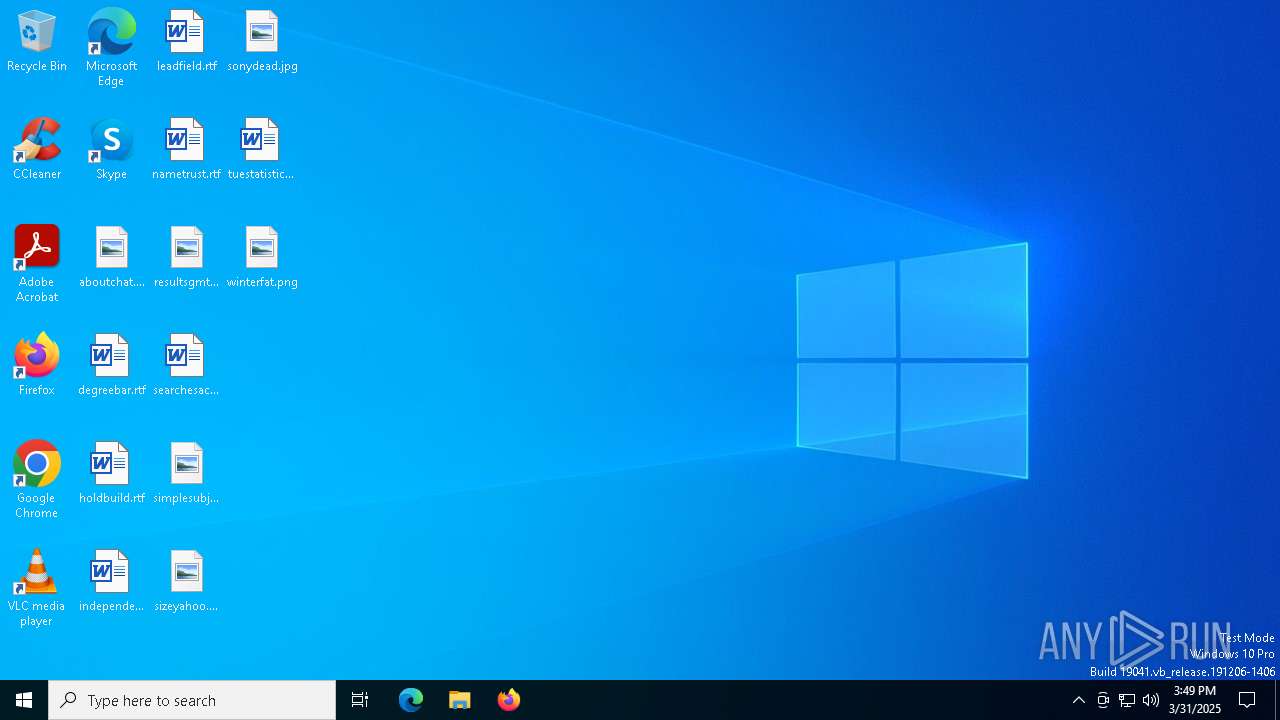
| File name: | Agent_Install.exe |
| Full analysis: | https://app.any.run/tasks/265caea7-6419-47dd-866e-b70aae27d95d |
| Verdict: | Malicious activity |
| Analysis date: | March 31, 2025, 15:49:07 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows, 4 sections |
| MD5: | F0CDF8C81C39103ECDD78BE577024C0A |
| SHA1: | 6EC07C440744EE7121661BA9A7D1D41250B6A275 |
| SHA256: | D8F0A8B6DC7F5F70798A61DCF2AA5D51DF6810E76496753C5FE68A20F6B88491 |
| SSDEEP: | 98304:hTSm0EdutnXW80otbFkkkkkk37MOGwwK3INNoA3uw7iR8VjI1jAH8RPxj05Bjyo7:XO2E1 |
MALICIOUS
Vulnerable driver has been detected
- LTSVC.exe (PID: 5376)
Starts NET.EXE for service management
- LTSVC.exe (PID: 5376)
- cmd.exe (PID: 7808)
- net.exe (PID: 6240)
Registers / Runs the DLL via REGSVR32.EXE
- LTSVC.exe (PID: 5376)
Create files in the Startup directory
- LTSVC.exe (PID: 5376)
Executing a file with an untrusted certificate
- LTTray.exe (PID: 864)
SUSPICIOUS
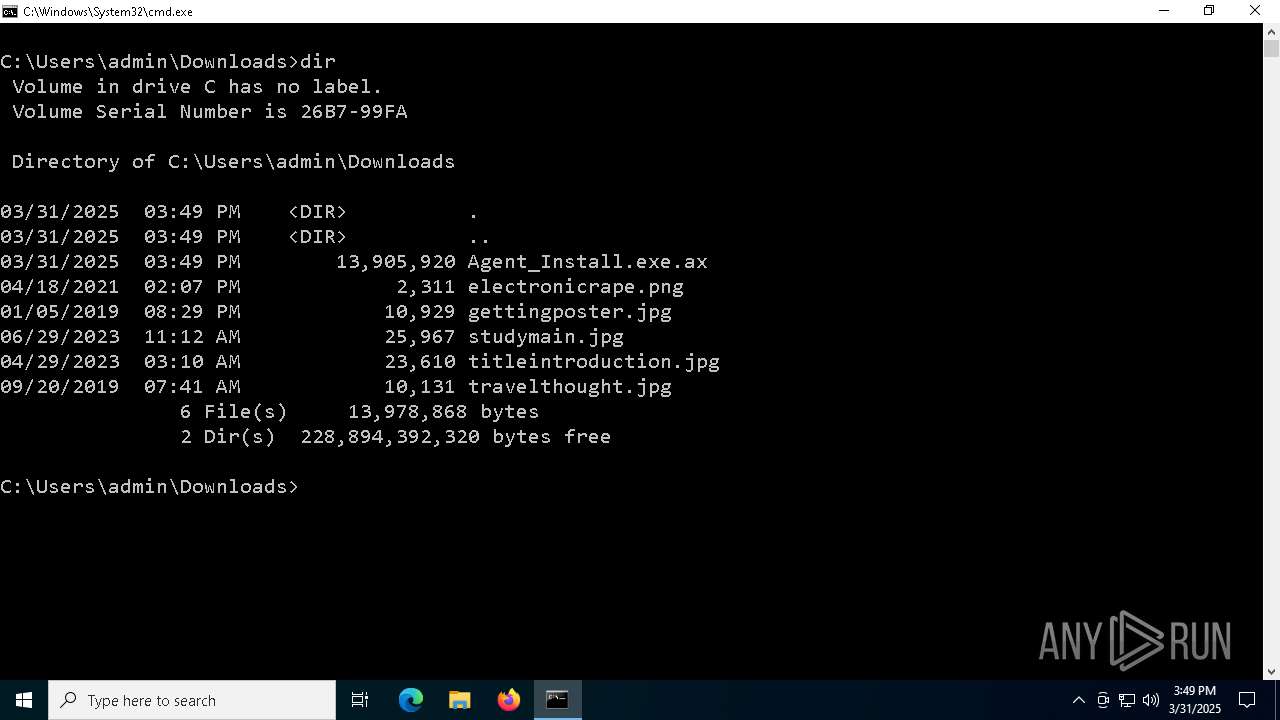
The executable file from the user directory is run by the CMD process
- Agent_Install.exe (PID: 7984)
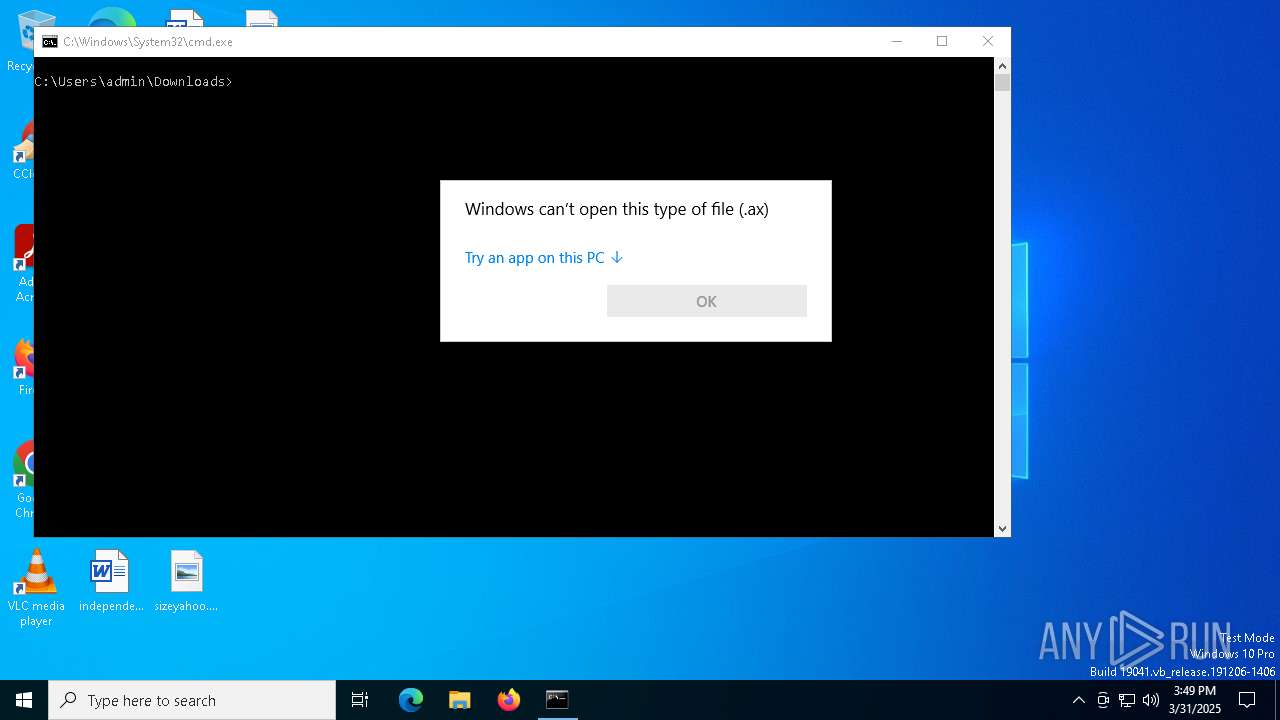
- Agent_Install.exe.ax (PID: 7516)
- Agent_Install.exe (PID: 8096)
- Agent_Install.exe (PID: 7996)
Starts application with an unusual extension
- cmd.exe (PID: 7456)
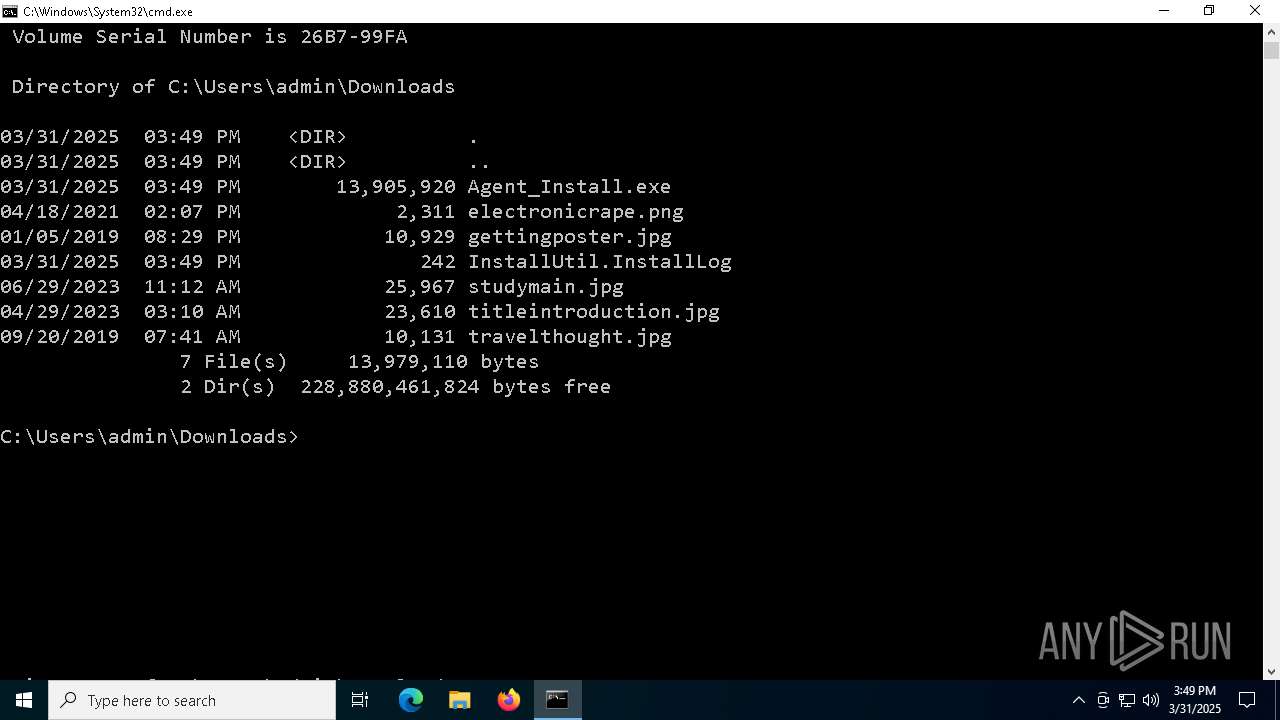
Executable content was dropped or overwritten
- cmd.exe (PID: 7456)
- Agent_Install.exe (PID: 8096)
- LTSVC.exe (PID: 5376)
Reads security settings of Internet Explorer
- Agent_Install.exe (PID: 8096)
- LTSVC.exe (PID: 5376)
- LTTray.exe (PID: 864)
Reads the date of Windows installation
- Agent_Install.exe (PID: 8096)
- LTSVC.exe (PID: 5376)
Creates or modifies Windows services
- InstallUtil.exe (PID: 6488)
- LTSVC.exe (PID: 5376)
Executes as Windows Service
- LTSVC.exe (PID: 5376)
- LTSvcMon.exe (PID: 1040)
Uses ROUTE.EXE to obtain the routing table information
- LTSVC.exe (PID: 5376)
