| File name: | 2025-05-16_b1ea0da65d77eaf98981e25be488e3b8_black-basta_elex_gcleaner_hijackloader |
| Full analysis: | https://app.any.run/tasks/8f6198f7-d34f-42b6-969c-bfb4b538e5fc |
| Verdict: | Malicious activity |
| Analysis date: | May 16, 2025, 06:10:16 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 8 sections |
| MD5: | B1EA0DA65D77EAF98981E25BE488E3B8 |
| SHA1: | D951847B793A1331446635409CAB3219C7DF4D41 |
| SHA256: | D8B380724E5B79709D25B3A6F111BC2756184B176404426288744214BF16CF69 |
| SSDEEP: | 98304:zSYpVEm5sn6gNEkdfaTgmHihuRB3FKFfpRBVnf9D0ks+Zo8Y1F2qaVhKffn7YAxV:taABbSuMv2caz |
MALICIOUS
Executing a file with an untrusted certificate
- Setup.exe (PID: 7608)
- 8599134700.exe (PID: 7460)
- 8599134700.exe (PID: 7536)
CANBIS mutex has been found
- 2025-05-16_b1ea0da65d77eaf98981e25be488e3b8_black-basta_elex_gcleaner_hijackloader.exe (PID: 7332)
SUSPICIOUS
Executable content was dropped or overwritten
- 2025-05-16_b1ea0da65d77eaf98981e25be488e3b8_black-basta_elex_gcleaner_hijackloader.exe (PID: 7332)
- 8599134700.exe (PID: 7536)
Process drops legitimate windows executable
- 2025-05-16_b1ea0da65d77eaf98981e25be488e3b8_black-basta_elex_gcleaner_hijackloader.exe (PID: 7332)
- 8599134700.exe (PID: 7536)
Starts a Microsoft application from unusual location
- 8599134700.exe (PID: 7460)
- 8599134700.exe (PID: 7536)
Reads security settings of Internet Explorer
- 2025-05-16_b1ea0da65d77eaf98981e25be488e3b8_black-basta_elex_gcleaner_hijackloader.exe (PID: 7332)
Creates file in the systems drive root
- 8599134700.exe (PID: 7536)
There is functionality for communication over UDP network (YARA)
- 2025-05-16_b1ea0da65d77eaf98981e25be488e3b8_black-basta_elex_gcleaner_hijackloader.exe (PID: 7332)
INFO
Checks supported languages
- 2025-05-16_b1ea0da65d77eaf98981e25be488e3b8_black-basta_elex_gcleaner_hijackloader.exe (PID: 7332)
- Setup.exe (PID: 7608)
- 8599134700.exe (PID: 7536)
Reads the machine GUID from the registry
- 8599134700.exe (PID: 7536)
Reads the computer name
- 8599134700.exe (PID: 7536)
- 2025-05-16_b1ea0da65d77eaf98981e25be488e3b8_black-basta_elex_gcleaner_hijackloader.exe (PID: 7332)
- Setup.exe (PID: 7608)
The sample compiled with korean language support
- 8599134700.exe (PID: 7536)
The sample compiled with japanese language support
- 8599134700.exe (PID: 7536)
The sample compiled with english language support
- 8599134700.exe (PID: 7536)
- 2025-05-16_b1ea0da65d77eaf98981e25be488e3b8_black-basta_elex_gcleaner_hijackloader.exe (PID: 7332)
