| File name: | AutoLogger.exe |
| Full analysis: | https://app.any.run/tasks/a1dc5c53-f0e6-49d0-9935-a292844e400d |
| Verdict: | No threats detected |
| Analysis date: | March 25, 2019, 18:56:35 |
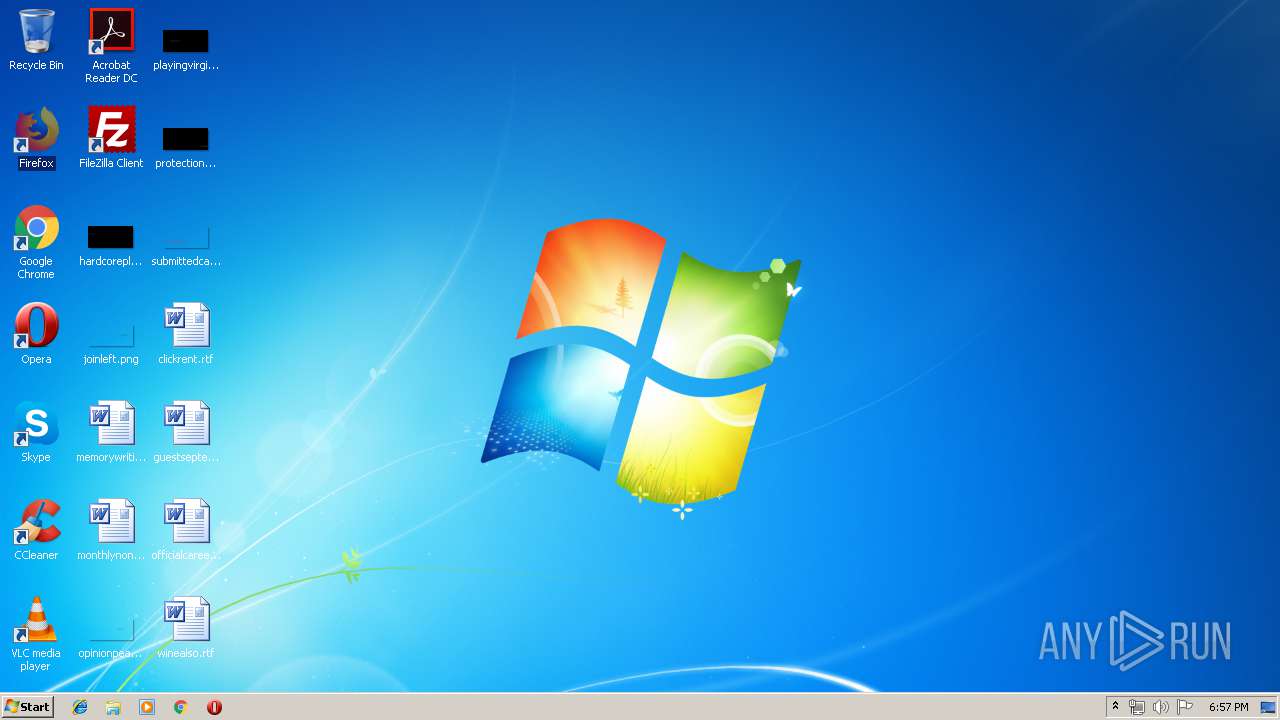
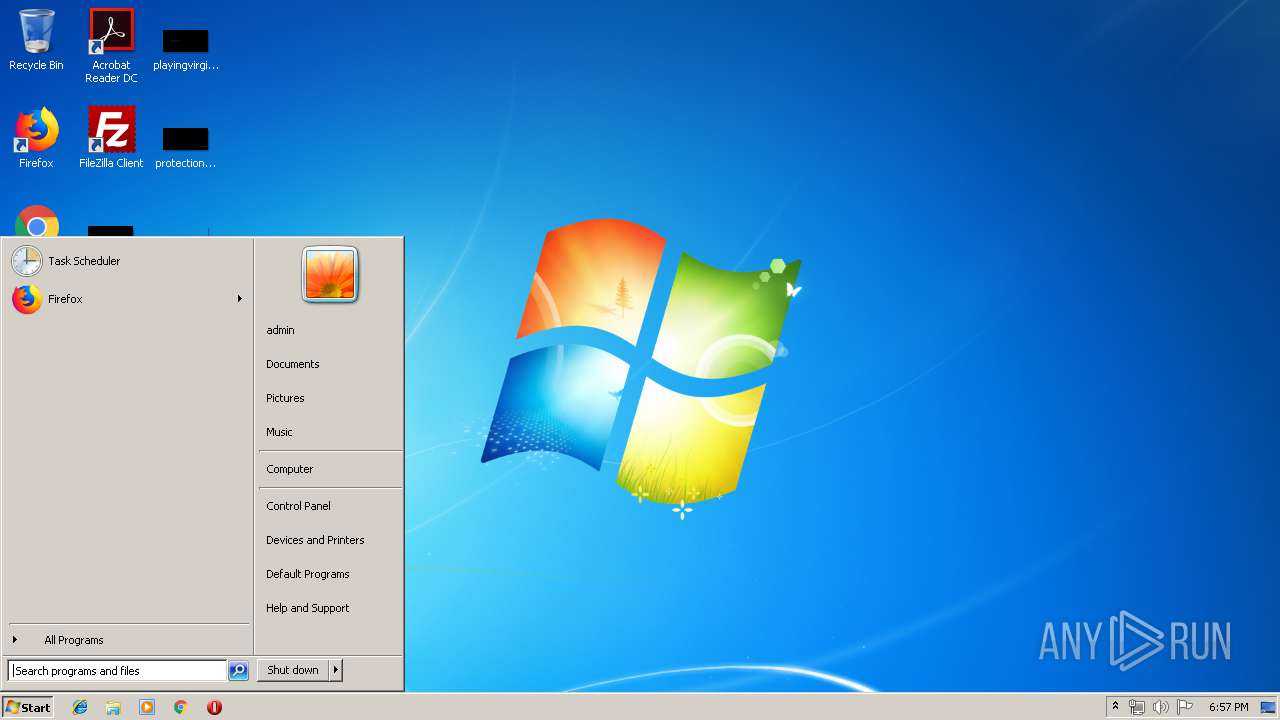
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 142E072DC826C85F965ED181D93C2B5F |
| SHA1: | E303352A18714687B49BE5E4E11D3003D78809DB |
| SHA256: | D8ABAB07B5AAD79B7E2599AFB4FD9ECE84D4297FC21CE69DC0536EF84FBD20B2 |
| SSDEEP: | 196608:E1EjUd7KusQ7bwCAS0sX+OuWjkb0ESbzuM6eNT1JDTZ2inFHKQ1Vn8i0zOfoIgzH:E1wpuscwCeg5VjlEVSNTbR2iAQrPkPT |
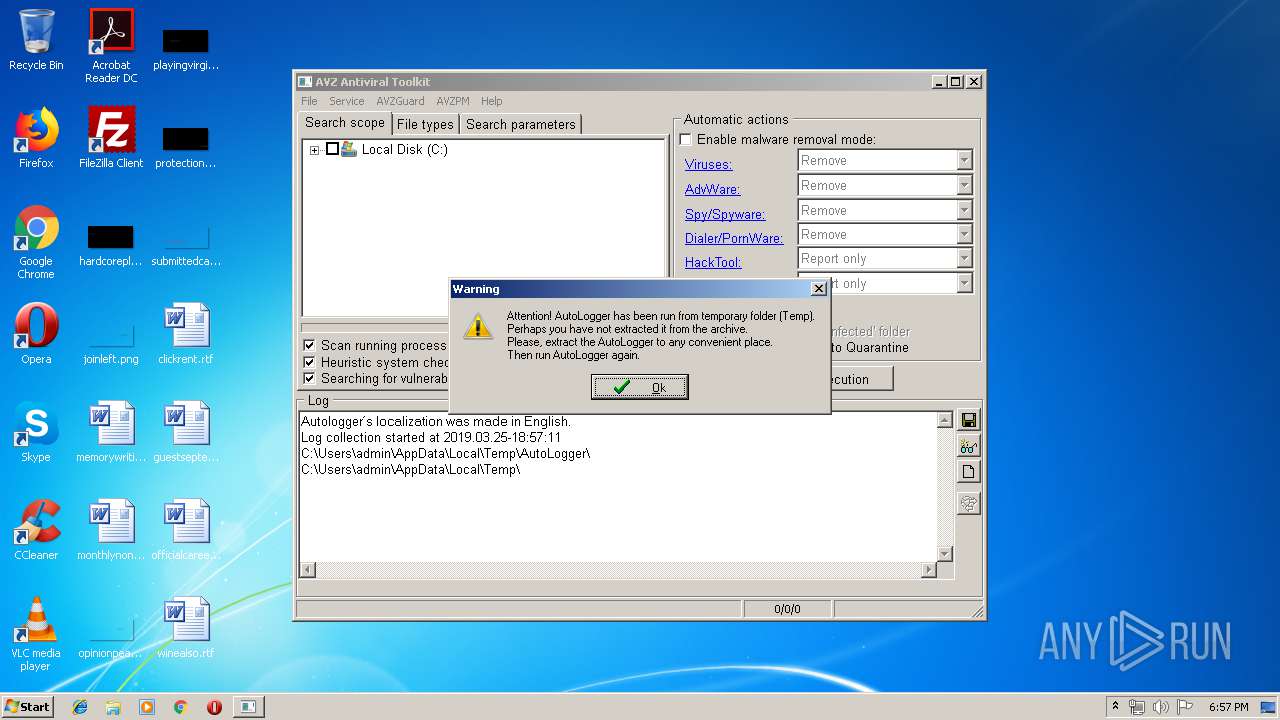
MALICIOUS
Application was dropped or rewritten from another process
- avz.exe (PID: 2740)
SUSPICIOUS
Executable content was dropped or overwritten
- AutoLogger.exe (PID: 3600)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic Win/DOS Executable (50) |
|---|---|---|
| .exe | | | DOS Executable Generic (49.9) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2016:04:03 00:14:00+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 8 |
| CodeSize: | 101888 |
| InitializedDataSize: | 223232 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x193af |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.7.0.3900 |
| ProductVersionNumber: | 1.7.0.3900 |
| FileFlagsMask: | 0x003f |
| FileFlags: | Private build |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unknown (FDE9) |
| Comments: | - |
| CompanyName: | Company © regist & Drongo |
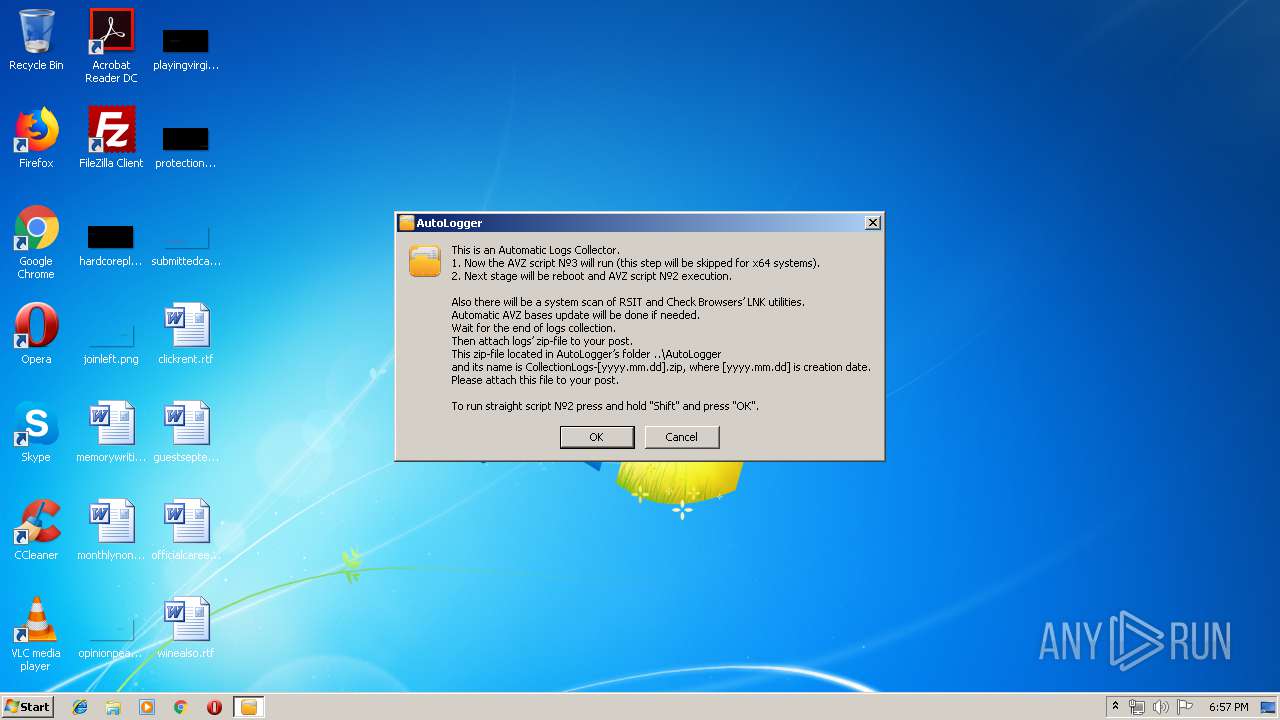
| FileDescription: | Automatic log collector |
| FileVersion: | 1.0.2.4 |
| InternalName: | AutoLogger |
| LegalCopyright: | All rights for Autologger reserved by regist & Drongo © Copyright 2013 - 2017 |
| LegalTrademarks: | - |
| OriginalFileName: | AutoLogger.exe |
| PrivateBuild: | - |
| ProductName: | AutoLogger |
| ProductVersion: | 1.0.2.4 |
| SpecialBuild: | - |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 02-Apr-2016 22:14:00 |
| Detected languages: |
|
| Comments: | - |
| CompanyName: | Company © regist & Drongo |
| FileDescription: | Автоматический сборщик логов |
| FileVersion: | 1.0.2.4 |
| InternalName: | AutoLogger |
| LegalCopyright: | Все права на AutoLogger принадлежат regist & Drongo © Copyright 2013 - 2017 |
| LegalTrademarks: | - |
| OriginalFilename: | AutoLogger.exe |
| PrivateBuild: | - |
| ProductName: | AutoLogger |
| ProductVersion: | 1.0.2.4 |
| SpecialBuild: | - |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0060 |
| Pages in file: | 0x0001 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000060 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 02-Apr-2016 22:14:00 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00018D6A | 0x00018E00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.69082 |
.rdata | 0x0001A000 | 0x00003FA0 | 0x00004000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.7721 |
.data | 0x0001E000 | 0x00004B90 | 0x00000800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.63636 |
.rsrc | 0x00023000 | 0x0002DAC9 | 0x0002DC00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.64746 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.14631 | 1425 | UNKNOWN | UNKNOWN | RT_MANIFEST |
2 | 6.13752 | 1128 | UNKNOWN | UNKNOWN | RT_ICON |
3 | 6.48221 | 2440 | UNKNOWN | UNKNOWN | RT_ICON |
4 | 7.96191 | 21052 | UNKNOWN | UNKNOWN | RT_ICON |
5 | 6.20237 | 4264 | UNKNOWN | UNKNOWN | RT_ICON |
6 | 6.27832 | 9640 | UNKNOWN | UNKNOWN | RT_ICON |
7 | 6.18354 | 16936 | UNKNOWN | UNKNOWN | RT_ICON |
8 | 6.26713 | 21640 | UNKNOWN | UNKNOWN | RT_ICON |
9 | 6.41427 | 38056 | UNKNOWN | UNKNOWN | RT_ICON |
101 | 3.03466 | 132 | UNKNOWN | UNKNOWN | RT_GROUP_ICON |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
MSVCRT.dll |
OLEAUT32.dll |
SHELL32.dll |
USER32.dll |
ole32.dll |
Total processes
37
Monitored processes
3
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1812 | "C:\Users\admin\AppData\Local\Temp\AutoLogger.exe" | C:\Users\admin\AppData\Local\Temp\AutoLogger.exe | — | explorer.exe | |||||||||||
User: admin Company: Company © regist & Drongo Integrity Level: MEDIUM Description: Automatic log collector Exit code: 3221226540 Version: 1.0.2.4 Modules
| |||||||||||||||
| 2740 | "C:\Users\admin\AppData\Local\Temp\AutoLogger\AVZ\avz.exe" Script=AVZ\GeneralScript.txt HiddenMode=0 | C:\Users\admin\AppData\Local\Temp\AutoLogger\AVZ\avz.exe | — | AutoLogger.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 3600 | "C:\Users\admin\AppData\Local\Temp\AutoLogger.exe" | C:\Users\admin\AppData\Local\Temp\AutoLogger.exe | explorer.exe | ||||||||||||
User: admin Company: Company © regist & Drongo Integrity Level: HIGH Description: Automatic log collector Exit code: 0 Version: 1.0.2.4 Modules
| |||||||||||||||
Total events
713
Read events
709
Write events
4
Delete events
0
Modification events
| (PID) Process: | (3600) AutoLogger.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3600) AutoLogger.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
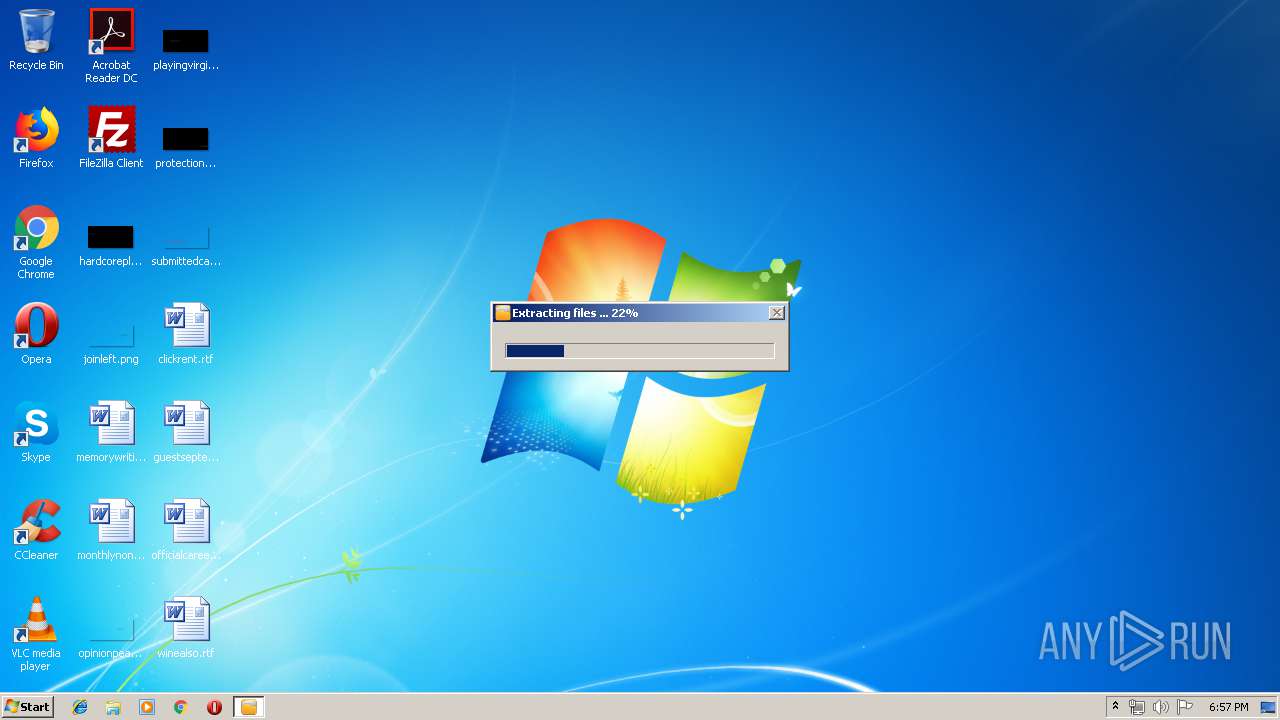
Executable files
7
Suspicious files
1
Text files
13
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3600 | AutoLogger.exe | C:\Users\admin\AppData\Local\Temp\AutoLogger\AVZ\GeneralScript.txt | text | |
MD5:— | SHA256:— | |||
