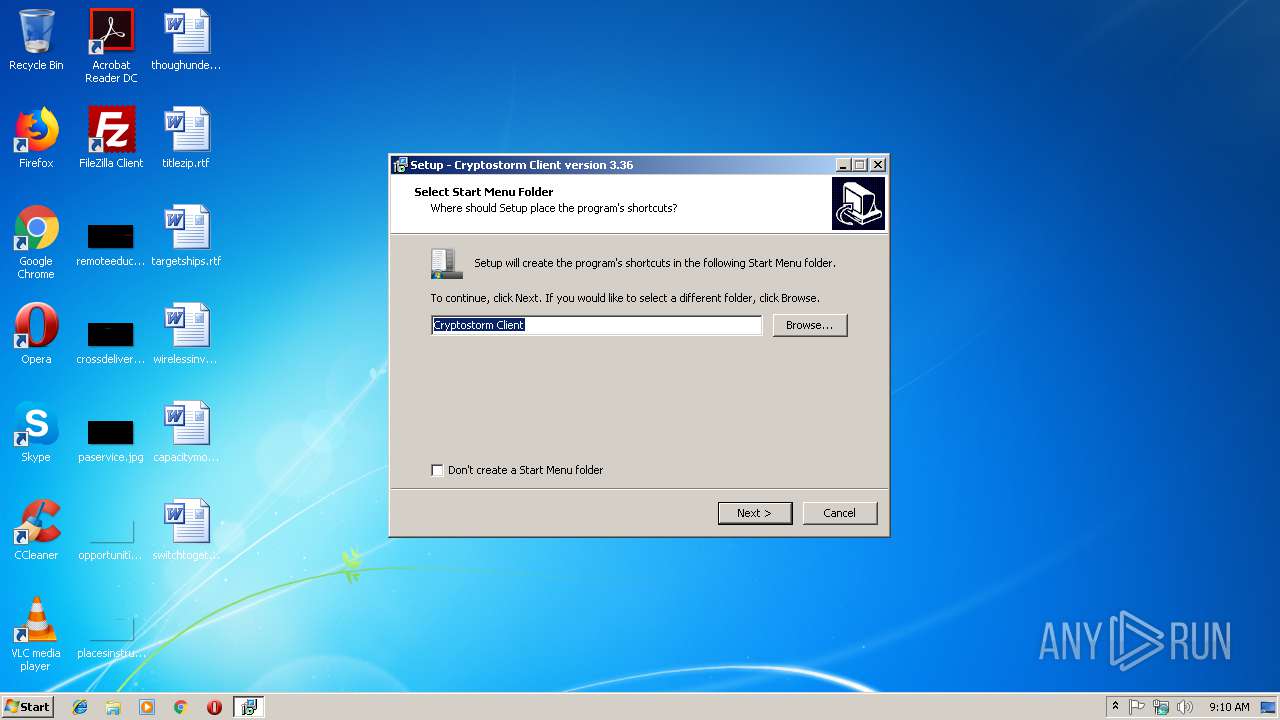
| Comments: | This installation was built with Inno Setup. |
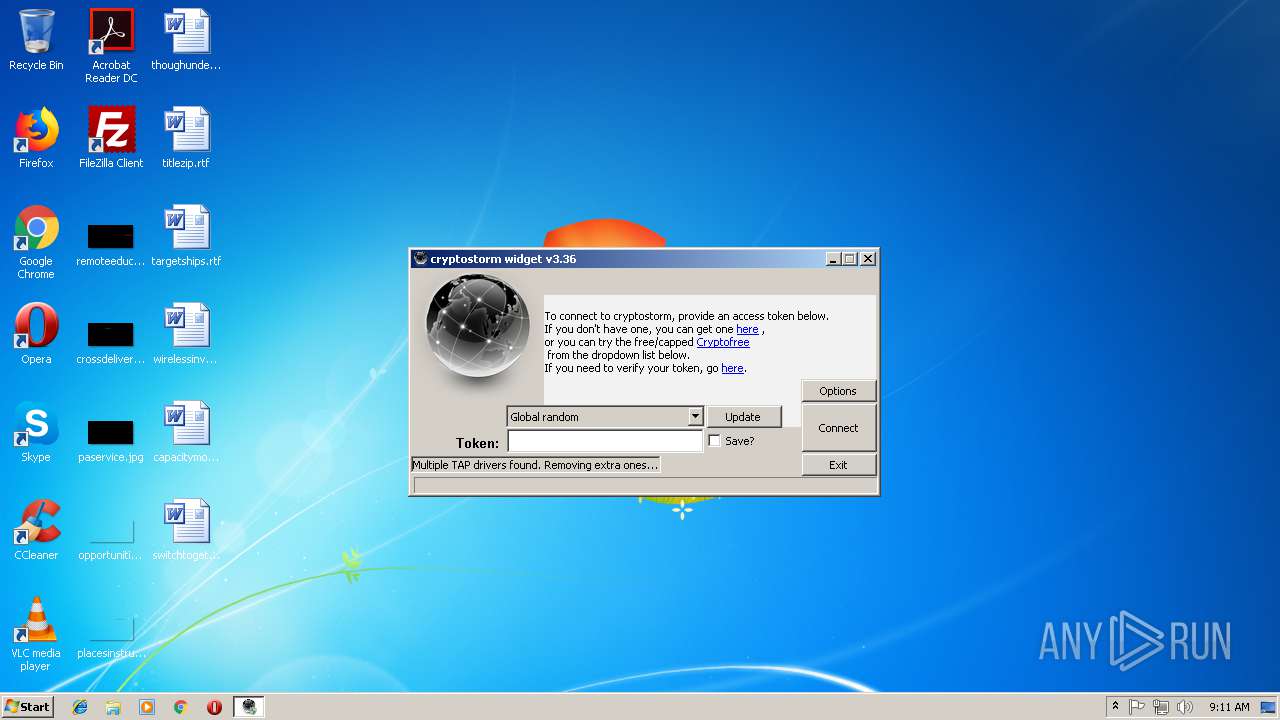
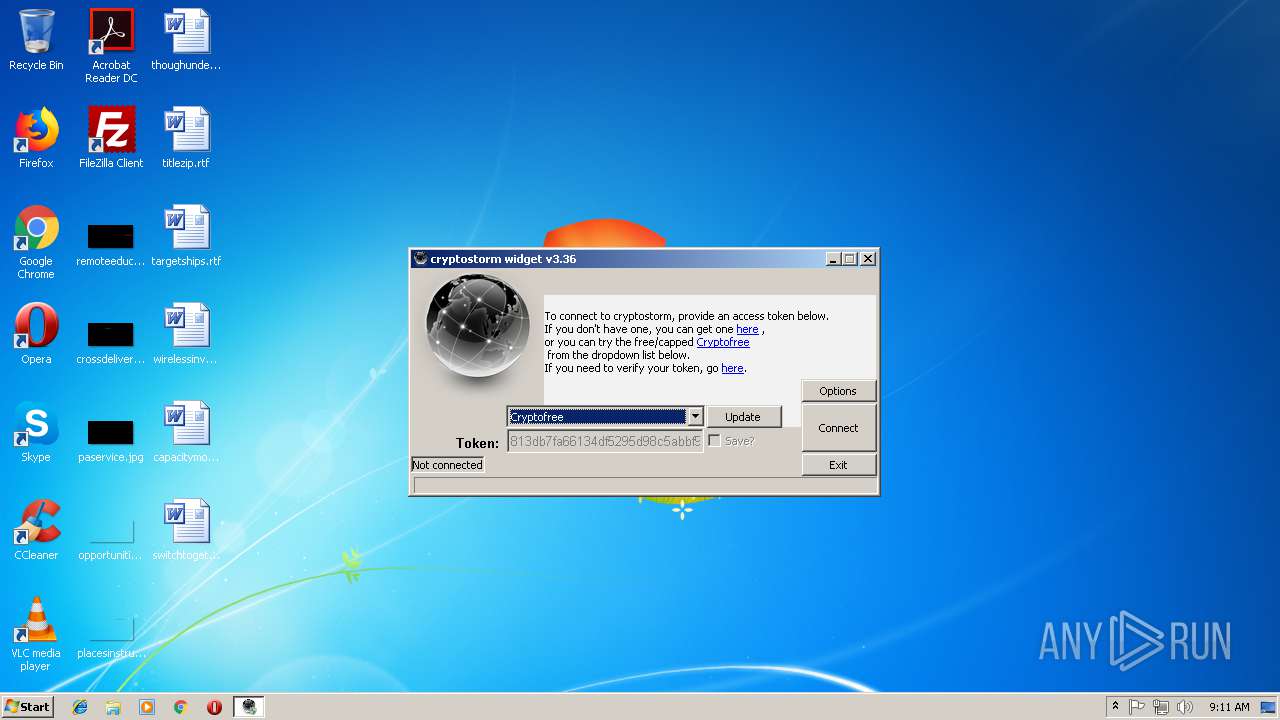
| CompanyName: | cryptostorm.is private network |
| FileDescription: | Cryptostorm Client Setup |
| FileVersion: | 3.36 |
| LegalCopyright: | |
| ProductName: | cstorm network access widget |
| ProductVersion: | 3.36 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 14-Jun-2018 13:27:46 |
| Detected languages: |
|
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | cryptostorm.is private network |
| FileDescription: | Cryptostorm Client Setup |
| FileVersion: | 3.36 |
| LegalCopyright: | - |
| ProductName: | cstorm network access widget |
| ProductVersion: | 3.36 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 8 |
| Time date stamp: | 14-Jun-2018 13:27:46 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0000F25C | 0x0000F400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.37588 |
.itext | 0x00011000 | 0x00000FA4 | 0x00001000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.77877 |
.data | 0x00012000 | 0x00000C8C | 0x00000E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.30283 |