Process checks computer location settings
- 2025-05-16_b1ea0da65d77eaf98981e25be488e3b8_black-basta_elex_gcleaner_hijackloader.exe (PID: 7332)
The sample compiled with chinese language support
- 8599134700.exe (PID: 7536)
The sample compiled with french language support
- 8599134700.exe (PID: 7536)
The sample compiled with russian language support
- 8599134700.exe (PID: 7536)
The sample compiled with Italian language support
- 8599134700.exe (PID: 7536)
The sample compiled with german language support
- 8599134700.exe (PID: 7536)
The sample compiled with spanish language support
- 8599134700.exe (PID: 7536)
Reads the software policy settings
- slui.exe (PID: 8084)
Checks proxy server information
- slui.exe (PID: 8084)
Reads CPU info
- Setup.exe (PID: 7608)
Create files in a temporary directory
- Setup.exe (PID: 7608)
Failed to create an executable file in Windows directory
- 2025-05-16_b1ea0da65d77eaf98981e25be488e3b8_black-basta_elex_gcleaner_hijackloader.exe (PID: 7332)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable Borland Delphi 7 (55.2) |
|---|---|---|
| .exe | | | Win32 Executable Borland Delphi 5 (37.5) |
| .exe | | | InstallShield setup (3.5) |
| .exe | | | Win32 Executable Delphi generic (1.1) |
| .scr | | | Windows screen saver (1) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 1992:06:19 22:22:17+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, Bytes reversed lo, 32-bit, Bytes reversed hi |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 46080 |
| InitializedDataSize: | 7680 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xc254 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Total processes
133
Monitored processes
5
Malicious processes
2
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 7332 | "C:\Users\admin\Desktop\2025-05-16_b1ea0da65d77eaf98981e25be488e3b8_black-basta_elex_gcleaner_hijackloader.exe" | C:\Users\admin\Desktop\2025-05-16_b1ea0da65d77eaf98981e25be488e3b8_black-basta_elex_gcleaner_hijackloader.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Modules
| |||||||||||||||
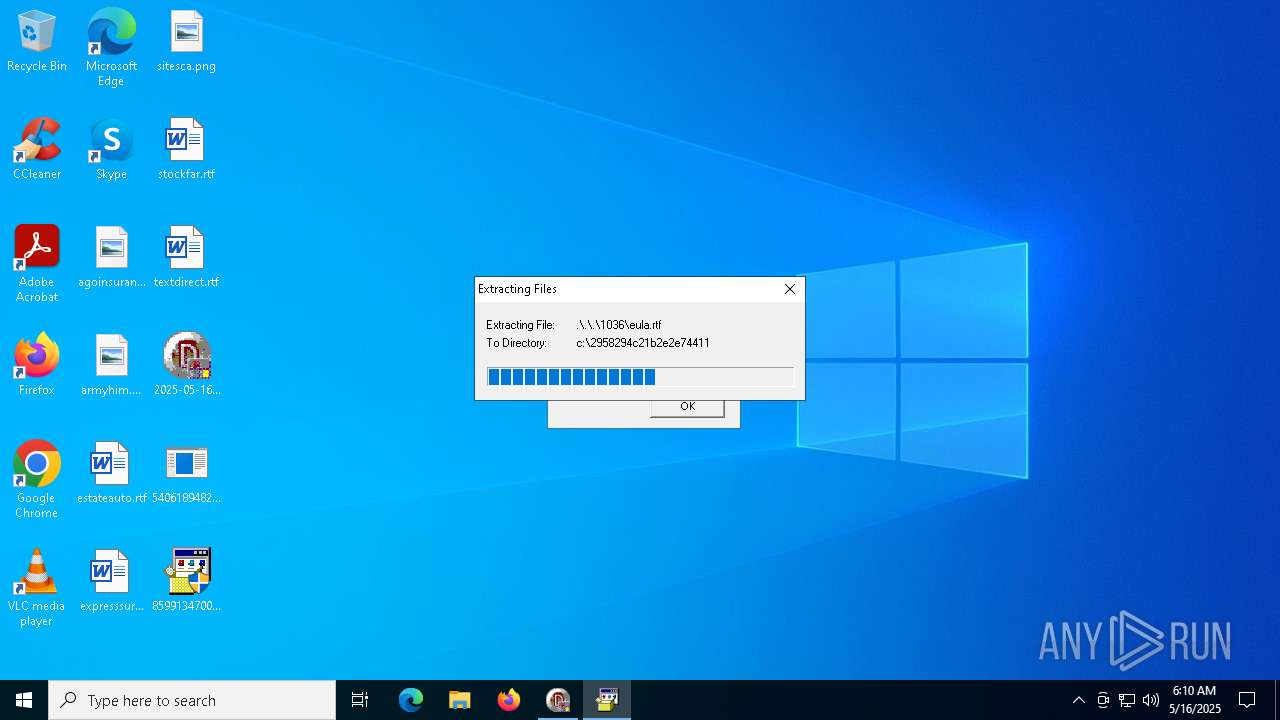
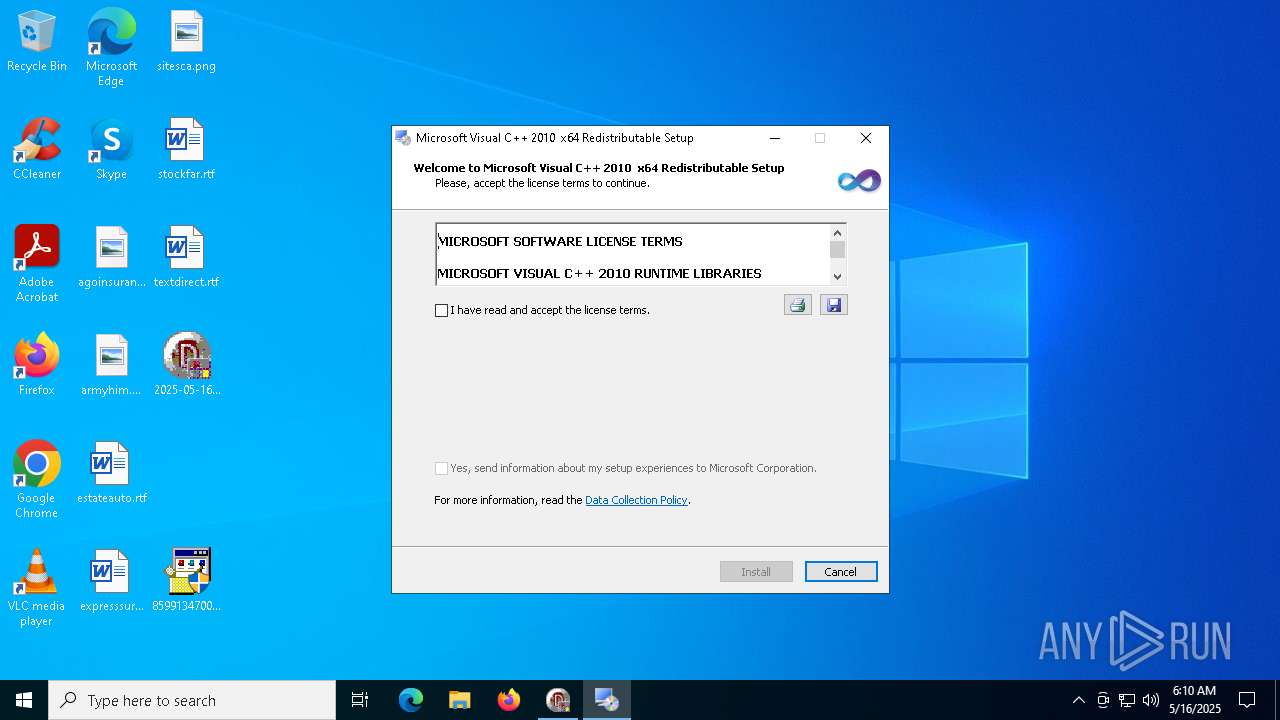
| 7460 | "C:\Users\admin\Desktop\8599134700.exe" | C:\Users\admin\Desktop\8599134700.exe | — | 2025-05-16_b1ea0da65d77eaf98981e25be488e3b8_black-basta_elex_gcleaner_hijackloader.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Visual C++ 2010 x64 Redistributable Setup Exit code: 3221226540 Version: 10.0.30319.01 Modules
