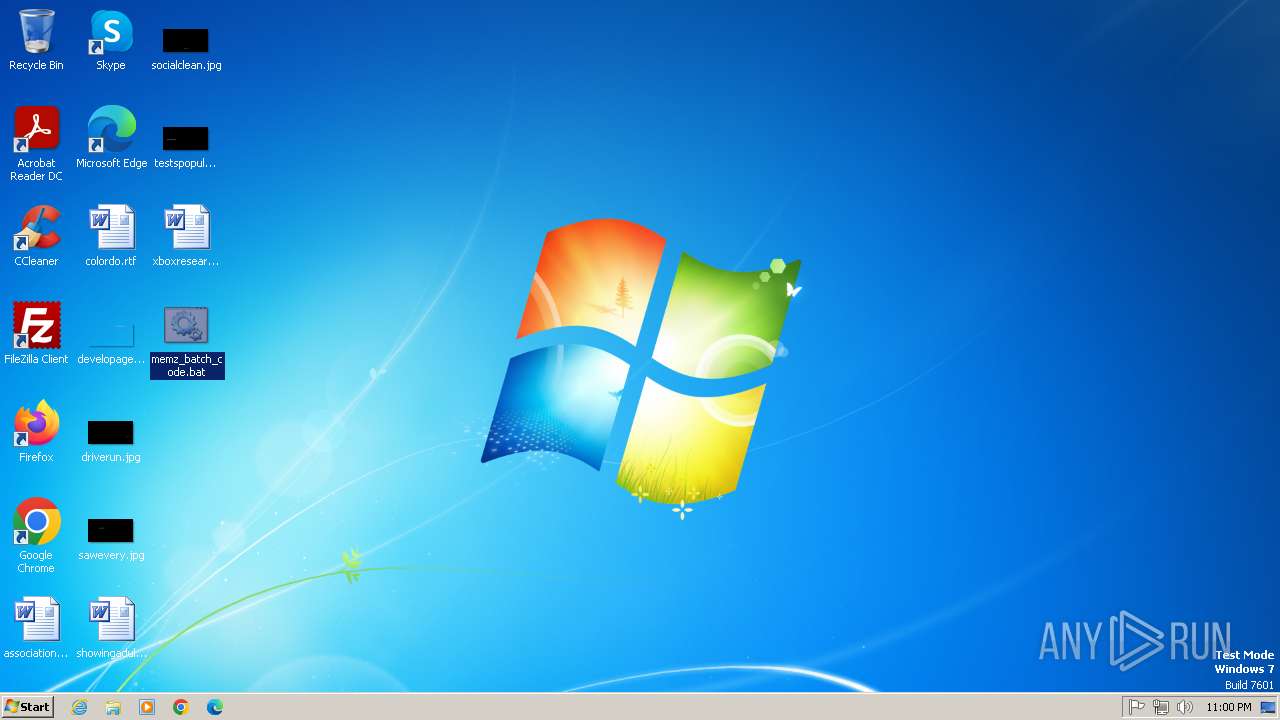
| File name: | memz_batch_code.bat |
| Full analysis: | https://app.any.run/tasks/43446021-2434-44bf-b2ec-409e86360081 |
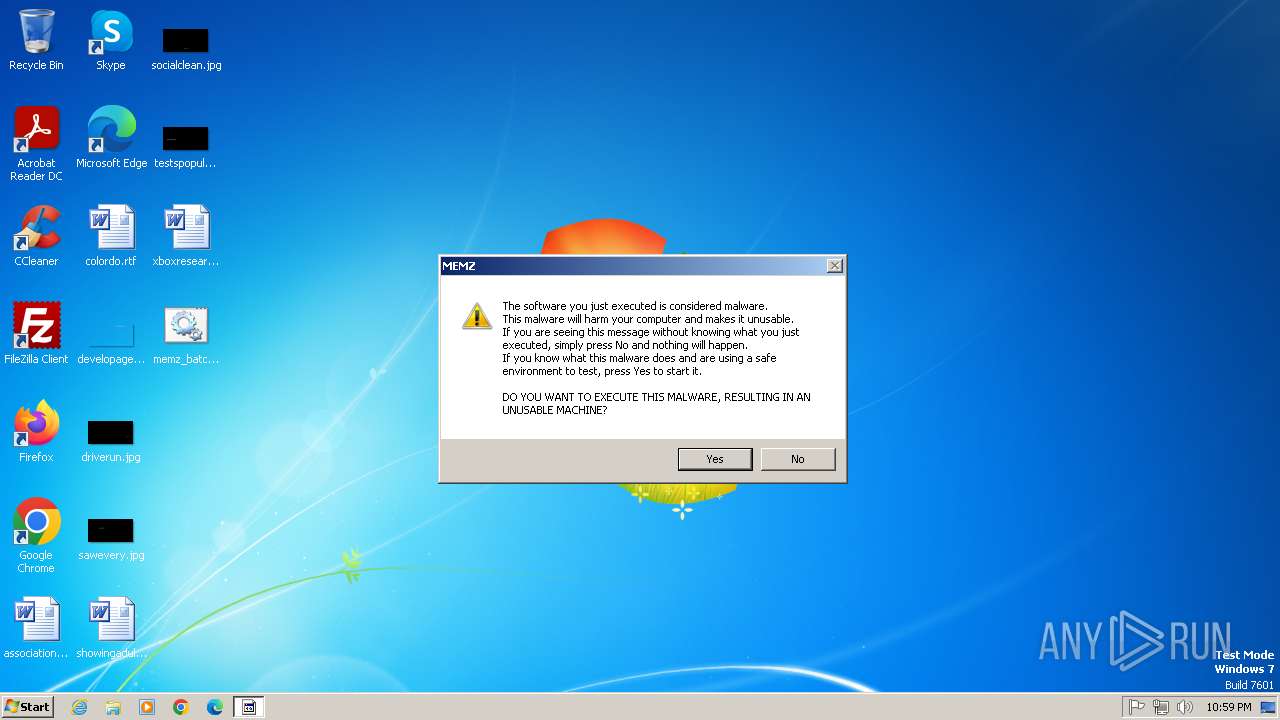
| Verdict: | Malicious activity |
| Analysis date: | May 17, 2025, 21:59:52 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
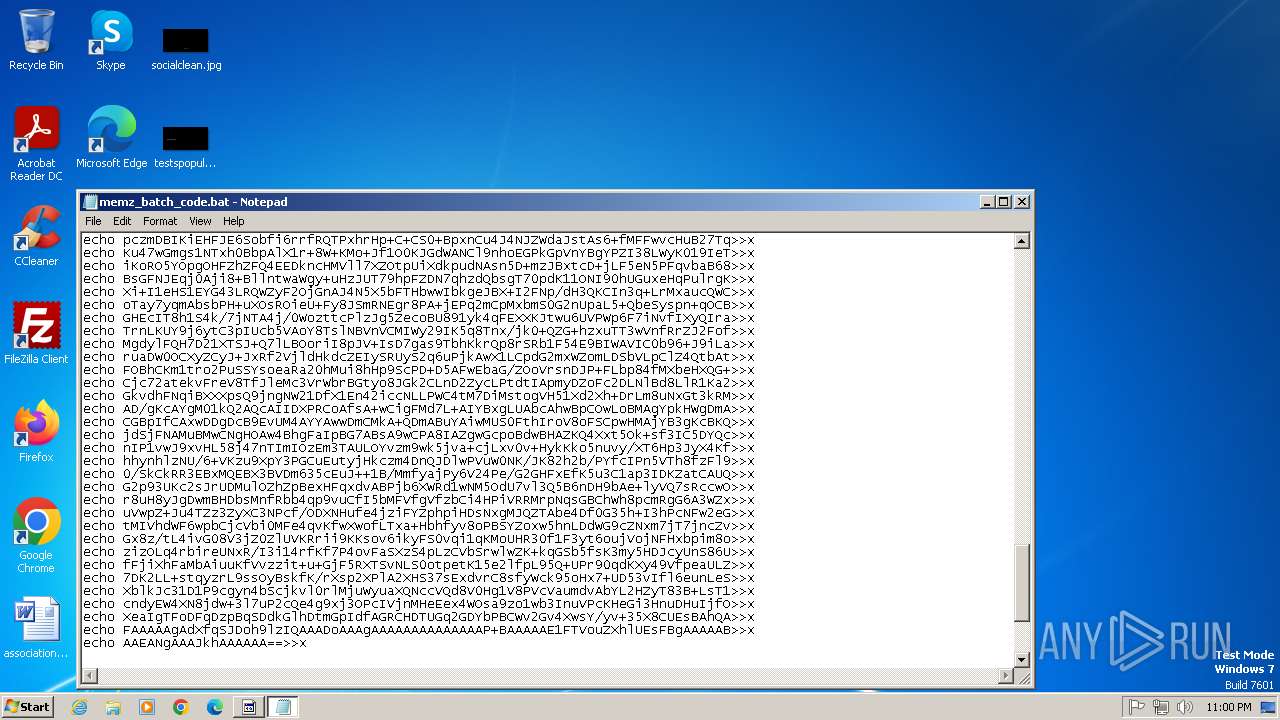
| MIME: | text/plain |
| File info: | ASCII text, with CRLF line terminators |
| MD5: | 44FBD58C401A7786DA2E8B6A6291379E |
| SHA1: | 9DBFD08FA557D9DCE79911EB4BBDDB2008D4F53F |
| SHA256: | D8B47727EA05305AD396977B336C3BFC86AE122CDDE01976FA9B0C3A7C2D3F24 |
| SSDEEP: | 192:vOyUySl0UaDz2gWsIzlmj+BxZ3yqueWQx0lZicyC8Sh31xcjBzyxwn7AVhllz3:vVODaDSHMql3yqlxy5L1xcjwrlz3 |
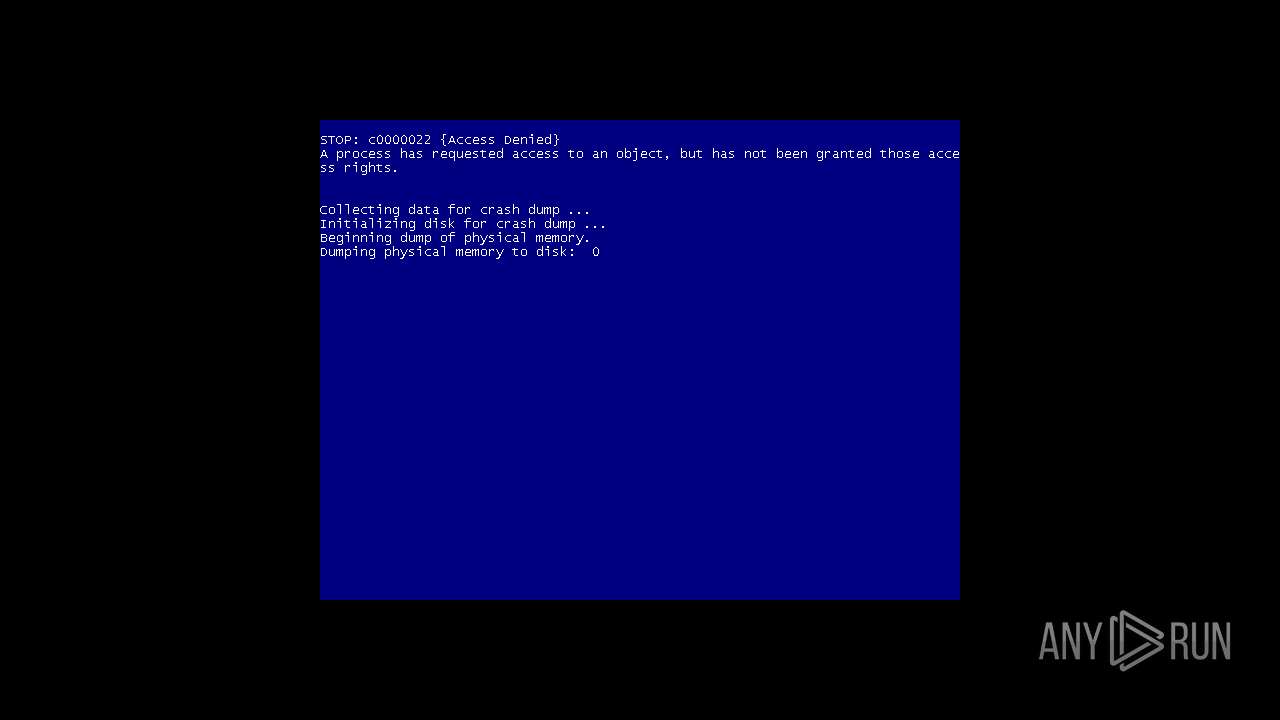
MALICIOUS
Gets a file object corresponding to the file in a specified path (SCRIPT)
- cscript.exe (PID: 1760)
Uses base64 encoding (SCRIPT)
- cscript.exe (PID: 1760)
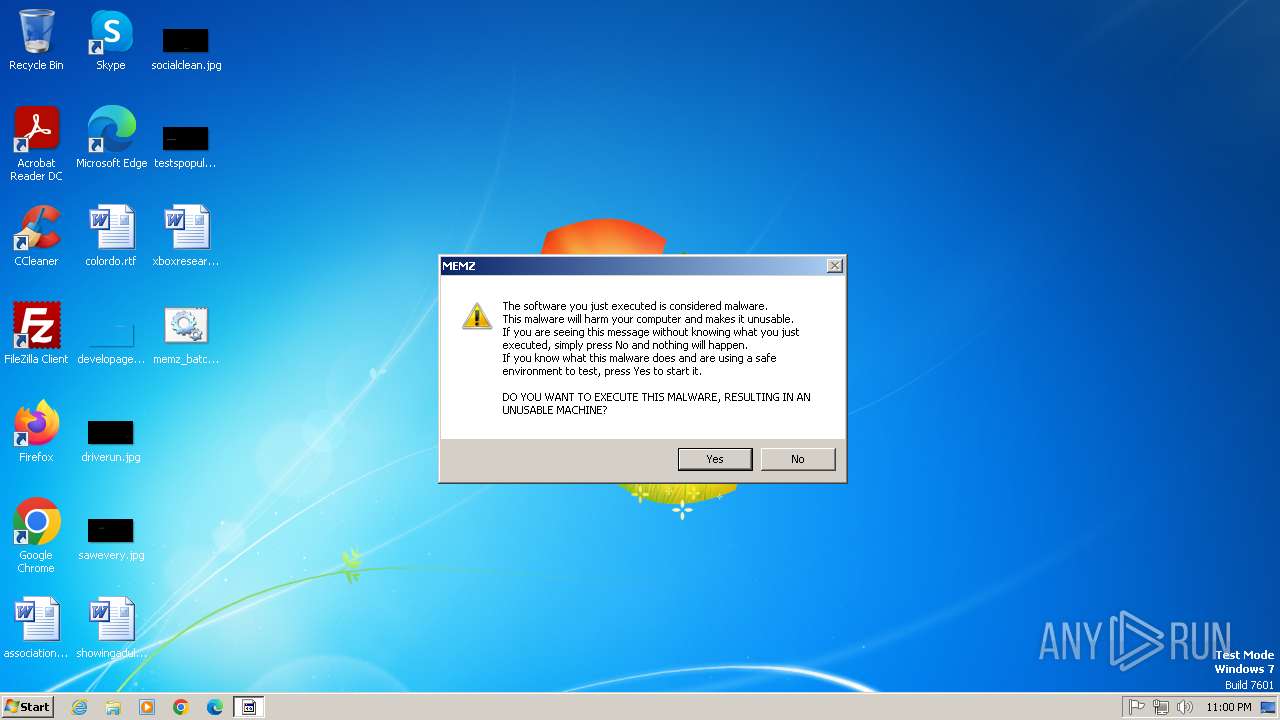
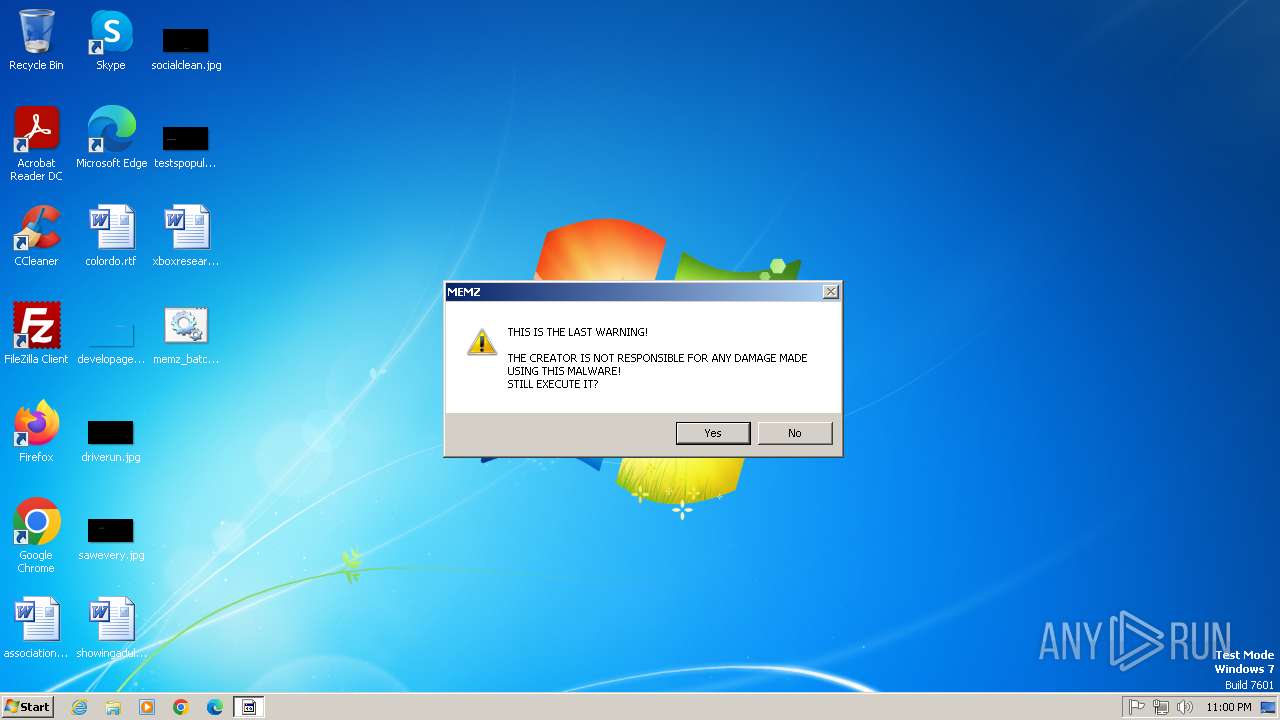
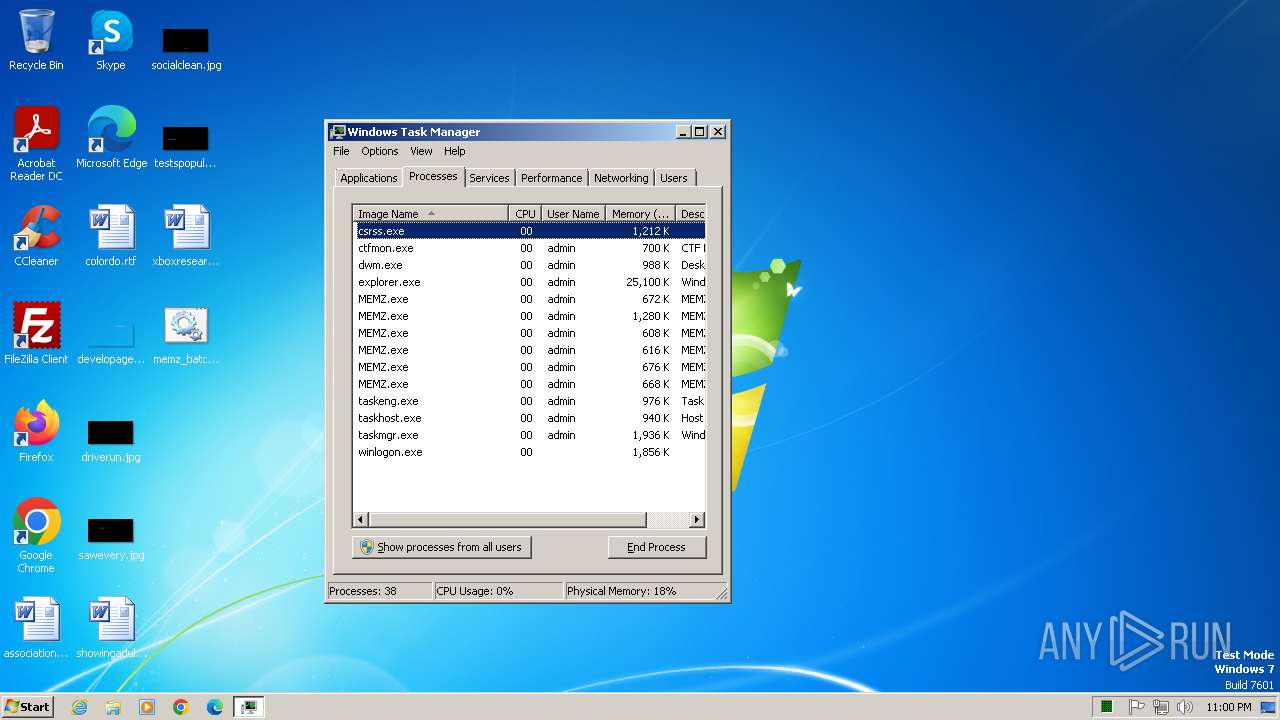
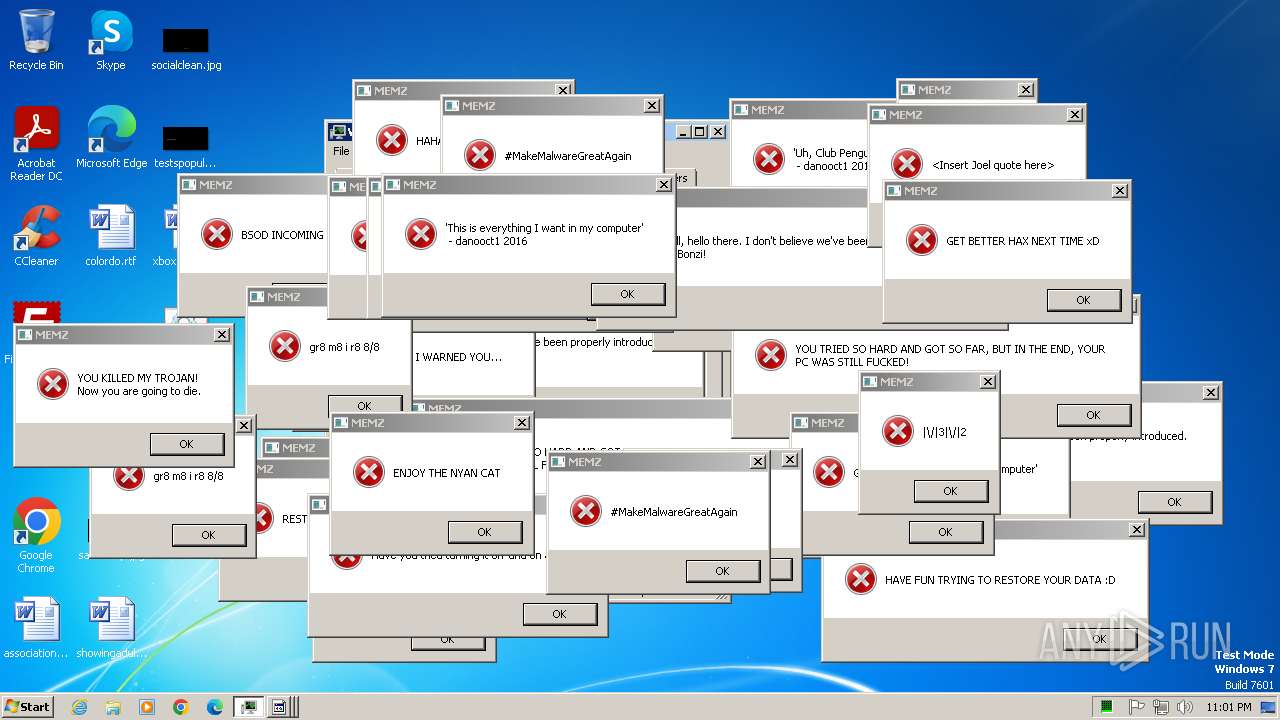
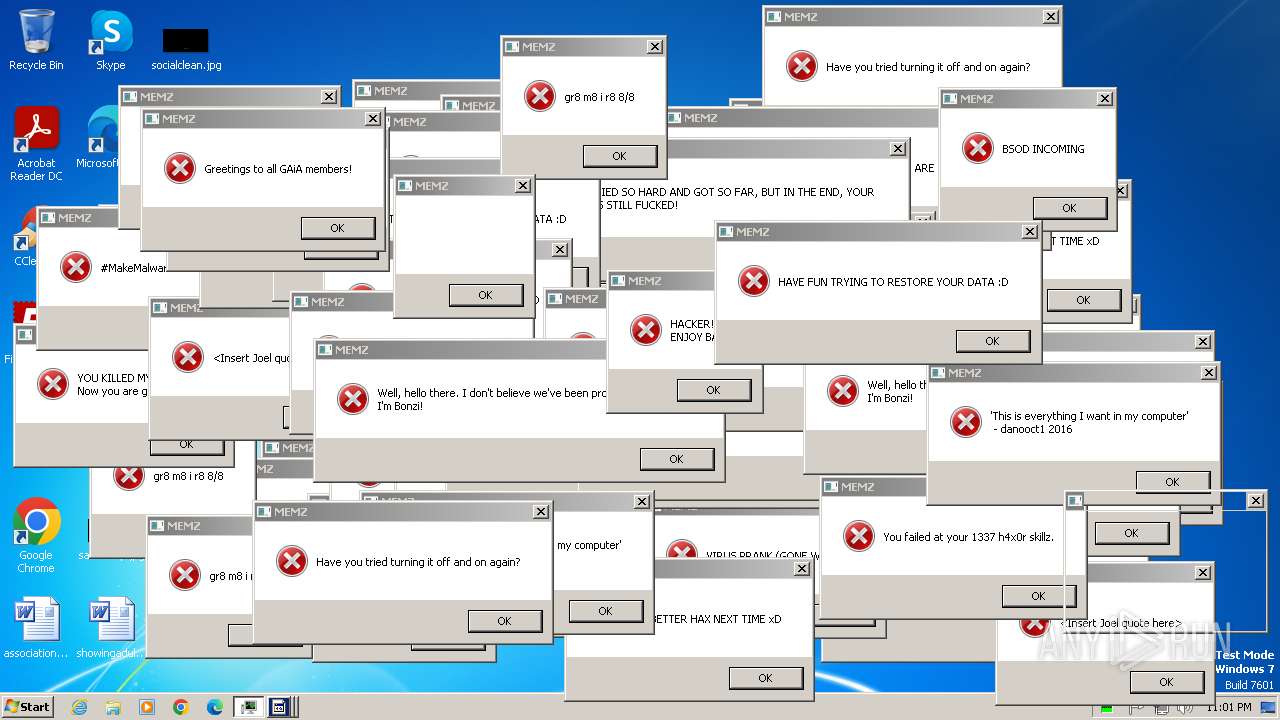
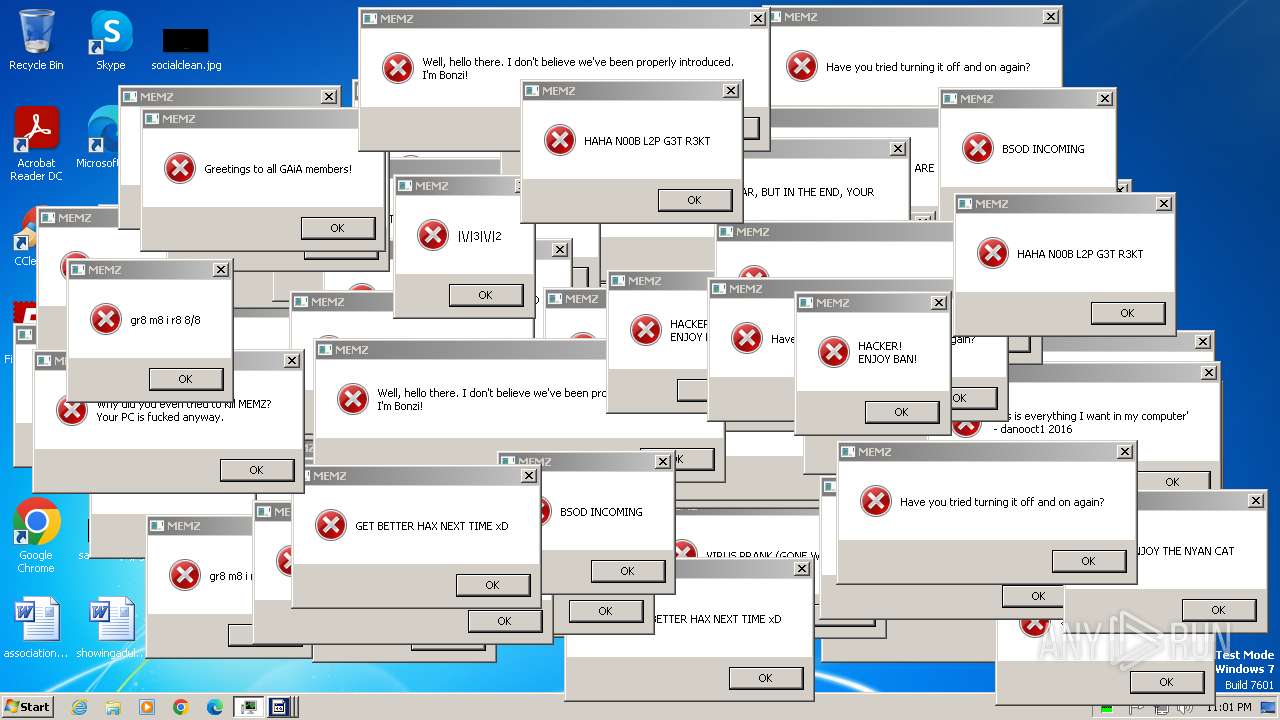
MEMZ has been detected (YARA)
- MEMZ.exe (PID: 2056)
- MEMZ.exe (PID: 2392)
- MEMZ.exe (PID: 892)
- MEMZ.exe (PID: 2528)
- MEMZ.exe (PID: 2508)
- MEMZ.exe (PID: 2912)
- MEMZ.exe (PID: 1500)
SUSPICIOUS
The process executes JS scripts
- cmd.exe (PID: 2840)
Creates FileSystem object to access computer's file system (SCRIPT)
- cscript.exe (PID: 1760)
Sets XML DOM element text (SCRIPT)
- cscript.exe (PID: 1760)
Creates XML DOM element (SCRIPT)
- cscript.exe (PID: 1760)
Script creates XML DOM node (SCRIPT)
- cscript.exe (PID: 1760)
Creates a Stream, which may work with files, input/output devices, pipes, or TCP/IP sockets (SCRIPT)
- cscript.exe (PID: 1760)
Writes binary data to a Stream object (SCRIPT)
- cscript.exe (PID: 1760)
Saves data to a binary file (SCRIPT)
- cscript.exe (PID: 1760)
Creates a Folder object (SCRIPT)
- cscript.exe (PID: 1760)
Reads the Internet Settings
- cscript.exe (PID: 1760)
- MEMZ.exe (PID: 2056)
- cmd.exe (PID: 2840)
- MEMZ.exe (PID: 1500)
There is functionality for taking screenshot (YARA)
- MEMZ.exe (PID: 2056)
- MEMZ.exe (PID: 2528)
- MEMZ.exe (PID: 1500)
- MEMZ.exe (PID: 892)
- MEMZ.exe (PID: 2392)
- MEMZ.exe (PID: 2508)
- MEMZ.exe (PID: 2912)
Reads security settings of Internet Explorer
- MEMZ.exe (PID: 2056)
- MEMZ.exe (PID: 1500)
Executable content was dropped or overwritten
- cscript.exe (PID: 1760)
The executable file from the user directory is run by the CMD process
- MEMZ.exe (PID: 2332)
- MEMZ.exe (PID: 2408)
- MEMZ.exe (PID: 2056)
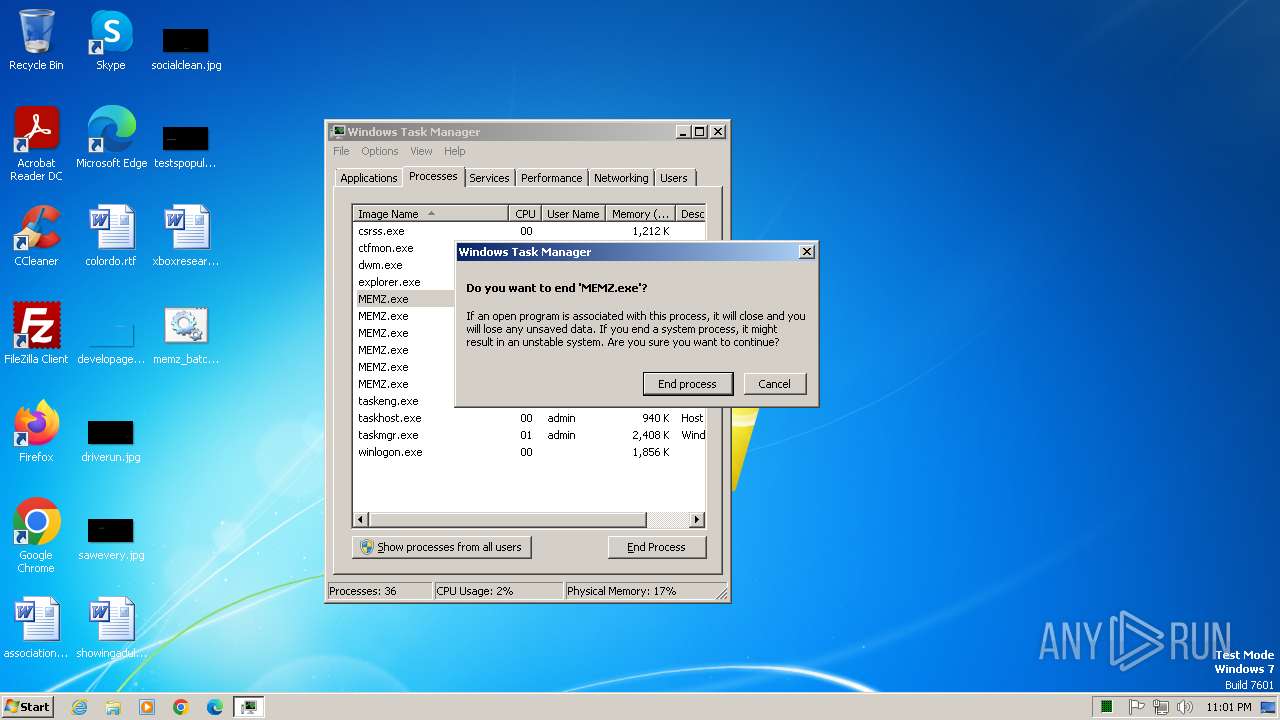
Application launched itself
- MEMZ.exe (PID: 2056)
Start notepad (likely ransomware note)
- MEMZ.exe (PID: 1500)
Creates file in the systems drive root
- notepad.exe (PID: 3096)