.bss | 0x00013000 | 0x000056BC | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x00019000 | 0x00000E04 | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.59781 |
.tls | 0x0001A000 | 0x00000008 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x0001B000 | 0x00000018 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 0.204488 |
.rsrc | 0x0001C000 | 0x0000B200 | 0x0000B200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.14263 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.13965 | 1580 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 3.47151 | 1384 | UNKNOWN | Dutch - Netherlands | RT_ICON |
3 | 3.91708 | 744 | UNKNOWN | Dutch - Netherlands | RT_ICON |
4 | 3.91366 | 2216 | UNKNOWN | Dutch - Netherlands | RT_ICON |
4091 | 2.56031 | 104 | UNKNOWN | UNKNOWN | RT_STRING |
4092 | 3.25287 | 212 | UNKNOWN | UNKNOWN | RT_STRING |
4093 | 3.26919 | 164 | UNKNOWN | UNKNOWN | RT_STRING |
4094 | 3.33268 | 684 | UNKNOWN | UNKNOWN | RT_STRING |
4095 | 3.34579 | 844 | UNKNOWN | UNKNOWN | RT_STRING |
4096 | 3.28057 | 660 | UNKNOWN | UNKNOWN | RT_STRING |
Imports
advapi32.dll |
comctl32.dll |
kernel32.dll |
oleaut32.dll |
user32.dll |
Total processes
185
Monitored processes
142
Malicious processes
26
Suspicious processes
10