| |||||||||||||||
| 7536 | "C:\Users\admin\Desktop\8599134700.exe" | C:\Users\admin\Desktop\8599134700.exe | 2025-05-16_b1ea0da65d77eaf98981e25be488e3b8_black-basta_elex_gcleaner_hijackloader.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Visual C++ 2010 x64 Redistributable Setup Version: 10.0.30319.01 Modules
| |||||||||||||||
| 7608 | c:\2958294c21b2e2e74411\Setup.exe | C:\2958294c21b2e2e74411\Setup.exe | — | 8599134700.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Setup Installer Version: 10.0.30319.1 built by: RTMRel Modules
| |||||||||||||||
| 8084 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
4 216
Read events
4 216
Write events
0
Delete events
0
Modification events
Executable files
17
Suspicious files
1
Text files
47
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7332 | 2025-05-16_b1ea0da65d77eaf98981e25be488e3b8_black-basta_elex_gcleaner_hijackloader.exe | C:\Users\admin\Desktop\5406189482.exe | executable | |
MD5:B1EA0DA65D77EAF98981E25BE488E3B8 | SHA256:D8B380724E5B79709D25B3A6F111BC2756184B176404426288744214BF16CF69 | |||
| 7332 | 2025-05-16_b1ea0da65d77eaf98981e25be488e3b8_black-basta_elex_gcleaner_hijackloader.exe | C:\Users\admin\Desktop\8599134700.exe | executable | |
MD5:630D75210B325A280C3352F879297ED5 | SHA256:B06546DDC8CA1E3D532F3F2593E88A6F49E81B66A9C2051D58508CC97B6A2023 | |||
| 7536 | 8599134700.exe | C:\2958294c21b2e2e74411\SetupUi.xsd | xml | |
MD5:2FADD9E618EFF8175F2A6E8B95C0CACC | SHA256:222211E8F512EDF97D78BC93E1F271C922D5E91FA899E092B4A096776A704093 | |||
| 7536 | 8599134700.exe | C:\2958294c21b2e2e74411\SetupUi.dll | executable | |
MD5:EB881E3DDDC84B20BD92ABCEC444455F | SHA256:11565D97287C01D22AD2E46C78D8A822FA3E6524561D4C02DFC87E8D346C44E7 | |||
| 7536 | 8599134700.exe | C:\2958294c21b2e2e74411\DHtmlHeader.html | html | |
MD5:CD131D41791A543CC6F6ED1EA5BD257C | SHA256:E139AF8858FE90127095AC1C4685BCD849437EF0DF7C416033554703F5D864BB | |||
| 7536 | 8599134700.exe | C:\2958294c21b2e2e74411\Strings.xml | xml | |
MD5:332ADF643747297B9BFA9527EAEFE084 | SHA256:E49545FEEAE22198728AD04236E31E02035AF7CC4D68E10CBECFFD08669CBECA | |||
| 7536 | 8599134700.exe | C:\2958294c21b2e2e74411\sqmapi.dll | executable | |
MD5:3F0363B40376047EFF6A9B97D633B750 | SHA256:BD6395A58F55A8B1F4063E813CE7438F695B9B086BB965D8AC44E7A97D35A93C | |||
| 7536 | 8599134700.exe | C:\2958294c21b2e2e74411\SetupEngine.dll | executable | |
MD5:84C1DAF5F30FF99895ECAB3A55354BCF | SHA256:7A0D281FA802D615EA1207BD2E9EBB98F3B74F9833BBA3CB964BA7C7E0FB67FD | |||
