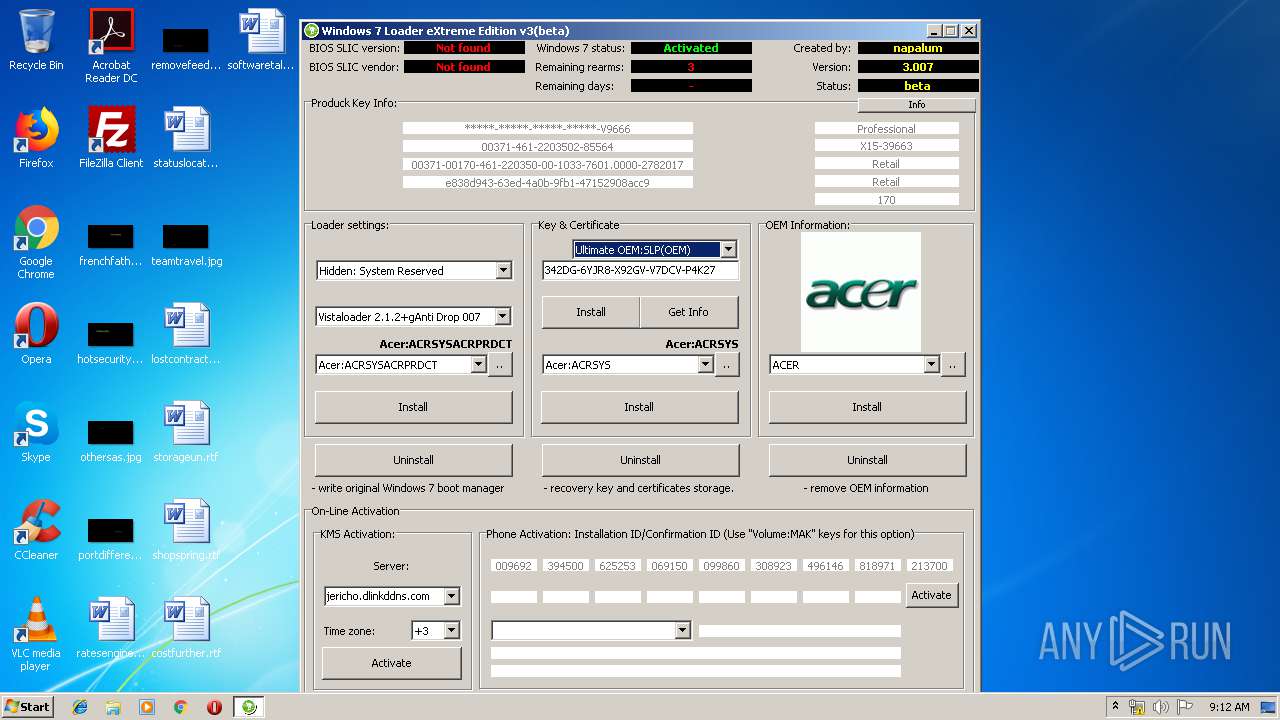
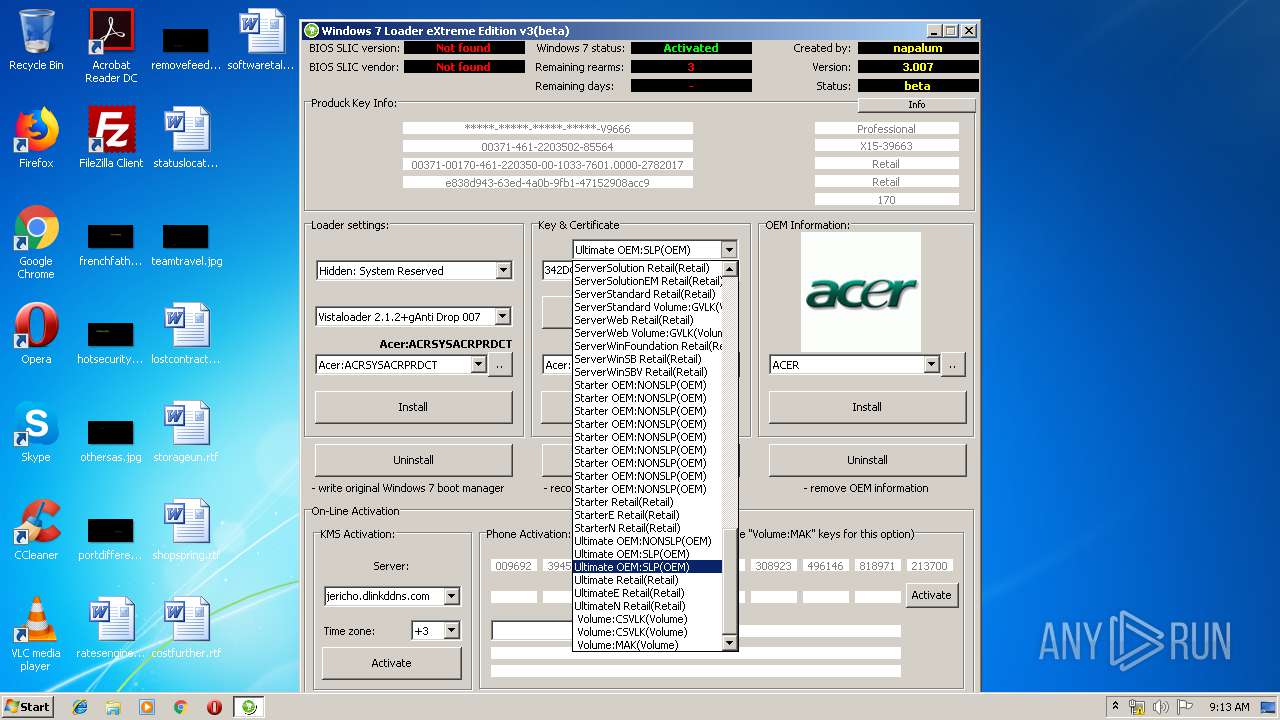
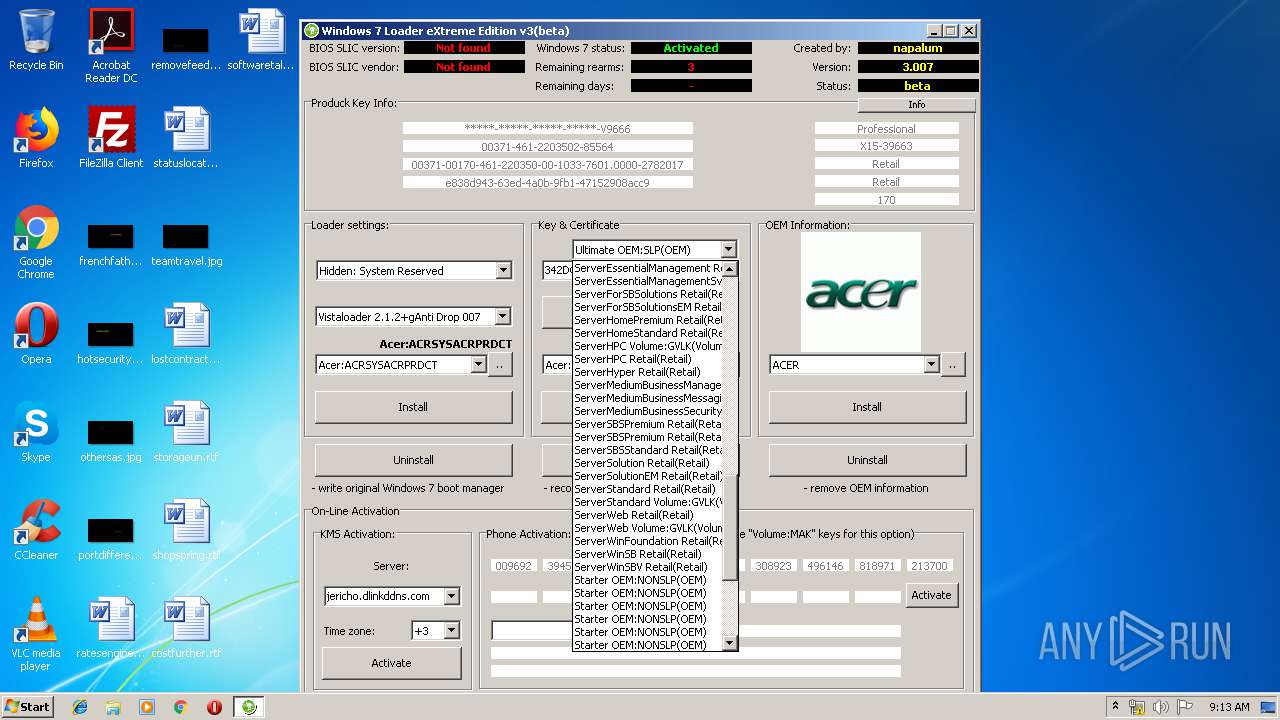
| File name: | w7lxe.exe |
| Full analysis: | https://app.any.run/tasks/88b83f0b-5553-4670-84e1-a2d47f3e766a |
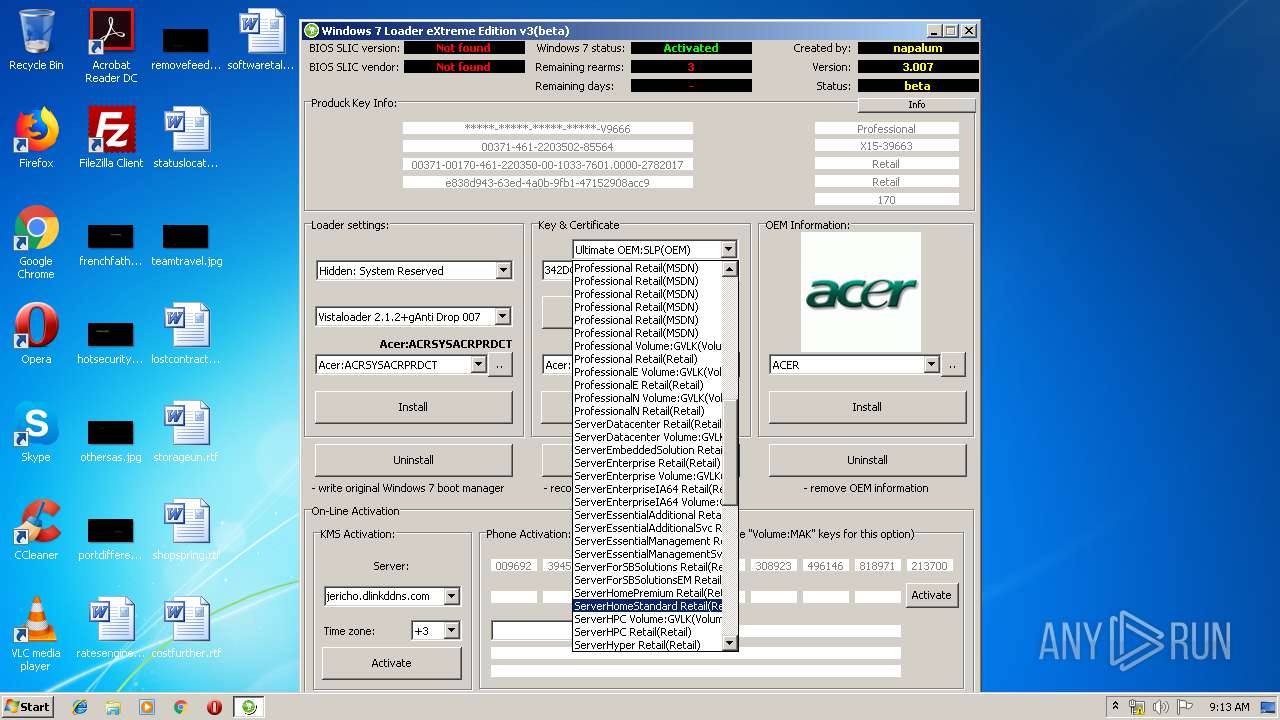
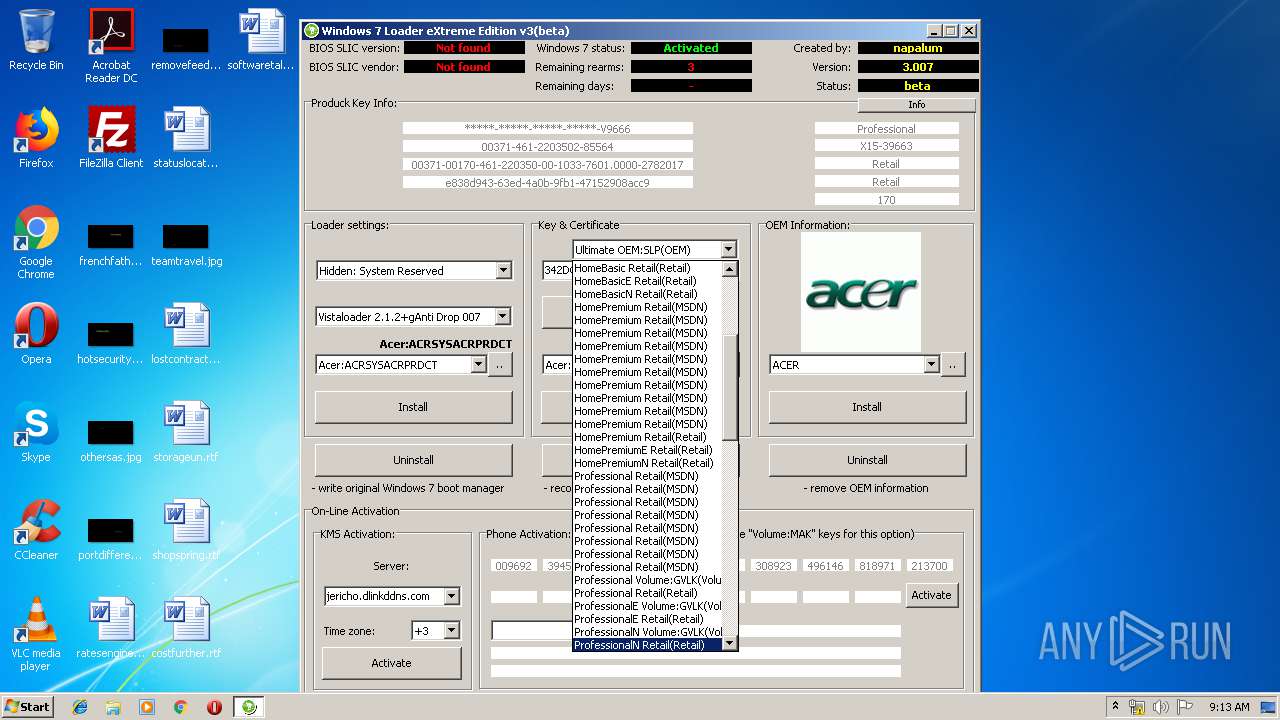
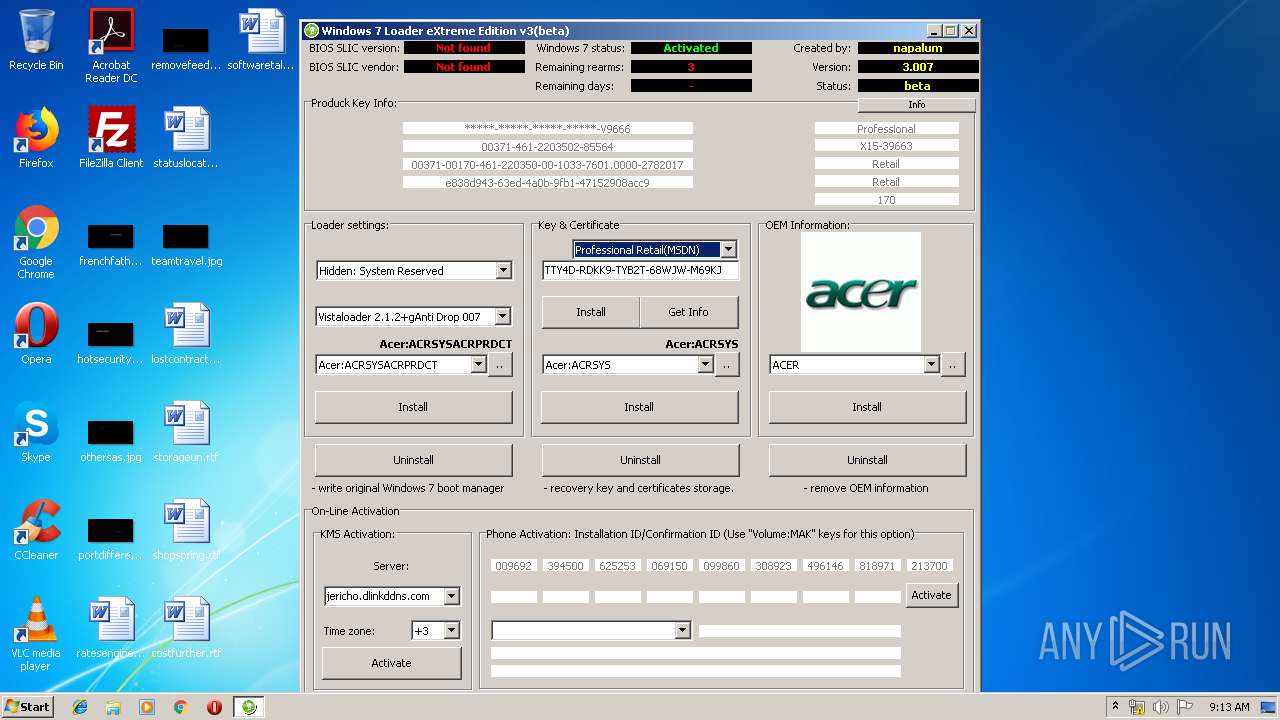
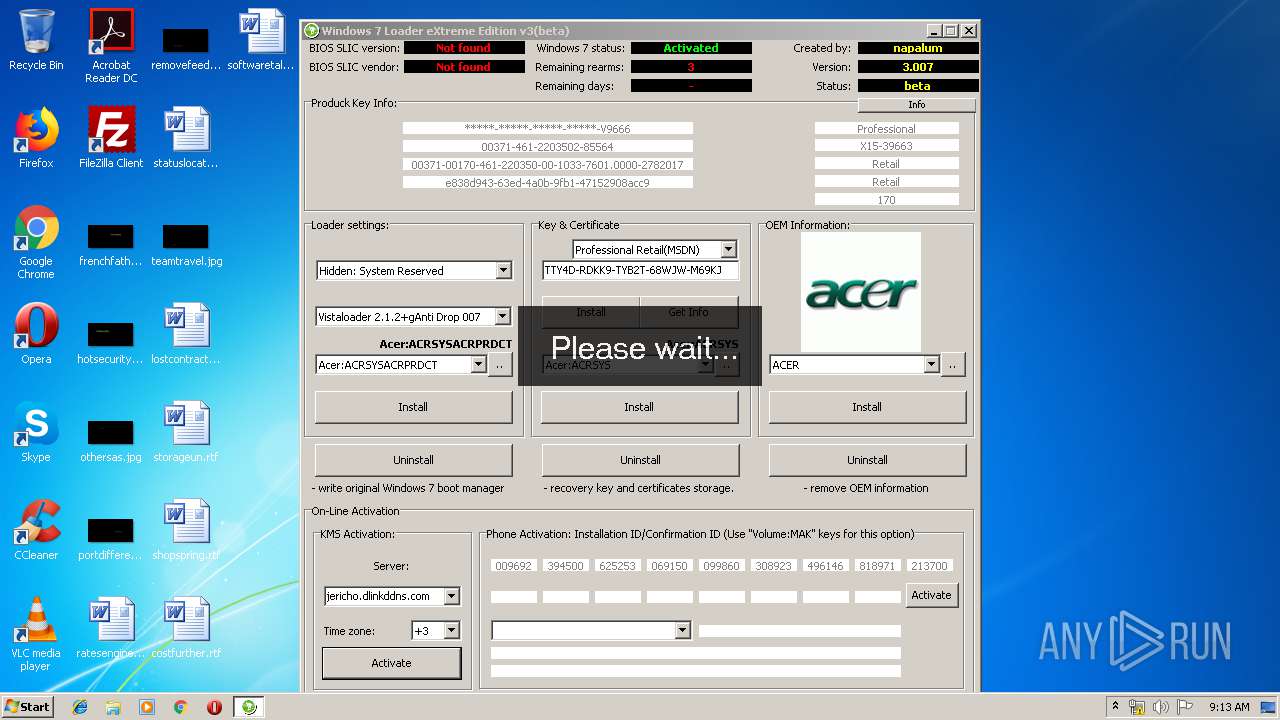
| Verdict: | Suspicious activity |
| Analysis date: | May 28, 2019, 08:12:17 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 00C55A49AEBE1640DDD2BB712822778B |
| SHA1: | 73CF6395F9EDC294F430B252649CC8A07A6CFAF3 |
| SHA256: | D8BCC5653D290360911096837B5877F5EC3170598692C6842916D3E6105ACAC7 |
| SSDEEP: | 49152:+xKSyFvg6PxpigGjltzT2V0R5fsLD1YeoLD/YeoSD6Uqeurn8UiRl:rOgGjX00R5fIXahN7qIUib |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads Environment values
- w7lxe.exe (PID: 3416)
Reads Windows Product ID
- w7lxe.exe (PID: 3416)
Creates files in the Windows directory
- w7lxe.exe (PID: 3416)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Inno Setup installer (62.7) |
