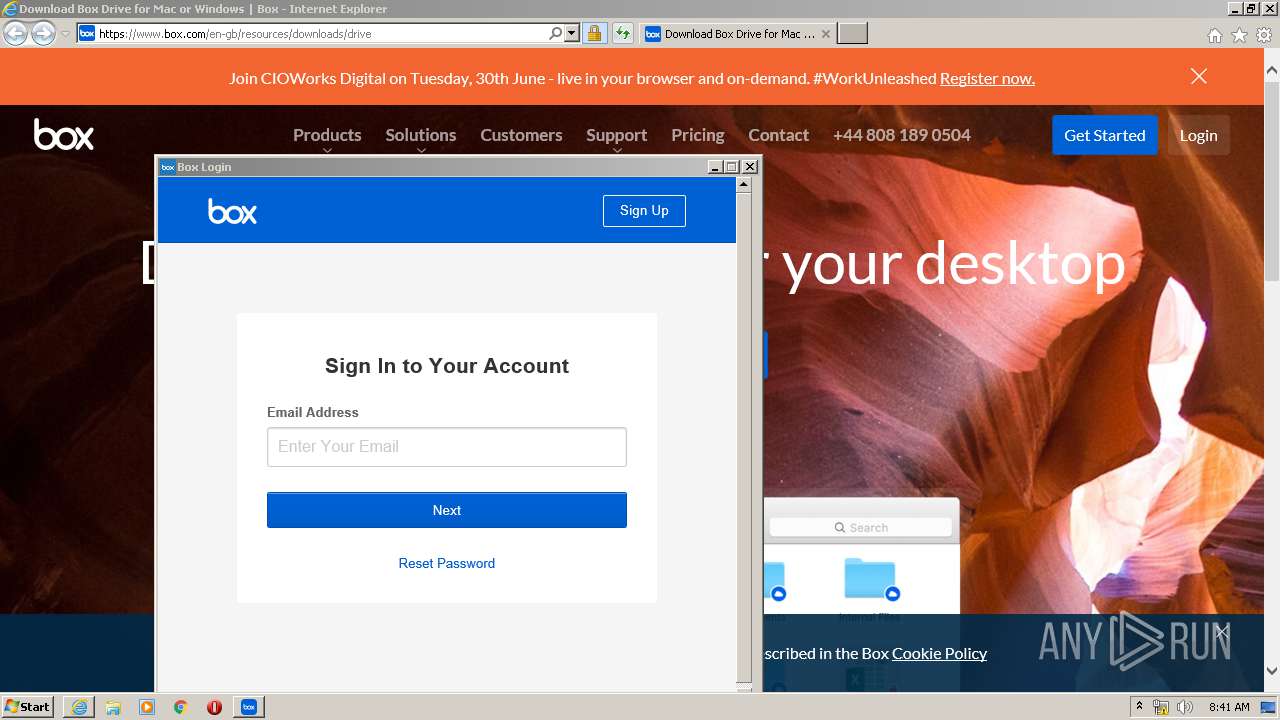
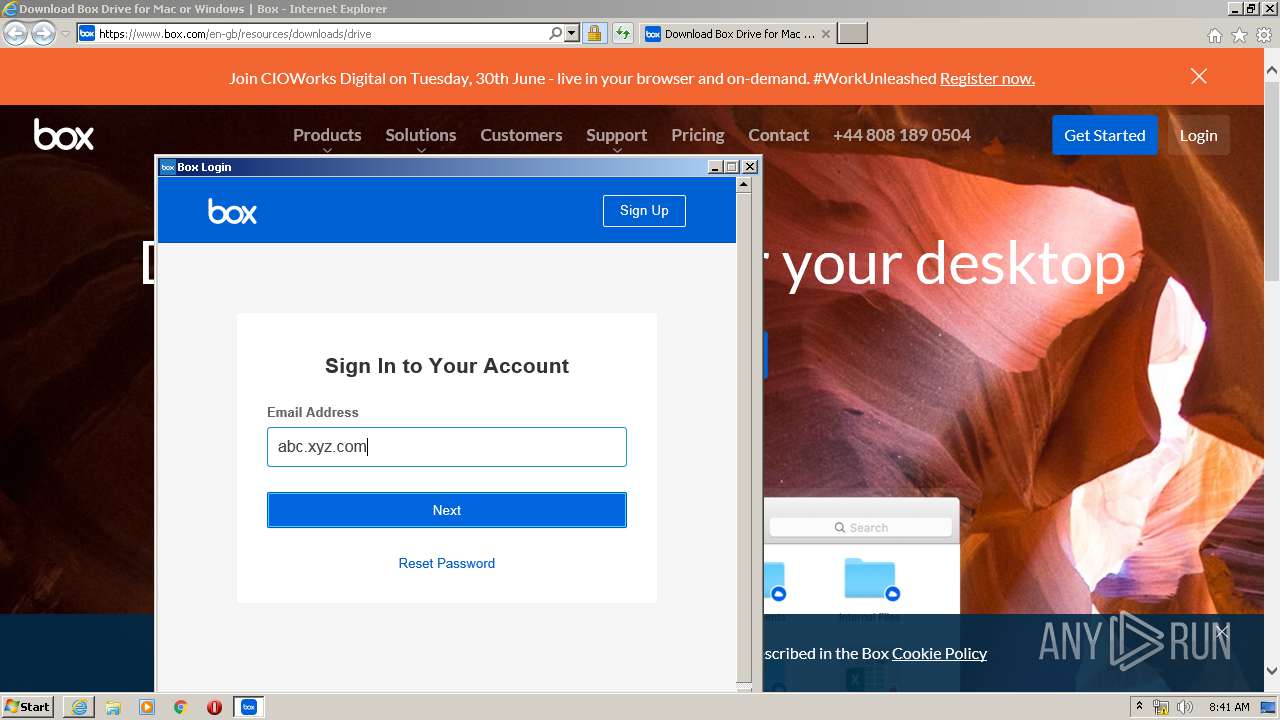
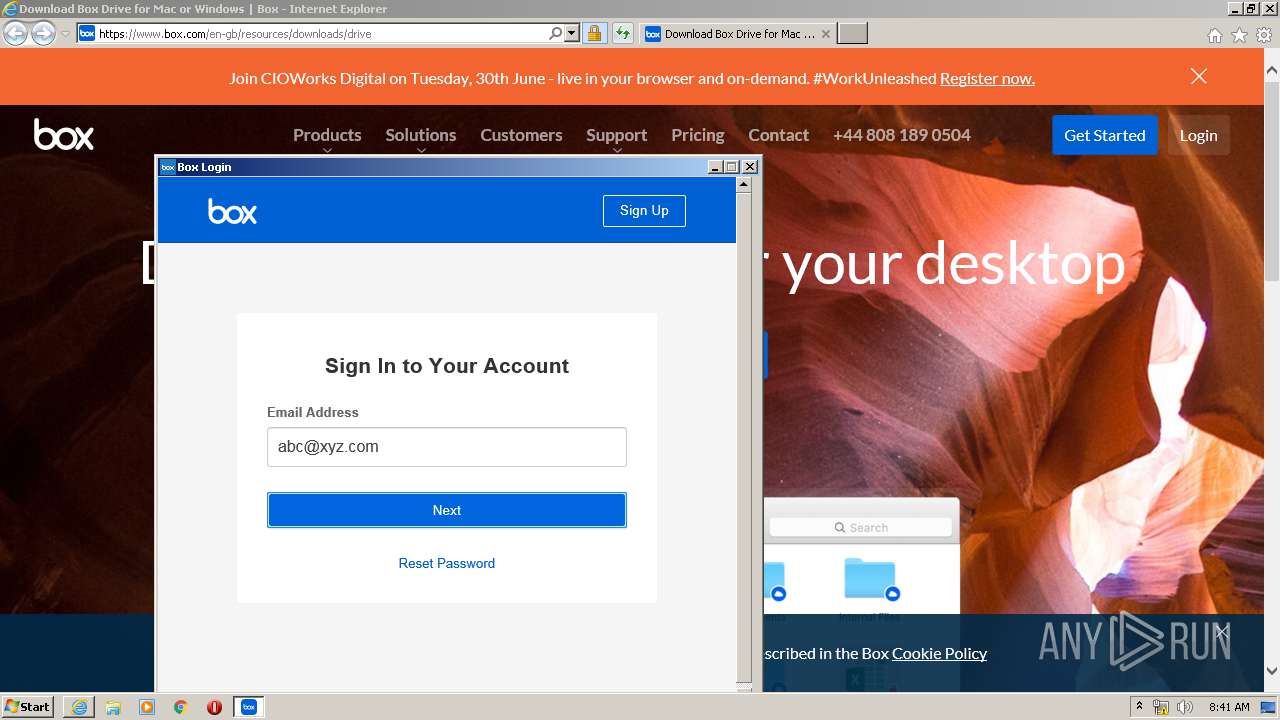
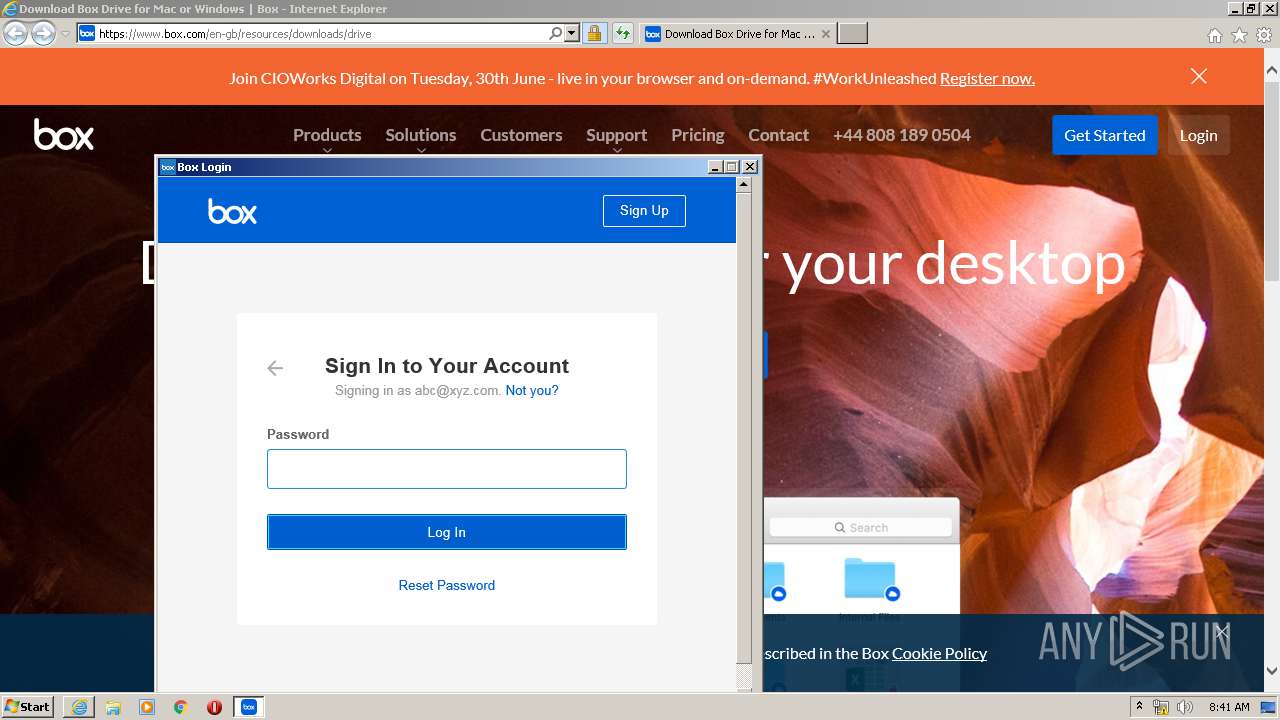
| URL: | https://www.box.com/resources/downloads/drive?utm_medium=email_iter&utm_source=enduser_1_b_4768&utm_theme=&id=7010e000000x7Sw |
| Full analysis: | https://app.any.run/tasks/ca2f5154-2ba1-4a9b-92de-070cf6f73e1b |
| Verdict: | Malicious activity |
| Analysis date: | May 19, 2020, 07:38:21 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | FAAD47A9A9716C67527710F804B10F07 |
| SHA1: | A34022849A99E0D24A89F817E01C8BAFF042E12C |
| SHA256: | D8C63B0E3F58E289F6BEB007CE09EA17E4F54E218F1E1969EBE654C654DE209F |
| SSDEEP: | 3:N8DSLqJdnWtXKhe8BRIYrJ6GI9KQWomP1STdQImLQujqdQ:2OLqJQta2Q6GiWhdg/KQED |
MALICIOUS
Loads dropped or rewritten executable
- rundll32.exe (PID: 3420)
- Box.Desktop.UpdateService.exe (PID: 3324)
- rundll32.exe (PID: 3624)
- streem.exe (PID: 2344)
- rundll32.exe (PID: 3044)
- werfault.exe (PID: 2364)
- Box.exe (PID: 3652)
- explorer.exe (PID: 3676)
- svchost.exe (PID: 860)
- BoxUI.exe (PID: 2472)
Application was dropped or rewritten from another process
- Box.Desktop.UpdateService.exe (PID: 3324)
- streem.exe (PID: 2344)
- Box.exe (PID: 3652)
- BoxUI.exe (PID: 2472)
Actions looks like stealing of personal data
- explorer.exe (PID: 3676)
Loads the Task Scheduler COM API
- explorer.exe (PID: 3676)
SUSPICIOUS
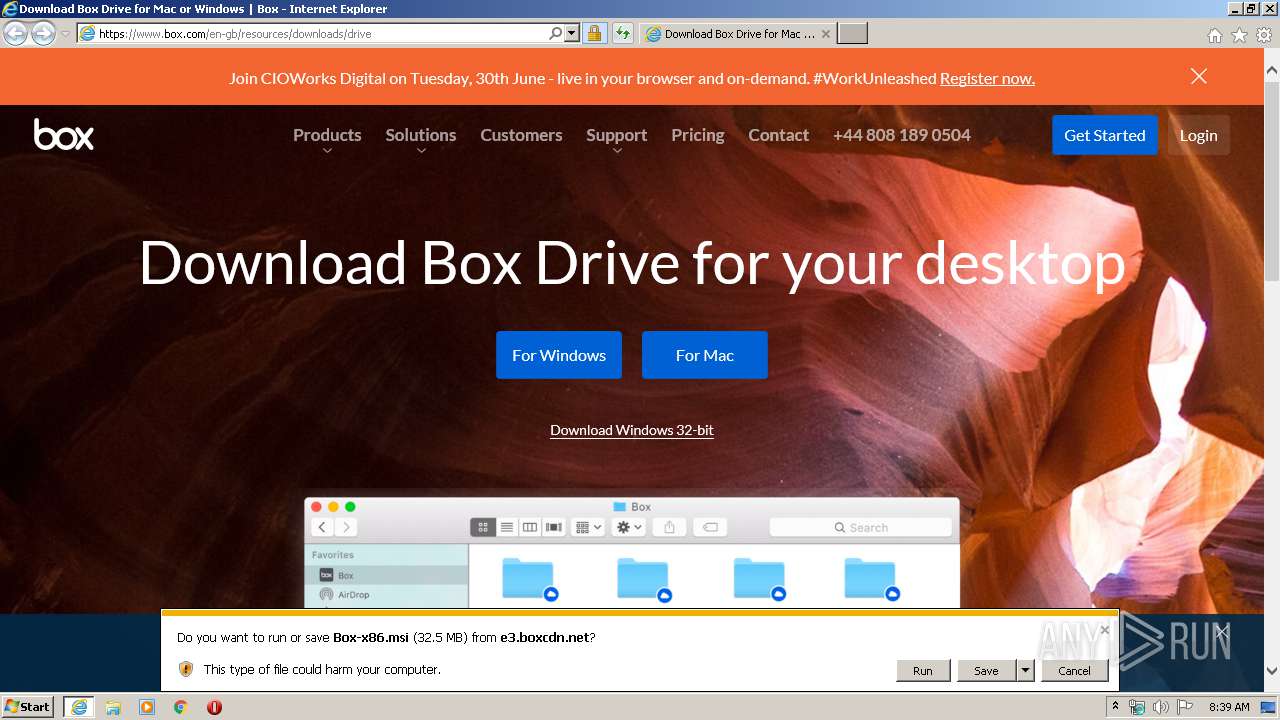
