| File name: | setup_rk_free_229_s.exe |
| Full analysis: | https://app.any.run/tasks/83c2aad5-b2c2-4d36-8a24-feacf275832e |
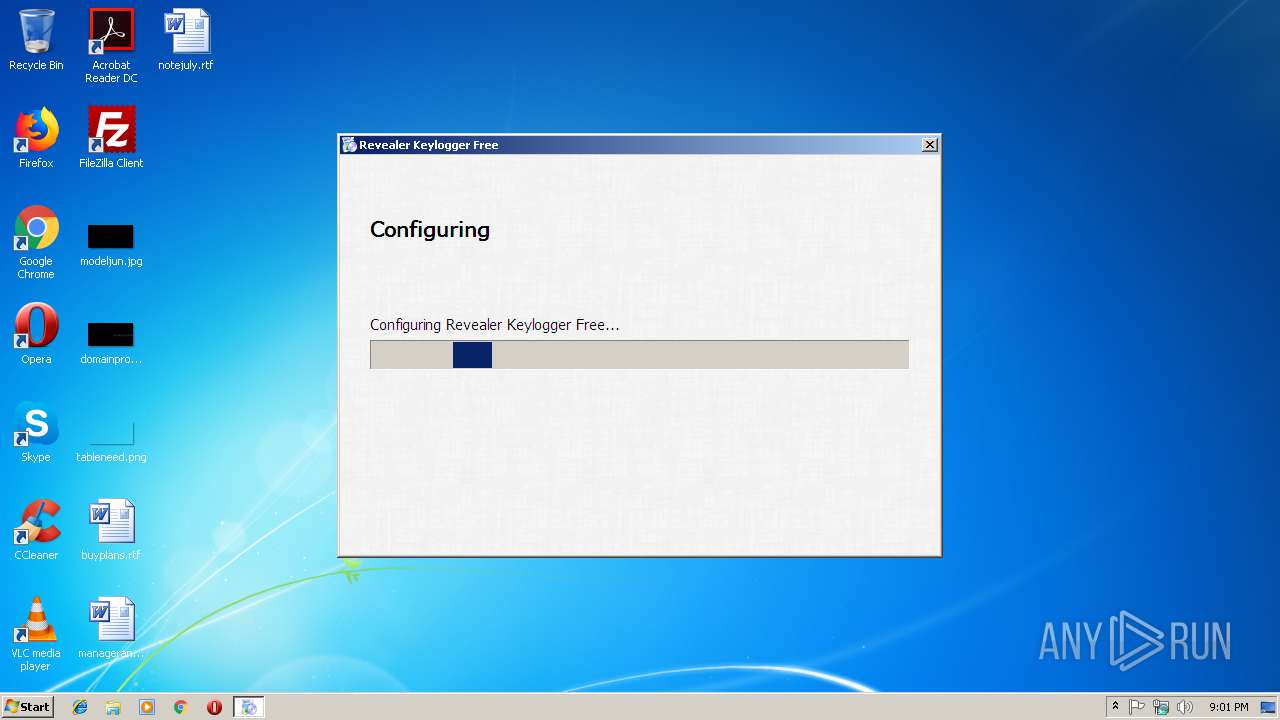
| Verdict: | Suspicious activity |
| Analysis date: | March 19, 2019, 21:01:16 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | C9C1435B1D007A820266C29299B1194A |
| SHA1: | 5EA361FCAF072C4F25D2CDC198E88DDB8B537846 |
| SHA256: | D8E5FE0ACA6593EA1524879C305A4C7C06CA101D5BC781EADECA4CBDE8720D88 |
| SSDEEP: | 24576:tX8D2lHV4a/G9x1UhjU+EwhrrngwmsemZEqda7wLBk9mzLsKXcUpS8aNNGy+6m8U:KGHV477/bornT9xZddHkmLx3OAQxhk |
MALICIOUS
Application was dropped or rewritten from another process
- setup.exe (PID: 2132)
- 7za.exe (PID: 3092)
- rvlkl.exe (PID: 2556)
- rvlkl.exe (PID: 2556)
Writes to a start menu file
- setup.exe (PID: 2132)
SUSPICIOUS
Executable content was dropped or overwritten
- setup_rk_free_229_s.exe (PID: 2768)
- setup.exe (PID: 2132)
- 7za.exe (PID: 3092)
Creates files in the Windows directory
- setup.exe (PID: 2132)
Creates files in the program directory
- setup.exe (PID: 2132)
- rvlkl.exe (PID: 2556)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | InstallShield setup (54.3) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (34.8) |
| .exe | | | Win32 Executable (generic) (5.6) |
| .exe | | | Generic Win/DOS Executable (2.5) |
| .exe | | | DOS Executable Generic (2.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:07:14 17:22:00+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 14.11 |
| CodeSize: | 46592 |
| InitializedDataSize: | 1307648 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x2492 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 14-Jul-2018 15:22:00 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000108 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 14-Jul-2018 15:22:00 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0000B527 | 0x0000B600 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.61605 |
.rdata | 0x0000D000 | 0x00005F94 | 0x00006000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.92725 |
.data | 0x00013000 | 0x000012F4 | 0x00000800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.0211 |
.rsrc | 0x00015000 | 0x00136ED0 | 0x00137000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.44224 |
.reloc | 0x0014C000 | 0x00000F60 | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.47339 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.09715 | 1498 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 3.47151 | 1384 | UNKNOWN | English - United States | RT_ICON |
3 | 3.91708 | 744 | UNKNOWN | English - United States | RT_ICON |
4 | 3.91366 | 2216 | UNKNOWN | English - United States | RT_ICON |
500 | 2.64576 | 62 | UNKNOWN | English - United States | RT_GROUP_ICON |
530 | 6.63812 | 733696 | UNKNOWN | English - United States | UNKNOWN |
531 | 7.9993 | 254298 | UNKNOWN | English - United States | UNKNOWN |
532 | 7.99924 | 278794 | UNKNOWN | English - United States | UNKNOWN |
Imports
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
SHLWAPI.dll |
USER32.dll |
ole32.dll |
Total processes
40
Monitored processes
6
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2132 | "C:\Users\admin\AppData\Local\Temp\setup.exe" | C:\Users\admin\AppData\Local\Temp\setup.exe | setup_rk_free_229_s.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
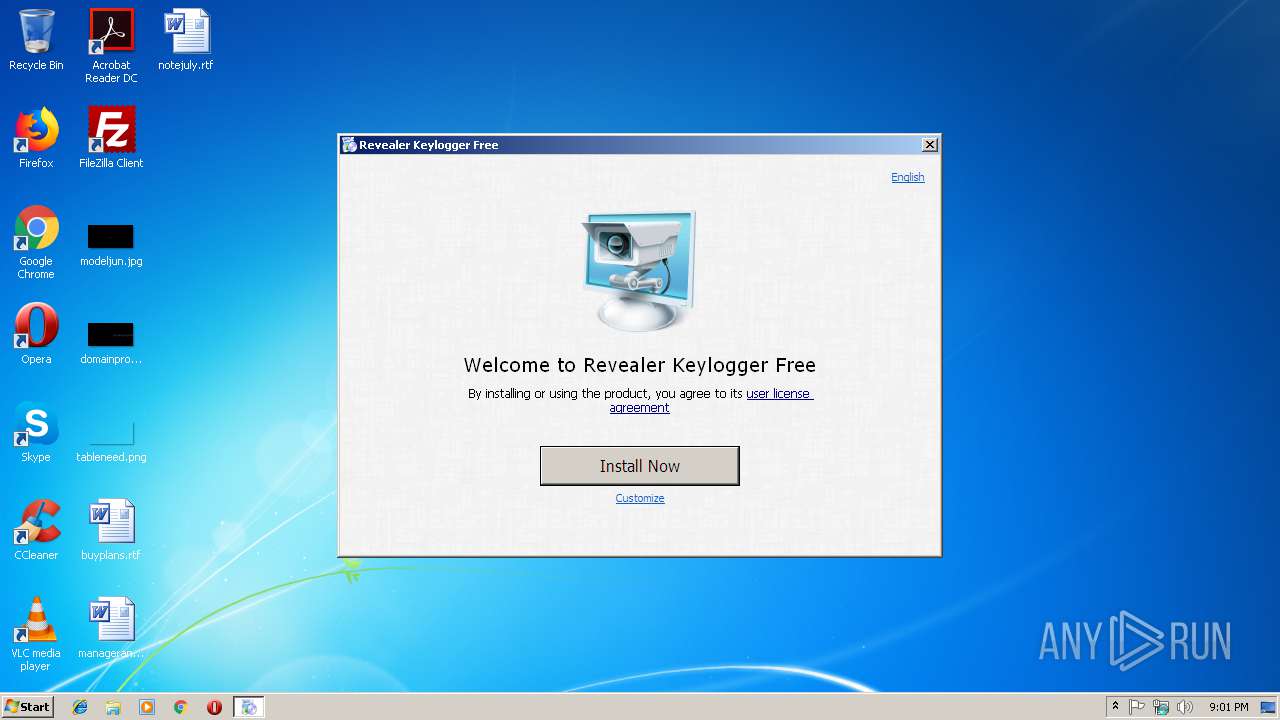
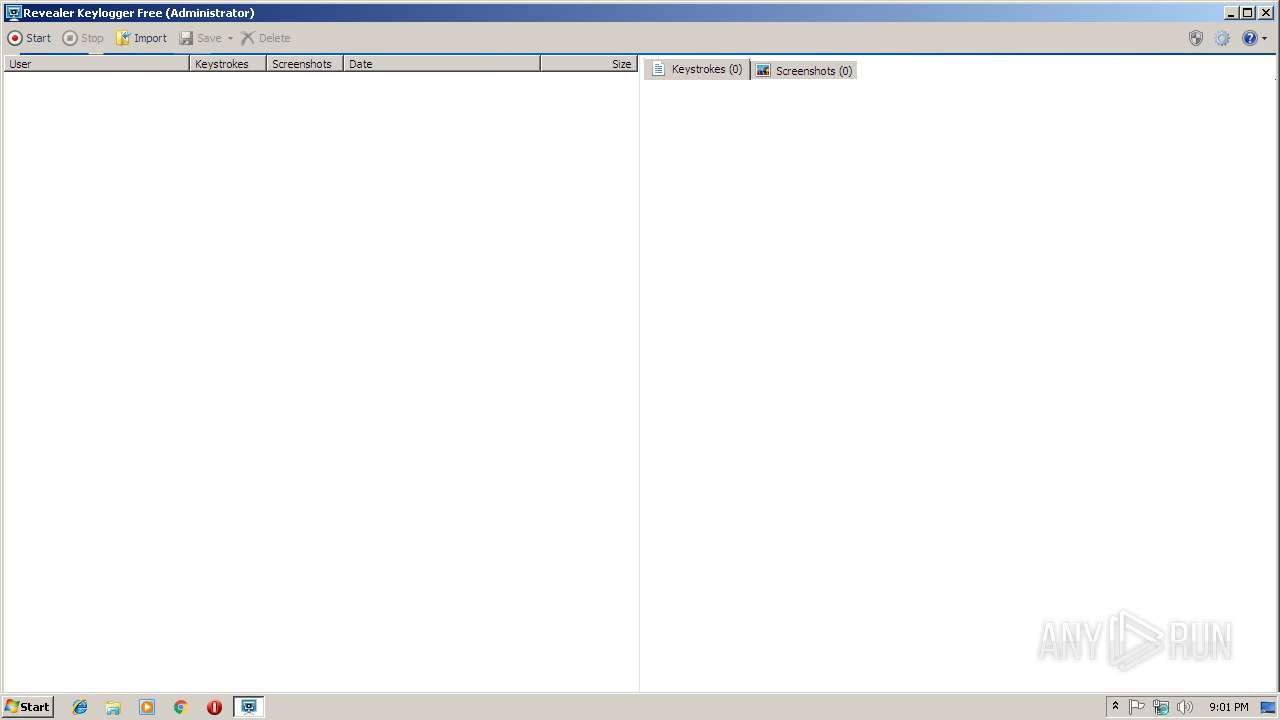
| 2556 | "C:\Windows\system32\rvlkl.exe" | C:\Windows\system32\rvlkl.exe | — | setup.exe | |||||||||||
User: admin Company: Logixoft Integrity Level: HIGH Description: Revealer Keylogger Free Exit code: 3221226540 Version: 2.2.9.0 Modules
| |||||||||||||||
| 2556 | "C:\Windows\system32\rvlkl.exe" | C:\Windows\system32\rvlkl.exe | — | setup.exe | |||||||||||
User: admin Company: Logixoft Integrity Level: HIGH Description: Revealer Keylogger Free Exit code: 0 Version: 2.2.9.0 Modules
| |||||||||||||||
| 2768 | "C:\Users\admin\AppData\Local\Temp\setup_rk_free_229_s.exe" | C:\Users\admin\AppData\Local\Temp\setup_rk_free_229_s.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
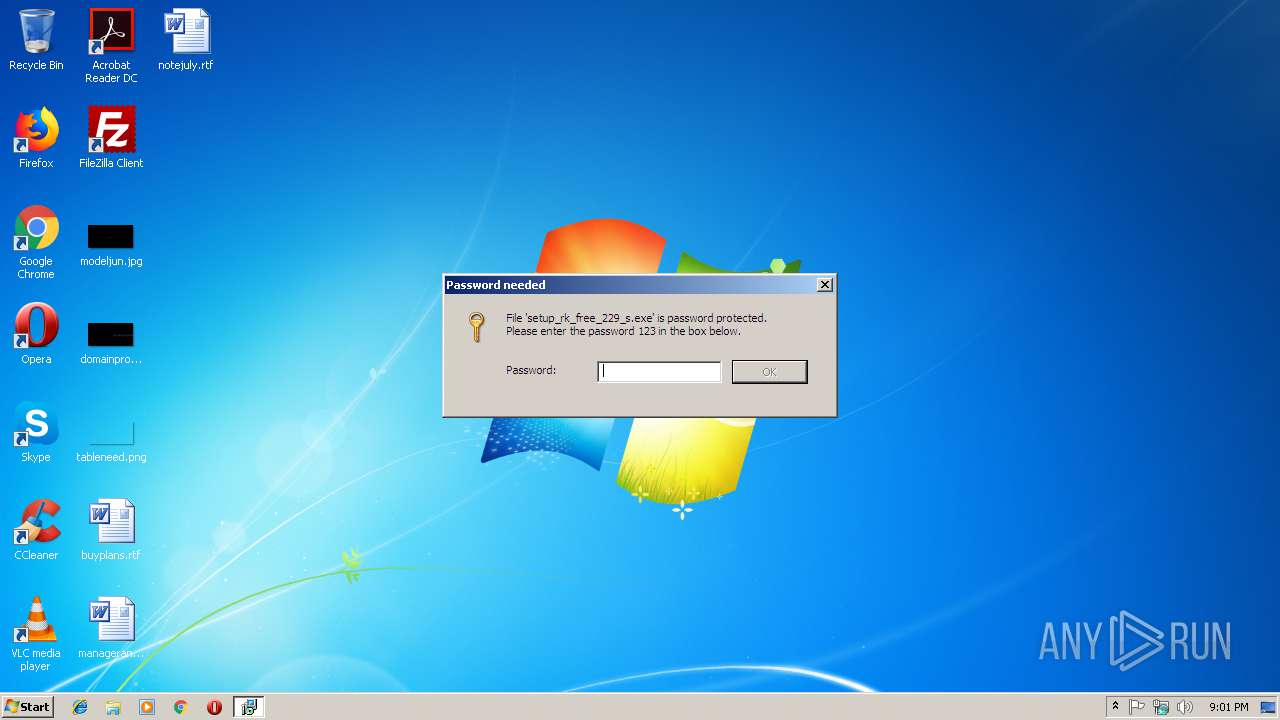
| 3092 | "C:\Users\admin\AppData\Local\Temp\7za.exe" x setup.7z setup.exe -p123 | C:\Users\admin\AppData\Local\Temp\7za.exe | setup_rk_free_229_s.exe | ||||||||||||
User: admin Company: Igor Pavlov Integrity Level: HIGH Description: 7-Zip Standalone Console Exit code: 0 Version: 18.05 Modules
| |||||||||||||||
| 3468 | "C:\Users\admin\AppData\Local\Temp\setup_rk_free_229_s.exe" | C:\Users\admin\AppData\Local\Temp\setup_rk_free_229_s.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
Total events
555
Read events
545
Write events
10
Delete events
0
Modification events
| (PID) Process: | (2768) setup_rk_free_229_s.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2768) setup_rk_free_229_s.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2132) setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows Defender\Exclusions\Paths |
| Operation: | write | Name: | C:\Windows\system32\rvlkl.exe |
Value: 0 | |||
| (PID) Process: | (2132) setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows Defender\Exclusions\Processes |
| Operation: | write | Name: | C:\Windows\system32\rvlkl.exe |
Value: 0 | |||
| (PID) Process: | (2132) setup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2132) setup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
3
Suspicious files
4
Text files
1
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2132 | setup.exe | C:\ProgramData\rvlkl\conf_ | — | |
MD5:— | SHA256:— | |||
| 2556 | rvlkl.exe | C:\ProgramData\rvlkl\conf_ | — | |
MD5:— | SHA256:— | |||
| 3092 | 7za.exe | C:\Users\admin\AppData\Local\Temp\setup.exe | executable | |
MD5:— | SHA256:— | |||
| 2768 | setup_rk_free_229_s.exe | C:\Users\admin\AppData\Local\Temp\setup.7z | compressed | |
MD5:— | SHA256:— | |||
| 2132 | setup.exe | C:\ProgramData\rvlkl\conf | binary | |
MD5:— | SHA256:— | |||
| 2132 | setup.exe | C:\Windows\system32\rvlkl.exe | executable | |
MD5:— | SHA256:— | |||
| 2132 | setup.exe | C:\ProgramData\Microsoft\Windows\Start Menu\Programs\Startup\rvlkl.lnk | lnk | |
MD5:— | SHA256:— | |||
| 2132 | setup.exe | C:\ProgramData\rvlkl\log.css | text | |
MD5:ABFA89F05A1407C1115E5E921AAEAA1A | SHA256:D2711FEEA4BC505A3E1D932D81AE4155705D61EAE1E4375016C8F70E83726DA9 | |||
| 2768 | setup_rk_free_229_s.exe | C:\Users\admin\AppData\Local\Temp\7za.exe | executable | |
MD5:744D0E63BCB20438DD3EFCD764503490 | SHA256:77613CCA716EDF68B9D5BAB951463ED7FADE5BC0EC465B36190A76299C50F117 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report