|---|---|---|
| .exe | | | Win32 EXE PECompact compressed (generic) (23.7) |
| .exe | | | EXEPACK compressed DOS Executable (7.4) |
| .exe | | | Win32 Executable (generic) (2.5) |
| .exe | | | Win16/32 Executable Delphi generic (1.1) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2009:08:24 21:36:01+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 1279488 |
| InitializedDataSize: | 3260928 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x139548 |
| OSVersion: | 5 |
| ImageVersion: | - |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 3.0.0.0 |
| ProductVersionNumber: | 3.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | Pre-release |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| CompanyName: | - |
| FileDescription: | - |
| FileVersion: | 3.0.0.0 |
| InternalName: | - |
| LegalCopyright: | - |
| LegalTrademarks: | - |
| OriginalFileName: | - |
| ProductName: | - |
| ProductVersion: | 3.0.0.0 |
| Comments: | - |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 24-Aug-2009 19:36:01 |
| Detected languages: |
|
| CompanyName: | - |
| FileDescription: | - |
| FileVersion: | 3.0.0.0 |
| InternalName: | - |
| LegalCopyright: | - |
| LegalTrademarks: | - |
| OriginalFilename: | - |
| ProductName: | - |
| ProductVersion: | 3.0.0.0 |
| Comments: | - |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 10 |
| Time date stamp: | 24-Aug-2009 19:36:01 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00136D74 | 0x00136E00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.45355 |
.itext | 0x00138000 | 0x00001664 | 0x00001800 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.01523 |
.data | 0x0013A000 | 0x000071CC | 0x00007200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.92615 |
.bss | 0x00142000 | 0x00005820 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x00148000 | 0x00003C6C | 0x00003E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.18202 |
.didata | 0x0014C000 | 0x000003A6 | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.6513 |
.tls | 0x0014D000 | 0x0000003C | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x0014E000 | 0x00000018 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 0.210826 |