Drops a system driver (possible attempt to evade defenses)
- LTSVC.exe (PID: 5376)
Process drops legitimate windows executable
- LTSVC.exe (PID: 5376)
Uses NETSH.EXE to add a firewall rule or allowed programs
- cmd.exe (PID: 7148)
- cmd.exe (PID: 2772)
- cmd.exe (PID: 4944)
- cmd.exe (PID: 6576)
- cmd.exe (PID: 3896)
- cmd.exe (PID: 5744)
- cmd.exe (PID: 8040)
- cmd.exe (PID: 8048)
- cmd.exe (PID: 6744)
- cmd.exe (PID: 7400)
- cmd.exe (PID: 780)
- cmd.exe (PID: 7704)
- cmd.exe (PID: 2064)
Starts CMD.EXE for commands execution
- LTSVC.exe (PID: 5376)
Uses NETSH.EXE to delete a firewall rule or allowed programs
- cmd.exe (PID: 7392)
- cmd.exe (PID: 6700)
- cmd.exe (PID: 7360)
- cmd.exe (PID: 7800)
Creates/Modifies COM task schedule object
- regsvr32.exe (PID: 6560)
INFO
Reads Microsoft Office registry keys
- OpenWith.exe (PID: 7552)
Reads the machine GUID from the registry
- Agent_Install.exe (PID: 8096)
- InstallUtil.exe (PID: 6488)
- LTSVC.exe (PID: 5376)
- InstallUtil.exe (PID: 6988)
- LTSvcMon.exe (PID: 1040)
- LTTray.exe (PID: 864)
Reads the computer name
- Agent_Install.exe (PID: 8096)
- InstallUtil.exe (PID: 6488)
- LTSVC.exe (PID: 5376)
- InstallUtil.exe (PID: 6988)
- LTSvcMon.exe (PID: 1040)
- LTTray.exe (PID: 864)
Checks supported languages
- Agent_Install.exe (PID: 8096)
- InstallUtil.exe (PID: 6488)
- LTSVC.exe (PID: 5376)
- LTSvcMon.exe (PID: 1040)
- InstallUtil.exe (PID: 6988)
- LTTray.exe (PID: 864)
Disables trace logs
- Agent_Install.exe (PID: 8096)
Create files in a temporary directory
- Agent_Install.exe (PID: 8096)
Reads Environment values
- Agent_Install.exe (PID: 8096)
- LTSVC.exe (PID: 5376)
- LTSvcMon.exe (PID: 1040)
Checks proxy server information
- Agent_Install.exe (PID: 8096)
- LTTray.exe (PID: 864)
CONNECTWISE has been detected
- Agent_Install.exe (PID: 8096)
- InstallUtil.exe (PID: 6488)
- LTSVC.exe (PID: 5376)
- InstallUtil.exe (PID: 6988)
- LTSvcMon.exe (PID: 1040)
- LTTray.exe (PID: 864)