| 3600 | AutoLogger.exe | C:\Users\admin\AppData\Local\Temp\AutoLogger\AVZ\ru_loc.ini | text | |
MD5:— | SHA256:— | |||
| 3600 | AutoLogger.exe | C:\Users\admin\AppData\Local\Temp\AutoLogger\AVZ\avz.exe | executable | |
MD5:— | SHA256:— | |||
| 3600 | AutoLogger.exe | C:\Users\admin\AppData\Local\Temp\AutoLogger\AVZ\Script2.txt | text | |
MD5:— | SHA256:— | |||
| 3600 | AutoLogger.exe | C:\Users\admin\AppData\Local\Temp\AutoLogger\CheckBrowsersLNK\Check Browsers LNK.exe | executable | |
MD5:— | SHA256:— | |||
| 3600 | AutoLogger.exe | C:\Users\admin\AppData\Local\Temp\AutoLogger\AVZ\RunUnlock.inf | binary | |
MD5:— | SHA256:— | |||
| 3600 | AutoLogger.exe | C:\Users\admin\AppData\Local\Temp\AutoLogger\AVZ\en_loc.ini | text | |
MD5:— | SHA256:— | |||
| 3600 | AutoLogger.exe | C:\Users\admin\AppData\Local\Temp\AutoLogger\AVZ\7za.exe | executable | |
MD5:744D0E63BCB20438DD3EFCD764503490 | SHA256:77613CCA716EDF68B9D5BAB951463ED7FADE5BC0EC465B36190A76299C50F117 | |||
| 3600 | AutoLogger.exe | C:\Users\admin\AppData\Local\Temp\AutoLogger\RSIT\HiJackThis.exe | executable | |
MD5:47811D50390A86A17102D7496E6EABB9 | SHA256:9DA5A899B9D55E1D43718EC0AD6368F9E9EF0242A4E88CD5DDB2CC6D7BFA5FB3 | |||
| 3600 | AutoLogger.exe | C:\Users\admin\AppData\Local\Temp\AutoLogger\HiJackThis\HiJackThis.exe | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report