.reloc | 0x0014F000 | 0x000191FC | 0x00019200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.71308 |
.rsrc | 0x00169000 | 0x002F8000 | 0x002F7A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.05442 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.91819 | 859 | UNKNOWN | Russian - Russia | RT_MANIFEST |
2 | 4.91831 | 861 | UNKNOWN | Russian - Russia | RT_MANIFEST |
3 | 3.00046 | 308 | UNKNOWN | English - United States | RT_CURSOR |
4 | 2.56318 | 308 | UNKNOWN | English - United States | RT_CURSOR |
5 | 2.6949 | 308 | UNKNOWN | English - United States | RT_CURSOR |
6 | 2.62527 | 308 | UNKNOWN | English - United States | RT_CURSOR |
7 | 2.91604 | 308 | UNKNOWN | English - United States | RT_CURSOR |
4075 | 3.28395 | 2072 | UNKNOWN | UNKNOWN | RT_STRING |
4076 | 3.2898 | 2372 | UNKNOWN | UNKNOWN | RT_STRING |
4077 | 3.32067 | 816 | UNKNOWN | UNKNOWN | RT_STRING |
Imports
ADVAPI32.DLL |
advapi32.dll |
comctl32.dll |
comdlg32.dll |
connect.dll |
gdi32.dll |
kernel32.dll |
msimg32.dll |
ole32.dll |
oleaut32.dll |
Total processes
38
Monitored processes
2
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2656 | "C:\Users\admin\AppData\Local\Temp\w7lxe.exe" | C:\Users\admin\AppData\Local\Temp\w7lxe.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Version: 3.0.0.0 | |||||||||||||||
| 3416 | "C:\Users\admin\AppData\Local\Temp\w7lxe.exe" | C:\Users\admin\AppData\Local\Temp\w7lxe.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Version: 3.0.0.0 Modules
| |||||||||||||||
Total events
14
Read events
13
Write events
1
Delete events
0
Modification events
| (PID) Process: | (3416) w7lxe.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowsUpdate\Auto Update |
| Operation: | write | Name: | AUOptions |
Value: 2 | |||
Executable files
0
Suspicious files
2
Text files
8
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3416 | w7lxe.exe | \\?\Volume{e1a82db3-a9f0-11e7-b142-806e6f6e6963} | — | |
MD5:— | SHA256:— | |||
| 3416 | w7lxe.exe | \\?\Volume{e1a82db3-a9f0-11e7-b142-806e6f6e6963}\xeldr | binary | |
MD5:AB1E4C29D248117EF77182FDE44DAB6E | SHA256:4E457747AB51B3793A23E1E25CA4F7C8188E7F2C245DCD356FE4CC1D7FD5F834 | |||
| 3416 | w7lxe.exe | C:\Windows\system32\oobe\info\ACER_BADGE.bmp | image | |
MD5:248CB8A3431BA3C8BA18CC1023DE7FE6 | SHA256:8A0AEB491FE16FFC71D7C091965C871D774E40AB8873565745C5E7DC331838DA | |||
| 3416 | w7lxe.exe | \\?\Volume{e1a82db3-a9f0-11e7-b142-806e6f6e6963}\bootsect.lxe.bak | dsk | |
MD5:1089A9D32AE68D6C710B583CE3193E00 | SHA256:F5852A79973C7779654C59CCEABA7DF7B5B91760F096290803828BBBE73ADCC5 | |||
| 3416 | w7lxe.exe | C:\Windows\system32\oobe\info\ACER_BAR.bmp | image | |
MD5:— | SHA256:— | |||
| 3416 | w7lxe.exe | C:\Windows\system32\oobe\info\ACER_MCE_LOGO.png | image | |
MD5:4245DA381474819BF5FF6123A2D33108 | SHA256:B999107AF32ED31E7C306F6D80FC87FEE4F667AEE958345D05FEE932329606ED | |||
| 3416 | w7lxe.exe | C:\Windows\system32\oobe\info\ACER_LOGO.png | image | |
MD5:3A76E2E9FC8DD70BDC5FA77DBDD61A0D | SHA256:E31CD014BCC188825128A7B0C1AC51DD81C64035F9745B2C4018D8BD8CB49152 | |||
| 3416 | w7lxe.exe | C:\Windows\system32\oobe\info\ACERLOGO.gif | image | |
MD5:76212994961049C5EAC2AE5F1252C800 | SHA256:C3C9244A373CFA5B884760661FAD0D4D683190FB9FF441B6EF97C128D7D355D9 | |||
| 3416 | w7lxe.exe | C:\Windows\system32\oobe\info\ACER_BAR.png | image | |
MD5:837C15152590473DF117E715C2E34981 | SHA256:B27AF42311D6E60E6942A6616F0C79486113CA03568B39BCA0A6B25B20020249 | |||
| 3416 | w7lxe.exe | C:\Windows\system32\oobe\info\oobe.xml | text | |
MD5:9E49421BA095A281E882B0F6F95A94B1 | SHA256:B4891C11A62D203B5622549392BBBD81051FB91BAA50249F63DF145D6A04BA19 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
2
DNS requests
2
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2608 | wmiprvse.exe | POST | 302 | 23.222.42.9:80 | http://go.microsoft.com/fwlink/?LinkID=88339 | NL | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2608 | wmiprvse.exe | 23.222.42.9:80 | go.microsoft.com | Akamai Technologies, Inc. | NL | whitelisted |
2608 | wmiprvse.exe | 65.52.98.231:443 | activation.sls.microsoft.com | Microsoft Corporation | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
go.microsoft.com |
| whitelisted |
activation.sls.microsoft.com |
| whitelisted |