| 7536 | 8599134700.exe | C:\2958294c21b2e2e74411\watermark.bmp | image | |
MD5:1A5CAAFACFC8C7766E404D019249CF67 | SHA256:2E87D5742413254DB10F7BD0762B6CDB98FF9C46CA9ACDDFD9B1C2E5418638F2 | |||
| 7536 | 8599134700.exe | C:\2958294c21b2e2e74411\Setup.exe | executable | |
MD5:006F8A615020A4A17F5E63801485DF46 | SHA256:D273460AA4D42F0B5764383E2AB852AB9AF6FECB3ED866F1783869F2F155D8BE | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
11
TCP/UDP connections
49
DNS requests
17
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2104 | svchost.exe | GET | 200 | 2.20.245.139:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
2104 | svchost.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
1196 | RUXIMICS.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
1196 | RUXIMICS.exe | GET | 200 | 2.20.245.139:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
7892 | SIHClient.exe | GET | 200 | 23.219.150.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Update%20Signing%20CA%202.1.crl | unknown | — | — | whitelisted |
7892 | SIHClient.exe | GET | 200 | 2.19.11.105:80 | http://crl.microsoft.com/pki/crl/products/MicTimStaPCA_2010-07-01.crl | unknown | — | — | whitelisted |
7892 | SIHClient.exe | GET | 200 | 2.19.11.105:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut_2010-06-23.crl | unknown | — | — | whitelisted |
7892 | SIHClient.exe | GET | 200 | 23.219.150.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7892 | SIHClient.exe | GET | 200 | 23.219.150.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Signing%20CA%202.1.crl | unknown | — | — | whitelisted |
7892 | SIHClient.exe | GET | 200 | 23.219.150.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Signing%20CA%202.2.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2104 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1196 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2104 | svchost.exe | 2.20.245.139:80 | crl.microsoft.com | Akamai International B.V. | SE | whitelisted |
1196 | RUXIMICS.exe | 2.20.245.139:80 | crl.microsoft.com | Akamai International B.V. | SE | whitelisted |
2104 | svchost.exe | 2.23.246.101:80 | www.microsoft.com | Ooredoo Q.S.C. | QA | whitelisted |
1196 | RUXIMICS.exe | 2.23.246.101:80 | www.microsoft.com | Ooredoo Q.S.C. | QA | whitelisted |
3216 | svchost.exe | 172.211.123.250:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
uk.undernet.org |
| unknown |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |