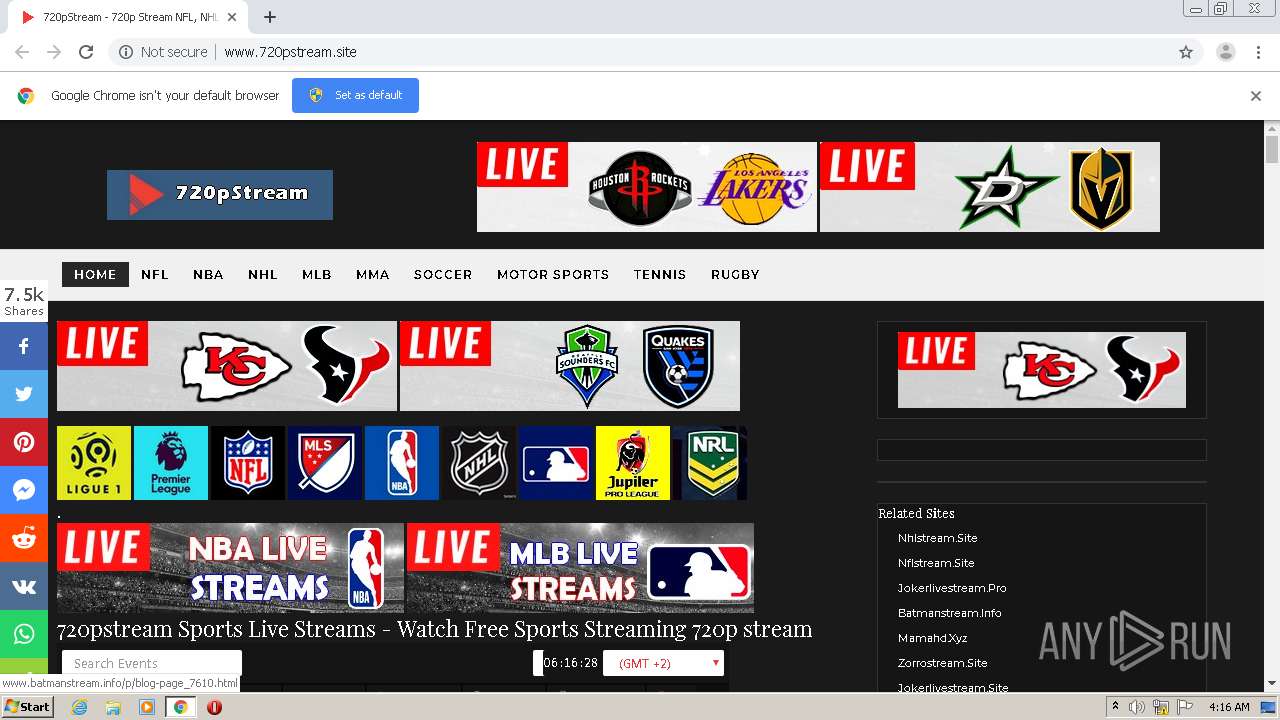
| URL: | http://www.720pstream.site/ |
| Full analysis: | https://app.any.run/tasks/fc1e374b-220c-4f30-aa0b-d47b2f5ef41e |
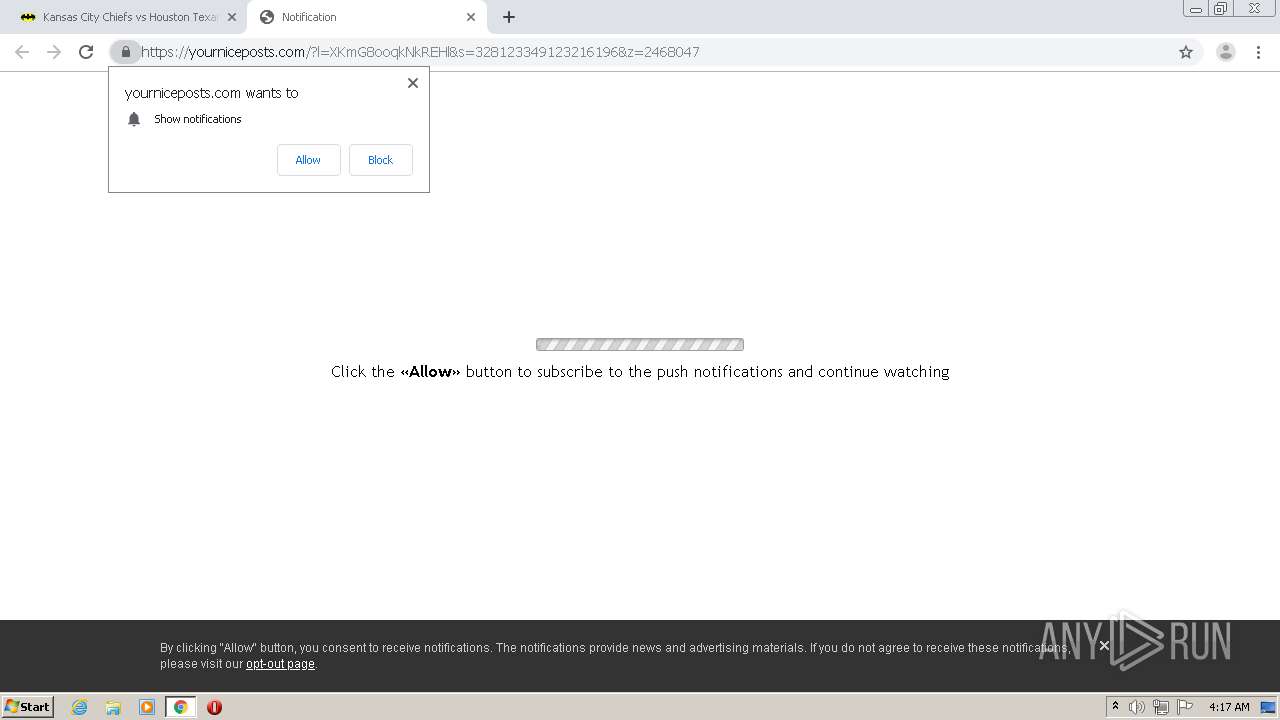
| Verdict: | Malicious activity |
| Analysis date: | September 11, 2020, 03:15:55 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | CF91A786793C9A2B425F49BD263BDDE7 |
| SHA1: | 3E78C0EFCD8477E9BB0D1414F6C274D87EDDB9BF |
| SHA256: | D890C6DA736831E191C0A3EF4AF9835419D93A52DD15DA496BE6A7A8CFF78148 |
| SSDEEP: | 3:N1KJS4kHOK:Cc4cOK |
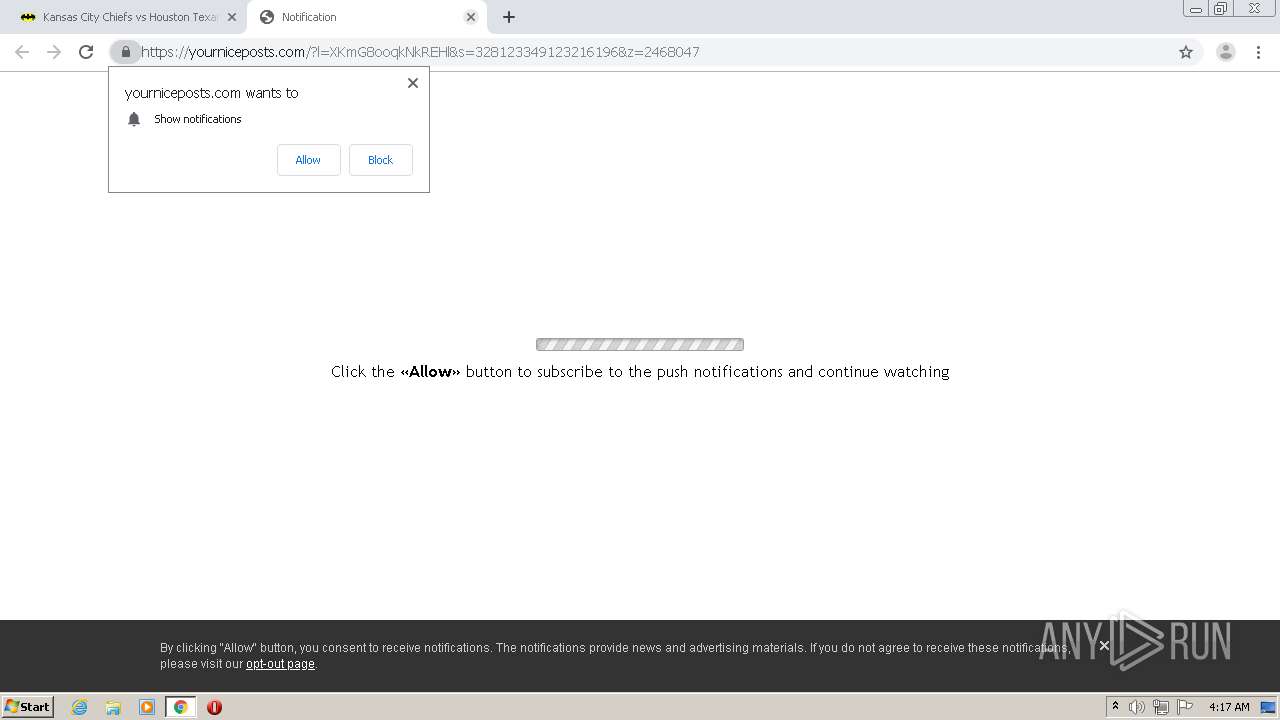
MALICIOUS
No malicious indicators.SUSPICIOUS
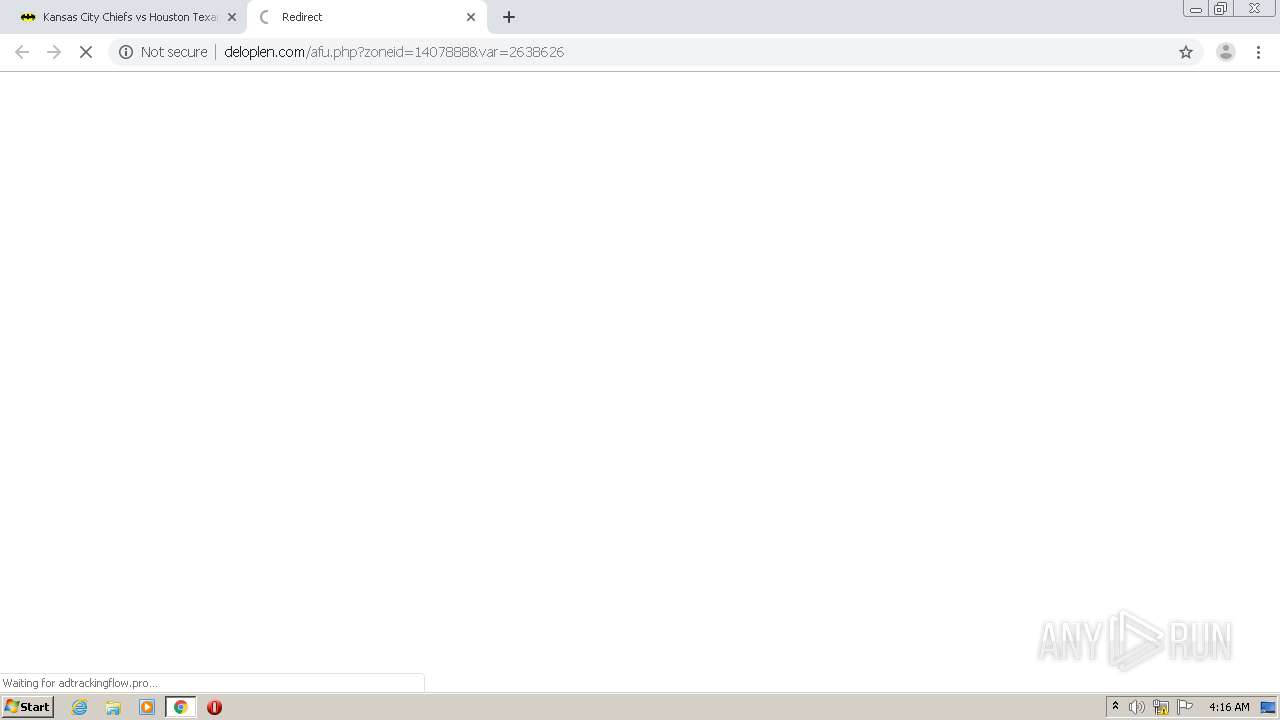
Modifies files in Chrome extension folder
- chrome.exe (PID: 1264)
INFO
Application launched itself
- chrome.exe (PID: 1264)
Reads settings of System Certificates
- chrome.exe (PID: 1520)
Reads the hosts file
- chrome.exe (PID: 1520)
- chrome.exe (PID: 1264)
Creates files in the user directory
- chrome.exe (PID: 1264)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
85
Monitored processes
51
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 180 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1036,3626013050212711342,785210796907590587,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=12898639824071970101 --renderer-client-id=21 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=5068 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1240 