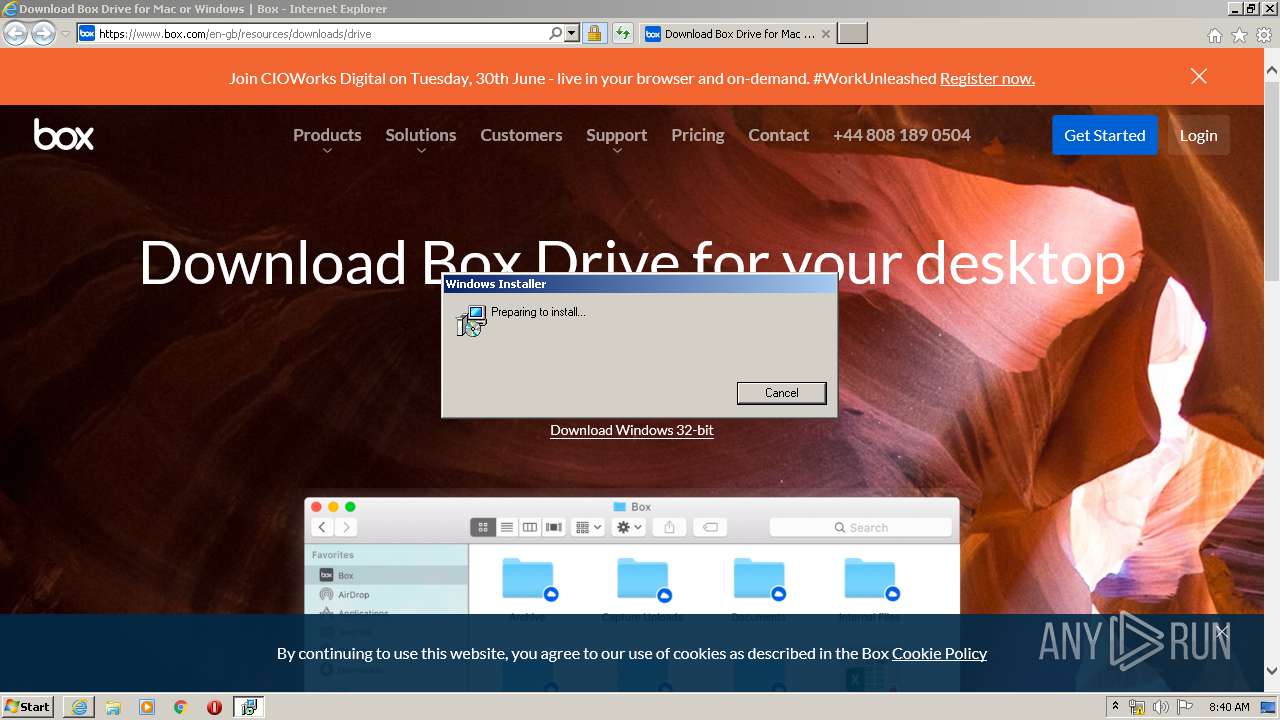
Starts Microsoft Installer
- iexplore.exe (PID: 3436)
Uses RUNDLL32.EXE to load library
- MsiExec.exe (PID: 3400)
- MsiExec.exe (PID: 3128)
Executable content was dropped or overwritten
- rundll32.exe (PID: 3420)
- rundll32.exe (PID: 3624)
- streem.exe (PID: 2344)
- rundll32.exe (PID: 3044)
Creates files in the program directory
- Box.Desktop.UpdateService.exe (PID: 3324)
- streem.exe (PID: 2344)
Executed as Windows Service
- Box.Desktop.UpdateService.exe (PID: 3324)
Creates files in the Windows directory
- streem.exe (PID: 2344)
- werfault.exe (PID: 2364)
Creates files in the driver directory
- streem.exe (PID: 2344)
Creates or modifies windows services
- streem.exe (PID: 2344)
Creates COM task schedule object
- streem.exe (PID: 2344)
Loads Python modules
- Box.exe (PID: 3652)
Reads internet explorer settings
- Box.exe (PID: 3652)
Reads Environment values
- BoxUI.exe (PID: 2472)
Reads Internet Cache Settings
- Box.exe (PID: 3652)
Creates files in the user directory
- Box.exe (PID: 3652)
INFO
Reads Internet Cache Settings
- iexplore.exe (PID: 3436)
- iexplore.exe (PID: 2692)
Changes internet zones settings
- iexplore.exe (PID: 3436)
Application launched itself
- iexplore.exe (PID: 3436)
Reads settings of System Certificates
- iexplore.exe (PID: 2692)
- Box.exe (PID: 3652)
- iexplore.exe (PID: 3436)
Creates files in the user directory
- iexplore.exe (PID: 2692)
- iexplore.exe (PID: 3436)
Modifies the phishing filter of IE
- iexplore.exe (PID: 3436)
Reads internet explorer settings
- iexplore.exe (PID: 2692)
Loads dropped or rewritten executable
- MsiExec.exe (PID: 3400)
- MsiExec.exe (PID: 3128)
Dropped object may contain Bitcoin addresses
- Box.exe (PID: 3652)
Changes settings of System certificates
- iexplore.exe (PID: 3436)
Adds / modifies Windows certificates
- iexplore.exe (PID: 3436)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
58
Monitored processes
15
Malicious processes
10
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
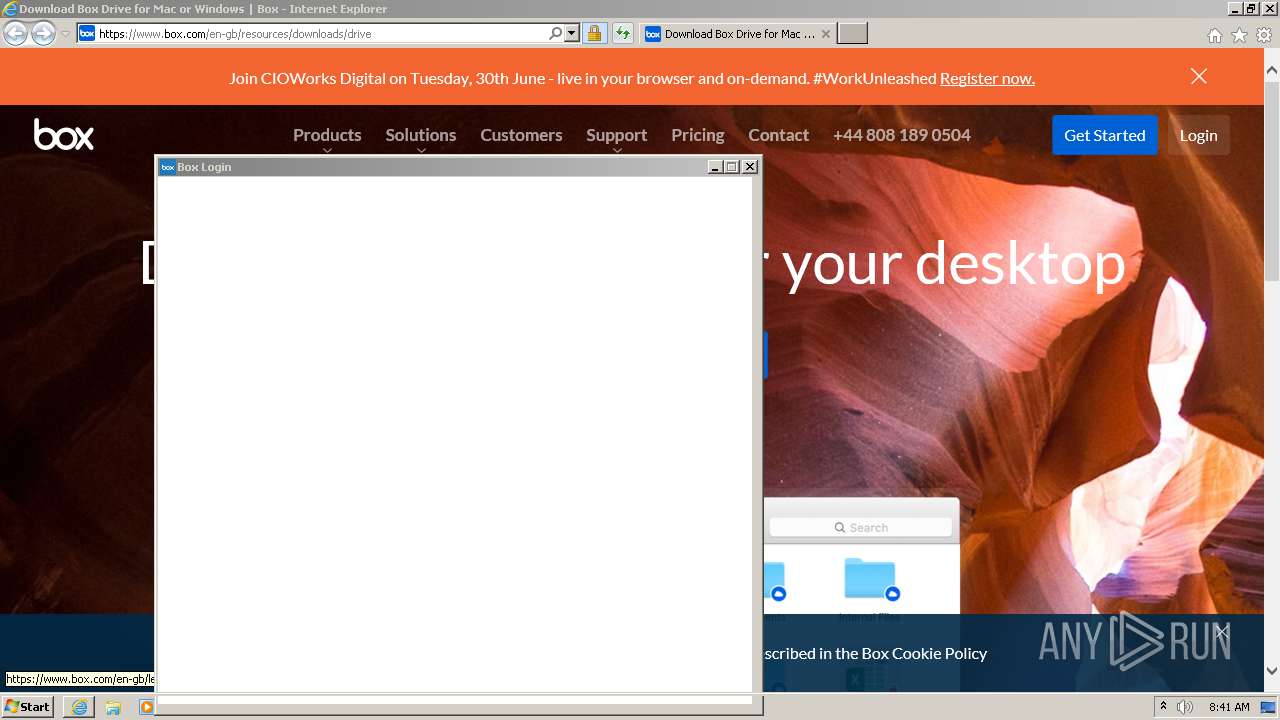
| 580 | "C:\Windows\System32\msiexec.exe" /i "C:\Users\admin\Downloads\Box-x86.msi" | C:\Windows\System32\msiexec.exe | — | iexplore.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 860 | C:\Windows\system32\svchost.exe -k netsvcs | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2344 | "C:\Program Files\Box\Box\FS\streem.exe" --install-cbfs --cbfs-cab-path "C:\Program Files\Box\Box\FS\cbfsconnect.cab" | C:\Program Files\Box\Box\FS\streem.exe | rundll32.exe | ||||||||||||
User: SYSTEM Company: Box, Inc. Integrity Level: SYSTEM Description: Box Drive File System Exit code: 0 Version: 2.14.377.0 Modules
| |||||||||||||||
| 2364 | "C:\Windows\system32\werfault.exe" -s -t 2700 -i 2344 -e 2344 -c 0 | C:\Windows\system32\werfault.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Problem Reporting Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2472 | "C:\Program Files\Box\Box\ui\BoxUI.exe" --product-name Box | C:\Program Files\Box\Box\ui\BoxUI.exe | — | Box.exe | |||||||||||
User: admin Company: Box, Inc. Integrity Level: MEDIUM Description: Box Exit code: 0 Version: 2.14.377.0 Modules
| |||||||||||||||
| 2692 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3436 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3044 | rundll32.exe "C:\Windows\Installer\MSID7B7.tmp",zzzzInvokeManagedCustomActionOutOfProc SfxCA_11196359 32 Box.Desktop.Installer.CustomActions!CustomActions.CustomActions.KillExplorer | C:\Windows\system32\rundll32.exe | MsiExec.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3128 | C:\Windows\system32\MsiExec.exe -Embedding F1206E03AAB6597DF854034EA4C132F3 | C:\Windows\system32\MsiExec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3324 | "C:\Program Files\Box\Box\Box.Desktop.UpdateService.exe" | C:\Program Files\Box\Box\Box.Desktop.UpdateService.exe | services.exe | ||||||||||||
User: SYSTEM Company: Box, Inc. Integrity Level: SYSTEM Description: Box.Desktop.UpdateService Exit code: 0 Version: 2.14.377.0 Modules
| |||||||||||||||
| 3400 | C:\Windows\system32\MsiExec.exe -Embedding 34F4863C0E8E99C90E8151242E33CCB2 M Global\MSI0000 | C:\Windows\system32\MsiExec.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
15 306
Read events
4 610
Write events
7 235
Delete events
3 461
Modification events
| (PID) Process: | (860) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\WMI Writer |
| Operation: | write | Name: | AeFileID |
Value: 300030003000300037003900370065006500350033006600340039003700330062003400330035003900330032006300350037003300660030003400310033006100660064003500390037003700620061006600300065000000 | |||
| (PID) Process: | (860) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\WMI Writer |
| Operation: | write | Name: | AeProgramID |
Value: 300030003000300064006100330039006100330065006500350065003600620034006200300064003300320035003500620066006500660039003500360030003100380039003000610066006400380030003700300039000000 | |||
| (PID) Process: | (3436) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 2536836414 | |||
| (PID) Process: | (3436) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30813616 | |||
| (PID) Process: | (3436) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3436) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3436) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3436) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3436) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3436) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A1000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
Executable files
28
Suspicious files
97
Text files
152
Unknown types
68
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2692 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Tar87EC.tmp | — | |
MD5:— | SHA256:— | |||
| 2692 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\4344B8AF97AF3A423D9EE52899963CDE_D9A08E1A5395B4309E69F79BD92353F4 | der | |
MD5:— | SHA256:— | |||
| 2692 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\GCONS4CO.txt | text | |
MD5:— | SHA256:— | |||
| 2692 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\B398B80134F72209547439DB21AB308D_9487BC0D4381A7CDEB9A8CC43F66D27C | der | |
MD5:— | SHA256:— | |||
| 2692 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\js_mM5YrQP95aiKfGOHyt0sUrnO38sE_X5GXGfTaCDv94M[1].js | text | |
MD5:— | SHA256:— | |||
| 2692 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\EDC238BFF48A31D55A97E1E93892934B_C20E0DA2D0F89FE526E1490F4A2EE5AB | binary | |
MD5:— | SHA256:— | |||
| 2692 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\W6ZDP4XN.txt | — | |
MD5:— | SHA256:— | |||
| 2692 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\6GWXRESO.txt | — | |
MD5:— | SHA256:— | |||
| 2692 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\5KDB746V.txt | — | |
MD5:— | SHA256:— | |||
| 2692 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\5FVUHF0G.txt | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
41
TCP/UDP connections
123
DNS requests
55
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2692 | iexplore.exe | GET | 200 | 2.16.186.11:80 | http://isrg.trustid.ocsp.identrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRv9GhNQxLSSGKBnMArPUcsHYovpgQUxKexpHsscfrb4UuQdf%2FEFWCFiRACEAoBQUIAAAFThXNqC4Xspwg%3D | unknown | der | 1.37 Kb | whitelisted |
2692 | iexplore.exe | GET | 200 | 172.217.22.35:80 | http://ocsp.pki.goog/gts1o1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEEdhjx3SPuvgCAAAAAA9OJY%3D | US | der | 471 b | whitelisted |
2692 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAVG%2Fhgj9%2BGUHaOfzhTEYXM%3D | US | der | 471 b | whitelisted |
2692 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://status.geotrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBR3enuod9bxDxzpICGW%2B2sabjf17QQUkFj%2FsJx1qFFUd7Ht8qNDFjiebMUCEALNo3c4NqEU2%2FH7gjOhvac%3D | US | der | 471 b | whitelisted |
2692 | iexplore.exe | GET | 200 | 172.217.22.35:80 | http://ocsp.pki.goog/gsr2/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBTgXIsxbvr2lBkPpoIEVRE6gHlCnAQUm%2BIHV2ccHsBqBt5ZtJot39wZhi4CDQHjtJqhjYqpgSVpULg%3D | US | der | 468 b | whitelisted |
2692 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfqhLjKLEJQZPin0KCzkdAQpVYowQUsT7DaQP4v0cB1JgmGggC72NkK8MCEATh56TcXPLzbcArQrhdFZ8%3D | US | der | 471 b | whitelisted |
2692 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA%2Fz5hY5qj0aEmX0H4s05bY%3D | US | der | 1.47 Kb | whitelisted |
2692 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQQX6Z6gAidtSefNc6DC0OInqPHDQQUD4BhHIIxYdUvKOeNRji0LOHG2eICEA%2B%2Fr9H1a5saKsFgQN3EIPc%3D | US | der | 471 b | whitelisted |
2692 | iexplore.exe | GET | 200 | 172.217.22.35:80 | http://ocsp.pki.goog/gts1o1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEDCIywS5x90SCAAAAAA9OJc%3D | US | der | 471 b | whitelisted |
2692 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAH9o%2BtuynXIiEOLckvPvJE%3D | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2692 | iexplore.exe | 185.235.236.197:443 | account.box.com | — | — | suspicious |
2692 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2692 | iexplore.exe | 104.16.74.20:443 | cdn03.boxcdn.net | Cloudflare Inc | US | shared |
2692 | iexplore.exe | 2.18.69.88:443 | assets.adobedtm.com | Akamai International B.V. | — | whitelisted |
2692 | iexplore.exe | 151.101.66.109:443 | polyfill.io | Fastly | US | unknown |
2692 | iexplore.exe | 184.30.221.218:443 | munchkin.marketo.net | Akamai International B.V. | NL | whitelisted |
2692 | iexplore.exe | 143.204.201.74:443 | api.company-target.com | — | US | malicious |
2692 | iexplore.exe | 172.217.16.138:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
2692 | iexplore.exe | 147.75.100.189:443 | static.hotjar.com | Packet Host, Inc. | US | unknown |
2692 | iexplore.exe | 192.124.249.22:80 | ocsp.godaddy.com | Sucuri | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.box.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
status.geotrust.com |
| whitelisted |
boxinc.tt.omtrdc.net |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
cdn03.boxcdn.net |
| whitelisted |
assets.adobedtm.com |
| whitelisted |
polyfill.io |
| whitelisted |
munchkin.marketo.net |
| whitelisted |
fonts.googleapis.com |
| whitelisted |