Process checks computer location settings
- Agent_Install.exe (PID: 8096)
The sample compiled with french language support
- LTSVC.exe (PID: 5376)
Prints a route via ROUTE.EXE
- ROUTE.EXE (PID: 1052)
Creates files in the program directory
- LTSVC.exe (PID: 5376)
The sample compiled with english language support
- LTSVC.exe (PID: 5376)
Reads the software policy settings
- LTTray.exe (PID: 864)
- LTSVC.exe (PID: 5376)
Creates files or folders in the user directory
- LTTray.exe (PID: 864)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .ax | | | DirectShow filter (35.6) |
|---|---|---|
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (12.9) |
| .exe | | | InstallShield setup (7.6) |
| .exe | | | Win32 EXE PECompact compressed (generic) (7.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2011:11:28 22:15:16+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 8 |
| CodeSize: | 13875712 |
| InitializedDataSize: | 29184 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xd3d9ce |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 41.202.4349.18474 |
| ProductVersionNumber: | 3.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | LabTech Silent Installer. |
| CompanyName: | LabTech Software |
| FileDescription: | LTSilent |
| FileVersion: | 41.202.4349.18474 |
| InternalName: | LTSilent.exe |
| LegalCopyright: | Copyright© 2005-2011 LabTech Software |
| OriginalFileName: | LTSilent.exe |
| ProductName: | LabTech MSP |
| ProductVersion: | 3 |
| AssemblyVersion: | 41.202.4349.18474 |
Total processes
208
Monitored processes
77
Malicious processes
4
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 300 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 616 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 644 | netsh advfirewall firewall Add rule name="Allow Local Redir" dir=in protocol=tcp localip=127.0.0.1 action=allow | C:\Windows\System32\netsh.exe | — | cmd.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Network Command Shell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 780 | "CMD.exe" /c netsh advfirewall firewall add rule name="AgentTray" dir=in action=allow program="%Windir%\LTsvc\LTTray.exe" enable=yes | C:\Windows\System32\cmd.exe | — | LTSVC.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 856 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 864 | C:\WINDOWS\LTsvc\LTTray.exe | C:\Windows\LTSvc\LTTray.exe | LTSVC.exe | ||||||||||||
User: admin Company: LabTech Software Integrity Level: MEDIUM Description: LabTech Tray Version: 41.101.4337.28669 Modules
| |||||||||||||||
| 1040 | "C:\WINDOWS\LTsvc\LTSvcMon.exe" | C:\Windows\LTSvc\LTSvcMon.exe | — | services.exe | |||||||||||
User: SYSTEM Company: LabTech Software Integrity Level: SYSTEM Description: LabTech Service Watchdog Version: 41.102.4302.30122 Modules
| |||||||||||||||
| 1052 | "route" print | C:\Windows\System32\ROUTE.EXE | — | LTSVC.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: TCP/IP Route Command Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1052 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1548 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
17 441
Read events
17 319
Write events
122
Delete events
0
Modification events
| (PID) Process: | (8096) Agent_Install.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Agent_Install_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (8096) Agent_Install.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Agent_Install_RASAPI32 |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (8096) Agent_Install.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Agent_Install_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (8096) Agent_Install.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Agent_Install_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: | |||