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 280 | C:\Windows\system32\ipconfig.exe /flushdns | C:\Windows\system32\ipconfig.exe | — | csvpn32.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: IP Configuration Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 296 | cmd.exe /x/d/c "..\bin\tap32.exe remove tap0901 2>&1" | C:\Windows\system32\cmd.exe | — | client.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 456 | netsh advfirewall firewall add rule name="IPv6 protocol 60" protocol=60 action=block dir=out | C:\Windows\system32\netsh.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 588 | netsh advfirewall firewall add rule name="No STUN leak for j00!" dir=in action=block protocol=UDP remoteport=3478 | C:\Windows\system32\netsh.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1008 | ..\bin\32\csvpn32.exe --show-adapters | C:\Program Files\Cryptostorm Client\bin\32\csvpn32.exe | — | cmd.exe | |||||||||||
User: admin Company: The OpenVPN Project Integrity Level: HIGH Description: OpenVPN Daemon Exit code: 0 Version: 2.3.18.0 Modules
| |||||||||||||||
| 1140 | cmd.exe /x/d/c "..\bin\32\csvpn32.exe --show-adapters 2>&1" | C:\Windows\system32\cmd.exe | — | client.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1288 | netsh advfirewall firewall add rule name="IPv6 protocol 43" protocol=43 action=block dir=out | C:\Windows\system32\netsh.