- MEMZ.exe (PID: 1500)
INFO
Reads security settings of Internet Explorer
- cscript.exe (PID: 1760)
Creates files or folders in the user directory
- cscript.exe (PID: 1760)
Reads the computer name
- MEMZ.exe (PID: 2056)
- MEMZ.exe (PID: 1500)
Checks supported languages
- MEMZ.exe (PID: 2392)
- MEMZ.exe (PID: 2528)
- MEMZ.exe (PID: 2508)
- MEMZ.exe (PID: 892)
- MEMZ.exe (PID: 2912)
- MEMZ.exe (PID: 2056)
- MEMZ.exe (PID: 1500)
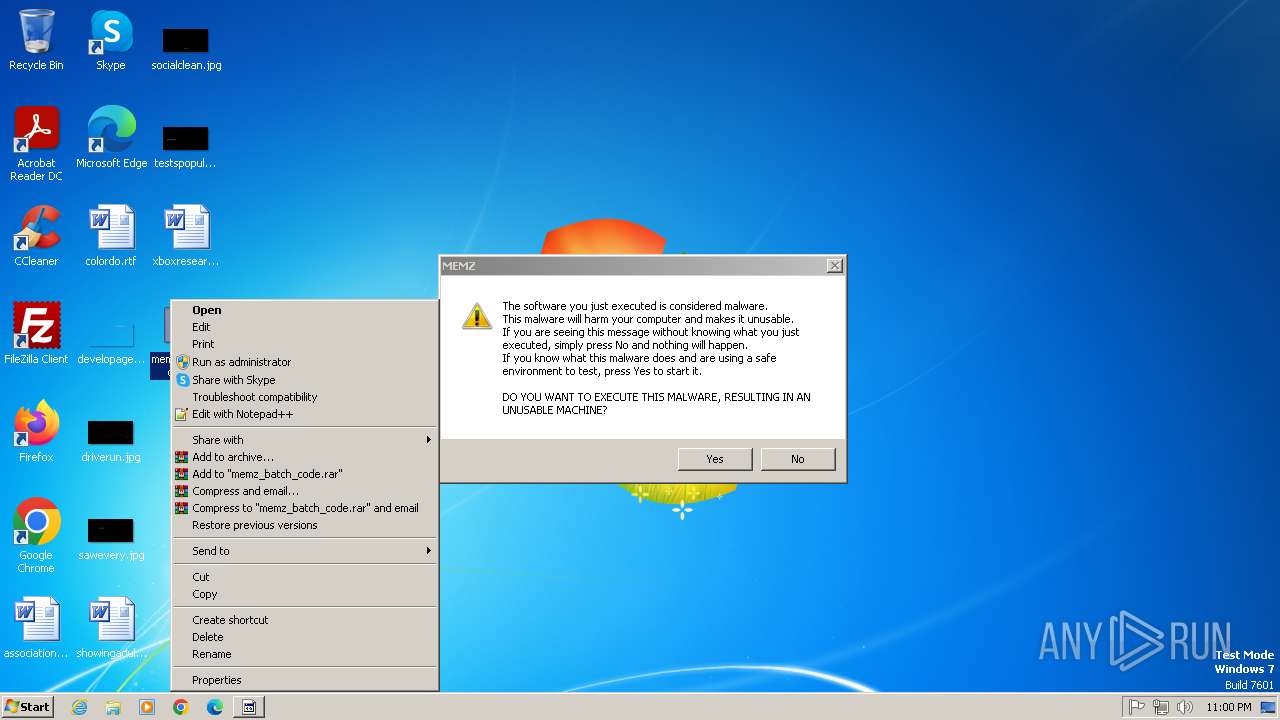
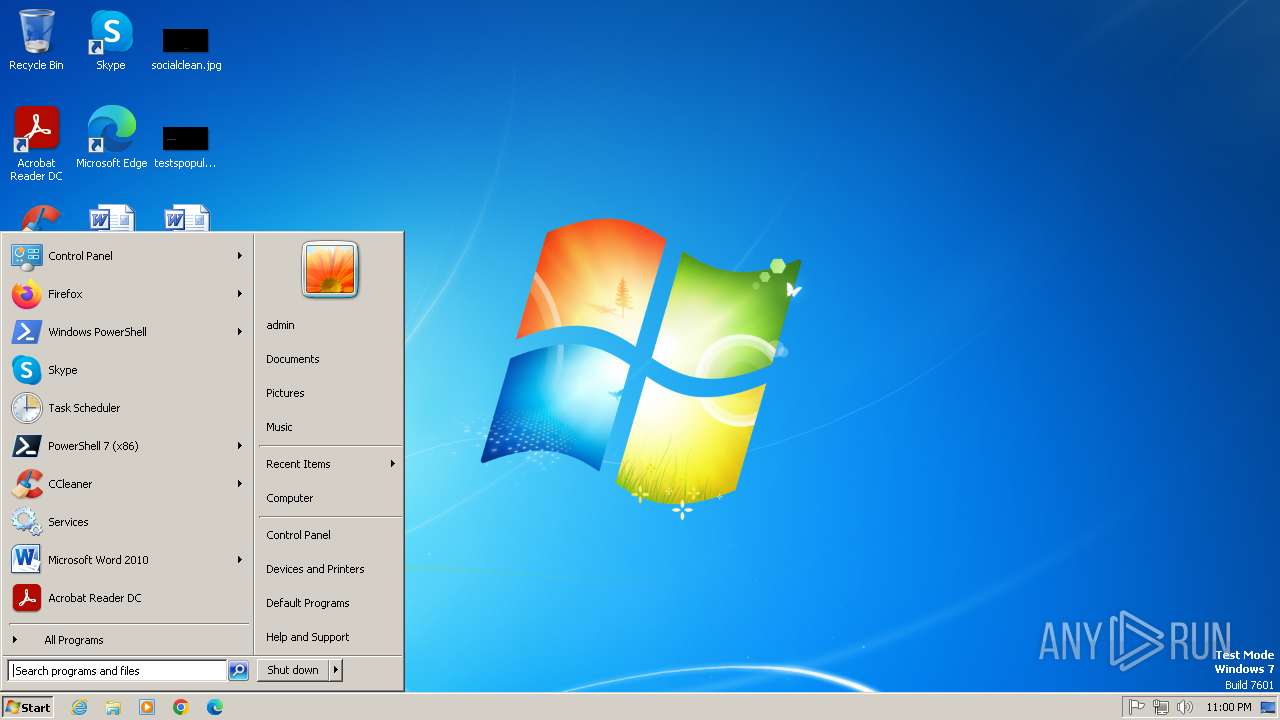
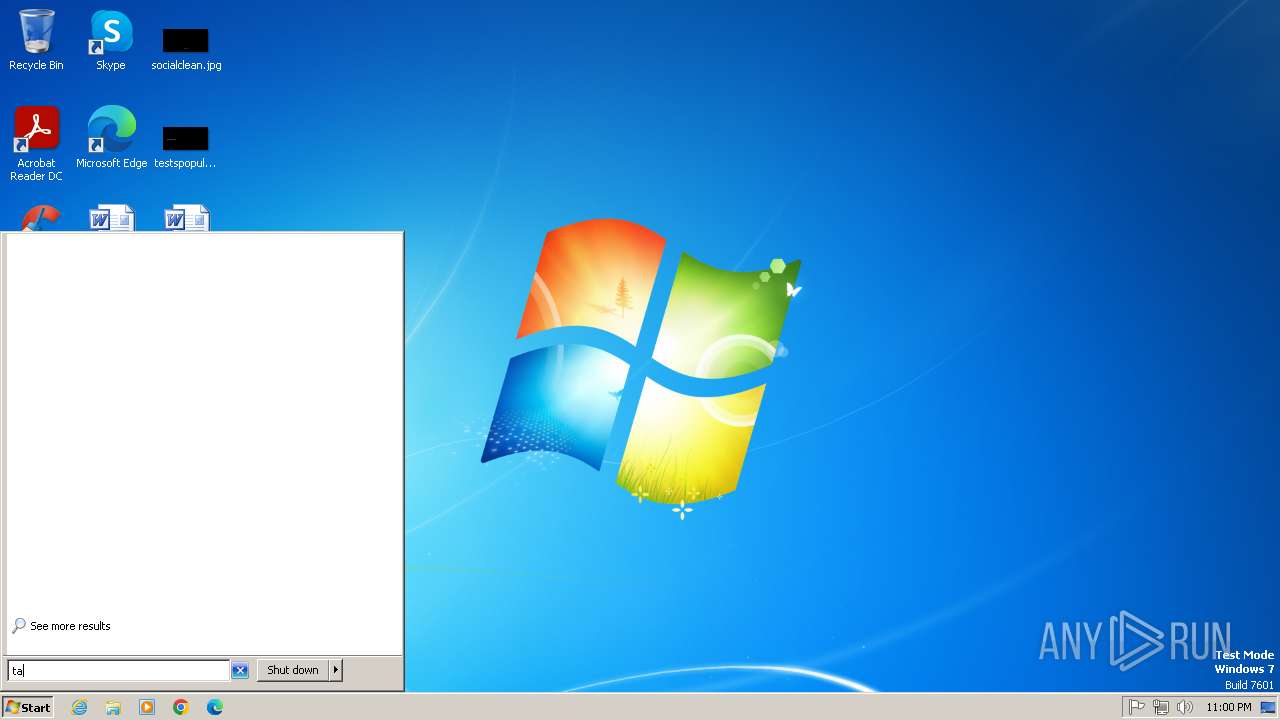
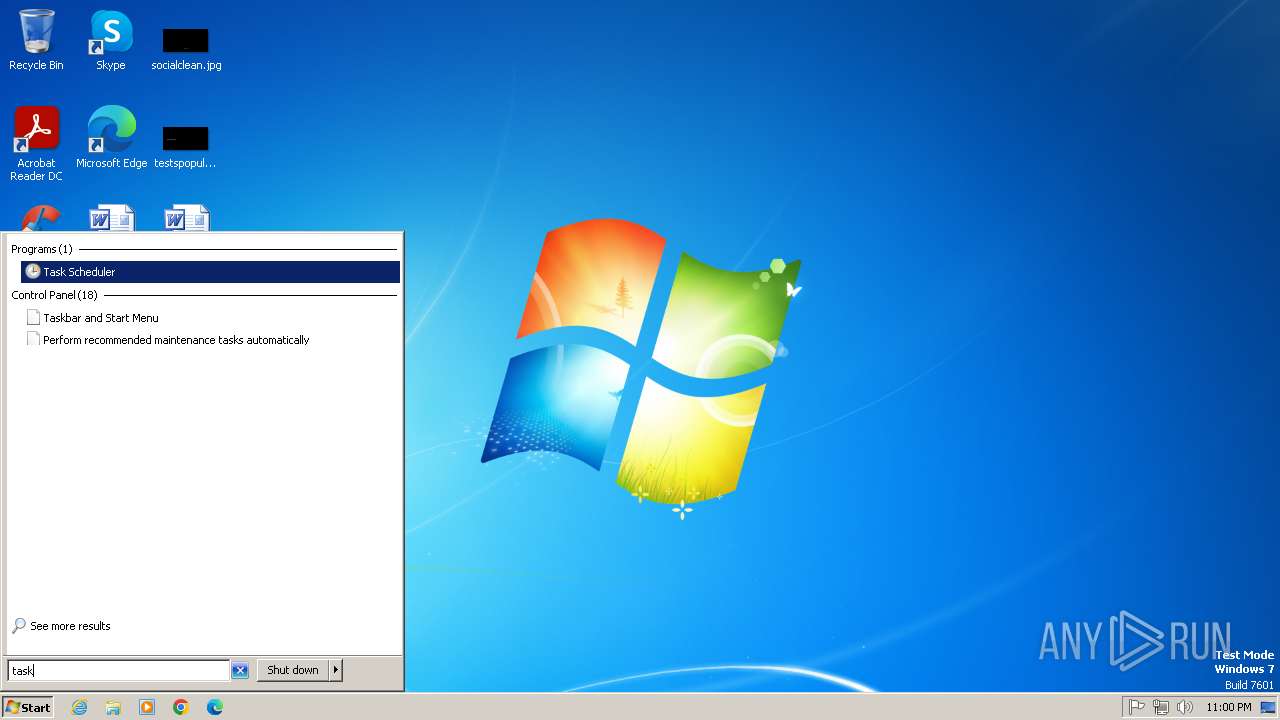
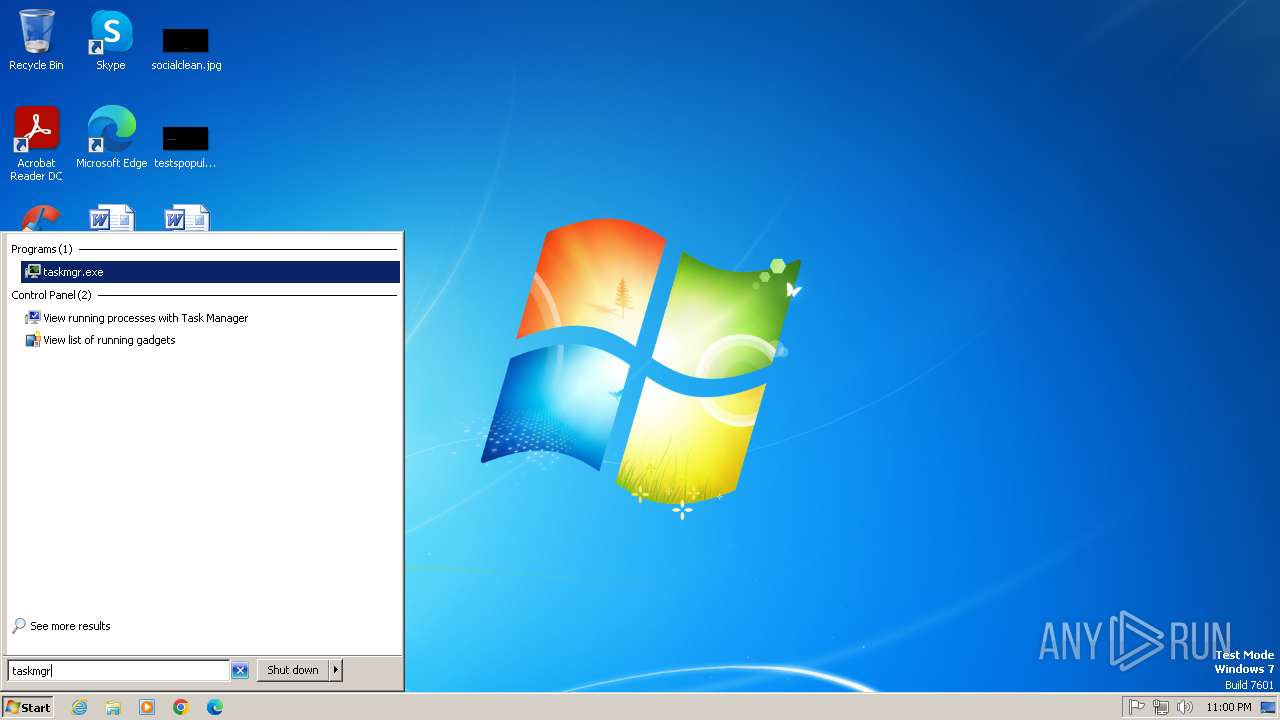
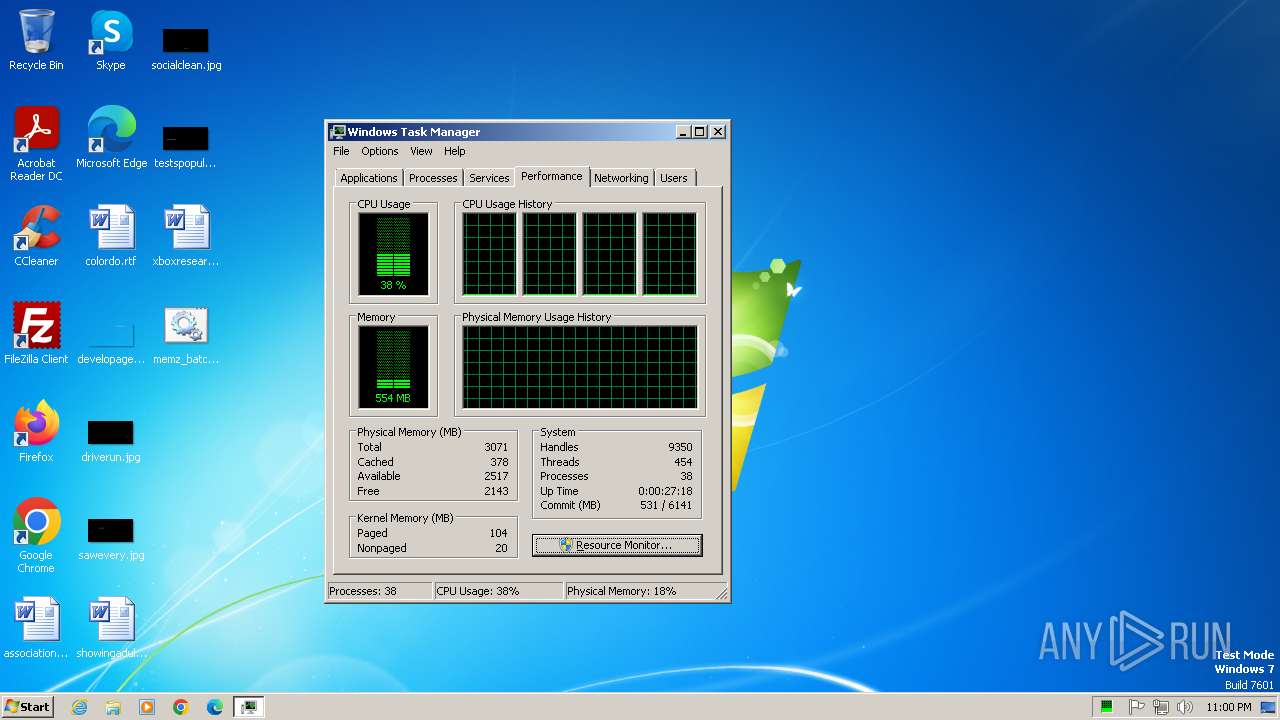
Manual execution by a user
- notepad.exe (PID: 3044)
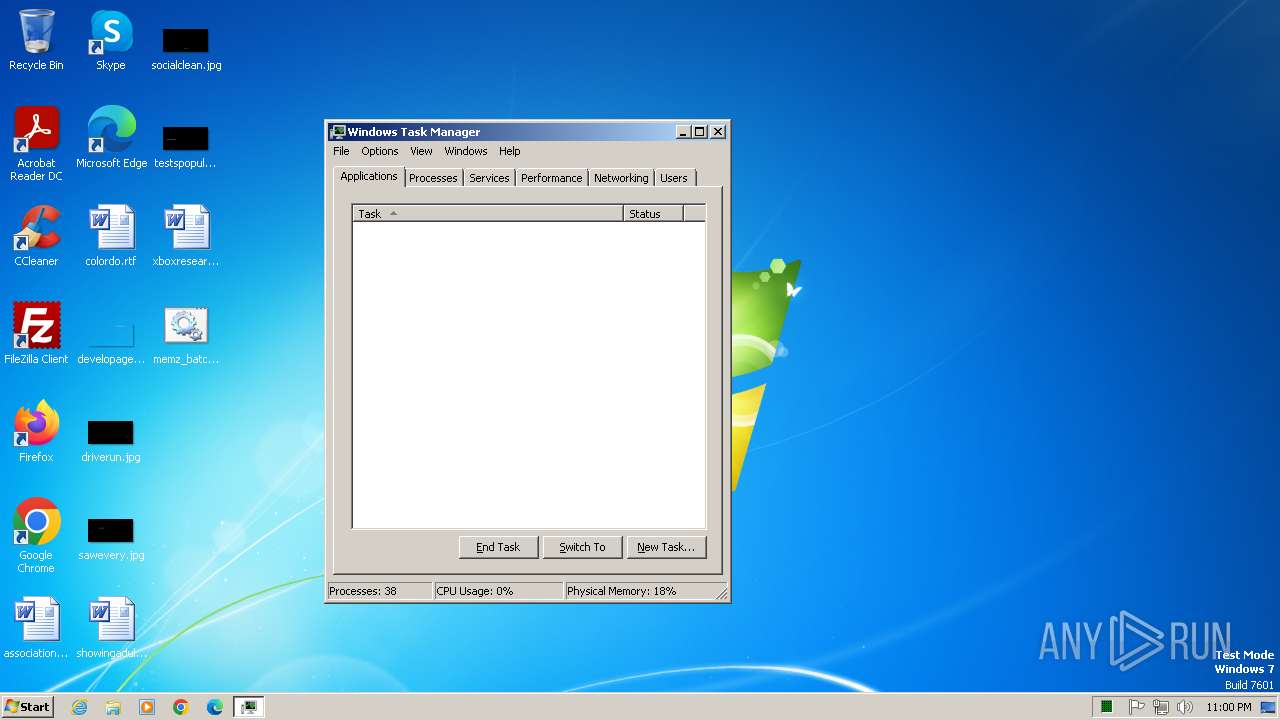
- taskmgr.exe (PID: 2420)
Reads the machine GUID from the registry
- MEMZ.exe (PID: 2392)
- MEMZ.exe (PID: 2912)
- MEMZ.exe (PID: 2508)
- MEMZ.exe (PID: 2528)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