| (PID) Process: | (8096) Agent_Install.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Agent_Install_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: | |||
| (PID) Process: | (8096) Agent_Install.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Agent_Install_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (8096) Agent_Install.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Agent_Install_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (8096) Agent_Install.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Agent_Install_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (8096) Agent_Install.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Agent_Install_RASMANCS |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (8096) Agent_Install.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Agent_Install_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
Executable files
23
Suspicious files
6
Text files
9
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 8096 | Agent_Install.exe | C:\Windows\LTSvc\LabTech.ico | image | |
MD5:A13E8D3448A37152C9C6D70F2D60CC4F | SHA256:359F8A86047C64DCE9ABC722AB837ADE977ABBAB848C1C2CB760B01EECDC218F | |||
| 6488 | InstallUtil.exe | C:\Windows\LTSvc\LTSVC.InstallState | text | |
MD5:6EE98DF604A68C463EFA2EBE0A905B4E | SHA256:7D513E492F77753DA3FE2A95F6E34A4938C67019421367625A61C31BBF7EAE36 | |||
| 8096 | Agent_Install.exe | C:\Windows\LTSvc\LTTray.exe | executable | |
MD5:531B021377826C63A4D54DFC9616738A | SHA256:DC3D3B390EBC815674F861F44EC8BD06E49C05AC53FFB313209C9DEBC769D8F6 | |||
| 5376 | LTSVC.exe | C:\Windows\LTSvc\cpuidsdk64.dll | executable | |
MD5:13BBBDFF8FDC4E9D2B91C629EE9729B8 | SHA256:7968C19E94863397578894EB59E9F9D0B9682D24FFFC9AA7917E4C08987F3E64 | |||
| 5376 | LTSVC.exe | C:\Windows\LTSvc\Interfaces.dll | executable | |
MD5:68D284203B4EA327B0504294D0A68D70 | SHA256:BAA8E3E150D95905C17A73A0467D748685F00E7841EB62A24ADD3CB986291B60 | |||
| 5376 | LTSVC.exe | C:\Windows\LTSvc\wodVPN.dll | executable | |
MD5:97C73BD1CC0011D111316D924532BE35 | SHA256:3E31FAC9BA997FAF1ADE072050AC56CF4D1BDDD47F5DD342825E04E8AF91A9FA | |||
| 8096 | Agent_Install.exe | C:\Windows\LTSvc\LTSVC.exe | executable | |
MD5:503E47FB6249D7D9AC2CA3FE7810C3C1 | SHA256:C1692BFF9ECD79AFDB161616E84D1B7D07167AD8F9255F722143C501EA94B763 | |||
| 7456 | cmd.exe | C:\Users\admin\Downloads\Agent_Install.exe | executable | |
MD5:F0CDF8C81C39103ECDD78BE577024C0A | SHA256:D8F0A8B6DC7F5F70798A61DCF2AA5D51DF6810E76496753C5FE68A20F6B88491 | |||
| 5376 | LTSVC.exe | C:\Windows\LTSvc\LTErrors.txt | text | |
MD5:A7FABF08E5151044B717F95D3C88A7E9 | SHA256:5969B492BC355A4251BB3CF8671DC03155216A24442C480C042533AF0762400F | |||
| 5376 | LTSVC.exe | C:\Windows\LTSvc\cpuidsdk.dll | executable | |
MD5:13BBBDFF8FDC4E9D2B91C629EE9729B8 | SHA256:7968C19E94863397578894EB59E9F9D0B9682D24FFFC9AA7917E4C08987F3E64 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
19
DNS requests
14
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.48.23.175:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | DE | binary | 825 b | whitelisted |
8160 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | QA | binary | 419 b | whitelisted |
8160 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | QA | binary | 407 b | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | DE | binary | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2568 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2104 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.48.23.175:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3216 | svchost.exe | 20.7.2.167:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6544 | svchost.exe | 40.126.31.0:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6544 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
8160 | SIHClient.exe | 20.12.23.50:443 | slscr.update.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
labtech.provationtech.com |
| unknown |