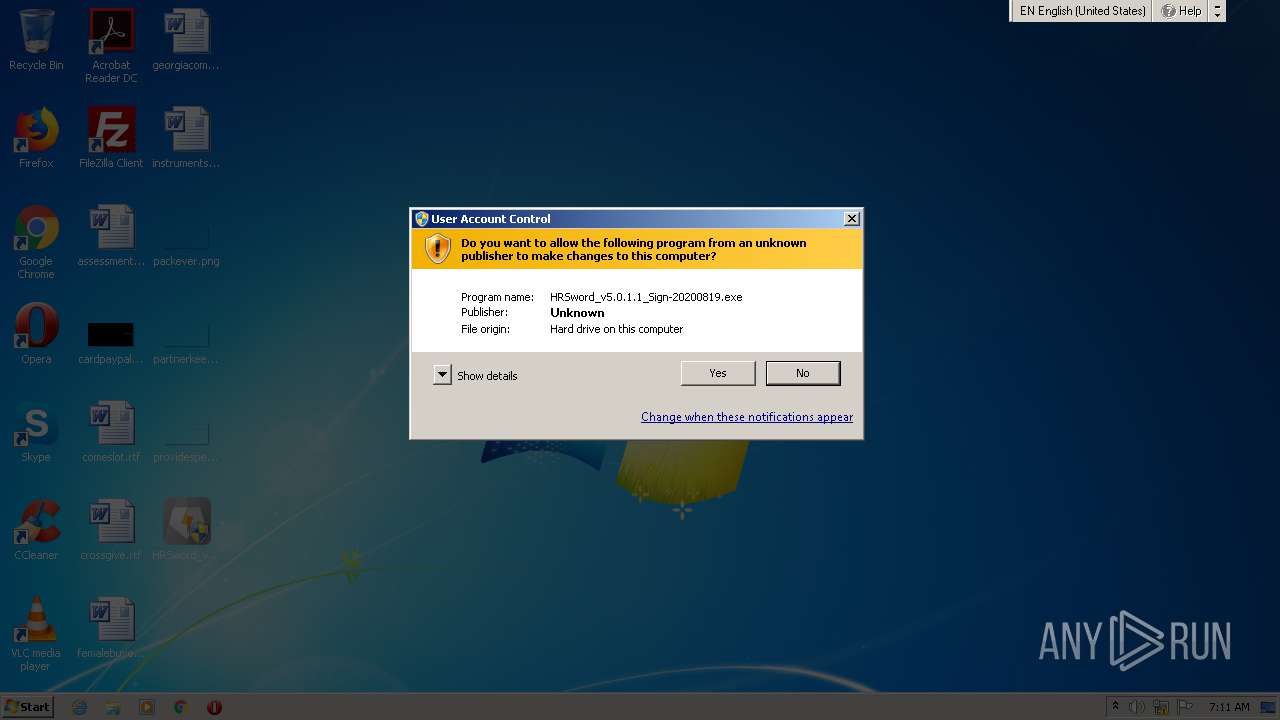
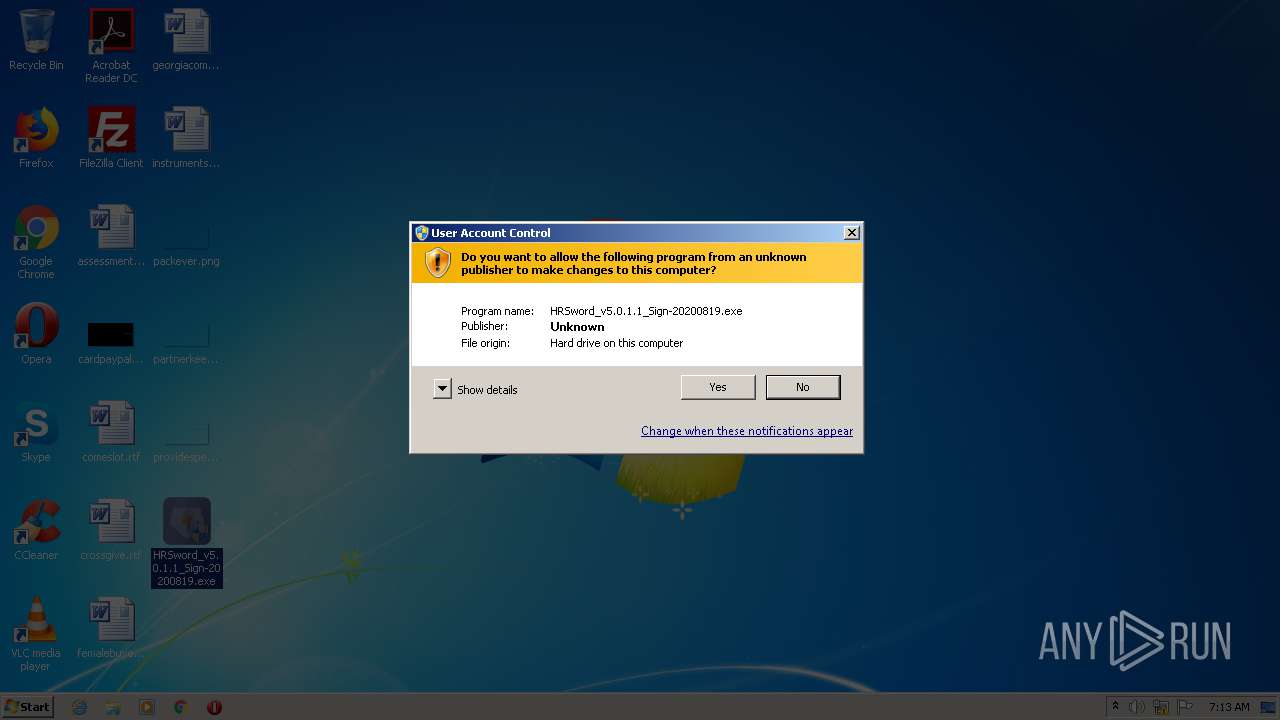
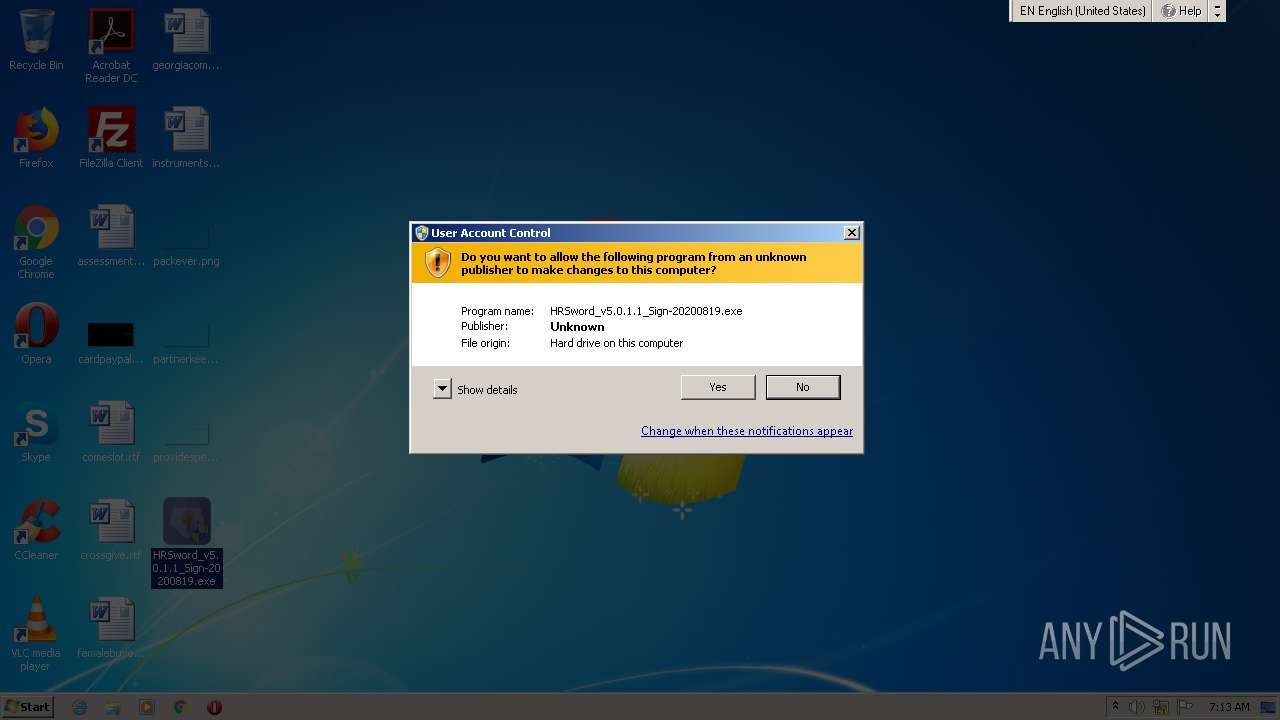
| File name: | HRSword_v5.0.1.1_Sign-20200819.exe |
| Full analysis: | https://app.any.run/tasks/3dfba472-c36a-4434-bc3d-ec640c605851 |
| Verdict: | Malicious activity |
| Analysis date: | September 30, 2020, 06:11:20 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, UPX compressed |
| MD5: | 5DCC1758A874241A0B8FC2268860EEA0 |
| SHA1: | CC7A4D5483D24FF706B6905787C8839817F1FCAC |
| SHA256: | D89B82F8699A59F4138C995A4FF1FB6A6E3993BEDFD4AC858F9F714C52AC49FE |
| SSDEEP: | 49152:NjP/JMkPMnXvJXWg4qXXOeQ9yCiOlG3nIl7VcHBsB2:ND/JPMXBGg4OXOeQ9AOlG3nItV6Ba2 |
MALICIOUS
Loads dropped or rewritten executable
- HRSword.exe (PID: 3936)
- HRSword.exe (PID: 3076)
Application was dropped or rewritten from another process
- usysdiag.exe (PID: 2572)
- HRSword.exe (PID: 3936)
- HRSword.exe (PID: 3076)
- usysdiag.exe (PID: 916)
Loads the Task Scheduler COM API
- HRSword.exe (PID: 3936)
- HRSword.exe (PID: 3076)
Starts NET.EXE for service management
- cmd.exe (PID: 3680)
Changes settings of System certificates
- usysdiag.exe (PID: 2572)
SUSPICIOUS
Starts CMD.EXE for commands execution
- HRSword_v5.0.1.1_Sign-20200819.exe (PID: 3608)
- cmd.exe (PID: 3680)
- HRSword_v5.0.1.1_Sign-20200819.exe (PID: 2888)
- cmd.exe (PID: 2484)
Executable content was dropped or overwritten
- HRSword_v5.0.1.1_Sign-20200819.exe (PID: 3608)
- cmd.exe (PID: 1688)
- cmd.exe (PID: 3684)
- cmd.exe (PID: 1712)
- HRSword_v5.0.1.1_Sign-20200819.exe (PID: 2888)
- cmd.exe (PID: 2152)
- cmd.exe (PID: 3824)
- cmd.exe (PID: 624)
Creates files in the Windows directory
- cmd.exe (PID: 3684)
- cmd.exe (PID: 1712)
- cmd.exe (PID: 3824)
- cmd.exe (PID: 624)
Application launched itself
- cmd.exe (PID: 3680)
- cmd.exe (PID: 2484)
Creates files in the driver directory
- cmd.exe (PID: 3684)
- cmd.exe (PID: 1712)
- cmd.exe (PID: 3824)
- cmd.exe (PID: 624)
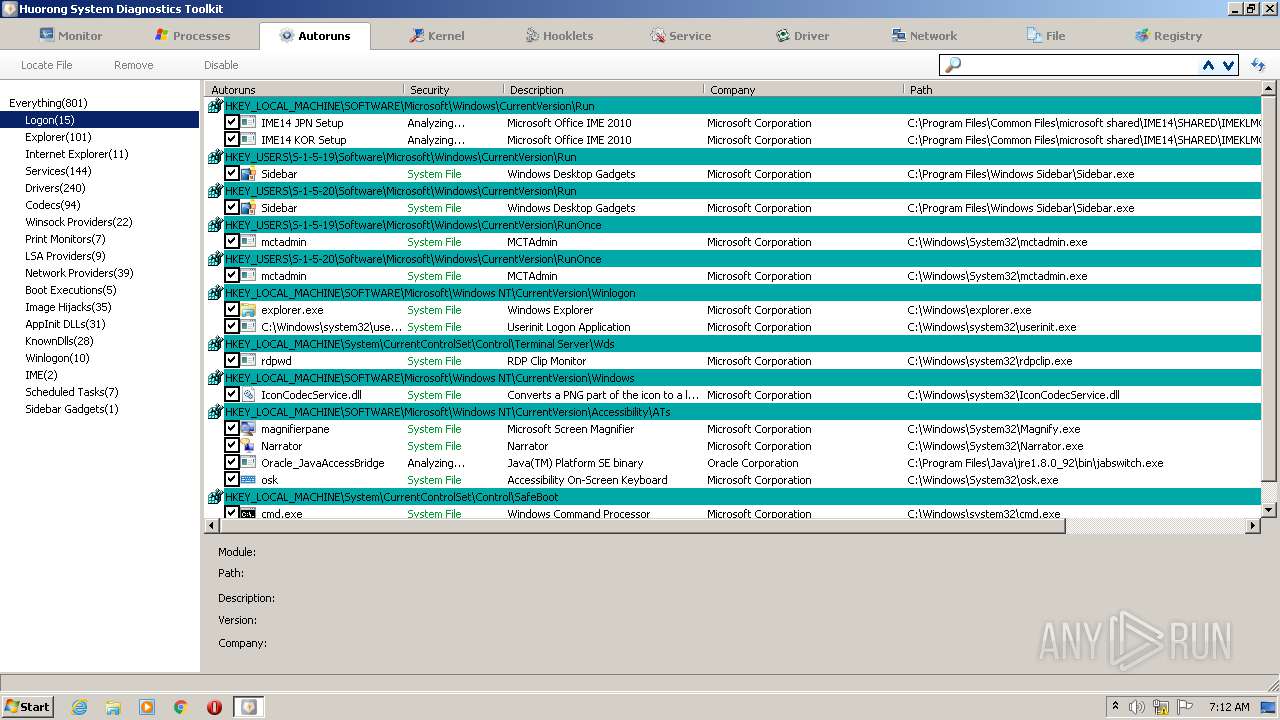
Uses REG.EXE to modify Windows registry
- cmd.exe (PID: 3680)
- cmd.exe (PID: 2484)
Creates or modifies windows services
- reg.exe (PID: 2968)
- reg.exe (PID: 2728)
- reg.exe (PID: 1504)
- reg.exe (PID: 4008)
- reg.exe (PID: 3648)
- reg.exe (PID: 2988)
- reg.exe (PID: 292)
- reg.exe (PID: 2492)
- reg.exe (PID: 3132)
- reg.exe (PID: 2428)
Starts SC.EXE for service management
- cmd.exe (PID: 3680)
- cmd.exe (PID: 2484)
Removes files from Windows directory
- cmd.exe (PID: 3680)
Adds / modifies Windows certificates
- usysdiag.exe (PID: 2572)
INFO
Manual execution by user
- HRSword_v5.0.1.1_Sign-20200819.exe (PID: 3724)
- HRSword_v5.0.1.1_Sign-20200819.exe (PID: 2284)
- HRSword_v5.0.1.1_Sign-20200819.exe (PID: 2888)
Reads settings of System Certificates
- usysdiag.exe (PID: 2572)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic Win/DOS Executable (50) |
|---|---|---|
| .exe | | | DOS Executable Generic (49.9) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2012:12:31 01:38:51+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 8 |
| CodeSize: | 65536 |
| InitializedDataSize: | 16384 |
| UninitializedDataSize: | 98304 |
| EntryPoint: | 0x28920 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 5.0.1.1 |
| ProductVersionNumber: | 5.0.0.1 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Unknown (0009) |
| CharacterSet: | Unicode |
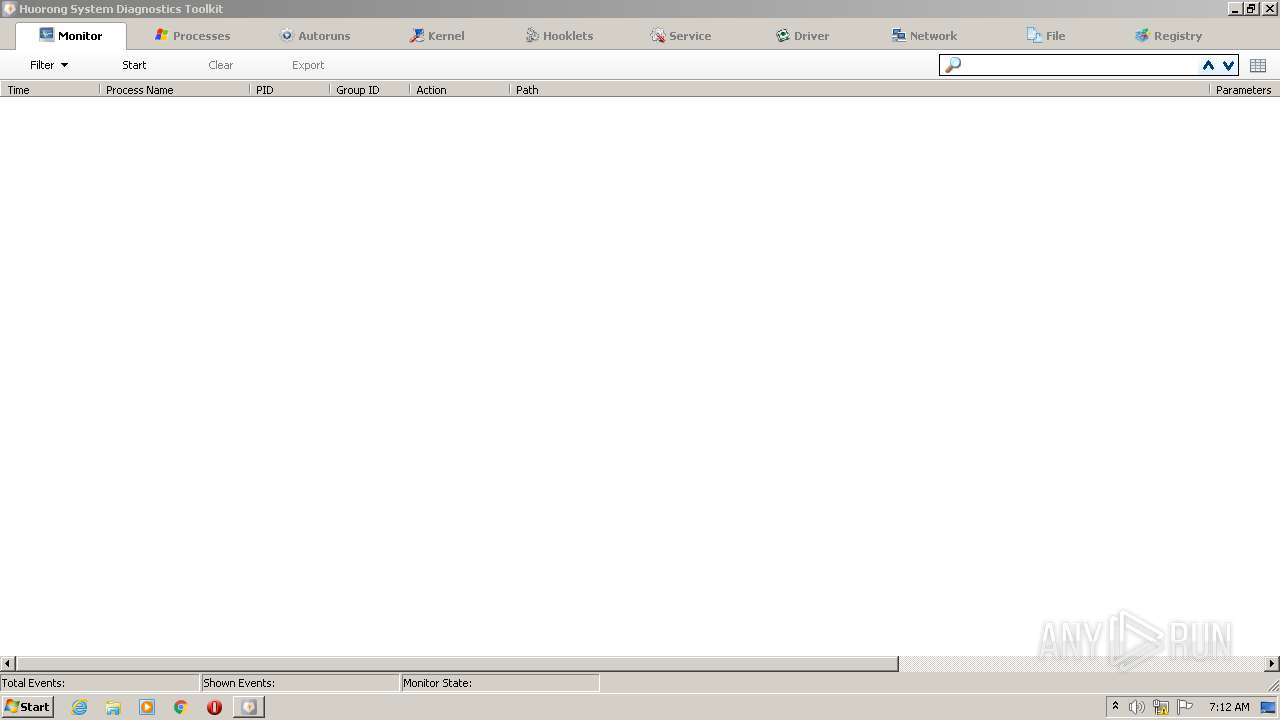
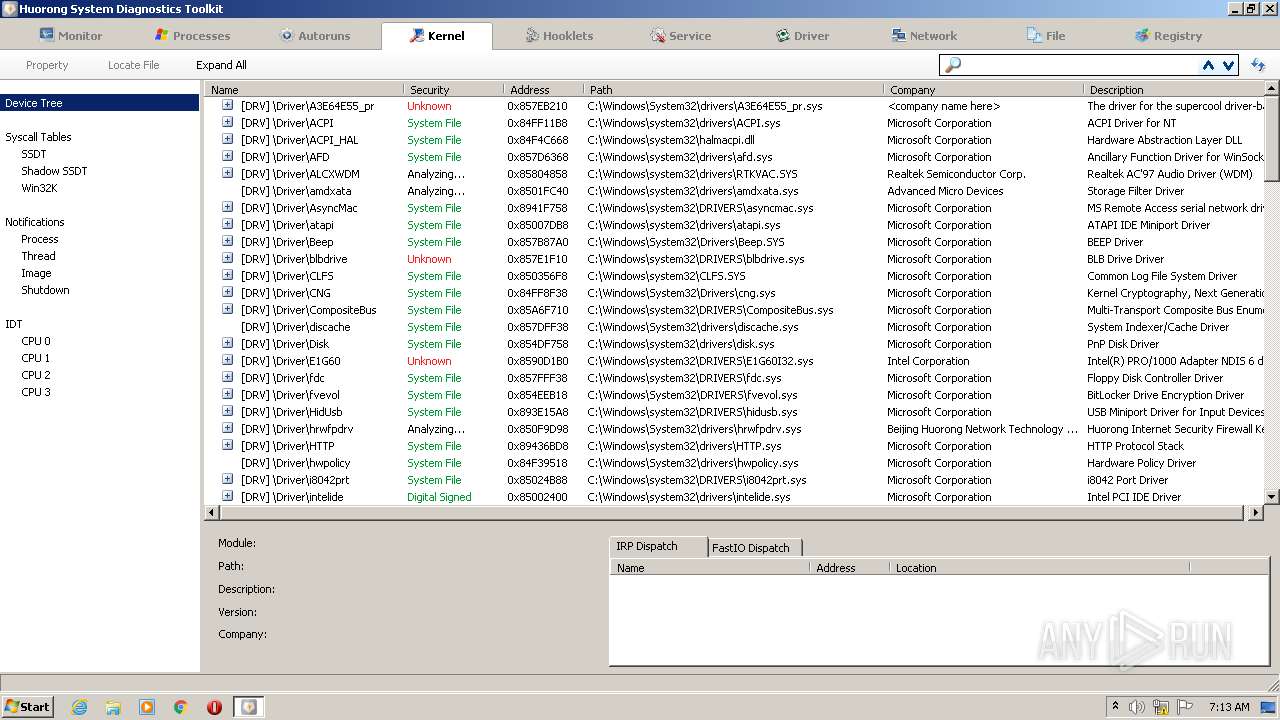
| CompanyName: | Beijing Huorong Network Technology Co., Ltd. |
| FileDescription: | Huorong Sword GUI Frontend |
| FileVersion: | 5.0.1.1 |
| InternalName: | HRSword |
| LegalCopyright: | Beijing Huorong Network Technology Co., Ltd. |
| OriginalFileName: | HRSword.exe |
| ProductName: | Huorong Internet Security |
| ProductVersion: | 5.0.0.1 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 31-Dec-2012 00:38:51 |
| Detected languages: |
|
| CompanyName: | Beijing Huorong Network Technology Co., Ltd. |
| FileDescription: | Huorong Sword GUI Frontend |
| FileVersion: | 5.0.1.1 |
| InternalName: | HRSword |
| LegalCopyright: | Beijing Huorong Network Technology Co., Ltd. |
| OriginalFilename: | HRSword.exe |
| ProductName: | Huorong Internet Security |
| ProductVersion: | 5.0.0.1 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0060 |
| Pages in file: | 0x0001 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000060 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 31-Dec-2012 00:38:51 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
UPX0 | 0x00001000 | 0x00018000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
UPX1 | 0x00019000 | 0x00010000 | 0x0000FC00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.91125 |
.rsrc | 0x00029000 | 0x00004000 | 0x00003400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 6.33064 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.41855 | 1528 | UNKNOWN | Chinese - PRC | RT_MANIFEST |
50 | 6.04792 | 9640 | UNKNOWN | UNKNOWN | RT_ICON |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.DLL |
MSVCRT.dll |
OLEAUT32.dll |
SHELL32.dll |
USER32.dll |
ole32.dll |
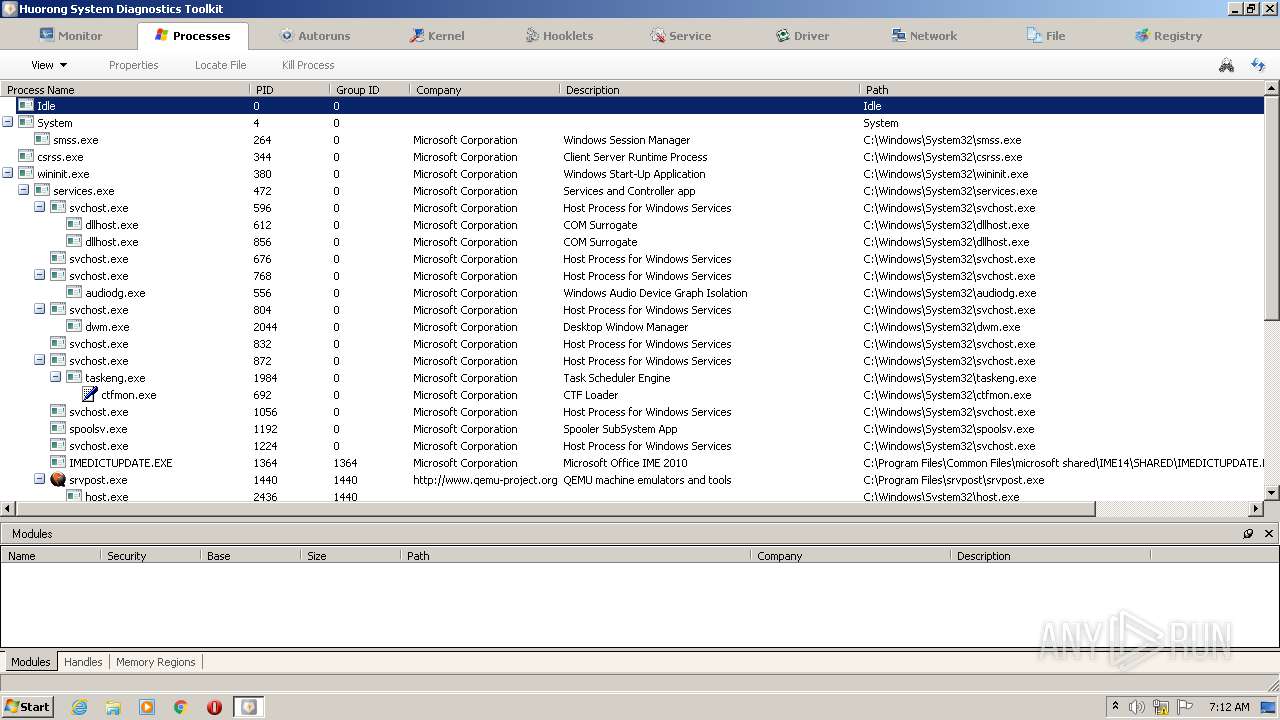
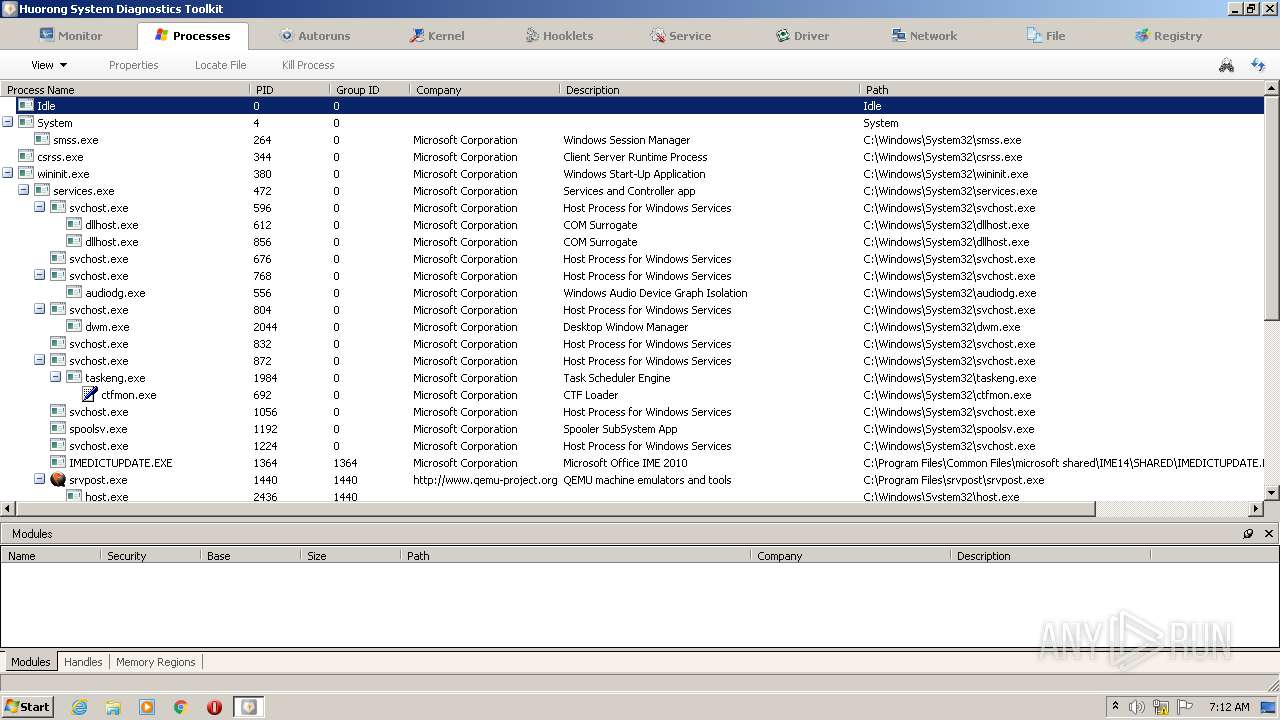
Total processes
101
Monitored processes
57
Malicious processes
7
Suspicious processes
4
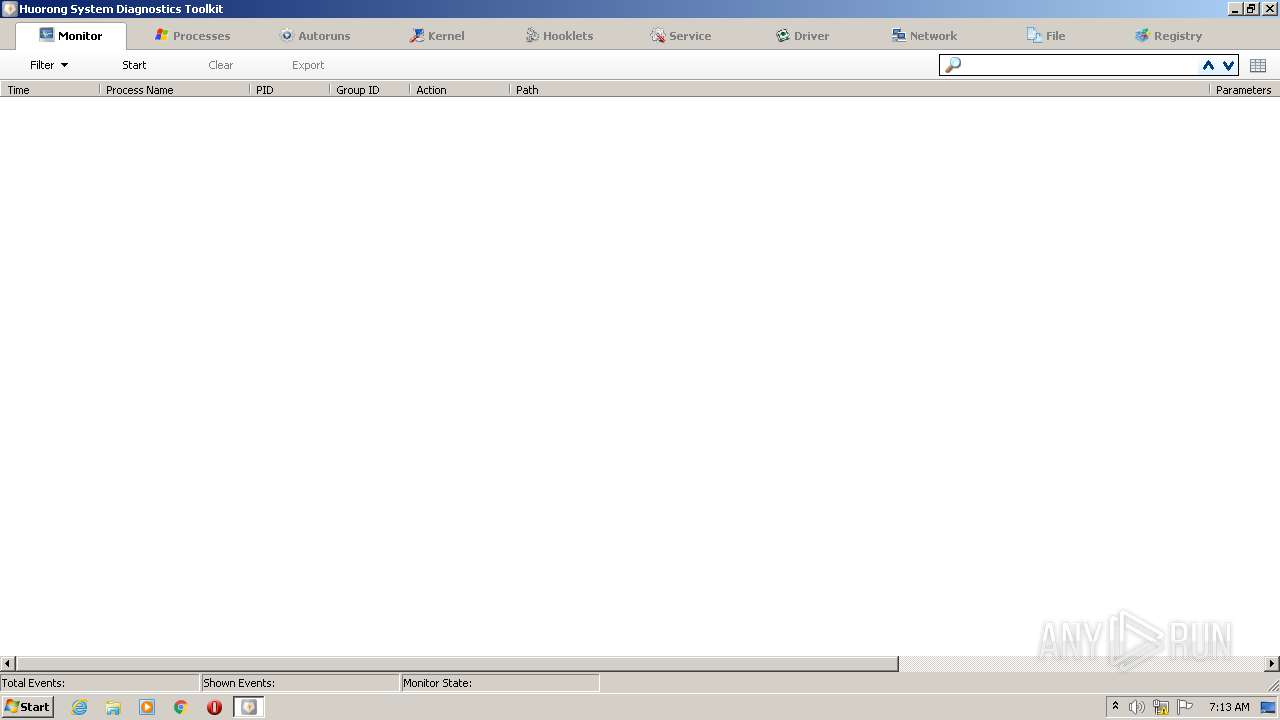
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 292 | reg add "HKLM\SYSTEM\CurrentControlSet\Services\hrwfpdr" /f /v "ImagePath" /t REG_EXPAND_SZ /d "system32\DRIVERS\hrwfpdrv.sys" | C:\Windows\system32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 624 | C:\Windows\system32\cmd.exe /S /D /c" copy Drivers\x32\hrwfpdrv.sys "C:\Windows\System32\drivers\" 1>NUL 2>NUL" | C:\Windows\system32\cmd.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 916 | "C:\Users\admin\AppData\Local\Temp\7ZipSfx.000\usysdiag.exe" 272 | C:\Users\admin\AppData\Local\Temp\7ZipSfx.000\usysdiag.exe | — | HRSword.exe | |||||||||||
User: admin Company: Beijing Huorong Network Technology Co., Ltd. Integrity Level: HIGH Description: Huorong Sysdiag Helper Exit code: 0 Version: 1.0.0.1 Modules
| |||||||||||||||
| 972 | net stop "hrwfpdrv" | C:\Windows\system32\net.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 2 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1236 | sc start sysdiag | C:\Windows\system32\sc.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: A tool to aid in developing services for WindowsNT Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1504 | reg add "HKLM\SYSTEM\CurrentControlSet\Services\sysdiag" /f /v "Start" /t reg_dword /d "1" | C:\Windows\system32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1688 | C:\Windows\system32\cmd.exe /S /D /c" copy Drivers\x32\usysdiag.exe "C:\Users\admin\AppData\Local\Temp\7ZipSfx.000\\" 1>NUL 2>NUL" | C:\Windows\system32\cmd.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1712 | C:\Windows\system32\cmd.exe /S /D /c" copy Drivers\x32\hrwfpdrv.sys "C:\Windows\System32\drivers\" 1>NUL 2>NUL" | C:\Windows\system32\cmd.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1728 | C:\Windows\system32\cmd.exe /S /D /c" echo y" | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1756 | reg delete "HKLM\SYSTEM\CurrentControlSet\Services\hrwfpdr" /f | C:\Windows\system32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 116
Read events
1 067
Write events
46
Delete events
3
Modification events
| (PID) Process: | (3608) HRSword_v5.0.1.1_Sign-20200819.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3608) HRSword_v5.0.1.1_Sign-20200819.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2968) reg.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\sysdiag |
| Operation: | write | Name: | ImagePath |
Value: system32\DRIVERS\sysdiag.sys | |||
| (PID) Process: | (2728) reg.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\hrwfpdr |
| Operation: | write | Name: | ImagePath |
Value: system32\DRIVERS\hrwfpdrv.sys | |||
| (PID) Process: | (1504) reg.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\sysdiag |
| Operation: | write | Name: | Start |
Value: 1 | |||
| (PID) Process: | (4008) reg.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\hrwfpdr |
| Operation: | write | Name: | Start |
Value: 1 | |||
| (PID) Process: | (3648) reg.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\sysdiag |
| Operation: | write | Name: | Group |
Value: PNP_TDI | |||
| (PID) Process: | (4032) reg.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\sysdiag\Instances |
| Operation: | write | Name: | DefaultInstance |
Value: sysdiag | |||
| (PID) Process: | (3348) reg.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\sysdiag\Instances\sysdiag |
| Operation: | write | Name: | Altitude |
Value: 324600 | |||
| (PID) Process: | (3640) reg.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\sysdiag\Instances\sysdiag |
| Operation: | write | Name: | Flags |
Value: 0 | |||
Executable files
30
Suspicious files
0
Text files
2
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2572 | usysdiag.exe | C:\Users\admin\AppData\Local\Temp\Cab546.tmp | — | |
MD5:— | SHA256:— | |||
| 2572 | usysdiag.exe | C:\Users\admin\AppData\Local\Temp\Tar547.tmp | — | |
MD5:— | SHA256:— | |||
| 2572 | usysdiag.exe | C:\Users\admin\AppData\Local\Temp\Cab5D5.tmp | — | |
MD5:— | SHA256:— | |||
| 2572 | usysdiag.exe | C:\Users\admin\AppData\Local\Temp\Cab5D6.tmp | — | |
MD5:— | SHA256:— | |||
| 2572 | usysdiag.exe | C:\Users\admin\AppData\Local\Temp\Cab5D9.tmp | — | |
MD5:— | SHA256:— | |||
| 2572 | usysdiag.exe | C:\Users\admin\AppData\Local\Temp\Cab5EB.tmp | — | |
MD5:— | SHA256:— | |||
| 2572 | usysdiag.exe | C:\Users\admin\AppData\Local\Temp\Tar5D8.tmp | — | |
MD5:— | SHA256:— | |||
| 2572 | usysdiag.exe | C:\Users\admin\AppData\Local\Temp\Tar5DA.tmp | — | |
MD5:— | SHA256:— | |||
| 2572 | usysdiag.exe | C:\Users\admin\AppData\Local\Temp\Tar5EC.tmp | — | |
MD5:— | SHA256:— | |||
| 2572 | usysdiag.exe | C:\Users\admin\AppData\Local\Temp\Tar5D7.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report