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1332 | ..\bin\32\cs-dnsc-p.exe | C:\Program Files\Cryptostorm Client\bin\32\cs-dnsc-p.exe | client.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1380 | cmd.exe /x/d/c "..\bin\32\csvpn32.exe --show-adapters 2>&1" | C:\Windows\system32\cmd.exe | — | client.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1396 | netsh advfirewall firewall add rule name="IPv6 protocol 44" protocol=44 action=block dir=out | C:\Windows\system32\netsh.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
5 610
Read events
1 822
Write events
3 620
Delete events
168
Modification events
| (PID) Process: | (2644) cryptostorm_setup.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Owner |
Value: 540A0000A2B964D4B1A1D401 | |||
| (PID) Process: | (2644) cryptostorm_setup.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | SessionHash |
Value: 6E0C4D07ECEF43FAB177AA78D467D1D2122D9B2461441E9E7591104476CFE747 | |||
| (PID) Process: | (2644) cryptostorm_setup.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Sequence |
Value: 1 | |||
| (PID) Process: | (2644) cryptostorm_setup.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | RegFilesHash |
Value: 666F0F5CA0D76FB11AB8774C756D1EA107DC0CED775DF464B1C8A88446475A6F | |||
| (PID) Process: | (2644) cryptostorm_setup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{35A52EE3-6D23-4AA6-B881-3F10658D626C}_is1 |
| Operation: | write | Name: | Inno Setup: Setup Version |
Value: 5.6.1 (u) | |||
| (PID) Process: | (2644) cryptostorm_setup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{35A52EE3-6D23-4AA6-B881-3F10658D626C}_is1 |
| Operation: | write | Name: | Inno Setup: App Path |
Value: C:\Program Files\Cryptostorm Client | |||
| (PID) Process: | (2644) cryptostorm_setup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{35A52EE3-6D23-4AA6-B881-3F10658D626C}_is1 |
| Operation: | write | Name: | InstallLocation |
Value: C:\Program Files\Cryptostorm Client\ | |||
| (PID) Process: | (2644) cryptostorm_setup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{35A52EE3-6D23-4AA6-B881-3F10658D626C}_is1 |
| Operation: | write | Name: | Inno Setup: Icon Group |
Value: Cryptostorm Client | |||
| (PID) Process: | (2644) cryptostorm_setup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{35A52EE3-6D23-4AA6-B881-3F10658D626C}_is1 |
| Operation: | write | Name: | Inno Setup: User |
Value: admin | |||
| (PID) Process: | (2644) cryptostorm_setup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{35A52EE3-6D23-4AA6-B881-3F10658D626C}_is1 |
| Operation: | write | Name: | Inno Setup: Selected Tasks |
Value: | |||
Executable files
138
Suspicious files
86
Text files
416
Unknown types
31
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2644 | cryptostorm_setup.tmp | C:\Program Files\Cryptostorm Client\is-HU7LQ.tmp | — | |
MD5:— | SHA256:— | |||
| 2644 | cryptostorm_setup.tmp | C:\Program Files\Cryptostorm Client\bin\is-00300.tmp | — | |
MD5:— | SHA256:— | |||
| 2644 | cryptostorm_setup.tmp | C:\Program Files\Cryptostorm Client\bin\is-00278.tmp | — | |
MD5:— | SHA256:— | |||
| 2644 | cryptostorm_setup.tmp | C:\Program Files\Cryptostorm Client\bin\is-FDNGO.tmp | — | |
MD5:— | SHA256:— | |||
| 2644 | cryptostorm_setup.tmp | C:\Program Files\Cryptostorm Client\bin\is-S47QE.tmp | — | |
MD5:— | SHA256:— | |||
| 2644 | cryptostorm_setup.tmp | C:\Program Files\Cryptostorm Client\bin\is-THUE3.tmp | — | |
MD5:— | SHA256:— | |||
| 2644 | cryptostorm_setup.tmp | C:\Program Files\Cryptostorm Client\bin\is-AJH0L.tmp | — | |
MD5:— | SHA256:— | |||
| 2644 | cryptostorm_setup.tmp | C:\Program Files\Cryptostorm Client\bin\is-V4TEP.tmp | — | |
MD5:— | SHA256:— | |||
| 2644 | cryptostorm_setup.tmp | C:\Program Files\Cryptostorm Client\bin\is-R4HBI.tmp | — | |