50
Monitored processes
14
Malicious processes
9
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 892 | "C:\Users\admin\AppData\Roaming\MEMZ.exe" /watchdog | C:\Users\admin\AppData\Roaming\MEMZ.exe | MEMZ.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 1 Modules
| |||||||||||||||
| 1500 | "C:\Users\admin\AppData\Roaming\MEMZ.exe" /main | C:\Users\admin\AppData\Roaming\MEMZ.exe | MEMZ.exe | ||||||||||||
User: admin Integrity Level: HIGH Modules
| |||||||||||||||
| 1760 | cscript x.js | C:\Windows\System32\cscript.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Console Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 2056 | "C:\Users\admin\AppData\Roaming\MEMZ.exe" | C:\Users\admin\AppData\Roaming\MEMZ.exe | cmd.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2332 | "C:\Users\admin\AppData\Roaming\MEMZ.exe" | C:\Users\admin\AppData\Roaming\MEMZ.exe | — | cmd.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 2392 | "C:\Users\admin\AppData\Roaming\MEMZ.exe" /watchdog | C:\Users\admin\AppData\Roaming\MEMZ.exe | MEMZ.exe | ||||||||||||
User: admin Integrity Level: HIGH Modules
| |||||||||||||||
| 2408 | "C:\Users\admin\AppData\Roaming\MEMZ.exe" | C:\Users\admin\AppData\Roaming\MEMZ.exe | — | cmd.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 2420 | "C:\Windows\system32\taskmgr.exe" | C:\Windows\System32\taskmgr.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Task Manager Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2508 | "C:\Users\admin\AppData\Roaming\MEMZ.exe" /watchdog | C:\Users\admin\AppData\Roaming\MEMZ.exe | MEMZ.exe | ||||||||||||
User: admin Integrity Level: HIGH Modules
| |||||||||||||||
| 2528 | "C:\Users\admin\AppData\Roaming\MEMZ.exe" /watchdog | C:\Users\admin\AppData\Roaming\MEMZ.exe | MEMZ.exe | ||||||||||||
User: admin Integrity Level: HIGH Modules
| |||||||||||||||
Total events
2 372
Read events
2 300
Write events
72
Delete events
0