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1036,3626013050212711342,785210796907590587,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=17922086887735915567 --renderer-client-id=40 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2092 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1264 | "C:\Program Files\Google\Chrome\Application\chrome.exe" "http://www.720pstream.site/" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1340 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1036,3626013050212711342,785210796907590587,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=14036281823880602713 --renderer-client-id=13 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4456 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1384 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1036,3626013050212711342,785210796907590587,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=6067342068033462877 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2276 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1396 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1036,3626013050212711342,785210796907590587,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=14724240092296707196 --renderer-client-id=31 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4440 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1440 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1036,3626013050212711342,785210796907590587,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=4294549798358400081 --renderer-client-id=26 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4016 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1520 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1036,3626013050212711342,785210796907590587,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=3113743979754806735 --mojo-platform-channel-handle=1648 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1548 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1036,3626013050212711342,785210796907590587,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=17135669488364192801 --renderer-client-id=23 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1336 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1696 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1036,3626013050212711342,785210796907590587,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=2149267810264061603 --renderer-client-id=25 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4388 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
869
Read events
748
Write events
116
Delete events
5
Modification events
| (PID) Process: | (1264) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1264) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (1264) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (1264) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (1264) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2616) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 1264-13244267769560500 |
Value: 259 | |||
| (PID) Process: | (1264) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (1264) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (1264) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 2832-13239195546717773 |
Value: 0 | |||
| (PID) Process: | (1264) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
125
Text files
238
Unknown types
10
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1264 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1264 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\18383a89-62aa-4717-a411-40163e316e3c.tmp | — | |
MD5:— | SHA256:— | |||
| 1264 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000032.dbtmp | — | |
MD5:— | SHA256:— | |||
| 1264 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF207af1.TMP | text | |
MD5:— | SHA256:— | |||
| 1264 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 1264 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF207b00.TMP | text | |
MD5:— | SHA256:— | |||
| 1264 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 1264 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1264 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RF207cc5.TMP | — | |
MD5:— | SHA256:— | |||
| 1264 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
52
TCP/UDP connections
174
DNS requests
122
Threats
10
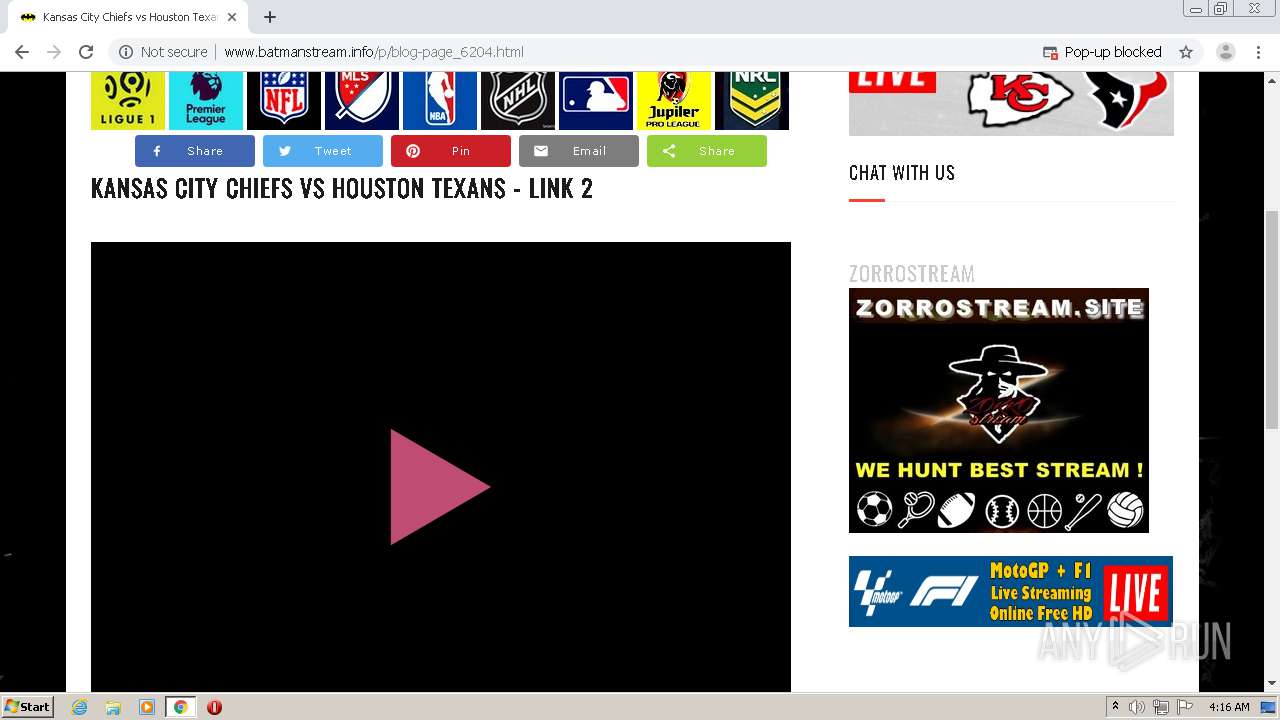
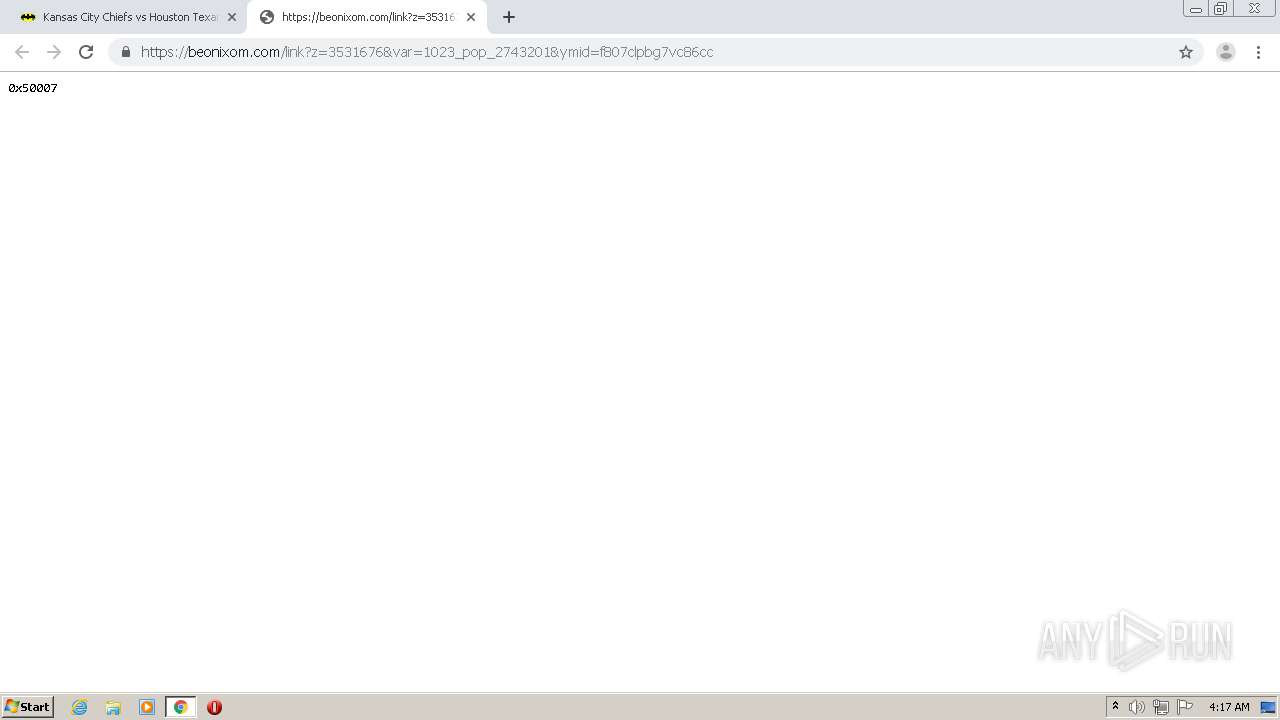
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1520 | chrome.exe | GET | — | 208.93.230.16:80 | http://st.chatango.com/js/gz/emb.js | US | — | — | whitelisted |
1520 | chrome.exe | GET | 204 | 35.190.71.96:80 | http://onclickgenius.com/script/suurl.php?r=3596103&cbrandom=0.9779312387233872&cbiframe=0&cbWidth=1280&cbHeight=572&cbtitle=720pStream%20-%20720p%20Stream%20NFL%2C%20NHL%2C%20NBA%2C%20MLB%20Sports%20Streaming%20Online&cbref=&cbdescription=Watch%20Live%20Stream%20Sport%20and%20TV%20Online%20on%20720pstream%20.%20720pstream%20brings%20Sports%20live%20and%20free%20to%20your%20pc%20and%20mobile.720pstrmss%20live%20stream%20Free%20live%20Sports%20streaming%20online.&cbkeywords=buffstream%2C%20buff%20stream%20live%20stream%2C%20buffstream%20streaming%2C%20MamaHD%20live%20nfl%2C%20buffstreams%20rugby%20live%20stream%2C%20buffstream%20%20live%20tennis%20stream%2C%20live%20football%2C%20live%20handball%2C%20hockey%20live%20stream&cbcdn=acacdn.com | US | — | — | whitelisted |
1520 | chrome.exe | GET | 406 | 18.156.95.187:80 | http://g.ezoic.net/ezoic/ezoiclitedata.go?did=82980 | US | text | 50 b | whitelisted |
1520 | chrome.exe | GET | 200 | 139.45.196.147:80 | http://pushnevis.com/ntfc.php?p=2638624 | US | text | 12.5 Kb | malicious |
1520 | chrome.exe | GET | 200 | 104.31.90.194:80 | http://www.720pstream.site/favicon.ico | US | image | 302 b | malicious |
1520 | chrome.exe | GET | 302 | 172.217.16.174:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWFjQUFXV2lsMkZVdjR5Vk5VZHJTM3E1dw/7919.1028.0.0_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 526 b | whitelisted |
1520 | chrome.exe | GET | 200 | 104.22.53.65:80 | http://www.statcounter.com/counter/counter_xhtml.js | US | text | 12.7 Kb | whitelisted |
1520 | chrome.exe | GET | 200 | 172.217.18.1:80 | http://2.bp.blogspot.com/-0OvlLAjfbww/Wj1KsDA2h-I/AAAAAAAAAZs/nfllX9b9uBAOKShfGjji_SS70wk9XSU_gCK4BGAYYCw/s1600/header-logo%2B%25281%2529.png | US | image | 28.2 Kb | whitelisted |
1520 | chrome.exe | GET | 200 | 74.125.173.168:80 | http://r3---sn-1gieen7e.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWFjQUFXV2lsMkZVdjR5Vk5VZHJTM3E1dw/7919.1028.0.0_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mh=sX&mip=185.212.170.95&mm=28&mn=sn-1gieen7e&ms=nvh&mt=1599794058&mv=m&mvi=3&pl=24&shardbypass=yes | US | crx | 834 Kb | whitelisted |
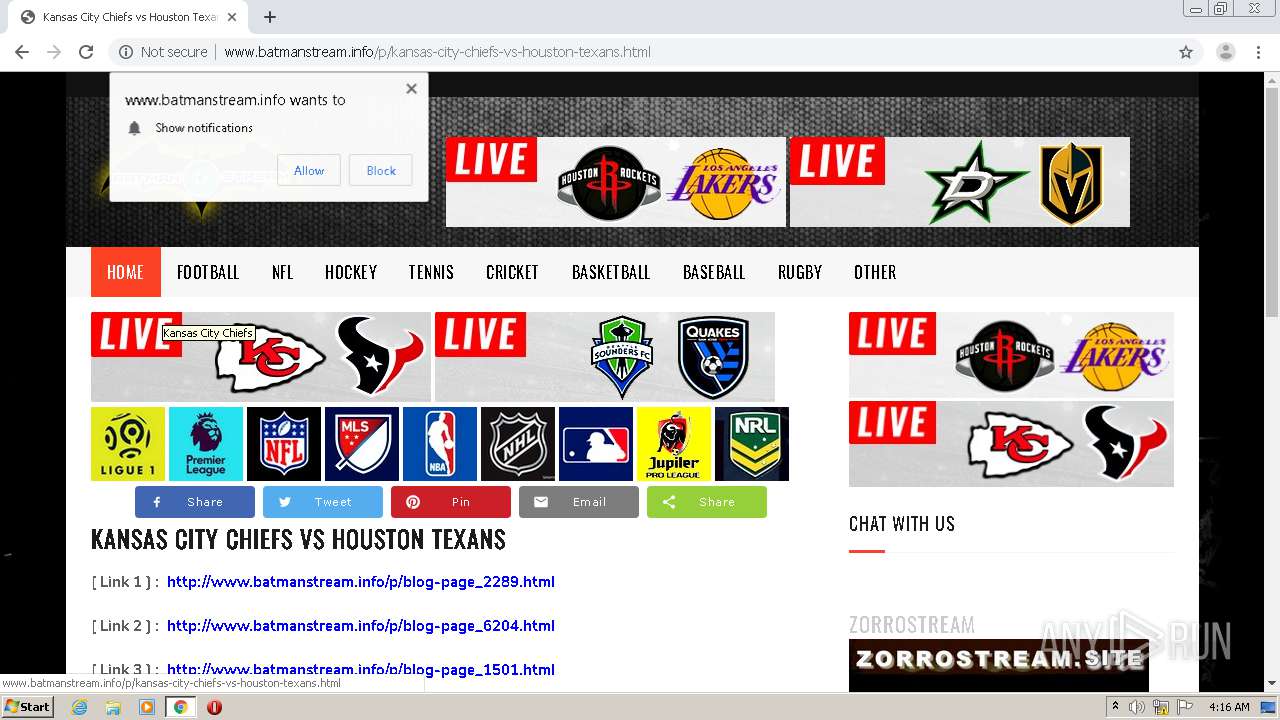
1520 | chrome.exe | GET | 200 | 172.67.162.198:80 | http://www.batmanstream.info/p/kansas-city-chiefs-vs-houston-texans.html | US | html | 85.5 Kb | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1520 | chrome.exe | 143.204.94.55:80 | platform-api.sharethis.com | — | US | unknown |
1520 | chrome.exe | 216.58.208.35:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
1520 | chrome.exe | 209.197.3.15:80 | maxcdn.bootstrapcdn.com | Highwinds Network Group, Inc. | US | whitelisted |
1520 | chrome.exe | 104.31.90.194:80 | www.720pstream.site | Cloudflare Inc | US | shared |
1520 | chrome.exe | 104.22.53.65:443 | www.statcounter.com | Cloudflare Inc | US | suspicious |
1520 | chrome.exe | 216.58.205.237:443 | accounts.google.com | Google Inc. | US | whitelisted |
1520 | chrome.exe | 13.224.193.81:443 | buttons-config.sharethis.com | — | US | suspicious |
1520 | chrome.exe | 216.58.212.142:443 | apis.google.com | Google Inc. | US | whitelisted |
1520 | chrome.exe | 172.217.23.137:443 | www.blogger.com | Google Inc. | US | whitelisted |
1520 | chrome.exe | 172.67.157.64:80 | acdcdn.com | — | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
www.720pstream.site |
| malicious |
accounts.google.com |
| shared |
www.blogger.com |
| shared |
fonts.googleapis.com |
| whitelisted |
maxcdn.bootstrapcdn.com |
| whitelisted |
platform-api.sharethis.com |
| whitelisted |
ajax.googleapis.com |
| whitelisted |
1.bp.blogspot.com |
| whitelisted |
2.bp.blogspot.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1048 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .to TLD |
1048 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .life TLD |
1048 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .life TLD |
1048 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .to TLD |
1520 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Response) |
1520 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Response) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Response) |