MD5:— | SHA256:— | |||
| 2644 | cryptostorm_setup.tmp | C:\Program Files\Cryptostorm Client\bin\is-1C9AO.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
64
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
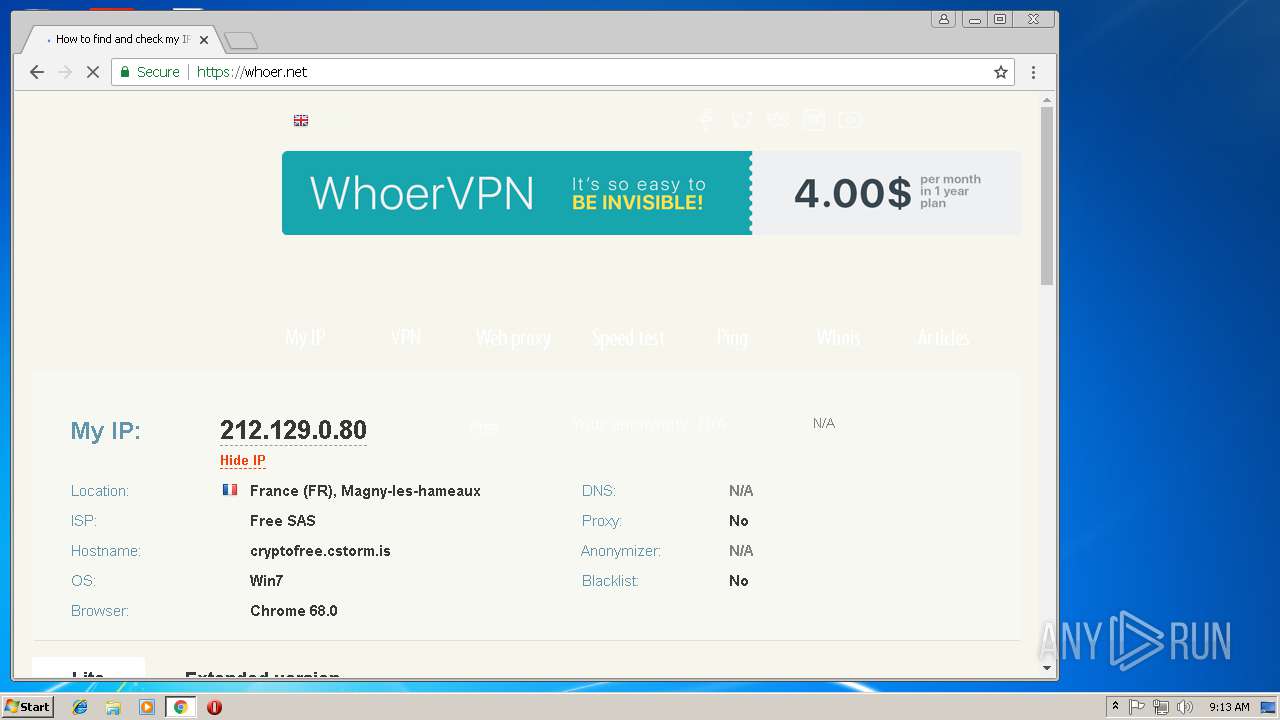
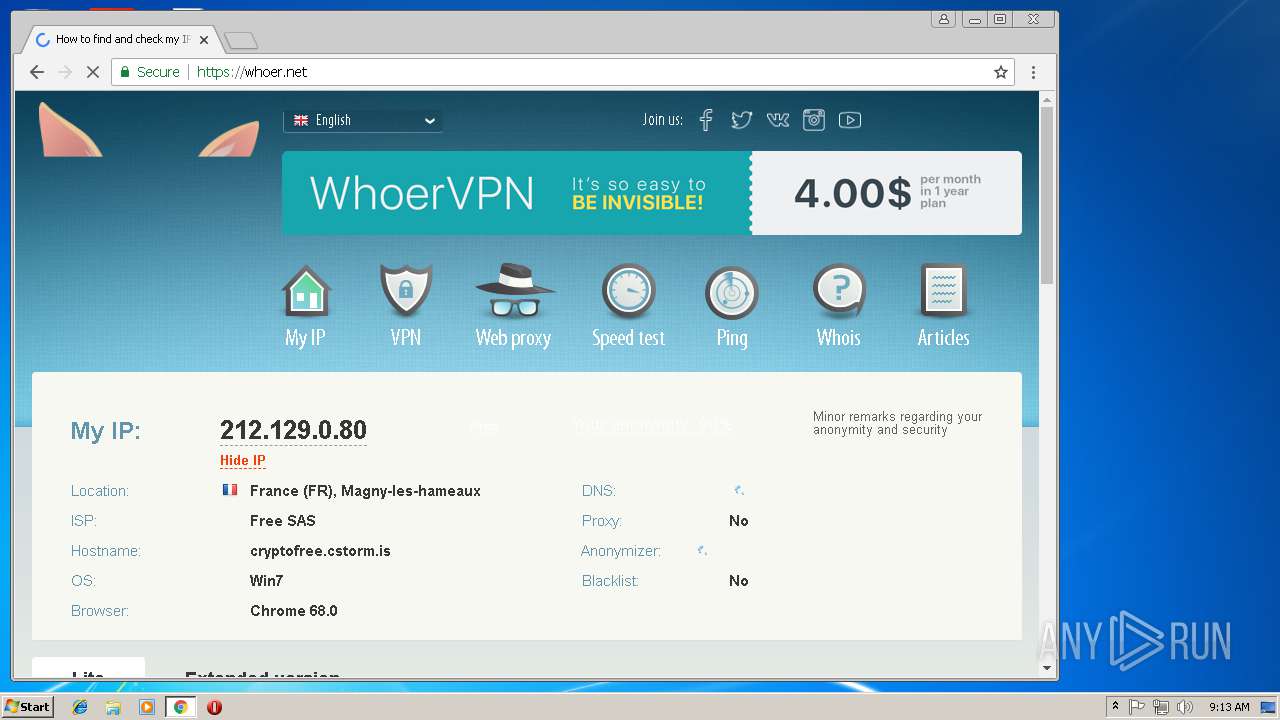
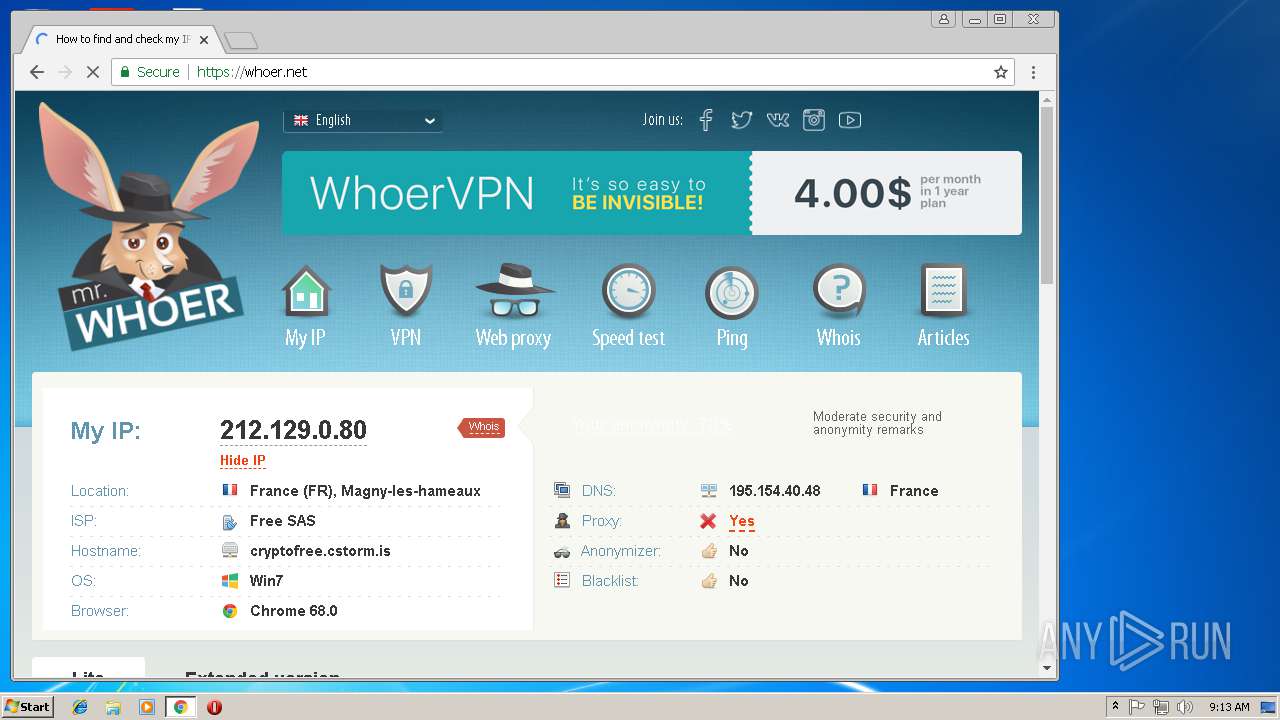
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1332 | cs-dnsc-p.exe | 5.254.96.195:443 | — | Voxility S.R.L. | RO | unknown |
1332 | cs-dnsc-p.exe | 198.7.58.227:443 | — | Leaseweb USA, Inc. | US | unknown |
1332 | cs-dnsc-p.exe | 104.238.195.139:443 | — | Versaweb, LLC | US | unknown |
1332 | cs-dnsc-p.exe | 173.234.56.115:443 | — | Nobis Technology Group, LLC | US | unknown |
1332 | cs-dnsc-p.exe | 173.208.95.75:443 | — | Nobis Technology Group, LLC | US | unknown |
1332 | cs-dnsc-p.exe | 5.133.8.187:443 | — | Artnet Spolka z ograniczona odpowiedzialnoscia | PL | unknown |
1332 | cs-dnsc-p.exe | 212.129.46.86:443 | — | Online S.a.s. | FR | unknown |
1332 | cs-dnsc-p.exe | 213.163.64.208:443 | — | i3D.net B.V | NL | unknown |
1332 | cs-dnsc-p.exe | 64.120.5.251:443 | — | — | US | unknown |
1332 | cs-dnsc-p.exe | 81.17.31.34:443 | — | Private Layer INC | CH | unknown |