Modification events
| (PID) Process: | (1760) cscript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (1760) cscript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (1760) cscript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (1760) cscript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (2840) cmd.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2840) cmd.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2840) cmd.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (2840) cmd.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (2056) MEMZ.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2056) MEMZ.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
Executable files
1
Suspicious files
2
Text files
2
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1500 | MEMZ.exe | \Device\Harddisk0\DR0 | — | |
MD5:— | SHA256:— | |||
| 1760 | cscript.exe | C:\Users\admin\AppData\Roaming\MEMZ.exe | executable | |
MD5:19DBEC50735B5F2A72D4199C4E184960 | SHA256:A3D5715A81F2FBEB5F76C88C9C21EEEE87142909716472F911FF6950C790C24D | |||
| 2840 | cmd.exe | C:\Users\admin\Desktop\x | text | |
MD5:CFC1E7E18B9F9B70310C88F922E59B29 | SHA256:3DCF309E134AE67CAED27FA52782267C90646B405C4A9594041B284733B8E346 | |||
| 2840 | cmd.exe | C:\Users\admin\Desktop\x.js | text | |
MD5:D94C93F882CF030ED9D66CC35796731D | SHA256:F7941E6BE49D757B46B9D6FB5ECB15392EC36A64E8906692D2EEB2BA9FC67CB6 | |||
| 1760 | cscript.exe | C:\Users\admin\Desktop\z.zip | compressed | |
MD5:63EE4412B95D7AD64C54B4BA673470A7 | SHA256:44C1857B1C4894B3DFBACCBE04905652E634283DCF6B06C25A74B17021E2A268 | |||
| 1500 | MEMZ.exe | C:\note.txt | binary | |
MD5:AFA6955439B8D516721231029FB9CA1B | SHA256:8E9F20F6864C66576536C0B866C6FFDCF11397DB67FE120E972E244C3C022270 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
6
DNS requests
1
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 224.0.0.252:5355 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |